ZLoader is back and armed with new capabilities.
Threat hunters have discovered a new campaign distributing ZLoader malware, nearly two years after its control network was disrupted in April 2022.
The takedown of 65 domains by a coalition led by Microsoft’s Digital Crimes Unit significantly impacted ZLoader’s operations, but according to Zscaler ThreatLabz, since September 2023, a new version of ZLoader has been under development, featuring major updates to its loader module.
The latest versions, 2.1.6.0 and 2.1.7.0, have introduced techniques like junk code and string obfuscation to hinder analysis, and they require a specific filename to execute on targeted hosts, potentially evading detection by automated malware analysis tools.
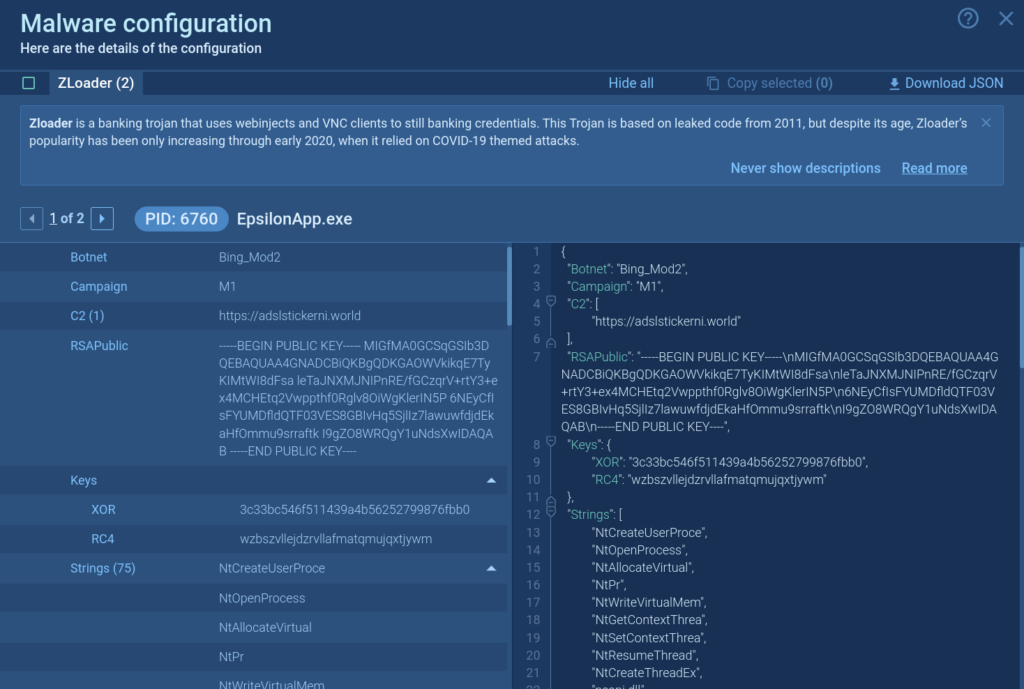
These versions also encrypt their configuration using RC4 encryption with a hard-coded key, hiding details about the campaign and command-and-control servers. An updated domain generation algorithm provides a backup communication method in case the primary servers are taken down. This resilience suggests that despite previous setbacks, ZLoader remains a significant threat, with potential for new ransomware attacks, indicating that the operational takedown hindered but didn’t eliminate the threat group behind it.
What is ZLoader
ZLoader, also known as Terdot, DELoader, or Silent Night, evolved from the Zeus banking trojan that appeared in 2015. Initially a banking malware, it later shifted to deploy other malicious payloads, like ransomware. Originating from code that leaked in 2011, Zloader has been gaining popularity through 2020 by leveraging COVID-19 themed attacks, until its control servers were taken down.
