Malware is a complicated creature, it changes fast acquiring new features and adapting to any kind of environment. The main challenge for cybersecurity specialists is to keep updated and respond as quickly as possible. And our service can give you a hand with that.
ANY.RUN is a service that provides a large database full of various samples, fresh IOCs, and detailed reports. All malware hunters of ANY.RUN community can investigate and collect IOCs to improve the security of their own companies.
In this post, we will tell you about the top 3 of the most recent and interesting malware cases that were uploaded to ANY.RUN: advanced malicious programs, unusual tactics, and the best features to reveal the attacks for careful investigation.
All use cases are available for your research. Make sure to check them out, they are definitely worth your attention.
Malware case with geofence
Malware authors and distributors use different tricks to minimize malware detonation and subsequent detection on non-targeted machines. One of them is geofence. So, let’s analyze the sample with the geofence case.
Cybercriminals can target a particular country. And their malware campaigns neither detonate nor send the payload if the infected machine is from a non-targeted region. The country of origin is often determined by the locale or IP address of the infected machine.
Malicious documents from this task send a request to the Command & Control server but don’t receive anything back.
By looking at the Files tab we can make sure that no executable files are downloaded. The image used in the maldoc has text in Italian.
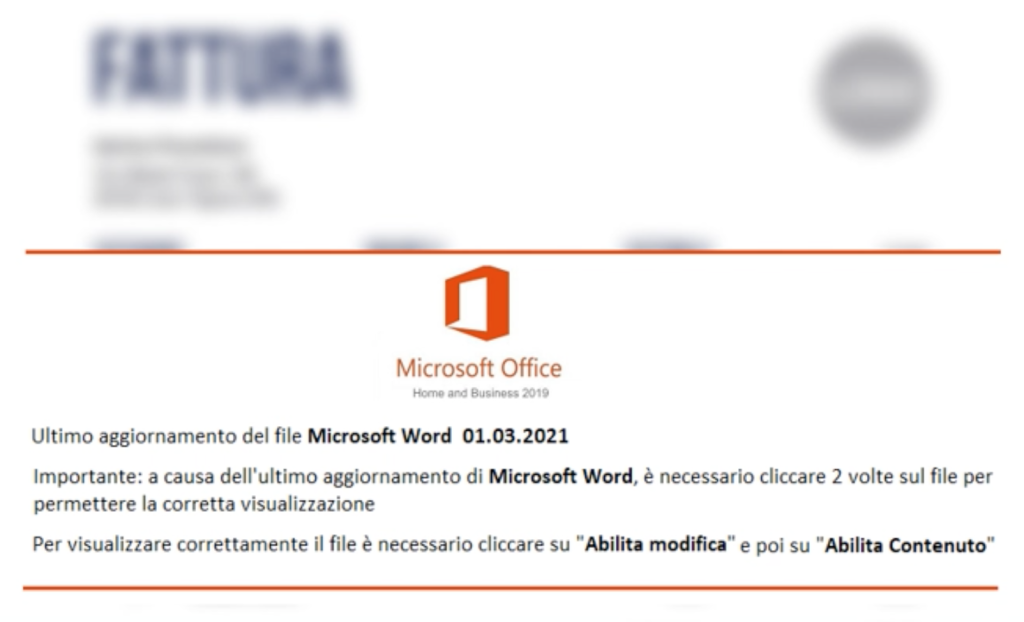
Let’ stop the task and restart it. But this time we reroute traffic using ANY.RUN’s Tor feature. Based on the language used in the picture in the malicious document, we can guess that it’s Italy.
As you may notice WINWORD.exe creates the child process Regsvr32.exe. It, in turn, should run the deli.png file.
And here it is – an executable file deli with a .png extension. A wrong extension’s goal is to mislead users and detection systems. The process stops file operations and now waits for some network activity to trigger its execution.
Let’s start a web browser and minimize the process tree. This indicator shows us that the process connects to the network.
A few moments later Internet Explorer is executed via COM and starts sending packets. Ursnif is detected! Its execution is triggered after it hooks the network’s API.
There are malware families that try to evade execution to avoid detection no matter what: a malicious document doesn’t receive the payload if it is opened on the system from a non-targeted county. Or an executable doesn’t run unless the network activity starts.
In all geofence use cases ANY.RUN functionality will help you conduct successful and full-fledged analysis!
Malware case with bitness change
Analysts do their best to trigger malware and make it active. There are several ways to do it and today we will talk about changing configurations of the virtual machine (VM). The example with the bitness of the operating system is on the focus.
In this task, you can see DocuSign-themed malicious documents which were previously used to deliver Qbot and Icedid. This time it delivers Trickbot.
Currently, this malware is working well only in 64-bit systems. So, we need to get our VM set for this task. Thankfully, changing the bitness is not an issue: you need neither installing nor downloading any additional equipment. With ANY.RUN’s helpful feature choose the required system before starting a task and start your analysis in a minute.
The execution flow of the Trickbot in this task remains the same as usual. But there are a couple of updates: rundll32.exe process triggering wermgr.exe – there is now additional host discovery activity including ipconfig various net commands and nltest checking for domain trusts.
By clicking on the Files tab we can see which modules Trickbot dropped during the task. In our case module shareDll64 for lateral movement & propagation, pwgrab64 credential stealer, and module networkDll64 for network recon was dropped.
We put together malicious documents in clusters based on their similarity and template appearance. DocuSign-themed maldocs united under the maldoc-42 tag. By looking at tasks under the maldoc cluster, analysts can collect additional IOCs, track updates of the execution chain and find fresh binary samples.
Maldoc clusters also may help you to do retro perspective analysis. For example, you come across a new maldoc but C2 is already off and the payload isn’t delivered. By filtering tasks by maldoc cluster analysts can take a look back in time and find a task in which payload was delivered to the infected system. ANY.RUN database can come in handy, you’ll find the sample you need, for sure.
Malware case with fast detection
If an attack happens, malware analytics have to respond as quickly as possible. Time is what matters the most here. And the first step to improve security is to identify the malware fast.
Here is a task with fast detection and analysis. The Excel document from this sample contains a malicious program. And it takes 28 seconds for ANY.RUN to detect a Formbook.
Even by looking at the process tree, you can say that Formbook is in front of you without waiting for tags. Malicious payload injects itself in system processes from the hardcoded list and then spawns the child cmd.exe process which deletes the initial payload.
After that trojan injects into the Explorer.exe process and starts its malicious activity. In this case, Formbook is detected by Suricata IDS rules, but it is also often detected by created files. And it’s helpful that the whole analysis takes less than a minute.
Cunning malware creators are never standing still and do their best to evade execution by non-target users and avoid detection of malware. ANY.RUN service always tries to be aware of new tweaks and provides the needed features for detecting crooks’ schemes.







0 comments