CISOs are under pressure to prove that their security programs can detect threats early, reduce business risk, and support fast, confident response. But that becomes harder when attackers stop relying on obviously malicious tools.
In recent phishing-to-RMM campaigns observed by ANY.RUN analysts, threat actors are using fake Microsoft, Adobe, and OneDrive pages to deliver legitimate remote management tools instead of traditional malware. Once installed, these tools can give attackers remote access to a victim’s device while blending into software categories many enterprises already use or allow.
For security leaders, this creates a difficult visibility problem. The payload may be legitimate. The infrastructure may be trusted. The user action may look like a routine download. Yet the outcome is the same: unauthorized remote access inside the environment.
Key Takeaways
- Phishing-to-RMM attacks create a dangerous visibility gap for enterprise SOCs: Attackers can deliver legitimate remote management tools through phishing pages that impersonate trusted services like Microsoft, Adobe, and OneDrive.
- The payload may not look malicious on its own: Tools such as ScreenConnect and LogMeIn Rescue can appear as legitimate remote administration software, especially in organizations where RMM usage is already allowed.
- Domain reputation is not enough: These attacks may use legitimate platforms, vendor infrastructure, or compromised websites instead of obvious newly registered domains.
- The real signal is in the full attack chain: SOC teams need to connect the phishing lure, download context, execution behavior, RMM installation, and outbound connections.
- For CISOs, the risk is operational as much as technical: Missed phishing-to-RMM activity can lead to slower detection, longer attacker dwell time, delayed containment, and weaker confidence in approved remote access tools.
- ANY.RUN helps turn gray-zone activity into evidence: With Interactive Sandbox and Threat Intelligence, teams can safely analyze suspicious URLs and files, trace RMM behavior, and investigate related phishing-to-RMM chains.
The Blind Spot: When “Allowed” Tools Become the Attack Path
Most enterprise security programs are built to separate malicious activity from normal operations. Phishing-to-RMM attacks blur that line.
An RMM installer can pass basic checks because it is not malware by design. But the risk is not in the tool alone. It is in the context around it: how it reached the user, whether the download was expected, which endpoint launched it, and what connection followed.
For CISOs, this is where the risk becomes critical. Unauthorized access can hide inside routine-looking activity, giving the business a false sense of control while the attacker is already inside.
The outcome can be serious:
- Slower detection because the activity does not look like classic malware
- Longer attacker dwell time inside the environment
- Higher risk of lateral movement from the compromised endpoint
- More pressure on SOC teams to investigate ambiguous alerts
- Delayed containment because the initial access path is harder to prove
- Weaker confidence in whether approved remote access tools are being used safely
Which Organizations are Most Exposed
ANY.RUN data shows that phishing-to-RMM activity is primarily concentrated in the United States, followed by Canada, Europe, and Australia. The most affected industries include Education, Technology, Banking, Government, Manufacturing, and Finance.
These sectors often depend on remote administration for IT support, distributed workforce management, and endpoint maintenance. That reliance creates more room for abuse: when RMM tools are already part of normal operations, unauthorized access can take longer to recognize and contain.
How Legitimate RMM Tools Are Delivered Through Phishing
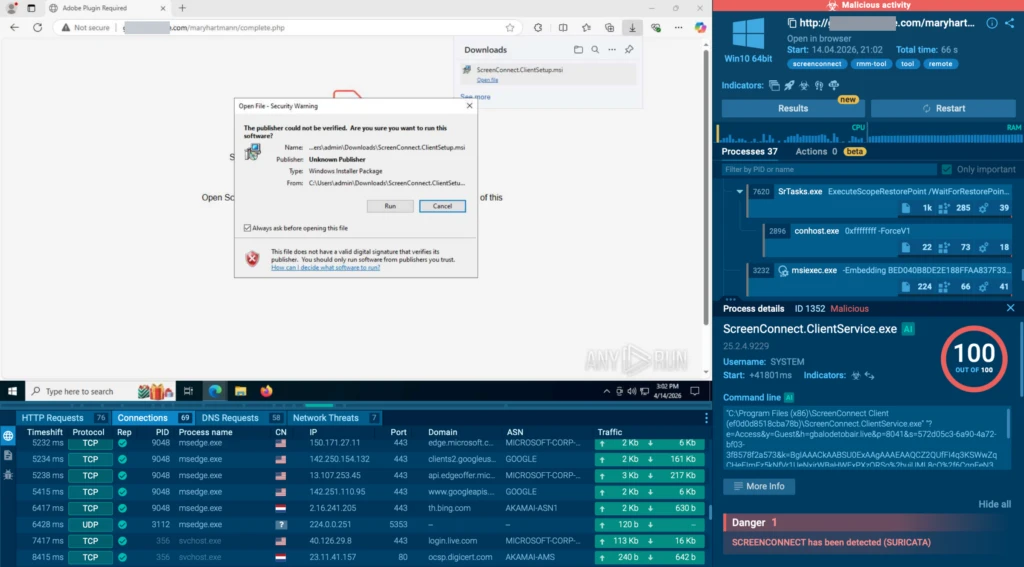
Since early April, the ANY.RUN team has observed a rise in phishing-to-RMM attacks, where threat actors use phishing to deliver legitimate remote management tools and gain remote access to victims’ devices.
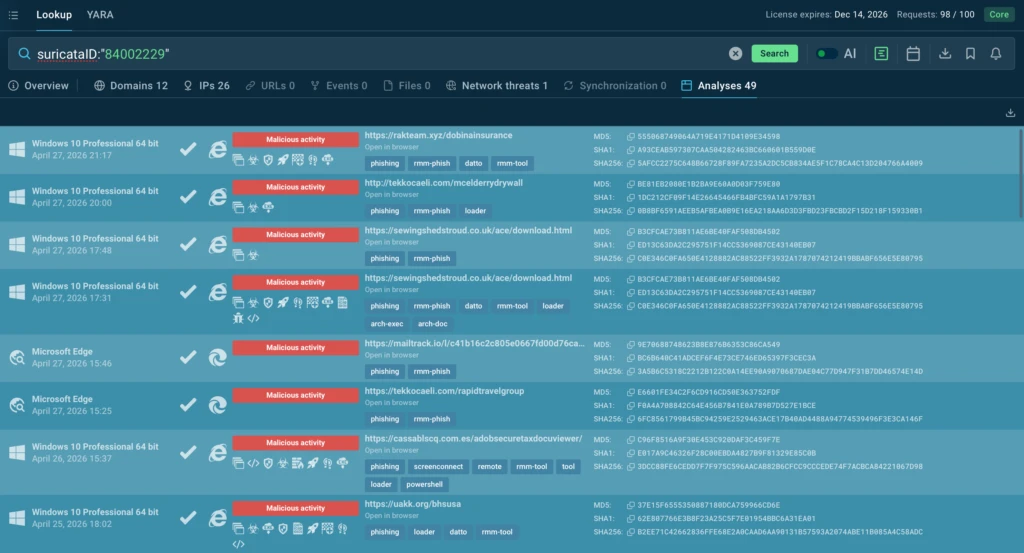
For just one of these campaigns, we are seeing more than 50 public analyses in ANY.RUN every week: suricataID:”84002229″
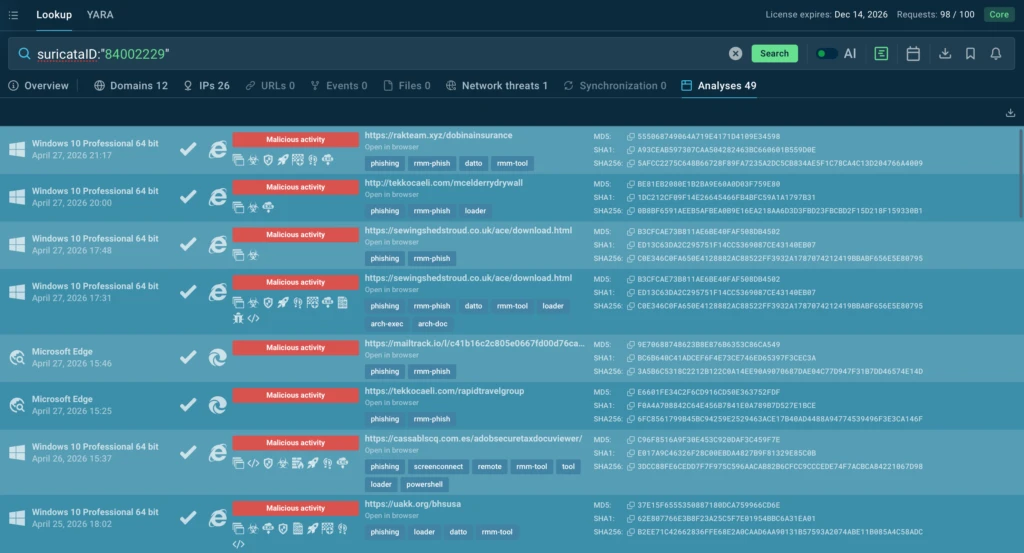
Phishing campaigns that deliver RMM tools are especially dangerous for SOC teams because these tools can appear to be legitimate remote administration software. If an organization already uses or allows RMM solutions, the launch of ScreenConnect may not immediately trigger security policies.
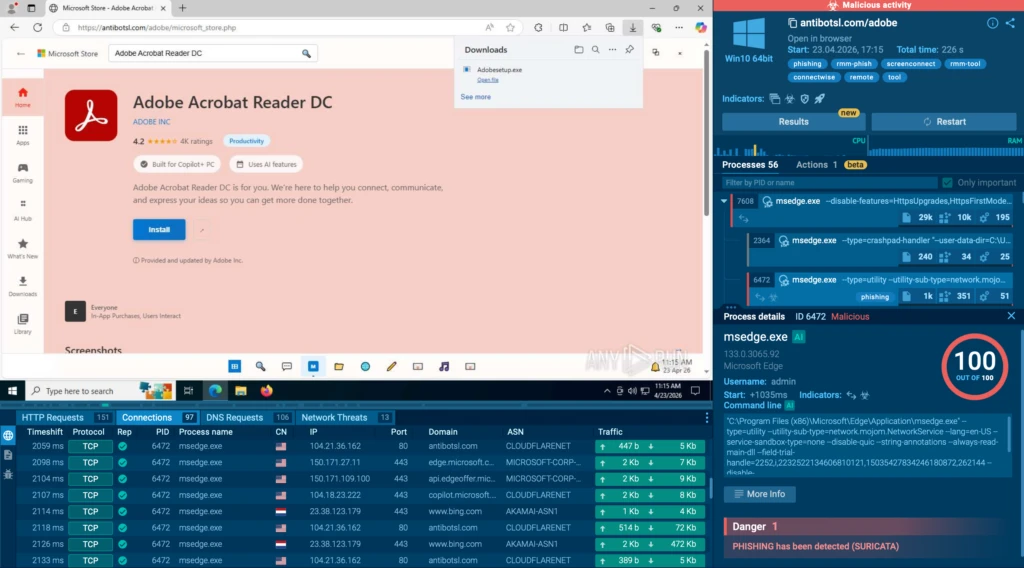
The screenshot below shows a phishing page impersonating Microsoft Store and Adobe Acrobat Reader DC. The user is prompted to download Adobesetup.exe, but behind that name is ScreenConnect; an RMM tool that attackers can use to establish remote access to the system.
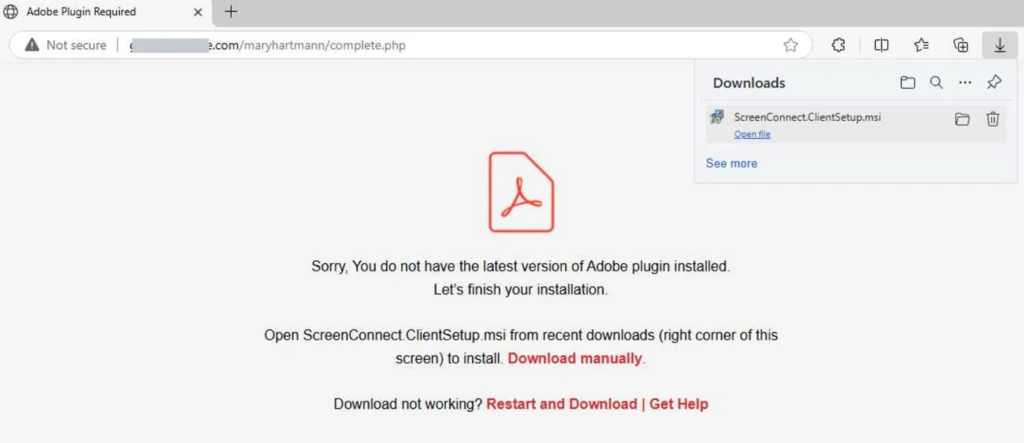
Another example shows the attack disguised as a protected Microsoft OneDrive download. The page at vmail.app.n8n.cloud displays a “Verify to Download” prompt for what appears to be a PDF document. Once the user clicks, they receive ScreenConnect.ClientSetup.exe:
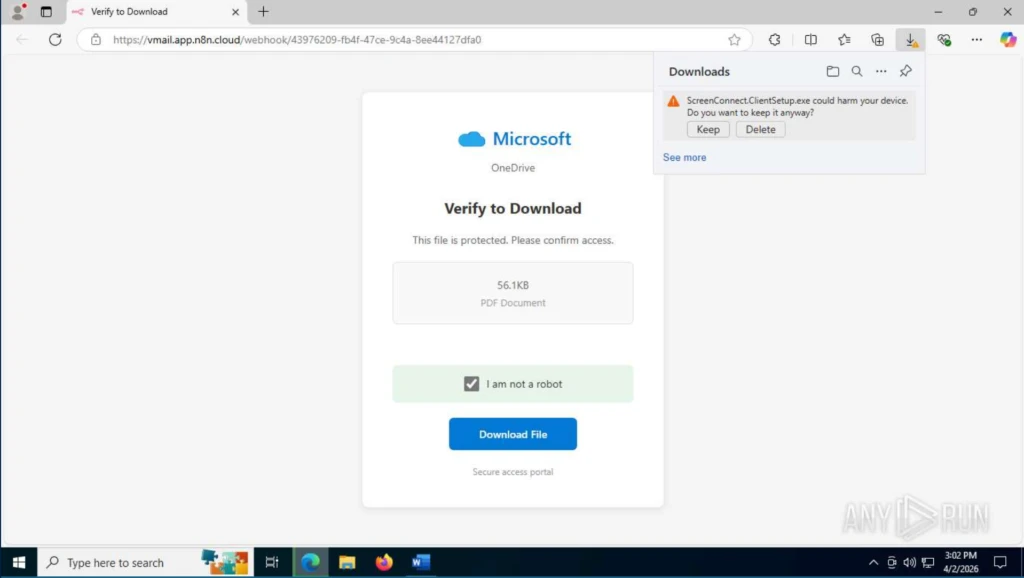
This chain makes SOC triage more difficult: the phishing landing page is hosted on the legitimate n8n.cloud platform, while the RMM agent download and subsequent connection occur through legitimate ScreenConnect infrastructure.
The attack does not rely on obvious newly registered domains, which are often an easy signal for blocking. As a result, detection needs to be based on behavior, download context, and anomalies around RMM execution, not domain reputation alone.

In addition to ScreenConnect, threat actors use other legitimate RMM and remote-access tools in these phishing chains, including Datto RMM, ITarian, LogMeIn Rescue, Action1 RMM, NetSupport, Syncro, MeshAgent, SimpleHelp, RustDesk, and Splashtop.
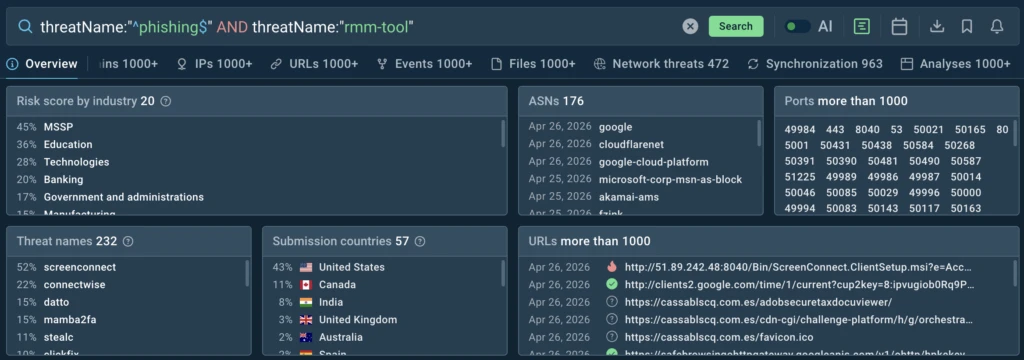
To retrospectively track similar chains in ANY.RUN Threat Intelligence, teams can use the following query. As part of TI Lookup, every user has access to 20 full queries:
threatName:”^phishing$” and threatName:”rmm-tool”
In addition to standard installers, threat actors are also using more sophisticated delivery methods, as shown in this public analysis:
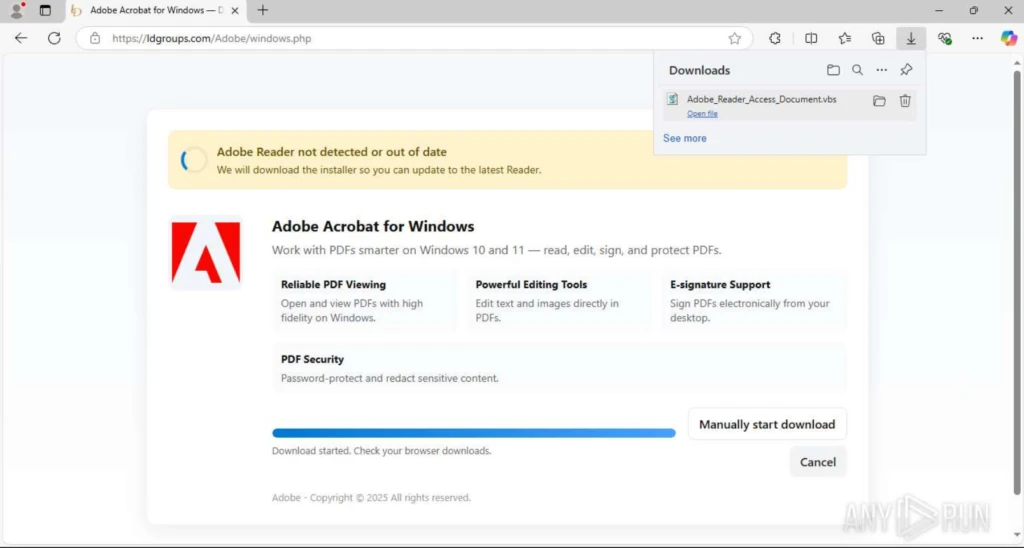
In this example, the user is shown a phishing page with an Adobe document download lure. Instead of the expected file, the page delivers a VBS script.
Once executed, the script attempts to elevate privileges through UAC, disable SmartScreen, and weaken Microsoft Defender protections. It then silently downloads the LogMeIn Rescue installer, removes the Mark-of-the-Web, and runs a quiet installation via msiexec, turning the endpoint into a system with unattended RMM access.
