Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


BQTLock is a ransomware-as-a-service (RaaS) malware family that emerged in 2025 and quickly gained attention due to its combination of file encryption, credential theft, and data exfiltration. BQTLock encrypts files using a hybrid AES-256 and RSA-4096 encryption scheme, demands payment in Monero cryptocurrency, and performs data theft and system reconnaissance.
|
Ransomware
Type
:
|
Unknown
Origin
:
|
|
15 July, 2025
First seen
:
|
8 April, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
15 July, 2025
First seen
:
|
8 April, 2026
Last seen
:
|

 438
438
 0
0

 2150
2150
 0
0

 2964
2964
 0
0
destinationIP:"92.113.146.56".
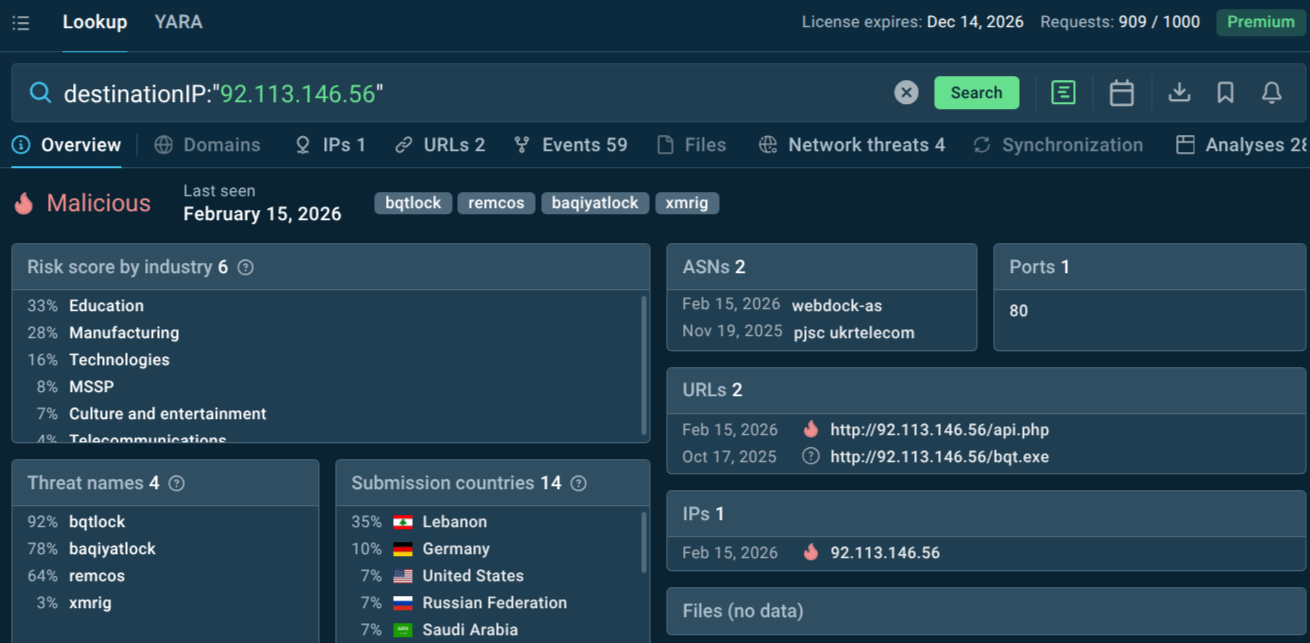 BQTLock domain with context data and malware analyses
BQTLock domain with context data and malware analyses
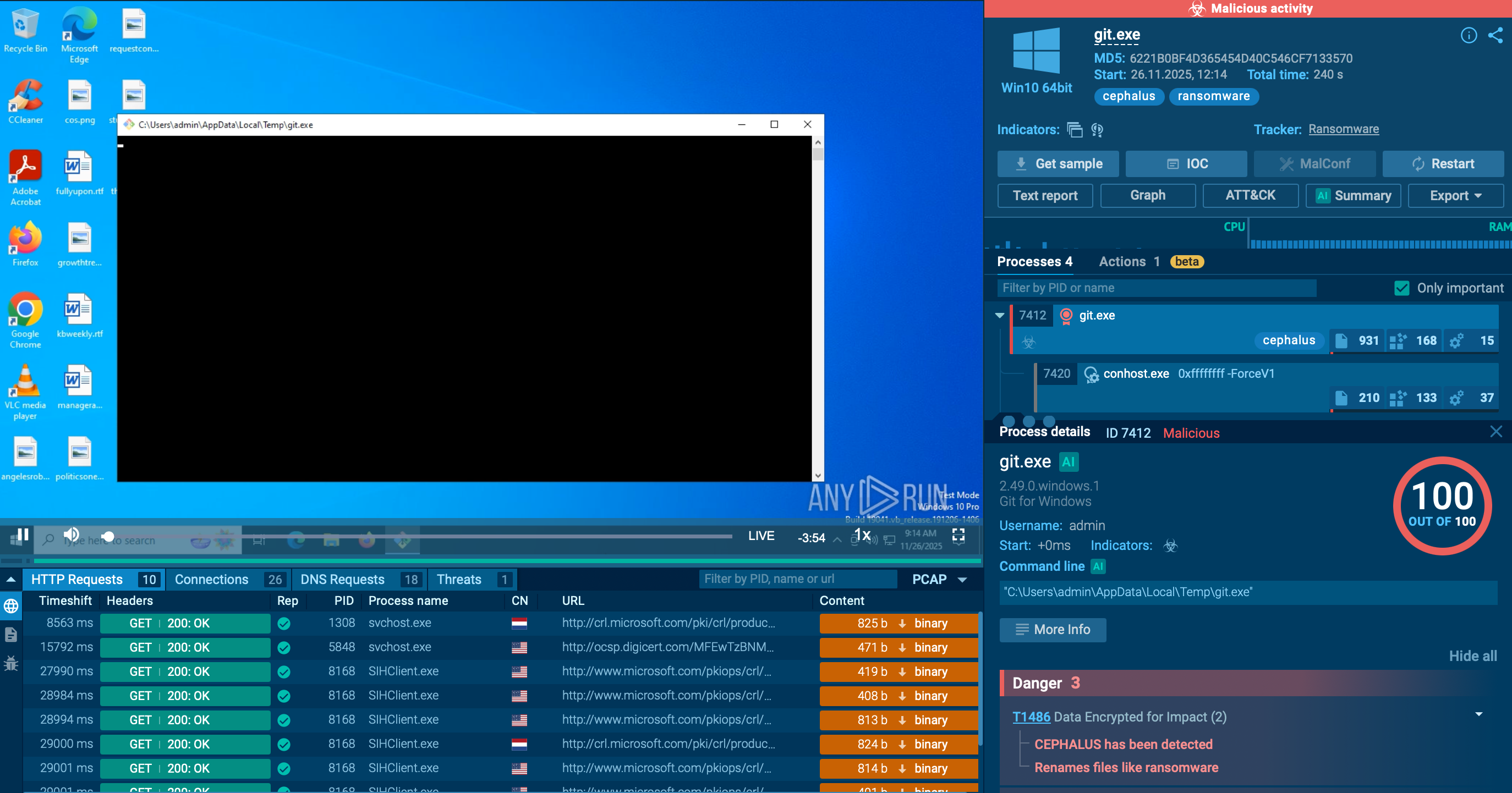
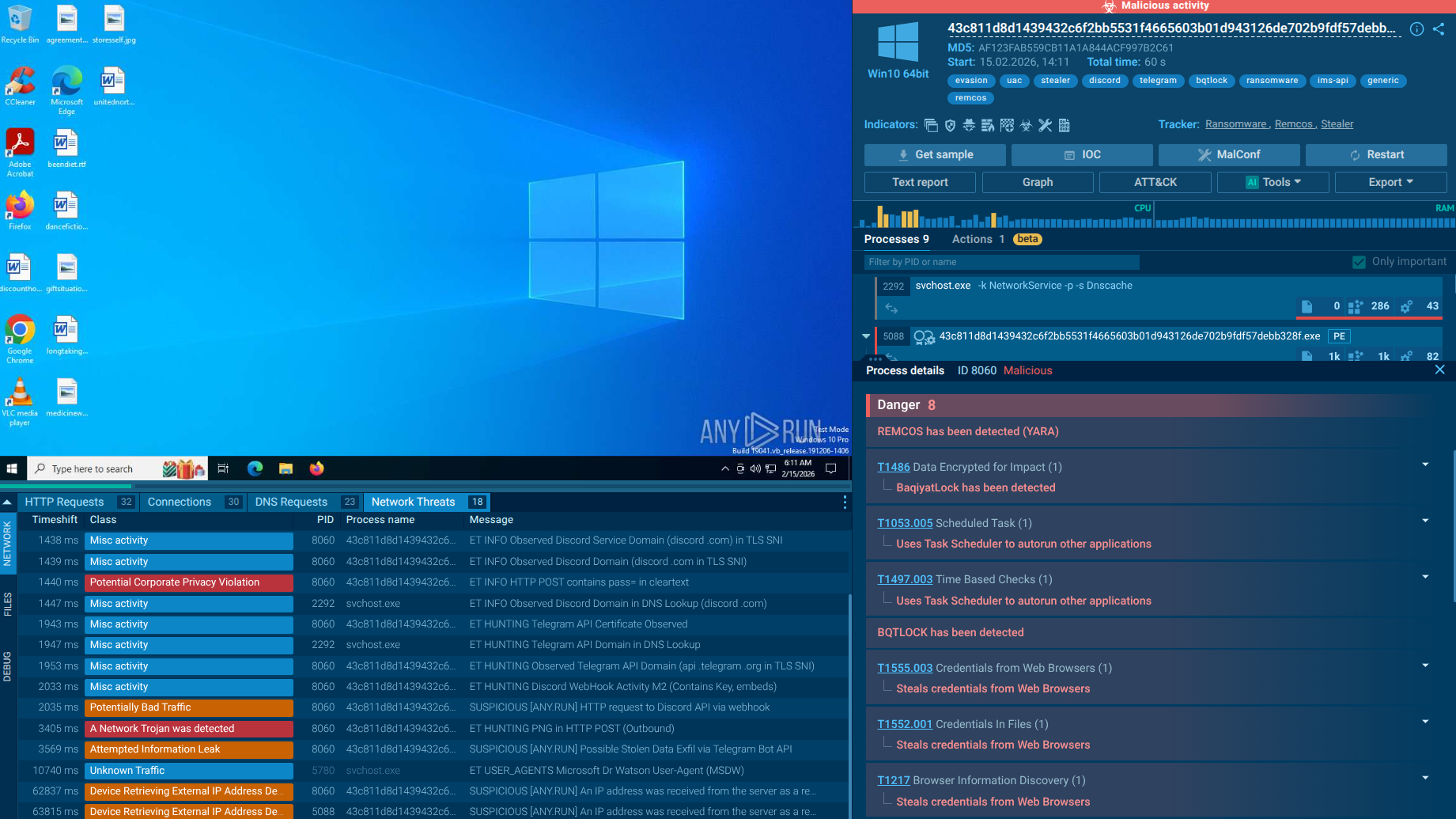 BQTLock fresh sample analysis in Interactive Sandbox
BQTLock fresh sample analysis in Interactive Sandbox
BQTLock is a sophisticated ransomware strain that emerged in mid-July 2025, operating under a full Ransomware-as-a-Service (RaaS) model. Also known as BaqiyatLock, it combines powerful hybrid encryption, advanced anti-analysis evasion, credential theft, and aggressive double-extortion tactics into a single, commercially distributed package. Linked to the threat actor known as ZerodayX (the alleged leader of the pro-Palestinian hacktivist group Liwaa Mohammed) BQTLock has attracted significant attention from security researchers for the speed of its development, the sophistication of its evasion mechanisms, and its openly commercial approach to cybercrime.
BQTLock represents a new generation of ransomware built for commercial scalability rather than targeted deployment by a single group. From its first appearance in July 2025, the malware has evolved rapidly. Researchers observed a significantly enhanced variant released on August 5, 2025, just weeks after the original, incorporating credential harvesting and expanded UAC bypass techniques.
