What is Gh0st RAT malware?
Gh0st RAT is one of the long-standing members of the global threat landscape. Launched in 2008, it remains in full operation to this day. The RAT part in the malware’s name stands for Remote Access Trojan, meaning that it provides attackers with the capacity to control the victim’s machine and manipulate it.
The original developers of Gh0st RAT were from China. However, due to the open-source nature of its code, criminals from many other countries have created their iterations of the malicious software. As a result, there are many versions of this trojan with varying sets of features.
If you're interested in exploring variants of Gh0st, we recommend reading our article about Gh0stBins, Gh0stBins, Chinese RAT: Malware Analysis, Protocol Description, RDP Stream Recovery.
The most notable aspect of Gh0st RAT is that it has been utilized by criminal groups linked to the Chinese government. For instance, in 2009, the malware was used to target Tibetan organizations. There were also instances of attacks on businesses in various fields, including healthcare and banking.
Technical details of the Gh0st RAT malicious software
The standard set of features of Gh0st RAT includes the following:
- Mouse and keyboard manipulation: The malware can record the keys that a user presses on their keyboard, as well as the movements of the mouse. Thus, attackers can discover passwords and other credentials used by the victim. It also can disable these devices.
- Screenshot and webcam capturing: Gh0st can take a picture of the user's computer screen and webcam. This is often employed by threat actors to conduct surveillance.
- Microphone recording: The malware is also capable of listening to the user's microphone.
- File system access: The RAT can transfer files between the infected computer and its remote server. Subsequently, it can both steal sensitive information and drop additional malware, as well as execute it and run programs or scripts.
- System reboot: It can restart the system to gain persistence and shut it down completely to prevent the victim from attempting to mitigate the threat.
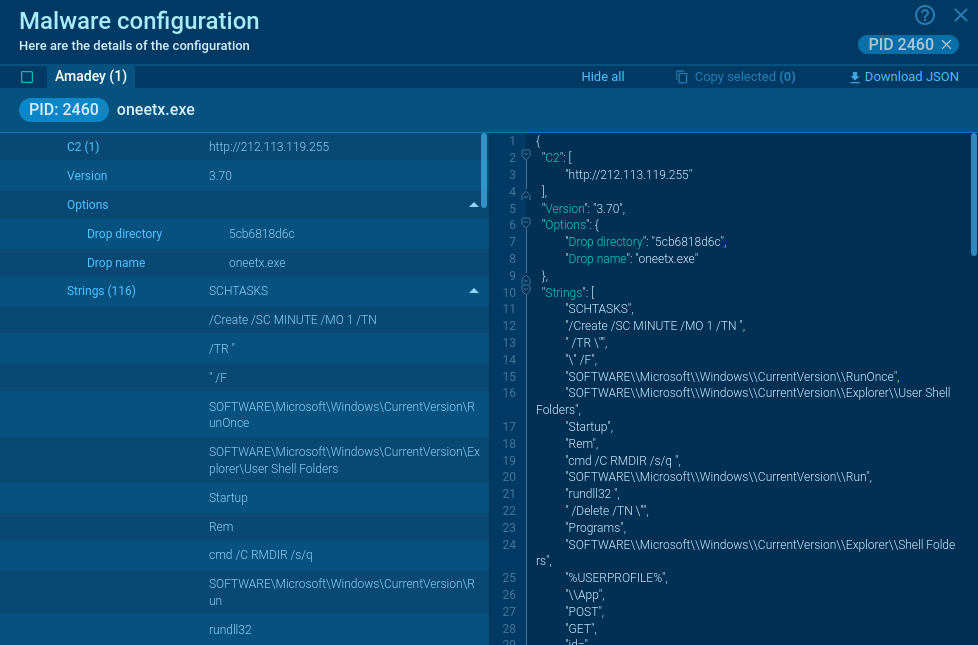
To persist on the system, Gh0st RAT adds registry entries that allow it to automatically execute itself on every system startup. The malware can scan the system to determine if it is running inside a virtual machine and if antivirus software is installed. These actions help it hide its behavior from security analysts and avoid detection. It also utilizes encryption to obfuscate its functions.
