Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


Moonrise RAT is a newly discovered Go-based remote access trojan with zero detections at launch, featuring credential theft, keylogging, webcam access, clipboard hijacking, and UAC bypass.
|
RAT
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
12 March, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 February, 2026
First seen
:
|
12 March, 2026
Last seen
:
|

 457
457
 0
0
 6854
6854
 0
0

 663
663
 0
0
destinationIP:"193.23.199.88".
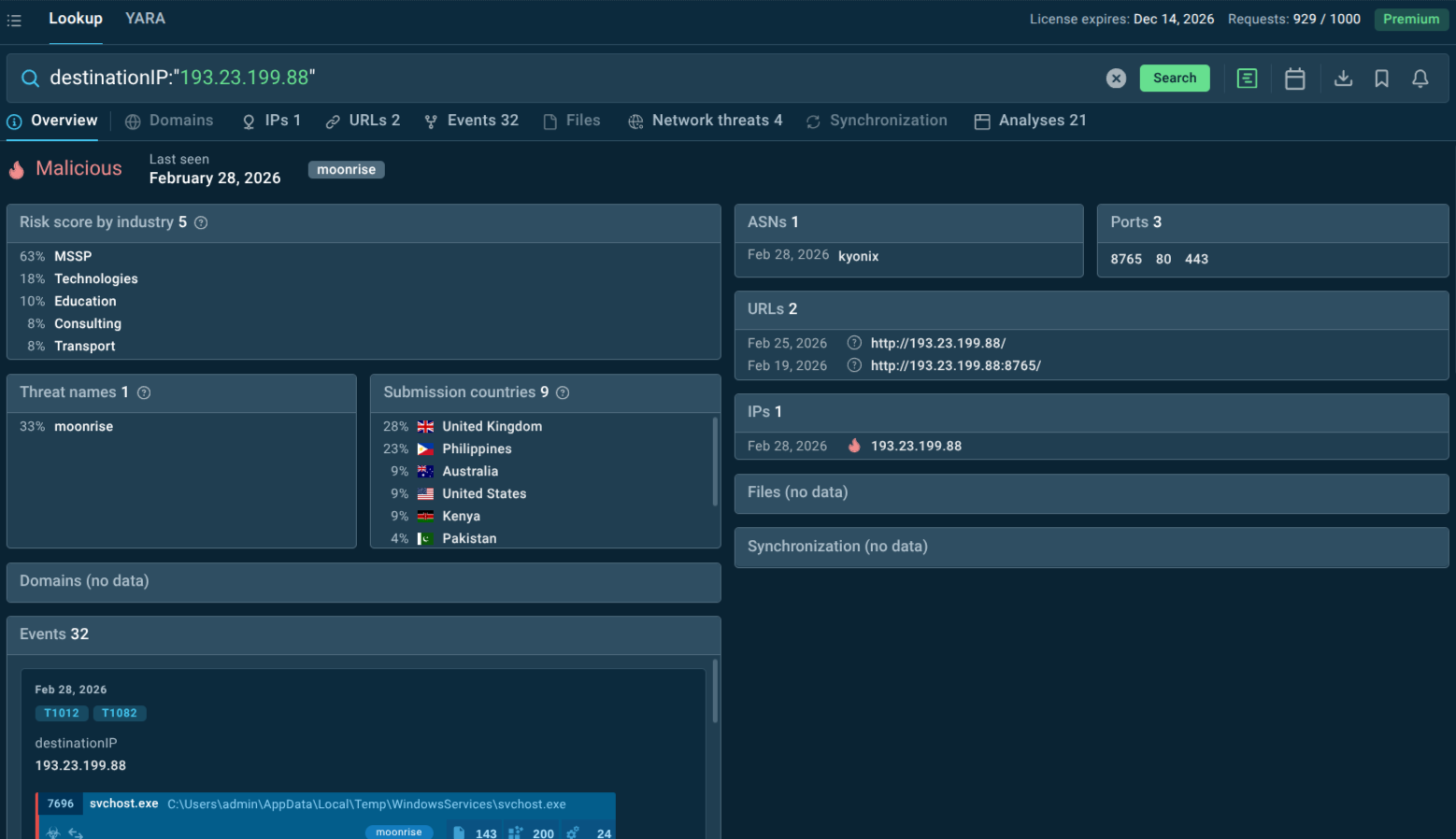 Domain linked to Moonrise with context data and malware analyses
Domain linked to Moonrise with context data and malware analyses
