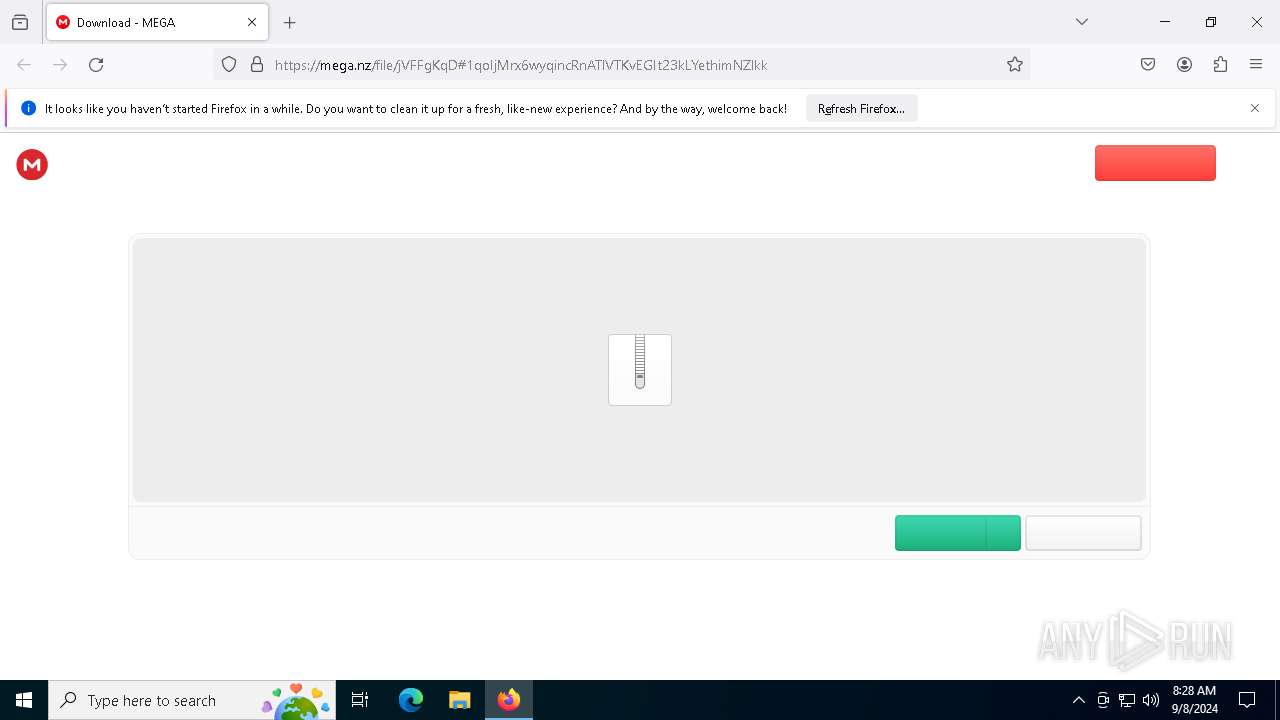
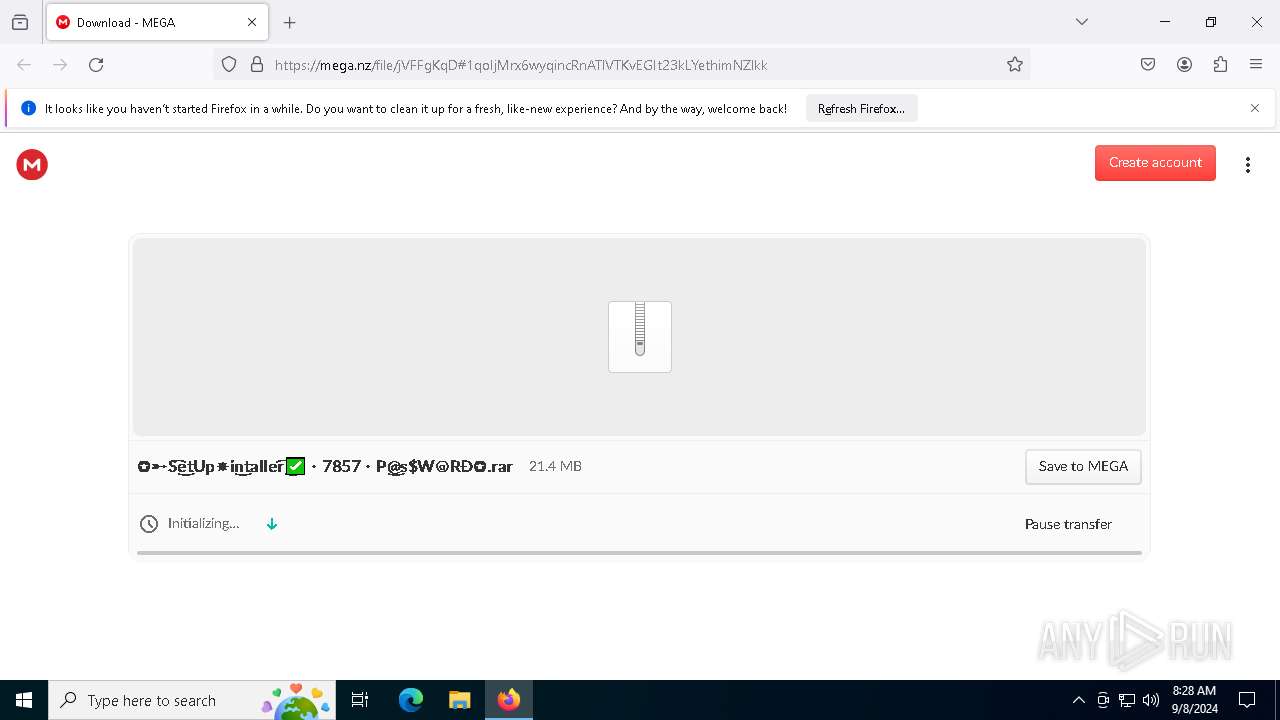
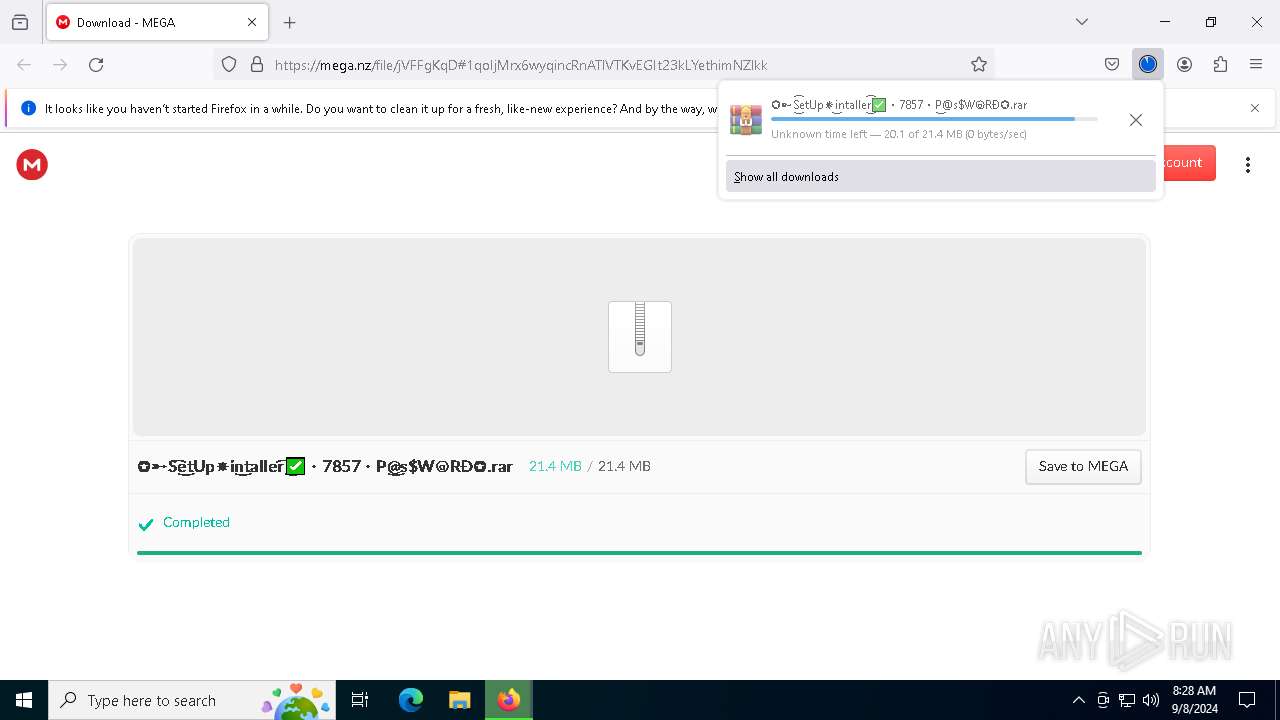
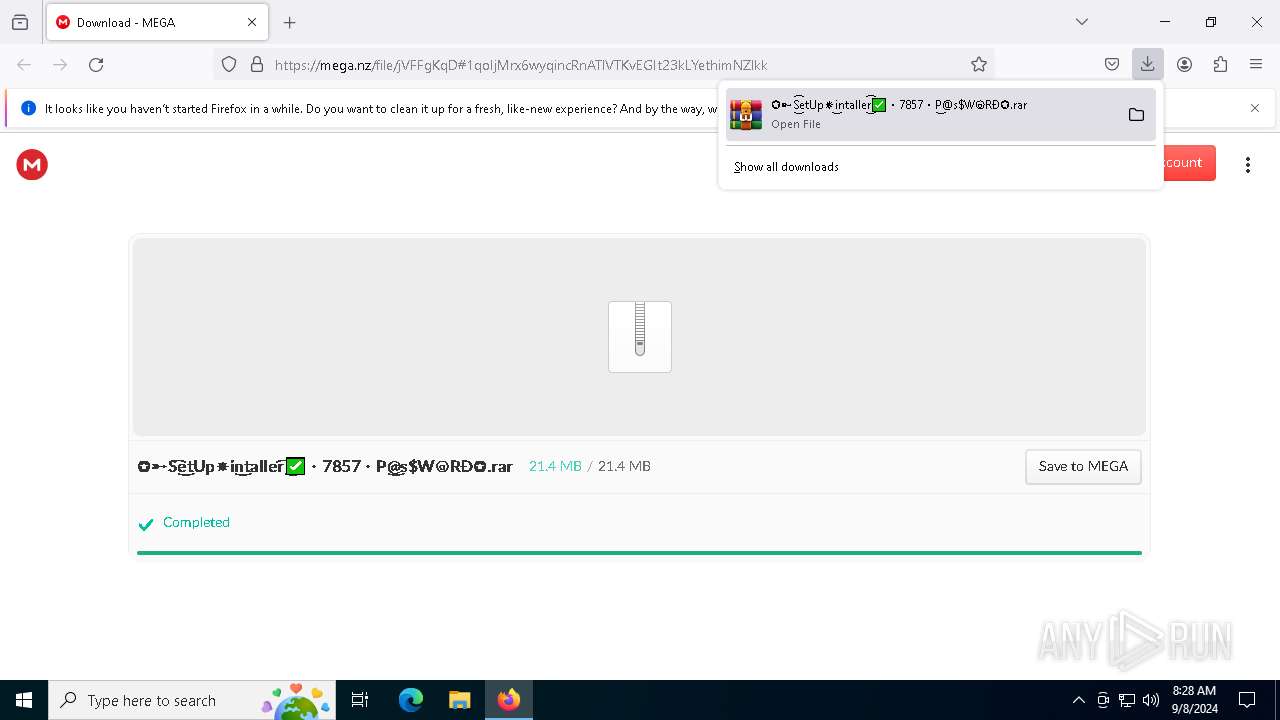
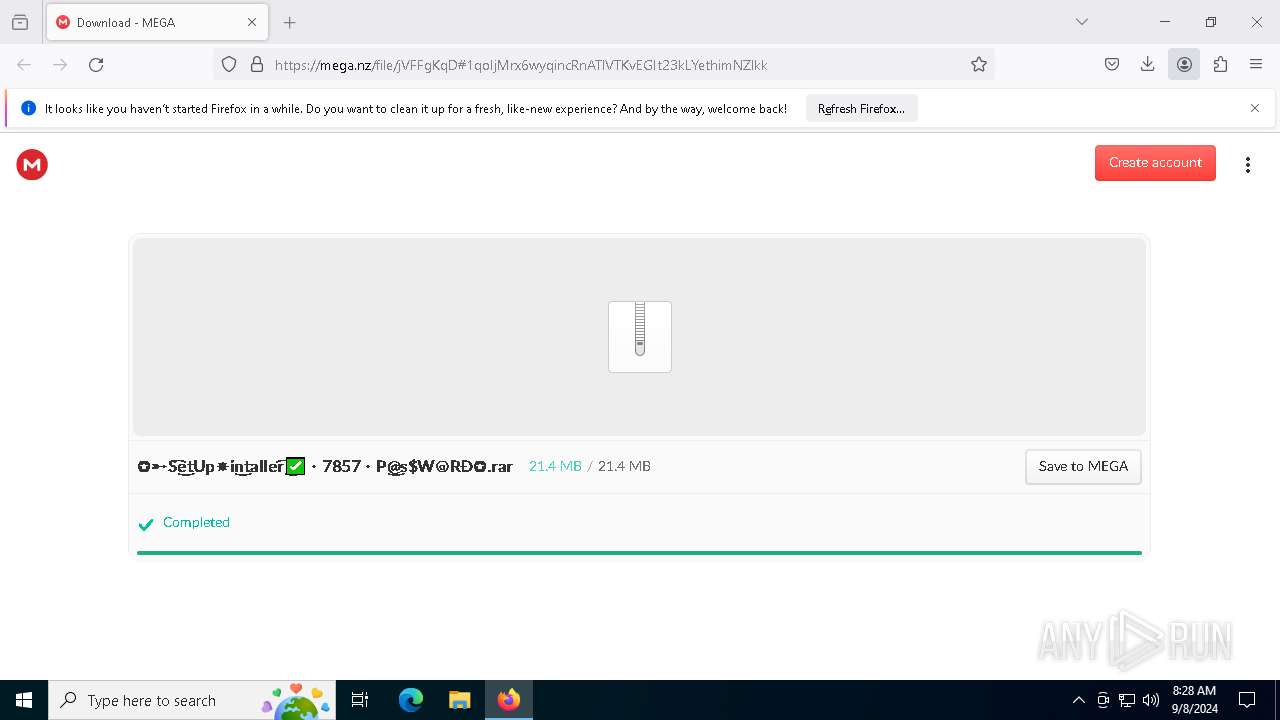
| URL: | https://mega.nz/file/jVFFgKqD#1qoIjMrx6wyqincRnATlVTKvEGIt23kLYethimNZlkk |
| Full analysis: | https://app.any.run/tasks/20c700e6-4c01-486b-83ed-09b2280bfff7 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 08, 2024, 08:28:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 359AA9639A0224F0F815AC81DF765604 |
| SHA1: | 041C09C9966BEF761FE8958167C8D7DF5173B18D |
| SHA256: | FFB5D2D4A09F9FA5FBA54661A2D1C7EBD627B5690C5AB3BBE8408DD26DBA947D |
| SSDEEP: | 3:N8X/iQmhH0H3LpnsxWGRrCO:2ji0H3LpniWUR |
MALICIOUS
LUMMA has been detected (SURICATA)
- SearchIndexer.exe (PID: 7732)
Stealers network behavior
- SearchIndexer.exe (PID: 7732)
LUMMA has been detected (YARA)
- SearchIndexer.exe (PID: 7732)
Bypass execution policy to execute commands
- powershell.exe (PID: 2228)
Changes powershell execution policy (Bypass)
- SearchIndexer.exe (PID: 7732)
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 2228)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7156)
Changes the autorun value in the registry
