Security teams don’t lack alerts, they lack fast, reliable context for decision-making. When threat analysis and intelligence are not an integrated part of the SOC workflow, investigations slow down, MTTR grows, and the risk of missed incidents increases. Adding behavioral analysis and live intelligence directly into SIEM closes this gap, turning monitoring, triage, and response into faster, higher-ROI processes.
That’s exactly how ANY.RUN‘s integration with Splunk Enterprise brings value to security teams.
ANY.RUN & Splunk Enterprise: About the Integration
The ANY.RUN integration embeds behavioral analysis and live threat intelligence directly into Splunk Enterprise as native data sources.
Integrate ANY.RUN in your Splunk environment now →
Instead of exporting reports or attaching external files, analysis results and intelligence data are ingested as structured Splunk events. This allows them to be searched, correlated, visualized, and used in alerts and dashboards using standard SIEM mechanisms.
The integration helps SOC teams:
- Boost triage quality of suspicious URLs with sandbox analysis: Behavioral verdicts inside Splunk help analysts make faster, evidence-based decisions, reducing MTTR and lowering the risk of missed threats.
- Accelerate alert validation with context enrichment: Instant IOC context speeds up prioritization, shortens investigation time per alert, and reduces operational overhead.
- Expand threat coverage with actionable intel: Fresh, verified malicious IPs, domains, and URLs strengthen correlation rules, improve MTTD, and reduce blind spots in detection.
- Improve SOC reporting & visibility: Dashboards built on sandbox submissions, verdict trends, enriched indicators, and campaign tags help SOC managers monitor workload, track investigation efficiency, and measure detection performance over time.
- Meet SLAs and KPIs: For MSSP teams, the integration helps fix triage and response inefficiencies, manage a larger load of alerts without scaling the team, and deliver consistent results to more clients.
All components are designed to work inside existing SOC workflows. No separate consoles, no manual data transfer, no parallel processes.
As a result, malware analysis and threat enrichment become part of detection logic and investigation pipelines, not side tasks handled outside the SIEM.
ANY.RUN Sandbox: Improve Triage, Detect More Phishing Attacks
The ANY.RUN Interactive Sandbox integration allows security teams to submit suspicious URLs directly from Splunk for analysis and receive structured results as native Splunk events.
Returned data includes verdict, risk score, extracted indicators, and a direct link to the full analysis session for deeper investigation. These results can immediately participate in correlation searches, alerts, dashboards, and response workflows inside the SIEM.
- Faster MTTR: Sandbox verdicts appear directly in Splunk, helping teams move from alert to containment faster.
- Higher detection rate of evasive attacks: Full behavioral execution increases the chance of catching threats that static checks miss.
- More cases closed by Tier 1 analysts: Clear, evidence-based verdicts allow junior analysts to confidently resolve more alerts without waiting for higher tiers.
- Lower false negative rate: Behavioral analysis reduces the risk of incorrectly closing alerts that later turn into confirmed incidents.