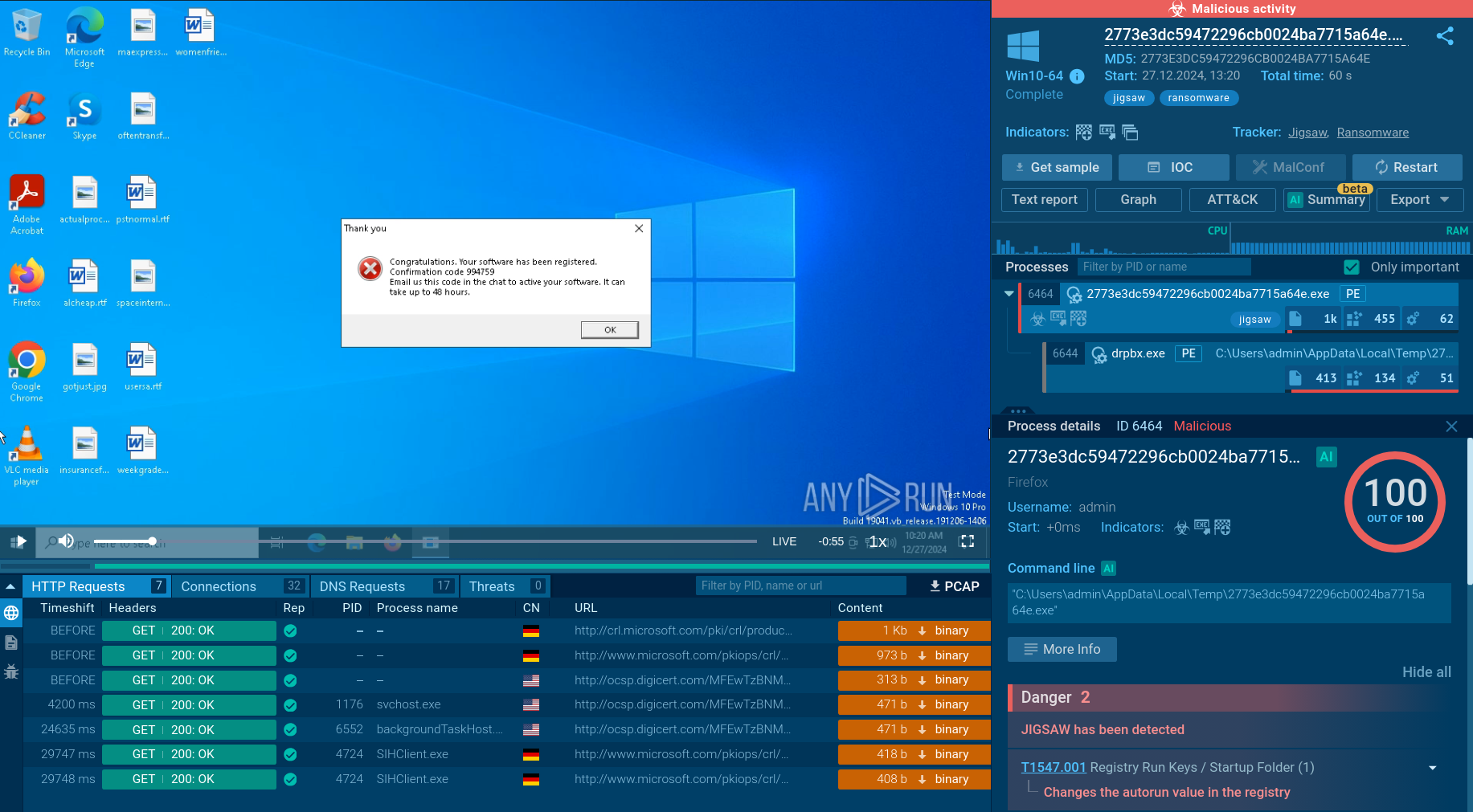
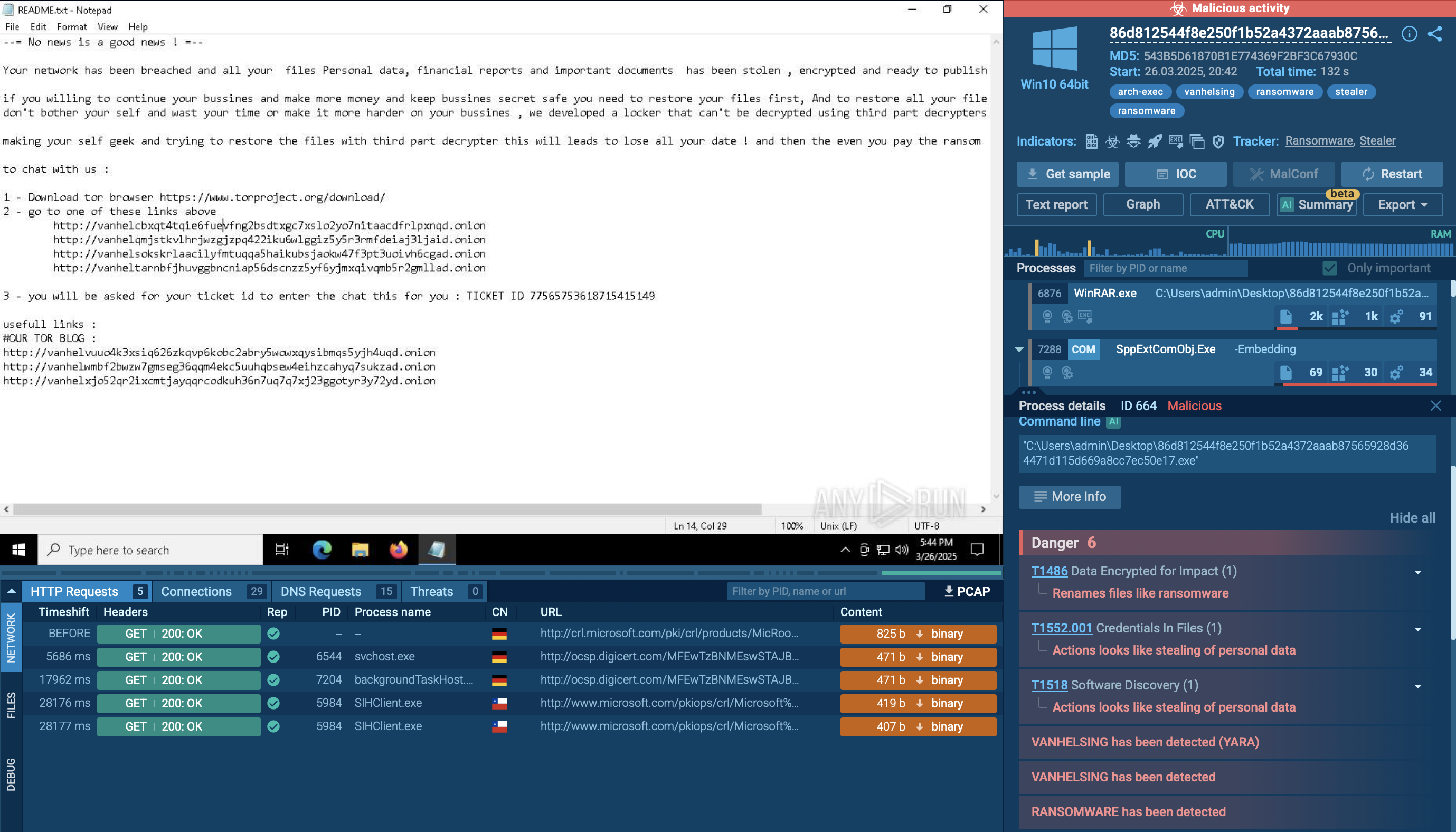
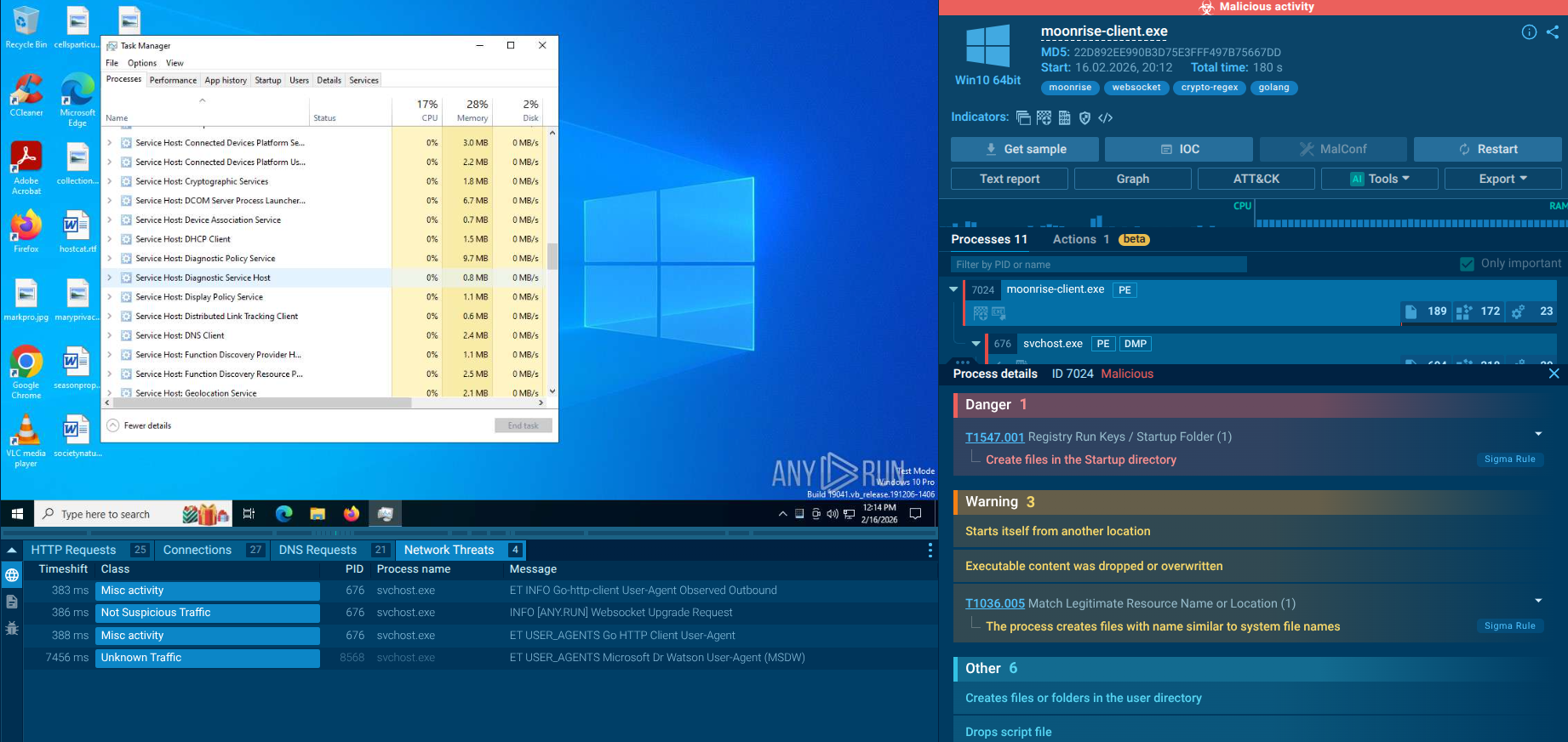 Moonrise RAT fresh sample analysis in Interactive Sandbox
Moonrise RAT fresh sample analysis in Interactive Sandbox
Moonrise is a full-featured remote access trojan engineered for stealth, persistence, and broad operational control. Identified by ANY.RUN researchers in early 2026, it was found to operate without triggering a single vendor alert on VirusTotal at the time of analysis — meaning it could steal credentials, execute remote commands, and establish persistent backdoor access while security teams had no indication anything was wrong.
The selection of Go as a development language is a deliberate technical choice: Go produces self-contained binaries with no external runtime dependencies, supports cross-platform compilation, and is notoriously difficult for traditional AV engines to fingerprint because its compiled output does not resemble the patterns associated with older malware codebases.
The malware's C2 communication is conducted via the WebSocket protocol, enabling it to masquerade as ordinary HTTPS traffic and blend into normal network activity. From the moment of infection, Moonrise establishes a persistent, bidirectional channel with its operator infrastructure — initiating a session handshake before any vendor signatures have been published.
Its command set is remarkably broad. Moonrise supports session management, full host reconnaissance, active command execution, credential harvesting, live user monitoring, privilege manipulation, and disruptive functions (fun_bsod, fun_shutdown, fun_restart, voltage_drop). The malware also supports lifecycle management via update and uninstall commands, allowing operators to modify or remove the implant after use.
This depth of functionality places Moonrise well above simple backdoors. It is a comprehensive offensive toolkit capable of supporting everything from initial access and reconnaissance to data exfiltration and secondary payload delivery — all while staying beneath static detection thresholds.
Moonrise presents risk across multiple dimensions:
Operational Risk
Long dwell time due to stealthy C2,
Lateral movement before detection,
Privilege escalation and domain compromise.
Financial Risk
Data theft leading to regulatory fines,
Ransomware deployment as secondary stage,
Business interruption.
Strategic Risk
Intellectual property exfiltration,
Access resale in underground markets,
Supply chain infiltration.
Moonrise is particularly dangerous because it often acts as an access broker tool. It may not be the final payload. It is the key that opens the vault for other actors.
Based on what Moonrise can do and how similar Go-based RATs have been deployed historically, the following sectors face elevated risk:
Credential theft, clipboard monitoring (including cryptocurrency wallet address hijacking via clipper_get_addresses and clipper_set_address), and keylogging make financial institutions especially attractive targets.
Healthcare remains the most breached industry globally, with breach costs averaging $10.3 million per incident. Moonrise's ability to exfiltrate data silently makes it well-suited for targeting patient records, insurance data, and pharmaceutical IP.
Technology and SaaS companies, as organizations that manage infrastructure for third parties, are high-value targets for initial access brokers and nation-state actors. A compromised DevOps endpoint can cascade into supply chain compromise.
Legal and professional services handling sensitive client data — contracts, litigation strategy, M&A intelligence — are highly vulnerable to the kind of silent exfiltration Moonrise enables.
Moonrise's webcam, microphone, and screen streaming capabilities align with espionage use cases. Government and defense contractors that work with sensitive national security data are natural targets.
As RAT activity in manufacturing surged 174% for comparable tools in Q4 2025 (per ANY.RUN data), operational technology environments and industrial control systems represent a growing attack surface. Manufacturing and critical infrastructure are at risk.
Decentralized IT environments, legacy systems, and limited security budgets make universities and research institutions particularly vulnerable to low-detection threats like Moonrise.
The defining challenge Moonrise poses is temporal: it acts before defenses can recognize it. Proactive threat intelligence tools address exactly this gap.
ANY.RUN Threat Intelligence Feeds provide a continuous stream of fresh, validated indicators derived from analysis sessions by 600,000+ security professionals across 15,000+ organizations. For Moonrise specifically, TI Feeds would surface the C2 IP (193.23.199.88) and associated file hashes before your internal systems encounter them, allowing defensive infrastructure to block the threat at the perimeter rather than detect it post-compromise.
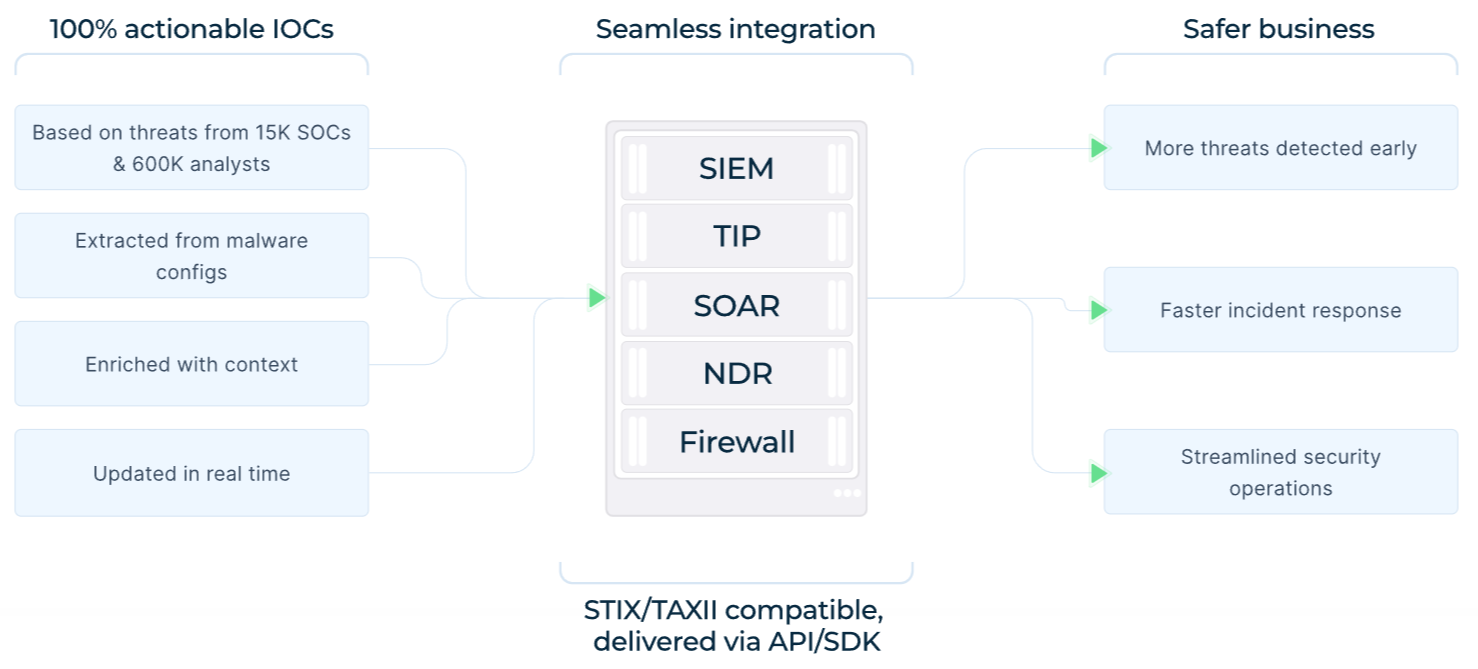 TI Feeds: benefits, data sources, integration options
TI Feeds: benefits, data sources, integration options
When an alert does fire — an unusual outbound connection, a suspicious process spawned by svchost.exe, or an unexpected file execution — Threat Intelligence Lookup allows analysts to instantly pivot on any observable indicator. A hash, IP, domain, or URL can be cross-referenced against the ANY.RUN database to retrieve related sandbox analyses, historical sightings, linked infrastructure, and associated malware families.
sha256:"ed5471d42bef6b32253e9c1aba49b01b8282fd096ad0957abcf1a1e27e8f7551".
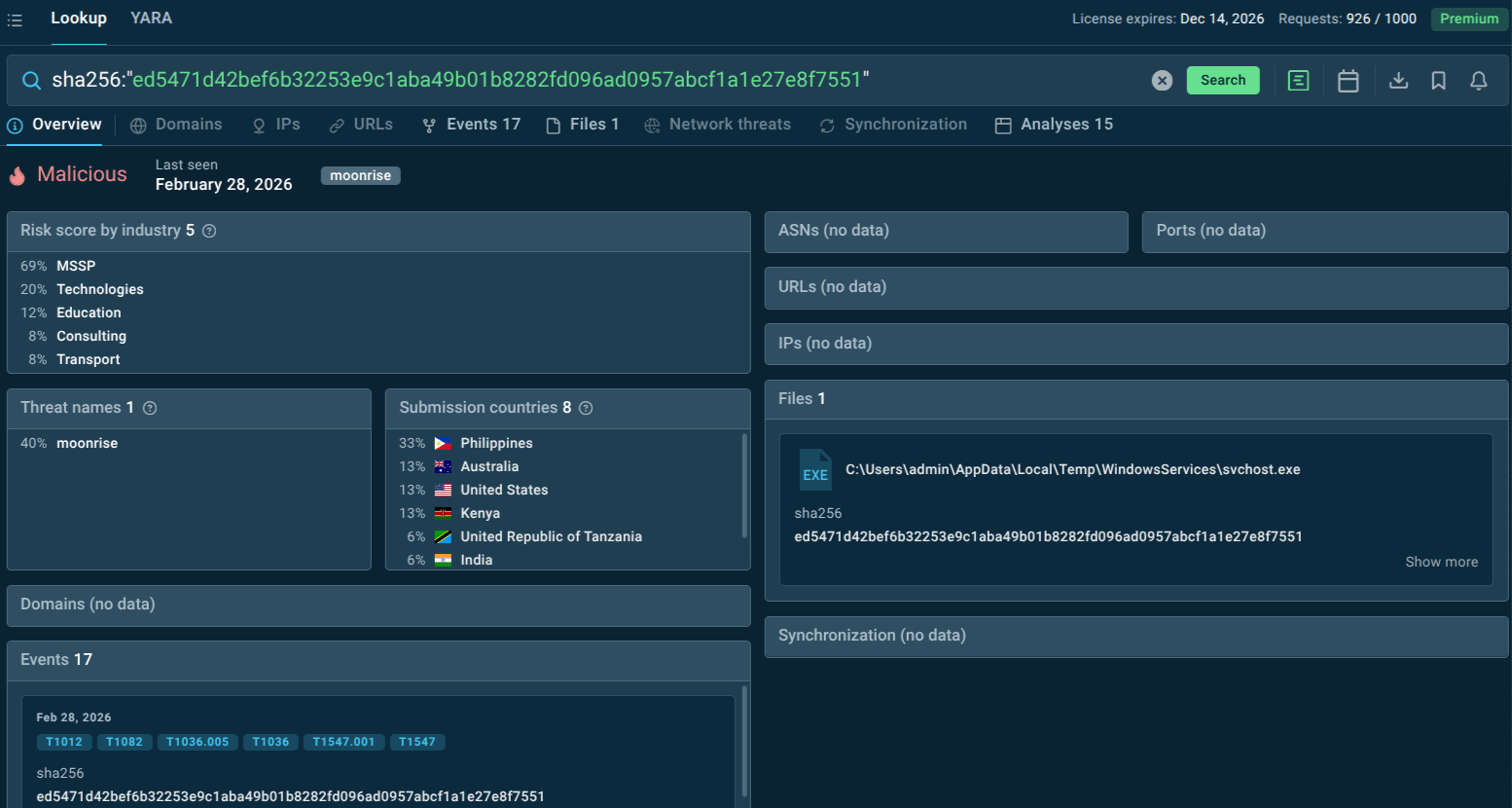 File hash observed in Moonrise samples
File hash observed in Moonrise samples
Other Defensive Measures
Deploy behavioral EDR solutions capable of detecting anomalous process trees, unexpected UAC bypass attempts, and unauthorized access to audio/video hardware.
Implement network segmentation and egress filtering to limit the blast radius of any single compromised endpoint.
Enforce multi-factor authentication across all critical systems to reduce the value of stolen credentials.
Conduct regular threat hunting exercises focused on weak signals: unexpected WebSocket connections, svchost.exe spawning cmd.exe, and new scheduled tasks or registry run keys.
Use ANY.RUN's Interactive Sandbox to safely analyze suspicious files and URLs in a controlled environment before they reach production systems.
Establish a patch cadence and ensure endpoint security software is current, reducing the attack surface Moonrise can exploit during initial access.
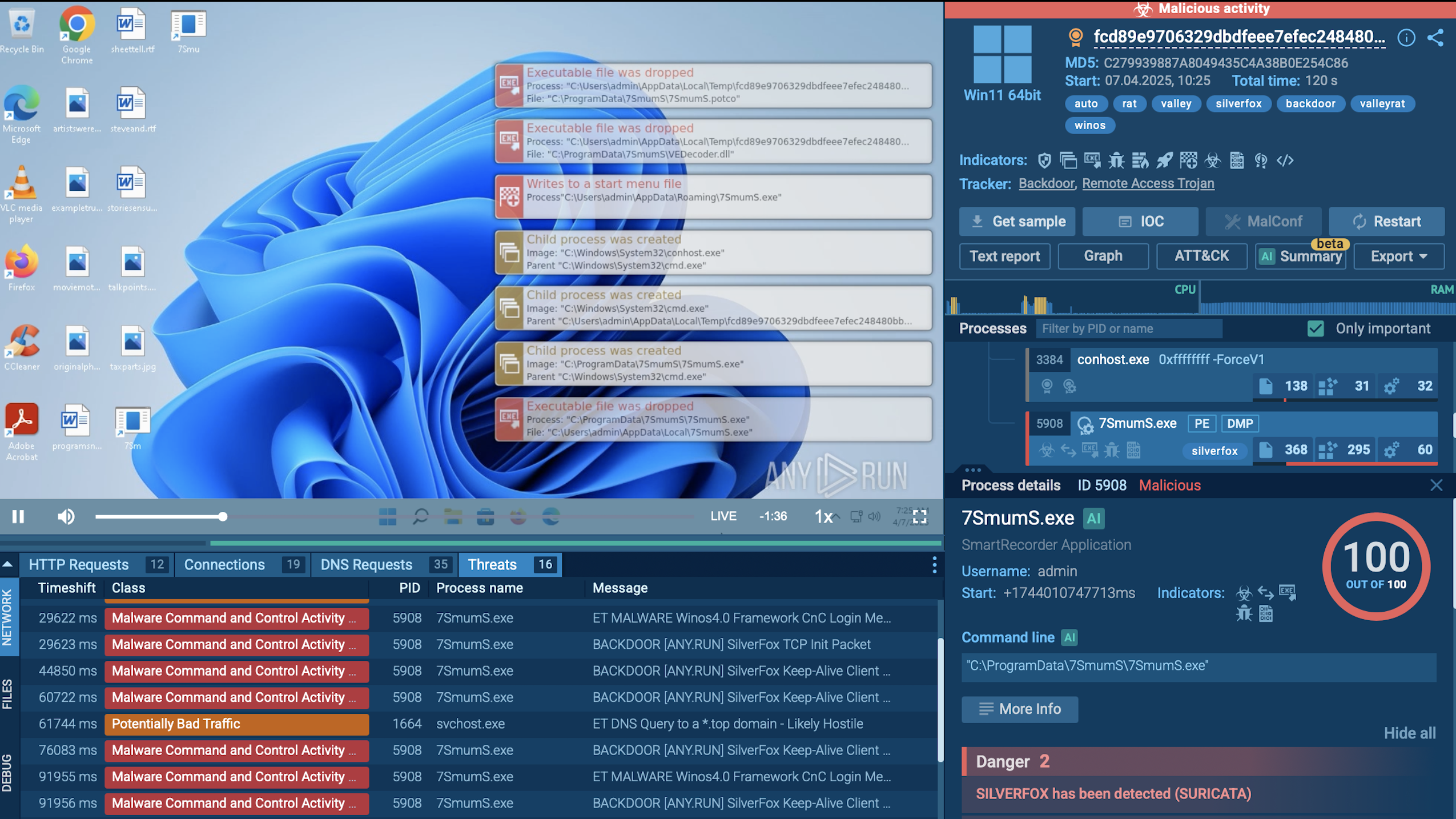
Like most RATs, Moonrise relies on social engineering to achieve initial execution.
Malicious document attachments: PDF, Word, or Excel files containing macros or embedded exploits that trigger payload download and execution.
Executable masquerading: Binaries disguised as legitimate software installers, game cracks, or utility tools, distributed through phishing emails, fake download pages, or social media.
Archive files: ZIP, RAR, or ISO containers that bypass email filtering and deliver the payload when extracted and executed by the user.
Script-based delivery: PowerShell or batch scripts that download and execute Moonrise from remote infrastructure, often triggered by document macros.
Spear-phishing: Targeted emails crafted to impersonate trusted contacts or internal IT communications, increasing the likelihood of user execution.
Moonrise operates through a structured, session-oriented command loop. Its operation can be broken into seven phases:
Phase 1 — Session Establishment: The malware initiates contact with its C2 server via WebSocket protocol. It sends client_hello and connected signals, then maintains the session with periodic ping/pong heartbeats. This phase completes silently, with no user-visible behavior.
Phase 2 — Host Reconnaissance: The operator requests a comprehensive picture of the victim environment via process_list, file_list, monitors_list, webcam_list, and screenshot commands.
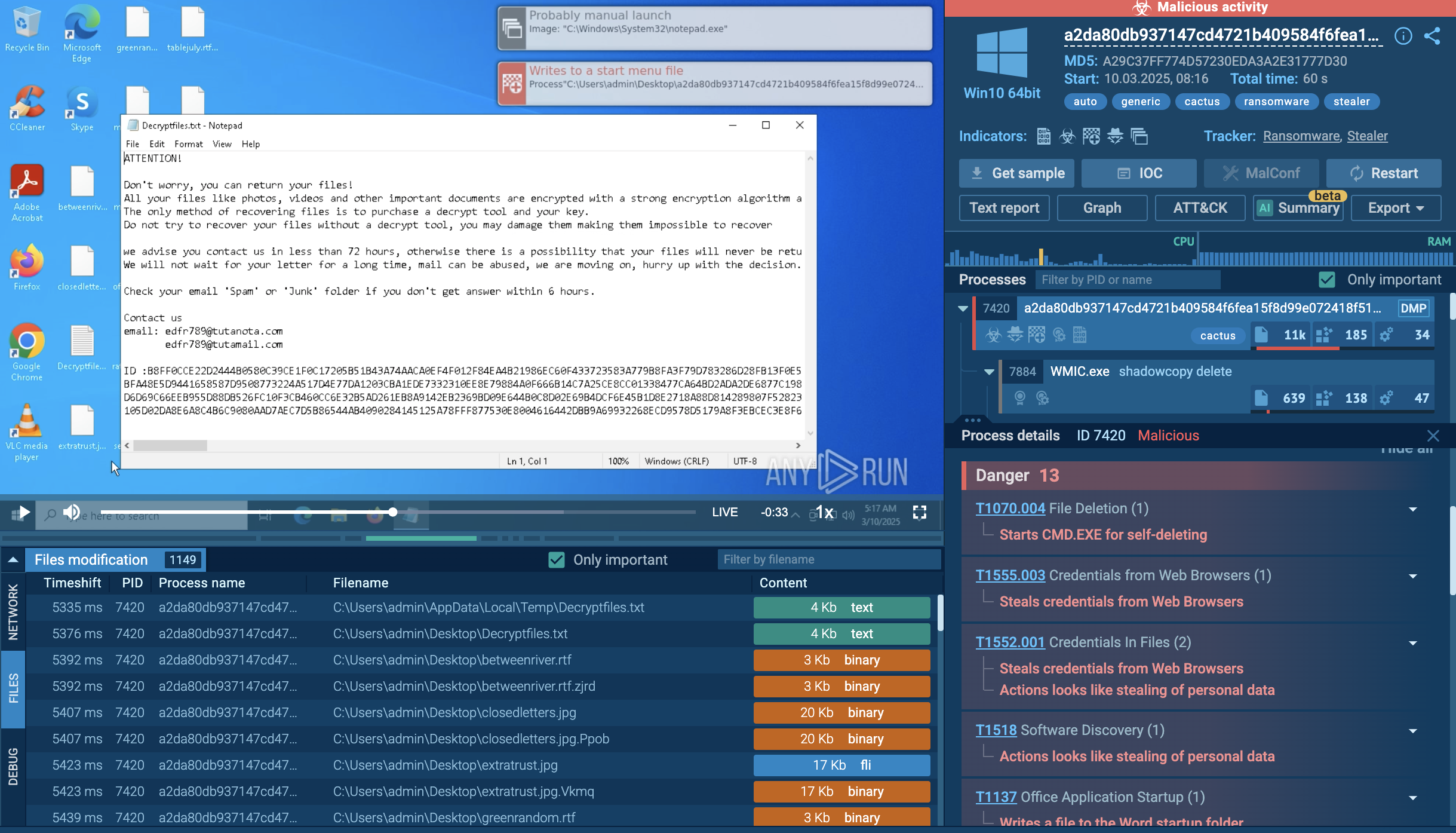
Phase 3 — Active Control: Using cmd, process_kill, file_upload, file_run, file_execute, file_delete, mkdir, and explorer_restart, the operator takes direct control of the endpoint — running commands, terminating security processes, uploading payloads, and modifying the file system.
Phase 4 — Credential Harvesting: The stealer module extracts credentials from browsers, applications, and system memory.
Phase 5 — Live Surveillance: Keyloggers, clipboard monitors, screen streaming, webcam capture, and microphone recording convert the endpoint into a real-time surveillance node. The clipper module can also substitute cryptocurrency wallet addresses in the clipboard, redirecting transactions to attacker-controlled wallets.
Phase 6 — Privilege Escalation and Persistence: uac_bypass allows elevation to administrator privileges. rootkit_enable installs rootkit components to hide the malware's presence. watchdog_status and protection_config ensure the malware monitors its own integrity and resists removal.
Phase 7 — Lifecycle Management: The update command allows operators to deploy new versions of Moonrise without re-infecting the host. The uninstall command cleanly removes the malware after an operation is complete — leaving minimal forensic trace.
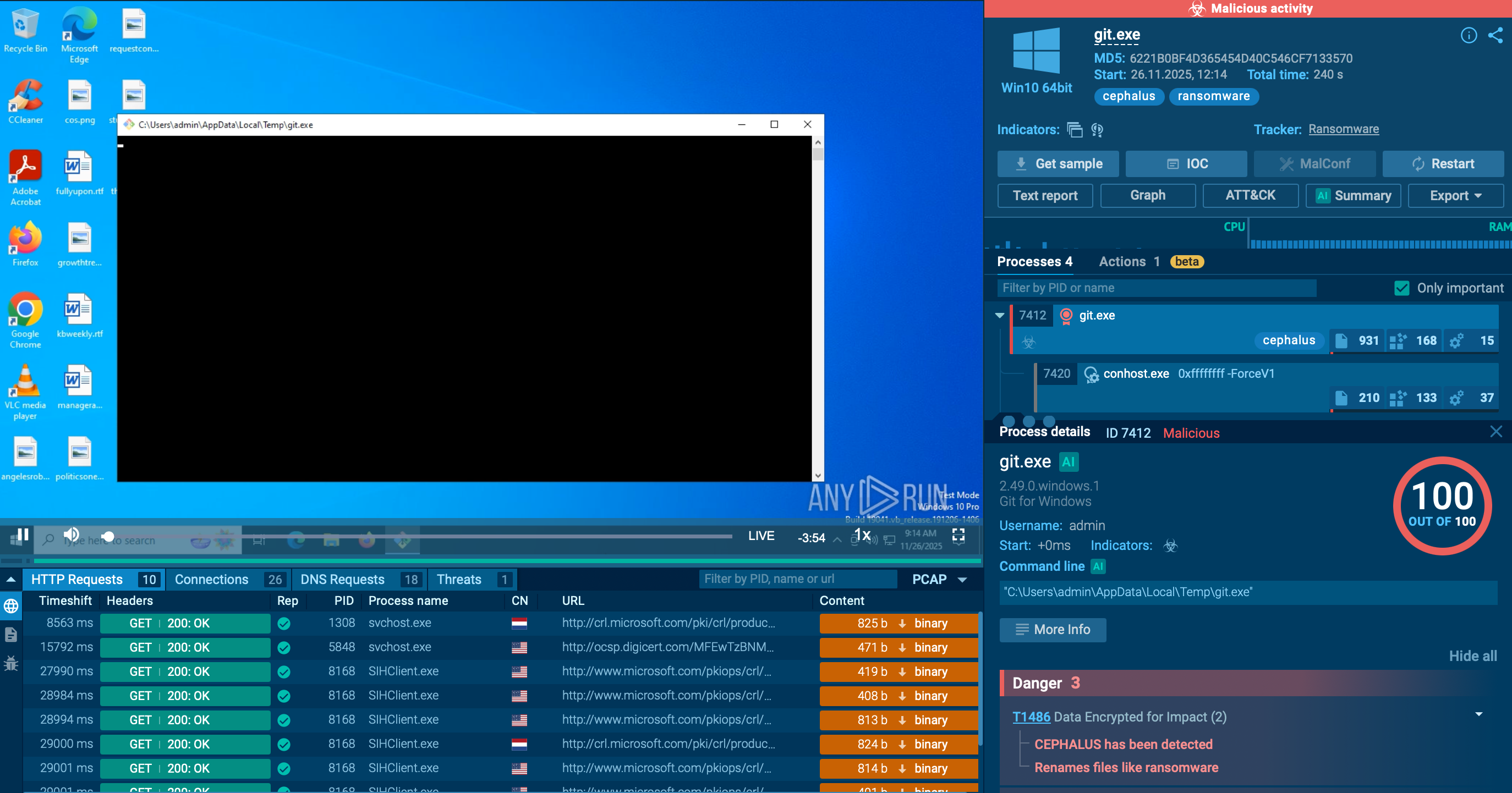
You can follow the full Moonrise chain in real time, from execution to C2 control, and note the behaviors you can use for detection and triage.
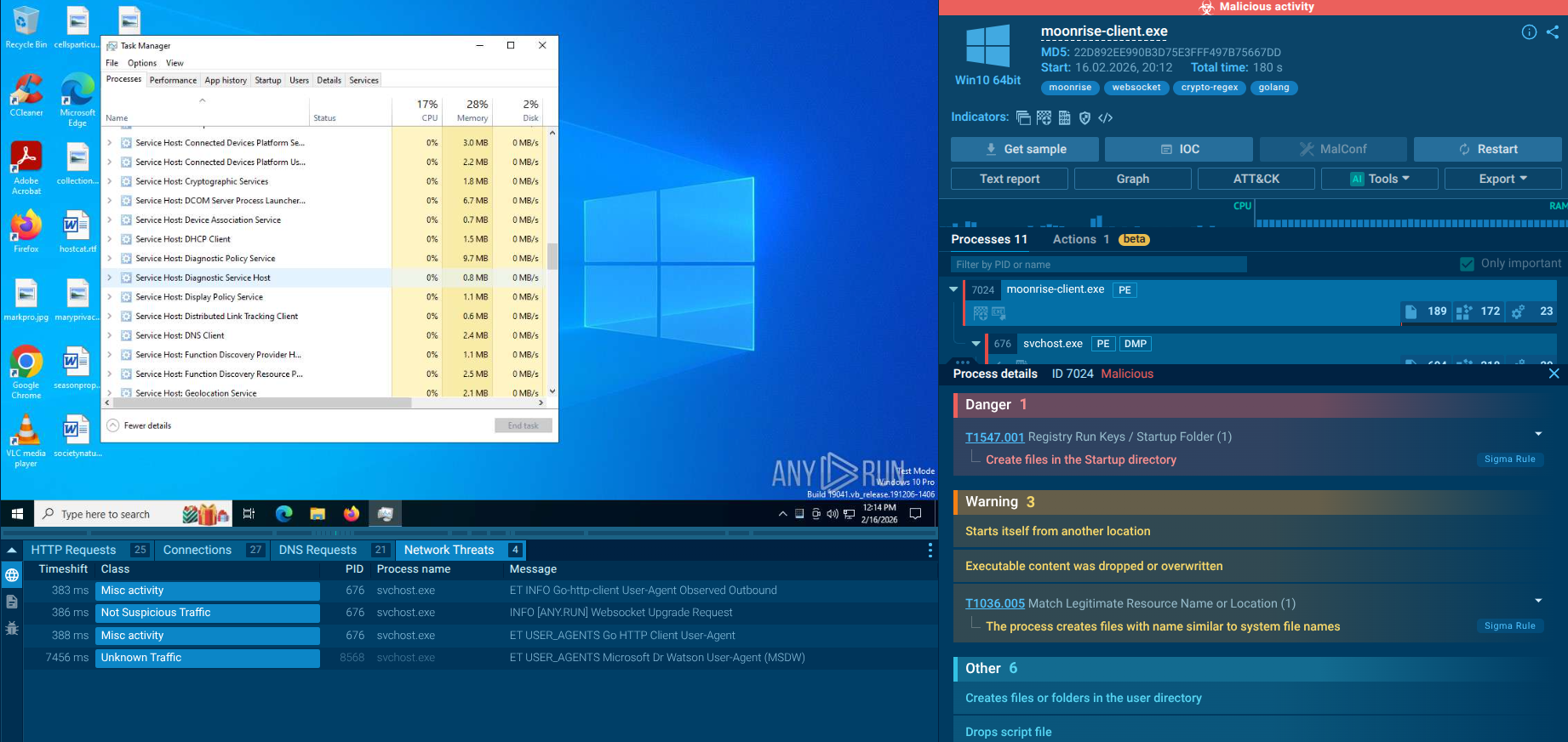 ANY.RUN sandbox revealing Moonrise full attack chain
ANY.RUN sandbox revealing Moonrise full attack chain
Within minutes of execution, Moonrise established outbound communication and began responding to operator-driven commands. What looked harmless in static checks immediately revealed interactive control once behavior was observed.
1. Session Registration and Persistent Communication
The communication begins with the commands that handle client identification and keep the WebSocket session alive. This confirms that the infected system is actively connected and ready to receive instructions. At this stage, traditional static checks still show nothing suspicious. But behaviorally, the endpoint is already under remote control.
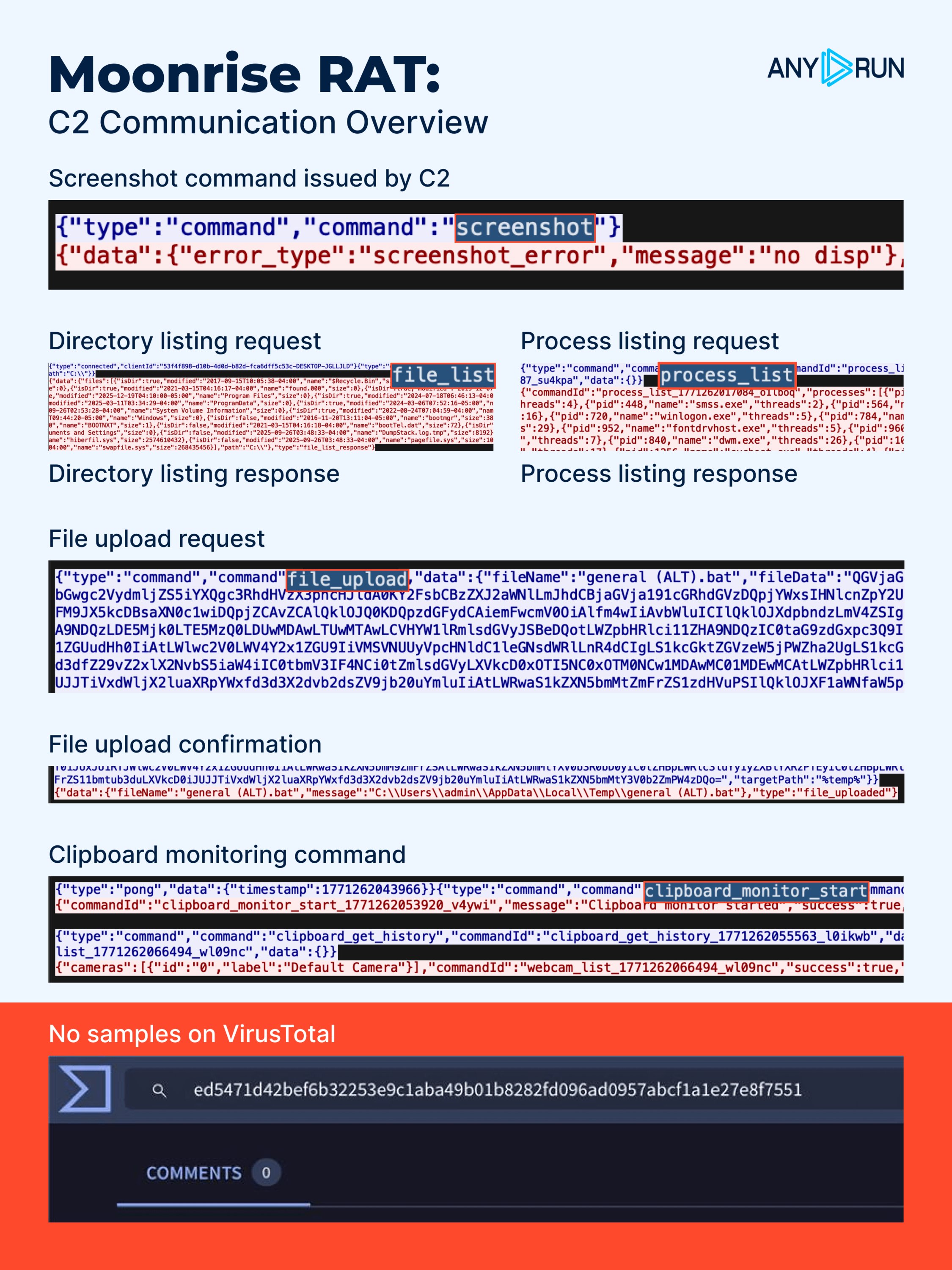 C2 communication overview of Moonrise RAT
C2 communication overview of Moonrise RAT
2. Visibility Into the Host Environment
Once the session is established, the operator starts requesting information about the system that allows to inspect running processes, review directory structures, identify connected displays, and check for available multimedia devices. Even when screen capture fails in a headless environment, the attempt itself signals active operator-driven interaction.
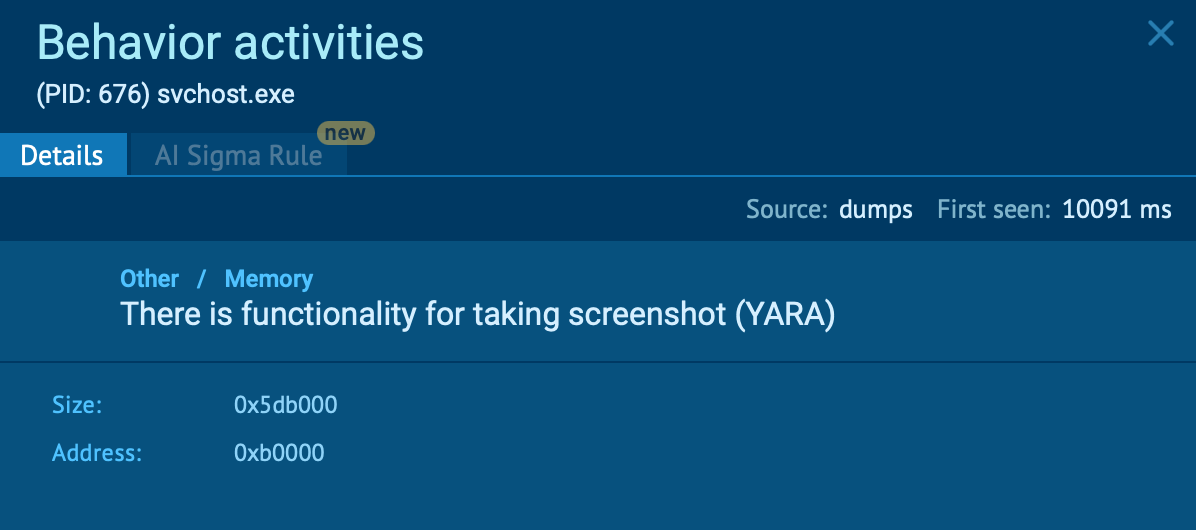 YARA rule match confirming screenshot functionality inside the Moonrise process
YARA rule match confirming screenshot functionality inside the Moonrise process
3. Direct System Interaction and Control
Operators can run system commands remotely, terminate selected processes, upload additional payloads, execute them, modify directories, and restart system components.
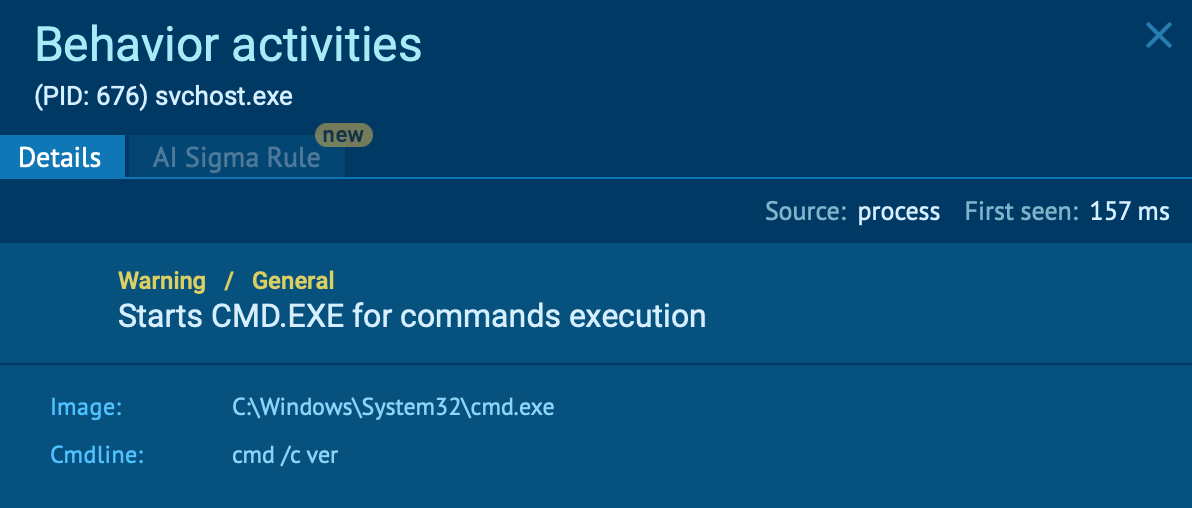 svchost.exe spawning cmd.exe to execute system commands inside the ANY.RUN sandbox
svchost.exe spawning cmd.exe to execute system commands inside the ANY.RUN sandbox
4. Credential Access and Data Extraction
Functions like stealer, keylogger_logs, clipboard_history enable collection of stored credentials, extracted files, logged keystrokes, and clipboard content. If sensitive data is copied between applications, such as passwords or financial details, it becomes accessible to the operator.
5. Active User Monitoring
Another set of commands allows malefactor to monitor user input, track clipboard changes, capture screen content, and access audio or video devices.
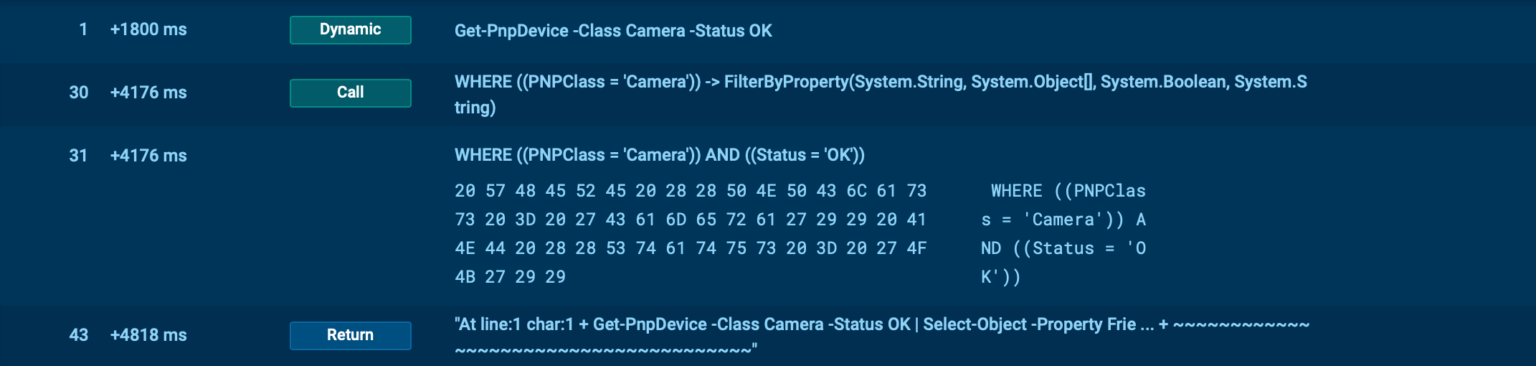 Moonrise RAT checks for available and operational camera hardware before attempting capture
Moonrise RAT checks for available and operational camera hardware before attempting capture
6. Privilege and System-Level Capabilities
Moonrise also contains commands related to privilege handling and system configuration. These suggest support for privilege manipulation, system configuration changes, and persistence-related behavior. While not all commands may be triggered in every session, their presence indicates extended control options.
7. Lifecycle Management and Disruption
Lifecycle management functions let operators modify or remove the deployed version of the malware. This indicates support for maintaining or adjusting the infection over time.
Even for zero-day threats like Moonrise, TI Lookup surfaces all sandbox sessions in which associated infrastructure appeared, giving teams visibility into the timeline and scope of the threat. Confirmed Moonrise indicators (e.g., C2 IP 193.23.199.88) can be used as pivots to discover related samples, associated domains, and attacker infrastructure clusters, enabling proactive hunting rather than reactive response.
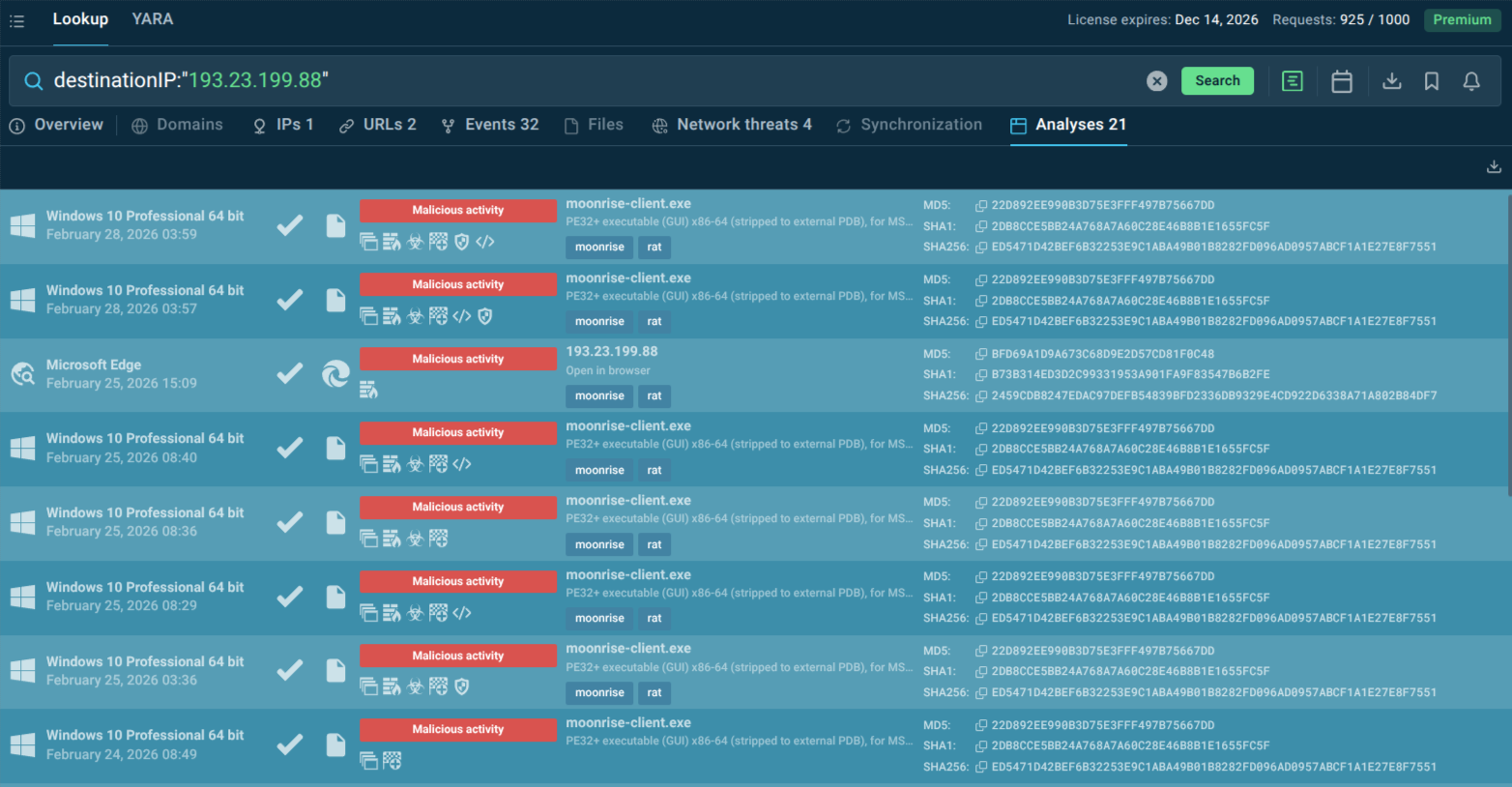 TI Lookup displays sandbox analyses related to the IP address used in the Moonrise attack
TI Lookup displays sandbox analyses related to the IP address used in the Moonrise attack
Rich context around any indicator helps Tier-1 analysts quickly distinguish genuine Moonrise-related activity from noise, reducing unnecessary escalations and improving MTTR.
Lookup integrates with existing SIEM, SOAR, and ticketing systems, allowing enrichment workflows to be automated and embedded in existing SOC processes.
MSSPs can leverage TI Lookup to investigate indicators across client environments and share relevant intelligence, improving coverage without duplicating manual research effort.
Moonrise is a case study in what makes modern malware genuinely dangerous: not raw power, but strategic invisibility. Its Go-based architecture, WebSocket C2, zero static detections at launch, and comprehensive command set combine to create a threat that can operate undetected for extended periods — stealing credentials, establishing persistence, staging payloads, and surveilling users while security teams have no indication anything is wrong.
For companies, the consequence is not just a technical incident but a business crisis: extended dwell time, stolen credentials, potential ransomware staging, regulatory exposure, and reputational damage. The financial services, healthcare, technology, legal, and government sectors face the highest exposure, but no industry is immune to a RAT that can bypass static defenses so effectively.
The defensive answer is not more signatures — it is faster behavioral clarity. ANY.RUN's Threat Intelligence Feeds and TI Lookup together address Moonrise's core advantage: they surface new infrastructure and behavioral indicators before static detection catches up, enable rapid enrichment and pivot during triage, and support proactive hunting to catch the next Moonrise-class threat before it becomes a costly incident.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.