Security professionals rely on early detection signals to prioritize and contain incidents. But what happens when a fully capable RAT generates none?
In a recent investigation, the ANY.RUN experts uncovered a new Go-based remote access trojan we named Moonrise. At the time of analysis, it wasn’t detected on VirusTotal and had no vendor signatures tied to it.
That’s the problem teams can’t ignore: credential theft, remote command execution, and persistence can be active while static checks stay silent. The result is slower triage, and more escalations.
Let’s break down Moonrise’s full attack chain and show how you can detect similar threats earlier, before they turn into longer investigations and real business impact.
Key Takeaways
- Moonrise operated without early static detection, establishing active C2 communication before any vendor alerts were triggered.
- The RAT supports credential theft, remote command execution, persistence, and user monitoring, enabling full remote control of an infected endpoint.
- Silent C2 activity increases business exposure, extending dwell time and raising the risk of data loss, operational disruption, and financial impact.
- Static reputation checks alone are not enough. Behavior-based analysis is critical to confirm real attacker activity quickly.
What Moonrise Means for Organizations
Moonrise isn’t just a remote access tool. Its command set shows how an attacker can move from access to impact.
- Credential theft and clipboard monitoring can expose passwords, session tokens, and sensitive data copied between systems.
- Remote command execution and process control let operators run scripts, interfere with defenses, and manipulate business applications.
- File upload and execution creates a clean path to drop additional payloads, including stealers or ransomware.
- Screen capture, webcam, and microphone access can reveal what’s happening inside finance workflows, admin panels, and internal communications.
- Persistence and privilege-related functions increase dwell time and make removal harder.
One compromised endpoint can disrupt operations and lead to financial and reputational damage, especially when the malware stays below static detection thresholds long enough to expand access.
Attack Details Exposed: What We Observed in Execution
You can follow the full Moonrise chain in real time, from execution to C2 control, and note the behaviors you can use for detection and triage.
Check analysis session with Moonrise
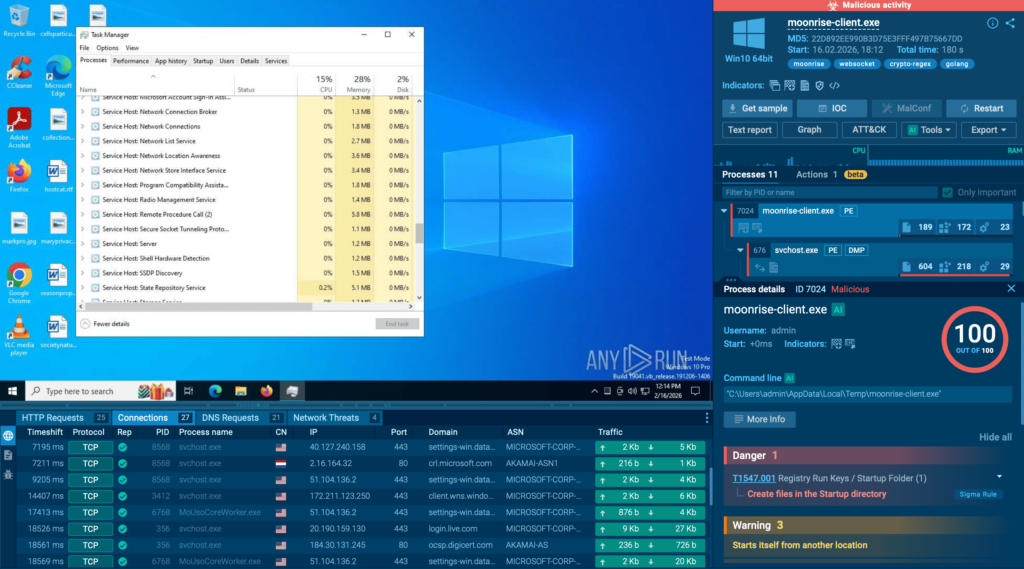
Within minutes of execution, Moonrise established outbound communication and began responding to operator-driven commands. What looked harmless in static checks immediately revealed interactive control once behavior was observed.
1. Session Registration and Persistent Communication
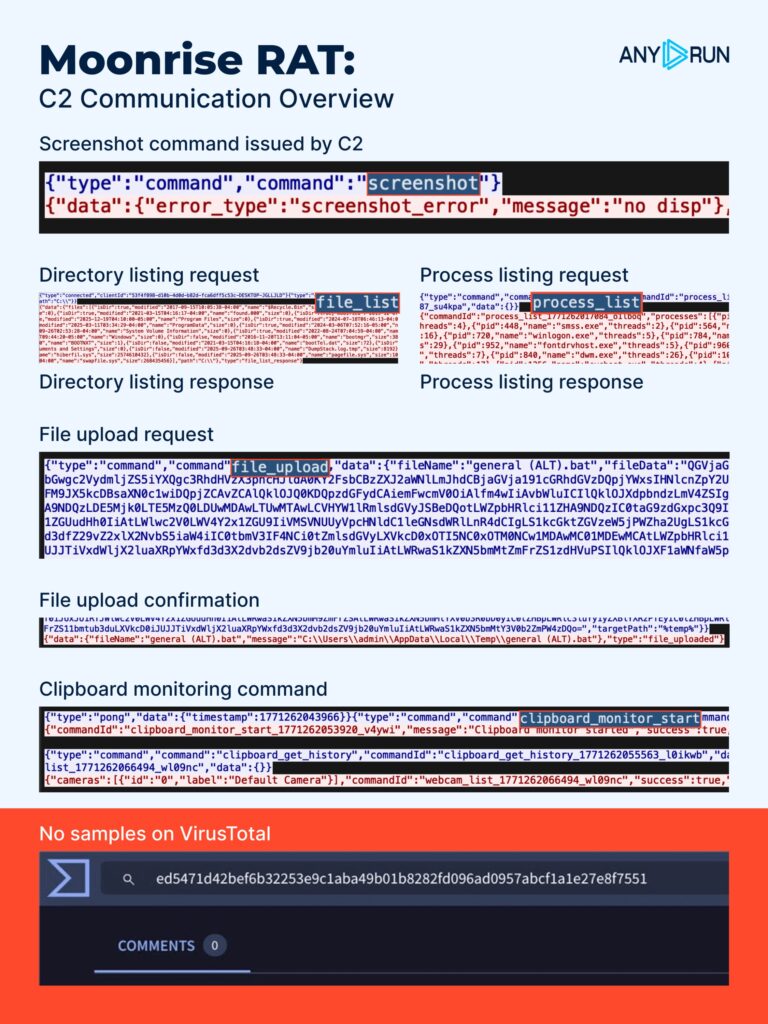
The communication begins with:
- client_hello
- connected
- ping/pong
These commands handle client identification and keep the WebSocket session alive. This confirms that the infected system is actively connected and ready to receive instructions.
At this stage, traditional static checks still show nothing suspicious. But behaviorally, the endpoint is already under remote control.
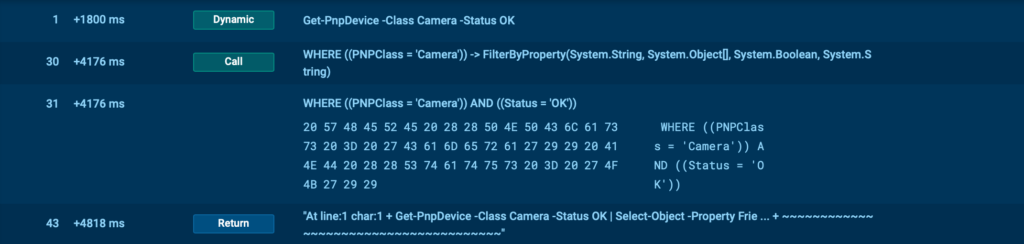
2. Visibility Into the Host Environment
Once the session is established, the operator starts requesting information about the system.
