What is Ficker Stealer malware?
Ficker Stealer is a type of malicious software written in the Rust programming language, which is openly sold on the internet via the Malware-as-a-Service (MaaS) model. Its primary function is to extract confidential data from computers running Windows operating systems. Due to its modular design, the malware can be easily configured to steal specific forms of data. For instance, some of the common types of information targeted by it include passwords, Windows Credential Manager data, crypto wallets, credit card details, and email and chat content.
The malware has been active since 2020 and continues to receive full support from its developers to this day. In fact, it possesses the capability of self-updating, allowing it to automatically get fresh updates from the C2 server. Although the original creators of Ficker Stealer remain unidentified, it is likely that they hail from one of the ex-USSR countries.
Technical details of the Ficker Stealer malicious software
Ficker Stealer sets itself apart from other stealers such as RedLine or Arkei by utilizing Rust, a programming language that offers improved performance and safety features compared to its predecessors such as C++. Rust's efficiency helps criminals develop more complex malicious programs, while its built-in safety mechanisms prevent various vulnerabilities within the code. As a result, identifying and combating Rust-based malware can be a tall order for researchers.
Ficker Stealer is engineered to illicitly extract confidential data from a victim's computing system. Once executed, it deploys an array of sophisticated techniques to collect sensitive information, including:
- Keylogging: It records the victim's keyboard input to obtain passwords and other confidential data.
- Browser tracking: it is capable of tracking users’ browser activities and harvesting information such as login credentials, autocomplete data, cookies, and browsing history.
- Process injection: Ficker can inject itself into legitimate processes within the victim's system, gaining access to protected parts of the system.
