Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


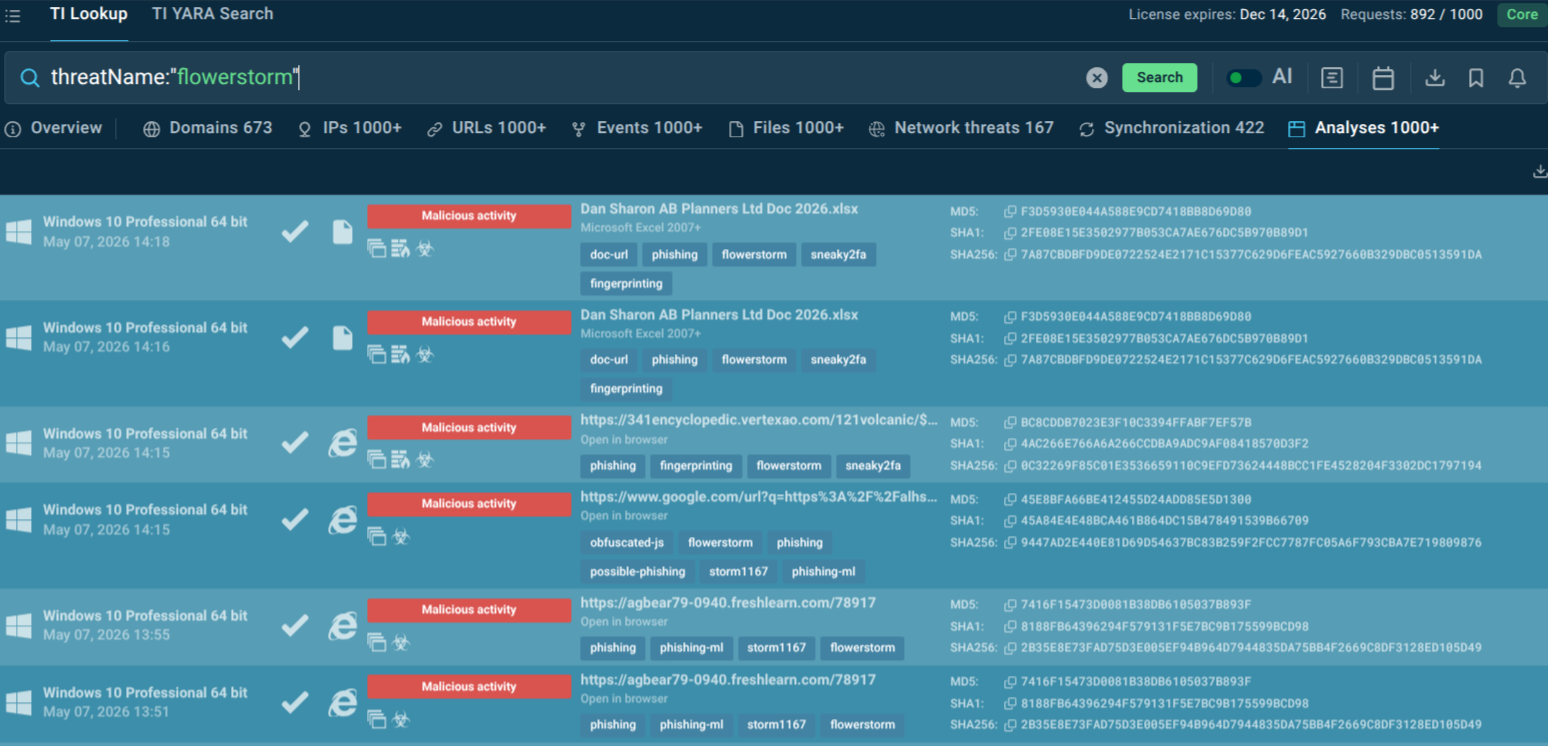
FlowerStorm is a phishing-as-a-service (PhaaS) platform used by cybercriminals to steal Microsoft 365 credentials and bypass multi-factor authentication (MFA) protections through adversary-in-the-middle (AiTM) attacks. Emerging after the disruption of Rockstar2FA in late 2024, FlowerStorm rapidly gained popularity among attackers targeting enterprises across North America and Europe.
|
Phishingkit
Type
:
|
Unknown
Origin
:
|
|
1 June, 2024
First seen
:
|
29 May, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 June, 2024
First seen
:
|
29 May, 2026
Last seen
:
|

 2385
2385
 0
0

 3432
3432
 0
0

 9118
9118
 0
0
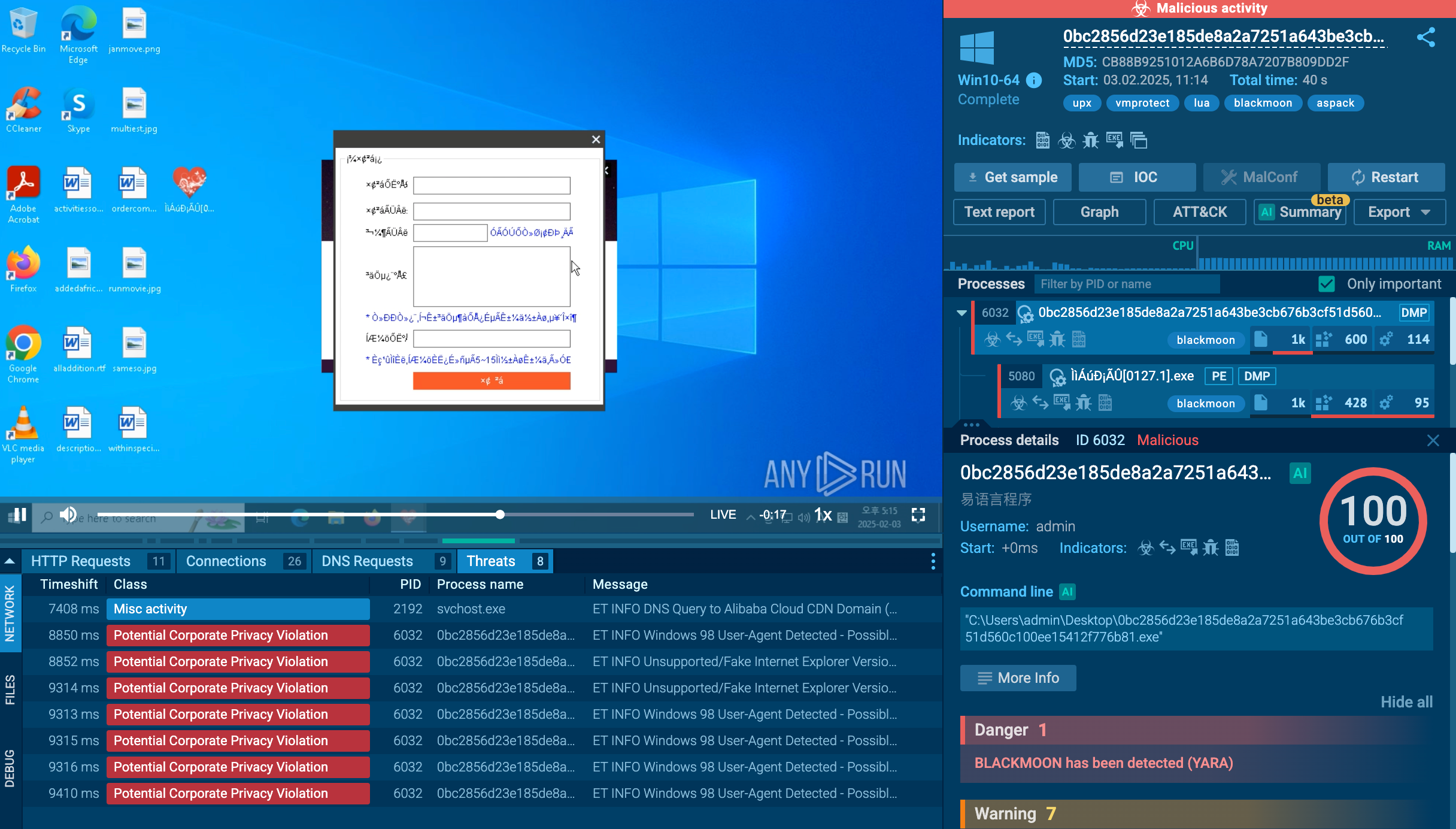
destinationIP:"172.67.215.79".
 FlowerStorm IP in sandbox analyses
FlowerStorm IP in sandbox analyses
Threat Intelligence Feeds automatically streams verified FlowerStorm IOCs (malicious IPs, domains, URLs) directly into SIEM, IDS/IPS, and EDR systems in STIX/TAXII format, enabling automated blocking of new phishing infrastructure before it reaches users.