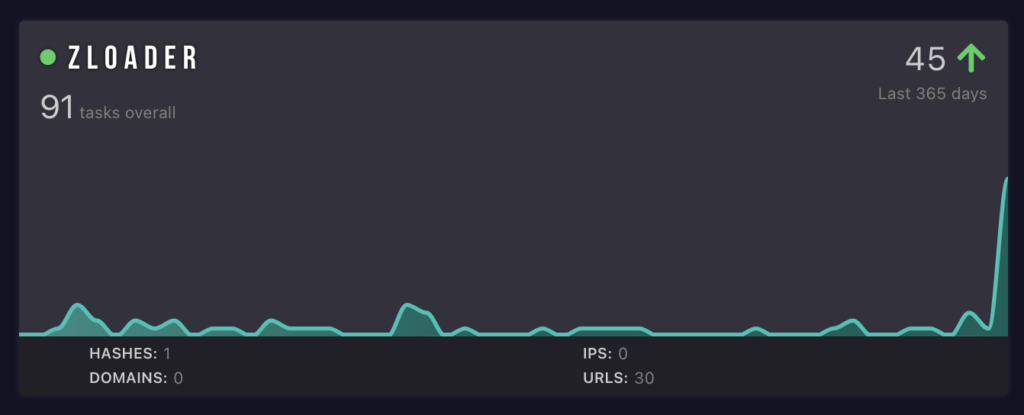
For more details — and the latest IOCs pulled from ANY.RUN Sandbox tasks — read ZLoader description in Malware Trends Tracker.
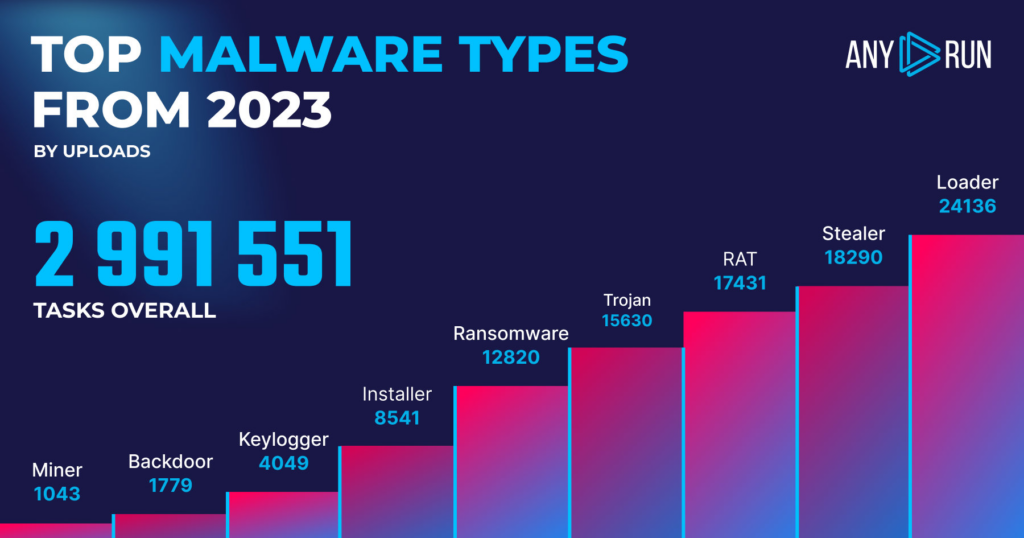
As the name suggests, ZLoader is designed to deliver additional malware onto the systems it infects. Loaders are notably prevalent in attack chains; with 24,136 detections, they were the most identified category in 2023, according to data from public tasks processed in ANY.RUN’s interactive cloud sandbox.
Read our full breakdown of 2023 malware trends.
Easily pull IOCs from the new ZLoader variant in ANY.RUN
To secure against the new ZLoader variant, companies should update their security systems with Indicators of Compromise, such as file hashes, C2 IP addresses, and URLs.
ANY.RUN interactive malware sandbox streamlines the IOC extraction process for security professionals. They can then use gathered indicators in endpoint security, SIEM, and SOAR systems to safeguard their infrastructure against ZLoader.
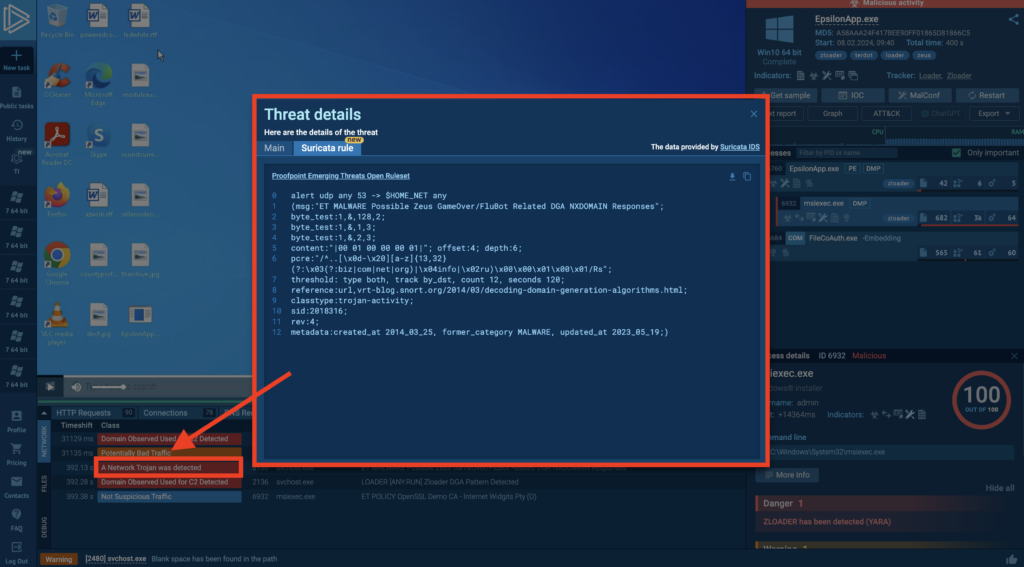
Let’s use this sandbox task as an example to illustrate how to pull IOCs from the new ZLoader variant.
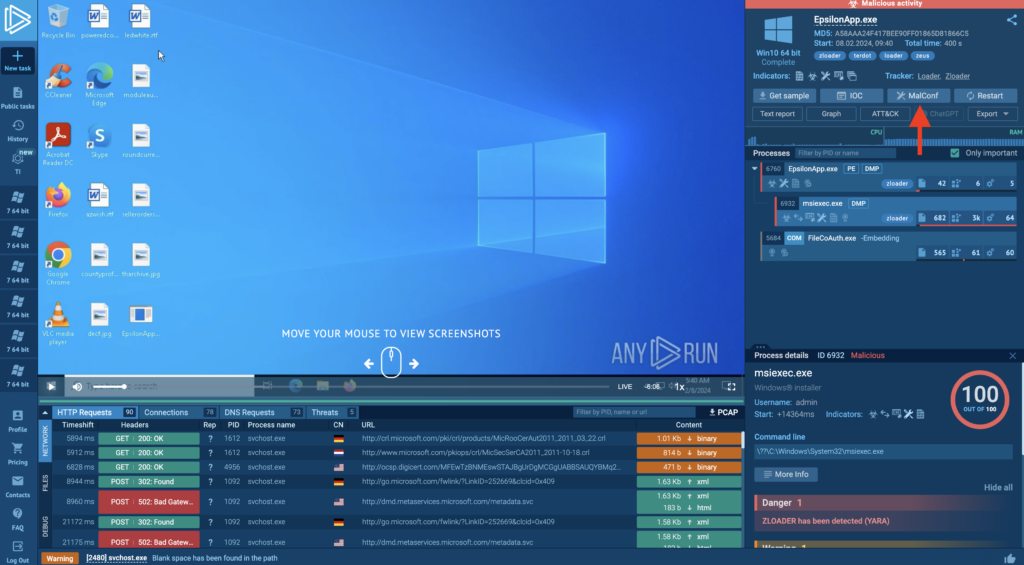
In ANY.RUN, you can extract valuable indicators of compromise such as C2 server addresses from malware, even if it is not actively connected to the control server. Simply open the malware configuration and copy the relevant information from there.
In addition to this, you get direct access to Suricata rules that were triggered during the task. Feel free to use them within your security infrastructure.
About ANY.RUN
ANY.RUN is a developer of cloud malware sandbox that handles the heavy lifting of malware analysis for SOC and DFIR teams, as well as Threat Intelligence Feeds and Threat Intelligence Lookup. Every day, 300,000 professionals use our platform to investigate incidents and streamline threat analysis.
Request a demo today and enjoy 14 days of free access to our Enterprise plan.








0 comments