The malware uses a hybrid encryption scheme combining AES-256 symmetric encryption with RSA-4096 asymmetric encryption. This pairing ensures that even if the symmetric key used to encrypt files is discovered, it cannot be decrypted without the attacker's private RSA key making recovery without paying the ransom effectively impossible absent a cryptographic flaw or law enforcement action. All encrypted files are appended with the .bqtlock extension, and victims are left with a ransom note.
BQTLock's ransom demands are structured as tiered "waves," priced in Monero (XMR) for maximum anonymity. Depending on the wave assignment found in the ransom note, victims may be charged between 13 XMR and 80 XMR (roughly $3,600 to over $22,000 at current exchange rates), with faster decryption processing tied to higher payment tiers. This gamified pricing structure is designed to maximize psychological pressure and speed of payment.
In addition to file encryption, BQTLock includes a mature information-stealing module. It harvests credentials stored in major browsers — Chrome, Firefox, Edge, Opera, and Brave — and accesses the Windows Credential Manager to extract system-level credentials. Stolen data is exfiltrated via Discord webhooks and Telegram channels.
BQTLock poses a multi-dimensional threat to organizations. Its dangers extend well beyond file encryption, touching operational continuity, data confidentiality, regulatory standing, and reputational integrity simultaneously.
Operational Disruption. Organizations that rely on real-time data access — hospitals, manufacturers, financial institutions — can find themselves operationally paralyzed within minutes. The 48-hour payment deadline and seven-day key destruction threat inject extreme urgency into crisis response, forcing organizations to make high-stakes decisions under pressure.
Data Theft and Double Extortion. Credentials extracted from browsers and the Windows Credential Manager can enable follow-on attacks — account takeovers, privilege escalation across cloud services, lateral movement into connected partner networks — that extend the damage of a single infection far beyond the initially compromised environment.
Persistence and Backdoor Access. BQTLock creates a hidden administrator account named BQTLockAdmin and establishes a scheduled task disguised as "Microsoft\Windows\Maintenance\SystemHealthCheck" that persists across reboots. This means that even after an organization believes it has remediated an infection, the threat actor may retain access to the environment.
Financial Impact. Beyond the ransom itself, organizations face the costs of incident response, forensic investigation, potential regulatory fines (especially under GDPR, HIPAA, or similar frameworks), and reputational damage.
BQTLock's RaaS model means that targeting decisions are partially decentralized. Affiliates choose their own victims, often guided by opportunism, data value, or ideological motivation. The hacktivist associations of its core developer suggest that geopolitically sensitive targets may be disproportionately represented. However, certain structural factors make some sectors especially vulnerable regardless of attacker intent.
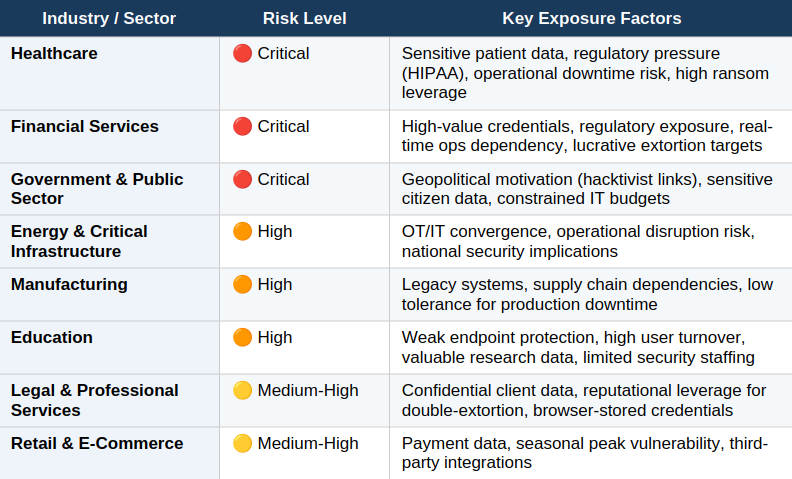 Is your business at risk? Most targeted sectors
Is your business at risk? Most targeted sectors
BQTLock's credential-harvesting capability introduces a second-order victimology: organizations whose credentials are stolen may find themselves targeted in subsequent, unrelated attacks by actors who purchase stolen data. Supply chain partners, cloud service providers, and third-party vendors connected to primary victims should also consider themselves at elevated risk following any confirmed BQTLock incident in their ecosystem.
ANY.RUN's TI Lookup gives security analysts instant access to a searchable database populated by real malware executions from 15,000 organizations worldwide. When a suspicious file hash, IP address, domain, or registry key appears in an alert, analysts can query TI Lookup and receive verdict and context within seconds, including whether the indicator has been associated with BQTLock activity. This eliminates hours of manual OSINT research and gives SOC teams the evidence they need to act decisively on high-priority incidents.
sha256:"4437ab9c5db3c5ebb9235b4adade504153fa39ca5774ac8c6145a0b7c97a97eb"
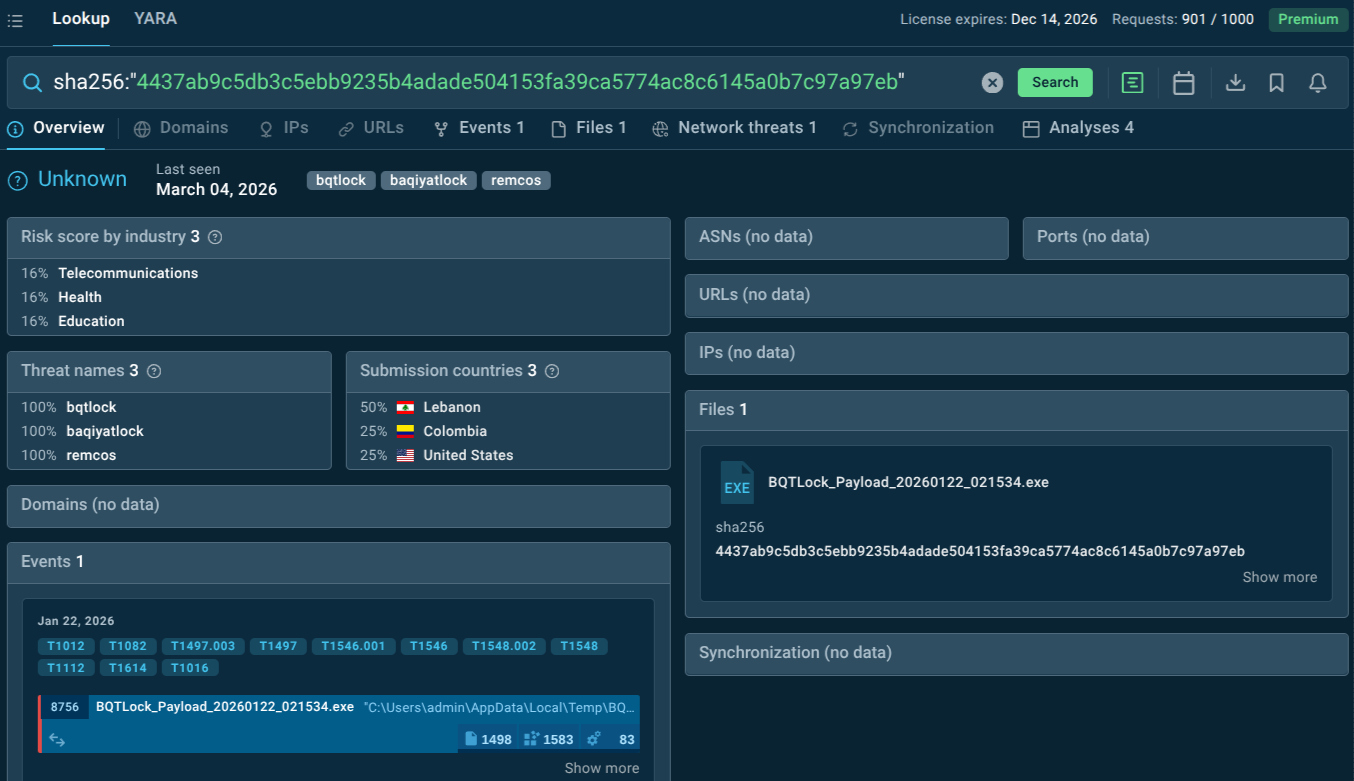 File hash linked to BQTLock samples
File hash linked to BQTLock samples
ANY.RUN's TI Feeds deliver a continuous stream of verified malicious network indicators extracted from live sandbox executions in STIX/TAXII format. Security teams can integrate these feeds directly into their SIEM, EDR, NGFW, IDS/IPS, or TIP platforms without custom development. As BQTLock evolves and new variants introduce new C2 infrastructure, TI Feeds ensure that downstream blocking rules are updated in near-real time — before most threat intelligence reports describing the new variant have even been written.
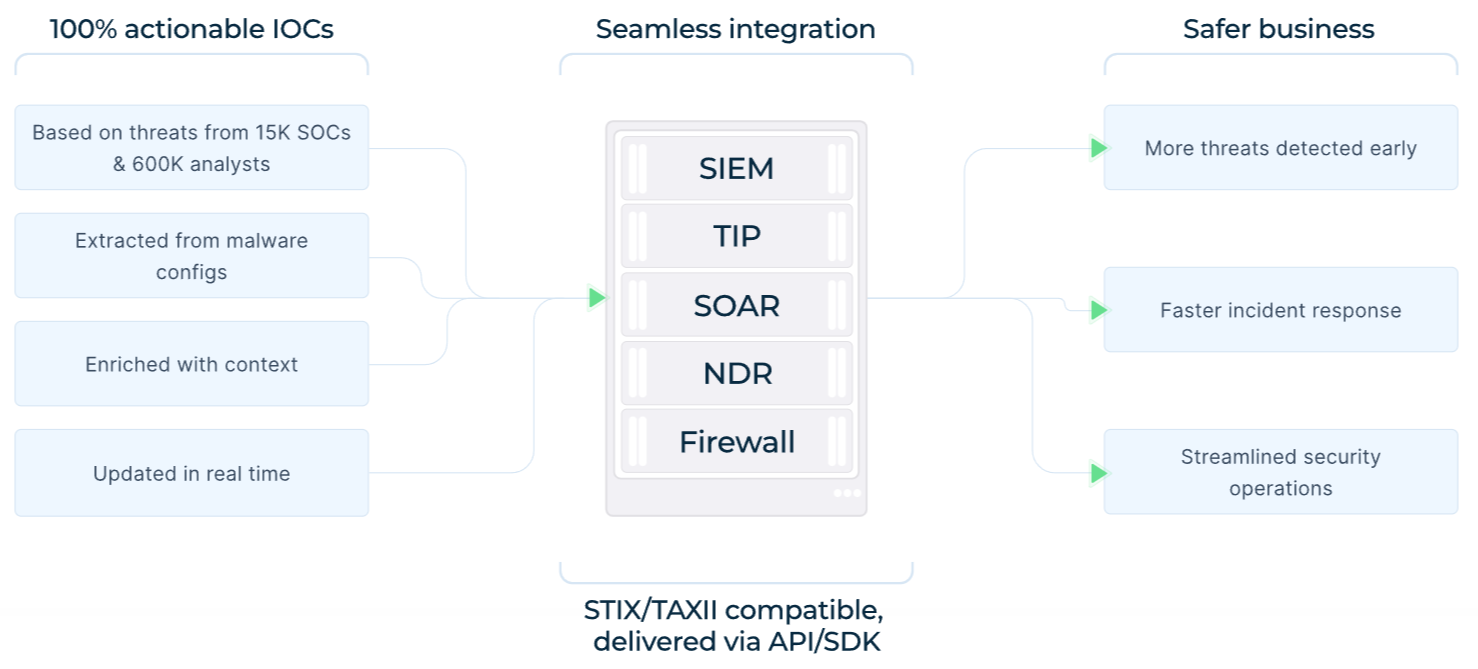 TI Feeds: benefits, data sources, integration options
TI Feeds: benefits, data sources, integration options
Other Defensive Measures
Implement offline, immutable backups on a regular schedule and test restoration procedures before an incident occurs.
Deploy endpoint detection and response (EDR) tools configured to flag process hollowing, unusual scheduled task creation, and new local administrator account creation — all behaviors exhibited by BQTLock.
