Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


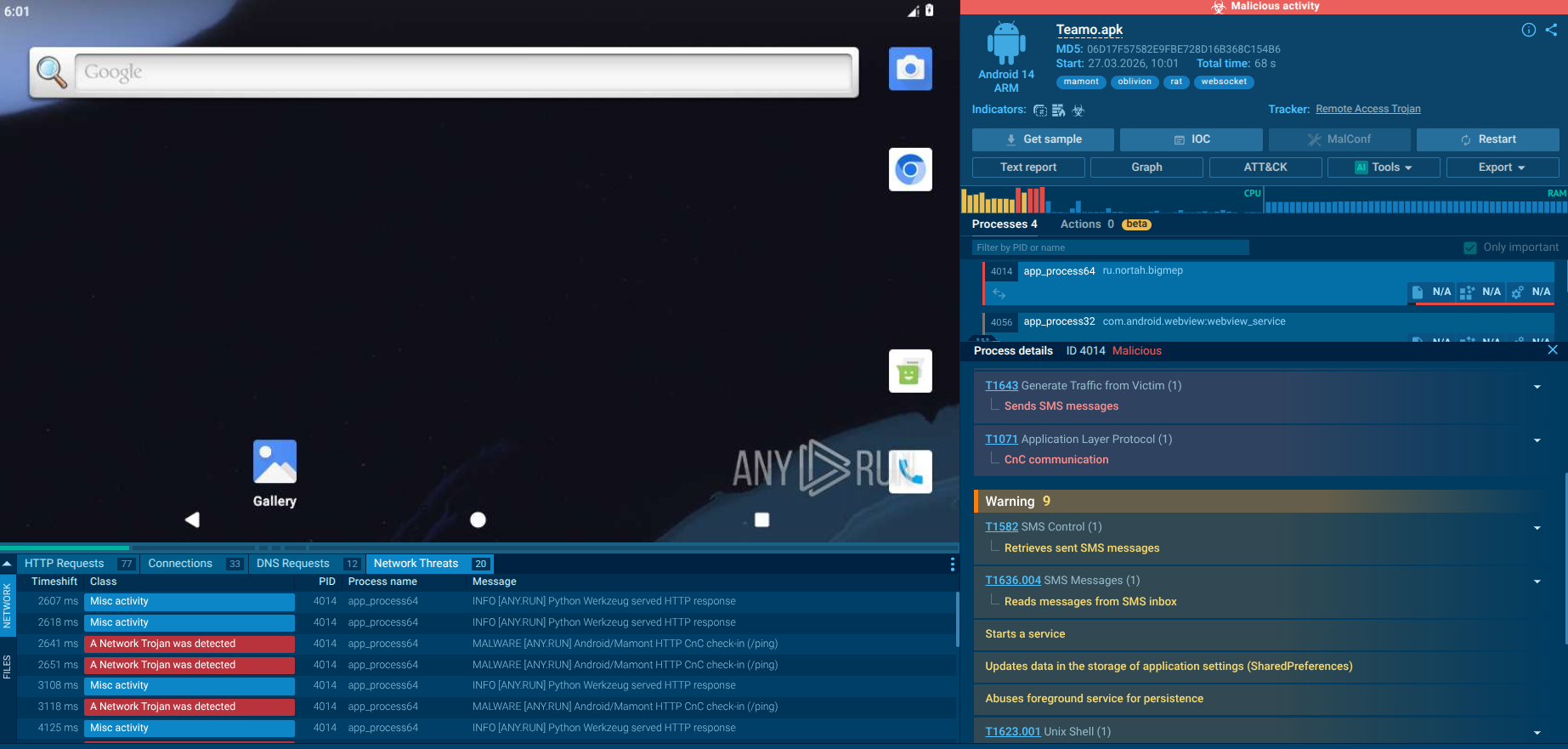
Oblivion RAT is a sophisticated Android Remote Access Trojan (RAT) offered as Malware-as-a-Service (MaaS) on cybercrime forums for as little as $300 per month. It equips even novice attackers with a complete toolkit, including a web-based APK builder, dropper generator mimicking Google Play updates, and a real-time C2 panel. The RAT enables full device takeover, data theft, and financial fraud through deceptive social engineering and Accessibility Service abuse.
|
RAT
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
17 April, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
17 April, 2026
Last seen
:
|

 3110
3110
 0
0

 6852
6852
 0
0

 7020
7020
 0
0
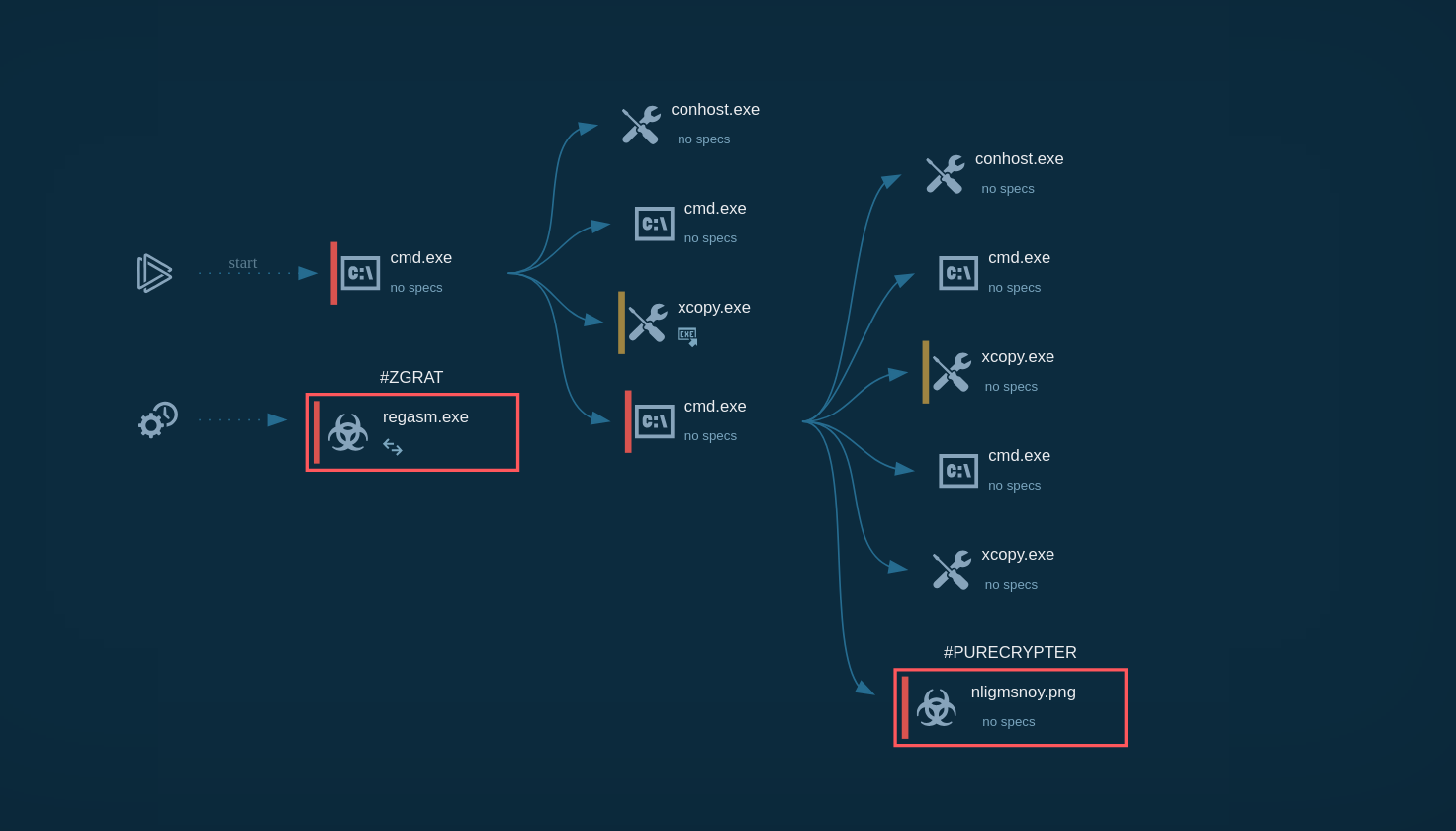
Oblivion RAT is a new Android MaaS RAT sold for $300/month with built-in APK and dropper builders for easy deployment.
It uses fake Google Play update pages and Accessibility Service abuse for silent, permissionless installation.
Core features include hidden VNC control, SMS/2FA interception, keylogging, and “Wealth Assessment” for targeting financial apps.
Businesses face risks of data theft, fraud, and compliance breaches, especially in finance, defense, and mobile-heavy sectors.
The threat has already infected over 7,500 devices since early 2026, with campaigns scaling rapidly via social engineering.
Use ANY.RUN TI Lookup to hunt Oblivion proactively: search IOCs and enrich investigations instantly to block emerging variants before they strike.
destinationIP:"193.221.200.242".
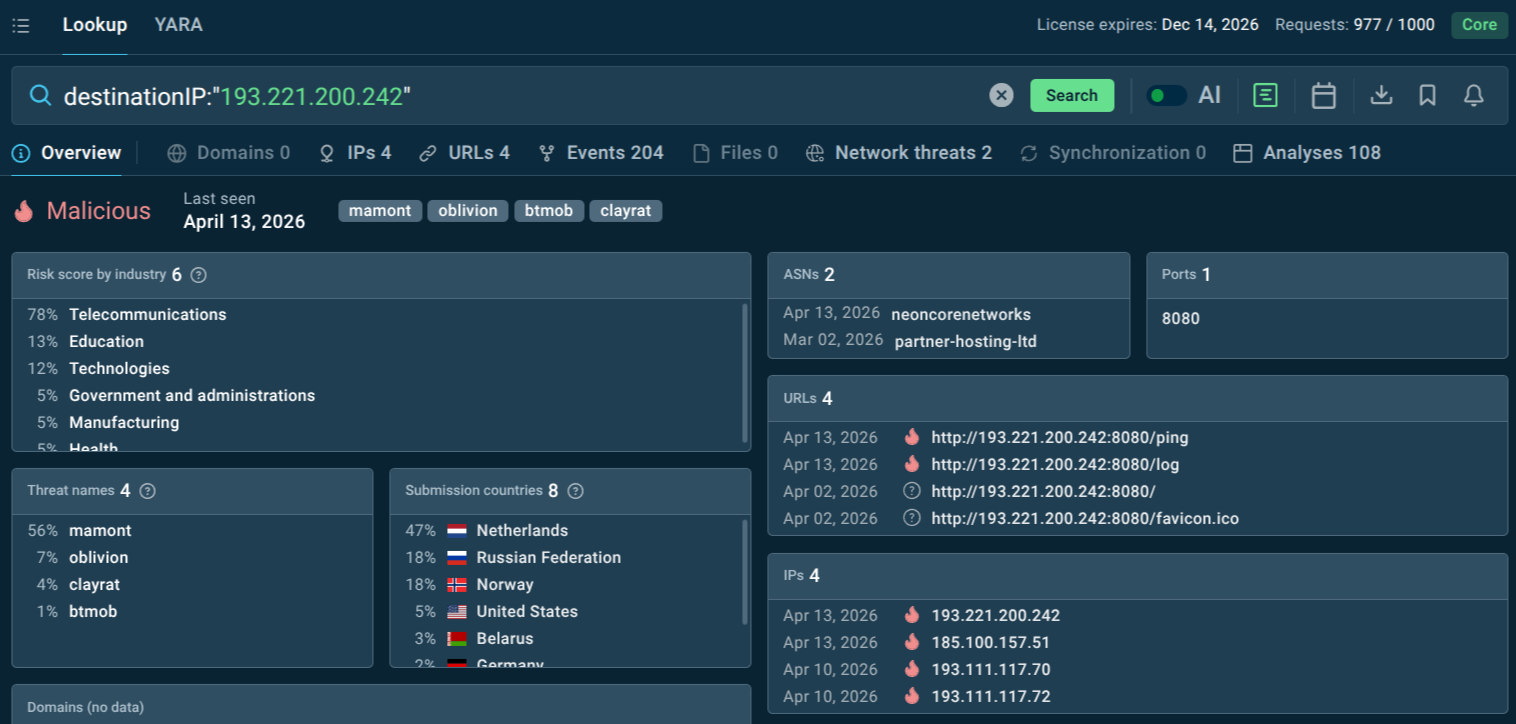 Malicious IP linked to Oblivion RAT
Malicious IP linked to Oblivion RAT
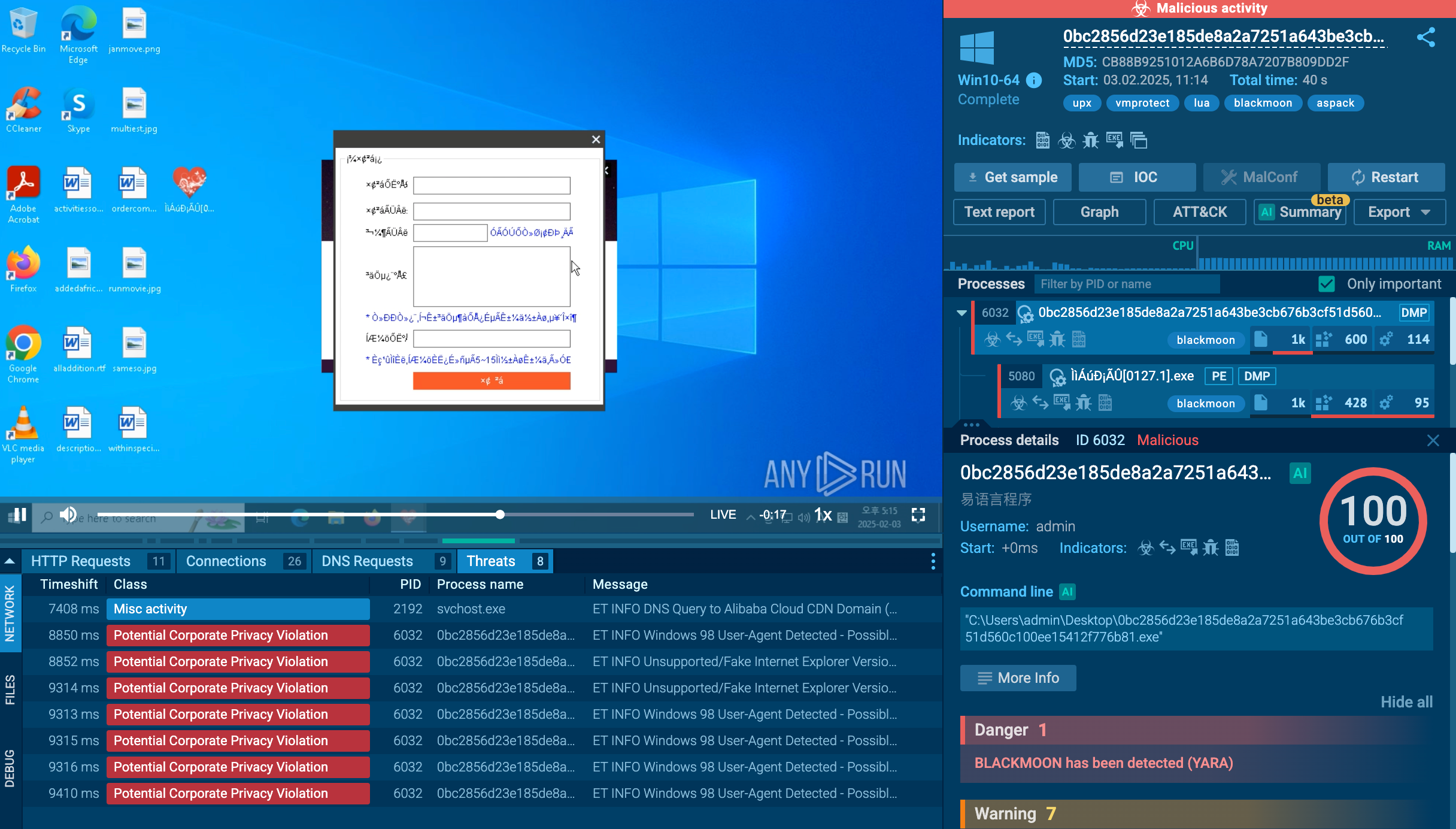
 Oblivion RAT fresh sample analysis in Interactive Sandbox
Oblivion RAT fresh sample analysis in Interactive Sandbox
Oblivion RAT is a newly emerged Android Remote Access Trojan (RAT) sold as a Malware-as-a-Service (MaaS) platform on underground cybercrime forums first publicly reported in February 2026. For a subscription starting at $300 per month, any would-be attacker gains access to a toolkit capable of silently hijacking nearly every Android device in active use today, no coding skills required.
The platform targets Android versions 8 through 16, covering virtually the entire active Android install base. Its combination of automated permission bypass, a Hidden VNC remote control channel, real-time OTP interception, and deep anti-removal persistence makes it one of the most capable and accessible mobile threats observed to date.
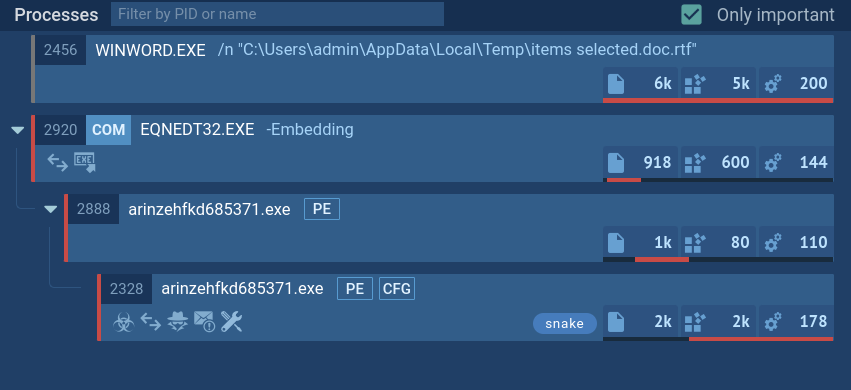
The platform consists of three core components that work in concert: a web-based APK Builder, a Dropper Builder, and a real-time command-and-control (C2) panel. Together these tools allow operators to build customized malware, deploy it convincingly to victims, and then manage hundreds of compromised devices through a single dashboard.
The APK Builder lets operators configure the malicious app's name, icon, and package name through a web interface. Two deployment modes are available. In stealth mode, the installed app immediately requests Accessibility Service permissions in the background, hides its icon from the home screen, and shows no visible interface at all.
In webview mode, the app opens a legitimate-looking website as a decoy while silently acquiring the same permissions behind the scenes. Default package name patterns (com.darkpurecore* for the dropper, net.darkhyperapps* for the implant) are visible across analyzed samples, providing a valuable detection foothold for defenders.
The Dropper Builder generates pixel-perfect imitations of the Google Play Store update flow. Victims are walked through three convincing pages: a fake download progress bar with a simulated security scan, a counterfeit Play Store listing complete with a developer name of 'LLC Google,' a 4.5-star rating, and an Update button, and finally a step-by-step guide framing sideloading as 'a standard security procedure.' All three pages auto-translate into the target's language, with confirmed presets for English and Russian.
On the technical side, Oblivion uses several anti-analysis techniques. Its most notable trick is a 'fake ZIP encryption' flag embedded in the APK that causes standard reverse-engineering tools like jadx and apktool to halt and report the file as encrypted. In reality, the contents are ordinarily compressed and can be extracted manually.
The malware's C2 configuration is stored as a plaintext Base64 string without meaningful encryption, inadvertently exposing critical infrastructure details including the C2 server address and operator authentication tokens prefixed with 'OBL_'. C2 communication runs over self-signed TLS with the Common Name set to 'OblivionServer,' another detection-friendly indicator.
Oblivion RAT poses a severe risk to enterprises by turning employee or contractor Android devices into persistent surveillance and fraud tools. It silently intercepts SMS-based 2FA codes, push notifications (including from corporate banking or email apps), keystrokes, contacts, call logs, GPS location, and files. In a BYOD or mobile-first environment, this enables credential theft for corporate accounts, data exfiltration, and even remote app control that could compromise internal systems.
The “Wealth Assessment” feature specifically flags financial apps, making it ideal for targeted business email compromise or account takeover fraud. Organizations face regulatory risks (e.g., GDPR, CCPA violations from stolen personal data), financial losses from fraud, and reputational damage. Its ability to bypass Google Play Protect (with some samples showing low detection rates) and major OEM security layers amplifies the threat to mobile endpoints, which are often the weakest link in corporate defenses.
While public data on specific victims remains limited due to the malware’s recency, Oblivion RAT’s design points to broad targeting via social engineering on messaging and dating apps. Over 7,500 infected devices have been observed globally since early 2026, with campaigns lasting an average of 21 days.
Potentially High-Risk Sectors:
Financial Services & Fintech: Wealth Assessment prioritizes banking/crypto apps; SMS/2FA interception enables account takeovers.
Defense, Media & Tech Research: Reported targeting in some campaigns; access to sensitive communications and location data.
Healthcare & Government: Mobile workforce handling sensitive data; potential for notification interception and surveillance.
Any Enterprise with BYOD/Mobile Workforce: High exposure via sideloaded apps; persistence on employee devices accessing corporate resources.
According to ANY.RUN threat intelligence data, the most recent Oblivion campaigns have been targeting IT, Telecom and Healthcare companies:
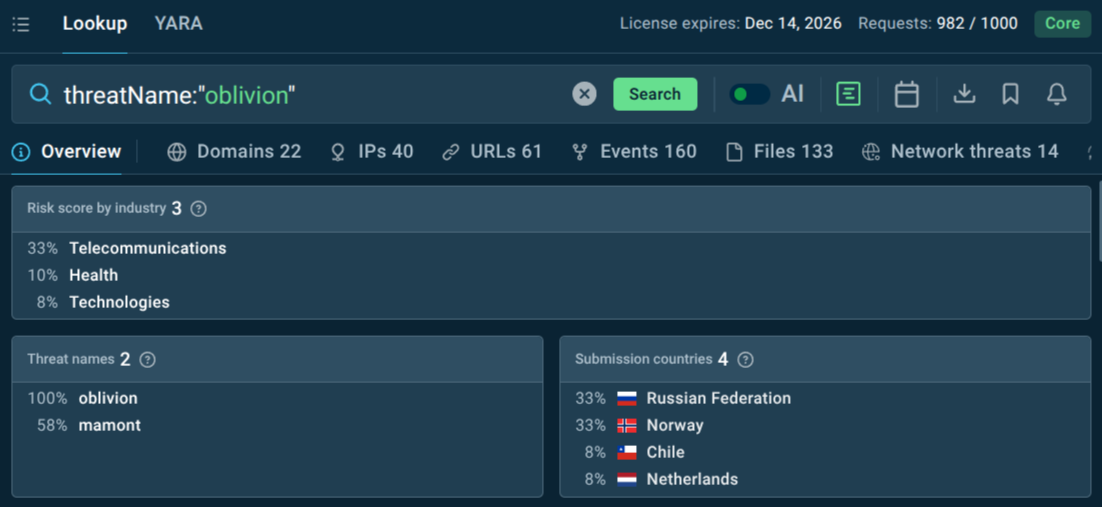 Industries targeted by Oblivion RAT
Industries targeted by Oblivion RAT
Oblivion's MaaS business model means attackers do not need specialized knowledge of any one sector. The Wealth Assessment module performs automatic target prioritization, the platform itself identifies which victims are most financially valuable. Organizations in any sector with employees using Android devices for work or authentication are within scope.
Oblivion employs a two-stage infection chain initiated through targeted social engineering:
1. Dropper Stage: Distributed via messaging/dating apps. The dropper APK contains a compressed payload and three embedded HTML pages mimicking Google Play update flows (progress bar, fake “LLC Google” listing, sideloading instructions). It tricks users into enabling unknown sources and installing the implant.
2. Implant Stage: The payload uses a fake Accessibility Service settings screen to gain control. Once enabled, it auto-grants permissions (SMS, notifications, storage, device admin) invisibly and hides all dialogs.
Key Spread Vectors: Phishing links in chats, fake app updates. No email or drive-by downloads reported, purely user-assisted sideloaded APKs. Persistence via boot receiver and anti-removal hooks ensures long-term access.
After installation:
Permission Escalation & Stealth: Abuses Accessibility Service for UI automation, keylogging, and dialog suppression. Hides icon and processes; blocks removal attempts.
Remote Control: Full HVNC with MediaProjection for touch input; victims see fake overlays while attackers interact live. Includes Screen Reader mode for banking apps.
Data Exfiltration: Intercepts SMS/OTP/2FA, notifications, keystrokes (timestamped by app), contacts, calls, location, files. Wealth Assessment scans apps for financial targeting.
C2 Communication: Self-signed TLS to IPs like 89.125.48.159:8888; config in plaintext base64.
Anti-Analysis: Fake ZIP encryption flag (bit 0x0809) fools tools like apktool/jadx.
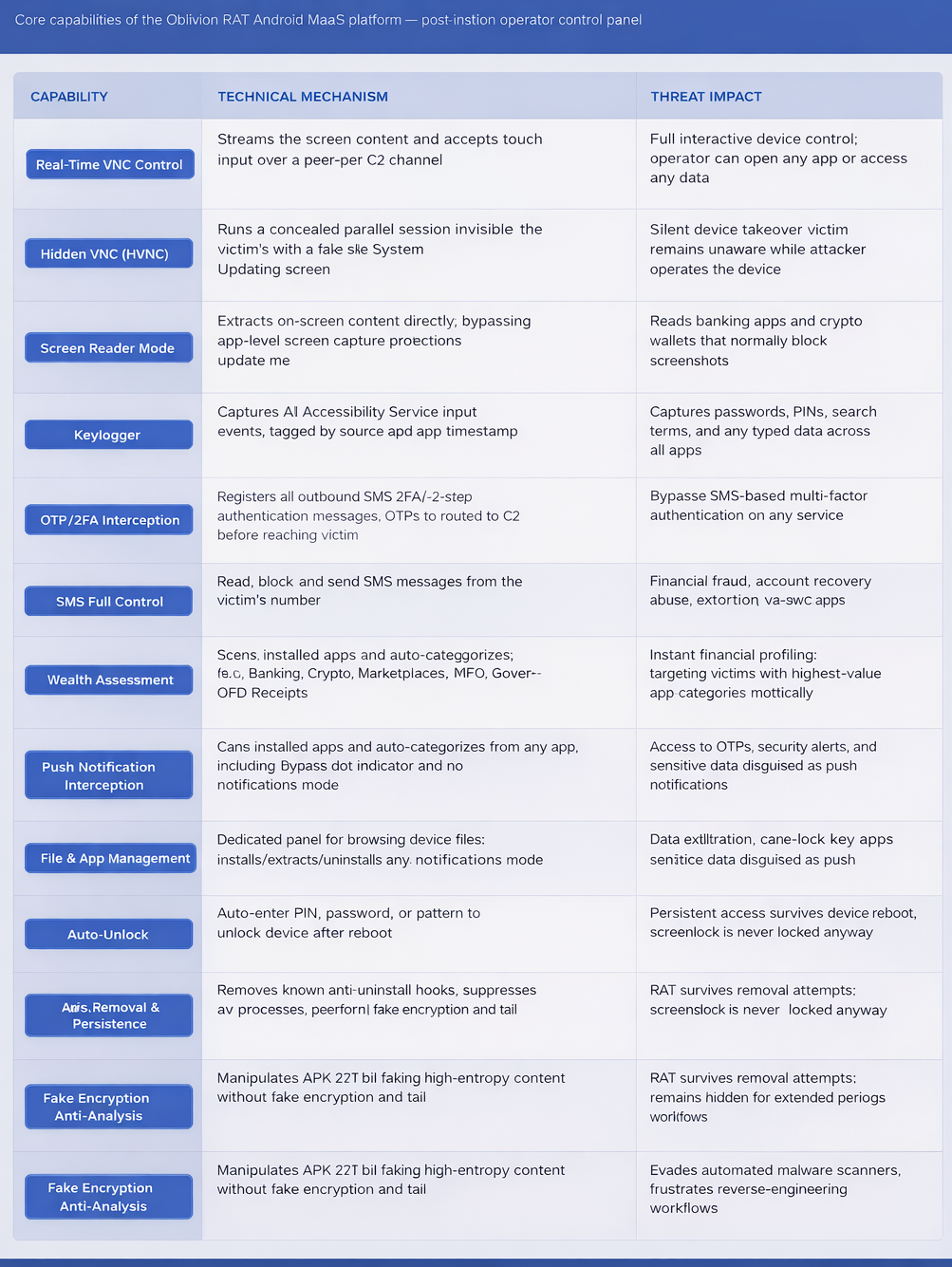 Oblivion capabilities and commands
Oblivion capabilities and commands
See the detonation of Oblivion
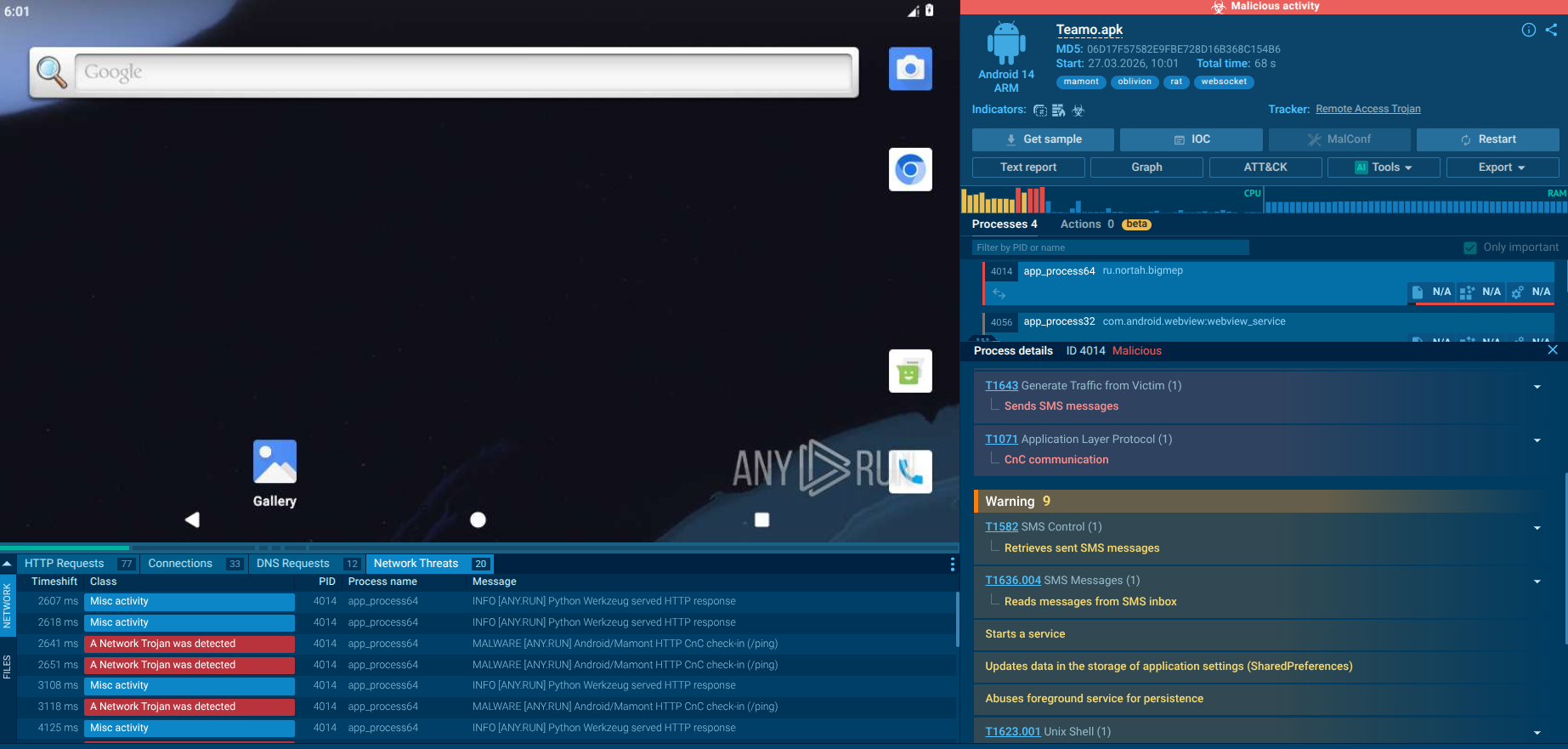 Oblivion RAT in action in the sandbox
Oblivion RAT in action in the sandbox
The analyzed sample of Oblivion RAT begins execution by performing basic environment validation. In the ANY.RUN sandbox session, the malware verifies the presence of a SIM card before continuing its activity. This check is commonly used to avoid execution in sandboxed or emulated environments where telephony features may be absent. After this validation, the malware proceeds with initializing its background components.
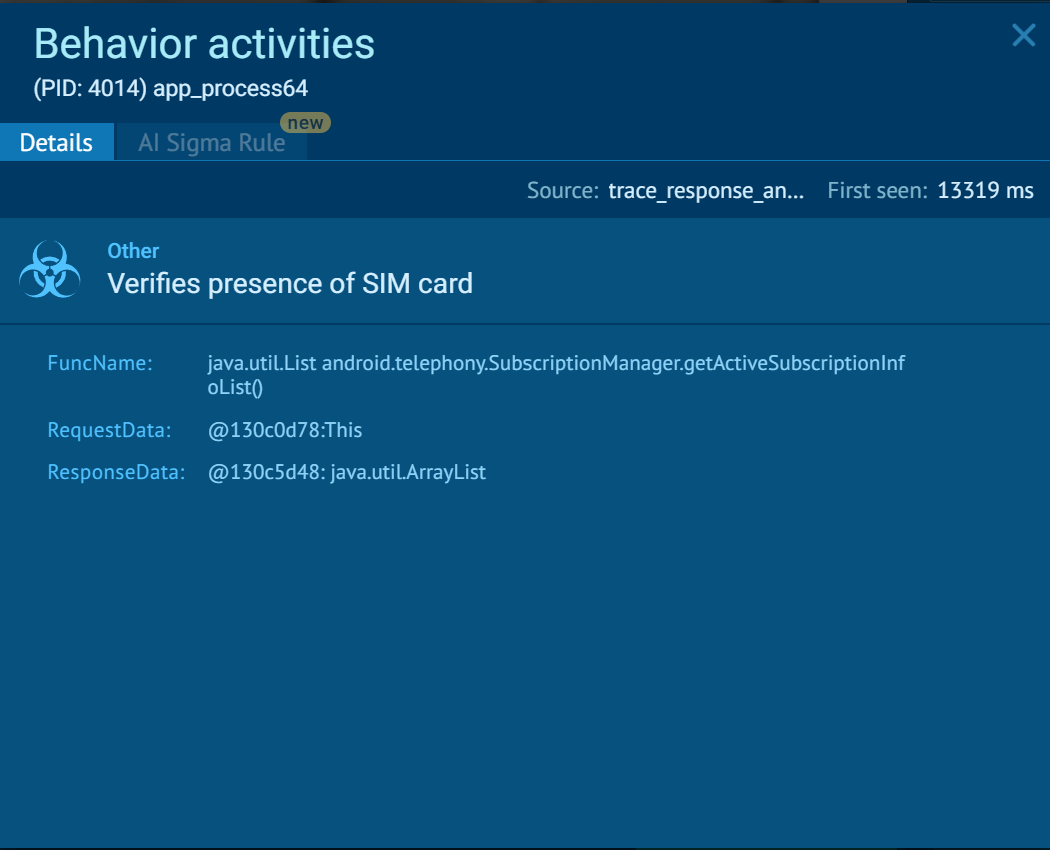 Oblivion RAT checks for a SIM card
Oblivion RAT checks for a SIM card
In the observed execution, the malware establishes persistence by starting a foreground service using Android system APIs. This allows it to remain active in the background with reduced risk of being terminated by the system. Additionally, it creates a WakeLock, which prevents the device from entering sleep mode and ensures continuous execution.
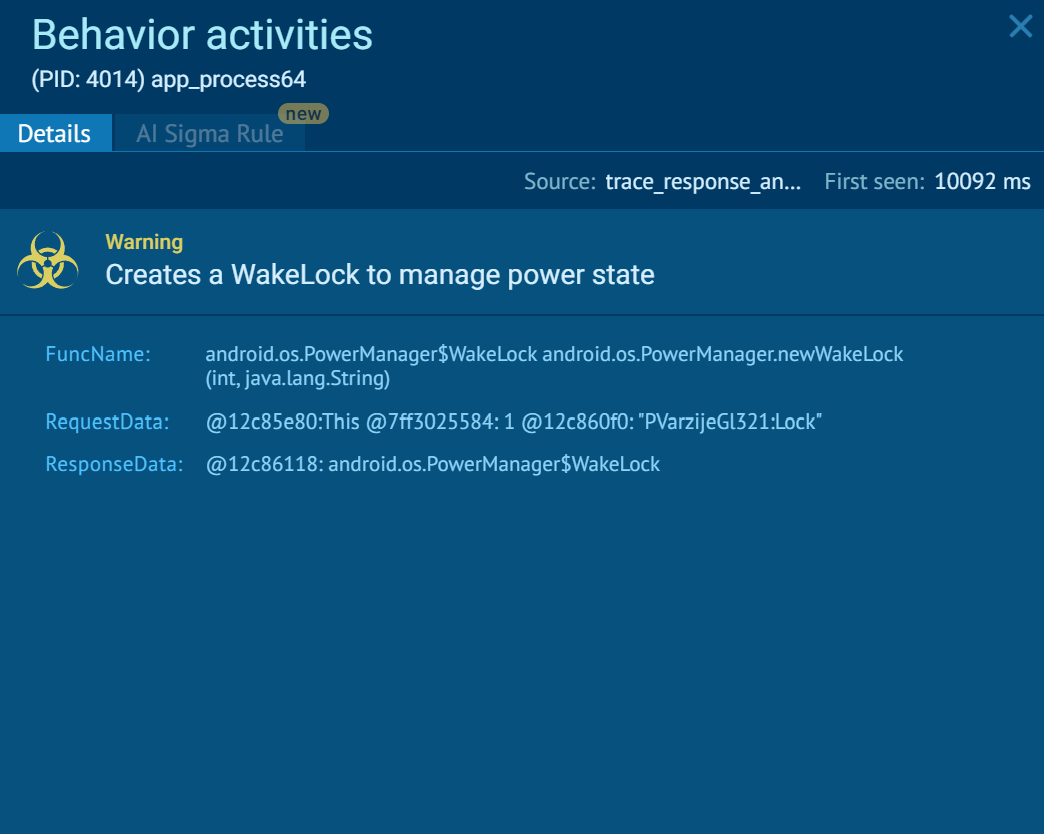 WakeLock created for persistence
WakeLock created for persistence
The malware demonstrates clear access to SMS data. In the analysis, it reads both the incoming messages via the SMS inbox...
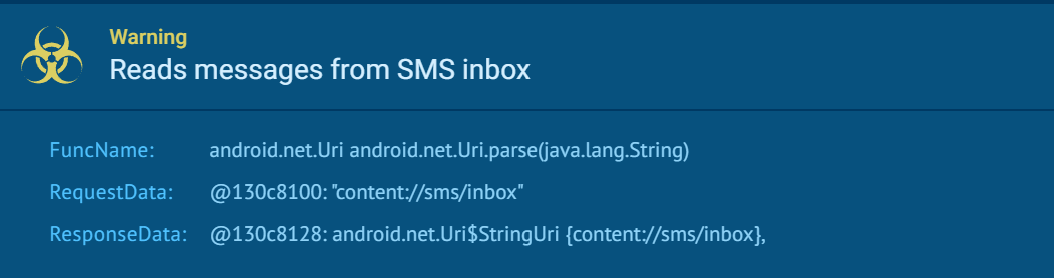 The malware reads incoming SMS
The malware reads incoming SMS
... and the previously sent messages via the sent folder.
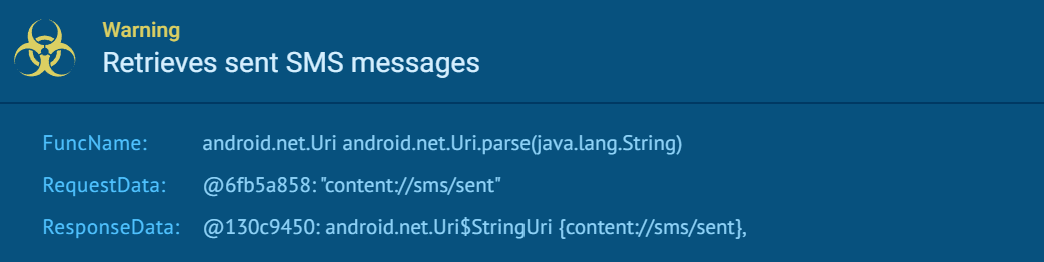 The malware reads sent SMS
The malware reads sent SMS
During execution, the malware generates a unique device identifier and stores it locally in shared preferences under its application directory.
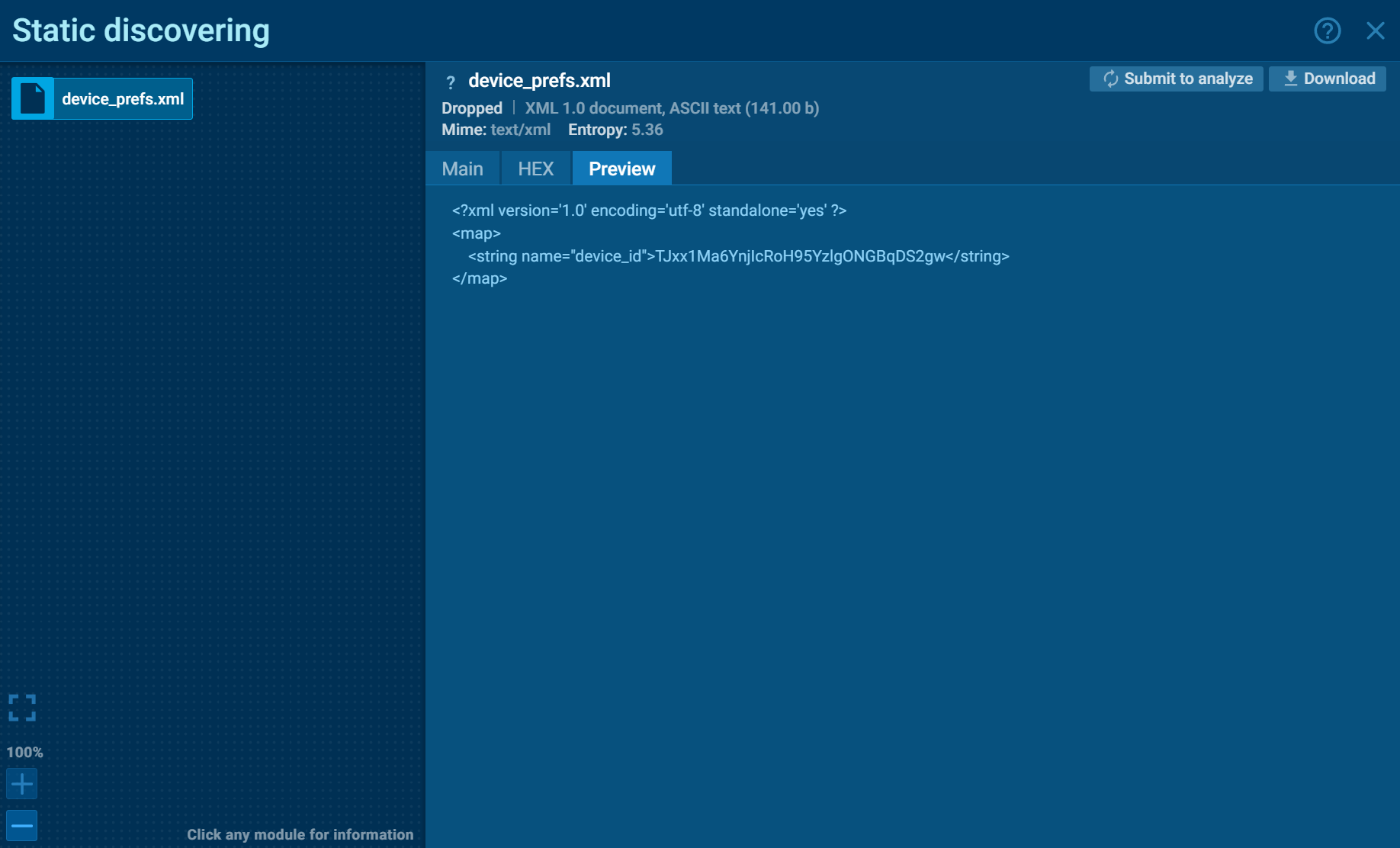 Device ID created by Oblivion
Device ID created by Oblivion
This identifier is then exfiltrated in two ways observed in the analysis session:
Sent via an HTTP POST request to a remote server;
Sent via SMS to a predefined phone number.
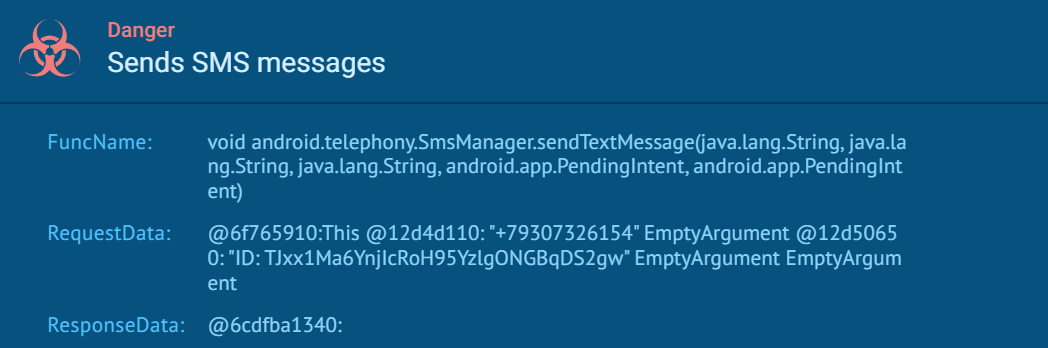 Oblivion exfiltration methods
Oblivion exfiltration methods
This dual communication method suggests redundancy in ensuring the attacker receives the device registration data. After transmitting this information, the malware enters a dormant state, awaiting further instructions from its command and control infrastructure.
In parallel, the sample opens a decoy interface using a WebView, loading a legitimate-looking website (Teamo).
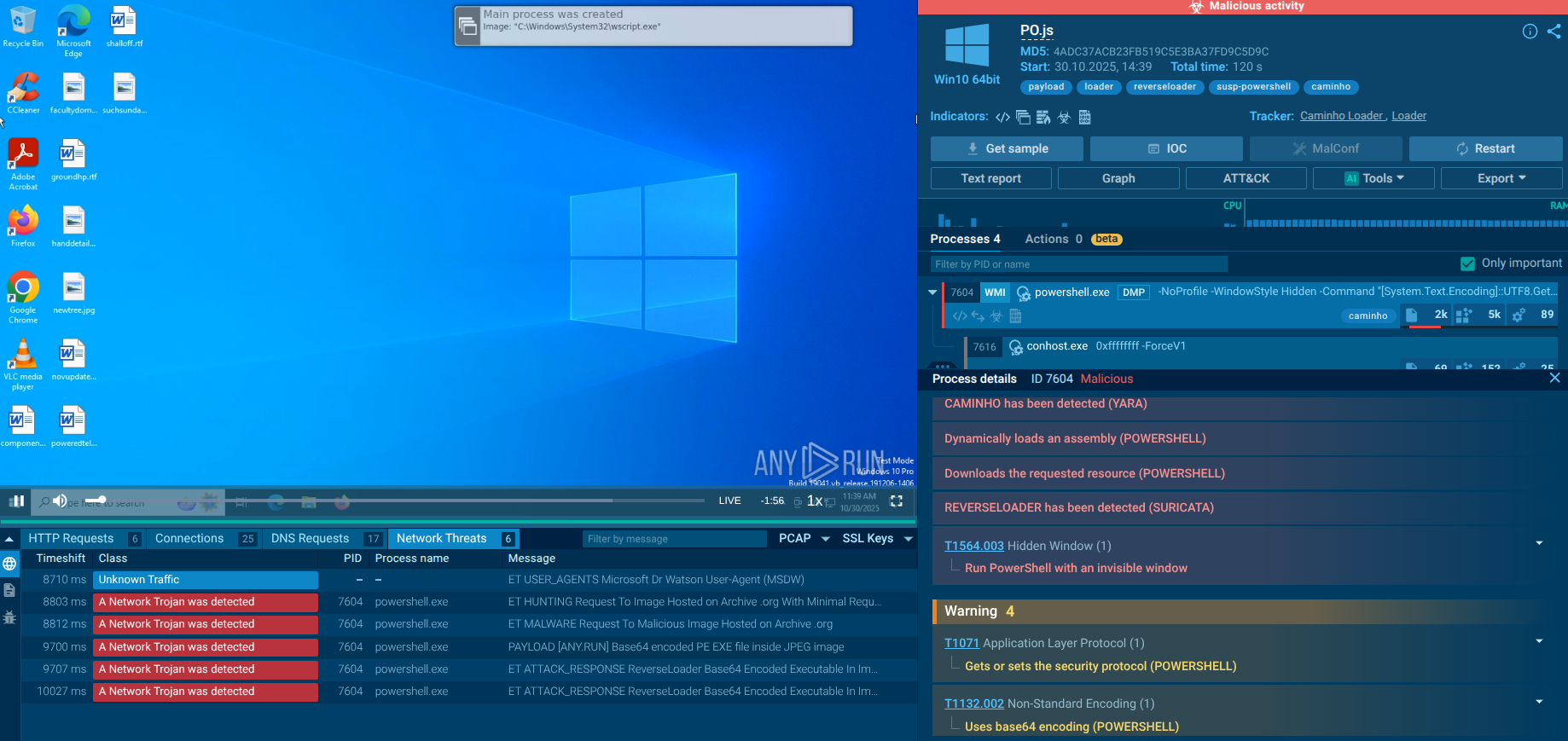
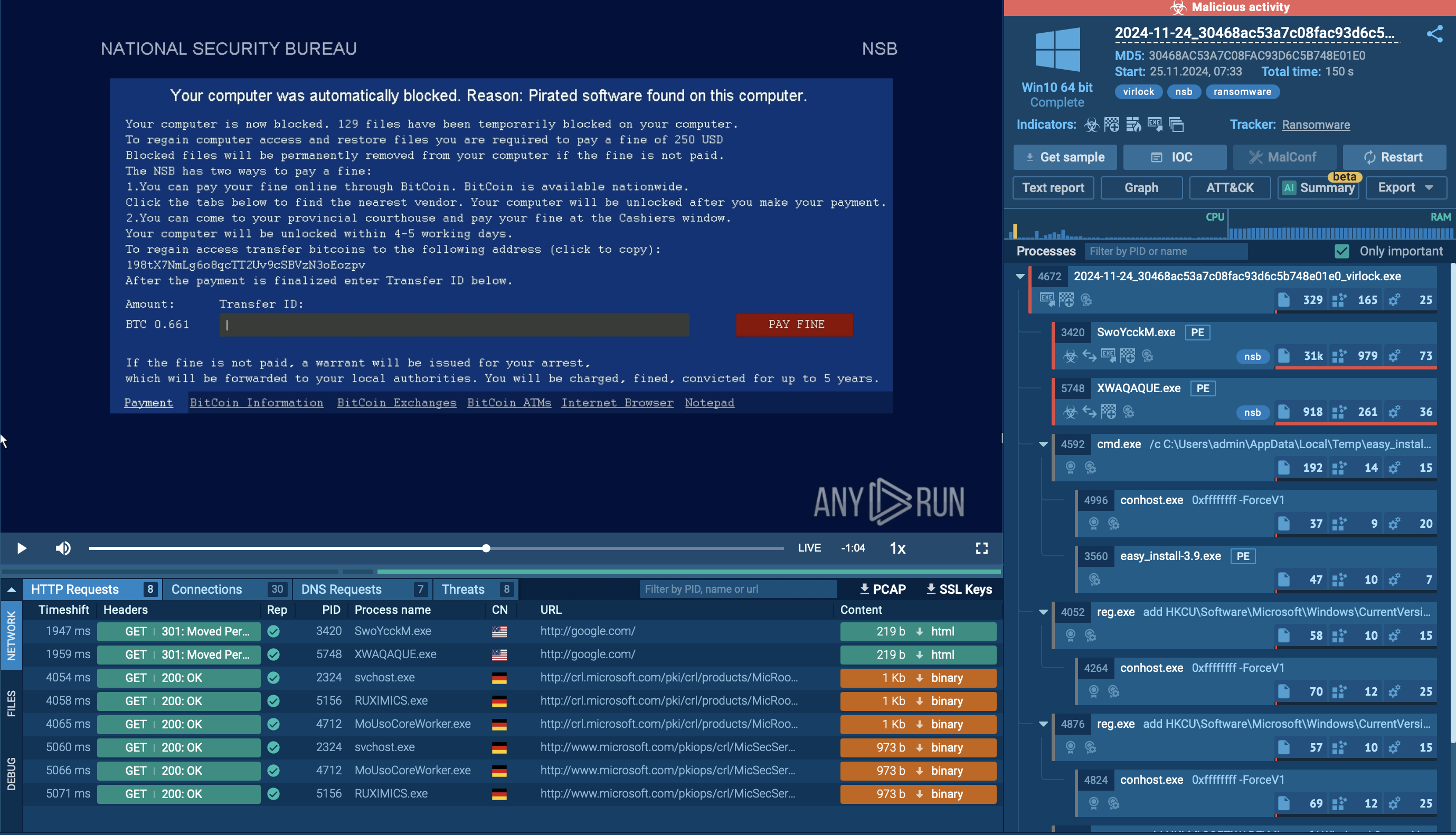
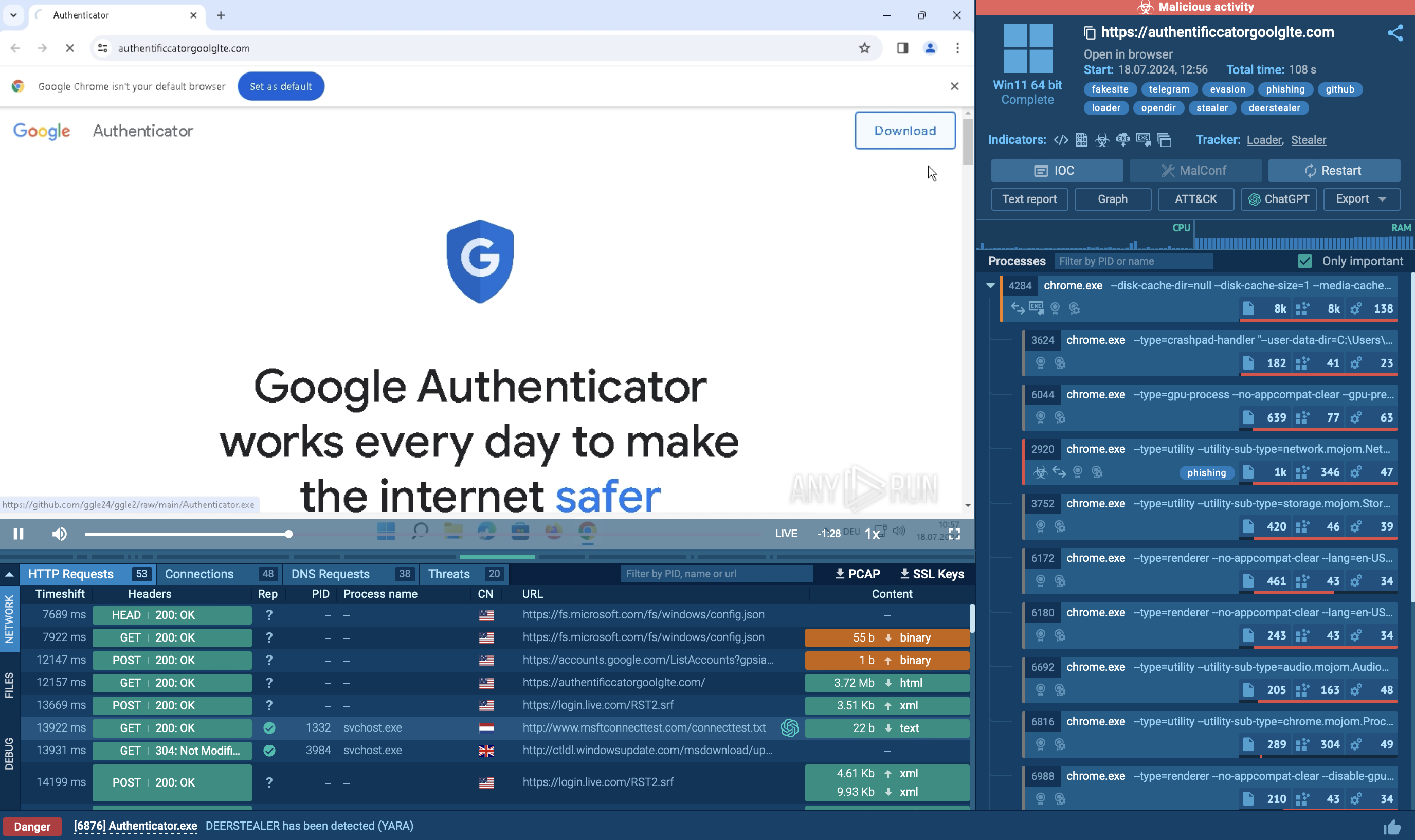
Proactive defense against a threat like Oblivion RAT requires moving beyond signature-based antivirus and embracing behavior-based detection, real-time threat intelligence, and dynamic malware analysis. ANY.RUN's suite of threat intelligence solutions is specifically designed for this challenge.
Businesses can leverage ANY.RUN’s Threat Intelligence Feeds to integrate fresh IOCs (C2 IPs, hashes, domains like oblvn.sbs) directly into SIEM, TIP, or XDR solutions for real-time blocking of known Oblivion infrastructure. TI Feeds provide organizations with continuously updated streams of Indicators of Compromise (IOCs) extracted directly from millions of live malware analysis sessions conducted by a global community of over 600,000 cybersecurity professionals.
TI Feeds integrate directly into existing security infrastructure via STIX and MISP formats, with API and SDK access for SIEM, IDS/IPS, and EDR platforms.
ANY.RUN's Threat Intelligence Lookup gives security teams direct, searchable access to the full database of IOCs, TTPs, processes, files, network connections, and registry activity recorded across millions of sandbox sessions.
For deeper analysis, submit suspicious Android samples to ANY.RUN’s Interactive Sandbox to observe the full infection chain, permission abuse, and C2 callbacks in a safe environment, generating actionable reports with behavioral insights.
 Oblivion TTPs mapped to MITRE ATT&CK matrix in the sandbox
Oblivion TTPs mapped to MITRE ATT&CK matrix in the sandbox
Additional Measures:
Enforce strict mobile device management (MDM) policies prohibiting sideloading and unknown sources.
Deploy enterprise mobile security solutions that monitor Accessibility Service abuse.
Educate employees on social engineering (especially fake updates in messaging apps).
Keep Android OS and apps updated; use Google Play Protect and OEM security features.
Implement app allowlisting and regular device audits for hidden processes.
Monitor for anomalous SMS/notification behavior and enable MFA via authenticator apps (not SMS).
Oblivion RAT exemplifies the growing accessibility of advanced mobile threats through MaaS platforms. Its combination of user-friendly builders, stealthy infection, and powerful post-exploitation capabilities makes it a formidable adversary for any organization reliant on Android devices. Proactive threat intelligence, sandbox analysis, and layered defenses are essential to stay ahead of such evolving risks.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.