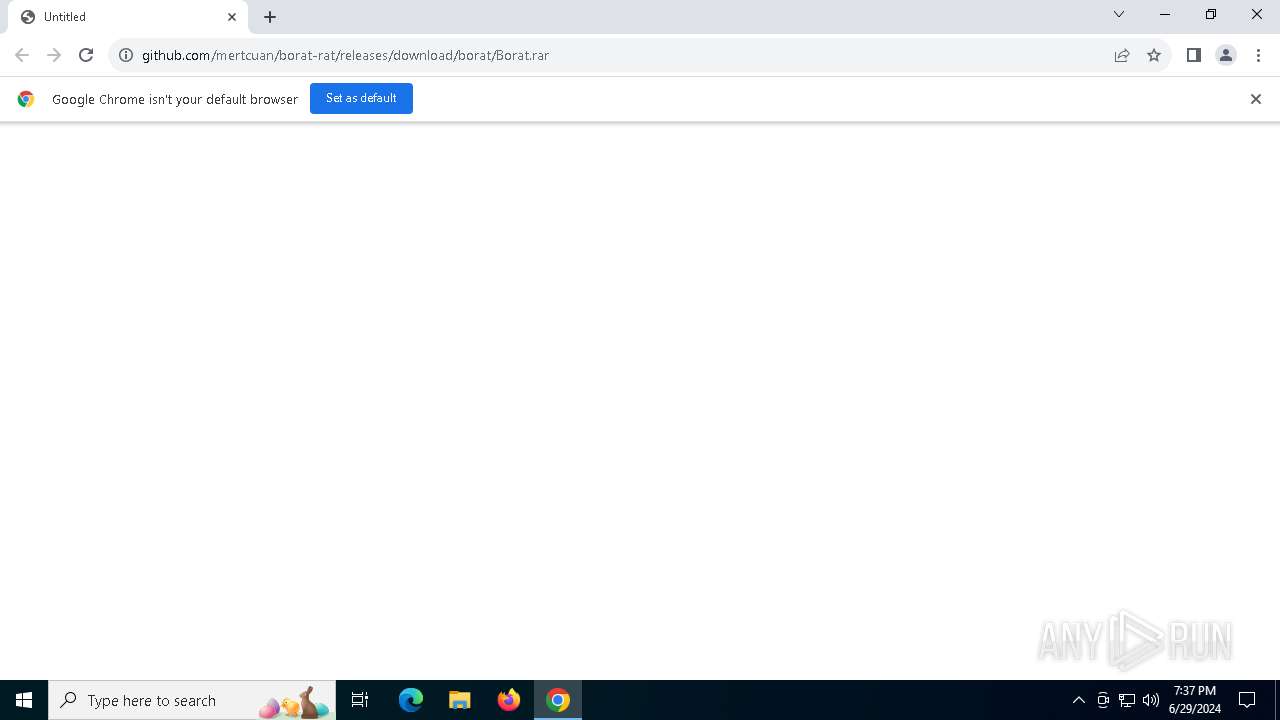
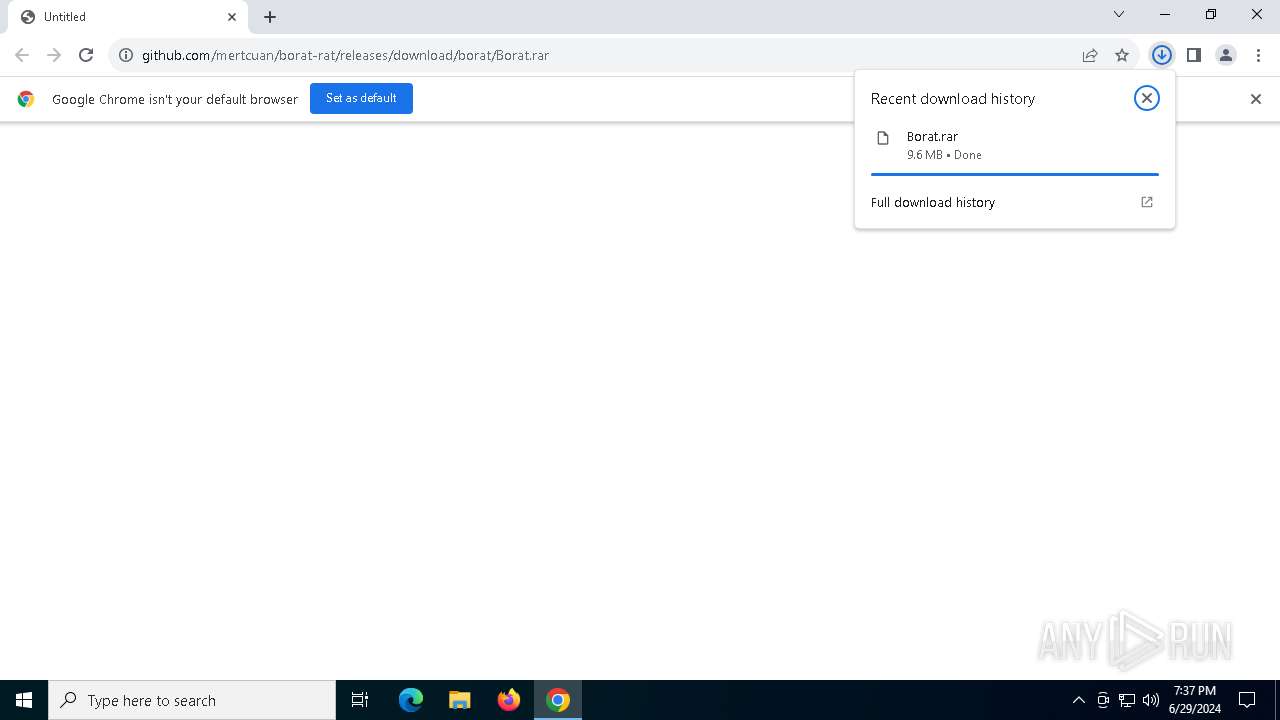
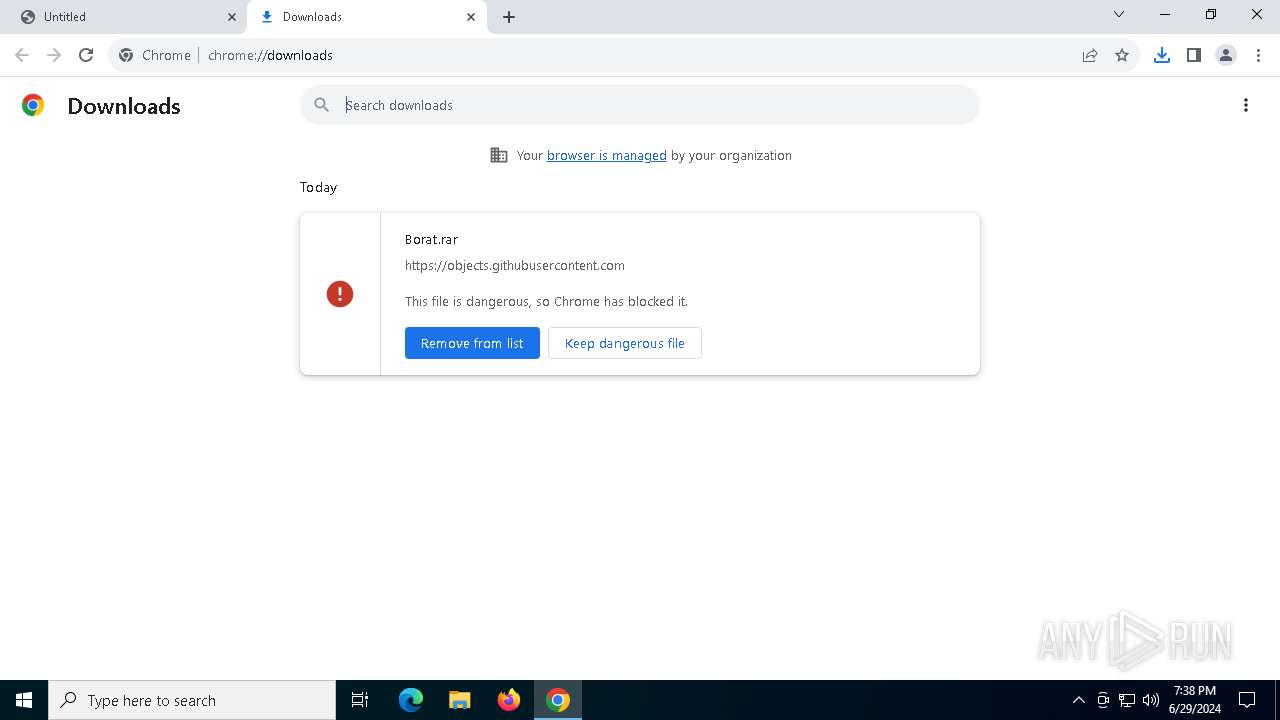
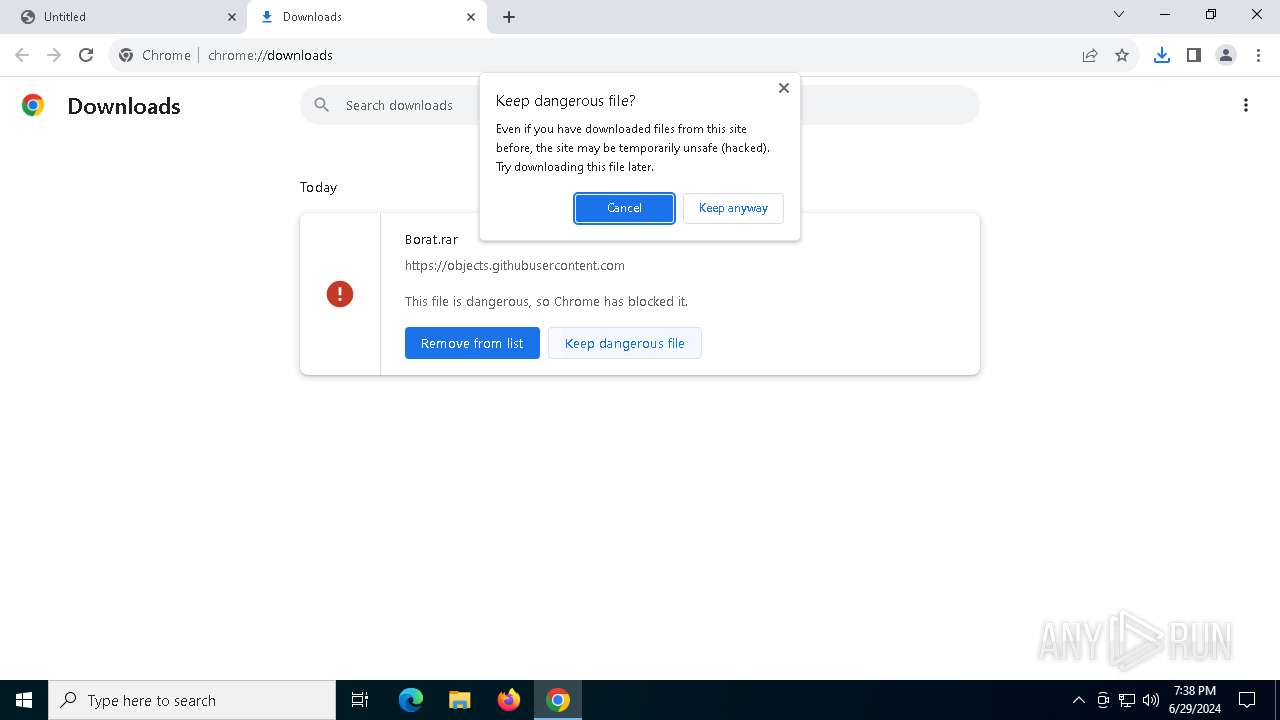
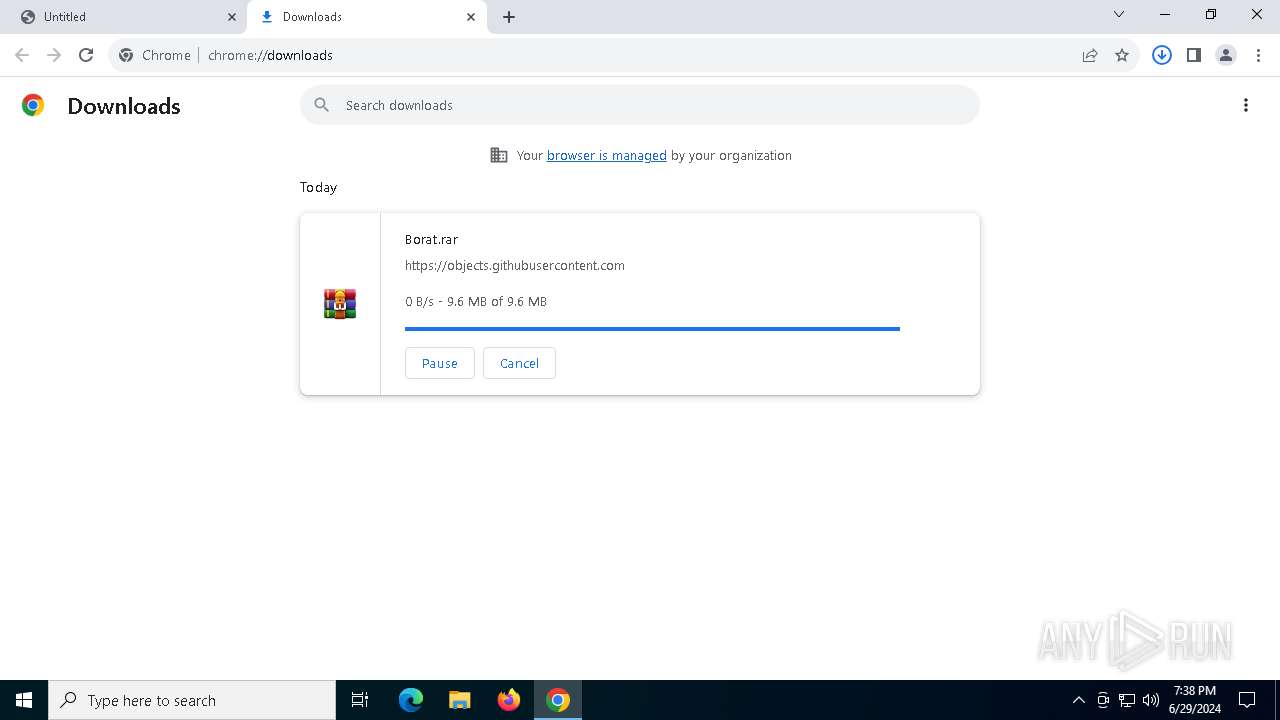
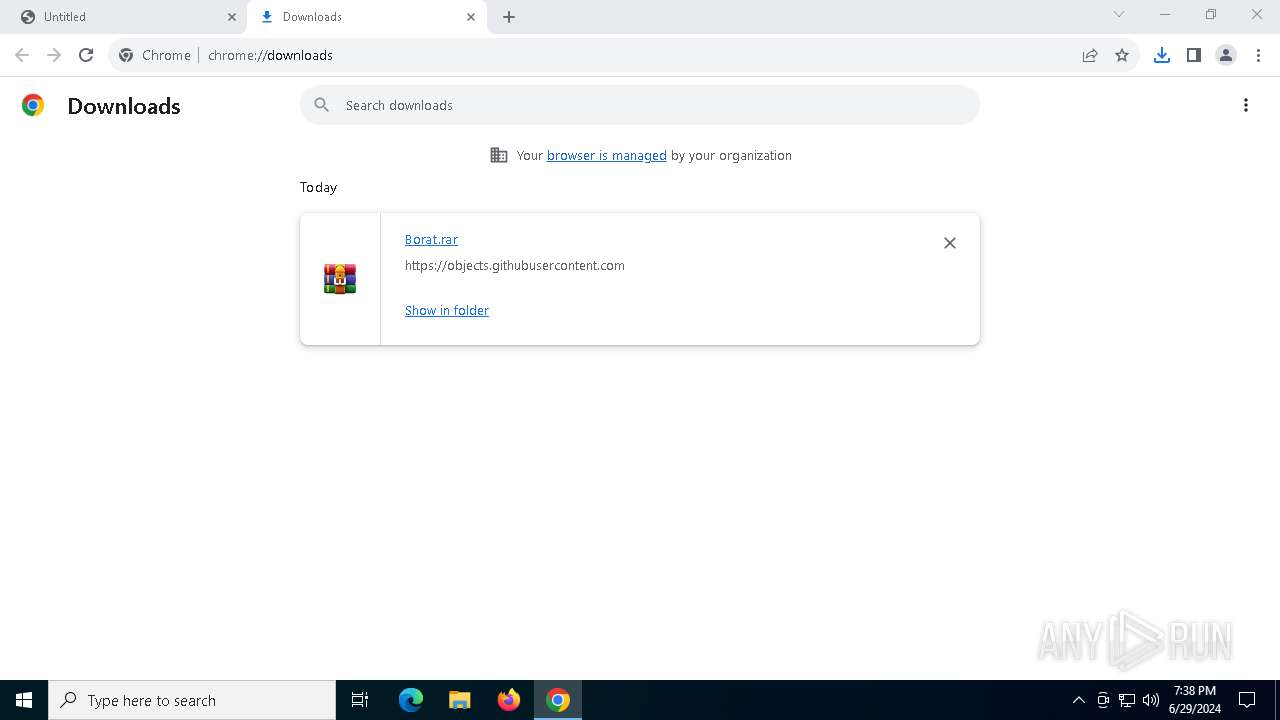
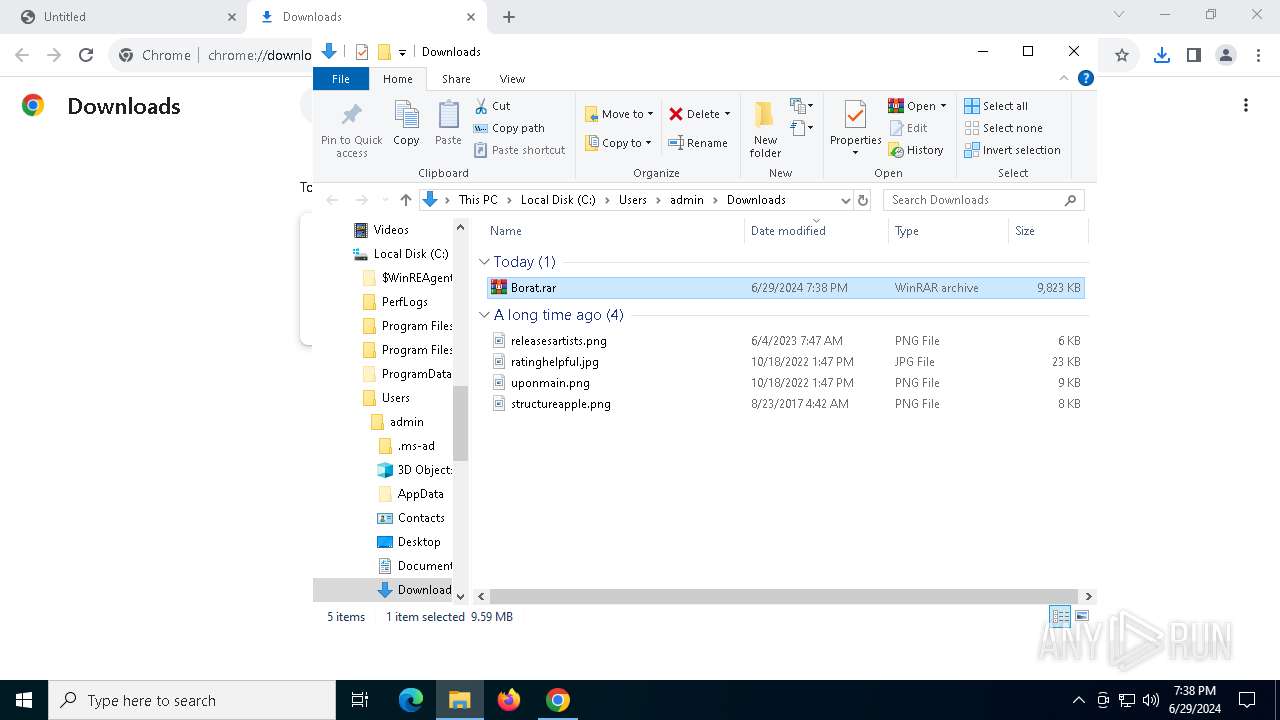
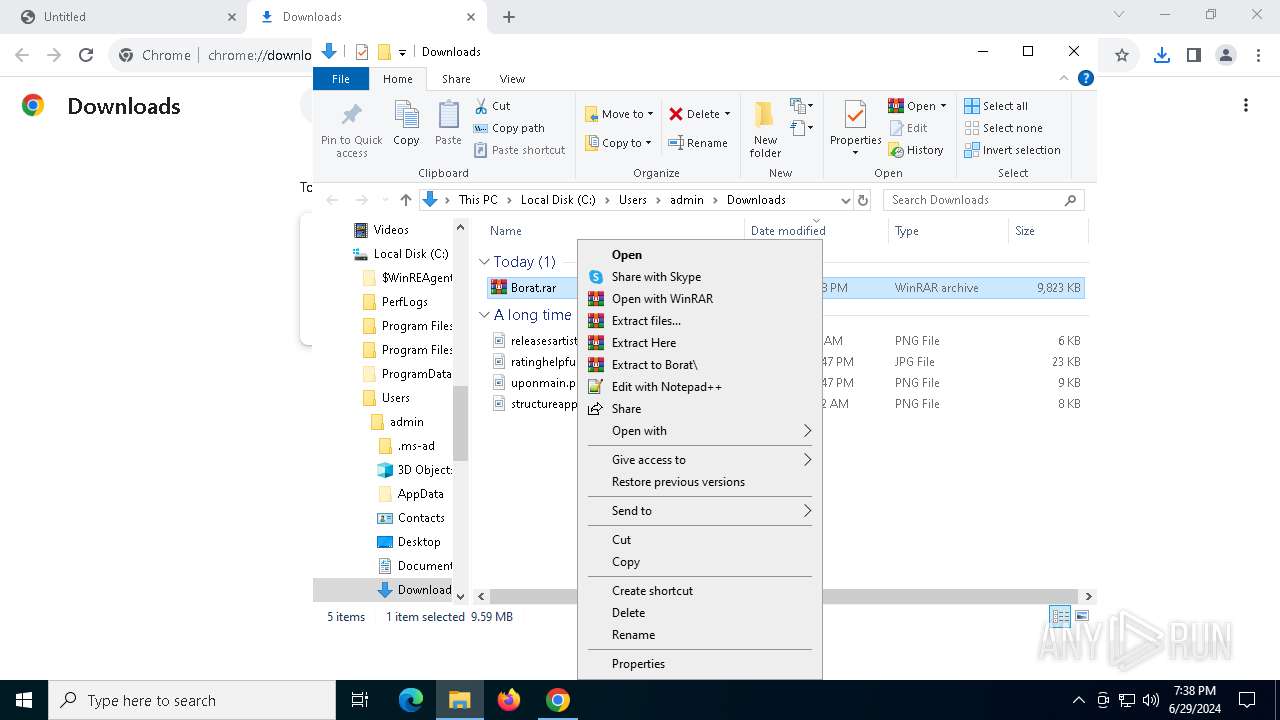
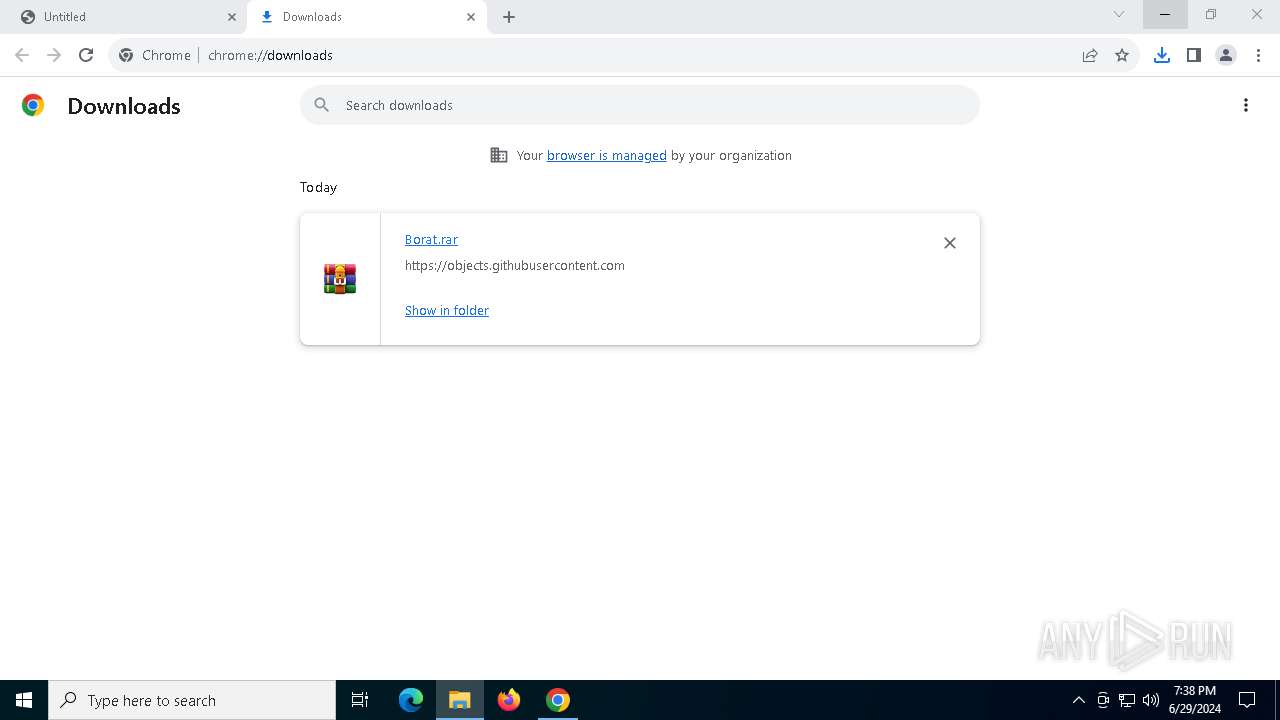
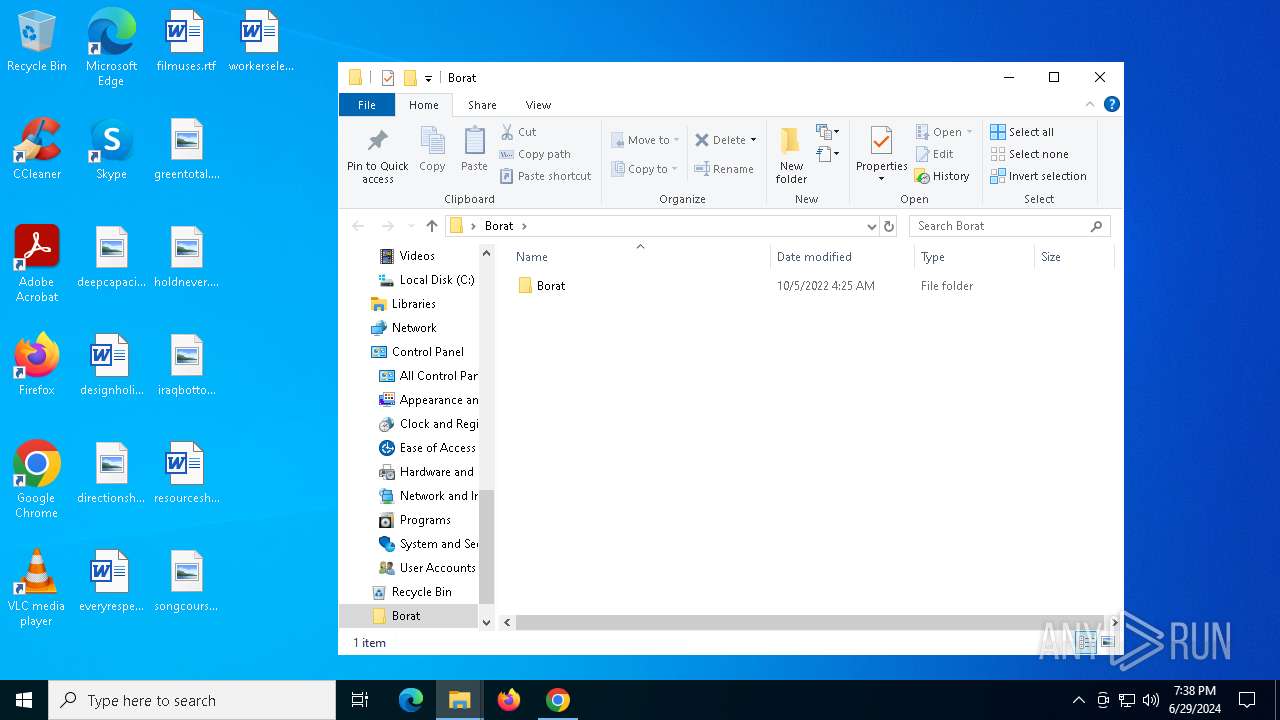
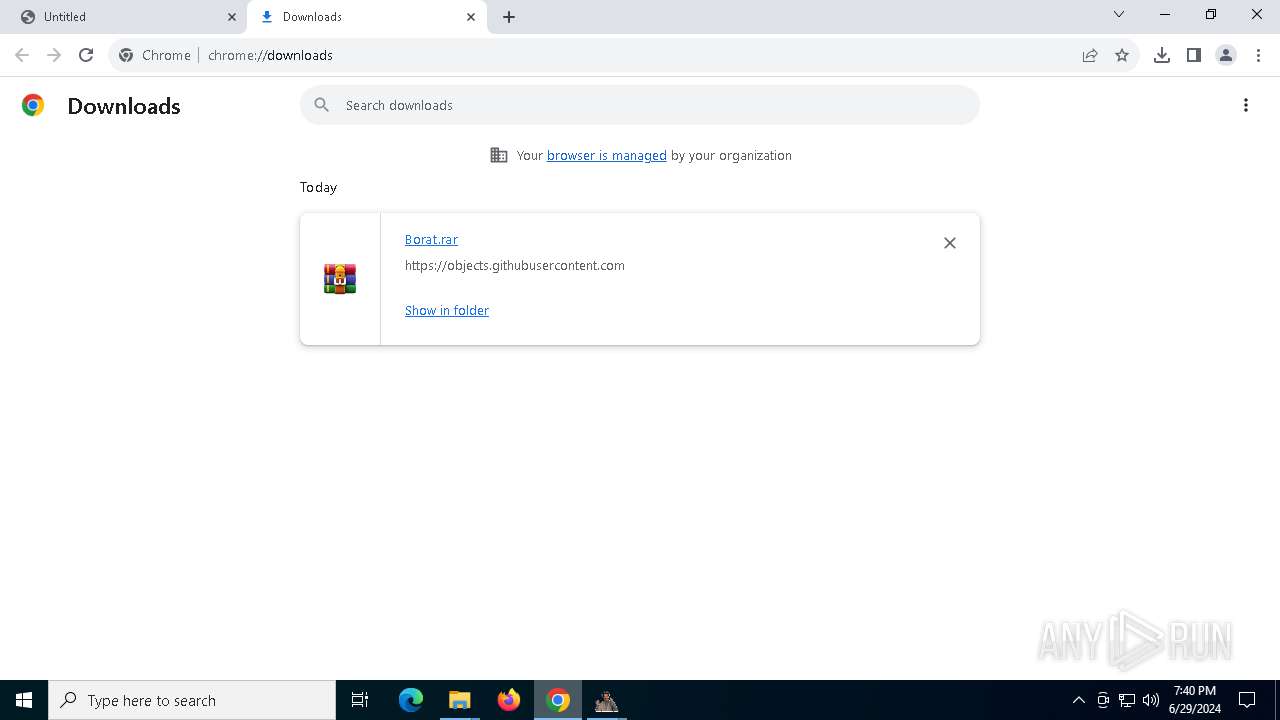
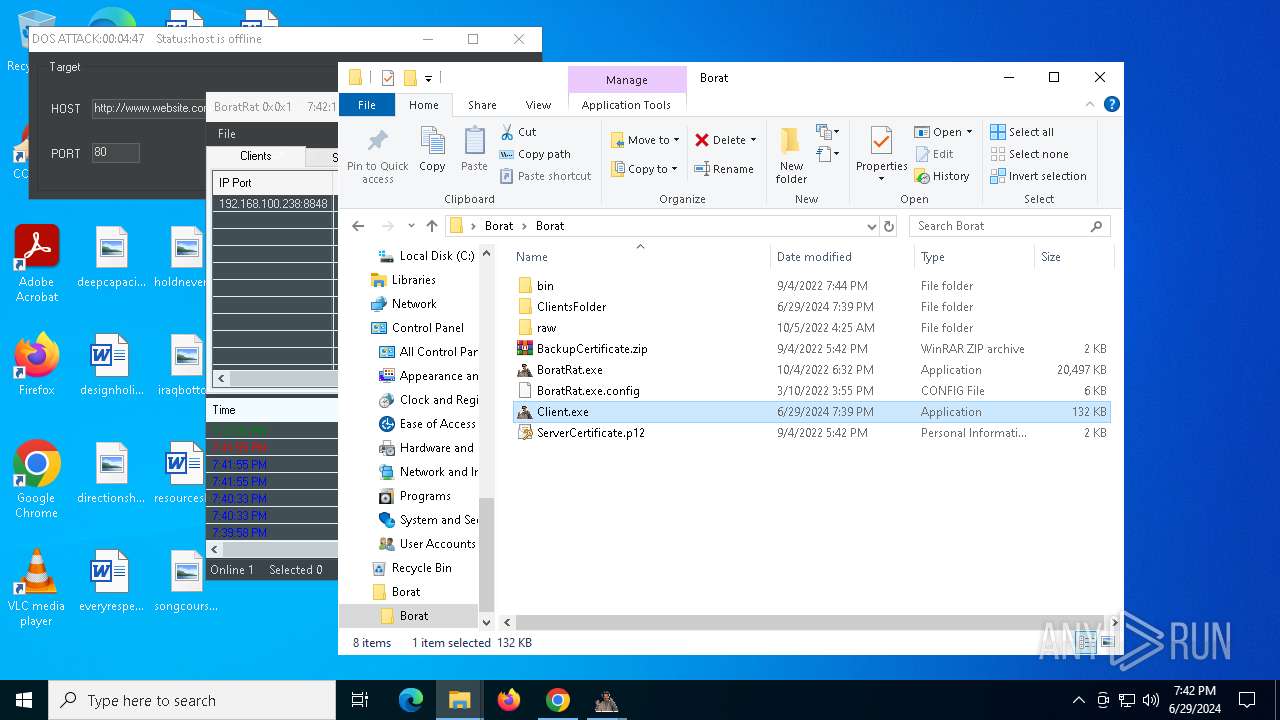
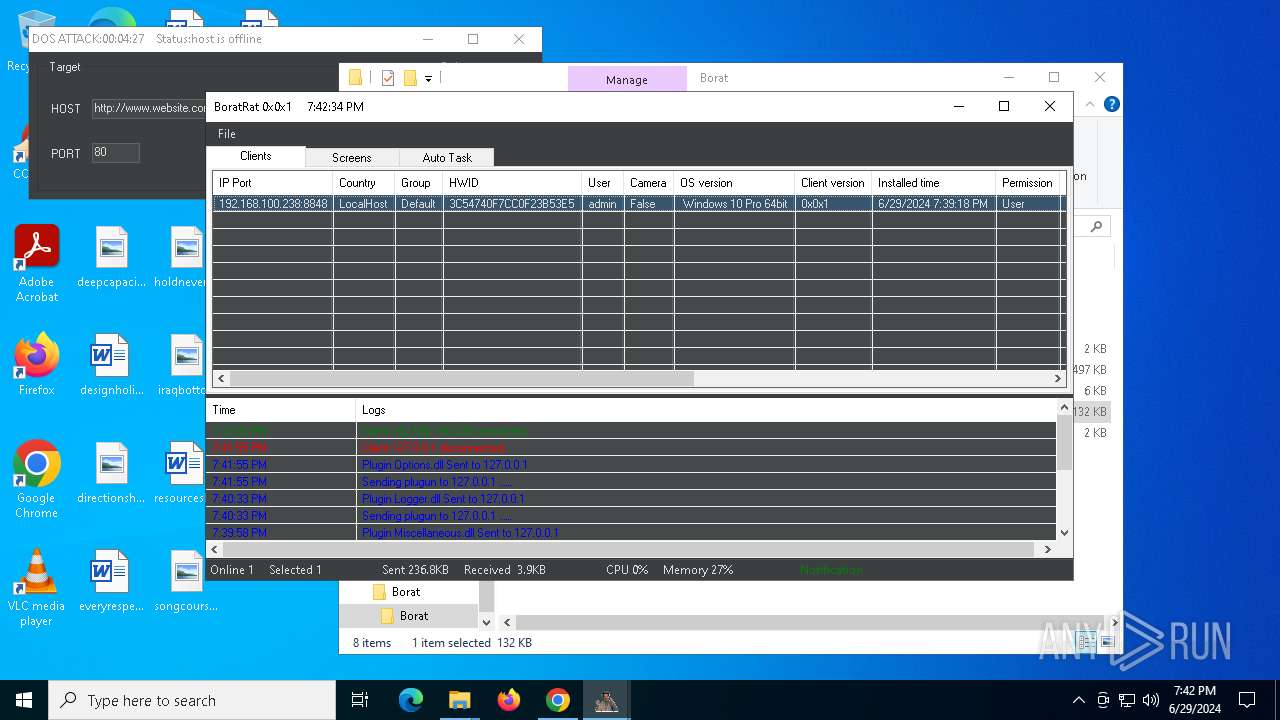
| URL: | https://github.com/mertcuan/borat-rat/releases/download/borat/Borat.rar |
| Full analysis: | https://app.any.run/tasks/174f6da8-2fdb-445e-8d07-c9d1b4604853 |
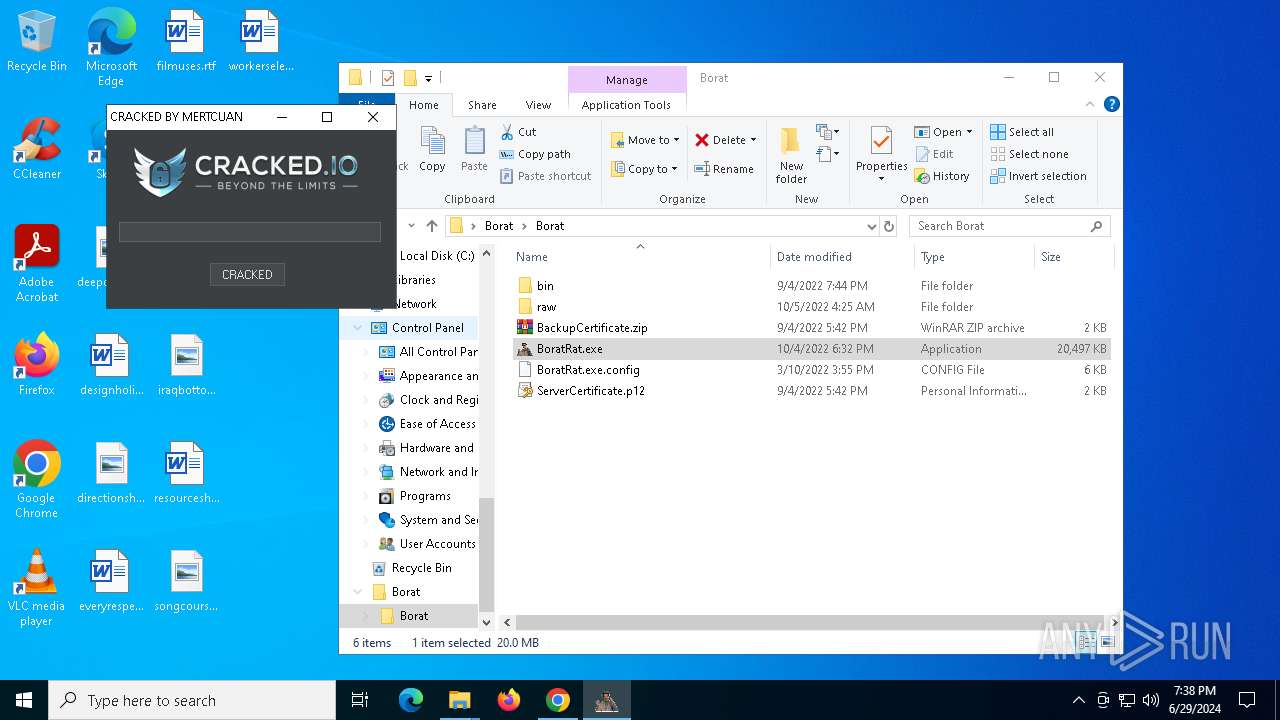
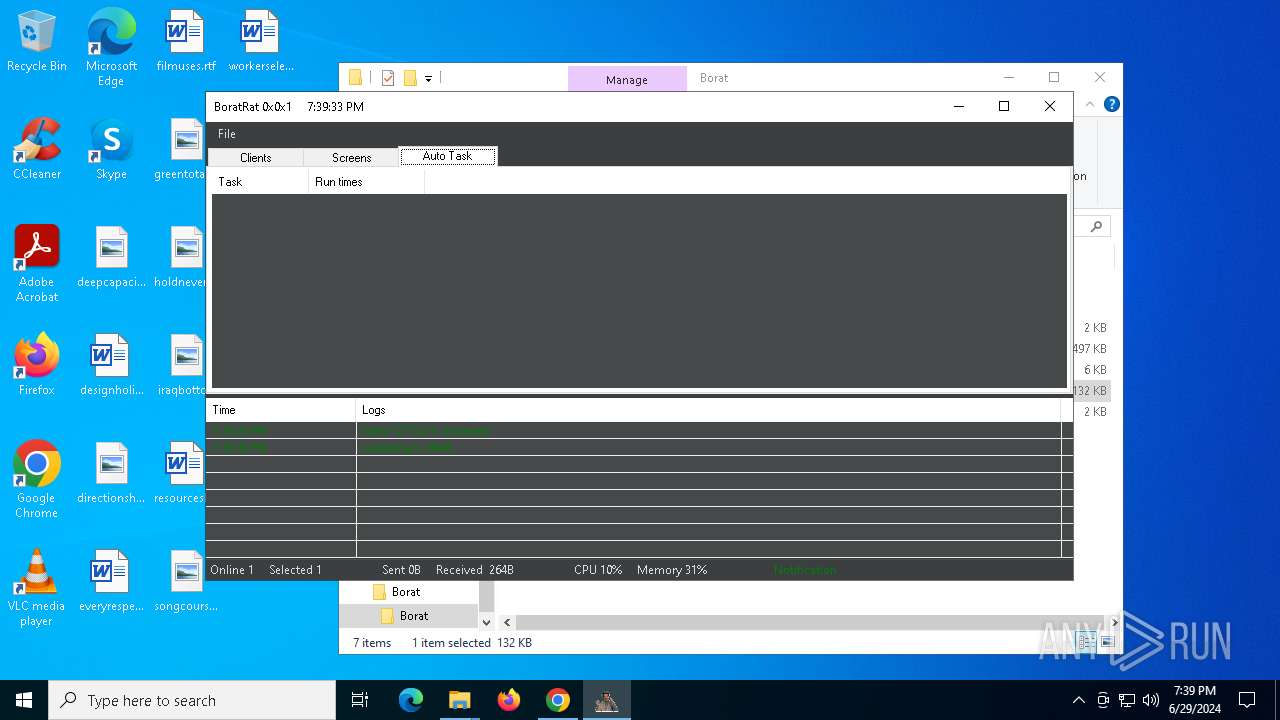
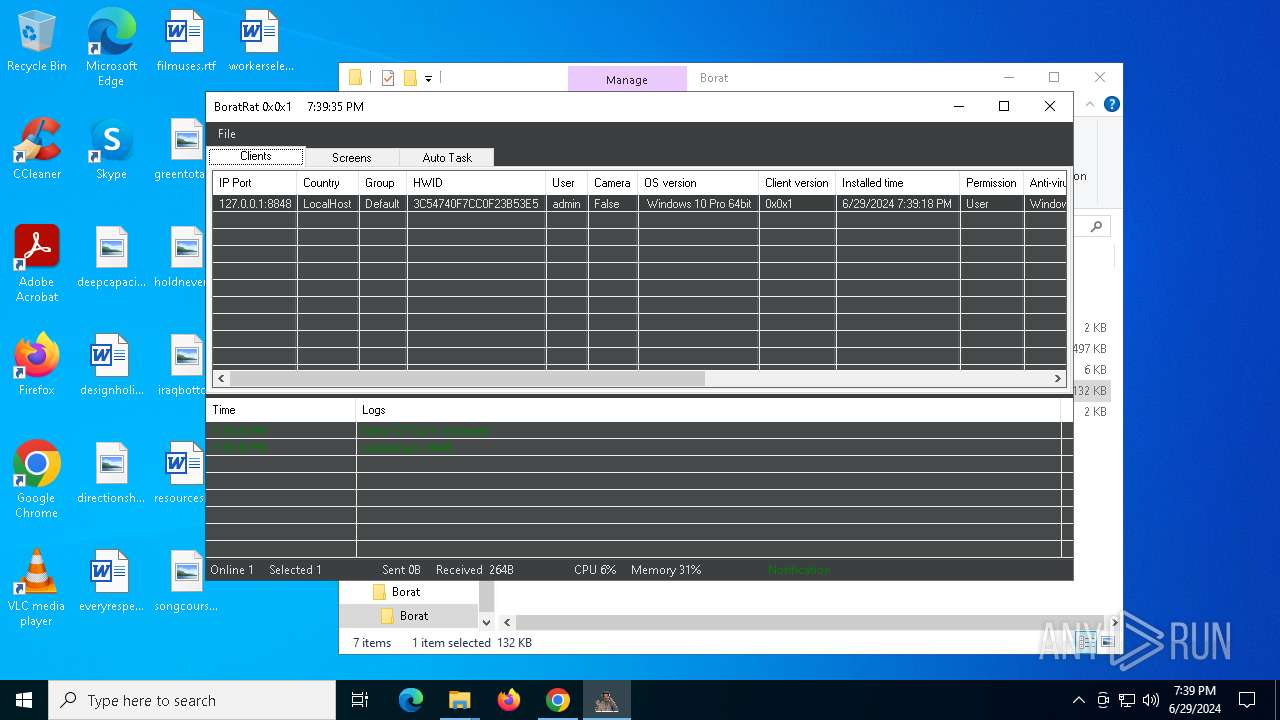
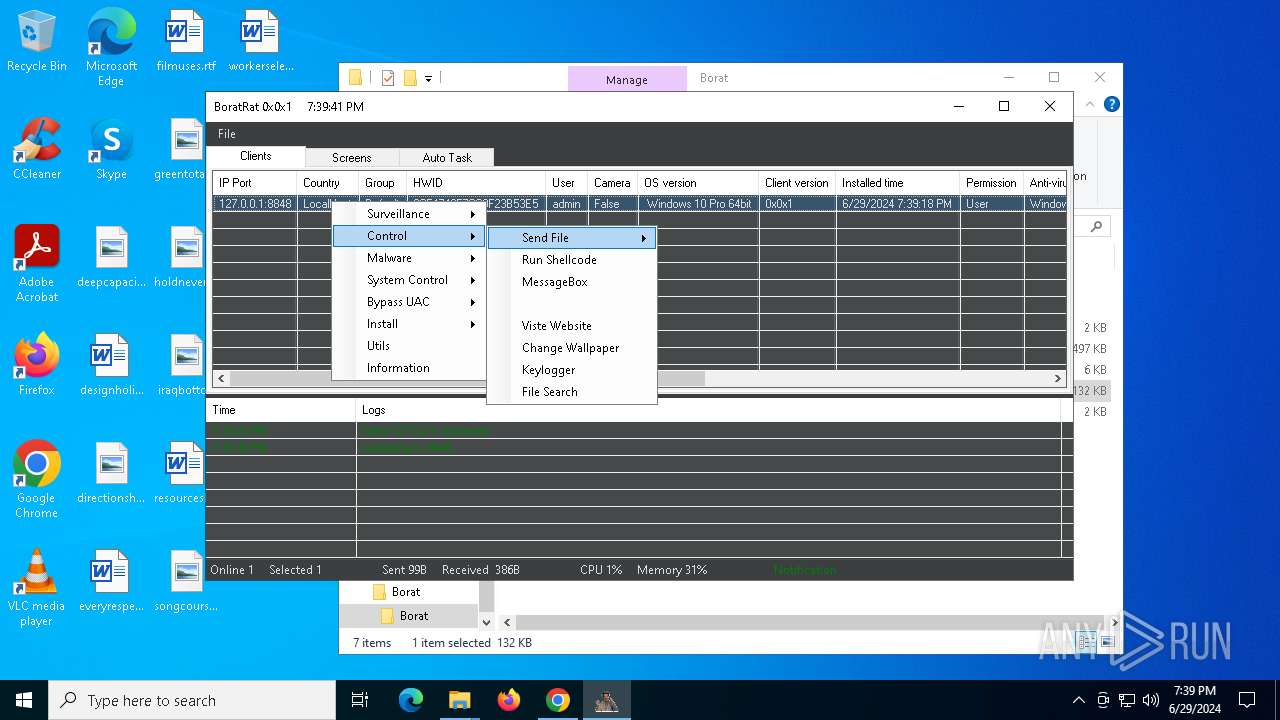
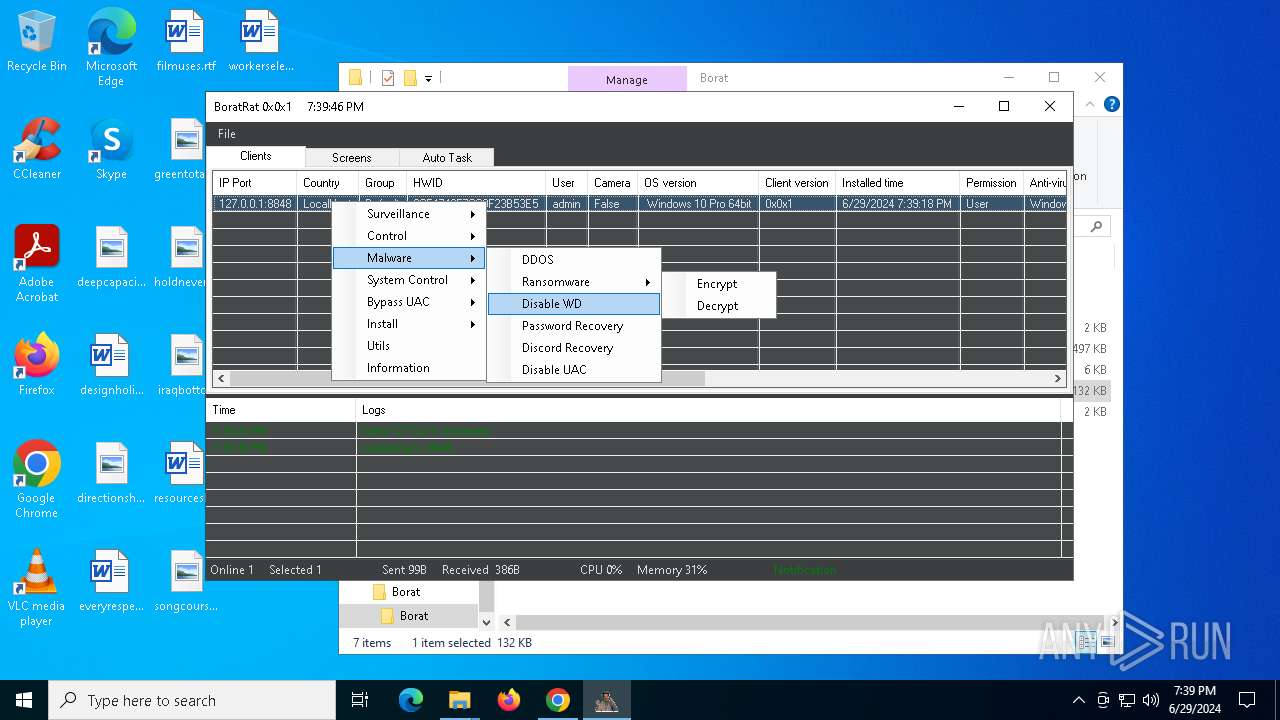
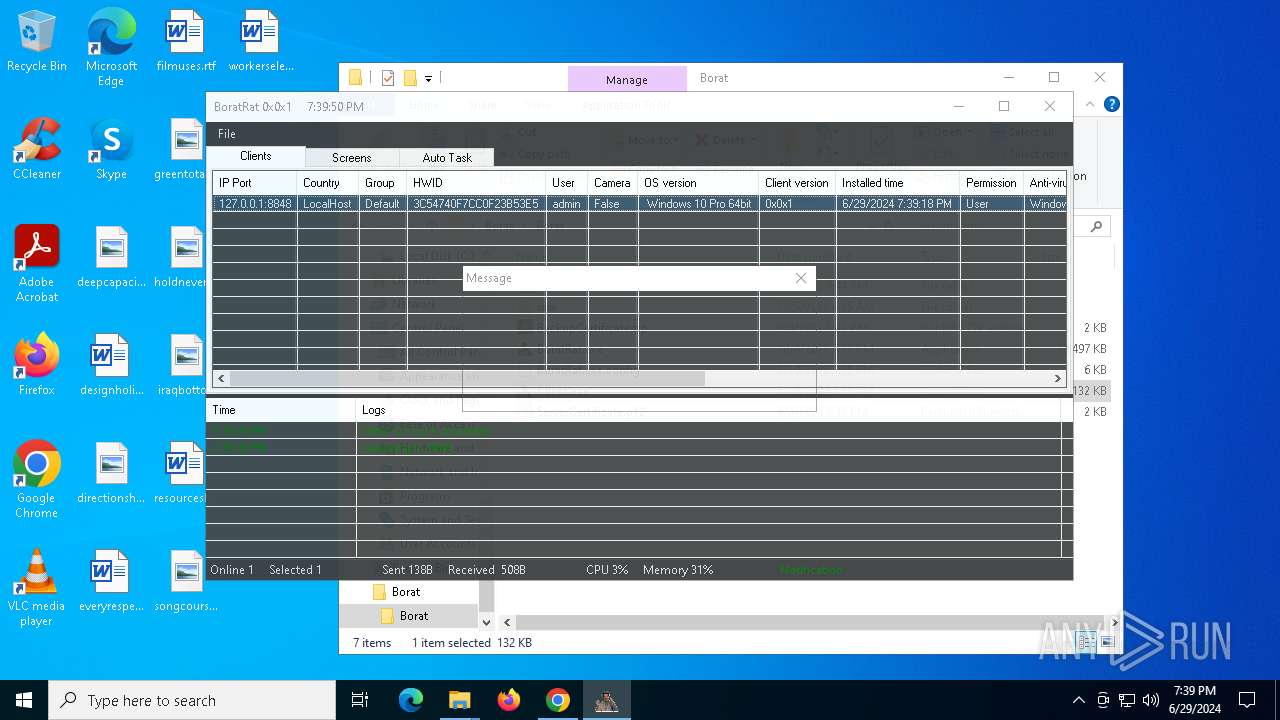
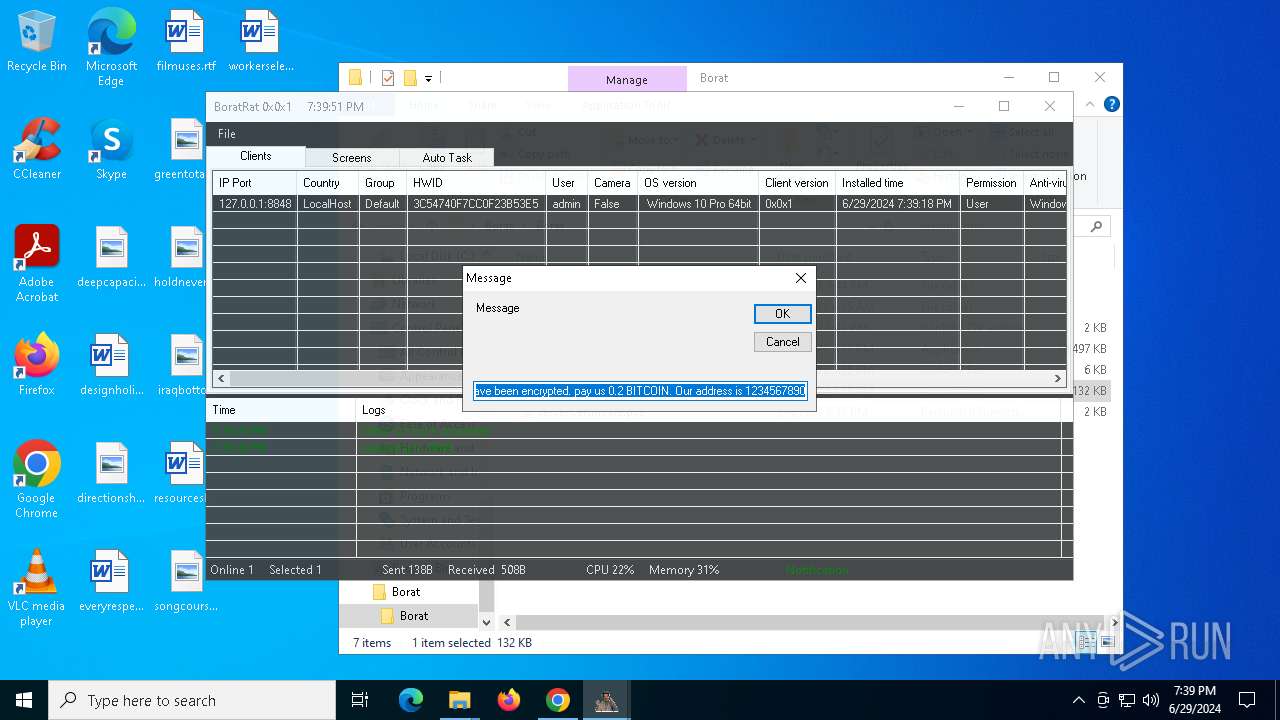
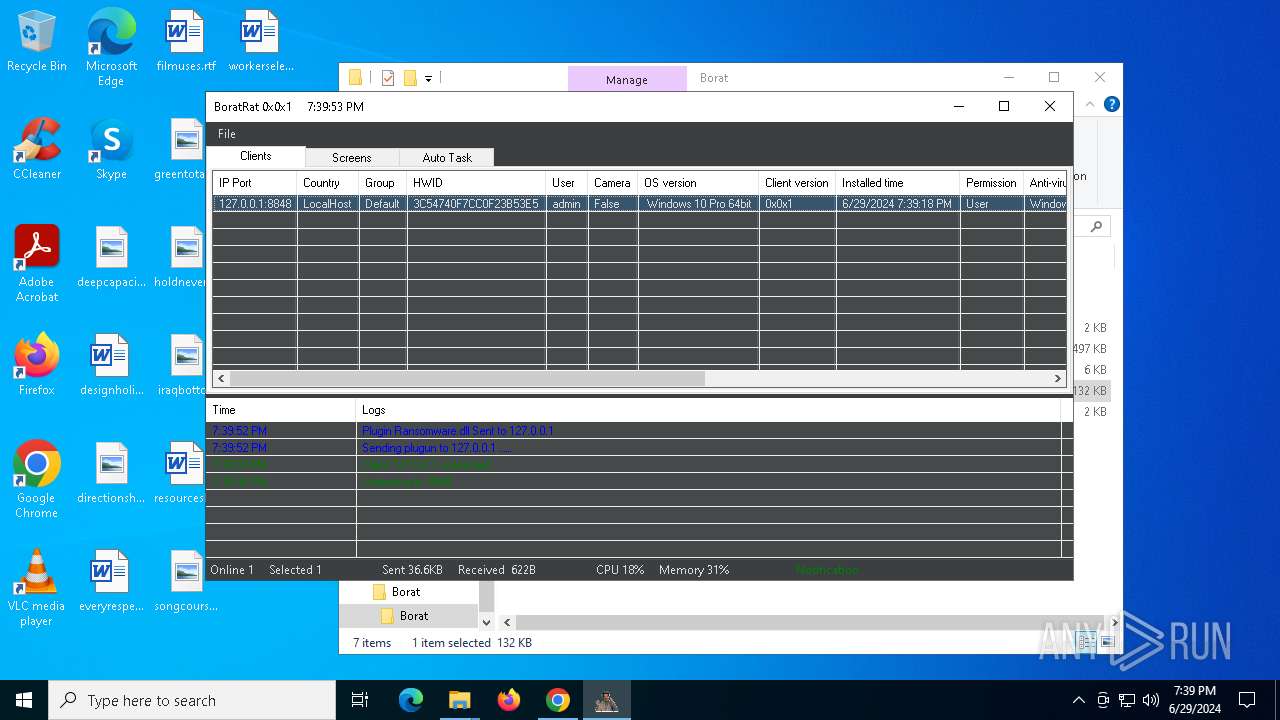
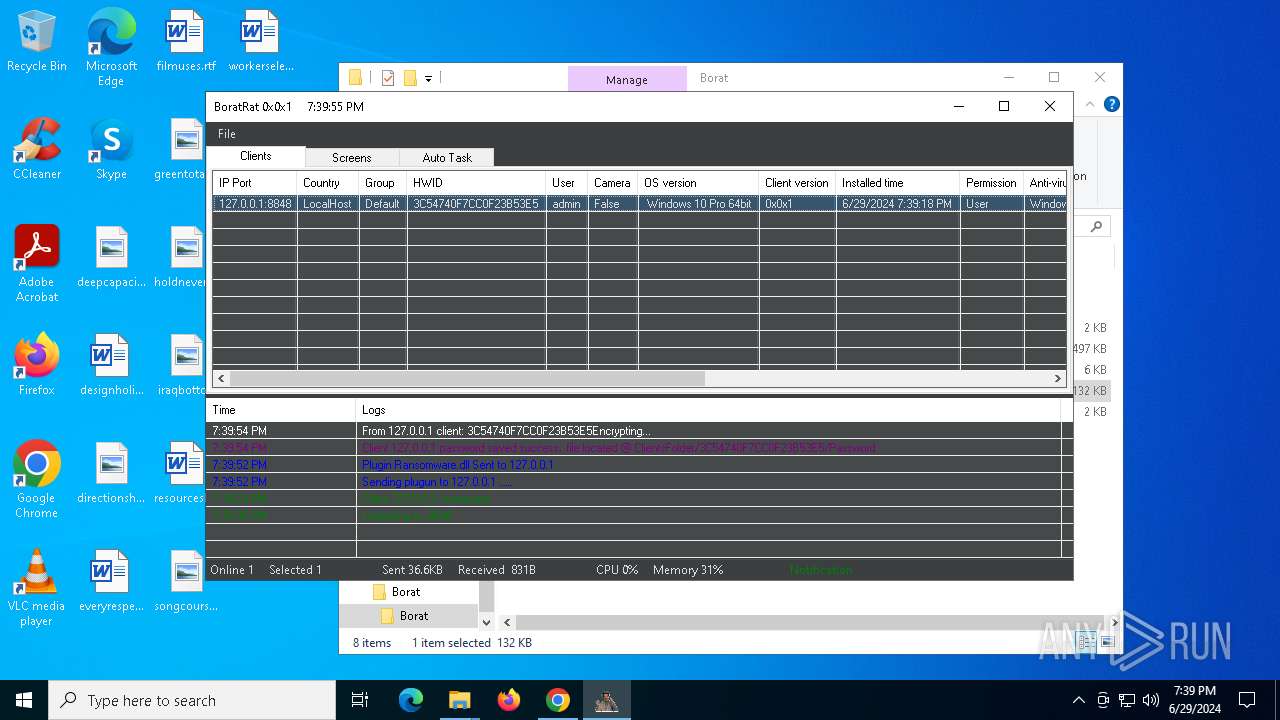
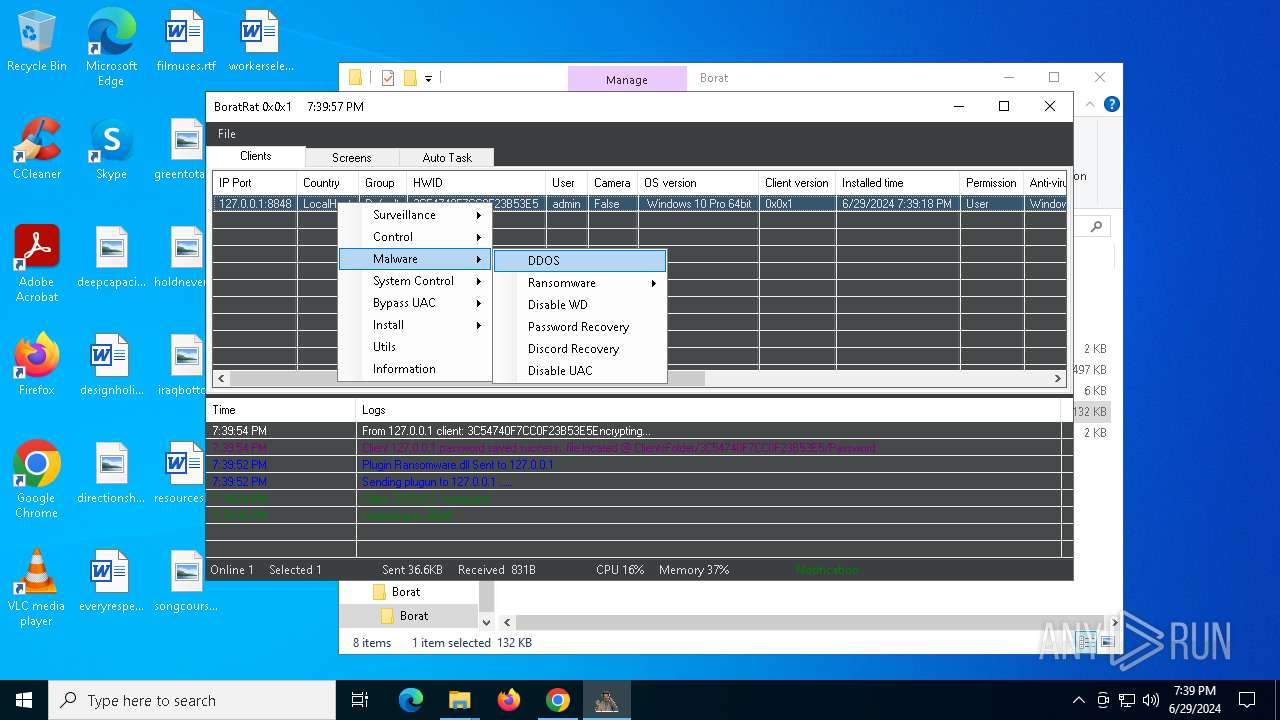
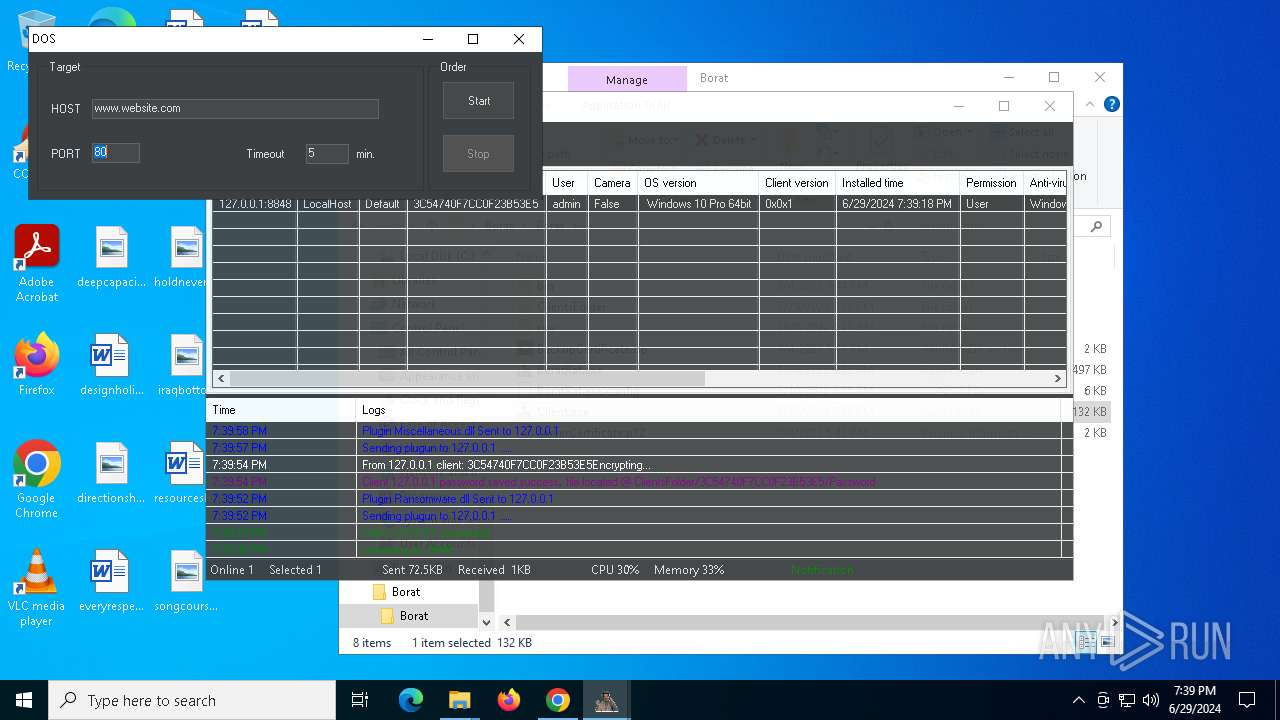
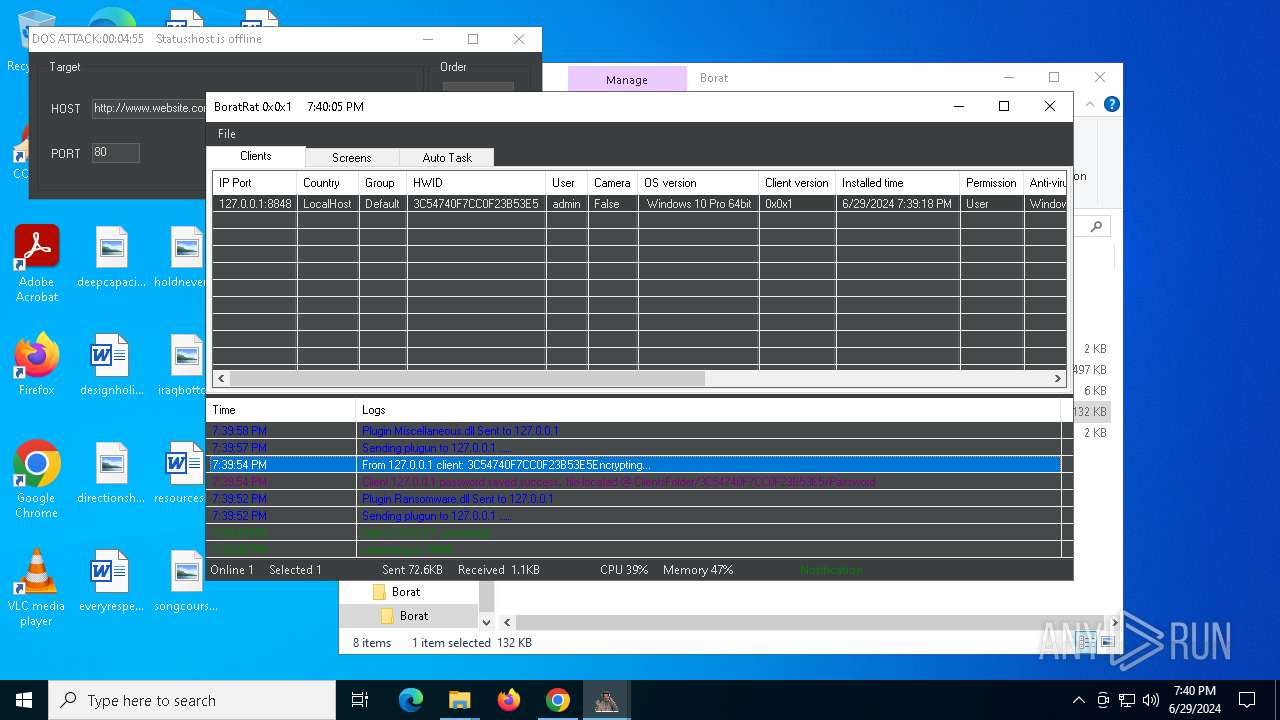
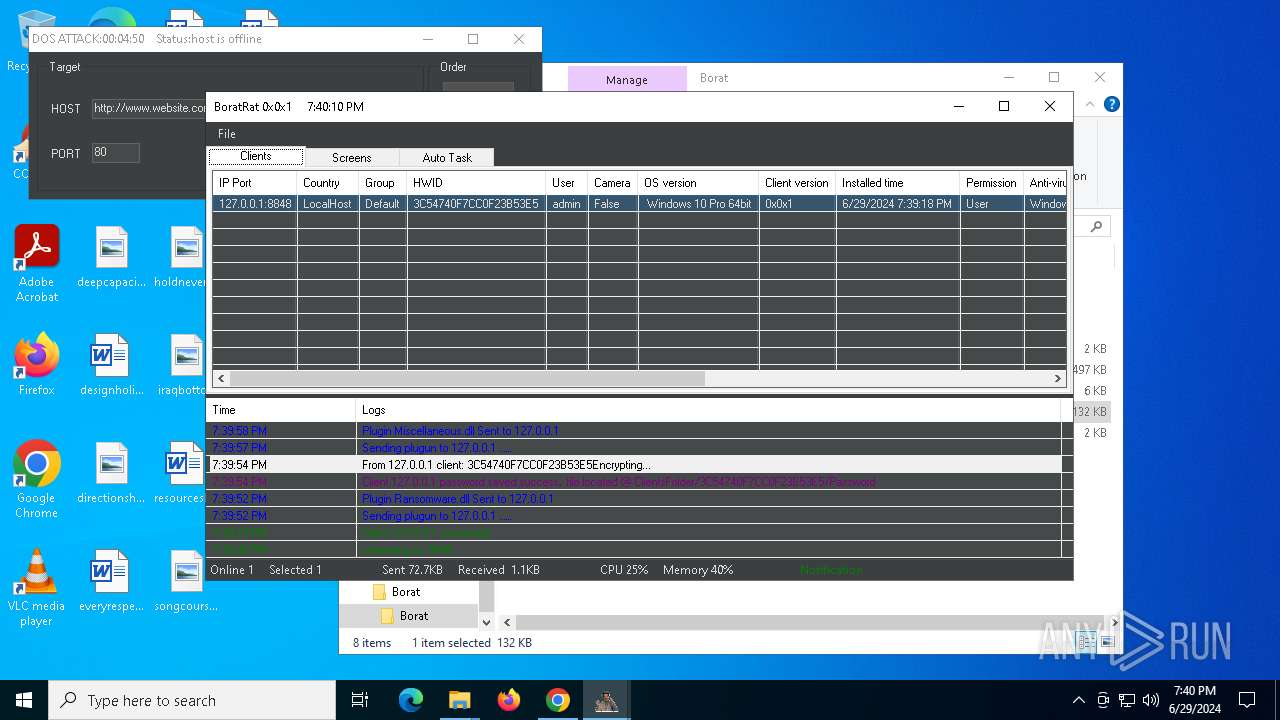
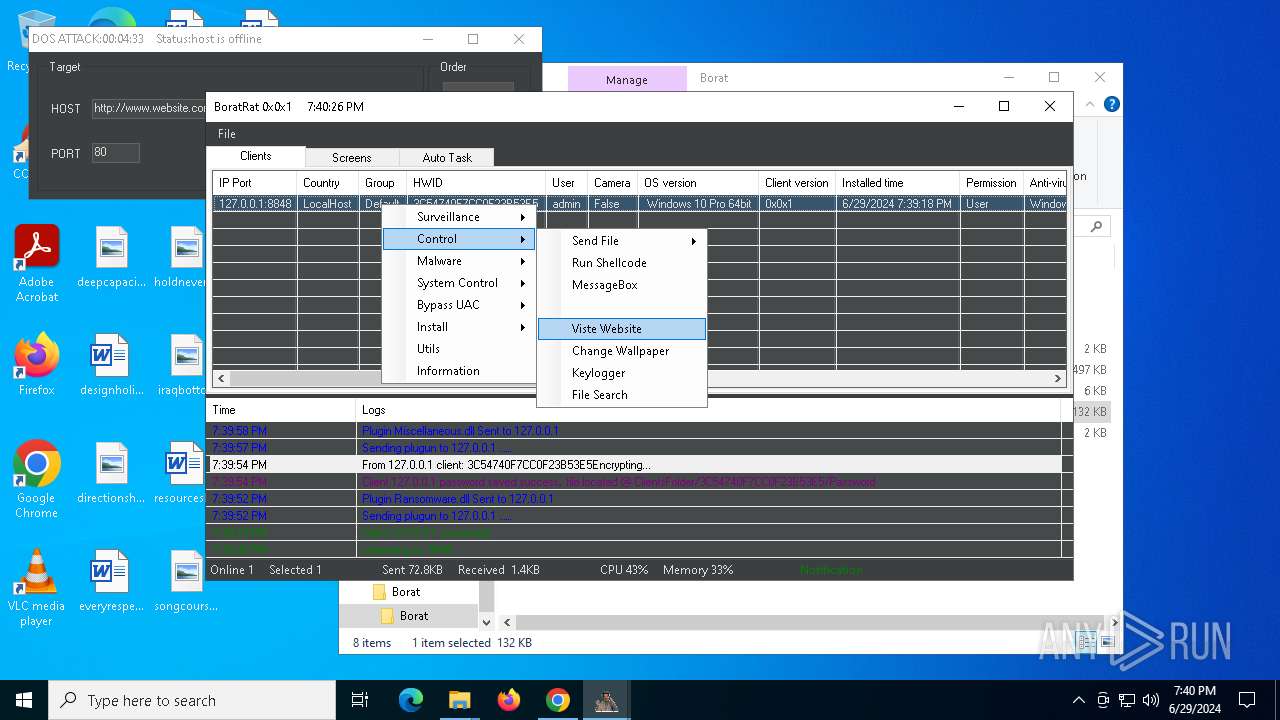
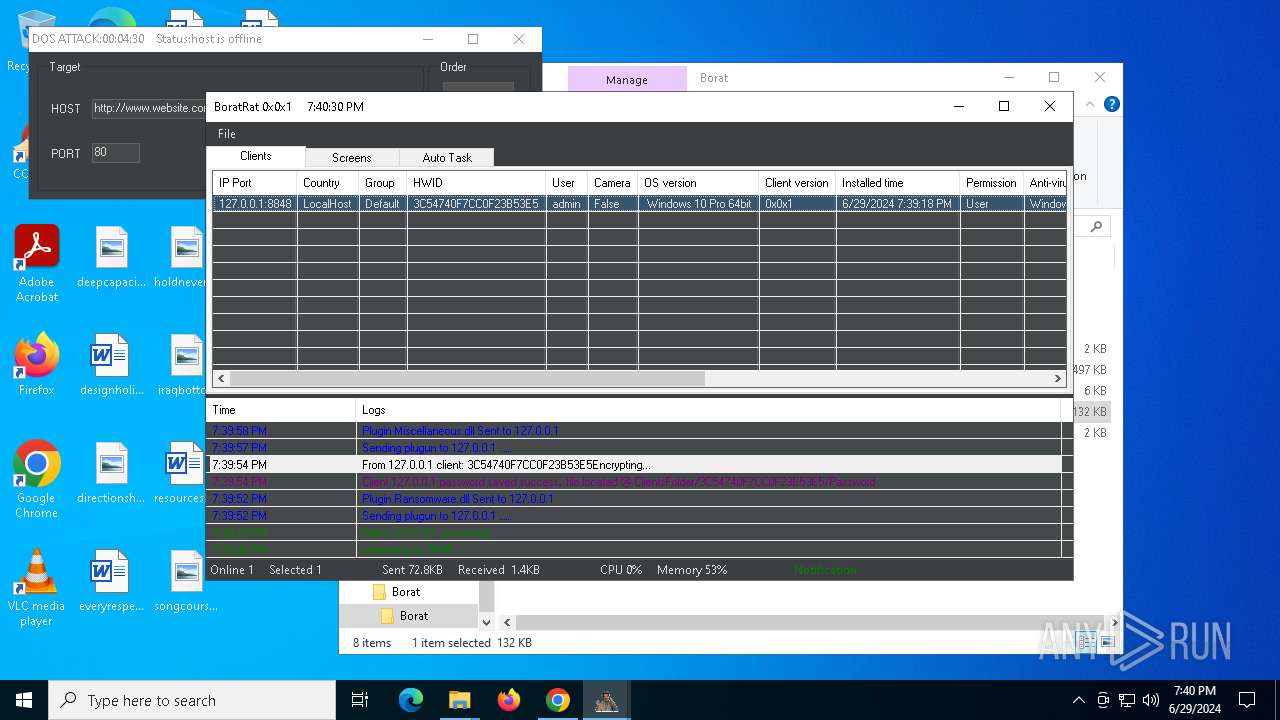
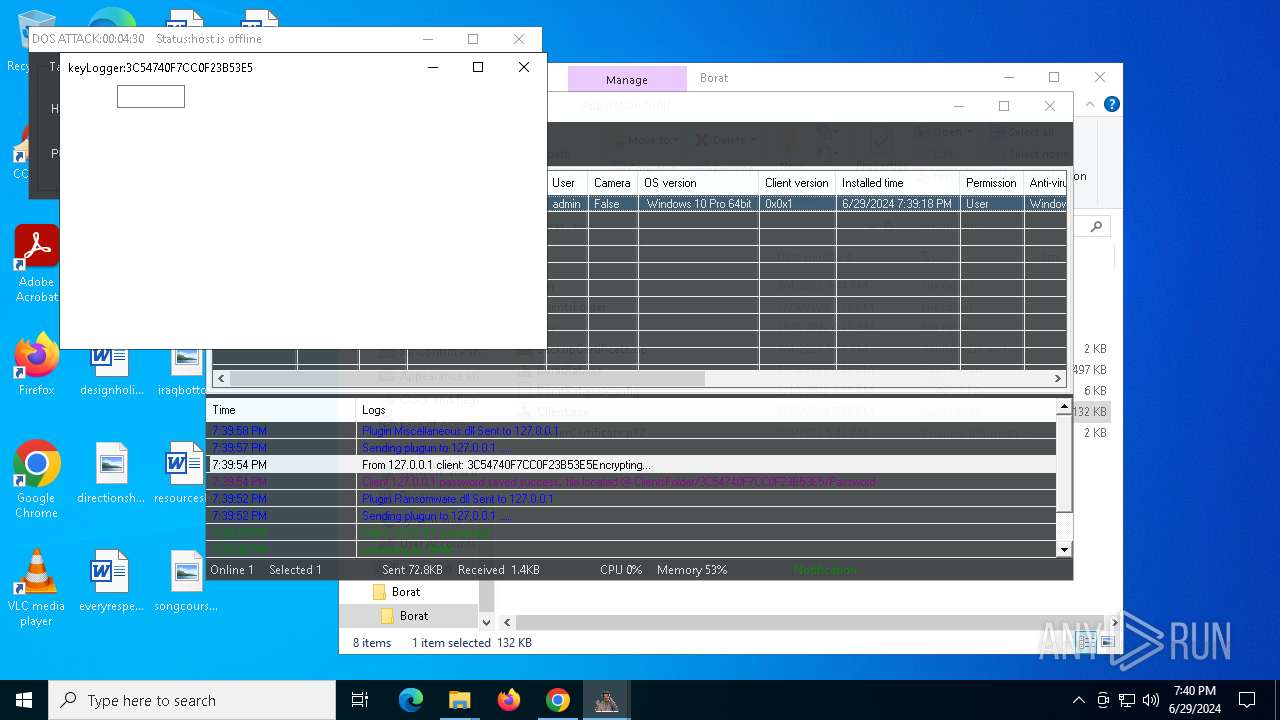
