February 2026 brought a surge of sophisticated cyber threats targeting businesses across industries. ANY.RUN’s analysts exposed and explored several major cyber threats this month, providing early visibility into emerging malware families and evolving attack techniques.
From new ransomware strains capable of encrypting entire environments in minutes, to fully undetected remote access trojans — the threat landscape this February demands attention from every security team.
Summary for Every Security Team to Focus
- Two new ransomware families, GREENBLOOD and BQTLock, capable of disrupting business operations within minutes and combining encryption with data theft, were identified this month.
- Two new RATs — Moonrise and Karsto — were caught with zero detections on VirusTotal at the time of analysis, illustrating the growing gap between static detection and real-world threats.
- Thread-hijack phishing reached a new level of sophistication, with attackers inserting themselves into real C-suite email conversations to deliver layered credential-theft campaigns using the EvilProxy phishing kit.
- Enterprise phishing infrastructure is now routinely hosted on trusted cloud platforms: Microsoft Azure, Google Firebase, and Cloudflare. This makes URL reputation checks and blocklists increasingly unreliable as standalone defenses.
1. The New Threats Nobody Had Signatures For
ANY.RUN analysts identified four new malicious families in February 2026 — two ransomware strains and two remote access trojans — all of which either evaded static detection entirely or compressed the window for defenders to respond.
GREENBLOOD: Fast Encryption, Evidence Removal, and Immediate Business Exposure
GREENBLOOD is a newly identified Go-based ransomware built for speed, stealth, and pressure. Rather than relying on encryption alone, it combines rapid file locking with self-deletion to reduce forensic visibility, and adds data-leak threats through a TOR-based site — transforming a technical incident into a full business crisis involving downtime, regulatory exposure, reputational damage, and recovery cost.
ANY.RUN’s Interactive Sandbox captured the full attack chain in real time.
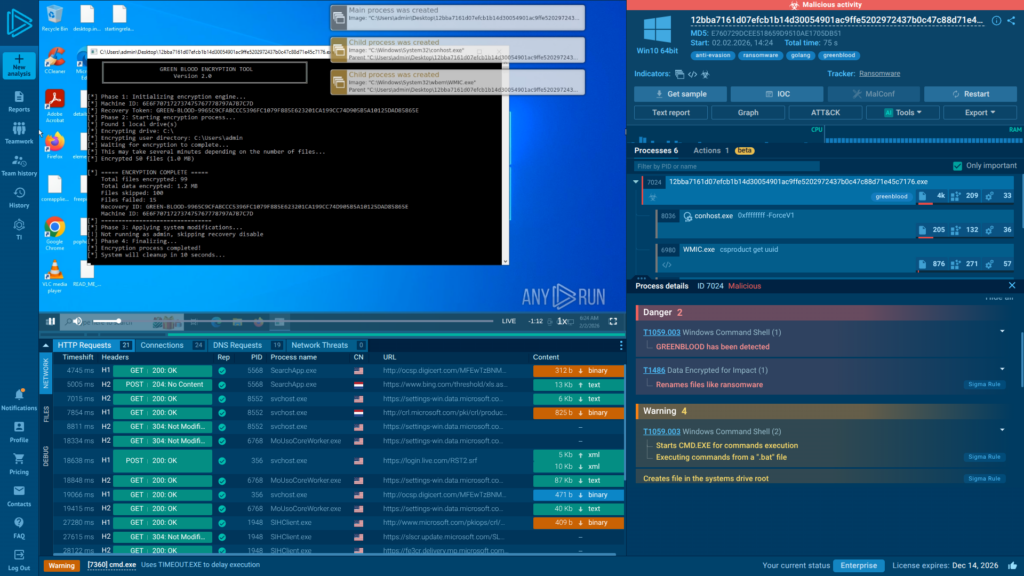
Analysts observed:
• ChaCha8-based encryption capable of disrupting operations within minutes of initial execution.
• Attempts to delete the original executable, limiting post-incident forensic visibility.
• A TOR-based leak site to add extortion leverage beyond file recovery.
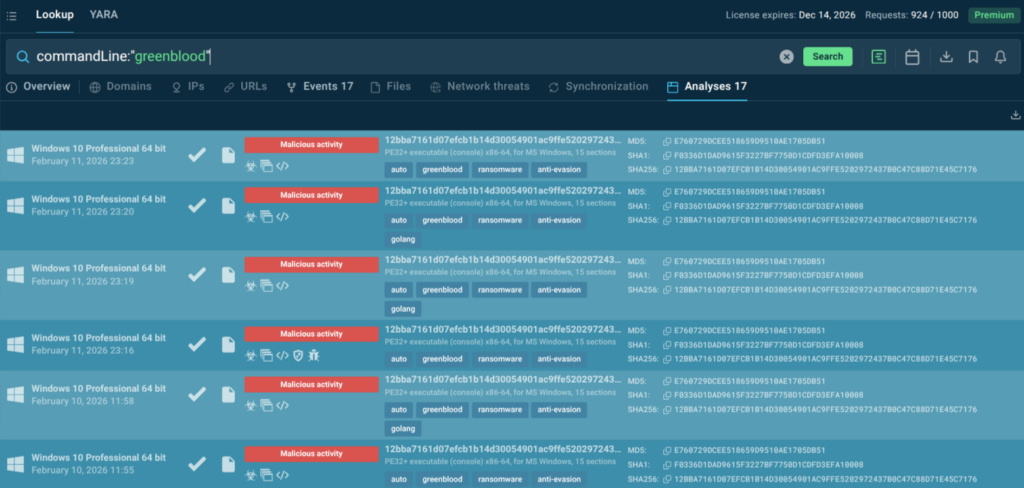
Teams using TI Lookup can search for other GREENBLOOD sample analyses to uncover variants and expand detection coverage across environments:
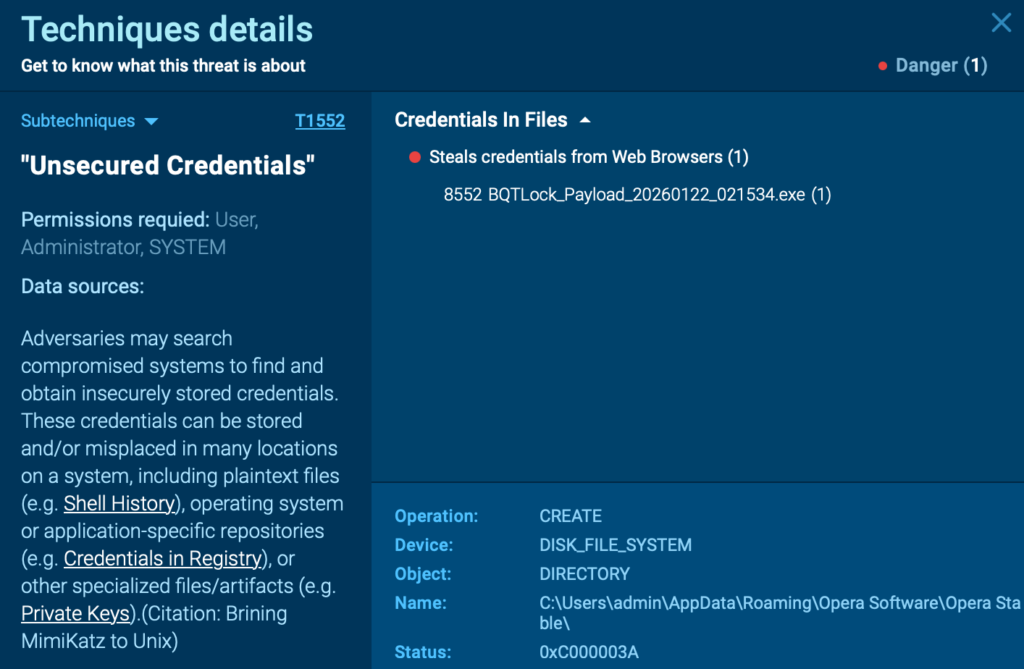
BQTLock: The Ransomware That Steals Your Data Before You Even Know It’s There
BQTLock is a stealthy ransomware-linked chain. Instead of triggering obvious alerts immediately, it blends into trusted Windows processes and delays visible damage — making early detection difficult and increasing the chance of data exposure, operational disruption, and financial loss.
Sandbox detonation revealed the complete kill chain, allowing SOC teams to act on early indicators (process injection, UAC bypass, persistence) before encryption begins.
See the execution chain of BQTLock
BQTLock injects the Remcos payload into explorer.exe, performs UAC bypass via fodhelper.exe, and creates autorun persistence for elevated access after reboot. Only after escalation does it shift to credential theft and screen capture:
This sequence shows how quickly a seemingly quiet infection can evolve into a full security and compliance incident.
Moonrise RAT: Zero Detections, Full Access, Total Silence
Moonrise is a newly discovered Go-based remote access trojan identified and named by ANY.RUN analysts in February 2026. At the time of analysis, the sample had not been submitted to VirusTotal and carried no vendor signatures — meaning it maintained active command-and-control communication while static defenses remained completely silent.
