| File name: | Launcher.exe |
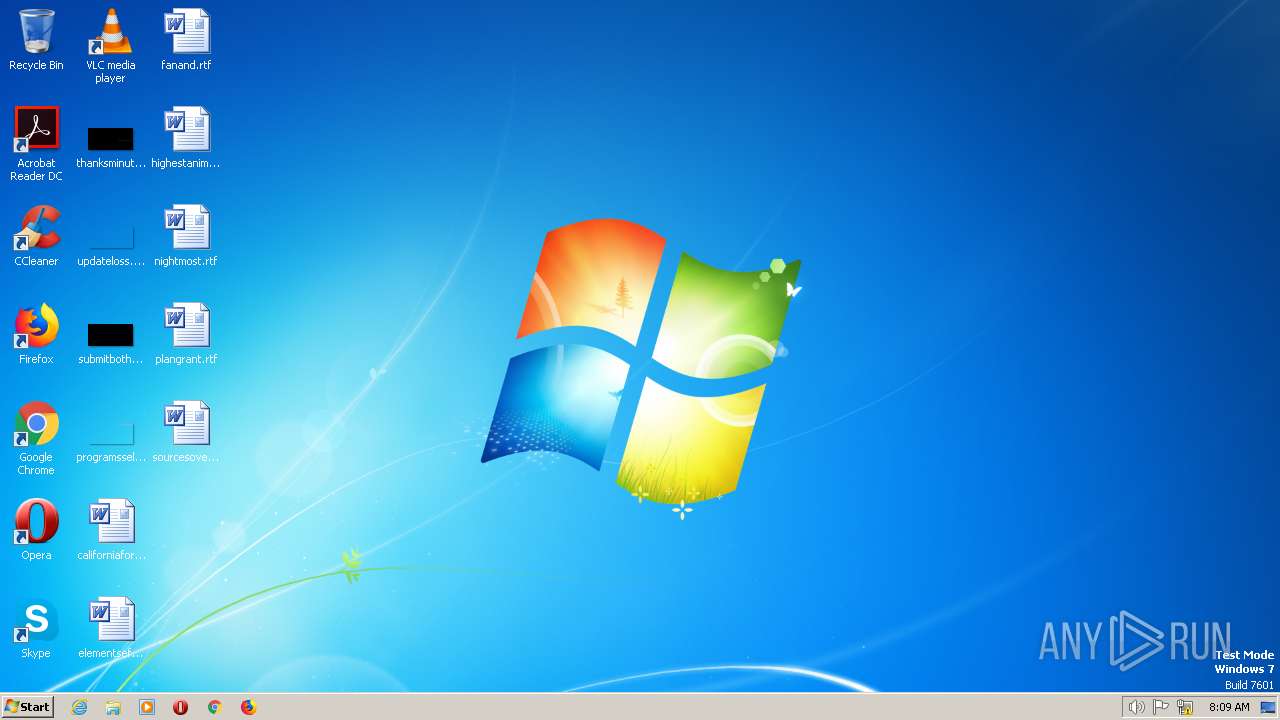
| Full analysis: | https://app.any.run/tasks/f9c1c0f9-2b30-4147-80cb-b4a1828b537e |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | July 03, 2023, 08:09:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | A78DCBD9BCF3738D09D091079A322E9C |
| SHA1: | D6FA5EC870EEBAFEE50405BB949FB9961F3D811D |
| SHA256: | FF59399142EEBC8E4829B279C9521FC671D3CCFF737F9B236D18C50F349599B0 |
| SSDEEP: | 6144:FjTdT8MLxjMo2ap5JnVdbFFX3nLXkG1xS+TPxb:Fl8MNfpLnVdbFFX3nLXkGLS+TPh |
MALICIOUS
REDLINE detected by memory dumps
- Launcher.exe (PID: 2432)
SUSPICIOUS
No suspicious indicators.INFO
The process checks LSA protection
- Launcher.exe (PID: 2432)
Reads the machine GUID from the registry
- Launcher.exe (PID: 2432)
Reads the computer name
- Launcher.exe (PID: 2432)
Checks supported languages
- Launcher.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2432) Launcher.exe
C2 (1)185.157.120.4:17355
Botnet940390866
Err_msg
Auth_valued3a4cefe2fe72d08728081e35dabf342
US (139)
Search
Reflection
Ammo
Function
Info
Roaming
UNKNOWN
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
ToString
os_crypt
encrypted_key
Network\
Inner
Unknown
:
Read
Kill
Microsoft
GetDirectories
MSObject12
EnumerateDirectories
String.Replace
String.Remove
net.tcp://
/
localhost
d3a4cefe2fe72d08728081e35dabf342
Authorization
ns1
GSMOQi8LN2U5EEcbLBgVAic3DBk8LjpYPTJcTw==
940390866
Twiscar
MSValue3
EnumerateFiles
ExpandEnvironmentVariables
MSValue2
MSValue1
FullName
Replace
Directory
wa
l
et
d
a
t
.
*wallet*
_
T
e
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
Environment
\Discord\Local Storage\leveldb
*.loSystem.Collections.Genericg
System.Collections.Generic
1
String
MyG
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
EngSubs
ElevatedDiagnostics\Reports
-
AddRange
%
(
UNIQUE
"
FileStream.IO
string.Empty
uint
UnmanagedType
hKey
pszProperty
Encoding
bMasterKey
{0}
|
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
Name
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
System.Text.RegularExpressions
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
_[
TRiD
| .exe | | | Clipper DOS Executable (33.5) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33.2) |
| .exe | | | DOS Executable Generic (33.2) |
EXIF
EXE
| ProductVersion: | 945 |
|---|---|
| ProductName: | mteHpYSWUj |
| OriginalFileName: | 2ryoToyK.exe |
| LegalTrademarks: | © American Colla USA Trademarks |
| LegalCopyright: | © American Colla USA All rights reserved. |
| InternalName: | 2CWm9P89OkGr |
| FileVersion: | 945 |
| FileDescription: | American Colla USA Product |
| CompanyName: | American Colla USA |
| Comments: | This is a legitimate application. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 945.0.0.0 |
| FileVersionNumber: | 945.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x5fd0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | - |
| CodeSize: | - |
| LinkerVersion: | - |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| TimeStamp: | 0000:00:00 00:00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
| Comments: | This is a legitimate application. |
| CompanyName: | American Colla USA |
| FileDescription: | American Colla USA Product |
| FileVersion: | 945 |
| InternalName: | 2CWm9P89OkGr |
| LegalCopyright: | © American Colla USA All rights reserved. |
| LegalTrademarks: | © American Colla USA Trademarks |
| OriginalFilename: | 2ryoToyK.exe |
| ProductName: | mteHpYSWUj |
| ProductVersion: | 945 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000064 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000EE0F | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.76337 |
.rdata | 0x00010000 | 0x0000316A | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.91077 |
.data | 0x00014000 | 0x0002189C | 0x00020E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.76112 |
.rsrc | 0x00036000 | 0x00000430 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.48561 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40863 | 972 | UNKNOWN | English - United States | RT_VERSION |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
31
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2432 | "C:\Users\admin\AppData\Local\Temp\Launcher.exe" | C:\Users\admin\AppData\Local\Temp\Launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
RedLine(PID) Process(2432) Launcher.exe C2 (1)185.157.120.4:17355 Botnet940390866 Err_msg Auth_valued3a4cefe2fe72d08728081e35dabf342 US (139) Search Reflection Ammo Function Info Roaming UNKNOWN cFileStreamredFileStreamit_cFileStreamardFileStreams FileStream \ ToString os_crypt encrypted_key Network\ Inner Unknown : Read Kill Microsoft GetDirectories MSObject12 EnumerateDirectories String.Replace String.Remove net.tcp:// / localhost d3a4cefe2fe72d08728081e35dabf342 Authorization ns1 GSMOQi8LN2U5EEcbLBgVAic3DBk8LjpYPTJcTw== 940390866 Twiscar MSValue3 EnumerateFiles ExpandEnvironmentVariables MSValue2 MSValue1 FullName Replace Directory wa l et d a t . *wallet* _ T e gr am ex \TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata Environment \Discord\Local Storage\leveldb *.loSystem.Collections.Genericg System.Collections.Generic 1 String MyG string.Replace %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl serviceInterface.Extension ProldCharotonVoldCharPN oldChar nSystem.CollectionspvoSystem.Collections* System.Collections EngSubs ElevatedDiagnostics\Reports - AddRange % ( UNIQUE " FileStream.IO string.Empty uint UnmanagedType hKey pszProperty Encoding bMasterKey {0} | https://api.ip.sb/ip 80 81 0.0.0.0 SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor System.Windows.Forms roSystem.Linqot\CISystem.LinqMV2 System.Linq SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller AdapterRAM Name SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente System.Management SerialNumber SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId=' System.Text.RegularExpressions ' FileSystem SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId=' System. ExecutablePath [ ] Concat0 MConcatb oConcatr Concat0 Concat SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem Memory {0}{1}{2} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion _[ | |||||||||||||||
Total events
157
Read events
157
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report