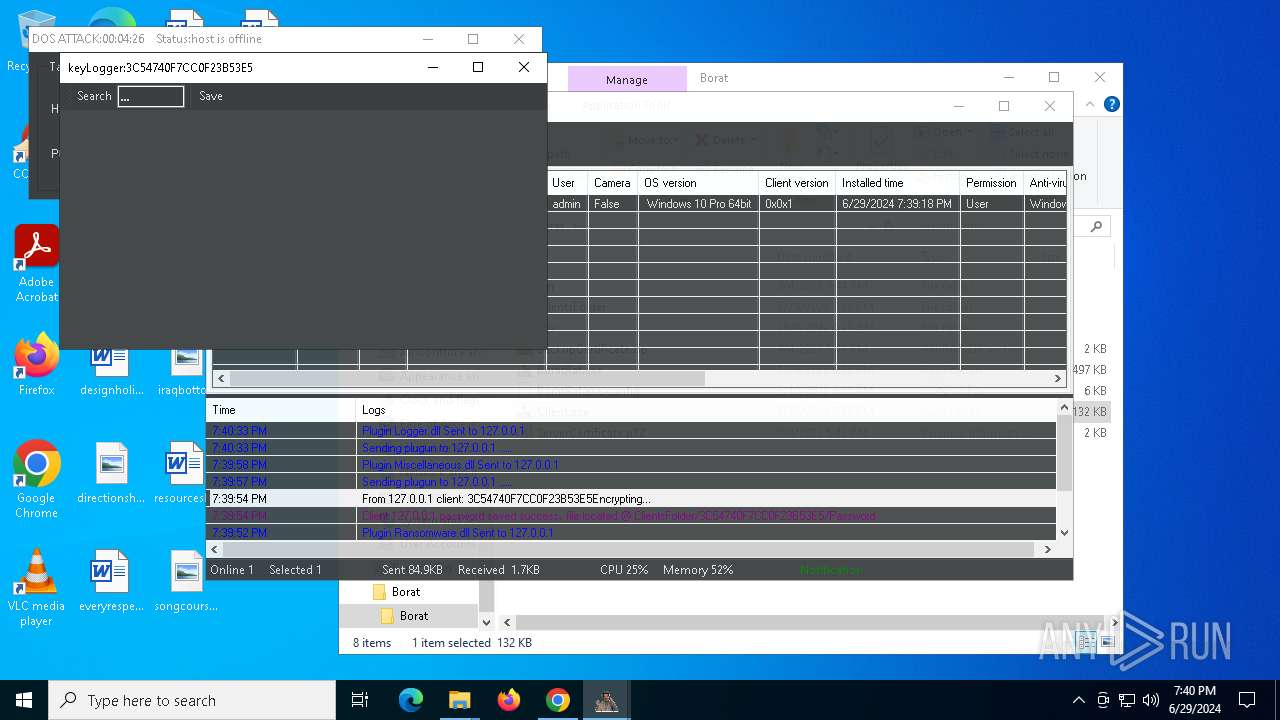
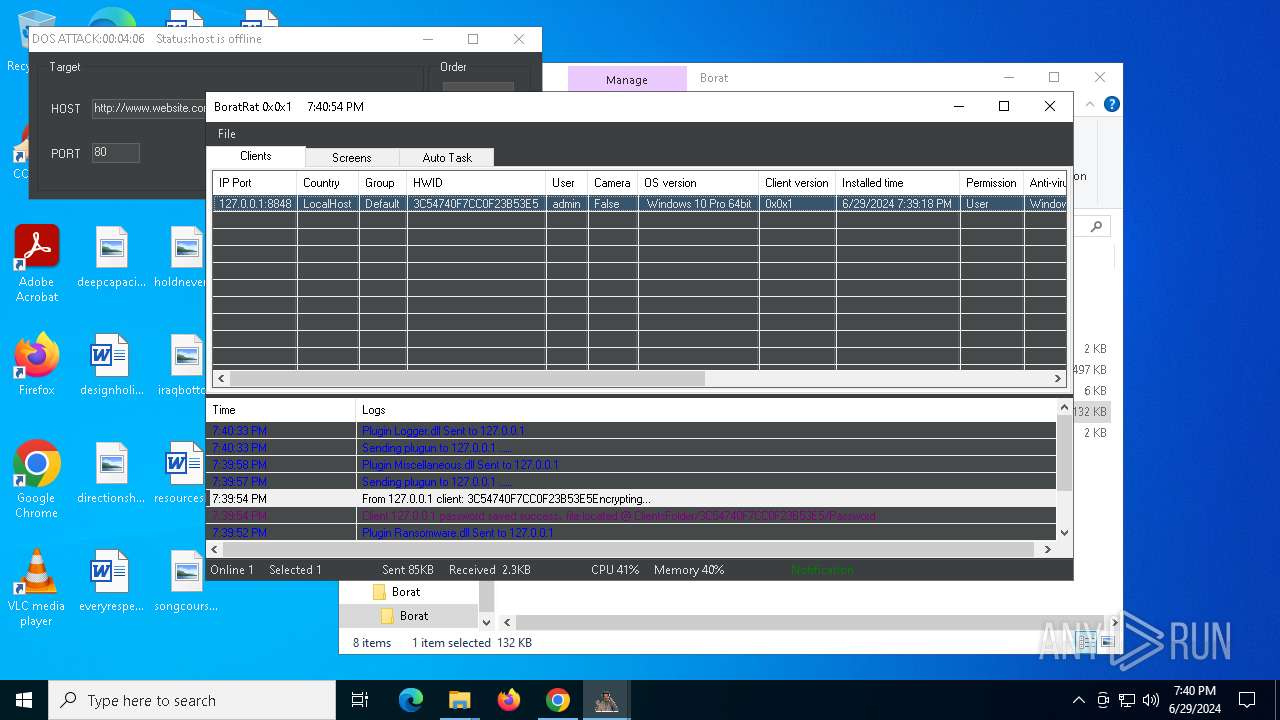
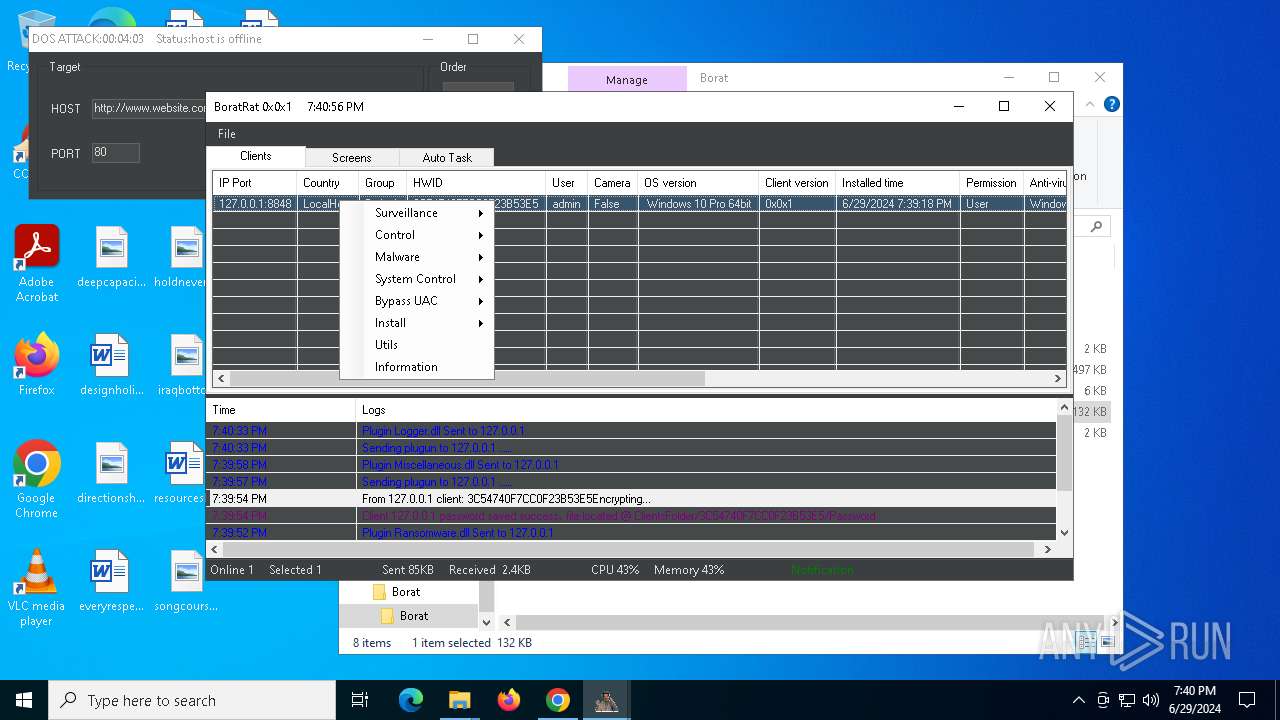
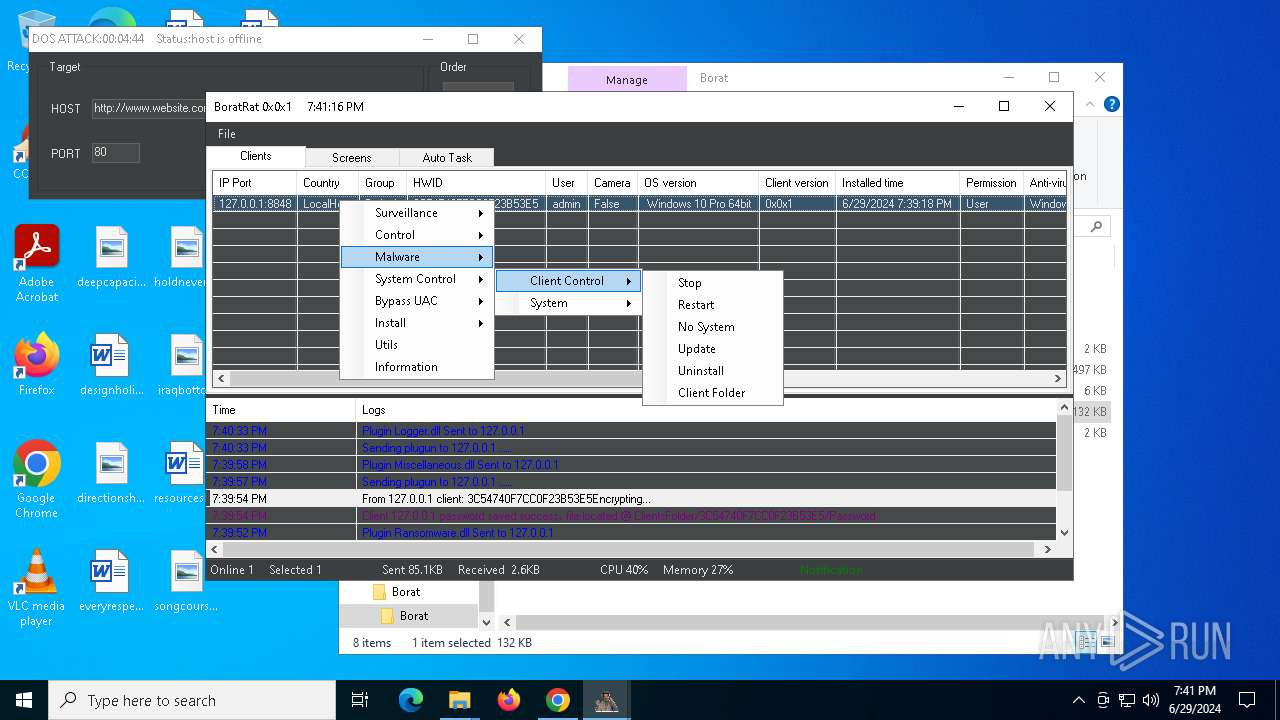
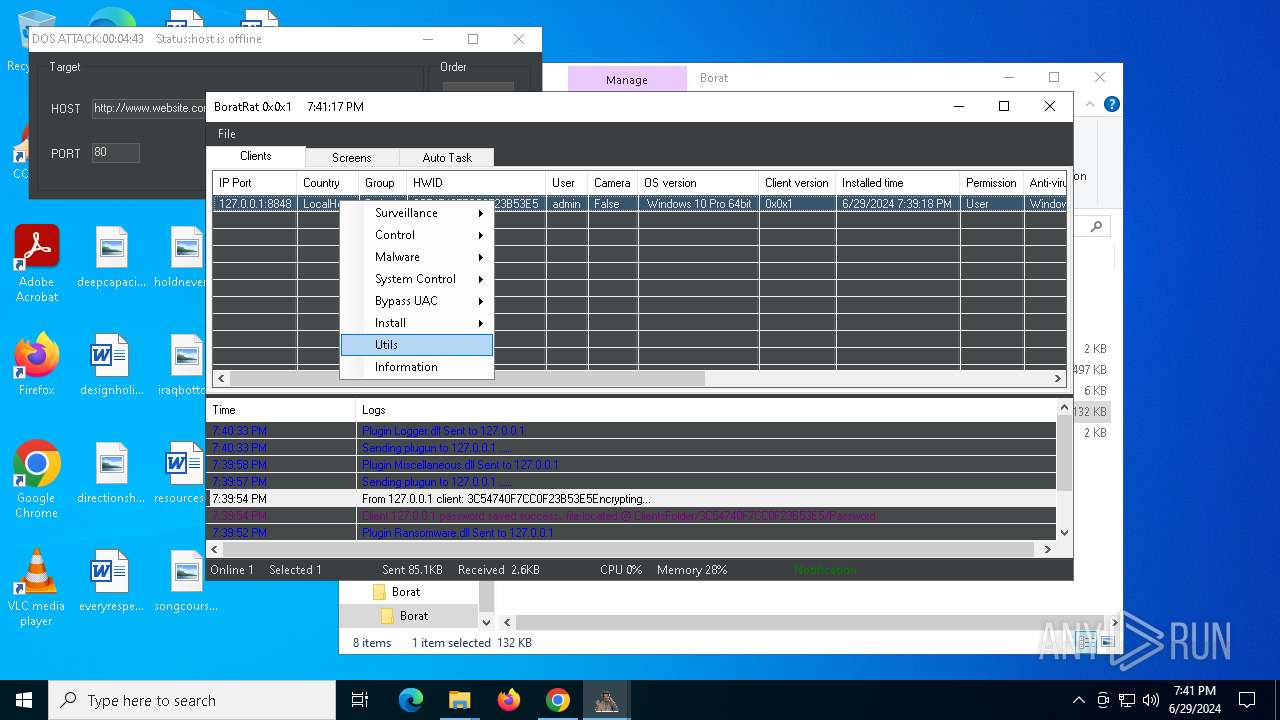
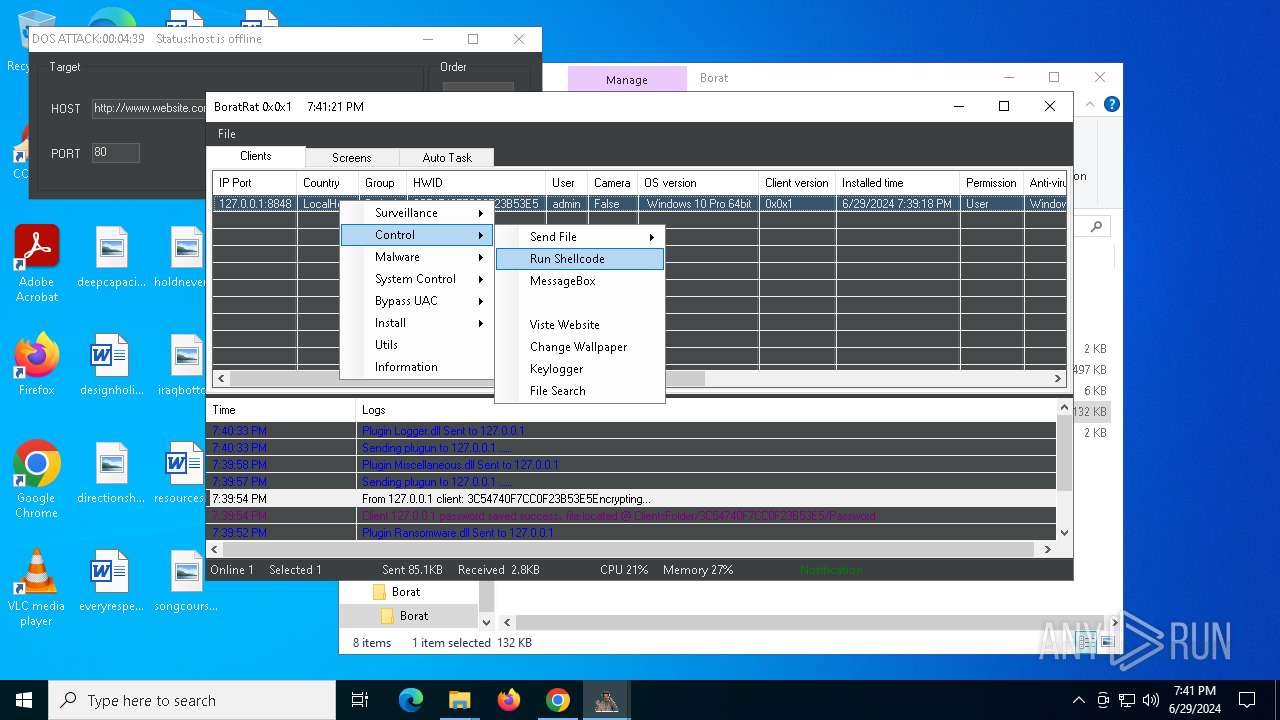
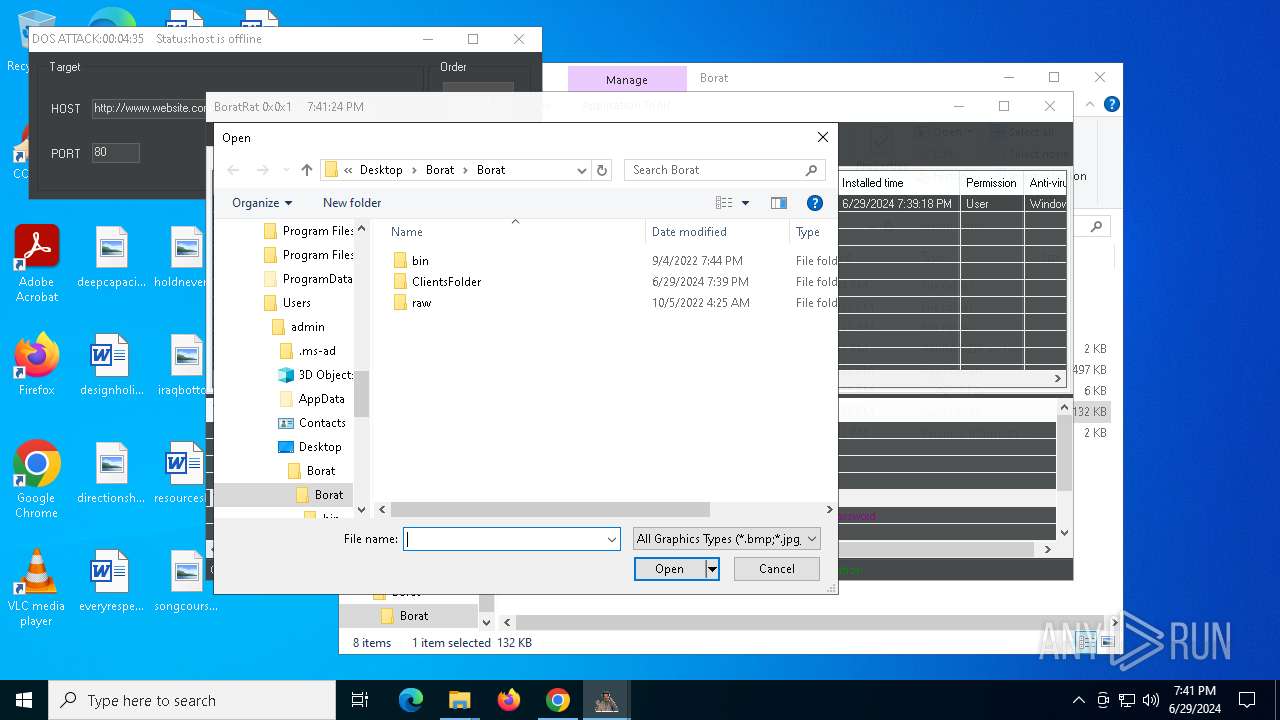
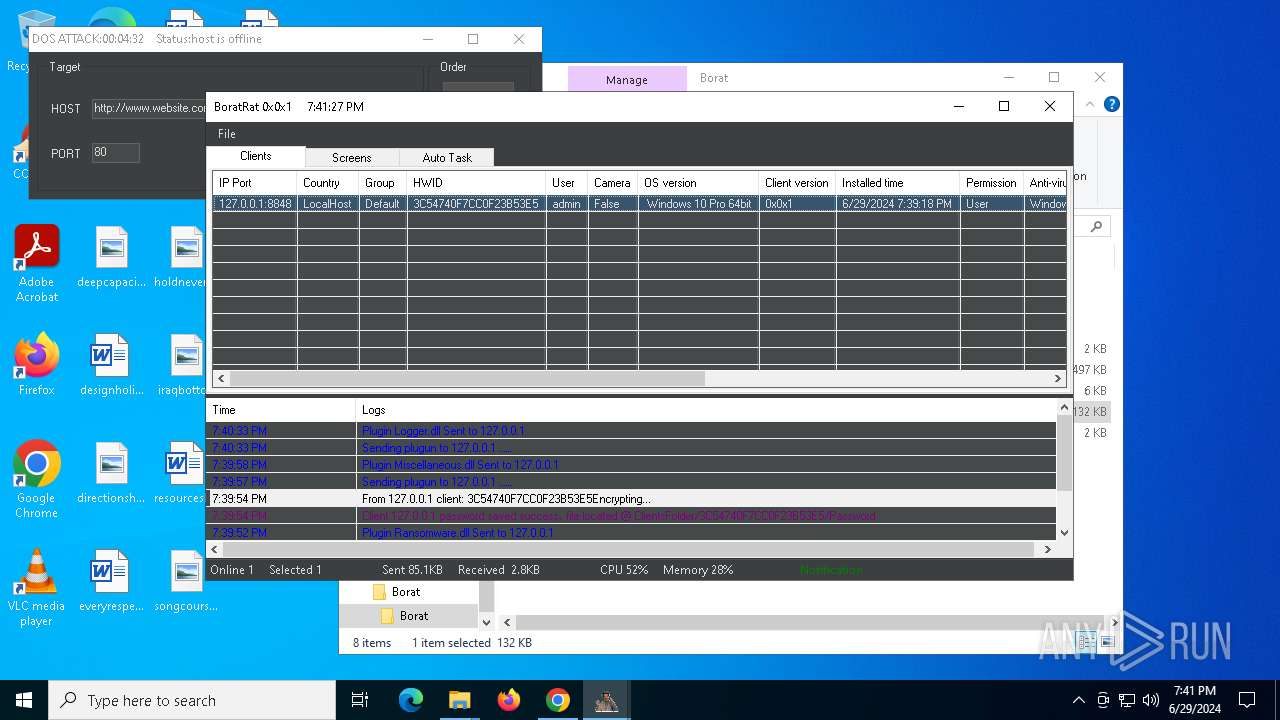
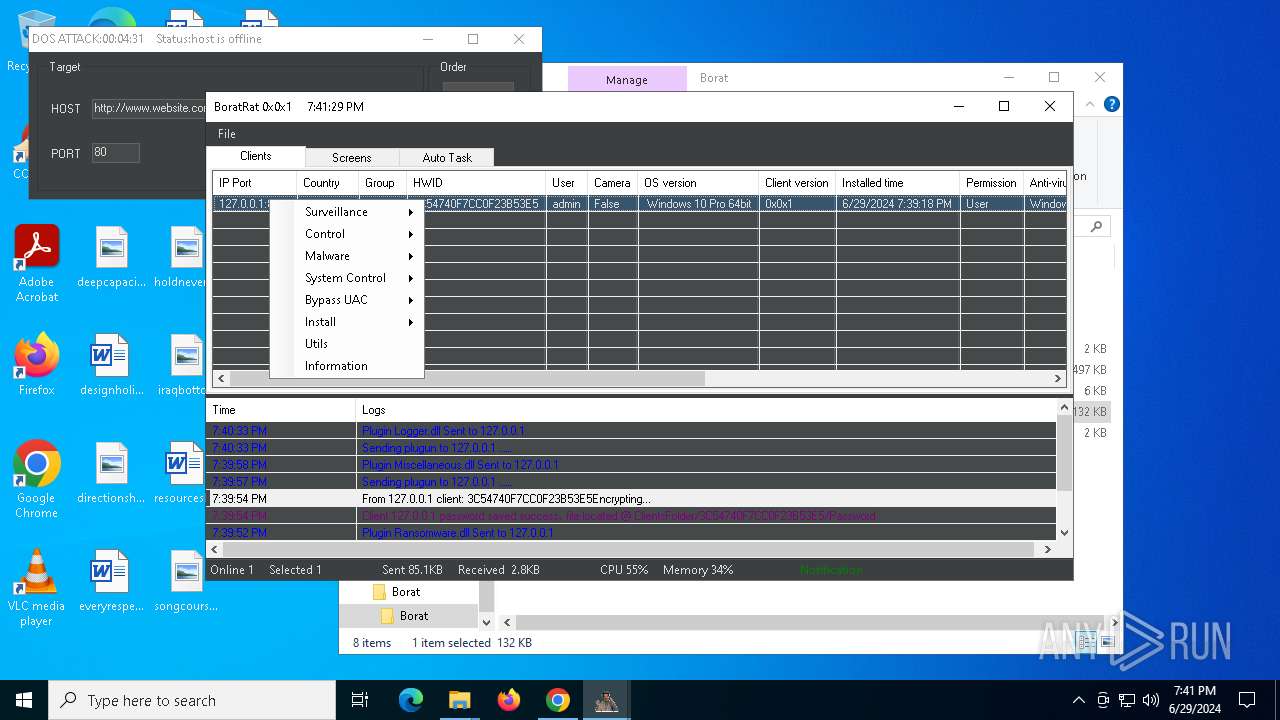
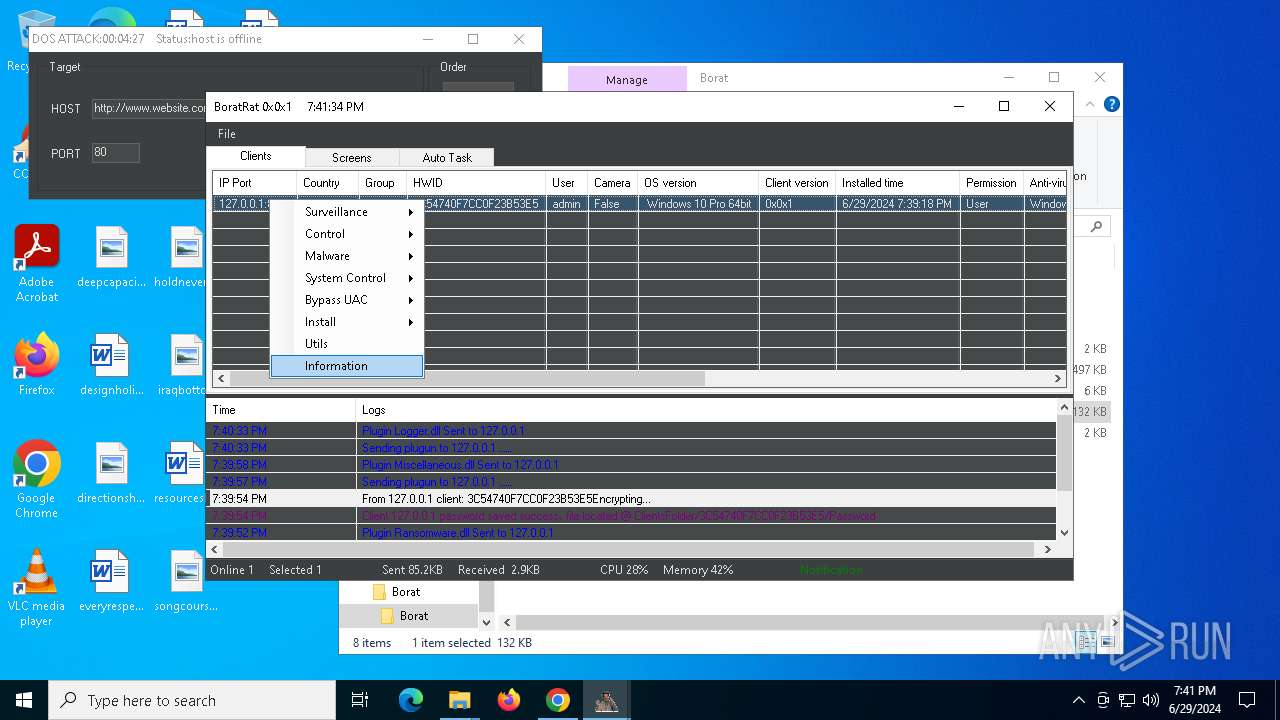
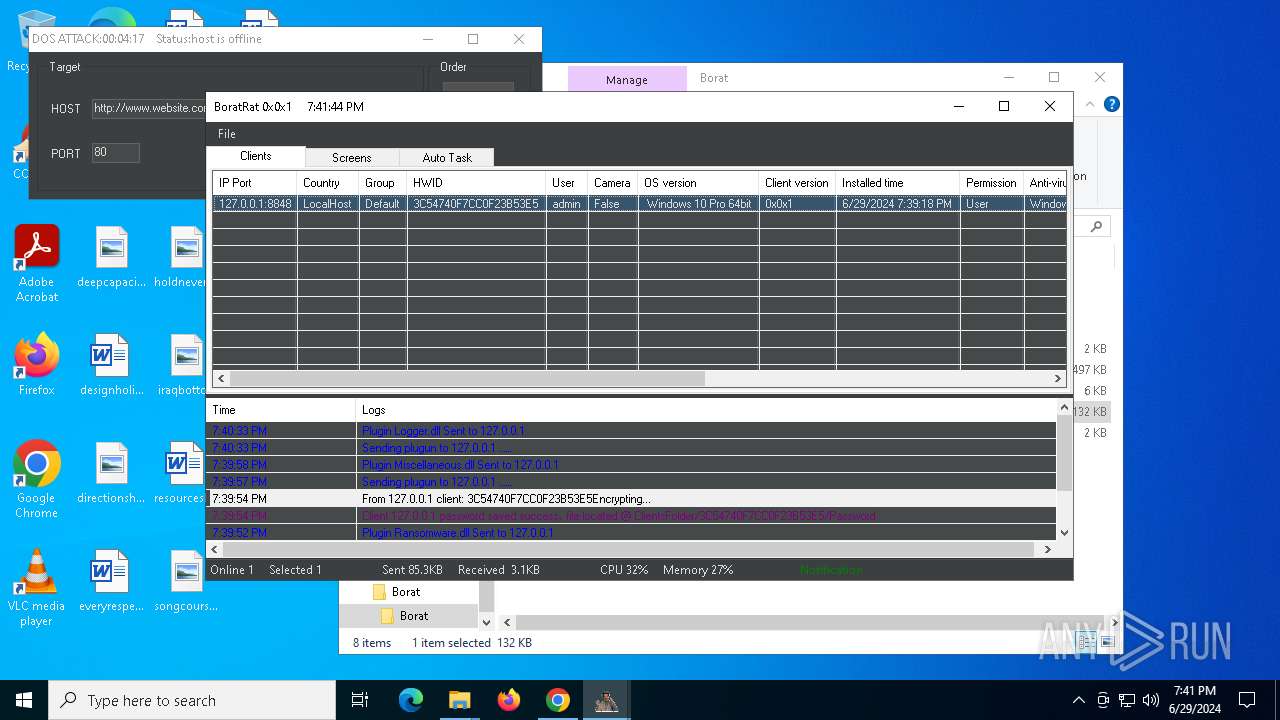
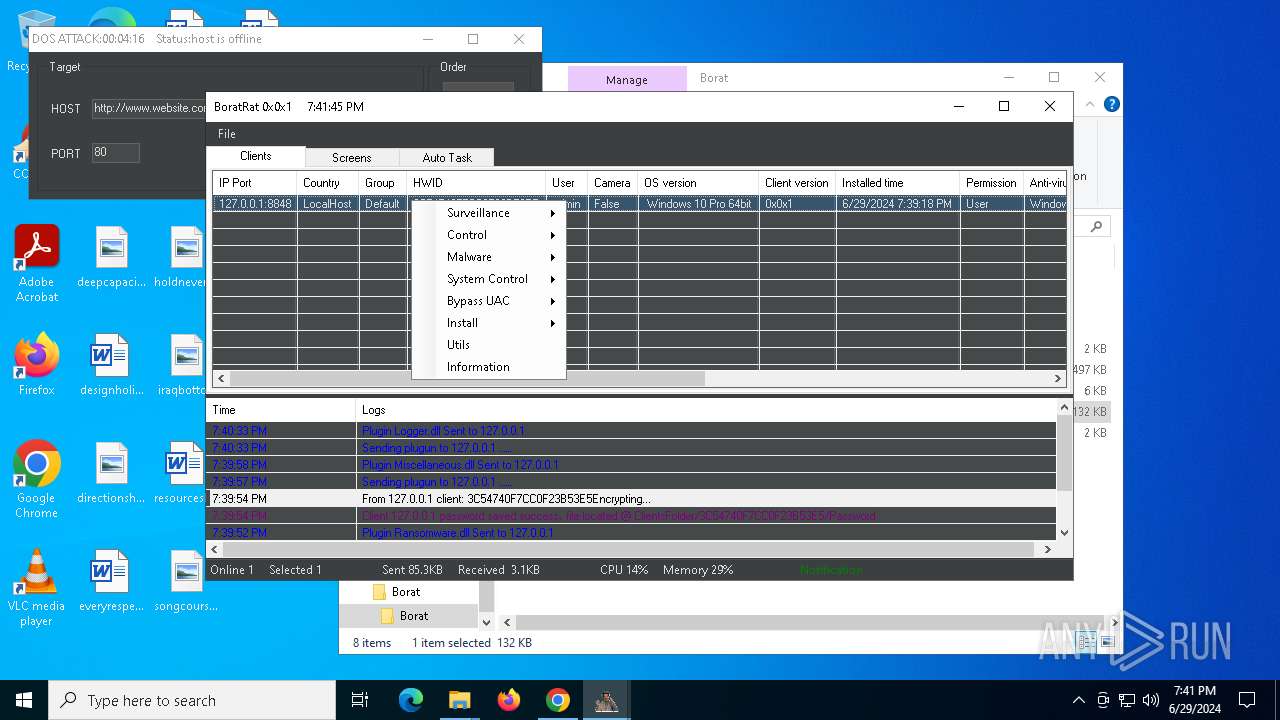
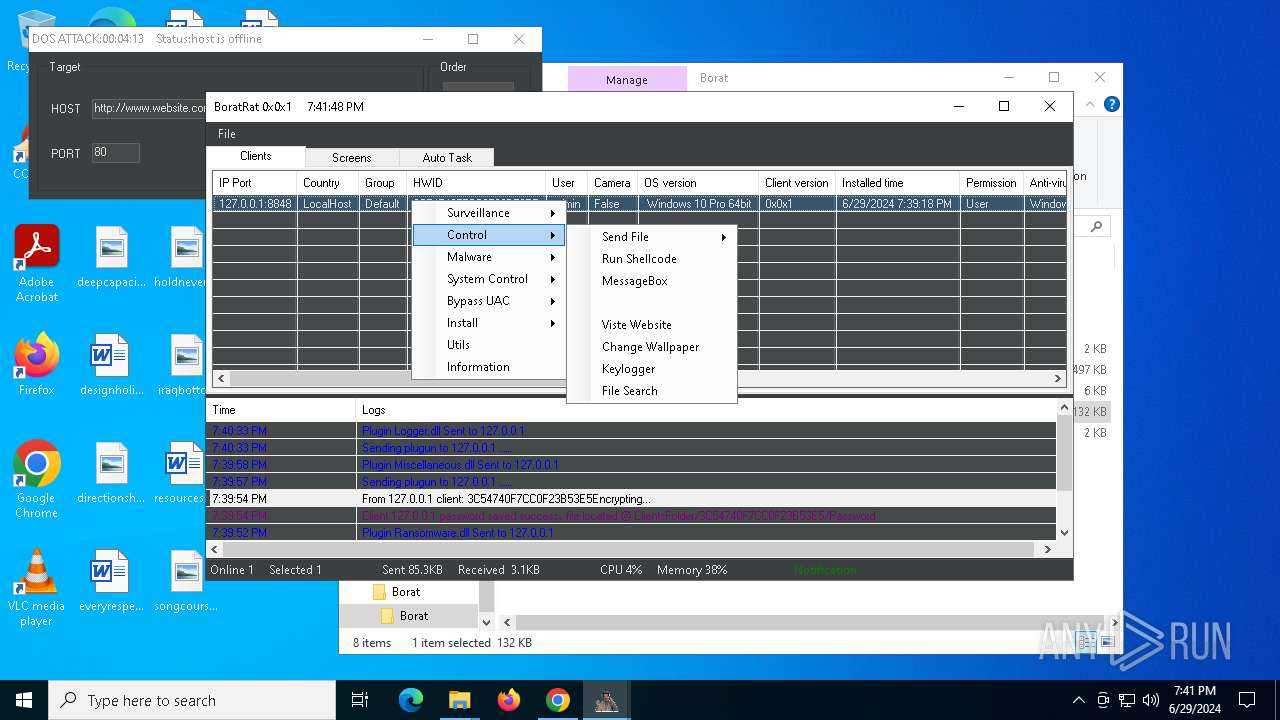
| Verdict: | Malicious activity |
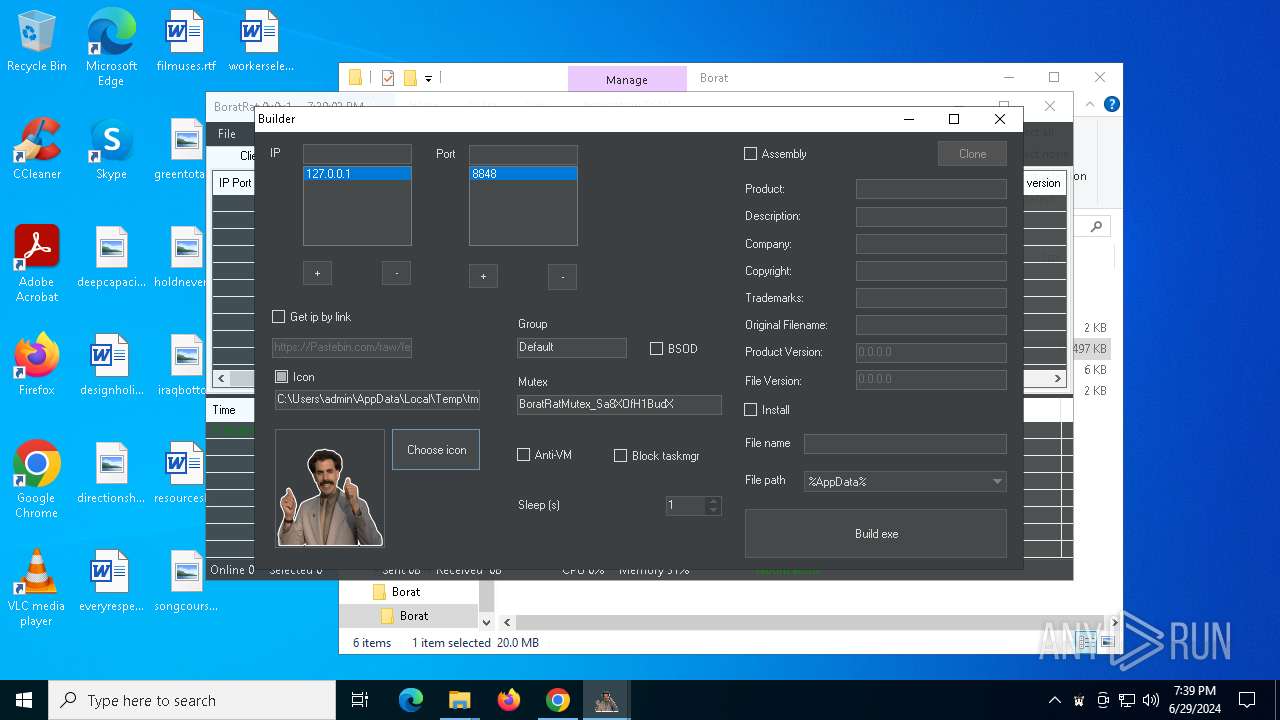
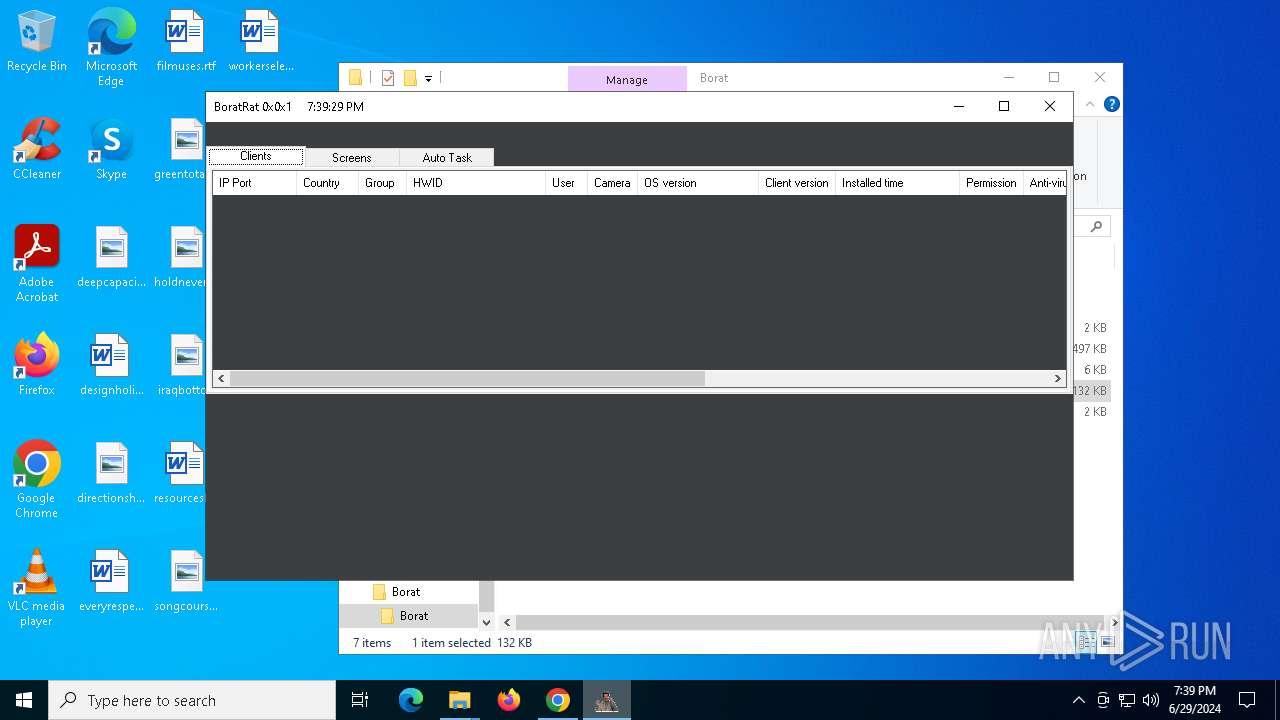
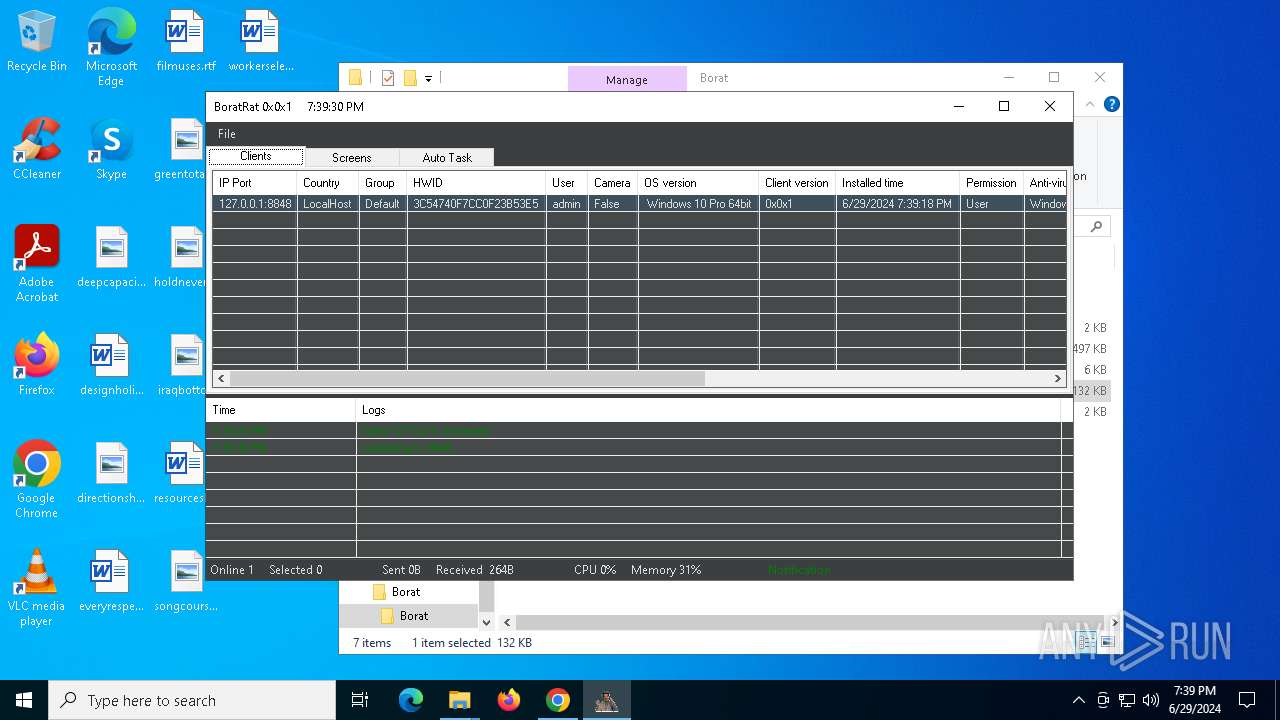
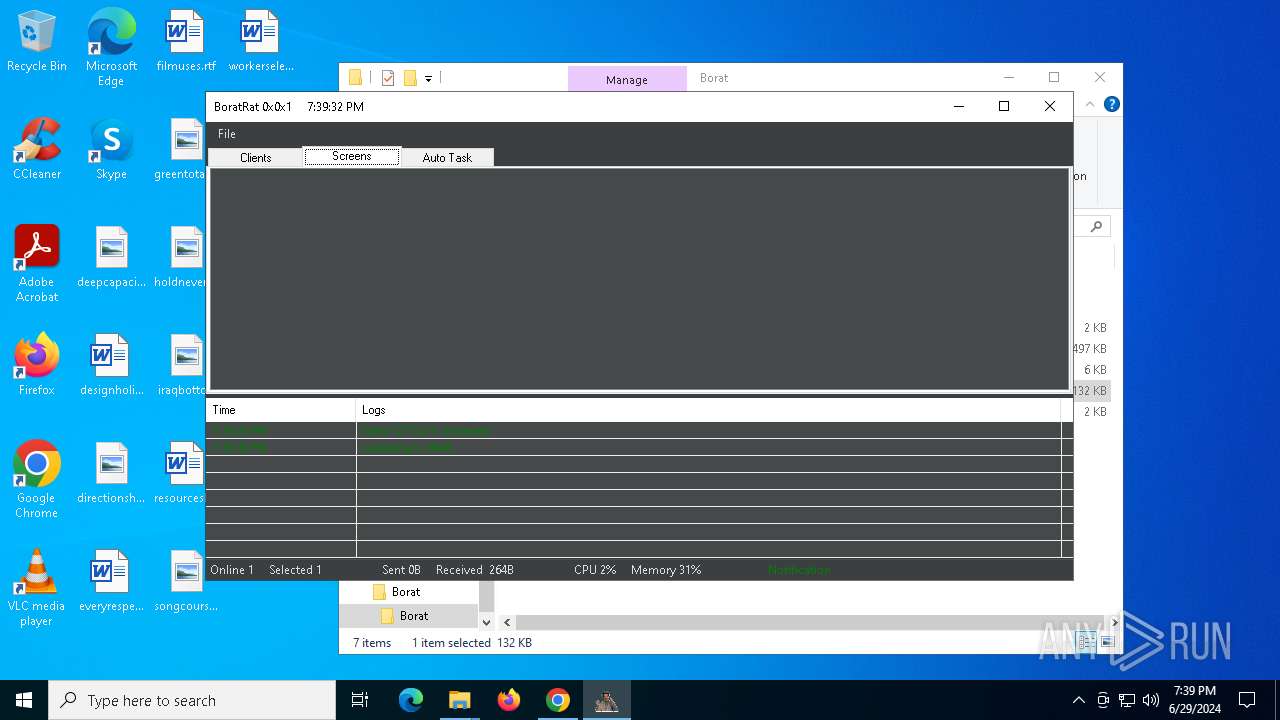
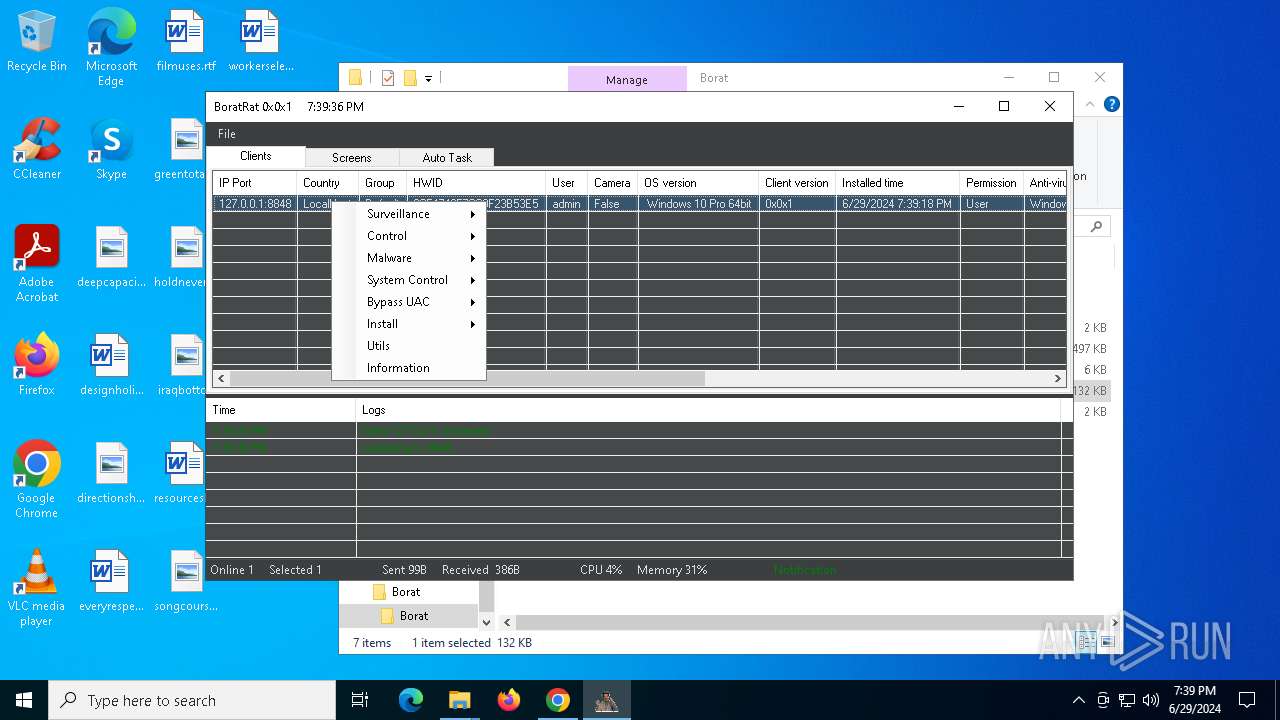
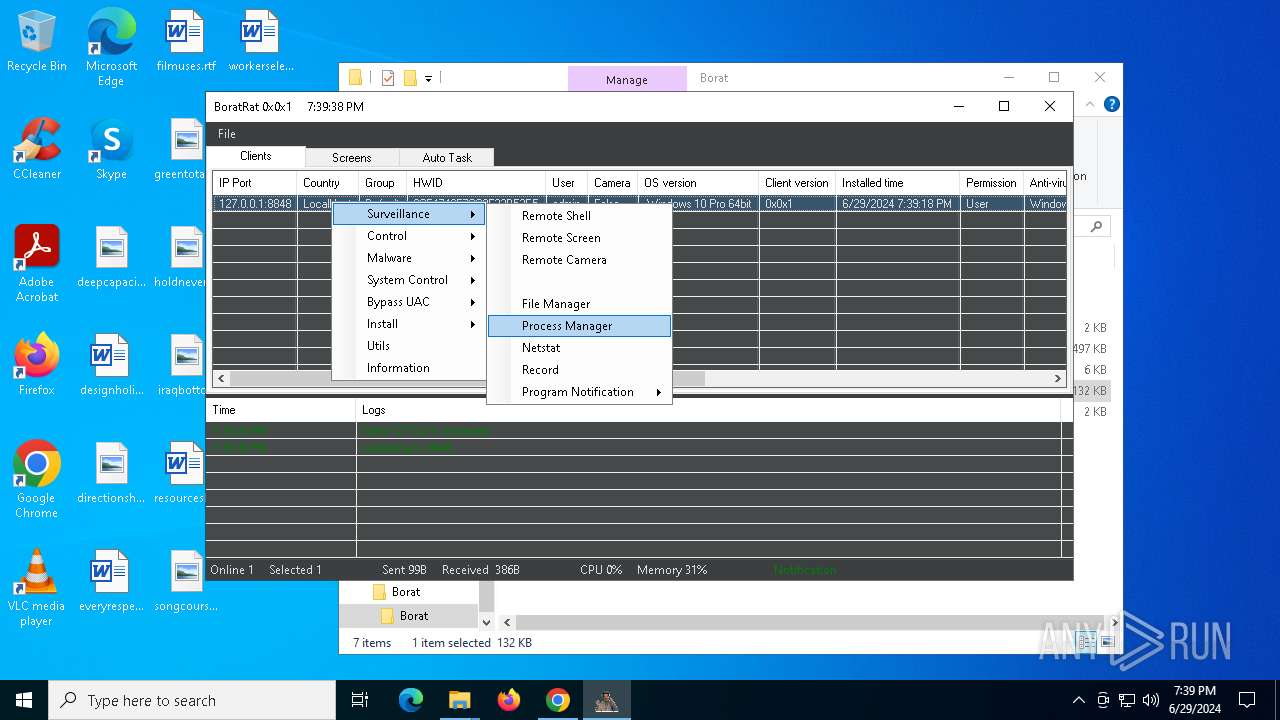
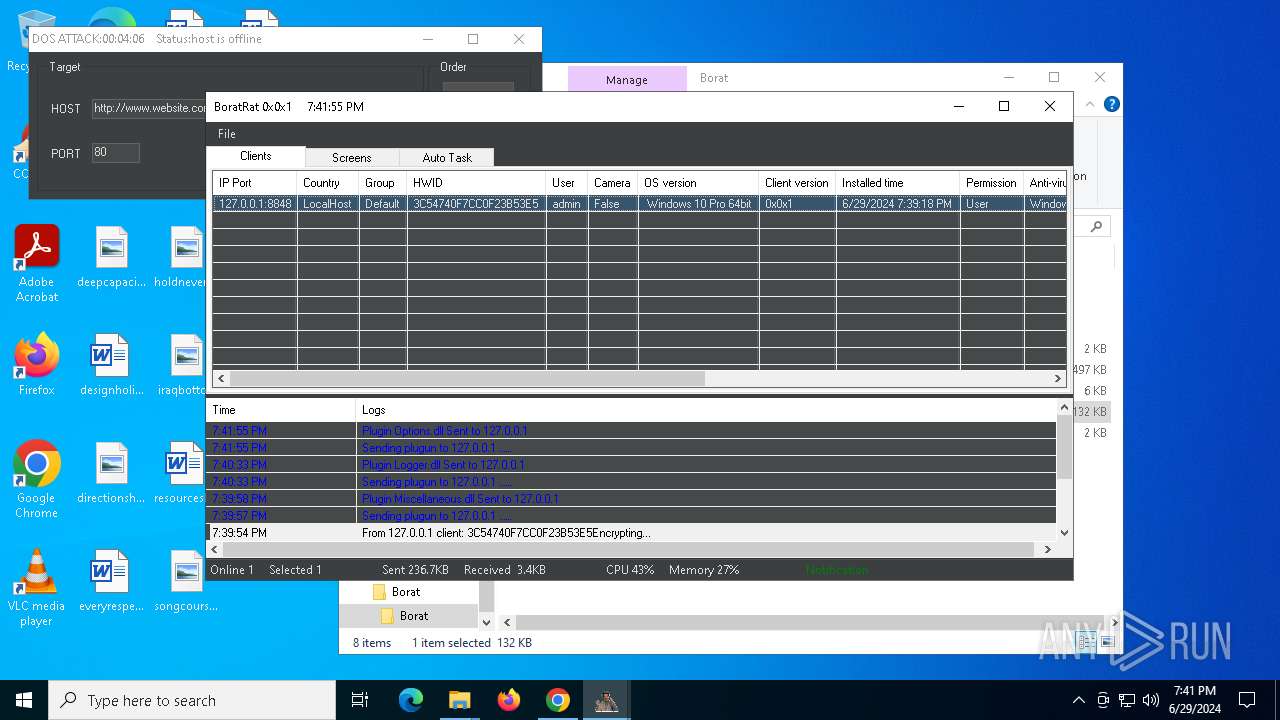
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | June 29, 2024, 19:37:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D20999CD4549BEAC11D7FFD65E7DAC96 |
| SHA1: | 1E51D3AF729A89879764426E89452C30C159BF0F |
| SHA256: | FF82C24F6B58E8CD04EF0A9FC1DA438E800D543881EE11D98CC30B8C5F3408EB |
| SSDEEP: | 3:N8tEd4FtsqEnKkCldXB:2uuFSqEnKbdXB |
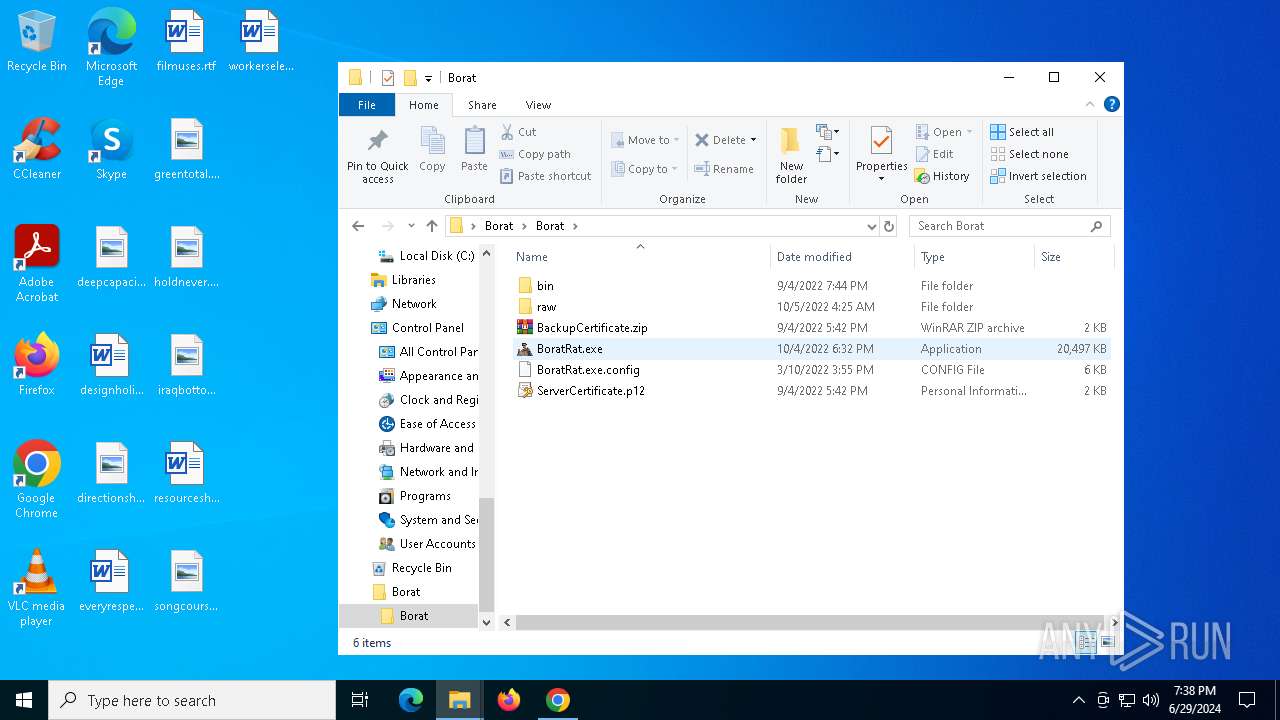
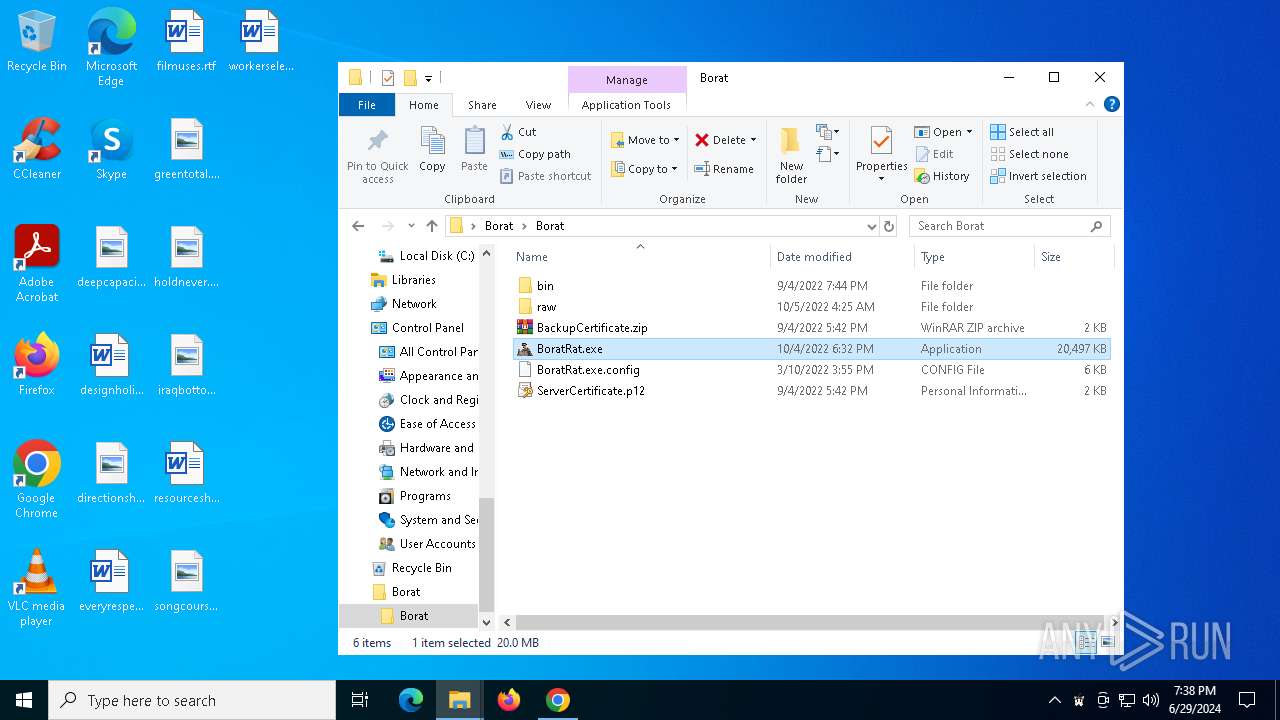
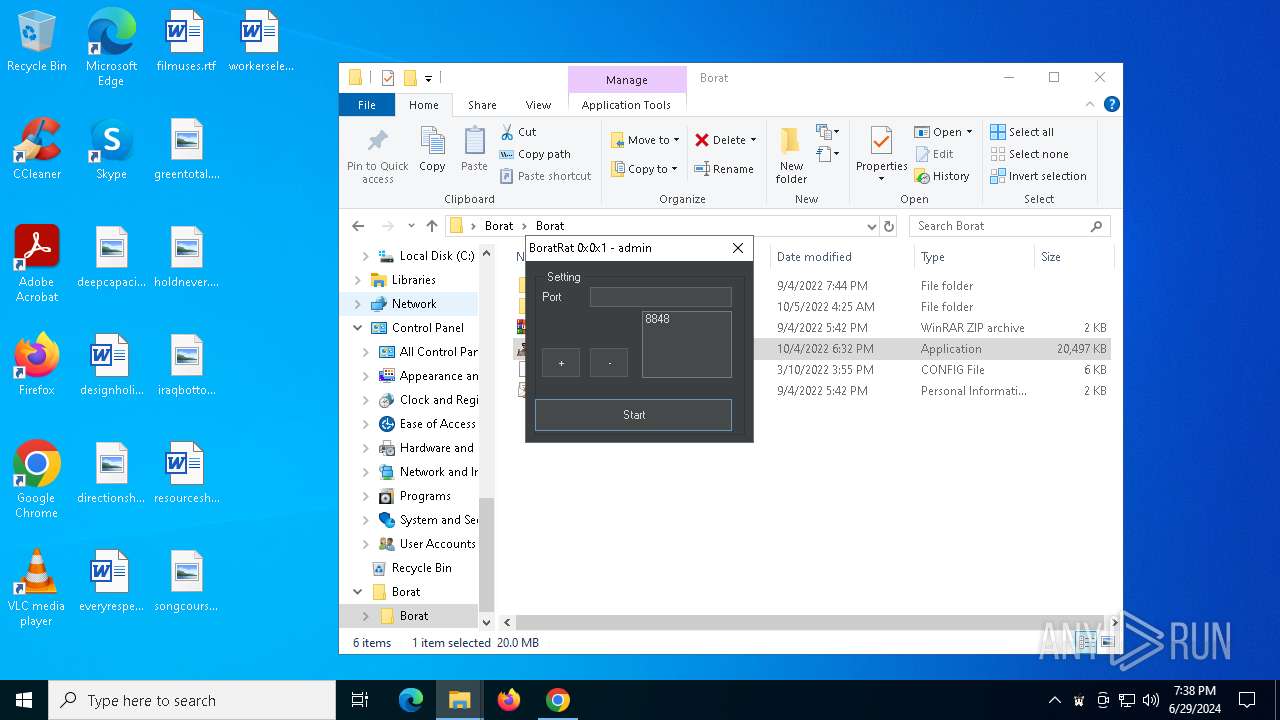
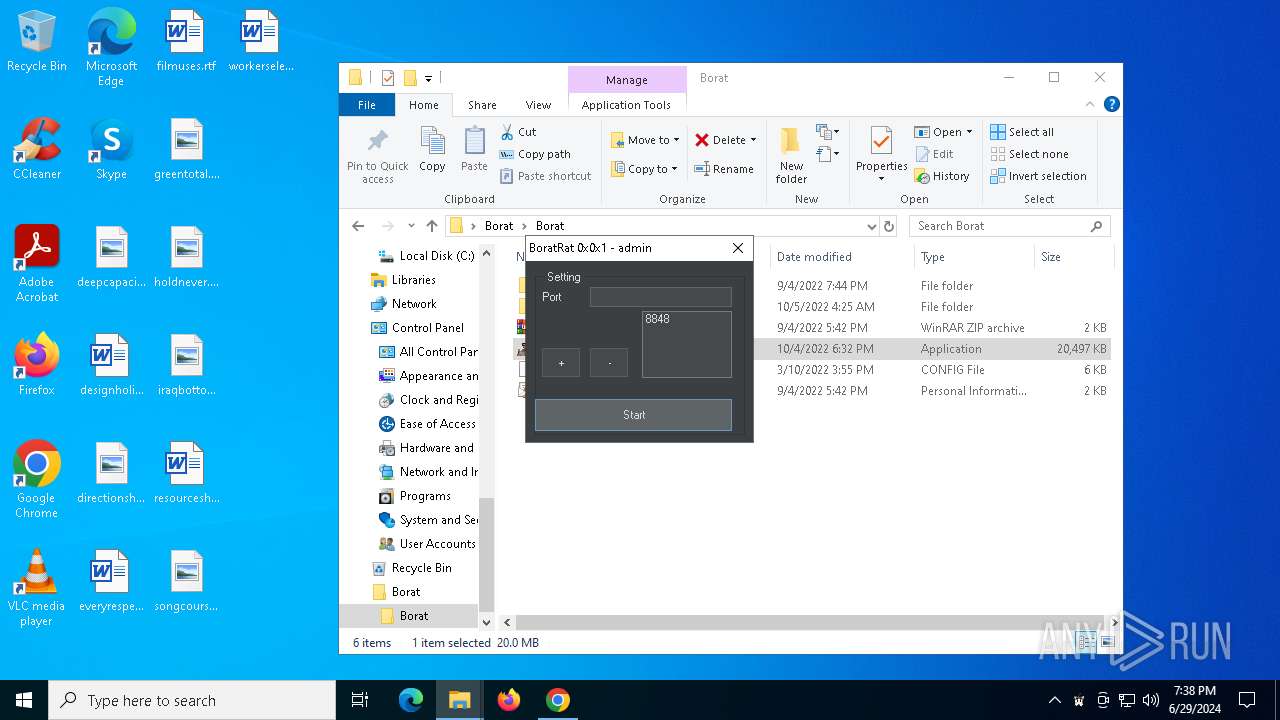
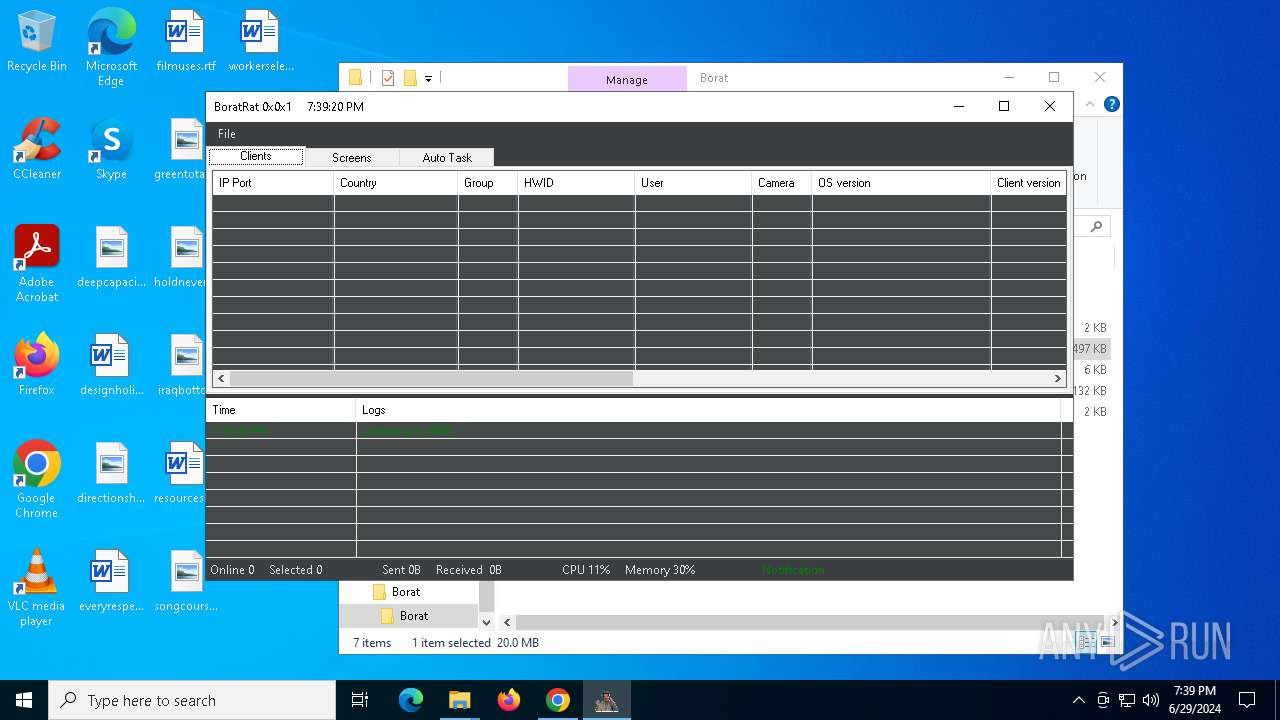
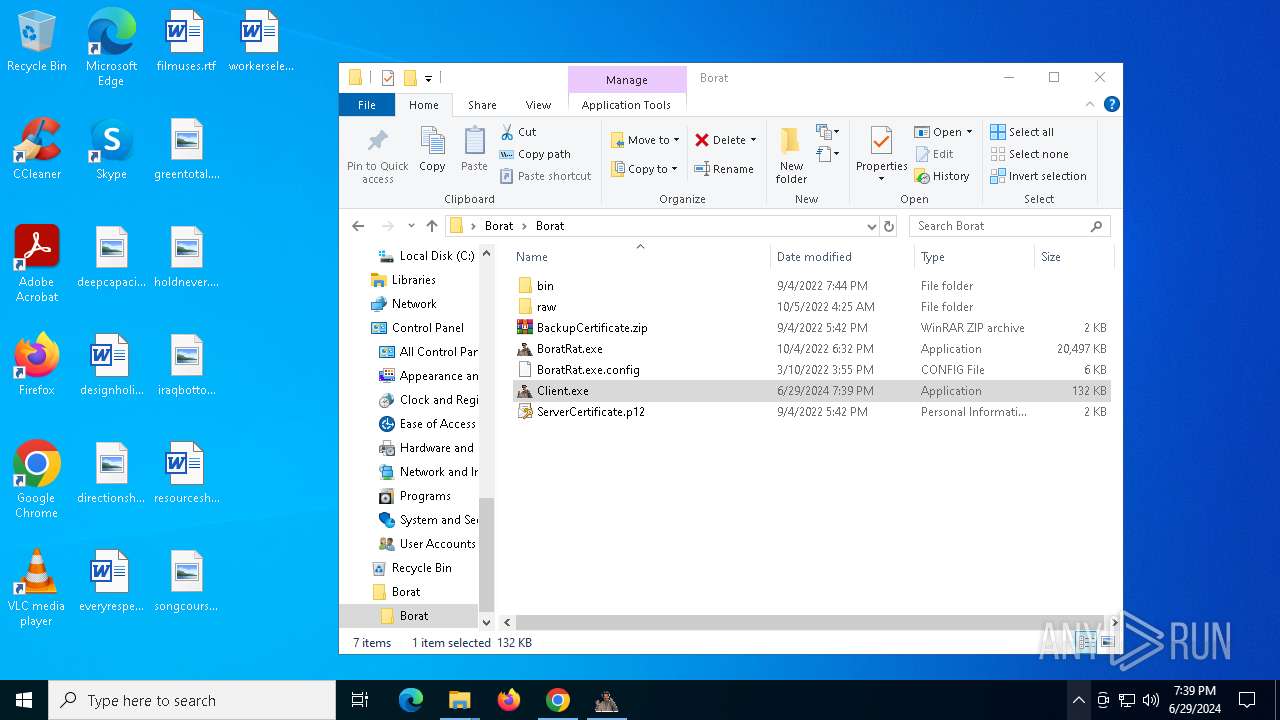
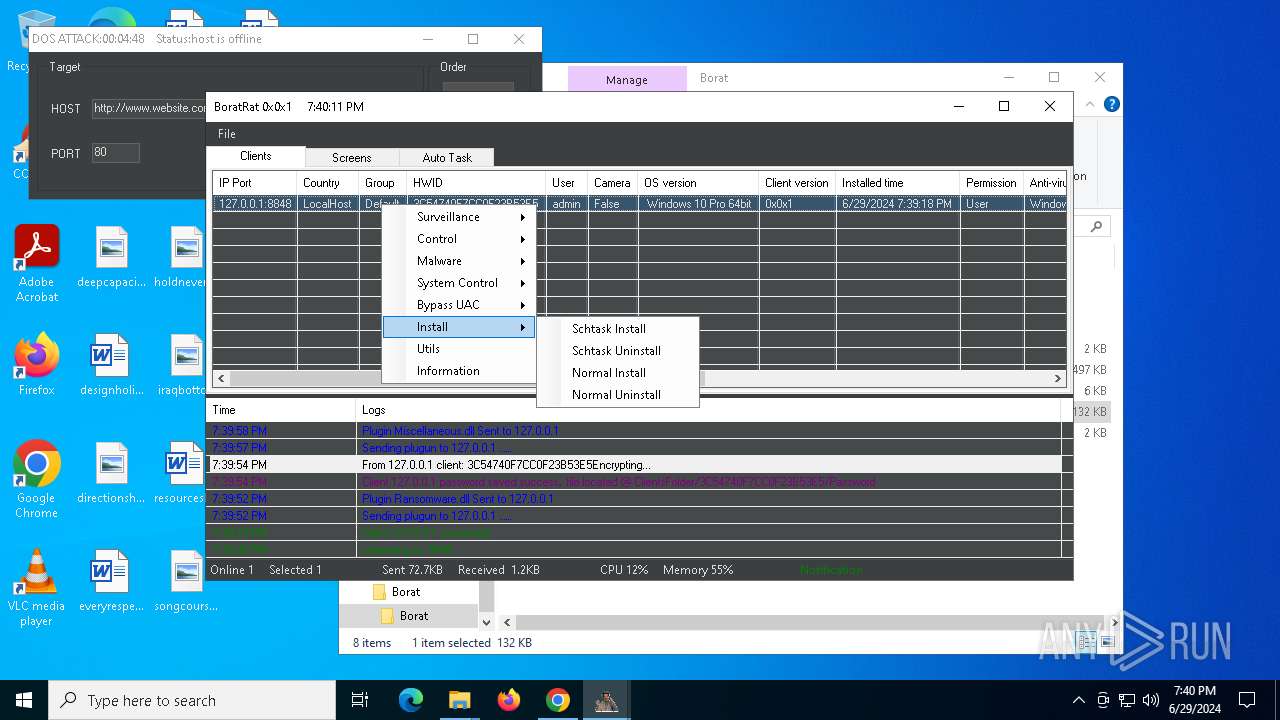
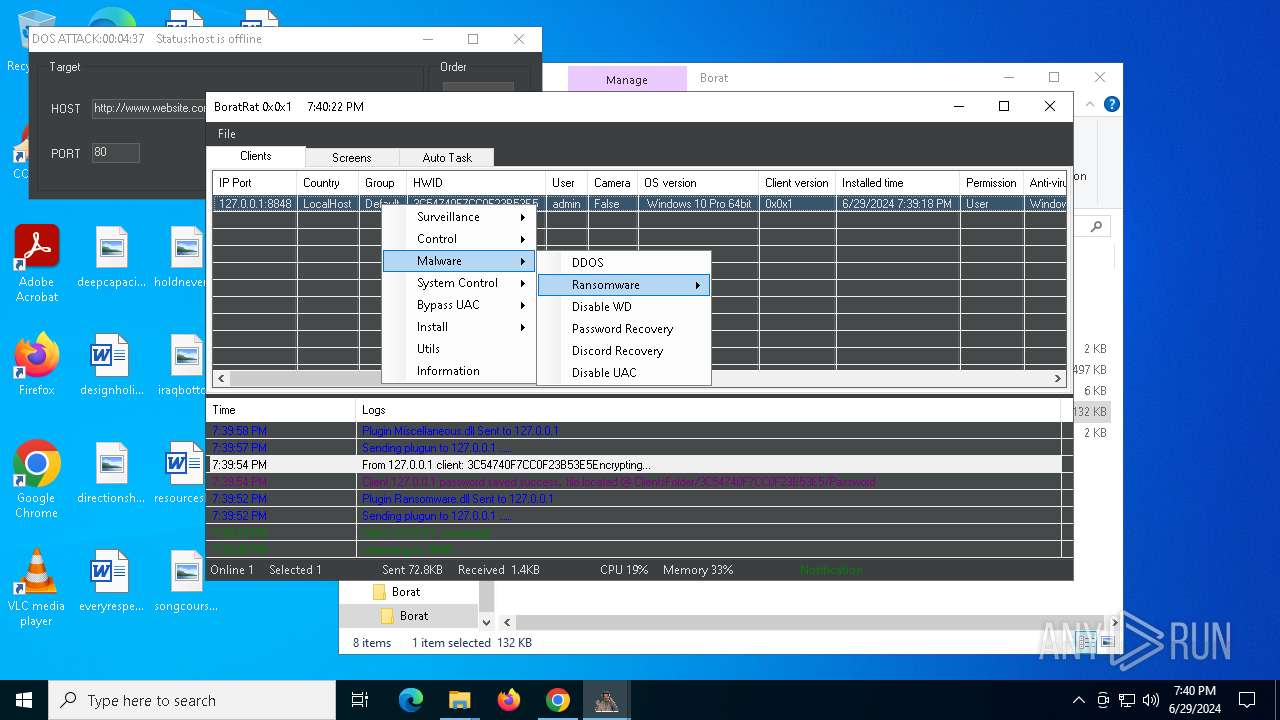
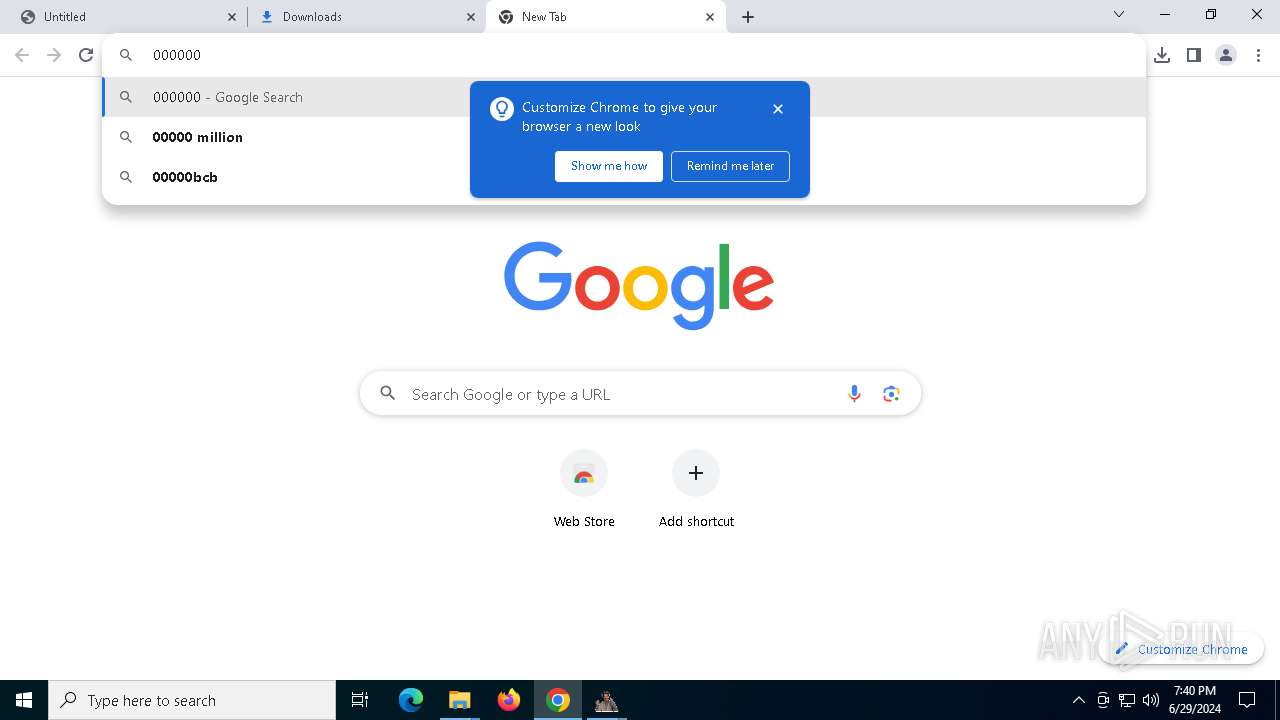
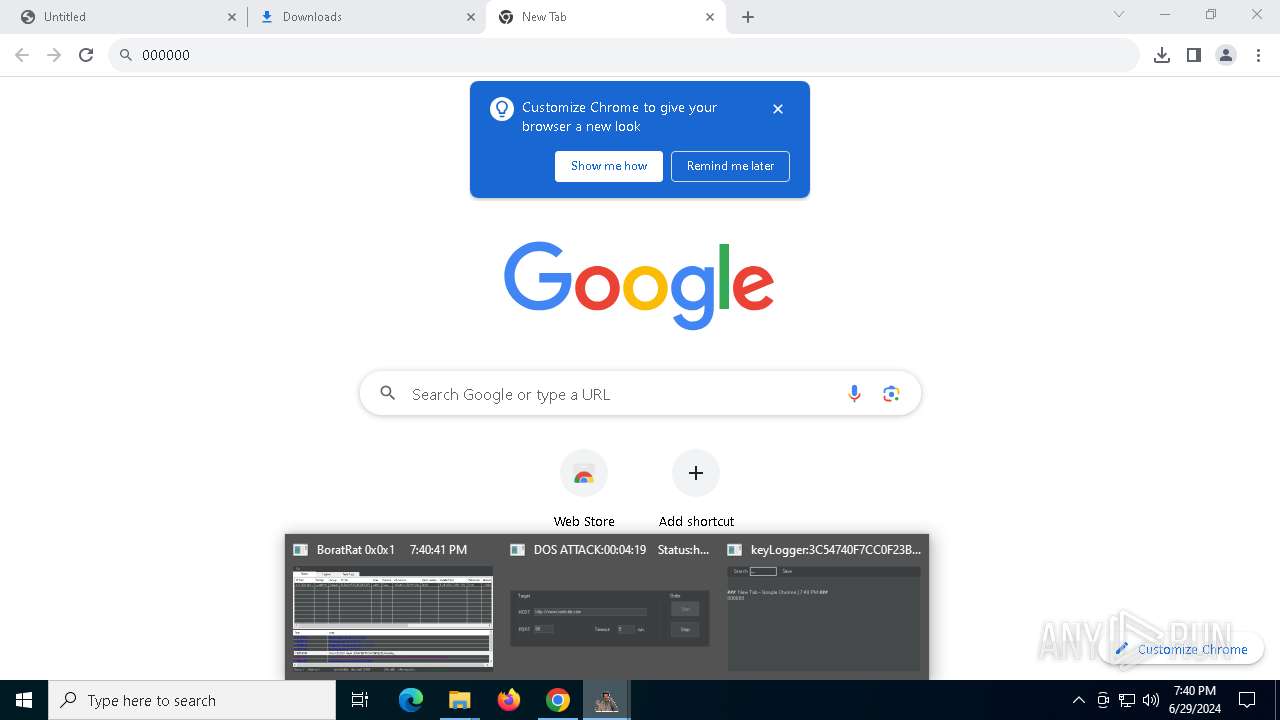
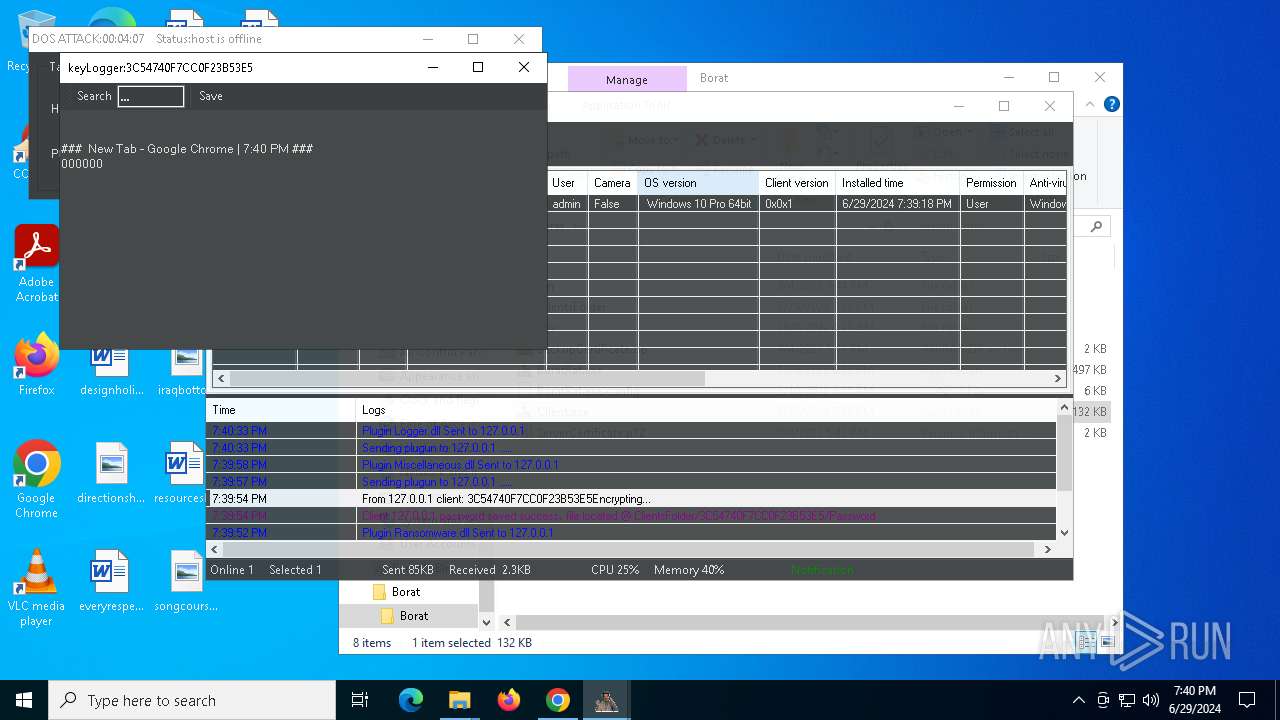
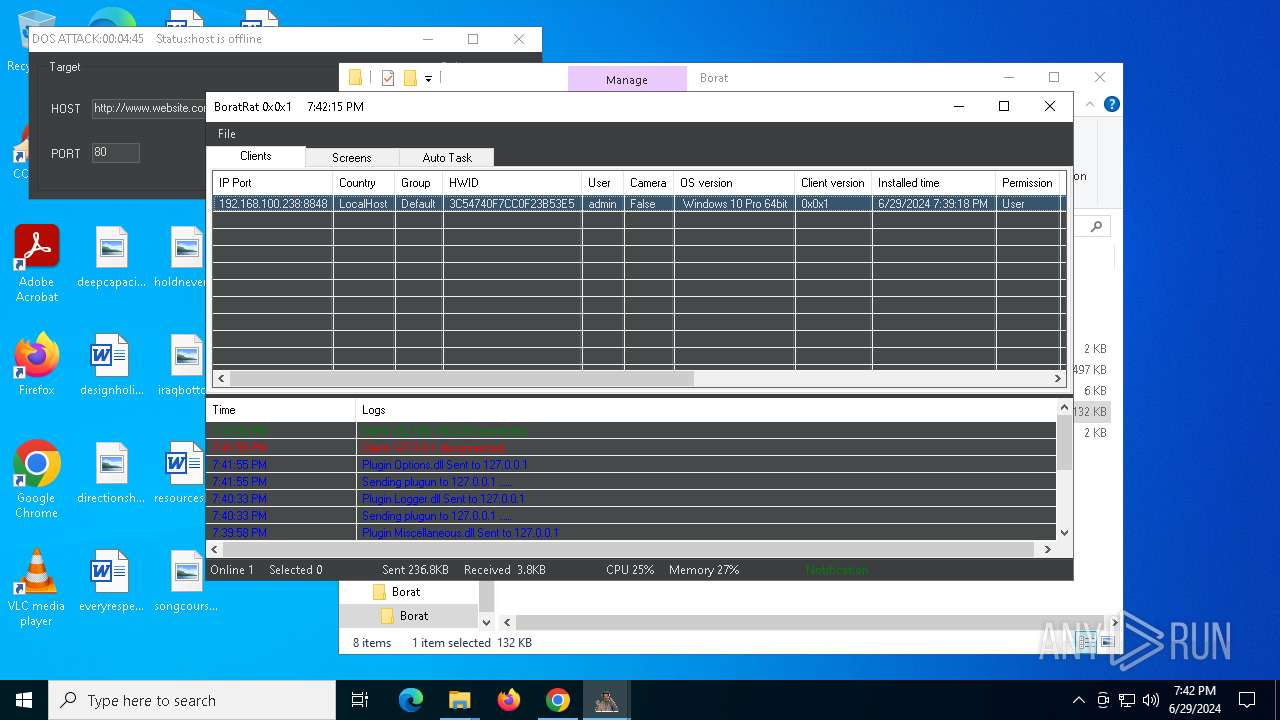
MALICIOUS
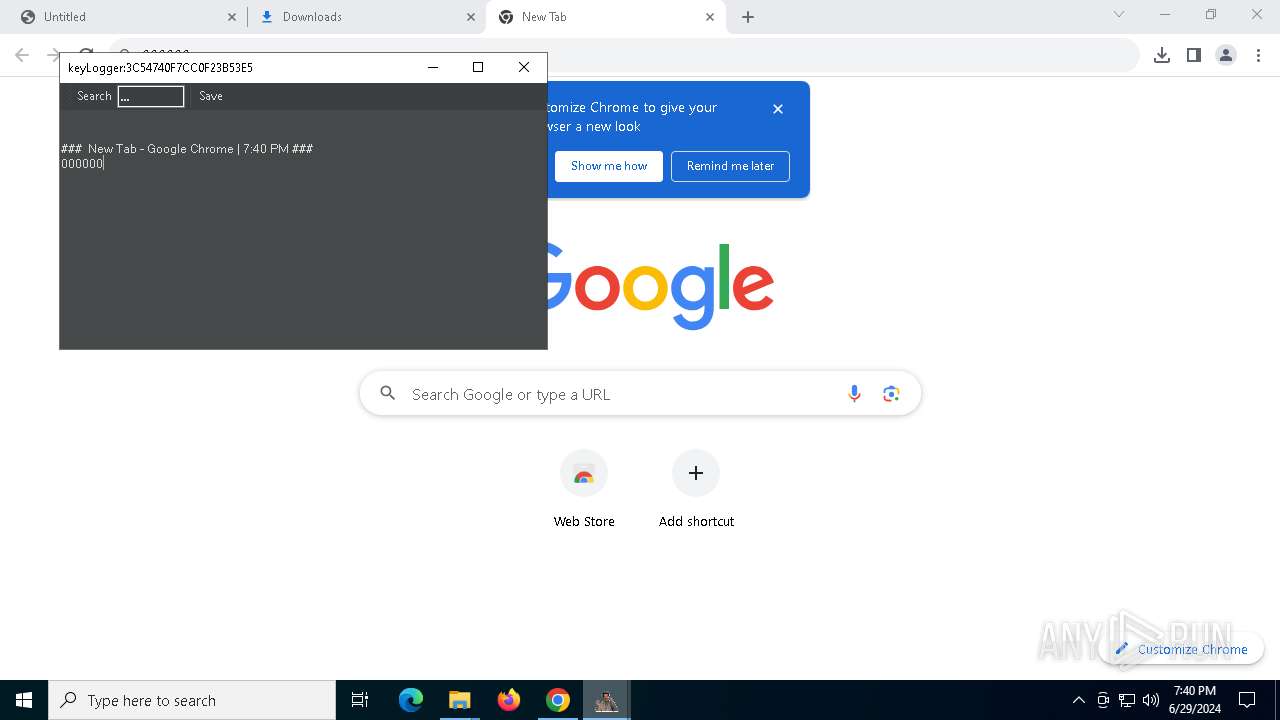
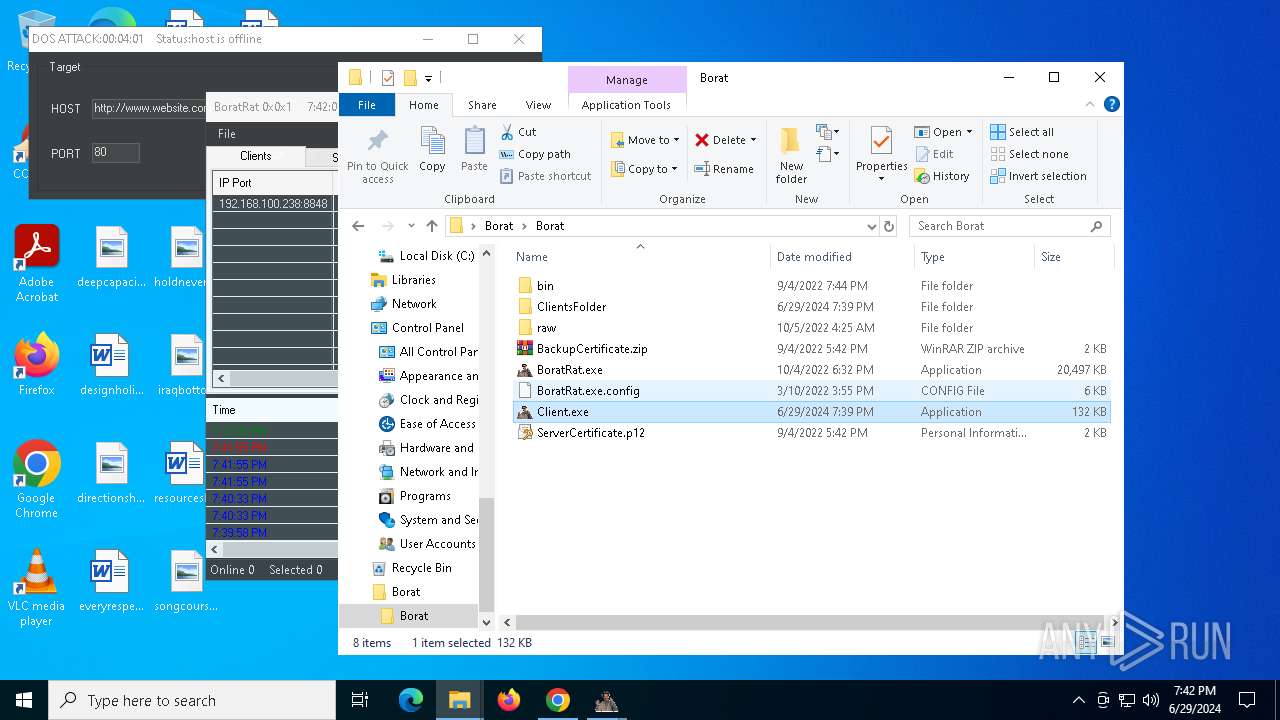
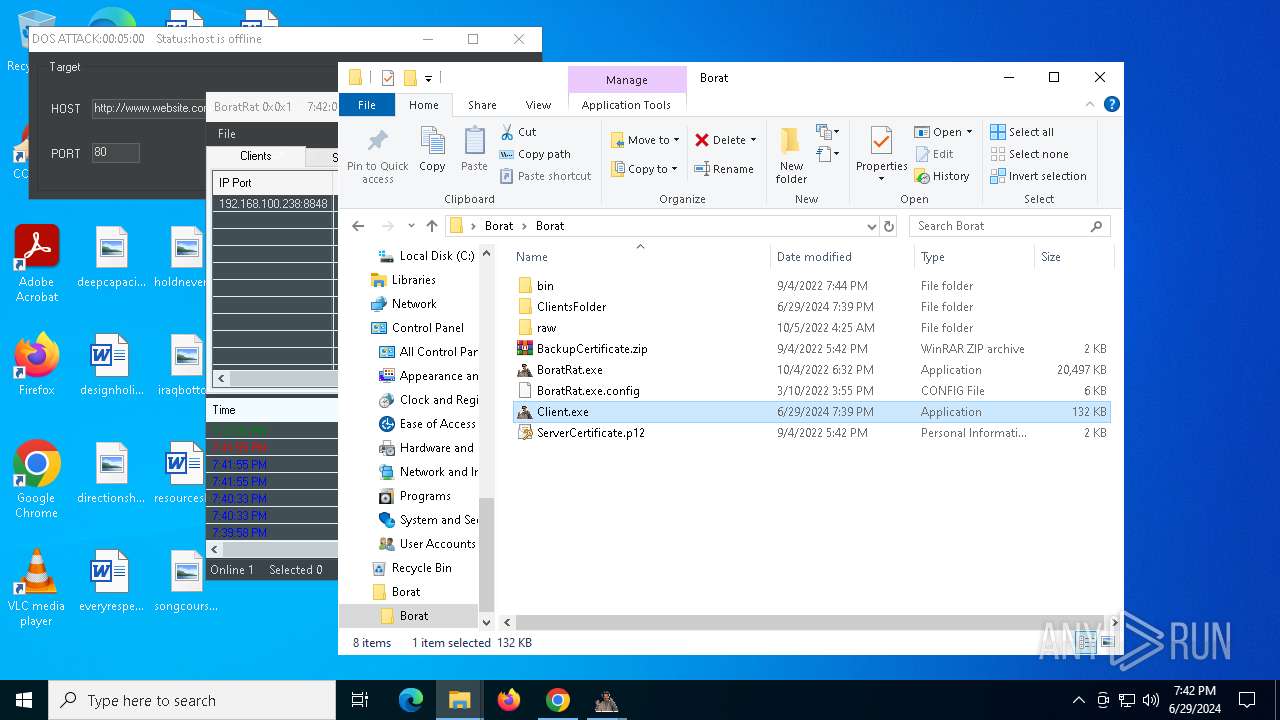
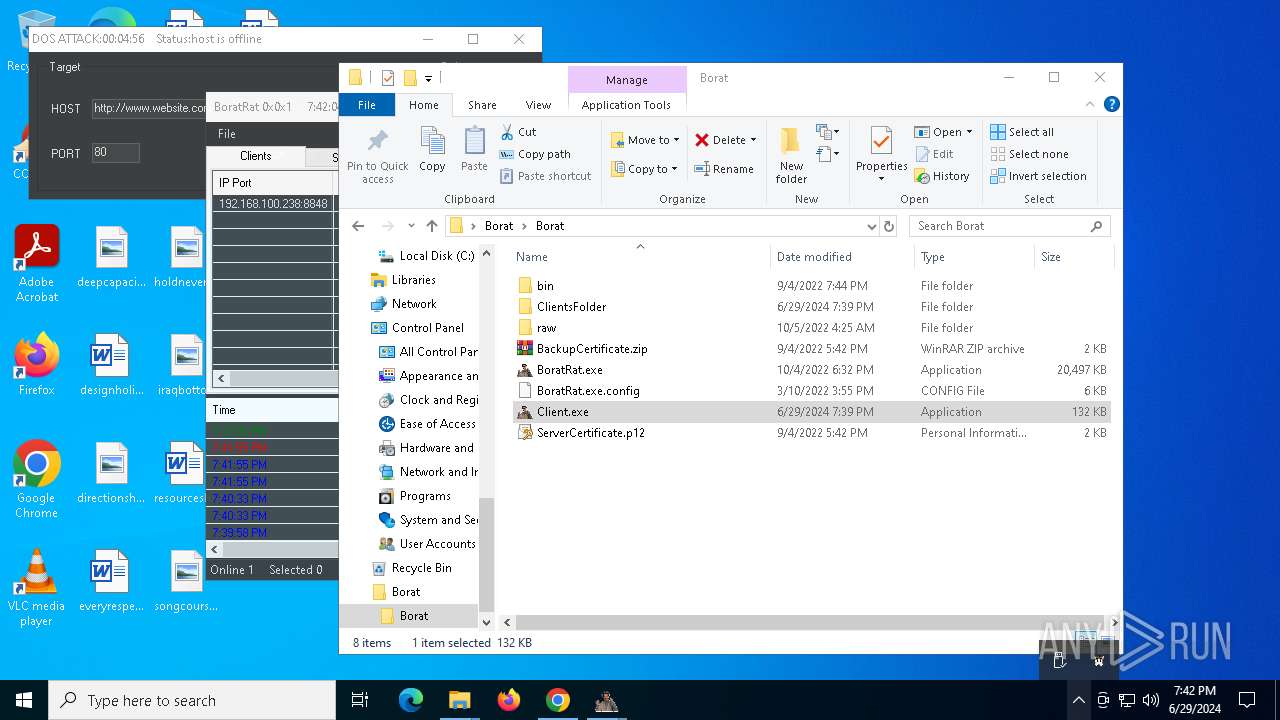
Actions looks like stealing of personal data
- WinRAR.exe (PID: 6768)
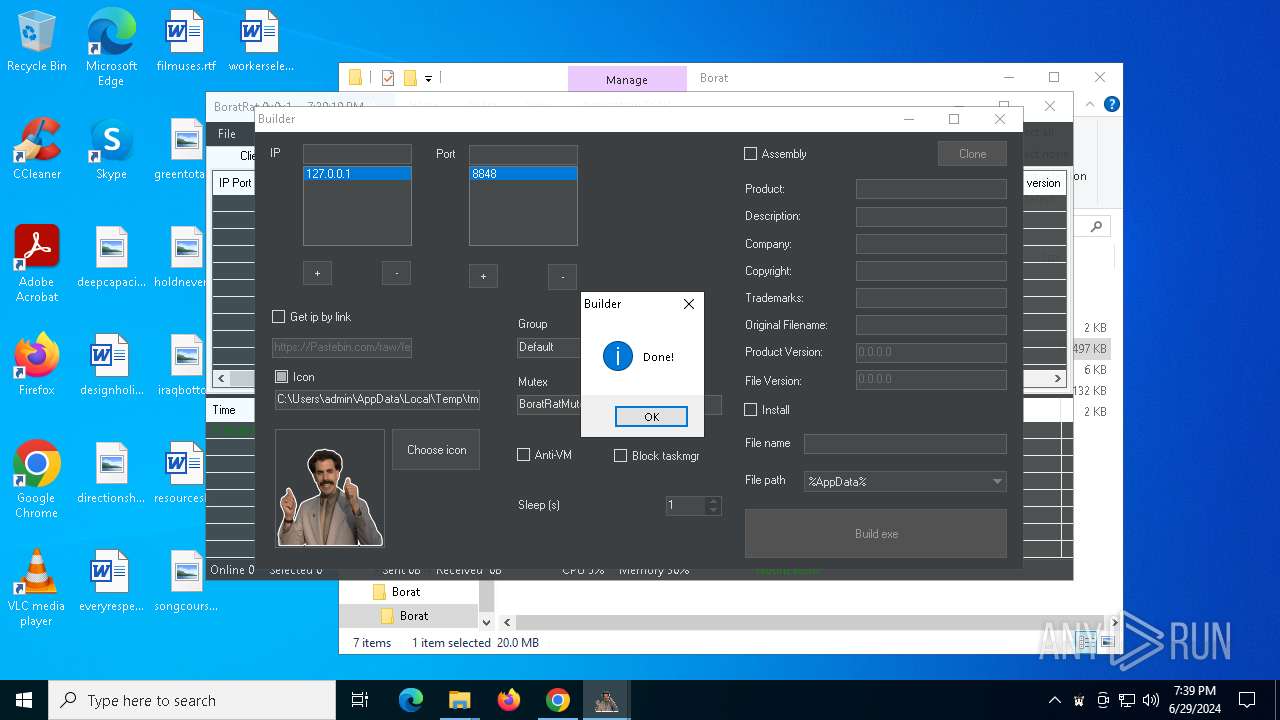
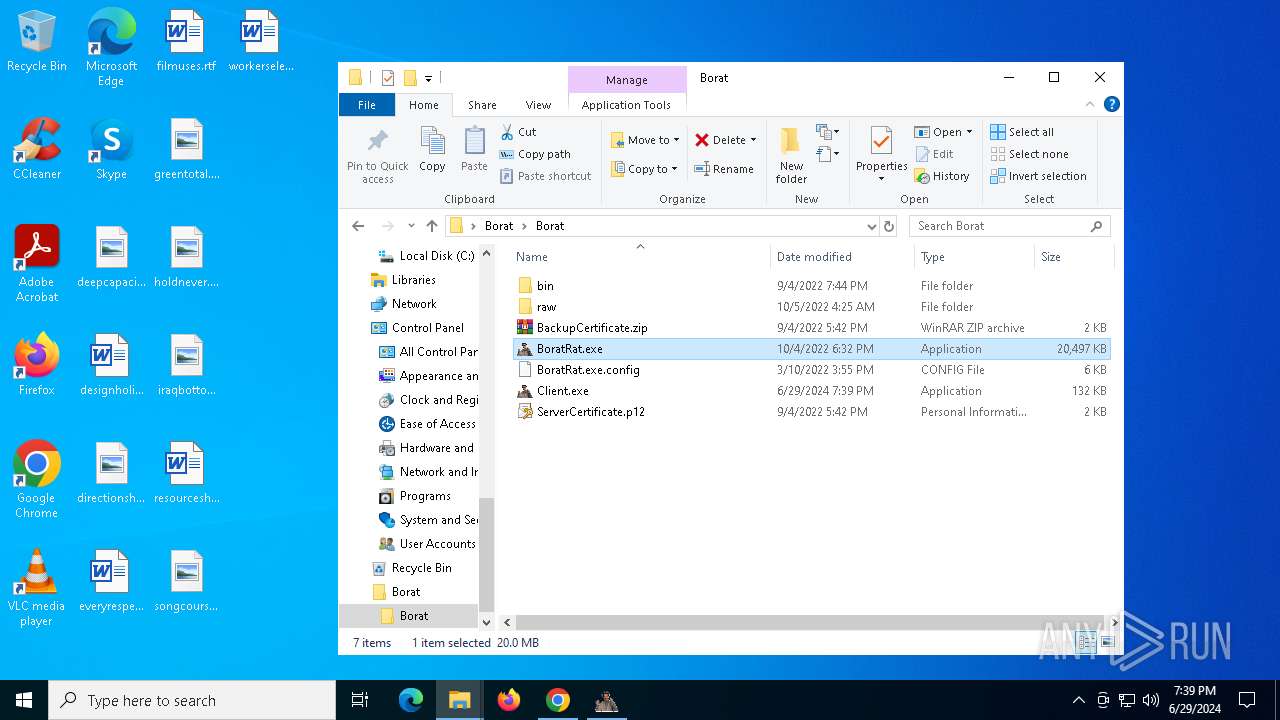
- BoratRat.exe (PID: 6448)
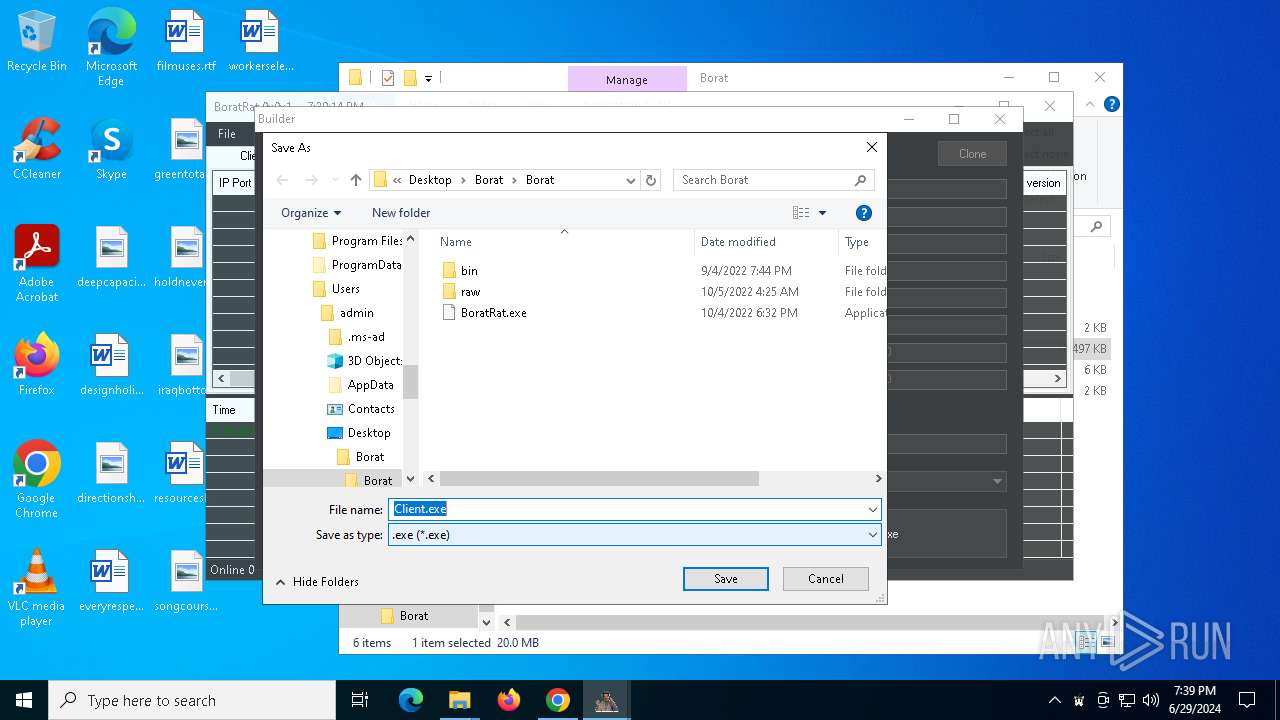
Drops the executable file immediately after the start
- BoratRat.exe (PID: 6448)
ASYNCRAT has been detected (YARA)
- BoratRat.exe (PID: 6448)
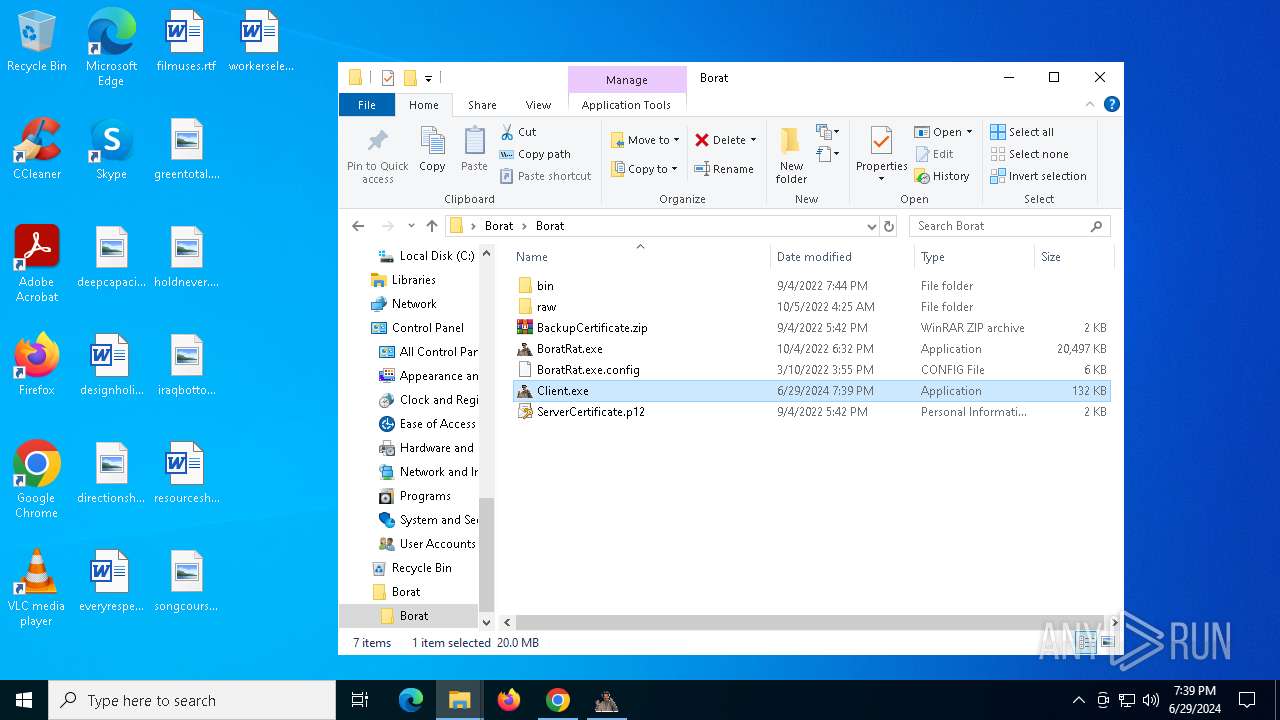
- Client.exe (PID: 6632)
LimeRAT is detected
- Client.exe (PID: 6632)
SUSPICIOUS
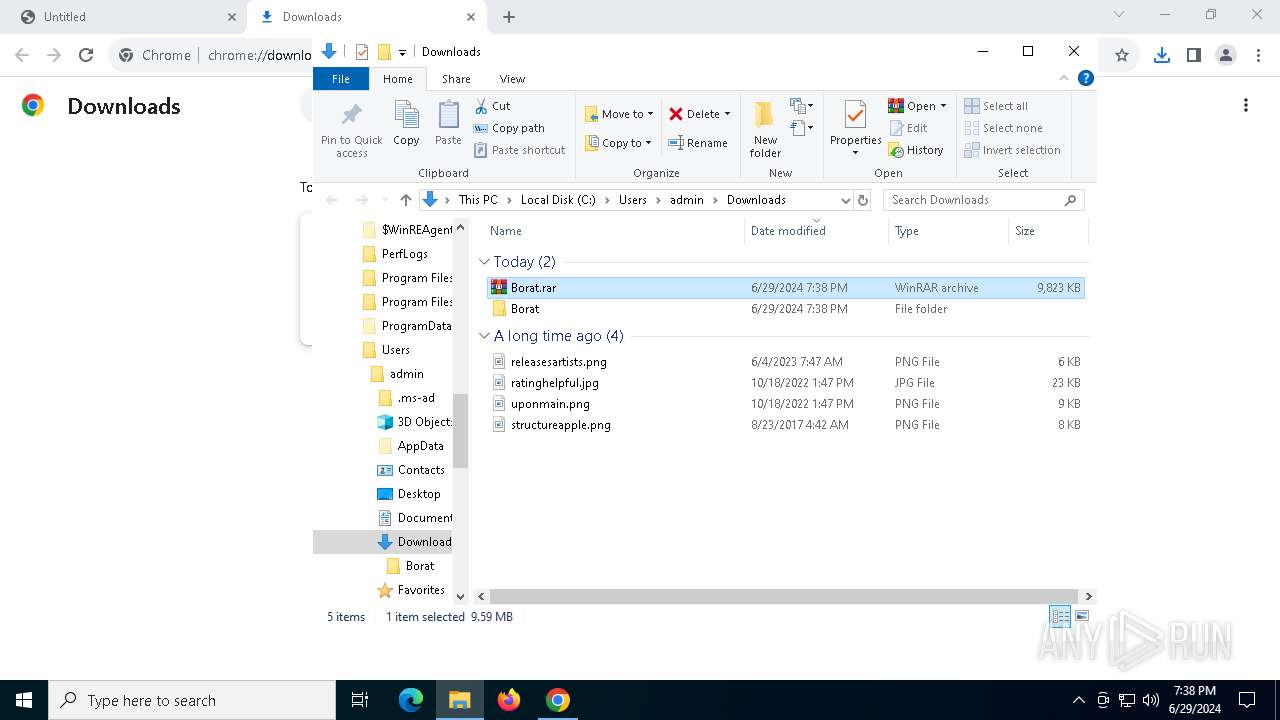
The process creates files with name similar to system file names
- WinRAR.exe (PID: 6768)
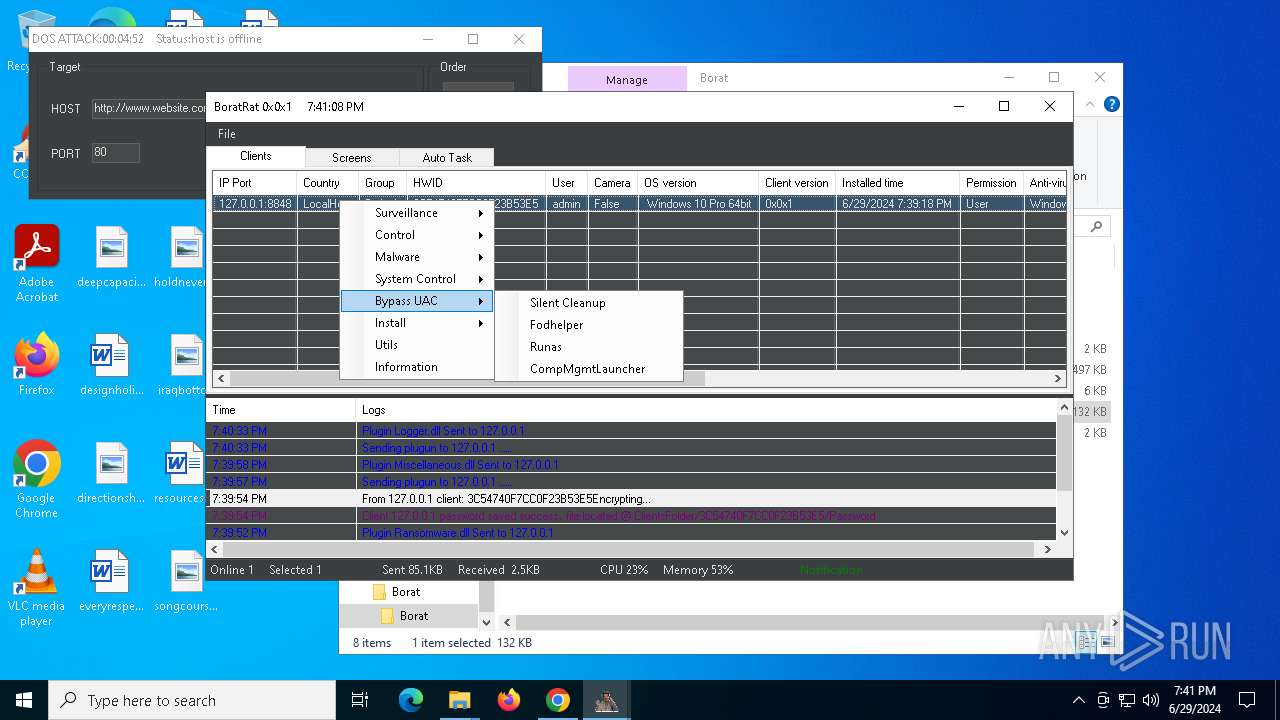
The process checks if it is being run in the virtual environment
- BoratRat.exe (PID: 6448)
Reads security settings of Internet Explorer
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 4004)
- StartMenuExperienceHost.exe (PID: 6868)
Creates file in the systems drive root
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 6632)
Executable content was dropped or overwritten
- BoratRat.exe (PID: 6448)
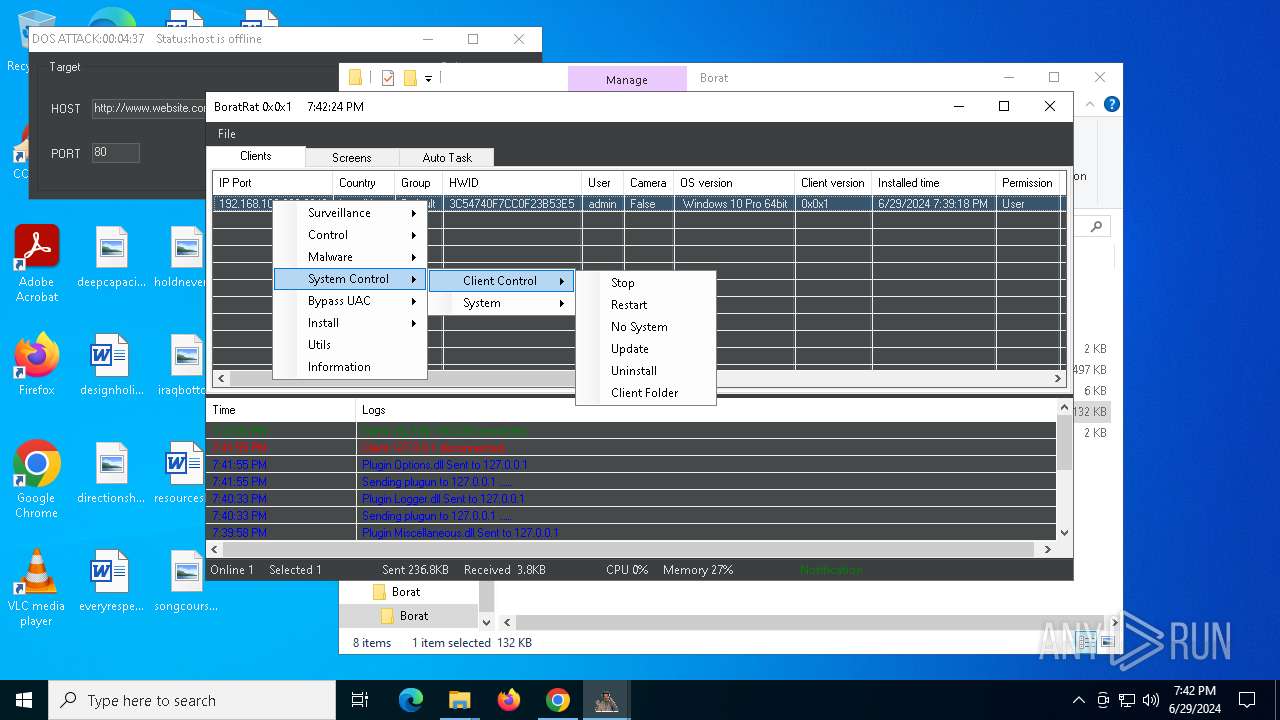
Starts CMD.EXE for commands execution
- Client.exe (PID: 6632)
- Client.exe (PID: 4004)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5344)
Executing commands from a ".bat" file
- Client.exe (PID: 6632)
Reads the date of Windows installation
- Client.exe (PID: 4004)
- StartMenuExperienceHost.exe (PID: 6868)
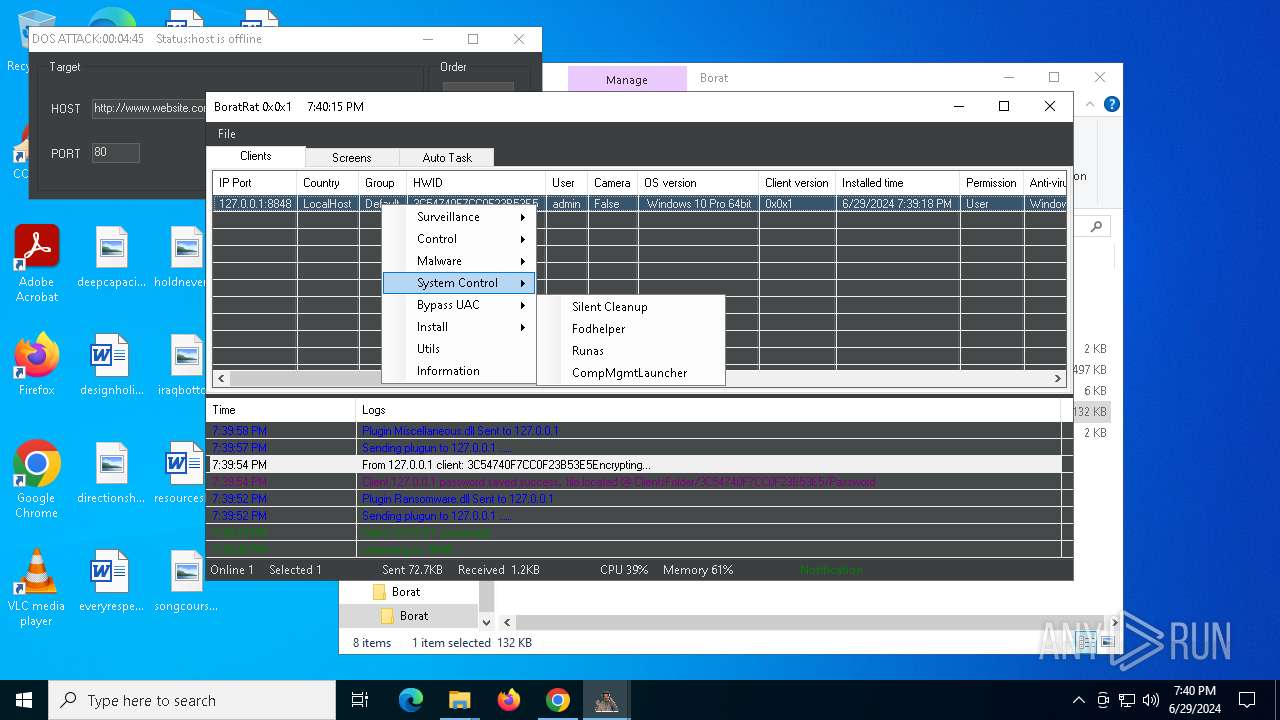
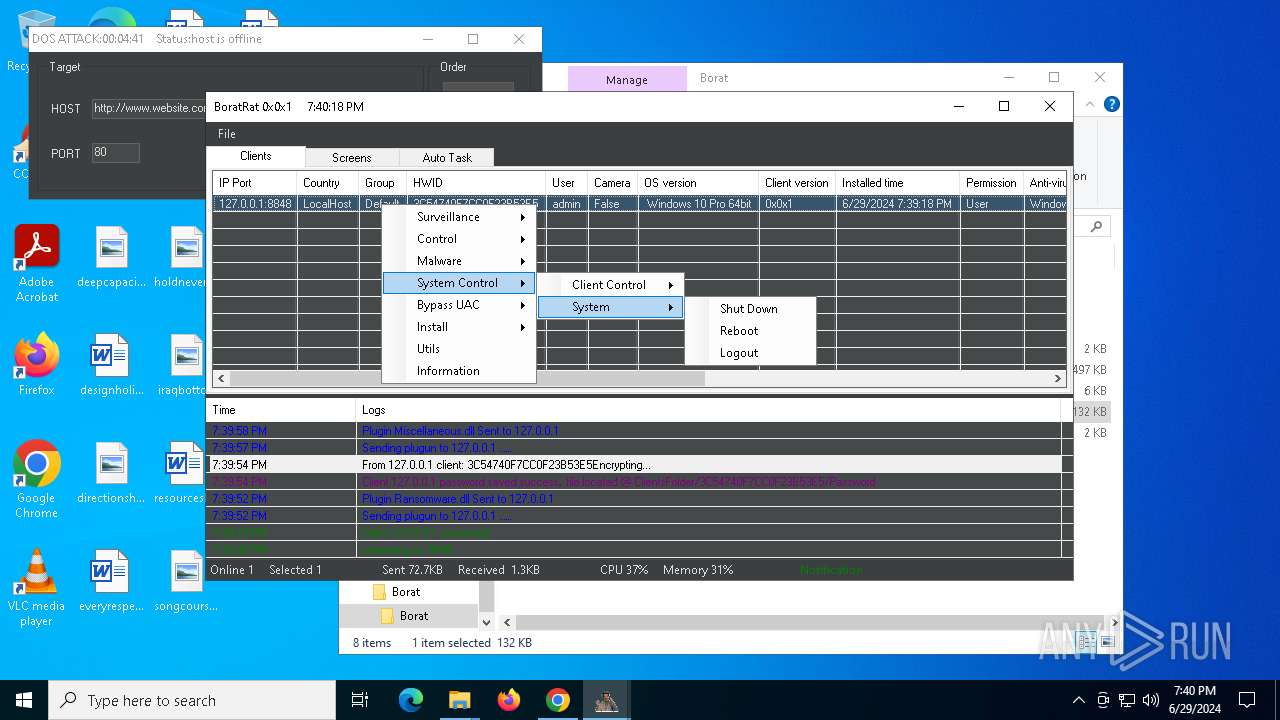
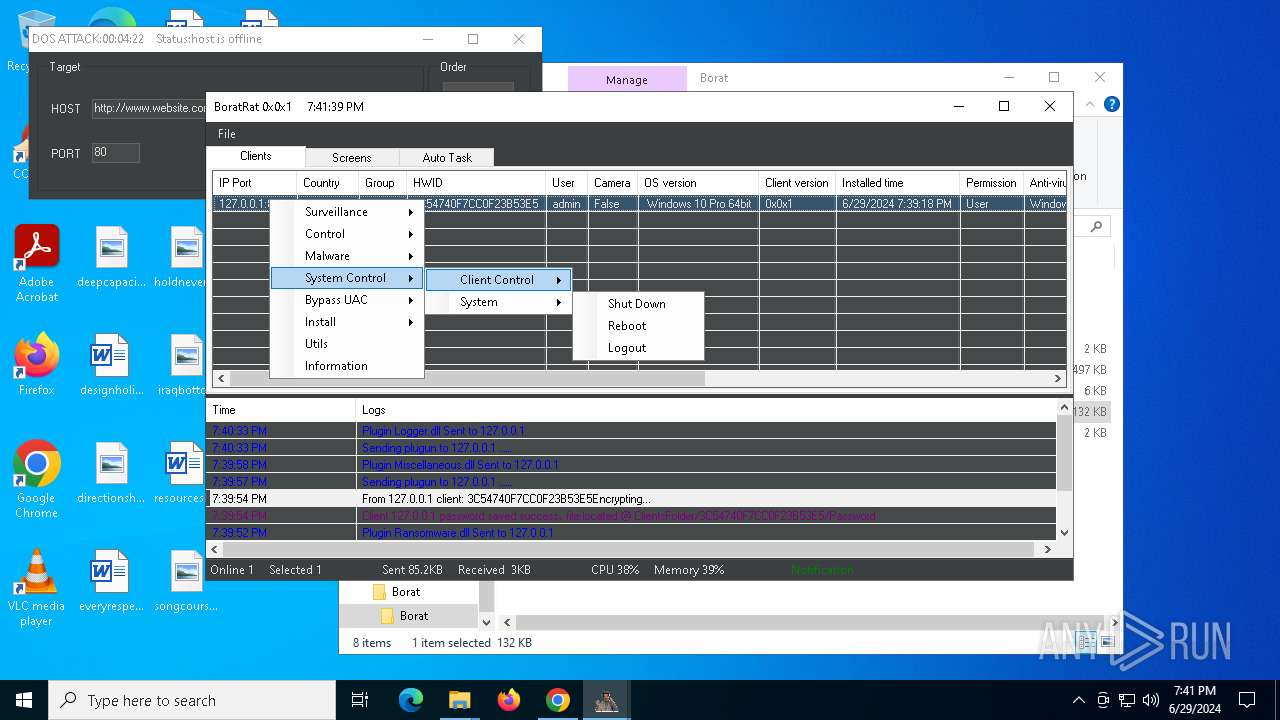
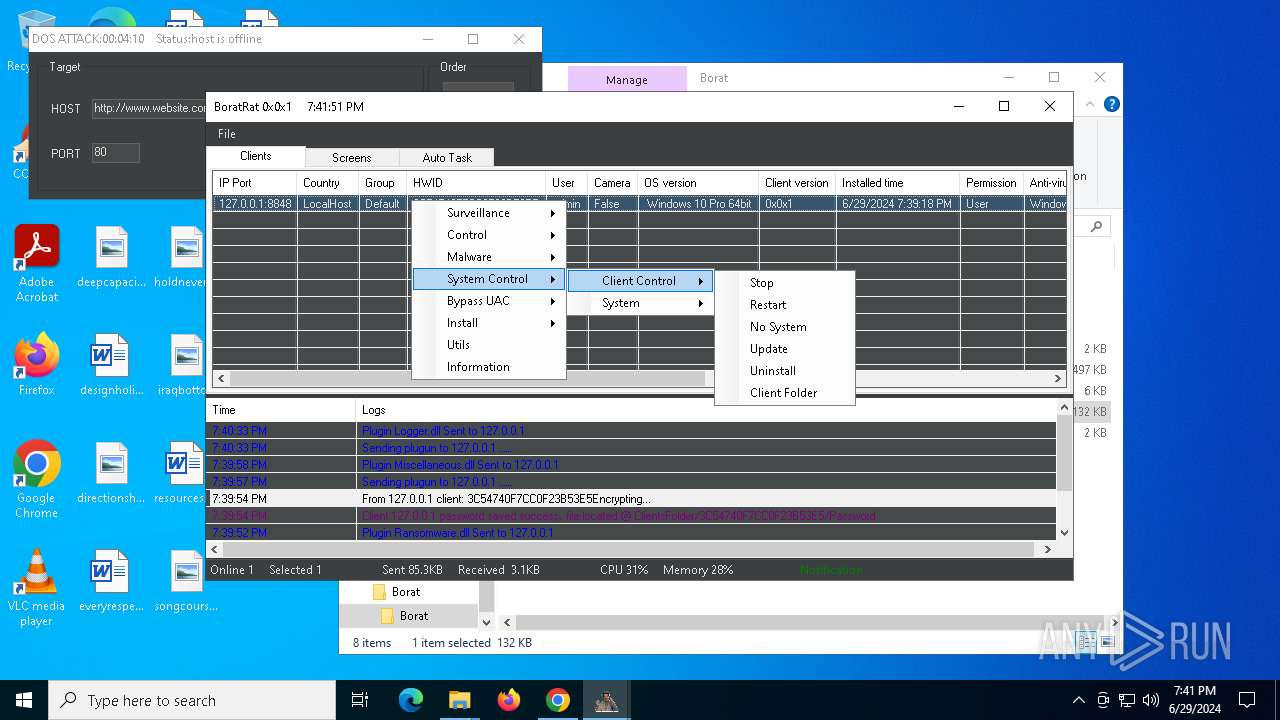
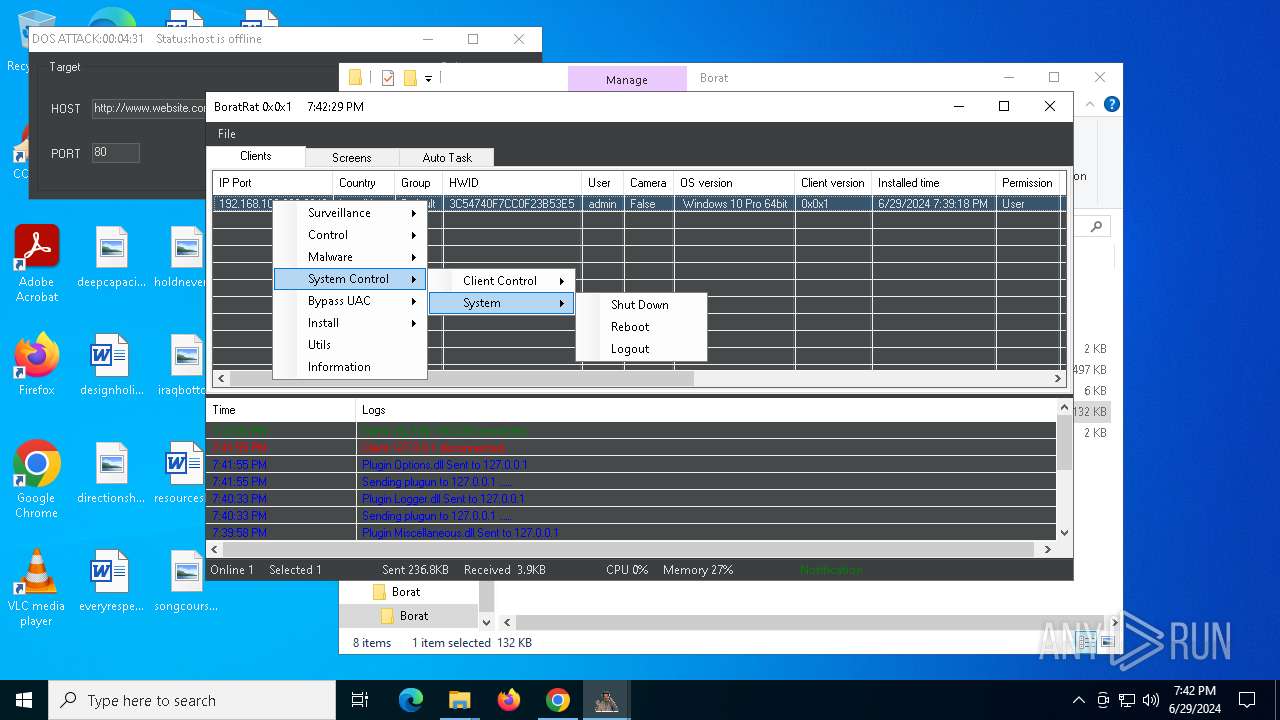
The system shut down or reboot
- cmd.exe (PID: 3396)
Executes application which crashes
- BoratRat.exe (PID: 6448)
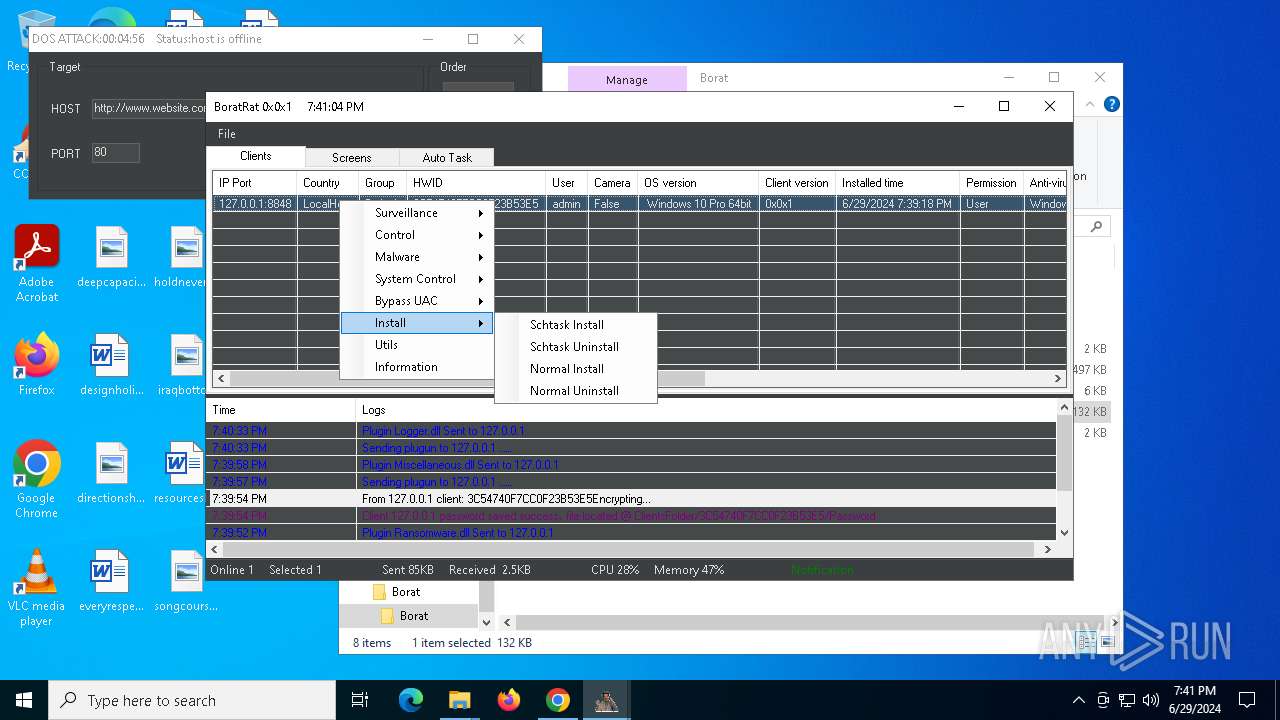
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 6604)
INFO
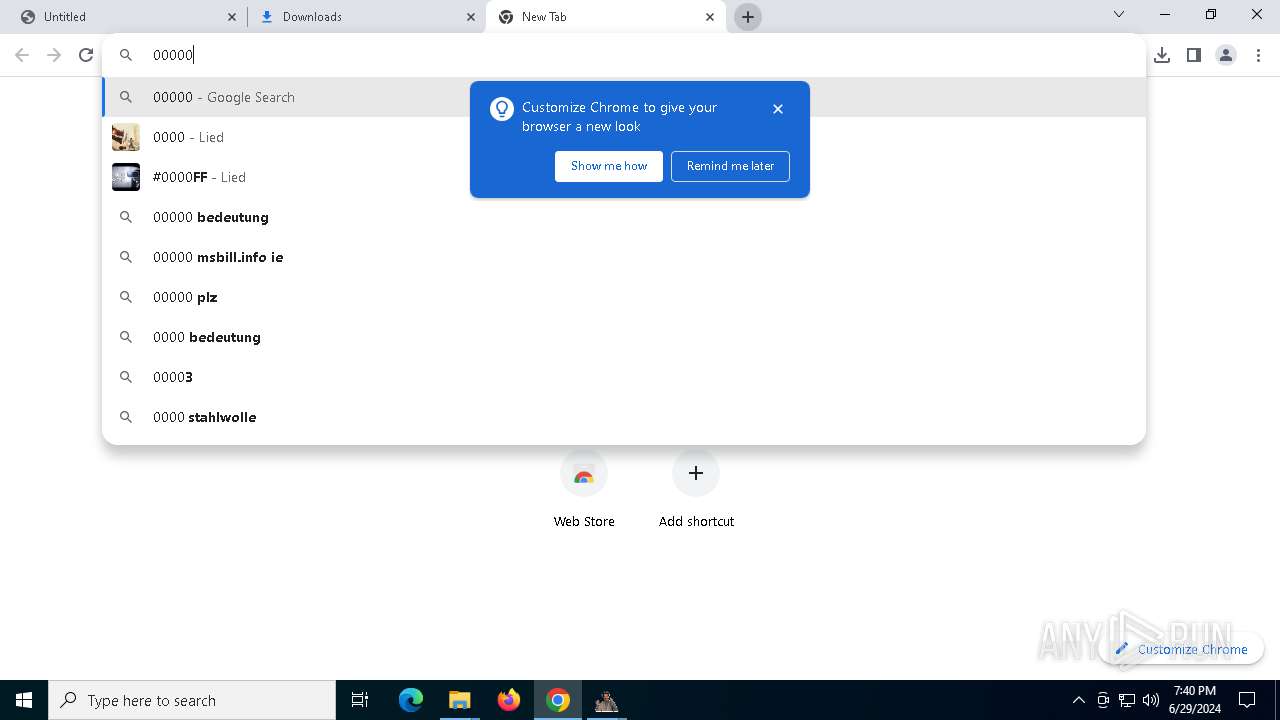
Application launched itself
- chrome.exe (PID: 5392)
Reads Microsoft Office registry keys
- chrome.exe (PID: 5392)
Reads the computer name
- TextInputHost.exe (PID: 3748)
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 6632)
- Client.exe (PID: 4004)
- Client.exe (PID: 2044)
- StartMenuExperienceHost.exe (PID: 6868)
- PLUGScheduler.exe (PID: 6604)
- SearchApp.exe (PID: 5308)
Checks supported languages
- TextInputHost.exe (PID: 3748)
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 6632)
- Client.exe (PID: 4004)
- Client.exe (PID: 2044)
- PLUGScheduler.exe (PID: 6604)
- StartMenuExperienceHost.exe (PID: 6868)
- SearchApp.exe (PID: 5308)
Drops the executable file immediately after the start
- chrome.exe (PID: 5392)
- WinRAR.exe (PID: 6768)
- chrome.exe (PID: 4136)
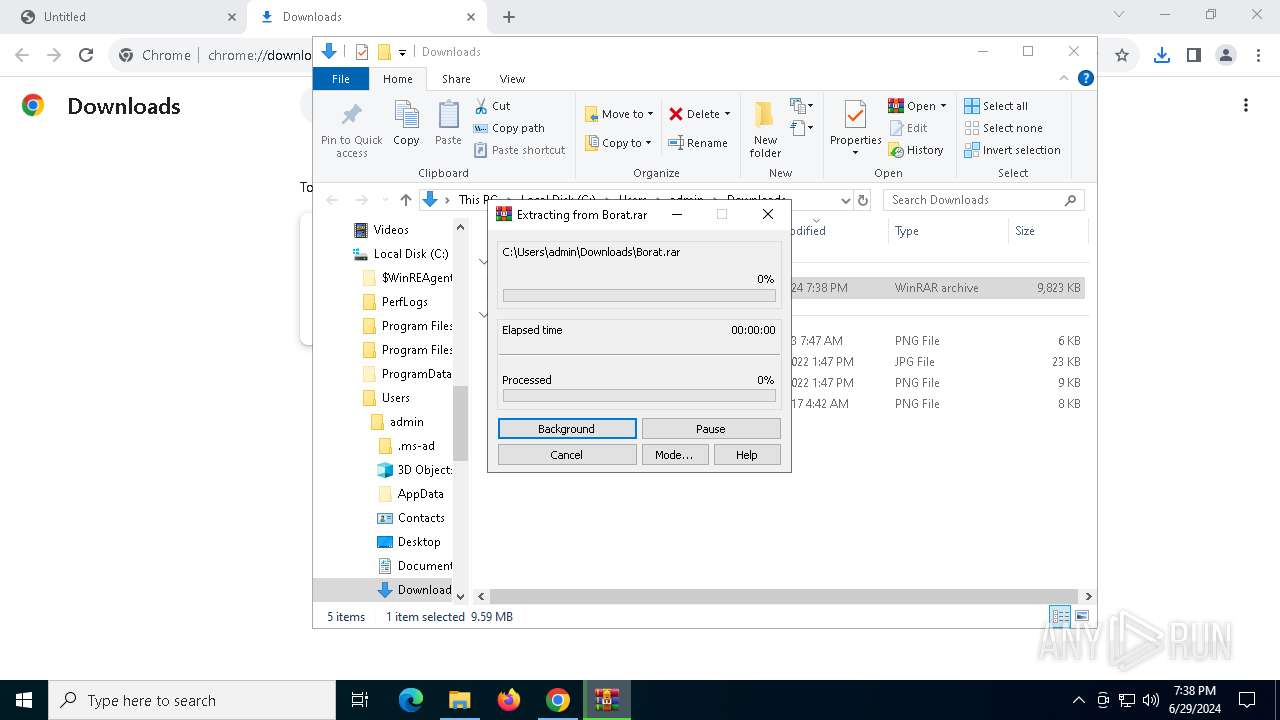
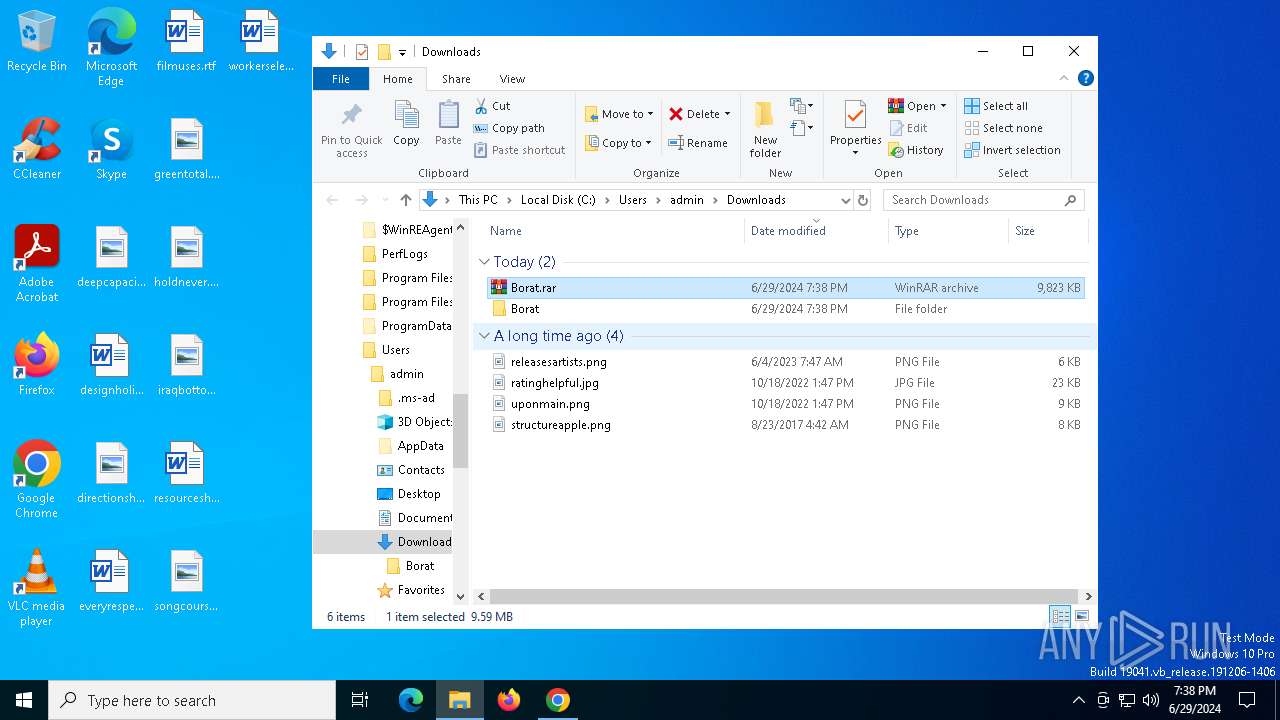
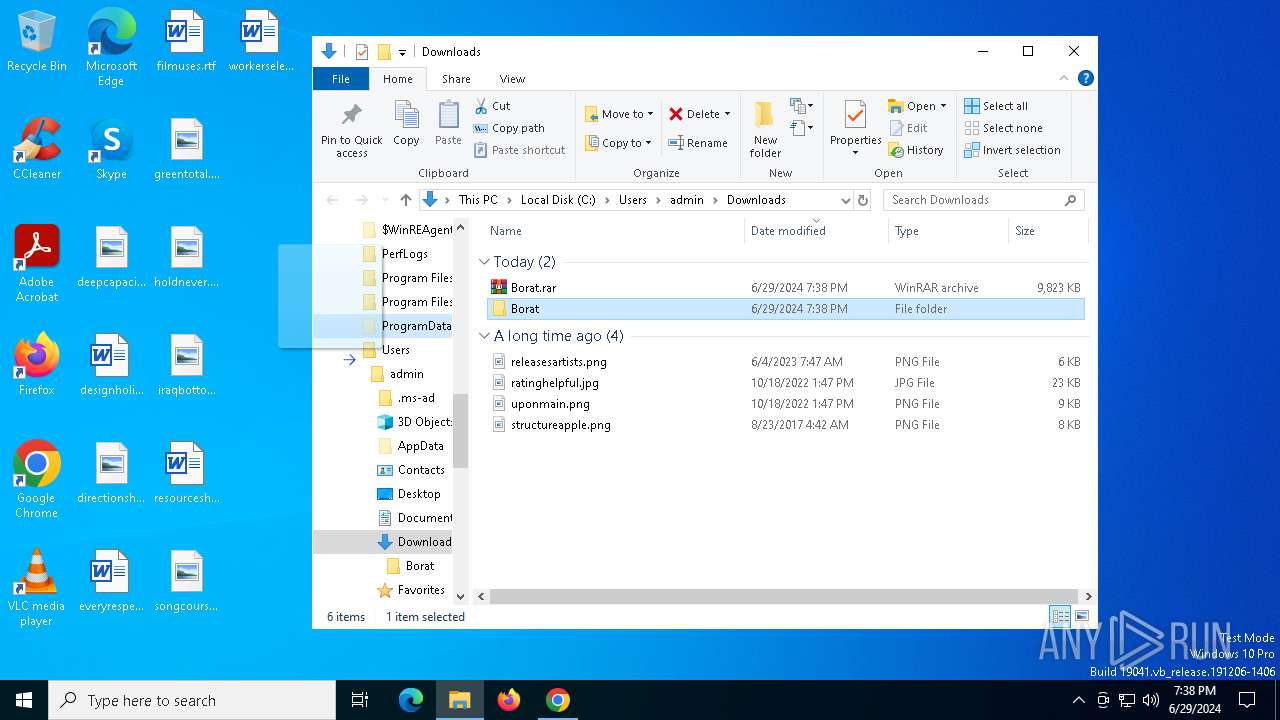
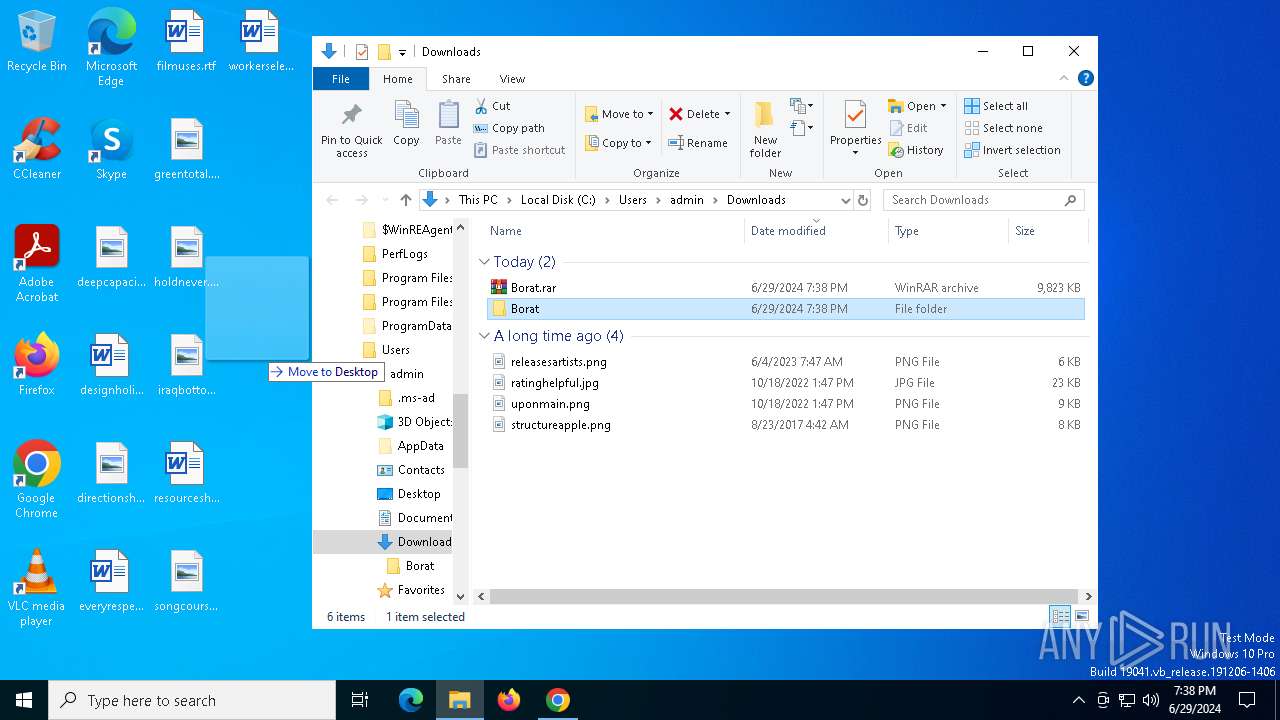
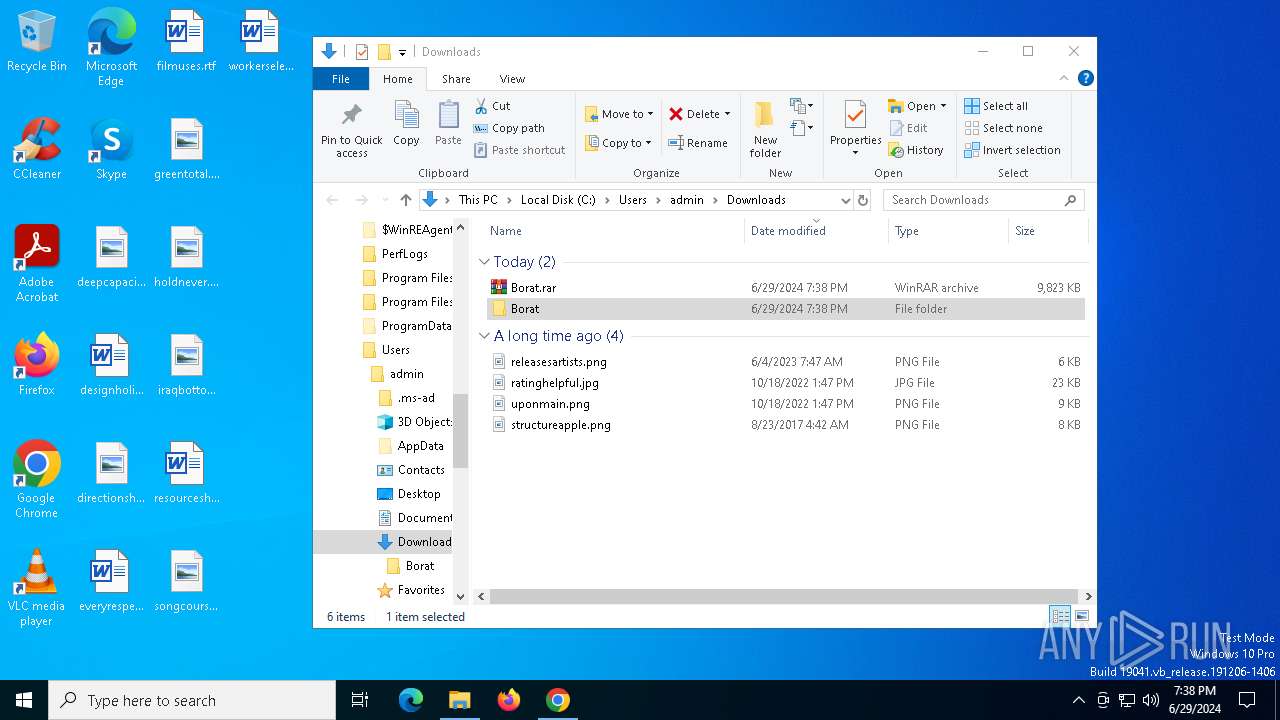
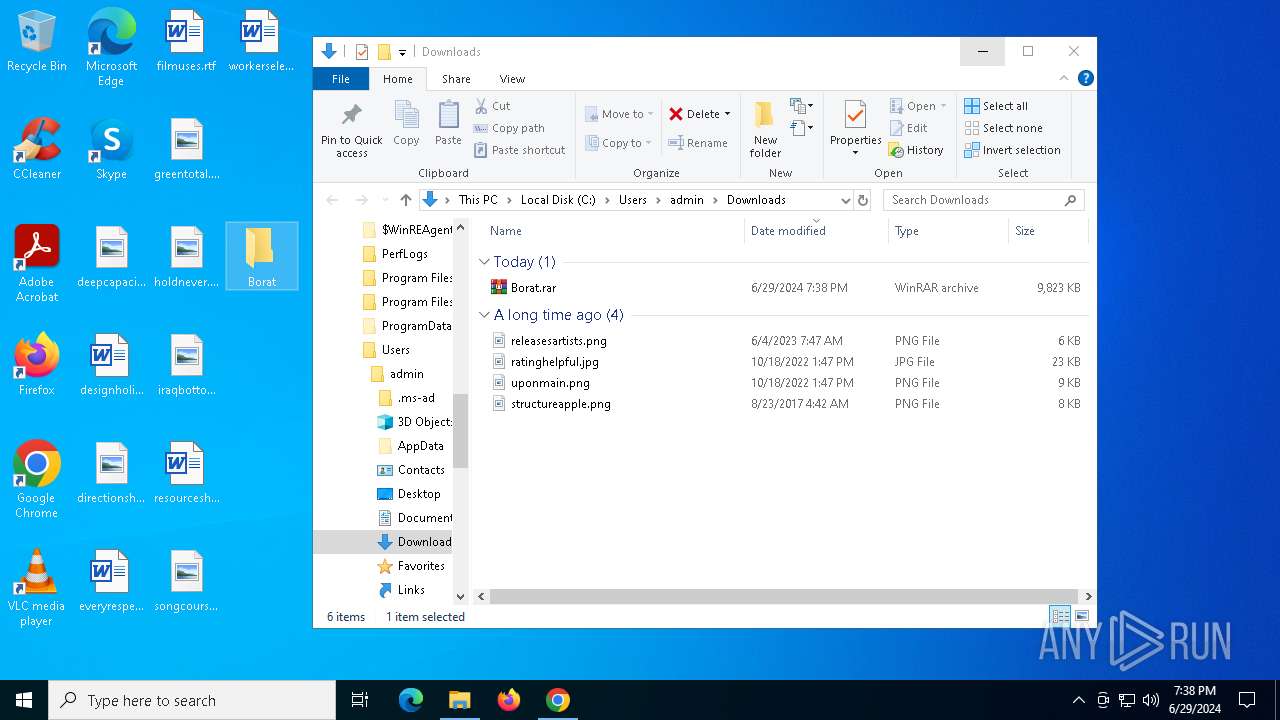
Manual execution by a user
- WinRAR.exe (PID: 6768)
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 6632)
- Client.exe (PID: 2044)
The process uses the downloaded file
- chrome.exe (PID: 5420)
- WinRAR.exe (PID: 6768)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6768)
- chrome.exe (PID: 4136)
Reads the machine GUID from the registry
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 6632)
- Client.exe (PID: 4004)
- Client.exe (PID: 2044)
- SearchApp.exe (PID: 5308)
Create files in a temporary directory
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 6632)
Creates files or folders in the user directory
- BoratRat.exe (PID: 6448)
Reads Environment values
- Client.exe (PID: 6632)
- BoratRat.exe (PID: 6448)
- Client.exe (PID: 4004)
Reads the software policy settings
- Client.exe (PID: 6632)
- Client.exe (PID: 4004)
Disables trace logs
- BoratRat.exe (PID: 6448)
Checks proxy server information
- BoratRat.exe (PID: 6448)
- SearchApp.exe (PID: 5308)
Process checks computer location settings
- Client.exe (PID: 4004)
- StartMenuExperienceHost.exe (PID: 6868)
- SearchApp.exe (PID: 5308)
Creates files in the program directory
- PLUGScheduler.exe (PID: 6604)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 1832)
Process checks Internet Explorer phishing filters
- SearchApp.exe (PID: 5308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
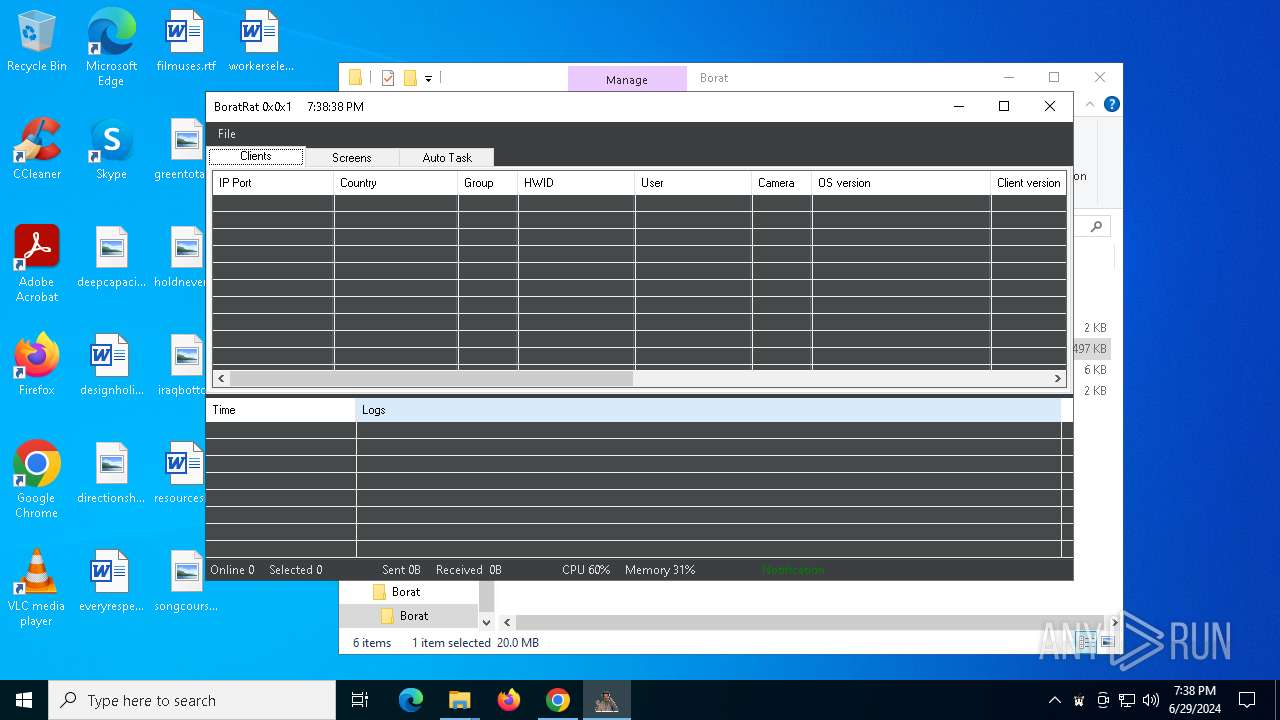
Total processes
208
Monitored processes
42
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4472 --field-trial-handle=1924,i,12694830992097680930,9258616286063255631,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\WerFault.exe -u -p 6448 -s 916 | C:\Windows\System32\WerFault.exe | — | BoratRat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 3221226091 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1596 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1632 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1768 | Shutdown /l /f | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1784 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1832 | C:\WINDOWS\system32\DllHost.exe /Processid:{3EB3C877-1F16-487C-9050-104DBCD66683} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\Desktop\Borat\Borat\Client.exe" | C:\Users\admin\Desktop\Borat\Borat\Client.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.7.0 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=840 --field-trial-handle=1924,i,12694830992097680930,9258616286063255631,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4600 --field-trial-handle=1924,i,12694830992097680930,9258616286063255631,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
53 211
Read events
52 929
Write events
257
Delete events
25
Modification events
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
32
Suspicious files
313
Text files
48
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1ae64a.TMP | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1ae65a.TMP | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5392 | chrome.exe | C:\USERS\ADMIN\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\VARIATIONS | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 5392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1ae64a.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
572
DNS requests
39
Threats
460
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3668 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ibecpvubwwy3i7q2f2ejvvcecu_20240622.646249836.14/obedbbhbpmojnkanicioggnmelmoomoc_20240622.646249836.14_all_ENUS500000_atnt6gk4yophdbqleiyvyvzyla.crx3 | unknown | — | — | unknown |
2872 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
2872 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
3872 | svchost.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1968 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
3872 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
3668 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | unknown |
1784 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6244 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
5392 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
6244 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
1544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6244 | chrome.exe | 185.199.111.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
1544 | svchost.exe | 192.229.221.95:80 | — | EDGECAST | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
accounts.google.com |
| shared |
login.live.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
go.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
r.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |
6632 | Client.exe | A Network Trojan was detected | ET MALWARE Possible MEME#4CHAN Exfil Activity |