Webinar
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


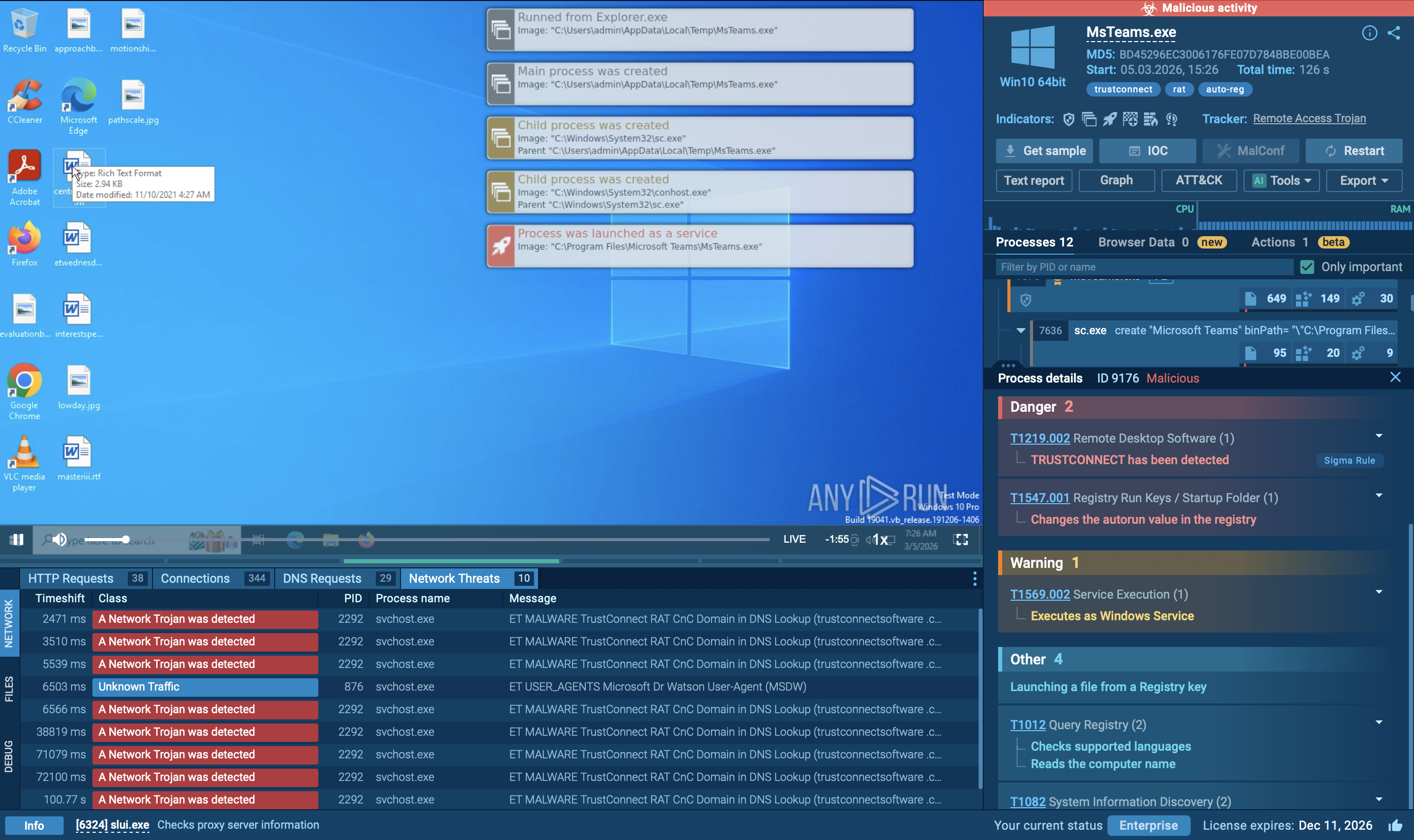
TrustConnect is a MaaS platform that disguises a Remote Access Trojan (RAT) as a legitimate Remote Monitoring and Management (RMM) tool. The operators built an AI-generated business website, obtained a fraudulently acquired Extended Validation (EV) code-signing certificate, and created fake customer statistics and documentation to make TrustConnect appear to the world — and to security tools — as a legitimate software company.
|
RAT
Type
:
|
Unknown
Origin
:
|
|
20 January, 2026
First seen
:
|
28 March, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
20 January, 2026
First seen
:
|
28 March, 2026
Last seen
:
|

 410
410
 0
0

 2431
2431
 0
0

 4666
4666
 0
0
TrustConnect is a professional MaaS RAT: its operators built a fake software company, obtained an EV certificate, and created a polished C2 dashboard. This level of investment signals a durable, scalable criminal enterprise, not a one-off campaign.
EV certificates are not trust guarantees: TrustConnect demonstrated that Extended Validation certificates can be obtained through deception.
Unlike passive infostealers, TrustConnect gives an operator complete interactive control of a victim machine — enabling banking fraud, data exfiltration, lateral movement, and sabotage in real time.
Infrastructure takedowns are temporary: TrustConnect rebranded to DocConnect within hours of its C2 being taken offline. Detection strategies must target persistent behavioral patterns and TTPs, not just static IOCs tied to a specific campaign.
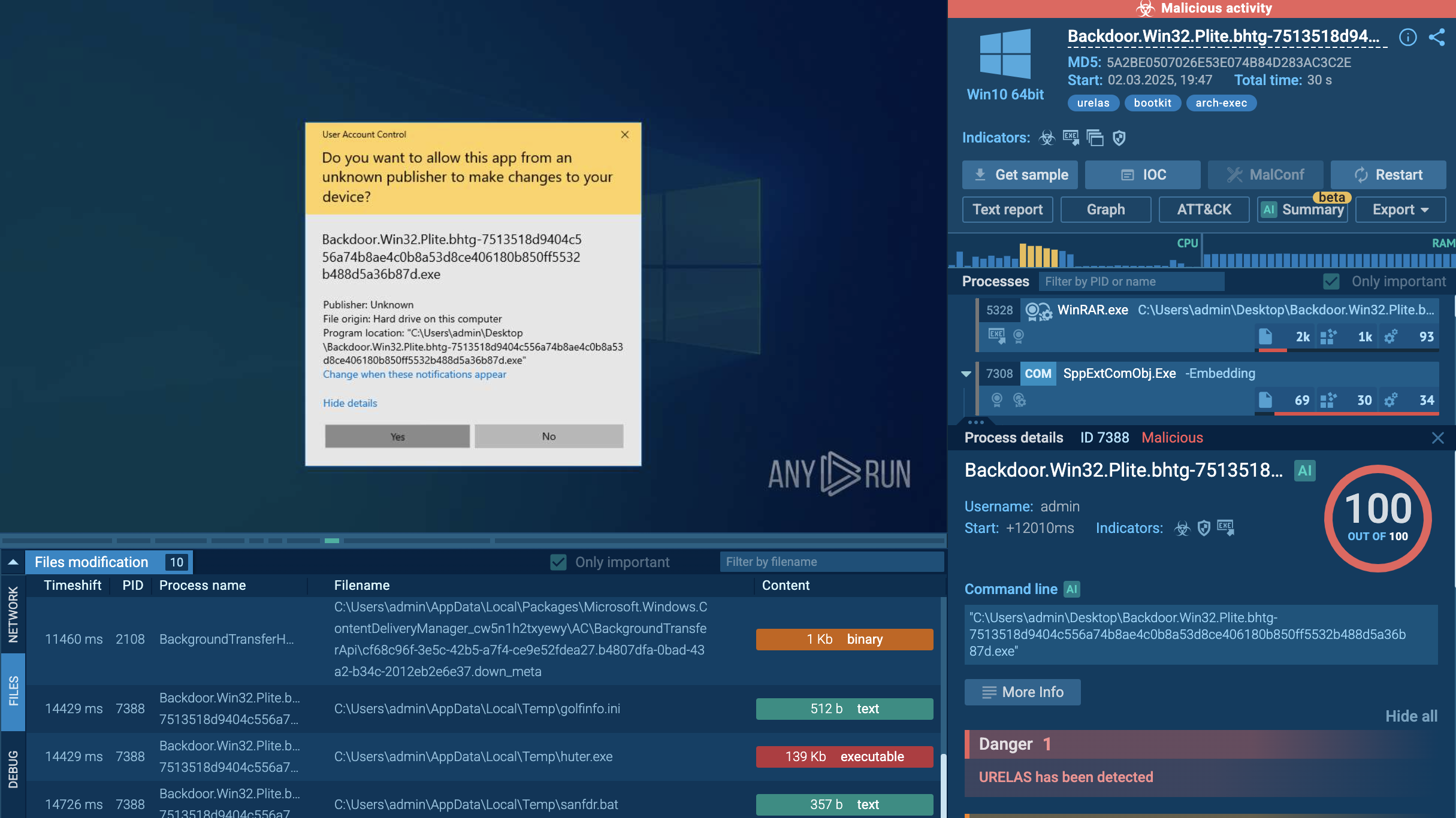
By detonating TrustConnect samples in ANY.RUN's cloud-based Interactive Sandbox, analysts can observe real-time C2 registration, RDP stream initiation, follow-on ScreenConnect deployment, and PowerShell execution — generating rich behavioral IOCs that static analysis tools miss entirely.
View TrustConnect sample analysis
 TrustConnect fresh sample analysis in Interactive Sandbox
TrustConnect fresh sample analysis in Interactive Sandbox
 TrustConnect sandbox analyses found in TI Lookup
TrustConnect sandbox analyses found in TI Lookup
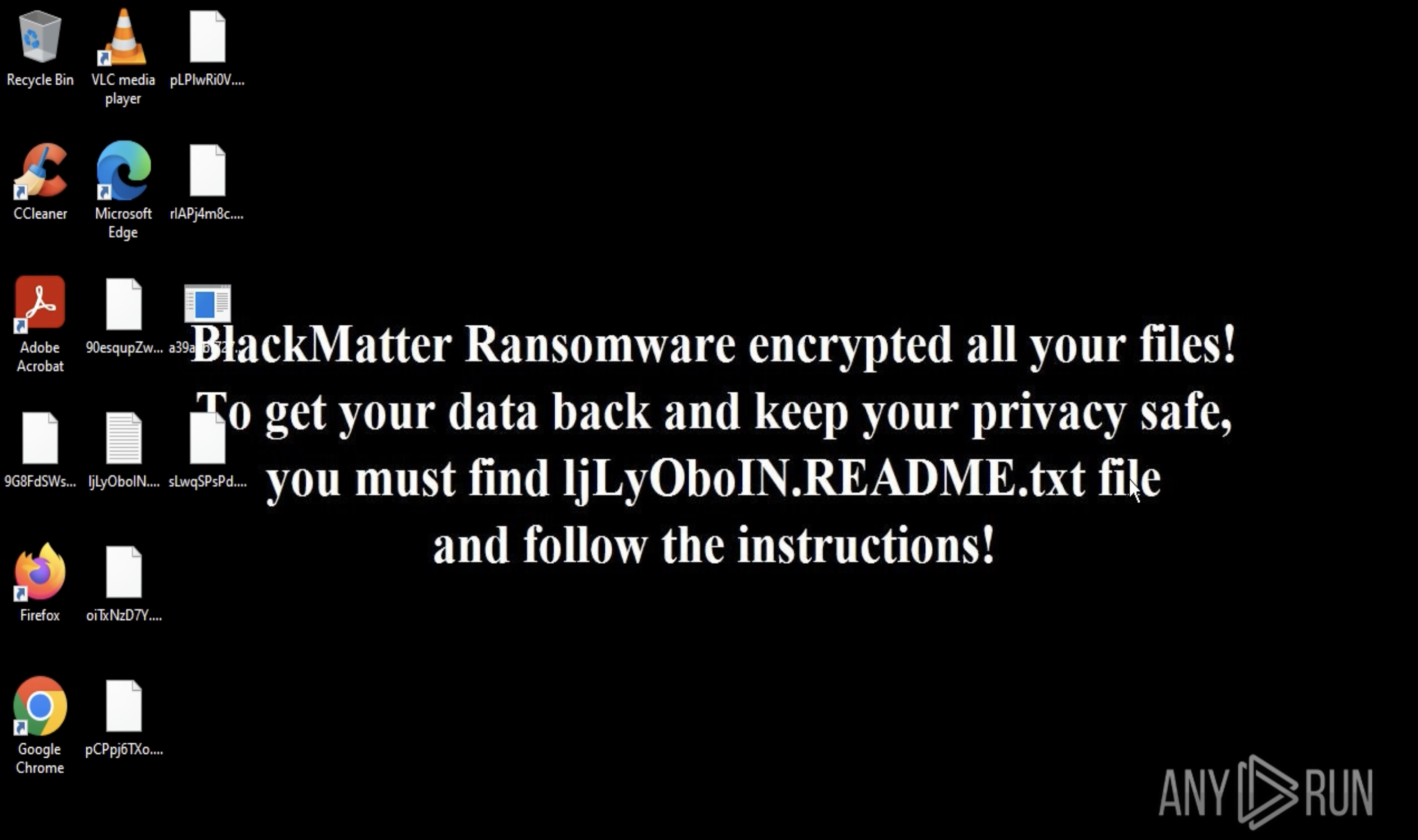
TrustConnect is part of a growing trend where cybercriminals design malware to resemble legitimate enterprise software products.
Instead of simply distributing a malicious executable, the operators behind TrustConnect built:
A professional website posing as a software vendor;
Documentation and support pages;
A subscription portal used as the malware command-and-control interface;
A digitally signed application using an Extended Validation (EV) certificate obtained under a fake company identity.
The malware is presented as a remote administration tool called TrustConnectAgent, which victims install believing it to be legitimate software. After installation, the malware establishes persistent communication with a centralized command portal where attackers manage infected systems.
Unlike many RATs, TrustConnect integrates features typical of enterprise RMM solutions, including remote desktop access, file transfers, and centralized device management.
The domain trustconnectsoftware[.]com was registered on January 12, 2026. Within days, the operator had:
Launched an AI-generated website presenting "TrustConnect Software PTY LTD" (nominally based in Alexandra, South Africa) as a legitimate SaaS provider;
Purchased an Extended Validation (EV) code-signing certificate under that fictitious company identity — EV certificates involve enhanced identity checks and cost thousands of dollars, giving malicious files the appearance of being trusted software;
Built a C2 backend (hosted at 178[.]128[.]69[.]245) serving both as a criminal subscription portal and as the actual malware command infrastructure;
Begun distributing malicious executables to victims by January 26–27, 2026.
The EV certificate was revoked on February 6, 2026, through a coordinated effort by Proofpoint and certificate-intelligence specialists at The Cert Graveyard. However, because certificate revocation is not retroactive, all signed samples distributed before that date remained valid. Proofpoint and anonymous industry partners took down the primary C2 infrastructure around February 17, 2026. Within hours, the operator had already pivoted to parallel infrastructure and began testing a rebranded variant called DocConnect (also dubbed "SHIELD OS v1.0"), this time using a React Single Page Application (SPA) backed by Supabase — demonstrating exceptional operational resilience.
Proofpoint assessed with moderate confidence that both the TrustConnect and DocConnect websites and agent codebases were developed with the assistance of AI tooling — a trend that is dramatically lowering the barrier to building convincing MaaS infrastructure.
TrustConnect poses a multi-dimensional threat to enterprises, specifically because it exploits the intersection of trusted software appearance, legitimate network protocols, and low operator technical skill requirements.
1. Full Remote Takeover
Once installed, TrustConnect gives the subscribing criminal complete keyboard-and-mouse control over the victim's workstation, including the ability to hide their own activity from the victim's screen. This goes far beyond passive data theft: an operator can actively conduct banking fraud, transfer files, install additional payloads, modify configurations, or pivot to other systems on the same network.
2. Trusted Software Masquerading
Because TrustConnect executables are signed with an EV certificate and visually mimic Zoom, Microsoft Teams, Adobe Reader, or Google Meet, complete with matching icons, file names, and metadata, they are highly likely to bypass standard user suspicion and first-generation signature-based antivirus scanning. Employees who routinely install IT tools or respond to IT helpdesk tickets are natural targets.
3. Multi-Layer Persistence
Proofpoint observed TrustConnect being used to deploy follow-on payloads — specifically, self-hosted instances of ScreenConnect from at least nine distinct servers (many running legacy versions with expired or revoked certificates). This creates a layered persistence mechanism: even if the initial TrustConnect agent is detected and removed, legitimate-looking RMM software remains on the system.
4. Resilient Infrastructure
The operator's ability to rebuild infrastructure within hours of takedown — and pivot to a rebranded DocConnect variant — means that enterprise defenders cannot rely on perimeter blocks of known IOCs alone. The threat is structurally resilient by design.
TrustConnect's attack surface is deliberately broad. The MaaS platform provides lure templates covering taxes, document sharing, bid invitations, meeting requests, government communications, and branded corporate software — meaning virtually any professional sector is a viable target. However, certain industries carry elevated structural risk:
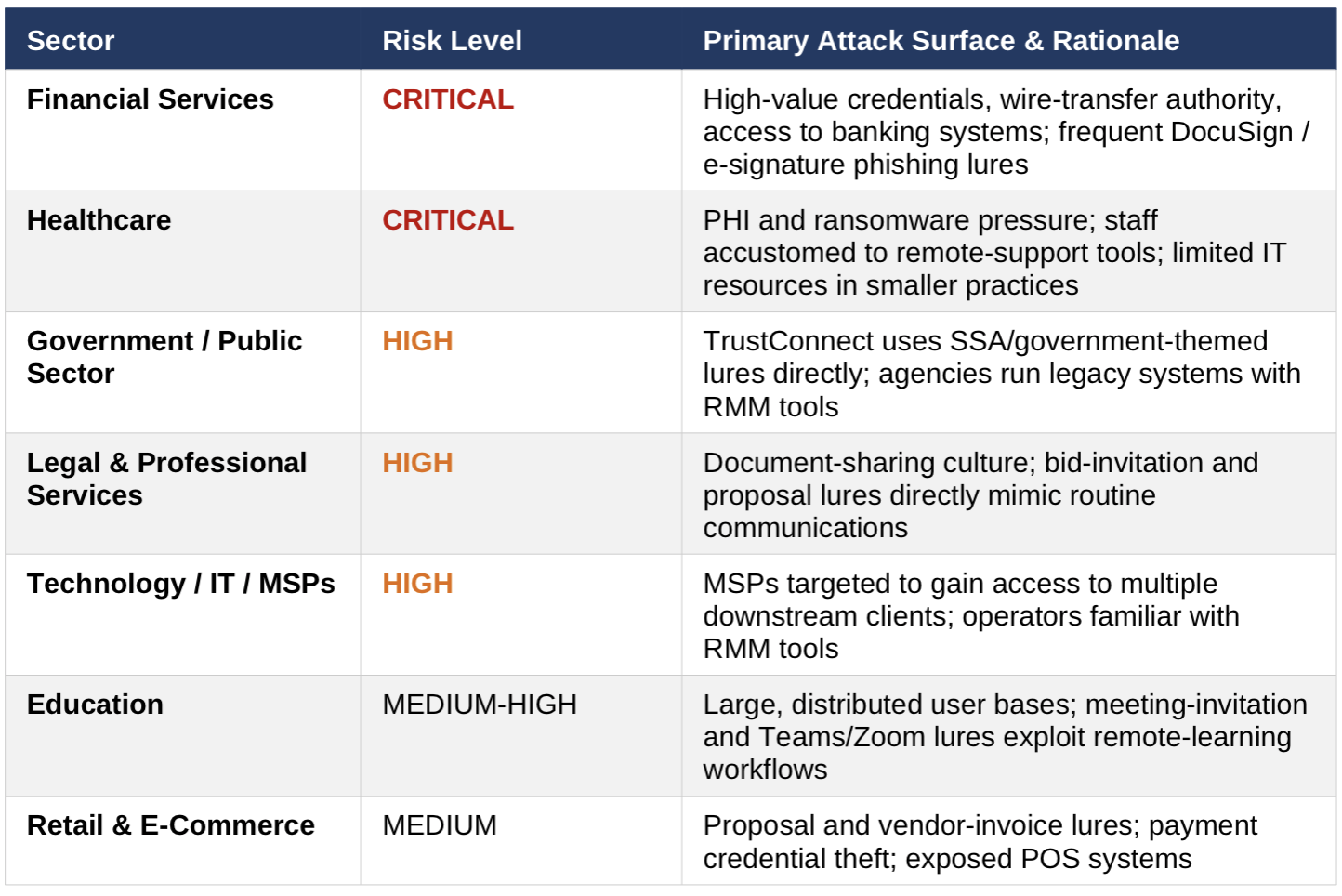 Is your business threatened by TrustConnect?
Is your business threatened by TrustConnect?
The healthcare, financial services, and government sectors are particularly attractive because they combine high-value data, mission-critical uptime requirements (creating ransomware leverage), and workforces accustomed to receiving documents and remote-support requests via email. MSSPs and IT service providers are especially high-value targets because compromising a single MSP can yield access to dozens of downstream client environments.
Reactive defenses are insufficient against an adversary that rebuilds infrastructure within hours and rebrands payloads overnight. Proactive threat intelligence is essential. ANY.RUN's Threat Intelligence Lookup and TI Feeds provide the contextual, continuously refreshed data organizations need to stay ahead of TrustConnect and its successors.
For TrustConnect specifically, TI Lookup enables defenders to:
destinationIP:"178.128.69.245".
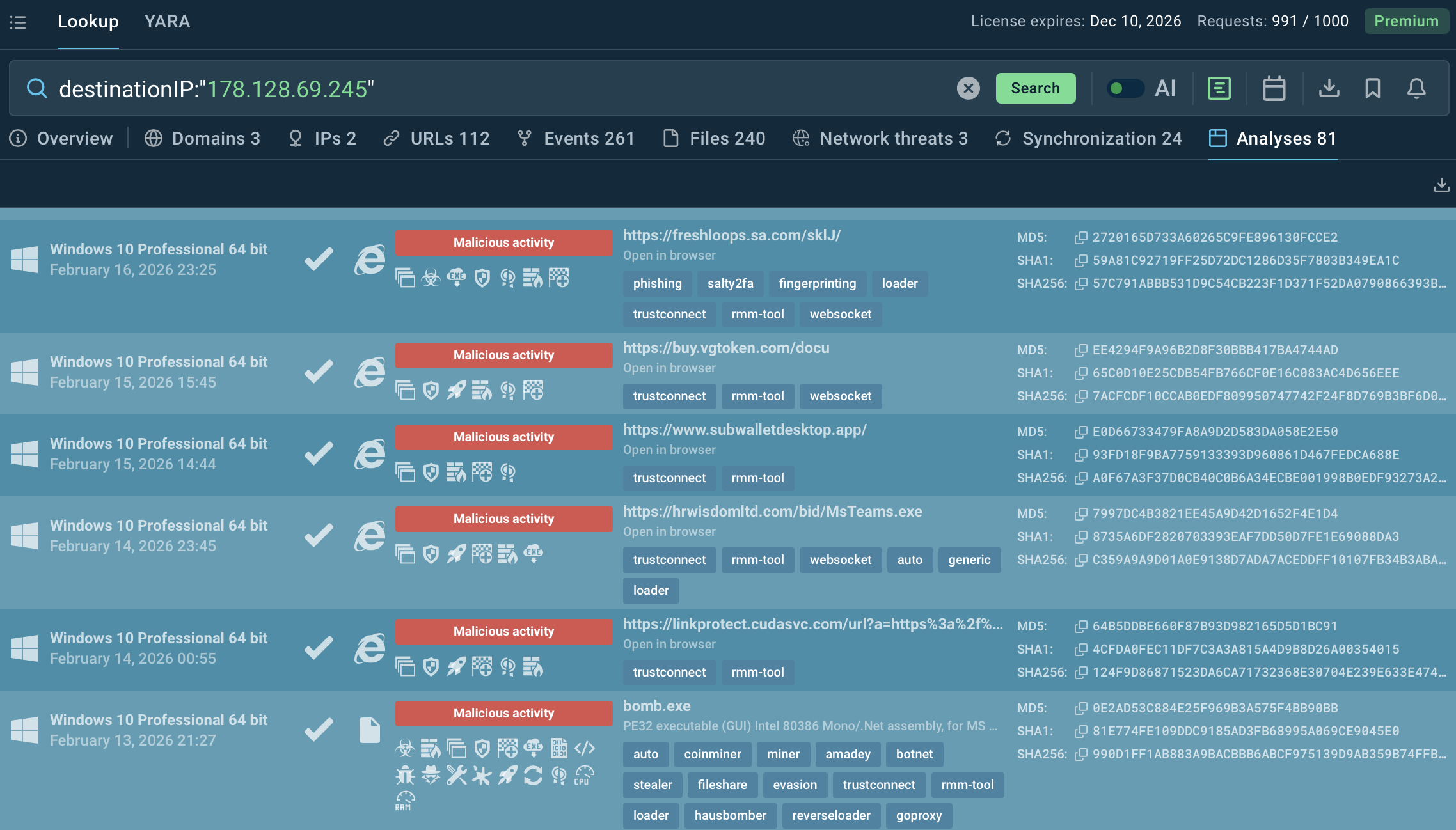 TrustConnect samples using the IP connection
TrustConnect samples using the IP connection
Query file hashes of known TrustConnect installers (MsTeams.exe, AdobeReader-XX.exe, etc.) to determine whether any have been seen in the environment.
Track the evolution of TrustConnect TTPs — including the pivot to DocConnect — before those indicators surface in other intelligence sources.
Search by behavioral artifacts such as the TrustConnectAgent.exe process name, PowerShell command-line patterns, or WebSocket-based screen streaming behavior.
filePath:"TrustConnectAgent.exe".