FlowerStorm is a commercially operated PhaaS platform that equips threat actors with everything needed to run professional-grade phishing campaigns. Unlike traditional phishing kits that simply collect entered passwords, FlowerStorm employs real-time AiTM proxy infrastructure. When a victim visits a fake Microsoft 365 login page and authenticates, FlowerStorm's backend relays those credentials to the real Microsoft service, intercepts the resulting authenticated session cookie, and delivers it to the attacker. The attacker can then replay that cookie and gain full access to the victim's account without ever knowing their password or needing to satisfy an MFA prompt.
The platform shares extensive structural and operational similarities with Rockstar2FA, a preceding PhaaS operation, with researchers suggesting at minimum a common ancestry between the two.
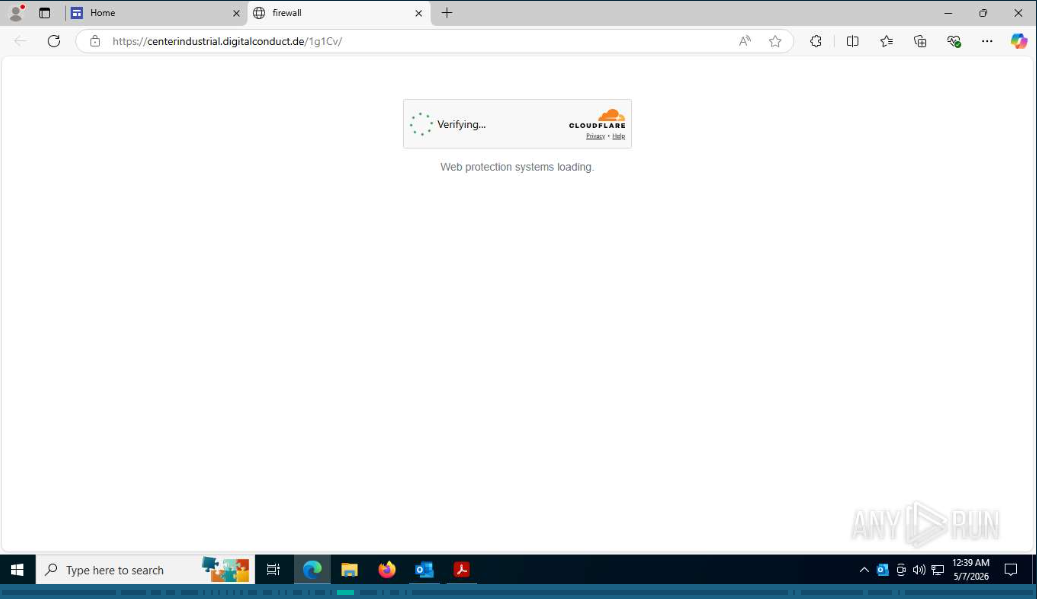
FlowerStorm's phishing portals are designed to closely mimic legitimate Microsoft 365 login pages, complete with Cloudflare Turnstile CAPTCHA challenges to block automated security scanners.
Credential data and JWT session tokens are exfiltrated to attacker-controlled backend servers using a standardized PHP file (next.php), which communicates via .ru, .moscow, and .com domains, as well as Cloudflare Pages infrastructure under .dev domains. The platform supports email validation, MFA relay, and session tracking, making it a complete identity theft engine.
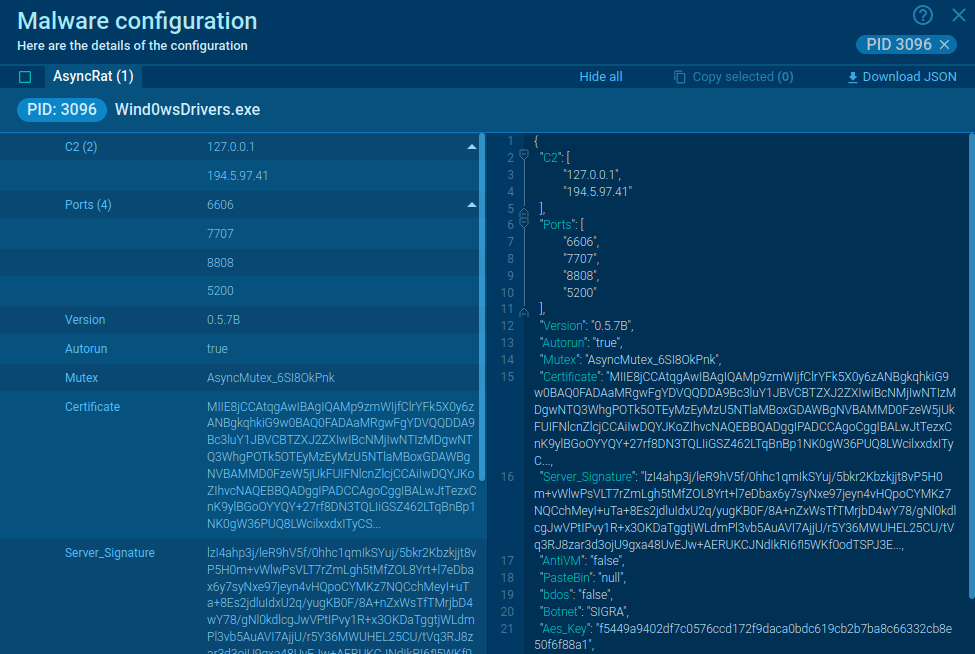
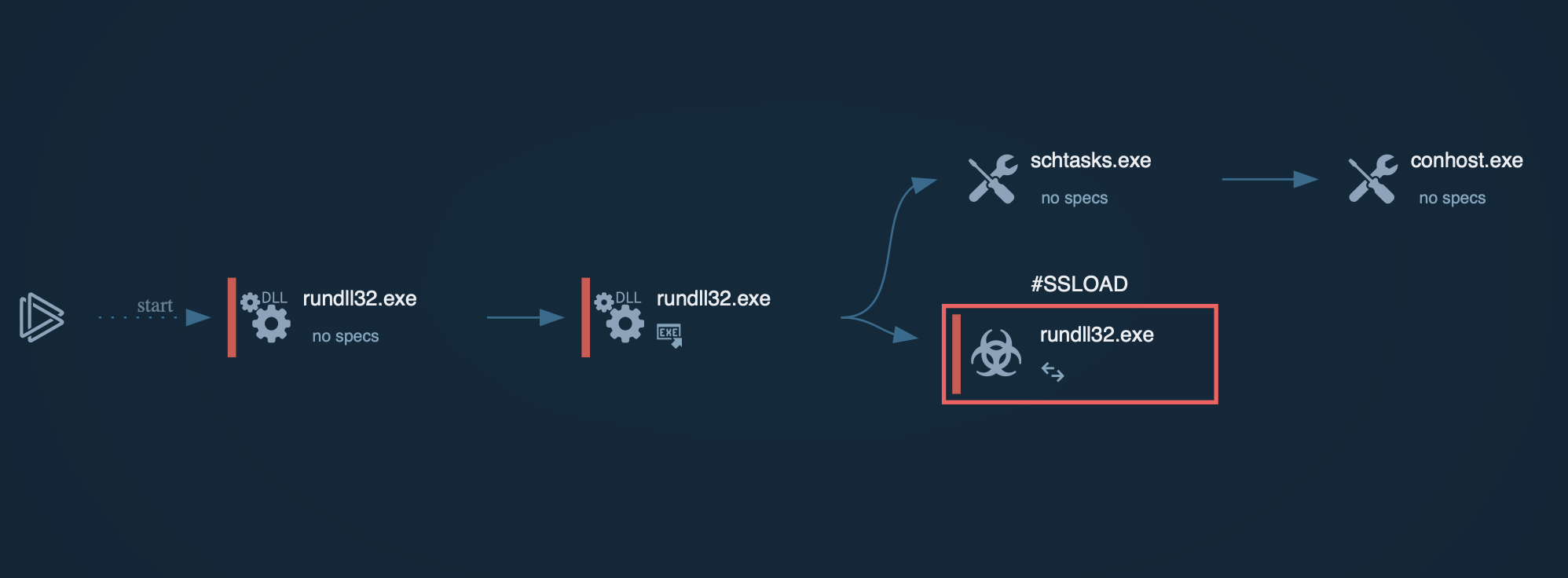
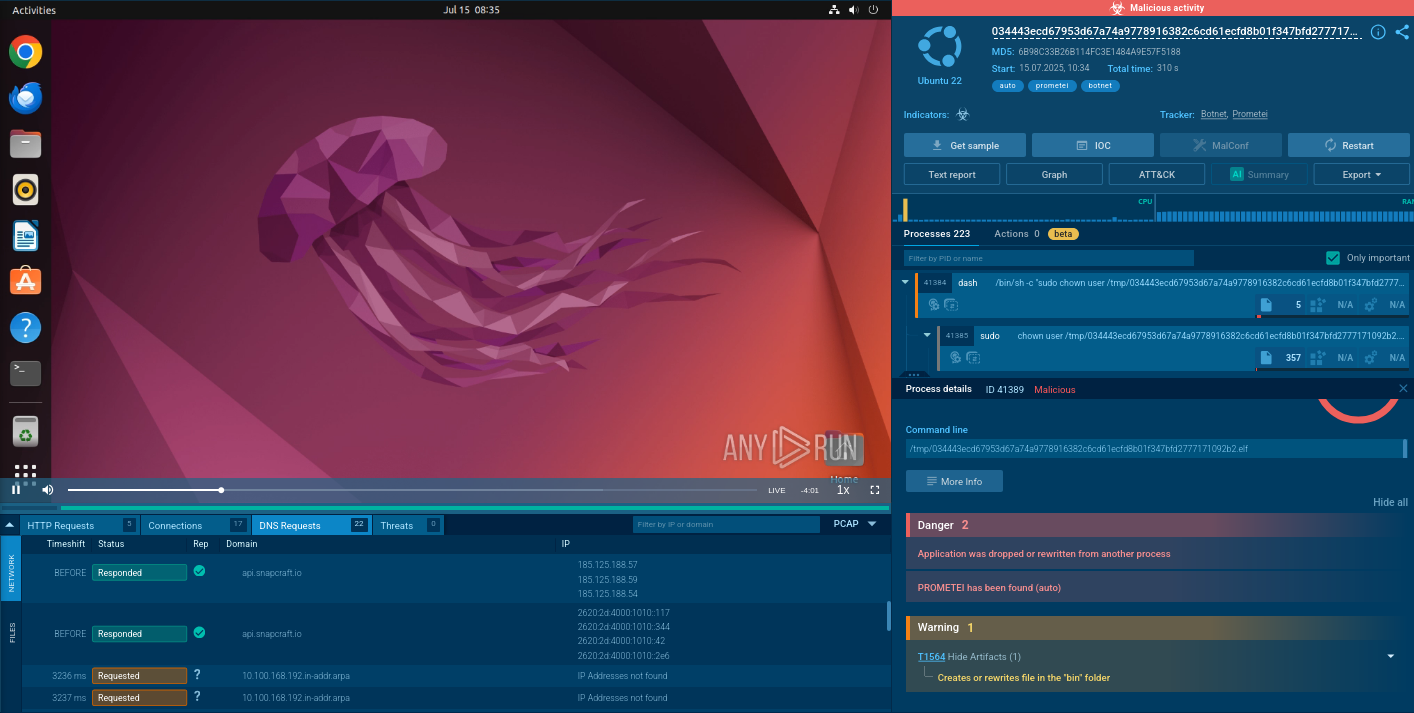
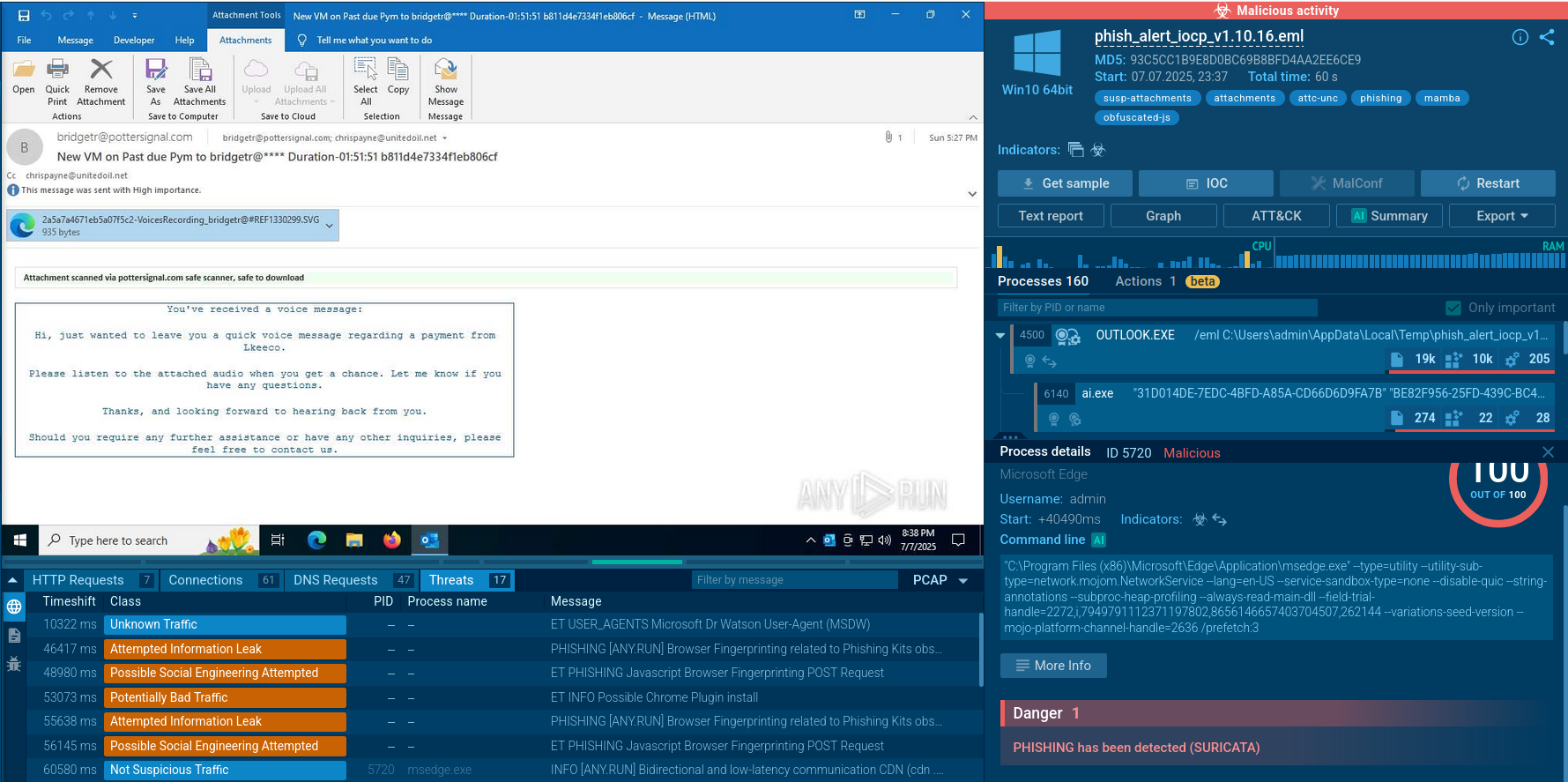
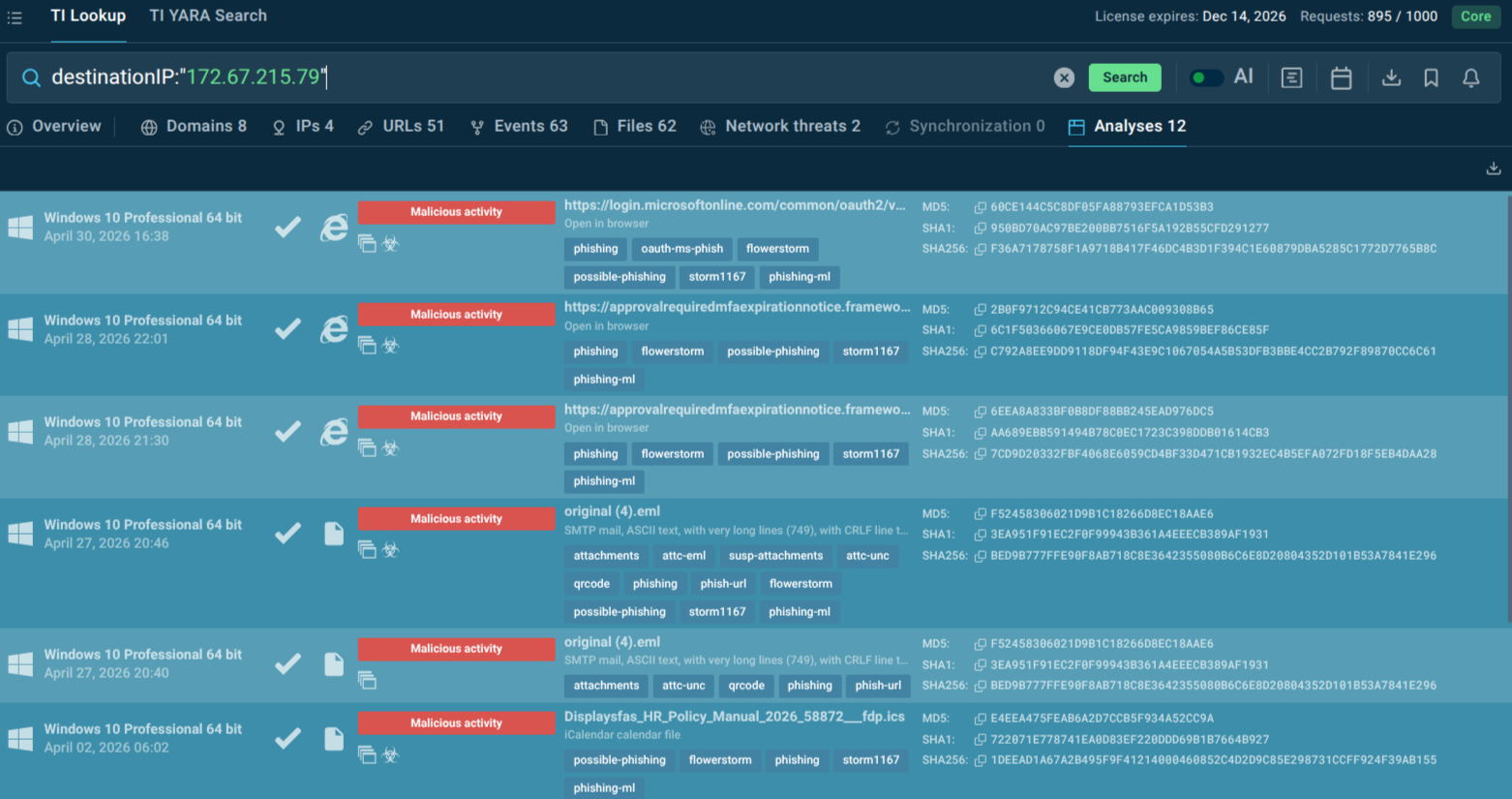
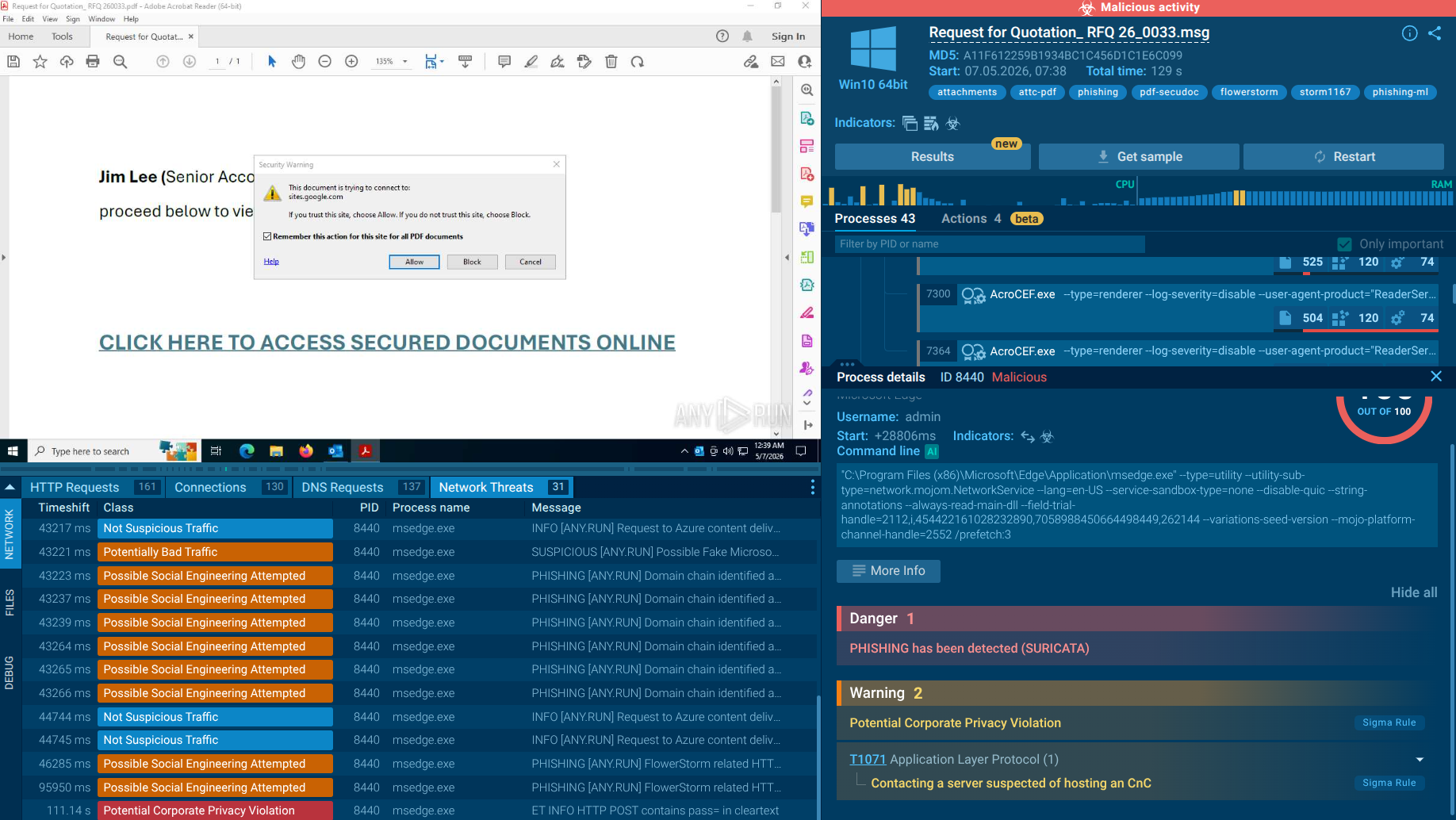
ANY.RUN’s Interactive Sandbox allows to safely detonate FlowerStorm samples and analyse full attack chain, connections, and processes:
 FlowerStorm detonated in Interactive Sandbox
FlowerStorm detonated in Interactive Sandbox
The platform uses plant-themed HTML titles (e.g., "Sprout," "Blossom," "Flower," "Leaf") for its phishing pages. It operates as a subscription service, often managed via Telegram bots, allowing even less-skilled attackers to deploy convincing fake Microsoft login portals.
FlowerStorm poses severe risks by enabling full account takeover of Microsoft 365 and associated enterprise resources. Once attackers obtain session tokens:
FlowerStorm and similar AiTM PhaaS kits disproportionately target organizations heavily reliant on Microsoft 365 for email, collaboration, and identity management.
Especially vulnerable sectors include:
FlowerStorm's attack chain begins at the inbox and, if successful, expands through the victim's network and contacts. The initial delivery mechanism relies primarily on crafted phishing emails, with the platform providing affiliates with the infrastructure to customize and deploy campaigns at scale.
Initial Delivery:
Victims receive a phishing email designed to create urgency or simulate a legitimate notification. FlowerStorm operators and their affiliates have used a variety of lure themes, including Microsoft security alerts, shared document notifications, HR communications (such as new employee announcements), and invoice or payment requests. The email contains a link that begins redirecting the victim through a chain of intermediary pages often hosted on legitimate services like Cloudflare Pages to obscure the final malicious destination from email security scanners.
Evasion of Automated Detection:
Multiple stages in the redirect chain use legitimate infrastructure (cloud CDNs, trusted domains) to make individual URLs appear benign. Cloudflare Turnstile CAPTCHA challenges are embedded in the phishing pages both to appear legitimate and to prevent security bots and web crawlers from analyzing the final landing page. The platform also employs JavaScript-based conditional page loading, so the malicious content is only served if the visitor appears to be a genuine human user.
Credential and Session Theft:
Once the victim reaches the fake Microsoft 365 login page and enters their credentials, FlowerStorm's AiTM proxy relays those credentials to the real Microsoft authentication service in real time. The victim successfully completes their MFA challenge (SMS code, authenticator app, push notification), and the resulting authenticated session cookie is intercepted by FlowerStorm's backend server via the next.php communication file. The victim is then redirected to a legitimate Microsoft page, often experiencing nothing unusual.
Post-Compromise Spread:
With a valid session cookie, the attacker logs into the victim's Microsoft 365 account. From this position, the attack can spread in several directions: internal phishing emails sent from the trusted compromised account, access to connected applications and data stores, password resets and privilege escalation to deepen control, and creation of persistent access mechanisms such as new OAuth app authorizations or hidden inbox rules.
At its core, FlowerStorm is a reverse-proxy phishing platform.
AiTM Proxy Architecture:
The attacker's server acts as a real-time man-in-the-middle between the victim's browser and the legitimate Microsoft authentication service. When the victim submits credentials, the proxy forwards them to Microsoft, receives a valid response (including an MFA challenge), and relays that challenge back to the victim. When the victim completes the MFA step, Microsoft issues an authenticated session cookie, which the proxy intercepts before passing the legitimate session back to the user.
Backend Communication (next.php):
FlowerStorm standardized its backend communication around a PHP file called next.php. This file handles credential transmission (email, password), JWT token exchange for session tracking, MFA relay logic, and success/failure signaling.
Anti-Bot and Evasion Mechanisms:
Credential Harvesting Fields:
The phishing portal captures standard Microsoft login fields (email, password) along with MFA tokens and session identifiers. The backend supports email-address validation (to confirm a target is a genuine corporate user before serving the full phishing flow) and dynamic MFA challenge relay.
Modern phishing threats move too quickly for static indicators alone. Security teams need continuous visibility into:
This is where Threat Intelligence becomes operational rather than theoretical.
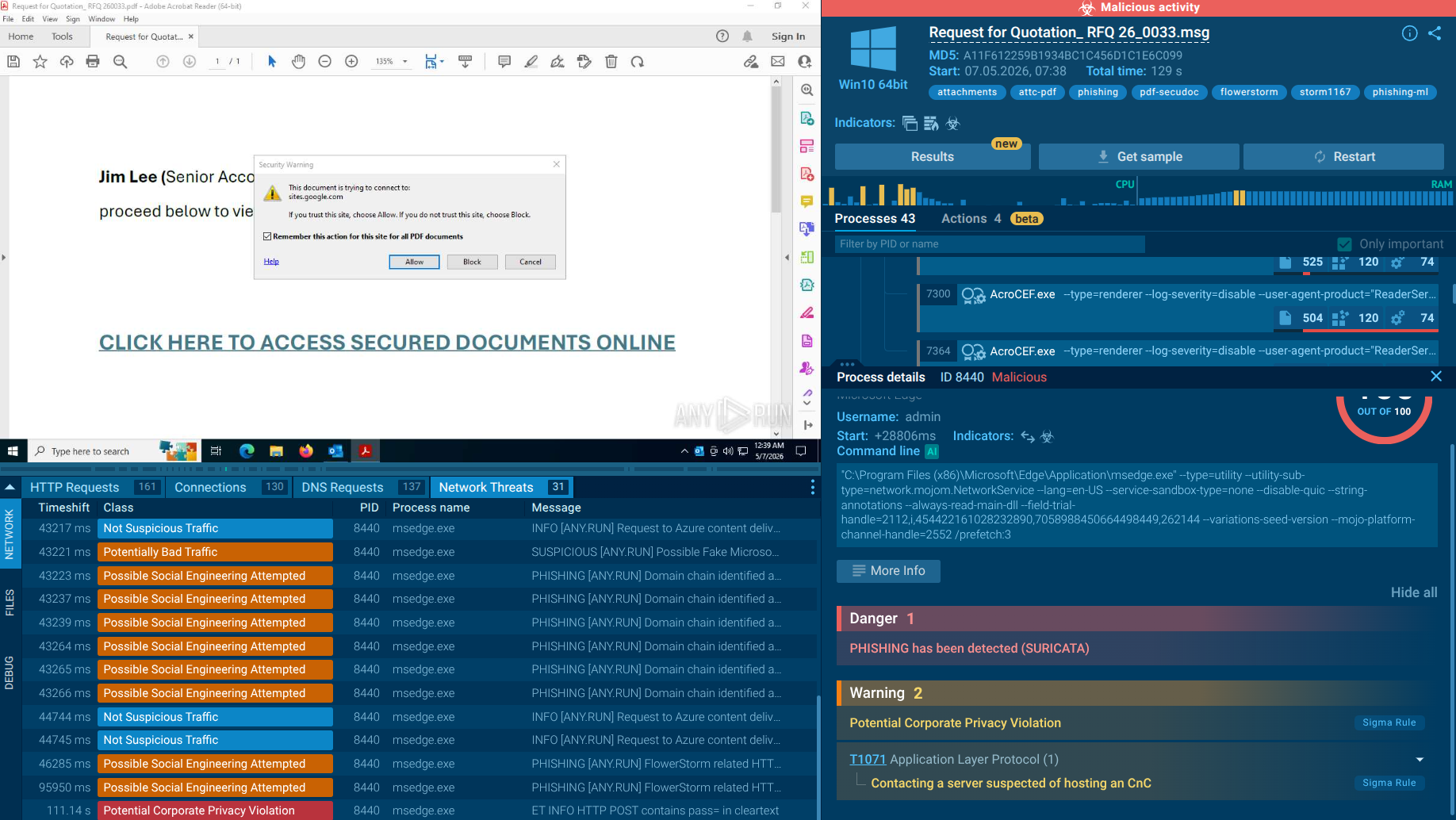
With Threat Intelligence Lookup, analysts can:
This helps SOC teams pivot from isolated alerts to full attack-chain visibility. Start the research with the threat name:
 FlowerStorm summary in TI Lookup
FlowerStorm summary in TI Lookup
Threat Intelligence Feeds help organizations to:
The biggest advantage is speed. FlowerStorm infrastructure changes rapidly, so automated IOC enrichment becomes critical.
Additional Measures:
Organizations should also:
A layered defense strategy is essential because no single control can stop AiTM phishing alone.
Using ANY.RUN’s Interactive Sandbox, analysts can detonate a suspicious file or a link, get it detected as a FlowerStorm attack sample, and observe the behavior, TTPs, and kill chain along with gathering additional IOCs.
View FlowerStorm analysis session
 FlowerStorm summary in TI Lookup
FlowerStorm summary in TI Lookup
The attack begins with an email disguised as a work document, a protected attachment, or a notification requiring review. Instead of being taken directly to a phishing page, the user is often first directed to an intermediate screen with a button to access the document or confirm opening the file.
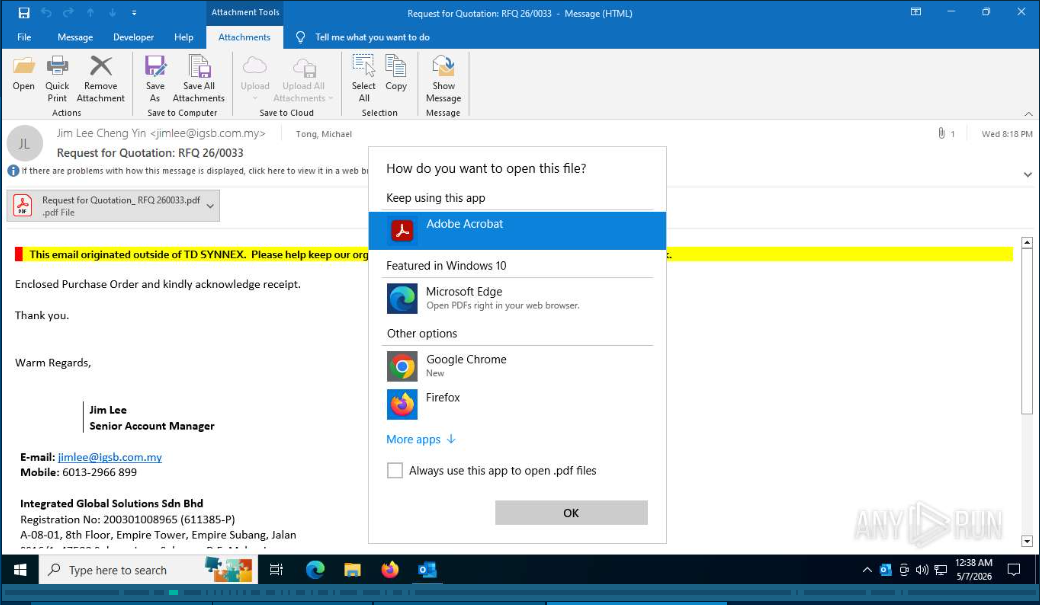 File opening request
File opening request
An important detail for SOC teams: The intermediate page can be hosted on legitimate infrastructure, such as platforms like Google Sites. This increases the victim’s trust and simultaneously complicates early detection, because the first stage of the attack chain passes through a well-known and generally legitimate service rather than an obviously malicious resource.
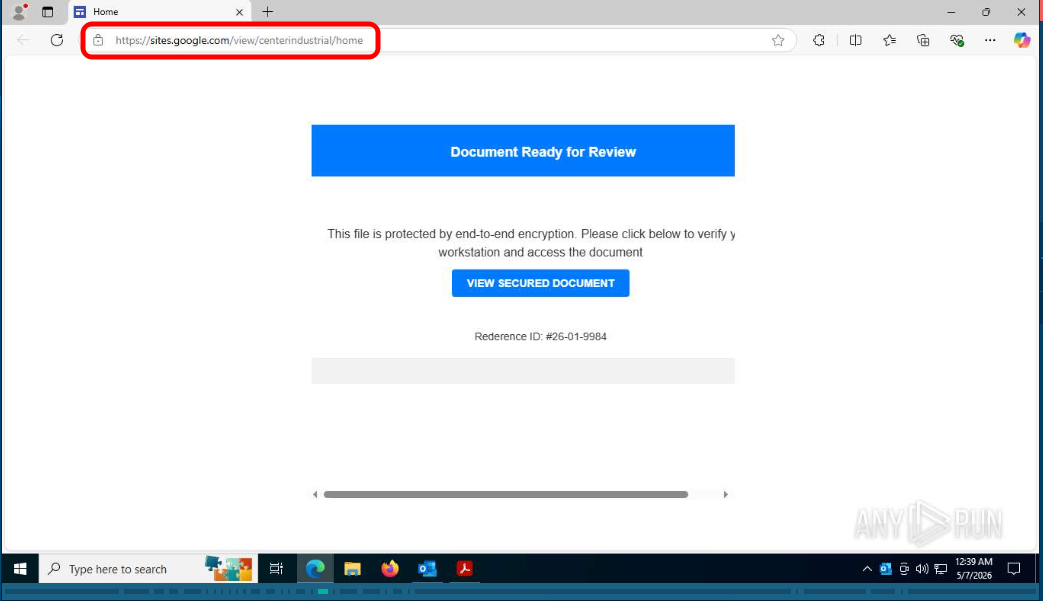 Page hosted on Google Sites
Page hosted on Google Sites
Next, the victim is redirected to a fake login page styled to look like Microsoft 365 or another cloud service. Visually, it replicates the normal authentication process: a familiar interface, standard login steps, and typical credential verification logic.
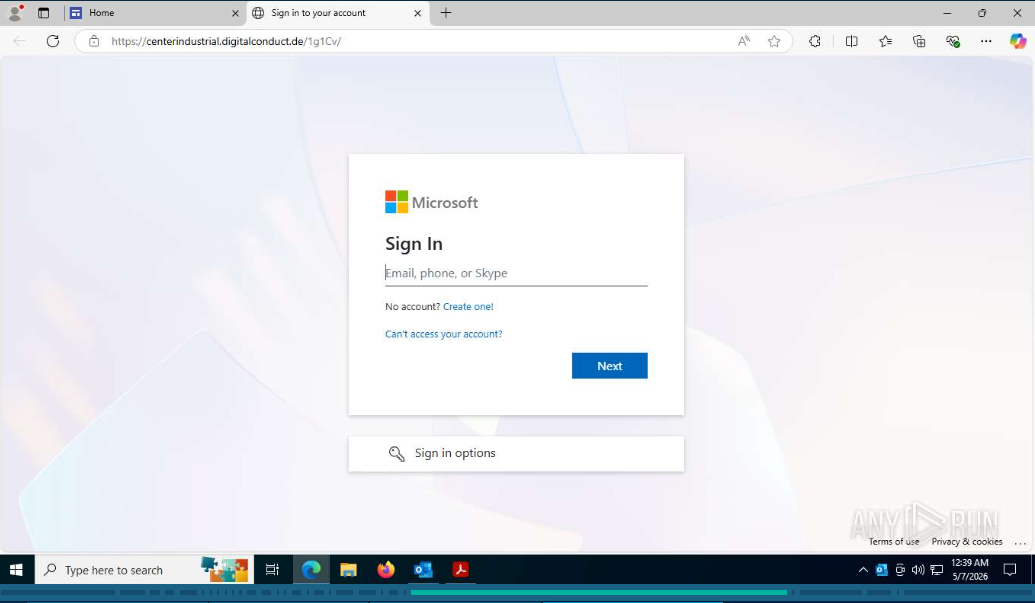 Fake Microsoft sign-in form
Fake Microsoft sign-in form
The key feature of FlowerStorm is that it does not operate as a primitive login and password stealer. Its goal is to guide the user through the entire authentication process, including the second factor, in order to obtain not only credentials but also artifacts of an active session. This allows attackers to use already authenticated access and bypass MFA not by “breaking” it, but by essentially hijacking the result of a successful login.
CAPTCHA or other anti-bot checks are often used in the chain. For attackers, this serves two purposes at once: such elements make the scenario more believable to the user and simultaneously hinder sandboxes, URL scanners, and some automated analysis tools from seeing the full attack chain. ANY.RUN’s Sandbox can interact with such elements emulating user behavior:
 CAPTCHA bypassed by Sandbox
CAPTCHA bypassed by Sandbox
After successfully completing all stages, attackers gain access to the cloud session and can act on behalf of the user without triggering immediate additional MFA prompts. Therefore, the real danger of FlowerStorm lies not only in stealing the password, but in the subsequent session hijacking, which can outwardly appear as normal user activity.
FlowerStorm represents the commoditization of advanced AiTM phishing, lowering the barrier for attackers while raising the stakes for organizations. Its rapid evolution and focus on Microsoft 365 highlight the need for proactive, intelligence-driven defenses beyond traditional MFA. By combining human vigilance with advanced tools like ANY.RUN's TI solutions and robust identity security, businesses can significantly reduce exposure.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.