Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


Octo malware, also known as ExobotCompact or Coper, is a sophisticated Android banking trojan that has evolved from earlier malware family Exobot. It poses a significant threat to financial institutions, mobile users, and enterprise networks.
|
Trojan
Type
:
|
Unknown
Origin
:
|
|
1 February, 2021
First seen
:
|
26 March, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 February, 2021
First seen
:
|
26 March, 2026
Last seen
:
|

 97
97
 0
0
 2336
2336
 0
0

 1719
1719
 0
0
Octo, also known as Coper or ExobotCompact, is an Android banking Trojan that evolved from the Exobot malware family, first observed in 2016. Initially based on the Marcher Trojan, Exobot targeted financial institutions globally until 2018, when a lighter version, ExobotCompact, emerged.
By 2021, a new variant appeared, named Coper by some antivirus vendors, but later renamed as Octo — a rebranded and enhanced ExobotCompact. In 2024, Octo2, an even more advanced iteration, was released, driven partly by the leak of Octo’s source code. The Malware-as-a-Service (MaaS) model makes Octo accessible to even novice cybercriminals.
Lineage:
The malware targets Android devices through social engineering and malicious app distribution:
Once installed, Octo prompts users to enable Accessibility Services and give out Device Admin privileges, granting extensive control over the device, and enhances remote access stability.
Its communications with C2 servers include dynamic configurations to target specific apps (e.g., to block push notifications from banking apps).
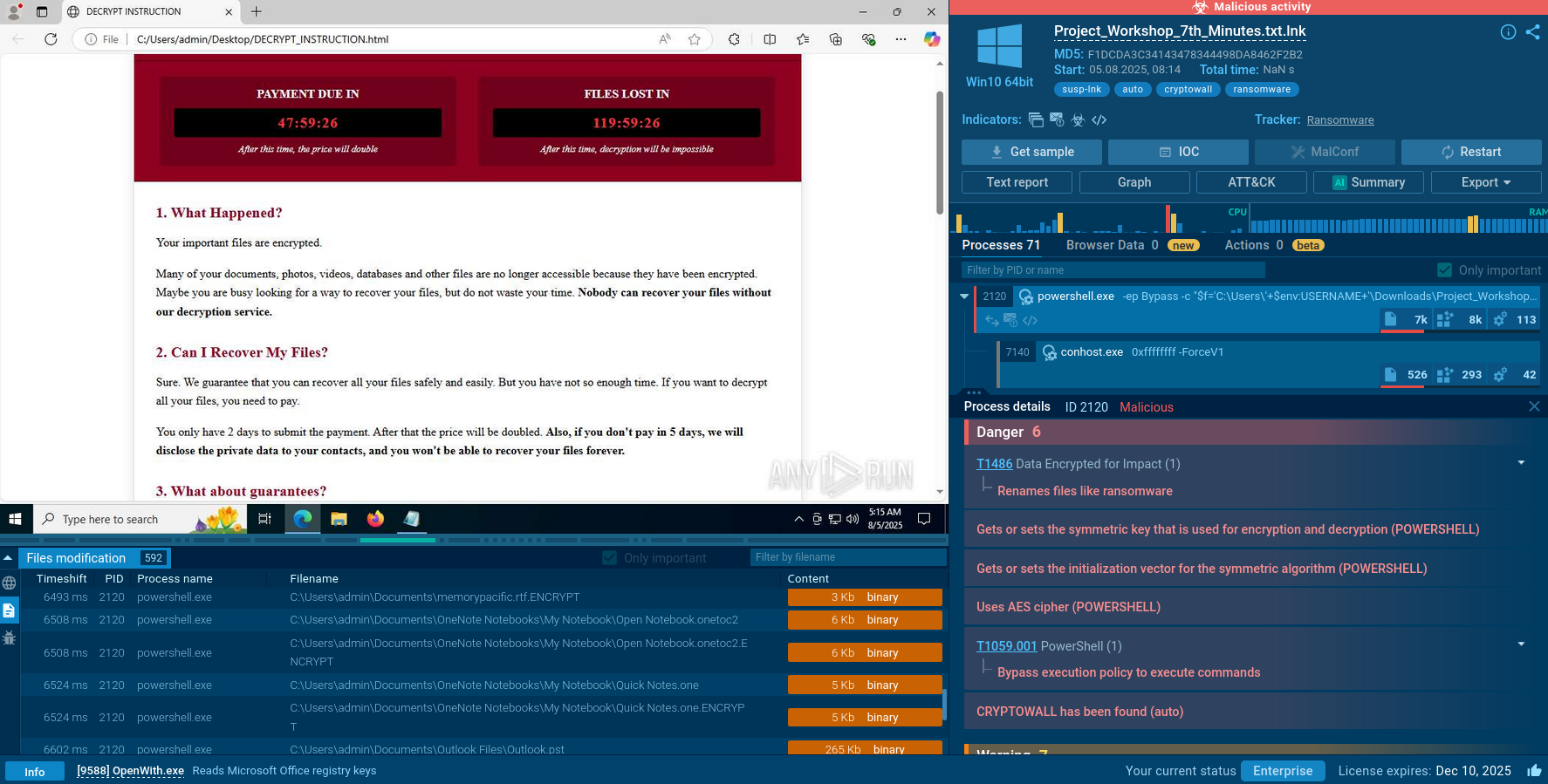
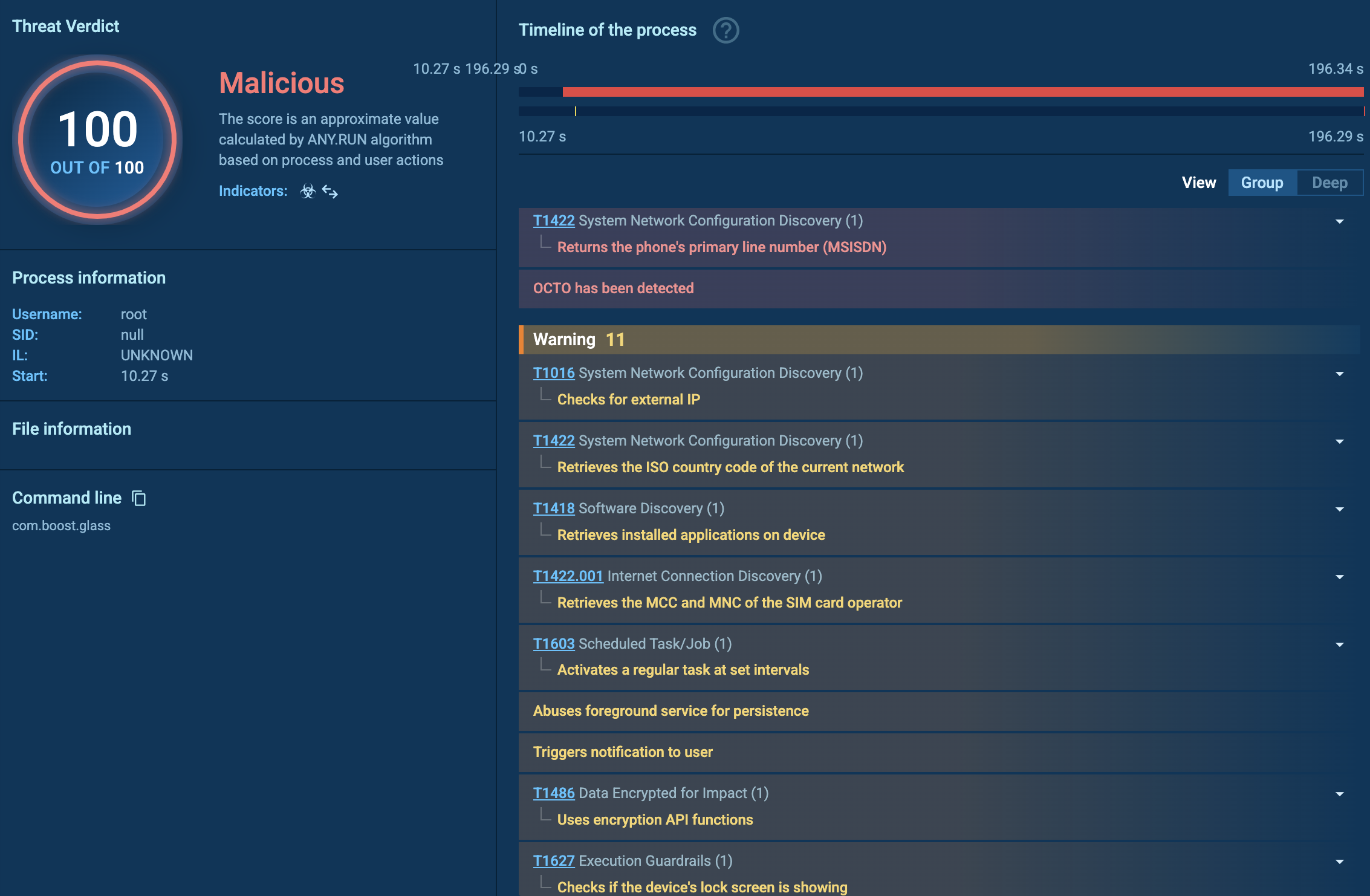
ANY.RUN’s Interactive Sandbox supports the analysis of APK files and enables the research of Android malware. Let us observe the behavior of an Octo sample where the malware is disguised as Google Chrome browser.
View Octo analysis session in the Sandbox
Once installed, Octo — also known as Coper or ExobotCompact — connects to its command and control (C2) server, potentially using a domain generation algorithm (DGA) to maintain resilient, encrypted communication. In our case, the address was toplamakampiyolculukhazirlik[.]xyz, visible in the DNS requests tab, though unresolved. The C2 provides configuration files and commands specifying which apps to target and what actions to take. In this task, the C2 was already offline.
Octo abuses Android’s Accessibility Service and MediaProjection APIs to gain full remote control, enabling real-time screen streaming, simulated taps, gestures, clipboard access, and text input. To stay hidden, it can display a black screen, dim brightness to zero, and disable notifications.
The malware supports keylogging, SMS and notification interception, blocking app alerts, screen locking/unlocking, muting sound, launching apps, and sending SMS. Attackers use AES-encrypted, Base64-encoded commands to control these features and perform on-device fraud—initiating and confirming transactions without triggering alarms.
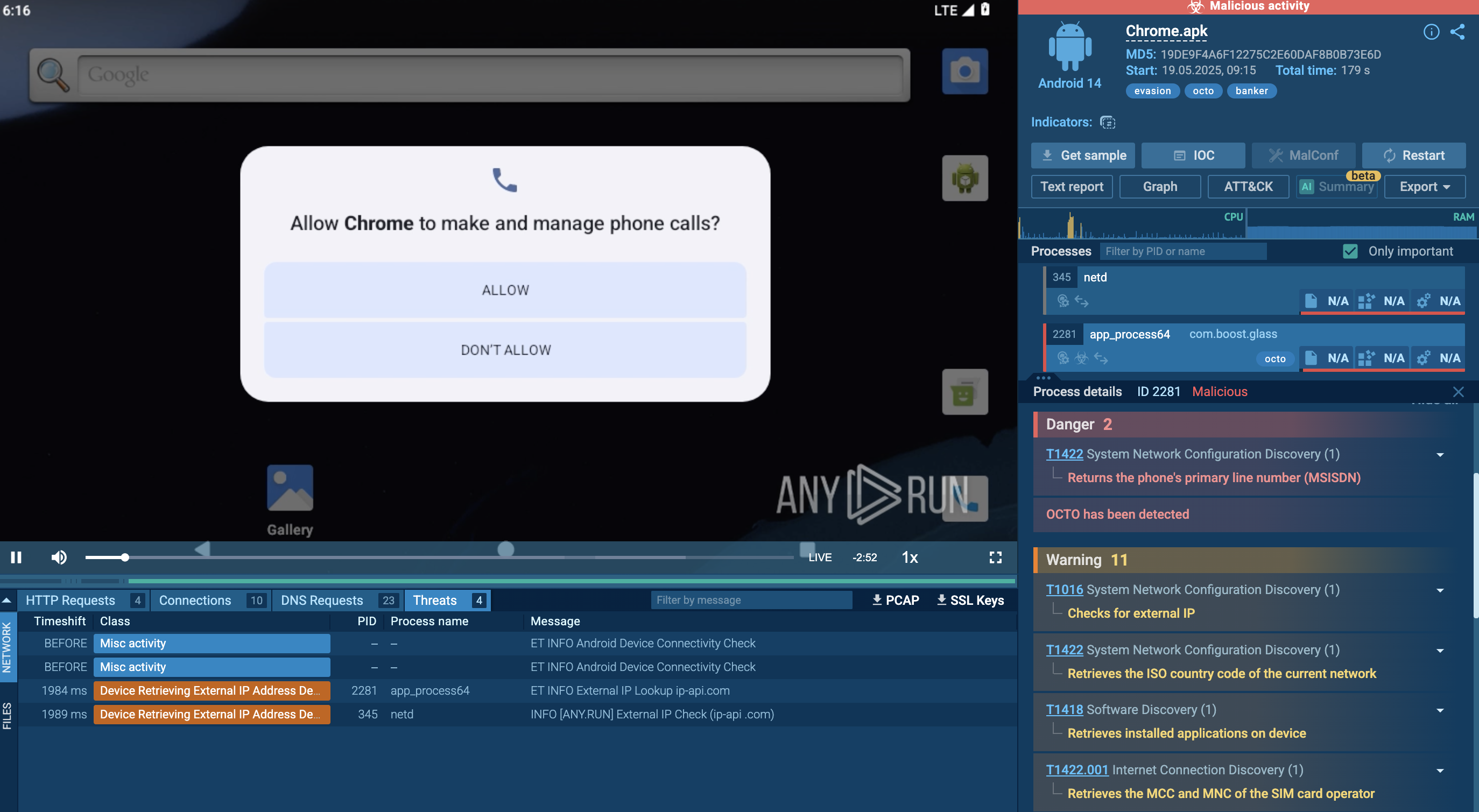 Octo mobile trojan analysis in ANY.RUN's Interactive Sandbox
Octo mobile trojan analysis in ANY.RUN's Interactive Sandbox
Octo can also inject fake overlays to steal credentials and uninstall competing or security apps to maintain persistence and avoid detection.
This malware employs advanced methods to avoid detection. It requires no root access using Accessibility Services for control. Its small, modular codebase demonstrates a lightweight footprint helping to avoid detection by traditional antiviruses. Besides, obfuscation is applied, along with multi-layered code encryption, dynamic loading of malicious libraries. Continuous updates by developers and forks from the 2024 source code leak keep Octo ahead of traditional detection methods.
While many campaigns are not publicly attributed due to the nature of mobile malware distribution, several have been documented by security vendors and researchers.
| Year | Campaign / Actor | Region | Method | Targets |
|---|---|---|---|---|
| 2022 | Coper (Octo variant) | Latin America | Fake banking apps, smishing | Colombian & Peruvian banks |
| 2022 | Octo advertised on dark web | Global | Malware-as-a-Service (MaaS) | European banks |
| 2022 | Fake Chrome Update | Global | Smishing, fake update | Generic users, credential theft |
| 2022–23 | Google Play fake apps | Global | Dropper apps | Banking and crypto users |
Octo can be detected by such indicators as C2 domains, IPs, and unusual DNS traffic. Among the behavioral indicators, analysts should pay attention to background services that relaunch on boot, the use of Accessibility APIs, and unexpected overlays over banking apps. Its APK signatures include package names often mimicking known apps and typical permissions requests, like SYSTEM_ALERT_WINDOW, BIND_ACCESSIBILITY_SERVICE.
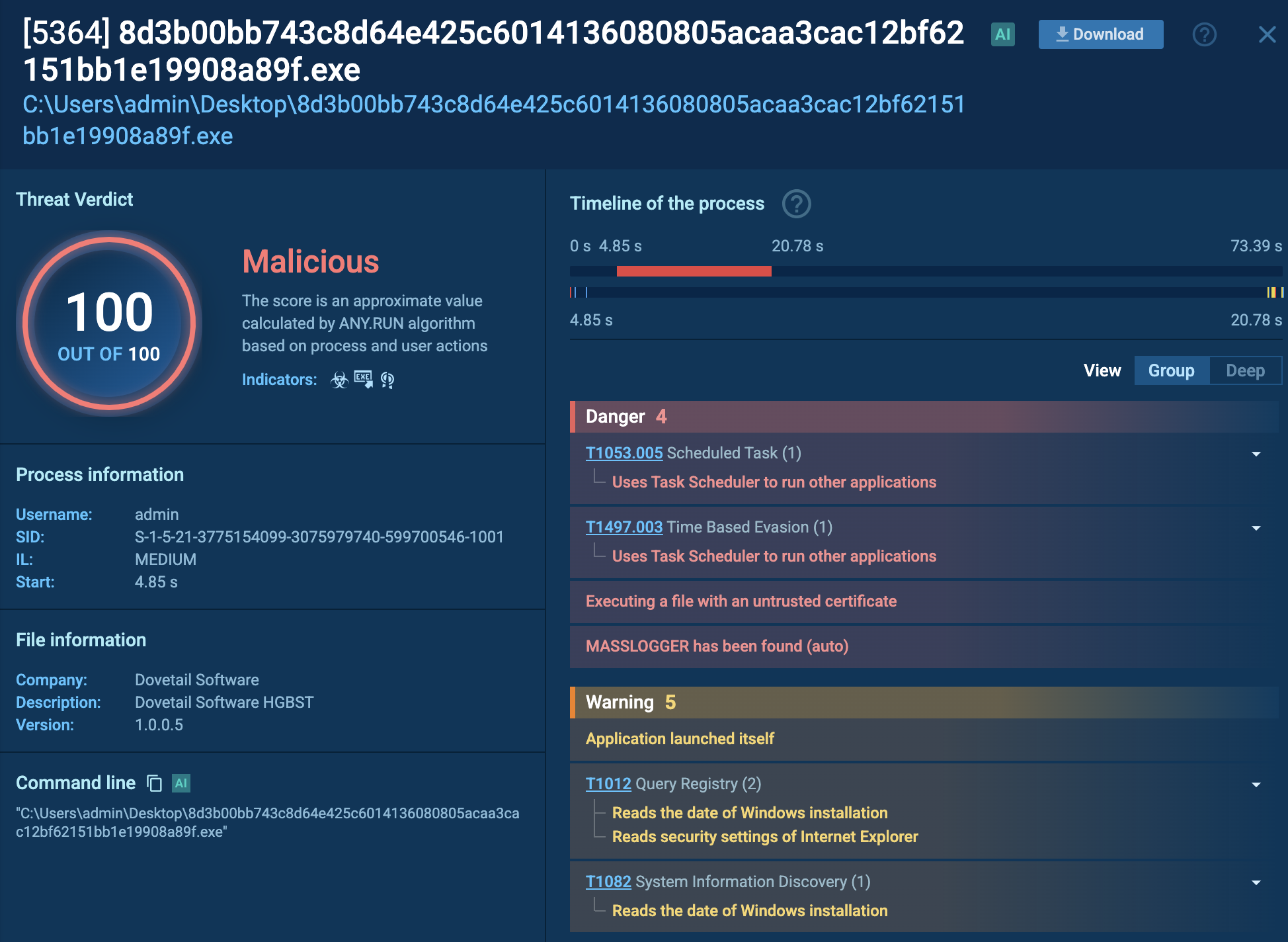
To start gathering actionable data via ANY.RUN's Threat Intelligence Lookup, search for the malware name and its aliases:
threatName:"octo" OR threatName:"exobot*"
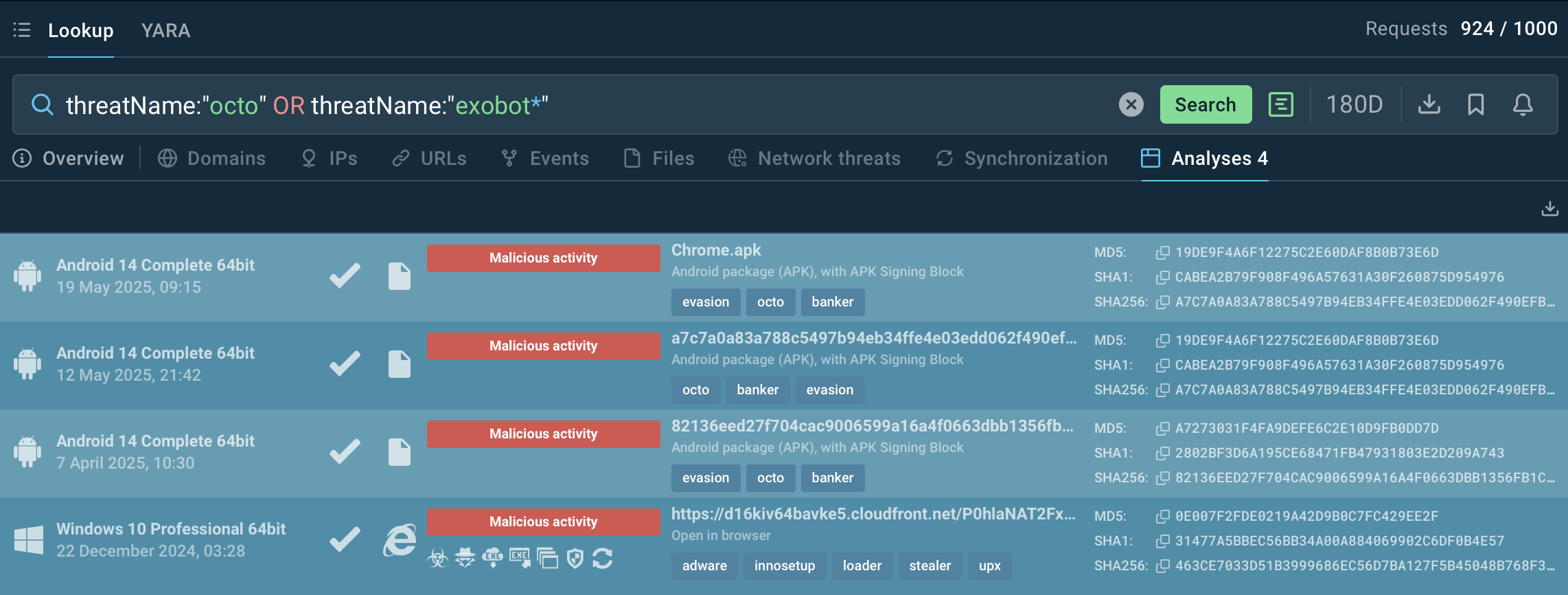 Add all of the Octo’s names to a single search request
Add all of the Octo’s names to a single search request
Select and view analysis sessions to collect IOCs, IOBs, view processes, and study the malware’s TTPs to set up detection and response system, to develop prevention and mitigation strategies.
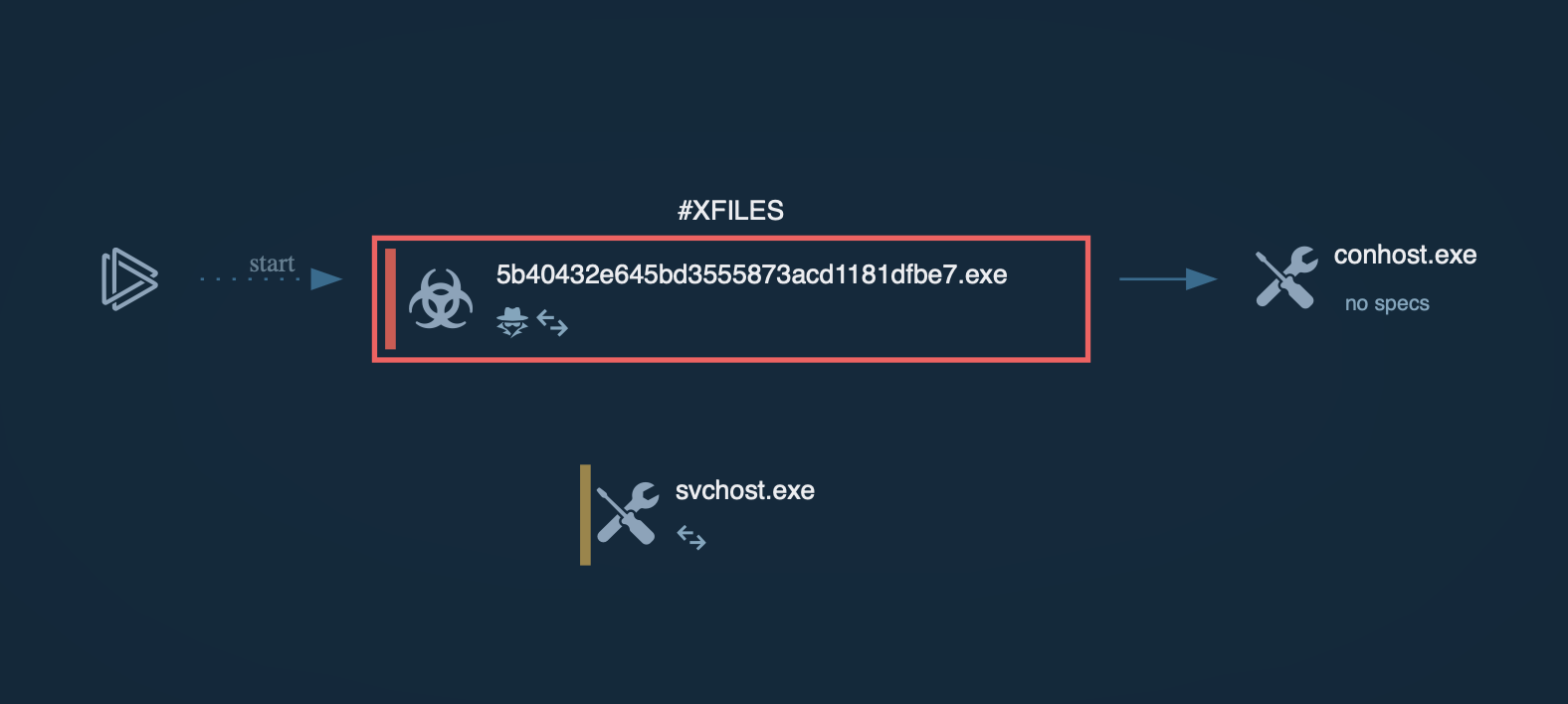
 View malicious processes in detail
View malicious processes in detail
Octo malware (ExobotCompact / Coper) is one of the most advanced mobile threats in circulation, particularly dangerous because it provides real-time remote access and can bypass many layers of authentication and fraud detection. While it mainly targets banking users, its modularity and stealth make it a viable tool for cybercrime groups and potential APT-style attacks against enterprises. Countering Octo demands robust threat intelligence, proactive user education, and strict device security practices.
Start with 50 requests in TI Lookup to collect IOCs on the evolving Android malware