Despite its low detection profile, Moonrise is fully equipped for high-impact operations.
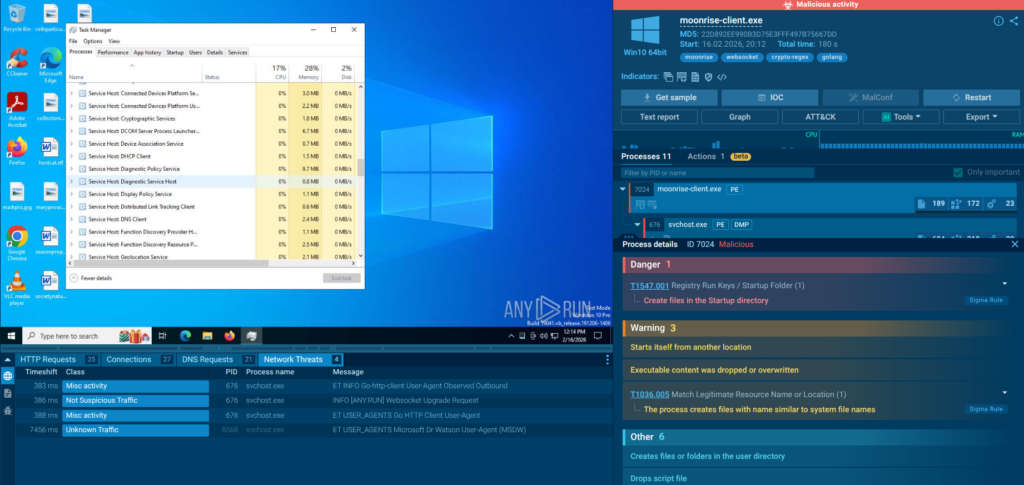
Behavioral analysis confirmed:
• Credential theft targeting stored passwords, authentication tokens, and browser data.
• Remote command execution, process control, and file upload/execution capabilities.
• Persistence mechanisms enabling long-term access even after system reboots.
• Extensive user monitoring: screen capture and streaming, webcam and microphone access, keystroke logging, and clipboard monitoring.
Moonrise’s silent operation extends attacker dwell time, raising the risk of data exfiltration and operational disruption long before any alert is generated. One compromised endpoint can become a pivot point for lateral movement across the entire environment.
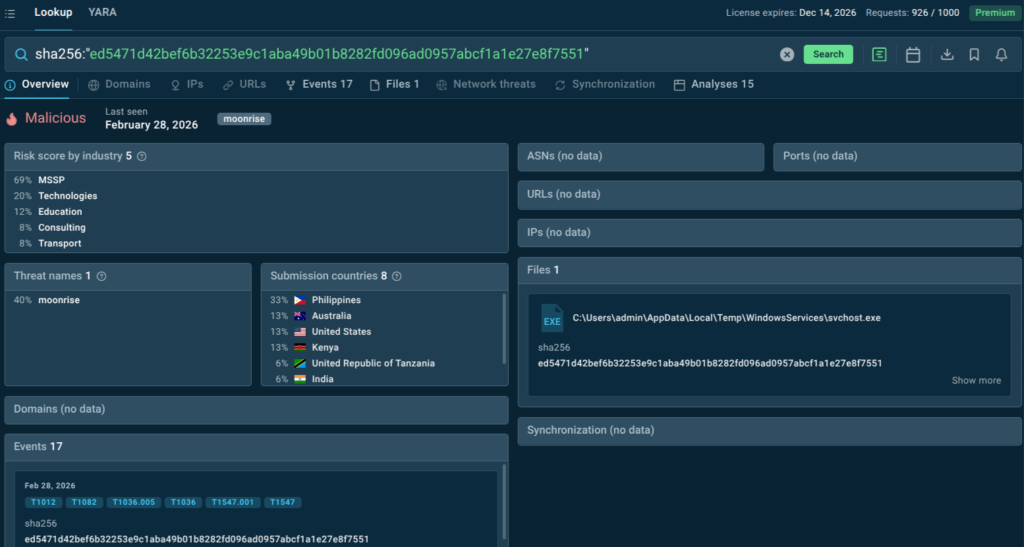
ANY.RUN Threat Intelligence Feeds provide a continuous stream of fresh, validated indicators derived from analysis sessions by 600,000+ security professionals across 15,000+ organizations. For Moonrise specifically, TI Feeds would surface the C2 IP (193[.]23[.]199[.]88) and associated file hashes before your internal systems encounter them, allowing defensive infrastructure to block the threat at the perimeter rather than detect it post-compromise.
Threat Intelligence Lookup, in its turn, allows analysts to instantly pivot on any observable indicator. A hash, IP, domain, or URL can be cross-referenced against the ANY.RUN database to retrieve related sandbox analyses, historical sightings, linked infrastructure, and associated malware families.
sha256:”ed5471d42bef6b32253e9c1aba49b01b8282fd096ad0957abcf1a1e27e8f7551″
Karsto RAT: It Profiles Your Organization Then Attacks
Karsto RAT is another newly identified malware family caught by ANY.RUN analysts this February with zero detections on VirusTotal at the time of discovery. Its modular architecture combined with built-in victim profiling capabilities allows attackers to map target environments before deciding which follow-on actions to take.
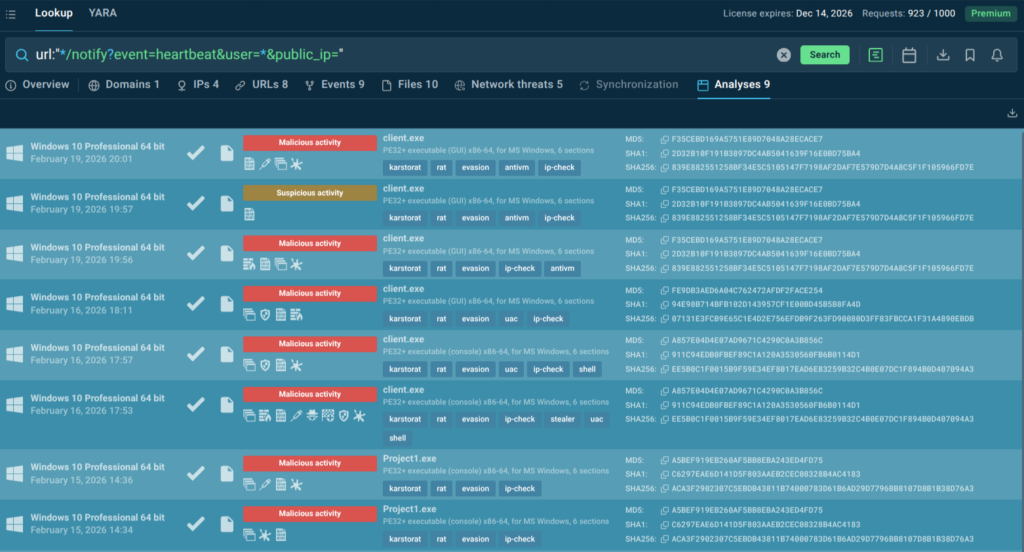
Karsto disguises its C2 traffic to blend with legitimate-looking network communication, significantly reducing the chance of detection by network monitoring tools. The malware checks the victim’s external IP via api[.]ipify[.]org and maintains heartbeat and logging endpoints with its C2. This behavior suggests selective activation of certain modules based on country, network, or public IP.
Functionally, the RAT combines surveillance and remote control: it steals credentials and tokens, logs keystrokes and clipboard data, executes remote commands, uploads payloads, and exfiltrates files, while also capturing screenshots, webcam, and audio activity on the infected host.
Like Moonrise, Karsto reinforces a critical lesson: waiting for antivirus vendors to flag a sample before taking action is no longer a viable strategy. Both RATs were capable, persistent, and actively harmful before any signatures existed. Behavior-based sandbox analysis remains the only reliable method to detect such threats at the earliest possible stage.
See sample execution in a live analysis session
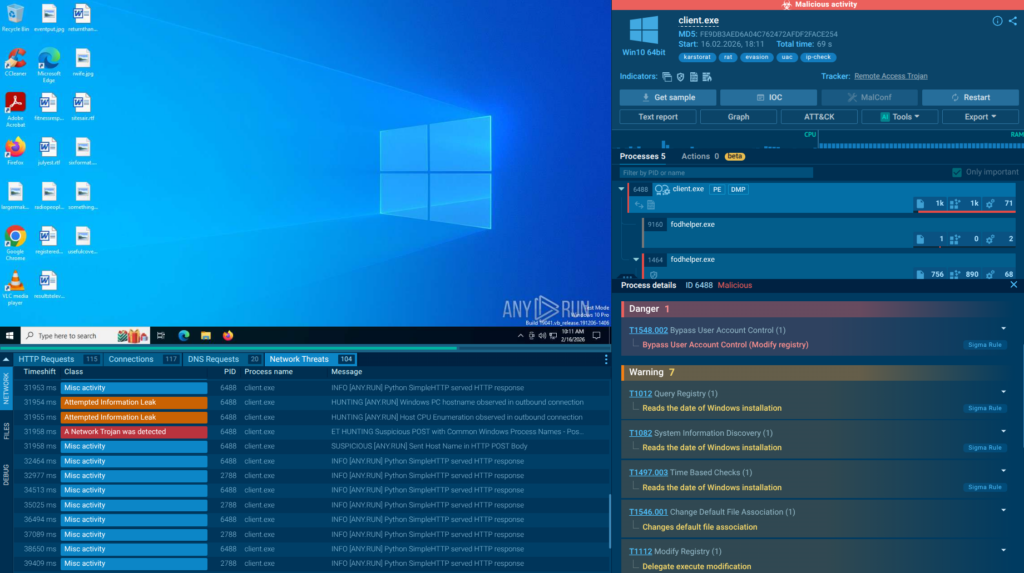
TI Lookup can be used to proactively track evolving attacks by behavioral traces:
url:”/notify?event=heartbeat&user=&public_ip=”
2. The Playbooks Your Defenses Weren’t Built For
Beyond new malware, February 2026 saw threat actors pushing the boundaries of phishing sophistication. The three trends below represent a fundamental shift in how attackers approach enterprise credential theft — moving from noisy, easily filtered attacks to highly targeted, trust-abusing campaigns hidden behind infrastructure defenders have historically considered safe.
Thread-Hijack Phishing: When the Trap Arrives Inside a Real Conversation
ANY.RUN analysts uncovered a sophisticated supply chain phishing campaign in which attackers hijacked an ongoing email thread among C-suite executives discussing a document awaiting final approval. The threat actor has likely compromised a contractor mailbox already involved in the conversation and posed as a legitimate participant replying directly with a phishing link mimicking a Microsoft authentication form.
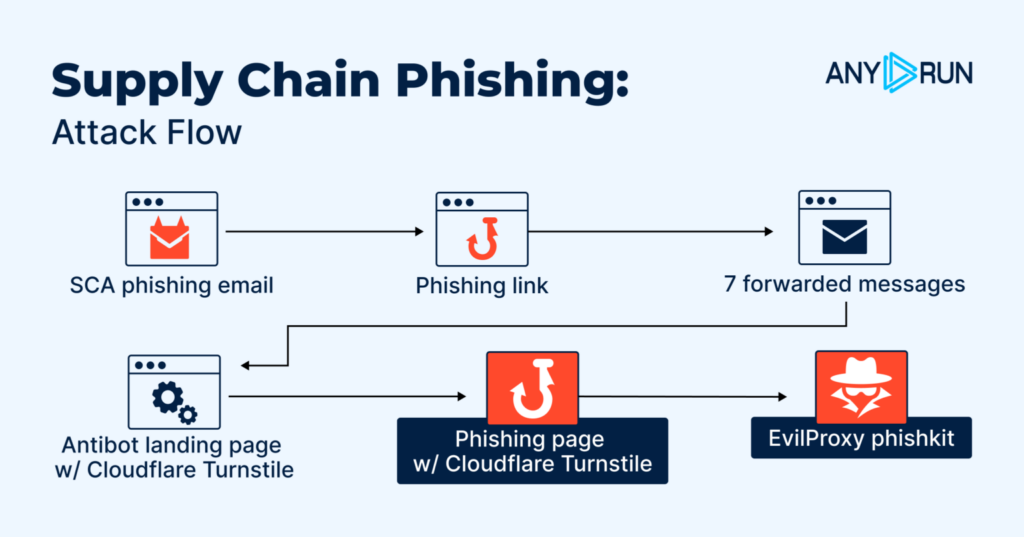
A supply chain phishing email triggered seven forwarded messages, building plausibility through internal forwarding chains. Recipients then encountered a Cloudflare Turnstile anti-bot page, a Turnstile-protected phishing page, and finally the EvilProxy adversary-in-the-middle kit — which captured Microsoft credentials and session tokens in real time.
What makes thread-hijack attacks particularly dangerous is their inherent credibility. The email arrives within a real, trusted business conversation, not as a cold phishing lure. There are no suspicious sender addresses, no typosquatted domains in the thread body, and no obvious red flags for email security gateways to catch.
The only reliable detection method is safe behavioral detonation of links at the time of delivery.
The business impact of a successful thread-hijack attack is severe: compromised executive credentials can give attackers access to sensitive communications, financial approval workflows, and cloud environments.
Using TI Lookup, analysts were able to pivot from this incident to a broader EvilProxy campaign active since early December 2025, primarily targeting organizations in the Middle East. Lookup results highlight the countries the malware campaigns are targeting lately, and what industries and sectors are reporting most detections recently.
domainName:”bctcontractors.com$” OR domainName:”himsanam.com$”
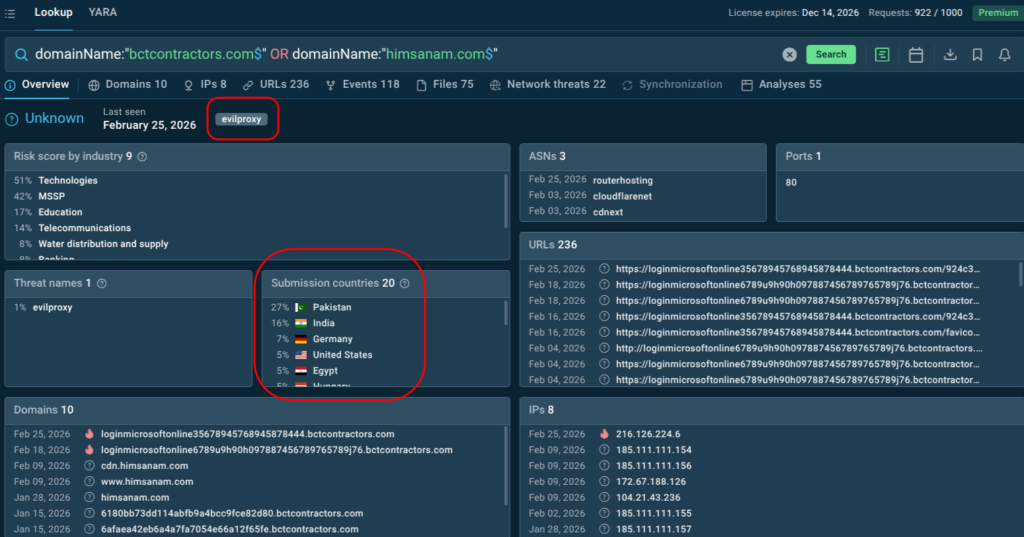
Compromised executive credentials can give attackers access to sensitive communications, financial approval workflows, and cloud environments. Detecting these attacks early requires solutions that can safely follow the full redirect chain and expose the phishing page behavior in seconds.
Hiding in Plain Sight: How Phishing Kits Moved Into Microsoft and Google’s Backyard
Another major trend identified by ANY.RUN this February is the systematic migration of phishing kit infrastructure onto legitimate cloud and CDN platforms. Rather than hosting credential-theft pages on newly registered domains which are quickly flagged and blocked, attackers are now deploying phishing content directly on Microsoft Azure Blob Storage, Google Firebase Storage, AWS CloudFront, and behind Cloudflare CDN.
Live examples can be explored using Threat Intelligence Lookup with queries like these:
threatName:”sneaky2fa” AND destinationIpAsn:”cloudflarenet”
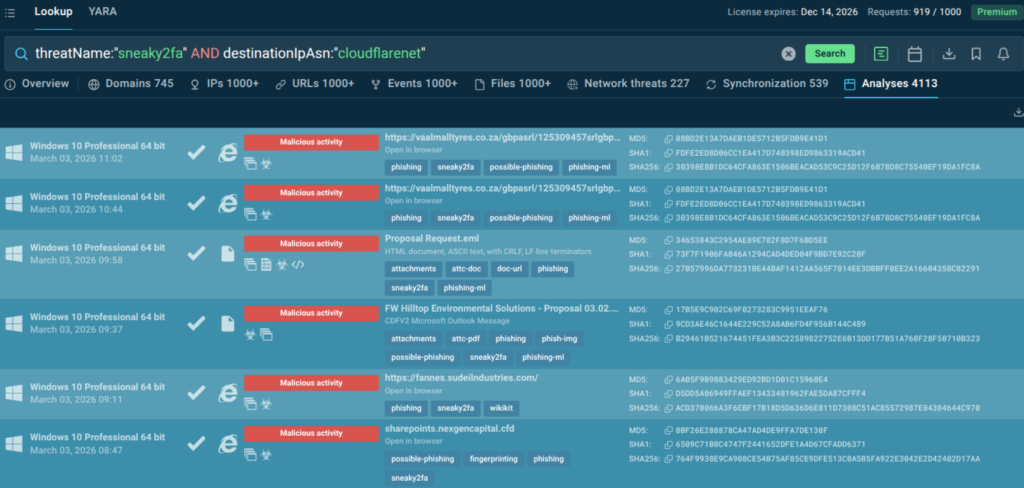
For defenders, this shift creates a major blind spot. Network traffic monitoring sees trusted cloud infrastructure, valid HTTPS certificates, and recognized ASN ranges. The origin server where the malicious content actually lives is hidden behind Cloudflare’s reverse proxy, making it impossible to block based on IP or domain reputation alone.
