Security teams don’t lack data. They lack timely, usable intelligence. Analysts spend too much time validating indicators, switching between tools, and figuring out what actually matters. This introduces delays and puts organizations at risk of a missed incident.
ANY.RUN solves this by bringing real-time, behavior-validated threat intelligence from ANY.RUN integrated into Elastic Security, where SOC and MSSP teams detect emerging cyberattacks earlier and respond faster without changing their workflows.
ANY.RUN Threat Intelligence Feeds x Elastic Security: About the Integration
Integrate ANY.RUN’s TI Feeds in Elastic Security →
Elastic Security unifies SIEM, endpoint security, and cloud security to help teams protect, investigate, and respond to threats.
Through the ANY.RUN Threat Intelligence Feeds integration, organizations can ingest third-party threat indicators into Elastic Security and use them in detection, investigation, and threat intelligence workflows. This helps analysts bring external threat context into the same platform they use for security operations.
ANY.RUN’s Threat Intelligence Feeds are built from live sandbox investigations across more than 15,000 organizations and 600,000 SOC professionals. Indicators reflect infrastructure actively used in phishing, malware delivery, and attacker campaigns, not delayed or aggregated data. Each IOC includes context and a direct link to the sandbox report, allowing analysts to quickly understand threat behavior and TTPs.
The integration is available as a plug-and-play solution that only requires an active TI Feeds license (via trial or a paid subscription).
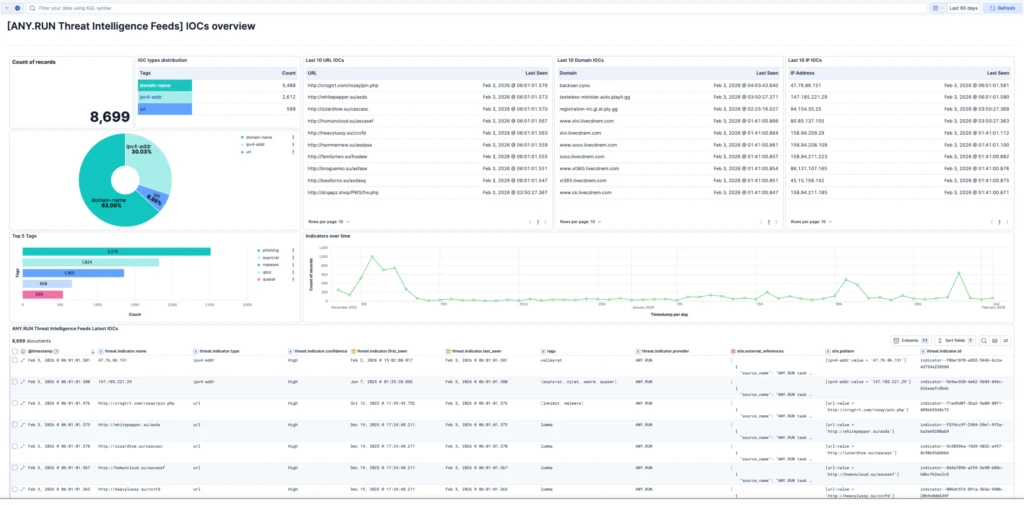
Once configured, Elastic Security can ingest indicators such as IPs, domains, and URLs from the integration on a scheduled basis. Those indicators can then be used across supported detection, investigation, and visualization workflows.
The additional context associated with ingested indicators can help analysts triage and investigate alerts more efficiently.
How Threat Intelligence Feeds Improve Detection and Shorten MTTR in Elastic Security
The integration embeds threat intelligence directly into daily SOC workflows inside Elastic Security. Analysts don’t need to manually check indicators in external tools or move data between systems.
Here is what your team gains:
- Detect threats early: Use fresh indicators from live attacks to identify malicious activity sooner.
- Validate alerts with real context: Use sandbox-backed evidence instead of relying only on static indicators.
- Reduce manual work: Eliminate repetitive enrichment steps and tool switching.
- Improve detection quality: Use high-confidence indicators directly in rules and correlation logic.
- Speed up triage and response: Access context instantly and make faster decisions.
Together, these improvements help reduce MTTD and MTTR, lower incident response costs, and increase analyst efficiency by enabling teams to handle more cases without expanding headcount.
Better detection coverage and earlier visibility into active threats contribute to overall business risk reduction by limiting the impact and spread of attacks.
How to Set Up ANY.RUN’s Threat Intelligence Feeds in Elastic Security
The integration is designed to be simple and flexible. Once you get an active TI Feeds access, you can navigate to the integration page and follow the instructions.
Indicators are automatically ingested into Elastic and continuously updated. They become part of detection, search, and response workflows.
With ANY.RUN Threat Intelligence Feeds in Elastic Security, teams can:
- Use ingested ANY.RUN indicators in Elastic Security detection workflows
- Match threat indicators against relevant security telemetry
- Support triage and investigation with additional indicator context
- Build dashboards and visualizations for threat intelligence monitoring
- Incorporate third-party indicators into detection and hunting workflows
Conclusion
With ANY.RUN Threat Intelligence Feeds integrated into Elastic’s Security platform can further enhance customer’s security detection with timely, behavior-validated intelligence., Organizations can detect threats early, reduce manual effort, and make fast, confident decisions.
This leads not only to better SOC performance, but also to measurable business impact. Early detection, fast response, and improved signal quality help reduce the likelihood and impact of incidents, ultimately lowering overall business risk.
About ANY.RUN
ANY.RUN helps security teams understand threats faster and take action with confidence. Its solutions are trusted by over 600,000 security professionals and more than 15,000 organizations across industries where speed and accuracy are critical for effective response.
ANY.RUN’s Interactive Sandbox allows teams to safely analyze suspicious files and URLs, observe real behavior in real time, and confirm threats before they spread.
Combined with Threat Intelligence Lookup and Threat Intelligence Feeds, it provides the context needed to prioritize alerts, reduce uncertainty, and stop advanced attacks earlier in the response cycle.




0 comments