- reg.exe (PID: 2724)
SUSPICIOUS
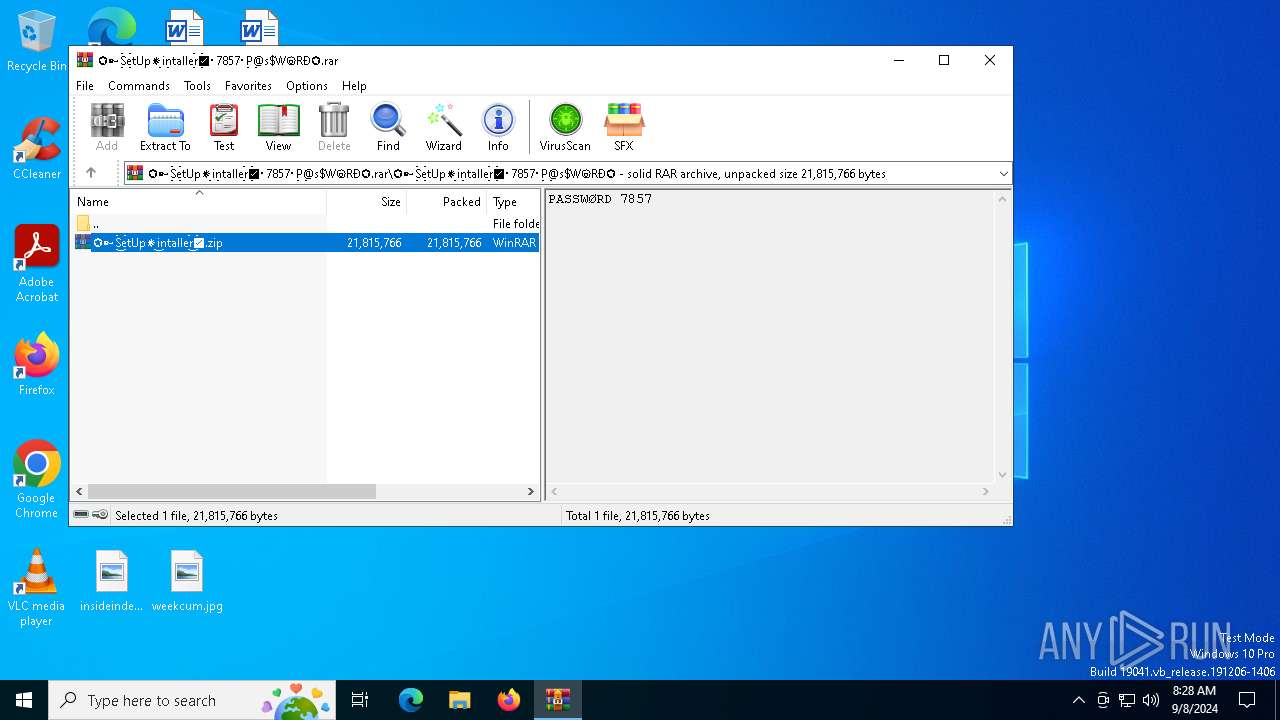
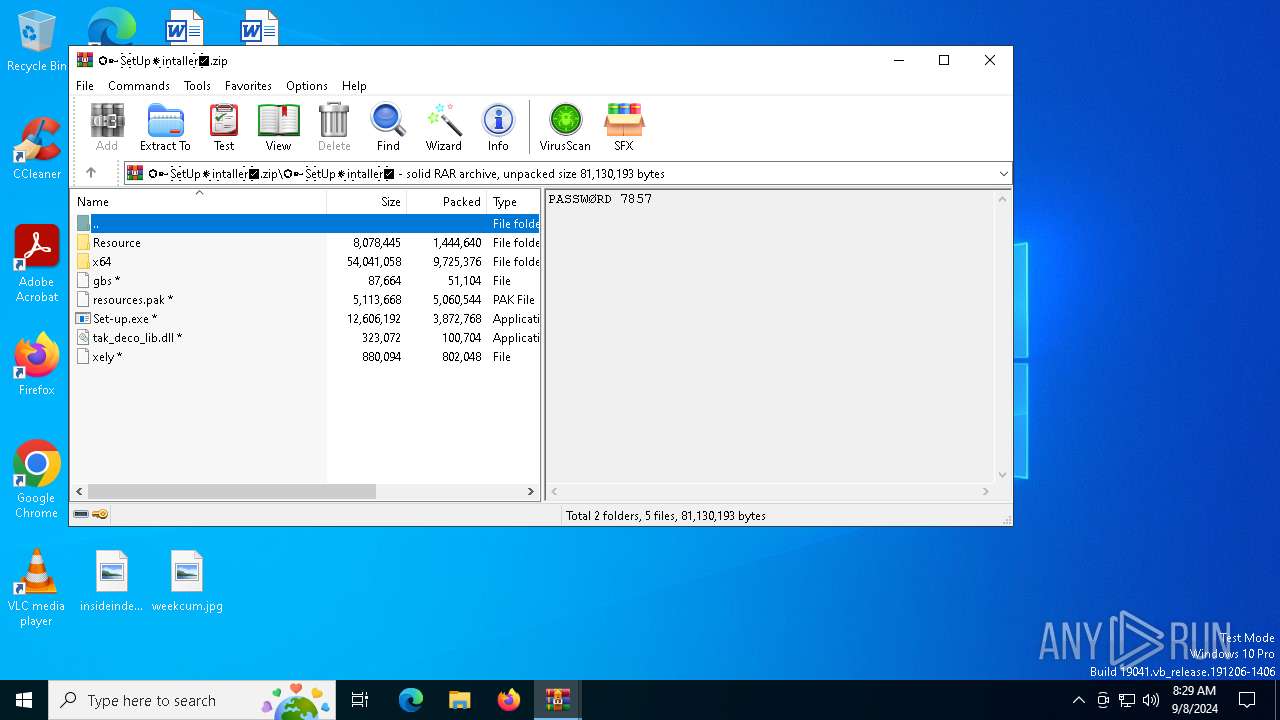
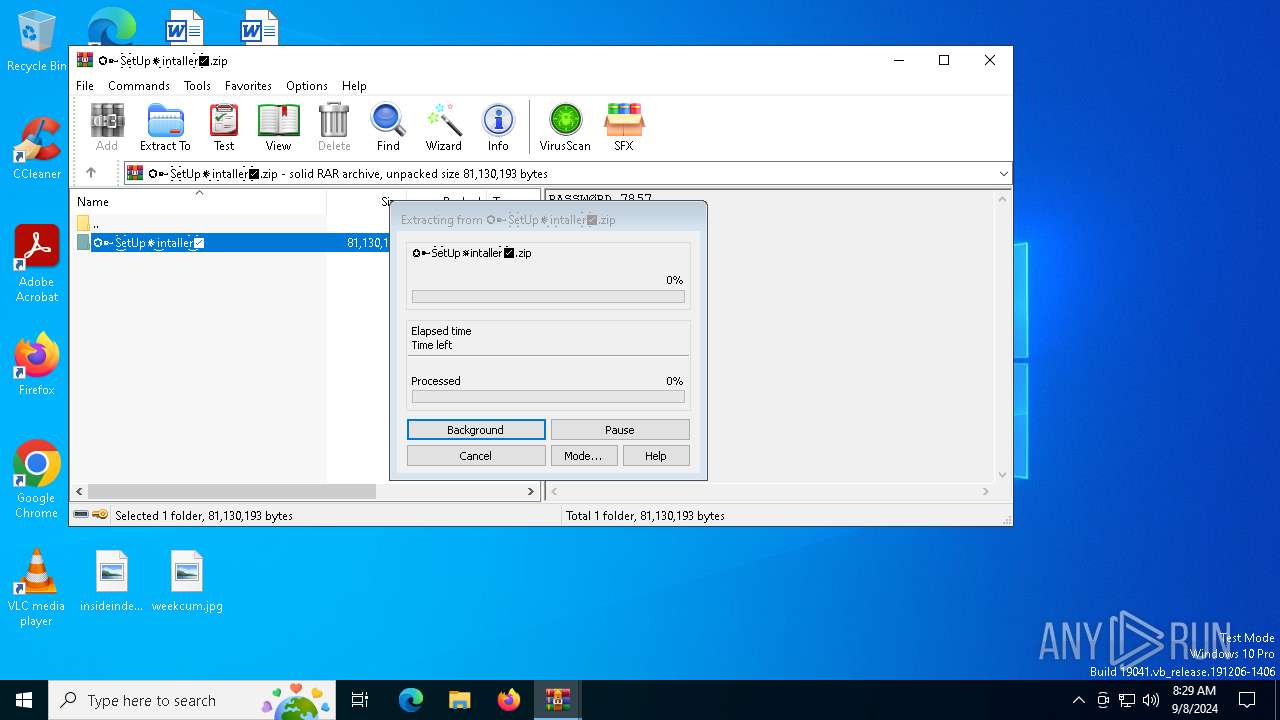
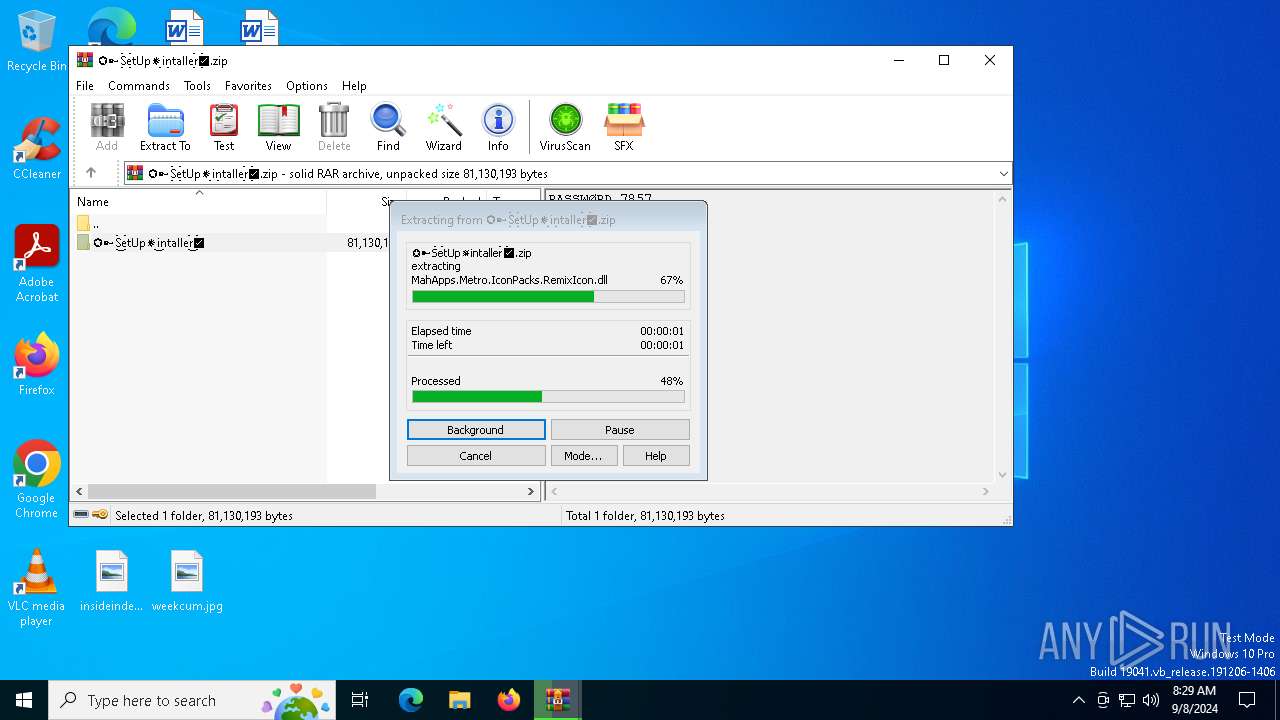
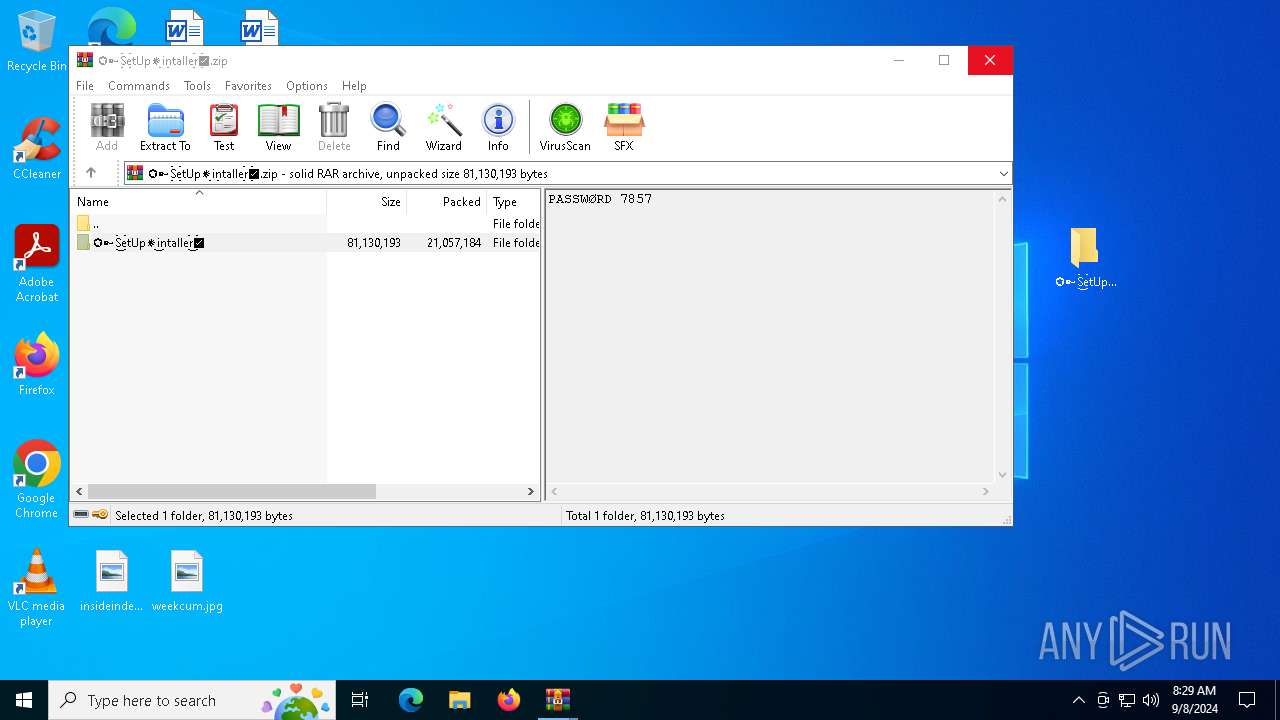
The process creates files with name similar to system file names
- WinRAR.exe (PID: 2868)
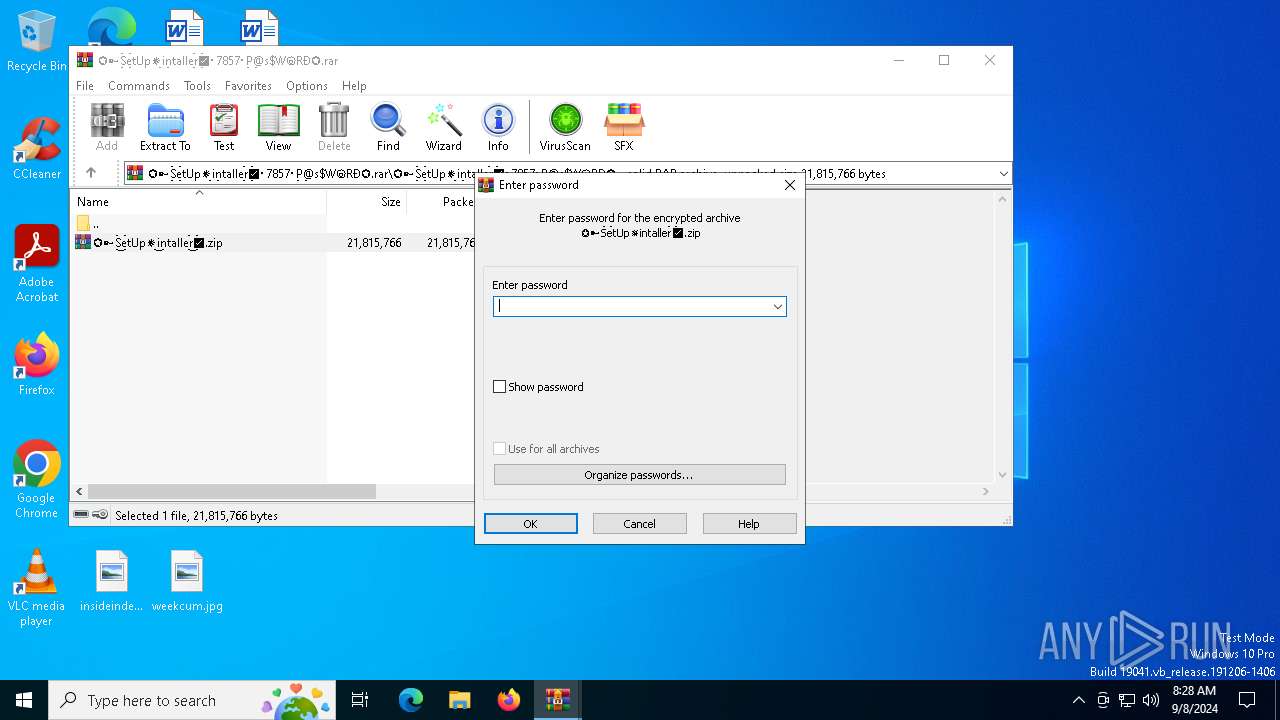
Process drops legitimate windows executable
- WinRAR.exe (PID: 2868)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8096)
Application launched itself
- WinRAR.exe (PID: 8096)
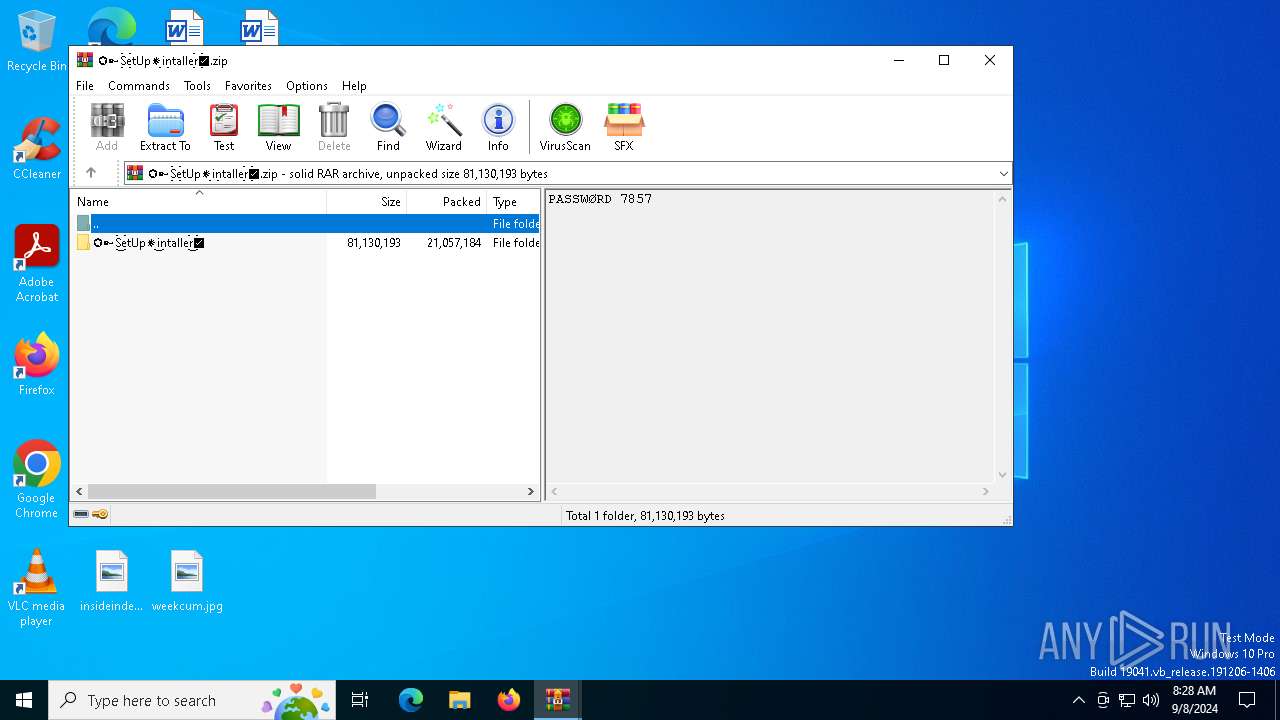
Executable content was dropped or overwritten
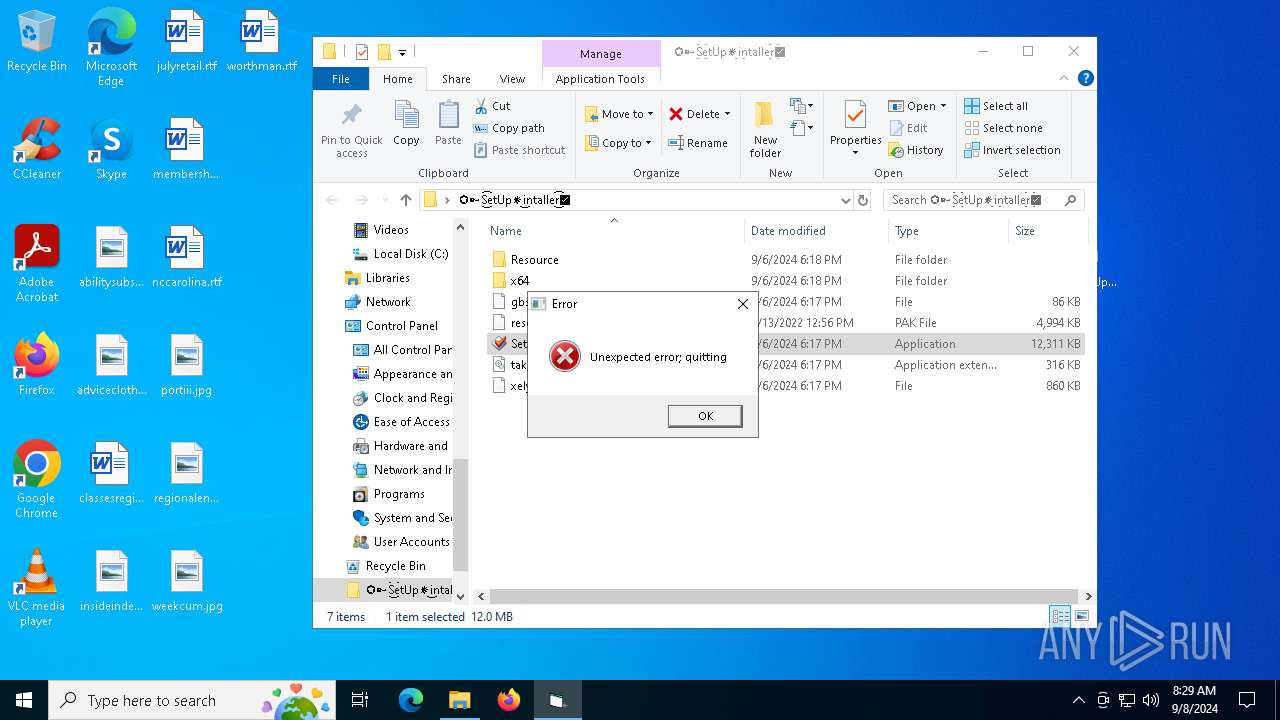
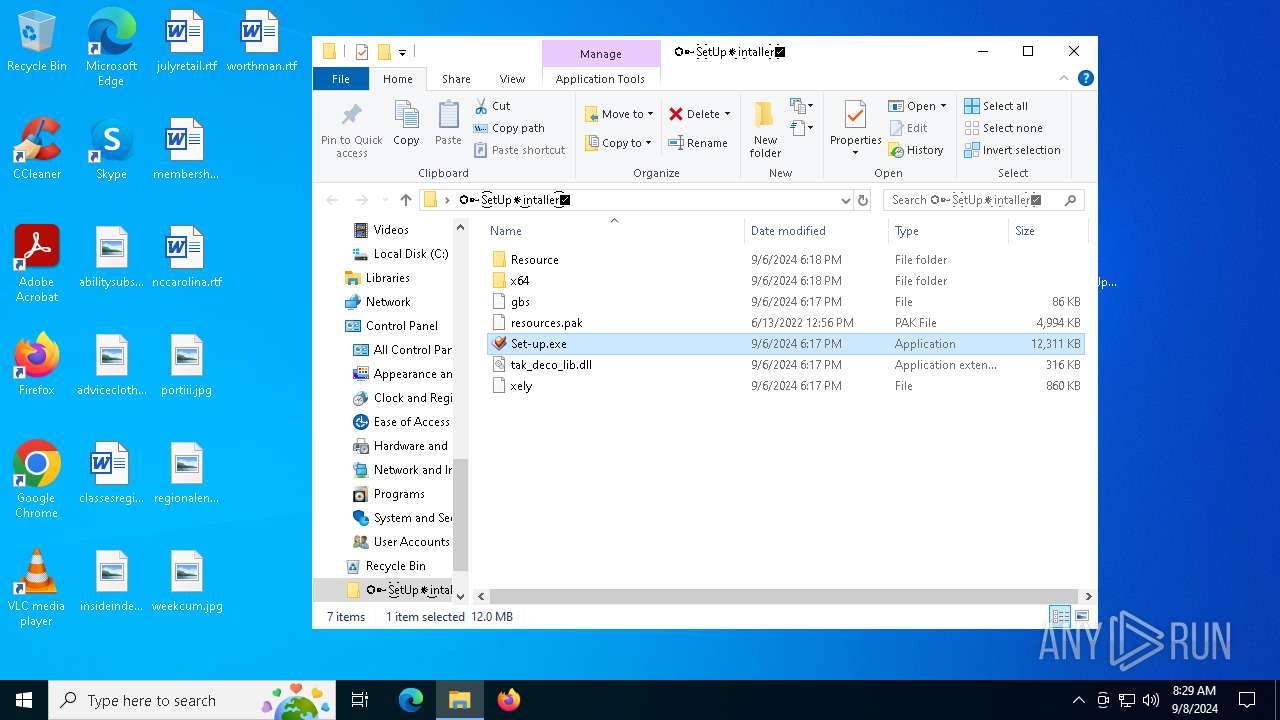
- Set-up.exe (PID: 7580)
- SearchIndexer.exe (PID: 7732)
- XJ5IRBADLFBCSQ09N2.exe (PID: 7912)
Starts application with an unusual extension
- Set-up.exe (PID: 7580)
- Set-up.exe (PID: 1440)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2228)
Starts POWERSHELL.EXE for commands execution
- SearchIndexer.exe (PID: 7732)
The process executes Powershell scripts
- SearchIndexer.exe (PID: 7732)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2228)
Starts CMD.EXE for commands execution
