Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


Diamotrix is a stealthy cryptocurrency clipper malware that silently monitors the Windows clipboard, waiting for the moment a user copies a digital wallet address. Diamotrix replaces it with an attacker-controlled wallet, invisibly redirecting any resulting transaction. Because blockchain transfers are irreversible, victims rarely discover the theft until the funds are long gone.
|
Clipper
Type
:
|
Unknown
Origin
:
|
|
1 June, 2024
First seen
:
|
6 April, 2026
Last seen
:
|
|
Clipper
Type
:
|
Unknown
Origin
:
|
|
1 June, 2024
First seen
:
|
6 April, 2026
Last seen
:
|

 456
456
 0
0

 2547
2547
 0
0

 4757
4757
 0
0
Diamotrix is often revealed by characteristic mutexes:
syncObjectName:"cleansystem_17582".
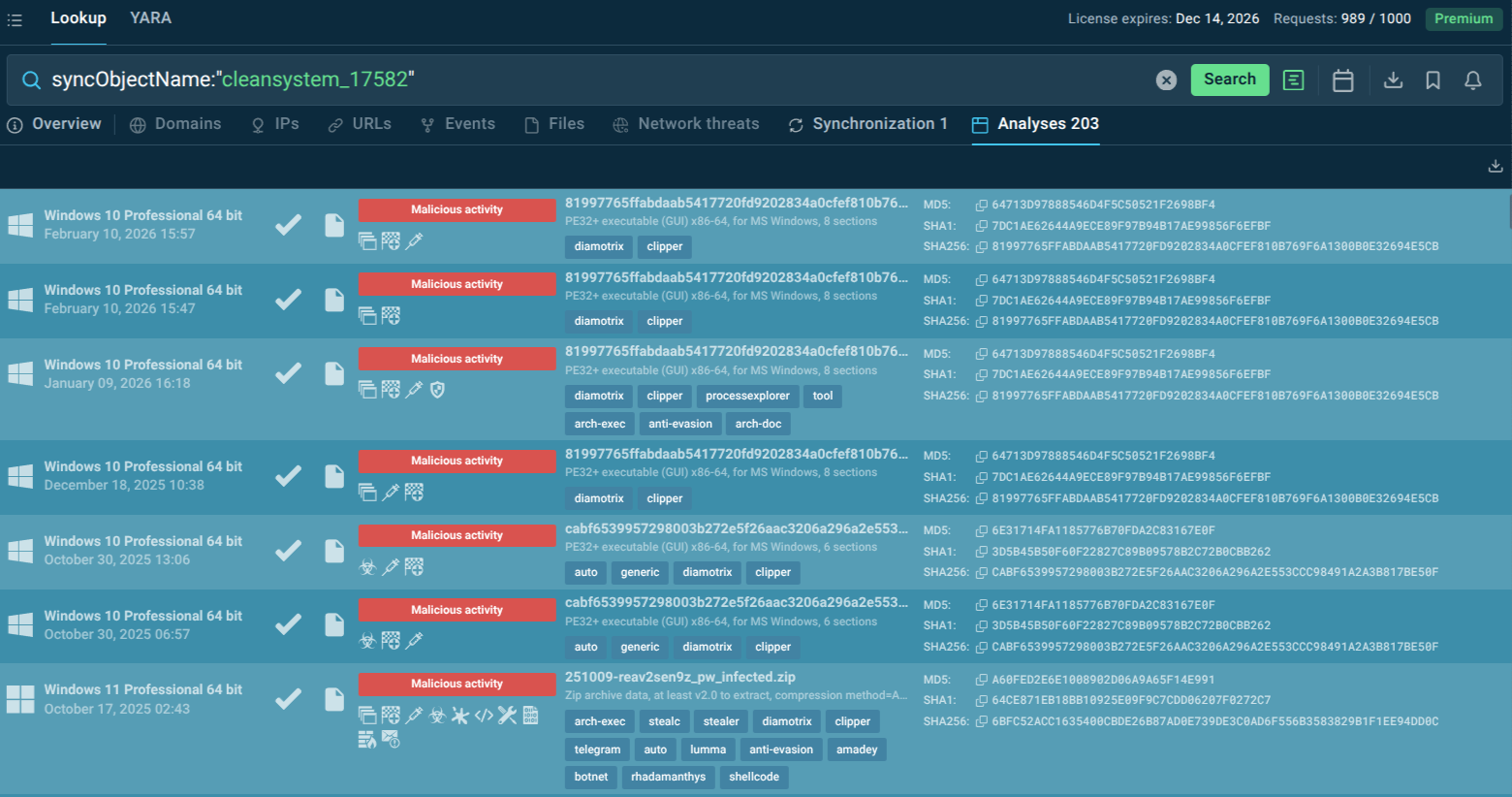 Mutex search in TI Lookup exposes Diamotrix samples
Mutex search in TI Lookup exposes Diamotrix samples
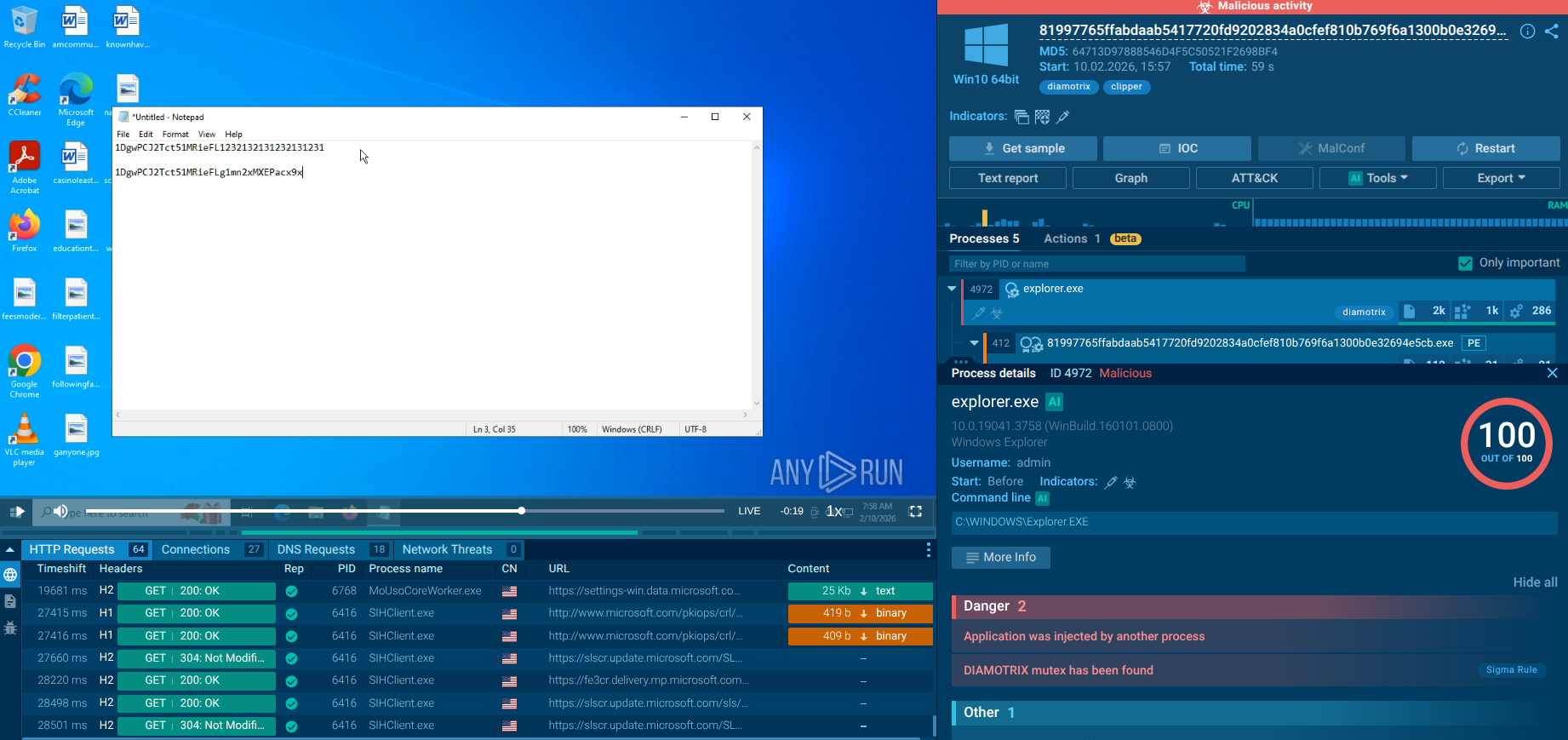 Diamotrix replaces crypto wallet address in the clipboard
Diamotrix replaces crypto wallet address in the clipboard
Diamotrix is a type of infostealer malware specifically classified as a "clipper." It is designed to monitor the clipboard data of an infected Windows system. When a user copies what appears to be a cryptocurrency wallet address, the malware swiftly replaces it with an address controlled by the attacker. If the user then pastes the address to send a payment, the funds are inadvertently sent to the thief's wallet. Fortinet's FortiGuard Labs has identified it as a botnet, meaning infected machines can be centrally controlled to carry out this clipboard monitoring and theft on a large scale.
First observed in active campaigns around mid-2024 and formally identified by security researchers in September 2024, Diamotrix is distributed as a loader-delivered payload, frequently deployed alongside other commodity stealers such as Sniffthem, Rhadamanthys, and Stealc. It targets the Windows platform and has been confirmed by FortiGuard Labs, ANY.RUN sandbox analyses, and Red Piranha threat intelligence as a significant and growing threat to individuals, businesses, and organizations that handle cryptocurrency.
Unlike ransomware or wiper malware, Diamotrix does not announce its presence. It is a passive, persistent threat designed to remain undetected for as long as possible, silently waiting for the right moment to act. The malware establishes persistence in the Windows startup directory, communicates with a command-and-control (C2) server to retrieve fresh attacker wallet addresses, and then continuously monitors clipboard events in the background.
The malware is compiled as a 32-bit PE executable, disguised with metadata mimicking legitimate Windows system components (e.g., CompanyName: “Soft”, ProductName: “Software”, file version strings that mimic system files). It uses process injection techniques, injecting its code into Windows Explorer (explorer.exe) and other trusted system processes to evade endpoint detection. Communication with the C2 server is conducted over HTTP, fetching an updated wallet address pack (diamotrix[.]pack) and sending stolen transaction data via POST requests to the C2 API.