Essentially, Gh0st operates similarly to other RAT malware families, such as njRAT and DCrat.
Execution process of Gh0st RAT
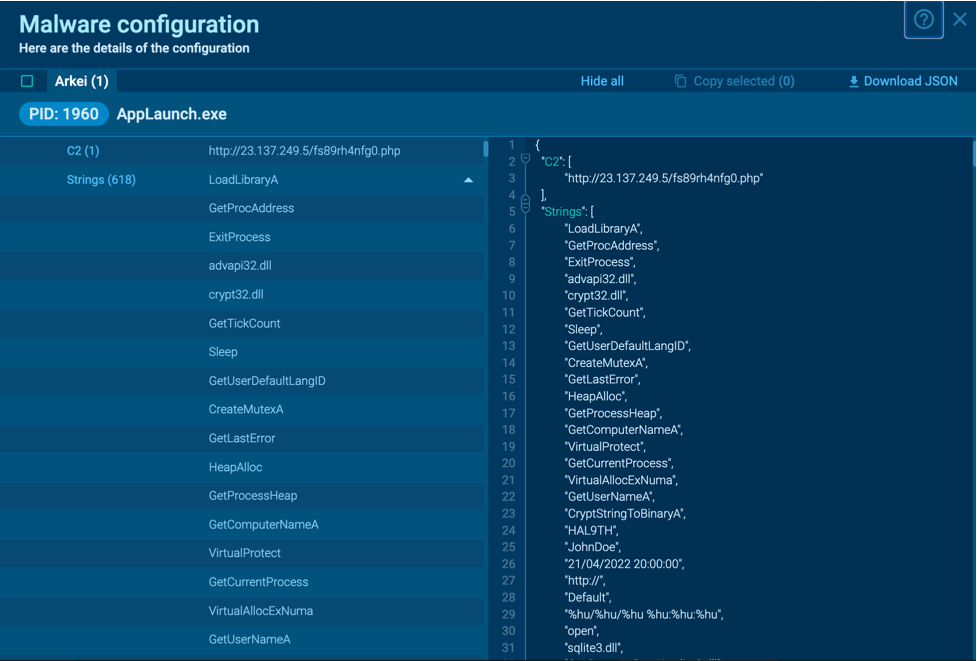
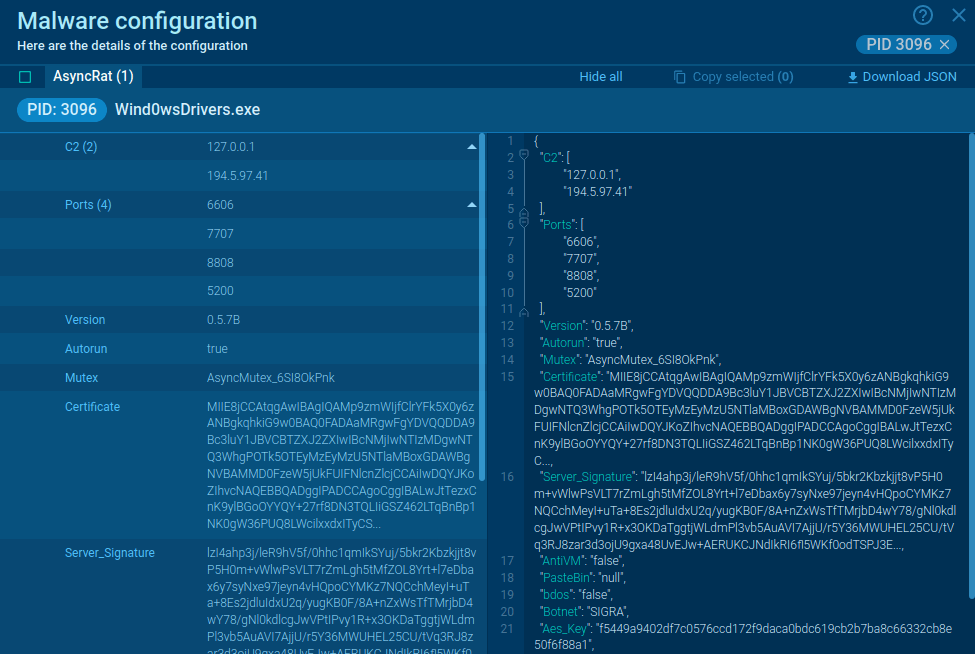
By uploading a sample of Gh0st RAT to ANY.RUN, an interactive sandbox for malware analysis, we can observe its malicious processes in detail and collect IOCs.
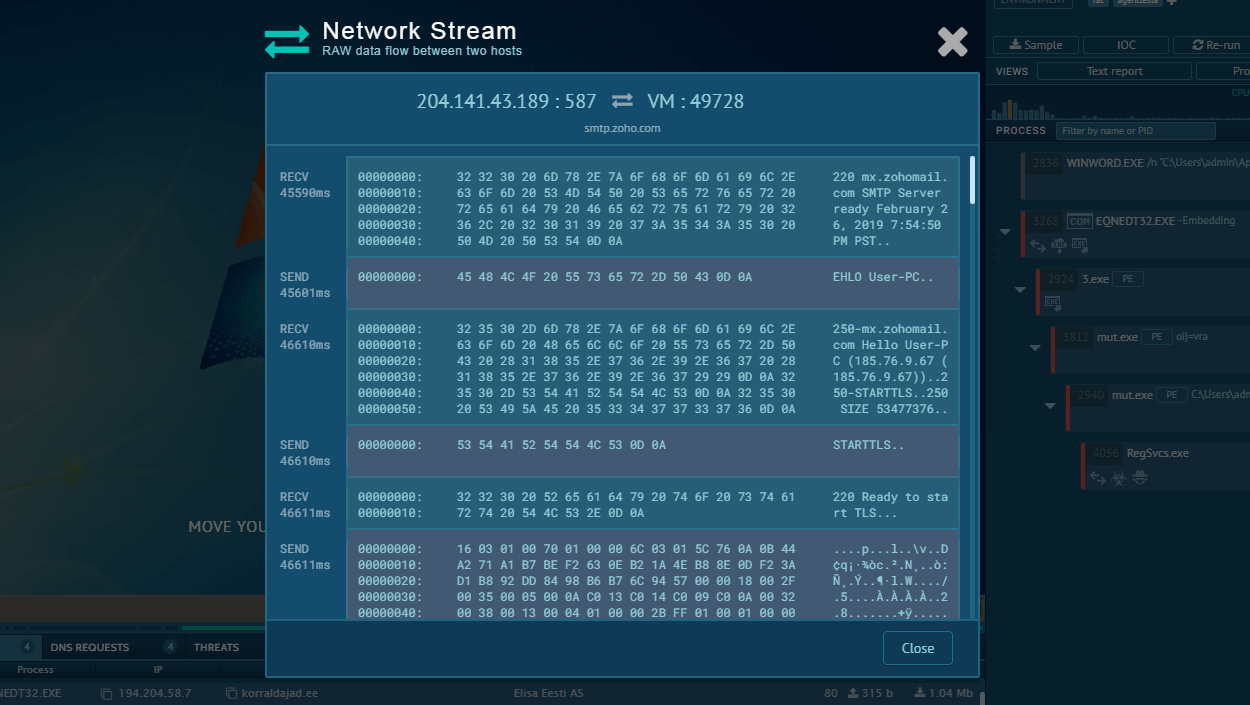
The execution process of the Gh0st Stealer typically begins with a user inadvertently downloading or executing a malicious file, often disguised as legitimate software or attached to phishing emails. Once executed, the malware establishes a connection to a remote command and control (C2) server, allowing the attacker to remotely control the infected system. This malware utilizes various system tools for execution, such as CMD in our example.
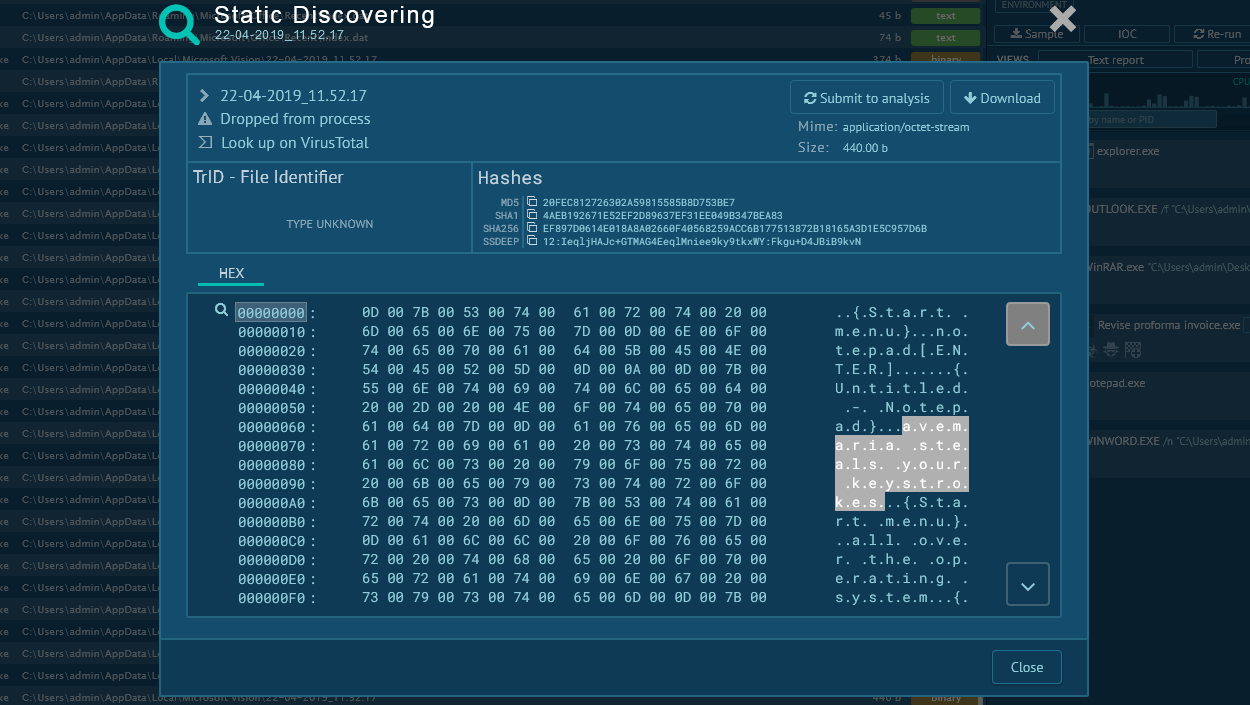
Gh0st Stealer then begins its data theft operations, scanning the system for sensitive information such as usernames, passwords, and financial data. Captured data is exfiltrated back to the attacker's server, where it can be used for malicious purposes or sold on the dark web. The malware may also maintain persistence on the compromised system, allowing for continued data theft and remote control capabilities. In our task stealer use steganography techniques in order to prevent the detection of hidden information – It hides an encrypted DLL file inside a downloaded JPEG image.
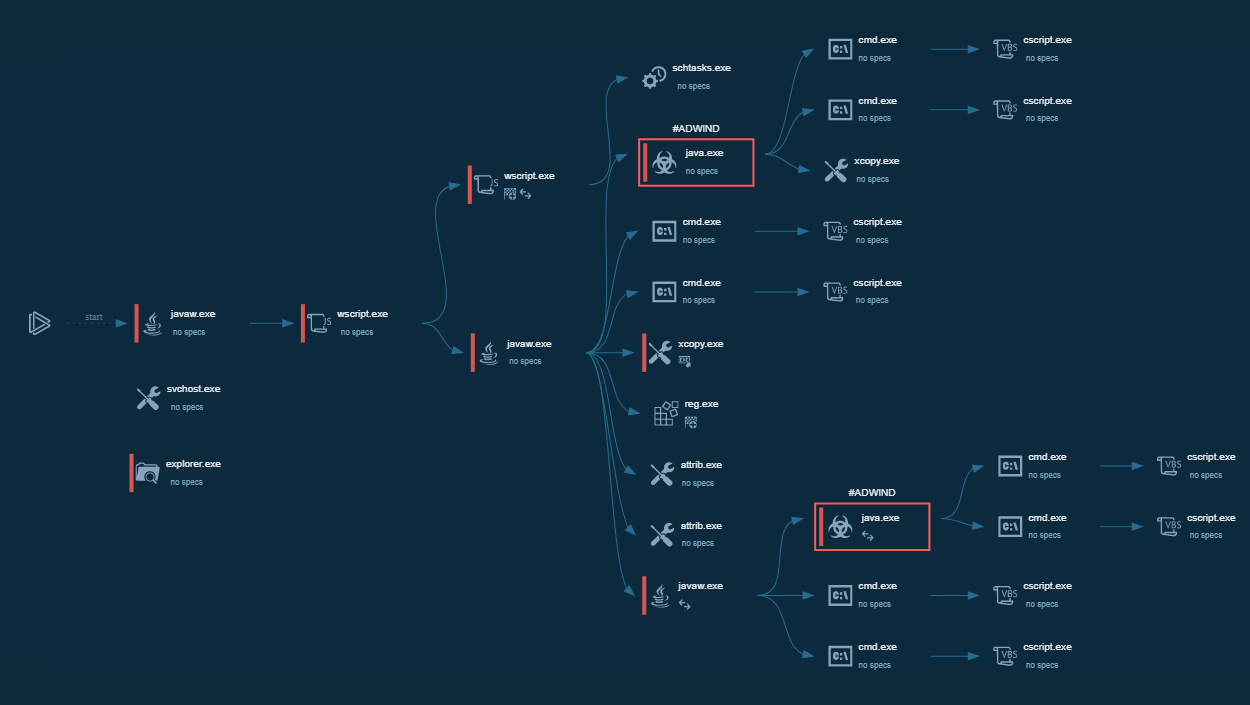
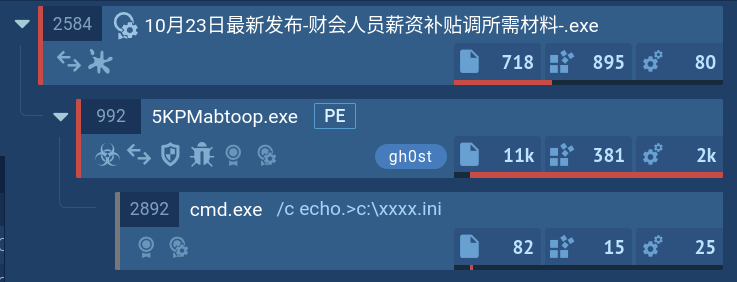 Gh0st process tree demonstrated in ANY.RUN
Gh0st process tree demonstrated in ANY.RUN
Distribution methods of the Gh0st RAT malware
As mentioned earlier, Gh0st RAT is often used in targeted campaigns against government organizations and businesses. In order to carry out them successfully, attackers implement the method of spear phishing.
This involves composing emails that are similar to those sent by legitimate entities to trick the victim into downloading a malicious attachment or clicking on an unsafe link.
Conclusion
Gh0stRAT is a veteran RAT with an open-source code that continues to be used by both individuals and organized groups in attacks around the world. Due to the fact that phishing campaigns constitute the key starting point of infection, businesses need to exercise extra vigilance when handling suspicious emails.
By analyzing all files and emails from unknown senders in ANY.RUN, companies can quickly identify whether they were targeted by criminals. The service offers conclusive verdicts on the malicious activities of samples and generates comprehensive reports, containing IOCs and configs to ensure future detection.
Try ANY.RUN for free – request a demo!



 0
0