Enforce application whitelisting to prevent the execution of unsigned or unexpected executables, particularly those delivered via ZIP archives.
Block execution of scripts and executables from temporary directories (e.g., C:\Windows\Temp) where BQTLock stages its payload.
Apply the principle of least privilege to limit the blast radius of any credential compromise; disable or restrict Windows Credential Manager storage for sensitive accounts.
Enable and monitor Windows Event Logs for UAC bypass attempts, particularly involving fodhelper.exe, eventvwr.exe, and CMSTP.exe.
Conduct phishing awareness training with emphasis on ZIP attachment risks and the dangers of executing files named generically (e.g., "Update.exe").
Use ANY.RUN's Sandbox to safely detonate suspicious files and observe full behavioral chains.
Common entry vectors include:
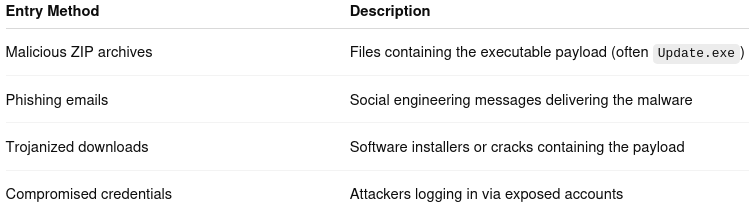 BQTLock initial access methods
BQTLock initial access methods
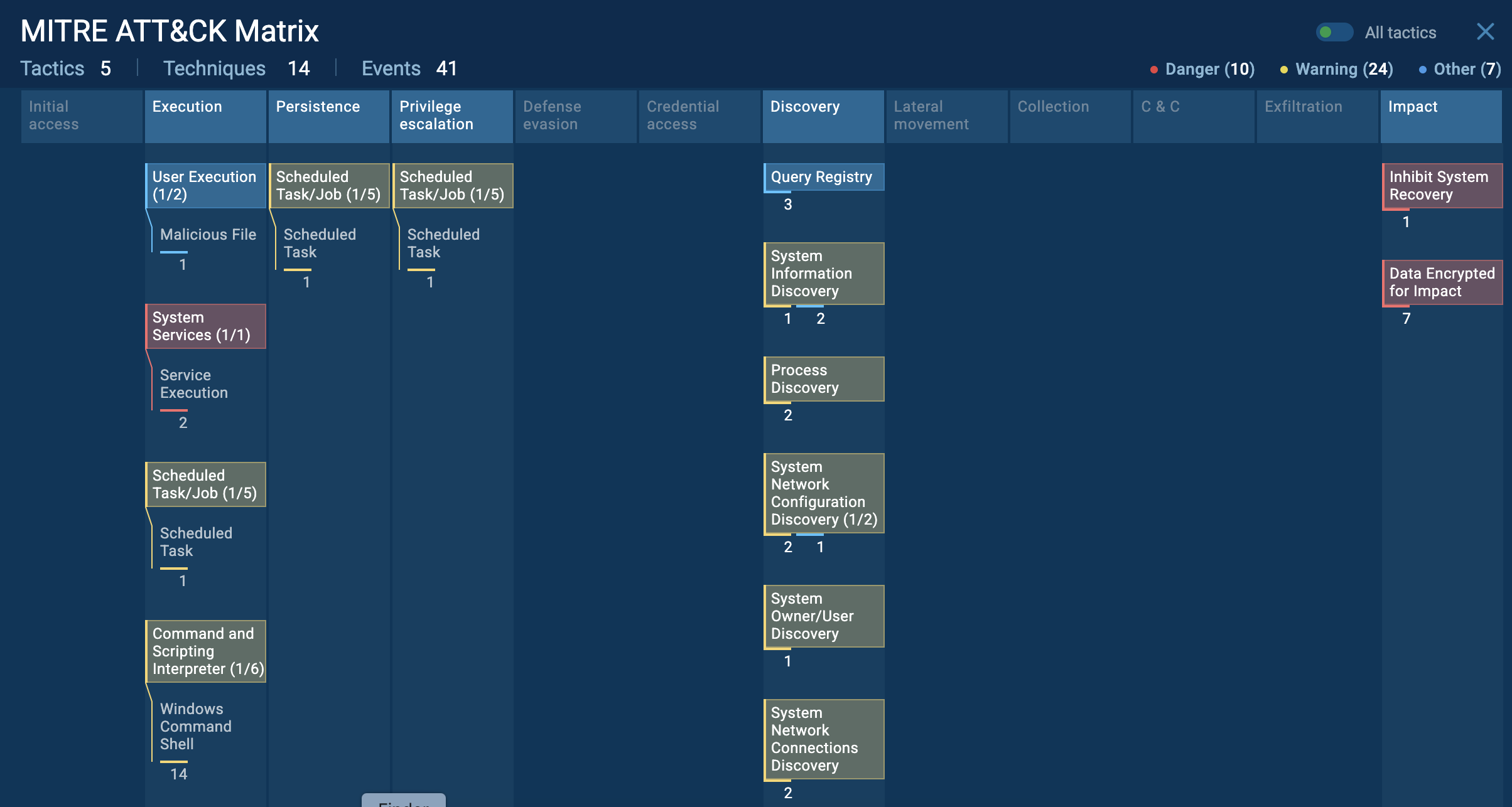
Execution and Privilege Escalation
Upon execution, BQTLock performs an immediate anti-analysis check using the IsDebuggerPresent() API and creates a global mutex to prevent duplicate execution. If no analysis environment is detected, it proceeds to escalate privileges through multiple UAC bypass techniques: abusing CMSTP.exe with crafted .inf files, and manipulating registry keys associated with fodhelper.exe and eventvwr.exe auto-elevation behaviors. These methods allow the malware to acquire administrative privileges without triggering visible UAC prompts to the user.
Lateral Movement
BQTLock checks the USB bus for connected removable media, enabling it to spread to other systems via external drives. It also enumerates shared network resources, potentially enabling encryption of mapped network drives visible from the initially compromised host. The credentials harvested from browsers and the Windows Credential Manager can be used to authenticate to additional systems within the network, supporting broader lateral movement.
