Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases
EvilTokens is a phishing-as-a-service (PhaaS) toolkit that emerged in mid-February 2026. It automates device code phishing attacks against Microsoft 365 and Entra ID environments. Unlike traditional credential-harvesting phishing, EvilTokens tricks users into completing legitimate authentication on Microsoft's own login pages, resulting in the issuance of valid OAuth access and refresh tokens directly to the attacker, effectively bypassing MFA without stealing passwords.
|
PHaaS
Type
:
|
Unknown
Origin
:
|
|
Unknown
First seen
:
|
8 June, 2026
Last seen
:
|
|
PHaaS
Type
:
|
Unknown
Origin
:
|
|
Unknown
First seen
:
|
8 June, 2026
Last seen
:
|

 2272
2272
 0
0

 5020
5020
 0
0

 4750
4750
 0
0
EvilTokens bypasses MFA by abusing Microsoft's own device code OAuth flow, obtaining valid tokens without password theft.
As a PhaaS kit sold on Telegram, it democratizes sophisticated attacks, enabling rapid scaling with minimal technical skill.
AI-powered features generate convincing lures and automate BEC, increasing both volume and success rates.
Persistent refresh tokens allow long-term access, device registration, and silent authentication across M365 services.
Organizations in finance, government, healthcare, and other M365-heavy sectors are prime targets globally.
Security teams can query ANY.RUN's Threat Intelligence Lookup for known EvilTokens domains, URLs, and infrastructure indicators in real time — enriching SIEM alerts, hunting for campaign IOCs, and staying ahead of the platform's rapid infrastructure rotation before damage is done.
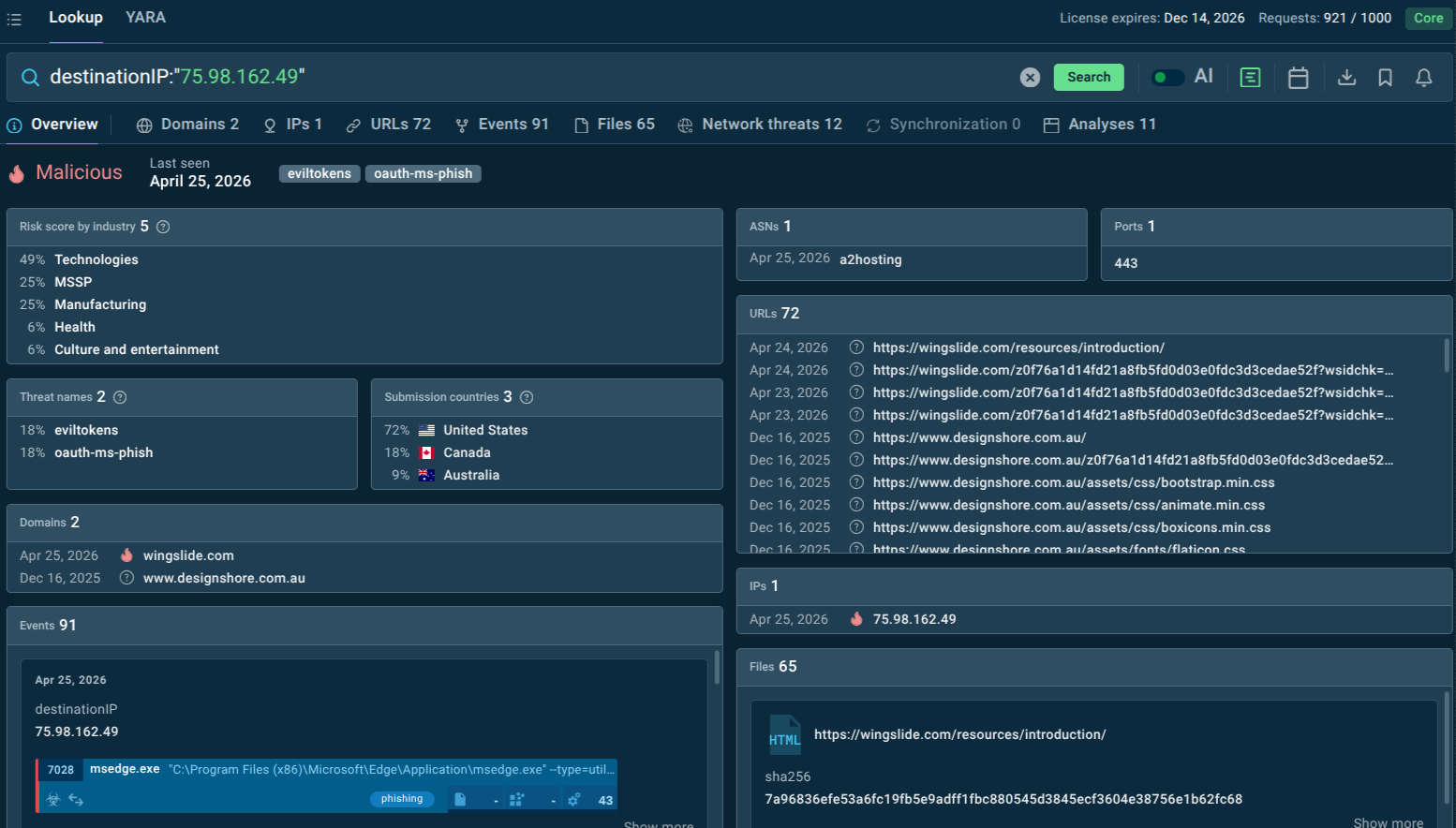 Malicious IP linked to EvilTokens
Malicious IP linked to EvilTokens
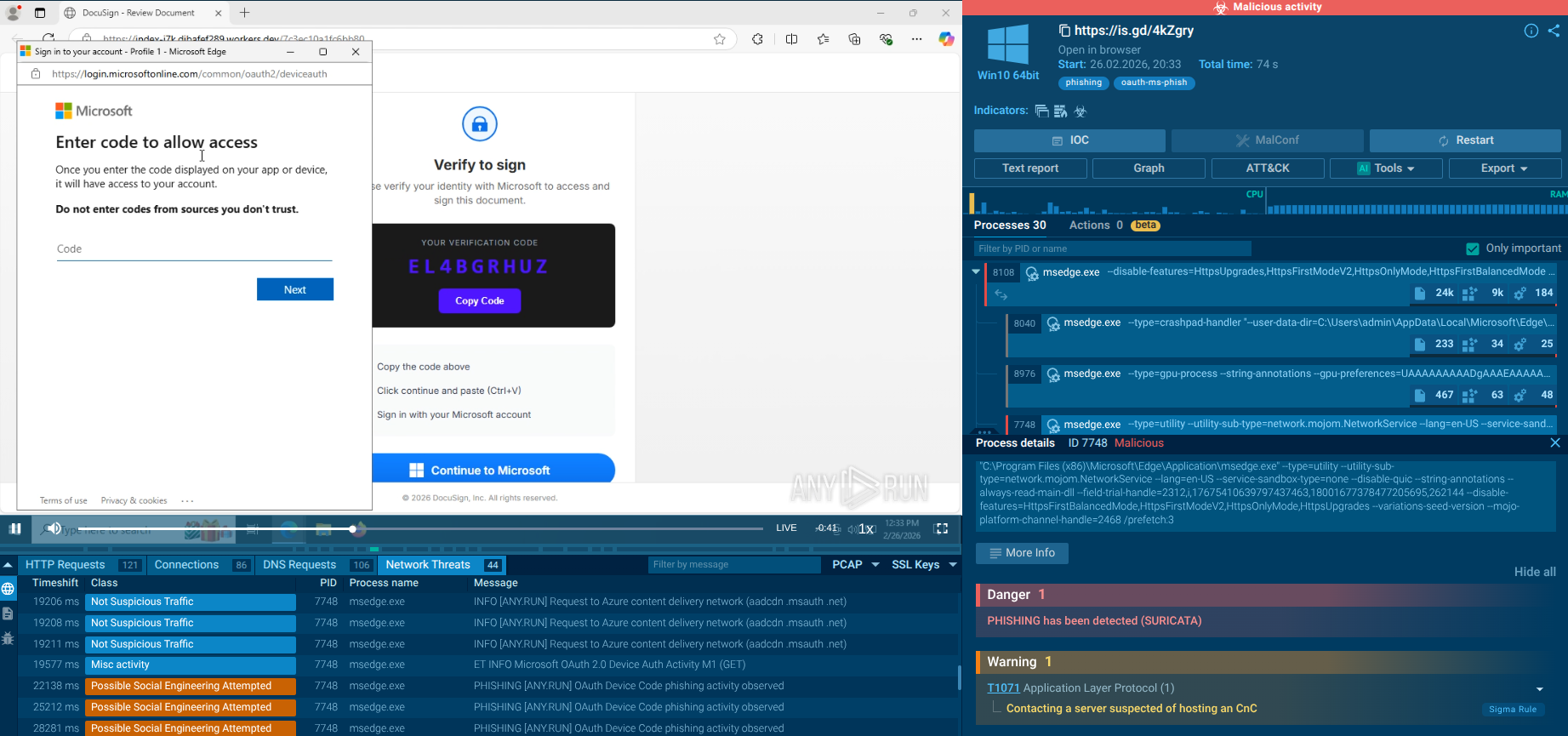 EvilTokens phishing analysis in Interactive Sandbox
EvilTokens phishing analysis in Interactive Sandbox
EvilTokens is a turnkey, productized PhaaS platform sold to criminal affiliates via Telegram. Unlike conventional phishing kits that replicate Microsoft login pages or intercept credentials in transit, EvilTokens abuses the legitimate OAuth 2.0 Device Authorization Grant (a Microsoft authentication flow designed for devices with limited input capabilities, such as smart TVs, IoT sensors, and printers) to steal valid OAuth tokens after the victim has completed a fully legitimate MFA challenge on Microsoft's real infrastructure.
First identified by Sekoia's Threat Detection & Research (TDR) team in early March 2026, EvilTokens had already been circulating in underground cybercrime communities since mid-February 2026. Its operator, known as eviltokensadmin, advertised the kit in private Telegram channels frequented by threat actors specializing in Adversary-in-the-Middle (AitM) phishing and BEC fraud.
What sets EvilTokens apart from the crowded phishing kit marketplace is its comprehensive, full-lifecycle attack package. Beyond the core phishing module, the platform provides affiliates with:
Ready-made phishing page templates impersonating services like Adobe Acrobat, DocuSign, SharePoint, OneDrive, and Microsoft itself.
Token weaponization tools to immediately leverage stolen OAuth credentials.
Email harvesting and inbox analysis powered by AI, using Meta's LLaMA model to automatically prioritize high-value conversations.
A built-in webmail client, internally branded "MailVault," styled to mimic Outlook, enabling attackers to read, compose, and send emails directly from compromised inboxes.
Reconnaissance via the Microsoft Graph API, including automatic detection of Exchange and Global Administrator accounts (flagged with a crown icon) to enable privilege escalation.
Keyword alerting via Telegram, so attackers are instantly notified when terms like "invoice," "wire transfer," or "payment" appear in harvested mailboxes.
AI-generated phishing lures, with LLMs crafting personalized and contextually convincing social engineering messages at scale.
Multi-tenant SaaS architecture, giving each affiliate their own isolated environment, unique credentials, and a pool of compromised accounts
The platform operates through fully featured Telegram bots and a Vue.js admin panel marketed externally as "MailVault — Enterprise Email Management Platform" to disguise its true nature. It is under continuous development, with the operator publicly announcing plans to expand support to Gmail and Okta phishing in the near future.
Researchers at Abnormal AI assessed with high confidence that EvilTokens' underlying code was likely AI-generated, reflecting a broader and alarming trend of AI accelerating both the development and operation of criminal phishing infrastructure.
How EvilTokens Threatens Businesses and Organizations
EvilTokens targets the identity layer — the very fabric of modern enterprise security —without triggering typical credential-based alerts.
Key risks include:
MFA Bypass: Instead of stealing passwords, attackers obtain valid tokens, effectively sidestepping MFA protections.
Persistent Access: Refresh tokens allow long-term access even after password resets.
Business Email Compromise (BEC): Attackers gain control of corporate email, enabling fraud, invoice manipulation, and executive impersonation.
Data Exfiltration: Access extends to email, cloud storage, Teams, and SSO-connected apps.
Stealth and Evasion: Because authentication occurs through legitimate Microsoft pages, detection becomes significantly harder.
EvilTokens is opportunistic, but not random. It gravitates toward roles with access and authority.
Most targeted sectors:
Finance & Banking (payment authorization, fraud potential);
Healthcare (sensitive data + weaker identity controls);
Government & Public Sector (high-value intelligence);
Technology & SaaS companies (cloud-heavy environments);
Logistics & Supply Chain (invoice and partner fraud vectors).
High-risk roles include:
CFOs and finance teams
HR and payroll staff
Executives and decision-makers
Campaigns have already impacted hundreds of organizations globally across industries. The most impacted countries as of late March 2026 include the United States, Australia, Canada, France, India, Switzerland, and the United Arab Emirates — essentially any country with a significant concentration of Microsoft 365 enterprise users and active cross-border financial flows.
EvilTokens' delivery chain is engineered for maximum deception at every stage.
Stage 1 — Initial lure delivery. Phishing emails are sent from previously compromised legitimate accounts — real Microsoft 365 or Google Workspace mailboxes belonging to other victims. This means the sender passes all standard email authentication checks: SPF PASS, DKIM PASS, and DMARC PASS. The lure emails impersonate routine business communications: shared document notifications from OneDrive or SharePoint, DocuSign signing requests, invoice approvals, calendar invites, or HR announcements.
Attachments may be PDF, HTML, DOCX, XLSX, or SVG files containing either a QR code or a hyperlink leading to the phishing infrastructure.
Stage 2 — Bot filter gate. Links in lure emails point not to EvilTokens infrastructure directly but to compromised legitimate websites where a PHP bot filter validates whether the visitor is a real browser executing JavaScript. Automated sandbox crawlers and security scanners that lack JavaScript are trapped in a meta refresh loop and never reach the payload, providing a layer of detection evasion.
Stage 3 — Identity verification gate page. Legitimate visitors are redirected to a gate page (versioned, branded "Identity Verification") that collects the target's email address and passes it to a Cloudflare Worker, further obscuring the backend infrastructure.
Stage 4 — Phishing page. The victim is presented with a page impersonating a trusted service (Adobe Acrobat, DocuSign, Microsoft). The page displays a legitimate Microsoft device code generated in real time by EvilTokens' C2 server calling Microsoft's /devicecode endpoint alongside instructions to "verify identity" by visiting Microsoft's real device login page and entering the displayed code.
Stage 5 — Token harvest. When the victim authenticates on Microsoft's genuine login page (completing real MFA in the process), EvilTokens' C2 simultaneously polls Microsoft's /token endpoint to collect the resulting OAuth access token and refresh token. The attacker now controls the session.
Stage 6 — Lateral spread. With access to the victim's mailbox and contacts, attackers identify further high-value targets within the organization and among its business partners, launching new lure campaigns from the now-compromised legitimate account, perpetuating the cycle.
Once tokens are harvested, EvilTokens provides a full post-compromise operational suite delivered through the MailVault admin panel.
Token weaponization. The short-lived access token (valid 60–90 minutes) is used immediately to extract emails from Exchange Online, documents from SharePoint and OneDrive, and conversation history from Microsoft Teams. The refresh token (valid 90 days, rolling) is used to silently obtain new access tokens, maintaining persistent access to the account without re-authentication.
Privilege escalation detection. JWT claim parsing within the MailVault panel automatically identifies whether the compromised account holds Exchange Administrator or Global Administrator roles flagging these high-privilege accounts so affiliates know to prioritize them for deeper exploitation.
AI-powered email analysis. Using Meta's LLaMA model integrated into the platform, EvilTokens automatically analyzes harvested emails to surface high-value threads: financial conversations, invoice chains, payment instructions, and sensitive business discussions.
Keyword alerting. A Telegram-integrated keyword scanner notifies affiliates in real time when target terms appear in harvested mailboxes, enabling rapid exploitation of time-sensitive financial transactions.
BEC operations via MailVault. The built-in webmail client allows attackers to read all emails in a compromised inbox, download attachments, and compose and send messages that genuinely originate from the victim's account. Attackers can insert themselves into ongoing financial threads, redirect payments, impersonate executives, or exfiltrate sensitive documents without any technical complexity.
Persistence and device registration. Refresh tokens can be used to register an attacker-controlled device in Entra ID, granting even more durable access that persists beyond password resets unless explicitly revoked at the device level.
AI-generated lures. LLMs integrated into the platform generate contextually tailored phishing messages for new targets, varying content across recipients to evade signature-based detection and reduce campaign fatigue.
Defending against a threat as technically sophisticated and rapidly evolving as EvilTokens requires moving from reactive incident response to proactive, intelligence-driven security.
ANY.RUN's Threat Intelligence Lookup gives security teams direct, real-time access to threat data collected from millions of malware analysis sessions in ANY.RUN's Interactive Sandbox. For EvilTokens specifically, TI Lookup enables organizations to:
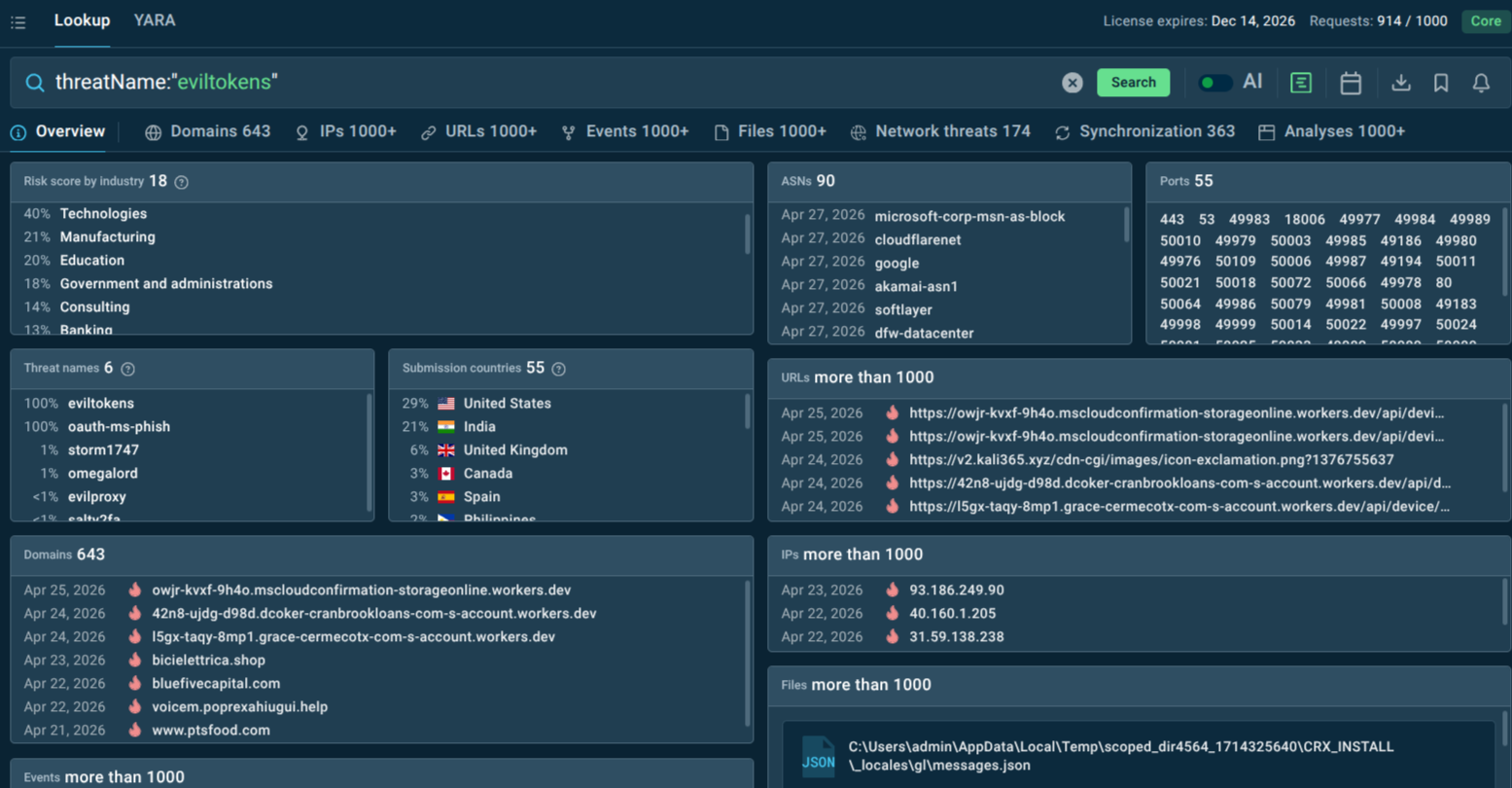 Fresh EvilTokens IOCs found in TI Lookup
Fresh EvilTokens IOCs found in TI Lookup
You can start from looking up the threat by name to get a selection of recent sandbox analysis sessions featuring EvilTokens attacks and pivot your research and hunting from there:
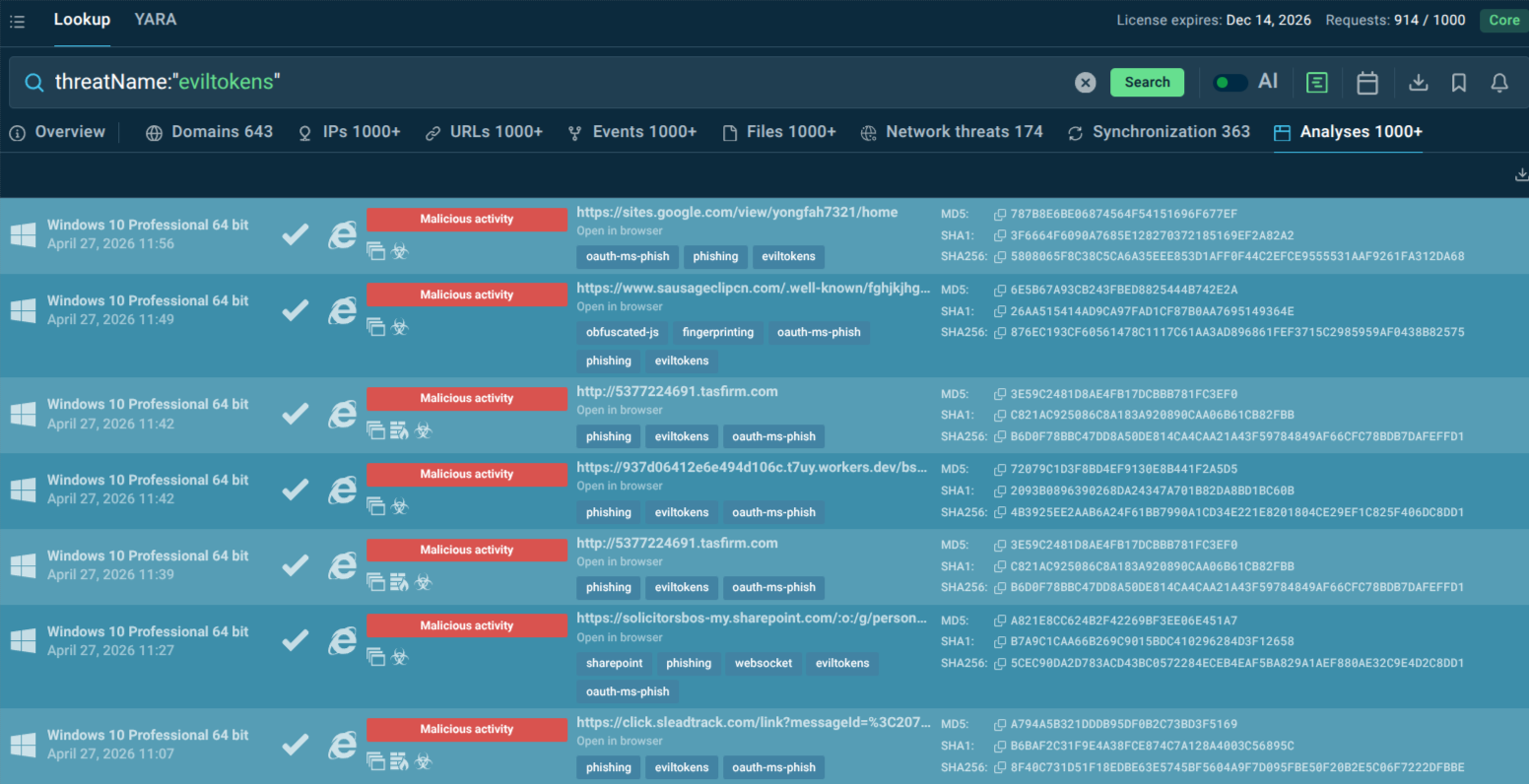 EvilTokens sandbox analyses found via TI Lookup
EvilTokens sandbox analyses found via TI Lookup
Additional Measures:
Enforcing Conditional Access policies to restrict or monitor device code flows.
User education on unusual "enter code on Microsoft login" requests.
Monitoring for anomalous token usage or new device registrations in Entra ID.
Advanced email filtering for AI-generated lures and attachment-based phishing.
Implementing least-privilege access and regular token reviews.
Behavioral analytics to detect post-compromise activity like unusual Graph API calls.
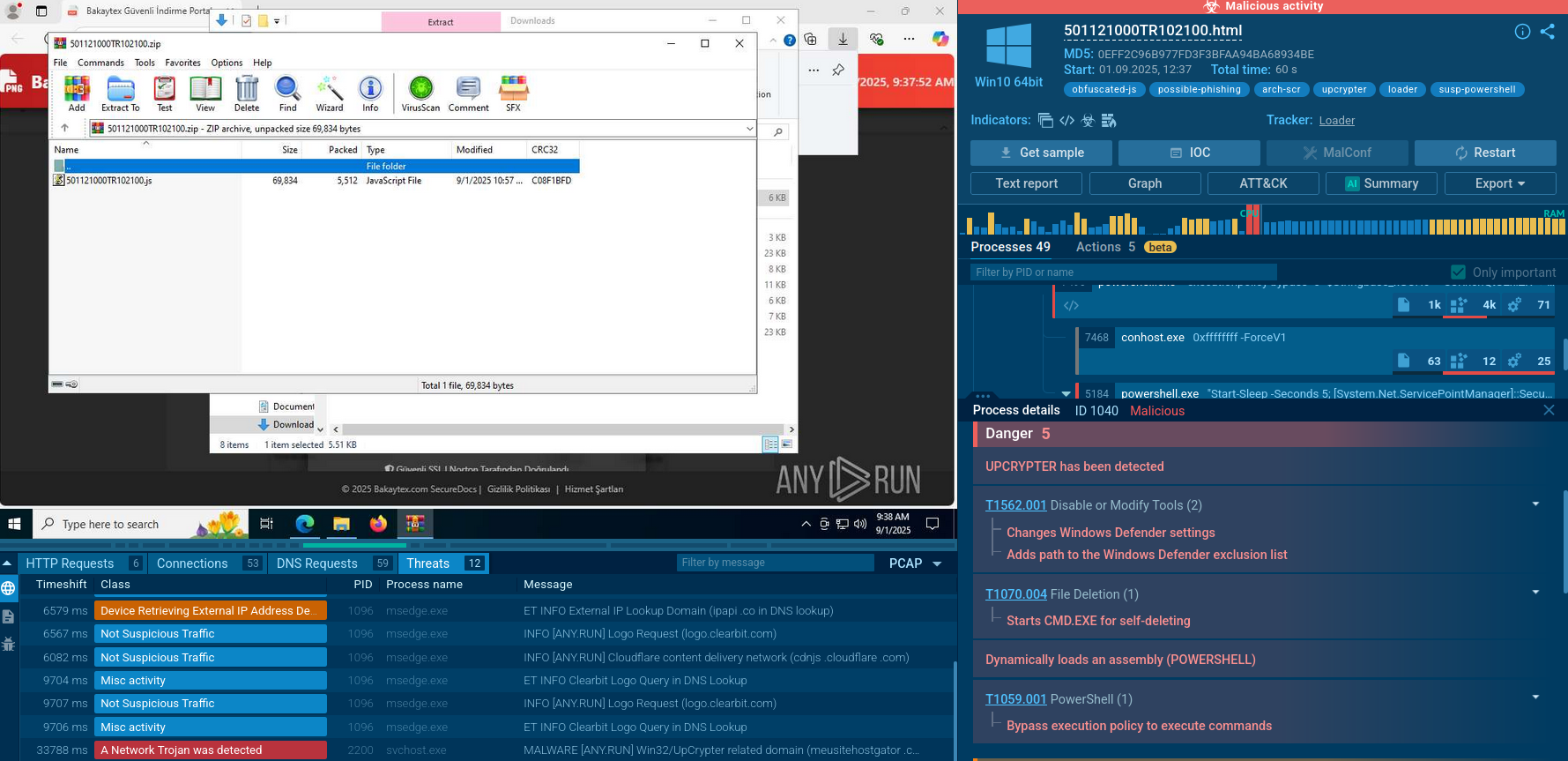
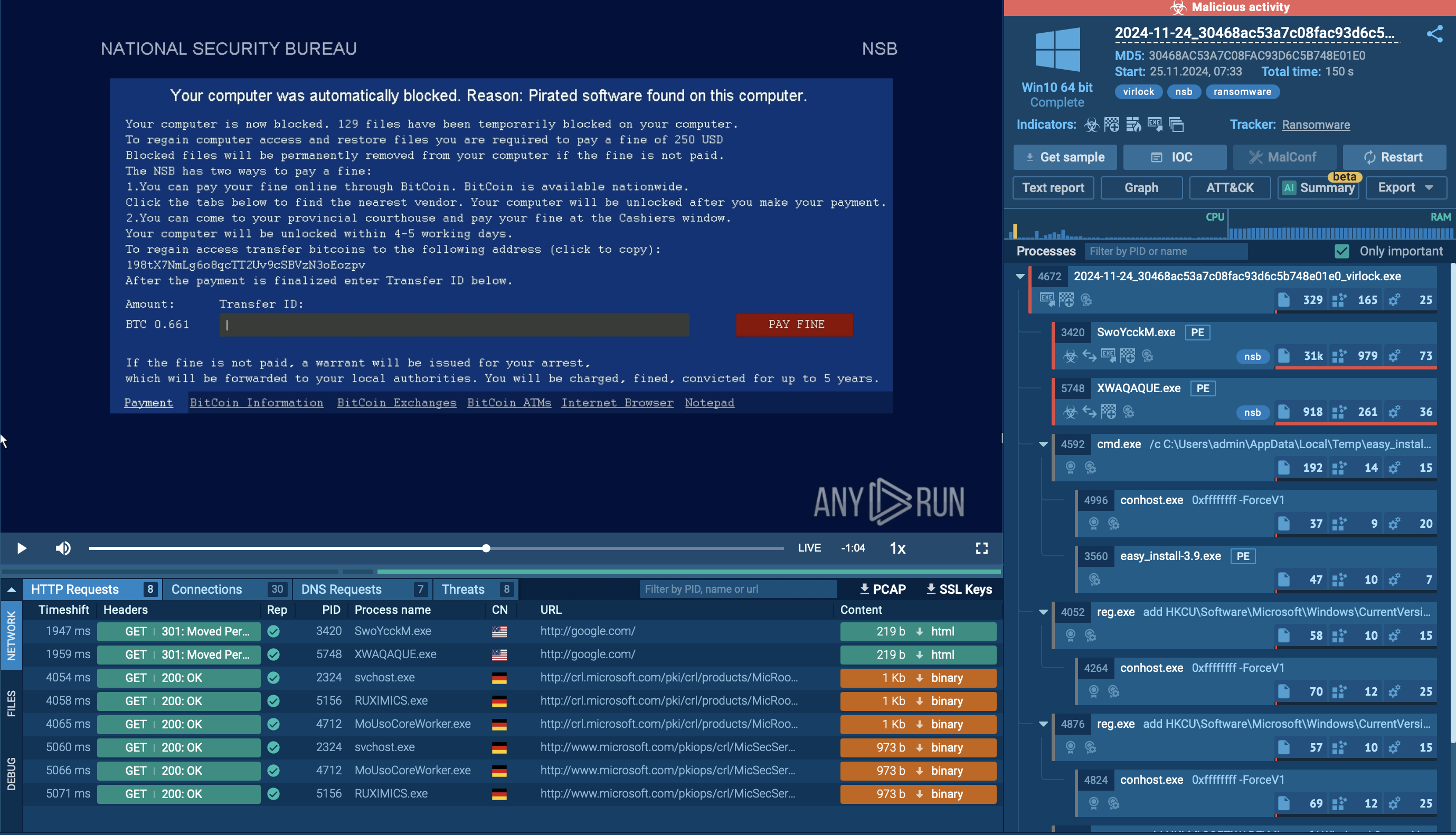
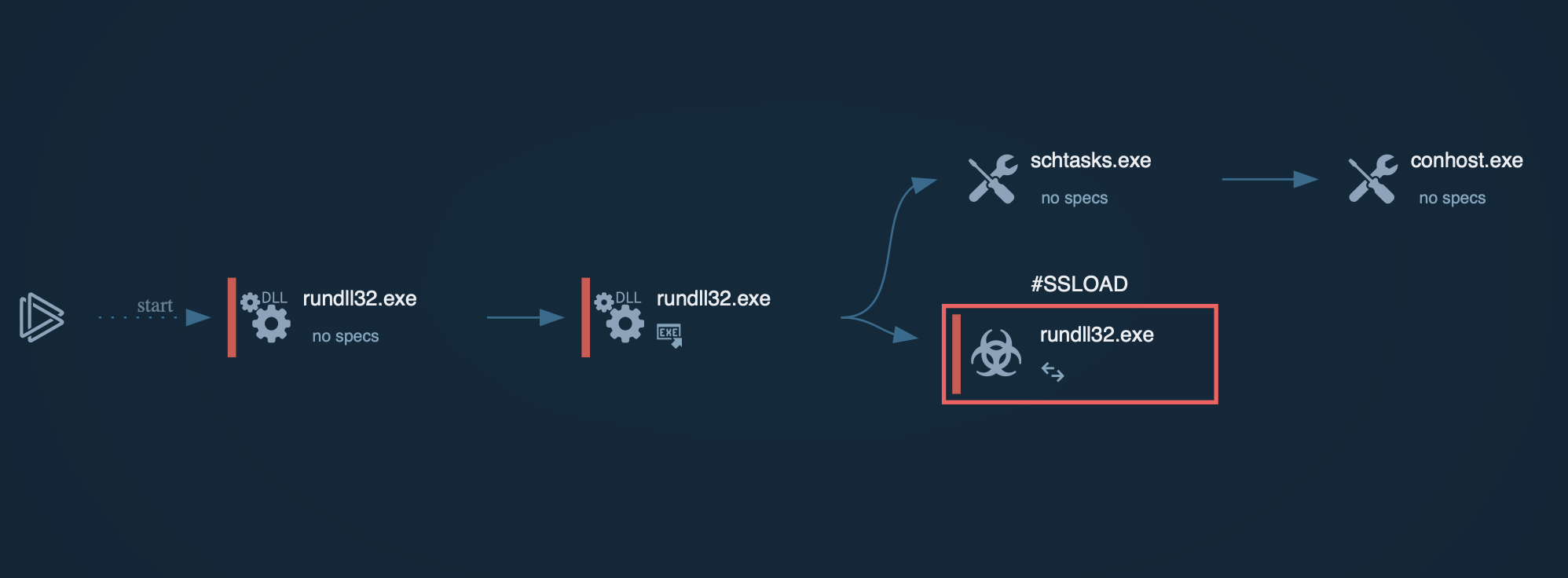
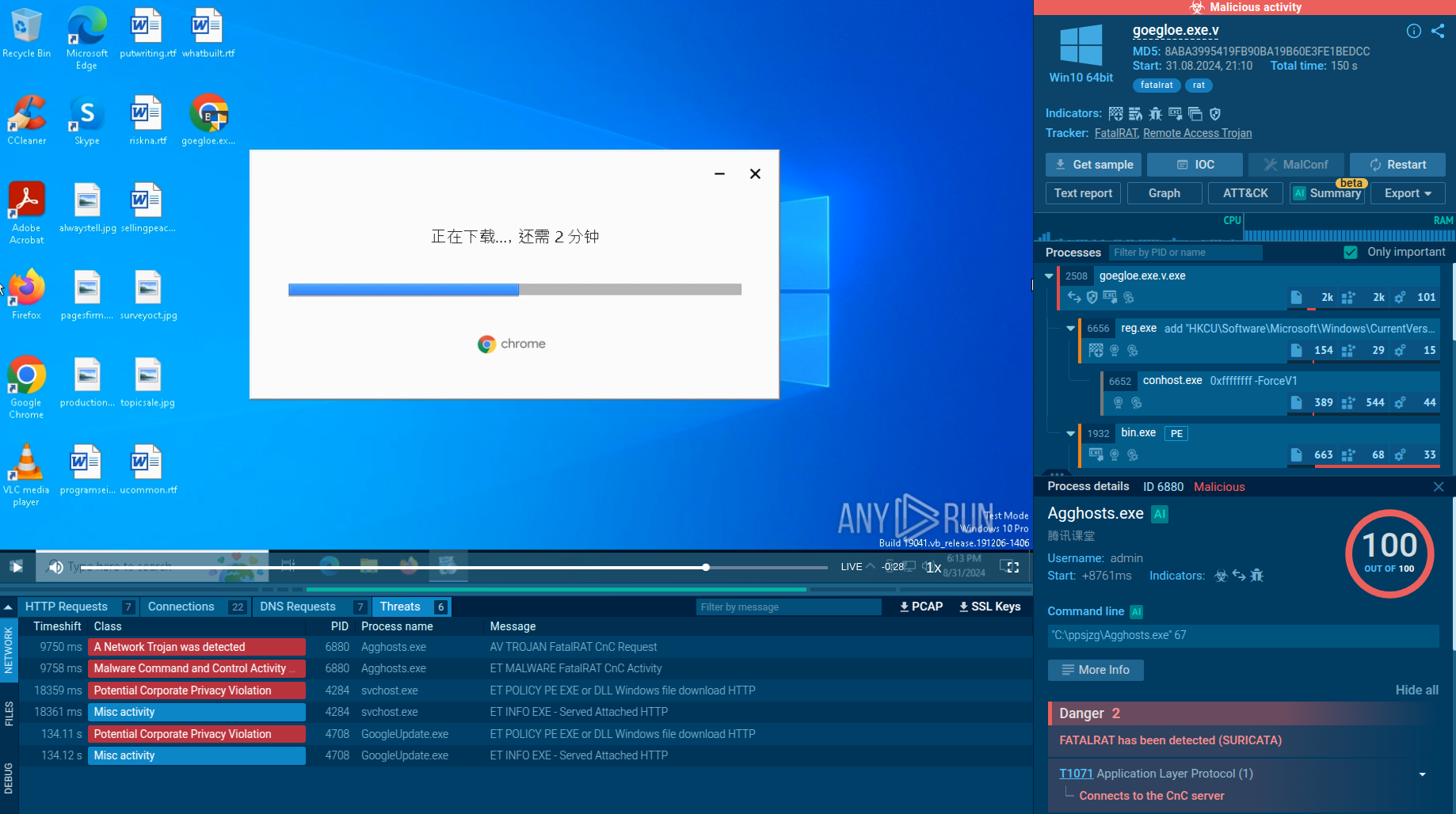
See the detonation of an EvilTokens sample
 EvilTokens attack chain in the sandbox
EvilTokens attack chain in the sandbox
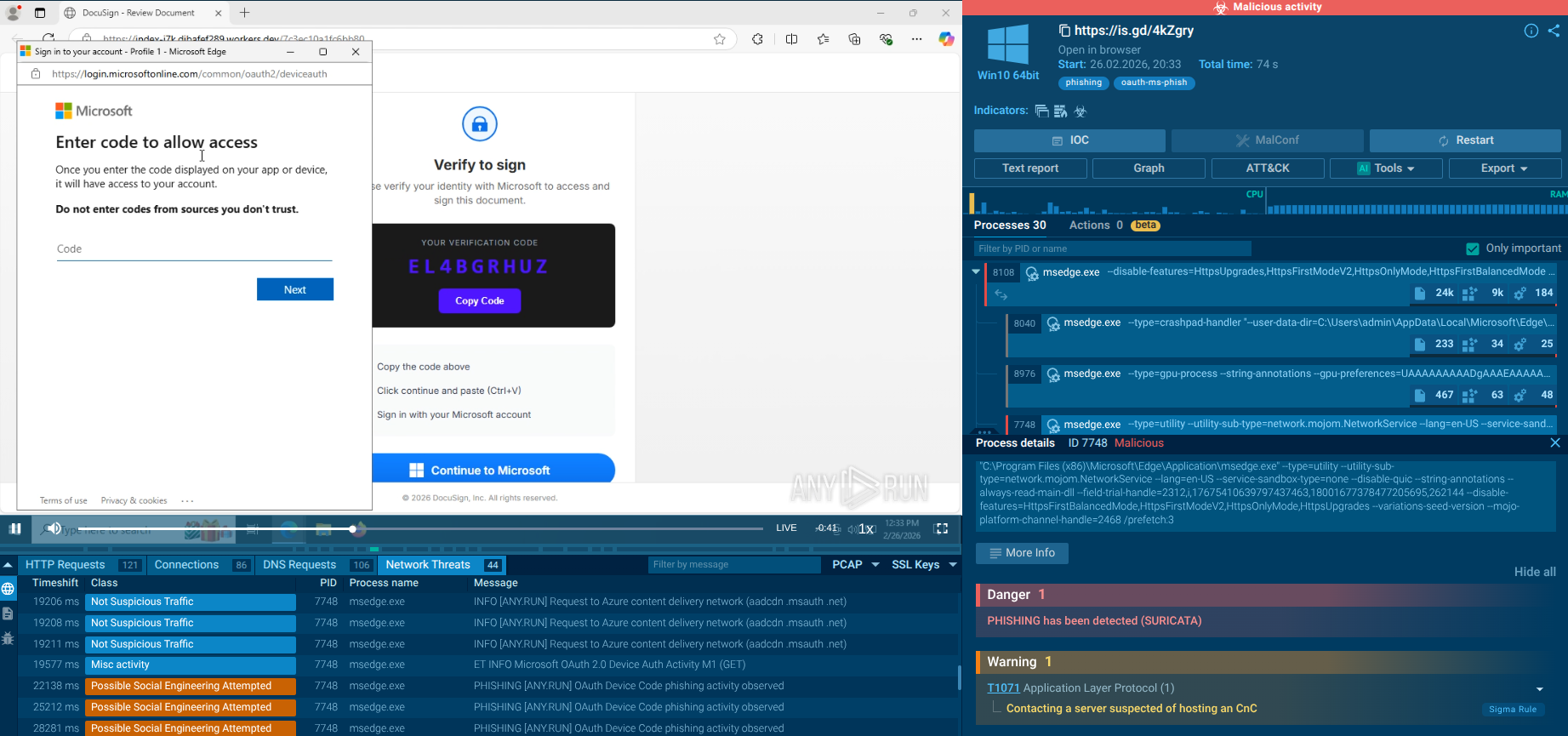
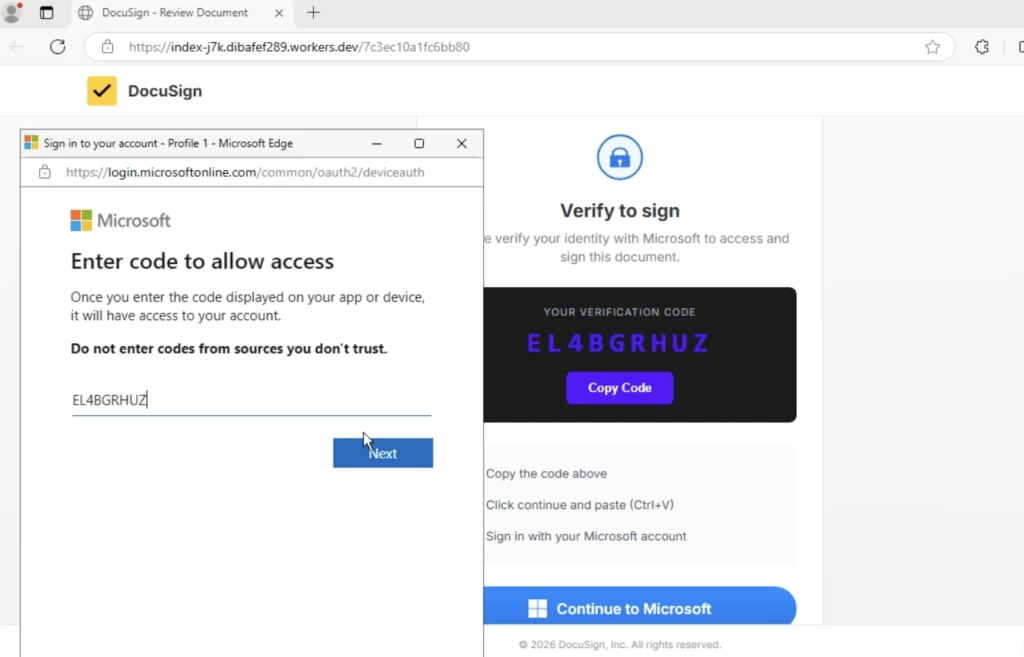
The attack often begins with a landing page impersonating DocuSign, prompting the user to “Review Document.” The victim is shown a verification code and instructed to copy it.
Key red flag: this is not a real DocuSign signing workflow. It is a scripted sequence:
Copy the verification code,
Click “Continue to Microsoft”,
Paste the code into Microsoft’s device login page.
The address bar typically shows a *.workers.dev domain instead of a legitimate DocuSign domain.
A Microsoft window then opens at login.microsoftonline.com/…/deviceauth, showing the form “Enter code to allow access.” The user enters the same code they were shown on the fake page. This action takes place on a legitimate Microsoft domain, even displaying Microsoft’s own warning: “Do not enter codes from sources you don’t trust.”
 Fake verification granting access to external client
Fake verification granting access to external client
The following screen states: “You’re signing in to Microsoft Office on another device…” From the victim’s perspective, the process still appears legitimate. In reality, they are approving access for an external client controlled by the attacker, not verifying the document they originally clicked.
The key point is: the user never enters their password on a fake site. Instead, they are guided through legitimate Microsoft infrastructure and manually transfer a code.
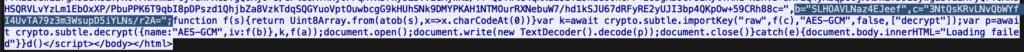
How Automatic SSL Decryption Ensures Instant Detection
From an investigation standpoint, these phishing pages often rely on JavaScript loaders and encrypted HTTPS traffic to hide the real workflow from traditional scanners.
This is where SSL decryption in the ANY.RUN Sandbox becomes critical. By extracting TLS encryption keys directly from process memory and decrypting HTTPS traffic during execution, the sandbox reveals the hidden scripts, API requests, and attacker infrastructure involved in the phishing flow.
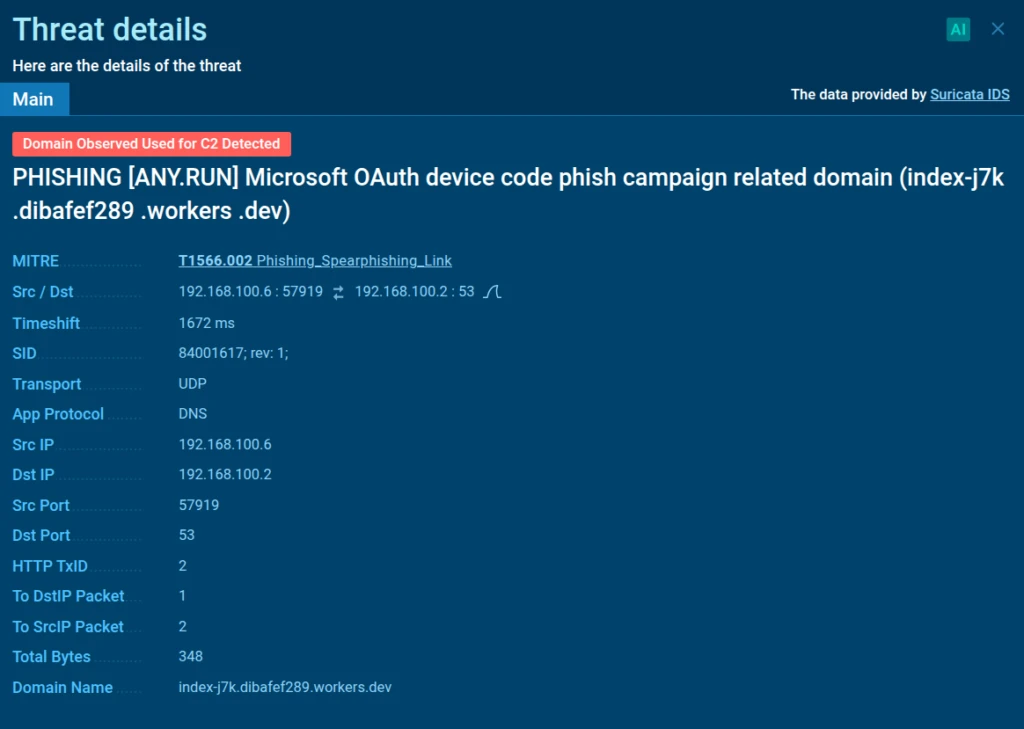 SSL decryption allows Suricata IDS rules to detect malicious encrypted traffic
SSL decryption allows Suricata IDS rules to detect malicious encrypted traffic
In this case, SSL decryption exposed the malicious JavaScript responsible for orchestrating the device authorization process and revealed high-confidence network indicators used by the phishing kit. Among them were specific API requests such as /api/device/start and /api/device/status/, along with a distinctive X-Antibot-Token header used in communication with the backend.
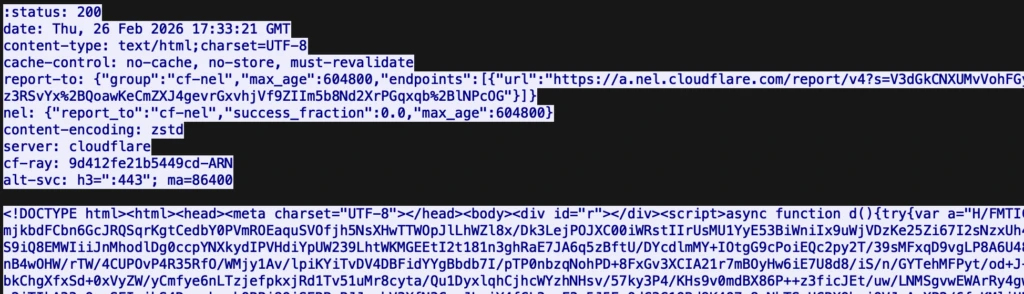
 Traffic decrypted with SSL decryption
Traffic decrypted with SSL decryption
When these artifacts appear in HTTP requests to non-legitimate hosts, they become high-signal network IOCs that analysts can use to detect related phishing infrastructure and pivot to other campaign assets during investigation.
EvilTokens signals a shift from credential theft to token exploitation at scale. By abusing trusted authentication flows, it dissolves the traditional boundaries of phishing detection. Its PhaaS accessibility, AI enhancements, and BEC integration amplify risks for Microsoft 365-dependent organizations. Proactive threat intelligence, policy hardening, and user awareness are essential to counter this stealthy threat before it leads to significant breaches.
Identity must be continuously verified, monitored, and contextualized.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.