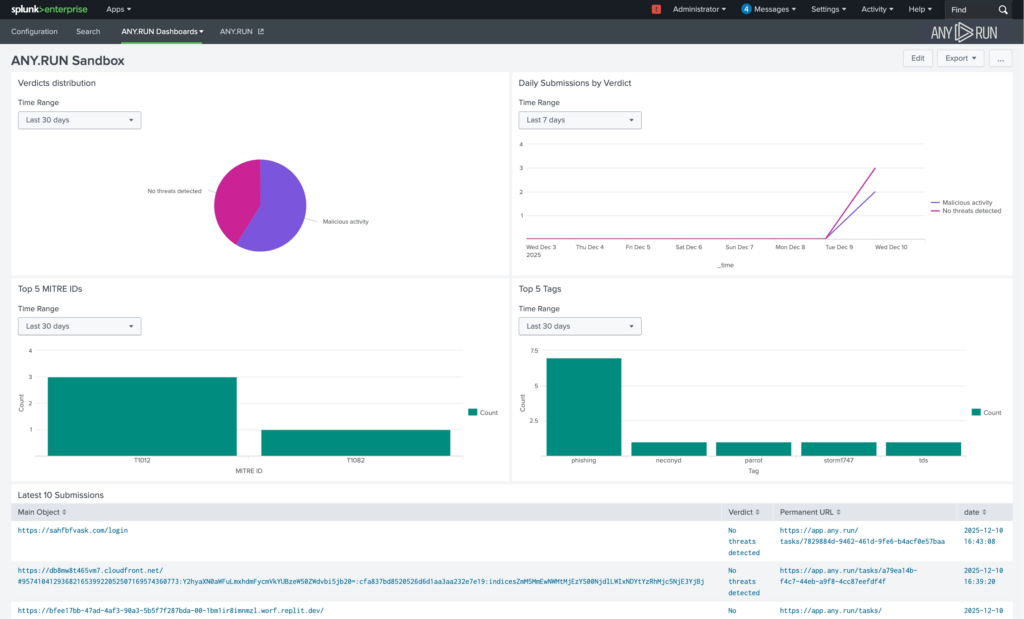
These improvements translate into lower investigation costs, fewer missed incidents, and more predictable incident response performance, with a 21-minute reduction in MTTR per case.
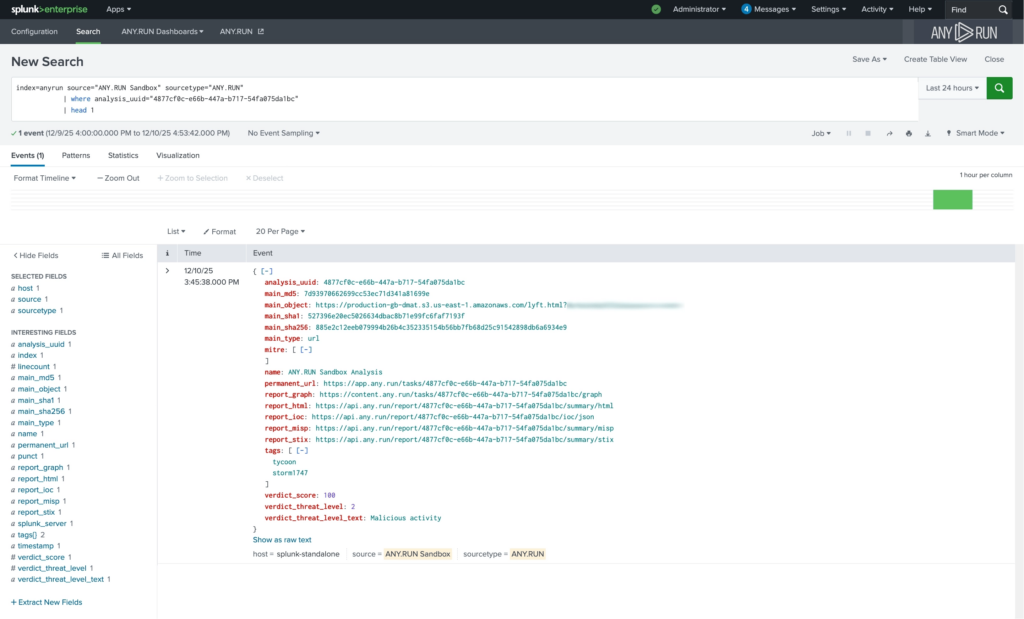
Practical Use Case: URL Analysis from SIEM Events
When a suspicious URL appears in a Splunk event, analysts can submit it directly to the ANY.RUN Sandbox. The analysis verdict returns as a native Splunk event and immediately participates in correlation, investigation, and response workflows.
ANY.RUN TI Lookup: Identify and Prioritize Critical Risks Faster
The ANY.RUN Threat Intelligence Lookup integration enables on-demand enrichment of IPs, domains, URLs, and file hashes directly inside Splunk. The intelligence is sourced from millions of malware & phishing investigations done manually by 15,000+ SOC teams and 600,000+ analysts inside ANY.RUN’s Interactive Sandbox.
Enrichment results are returned as structured Splunk events, including verdict, industry targeting, last seen data, tags, and a direct link to detailed intelligence in the ANY.RUN interface. This data can be searched, correlated, visualized, and incorporated into alerting logic using native SIEM capabilities.
- Faster triage decisions: Near-instant access to past analyses confirms whether an IOC is linked to real malicious activity, significantly reducing triage time.
- Smarter response actions: Behavioral context and mapped TTPs help teams choose more precise containment steps instead of reacting blindly.
- Fewer Tier 2 escalations: Tier 1 analysts receive enough context to make confident decisions independently, reducing internal bottlenecks.
- Stronger detection logic: Enrichment data becomes searchable and reusable in correlation rules, improving detection accuracy without adding new tools.
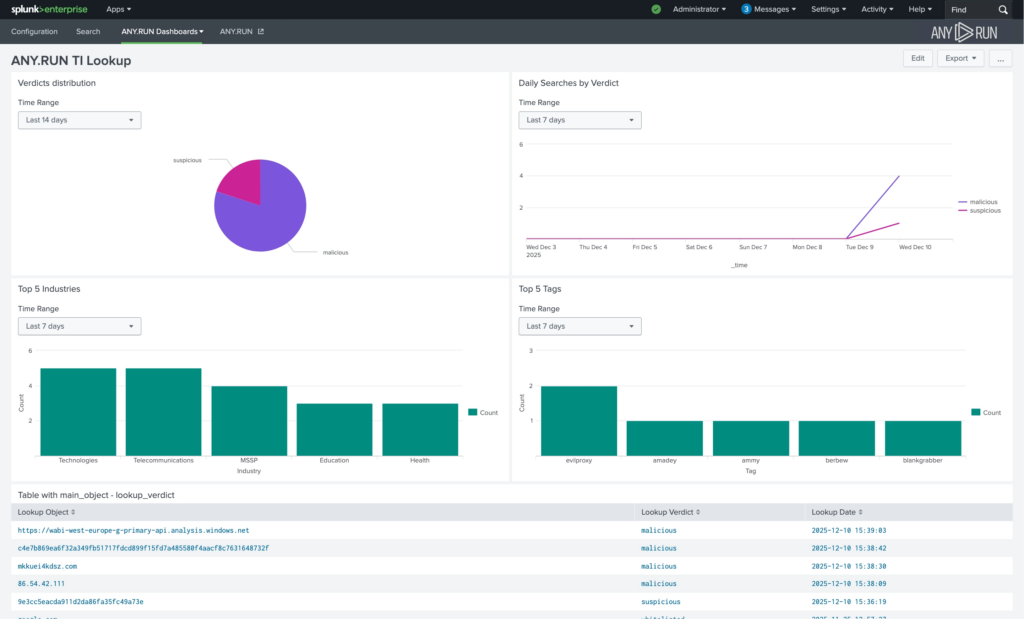
As a result, teams improve SLA adherence, reduce average investigation time per alert, and strengthen detection accuracy with 58% more threats identified overall.
This leads to faster response, better use of existing security investments, and lower exposure to sector-specific attacks.
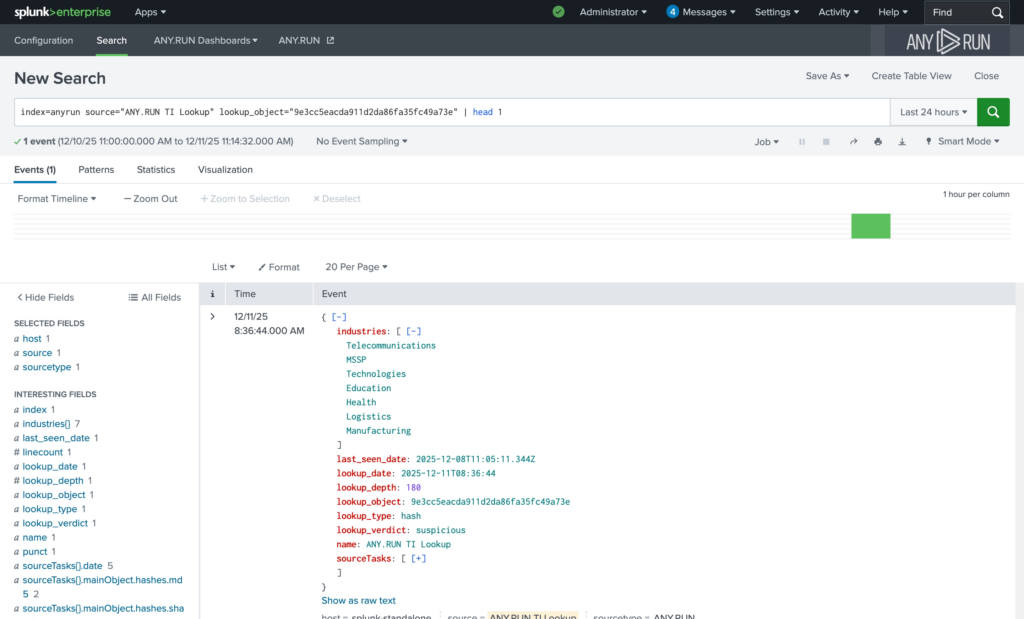
Practical Use Case: IOC Enrichment During Investigation
While reviewing an incident, analysts can enrich IPs, domains, URLs, or file hashes using TI Lookup. The contextual result is stored as a Splunk event, reducing manual research and accelerating decision-making.
ANY.RUN TI Feeds: Strengthen Defense Against Emerging Threats
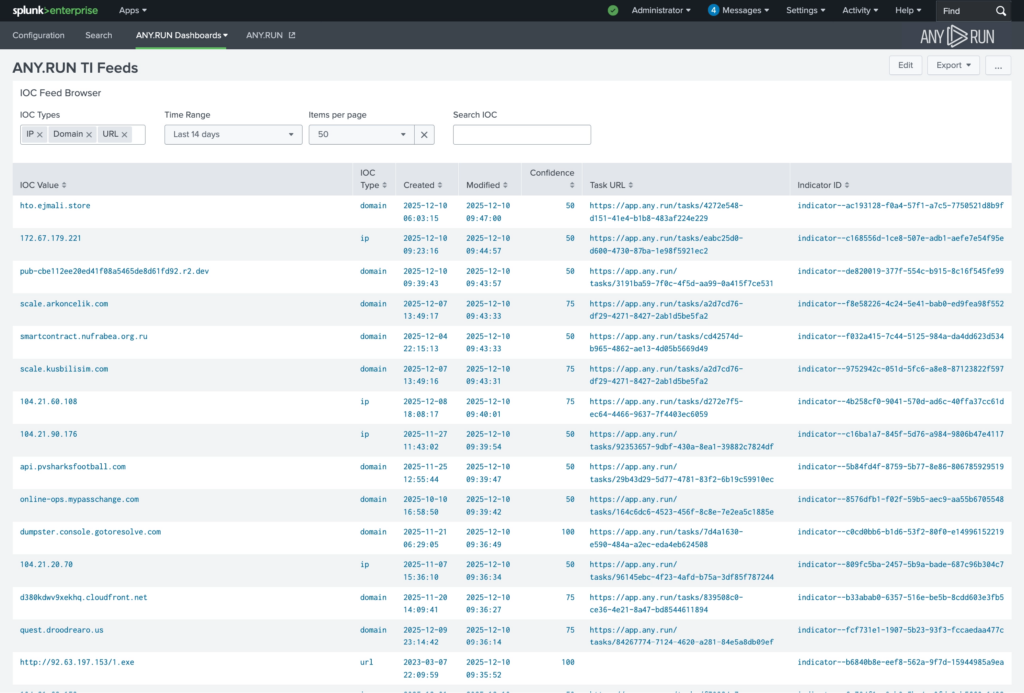
The ANY.RUN Threat Intelligence Feeds integration continuously streams verified malicious network indicators (IPs, domains, URLs) into Splunk, sourced from live sandbox analyses of real-world attacks across 15,000+ organizations.
Indicators delivered via ANY.RUN TI Feeds are stored in Splunk’s Key-Value Store (KV Store), making them searchable, filterable, and immediately usable in correlation rules, dashboards, and alerting workflows.
TI Feeds contain 99% unique malicious infrastructure not present in other intelligence sources.
- Earlier detection of emerging threats: Indicators are added to feeds as soon as they appear in live sandbox investigations, helping SOC teams identify new campaigns faster and reduce MTTD.
- Wider threat coverage: A high share of globally observed, unique malicious infrastructure improves visibility into phishing and malware activity that traditional feeds often miss.
- Reduced Tier 1 workload: Indicators are filtered for malicious activity, decreasing false positives and cutting investigation time spent on low-value alerts.
- Detection that scales automatically: Continuous feed updates strengthen correlation rules over time without requiring manual tuning or additional staffing.
This improves MTTD, reduces false positive rates, and increases detection rate by 36% on average.
For the business, that means lower breach probability, reduced operational disruption, and better return on existing SIEM investments as the environment grows.
Practical Use Case: Threat Correlation with Fresh IOCs
ANY.RUN’s TI Feeds continuously supply verified malicious infrastructure into Splunk. Detection rules can automatically correlate incoming events against fresh indicators, increasing detection accuracy and reducing blind spots.
How to Integrate ANY.RUN in Splunk Enterprise
The ANY.RUN integrations are available for installation via Splunkbase. Security teams can find and deploy the add-ons directly from the Splunk app marketplace by searching for “ANY.RUN,” enabling fast deployment without complex configuration or custom development.
Conclusion
By embedding sandbox analysis, live enrichment, and verified malicious infrastructure directly into Splunk, ANY.RUN helps SOC teams triage faster, prioritize more accurately, and improve detection logic. The result is lower MTTR, fewer missed incidents, and stronger protection without increasing operational complexity.
About ANY.RUN
Trusted by 600,000+ cybersecurity professionals and 15,000+ organizations across critical industries, including 64% of Fortune 500 companies, ANY.RUN helps security teams detect and investigate threats faster.
Our Interactive Sandbox provides real-time behavioral analysis of suspicious files and URLs, enabling confident triage and response.
Threat Intelligence Lookup and Threat Intelligence Feeds deliver live, verified threat data that strengthens detection and improves prioritization.
By embedding analysis and intelligence into daily SOC workflows, ANY.RUN helps organizations reduce response time, lower operational costs, and minimize security risk.
Request access to ANY.RUN’s solutions for your team →
FAQ
By embedding behavioral analysis and live threat intelligence directly into Splunk, threats are understood earlier in the attack chain. Earlier understanding leads to faster containment, lower incident impact, and reduced probability of breach-related downtime, fraud, or regulatory exposure.
SOC teams typically see reduced MTTR (up to 21 minutes per case), improved detection rate (up to 36%), and identification of up to 58% more threats through enriched intelligence. These improvements translate into fewer escalations, fewer missed incidents, and more predictable response performance.
The integration enables Tier 1 analysts to close more alerts independently by providing behavioral verdicts and context directly in Splunk. This reduces escalation rates, prevents backlog growth during alert spikes, and helps manage higher alert volumes without increasing headcount.
No architectural overhaul is required. ANY.RUN integrates as native data sources inside Splunk Enterprise. Analysis results and intelligence are ingested as structured events and used within existing dashboards, correlation rules, and response workflows.
Faster alert validation and clearer risk prioritization reduce investigation time per case. This stabilizes response timelines, improves MTTR consistency, and allows MSSPs to support more clients without degrading service quality.



0 comments