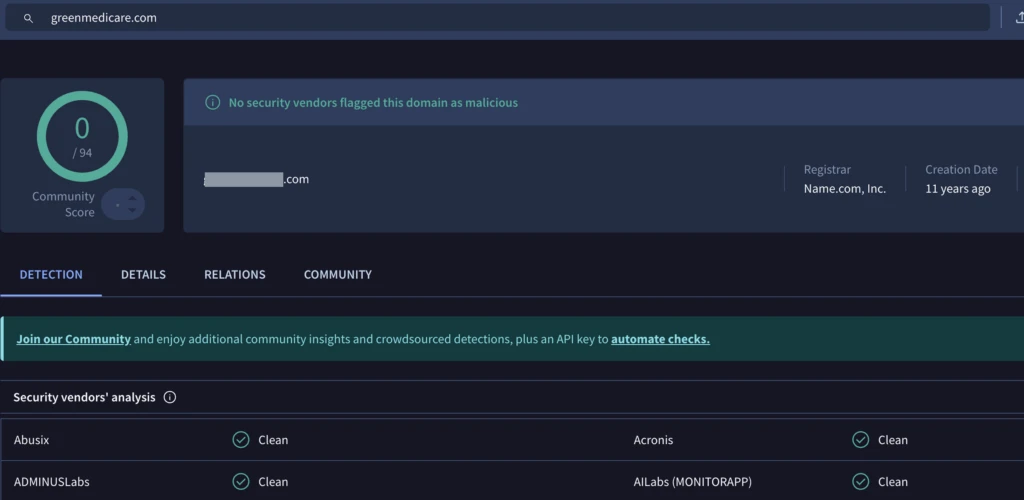
It is also worth noting that in campaigns like this, threat actors try to minimize easily blocked, lower-level IoCs from the Pyramid of Pain, such as newly registered domains.
Instead, phishing pages may be hosted on already existing websites. The domain itself appears legitimate, while the suspicious activity is hidden deeper in the URL — in an unusual URI path that may indicate SEO injection or a compromised website.
At the time of analysis, VirusTotal showed that no vendor had flagged this domain as malicious:
Taken together, these cases reflect a broader shift from malware-first initial access to phishing-first initial access. Threat actors are increasingly gaining access not through an obviously malicious payload, but through social engineering and legitimate remote administration tools.
How SOC Teams Can Close the RMM Visibility Gap
Phishing-to-RMM attacks cannot be handled like ordinary malware delivery. The payload may be legitimate, the infrastructure may be trusted, and the domain may not have a malicious reputation at the time of analysis.
To detect this activity earlier, SOC teams need visibility into the full attack chain, not just the final file. That means connecting:
- the phishing page that initiated the download
- the file or script delivered to the user
- the execution path on the endpoint
- attempts to weaken security controls
- RMM installation behavior
- outbound connections to remote access infrastructure
This is where ANY.RUN helps teams close the gap. With the Interactive Sandbox, security teams can safely examine suspicious URLs, files, and scripts during triage.
They can observe the phishing lure, delivered payload, execution flow, attempts to weaken security controls, RMM installation, and outbound connections in one controlled environment.
ANY.RUN Threat Intelligence adds the retrospective layer. Teams can search across public analyses, track phishing-to-RMM chains, pivot from one indicator to related activity, and understand whether a single event is part of a wider campaign.
For CISOs, this means more control over a risk that is usually hard to prove. The SOC can validate suspicious remote access activity faster, show how the access path started, and give leadership clearer evidence for containment and follow-up decisions.
Instead of relying on reputation-based signals or waiting for a high-confidence malware alert, security teams can prove when trusted tools are being abused. That gives CISOs stronger confidence in detection coverage, faster response readiness, and better visibility into whether approved remote access software is creating hidden business risk.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams detect, investigate, and respond to threats faster.
ANY.RUN solutions include Interactive Sandbox, Threat Intelligence Lookup, Threat Intelligence Feeds, and integrations for SOC workflows across SIEM, SOAR, EDR, and other security tools. Together, they help teams analyze suspicious files and URLs, uncover attacker behavior, enrich investigations with real-world threat context, and operationalize intelligence across their environment.
Built for security-conscious organizations, ANY.RUN is SOC 2 Type II attested and supports enterprise-ready controls such as SSO, MFA, granular privacy settings, and AES-256-CBC encryption.
Trusted by more than 15,000 organizations and 600,000 security professionals worldwide, ANY.RUN gives SOC teams the visibility they need to move from uncertain alerts to evidence-based decisions.







0 comments