Persistence
The malware establishes persistence through a scheduled task named "Microsoft\Windows\Maintenance\SystemHealthCheck", configured to execute at user logon with elevated privileges. It also creates a hidden administrator account (BQTLockAdmin) to maintain backdoor access. A self-deleting .bat script is deployed to remove the original executable and reduce forensic artifacts after the payload has completed its initial execution phase.
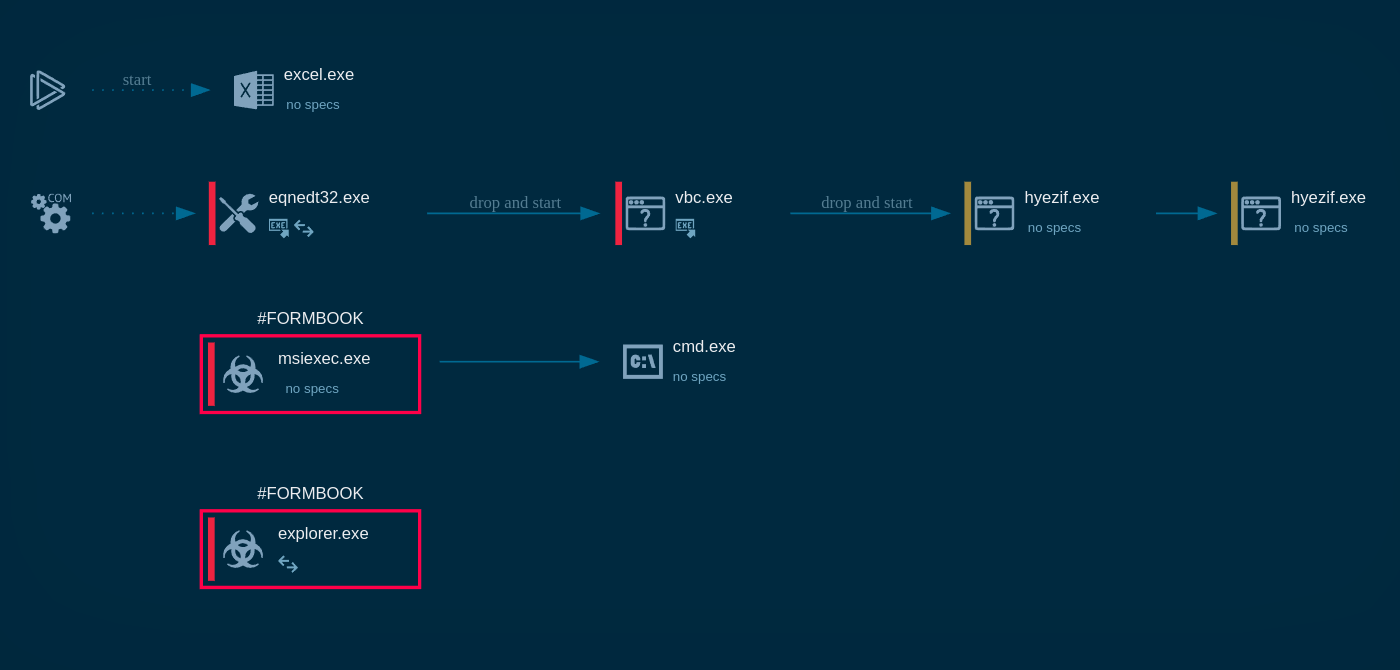
Process Injection and Code Hiding
BQTLock uses process hollowing targeting explorer.exe — a technique in which the malware injects its code into a legitimate Windows process, running malicious operations under the cover of a trusted system binary. This significantly reduces the likelihood of detection by security tools that whitelist known Windows processes.
Credential Theft
Credential harvesting targets browser data stores for Chrome, Firefox, Edge, Opera, and Brave, as well as the Windows Credential Manager. Credentials are temporarily written to C:\Windows\Temp\bqt_passwords.txt before exfiltration. Screenshots and system metadata are sent alongside credentials via Telegram bot tokens and Discord webhooks hardcoded in the malware's configuration.
Encryption Routine
The encryption engine uses AES-256 for the bulk encryption of file contents (fast, symmetric) and RSA-4096 to encrypt the AES key (making it irrecoverable without the attacker's private key). Files of all types are targeted; each receives the .bqtlock extension. A completion notification is sent to the attacker's Telegram channel, confirming successful encryption of the victim's environment.
Ransom Demand
The ransom note dropped to the victim's system includes a unique victim ID that maps to a specific payment wave tier, a Telegram contact link, and explicit warnings against using third-party recovery tools or backups. The 48-hour doubling deadline and seven-day key deletion threat are enforced through the RaaS platform's real-time infection monitoring dashboard.
