As part of a recent live expert panel, ANY.RUN together with threat researcher and ethical hacker Mauro Eldritch explored biggest security risks companies should be prepared for in 2026.
The discussion covered several relevant cases, from the Lazarus IT Workers operation to the rapid rise of AI-driven phishing attacks, and examined the common thread behind them: trust abuse.
Below are the key takeaways for those seeking a clearer view of modern cyber risks and how to prepare as a SOC leader.
Watch the full panel on our YouTube channel
Key Takeaways
- Trust abuse is becoming a primary attack vector, driven by AI-powered phishing and identity-based infiltration.
- Attacks increasingly lack clear indicators, making detection difficult for traditional SOC workflows.
- Focus on early detection through behavioral visibility, context, and process-based security.
- Combine sandbox analysis, threat intelligence, and contextual enrichment for faster, more accurate decisions.
Trust Abuse: Top Business Risk for 2026
In 2026, many cyberattacks don’t look like attacks at all. Instead of exploiting technical vulnerabilities, threat actors increasingly exploit human trust. This tactic is known as trust abuse, and it’s what many modern cyber threats are based on.
Businesses inevitably rely on trust between employees, systems, vendors, and partners. Without it, organizations cannot operate efficiently. Threat actors know what, so they’ve learnt to mimic legitimate identities, infiltrate communication channels and everyday workflows, and turn employees into unwitting entry points.
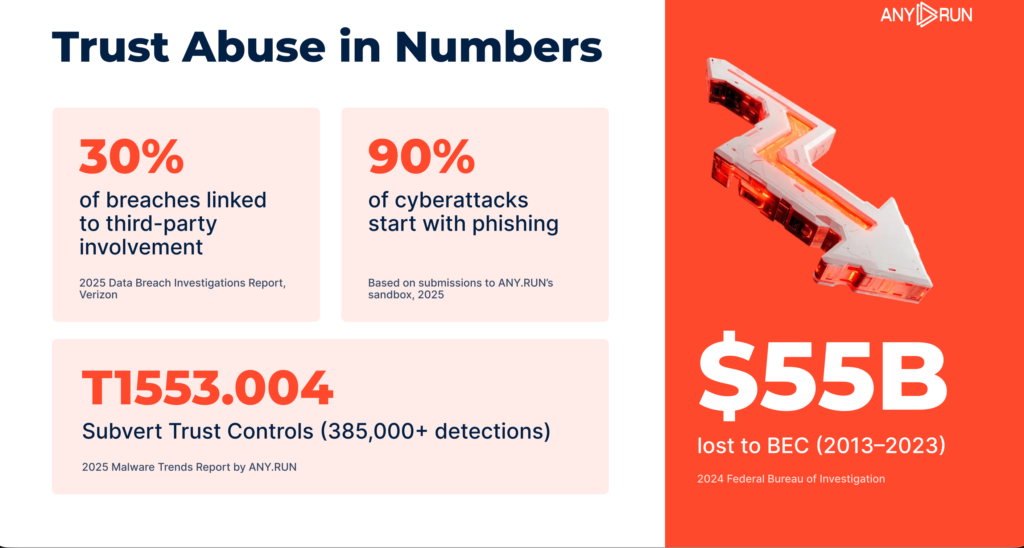
AI-assisted social engineering pushes trust abuse even further. These attacks closely resemble legitimate activity and often fail to trigger traditional alerts. For security leaders, this changes how risk must be understood.
Risk mitigation is no longer only about patching vulnerabilities or strengthening perimeter defenses. Detecting trust abuse requires visibility into behavior, context, and how trust moves inside the enterprise.
Case #1: Implications of Lazarus APT Infiltration
Lazarus, a North-Korean state-sponsored threat actor, has shifted its tactics. Instead of relying only on malware, the group infiltrates Western and Middle Eastern companies to conduct corporate espionage.
The scheme was investigated by Mauro Eldritch and Heiner García from NorthScan inside ANY.RUN’s controlled infrastructure. The researchers were able to trap the attackers in a sandbox environment and observe their activity while the threat actors believed they had gained access to a corporate network.
