Welcome to our new monthly synopsis of noteworthy malware and security news.
Let’s take a look at what’s been going on.
1. New threat alert: Rhadamanthys Stealer
The newly discovered malware strain is an infostealer that is being distributed through Google Ads phishing campaigns. It collects system data and targets the most popular cryptocurrency wallets.
Google’s advertising network is rapidly turning into a potent malware distribution channel. Despite the ongoing criticism from the cybersecurity community, Google seemingly does nothing to stop its abuse.
2. Malicious Python packages spread malware on Python Package Index (PyPI)
Three malicious packages named “colorslib,” “httpslib,” and “libhttps” were uploaded to Python Package Index (PyPI) repository by a threat actor named Lolip0p.
These packages were downloaded over 550 times before being removed from PyPI. The packages have identical setup scripts that download and run a malicious binary (“Oxzy.exe”) hosted on Dropbox.
The binary triggers the retrieval of another binary called “update.exe,” which is an information stealer and can drop additional malware, one of which is a trojan detected by Microsoft as Wacatac.
The packages were made to look legitimate by including a convincing project description.
3. Attackers hide malware in blank images to bypass the detection
A new phishing scam called the Blank Image Attack has been discovered by Avanan researchers.
The attack sends a blank image in an HTML attachment, which when opened, redirects the recipient to a malicious landing page that delivers malware. The attacker uses a legitimate link from DocuSign to trick the victim into trusting the email and its attachments.
The blank image contains an encoded JavaScript that bypasses antivirus services and redirects the victim to the malicious link. To avoid this attack, users should avoid opening .htm attachments to block HTML attachments.
Try ANY.RUN for Enterprises
Combat new threats together – ANALYZE MALWARE IN A TEAM
4. Google Ads phishing attacks target password managers
Reports indicate that malicious actors are running Google Ads phishing scams, targeting popular password management software. They’re after users’ master passwords.
Master passwords are used to encrypt credentials stored in online “password vaults”, which hold sensitive login data online to make it accessible from multiple devices. Getting access to the master password grants attackers full control over the vault.
Security breaches at LastPass and Norton have already shown just how effective such attacks can be.
5. Windows 11 now protects users from themselves
Smart App Control is a new safety feature that was added to Windows 11 in January. It is designed to block untrusted apps from running or files to be opened.
When a user clicks on a potentially malicious app, windows will now show a pop suggesting that the application may be unsafe. Only time will tell if Microsoft’s implementation will prove effective or if it evolves into scareware, similar to Apple’s implementation on Mac OS.
For now, the feature is available for testing to select users.
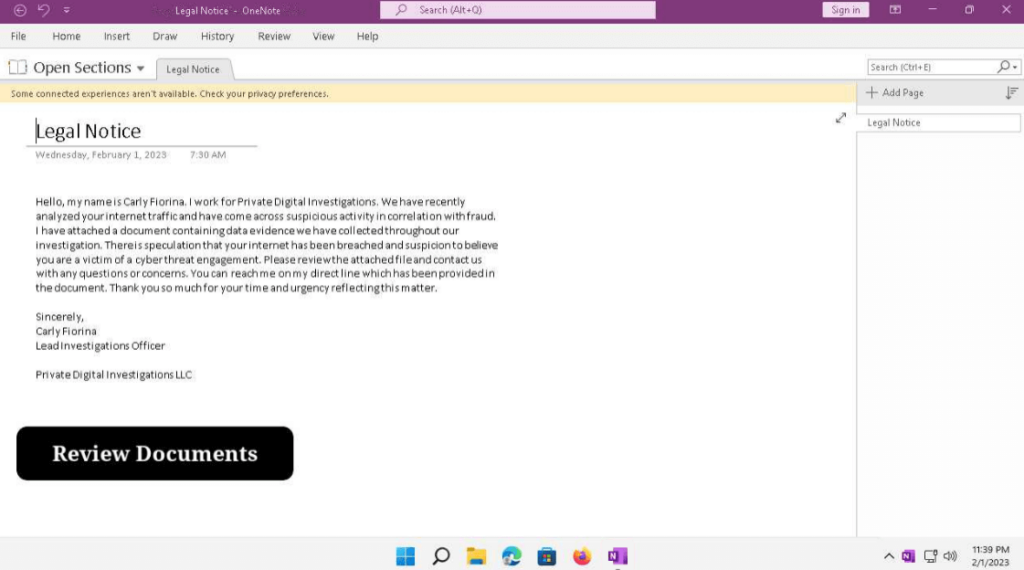
6. OneNote maldocs usage spiked in January
We’re seeing a spike in OneNote maldoc usage lately and crooks using different lures, such as Office365 and blurred documents. We found a fresh maldoc with “Legal Notice” lure which download Redline as a payload. Check out this task in ANY.RUN to see it in action.
ANY.RUN’s January updates
Deep malware analysis from our analyst team, the history of the most preventable ransomware, the most effective ways to use virtualization to provide additional security, and trends of the last year and ANY.RUN achievements in 2022 – ANY.RUN Blog is ready to share its own digest.
January gave us an amazing starting point with these posts:
- Annual Report 2022: trends of the last year and ANY.RUN achievements in 2022.
- 5 Ways Virtualization Can Improve Security: most effective ways to use virtualization to provide additional security.
- WannaCry: the history of the most preventable WannaCry ransomware.
- CryptBot Infostealer: deep malware analysis from our analyst team.
Wrapping up
What kind of posts are you looking forward to in February?
- Malware analysis
- Lifehacks
- Malicious history
Or suggest your idea in the comments!
1 comments








I have learn a few excellent stuff here. Definitely value bookmarking for revisiting. I surprise how much attempt you set to create one of these magnificent informative site.