For the purposes of evasion, the clipper checks supported languages (possible sandbox/geo-evasion), reads machine GUID, checks proxy server settings, mimics Windows Services process names. Obfuscation is based upon control flow flattening and anti-analysis techniques confirmed in multi-stage deployments.
For individual users, Diamotrix represents direct and immediate financial loss — a single intercepted Bitcoin or Ethereum transfer can result in thousands of dollars disappearing silently. For businesses and organizations, the threat surface is substantially larger and more complex.
Direct Financial Loss: Any employee or automated system that handles cryptocurrency payments, treasury operations, payroll in digital assets, or DeFi transactions is a potential victim. Because transactions are irreversible on blockchain networks, there is no mechanism for recovery once funds are diverted.
Operational and Reputational Damage: The business may face contractual disputes, damaged supplier relationships, and reputational harm. If the victim is a financial institution, exchange, or crypto-native business, the reputational fallout can be catastrophic.
Multi-Payload Risk Amplification: Diamotrix is rarely deployed alone, it commonly is part of a multi-payload bundle that also includes sophisticated information stealers. A single infection event can simultaneously result in credential theft, browser data exfiltration, and cryptocurrency transaction hijacking.
Persistence and Lateral Threat Potential: If initial triage misses the persistence mechanism, the malware will resume activity after remediation efforts, allowing attackers to continue extracting value indefinitely.
While any individual or entity using cryptocurrency is a potential target, specific sectors are at higher risk due to the nature of their transactions:
Cryptocurrency Exchanges and Fintech: Employees with access to hot wallets or large transaction capabilities are prime targets.
Real Estate and Legal Firms: These sectors increasingly handle large down payments or settlements in cryptocurrency.
Technology and SaaS Companies: Firms that accept cryptocurrency for payments are vulnerable.
High-Net-Worth Individuals: Executives and owners who personally manage crypto assets are attractive victims.
ANY.RUN’s Threat Intelligence solutions empower SOCs and MSSPs to combat Diamotrix by providing instant access to detailed malware verdicts, IOCs (hashes, domains, URLs, behavior signatures), and interactive sandbox reports. Business protection is assured by:
Rapid hash/domain lookup for incident triage and alert validation.
Contextual enrichment of alerts with real-time ANY.RUN analyses.
Proactive hunting for Diamotrix indicators in environments.
Reduced false positives and faster response times.
Cost-effective threat visibility and risk management.
Diamotrix’s threat model relies on speed: the malware needs only a fraction of a second to replace a clipboard entry, and the resulting transaction is irreversible. This means that retrospective detection — finding the infection after a theft has occurred — is fundamentally insufficient. Threat Intelligence Feeds shift the defense posture from reactive to proactive:
Real-time C2 blocking: As new Diamotrix C2 IP addresses and domains are identified through live sandbox analyses, TI Feeds push these indicators to SIEMs, firewalls, and IDS/IPS platforms in near-real-time — blocking communication before wallets can be fetched or data exfiltrated.