See full execution chain of BQTLock
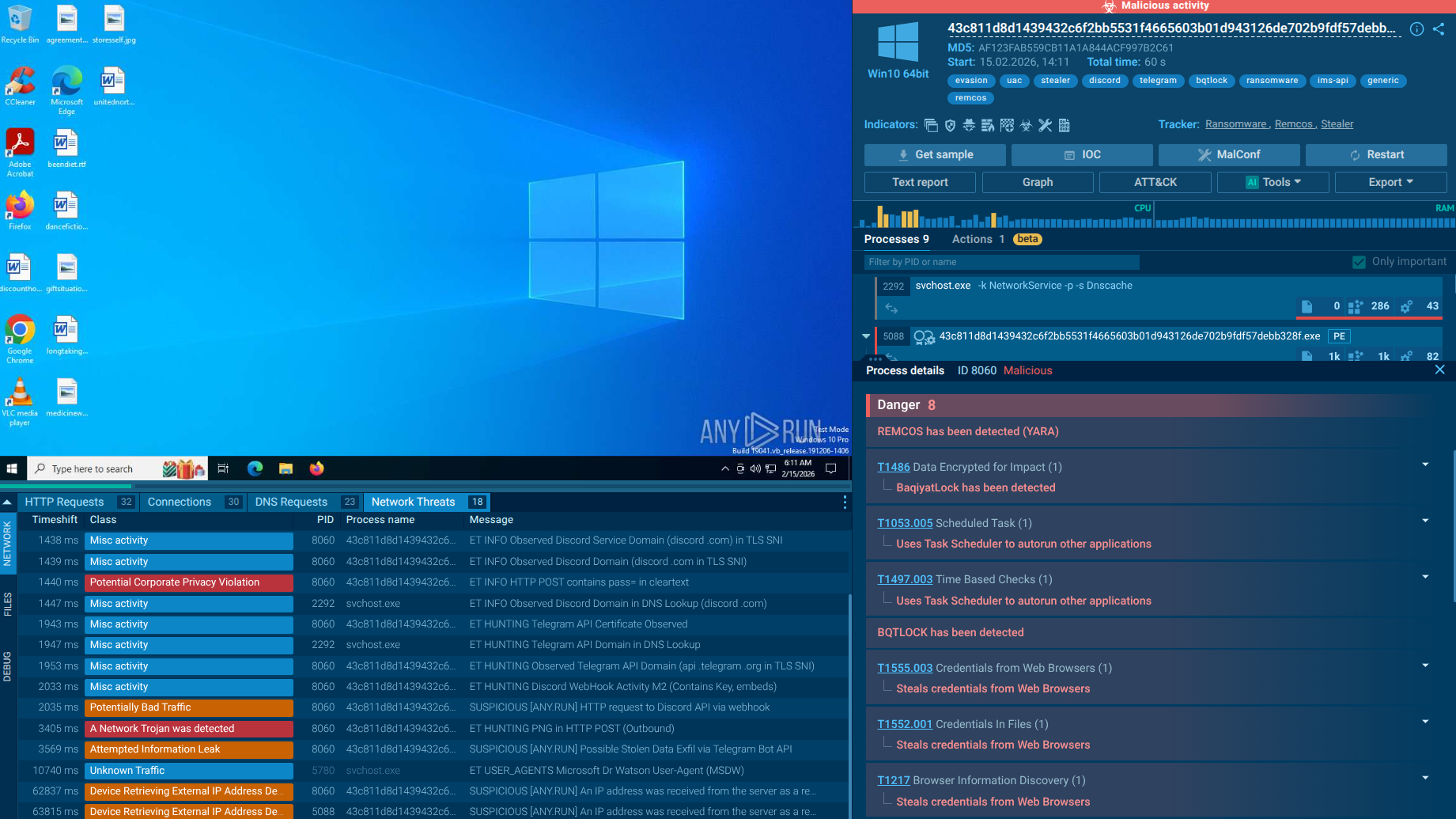 ANY.RUN sandbox revealing BQTLock behavior in real time
ANY.RUN sandbox revealing BQTLock behavior in real time
When launched, BQTLock performs a UAC bypass using fodhelper. When fodhelper.exe starts, it accesses a specific registry key and executes the command specified there. Because fodhelper.exe has the autoElevate flag, the operating system automatically elevates the privileges of the launched component. This allows the malware to obtain administrator privileges without displaying a UAC prompt to the user, resulting in the program running with admin rights.
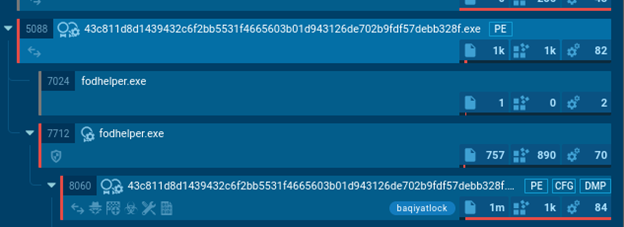 Upon-launch BQTLock activity
Upon-launch BQTLock activity
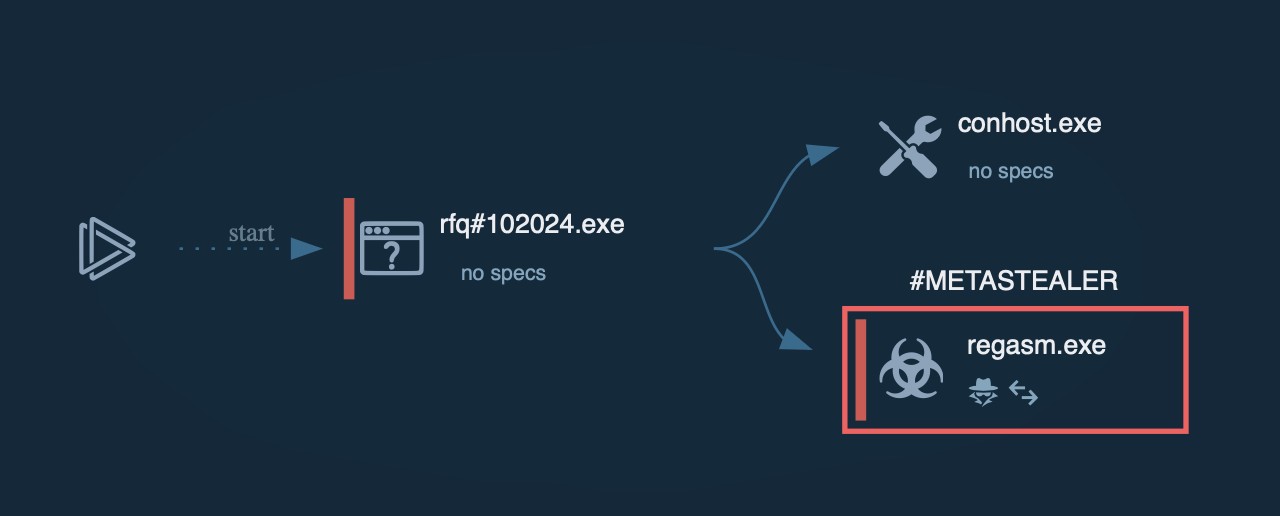
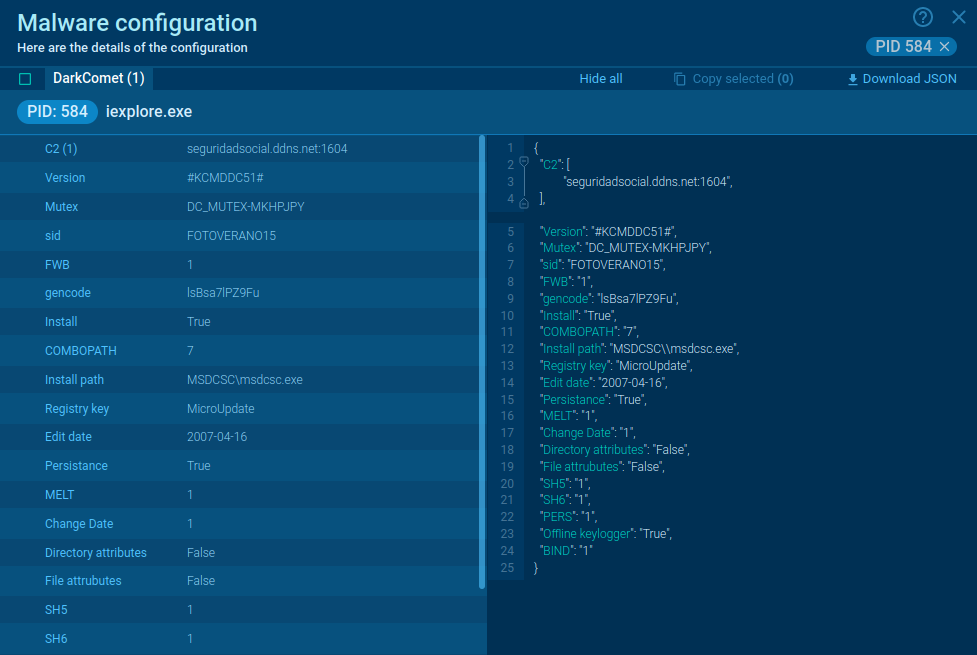
A distinctive feature of this campaign is the use of an infection chain involving Remcos, which is injected into the Windows Explorer process.
