Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


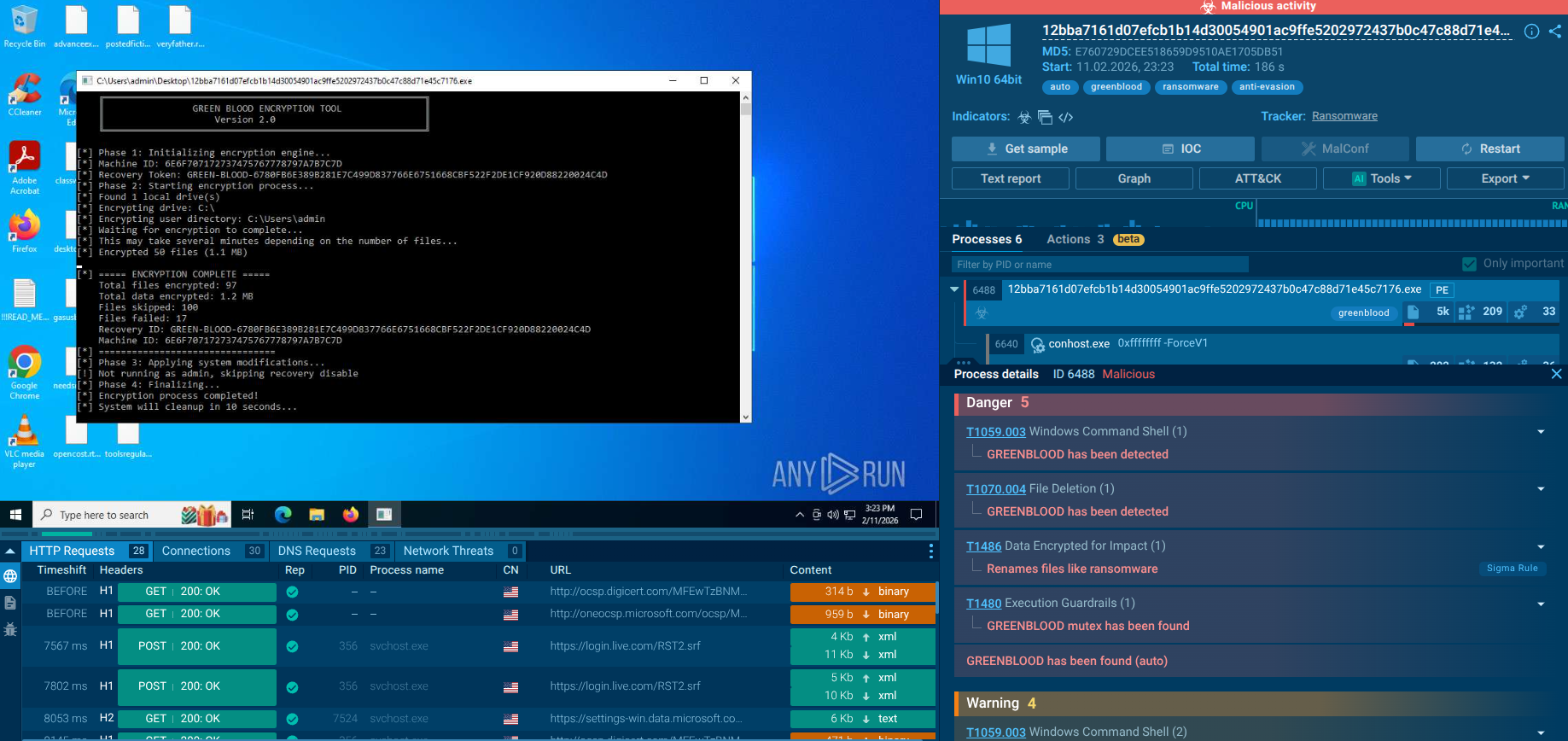
GREENBLOOD is a Go-based ransomware that uses concurrent ChaCha8 encryption to lock entire Windows environments in under a minute while systematically destroying backups, disabling defenses, and threatening double extortion through a Tor-based data leak site.
|
Ransomware
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
30 March, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
30 March, 2026
Last seen
:
|

 3317
3317
 0
0

 1637
1637
 0
0

 4682
4682
 0
0
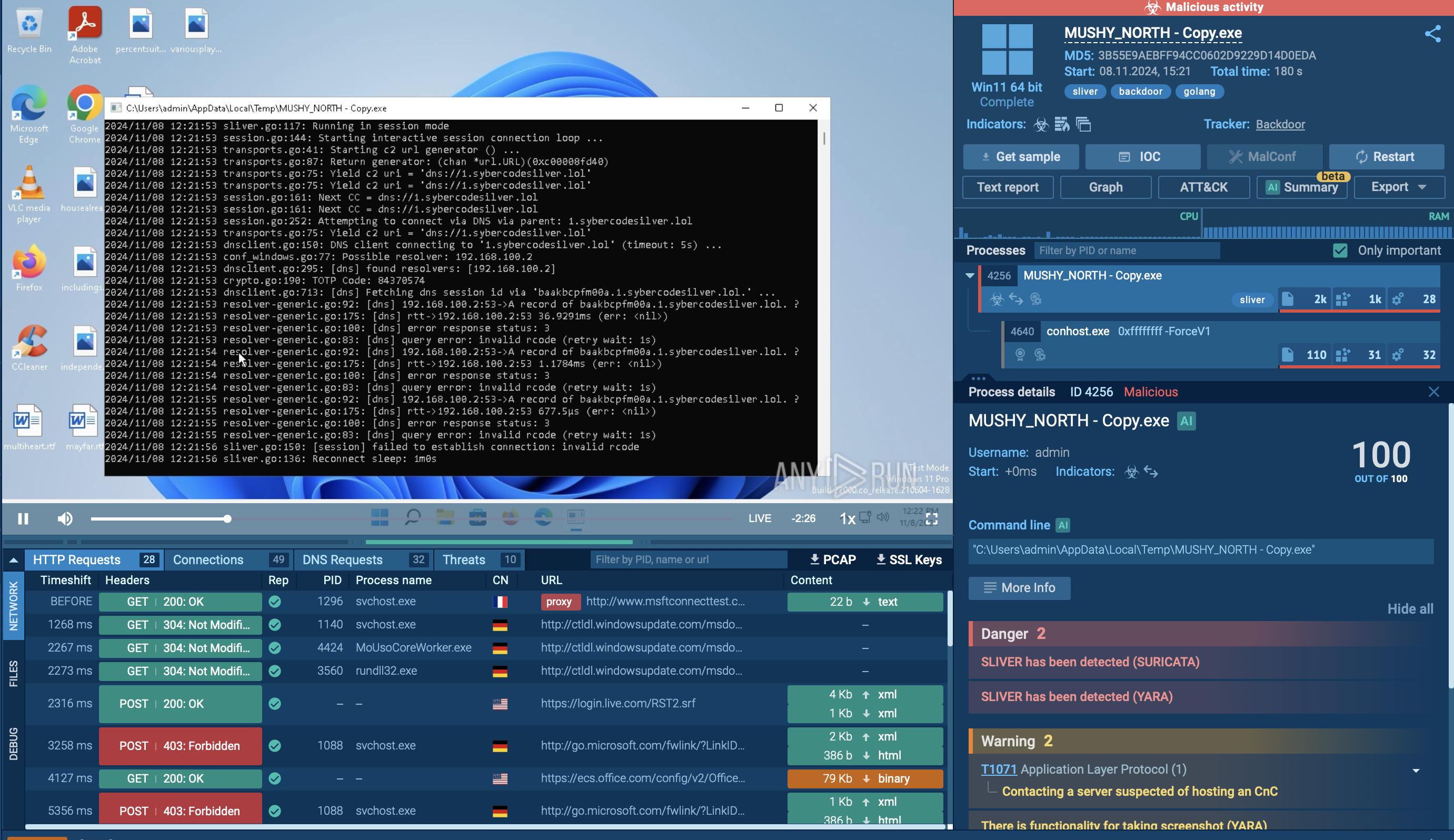
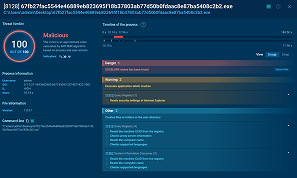
GREENBLOOD is built for speed: Its Go-based ChaCha8 encryption engine can lock an entire Windows environment in minutes, collapsing the detection-to-impact window to near zero for signature-based defenses.
Double extortion doubles the damage: GREENBLOOD combines file encryption with data exfiltration and Tor-based leak site pressure, turning a ransomware incident into a simultaneous data breach with regulatory and reputational consequences.
Recovery is systematically blocked: Before encrypting a single file, GREENBLOOD deletes shadow copies, removes backup catalogs, disables WinRE, kills Defender, and turns off the firewall.
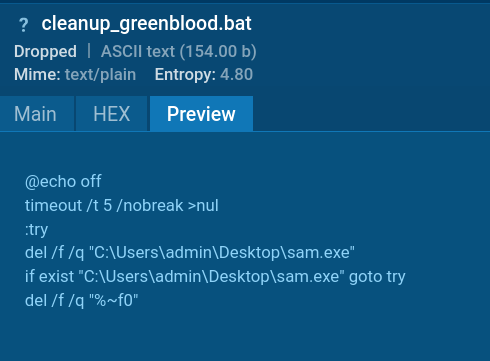
Self-deletion complicates forensics: The cleanup_greenblood.bat script removes the executable post-encryption, deliberately limiting the artifacts available for post-incident analysis and attribution.
Behavioral detection is the only viable pre-encryption defense. ANY.RUN's Interactive Sandbox captures the full GREENBLOOD attack chain, including shadow copy deletion, Defender disabling, and encryption, giving teams a clear verdict in under 60 seconds and enabling containment before downtime begins.
Observe GREENBLOOD detonated in the sandbox
 GREENBLOOD fresh sample analysis in Interactive Sandbox
GREENBLOOD fresh sample analysis in Interactive Sandbox
Start your research with the threat name and browse sandbox analyses to watch behavior and gather indicators:
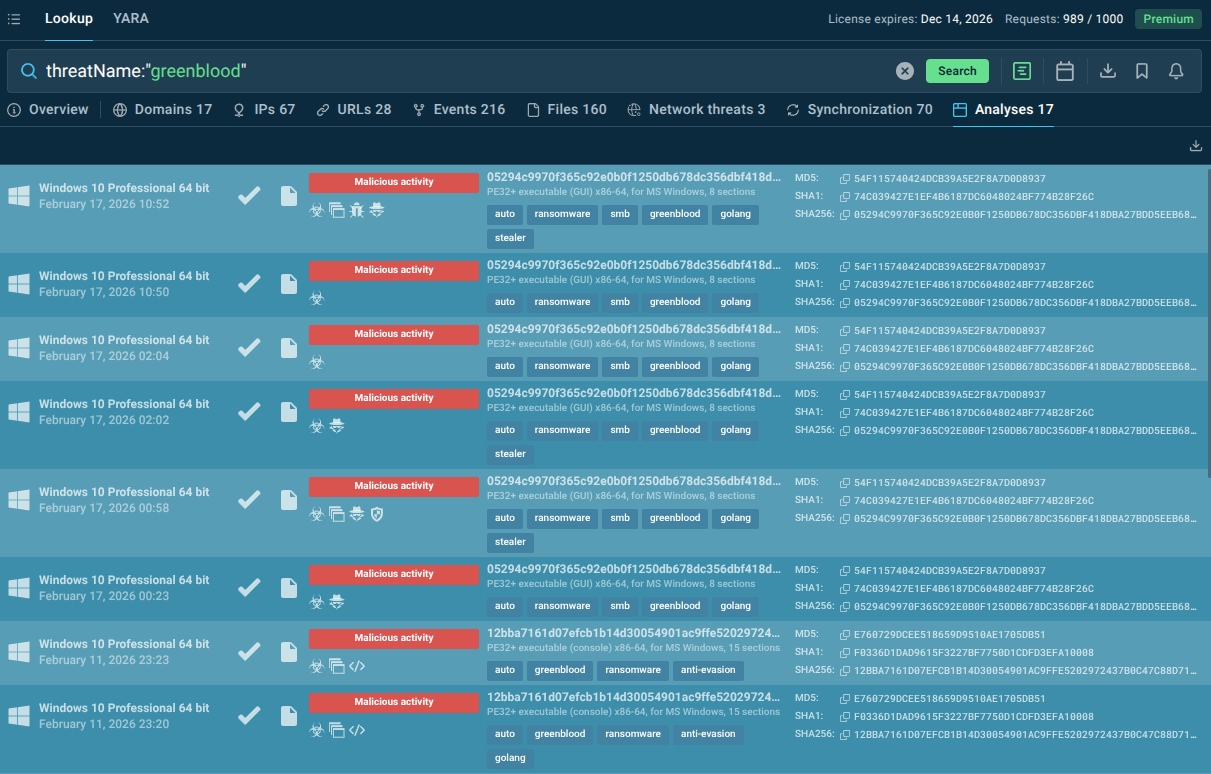 GREENBLOOD sandbox analyses found in TI Lookup
GREENBLOOD sandbox analyses found in TI Lookup
GREENBLOOD is an emerging ransomware family first identified in early 2026, operated by a threat actor group calling itself The Green Blood Group. Written in Go (Golang) and compiled as a Windows x64 executable, it is engineered for one overriding purpose: maximum disruption in minimum time.
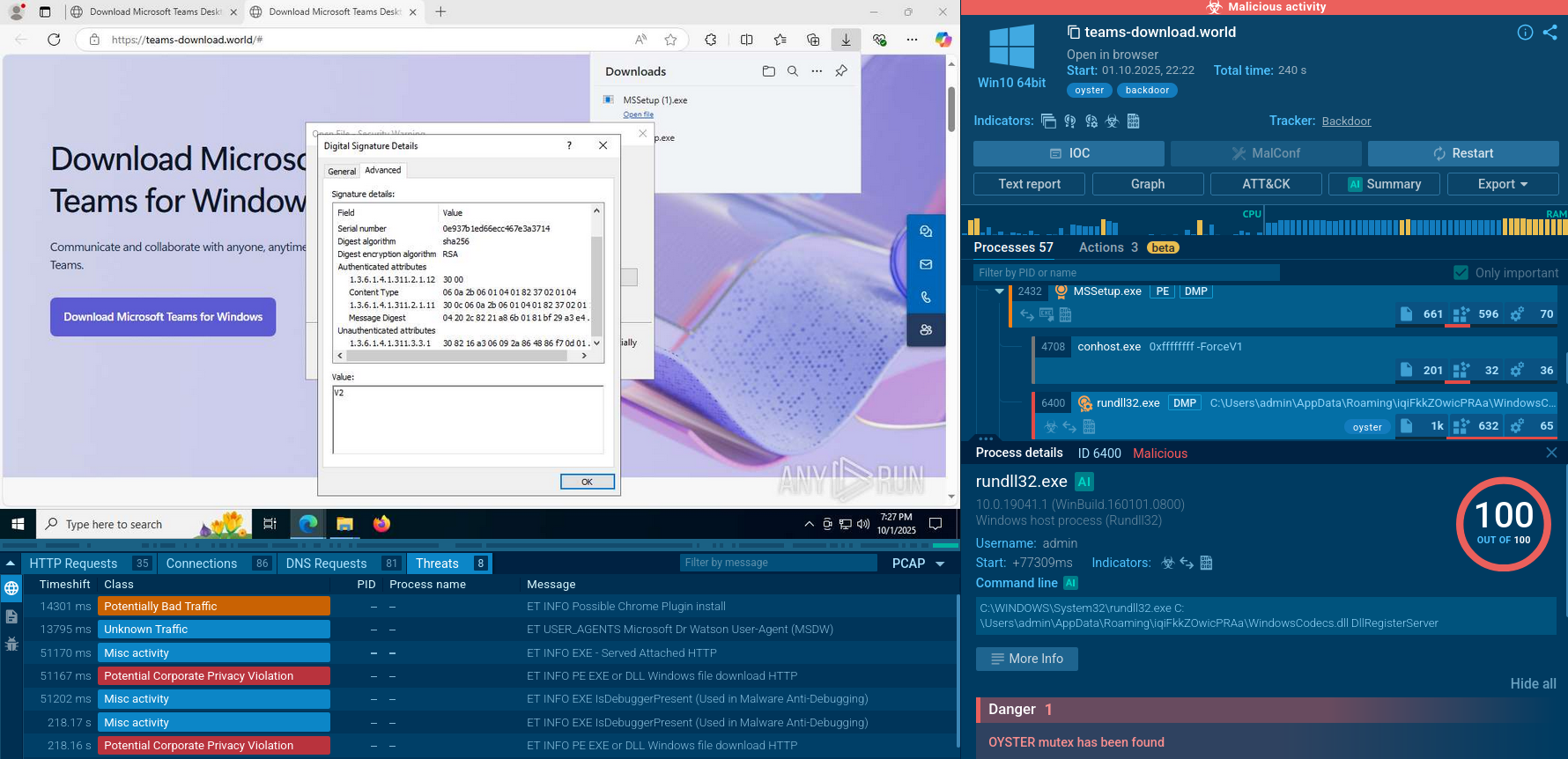
Unlike older ransomware strains that limit themselves to file encryption, GREENBLOOD combines high-speed ChaCha8 encryption with aggressive defense evasion, systematic destruction of recovery options, and double-extortion pressure through a Tor-based data leak site. The result is a threat that transforms a technical security incident into a full-blown business crisis: downtime, regulatory exposure, reputational damage, and mounting ransom costs, within minutes of execution.
The ransomware follows a structured, multi-phase attack pattern. Before a single file is encrypted, it profiles the victim machine, collects a unique hardware identifier (system UUID), and then systematically dismantles the defenses and recovery mechanisms that would allow an organization to recover without paying.
Volume Shadow Copies are deleted, the Windows Backup catalog is purged, the Windows Recovery Environment is disabled, the Windows Firewall is turned off, and Microsoft Defender's real-time protection is killed via registry modification. Only after this preparation phase does the encryption engine engage.
Encryption itself is driven by a concurrent, routine-based engine that walks the filesystem in parallel — traversing all logical drives and shell folders such as Desktop, Documents, and Downloads — and queues files for rapid locking using ChaCha8, a modern stream cipher known for its speed. Encrypted files receive the .tgbg or .gblood extension, and a ransom note (READ_ME_TO_RECOVER_FILES.txt or !!!READ_ME_TO_RECOVER_FILES!!!.txt) is deposited in every affected directory. Each ransom note contains a unique victim Recovery ID, demands payment in Bitcoin within seven days (with escalating price thereafter and a 21-day key destruction deadline), and provides contact emails at Proton and OnionMail addresses.
Once encryption finishes, GREENBLOOD launches a cleanup batch script (cleanup_greenblood.bat) from the %LOCALAPPDATA%\Temp directory, which deletes the ransomware executable itself and scrubs artifacts — a deliberate attempt to reduce forensic visibility and complicate post-incident analysis. The entire execution chain, from initial profiling to self-deletion, can complete in a matter of minutes.
GREENBLOOD doesn’t just compromise endpoints, it compromises decision-making time.
Key risks include:
Credential theft → lateral movement across systems;
Access resale → initial access brokers monetize your network;
Data exfiltration → intellectual property, financial data, customer records;
Ransomware staging → prepares infrastructure for high-impact attacks.
The real danger is delayed detection. By the time alerts fire, the attacker may already have mapped your environment.
The sectors most structurally vulnerable to GREENBLOOD’s type of attack include:
Healthcare: Patient data commands premium prices on dark markets, downtime is life-critical, and disclosure requirements are stringent. Healthcare led all industries in January 2026 ransomware incidents.
Financial services: High-value data, strict regulatory environments, and significant reputational stakes make payment more likely.
Manufacturing and industrial operations: Operational technology environments where downtime means immediate production and revenue loss.
Government and public sector: High-sensitivity data, often under-resourced security teams, and strong public pressure to restore services quickly.
Technology companies and IT service providers: Supply chain leverage — compromising one IT provider can cascade to dozens of downstream clients.
Education and research institutions: Large attack surfaces, valuable intellectual property, and historically limited security budgets.
Any organization running Windows environments with limited behavioral detection capability — particularly those relying on signature-based antivirus as a primary defense — is structurally at risk from GREENBLOOD.
Proactive defense against a threat like GREENBLOOD requires moving beyond reactive, signature-based detection. ANY.RUN provides two complementary tools designed specifically for this purpose.
ANY.RUN Threat Intelligence Lookup
TI Lookup allows security teams to search across millions of sandbox analyses using rich, contextual queries — command-line strings, file hashes, mutex names, network indicators, and more. This pivoting capability allows analysts to find related variants, track infrastructure reuse, and expand detection coverage across the environment — going far beyond what a single IOC or signature can offer.
TI Lookup also highlights the regions and industry recently targeted by the malware.
syncObjectName:"GREENBLOOD_ENCRYPTOR_MUTEX_2A3B4C5D"
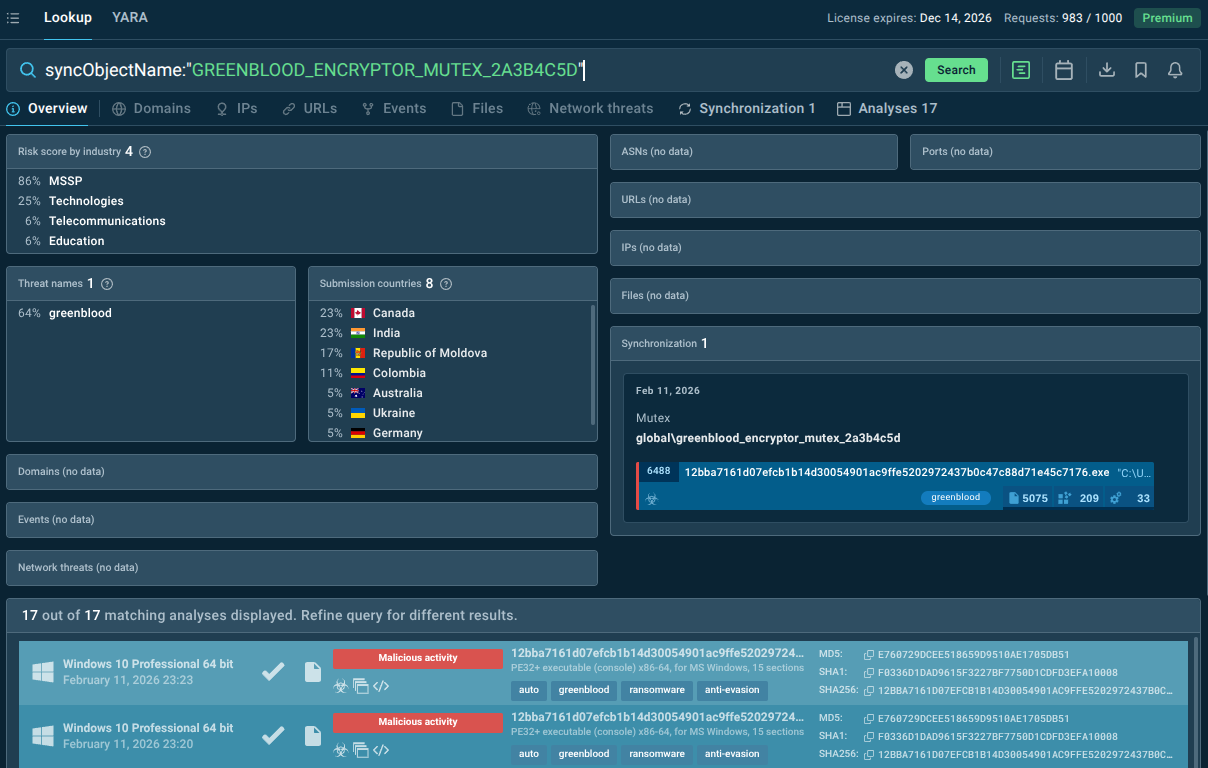 GREENBLOOD mutex queried in TI Lookup
GREENBLOOD mutex queried in TI Lookup
ANY.RUN Threat Intelligence Feeds
TI Feeds deliver continuously updated, machine-readable threat intelligence — IP addresses, domains, URLs, and behavioral indicators associated with active threats including GREENBLOOD — directly into your existing security stack (SIEMs, firewalls, EDR, SOAR platforms). This means:
GREENBLOOD-associated infrastructure is automatically blocked at the perimeter before malware can establish communication or exfiltrate data.
Detection rules in your SIEM are continuously enriched with fresh IOCs, reducing the dwell time window.
Threat hunting teams have a structured, up-to-date dataset to search for compromised hosts or lateral movement indicators.
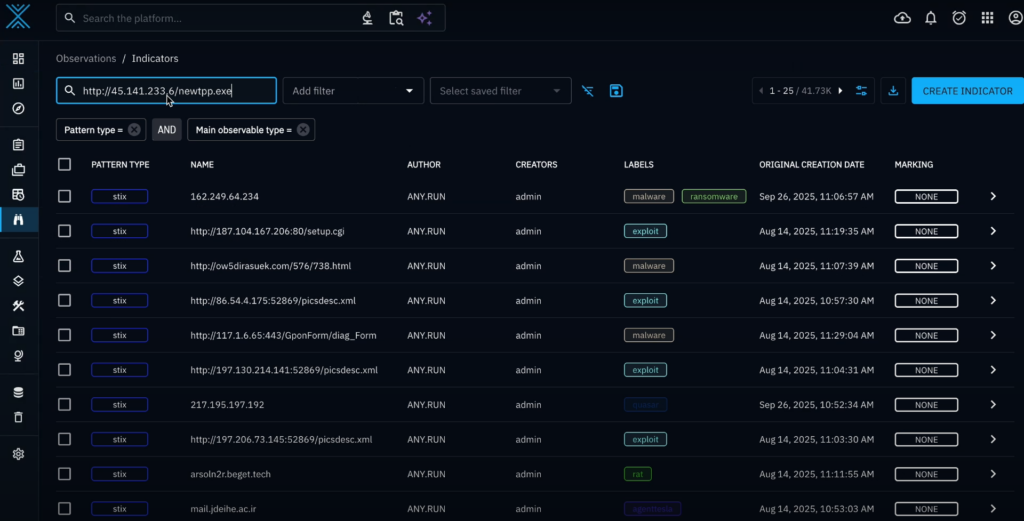 GREENBLOOD IOCs in TI Feeds
GREENBLOOD IOCs in TI Feeds
Additional Protective Measures
Behavioral detection: Deploy EDR solutions capable of flagging shadow copy deletion, Defender disabling via registry, and rapid file rename events — all GREENBLOOD hallmarks — regardless of the malware's specific hash.
Immutable backups: Maintain offline or air-gapped backups that cannot be reached by a compromised Windows process. GREENBLOOD specifically targets recoverable backups, so only truly isolated backups provide meaningful protection.
Privilege restriction: Limit the number of accounts with local Administrator rights. GREENBLOOD's most destructive capabilities — disabling recovery, killing Defender, wiping shadow copies — only activate when running with admin privileges.
Network segmentation: Limit lateral movement capability by segmenting internal networks and enforcing least-privilege access between segments.
Employee security awareness: Phishing and malicious attachments remain primary delivery vectors for ransomware. Regular, realistic training and phishing simulations reduce the likelihood of initial access.
GREENBLOOD's operators, consistent with modern professional ransomware groups, are not believed to rely on a single access vector. Based on observed behavior and infrastructure analysis, likely initial access methods include:
Phishing emails;
Exploitation of public-facing vulnerabilities;
Credential compromise;
Initial access brokers.
Once inside the network, GREENBLOOD's primary objective is to maximize the scope of encrypted systems before detection. The ransomware's concurrent, goroutine-based architecture means it does not process files sequentially — it spreads its encryption activity across multiple threads simultaneously, dramatically shortening the time required to impact the entire environment.
GREENBLOOD's execution flow breaks into several distinct phases:
Phase 1: Privilege and System Profiling
The binary checks for local Administrator group membership at runtime. If admin rights are confirmed, GREENBLOOD proceeds with its full recovery-inhibition and defense-suppression routine. It then collects the system UUID using Windows Management Instrumentation (wmic csproduct get uuid), generating a unique identifier per victim for key management and campaign tracking.
Phase 2: Recovery Destruction and Defense Suppression
Before encryption begins, GREENBLOOD executes a series of destructive commands:
vssadmin delete shadows /All /quiet — deletes all Volume Shadow Copies;
wmic shadowcopy delete — secondary shadow copy deletion;
wbadmin delete catalog -quiet — removes the Windows Backup catalog;
bcdedit /set {default} recoveryenabled No — disables Windows Recovery Environment;
bcdedit /set {default} bootstatuspolicy ignoreallfailures — suppresses boot failure warnings;
netsh advfirewall set allprofiles state off — disables Windows Firewall;
reg add ... DisableRealTimeMonitoring ... /d 1 — kills Defender real-time protection
Phase 3: Filesystem Traversal and Encryption
The EncryptionEngine — a developer-defined Go abstraction visible in the binary's preserved symbol names — uses a walkAndQueue method to traverse the filesystem. All logical drives and user shell folders are enumerated. A shouldEncryptFile function gates which files are processed. Qualifying files are encrypted using ChaCha8 and renamed with the .tgbg or .gblood extension. Ransom notes (READ_ME_TO_RECOVER_FILES.txt or !!!READ_ME_TO_RECOVER_FILES!!!.txt) are deposited in every directory containing encrypted files, with dynamically generated, per-victim Recovery IDs.
Phase 4: Extortion Infrastructure
Victims are directed to contact the operators via thegreenblood@proton[.]me or thegreenblood@onionmail[.]org, or to access the group's Tor-based leak site. Bitcoin payment is demanded within 7 days, with price escalation thereafter and a 21-day key destruction threat. The double-extortion model means non-payment results in stolen data being published on the leak site.
Phase 5: Self-Cleanup
Post-encryption, a batch script (cleanup_greenblood.bat) is executed from %LOCALAPPDATA%\Temp. This script deletes the ransomware executable and removes artifacts, deliberately hindering forensic analysis and incident reconstruction.
See full execution chain of GREENBLOOD
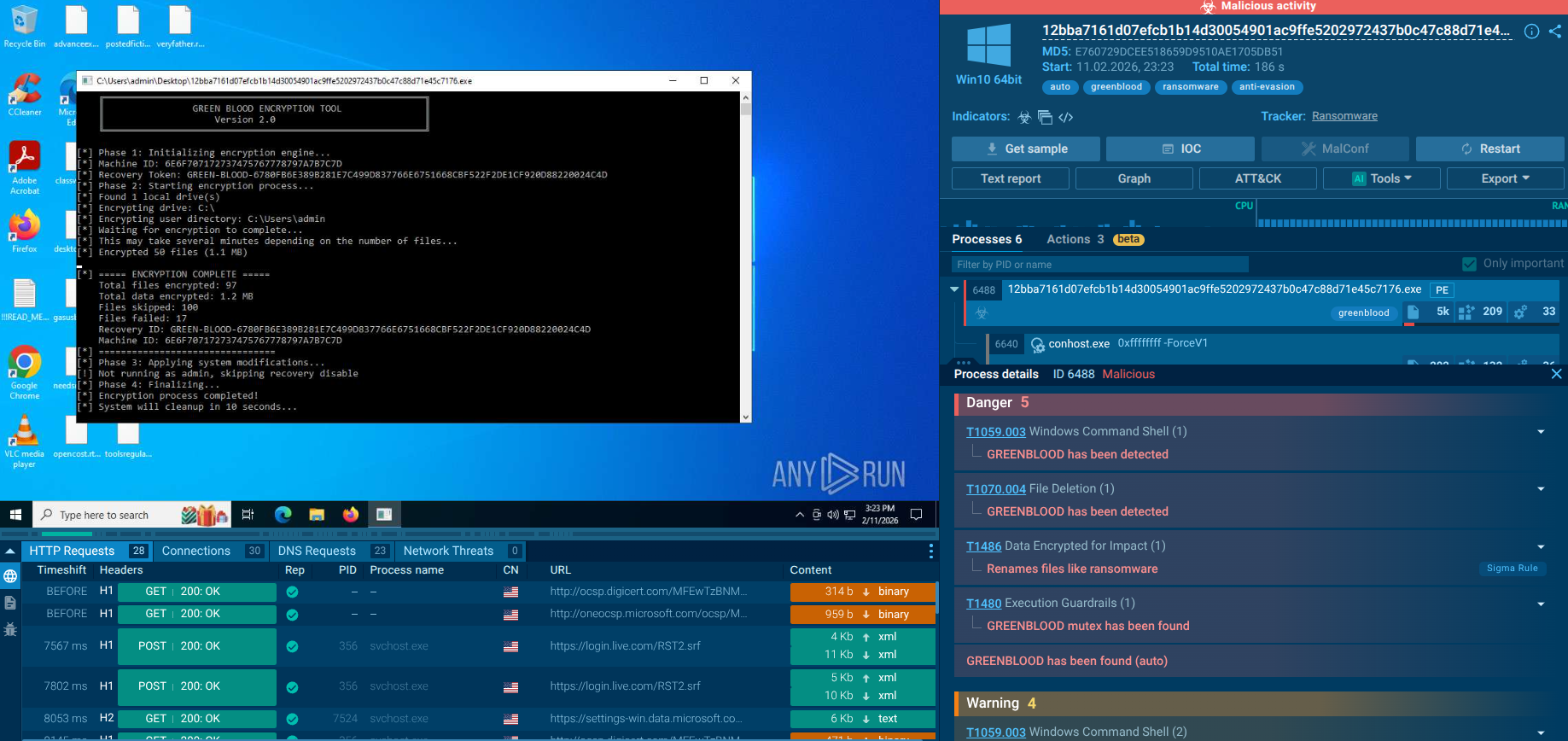 ANY.RUN sandbox revealing GREENBLOOD behavior in real time
ANY.RUN sandbox revealing GREENBLOOD behavior in real time
The ransomware creates a mutex at launch to ensure running a single copy in the system.
 GREENBLOOD’s signature mutex
GREENBLOOD’s signature mutex
When the encryption process begins, GREENBLOOD recursively scans directories and creates a queue of files to be encrypted. It filters out files from the predefined exclusion list (notably executables and critical system paths) to keep the system functional. Simultaneously, a ransom note is deployed.
 The malware creates a ransom note
The malware creates a ransom note
Finally, a batch script is executed to delete the ransomware executable.
 The final stage of GREENBLOOD chain
The final stage of GREENBLOOD chain
GREENBLOOD is not loud, flashy malware. It’s disciplined, adaptable, and patient. That combination makes it dangerous in modern environments where alert fatigue already clouds visibility.
Defending against it requires more than tools, it requires context. And context is exactly what strong threat intelligence delivers.
For businesses and security teams, the key lesson from GREENBLOOD is timing. The only effective defenses are those that operate before or during the early execution phase: behavioral detection, proactive threat intelligence, immutable backups, and a security architecture that assumes compromise and contains its blast radius.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.