- File extraction: The malware can be configured to gather various files from the compromised machine.
- Loader functionality: Attackers can utilize the malware to drop and execute other malicious programs.
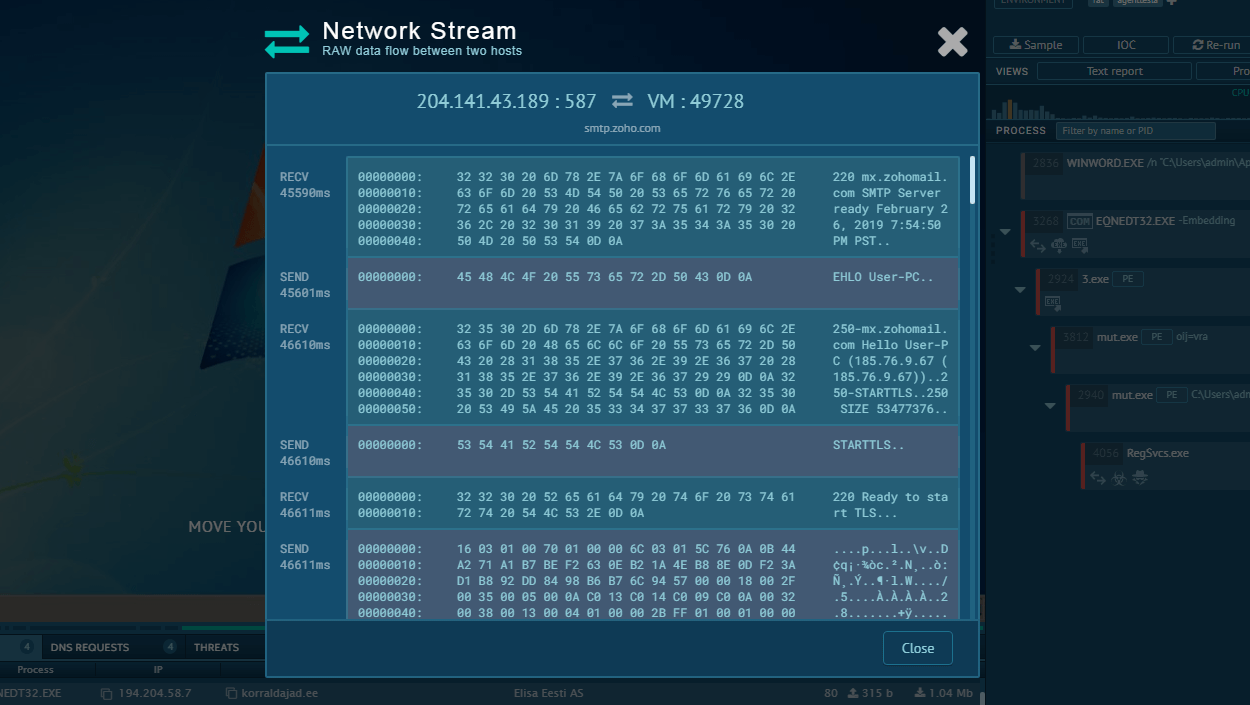
Additionally, to safeguard the data transferred to its C2 from being intercepted, Ficker Stealer utilizes encryption. What’s more, it reports back to the attackers following each successful operation, leaving no records or logs on the target computer. Subsequently, tracking Ficker's activities can be an intricate task. It also operates without the need for any extra DLLs to be downloaded or loaded at runtime, which enhances its stealth and efficiency.
Execution process of Ficker Stealer
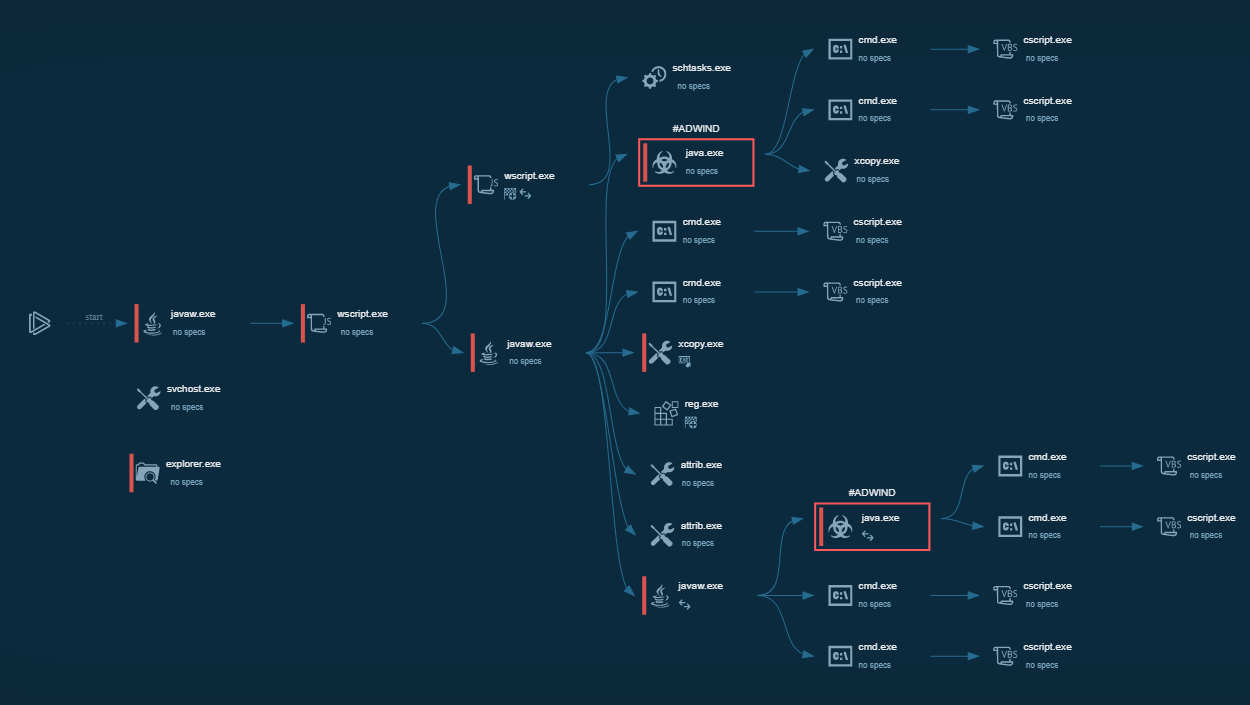
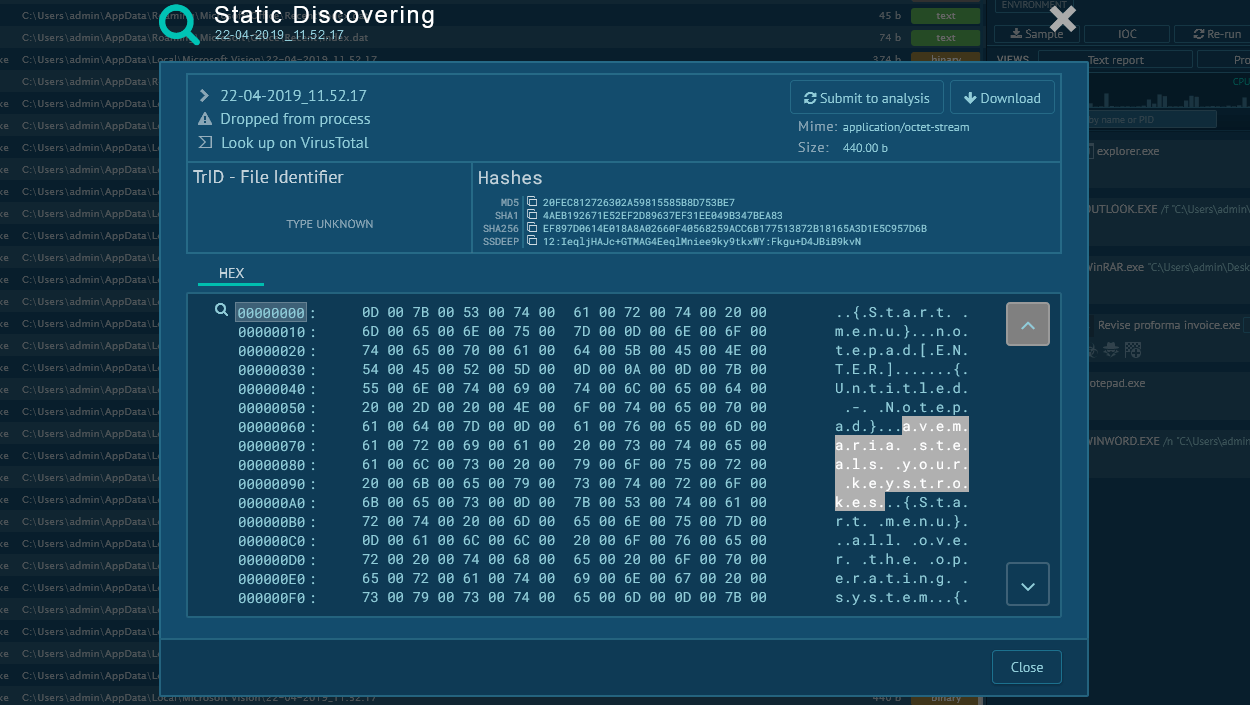
The malicious behavior of Ficker Stealer can be easily uncovered by uploading it to the ANY.RUN sandbox. Here is a sample of this malware on the platform.
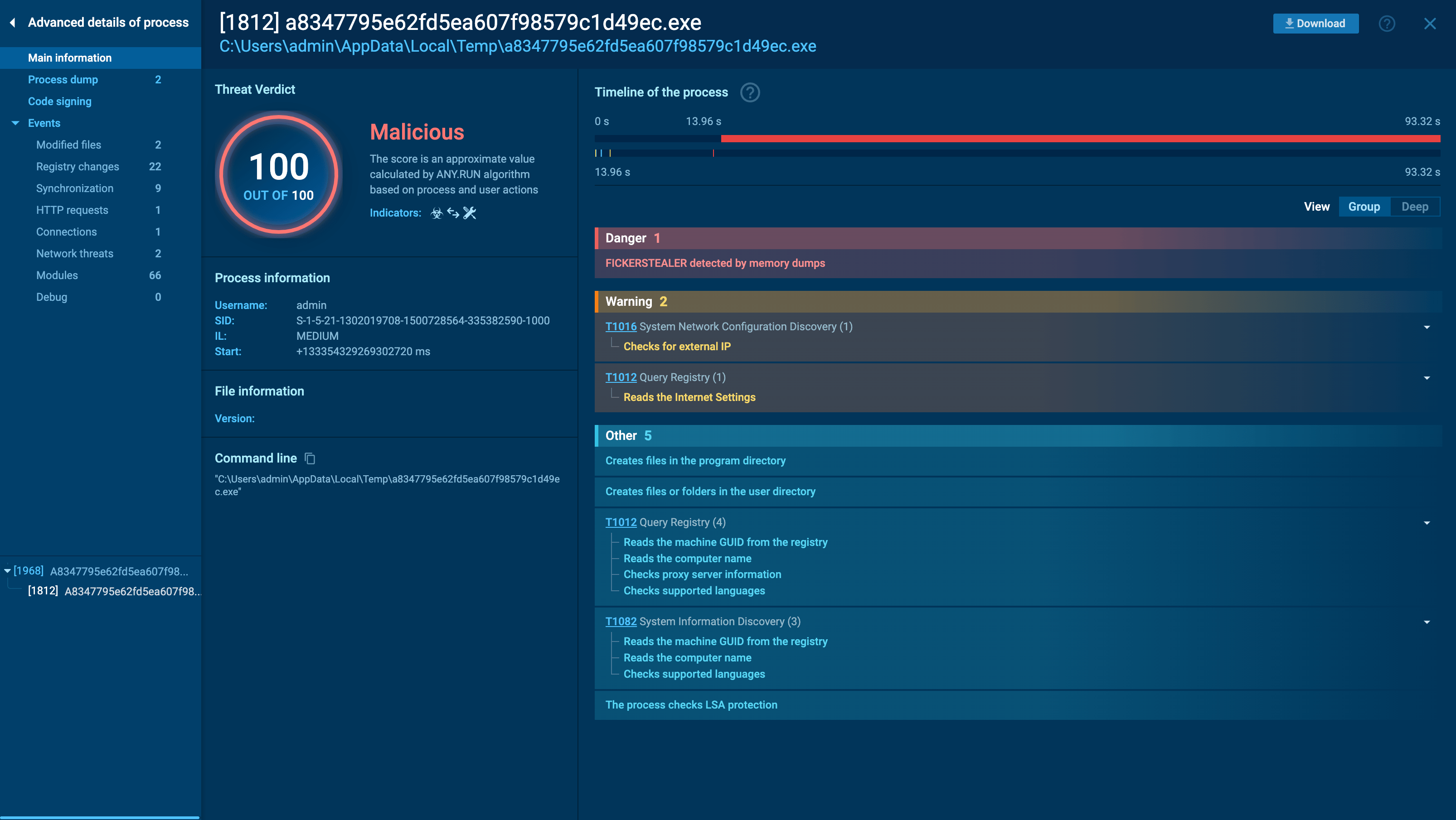 Ficker Stelaler in ANY.RUN
Ficker Stelaler in ANY.RUN
Ficker is a typical representative of the stealer malware family. It creates as little noise as possible in the infected system. The main idea: make its way into the system, start execution, steal information and credentials and try to stay invisible without alerting security solutions about the threat for as long as possible.
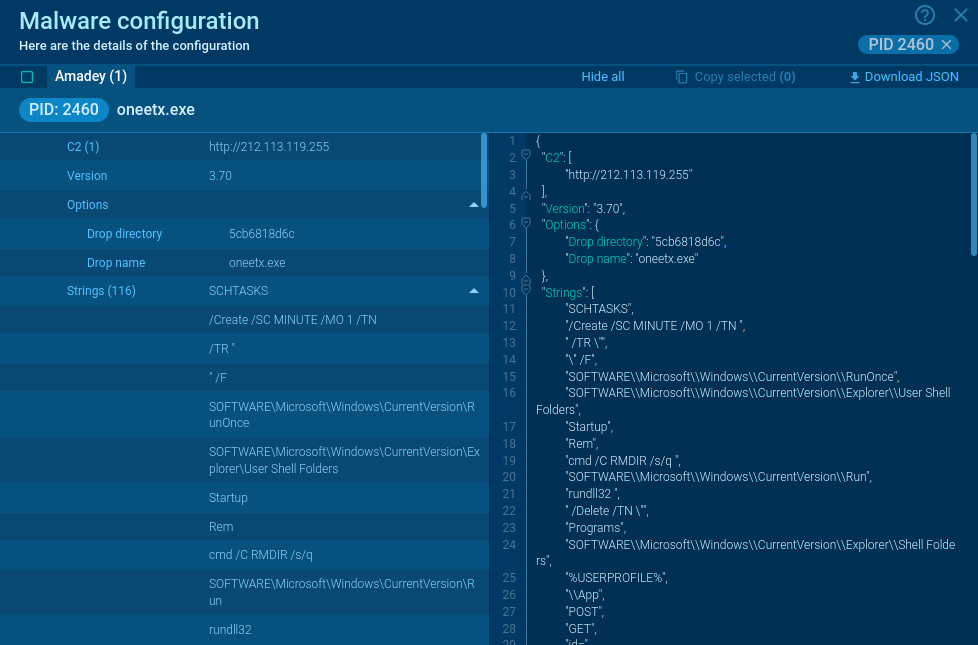
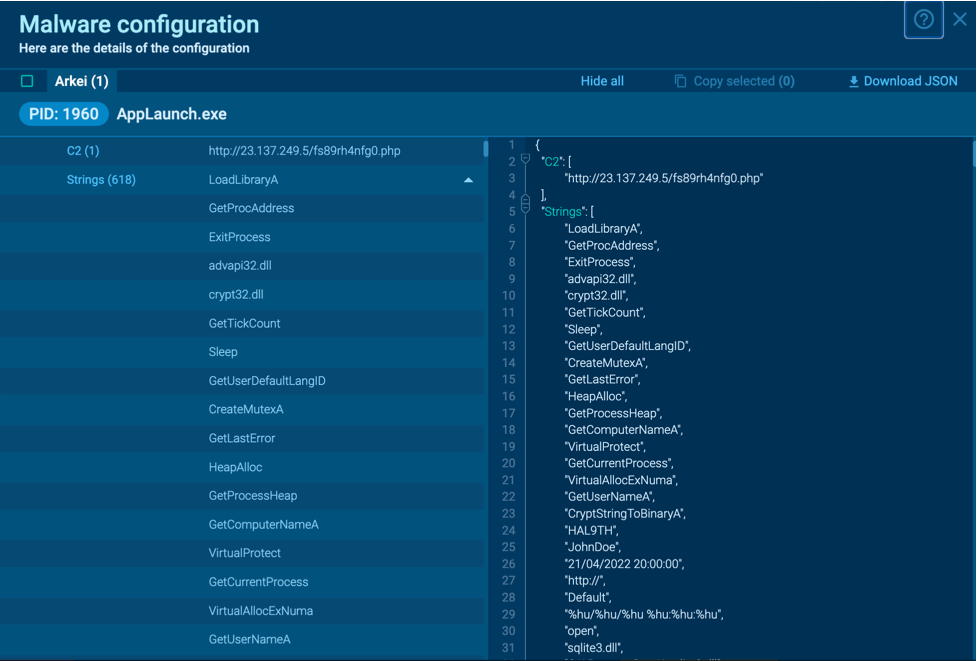
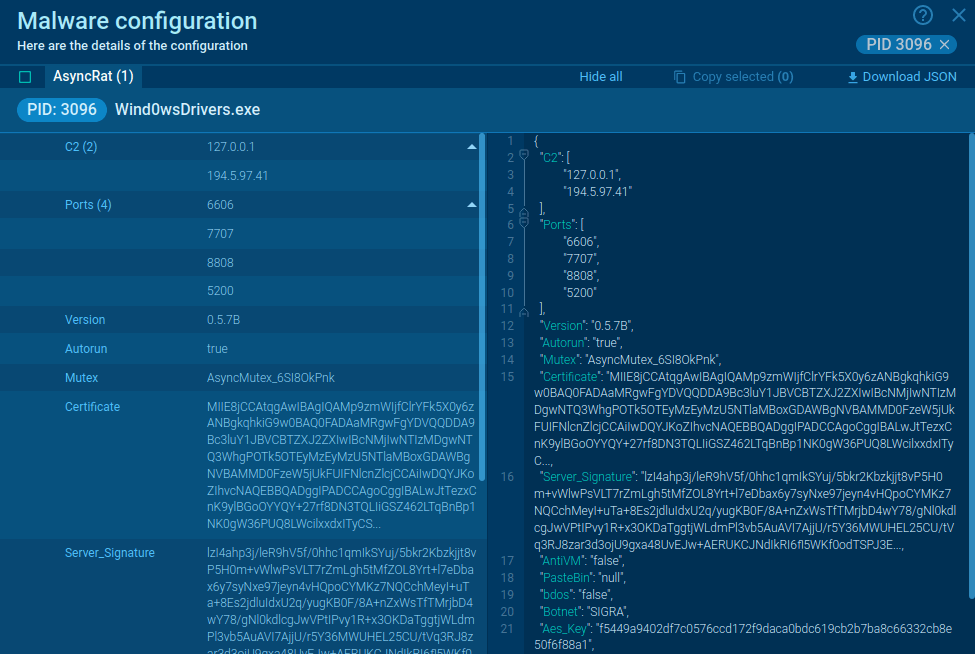
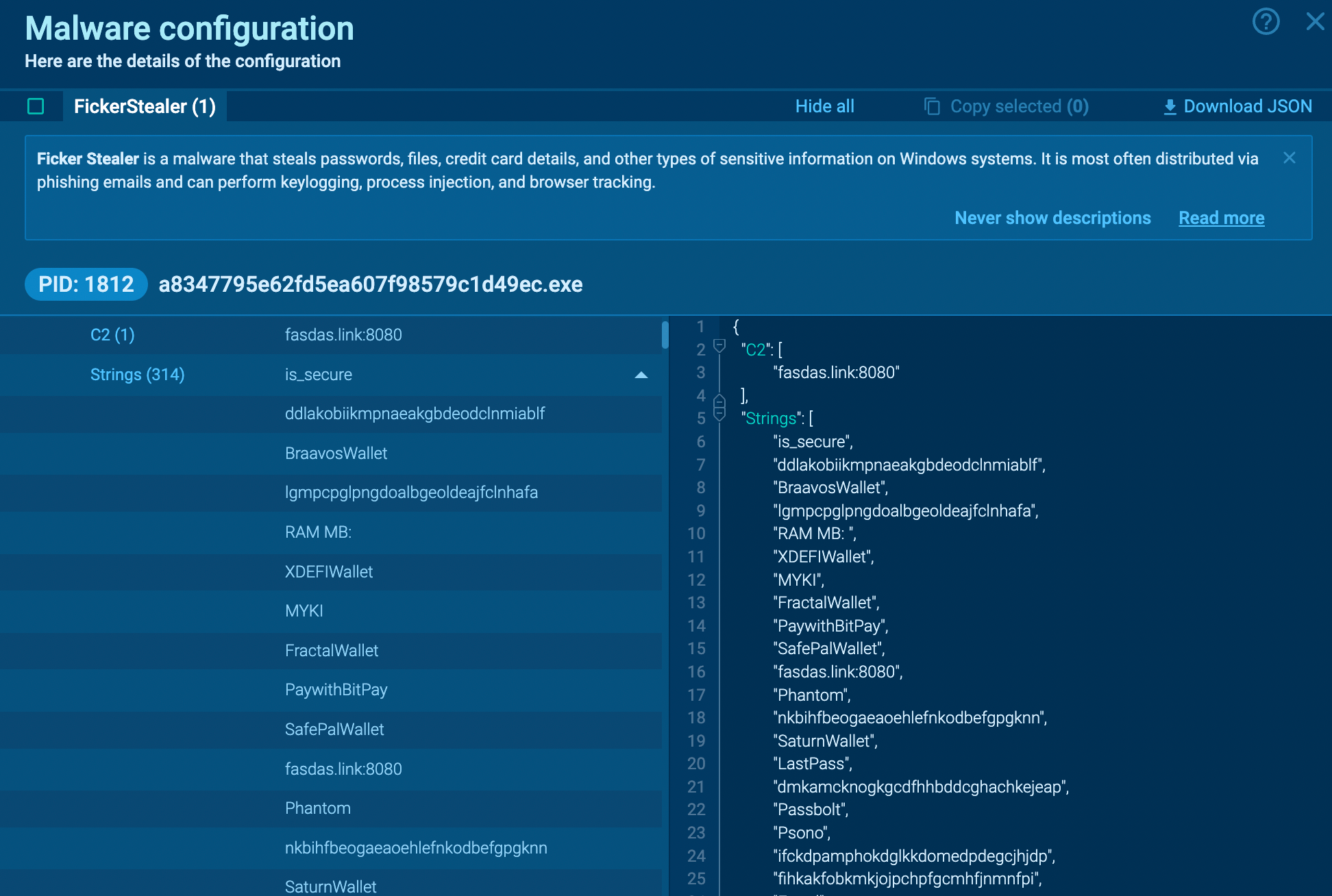 Ficker Stelaler configuration extracted in ANY.RUN
Ficker Stelaler configuration extracted in ANY.RUN
Like other malware families, this particular family may alter execution flows, but it will do so in a way that remains plain and simple. Stealers usually attempt to be less visible, so you may notice reduced activity during the execution of the Ficker, compared to what you might typically expect. After all the information is stolen, the malware may halt its execution and delete itself from the infected system. However, this behavior can vary across different versions and settings.
Distribution methods of the Ficker Stealer malware
Ficker Stealer can end up on a victim’s PC in several ways:
- Attackers may implant malicious code into websites’ infrastructure, which then gets automatically downloaded onto the devices of visitors. Such websites may look legitimate and, as a result, users may execute these downloaded files, while not being aware that their device has been compromised.
- Yet, the most common way Ficker Stealer reaches target computers is through phishing email campaigns. Attackers may exploit social engineering techniques to get people to download a file containing malicious macros. It has been observed that in many instances Ficker Stealer relies on the Hancitor loader for delivery.
Conclusion
Ficker Stealer is a serious threat to MS Windows users. To protect your system from this malware, you must exercise caution when accessing your email inbox. If you come across an email from an unfamiliar sender or if its contents appear suspicious, it is in your best interest to refrain from opening it or clicking on any links.
Instead, you can analyze these samples in the ANY.RUN malware analysis sandbox to promptly discover whether your file or URL is malicious or not. The platform lets you interact with malware in a safe VM environment in real time. Thanks to ANY.RUN, you can get an exhaustive overview of any threat’s behavior and gain insight into its IOCs, TTPs, and other crucial details.
Try ANY.RUN for free – request a demo!



 0
0