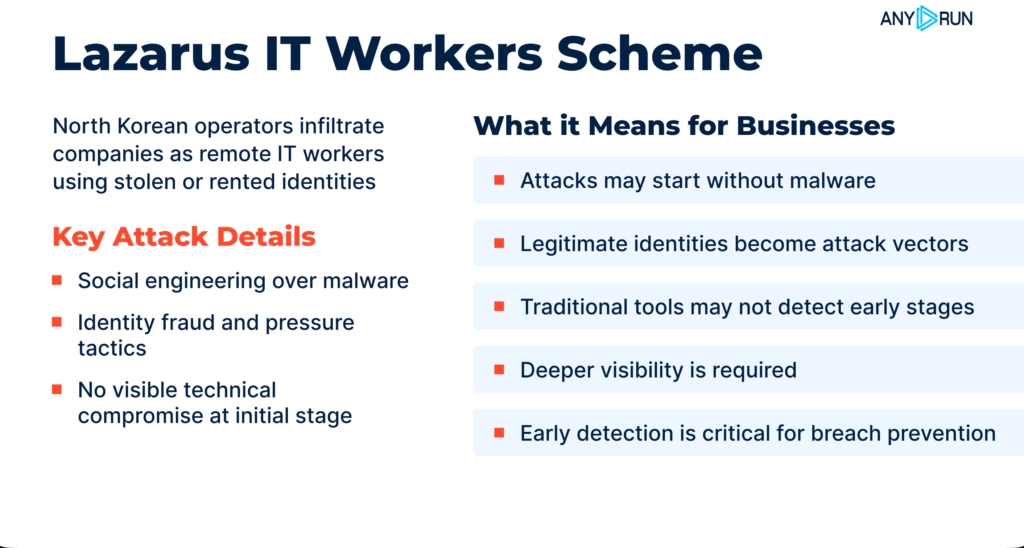
Lazarus operation is a vivid example of trust abuse in a business environment. No advanced malware was involved in the attack initially. Because of that, the potential implications for the victims can be catastrophic. Attacks like that don’t trigger alerts; there’s simply nothing suspicious to detect.
This is why, unlike short-lived malware campaigns, trust-based infiltrations can persist much longer. Once attackers gain access, they may embed themselves deeper in the organization or even place additional operatives inside the company.
ANY.RUN exposed this campaign before the broader market. The investigation was conducted entirely within our controlled infrastructure, which allowed researchers to observe attacker behavior in real time.
Read more on Lazarus case investigation supported by ANY.RUN
But most companies do not have the resources to monitor suspicious activity at this level.
In practice, risk mitigation depends on the ability to detect and interpret unusual behavior early, before it escalates into a full incident. Trust abuse attacks make early visibility and detection critical for enterprise security.
Case #2: Modern AI-Powered Phishing

Phishing attacks today look very different from the obvious scam emails many people are used to spotting. With AI-assisted tools, threat actors can now mimic completely normal email conversations, using polished language and highly personalized content.
AI makes these attacks both believable and scalable. The core vulnerability here is human trust, which becomes an easy entry point for attackers.
Modern phishing campaigns increasingly focus less on technical exploits and more on manipulating communication chains and legitimate domains that employees already trust.
As a result, traditional security tools are often left with no clear indicators of compromise to detect. These attacks blend into normal business communication, making them much harder to identify before damage occurs.
Building a SOC That Prevents Trust Abuse Attacks
To address this challenge, modern security requires a layered approach. Early detection does not depend on a single tool but on a set of coordinated processes. In particular, effective defense relies on three core SOC activities: monitoring, triage, and threat hunting.
Traditional security tools are important to have, but they aren’t universal. Unless they can show what happens after a user interacts with a suspicious file, link, or attachment, organizations may lack the full visibility needed to understand the threat. This gap leaves companies vulnerable to increasingly evasive attack techniques.
ANY.RUN helps strengthen these processes by providing greater visibility, faster investigations, and reliable threat context.
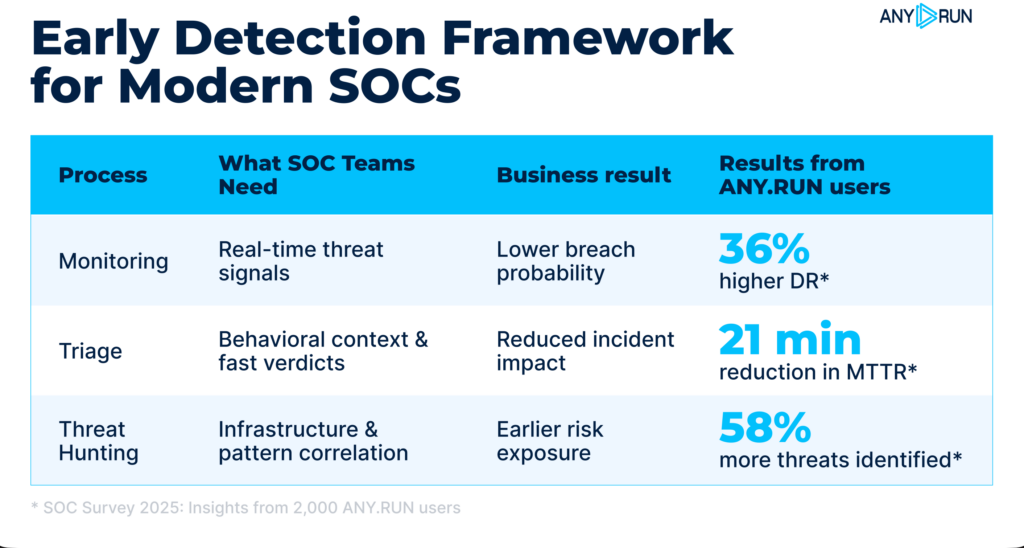
Monitoring: Detecting Threats Early
Effective monitoring helps identify threats before they reach internal systems, preventing breaches. ANY.RUN enhances monitoring by enabling teams to:
- Detect emerging threats early: By tapping into real-time intelligence from live attack data from 15K companies
- Maintain focus: Get only relevant signals through curated, high-confidence data
- Reduce alert noise: Gain continuous visibility and instant IOC enrichment drives confident decision-making
Rapid Triage: Understanding Alerts Faster
Triage is critical for handling high alert volumes and avoiding delays in response. ANY.RUN helps streamline triage by allowing teams to:
- Cut investigation time with rapid, interactive sandboxing for files and URLs providing in-depth view of behavioral activity.
- Reduce escalations with behavioral and contextual insight that enrich alerts for confident decisions by Tier-1 analysts.
- Lower operational costs by avoiding tool sprawl while delivering context-rich visibility into threats.
Threat Hunting: Identifying Patterns Proactively
Threat hunting focuses on uncovering patterns and anticipating attacker behavior. ANY.RUN supports proactive hunting by enabling teams to:
- Get early warning signs: Analysts can easily correlate indicators, infrastructure, and historical activity.
- Research and monitor trends: Identify relationships between campaigns, industries, regions, and threat actors.
- Explore TTPs: Detect reused techniques and infrastructure to build clearer profiles of attacker behavior.
By strengthening these three processes, organizations can achieve earlier detection, faster response, and more efficient SOC operations, reducing the risk of modern, trust-based attacks.
Conclusion
Enterprise cyber threats are shifting toward identity-based and trust-driven attacks. Campaigns like Lazarus and AI-powered phishing show that attackers no longer rely solely on malware or exploits.
For decision-makers, this means rethinking how risk is assessed and how security operations are structured. Visibility, context, and speed are becoming critical factors in effective defense.
Organizations that adapt their SOC processes to these realities will be better positioned to detect threats early and prevent incidents before they escalate.
About ANY.RUN
ANY.RUN delivers interactive malware analysis and actionable threat intelligence trusted by more than 15,000 organizations and 600,000 security analysts worldwide.
Interactive Sandbox, Threat Intelligence Lookup, and Threat Intelligence Feeds help SOC and MSSP teams analyze threats faster, investigate incidents with deeper context, and detect emerging attacks earlier.
ANY.RUN meets enterprise security and compliance expectations. The company is SOC 2 Type II certified, reinforcing its commitment to protecting customer data and maintaining strong security controls.




0 comments