- XJ5IRBADLFBCSQ09N2.exe (PID: 7912)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2180)
INFO
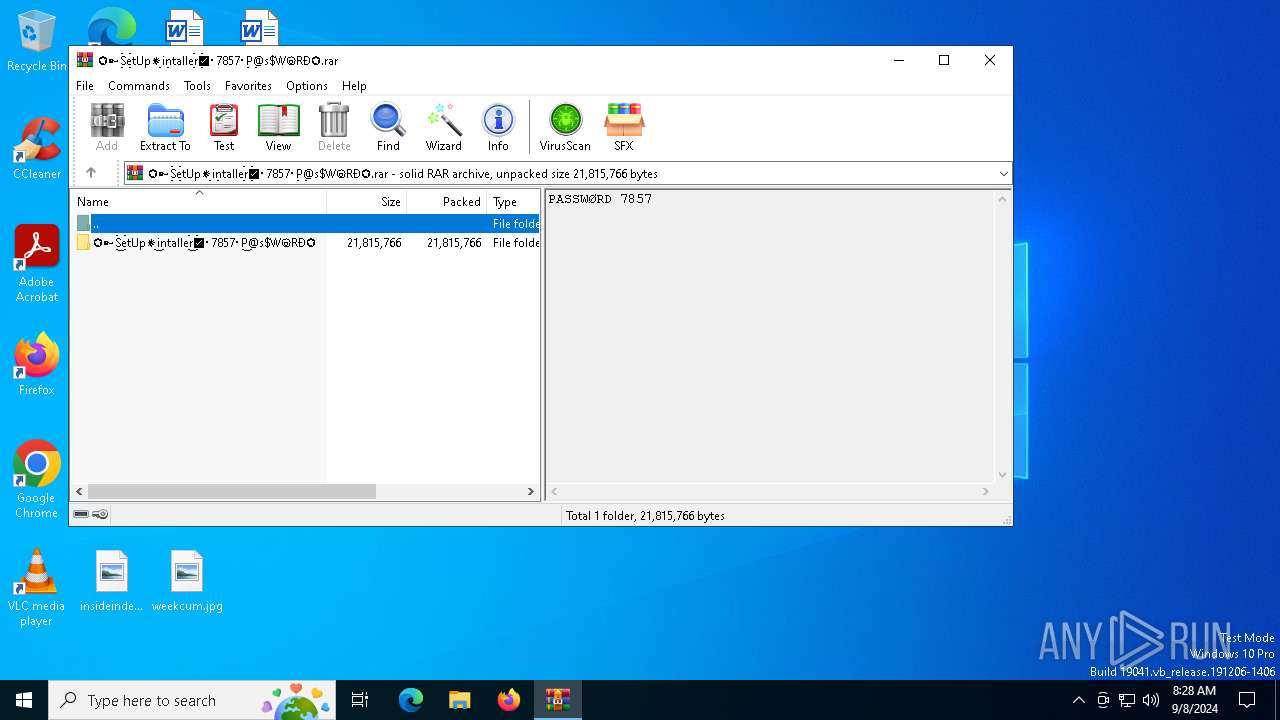
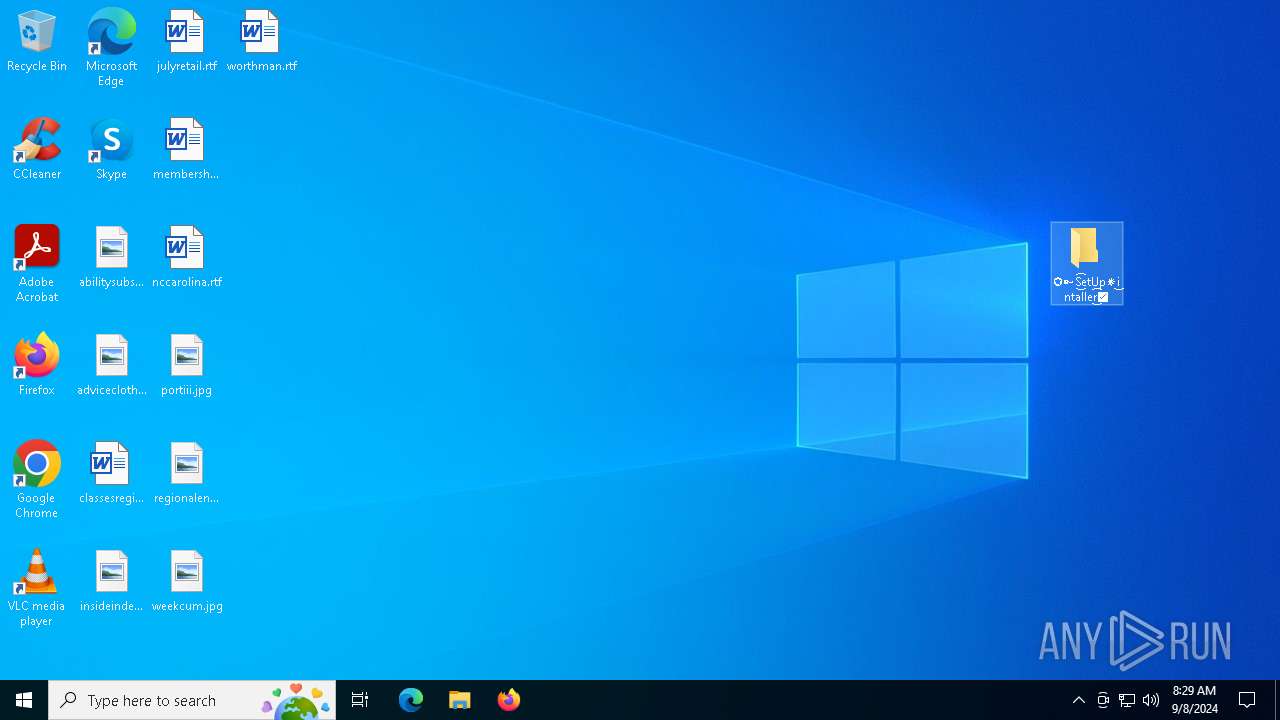
Manual execution by a user
- WinRAR.exe (PID: 8096)
- Set-up.exe (PID: 7580)
- Set-up.exe (PID: 1440)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2868)
The process uses the downloaded file
- WinRAR.exe (PID: 8096)
- firefox.exe (PID: 3984)
- WinRAR.exe (PID: 2868)
- powershell.exe (PID: 2228)
Application launched itself
- firefox.exe (PID: 3984)
- firefox.exe (PID: 6156)
Reads the computer name
- Set-up.exe (PID: 7580)
- StrCmp.exe (PID: 1172)
- more.com (PID: 7568)
- Set-up.exe (PID: 1440)
- more.com (PID: 7684)
- 9S8VSANVA8OA6BDXP84SBE7JIROV1.exe (PID: 8080)
- XJ5IRBADLFBCSQ09N2.exe (PID: 7912)
Checks supported languages
- Set-up.exe (PID: 7580)
- StrCmp.exe (PID: 1172)
- more.com (PID: 7568)
- Set-up.exe (PID: 1440)
- more.com (PID: 7684)
- XJ5IRBADLFBCSQ09N2.exe (PID: 7912)
- 9S8VSANVA8OA6BDXP84SBE7JIROV1.exe (PID: 8080)
Creates files or folders in the user directory
- Set-up.exe (PID: 7580)
Create files in a temporary directory
- Set-up.exe (PID: 7580)
- more.com (PID: 7568)
- Set-up.exe (PID: 1440)
