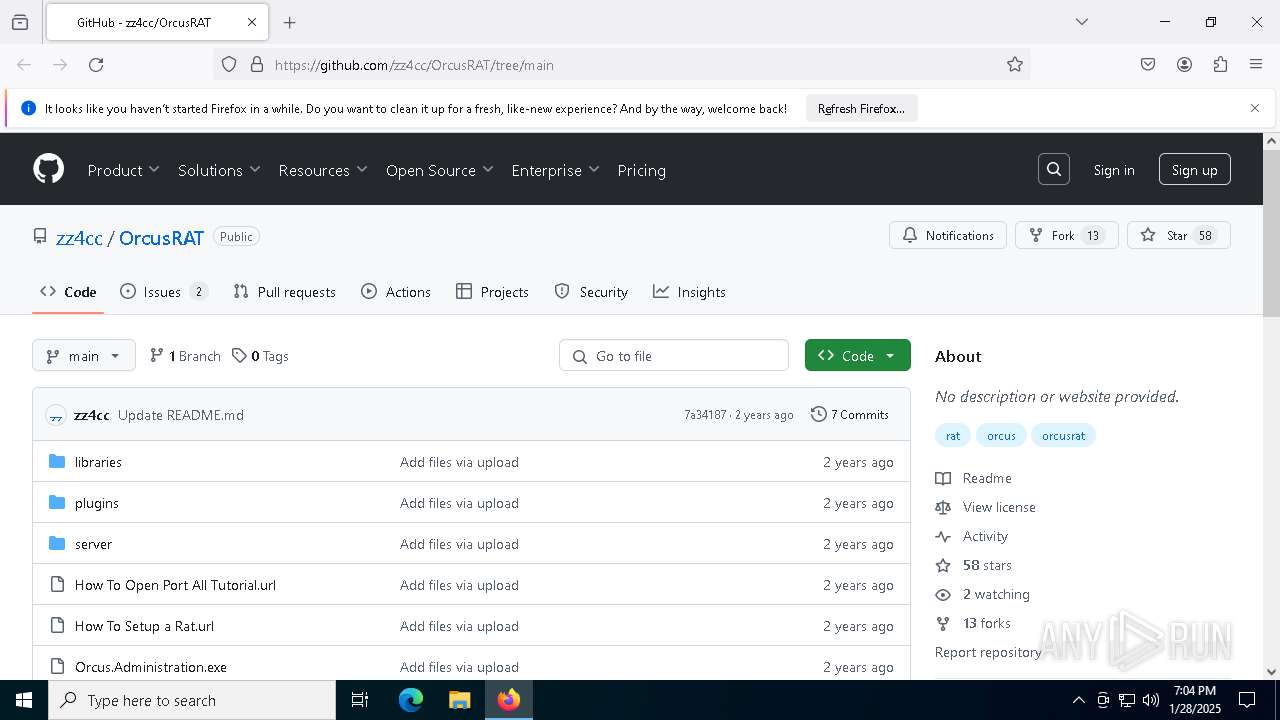
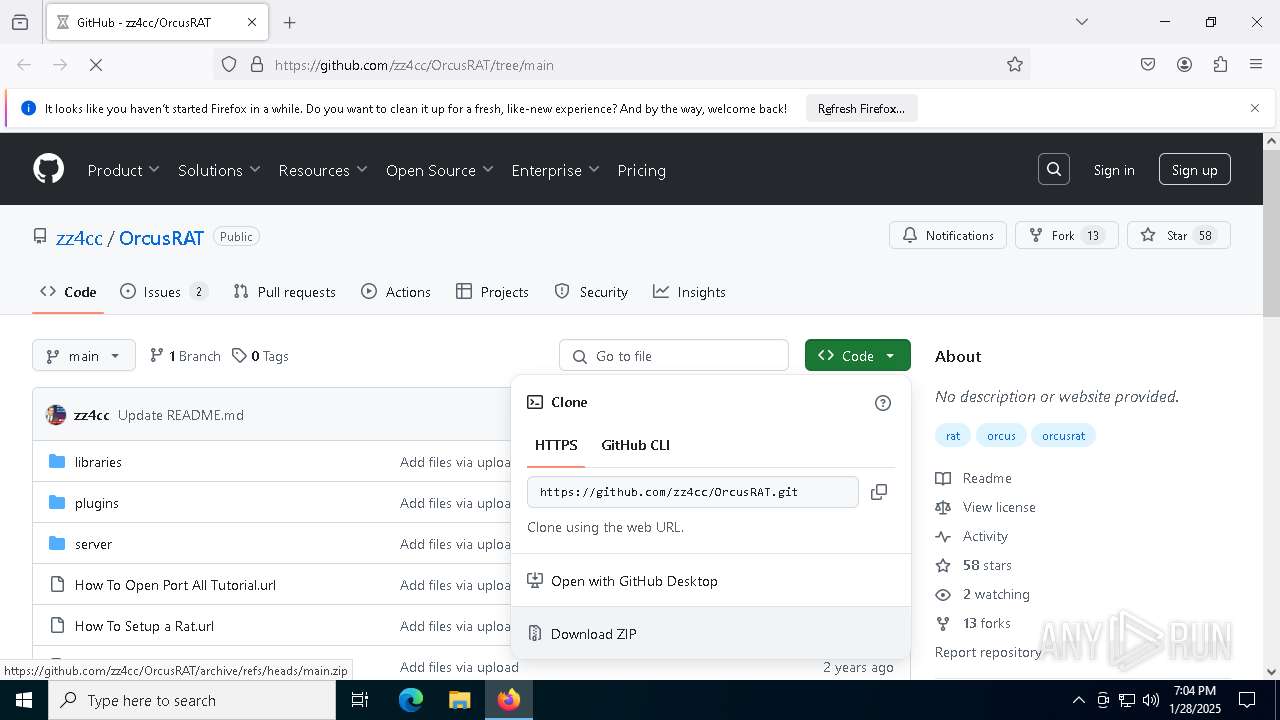
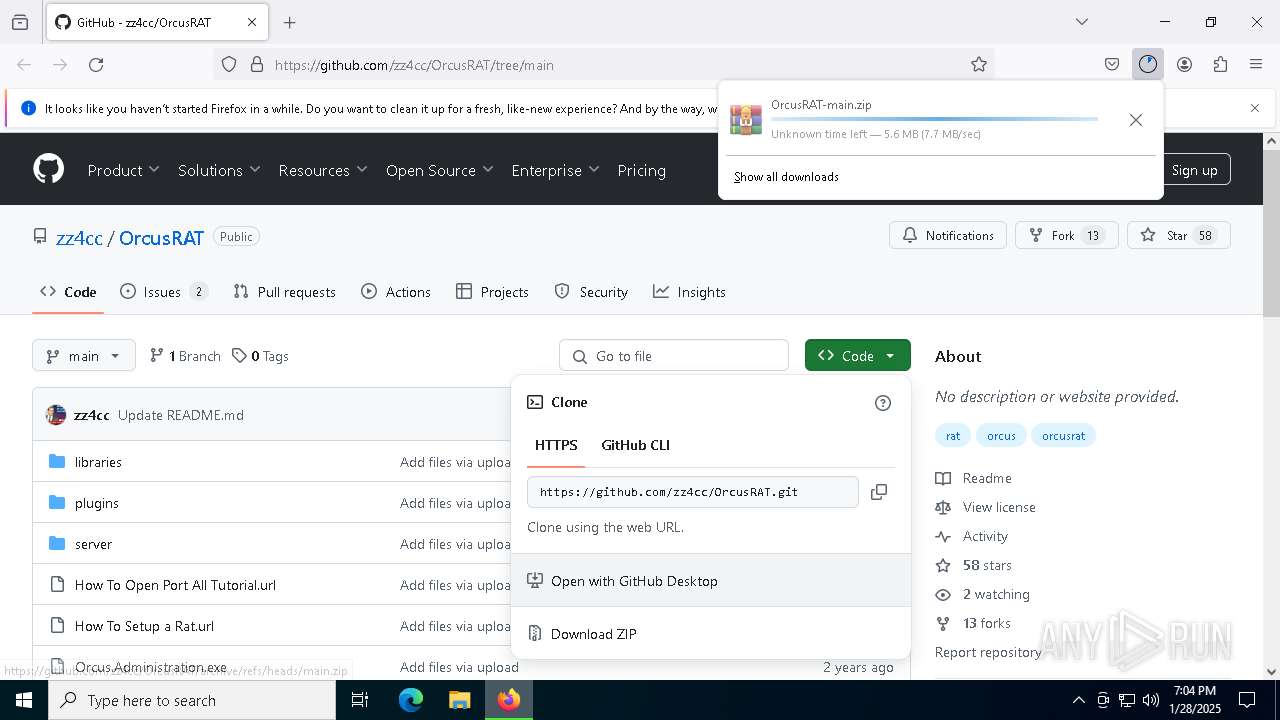
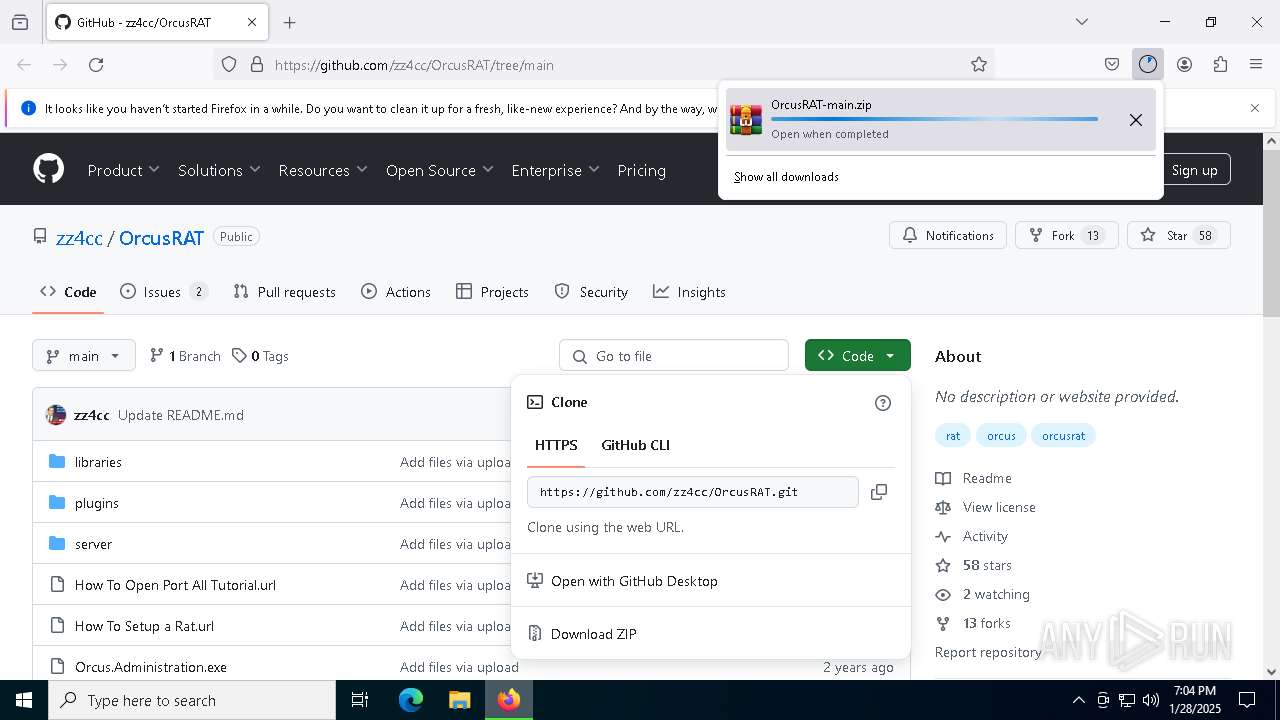
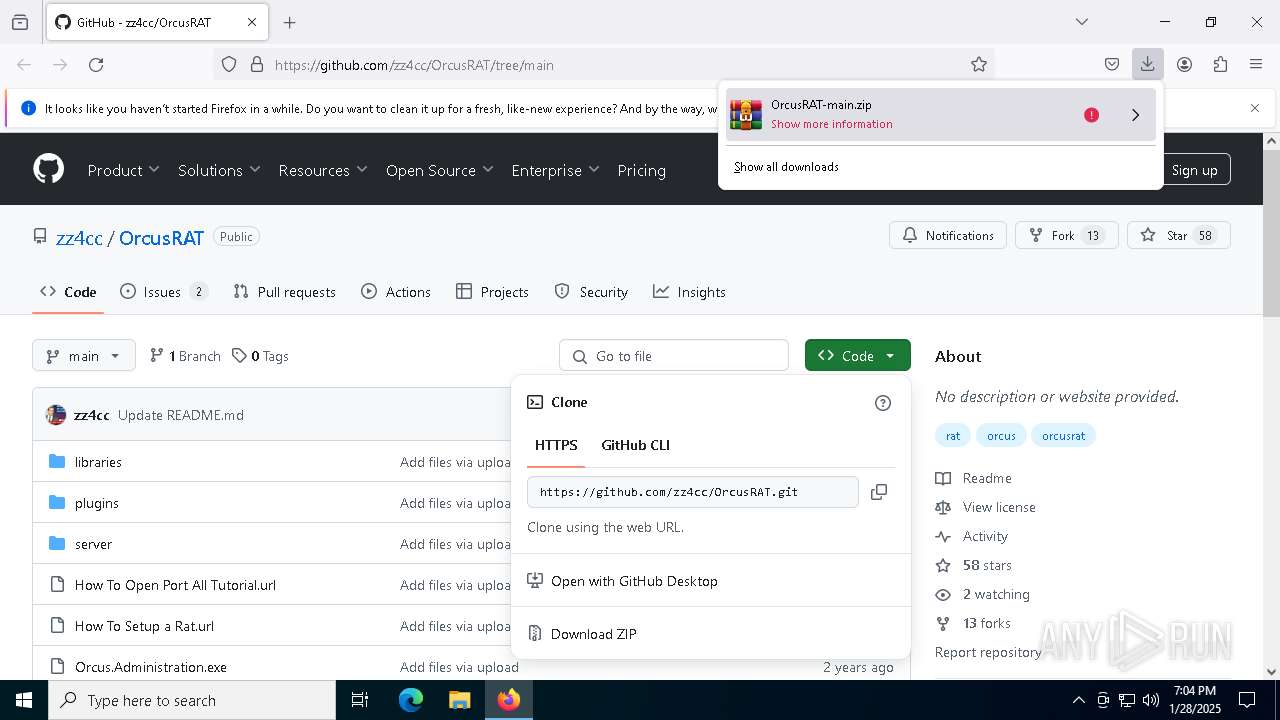
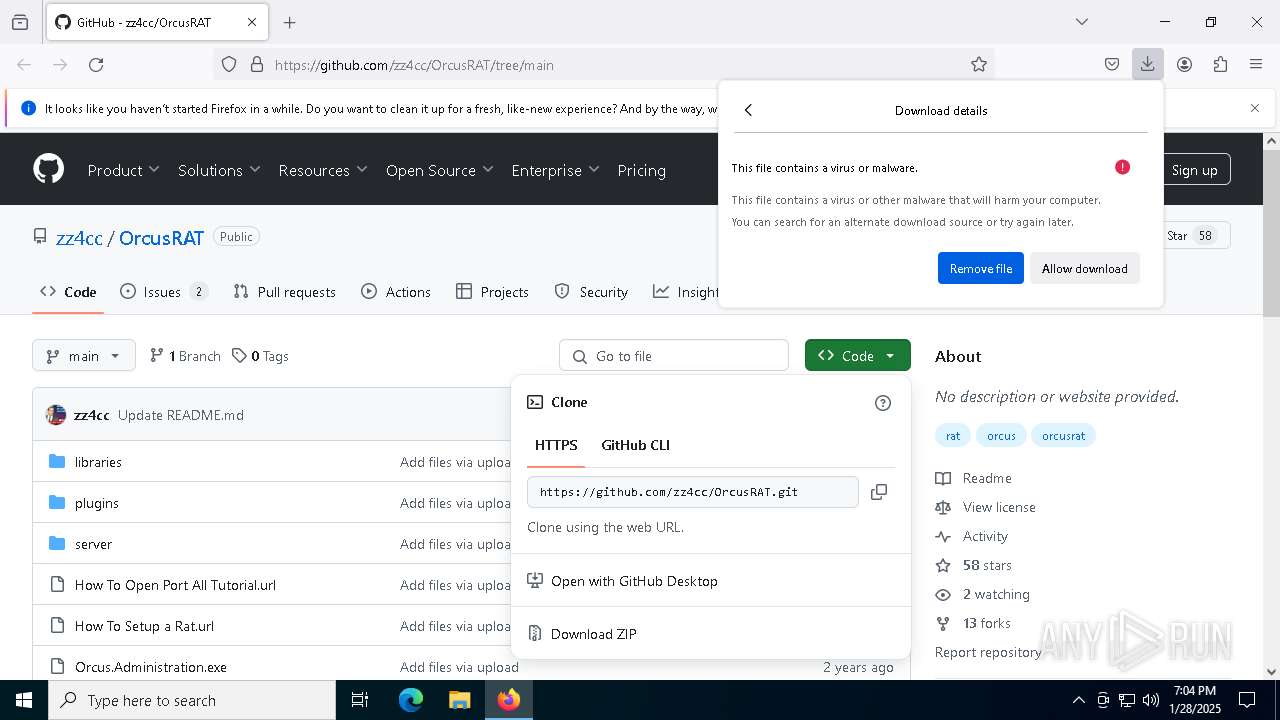
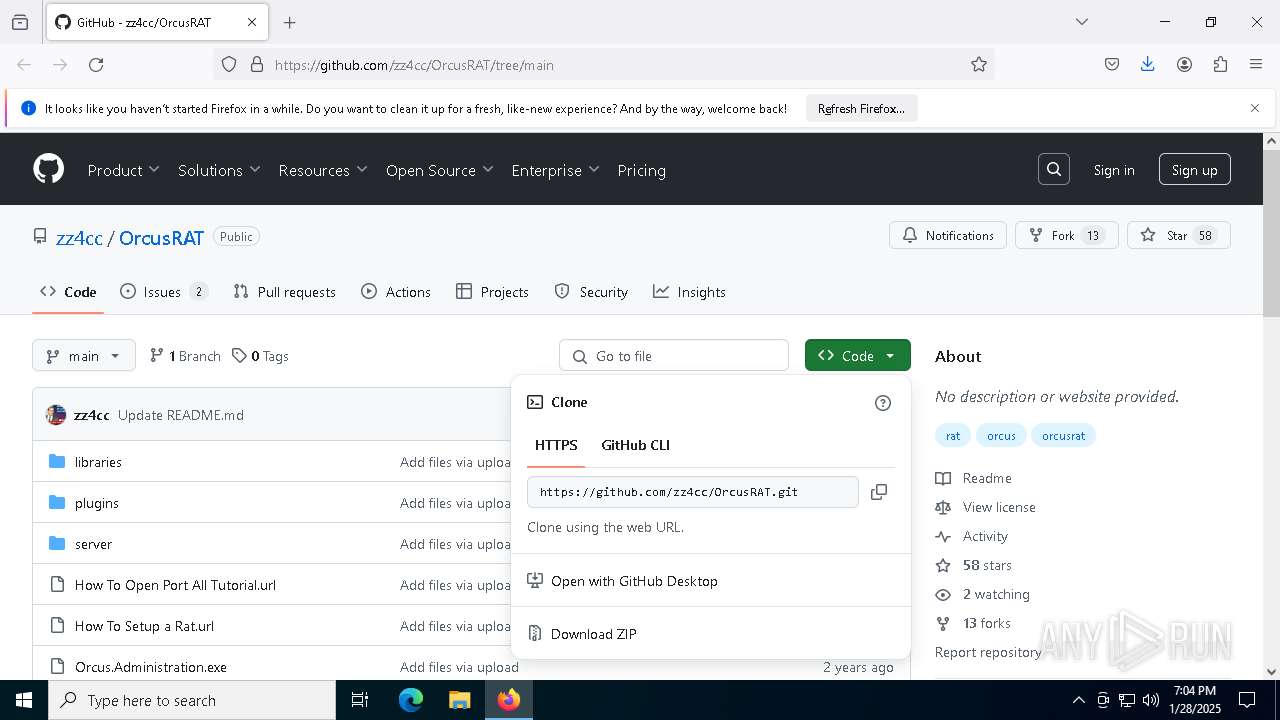
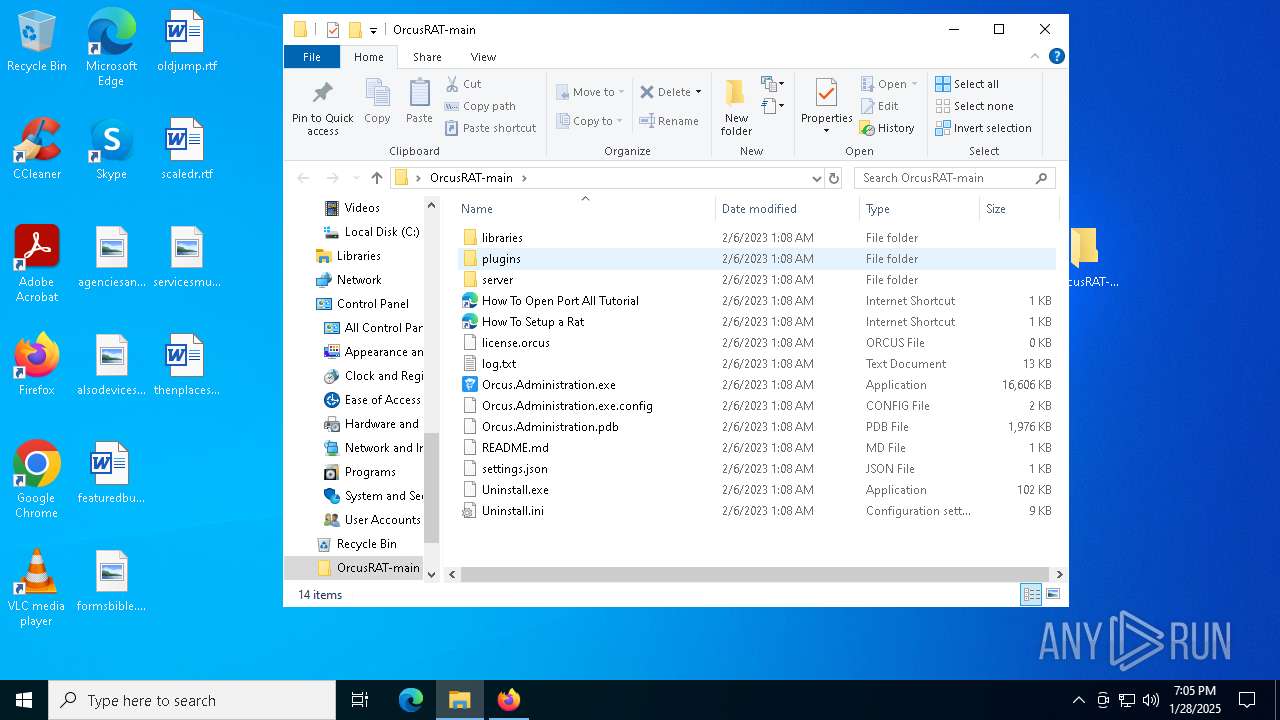
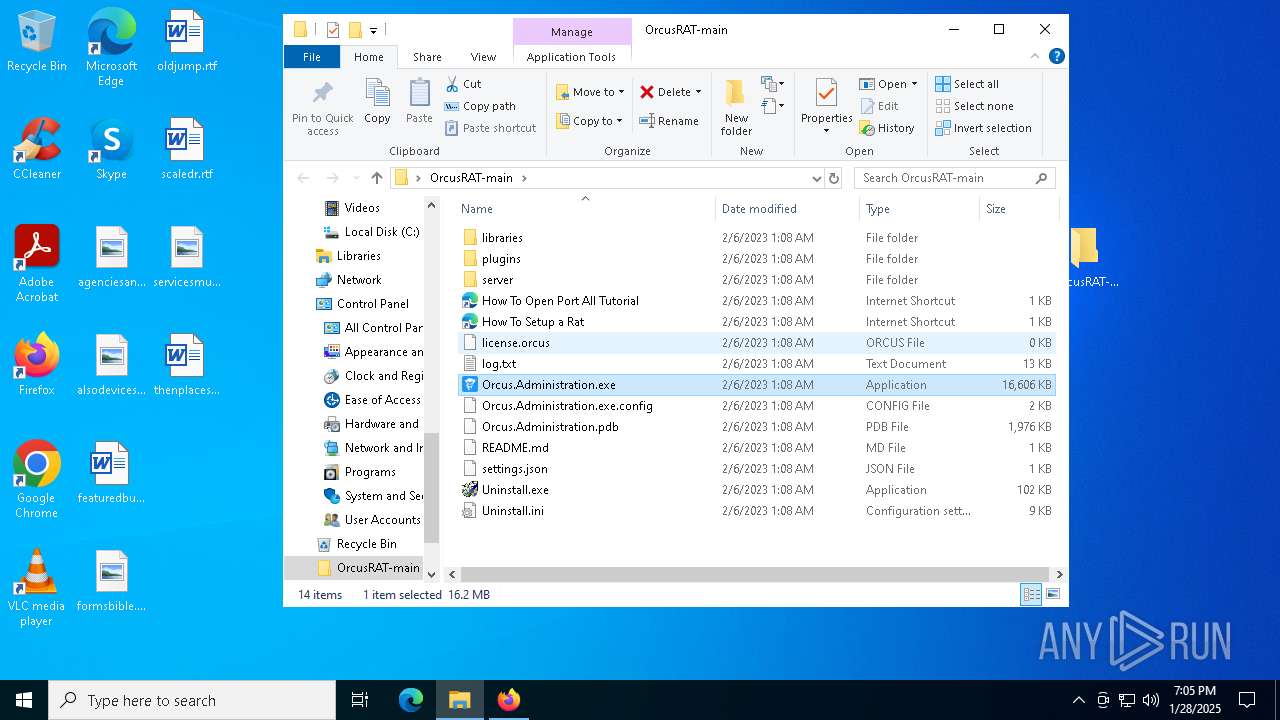
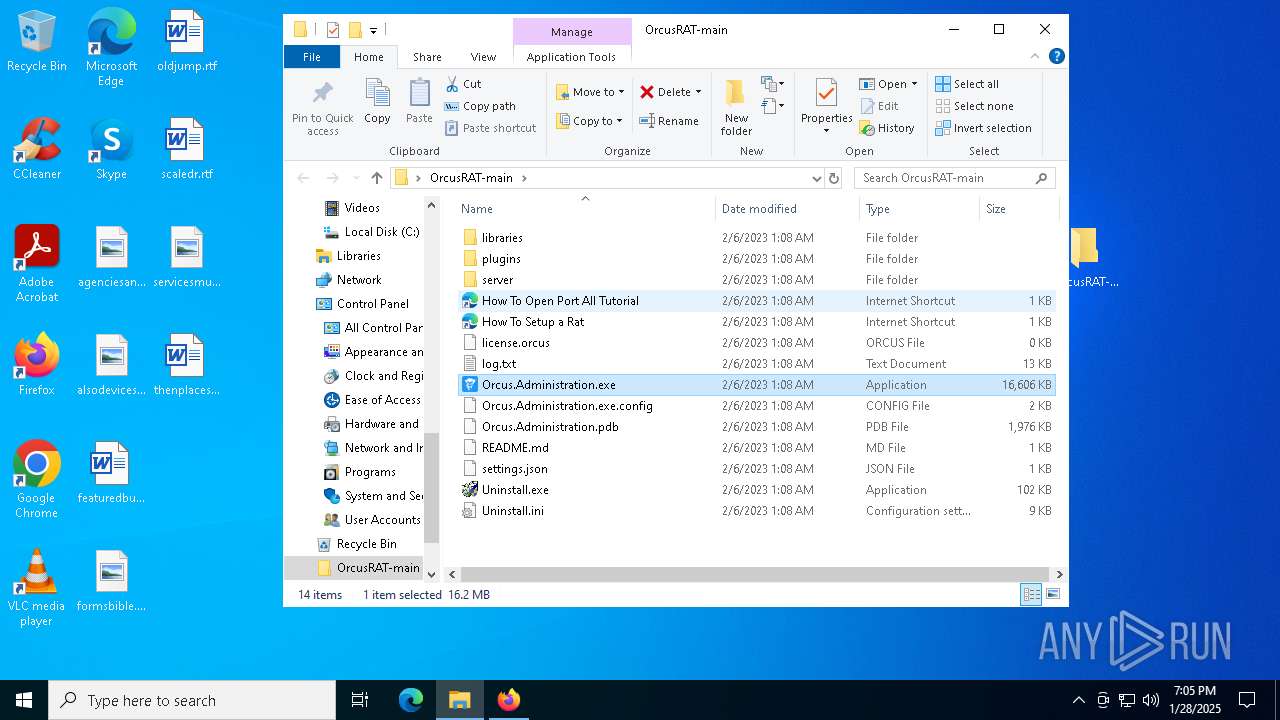
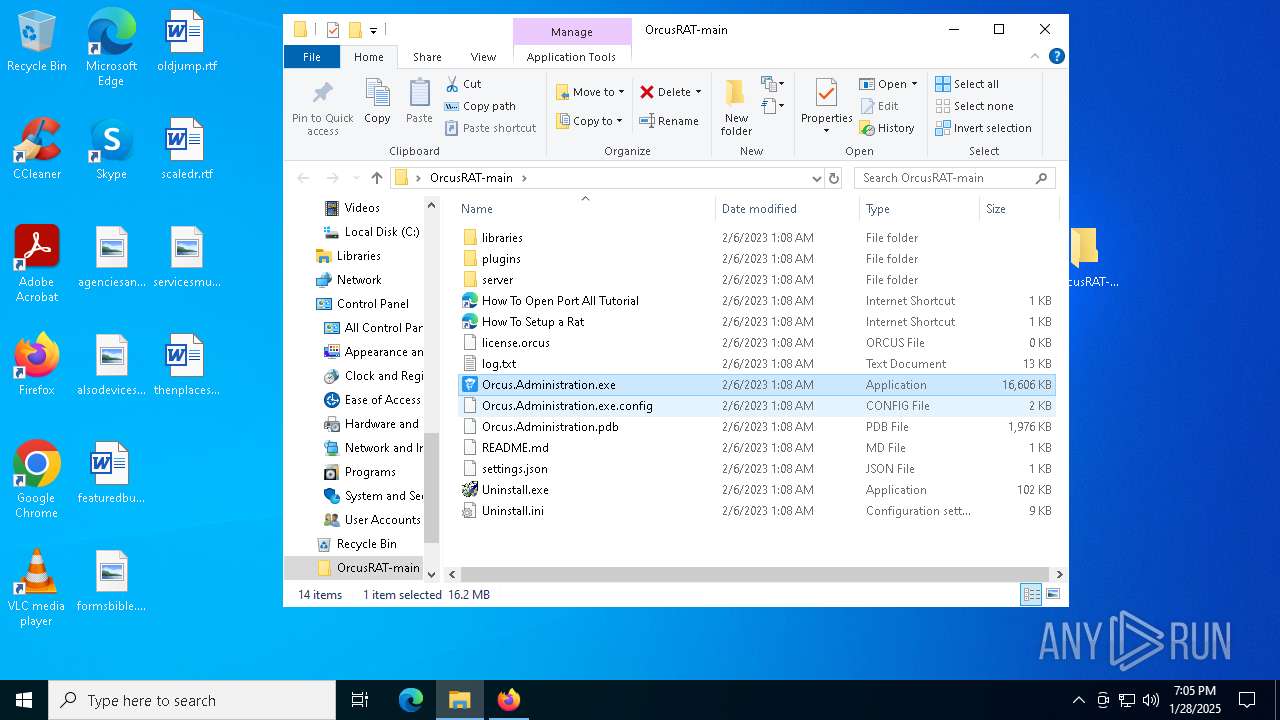
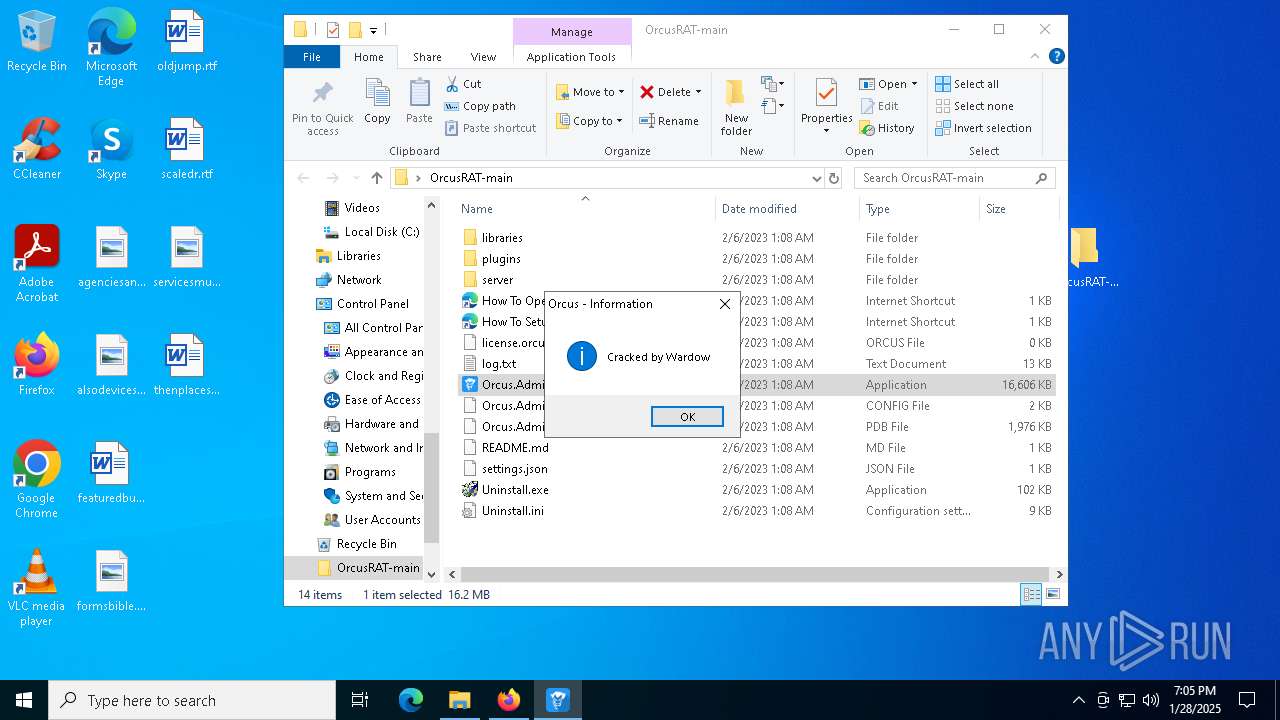
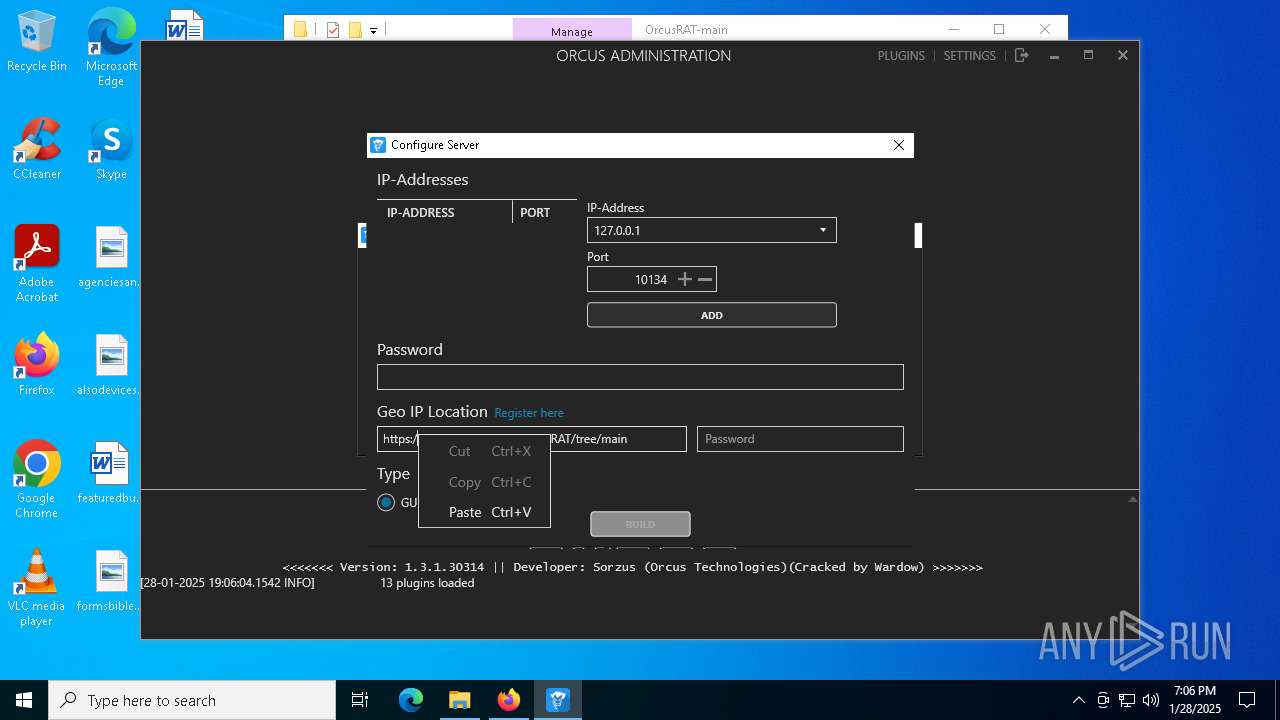
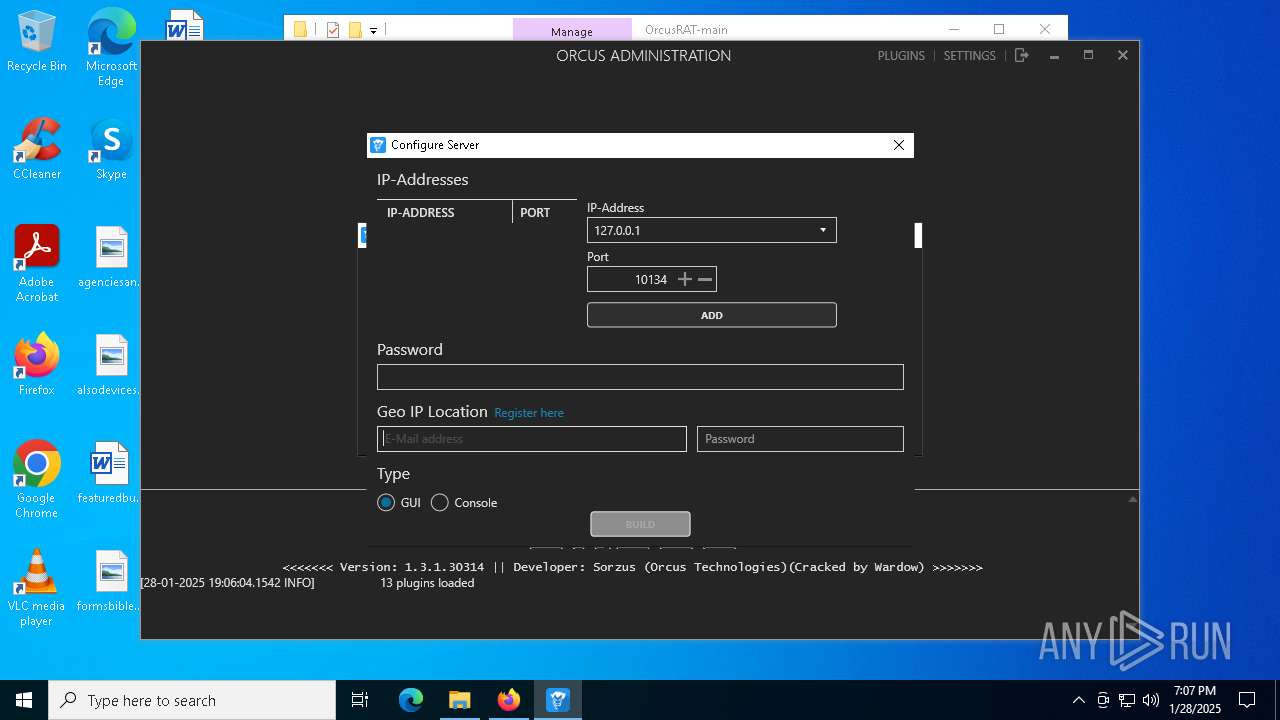
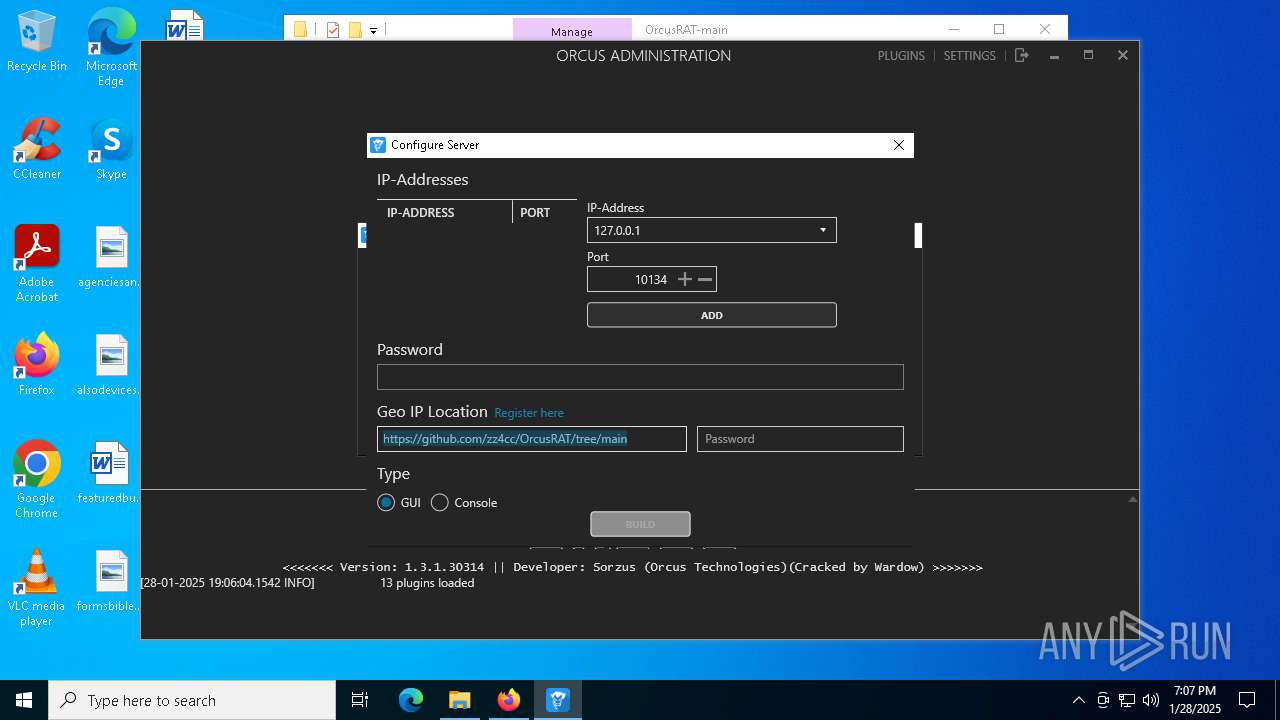
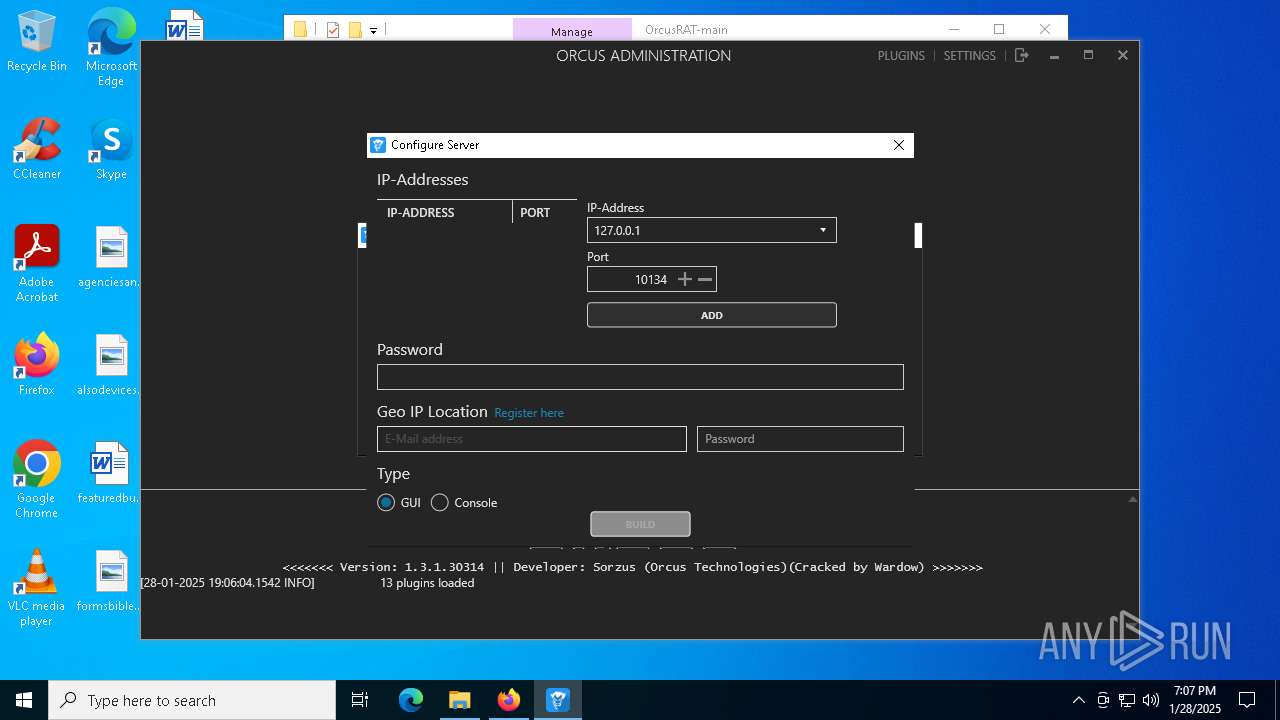
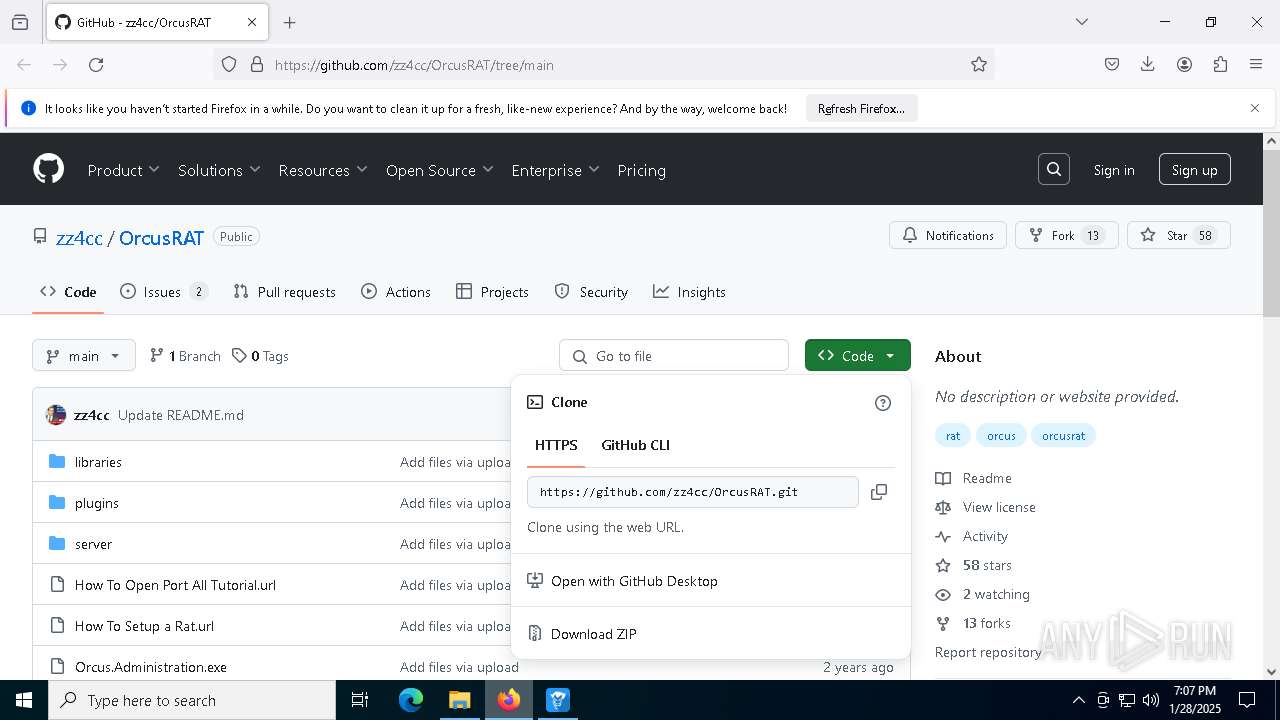
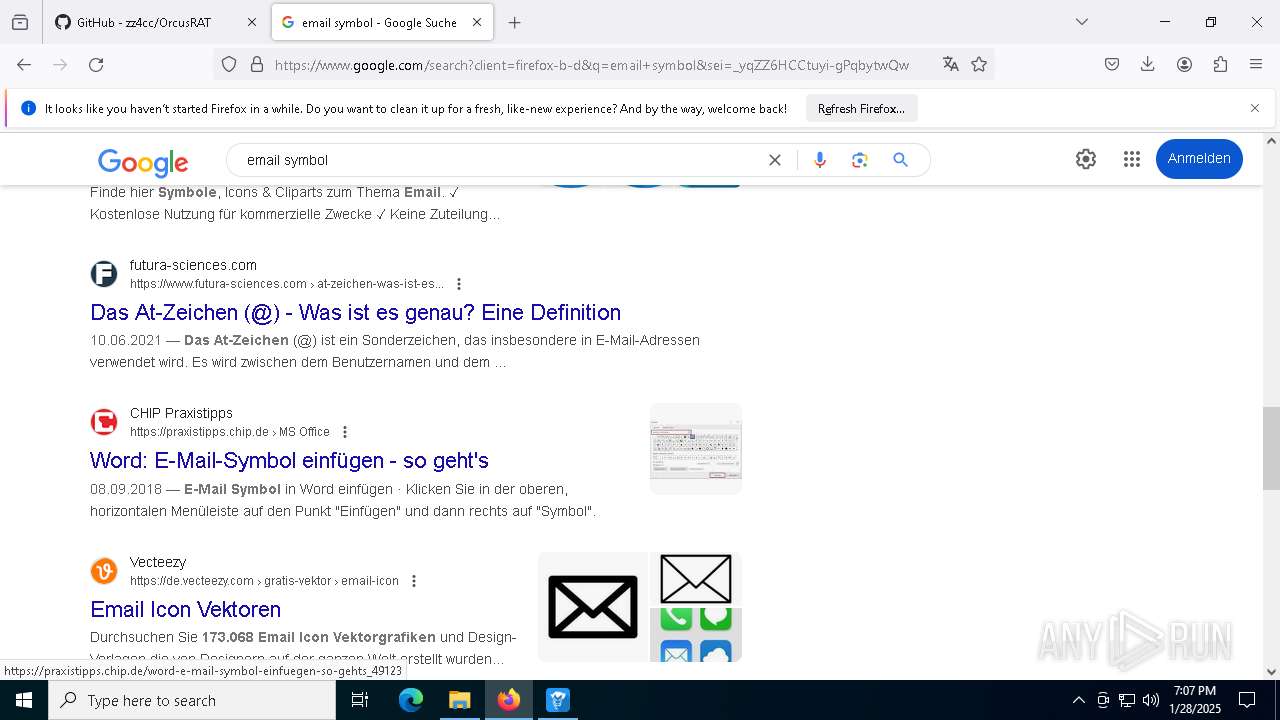
| URL: | https://github.com/zz4cc/OrcusRAT/tree/main |
| Full analysis: | https://app.any.run/tasks/4a563d32-3198-463a-9601-e1ed601016fe |
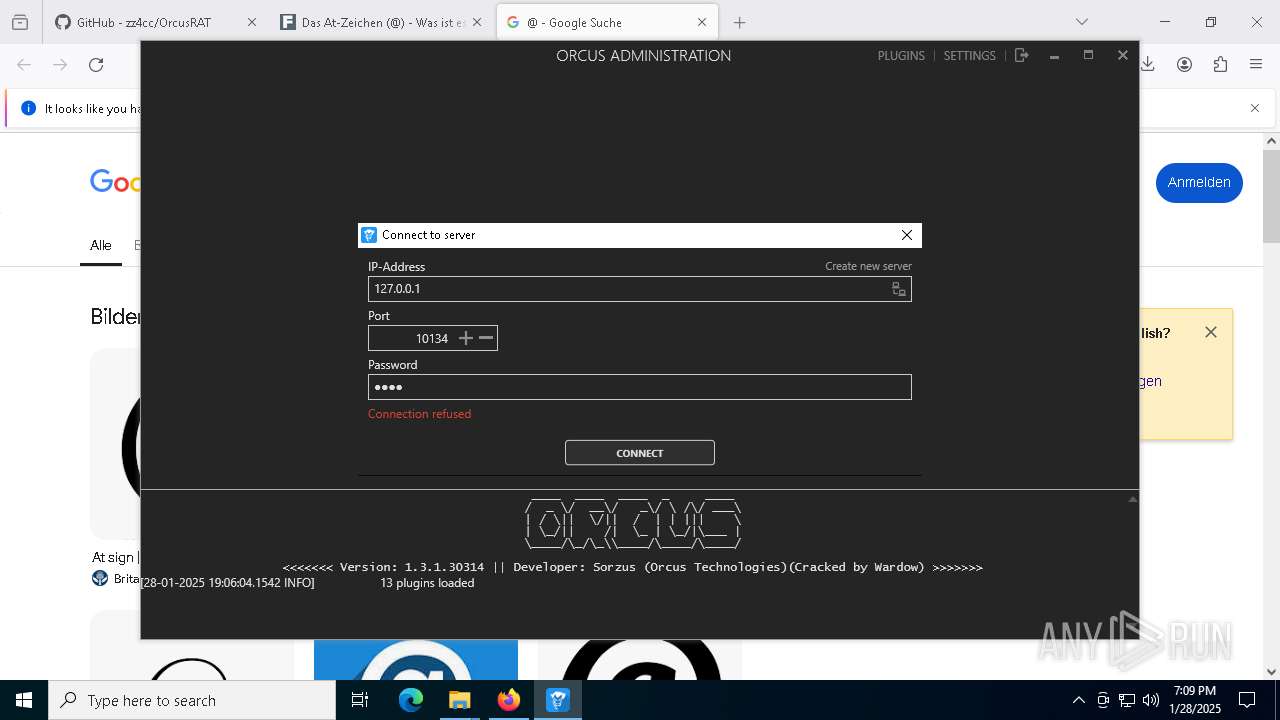
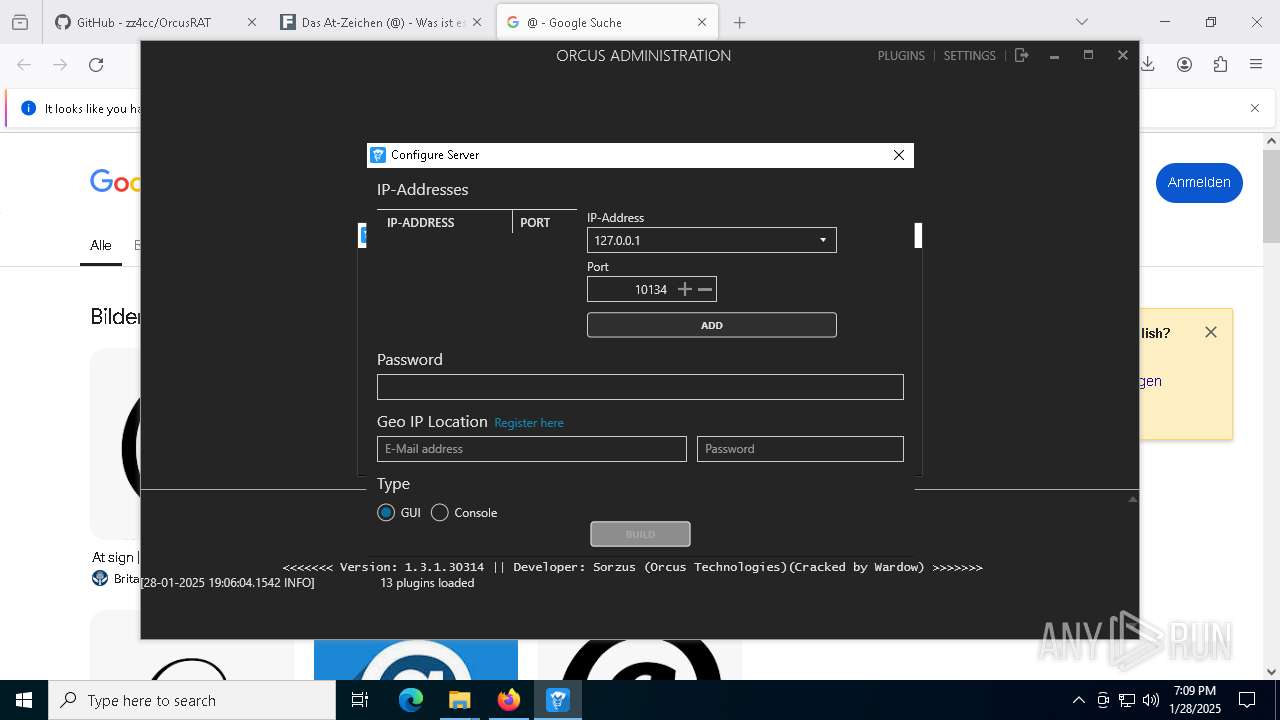
| Verdict: | Malicious activity |
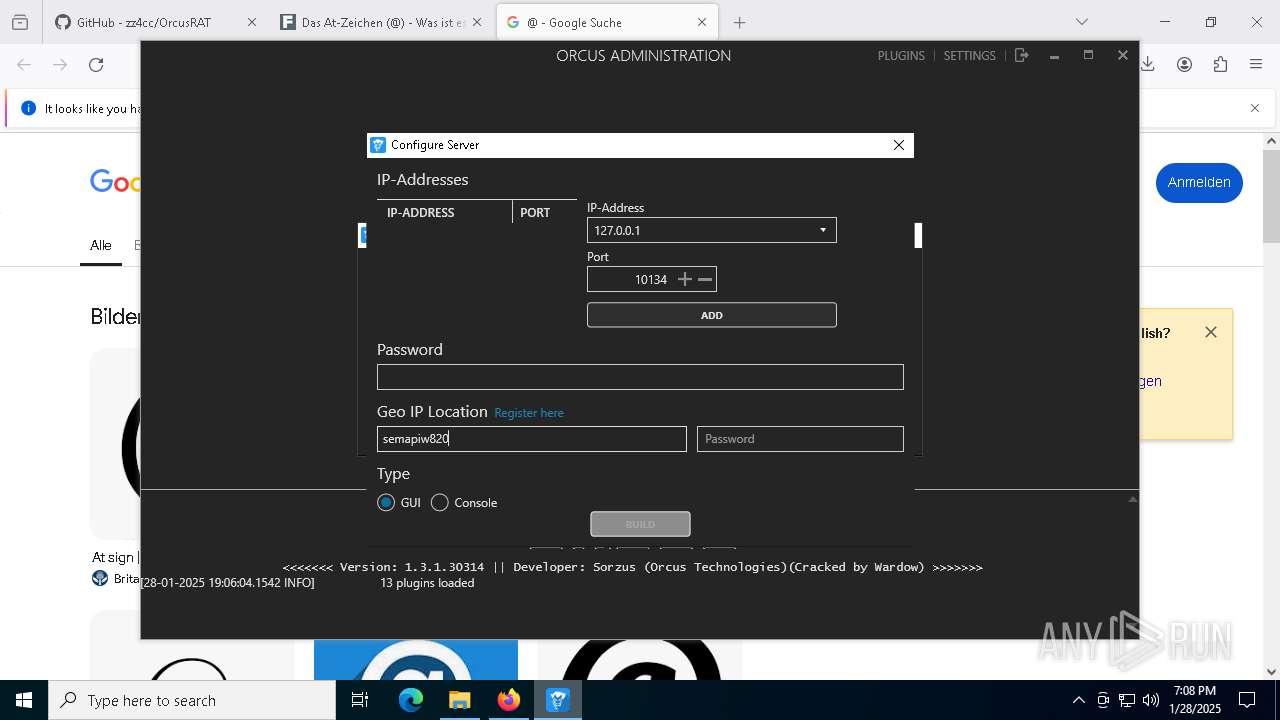
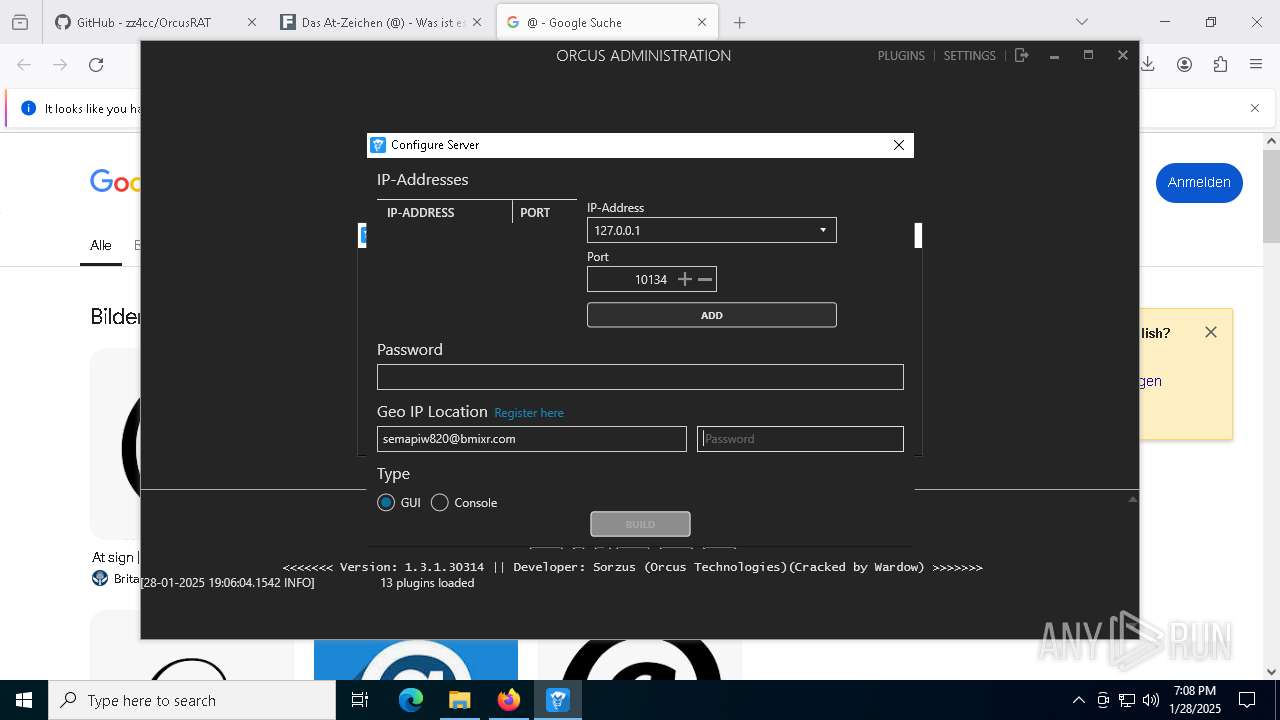
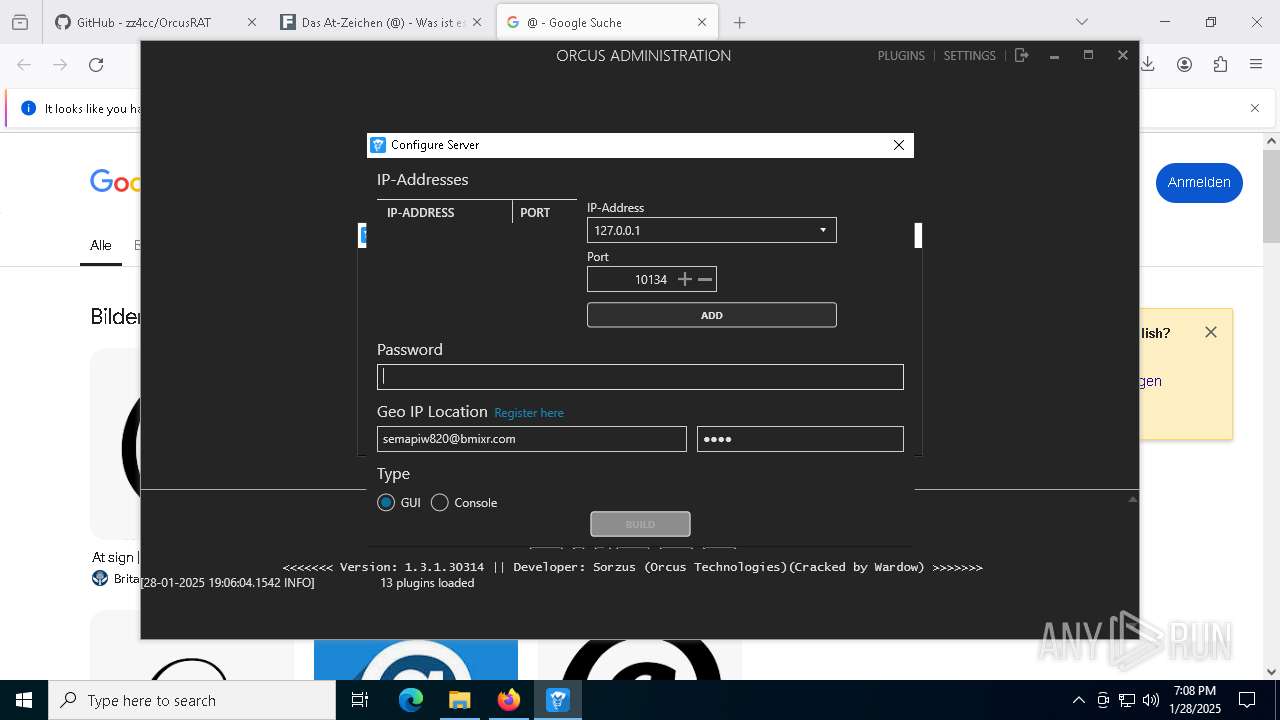
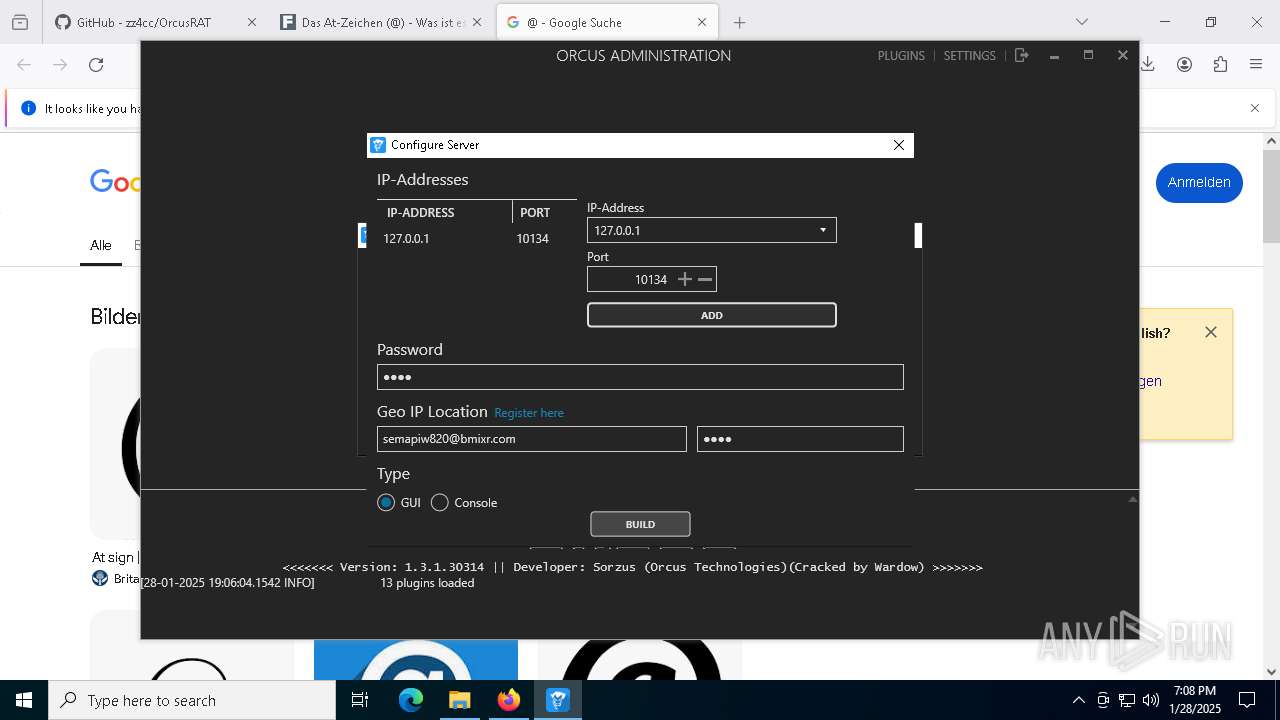
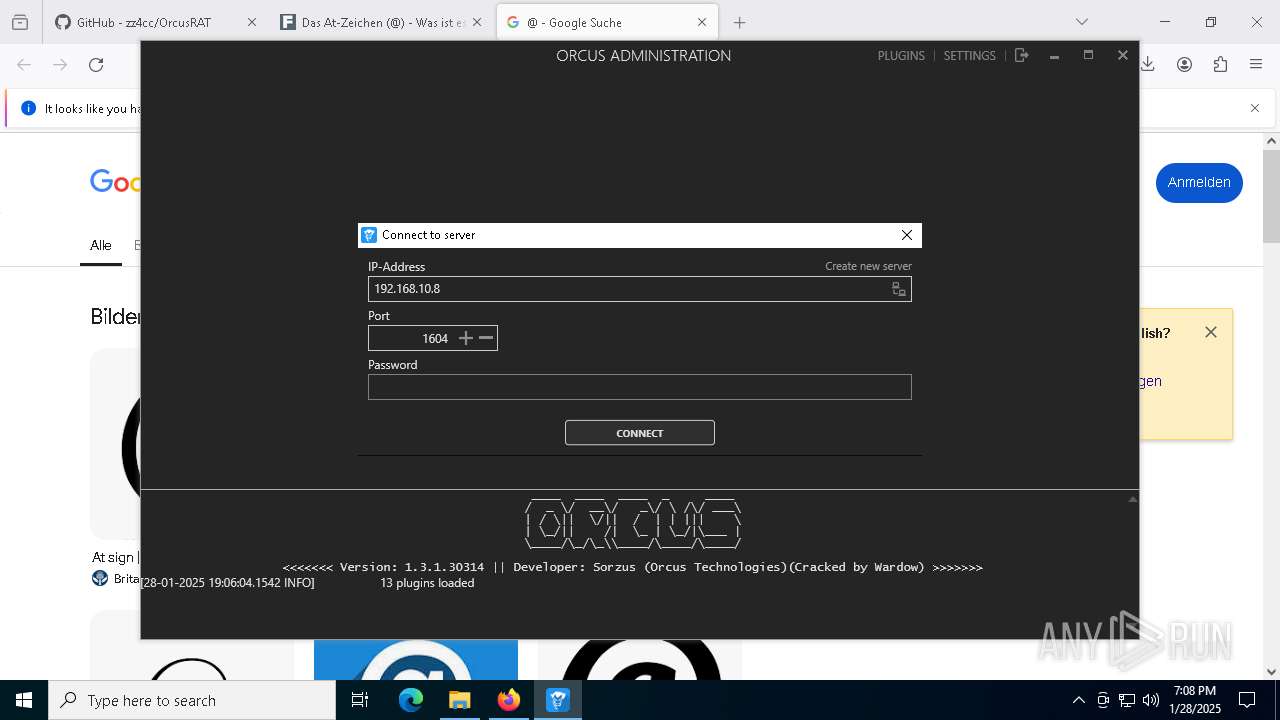
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | January 28, 2025, 19:04:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F26E89C293228DBA7E380C8A6D61F2DD |
| SHA1: | 60879DAC9067A8B3FA8FC7905F2F2C4ECF7E2459 |
| SHA256: | FEAC11B2BFD5C07B52D05F2D287C7E7EC22A54EB8283C3B1F164F6521B14A660 |
| SSDEEP: | 3:N8tEdvrRGQWBgIRn:2uRgDBgIRn |
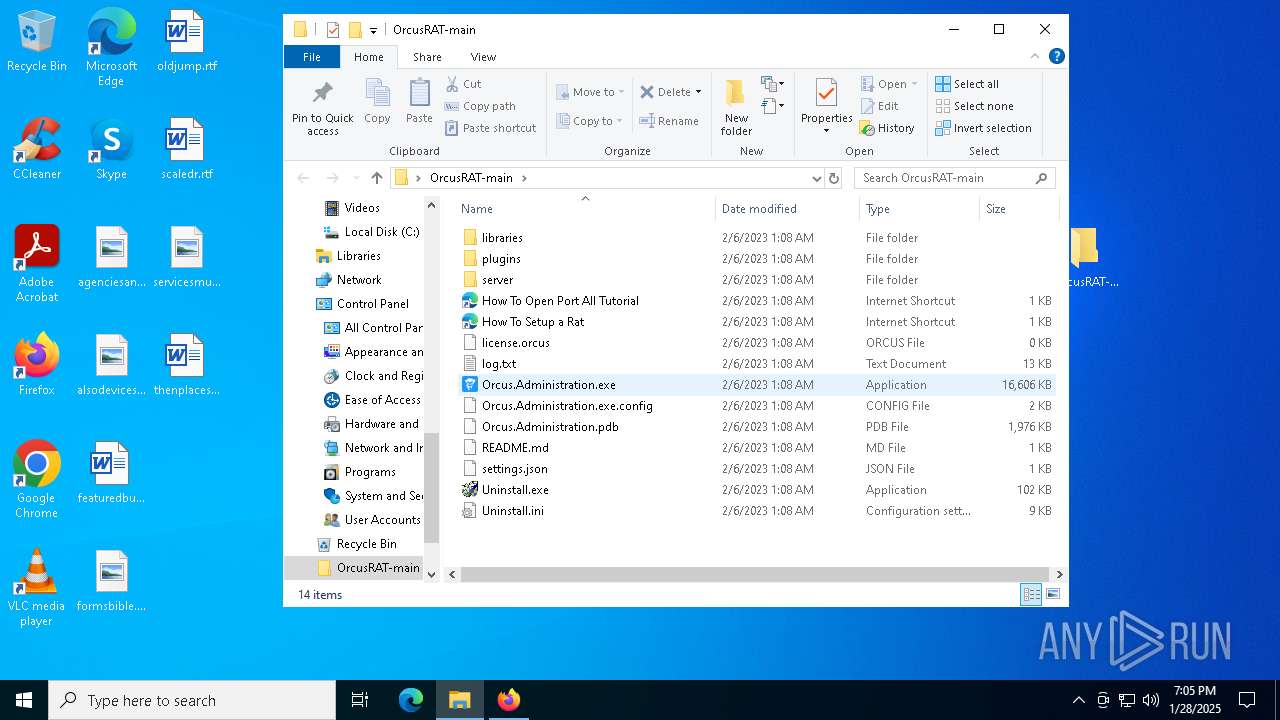
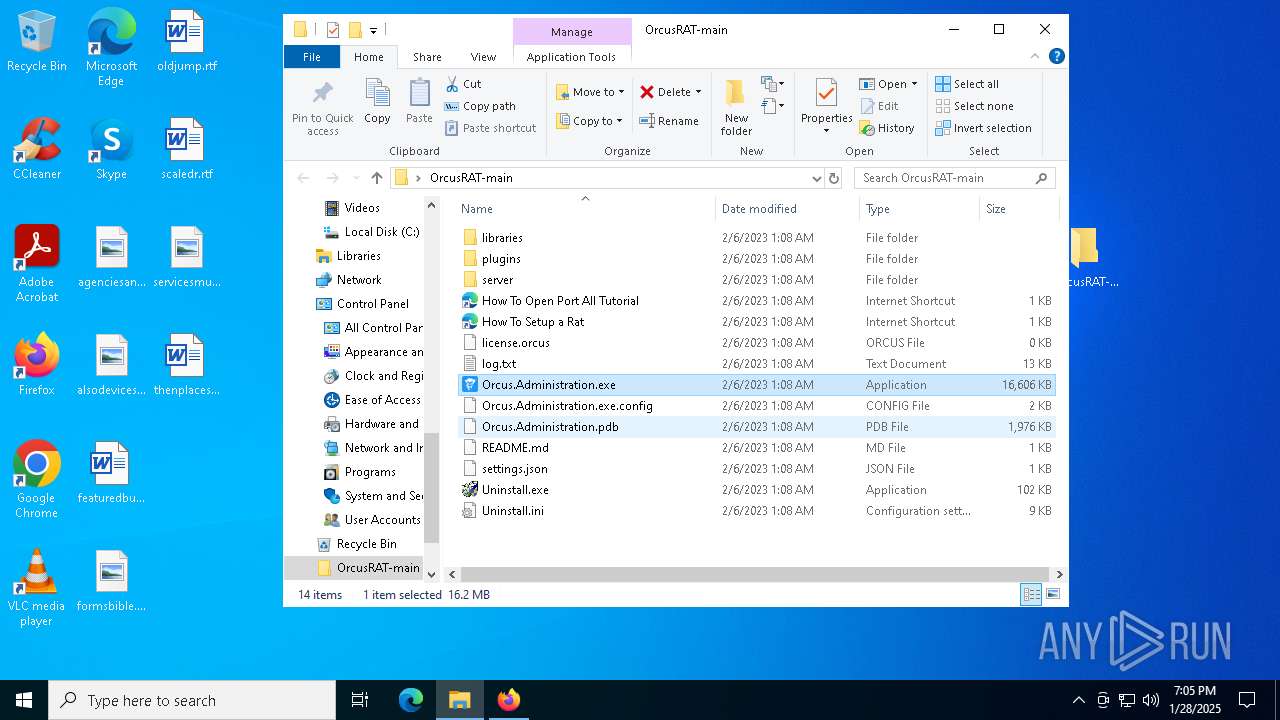
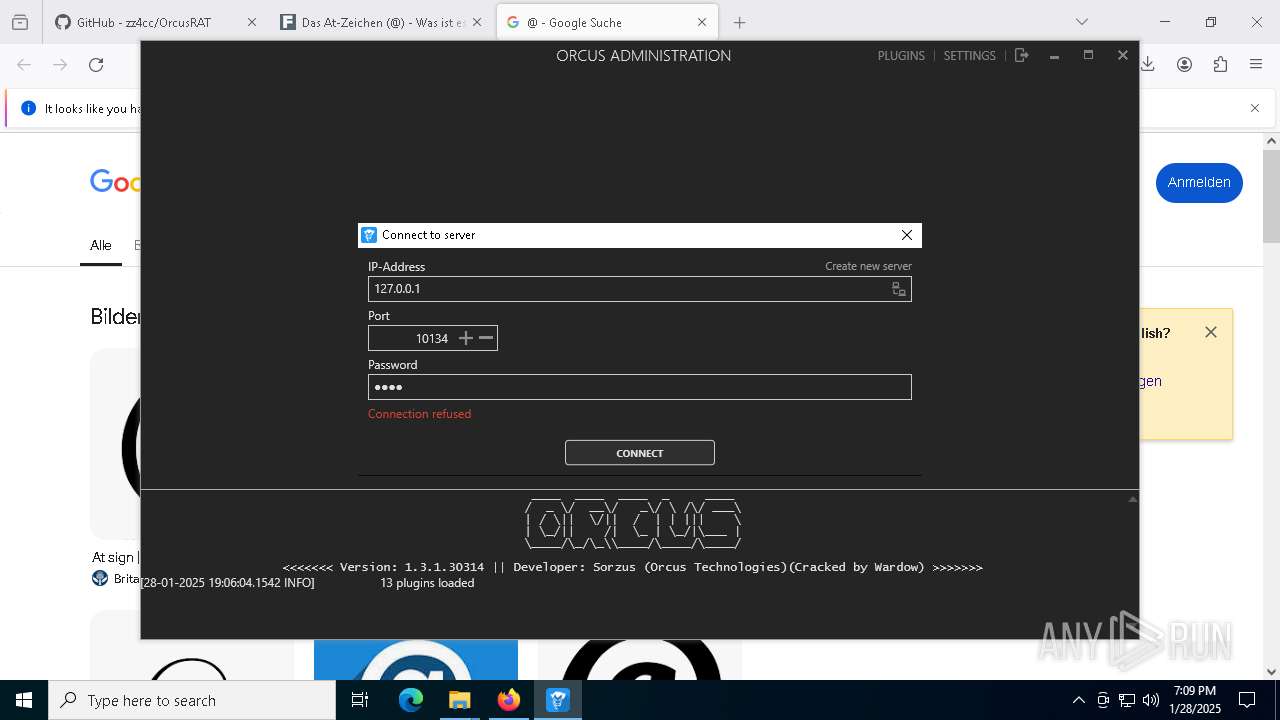
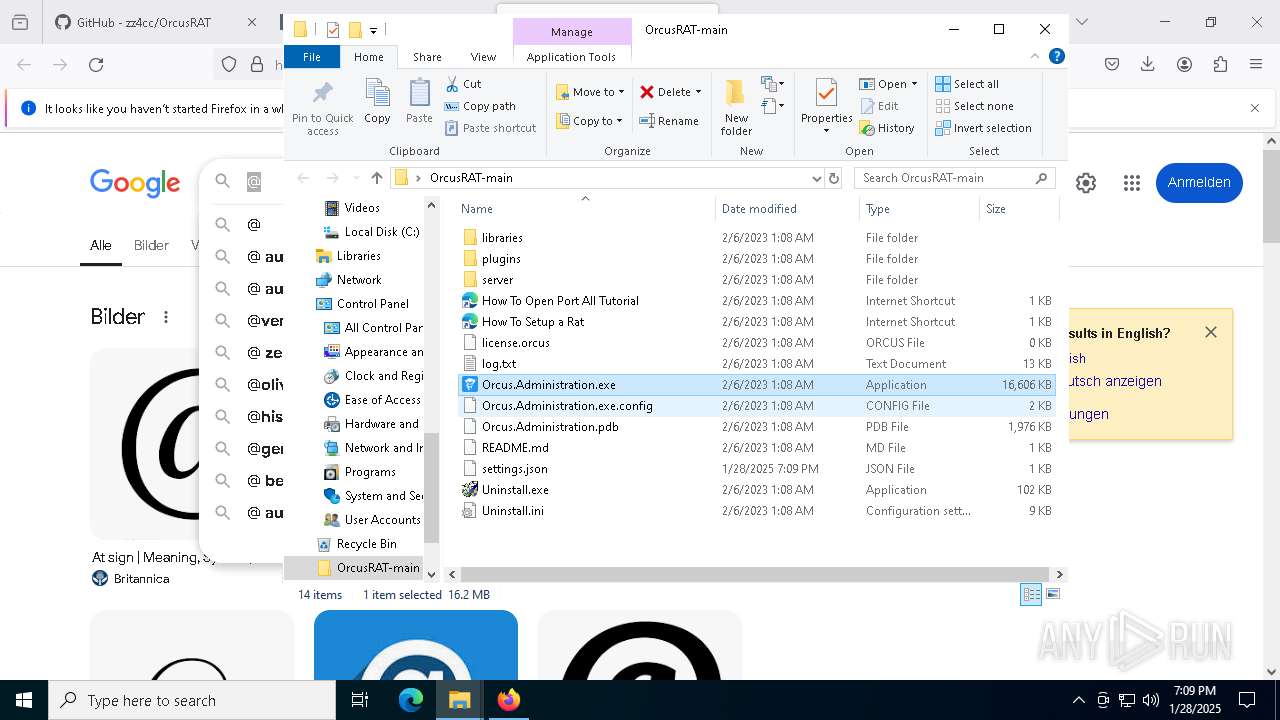
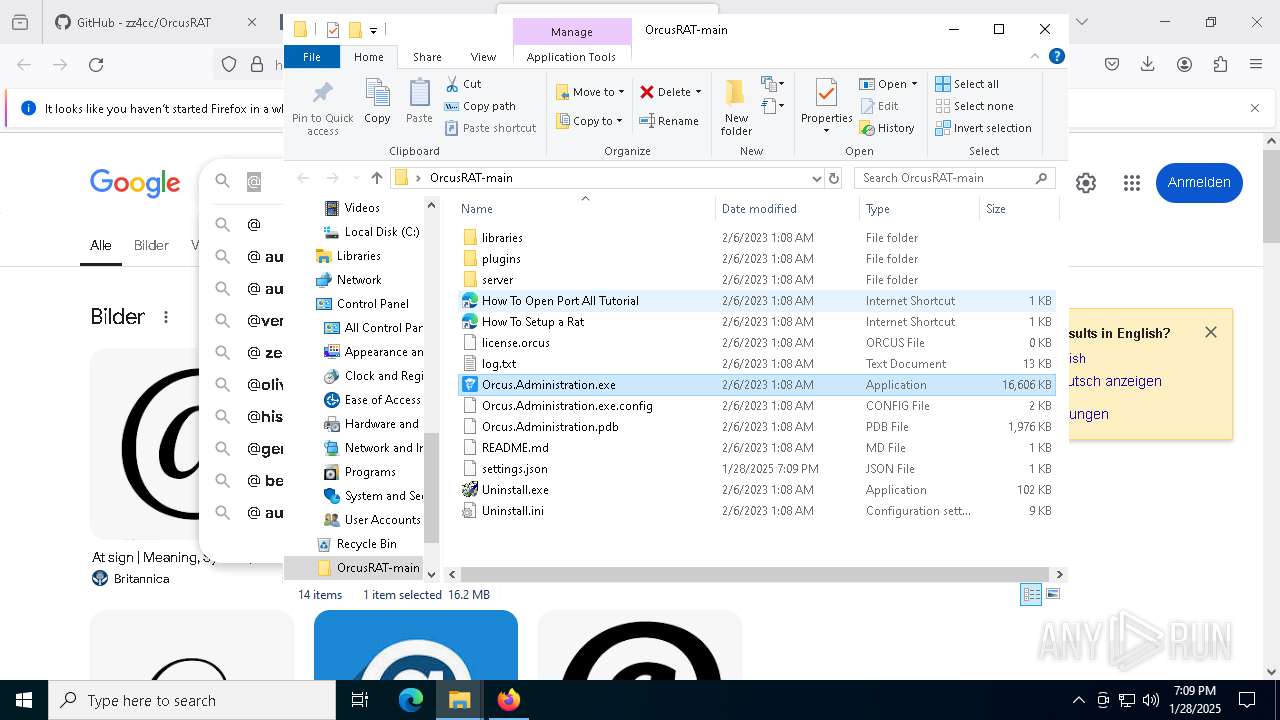
MALICIOUS
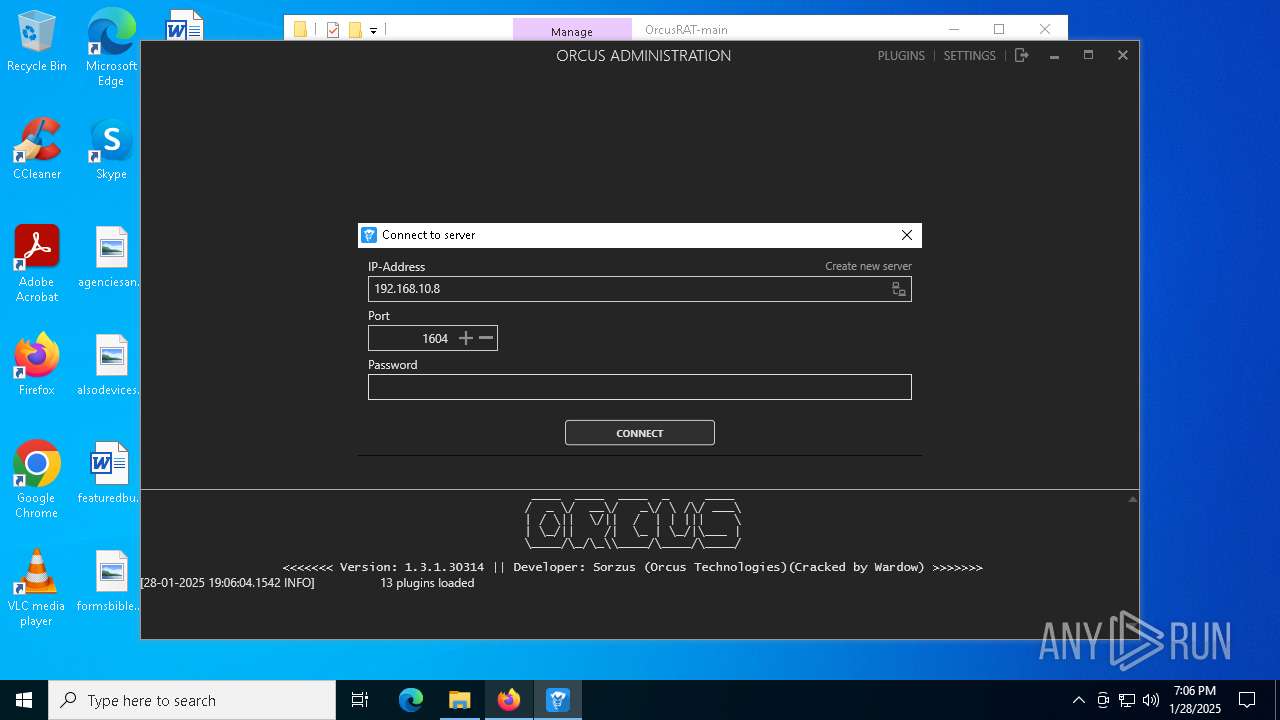
ORCUS has been detected (YARA)
- Orcus.Administration.exe (PID: 8076)
Orcus is detected
- Orcus.Administration.exe (PID: 8076)
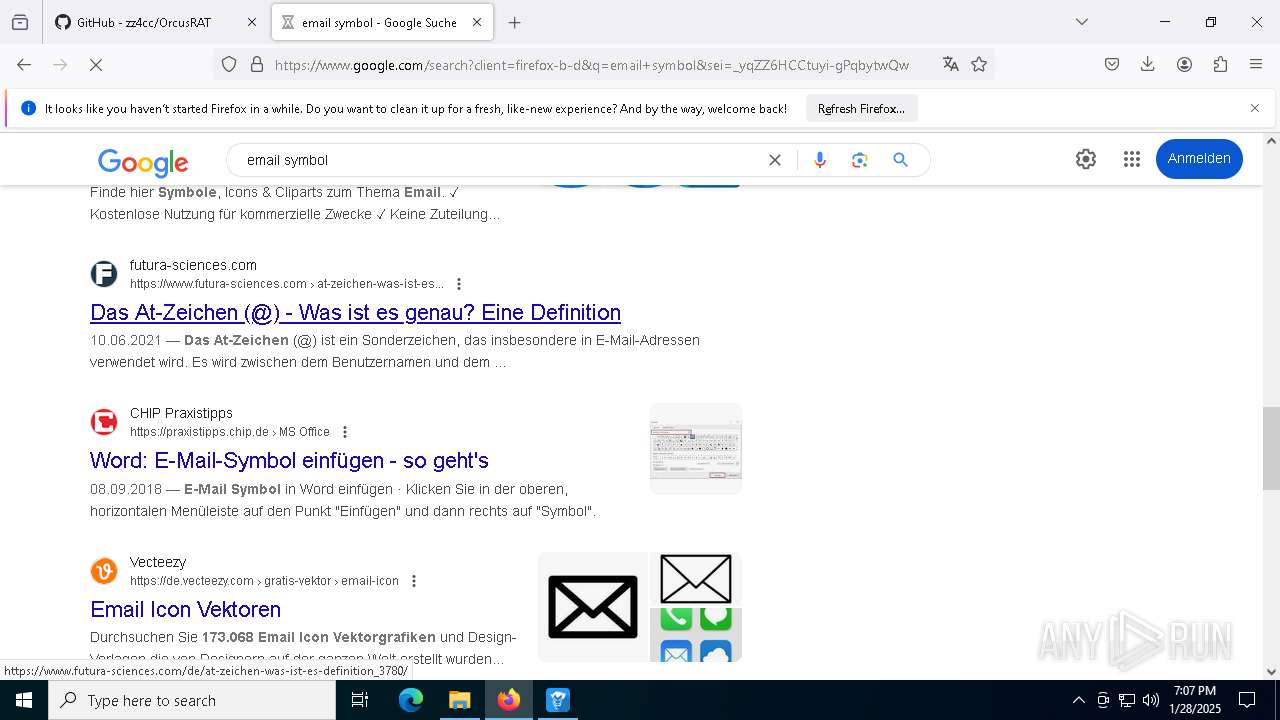
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 5872)
- firefox.exe (PID: 6336)
Reads security settings of Internet Explorer
- Orcus.Administration.exe (PID: 8076)
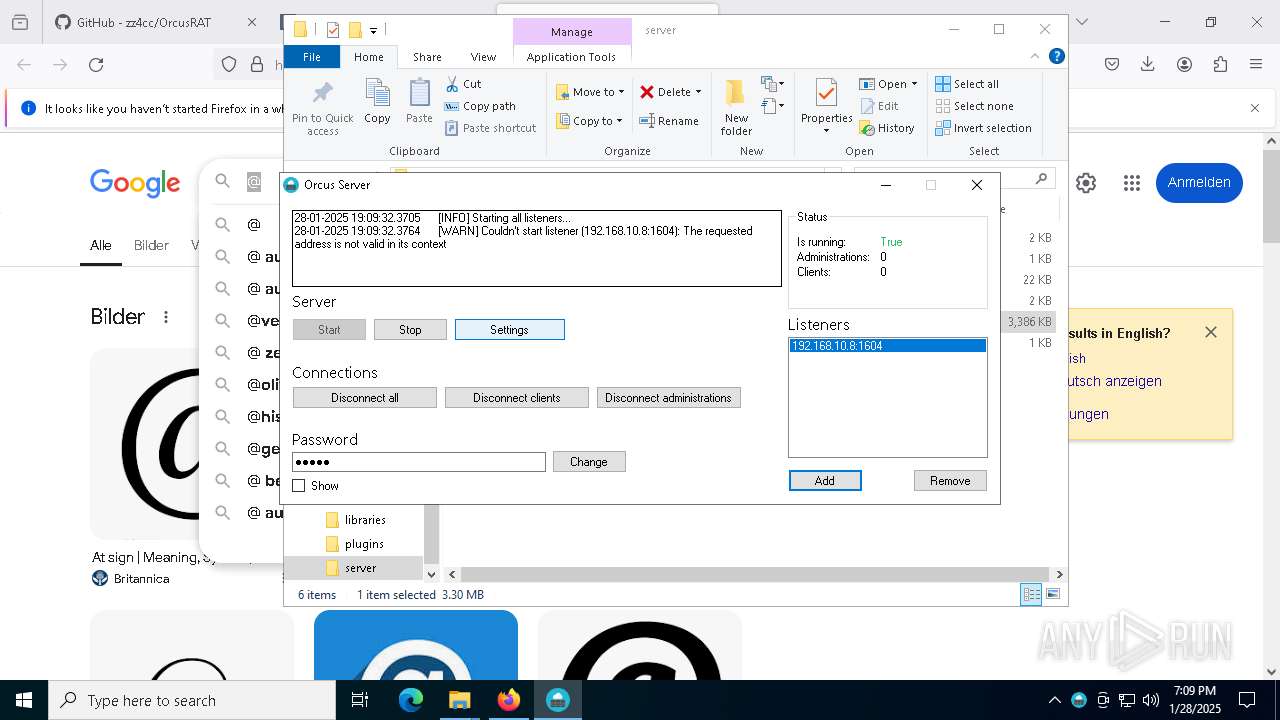
- Orcus.Server.exe (PID: 7240)
There is functionality for taking screenshot (YARA)
- Orcus.Administration.exe (PID: 8076)
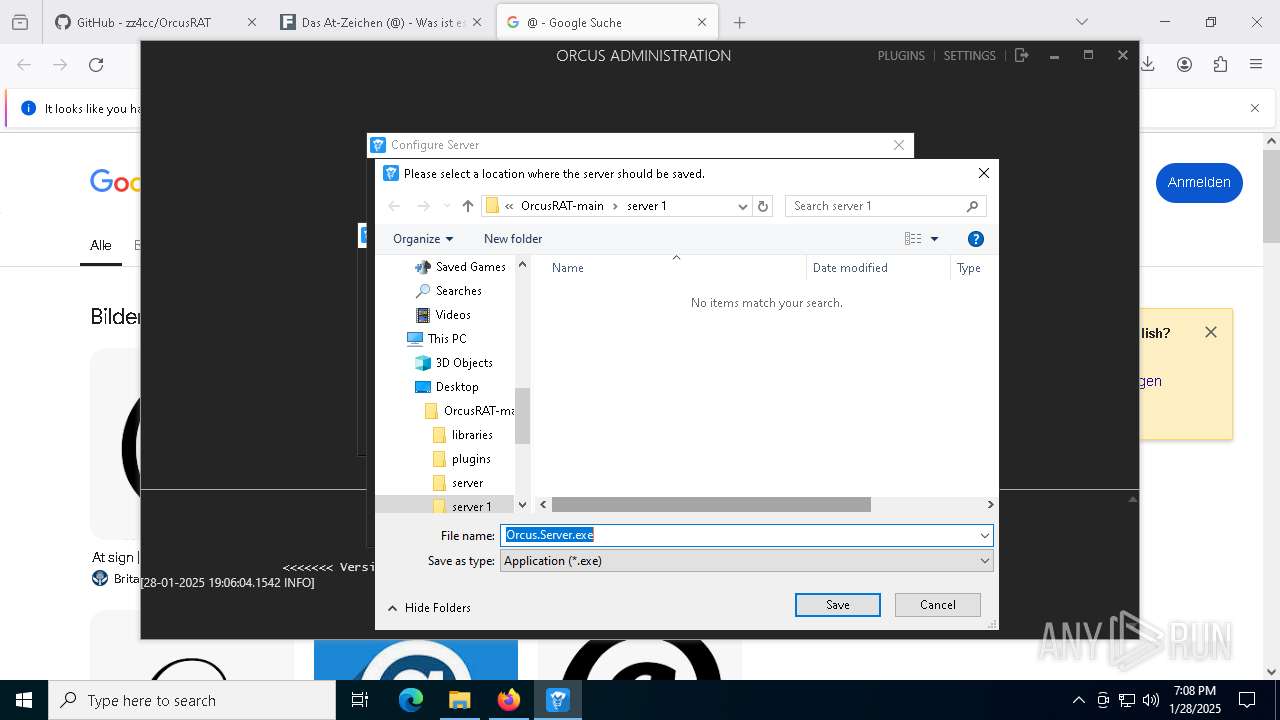
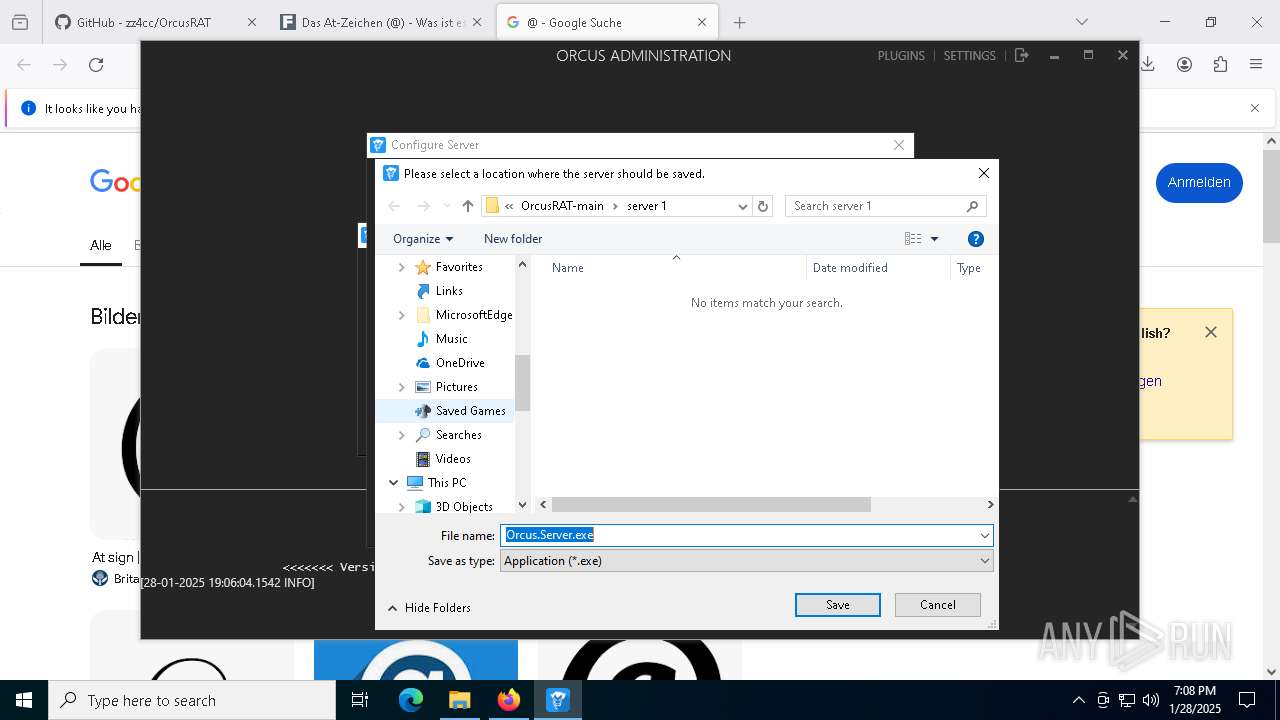
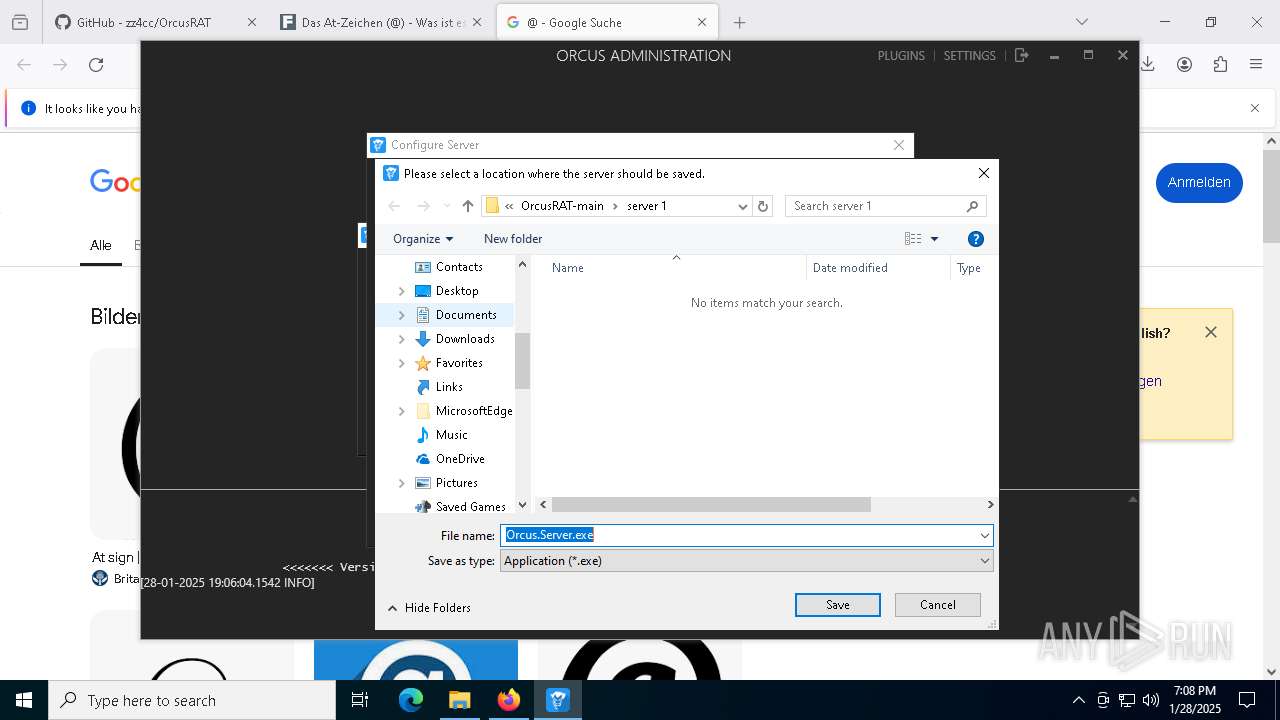
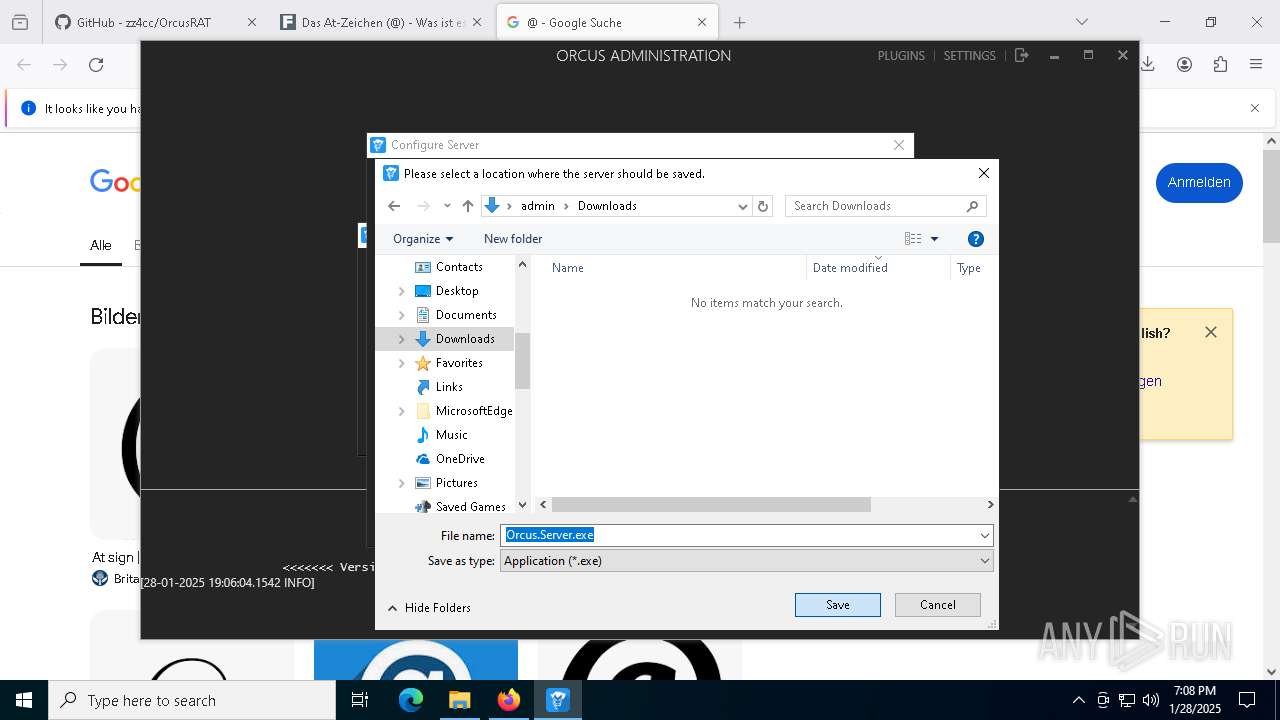
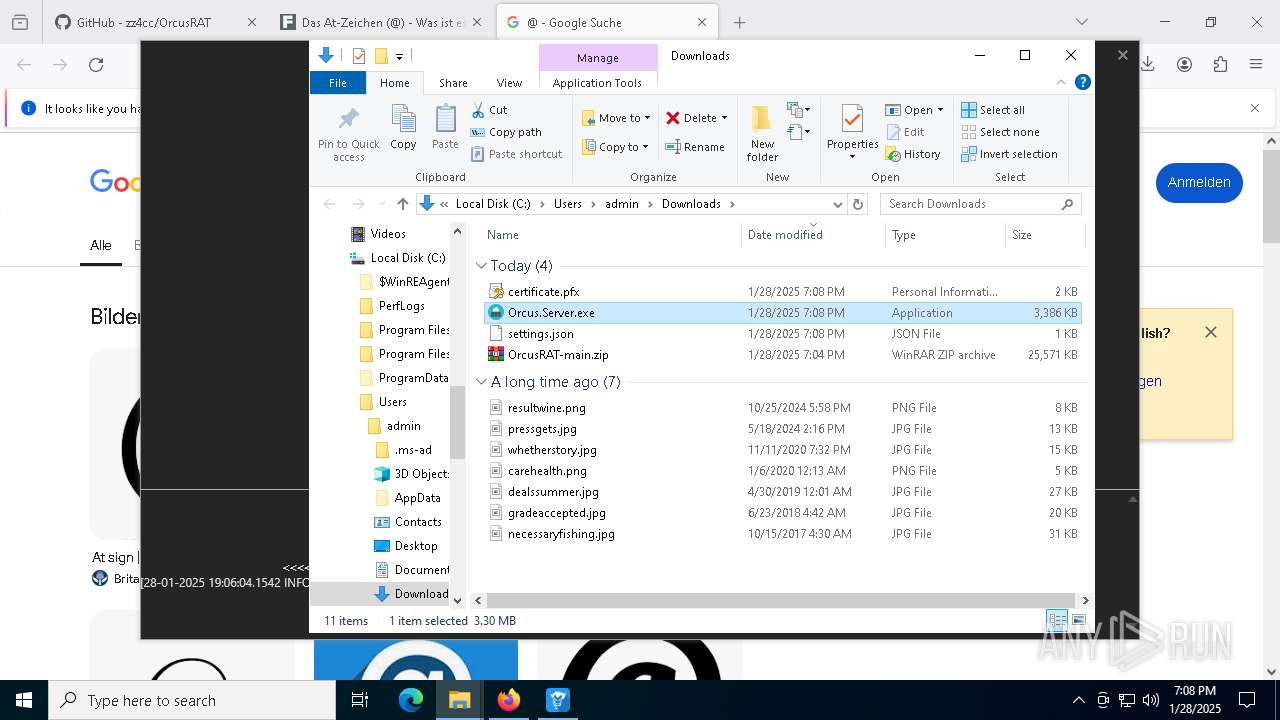
Executable content was dropped or overwritten
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
INFO
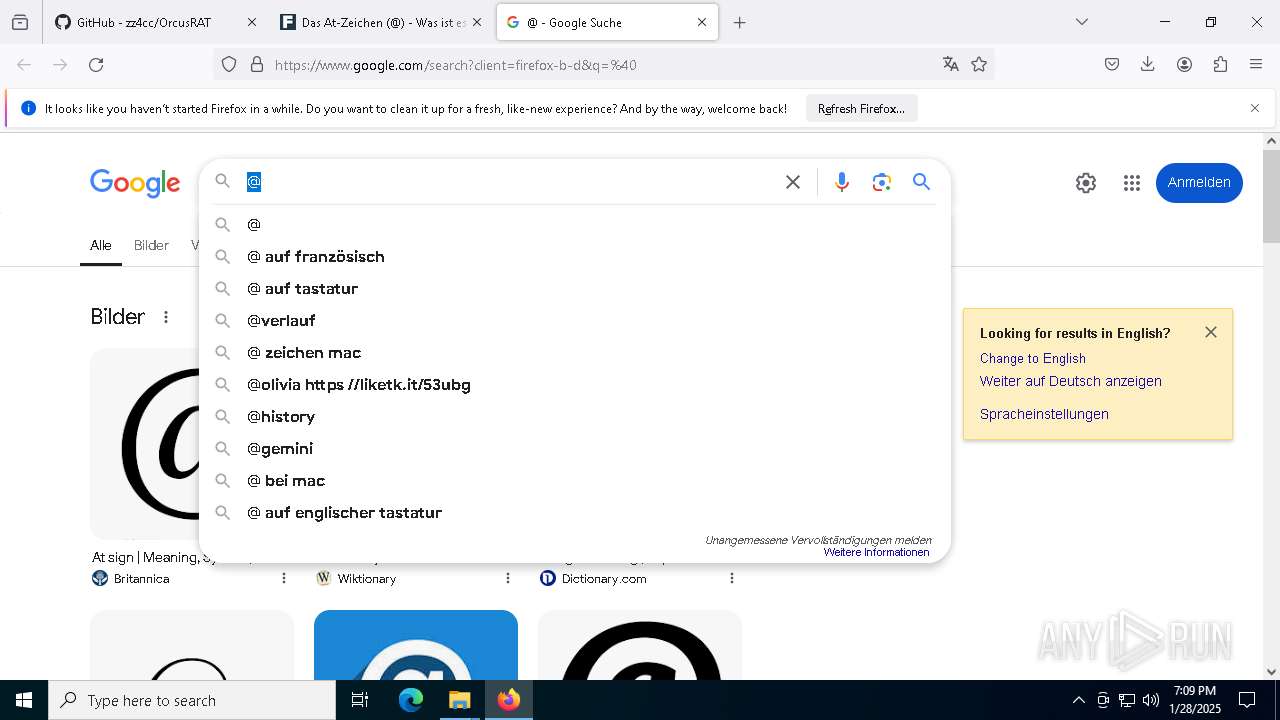
Application launched itself
- firefox.exe (PID: 6188)
- firefox.exe (PID: 6336)
Checks supported languages
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
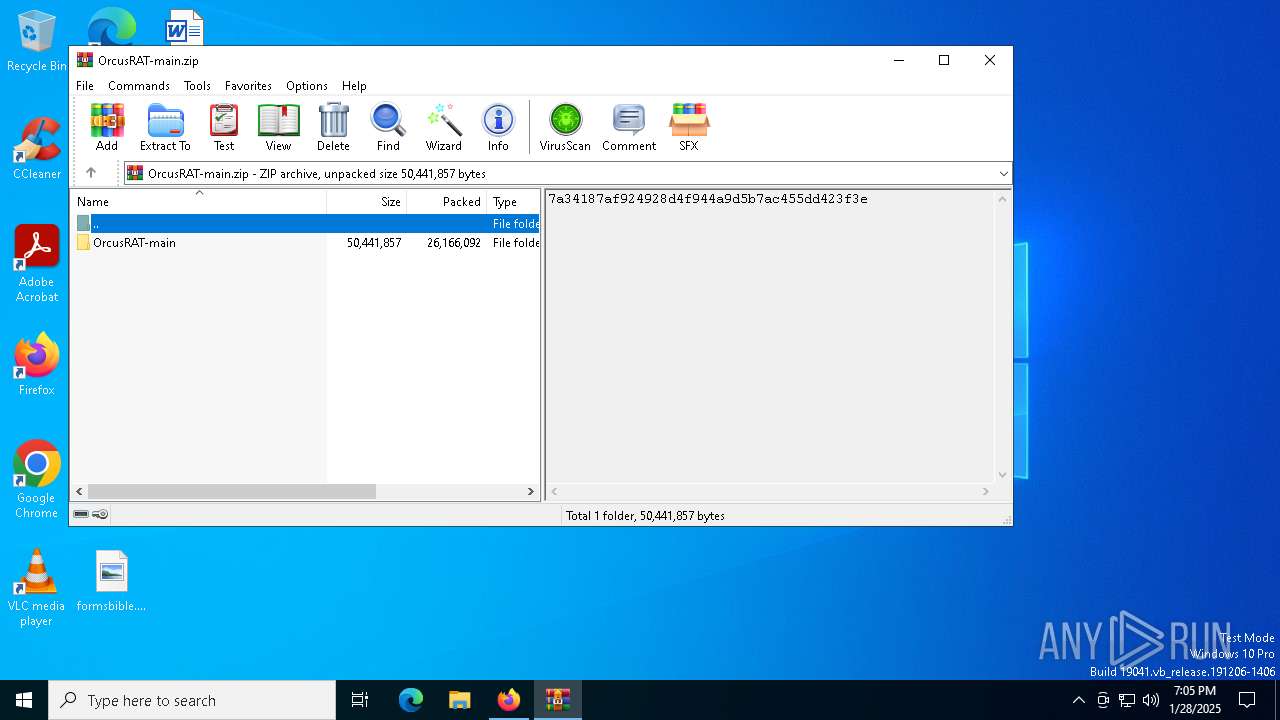
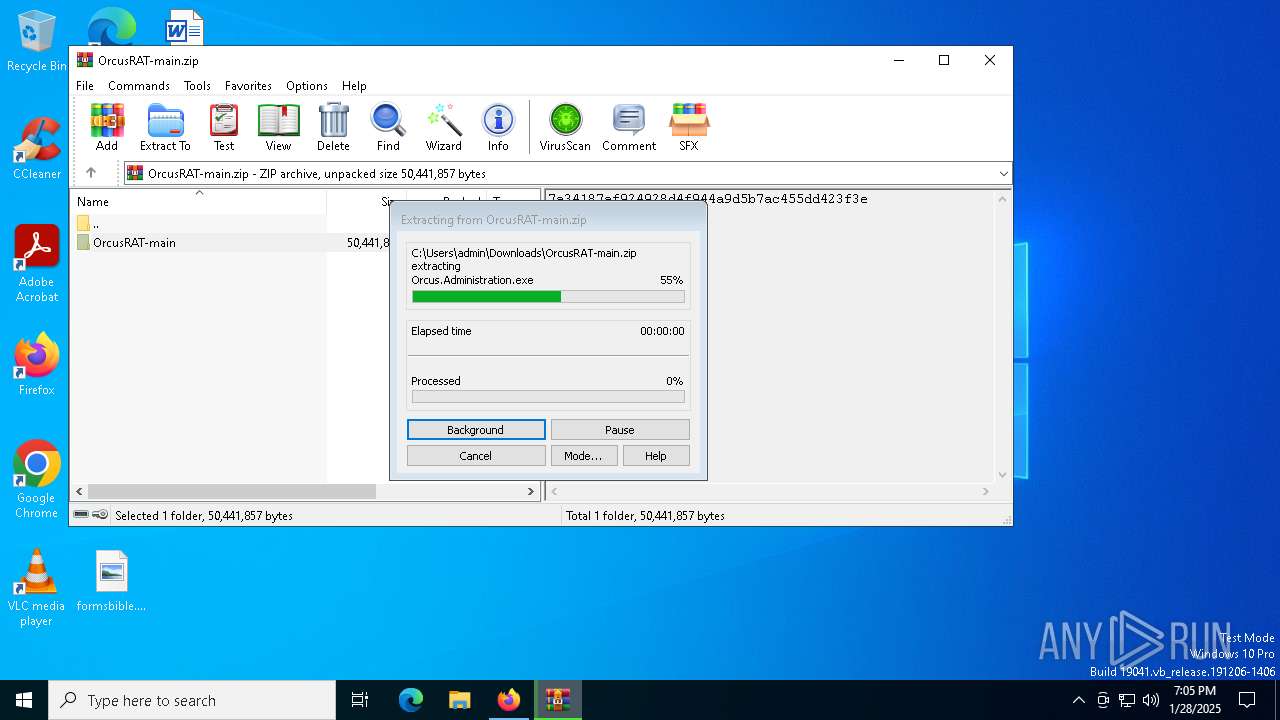
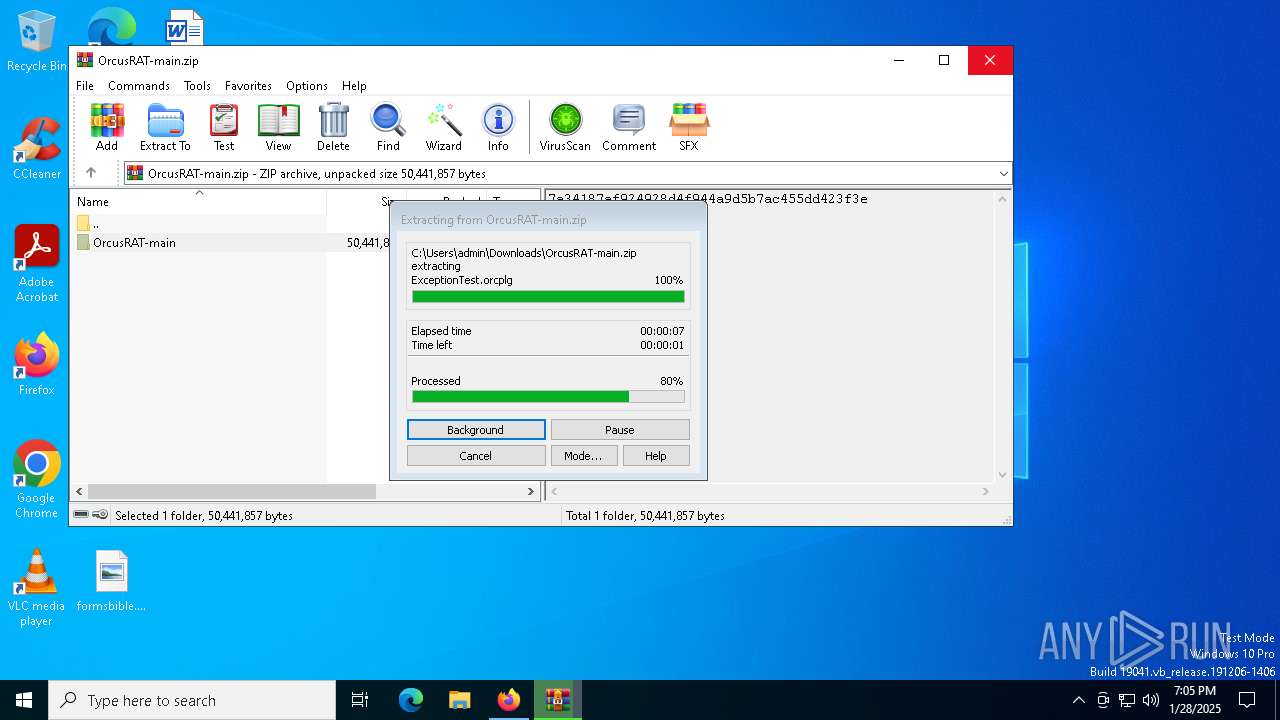
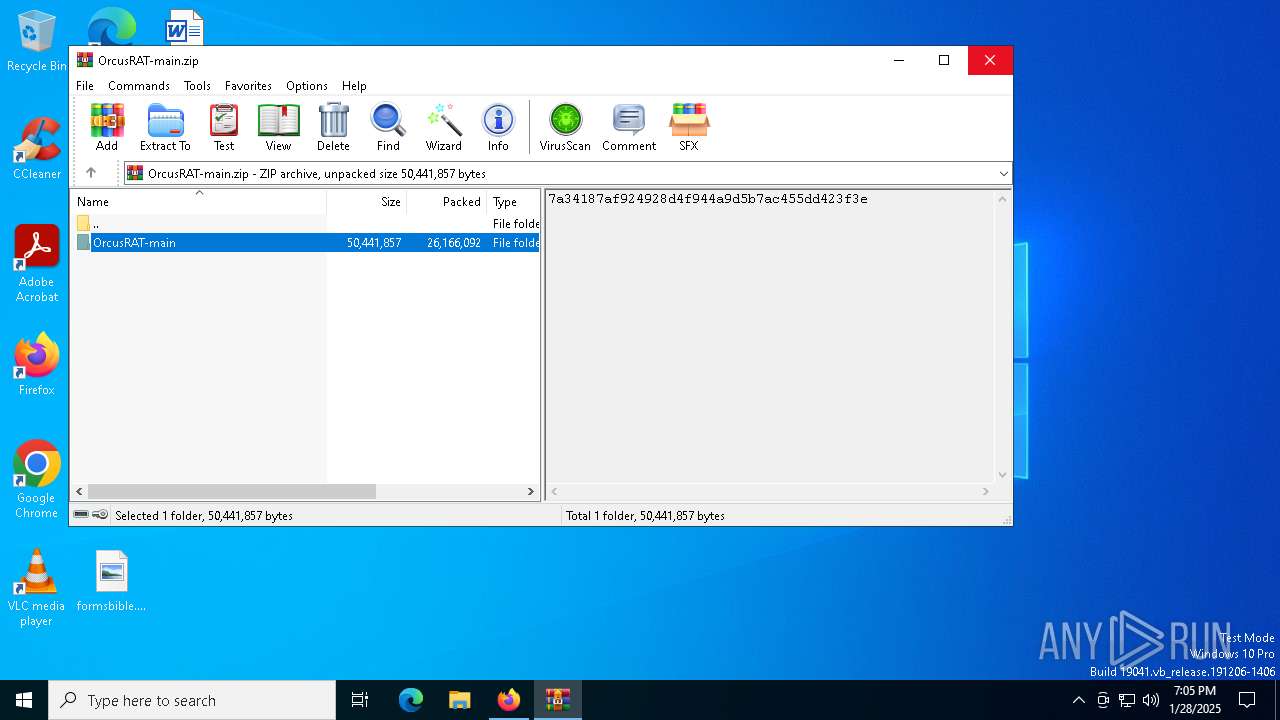
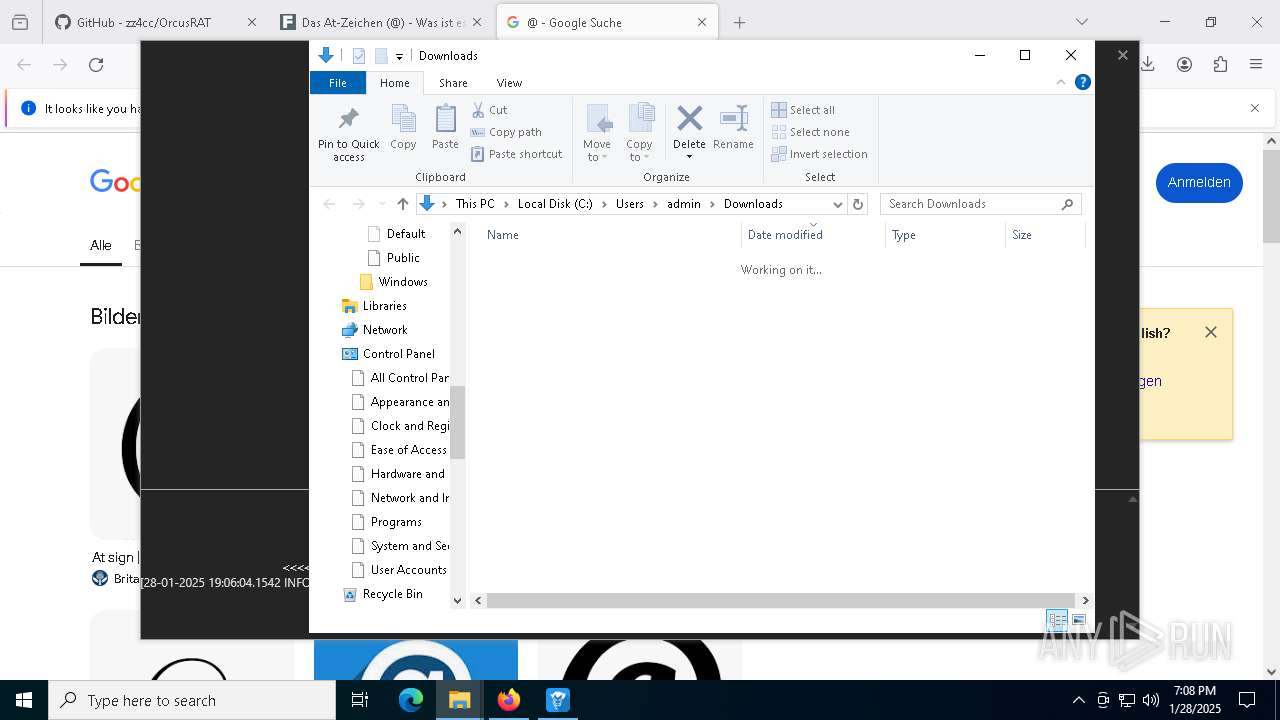
Manual execution by a user
- WinRAR.exe (PID: 5872)
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
- notepad.exe (PID: 5036)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5872)
Reads the machine GUID from the registry
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
Reads the computer name
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
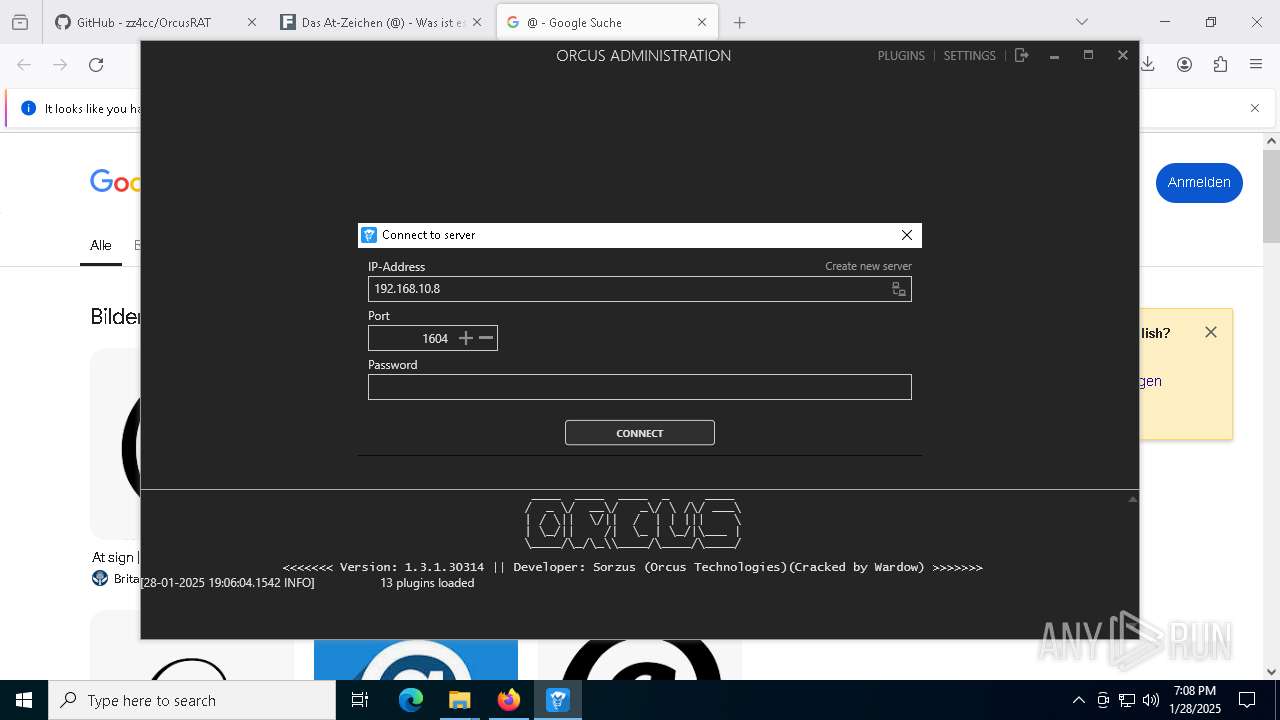
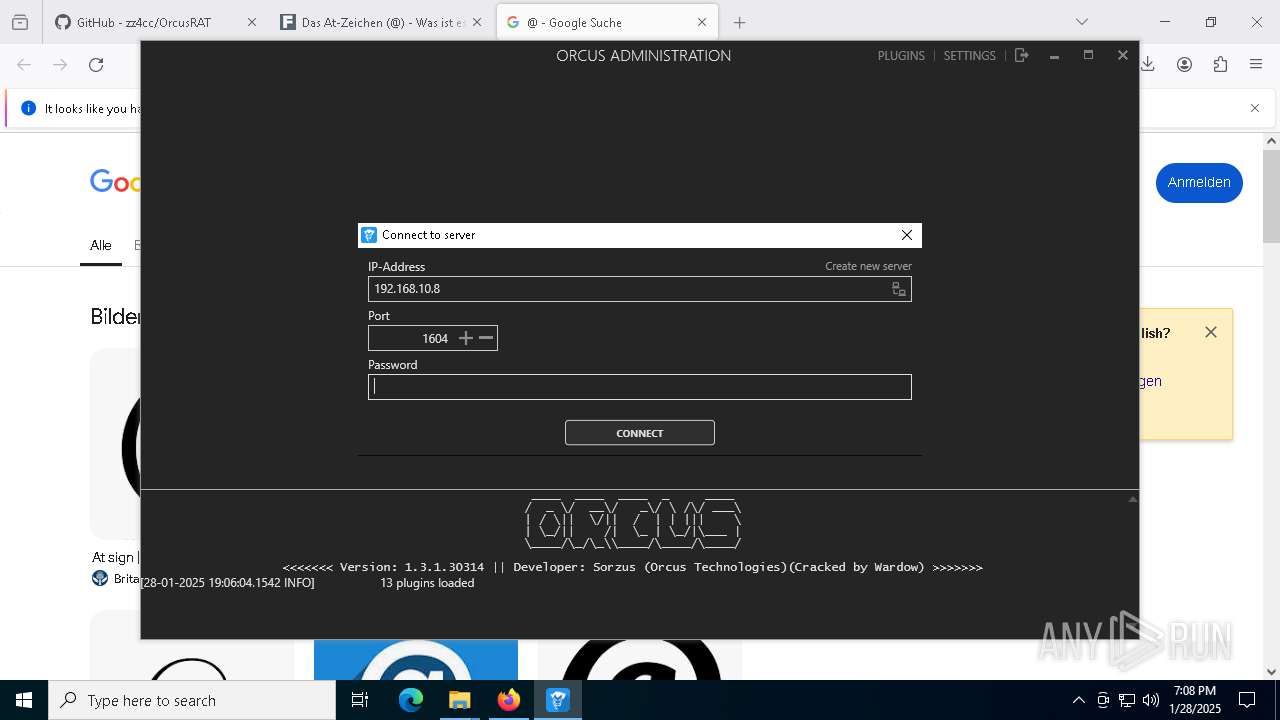
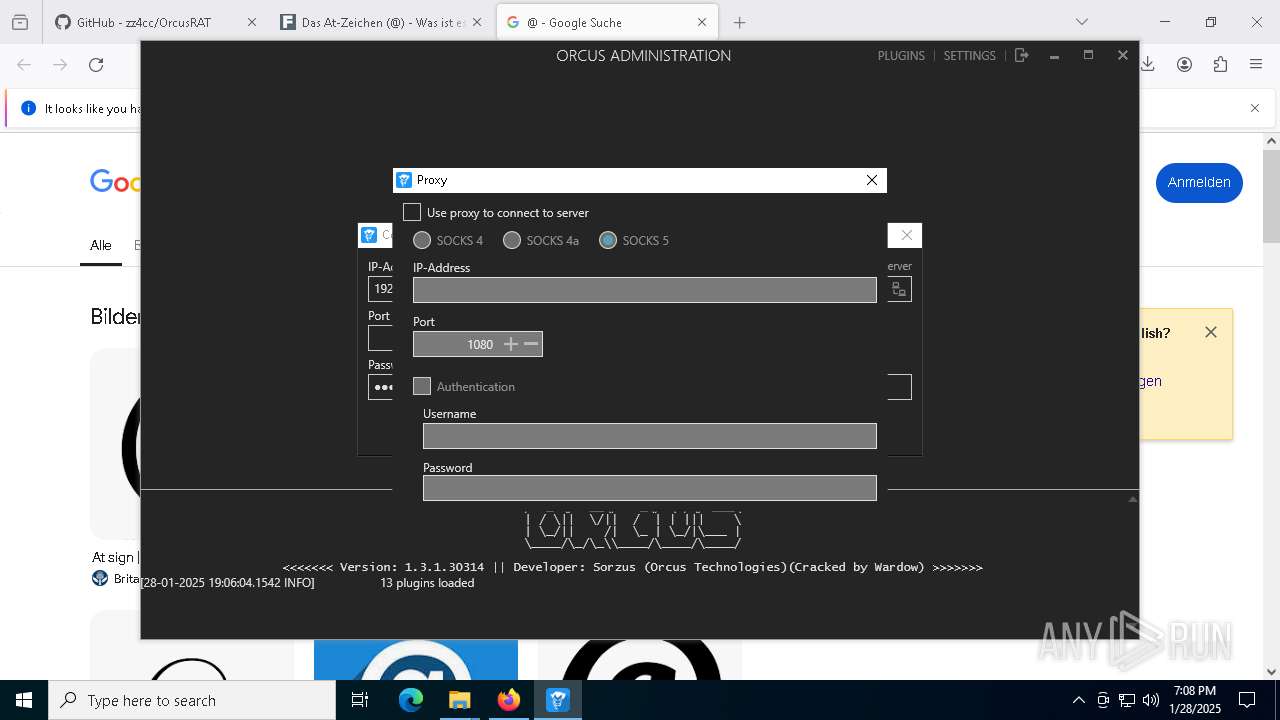
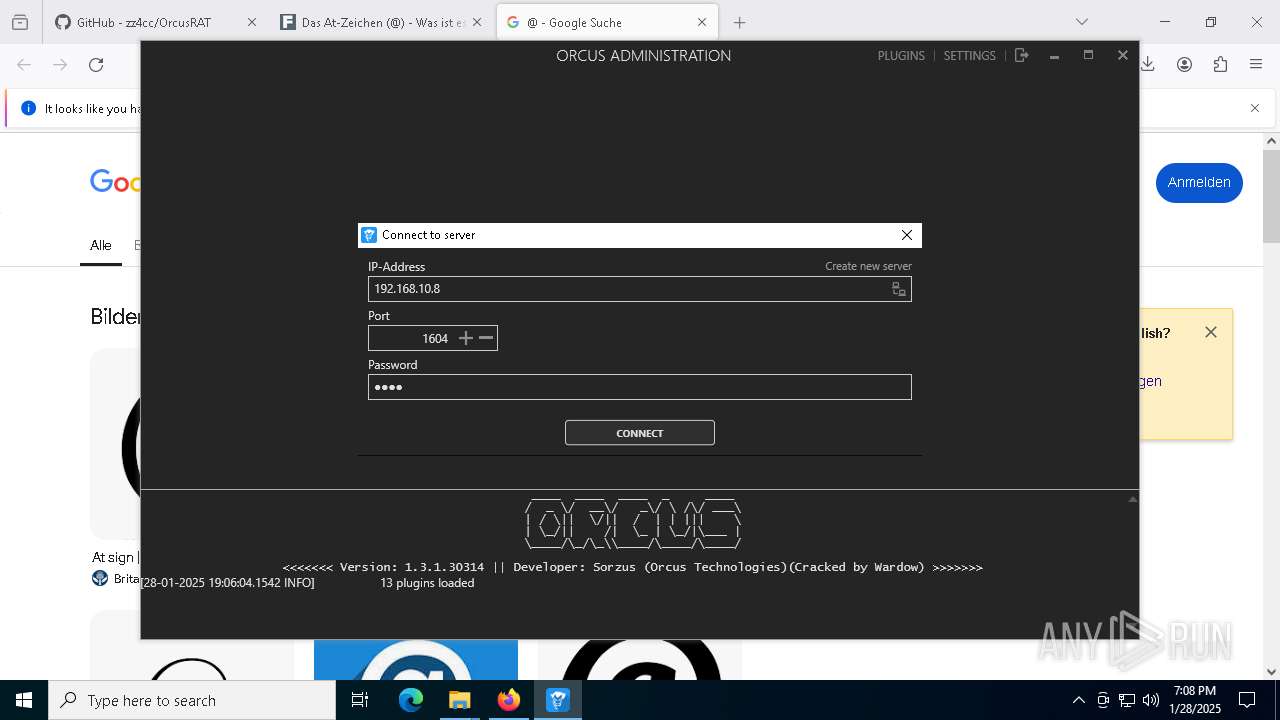
Checks proxy server information
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
Confuser has been detected (YARA)
- Orcus.Administration.exe (PID: 8076)
Disables trace logs
- Orcus.Administration.exe (PID: 8076)
Reads the software policy settings
- Orcus.Administration.exe (PID: 8076)
Create files in a temporary directory
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
Creates files or folders in the user directory
- Orcus.Administration.exe (PID: 8076)
- Orcus.Server.exe (PID: 7240)
Reads security settings of Internet Explorer
- explorer.exe (PID: 2756)
- notepad.exe (PID: 5036)
Process checks computer location settings
- Orcus.Administration.exe (PID: 8076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
159
Monitored processes
30
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7240 -childID 14 -isForBrowser -prefsHandle 7244 -prefMapHandle 7248 -prefsLen 32060 -prefMapSize 244583 -jsInitHandle 1292 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {13b51fbb-2bdc-4dab-9534-2252f5ae7126} 6336 "\\.\pipe\gecko-crash-server-pipe.6336" 22be0892850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6360 -childID 9 -isForBrowser -prefsHandle 6472 -prefMapHandle 952 -prefsLen 32060 -prefMapSize 244583 -jsInitHandle 1292 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {46049549-5e94-4544-a783-f7d5cbd2af9c} 6336 "\\.\pipe\gecko-crash-server-pipe.6336" 22bdf317690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2756 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6068 -childID 8 -isForBrowser -prefsHandle 6064 -prefMapHandle 5188 -prefsLen 32060 -prefMapSize 244583 -jsInitHandle 1292 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {59a20a47-fc0d-4d68-8022-c64a88215e0c} 6336 "\\.\pipe\gecko-crash-server-pipe.6336" 22bdd3784d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3848 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6472 -parentBuildID 20240213221259 -prefsHandle 6676 -prefMapHandle 6680 -prefsLen 39088 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {aa5aa5c0-88c7-4d96-81fb-32684079a539} 6336 "\\.\pipe\gecko-crash-server-pipe.6336" 22bde14b110 rdd | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
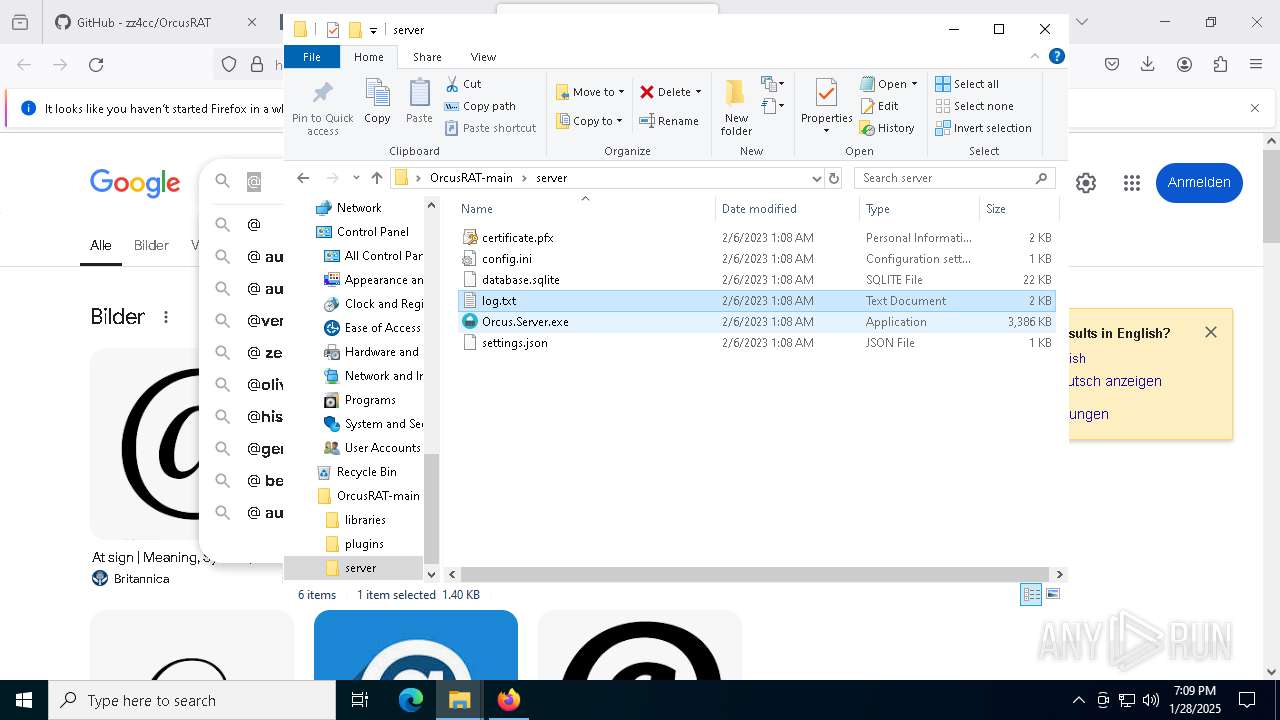
| 5036 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\OrcusRAT-main\server\log.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5192 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5984 -childID 13 -isForBrowser -prefsHandle 7204 -prefMapHandle 7200 -prefsLen 32060 -prefMapSize 244583 -jsInitHandle 1292 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {adddc7eb-71a3-472c-a5b9-686de4605d34} 6336 "\\.\pipe\gecko-crash-server-pipe.6336" 22bdf317690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5696 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6156 -childID 7 -isForBrowser -prefsHandle 6148 -prefMapHandle 2632 -prefsLen 32060 -prefMapSize 244583 -jsInitHandle 1292 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e30306bb-bf15-4193-a3ad-bb8b49280eaf} 6336 "\\.\pipe\gecko-crash-server-pipe.6336" 22bdcfdc310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\OrcusRAT-main.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
40 139
Read events
39 993
Write events
141
Delete events
5
Modification events
| (PID) Process: | (6336) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\OrcusRAT-main.zip | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
41
Suspicious files
282
Text files
77
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6336 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6336 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
271
DNS requests
321
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1620 | svchost.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1620 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6336 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6336 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6336 | firefox.exe | POST | 200 | 23.53.40.154:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6336 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
6336 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/jLM | unknown | — | — | whitelisted |
6336 | firefox.exe | POST | 200 | 23.53.40.123:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1620 | svchost.exe | 95.101.78.32:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1620 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.136:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
github.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
Process | Message |
|---|---|
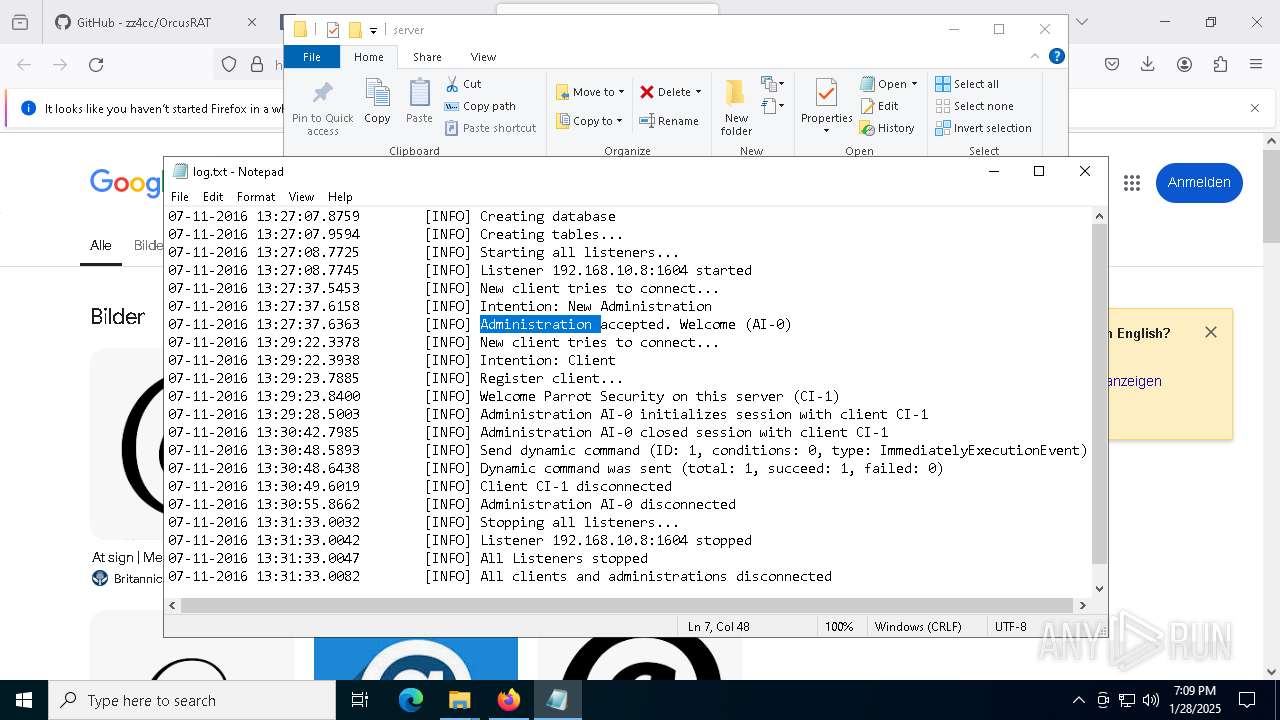
Orcus.Server.exe | Adding Key [CheckForDeadConnectionsRequestAnswer]=[20000]
|
Orcus.Server.exe | Adding section [SERVER]
|
Orcus.Server.exe | Adding Key [CheckForDeadConnectionsInterval]=[10000]
|
Orcus.Server.exe | Adding Key [CheckForDeadConnectionsTimeout]=[60000]
|
Orcus.Server.exe | Adding Key [ConnectionTimeout]=[10000]
|
Orcus.Server.exe | Adding Key [EnabledNamedPipe]=[true]
|
Orcus.Server.exe | Adding Key [CheckForDeadConnections]=[true]
|
Orcus.Server.exe | Adding Key [NamedPipeConnectionTimeout]=[4000]
|
Orcus.Server.exe | Adding section [CONFIG_FILE]
|
Orcus.Server.exe | Writing Key: UseServerIpAddressIfOutOfRange=true
|