Reaching a higher level of SOC maturity takes better, more consistent decision-making during malware and phishing investigation.
This requires a shift in how threat intelligence is used: not as a reference point, but as a core layer in the decision process.
Moving from reactive to confidently proactive security means establishing a threat intelligence workflow that:
- Solves key challenges, from alert fatigue to blind spots
- Integrates across SOC workflows, supporting them
- Delivers compounding value as a unified system
In this model, threat intelligence becomes part of the SOC’s operational fabric. That’s what ANY.RUN Threat Intelligence is designed for.
It becomes a layer inside your SOC’s operations. A layer that provides behavioral context, workflow support, and data delivery for faster triage, incident response, and threat hunting.
Read further to see how it changes each stage of your SOC operations.
Key takeaways
- Threat intelligence must move from data to decisions, as its value is measured by how it improves SOC actions, not how much data it provides.
- Context is the differentiator. Linking IOCs to behavior and TTPs is what enables accurate triage and detection.
- Unified TI drives consistency in SOC teams, embedding intelligence across workflows.
- Operationalized TI compounds over time. Every investigation strengthens detection, automation, and future response.
- ANY.RUN’s threat intelligence is built on live attack data that provides unique, real-time visibility into emerging threats and supports the full investigation cycle.
Solving Key SOC Challenges with Behavioral TI
Most threat intelligence today is still delivered as bare indicator feeds, standalone reports, or enrichment tools with fragmented intelligences that exist outside the core SOC workflow.
In this model, threat intelligence behaves as an input, not as part of the system itself. Indicators without context create noise. Context without operationalization creates friction. As a direct outcome, SOCs struggle with:
- Time-consuming manual enrichment
- Operational bottlenecks across processes
- Detection that gets delayed by the lack of fresh data
Human-centered challenges in SOC teams are often not analysts’ fault either. Alert fatigue and unnecessary escalations stem from fragmented, hard-to-access threat data that fails to deliver usable context during investigations.
The path to improvement lies in acquiring actionable threat intelligence that operationalizes SOC tasks and completes the workflow, supporting the entire investigation cycle.
Threat Intelligence That Offers More than Just Indicators
What SOC teams require is actionable intelligence that supports decisions and execution, enabling analysts to move from enrichment to understanding, and from understanding to detection and rapid response.
Where traditional TI may fail because of its fragmented, add-on nature, actionable threat intelligence encompasses the entire malware and phishing investigation cycle by:
- Connecting indicators to behavior (processes, command lines, network activity, registry changes)
- Providing immediate context for triage decisions
- Translating findings into detections and hunting hypotheses
- Continuously feeding SOC pipelines (SIEM, SOAR, EDR)
- Remaining relevant through real-time, fresh data
- Supporting both automation and analyst-driven workflows
This is threat intelligence that doesn’t exist beside your SOC, but an essential operational layer within it that turns repetitive work into a scalable workflow where each detection enhances overall security and proactive protection from similar threats in the future.
A key differentiator of effective threat intelligence is its foundation in live, real-world attack activity.
ANY.RUN Threat Intelligence is built on continuously analyzed data from over 15,000 organizations and 600,000 analysts conducting daily malware and phishing investigations worldwide. This creates a unique, constantly evolving dataset of active threats processed and validated to minimize noise.
Operational Impact of Actionable Threat Intelligence
| For analysts | Less manual work, faster understanding of threats, confident decisions during triage and investigation |
| For SOC leaders | Improved detection quality, reduced dwell time; consistent, predictable operations across teams |
| For CISOs | Lower risk exposure, better visibility into threats and coverage gaps; stronger confidence in security effectiveness and ROI |
ANY.RUN’s TI As an Operational Layer in Your SOC
ANY.RUN’s approach to behavioral threat intelligence is built around the idea of treating it not as a dataset but as an operational layer that connects context and action across the SOC lifecycle.
This approach reframes TI from a passive resource into an active component of the SOC system that:
1. Links Isolated IOCs to malware behavior and TTPs via TI Lookup
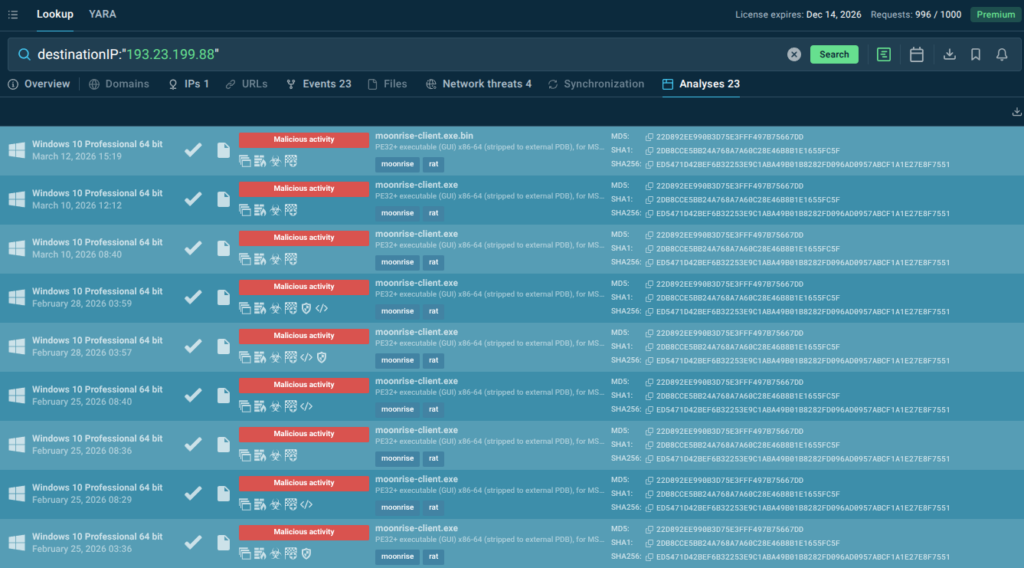
Instead of treating indicators as isolated data points, with Threat Intelligence Lookup (TI Lookup), a solution for instant enrichment and threat research, analysts immediately see how they behave in real attacks. Any artifact (IP, domain, hash, or URL) is enriched with execution context, infrastructure relationships, and associated TTPs.
This allows teams to move from “what is this?” to “how does this operate?” within seconds, improving triage quality and enabling faster, more confident decisions.
2. Embeds context directly into triage and response
Whether through integrations or manual use, threat intelligence from ANY.RUN becomes a part of the SOC investigation cycle that supports early detection and smart decisions.
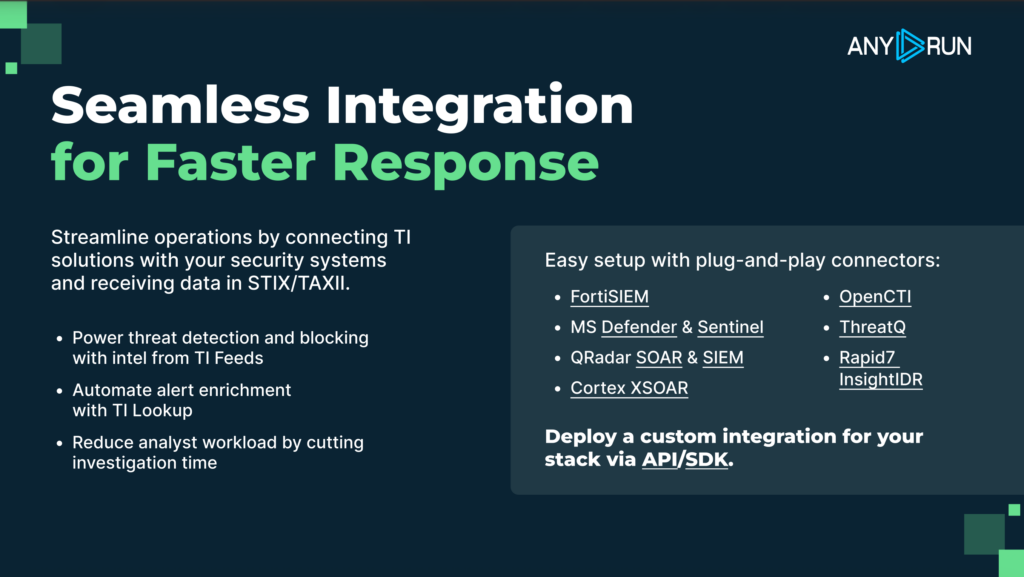
- Threat Intelligence Lookup and Threat Intelligence Feeds are available for integration via connectors or API/SDK. See all integrations
3. Enables conversion of intelligence into detections via YARA Search
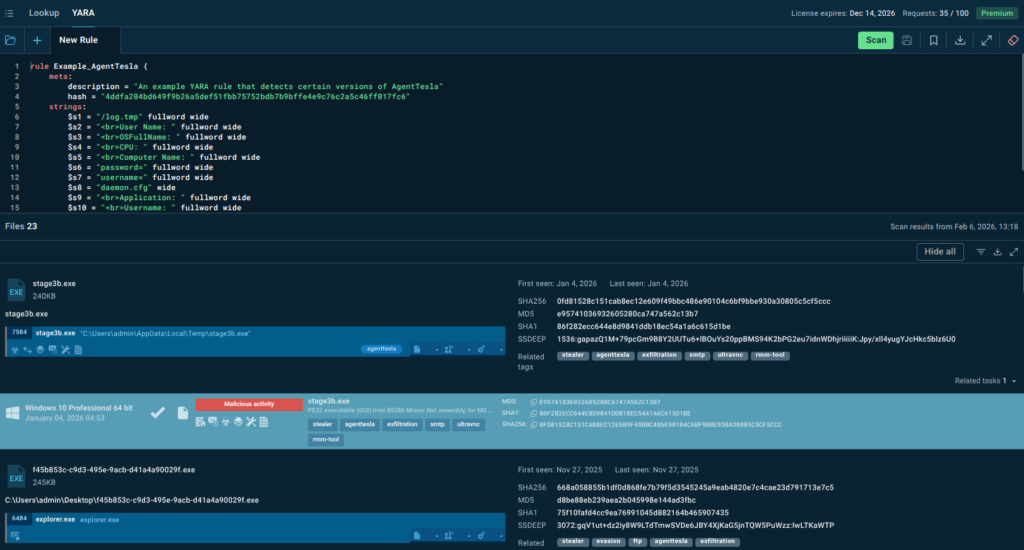
Threat intelligence becomes particularly valuable when it directly translates into detections. YARA Search enables that by helping analysts test, refine, validate, and create YARA rules to ensure coverage of relevant threats with reduced false positives.
The result is more reliable detections and greater confidence in security controls.
4. Delivers continuous, real-time intelligence streams via TI Feeds
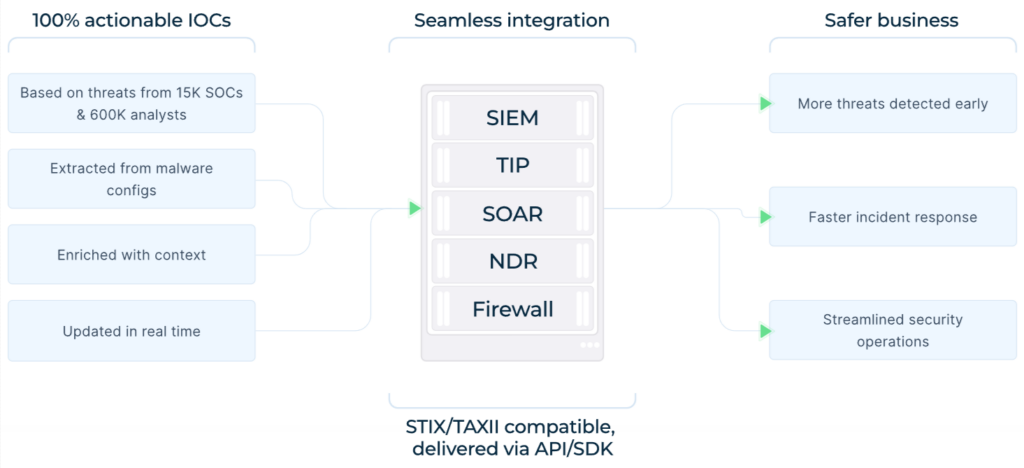
Threat Intelligence Feeds are continuously delivered into existing security pipelines rather than accessed on demand, and that’s how real-time, validated indicators sourced from live attack data flow directly into SIEM, SOAR, and EDR systems, supporting automated detection, correlation, and response.
This reduces manual workload, improves alert quality, and lowers dwell time.
5. Fills visibility gaps with TI Reports
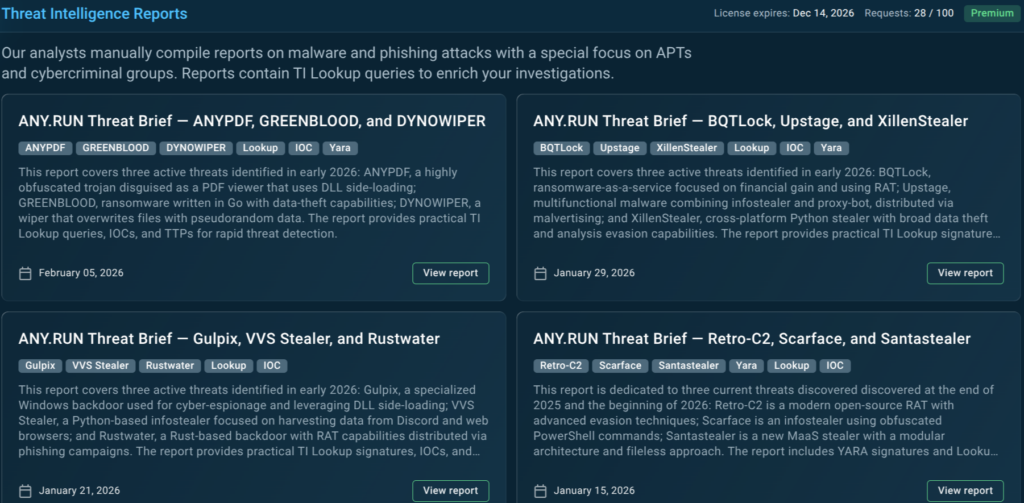
ANY.RUN TI Reports address the partial visibility challenge in SOC teams by providing threat overviews curated by our experts, turning analyst-driven insights into strategic intelligence with threat behaviors, TTPs, and detection opportunities already described and contextualized.
This enables teams to quickly understand emerging risks, validate their coverage, and identify blind spots without investing additional investigation time.
Threat Intelligence Across Processes and Outcomes
ANY.RUN Threat Intelligence’s goal is not to improve a single step, but to encompass the entire operational cycle.
| SOC Process | ANY.RUN’s Threat Intelligence Action | Outcomes |
|---|---|---|
| Triage and Alert Enrichment | Centralized validation of indicators with immediate context and prioritization; scalability for teams of any size and secure integration | Faster triage, reduced manual enrichment, fewer unnecessary escalations, improved MTTR and FP rate |
| Threat Hunting & Detection Engineering | Behavior-driven search with access to real attack data and analyses; supports conversion of findings into detections | Proactive threat discovery, stronger and more consistent detections, elimination of repetitive work |
| Incident Response | Immediate access to unified threat context across incidents, enabling consistent investigation and decision-making | Faster response, reduced dwell time, lower operational risk |
| SOC Management & Performance | Continuous, real-time intelligence aligned with current threats; visibility into threat landscape and coverage gaps | Improved MTTD/MTTR,measurable SOC performance, clearer ROI, and risk reduction |
Conclusion
High-performing SOCs are defined by how effectively threat intelligence is integrated into their operations.
When threat intelligence components operate as a unified system rather than isolated capabilities, they stop being tools and become part of the SOC’s operational infrastructure.
In this model, Threat Intelligence is:
- a unified, behavior-driven intelligence layer;
- a continuous link from indicators to behavior and from detection to automation;
- a real-time stream of relevant, active threat data;
- embedded across triage, incident response, threat hunting, detection, and management.
About ANY.RUN
ANY.RUN provides interactive malware analysis and behavior-driven threat intelligence solutions designed to support real-world SOC operations. The platform enables security teams to understand threats faster, make informed decisions, and operationalize intelligence across detection and response workflows.
Used by over 15,000 organizations and 600,000 security professionals worldwide, ANY.RUN delivers continuously updated intelligence based on live attack analysis. The company is SOC 2 Type II certified, ensuring strong security controls and protection of customer data.
FAQ
ANY.RUN Threat Intelligence features TI Lookup, TI Feeds, TI Reports, and YARA Search as a unified, behavior-driven intelligence layer that connects indicators with malware behavior, TTPs, and artifacts—supporting decision-making across SOC workflows.
Traditional feeds primarily deliver indicators. ANY.RUN’s TI provides context, behavioral analysis, and enables conversion into detections, while continuously integrating into SOC processes.
It is built on real-time analysis data from over 15,000 organizations and 600,000 analysts conducting malware and phishing investigations worldwide.
By reducing manual enrichment, accelerating triage and response, improving detection quality, and enabling more consistent, data-driven decisions.
Yes. It is designed to be used both manually by analysts and automatically via integrations with SIEM, SOAR, EDR, and other platforms.
By providing early visibility into emerging threats, improving detection coverage, and shortening the time between threat emergence and response.






0 comments