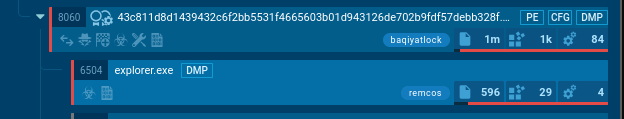 Remcos injected in Explorer
Remcos injected in Explorer
To ensure persistence in the system, the malware creates a task in the Windows Task Scheduler.
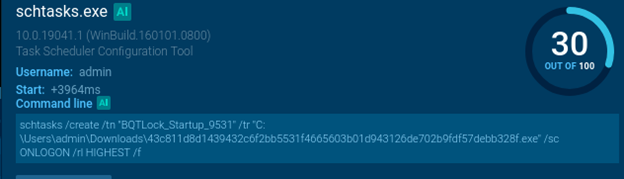 BQTLock’s Scheduler task
BQTLock’s Scheduler task
During execution, BQTLock modifies the system registry. This modification forces Windows Explorer to refresh its contents, allowing the victim to notice changes in the file system more quickly.
HTTP requests reveal connections to the service http://icanhazip[.]com/, which is used to determine the victim machine’s public IP address.
The malware also attempts to communicate with several command-and-control (C2) servers, including connection attempts to Discord and Telegram, which fail. A successful connection is established with http://92[.]113[.]146[.]56/api[.]php, followed by further communication with this endpoint.
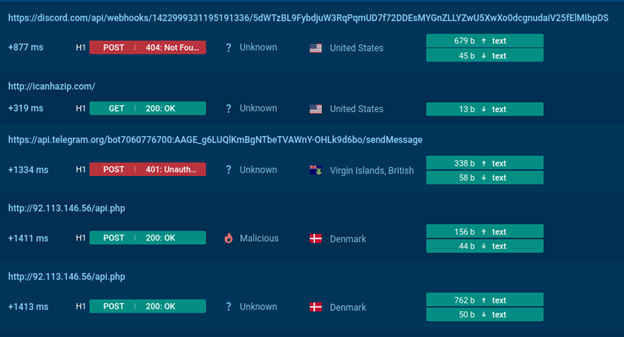 BQTLock’s connection requests
BQTLock’s connection requests
Files are encrypted with the .bqtlock extension, and a ransom note named README_TO_DECRYPT.txt is dropped. The malware also changes the desktop wallpaper.
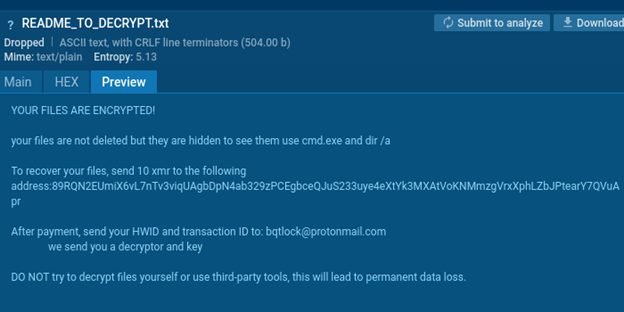 BQTLock’s ransom note
BQTLock’s ransom note
These parameters, including the C2 infrastructure, can be modified in the ransomware builder, so they may vary between different samples.
In addition to its primary functionality of file encryption, the malware includes data theft capabilities, such as taking screenshots or extracting stored passwords.
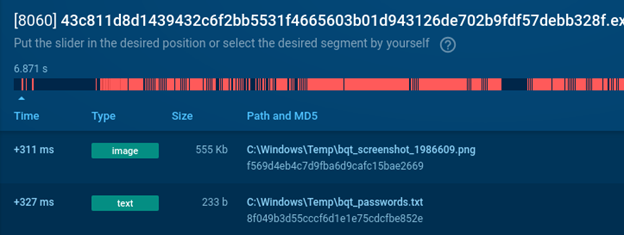 BQTLock’s harvesting sensitive data
BQTLock’s harvesting sensitive data
BQTLock illustrates how modern ransomware operations have evolved into commercialized cybercrime platforms.
Its combination of ransomware-as-a-service infrastructure, credential theft, advanced evasion techniques, and double extortion tactics makes it a serious threat for organizations of all sizes.
Because ransomware campaigns often rely on recognizable infrastructure and behavioral patterns, proactive threat intelligence and behavioral analysis are essential tools for identifying attacks before they cause operational damage.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.
.png)