The three most active phishing kits exploiting this technique are:
- Tycoon2FA, primarily abusing Microsoft Azure infrastructure;
- Sneaky2FA, commonly hosted on Google Firebase Storage and specifically designed to filter out personal email addresses in favor of corporate targets;
- EvilProxy, which uses similar cloud infrastructure in executive account takeover campaigns.
This trend represents a fundamental challenge for organizations that rely on URL reputation databases and domain blocklists as primary phishing defenses. When the hosting infrastructure is indistinguishable from legitimate Microsoft or Google services, static detection fails. ANY.RUN’s TI Lookup enables teams to search for specific behavioral patterns — such as Sneaky2FA threats targeting Cloudflare ASNs — to stay ahead of campaigns that would otherwise appear clean.
The Phishing Kit That Evolves Faster Than Your Defenses
Tycoon 2FA, one of the most active Phishing-as-a-Service platforms designed to bypass multi-factor authentication by intercepting session cookies in real time, continued its rapid development cycle into February 2026.
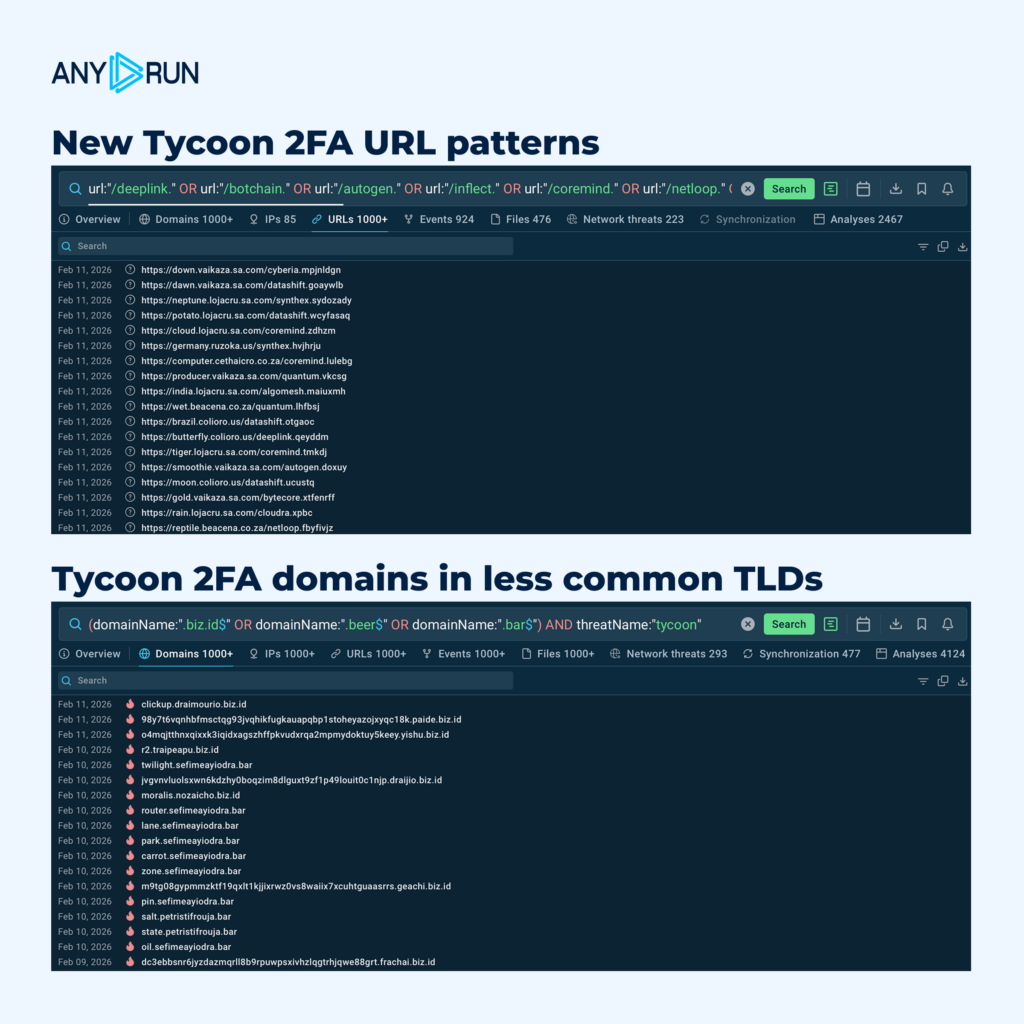
ANY.RUN’s experts are seeing new URL patterns tied to the phishkit campaigns, along with a spike in phishing domains in less common TLDs like .biz.id, .beer, and .bar.
From a business risk perspective, Tycoon 2FA’s ongoing evolution is significant for two reasons. First, it demonstrates that MFA is no longer a reliable last line of defense — by capturing session cookies at the moment of authentication, Tycoon 2FA renders most MFA implementations ineffective. Second, its PhaaS model means low-skill actors can access industrial-grade phishing infrastructure, enabling campaigns at a scale previously requiring significant technical capability.
For threat hunters, the challenge is validating patterns against real attacker behavior. Hunting breaks down when detections are built on isolated IOCs without execution context.
SOC teams use ANY.RUN’s TI Lookup to pivot from indicators to full attack context, uncovering recurring URL patterns, infrastructure reuse, and related artifacts across real sandbox sessions.
Use these search queries to explore updated Tycoon 2FA infrastructure, validate your hypotheses, and prioritize alerts by your industry & region:
Faster Threats, Higher Stakes: Protecting What Your Business Can’t Afford to Lose
The threats documented in February 2026 share something common: they are designed to defeat the tools and assumptions that most enterprise security programs still rely on. Signature-based antivirus misses zero-detection RATs. URL blocklists fail against cloud-hosted phishing. MFA is bypassed by adversary-in-the-middle kits. Email gateways cannot flag a reply within a real executive conversation.
For security teams and business leaders, the practical implications are clear. Speed matters most: GREENBLOOD can encrypt an environment in minutes, and BQTLock’s stealth setup phase is the narrowest window for containment. Static checks are no longer sufficient: Moonrise and Karsto both operated without any vendor signatures, meaning organizations that rely only on antivirus are flying blind. And infrastructure trust cannot be assumed: when Microsoft Azure and Google Firebase are used to host credential-theft pages, traditional reputation-based defenses have no reliable signal to act on.
Detect Evasive Threats with the Interactive Sandbox
ANY.RUN’s Sandbox enables security teams to detonate suspicious files and URLs in a safe, controlled environment and observe real behavior as it unfolds. For the threats documented this month, this means:
- confirming whether a suspicious link completes a full credential-theft redirect chain in under 60 seconds;
- observing ransomware encryption, self-deletion, and persistence behavior before it reaches production systems;
- identifying C2 communication from RATs that would pass signature-based checks without any flags.
Pivot IOCs and Enrich Them with Context
TI Lookup extends this capability into proactive threat hunting. Rather than waiting for an alert to arrive, analysts can query the database using behavioral indicators (command lines, TTPs, process behaviors, network connections, JA3 fingerprints, and more) to discover whether similar threats have appeared in other environments, identify campaign infrastructure before it targets the organization, and enrich alert triage with context that cuts investigation time significantly.
Expand Threat Coverage with TI Feeds
ANY.RUN’s Threat Intelligence Feeds deliver continuously updated IOCs and behavioral indicators extracted from millions of real sandbox analysis sessions directly into SIEM and EDR platforms.
Together, these solutions create a continuous intelligence cycle that supports every stage of the security workflow: safe detonation and behavior confirmation at Tier 1, deep campaign investigation and pivot analysis at Tier 2, and proactive hunting and detection engineering at Tier 3.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, integrates seamlessly into modern SOC operations and supports investigations from the first alert through containment and detection improvement.
Security teams use ANY.RUN’s Sandbox to safely execute suspicious files and URLs, observe real behavior in controlled environments, extract actionable indicators, and enrich findings instantly through TI Lookup and Threat Intelligence Feeds. This unified approach reduces uncertainty, improves validation accuracy, and strengthens response consistency across the organization.
Today, more than 600,000 security professionals across 15,000+ organizations rely on ANY.RUN to accelerate investigations, enhance detection resilience, and stay ahead of evolving phishing and malware campaigns.





0 comments