Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


MicroStealer is a rapidly emerging infostealer first prominently observed in late 2025. It specializes in stealing browser credentials, active session data, screenshots, cryptocurrency wallets, and system information. It spreads quickly with low detection rates thanks to a sophisticated multi-stage delivery chain and exfiltrates data via Discord webhooks and attacker-controlled servers.
|
Stealer
Type
:
|
Unknown
Origin
:
|
|
1 December, 2025
First seen
:
|
13 May, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 December, 2025
First seen
:
|
13 May, 2026
Last seen
:
|

 6206
6206
 0
0

 5793
5793
 0
0

 8565
8565
 0
0
 Malware overview in TI Lookup: landscape, IOCs, and more
Malware overview in TI Lookup: landscape, IOCs, and more
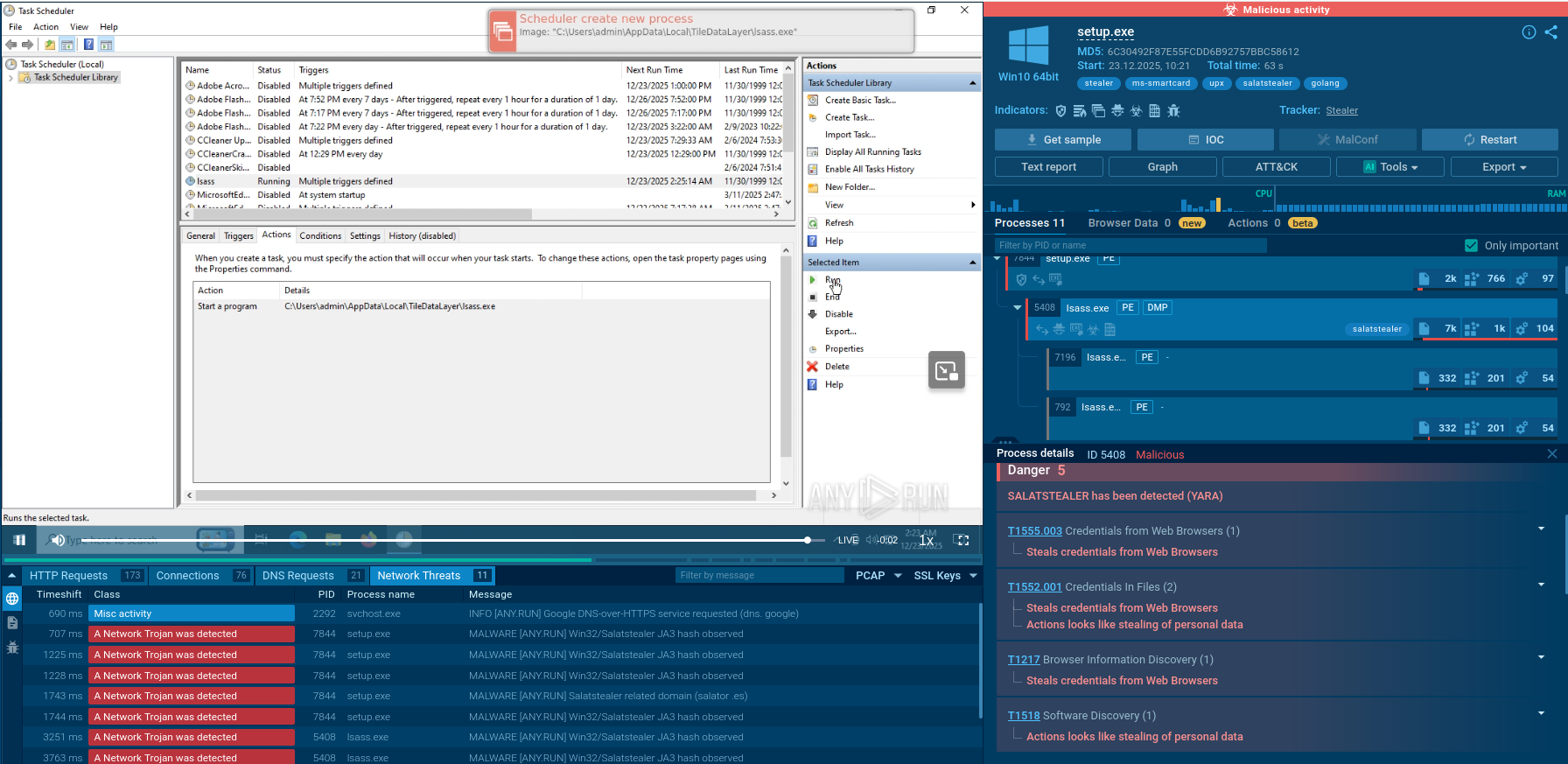
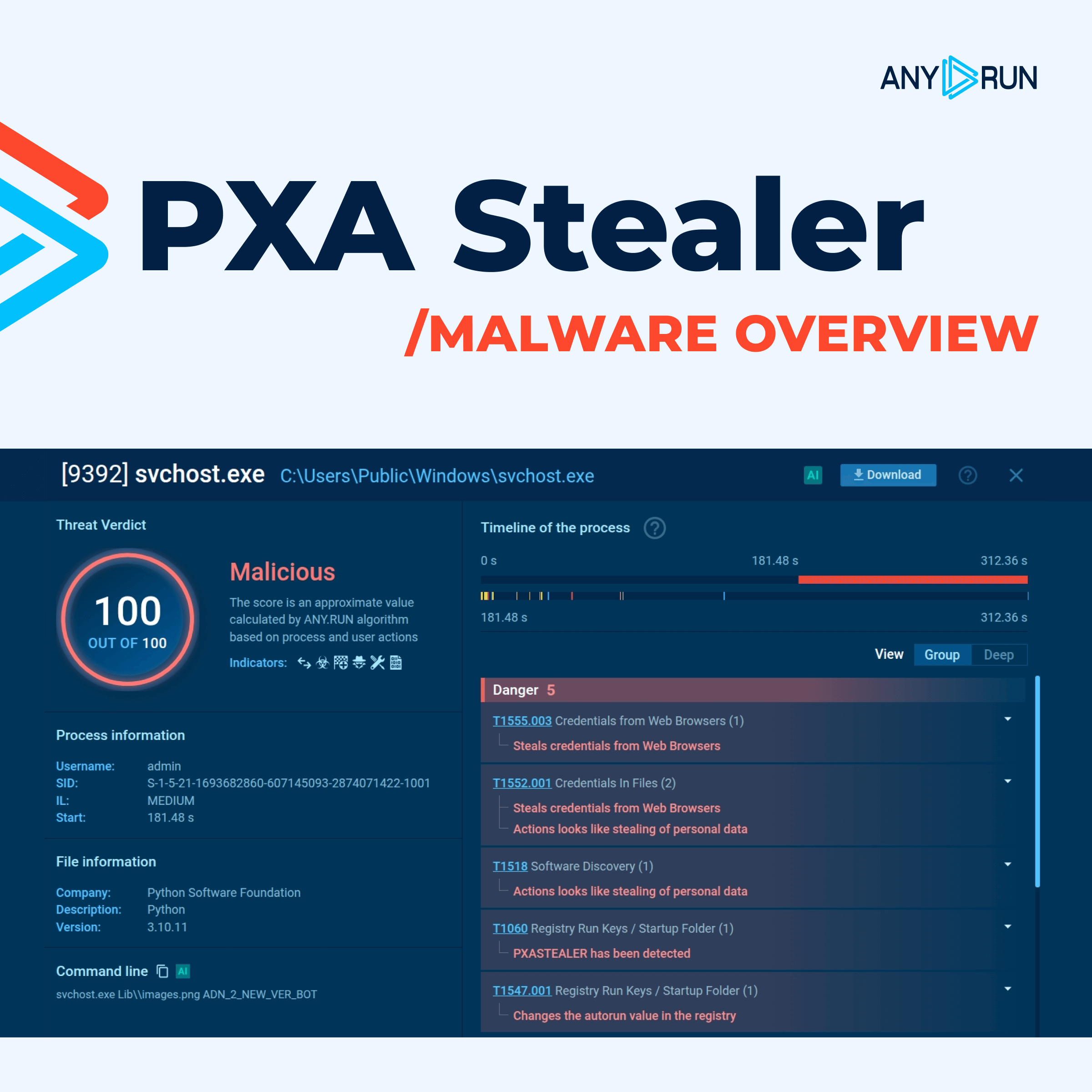
MicroStealer is an emerging infostealer malware that quietly targets browser credentials, session cookies, desktop screenshots, and cryptocurrency wallet files; all while evading traditional signature-based detection. First observed in December 2025, it gained rapid traction in sandbox environments within weeks of appearing in the wild, yet many security vendors still failed to flag it.