Observed commands include:
- process_list
- file_list
- webcam_list
- monitors_list
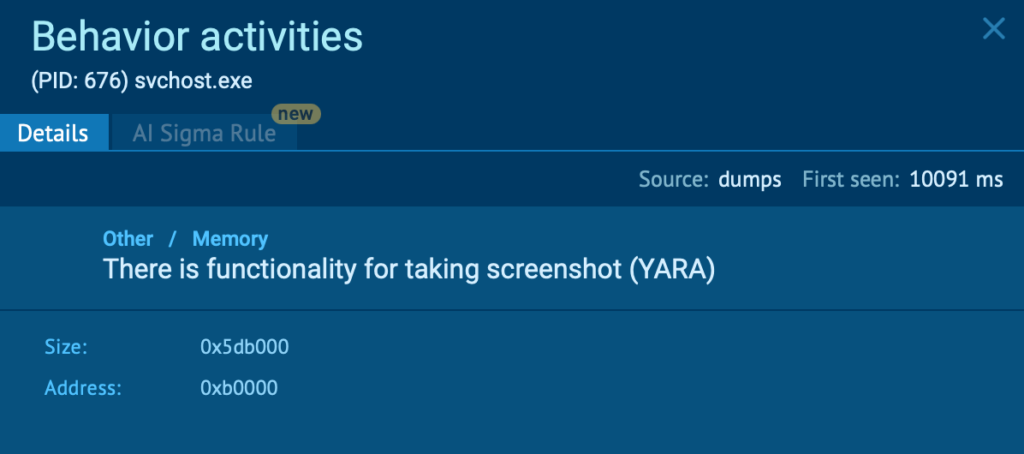
- screenshot
This allows the attacker to inspect running processes, review directory structures, identify connected displays, and check for available multimedia devices. Even when screen capture fails in a headless environment, the attempt itself signals active operator-driven interaction.
This stage provides the attacker with enough context to determine what data is accessible and which actions to take next.
3. Direct System Interaction and Control
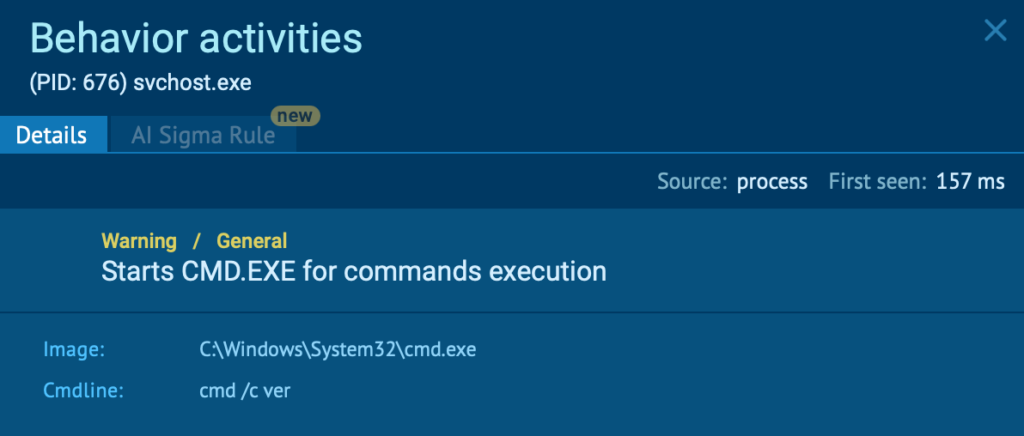
Moonrise supports active command execution and process manipulation:
- cmd
- process_kill
- file_upload
- file_run
- file_execute
- file_delete
- mkdir
- explorer_restart
Through these commands, the operator can run system commands remotely, terminate selected processes, upload additional payloads, execute them, modify directories, and restart system components.
This shifts the attack from observation to full control. At this point, the endpoint is no longer just compromised. It can be used to deploy further tools or prepare deeper access.
4. Credential Access and Data Extraction
The sample includes commands associated with data theft and credential harvesting:
- stealer
- steam
- file_download
- keylogger_logs
- clipboard_history
These functions enable collection of stored credentials, extracted files, logged keystrokes, and clipboard content. If sensitive data is copied between applications, such as passwords or financial details, it becomes accessible to the operator.
This is where technical compromise transitions into business exposure.
5. Active User Monitoring
Moonrise includes extensive user interaction monitoring capabilities:
- keylogger_start
- keylogger_stop
- keylogger_logs
- input
- clipboard_monitor_start
- clipboard_monitor_stop
- clipboard_history
- clipper_get_addresses
- clipper_set_address
- screenshot
- screen_stream_start
- screen_stream_stop
- webcam_capture
- microphone_record
These commands allow the operator to monitor user input, track clipboard changes, capture screen content, and access audio or video devices.
The infected endpoint effectively becomes a live surveillance point.
6. Privilege and System-Level Capabilities
Moonrise also contains commands related to privilege handling and system configuration:
- uac_bypass
- rootkit_enable
- rootkit_disable
- watchdog_status
- protection_config
- uxlocker_trigger
- voltage_drop
These suggest support for privilege manipulation, system configuration changes, and persistence-related behavior. While not all commands may be triggered in every session, their presence indicatesextended control options.
7. Lifecycle Management and Disruption
Moonrise includes lifecycle management functions:
- update
- uninstall
These allow the operator to modify or remove the deployed version of the malware. This indicates support for maintaining or adjusting the infection over time.
The command set also contains user-facing system interaction functions:
- fun
- fun_message
- fun_wallpaper
- fun_openurl
- fun_shake
- fun_sound
- fun_restart
- fun_shutdown
- fun_bsod
These commands suggest the ability to trigger visible system actions, including restarts or shutdown events, depending on operator intent.
Their presence reinforces that Moonrise provides broad remote interaction capabilities beyond silent monitoring.
Early Detection: 3-Step Loop That Works for Stealth RATs
Moonrise is a good example of an annoying reality: sometimes a RAT shows up with no clean static verdict, no reputation you can trust, and nothing obvious to latch onto. In those cases, early detection comes down to how quickly your team can move from unclear signals to evidence-based containment.
1. Monitoring: Catch the First Weak Signal Early
A lot of RAT incidents start with infrastructure: a fresh IP, a new domain, traffic that doesn’t match your baseline.
This is where ANY.RUN’s Threat Intelligence Feeds help. They continuously surface newly observed indicators and patterns based on telemetry and submissions from 15,000+ organizations and 600,000+ security professionals.
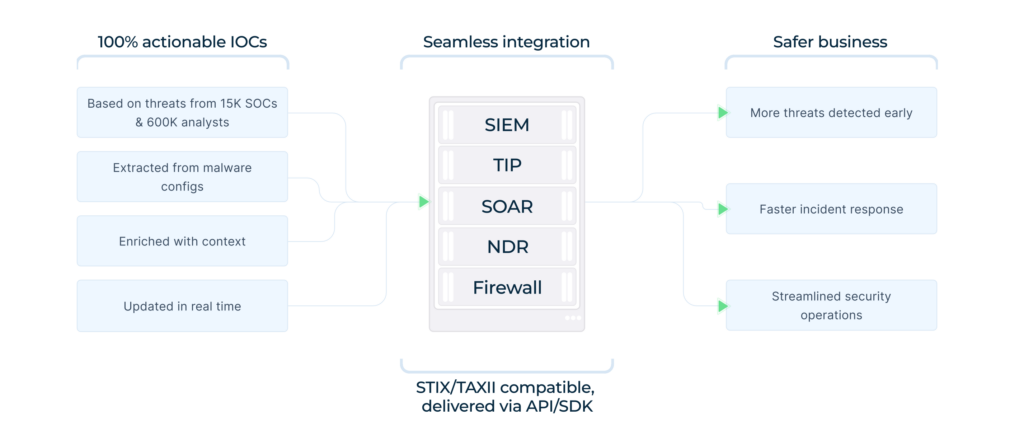
For SOC managers, that means fewer blind spots in day-to-day monitoring and earlier detection of suspicious infrastructure before it becomes a bigger incident.
2. Triage: Enrich Fast, Then Confirm with Behavior
When static checks don’t help, teams often lose time debating severity. That’s where MTTR grows and escalation pressure builds.
A cleaner path is enrich → execute → decide. Use Threat Intelligence Lookup to pull immediate context around a hash, URL, domain, or IP (relationships, related samples, historical sightings). Then run the artifact in the ANY.RUN Sandbox to confirm what it actually does in a safe environment.
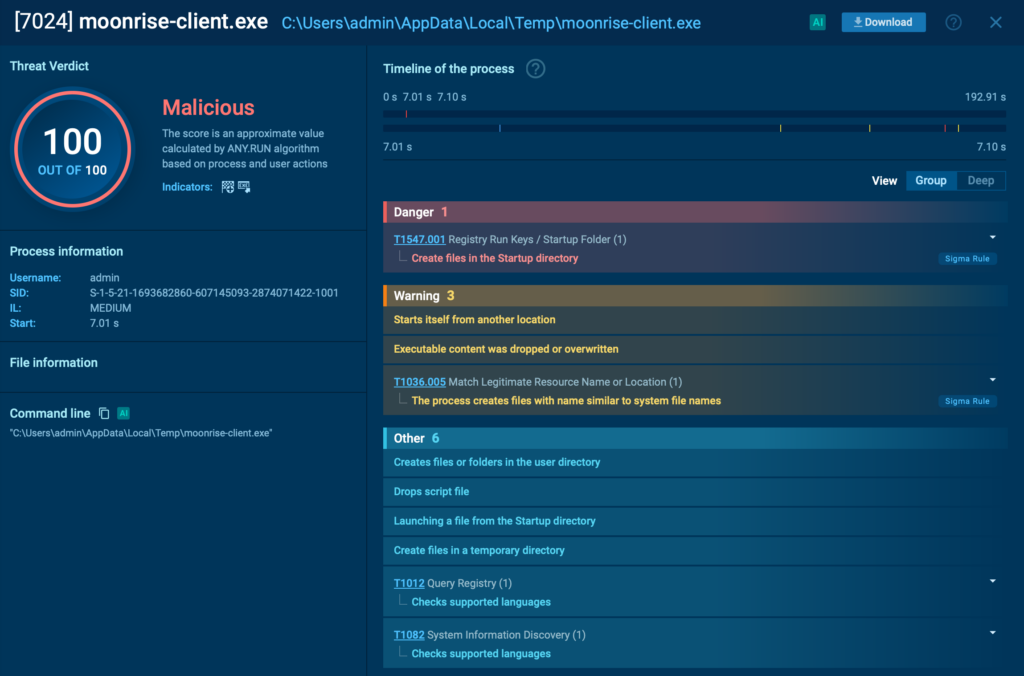
This is how teams replace uncertainty with evidence, reduce unnecessary Tier-1 escalations, and contain earlier, before a RAT turns into credential loss or broader access.
3. Threat Hunting: Turn One Confirmed Case into Wider Coverage
Once you confirm a RAT-like incident, the next step is making sure it doesn’t repeat under a slightly different wrapper. Threat Intelligence Lookup helps you pivot from confirmed indicators to related infrastructure and nearby samples, so hunting stays tied to what’s active now.
From there, you can pivot into related IPs/domains, cluster similar samples, and validate behavior in the sandbox to decide whether it’s the same activity or a lookalike.
Below is an example of a TI Lookup query for the Moonrise C2 IP observed in the attack:
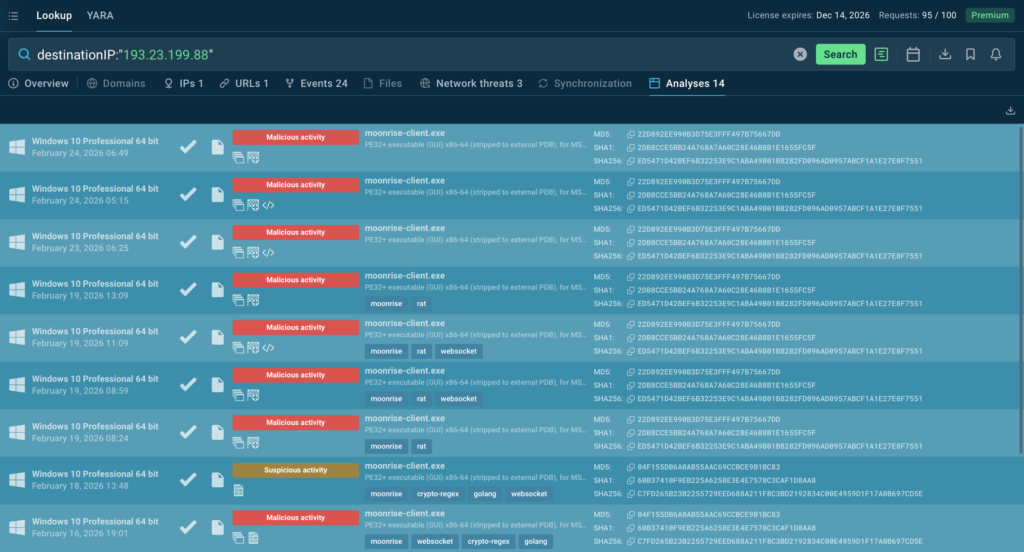
When these three motions run as a loop, monitoring, fast triage, and targeted hunting, stealth RATs stop being “late discoveries” and become manageable security events with lower response cost and less business exposure.
Conclusion: Reducing Exposure Starts with Faster Clarity
Moonrise is a reminder that the biggest risk isn’t the RAT itself but the time lost before it’s clearly identified. When static checks stay silent, attackers can steal credentials, stage more payloads, and lock in persistence while teams are still debating severity.
Reducing exposure comes down to one thing: faster clarity. Feed fresh infrastructure signals into monitoring, enrich quickly with TI Lookup, and confirm behavior in the sandbox before the case grows into a costly incident.
Bring speed and clarity to your SOC with ANY.RUN ➜
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, fits naturally into modern SOC workflows and supports investigations from initial alert to final containment.
It allows teams to safely execute suspicious files and URLs to observe real behavior, enrich indicators with immediate context through TI Lookup, and continuously monitor emerging infrastructure using Threat Intelligence Feeds. Together, these capabilities help reduce uncertainty, accelerate triage, and limit unnecessary escalations.
Today, more than 600,000 security professionals across 15,000+ organizations rely on ANY.RUN to make faster decisions, strengthen detection coverage, and stay ahead of evolving phishing and malware campaigns.
To stay informed about newly discovered threats and real-world attack analysis, follow ANY.RUN’s team on LinkedIn and X, where weekly updates highlight the latest research, detections, and investigation insights.
Indicators of Compromise (IOCs)
- 193[.]23[.]199[.]88
- c7fd265b23b2255729eed688a211f8c3bd2192834c00e4959d1f17a0b697cd5e
- 8a422b8c4c6f9a183848f8d3d95ace69abb870549b593c080946eaed9e5457ad
- 7609c7ab10f9ecc08824db6e3c3fa5cbdd0dff2555276e216abe9eebfb80f59b
- Ed5471d42bef6b32253e9c1aba49b01b8282fd096ad0957abcf1a1e27e8f7551
- 082fdd964976afa6f9c5d8239f74990b24df3dfa0c95329c6e9f75d33681b9f4
- 8d7c1bbdb6a8bf074db7fc1185ffd59af0faffb08e0eb46a373c948147787268







0 comments