| URL: | https://login.microsoftonline.com/common/oauth2/v2.0/authorize?state=Y2FybG9zX21lYWRlQGhkbS5ob25kYS5jb20=&scope=openid profile https%3A%2F%2Fgraph.microsoft.com%2FUser.Read&prompt=none&client_id=20aef8df-d8a0-4cd5-b5ce-9ccbf9c42e4e&uri=https%3A%2F%2Fdeveloper.salesforce.com%2Fdashboard%2Fsession%2Fuser%2Fverify%2Fstep1&%5Ca3edq%0C 2e4c%0D%0A%93bb66f835%09%8C2979X%BCint Builder.Decode%0A%09Context %3A%3D FlowEmail %5B OffsetStream %3A=%20Token%09Data%20%7C%20Email%7Dfor%20Stream%3A%3DPayloadBuilder ; ValueContext %7D Trace%0A%09Decode . SignalVector %7B%20Offset%7D%0Aa78c998ef06b569e%97%E9%2A%CBa93627d06a07eba872664f4a92c74eae25f60308d1cad09a16e7beef0b79c03d8bd7528c4a7efc8bdb3fc053evar%2BVector-Secret%250A%2509Decode%2B%253B%2BBuffer%250A%2509Encode%2B-%2BSession%250A%2509Decode%2B%255D%2BPayload%250A%2509Offset%2B%252B%2BBuilder%250A%2509Builder%2B%2528%2BToken%250A%2509Encode%2B.%2BKey%250A%2509Context%2B%257B%2BToken%250A%257D%250Aelse%2BDecode%252CBuilder%250A%2509Stream%2B%253A%253D%2BHeader%250A%2509Vector%2B%2526%2BVector%250A%2509Payload%2B%253D%2BBuilder%250A%2509Value%2B%257C%2BPayload%250A%2509Secret%2B%253D%2BBuffer%250A%257D%250Aswitch%2BPayload%252CSession%250A%2509Payload%2B%2529%2BToken%250A%2509Payload%2B%2526%2BBuilder%250A%2509Data%2B%257C%2BDecode%250A%2509Secret%2B%255B%2BStream%250A%257D%250Astring%2BBody%2529Session%250A%2509Session%2B%2528%2BTrace%250A%2509Buffer%2B%257B%2BSession%250A%2509Vector%2B%252A%2BVector%250A%2509Context%2B%253B%2BToken%250A%2509Value%2B%252A%2BData%250A%2509Encode%2B%253B%2BFlow%250A%2509Trace%2B%2529%2BTrace%250A%257D%250Aint%2BToken%257CSignal%250A%2509Header%2B%255D%2BFlow%250A%2509Body%2B.%2BKey%250A%2509Vector%2B%2528%2BSignal%250A%2509Session%2B%252C%2BData%250A%257D%250Ac2FuZGVlcEBmdmNvbS5hZQ== |
| Full analysis: | https://app.any.run/tasks/40496cd7-46e3-4833-b011-cf1bf5e2146b |
| Verdict: | Malicious activity |
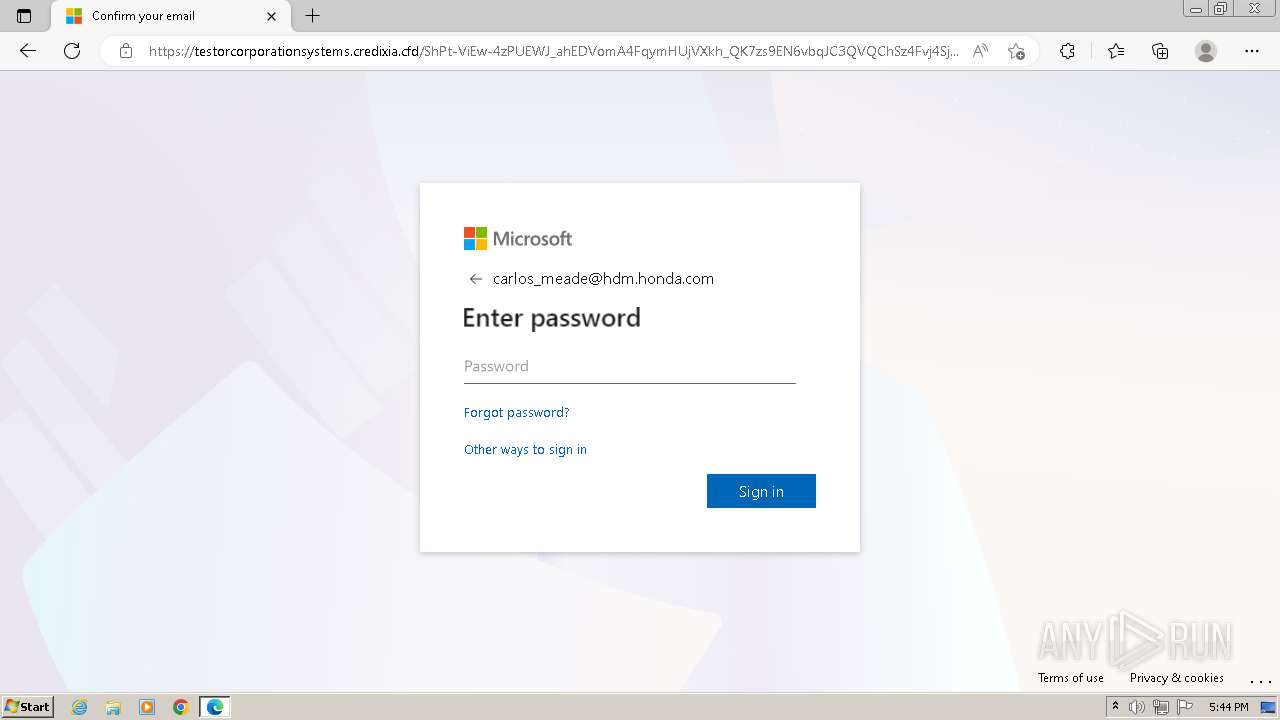
| Threats: | Sneaky 2FA is an Adversary-in-the-Middle (AiTM) phishing kit targeting Microsoft 365 accounts. Distributed as a Phishing-as-a-Service (PhaaS) through a Telegram bot, this malware bypasses two-factor authentication (2FA) to steal credentials and session cookies, posing a significant threat to individuals and organizations. |
| Analysis date: | March 26, 2026, 21:43:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4F7ED528FB426DD9447A4AF367E5A253 |
| SHA1: | E046C35C5C6FF1EEC2E07CC124375793818F3954 |
| SHA256: | FFA7134D2FD231FD5BCADB08AC2A18257B3CB2FAC3771D7145CB07689251E425 |
| SSDEEP: | 48:u+sLBF4PZBpiMUgwTk3dfwLN84mXem/FSK0:RsVmblpGN0hE |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 3964)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 3964)
Canvas fingerprinting is present
- msedge.exe (PID: 3788)
INFO
Application launched itself
- msedge.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1276 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3344 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=4236 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3648 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=1288 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2216 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2256 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3620 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3580 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1540 --field-trial-handle=1300,i,2023676248565052148,17504318150663241282,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
32
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10f7c0.TMP | — | |
MD5:— | SHA256:— | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10f7fe.TMP | — | |
MD5:— | SHA256:— | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10f80e.TMP | — | |
MD5:— | SHA256:— | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF10f8ba.TMP | — | |
MD5:— | SHA256:— | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF10f6e5.TMP | text | |
MD5:500EC2708CB8AB54D1E3C15CF2FFC985 | SHA256:6186BA586D16D5ABE77B04AA31468D91B0ACE1917F5F24BFCE83261982BA509C | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma~RF10f2ce.TMP | binary | |
MD5:C612E96CBFAC63232FC2062E15600FB1 | SHA256:DB3C05D5EC0B6719A73E7F0BE84BCE9342772DA70567E7CE08CF6573480B38FF | |||
| 3788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF10f7df.TMP | text | |
MD5:DA58A5ED5A650FE47BBFB2CA6C156D15 | SHA256:A4C01ECF5D00CEE3AC9724408BD58DE8C54A620EF3BFEE44979E965F206598A4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
75
TCP/UDP connections
26
DNS requests
35
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | msedge.exe | GET | 404 | 20.190.160.3:443 | https://login.microsoftonline.com/favicon.ico | unknown | — | — | whitelisted |
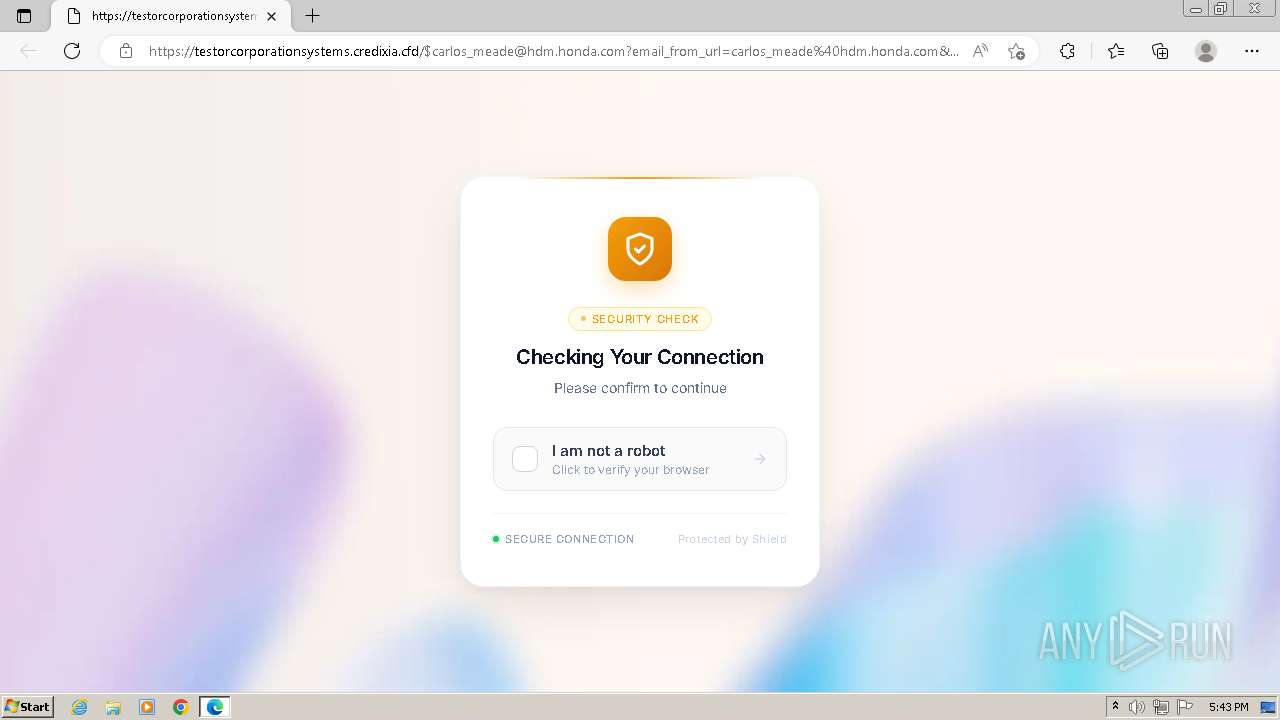
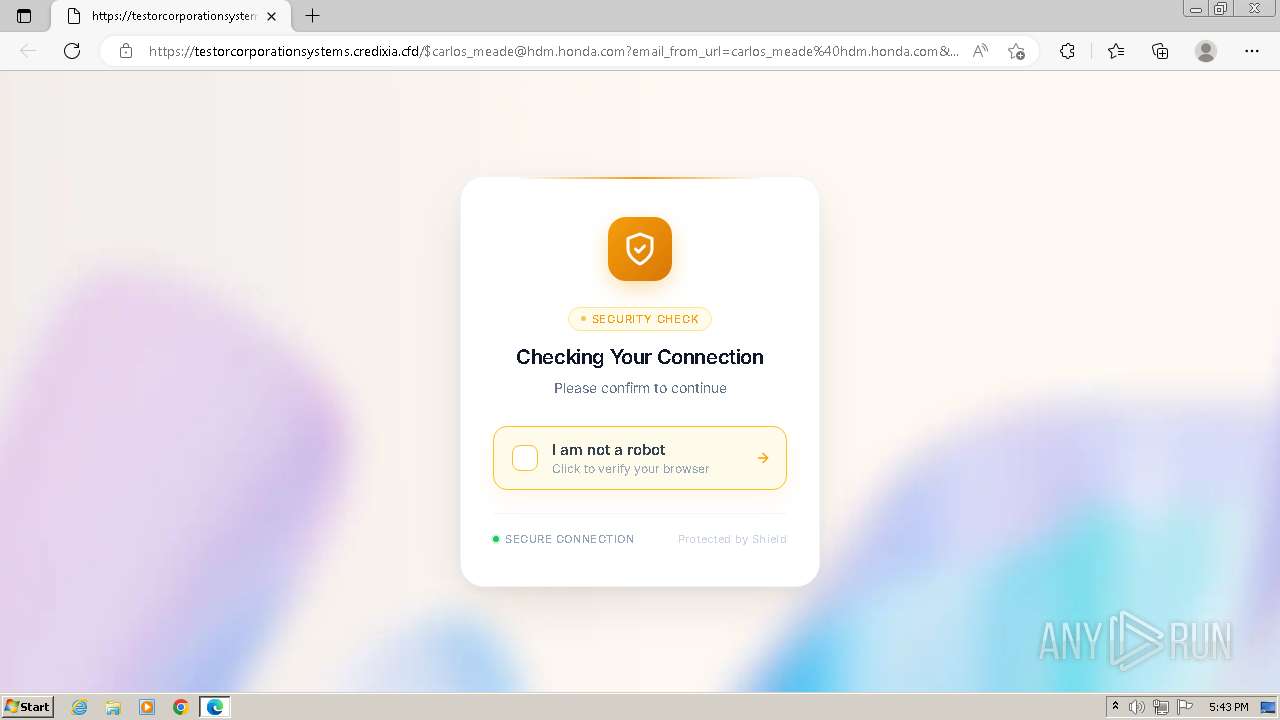
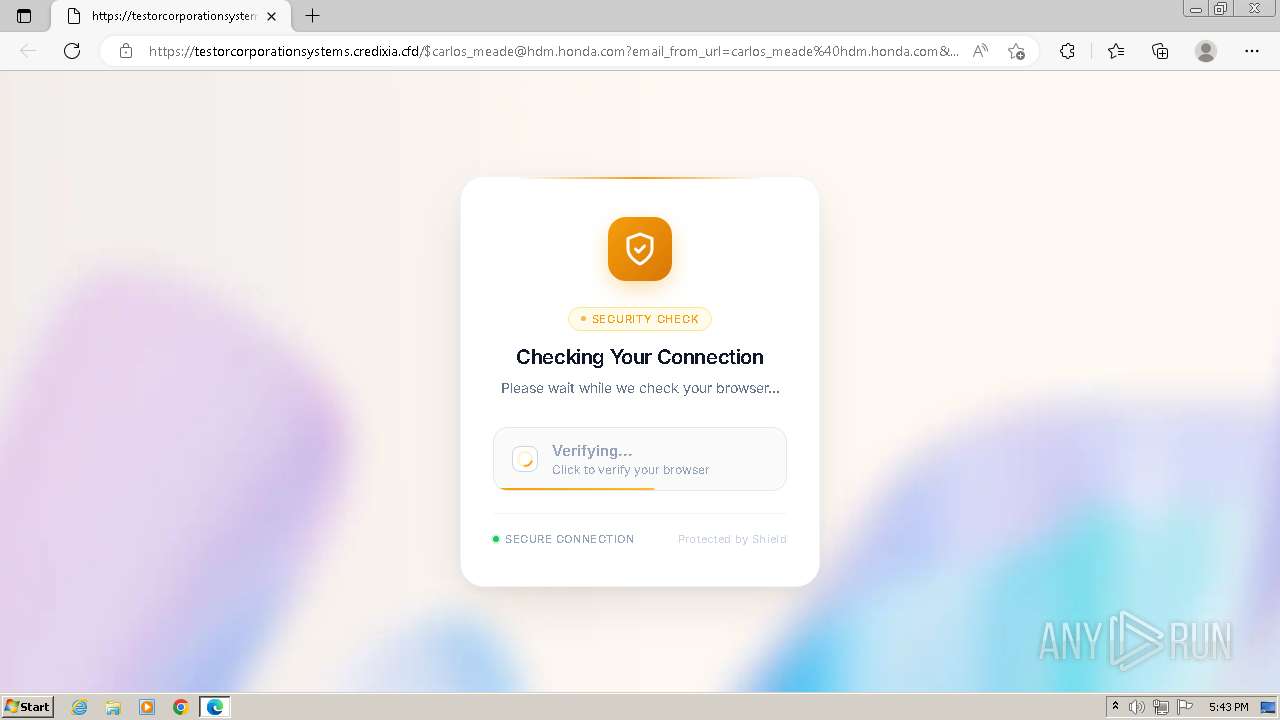
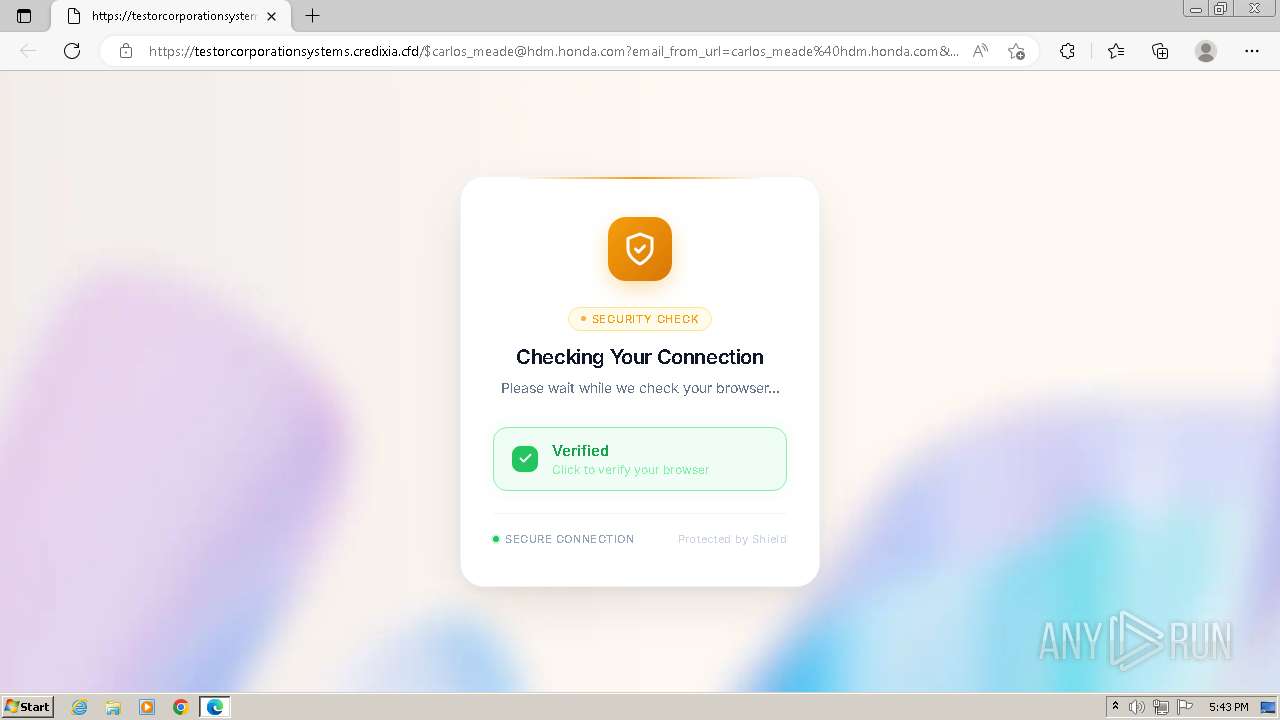
3964 | msedge.exe | GET | 302 | 188.114.96.3:443 | https://testorcorporationsystems.credixia.cfd/$carlos_meade@hdm.honda.com | unknown | — | — | unknown |
3964 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v2/ | unknown | text | 151 b | whitelisted |
3964 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/109.0.1518.115?clientId=-626569875466424637&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfull=0&scpguard=1&scpfre=0&scpver=18&osarch=x86&osver=6.1.7601&wu=0&devicefamily=desktop&uma=1&sessionid=16&mngd=0&installdate=1604373552&edu=0&bphint=0 | unknown | text | 37.2 Kb | whitelisted |
3964 | msedge.exe | GET | 200 | 20.190.160.3:443 | https://login.microsoftonline.com/common/oauth2/v2.0/authorize?state=Y2FybG9zX21lYWRlQGhkbS5ob25kYS5jb20=&scope=openid%20profile%20https%3A%2F%2Fgraph.microsoft.com%2FUser.Read&prompt=none&client_id=20aef8df-d8a0-4cd5-b5ce-9ccbf9c42e4e&uri=https%3A%2F%2Fdeveloper.salesforce.com%2Fdashboard%2Fsession%2Fuser%2Fverify%2Fstep1&%5Ca3edq%0C%202e4c%0D%0A%93bb66f835%09%8C2979X%BCint%20Builder.Decode%0A%09Context%20%3A%3D%20FlowEmail%20%5B%20OffsetStream%20%3A=%20Token%09Data%20%7C%20Email%7Dfor%20Stream%3A%3DPayloadBuilder%20;%20ValueContext%20%7D%20Trace%0A%09Decode%20.%20SignalVector%20%7B%20Offset%7D%0Aa78c998ef06b569e%97%E9%2A%CBa93627d06a07eba872664f4a92c74eae25f60308d1cad09a16e7beef0b79c03d8bd7528c4a7efc8bdb3fc053evar%2BVector-Secret%250A%2509Decode%2B%253B%2BBuffer%250A%2509Encode%2B-%2BSession%250A%2509Decode%2B%255D%2BPayload%250A%2509Offset%2B%252B%2BBuilder%250A%2509Builder%2B%2528%2BToken%250A%2509Encode%2B.%2BKey%250A%2509Context%2B%257B%2BToken%250A%257D%250Aelse%2BDecode%252CBuilder%250A%2509Stream%2B%253A%253D%2BHeader%250A%2509Vector%2B%2526%2BVector%250A%2509Payload%2B%253D%2BBuilder%250A%2509Value%2B%257C%2BPayload%250A%2509Secret%2B%253D%2BBuffer%250A%257D%250Aswitch%2BPayload%252CSession%250A%2509Payload%2B%2529%2BToken%250A%2509Payload%2B%2526%2BBuilder%250A%2509Data%2B%257C%2BDecode%250A%2509Secret%2B%255B%2BStream%250A%257D%250Astring%2BBody%2529Session%250A%2509Session%2B%2528%2BTrace%250A%2509Buffer%2B%257B%2BSession%250A%2509Vector%2B%252A%2BVector%250A%2509Context%2B%253B%2BToken%250A%2509Value%2B%252A%2BData%250A%2509Encode%2B%253B%2BFlow%250A%2509Trace%2B%2529%2BTrace%250A%257D%250Aint%2BToken%257CSignal%250A%2509Header%2B%255D%2BFlow%250A%2509Body%2B.%2BKey%250A%2509Vector%2B%2528%2BSignal%250A%2509Session%2B%252C%2BData%250A%257D%250Ac2FuZGVlcEBmdmNvbS5hZQ== | unknown | html | 24.4 Kb | whitelisted |
3964 | msedge.exe | GET | 200 | 95.100.135.57:443 | https://aadcdn.msftauth.net/shared/1.0/content/js/FetchSessions_Core_rDgHf4gCP_X0cckkwpBJVw2.js | unknown | — | 146 Kb | whitelisted |
3964 | msedge.exe | GET | 200 | 95.100.135.57:443 | https://aadcdn.msftauth.net/shared/1.0/content/js/FetchSessions_Core_rDgHf4gCP_X0cckkwpBJVw2.js | unknown | text | 146 Kb | whitelisted |
3964 | msedge.exe | GET | 200 | 20.190.160.3:443 | https://login.live.com/Me.htm?v=3 | unknown | — | 3.37 Kb | whitelisted |
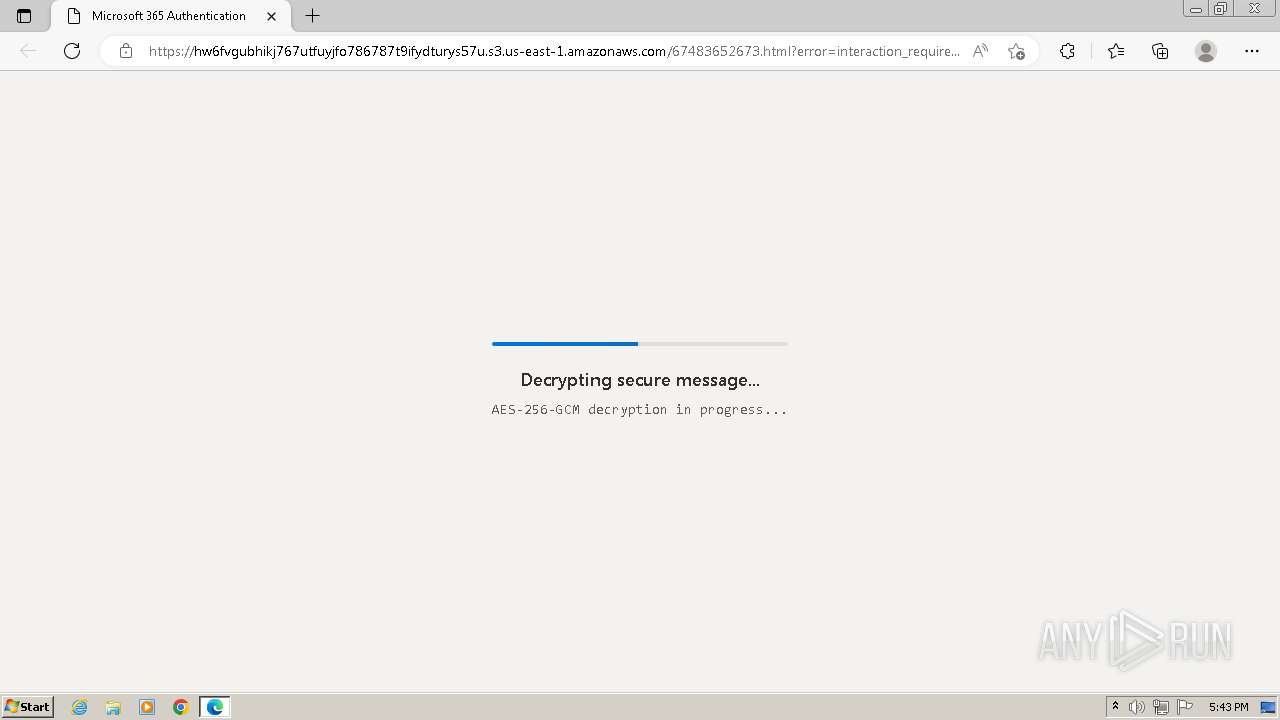
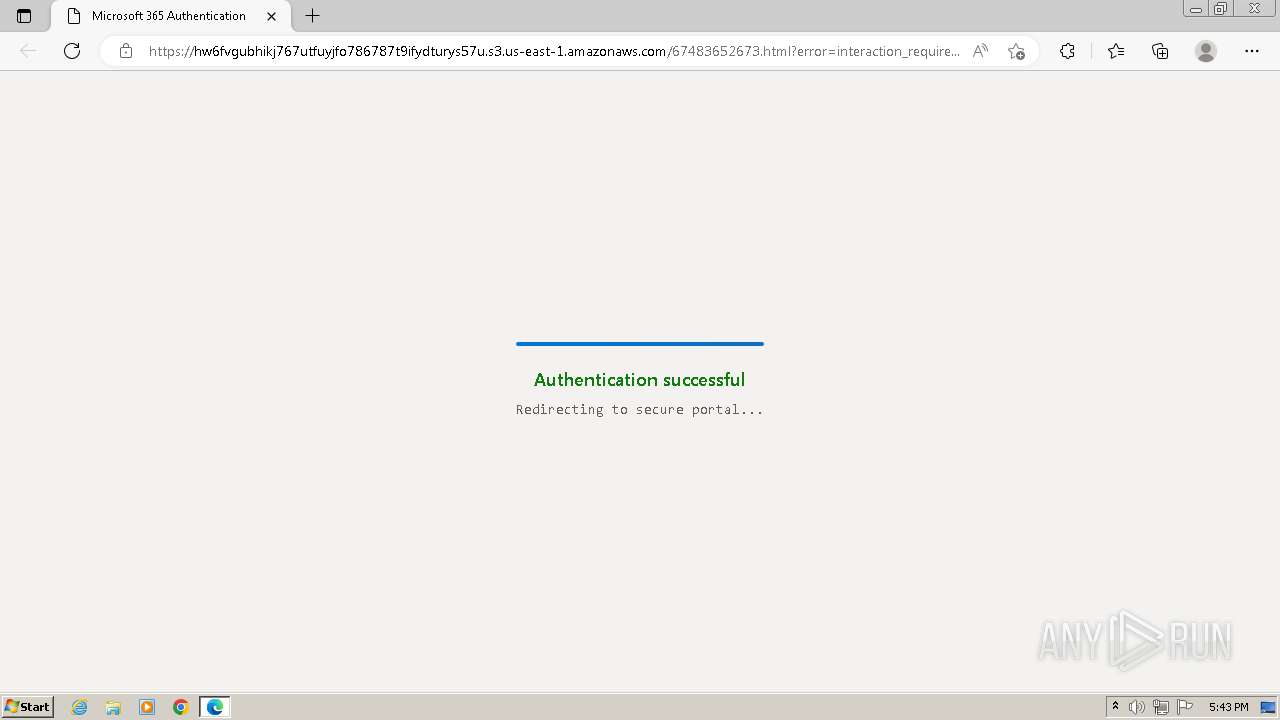
3964 | msedge.exe | GET | 200 | 52.217.173.170:443 | https://hw6fvgubhikj767utfuyjfo786787t9ifydturys57u.s3.us-east-1.amazonaws.com/67483652673.html?error=interaction_required&error_description=Session+information+is+not+sufficient+for+single-sign-on.&state=Y2FybG9zX21lYWRlQGhkbS5ob25kYS5jb20%3d | unknown | html | 9.36 Kb | unknown |
3964 | msedge.exe | GET | 403 | 52.217.173.170:443 | https://hw6fvgubhikj767utfuyjfo786787t9ifydturys57u.s3.us-east-1.amazonaws.com/favicon.ico | unknown | xml | 243 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1092 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
3964 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3964 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3788 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3964 | msedge.exe | 20.190.160.3:443 | login.microsoftonline.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3964 | msedge.exe | 95.100.135.57:443 | aadcdn.msftauth.net | AKAMAI-ASN1 | NL | whitelisted |
3964 | msedge.exe | 52.217.173.170:443 | hw6fvgubhikj767utfuyjfo786787t9ifydturys57u.s3.us-east-1.amazonaws.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
aadcdn.msftauth.net |
| whitelisted |
aadcdn.msauth.net |
| whitelisted |
login.live.com |
| whitelisted |
hw6fvgubhikj767utfuyjfo786787t9ifydturys57u.s3.us-east-1.amazonaws.com |
| unknown |
identity.nel.measure.office.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
3964 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Generic Phishing domain has been detected |
3964 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
3964 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Generic Phishing domain has been detected |
3964 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |