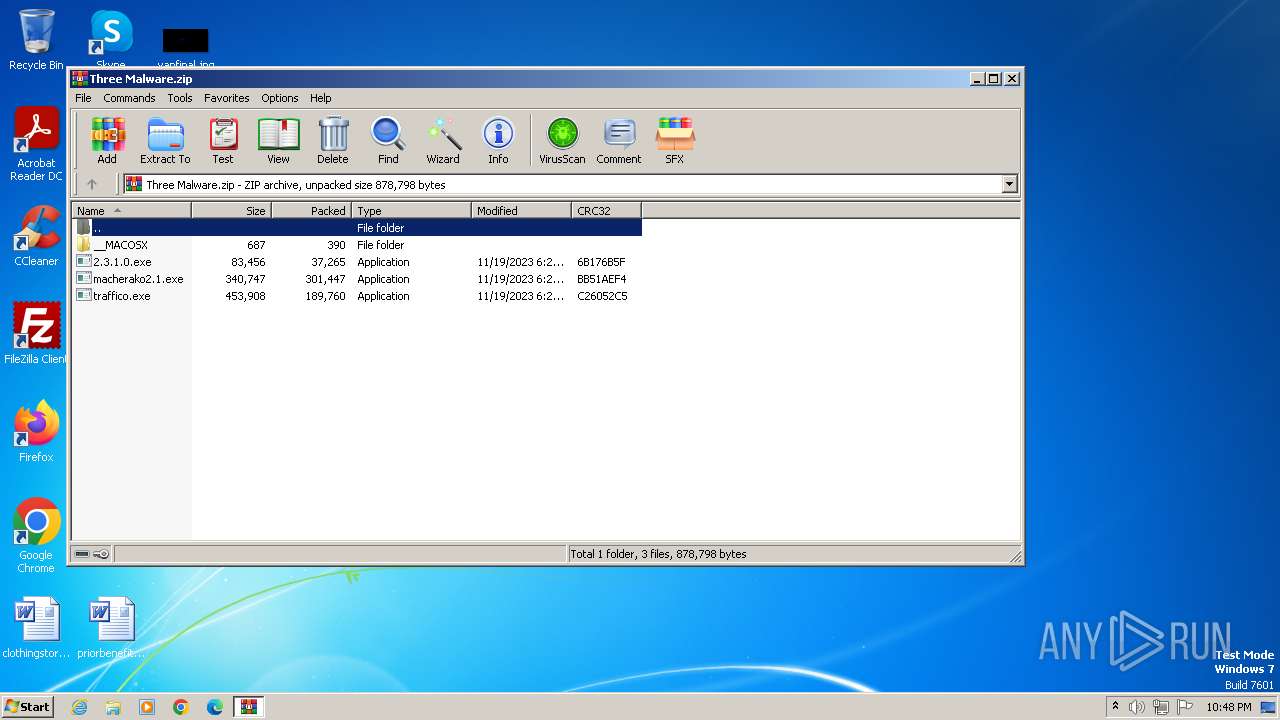
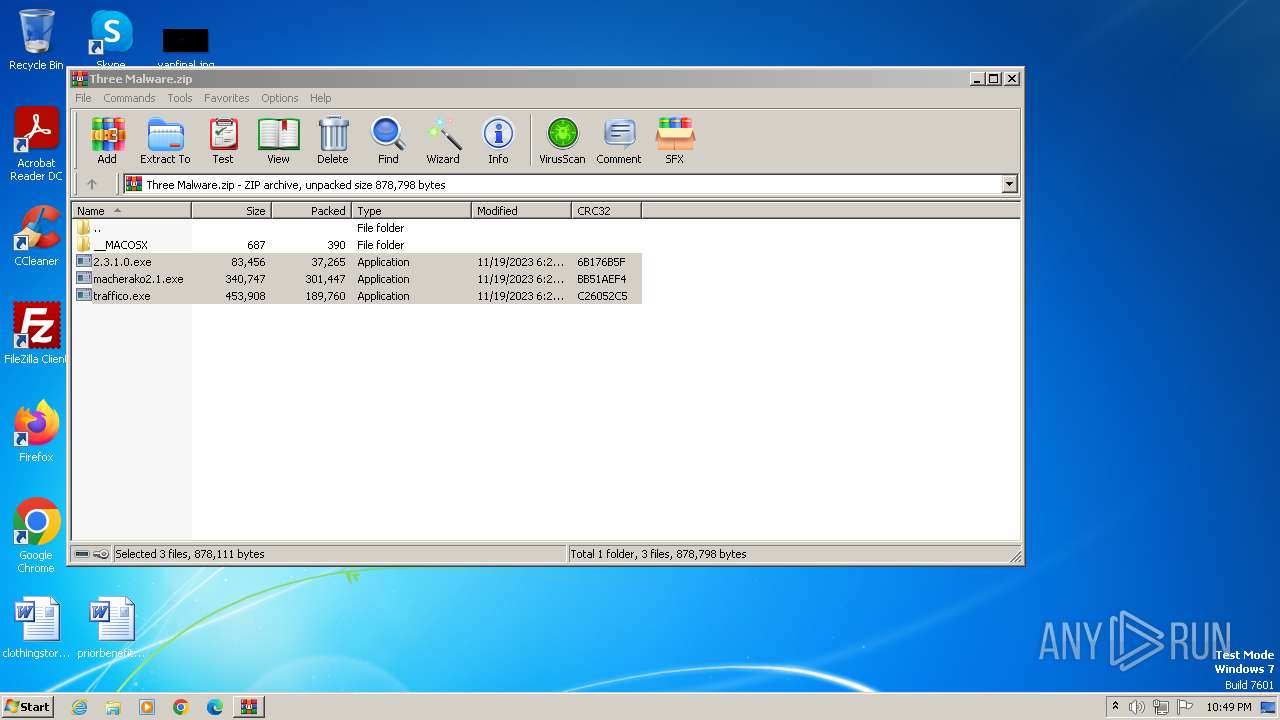
| File name: | Three Malware.zip |
| Full analysis: | https://app.any.run/tasks/7bd67ee5-8861-47f8-baa3-bbf69a5c65ec |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 20, 2023, 22:48:39 |
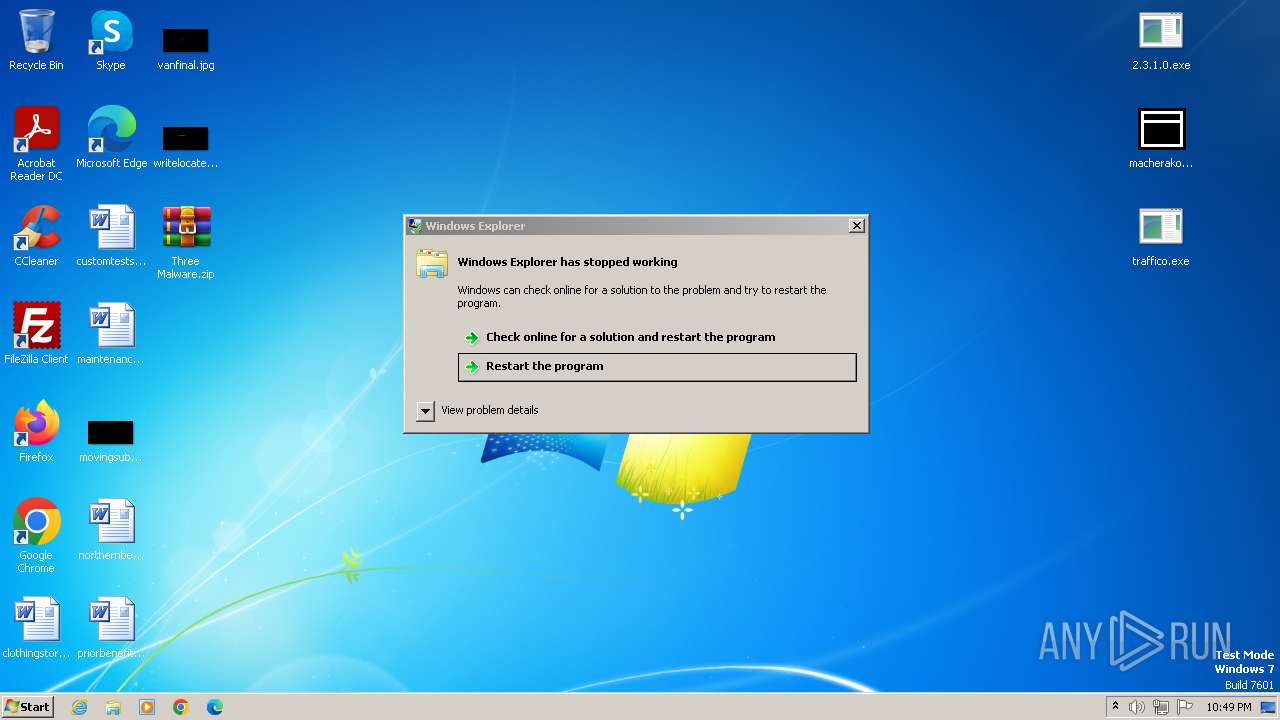
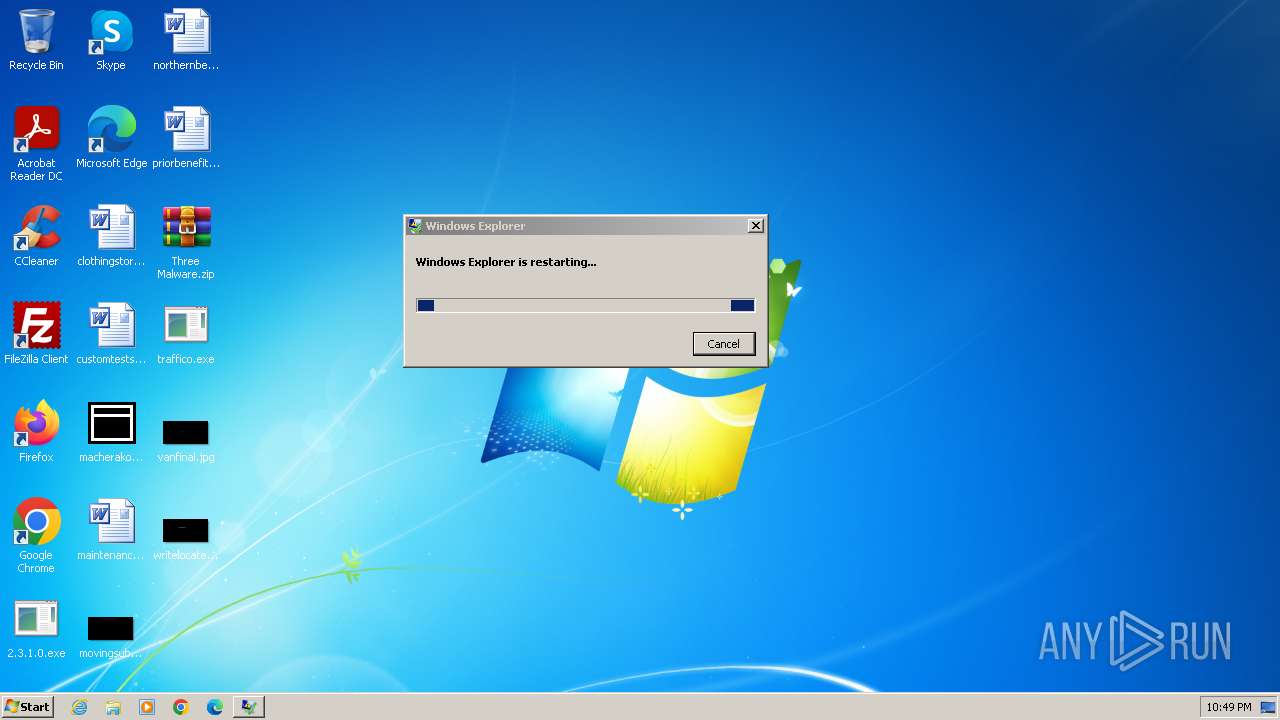
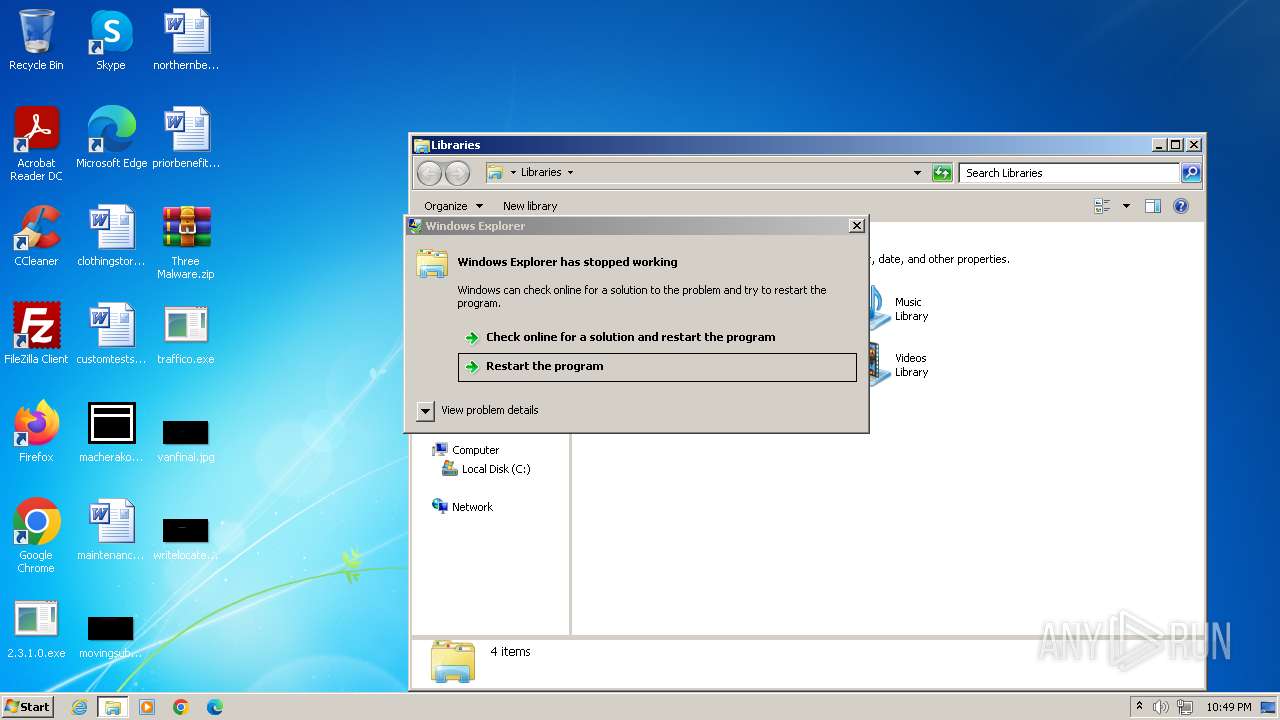
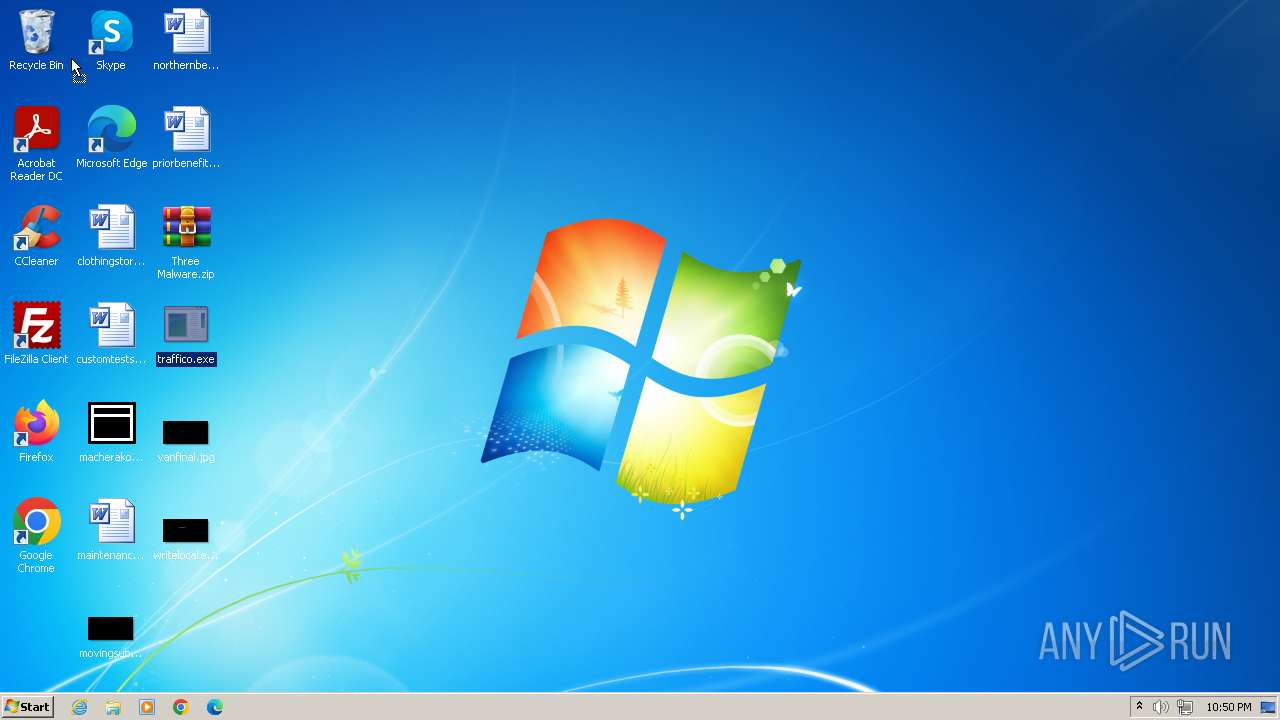
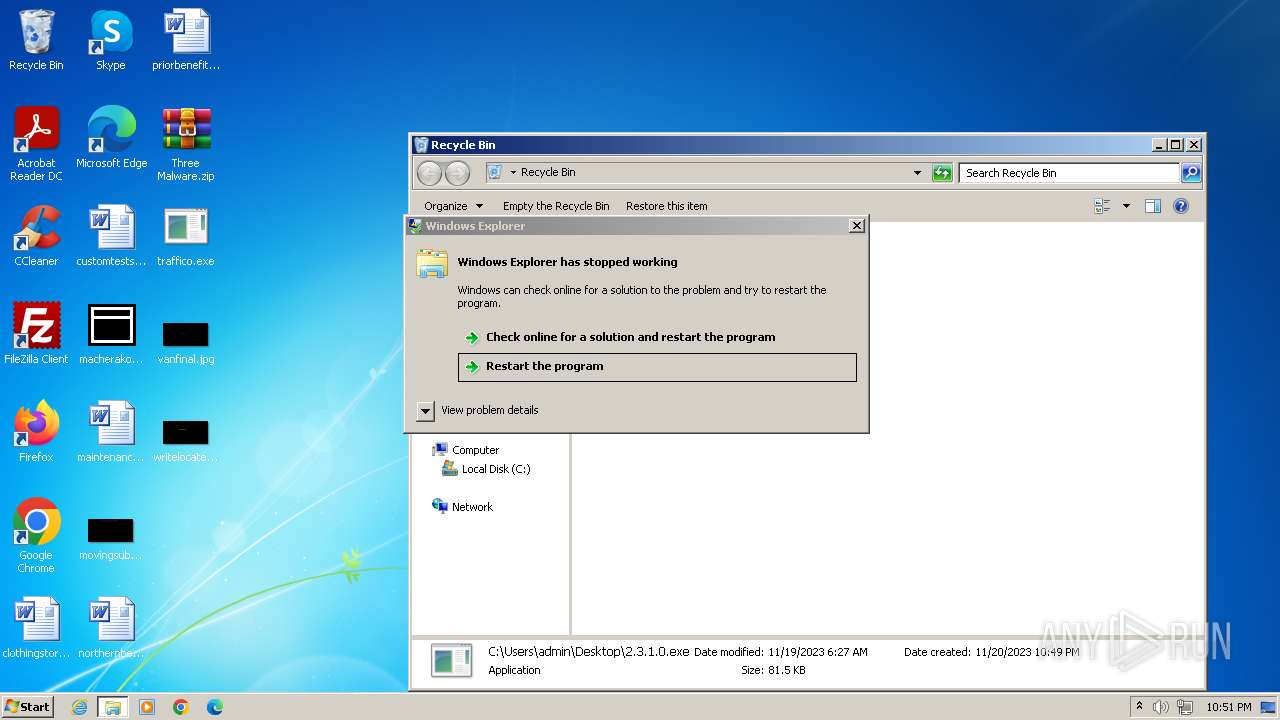
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9EFB1B0FAD0778B270835C199E0916A7 |
| SHA1: | 2DE9EE4C8783C881FFF622BFA3C09F93EE5C68DF |
| SHA256: | FFA53213AA9E6BF86464BC8A23B17FB908B7123C8D7C28EC118A31F2F754273C |
| SSDEEP: | 24576:PBeMSIMgPsEGoszbHM+mjbZWStr89E75T8octu9VCGLL:PBeMSIMgPsRoszbHM+mjbZWStr89E75X |
MALICIOUS
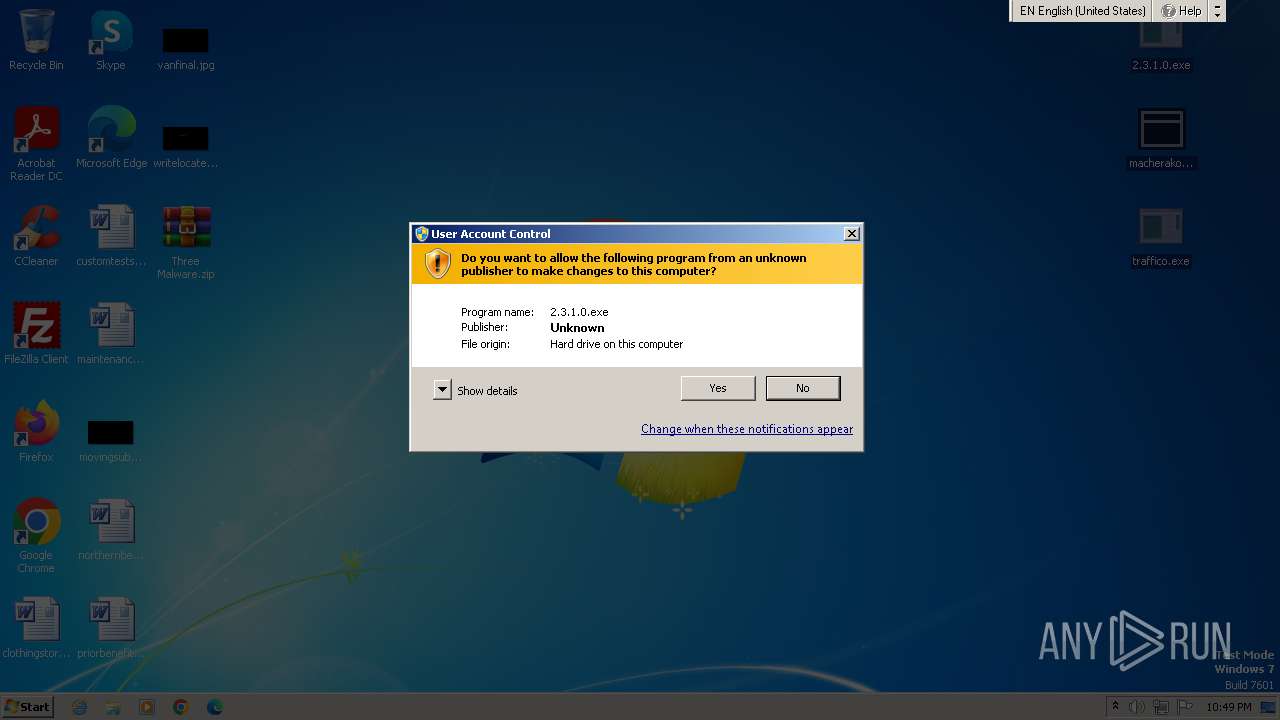
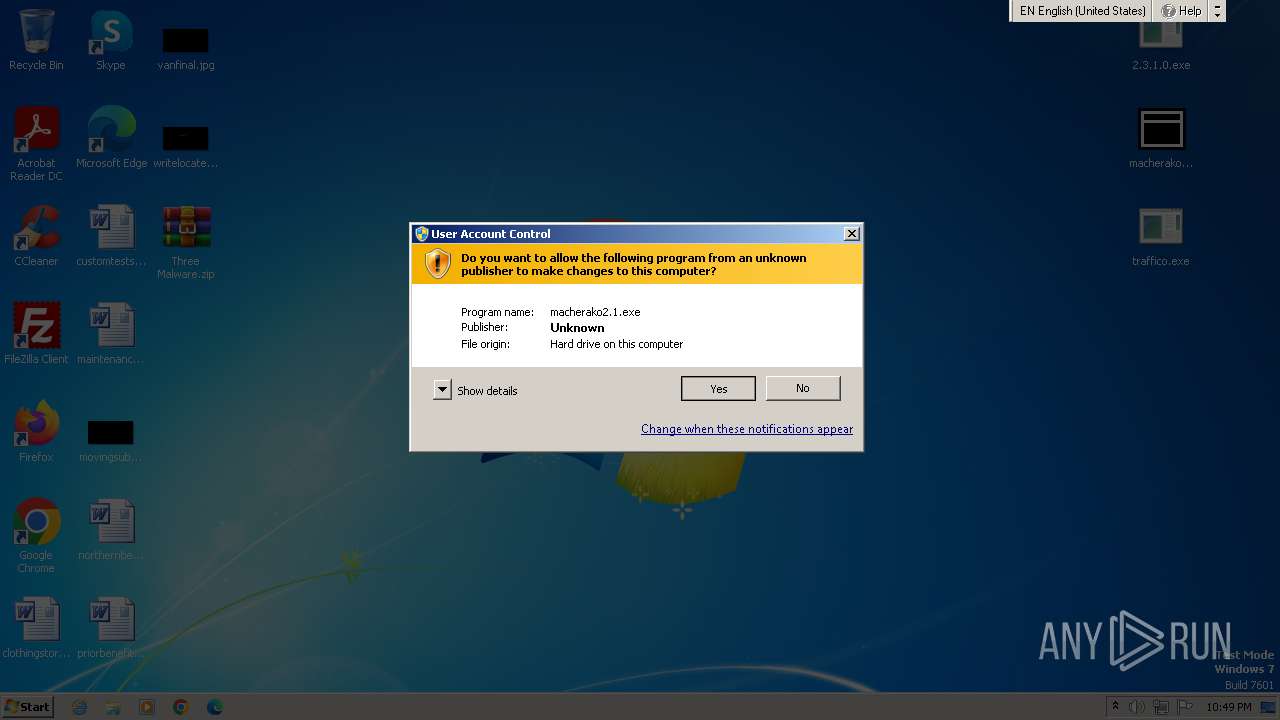
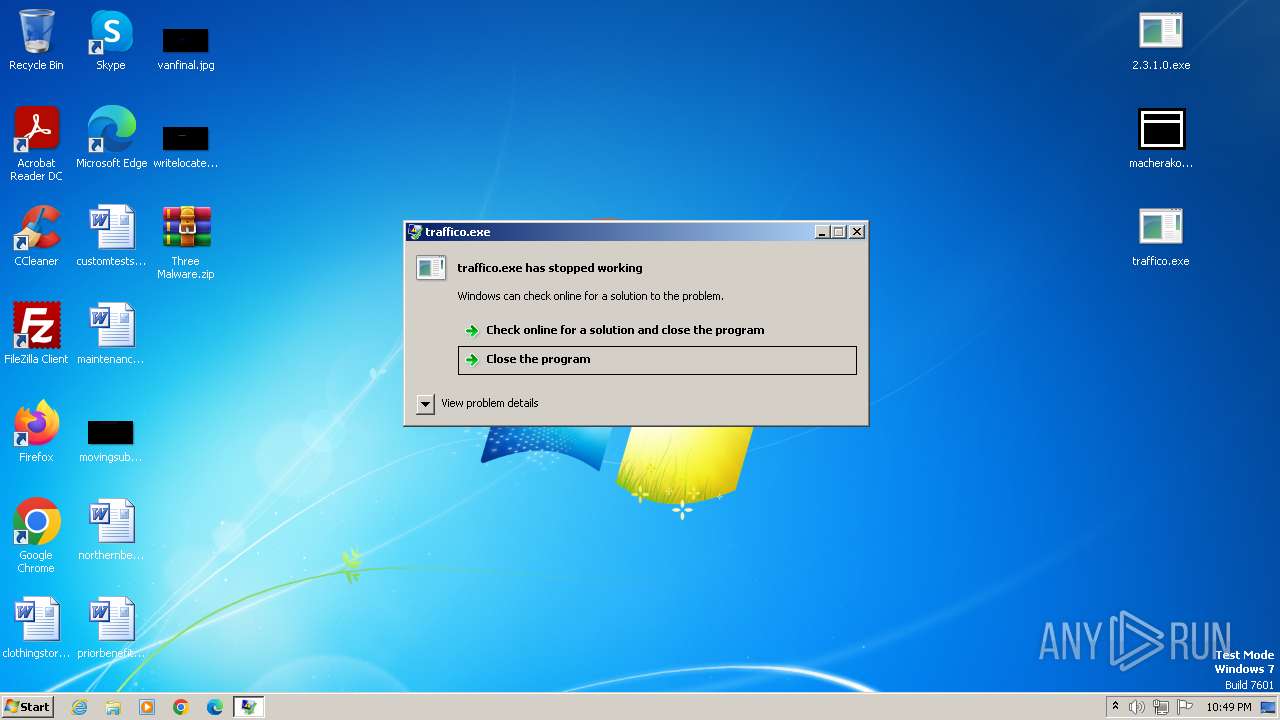
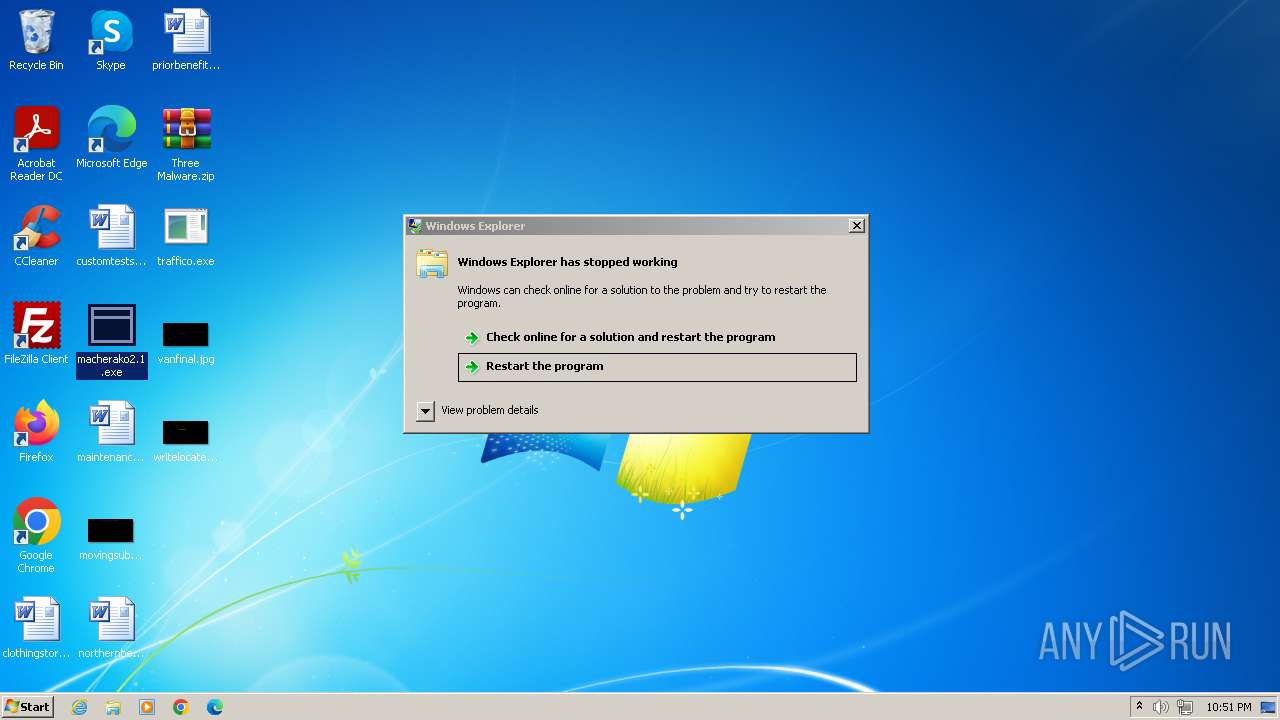
Drops the executable file immediately after the start
- macherako2.1.exe (PID: 3760)
- 2.3.1.0.exe (PID: 3724)
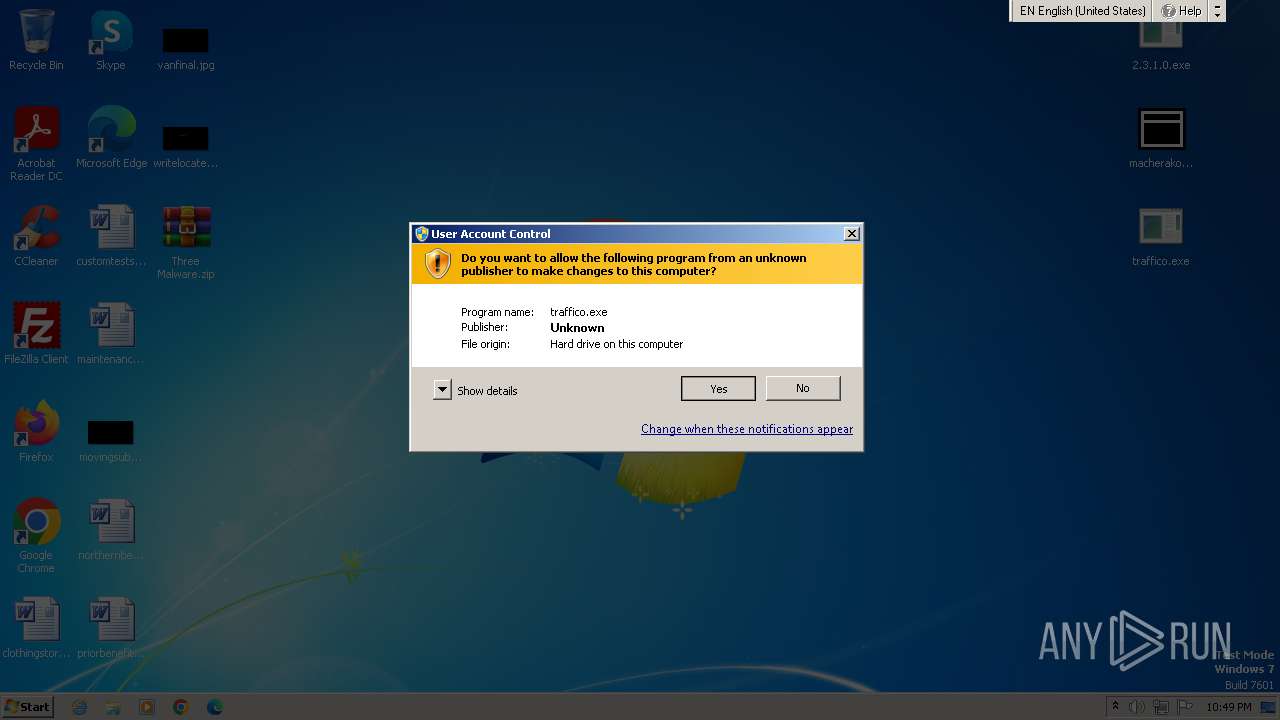
Connects to the CnC server
- 2.3.1.0.exe (PID: 3724)
- traffico.exe (PID: 3264)
RACCOON has been detected (SURICATA)
- 2.3.1.0.exe (PID: 3724)
FORMBOOK has been detected (YARA)
- NETSTAT.EXE (PID: 316)
Steals credentials from Web Browsers
- traffico.exe (PID: 3264)
REDLINE has been detected (SURICATA)
- traffico.exe (PID: 3264)
Actions looks like stealing of personal data
- traffico.exe (PID: 3264)
SUSPICIOUS
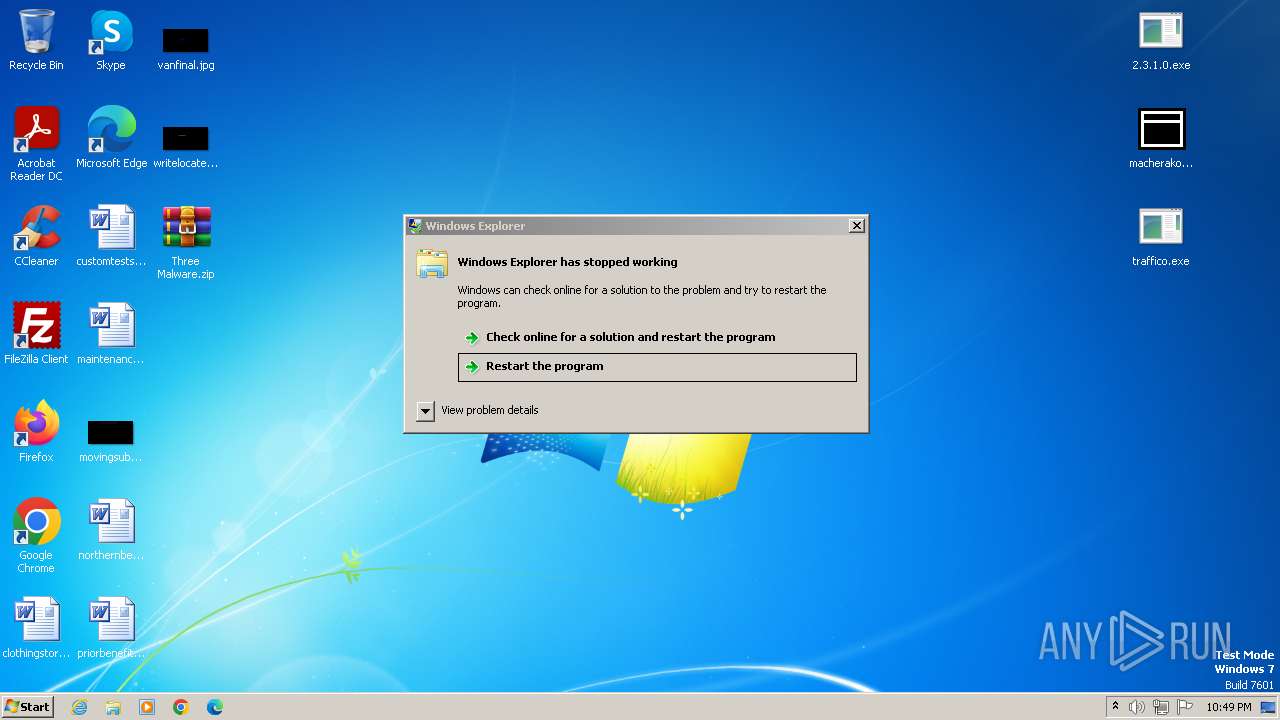
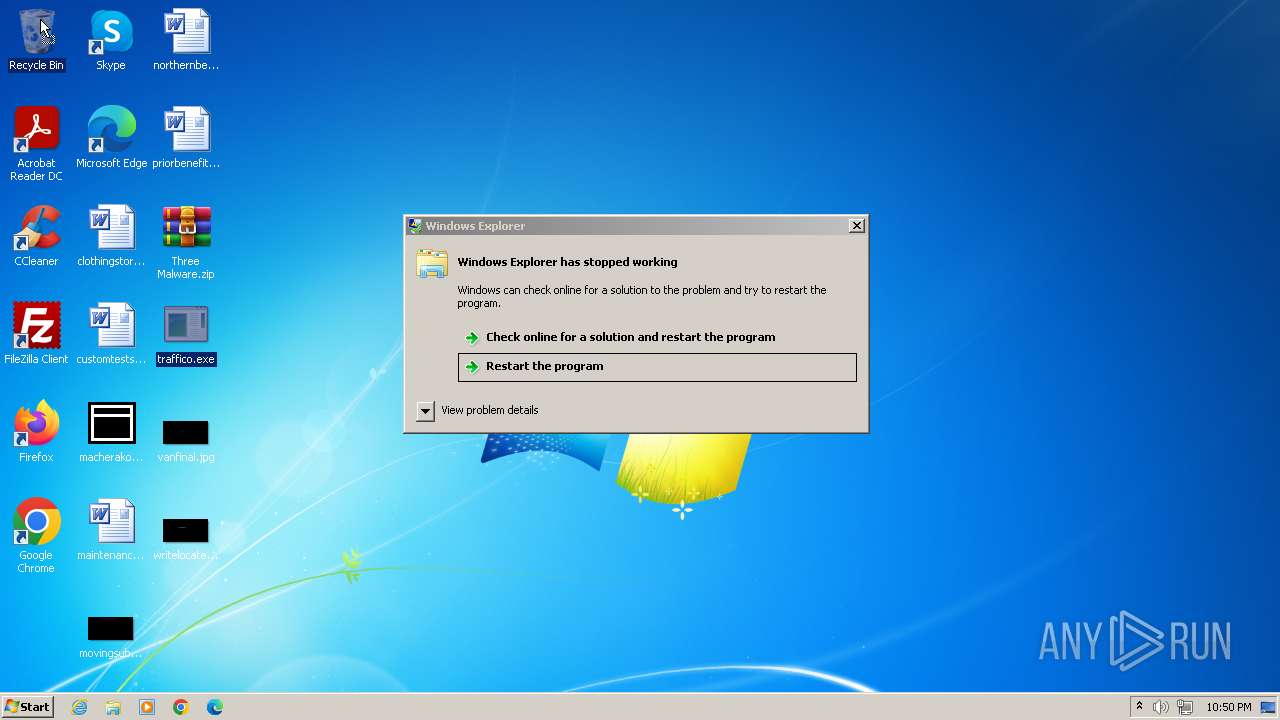
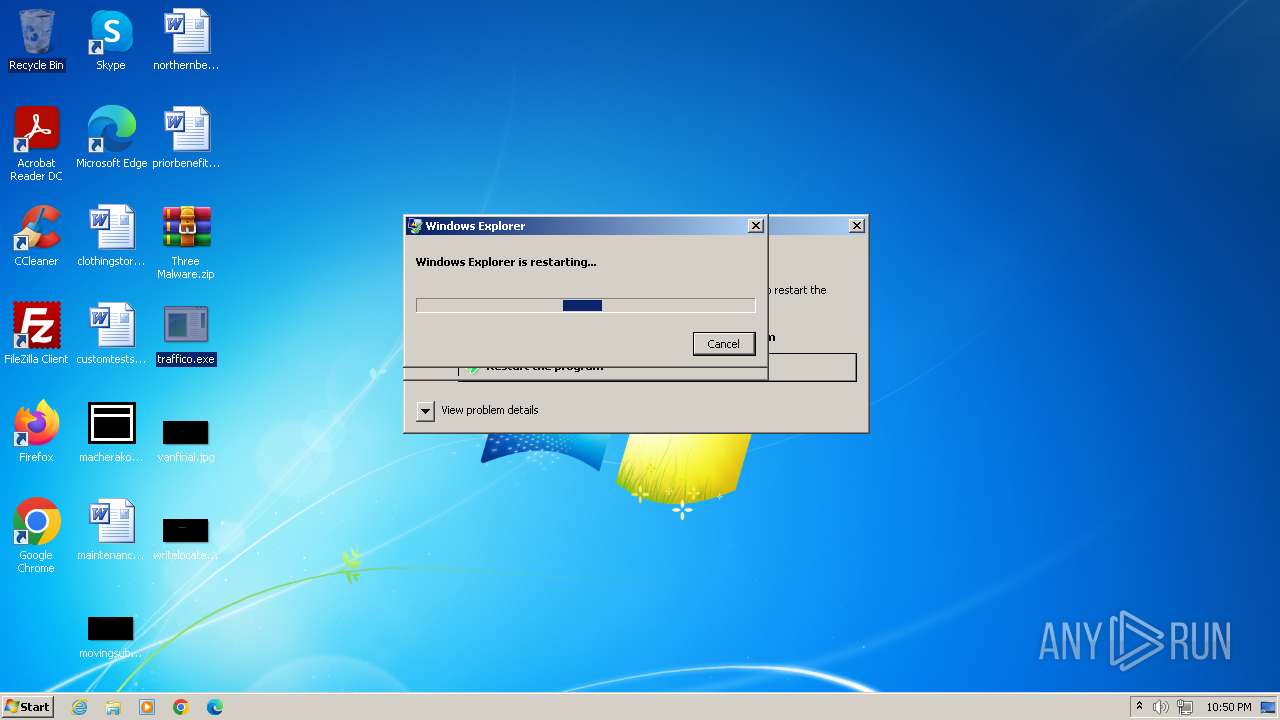
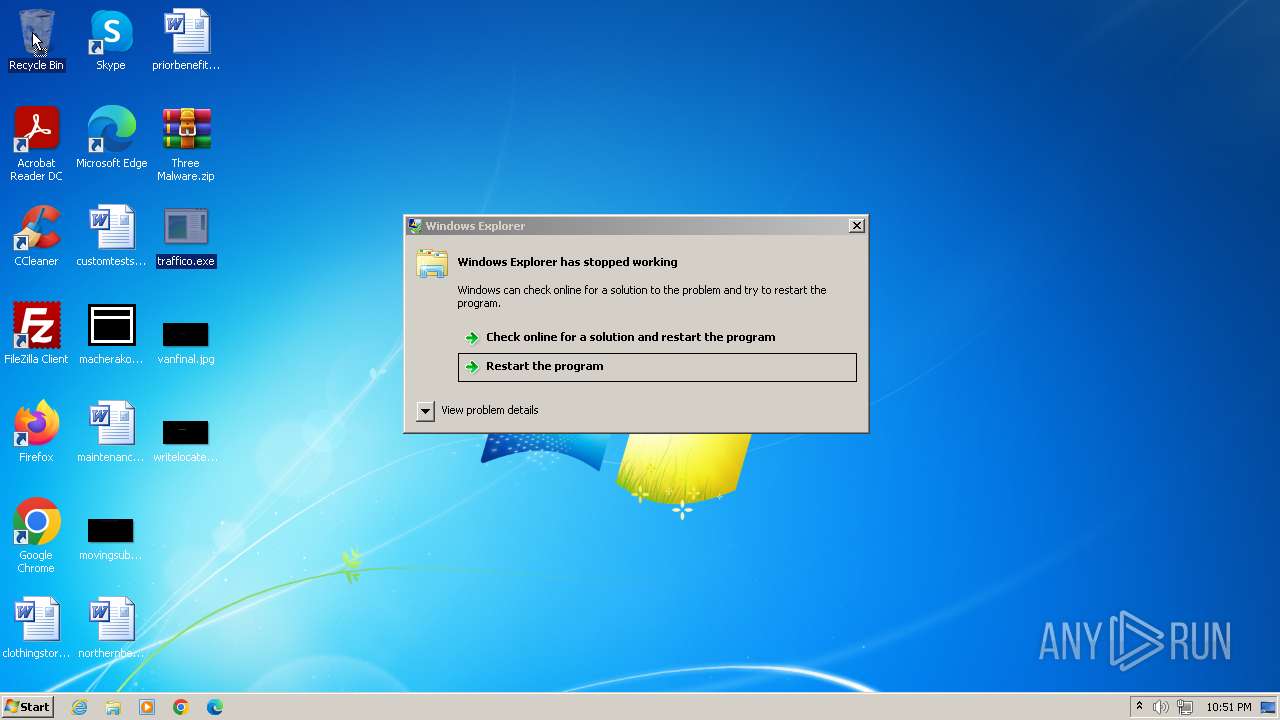
Application launched itself
- cegsxx.exe (PID: 3236)
Reads the Internet Settings
- 2.3.1.0.exe (PID: 3724)
Starts CMD.EXE for commands execution
- NETSTAT.EXE (PID: 316)
Connects to the server without a host name
- 2.3.1.0.exe (PID: 3724)
Connects to unusual port
- traffico.exe (PID: 3264)
Process requests binary or script from the Internet
- 2.3.1.0.exe (PID: 3724)
Searches for installed software
- traffico.exe (PID: 3264)
Reads browser cookies
- traffico.exe (PID: 3264)
The process drops Mozilla's DLL files
- 2.3.1.0.exe (PID: 3724)
The process drops C-runtime libraries
- 2.3.1.0.exe (PID: 3724)
Process drops legitimate windows executable
- 2.3.1.0.exe (PID: 3724)
Process drops SQLite DLL files
- 2.3.1.0.exe (PID: 3724)
INFO
Reads the machine GUID from the registry
- 2.3.1.0.exe (PID: 3724)
- wmpnscfg.exe (PID: 2880)
- wmpnscfg.exe (PID: 372)
- traffico.exe (PID: 3264)
- wmpnscfg.exe (PID: 3980)
- wmpnscfg.exe (PID: 908)
- wmpnscfg.exe (PID: 3908)
- wmpnscfg.exe (PID: 2992)
- wmpnscfg.exe (PID: 2788)
- wmpnscfg.exe (PID: 1460)
- wmpnscfg.exe (PID: 2460)
- wmpnscfg.exe (PID: 448)
Reads the computer name
- 2.3.1.0.exe (PID: 3724)
- macherako2.1.exe (PID: 3760)
- cegsxx.exe (PID: 2380)
- traffico.exe (PID: 1852)
- wmpnscfg.exe (PID: 2880)
- wmpnscfg.exe (PID: 372)
- traffico.exe (PID: 3264)
- wmpnscfg.exe (PID: 3980)
- wmpnscfg.exe (PID: 908)
- wmpnscfg.exe (PID: 3908)
- wmpnscfg.exe (PID: 2992)
- wmpnscfg.exe (PID: 2788)
- wmpnscfg.exe (PID: 2460)
- wmpnscfg.exe (PID: 448)
- wmpnscfg.exe (PID: 1460)
Checks supported languages
- 2.3.1.0.exe (PID: 3724)
- macherako2.1.exe (PID: 3760)
- cegsxx.exe (PID: 3236)
- traffico.exe (PID: 1852)
- cegsxx.exe (PID: 2380)
- wmpnscfg.exe (PID: 2880)
- wmpnscfg.exe (PID: 372)
- traffico.exe (PID: 3264)
- wmpnscfg.exe (PID: 3980)
- wmpnscfg.exe (PID: 908)
- wmpnscfg.exe (PID: 3908)
- wmpnscfg.exe (PID: 2992)
- wmpnscfg.exe (PID: 2788)
- wmpnscfg.exe (PID: 1460)
- wmpnscfg.exe (PID: 448)
- wmpnscfg.exe (PID: 2460)
Checks proxy server information
- 2.3.1.0.exe (PID: 3724)
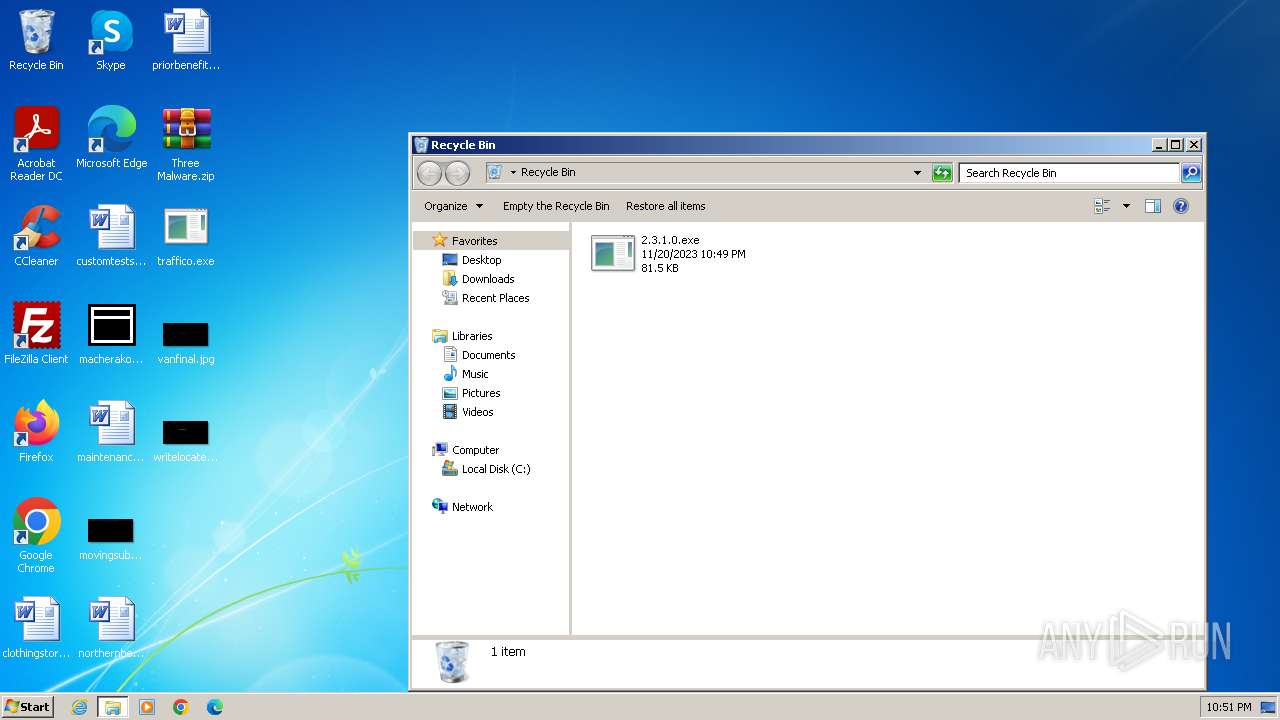
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3484)
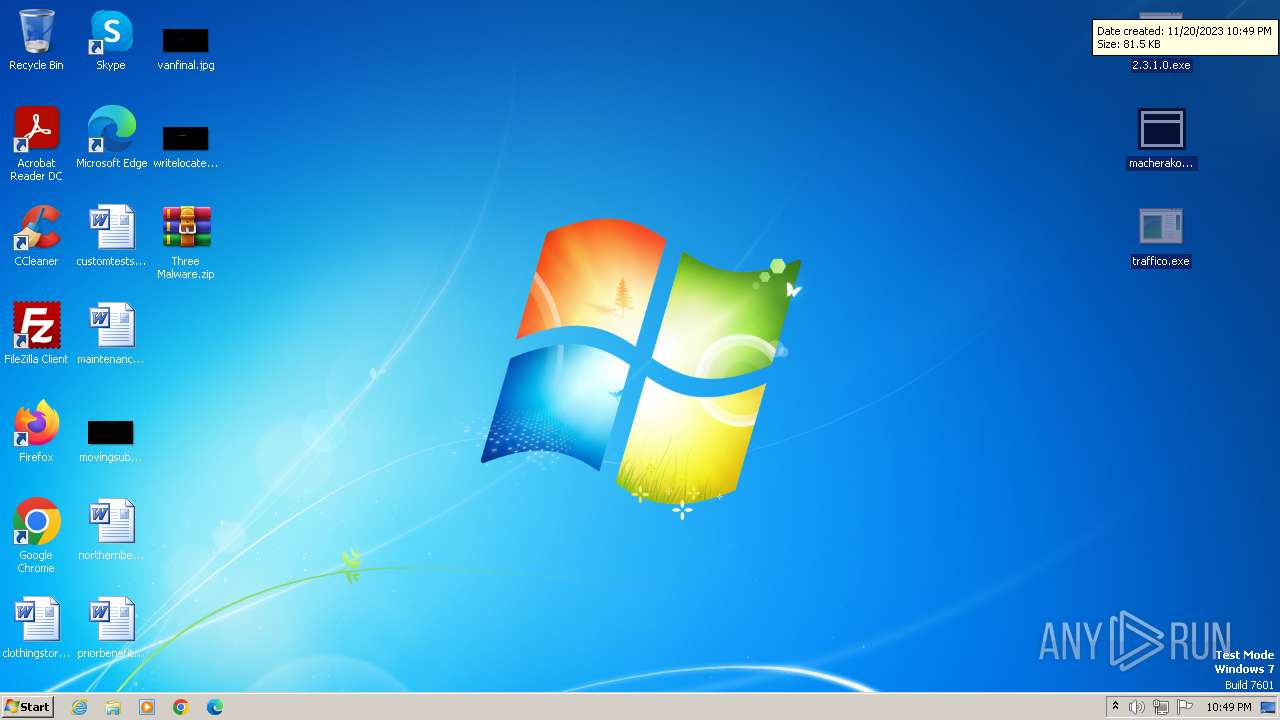
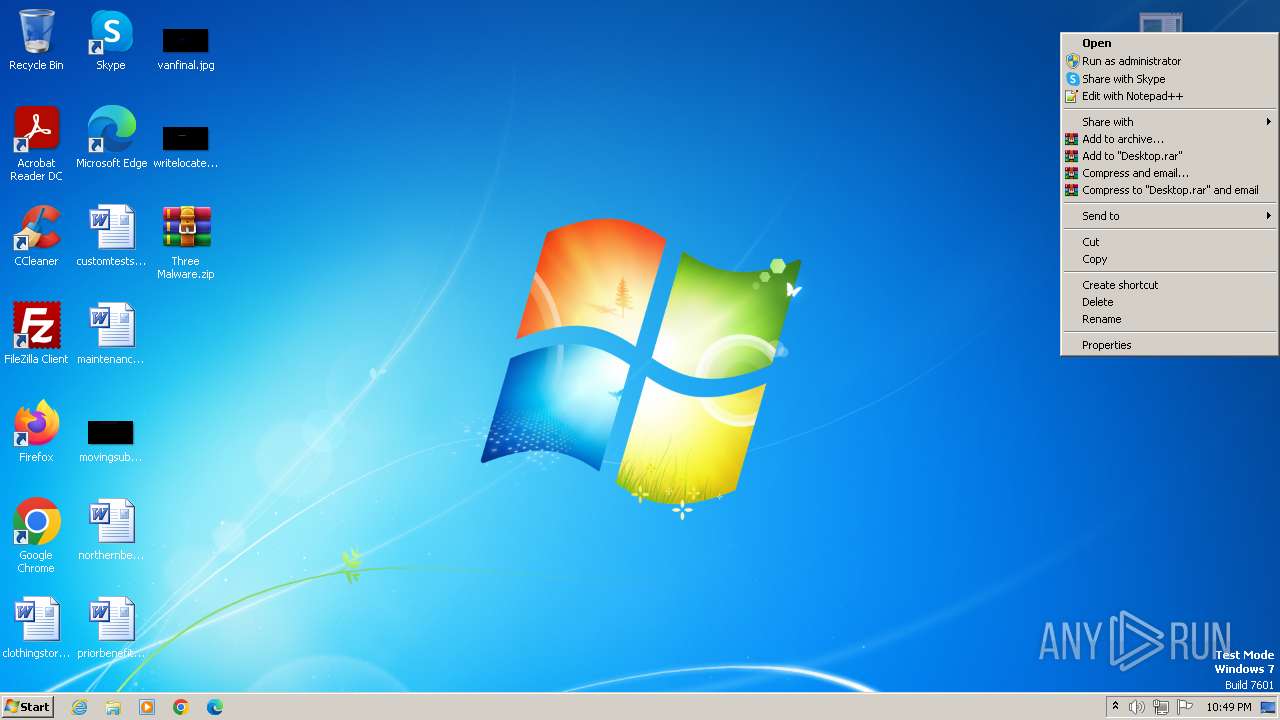
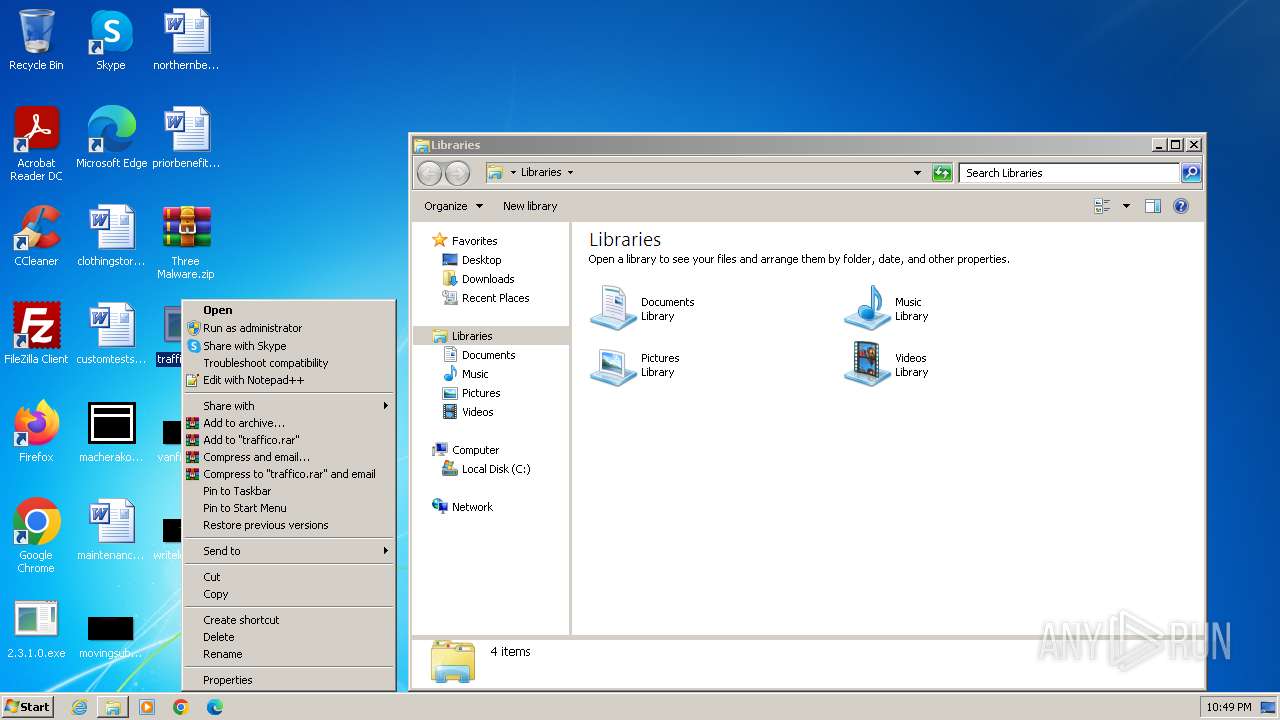
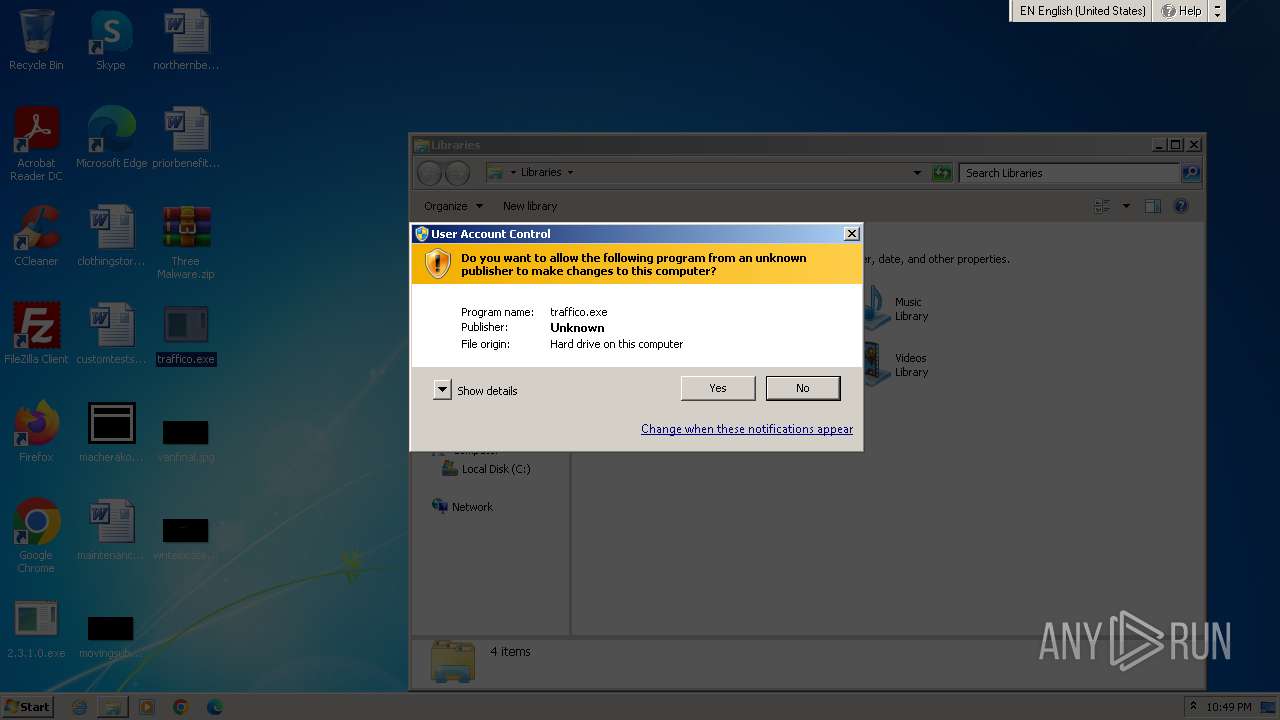
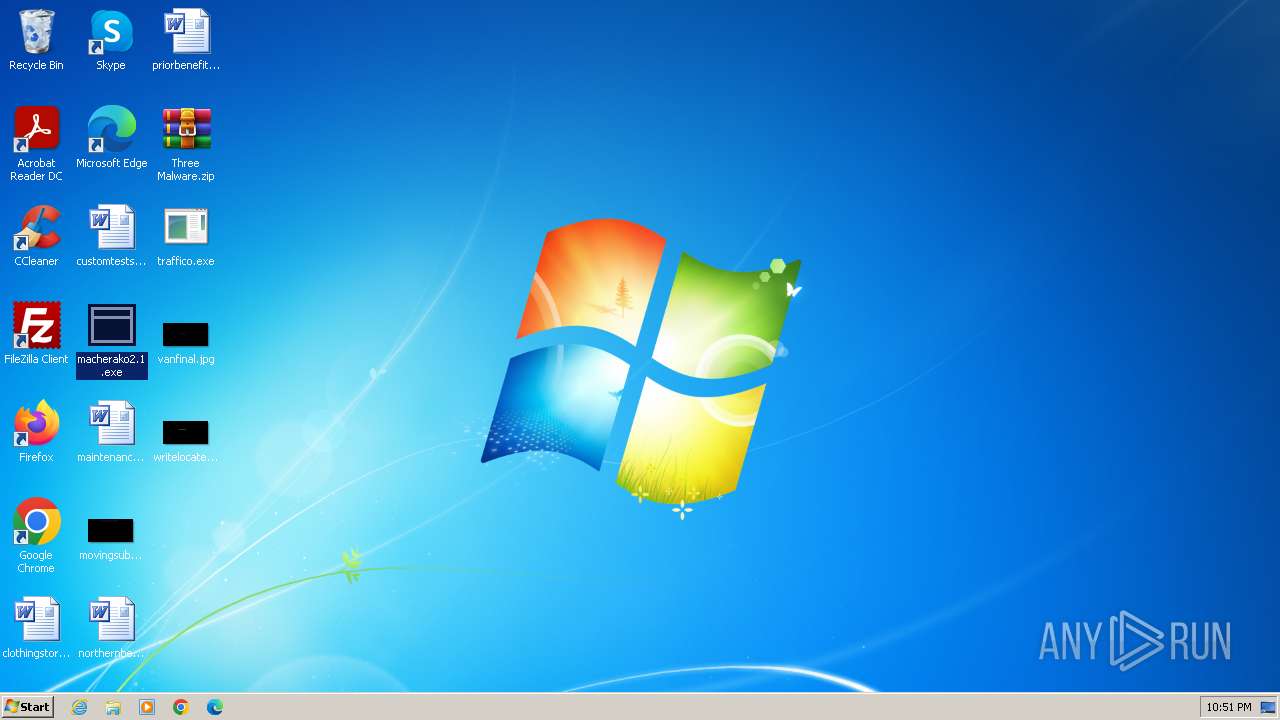
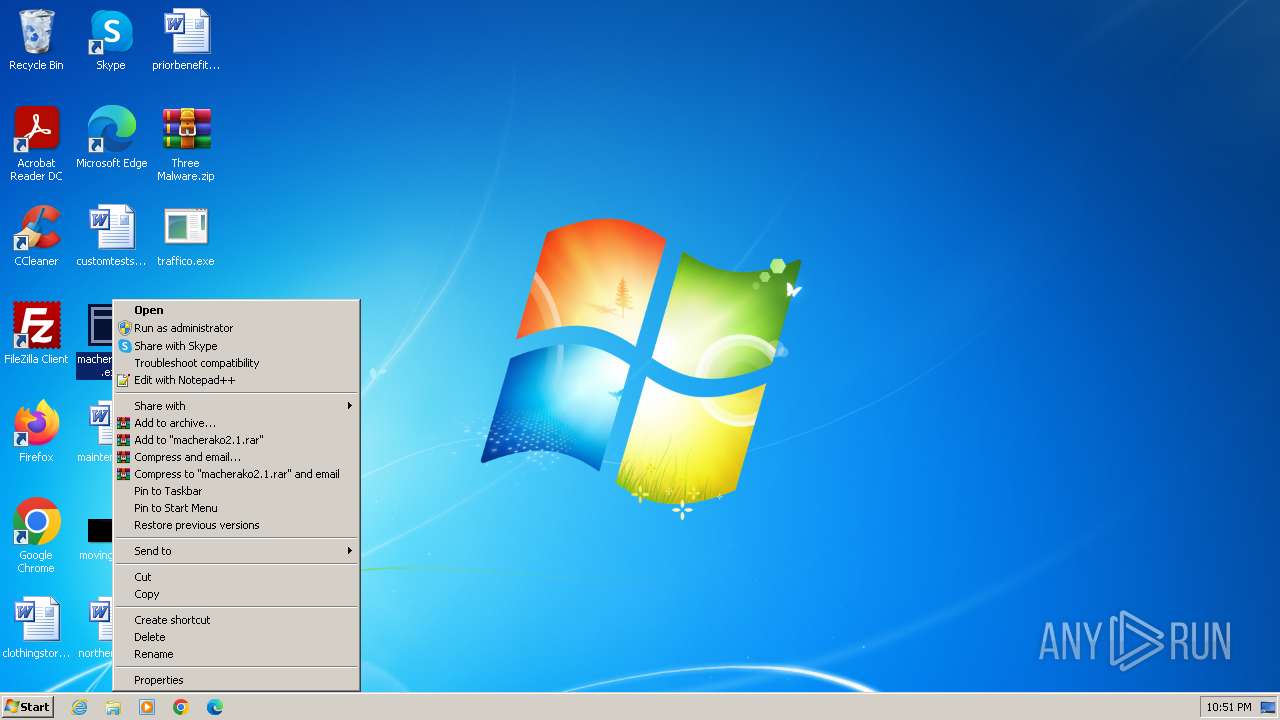
Manual execution by a user
- 2.3.1.0.exe (PID: 3724)
- macherako2.1.exe (PID: 3760)
- traffico.exe (PID: 1852)
- NETSTAT.EXE (PID: 316)
- wmpnscfg.exe (PID: 2880)
- wmpnscfg.exe (PID: 372)
- traffico.exe (PID: 3264)
- wmpnscfg.exe (PID: 3980)
- wmpnscfg.exe (PID: 908)
- wmpnscfg.exe (PID: 3908)
- wmpnscfg.exe (PID: 2992)
- wmpnscfg.exe (PID: 2788)
- wmpnscfg.exe (PID: 2460)
- wmpnscfg.exe (PID: 448)
- wmpnscfg.exe (PID: 1460)
Create files in a temporary directory
- macherako2.1.exe (PID: 3760)
Creates files or folders in the user directory
- 2.3.1.0.exe (PID: 3724)
Reads Environment values
- traffico.exe (PID: 3264)
Reads product name
- traffico.exe (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(316) NETSTAT.EXE
C2www.free-indeed.faith/tb8i/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)097jz.com
physium.net
sherwoodsubnet.com
scbaya.fun
us2048.top
danlclmn.com
starsyx.com
foxbox-digi.store
thefishermanhouse.com
salvanandcie.com
rykuruh.cfd
gelaoguan.net
petar-gojun.com
coandcompanyboutique.com
decentralizedcryptos.com
ecuajet.net
livbythebeach.com
cleaning-services-33235.bond
free-webbuilder.today
pussypower.net
tron-pk.xyz
heirvaeh.com
9129z18.com
0x0audits.top
gpoinad.com
texwwfrx.com
bonusurunler.online
babytoy-deals.com
8onlyfans.com
farmermapa.net
vallishealth.com
tiyu116.net
driftlessmenofthewoods.com
jaliyahsboutique.site
hillandvalley.wine
funlifeday.net
kmrcounselling.online
rolandofrias.online
6632k.vip
reporttask.online
99dd88.buzz
bradleymartinfitness.com
superflowers.pro
startaxeindhoven.com
districonsumohome.com
wombancircle.com
gdtanhua.icu
strikkzone.com
otismc.net
dataxmesh.com
assosolico.net
grataballi.com
geigenbau-duesseldorf.com
freightlizards.com
sololinkliving.com
hecticgame.com
stx.lat
cleanfood.bio
ismprojects.net
reillyleet.com
socialise.biz
collaco.info
genevalakeagent.com
drivefta.com
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:11:19 00:27:22 |
| ZipCRC: | 0x6b176b5f |
| ZipCompressedSize: | 37265 |
| ZipUncompressedSize: | 83456 |
| ZipFileName: | 2.3.1.0.exe |
Total processes
85
Monitored processes
19
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Windows\System32\NETSTAT.EXE" | C:\Windows\System32\NETSTAT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Formbook(PID) Process(316) NETSTAT.EXE C2www.free-indeed.faith/tb8i/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)097jz.com physium.net sherwoodsubnet.com scbaya.fun us2048.top danlclmn.com starsyx.com foxbox-digi.store thefishermanhouse.com salvanandcie.com rykuruh.cfd gelaoguan.net petar-gojun.com coandcompanyboutique.com decentralizedcryptos.com ecuajet.net livbythebeach.com cleaning-services-33235.bond free-webbuilder.today pussypower.net tron-pk.xyz heirvaeh.com 9129z18.com 0x0audits.top gpoinad.com texwwfrx.com bonusurunler.online babytoy-deals.com 8onlyfans.com farmermapa.net vallishealth.com tiyu116.net driftlessmenofthewoods.com jaliyahsboutique.site hillandvalley.wine funlifeday.net kmrcounselling.online rolandofrias.online 6632k.vip reporttask.online 99dd88.buzz bradleymartinfitness.com superflowers.pro startaxeindhoven.com districonsumohome.com wombancircle.com gdtanhua.icu strikkzone.com otismc.net dataxmesh.com assosolico.net grataballi.com geigenbau-duesseldorf.com freightlizards.com sololinkliving.com hecticgame.com stx.lat cleanfood.bio ismprojects.net reillyleet.com socialise.biz collaco.info genevalakeagent.com drivefta.com | |||||||||||||||
| 372 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | /c del "C:\Users\admin\AppData\Local\Temp\cegsxx.exe" | C:\Windows\System32\cmd.exe | — | NETSTAT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1852 | "C:\Users\admin\Desktop\traffico.exe" | C:\Users\admin\Desktop\traffico.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3762504530 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\cegsxx.exe" | C:\Users\admin\AppData\Local\Temp\cegsxx.exe | — | cegsxx.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 851
Read events
2 770
Write events
31
Delete events
50
Modification events
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
11
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3484.2613\traffico.exe | executable | |
MD5:FF4691F6C1F0E701303C2B135345890E | SHA256:06CF4C8C1B6AA436DFFF3EC427DBE4AE291D170A0AD7445003995BBF6CCB21CA | |||
| 3484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3484.2613\macherako2.1.exe | executable | |
MD5:5B691330ACAA3C5432B9CAADBEB82003 | SHA256:860B90BA1C36E237B2ACA9E77024D953E5AA3B9D4A736130D355DA6C76CF0930 | |||
| 3760 | macherako2.1.exe | C:\Users\admin\AppData\Local\Temp\cegsxx.exe | executable | |
MD5:0A1743CF9E74100A9FD023ACF3F36E49 | SHA256:5491E80A096D5F370F010E69D9ABA77EB3AB49F8A259DEA544106A7F4F7AAD74 | |||
| 3724 | 2.3.1.0.exe | C:\Users\admin\AppData\LocalLow\msvcp140.dll | executable | |
MD5:1FB93933FD087215A3C7B0800E6BB703 | SHA256:2DB7FD3C9C3C4B67F2D50A5A50E8C69154DC859780DD487C28A4E6ED1AF90D01 | |||
| 3724 | 2.3.1.0.exe | C:\Users\admin\AppData\LocalLow\vcruntime140.dll | executable | |
MD5:1B171F9A428C44ACF85F89989007C328 | SHA256:9D02E952396BDFF3ABFE5654E07B7A713C84268A225E11ED9A3BF338ED1E424C | |||
| 3724 | 2.3.1.0.exe | C:\Users\admin\AppData\LocalLow\freebl3.dll | executable | |
MD5:15B61E4A910C172B25FB7D8CCB92F754 | SHA256:B2AE93D30C8BEB0B26F03D4A8325AC89B92A299E8F853E5CAA51BB32575B06C6 | |||
| 3484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3484.2613\2.3.1.0.exe | executable | |
MD5:2EE11CEC1AADA0B6967AC085A7C9899B | SHA256:C6D0D98DD43822FE12A1D785DF4E391DB3C92846B0473B54762FBB929DE6F5CB | |||
| 3724 | 2.3.1.0.exe | C:\Users\admin\AppData\LocalLow\softokn3.dll | executable | |
MD5:63A1FE06BE877497C4C2017CA0303537 | SHA256:44BE3153C15C2D18F49674A092C135D3482FB89B77A1B2063D01D02985555FE0 | |||
| 3724 | 2.3.1.0.exe | C:\Users\admin\AppData\LocalLow\nss3.dll | executable | |
MD5:F67D08E8C02574CBC2F1122C53BFB976 | SHA256:C65B7AFB05EE2B2687E6280594019068C3D3829182DFE8604CE4ADF2116CC46E | |||
| 3724 | 2.3.1.0.exe | C:\Users\admin\AppData\LocalLow\sqlite3.dll | executable | |
MD5:DBF4F8DCEFB8056DC6BAE4B67FF810CE | SHA256:47B64311719000FA8C432165A0FDCDFED735D5B54977B052DE915B1CBBBF9D68 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
0
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3724 | 2.3.1.0.exe | POST | — | 193.233.132.12:80 | http://193.233.132.12/ | unknown | — | — | unknown |
3724 | 2.3.1.0.exe | GET | 200 | 193.233.132.12:80 | http://193.233.132.12/aN7jD0qO6kT5bK5bQ4eR8fE1xP7hL2vK/msvcp140.dll | unknown | executable | 438 Kb | unknown |
3724 | 2.3.1.0.exe | GET | 200 | 193.233.132.12:80 | http://193.233.132.12/aN7jD0qO6kT5bK5bQ4eR8fE1xP7hL2vK/nss3.dll | unknown | executable | 1.95 Mb | unknown |
3724 | 2.3.1.0.exe | GET | 200 | 193.233.132.12:80 | http://193.233.132.12/aN7jD0qO6kT5bK5bQ4eR8fE1xP7hL2vK/mozglue.dll | unknown | executable | 612 Kb | unknown |
3724 | 2.3.1.0.exe | GET | 200 | 193.233.132.12:80 | http://193.233.132.12/aN7jD0qO6kT5bK5bQ4eR8fE1xP7hL2vK/vcruntime140.dll | unknown | executable | 78.2 Kb | unknown |
3724 | 2.3.1.0.exe | GET | 200 | 193.233.132.12:80 | http://193.233.132.12/aN7jD0qO6kT5bK5bQ4eR8fE1xP7hL2vK/softokn3.dll | unknown | executable | 248 Kb | unknown |
3724 | 2.3.1.0.exe | GET | 200 | 193.233.132.12:80 | http://193.233.132.12/aN7jD0qO6kT5bK5bQ4eR8fE1xP7hL2vK/freebl3.dll | unknown | executable | 668 Kb | unknown |
3724 | 2.3.1.0.exe | GET | 200 | 193.233.132.12:80 | http://193.233.132.12/aN7jD0qO6kT5bK5bQ4eR8fE1xP7hL2vK/sqlite3.dll | unknown | executable | 1.05 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3724 | 2.3.1.0.exe | 193.233.132.12:80 | — | ATT-INTERNET4 | US | malicious |
3264 | traffico.exe | 194.49.94.80:42359 | — | Enes Koken | DE | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3724 | 2.3.1.0.exe | A Network Trojan was detected | ET MALWARE Win32/RecordBreaker CnC Checkin M1 |
3724 | 2.3.1.0.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
3724 | 2.3.1.0.exe | A suspicious filename was detected | ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity |
3724 | 2.3.1.0.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3264 | traffico.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
3264 | traffico.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer Related (MC-NMF Authorization) |
3264 | traffico.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity - MSValue (Outbound) |
3264 | traffico.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity - MSValue (Outbound) |
3264 | traffico.exe | A Network Trojan was detected | ET MALWARE Redline Stealer Activity (Response) |
3264 | traffico.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
Process | Message |
|---|---|
2.3.1.0.exe | tdxqivpkk |
2.3.1.0.exe | tmxpd7ohi |
2.3.1.0.exe | t7u6m37i2 |
2.3.1.0.exe | td4n89oo0 |
2.3.1.0.exe | thrmvjuov |
2.3.1.0.exe | t8vw7rgki |
2.3.1.0.exe | tkkij5u6v |
2.3.1.0.exe | tcyu0nuf6 |
2.3.1.0.exe | towmuv41y |
2.3.1.0.exe | tfwb5v3cm |