Fresh, low-noise IOCs: Indicators in TI Feeds are extracted from real, confirmed-malicious sandbox sessions rather than third-party aggregation, dramatically reducing false positives that cause alert fatigue.
STIX/TAXII delivery: TI Feeds are delivered in industry-standard STIX format via TAXII, enabling plug-and-play integration with platforms including MISP, ThreatQ, Splunk, Microsoft Sentinel, and other SIEM/SOAR/TIP solutions — no custom development required.
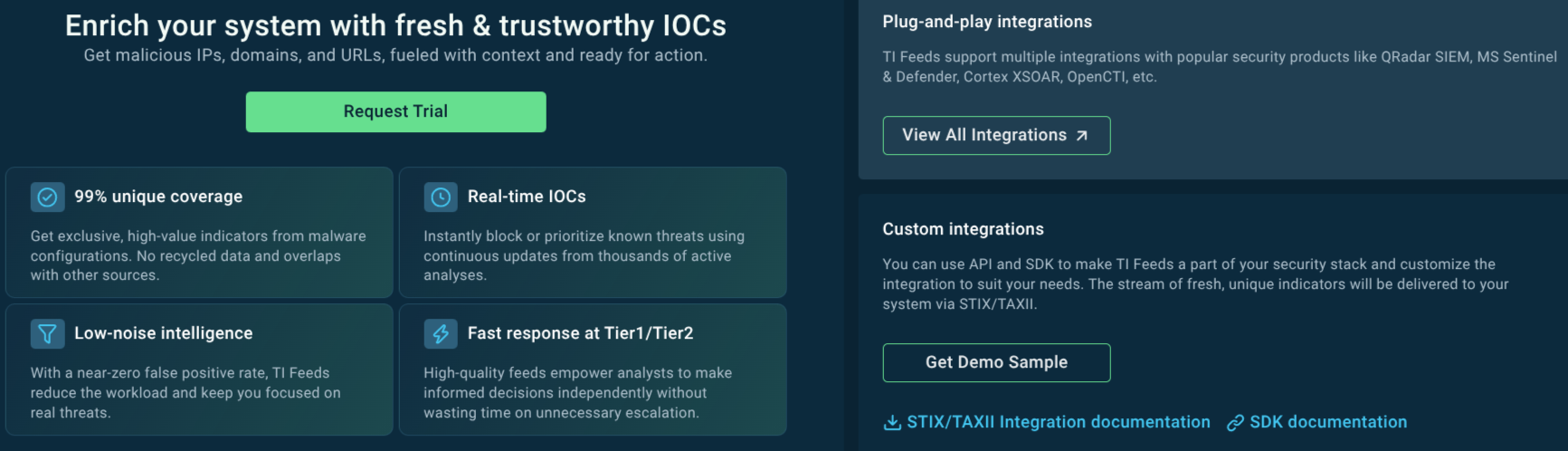 TI Feeds benefits and integration options
TI Feeds benefits and integration options
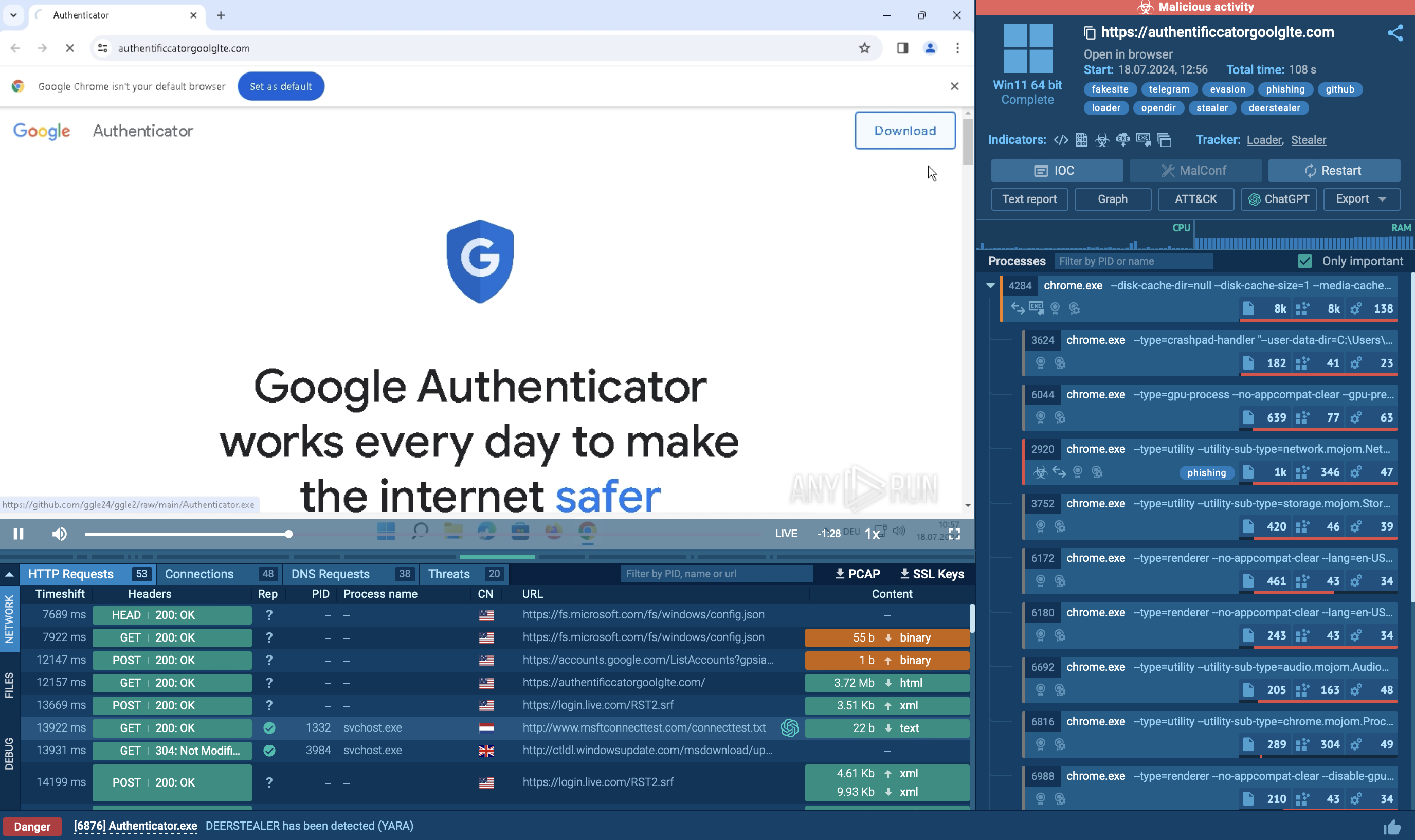
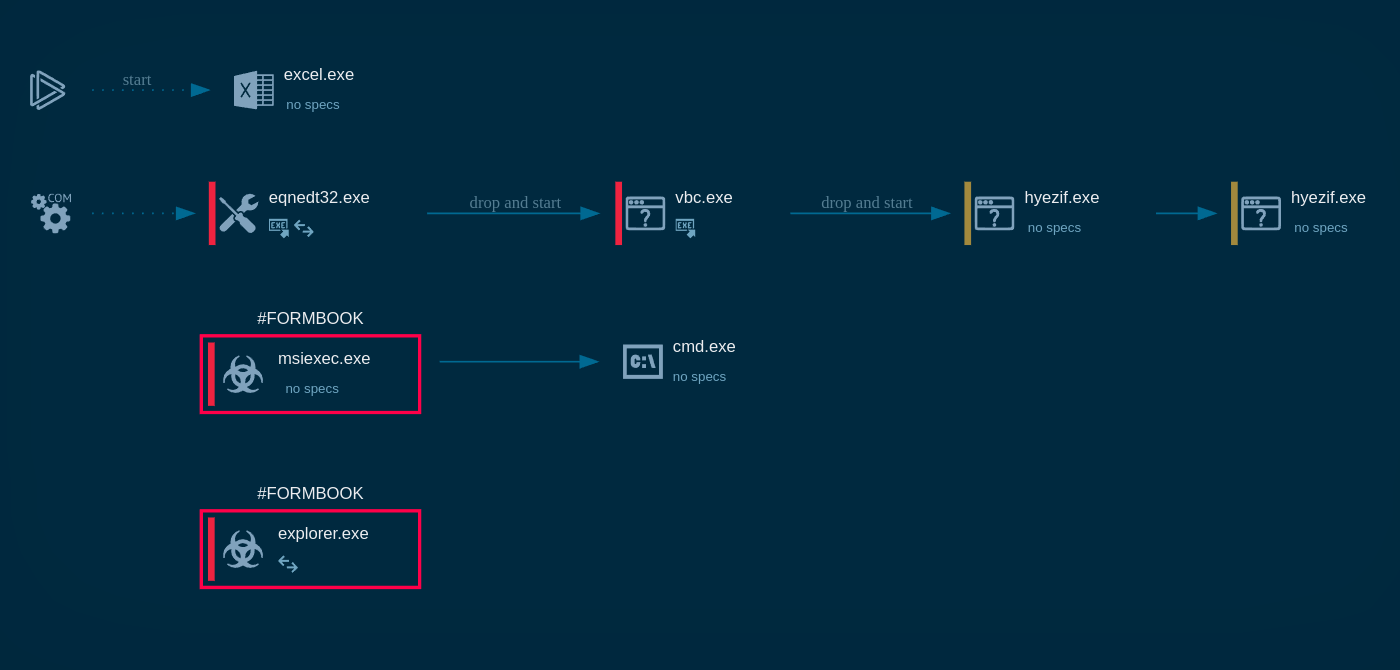
Diamotrix primarily infects systems through:
Spear-Phishing Emails: Malicious attachments disguised as legitimate documents or executables trick users into launching the malware.
Loader Malware: It is often dropped by other malware, such as the "Optimal Dropper" or loaders associated with SVCStealer, which act as delivery vehicles for multiple payloads.
Malicious Downloads: It can be hidden in cracked software, fake updates, or payloads hosted on malicious domains (e.g., diamotrix[.]online, diamotrix[.]club).
Once installed, Diamotrix establishes persistence through two mechanisms observed in sandbox analyses:
Registry persistence: Writes a startup entry to HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run, ensuring the malware relaunches after every system reboot under a randomized GUID-based folder and file name (e.g., {2F33566DA0B91573532102}).
Startup directory: Copies autoupdater.exe to the user’s Roaming AppData directory and places an executable in the Windows Startup folder, disguised as a legitimate autoupdater process.
The use of randomized GUID-based directory and file names makes static signature detection substantially more difficult, as each deployment generates a unique file path.
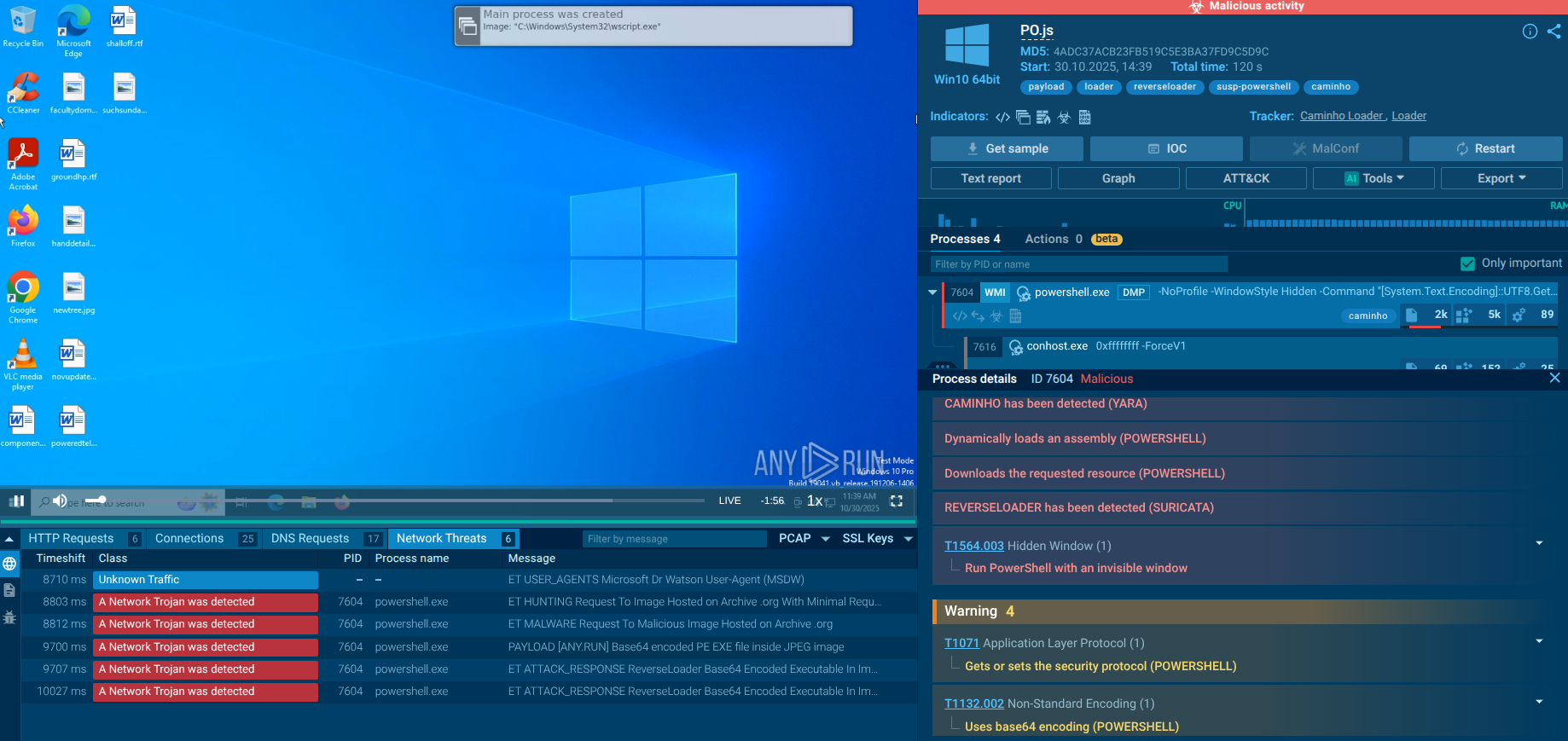
Initial Execution and Process Injection
Upon execution, the primary Diamotrix binary (or its loader component) first performs environmental checks: it reads the computer name, checks supported languages, reads the machine GUID from the registry, and checks proxy server information. These checks serve dual purposes gathering victim system intelligence and detecting sandbox or analysis environments. If the environment passes these checks, execution proceeds.
The malware then spawns autoupdater.exe in the user’s AppData\Roaming directory (disguised as a legitimate auto-update process) and uses it as a persistence relay. It also drops a secondary component which performs additional system enumeration.
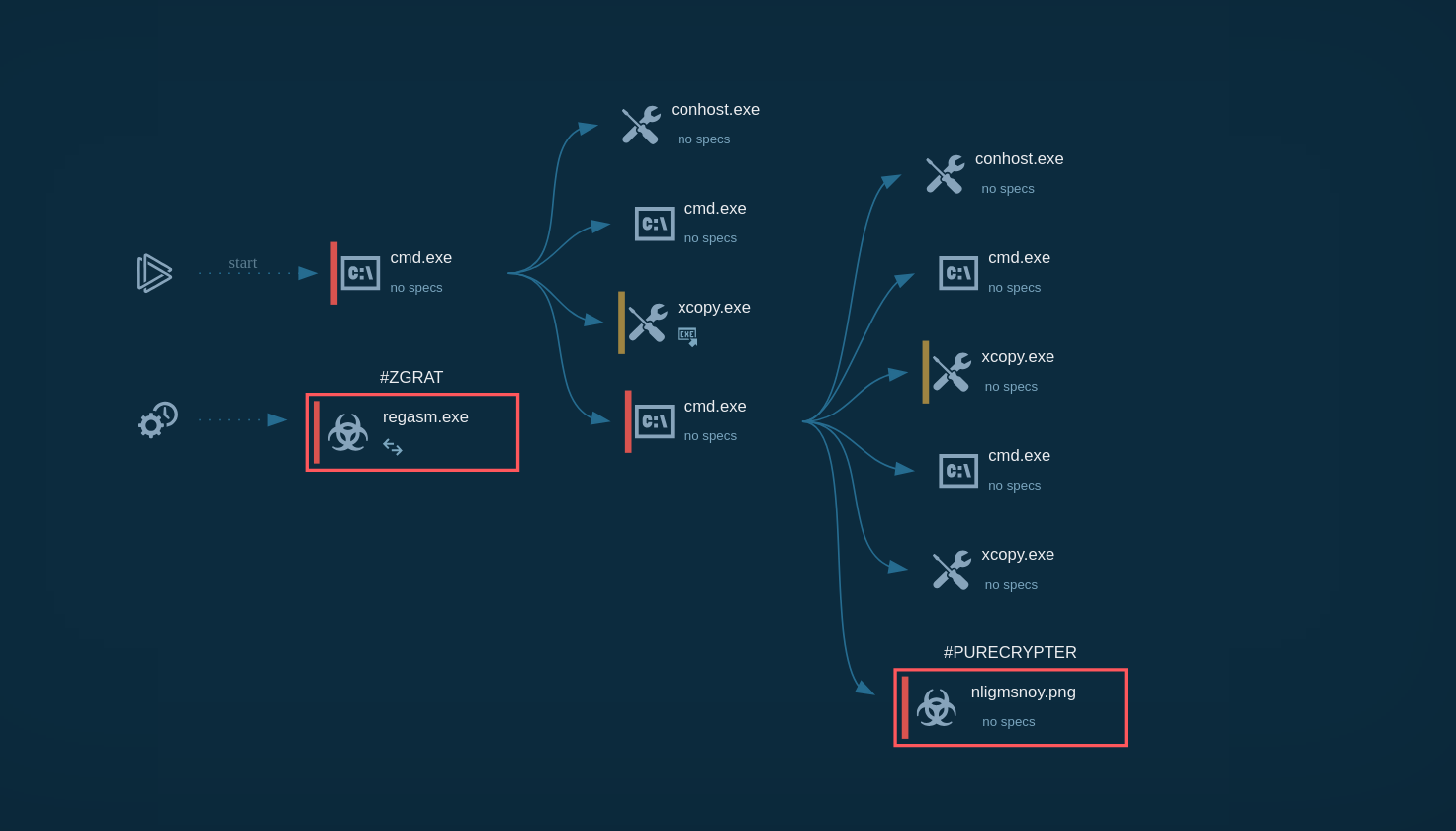
Code Injection into Trusted Processes
Diamotrix injects malicious code into two trusted Windows processes: svchost.exe (the Windows service host) and explorer.exe (Windows Explorer). Process injection into explorer.exe is particularly effective because explorer.exe is always running, operates at medium integrity level, and is rarely flagged as suspicious for making network connections. This injection ensures that the clipper operates persistently in the background.
C2 Communication and Wallet Retrieval
The injected code in explorer.exe initiates C2 communication via HTTP GET request to retrieve the attacker’s current wallet address pack (diamotrix.pack). This design is significant: rather than hardcoding a single wallet address, Diamotrix fetches addresses dynamically, allowing operators to rotate their wallets to evade blockchain-based tracking. The C2 infrastructure communicates over standard HTTP port 80, blending with legitimate web traffic.
Clipboard Monitoring and Address Substitution
With the attacker’s wallet addresses loaded, Diamotrix’s core function begins: continuous monitoring of the Windows clipboard. The malware uses regex-based pattern matching (crypto-regex) to identify valid cryptocurrency wallet addresses as they are copied by the user. Major cryptocurrencies are targeted, including but not limited to Bitcoin (BTC), Ethereum (ETH), and likely others based on the regex library used. When a match is detected, the malware silently replaces the clipboard content with the attacker’s wallet address.
Data Exfiltration
Beyond wallet substitution, Diamotrix exfiltrates transaction data and victim information via HTTP POST requests to the C2 API endpoint (api[.]php). This telemetry allows the attacker to monitor which victims are actively making cryptocurrency transactions, the amounts involved, and the success rate of the wallet substitution.
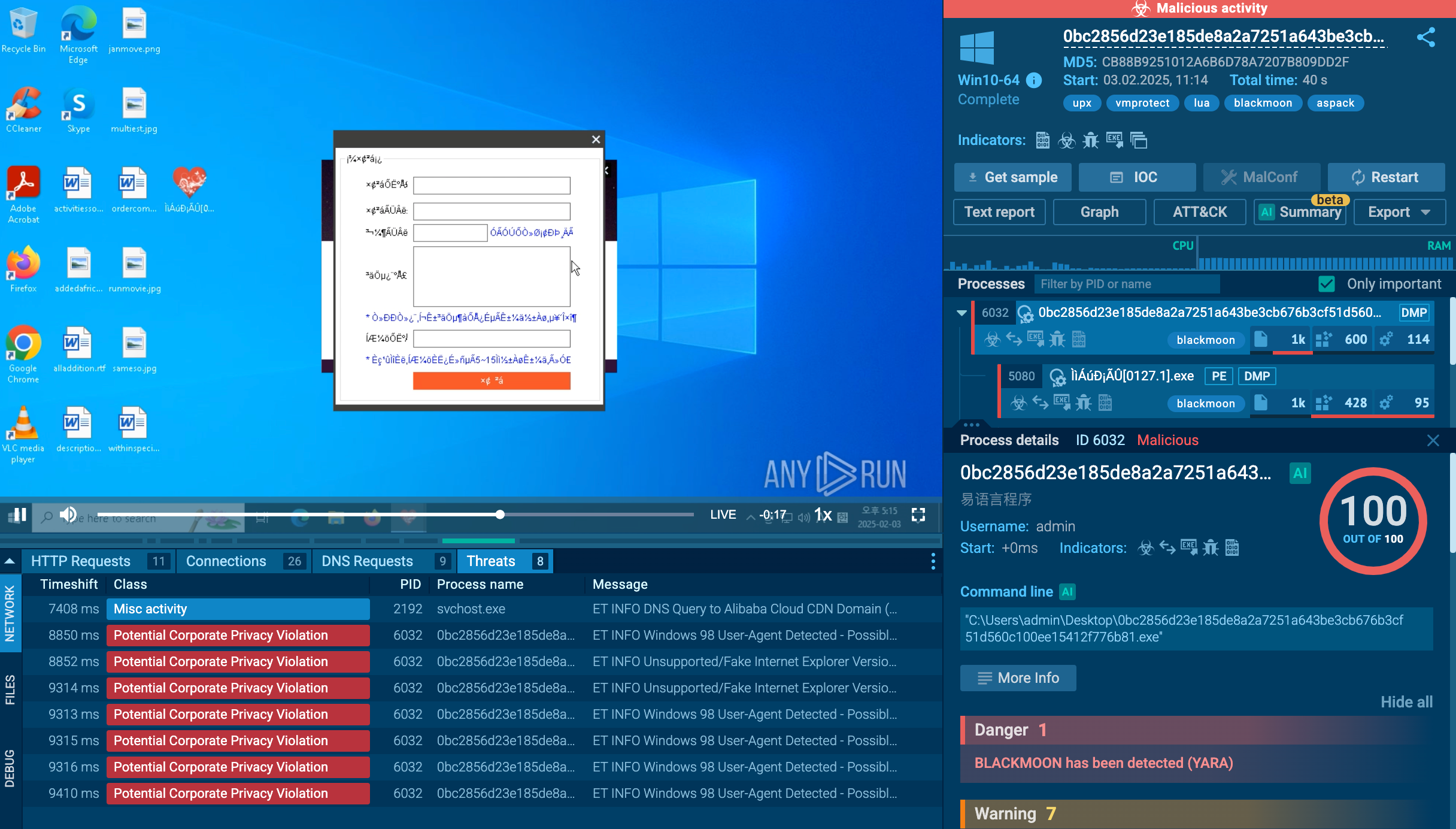
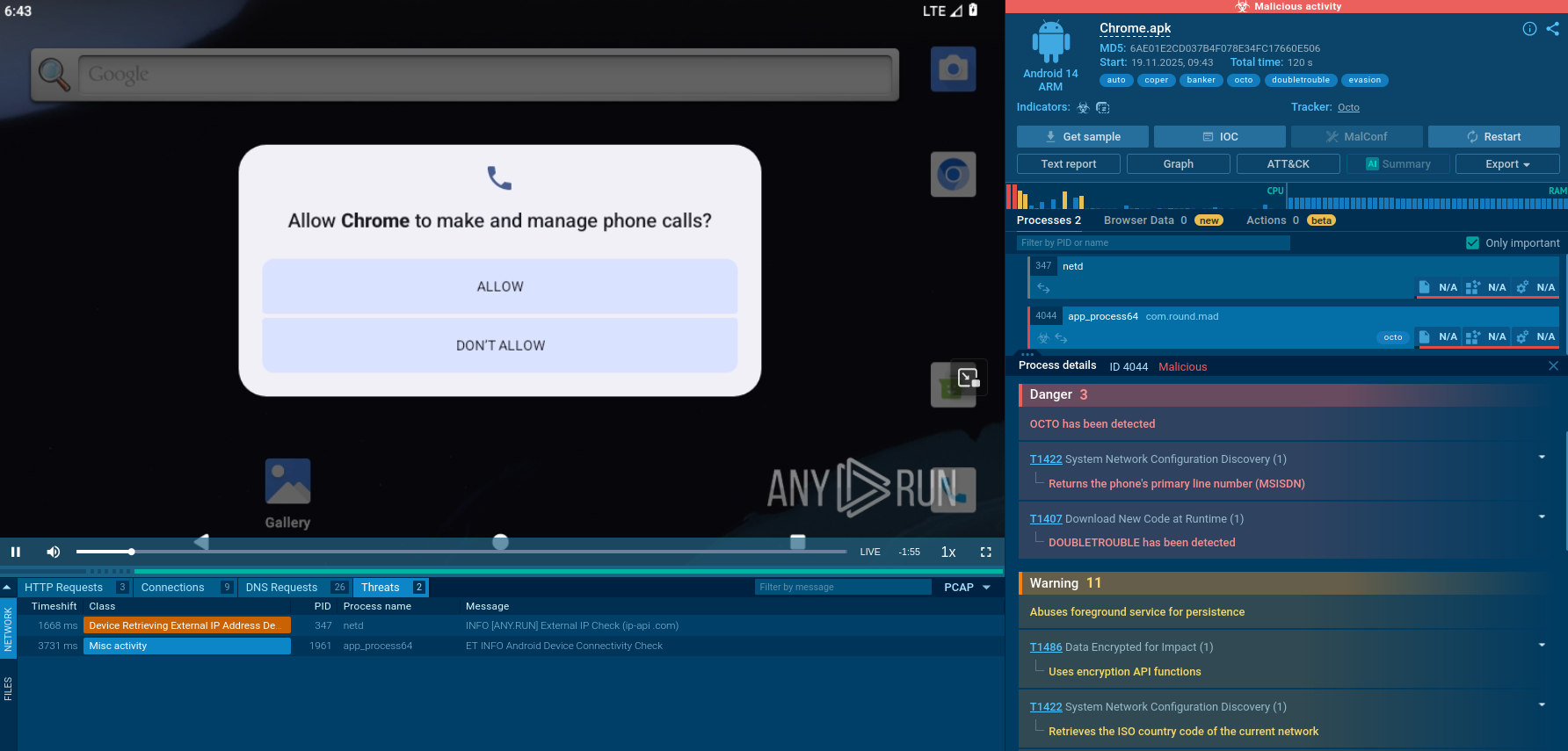
The key stages of Diamotrix attack chain are visible in ANY.RUN’s Interactive Sandbox safe detonations:
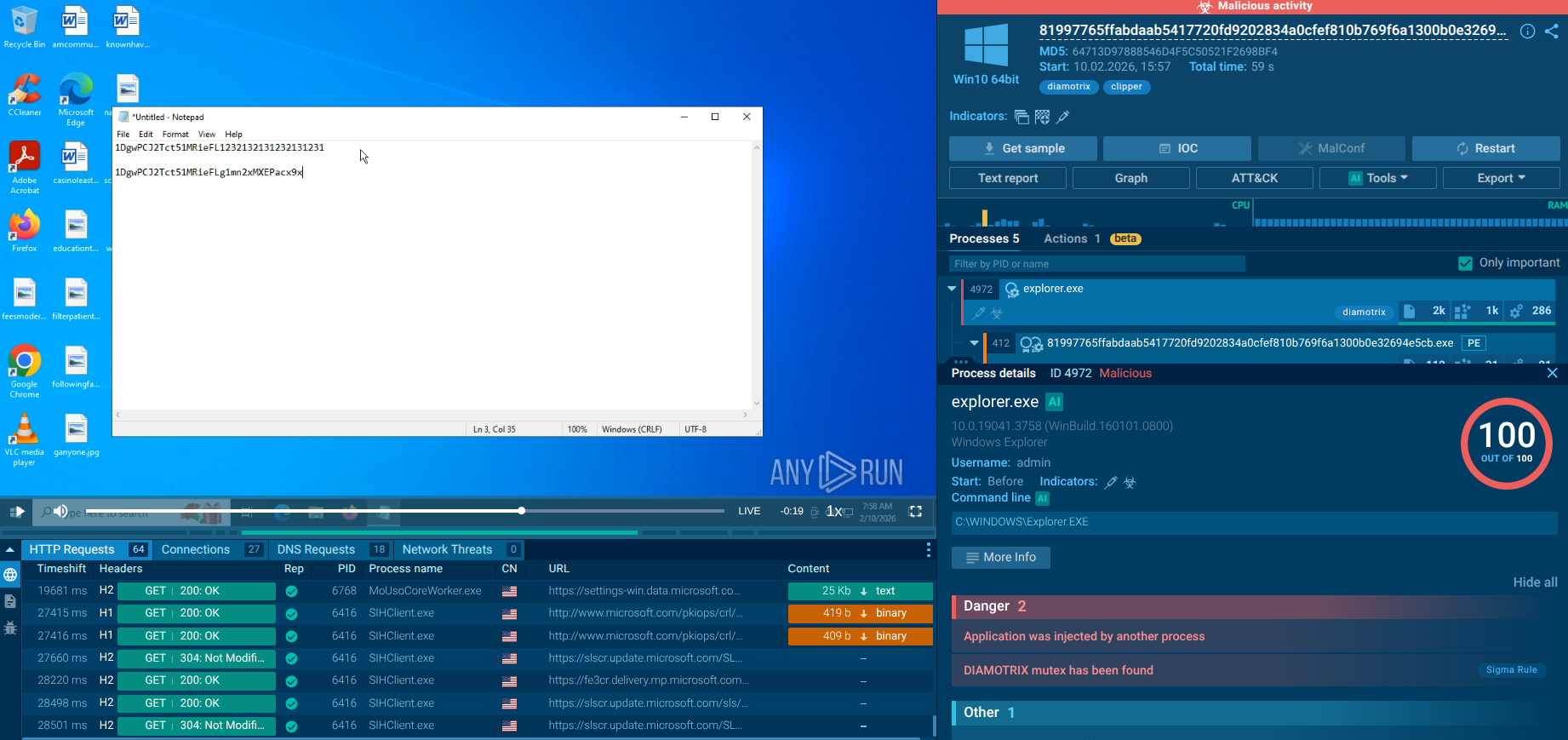 Diamotrix sample in the Interactive Sandbox
Diamotrix sample in the Interactive Sandbox
Upon launching the malicious file, Diamotrix injects its code into the legitimate system process explorer.exe.
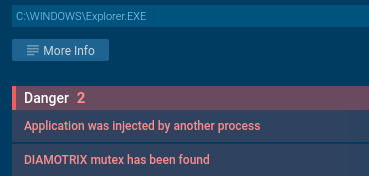 Diamotrix injected legal Windows process
Diamotrix injected legal Windows process
To ensure persistence, the malware creates its own copy named System.exe in the directory %AppData%\Roaming\2F33566DA0B91573532102, and then adds a corresponding entry to the registry's autorun section.
 Diamotrix secures persistence
Diamotrix secures persistence
The core functionality of Diamotrix as a crypto clipper is entirely based on monitoring and modifying the clipboard. The malware continuously tracks the clipboard contents in real time and, upon detecting a cryptocurrency wallet address, instantly replaces it with an address controlled by the attacker.
We can observe this behavior during an analysis due to the interactivity functions of ANY.RUN’s Sandbox. A legitimate Bitcoin address bc1qar0srrr7xfkvy5l643lydnw9re59gtzzwf5mdq was copied to the clipboard. Immediately afterward, Diamotrix substituted it with an attacker-controlled address. Repeated tests involving the copying of cryptocurrency addresses confirmed replacement in every case.
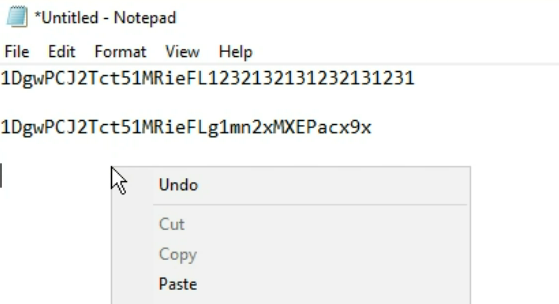 Diamotrix replaces Bitcoin address copied to the clipboard
Diamotrix replaces Bitcoin address copied to the clipboard
ANY.RUN's Threat Intelligence Lookup provides critical capabilities for detecting, investigating, and responding to Diamotrix threats:
Rapid IOC Validation and Enrichment
SOC analysts can query TI Lookup to instantly determine if an indicator is associated with known Diamotrix campaigns. The service provides contextual information including malware family classification, campaign attribution, and related artifacts - turning isolated indicators into actionable intelligence within seconds.
Deep Behavioral Analysis Access
TI Lookup gathers direct links to interactive sandbox sessions where Diamotrix was analyzed. Analysts can observe the complete execution chain. Start exploring with the threat name lookup:
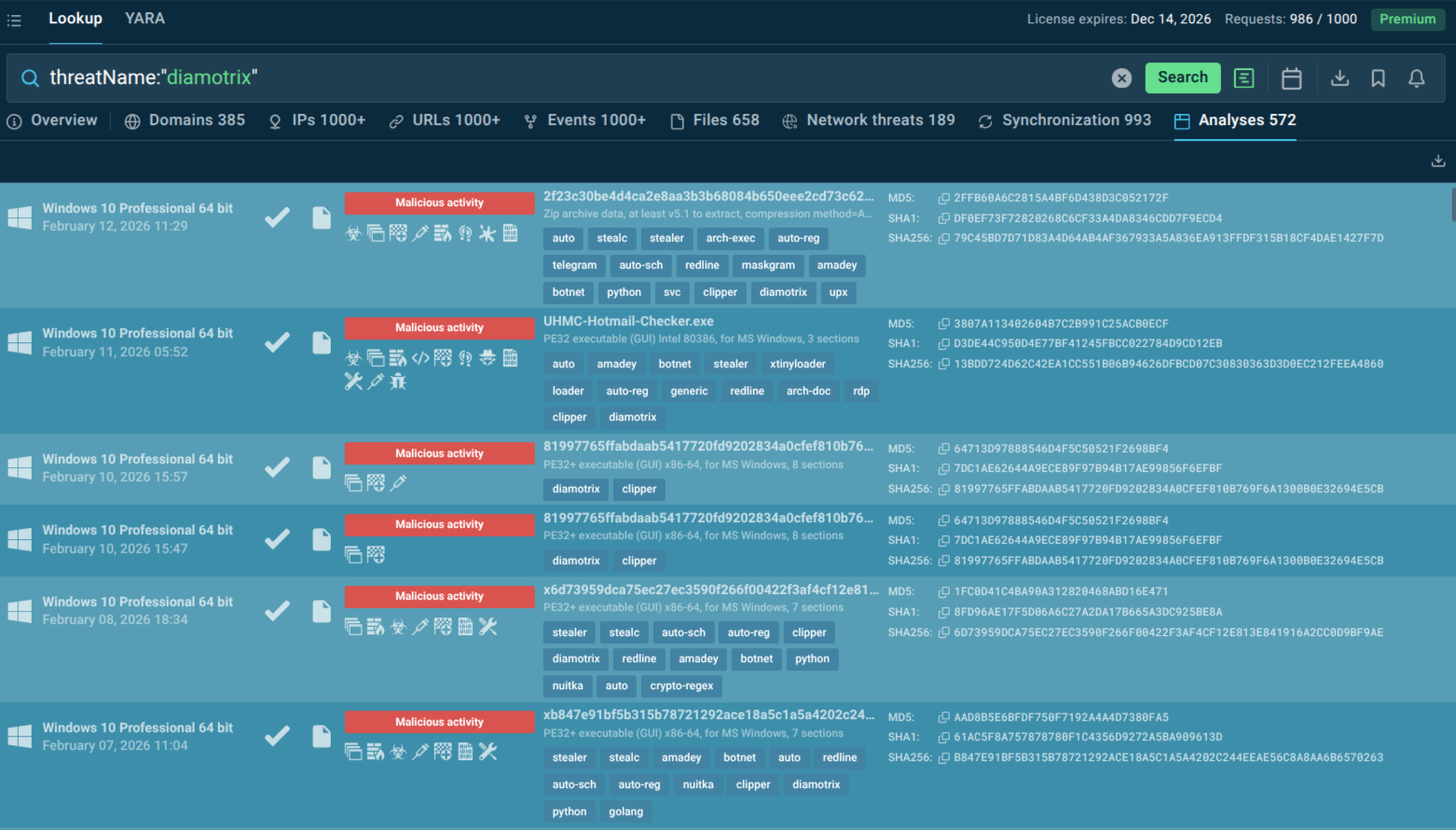 Fresh Diamotrix sandbox analyses found via TI Lookup
Fresh Diamotrix sandbox analyses found via TI Lookup
YARA Rule Development and Testing
TI Lookup's integrated YARA Search allows security teams to scan ANY.RUN's threat intelligence database with custom detection rules. Teams can develop YARA rules targeting Diamotrix unique characteristics like mutex names and immediately test them against millions of analyzed samples to validate effectiveness and minimize false positives.
Diamotrix represents a shift towards highly targeted, financially motivated cybercrime. By focusing on the simple act of "copy-paste," it exploits a moment of user trust to divert funds. Its distribution through sophisticated loader campaigns and its operation as a botnet make it a persistent threat. Defeating it requires a combination of user education, robust endpoint monitoring, and, most critically, access to real-time threat intelligence that can track its evolving infrastructure and behavioral patterns.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.