- more.com (PID: 7684)
- SearchIndexer.exe (PID: 7732)
- 9S8VSANVA8OA6BDXP84SBE7JIROV1.exe (PID: 8080)
Reads the software policy settings
- SearchIndexer.exe (PID: 7732)
- slui.exe (PID: 7956)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2228)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2228)
Creates files in the program directory
- XJ5IRBADLFBCSQ09N2.exe (PID: 7912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(7732) SearchIndexer.exe
C2 (9)evoliutwoqm.shop
condedqpwqm.shop
locatedblsoqp.shop
millyscroqwp.shop
stagedchheiqwo.shop
stamppreewntnq.shop
ceremonynekwqn.shop
caffegclasiqwp.shop
traineiwnqo.shop
Total processes
166
Monitored processes
37
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1172 | C:\Users\admin\AppData\Roaming\CHM\OWDWWOZJJTKSZAMRSZOHQQRTG\StrCmp.exe | C:\Users\admin\AppData\Roaming\CHM\OWDWWOZJJTKSZAMRSZOHQQRTG\StrCmp.exe | — | Set-up.exe | |||||||||||
User: admin Company: aaa Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
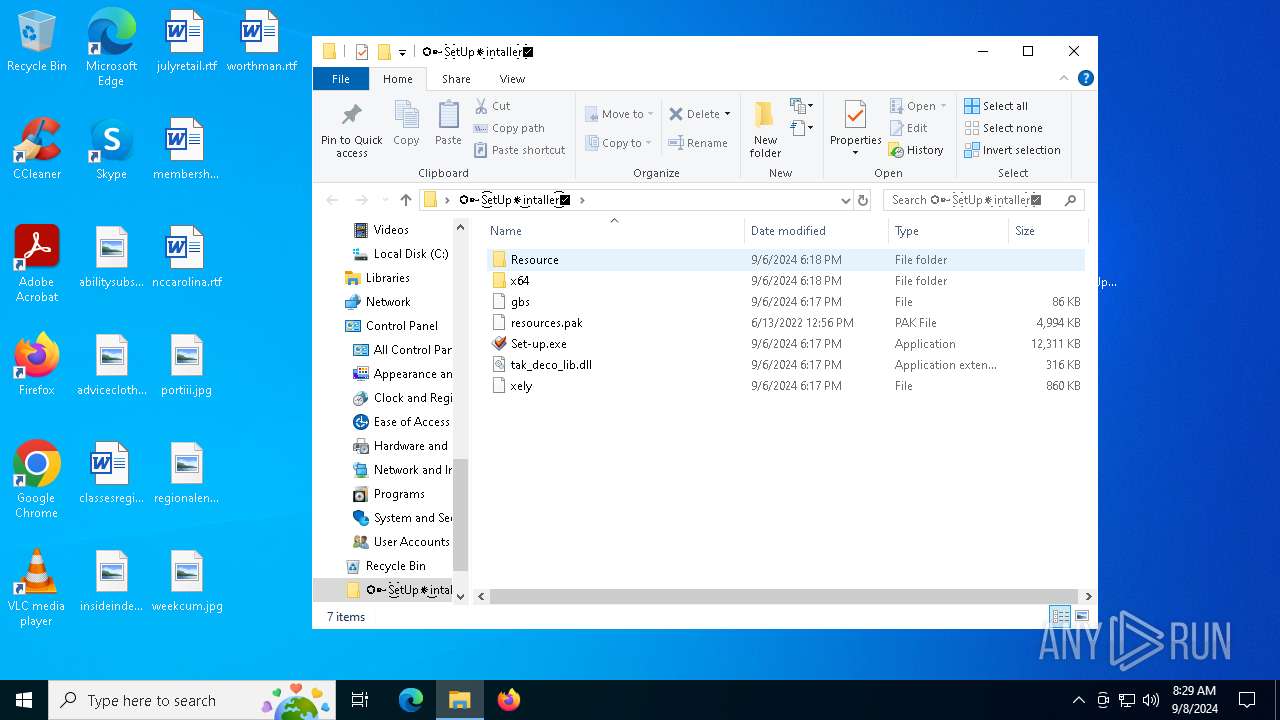
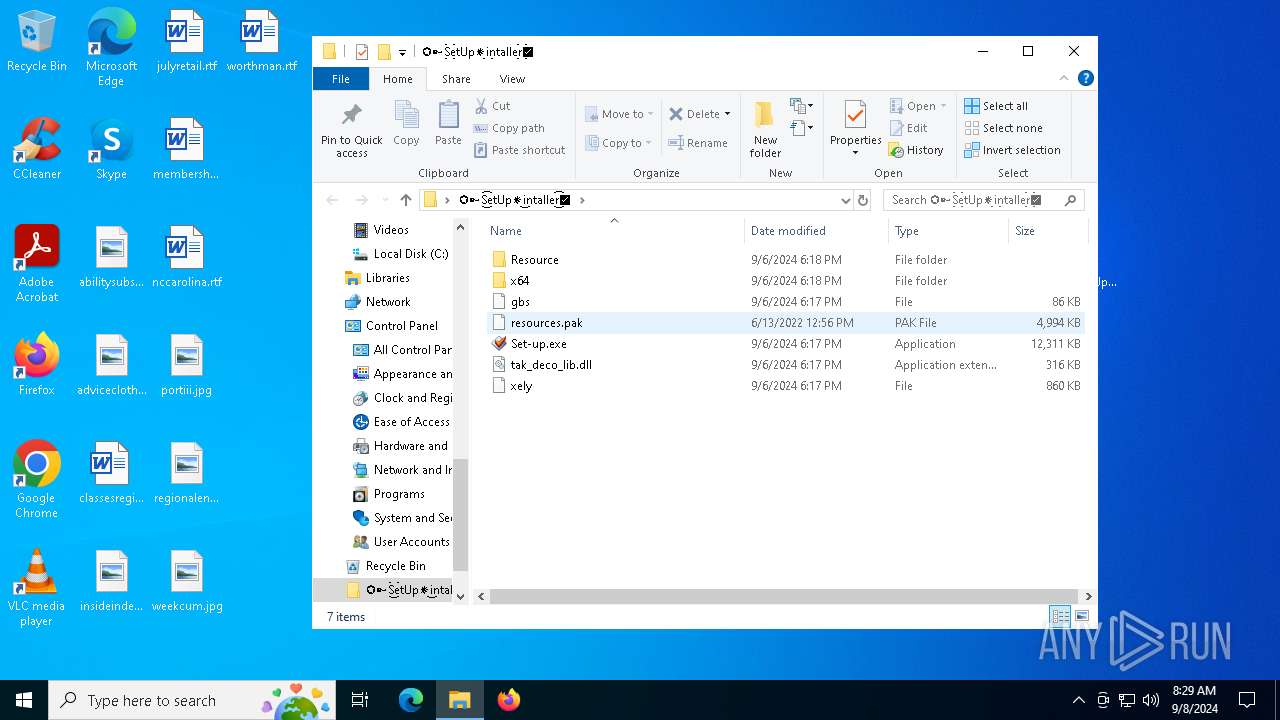
| 1440 | "C:\Users\admin\Desktop\✪➳S͜͡etUp✵i͜ntaller͜͡✅\Set-up.exe" | C:\Users\admin\Desktop\✪➳S͜͡etUp✵i͜ntaller͜͡✅\Set-up.exe | — | explorer.exe | |||||||||||
User: admin Company: Florian Heidenreich Integrity Level: MEDIUM Description: Mp3tag - the universal Tag editor Exit code: 1 Version: 3.26.0.0 Modules
| |||||||||||||||
| 2180 | cmd /c "reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v 514D3030303031 /t REG_SZ /d C:\ProgramData\514D3030303031.exe /f" | C:\Windows\SysWOW64\cmd.exe | — | XJ5IRBADLFBCSQ09N2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\LPBUO65ZPZ6GX7KEC999GRJ.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5188 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5136 -prefMapHandle 5196 -prefsLen 36339 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3800e2f0-34f4-4c5b-9cf4-14b22d7fdaa5} 3984 "\\.\pipe\gecko-crash-server-pipe.3984" 211a1e78b10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 2724 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v 514D3030303031 /t REG_SZ /d C:\ProgramData\514D3030303031.exe /f | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2868 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa8096.44476\✪➳S͜͡etUp✵i͜ntaller͜͡✅.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3980 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5176 -childID 3 -isForBrowser -prefsHandle 5248 -prefMapHandle 5244 -prefsLen 31108 -prefMapSize 244343 -jsInitHandle 1352 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e8c85524-1d8b-47b7-a7ec-28a35276b0aa} 3984 "\\.\pipe\gecko-crash-server-pipe.3984" 211a10cfd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://mega.nz/file/jVFFgKqD#1qoIjMrx6wyqincRnATlVTKvEGIt23kLYethimNZlkk | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4080 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5184 -childID 4 -isForBrowser -prefsHandle 5488 -prefMapHandle 5372 -prefsLen 31108 -prefMapSize 244343 -jsInitHandle 1352 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2d5e7d81-af77-4b6a-8b6c-82384c82a5a6} 3984 "\\.\pipe\gecko-crash-server-pipe.3984" 211a4a954d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
26 397
Read events
26 358
Write events
39
Delete events
0
Modification events
| (PID) Process: | (3984) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
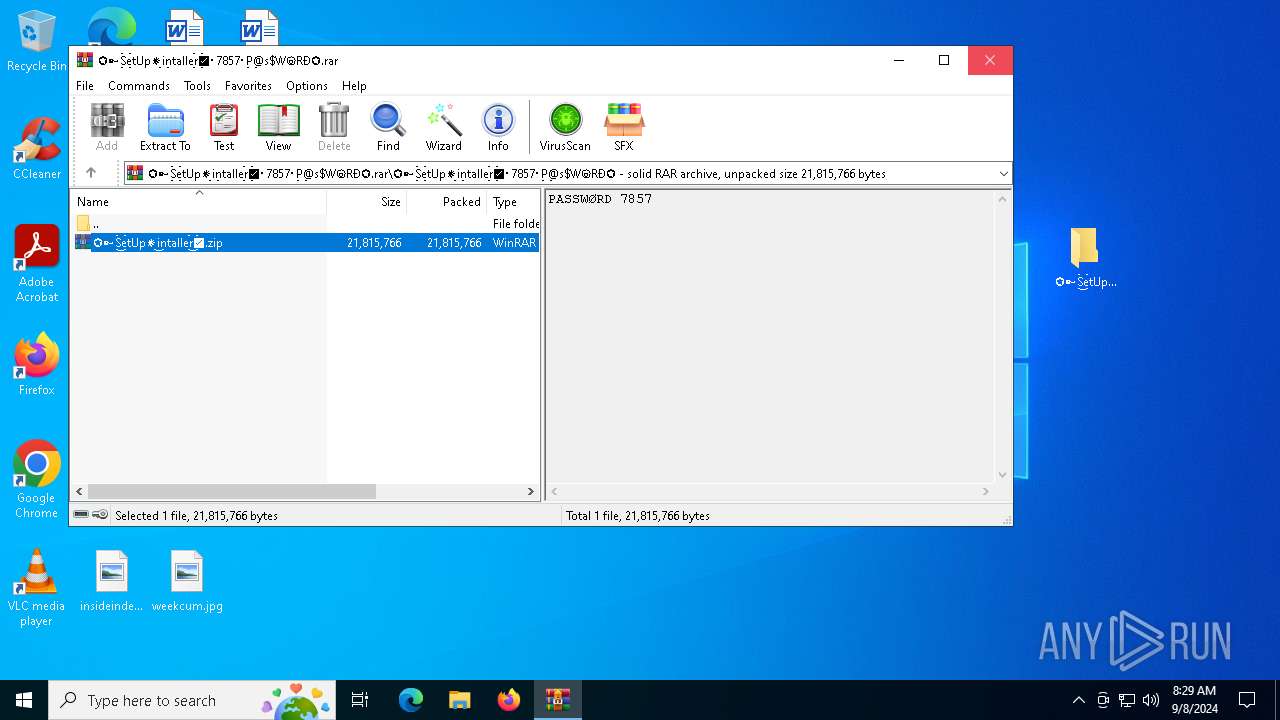
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\✪➳S͜͡etUp✵i͜ntaller͜͡✅・7857・P͜@s$WⓞRÐ✪.rar | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\✪➳S͜͡etUp✵i͜ntaller͜͡✅・7857・P͜@s$WⓞRÐ✪.rar | |||
Executable files
55
Suspicious files
210
Text files
415
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:D224E2044A488A9A13B773E3DD70293B | SHA256:EDBC889BCF6BF7BDBCF030615C133A90A5D3805111544F0D17272C262AE9DBC4 | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:70FFD9D7136D878B071F900BB88FF7F2 | SHA256:4A846F5E1858A55E794A82717812A95D5D8098138B5649520022A5686317F095 | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:46302B0DA5D6F36B895E0446BED815EE | SHA256:B031D6AFF6960A1A8F6C175154775408B23A6450D67BA6EFA93419BE3CC15F71 | |||
| 3984 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
80
DNS requests
102
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3984 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | unknown |
3984 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
3984 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
3984 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
3984 | firefox.exe | POST | 200 | 95.101.54.107:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
3984 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
3984 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/s/wr3/XjA | unknown | — | — | unknown |
3984 | firefox.exe | POST | 200 | 95.101.54.107:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
3984 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
3984 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1356 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6320 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3984 | firefox.exe | 142.250.181.234:443 | safebrowsing.googleapis.com | — | — | whitelisted |
3984 | firefox.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
3984 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
3984 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
3984 | firefox.exe | 66.203.127.13:443 | eu.static.mega.co.nz | MEGA Cloud Services Limited | NZ | shared |
3984 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
mega.nz |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
ipv4only.arpa |
| whitelisted |
example.org |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
prod.ads.prod.webservices.mozgcp.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2256 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2256 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
3984 | firefox.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |