What is Remcos trojan?
Remcos is a remote access trojan – a malware used to take remote control over infected PCs. This malicious software has been operational since 2016 when it first became available for sale in the underground hacker communities on the dark web.
Remcos RAT has been receiving substantial updates throughout its lifetime. In fact, this malware is being maintained extremely actively, with new releases coming out almost every month. In April 2019, the malware was available for purchase for as little as just over 60 dollars up to over 400 dollars depending on the selected package.
General description of Remcos trojan
This trojan is created and sold to clients by a “business” called Breaking Security. Although Breaking Security promises that the program is only available to those who intend to use it for legal purposes, in reality, Remcos RAT gives clients all necessary features to launch potentially destructive attacks. The malware can be purchased with different cryptocurrencies. The program can remotely control PCs with any Windows OS, including XP and newer. It can also capture screenshots, record keystrokes on infected machines, and send the collected information to host servers.
What’s more, it comes equipped with a crypto program that enables the malware to stay hidden from antivirus software. In fact, Breaking Security has released a video on its YouTube channel which demonstrates the analysis of how multiple antiviruses fail to detect the presence of the Remcos RAT. In addition, Breaking Security provides attackers with a keylogger that can be used to remotely record keystrokes of the victim, a mass mailer program that can be used to carry out distribution campaigns, and a DynDNS service with a client-server connection. With all additional services combined, purchasers gain all they need to create their own functioning botnets.
The company responsible for selling Remcos RAT to the criminals is registered in Germany. Germany is the only country out of all European Union members that do not allow looking up company details online. Therefore founders of Breaking Security are still not identified. The website itself does not provide any information about the company or the team behind Remcos. The domain name of the website itself is hosted on Cloudflare, and all information related to it is protected by the privacy policy of the hoster organization. Clearly, the people behind Breaking Security have taken a lot of effort to stay anonymous.
Remcos malware analysis
Remcos RAT execution and analysis can be watched in-depth in a video recorded in the ANY.RUN malware hunting service. Moreover, you can also research other malicious families there such as AZORult and Adwind.
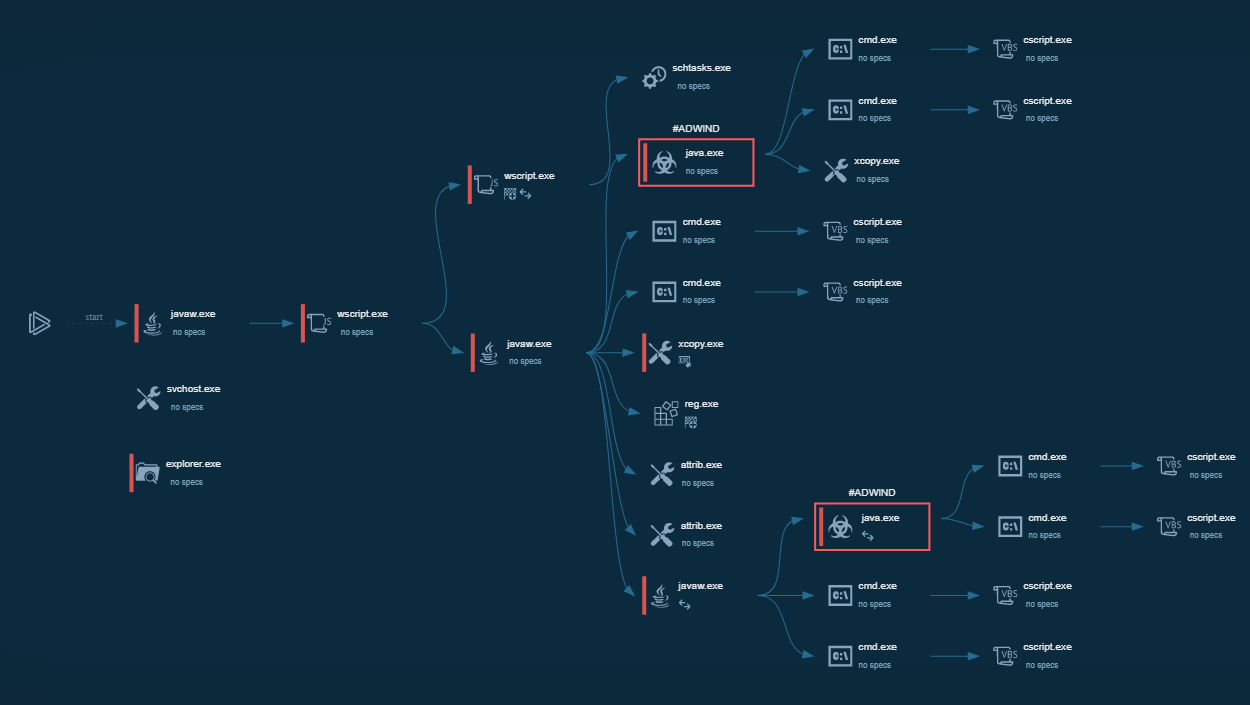
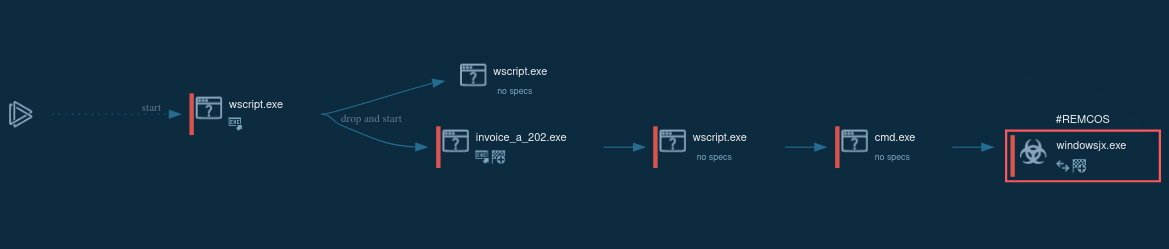 Figure 1: Displays the lifecycle of Remcos as presented by a visual graph generated by ANY.RUN
Figure 1: Displays the lifecycle of Remcos as presented by a visual graph generated by ANY.RUN
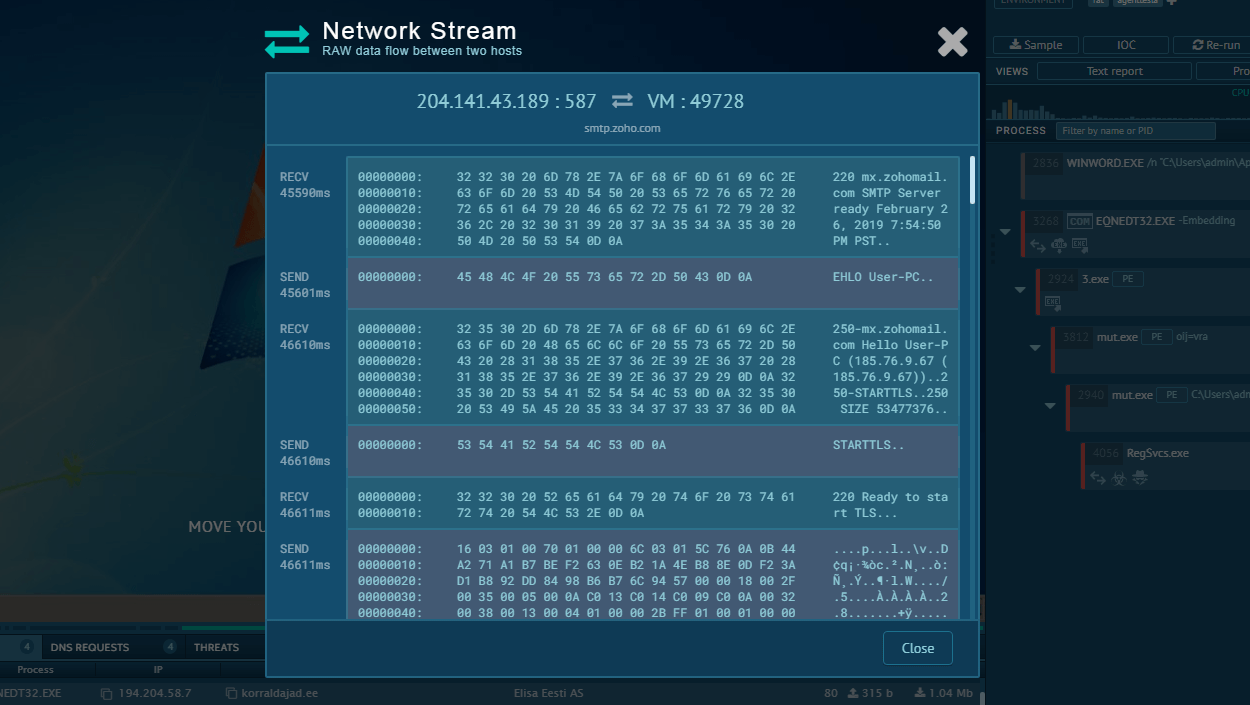
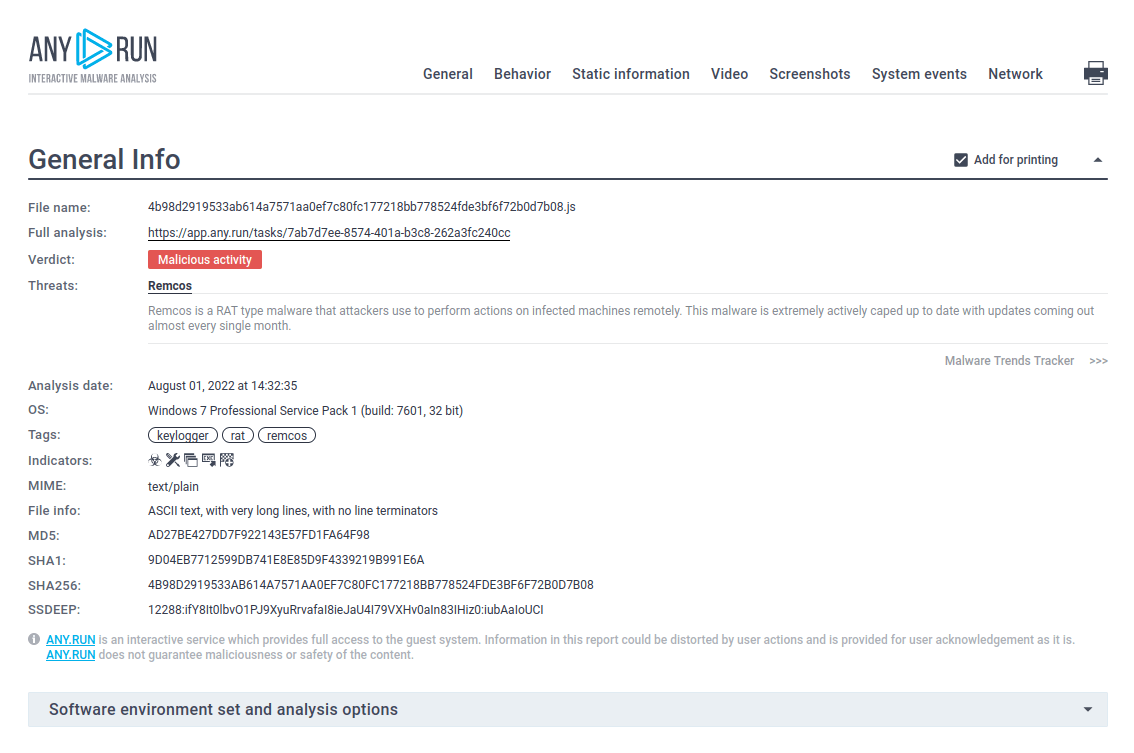 Figure 2: A customizable text report generated by ANY.RUN is a feature specifically developed to simplify the sharing of analysis results.
Figure 2: A customizable text report generated by ANY.RUN is a feature specifically developed to simplify the sharing of analysis results.
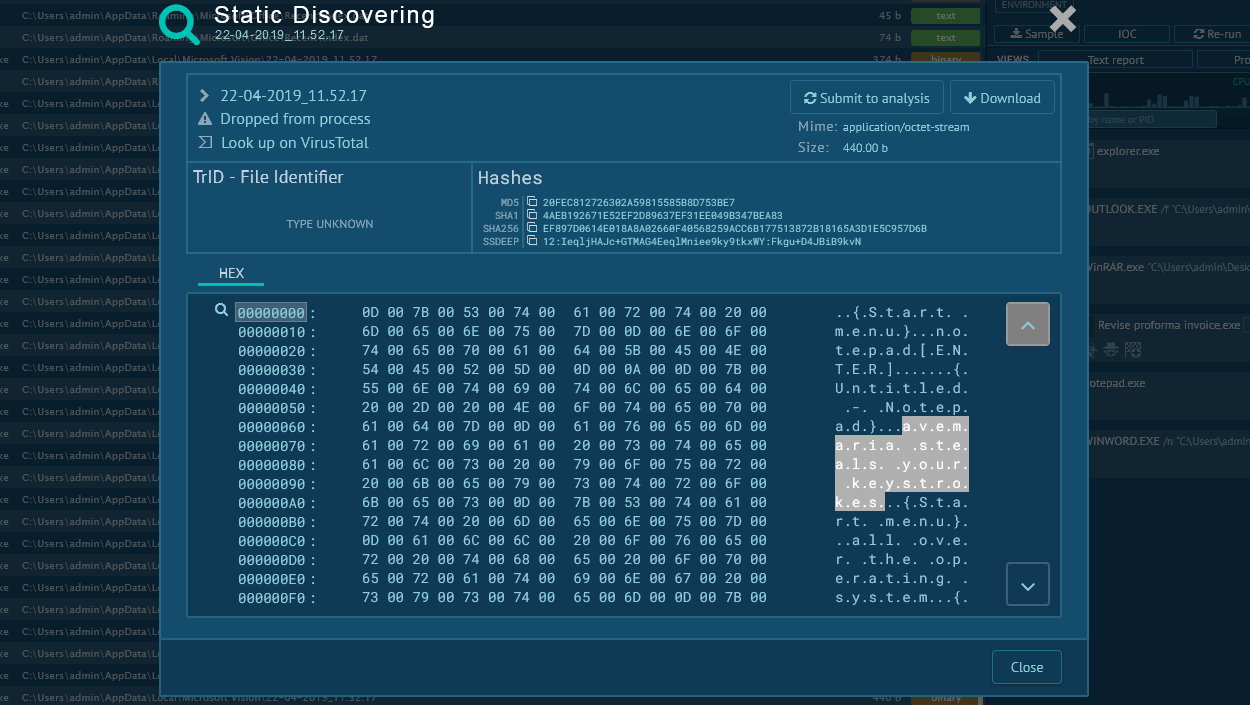
Remcos trojan execution process
Remcos trojan can be delivered in different forms. Based on RAT's analysis, it can be spread as an executable file with the name that should convince users to open it, or it pretends to be a Microsoft Word file that exploits vulnerabilities to download and execute the main payload, obfuscate the server component. In our analysis, after Remcos made its way to infect the device and begin the execution process, it started VBS script execution. Script ran command line and proceeded to drop an executable file from it. This file was the main payload, and it carried out the main malicious activities – stealing information, changing the autorun value in the registry, and connecting to the C2 server.
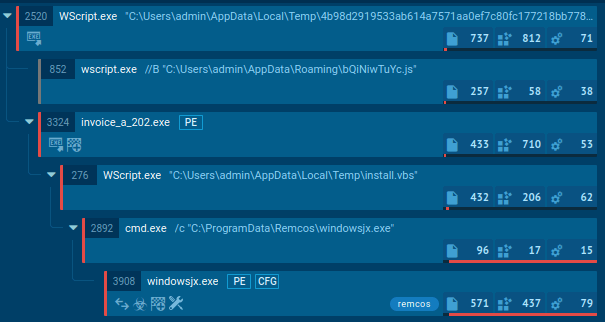 Figure 3: Execution processes of Remcos as displayed by the ANY.RUN malware analysis service
Figure 3: Execution processes of Remcos as displayed by the ANY.RUN malware analysis service
Distribution of Remcos
Although being distributed using multiple methods, being provided in a bundle with mass mailer software, the analysis proves that Remcos RAT usually gets into victims’ machines through malicious attachments in spam email campaigns. The attackers normally use phishing techniques to try and trick users into downloading file attachments, commonly – contaminated Microsoft Office files. Once downloaded, the files would prompt the users to activate the macros required for the execution of Ramcos to start.
Attackers who utilize this trojan are known to target specific organizations and sometimes go a long way to craft custom phishing emails designed to fool their victims. Corporations that are known to become targets of Remcos attacks include news agencies and businesses energy industry-related businesses.
If the victim does enable the macros, they reconstruct a small executable file which is then dropped to a pre-specified location and launched from there. This file then proceeds to download the main payload, which is Remcos itself, from a control server and then begin the execution process. Even though the location can vary from sample to sample, it usually includes one of the following locations, typical for malware creators: %APPDATA% and %TEMP%.
How to detect Remcos using ANY.RUN?
Cybersecurity specialists can easily detect Remcos – the trojan writes its name into a registry. Look at registry events: click on the process and then on the More Info button. If the Registry changes tab has a key like "HKEY_CURRENT_USER\Software\Remcos-{digits_letters}", you can be sure it’s Remcos.
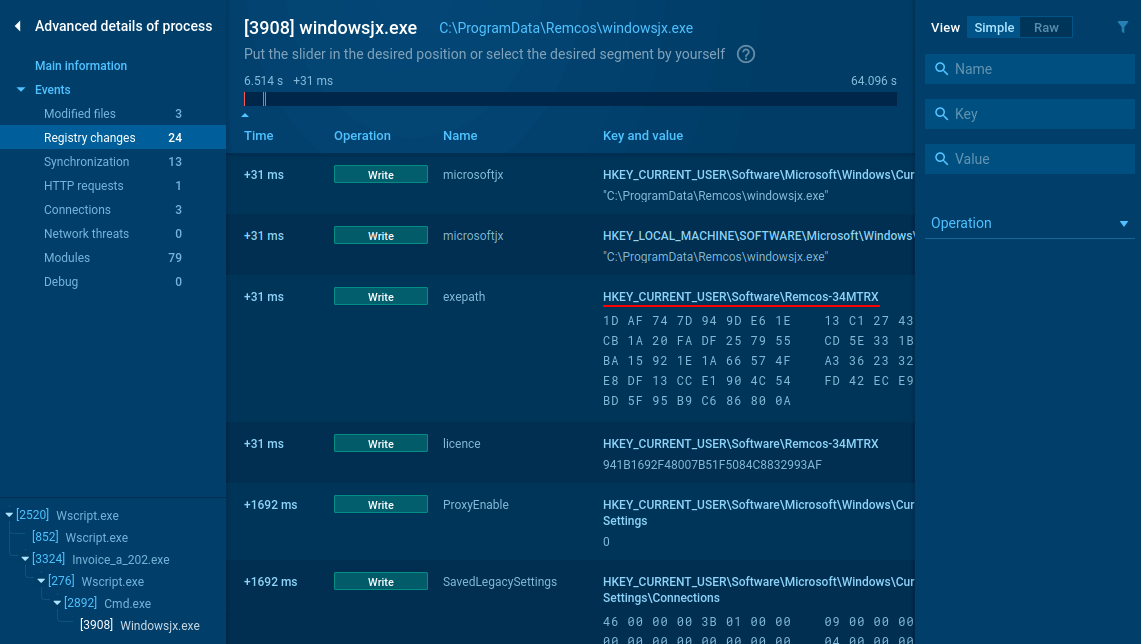 Figure 4: Remcos registry changes analysis
Figure 4: Remcos registry changes analysis
Conclusion
Remcos RAT is a dangerous trojan available to attackers for a relatively low price. Despite its accessibility, it comes equipped with enough robust features to allow attackers to set up their own effective botnets. What's more, it is modernized with updates released nearly every month by the owner company. Accessibility and powerful feature set helped to make Ramcos into a powerful and dangerous trojan.
Thankfully, malware hunting services such as ANY.RUN gives professionals an equally robust feature set to research threats like Ramcos and respond with effective countermeasures.



 0
0