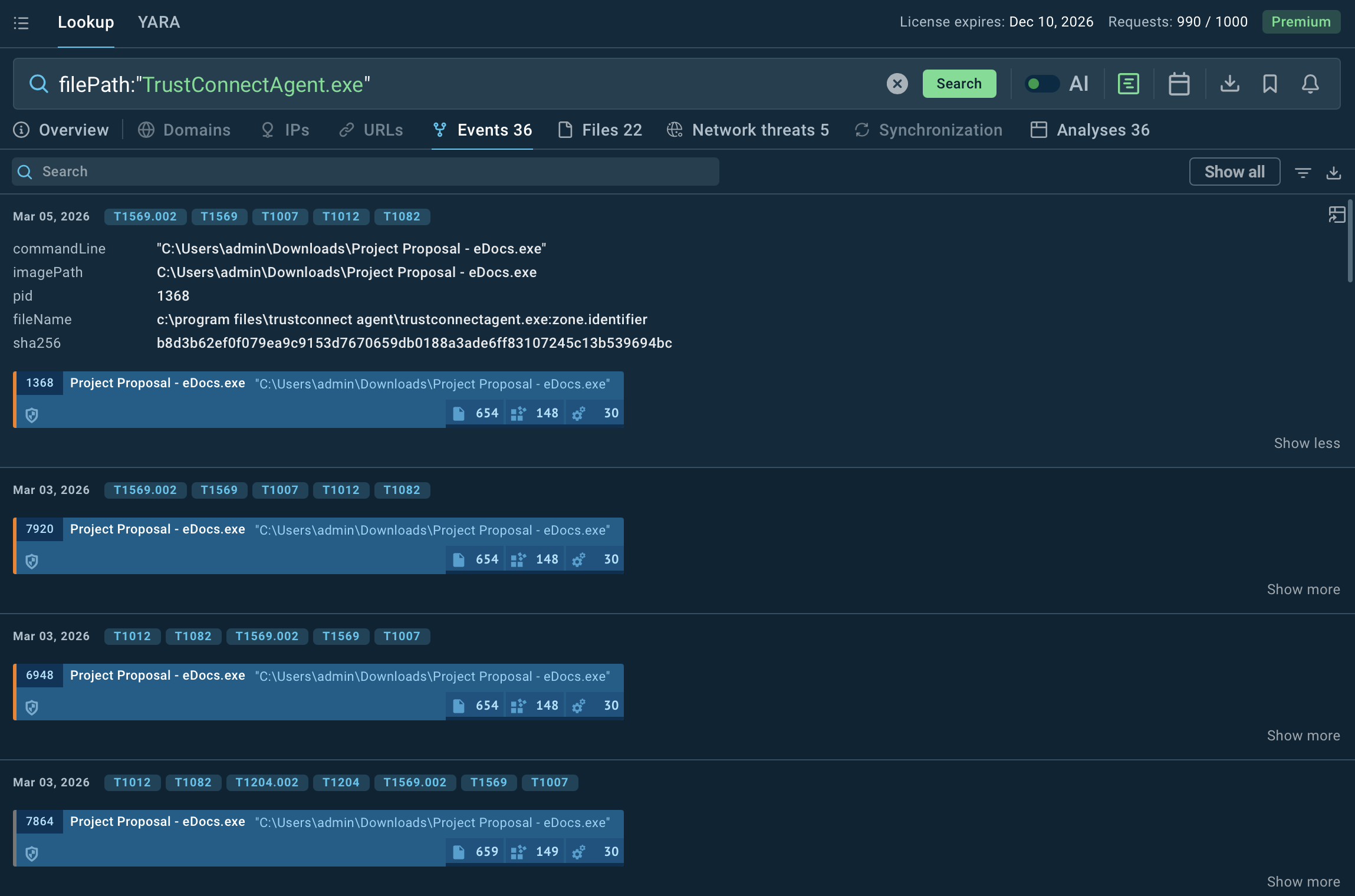 TrustConnect process in sandbox detonations
TrustConnect process in sandbox detonations
ANY.RUN's TI Feeds deliver continuously updated IOC streams — malicious IPs, URLs, domains — in STIX/TAXII format, directly compatible with SIEMs, TIPs, firewalls, IDS/IPS, and EDR platforms. Data is refreshed every two hours, drawn from the same sandbox analysis community and enriched with associated event fields (not just bare indicators) for full operational context. For TrustConnect:
Block known TrustConnect and DocConnect C2 infrastructure automatically in SIEM/firewall rules before an incident occurs.
Receive immediate IOC updates as the operator pivots to new hosting or generates new payload variants.
Use the associated event context — not just IP addresses, but the processes, file paths, and network behaviors tied to each IOC — to write precise detection rules.
Integrate TrustConnect-related indicators into EDR policies to flag execution of renamed or impersonated installer binaries.
Additional Protective Measures
Beyond ANY.RUN's intelligence products, organizations should implement the following defensive controls:
Email security hardening: Deploy advanced email gateway filtering with sandboxed attachment/URL detonation, covering tax, bid, DocuSign, meeting, and government-themed lures.
Application allowlisting: Prevent execution of unsigned or unknown executables in standard user environments; enforce signed binary policies aligned with known good publishers.
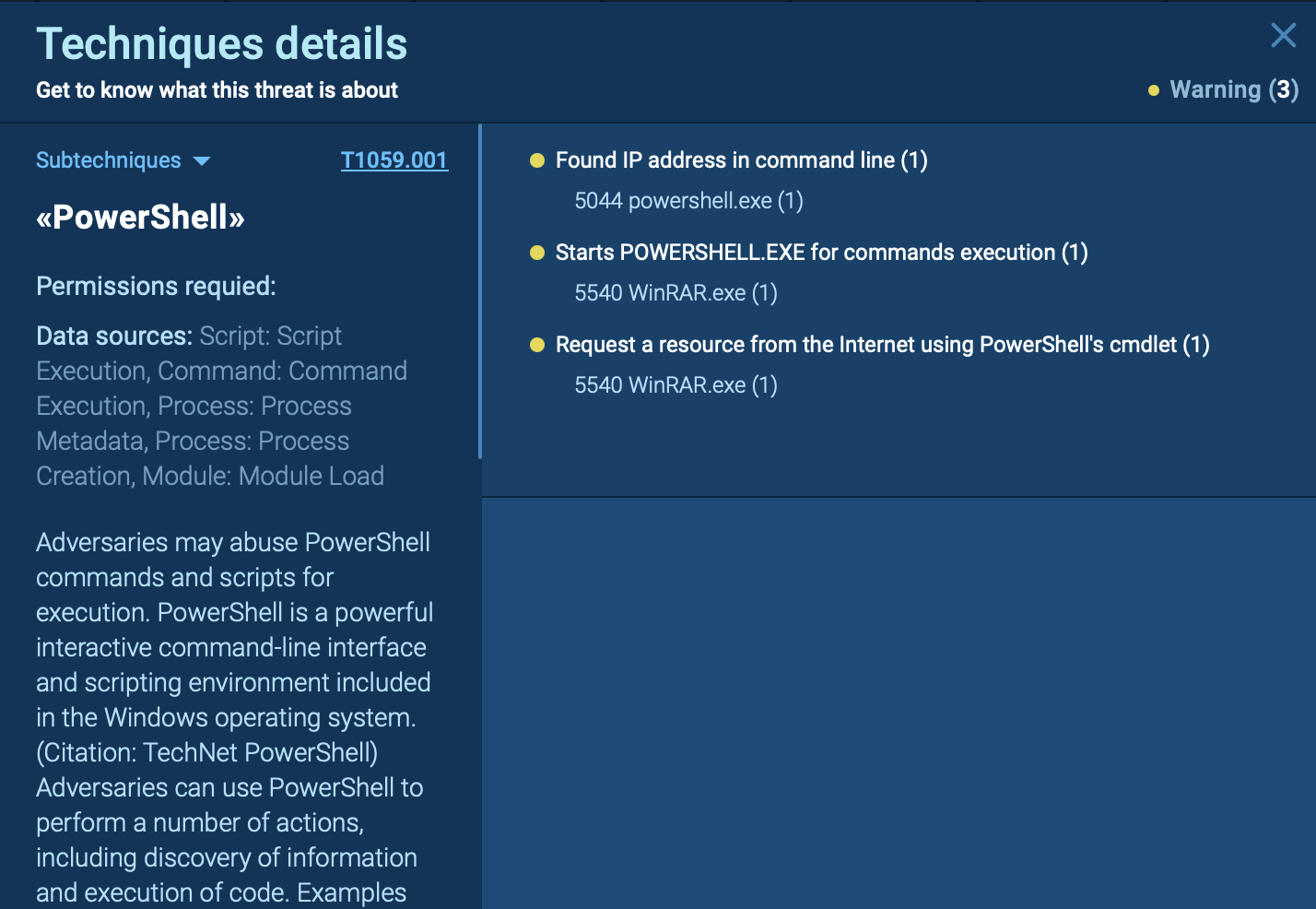
PowerShell restrictions: Implement Constrained Language Mode and script-block logging; alert on PowerShell one-liners consistent with ClickFix deployment patterns.
RMM governance: Maintain a formal inventory of authorized RMM tools; immediately investigate any RMM process not on the approved list.
EV certificate vigilance: Train security teams to understand that EV certificates do not equal trustworthiness — they can be fraudulently obtained.
User awareness training: Run simulated phishing campaigns using the exact lure types TrustConnect employs: meeting invites, bid requests, tax notices, DocuSign.
Network monitoring: Alert on outbound WebSocket connections to unexpected hosts; monitor for anomalous screen-sharing or RDP-over-browser traffic patterns.
Incident response planning: Ensure IR playbooks explicitly address MaaS RAT scenarios with follow-on RMM persistence.
See full execution chain of TrustConnect
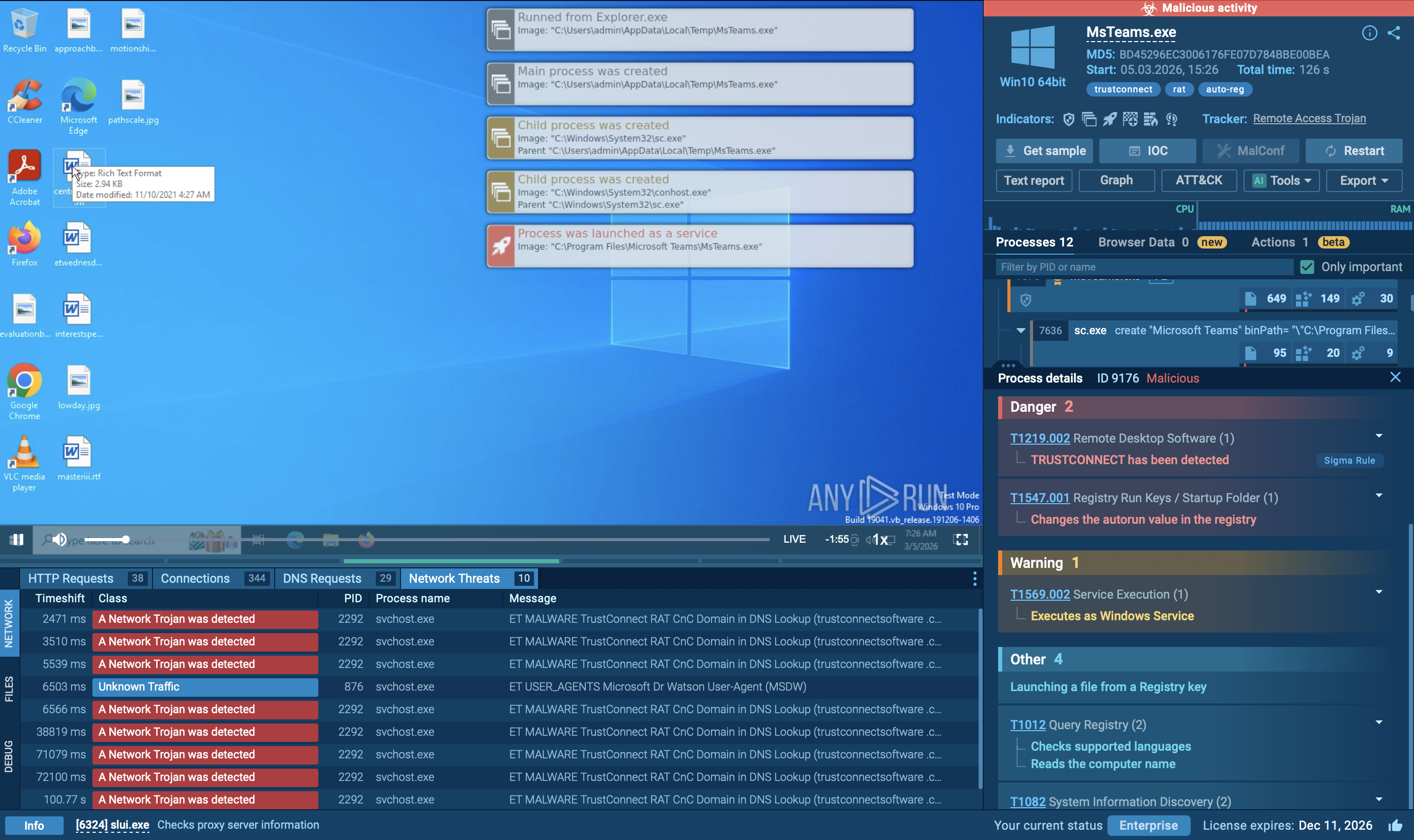 ANY.RUN sandbox revealing TrustConnect behavior in real time
ANY.RUN sandbox revealing TrustConnect behavior in real time
The file is downloaded under the name msteams and is signed by TrustConnect Software PTY LTD.
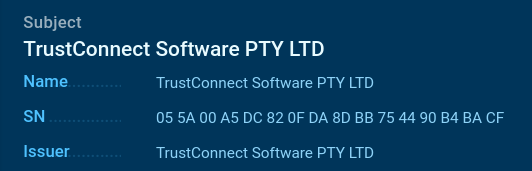 TrustConnect initial file
TrustConnect initial file
The configuration file config.json left by the sample reveals the main operational parameters of the malware. The ApiServer field specifies the C2 server address. The InstallToken and OrganizationId parameters are unique identifiers that link a specific victim to a particular operator in the TrustConnect management panel. The BrandName and ServiceName settings serve as obfuscation parameters.
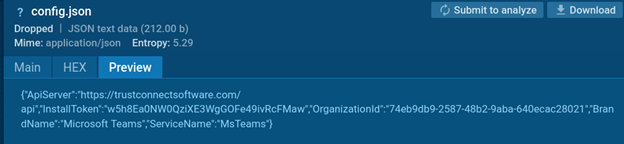 TrustConnect configuration file
TrustConnect configuration file
Next, the malware proceeds to follow this configuration. It copies itself to the folder C:\Program Files\Microsoft Teams\MsTeams.exe. It then registers itself in the Windows registry as an installed program: keys appear in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Microsoft Teams with the publisher listed as TrustConnect Software Ltd, allowing the malware to appear in the list of installed programs as a legitimate application.
At the same time, a Windows service named Microsoft Teams is created with the description “Microsoft Teams – Remote Support Agent.” This service adds the executable to system startup. Event sources TrustConnectAgent and MsTeams are also created in the Windows Application event log.
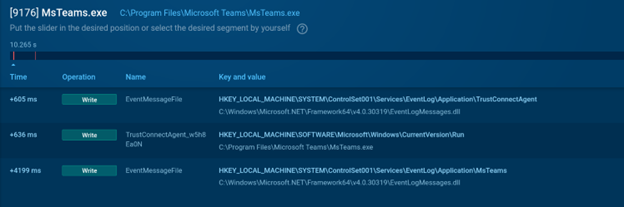 TrustConnect’s registry changes
TrustConnect’s registry changes
Additionally, a large number of connections were observed to 185[.]182[.]187[.]10, which resolves from the domain trustconnectsoftware.com.
TrustConnect demonstrates how cybercriminals are increasingly adopting enterprise-grade tactics to make malware appear legitimate.
By building a fake software company, purchasing a trusted digital certificate, and selling access through a subscription portal, the operators behind TrustConnect blurred the line between legitimate enterprise software and malware.
For organizations, this case highlights a key lesson: trust signals such as digital signatures or professional websites are no longer reliable indicators of safety.
Proactive threat intelligence, behavioral analysis, and strong detection workflows are essential to identifying and stopping threats like TrustConnect before they escalate into full-scale breaches.
Trial TI Lookup to start gathering actionable threat intelligence on the malware that threatens your business sector and region: just sign up to ANY.RUN.