Its deceptively sophisticated architecture — wrapping a Java-based payload inside an Electron application inside an NSIS installer — makes it harder to analyze statically and gives it an edge during the critical early window of a campaign.
MicroStealer is not just another entry in a crowded field: it represents a new wave of professionally engineered infostealers designed to infiltrate corporate environments and exfiltrate identity data before defenders even know to look.
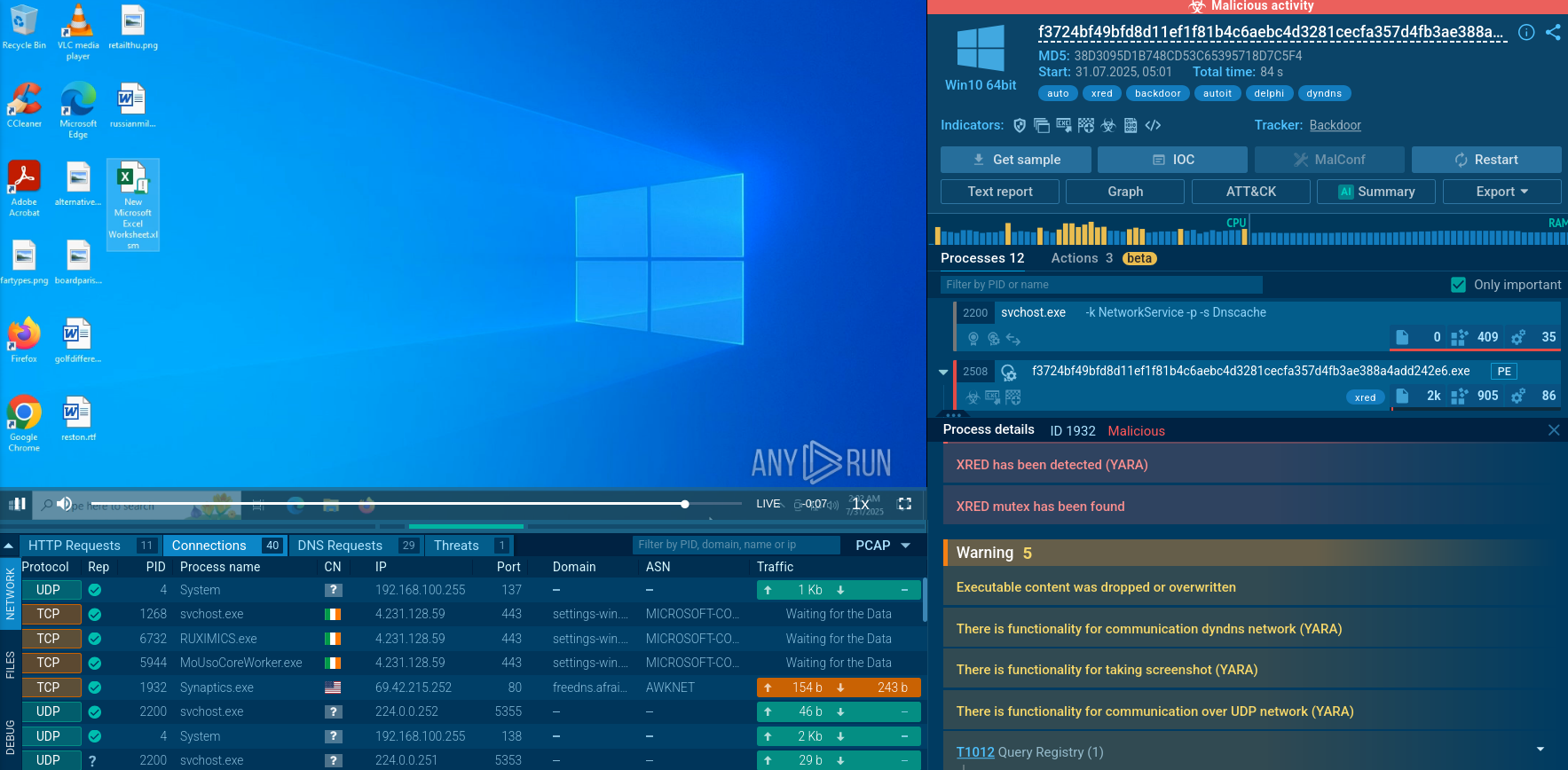
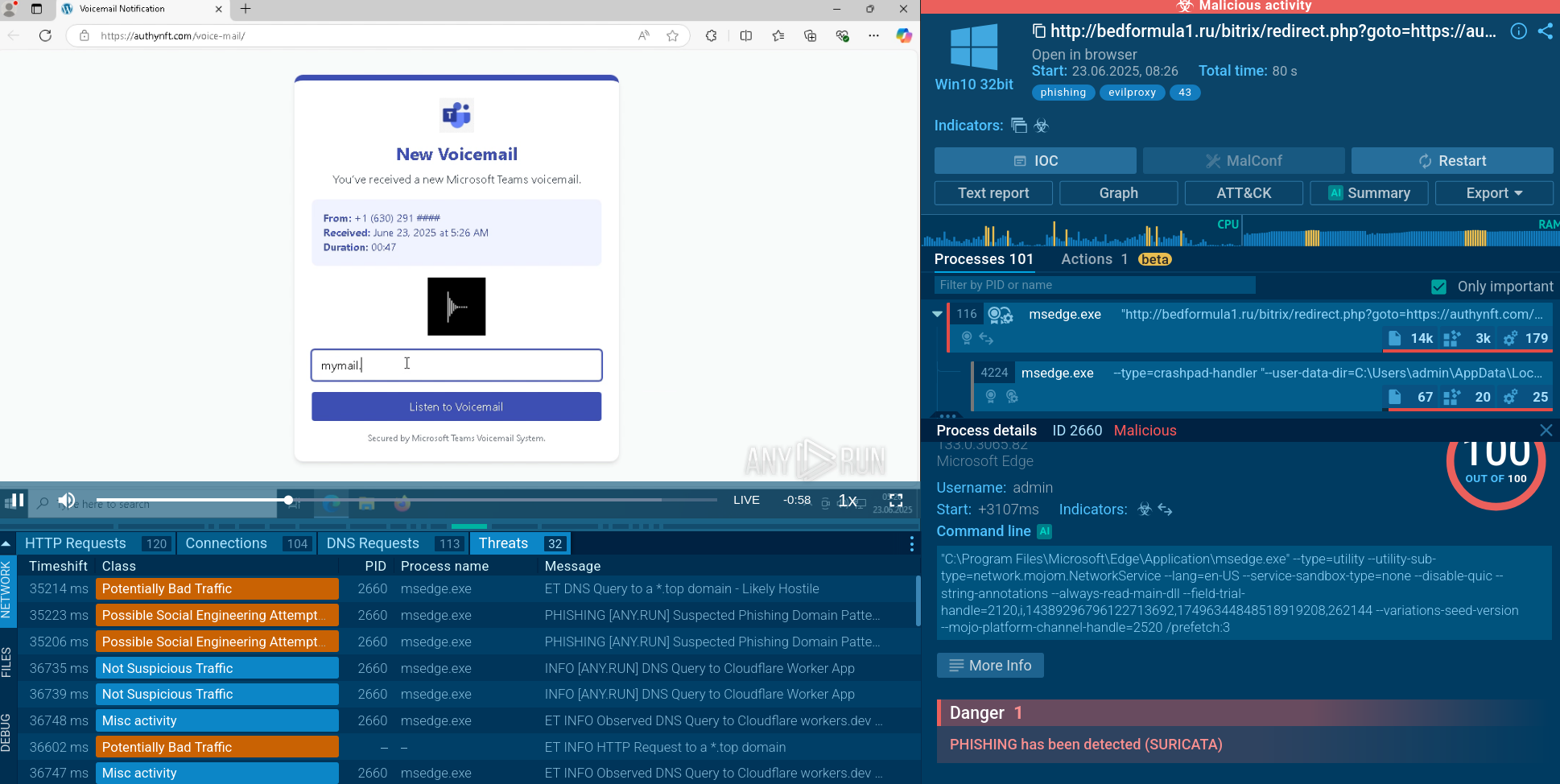
ANY.RUN’s Interactive Sandbox detects MicroStealer and lets observe the attack chain in its secure environment.
 MicroStealer detonated in Interactive Sandbox
MicroStealer detonated in Interactive Sandbox
The malware's Node.js component is heavily obfuscated using LZ-String UTF-16 compression, compressed string arrays with numeric indices, flattened control flow, and dead code padding. Before executing its main payload, MicroStealer checks the runtime environment for processes and services commonly associated with virtual machines — if detected, execution terminates immediately, a classic anti-analysis technique.
Once running, the stealer collects:
All collected data is archived and exfiltrated through two simultaneous channels: Discord webhooks and attacker-controlled exfiltration servers. Using dual channels is a resilience strategy: if one endpoint is taken down, the other ensures the stolen data still reaches the threat actor.
The malware's own User-Agent header during its initial connection to Discord reads: MicroStealer/1.0 — an unusually transparent self-identification that serves as a reliable network-level detection signature for defenders who know to look.
For detailed static analysis of MicroStealer sample performed by ANY.RUN's team, explore the article in the corporate blog.
MicroStealer poses significant risks beyond individual data theft:
Credential and Session Compromise: Steals browser-stored logins and active sessions for SaaS platforms, VPNs, cloud services, and corporate portals, enabling lateral movement and privilege escalation.
Persistent Stealth Access: Session hijacking blends malicious activity with legitimate traffic, prolonging undetected presence.
Business Email Compromise (BEC): Attackers gain control of corporate email, enabling fraud, invoice manipulation, and executive impersonation.
Data Exfiltration and Reckon: Quickly sends screenshots, profiles (e.g., Discord, Steam), and sensitive files, supporting targeted follow-on attacks or sale on underground markets.
Ransomware Gateway: Stolen initial access often feeds broader intrusions, BEC, or supply-chain attacks.
Compliance and Reputational Damage: Exposure of corporate identities risks regulatory violations and loss of trust.
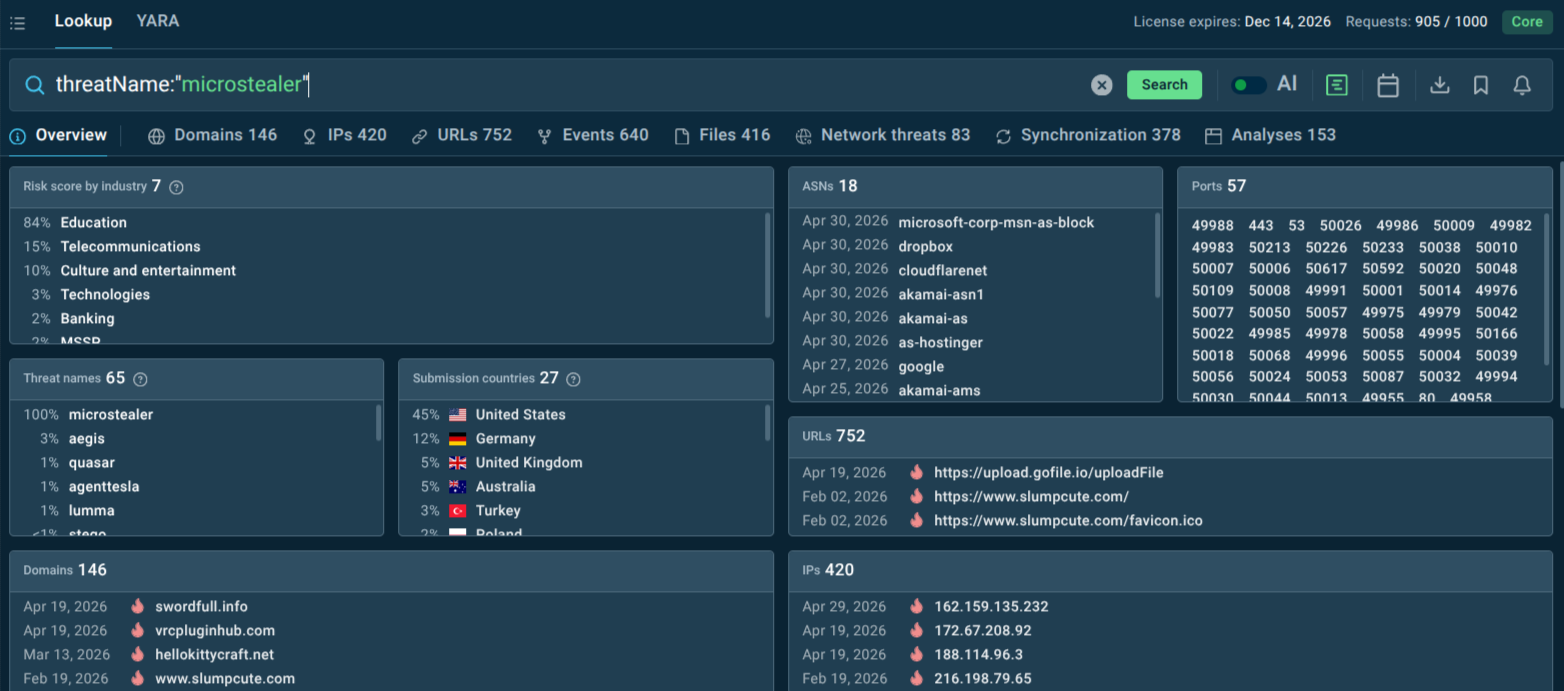
Analysis of MicroStealer submissions to the ANY.RUN sandbox shows that about 50% of observed sample uploads originated from the United States and Germany, indicating focused activity in these two major economies. The education and telecommunications sectors have shown the most elevated exposure among confirmed cases.
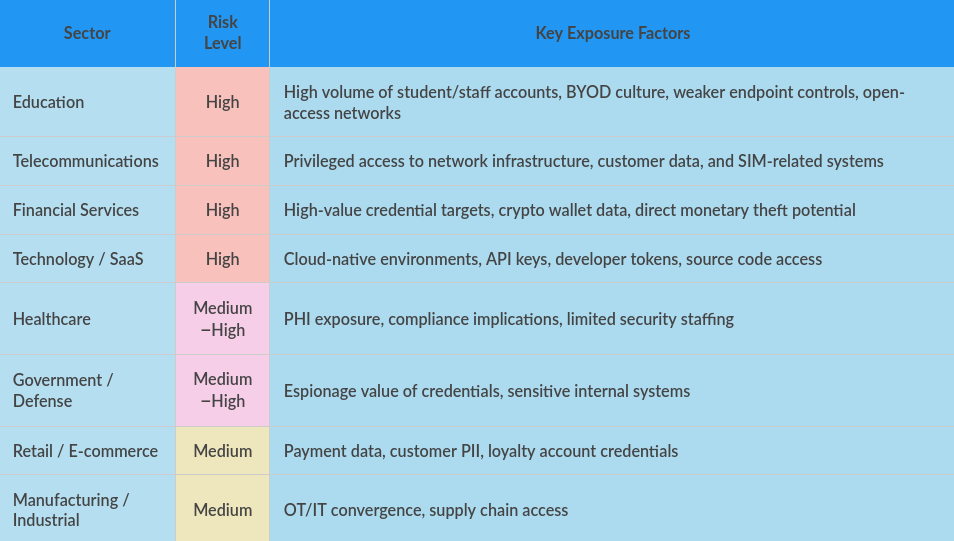 Industry risk profiles based on observed targeting and structural vulnerabilities
Industry risk profiles based on observed targeting and structural vulnerabilities
MicroStealer reflects a broader trend: infostealers evolving from simple credential grabbers into access brokers’ tools.
Key evolutionary traits:
While MicroStealer itself may appear under different names or variants, its behavior aligns with modern MaaS (Malware-as-a-Service) ecosystems.
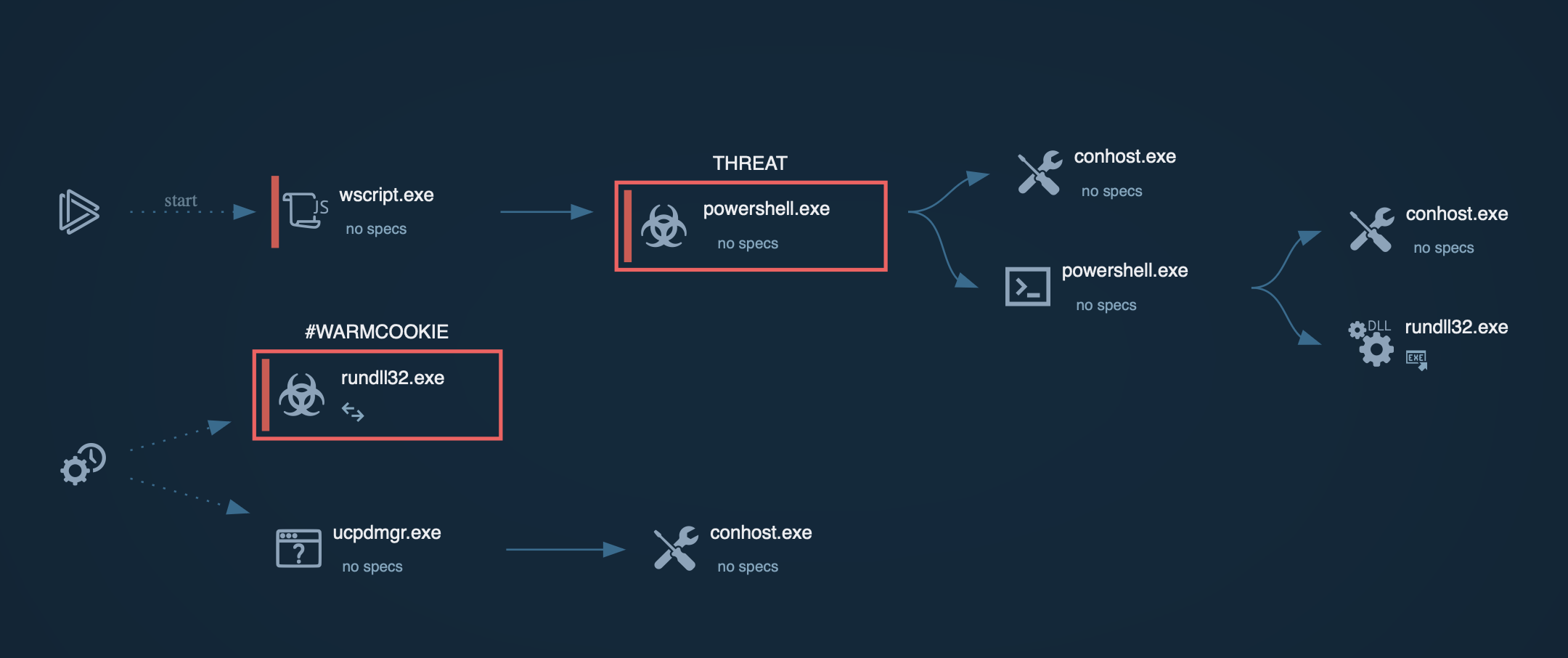
Common vectors:
Compromised or Impersonated Accounts: Social engineering via trusted-looking messages or posts.
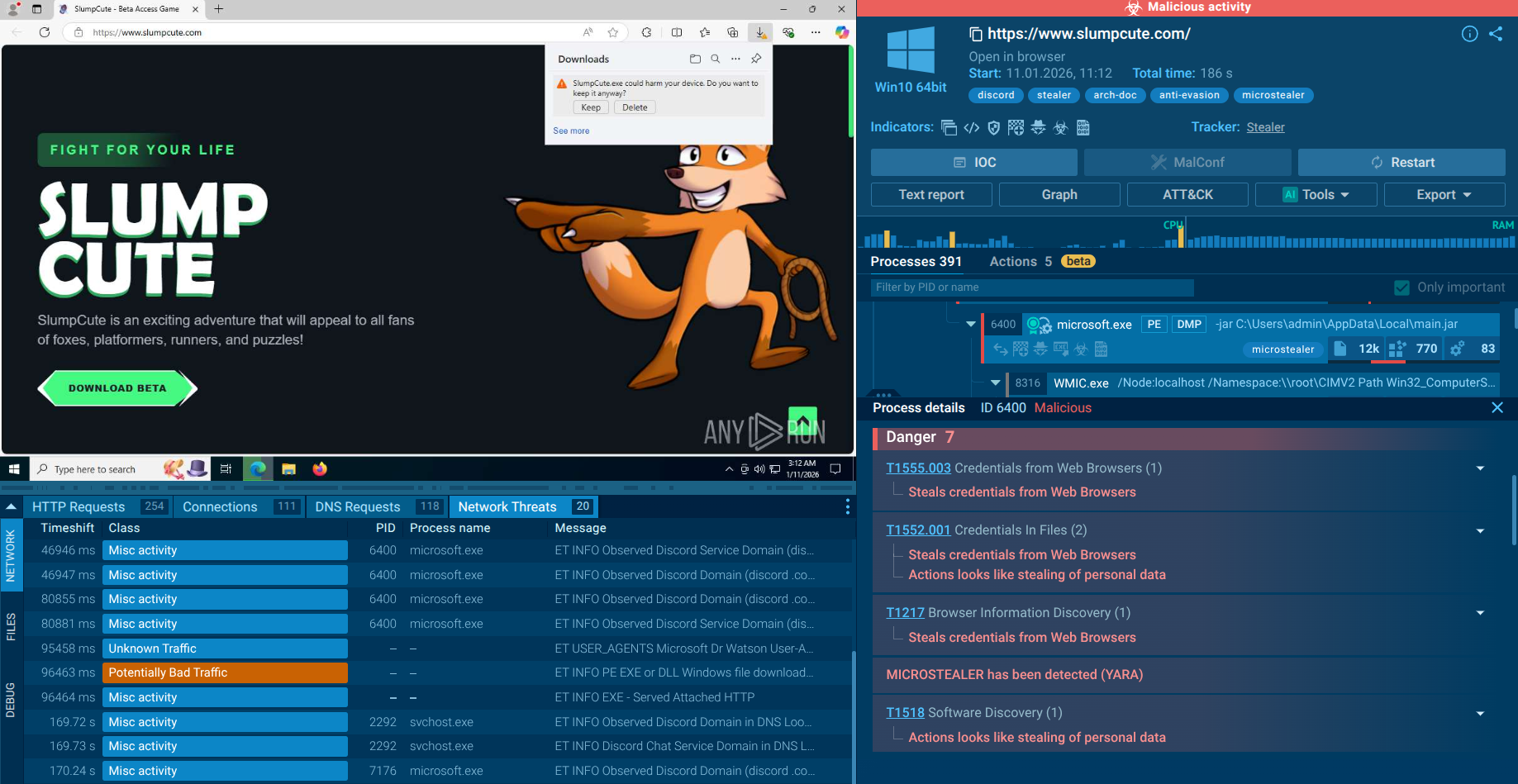
Malicious Downloads: Fake "Game Launcher" or software installers from attacker-controlled or compromised sites (e.g., Dropbox-hosted payloads, Discord CDN).
Phishing/Malvertising: Lures promising games, tools, or updates.
Drive-by or Trojanized Software: Especially in gaming/piracy ecosystems.
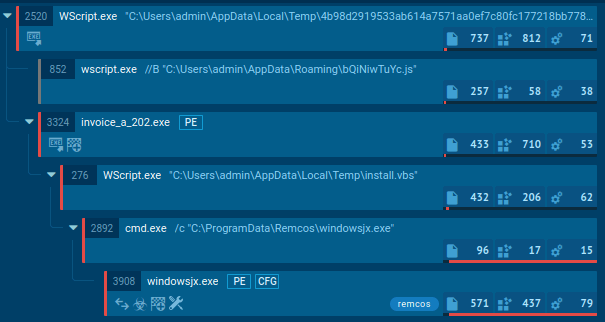
Once the victim runs the downloaded installer (RocobeSetup.exe), the NSIS installer silently deploys the Electron application and a UAC prompt is presented under the guise of a normal "Game Launcher" installation process — a social engineering layer built directly into the technical chain. MicroStealer does not use vulnerability exploitation for initial access; it relies entirely on the user making a trust-based decision to run the file.
MicroStealer's full execution chain can be broken into four distinct stages:
Stage 1: NSIS Installer (RocobeSetup.exe). The outer wrapper is a standard NSIS archive installer. It contains the Electron application, ASAR archives (app.asar and app.asar.unpacked), and the main payload — a JAR file accompanied by a bundled Java Runtime Environment — packaged inside module.zip.
Stage 2: Electron Application (Game Launcher.exe). The Electron app requests administrator privileges through a UAC dialog. Once elevated, it unpacks the bundled JRE and JAR file, placing them in %LOCALAPPDATA%. The Java executable is renamed miicrosoft[.]exe (a typosquat on the legitimate Microsoft name) to blend in with system processes during casual inspection.
Stage 3: Node.js Launcher (index.js inside app.asar). A heavily obfuscated Node.js script handles the extraction and launch of the JAR payload. Strings within the script are compressed using the LZ-String library's UTF-16 encoding and stored in a single Unicode variable, then split by a pipe delimiter and retrieved by numeric index. After extracting and deobfuscating this logic, the script resolves to a straightforward spawn() call that launches miicrosoft.exe -jar soft.jar in a detached, background process and then immediately terminates itself — ensuring the payload runs independently.
Stage 4: Java Payload (soft.jar). This is MicroStealer's core. The JAR file executes the actual credential-harvesting logic. Before beginning collection, it checks the execution environment against a list of processes and services associated with virtual machines; if a match is found, it exits. Otherwise, it:
Exfiltrates the archive to both a Discord webhook endpoint and a freshly registered attacker-controlled server, using the User-Agent string MicroStealer/1.0
The dual-destination exfiltration design ensures redundancy: if either the Discord webhook or the custom server becomes unavailable or is taken down, the other still delivers the stolen data. The use of newly registered domains for the secondary exfiltration endpoint also means these domains carry no historical threat reputation at the time of the attack, further evading domain-reputation-based network defenses.
The core challenge MicroStealer poses is detection lag: it spreads and exfiltrates data while antivirus signatures haven't caught up yet. This is where proactive threat intelligence — specifically ANY.RUN's TI Feeds and TI Lookup — provides a decisive defensive advantage.
ANY.RUN TI Lookup: Instant Contextual Investigation
Query TI Lookup for the threat name to instantly surface all related sandbox sessions, associated indicators, behavioral data, and attack chain details.
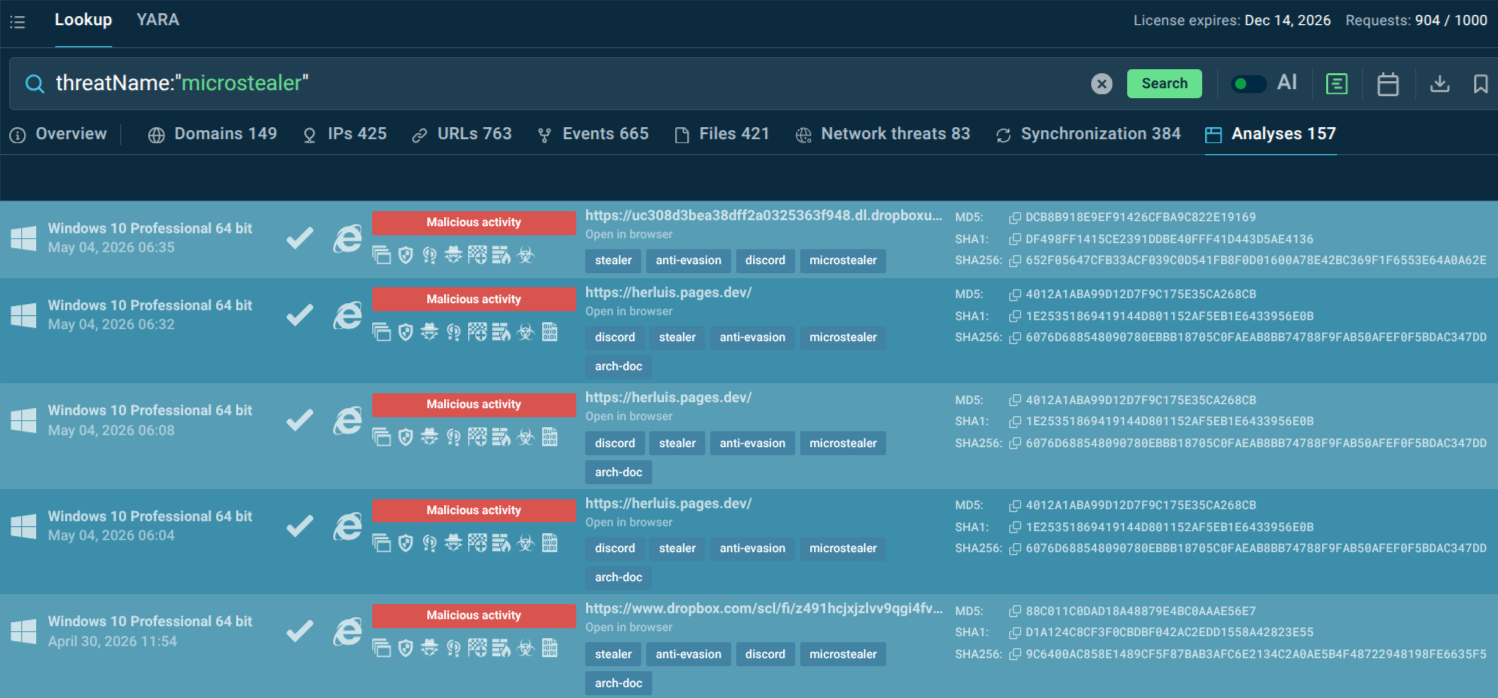 MicroStealer sandbox analyses found via TI Lookup
MicroStealer sandbox analyses found via TI Lookup
TI Lookup allows pivoting from a single suspicious indicator to a full picture of the threat: which domains were contacted, what files were dropped, which MITRE ATT&CK techniques were used, and how similar samples have behaved across prior investigations. This transforms a vague alert into actionable, scoped threat intelligence within minutes.
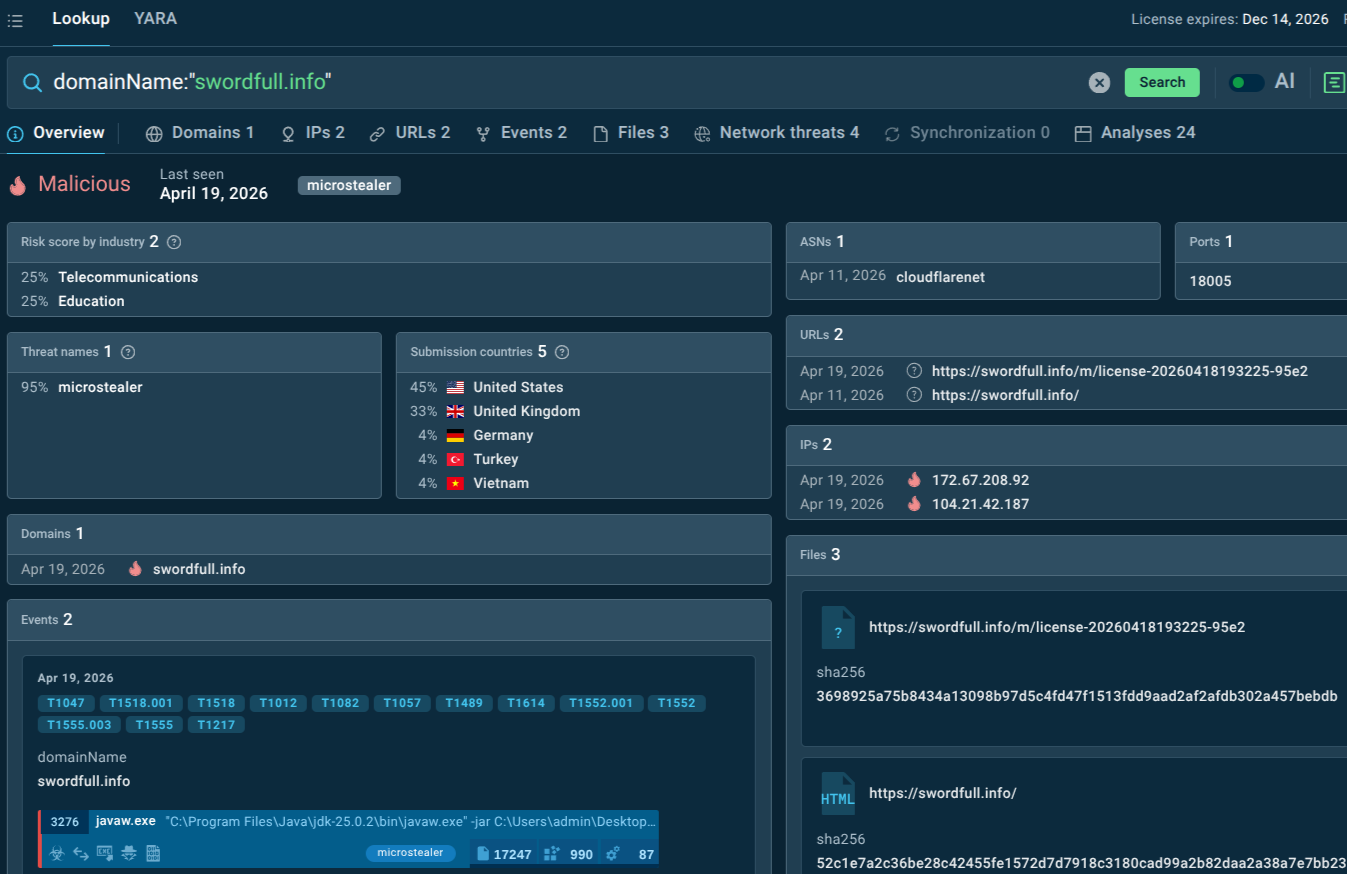 MicroStealer domain, IOCs, files, events
MicroStealer domain, IOCs, files, events
TI Lookup also supports industry and geographic threat landscape filtering, allowing security teams to assess whether a threat like MicroStealer is actively targeting their specific sector or region before committing investigation resources, enabling smarter alert prioritization.
ANY.RUN TI Feeds: Continuous IOC Delivery to Your Security Stack
Threat Intelligence Feeds provide a continuously updated stream of indicators of compromise (malicious IPs, domains, URLs) derived from real sandbox analysis sessions run by over 600,000 security researchers and analysts across more than 15,000 organizations. IOCs are delivered in STIX/TAXII format for direct integration with SIEM platforms, EDR systems, IDS/IPS, and threat intelligence platforms such as OpenCTI, ThreatConnect, and ThreatQ.
 TI Feeds integration options
TI Feeds integration options
Because MicroStealer relies heavily on fresh infrastructure (newly registered domains with no historical reputation), real-time feed delivery is specifically valuable against this threat. Every IOC in TI Feeds is accompanied by a full sandbox report: process trees, network traffic maps, MITRE ATT&CK technique mappings, and behavioral evidence — giving SOC analysts the context they need to act rather than just a raw indicator to block.
Additional Measures:
Robust endpoint detection with behavior-based analysis (sandboxing).
Browser security (e.g., session isolation, no saved credentials where possible).
MFA with hardware keys or phishing-resistant methods.
Least privilege, network segmentation, and regular credential rotation.
Email/web filtering and application allowlisting.
Monitor for anomalous Discord/webhook traffic or unusual Java/Electron processes.
Awareness training on social engineering and suspicious downloads.
New malware families like MicroStealer often lack clear static signatures or reliable reputation data, which slows down traditional investigation workflows.
Instead of relying only on static verdicts, analysts can quickly confirm what a suspicious file actually does by executing it in a controlled environment.
Running the sample in the ANY.RUN interactive sandbox reveals the full execution chain, including:
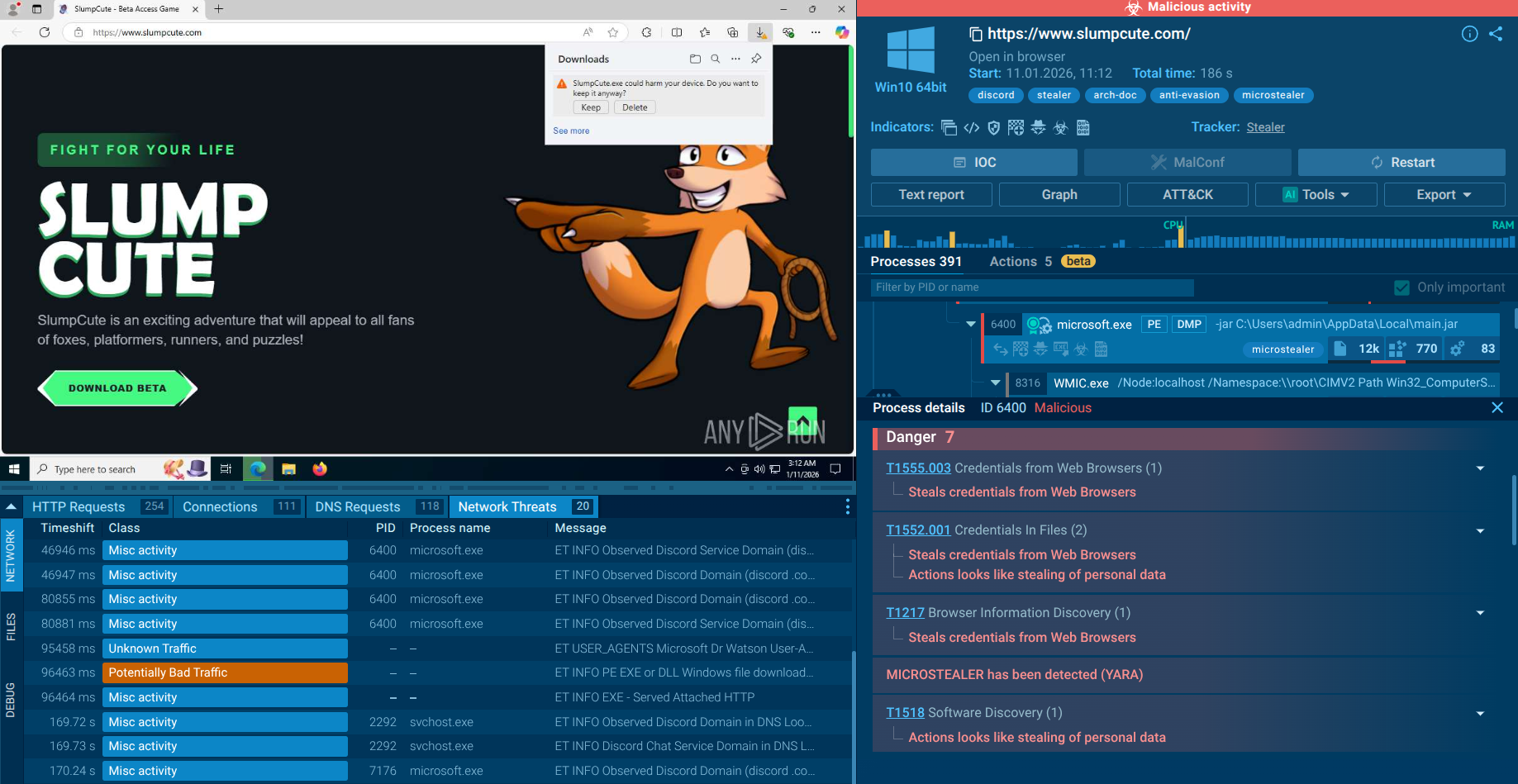 MicroStealer detonated in Interactive Sandbox
MicroStealer detonated in Interactive Sandbox
Within minutes, analysts can observe the complete attack chain, extract reliable IOCs, and determine whether the sample poses a real threat.
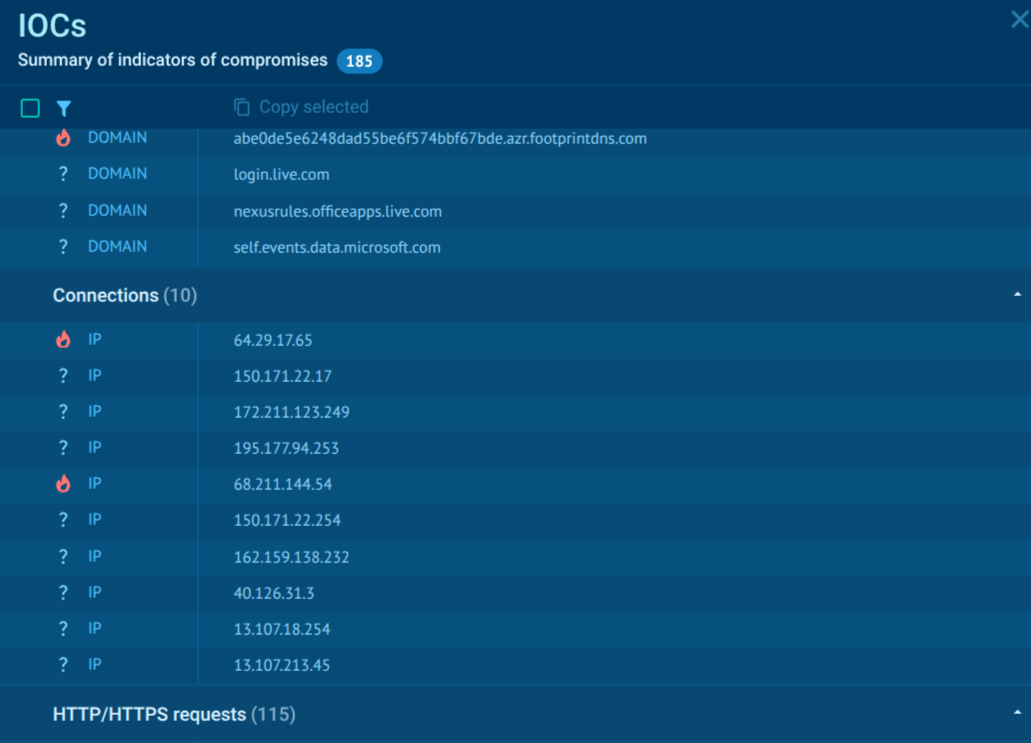 MicroStealer IOCs in Interactive Sandbox
MicroStealer IOCs in Interactive Sandbox
For SOC teams, this replaces guesswork with behavior-based evidence, helping reduce investigation time and avoid unnecessary escalations.
MicroStealer exemplifies the evolving infostealer threat: fast, evasive, and focused on high-value corporate identities. Its multi-stage design and session-stealing focus make traditional defenses insufficient. Organizations must combine proactive threat intelligence, behavioral detection, and human-centric security to stay ahead. Early visibility into such threats is key to preventing credential theft from escalating into major incidents.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.