| File name: | Client.exe |
| Full analysis: | https://app.any.run/tasks/ba0d583f-3eeb-41eb-9c0b-97ad7376322e |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | October 04, 2022, 21:21:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D1092DD29F82ABEA5AFAA9F47FCE5E46 |
| SHA1: | 5BA86062ED3721B7CEE08E1A07842BD84C6D3CB6 |
| SHA256: | FE1481B7E6AA4BD4A2FAA66FEF3D5BA0AC9842A7D9122749B56D2A4354425F8B |
| SSDEEP: | 1536:rntG0AI1JfxQ7CqmB9x1bbsTxR7mWa+askNpqKmY7:rnWI/x/q8n1bbsTLmTKkWz |
MALICIOUS
ASYNCRAT was detected
- Client.exe (PID: 3156)
ASYNCRAT detected by memory dumps
- Client.exe (PID: 3156)
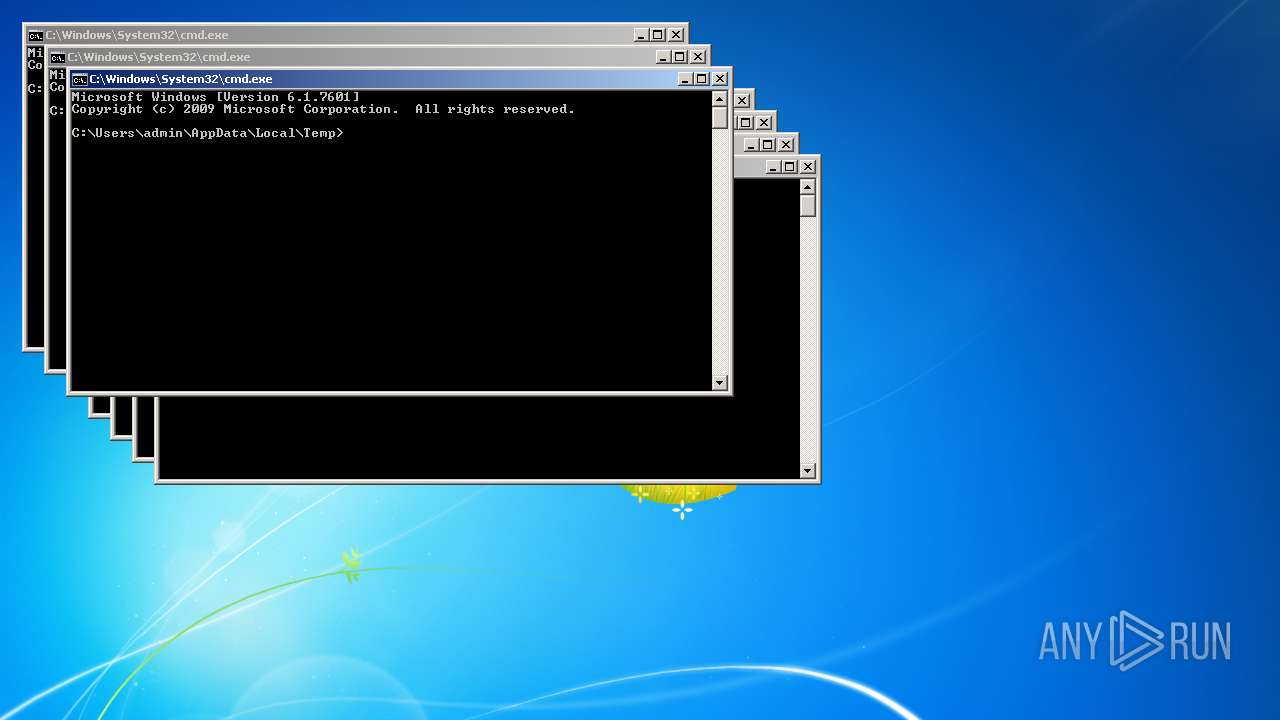
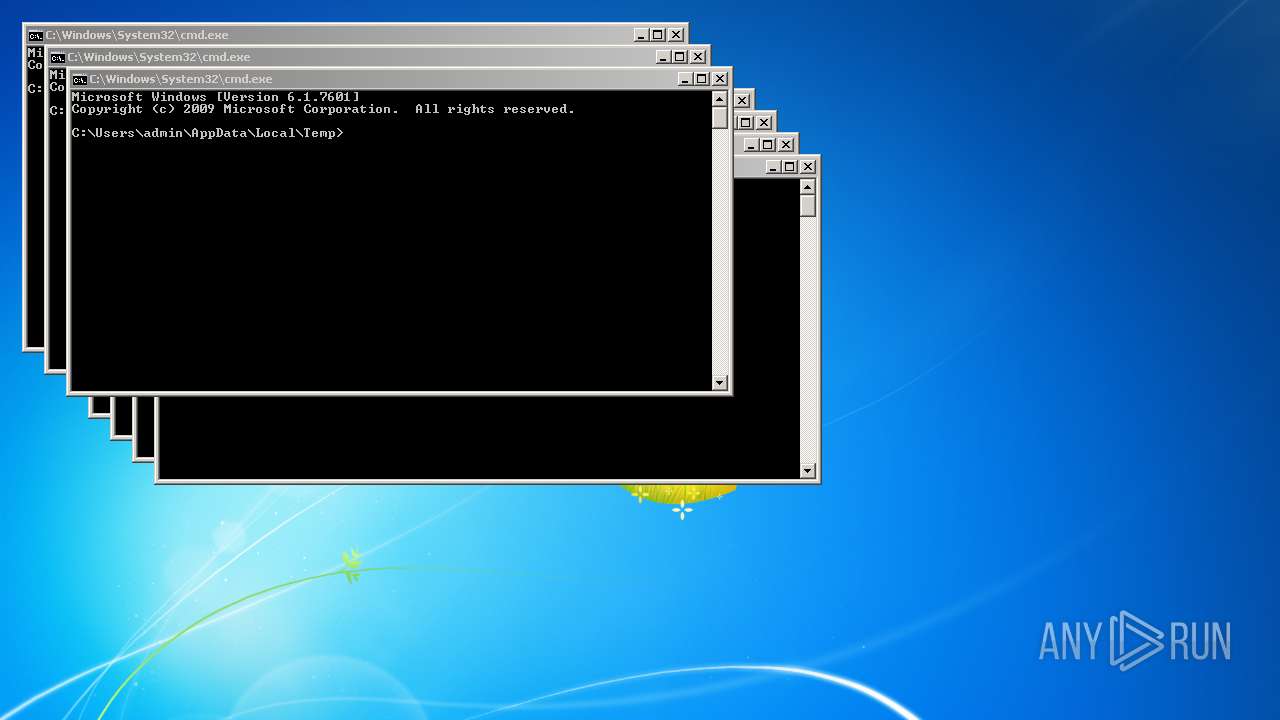
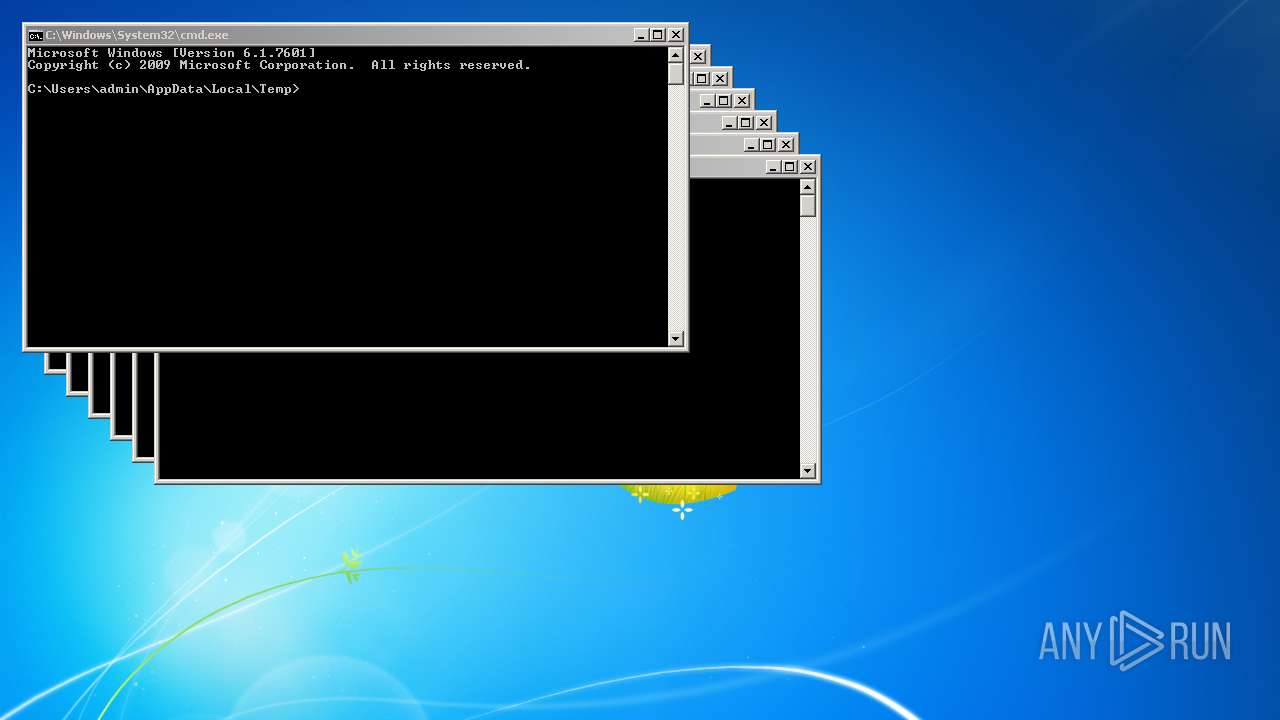
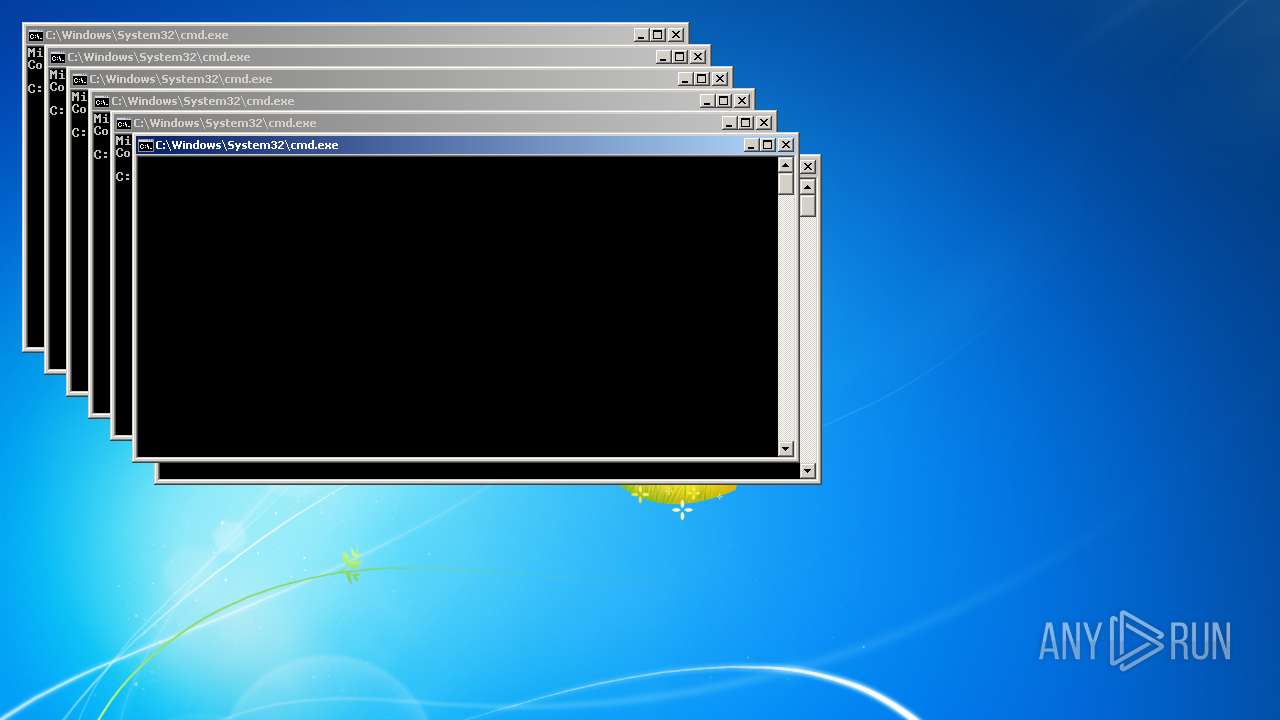
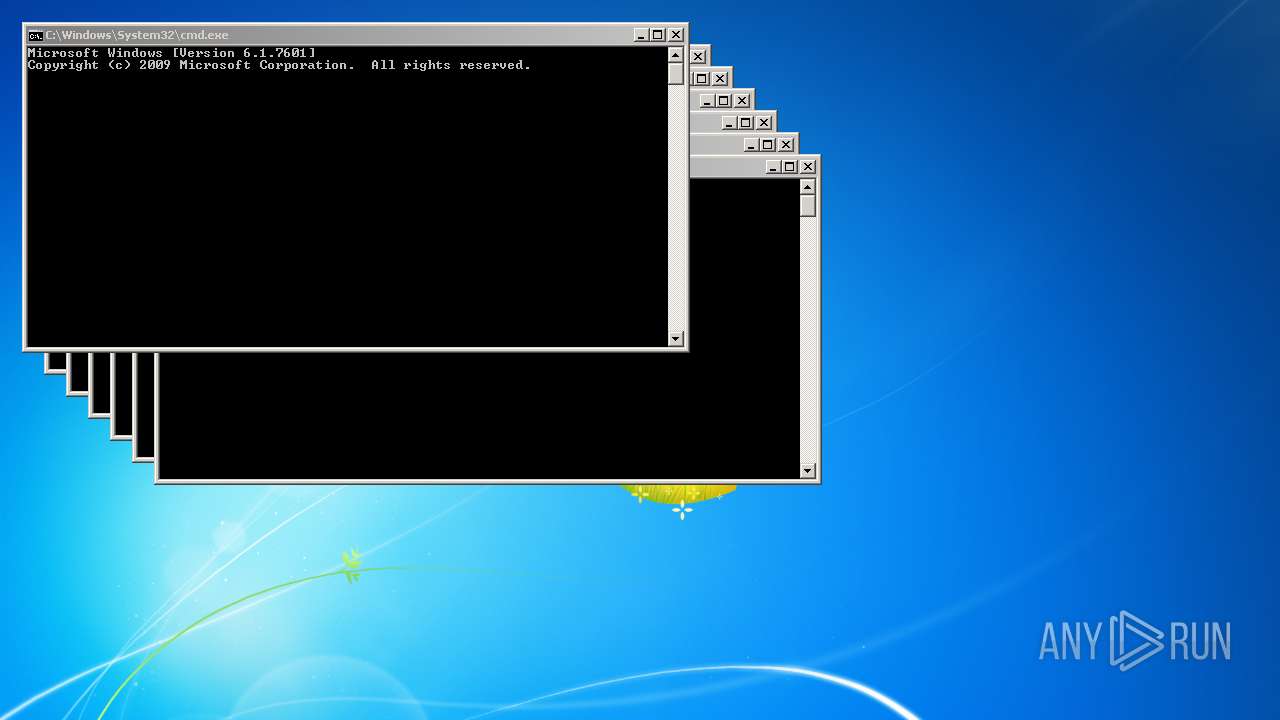
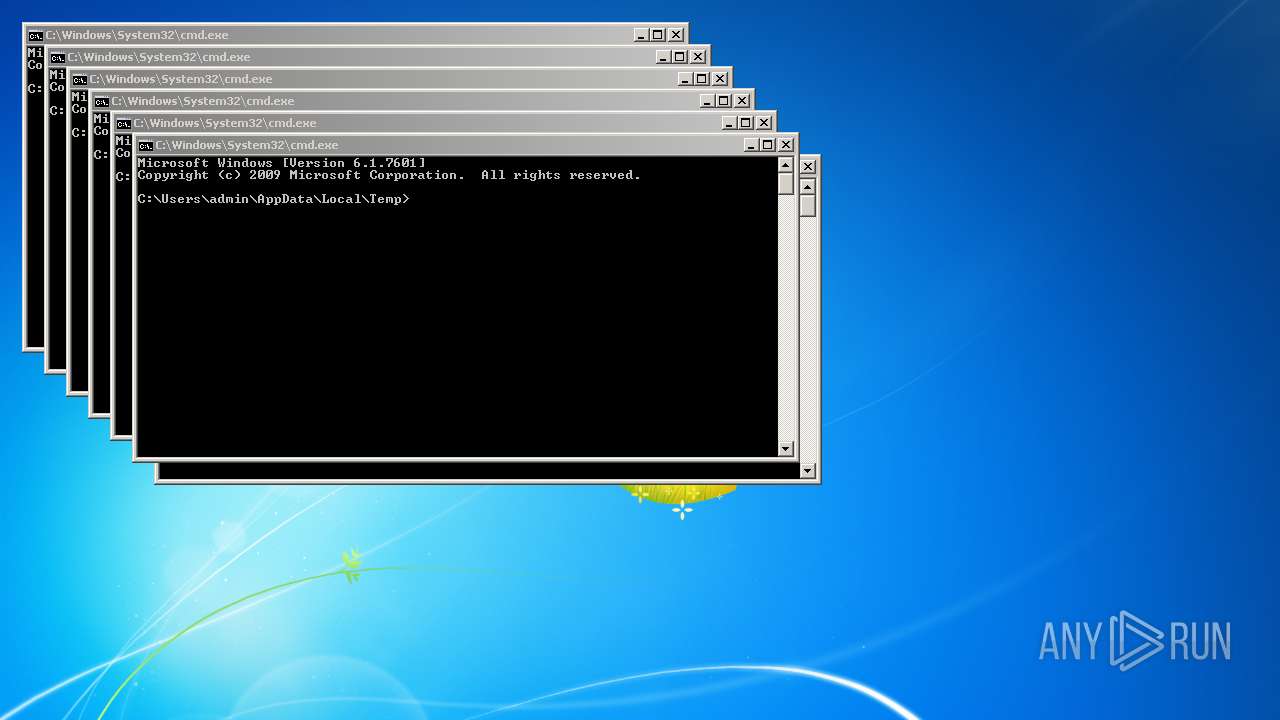
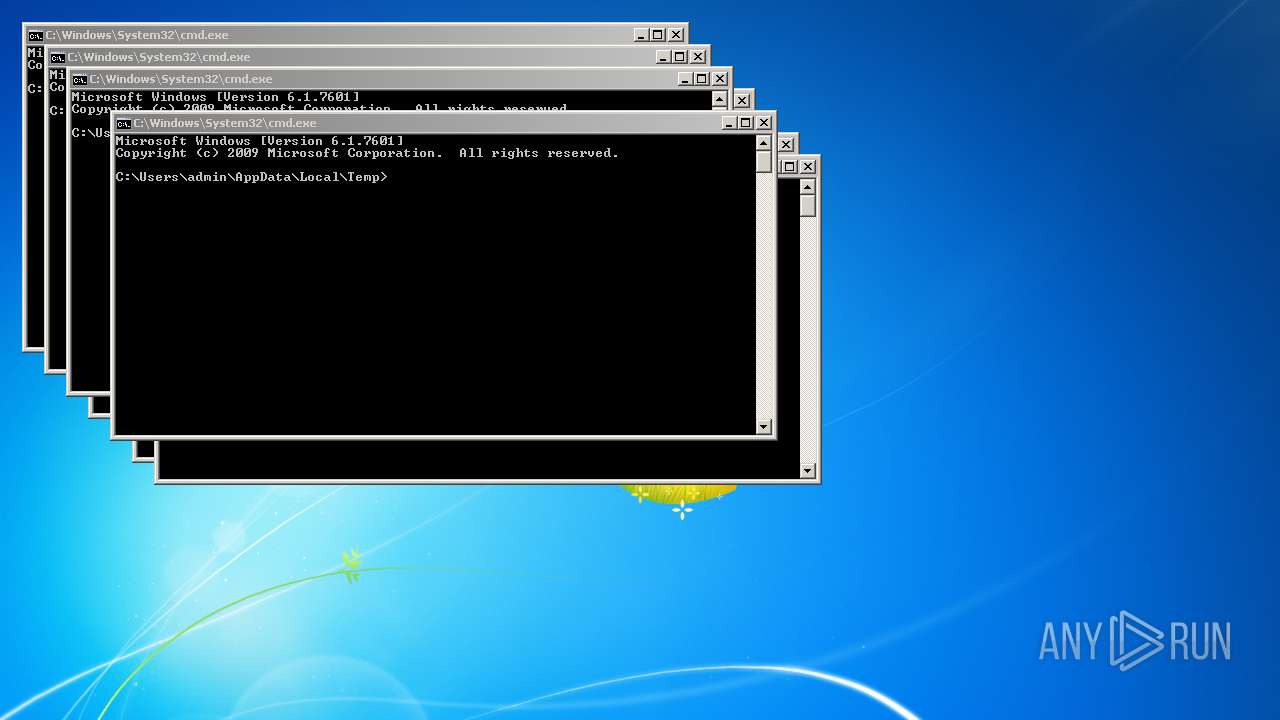
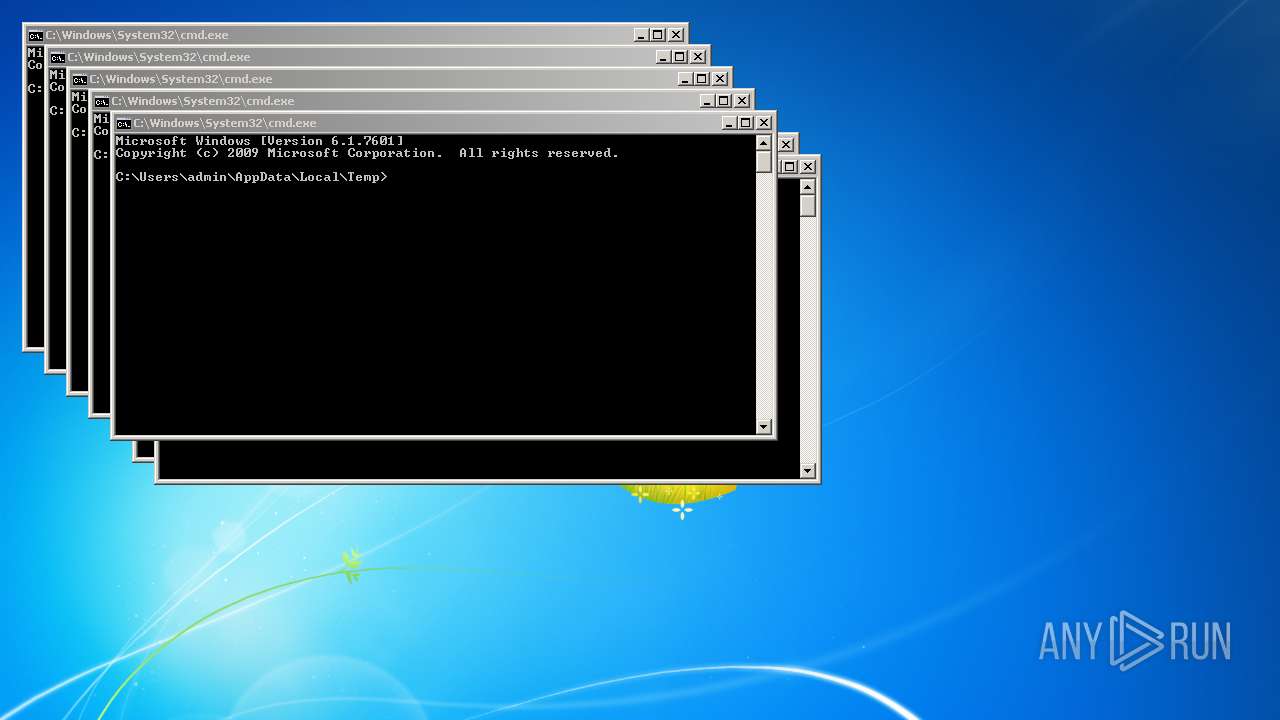
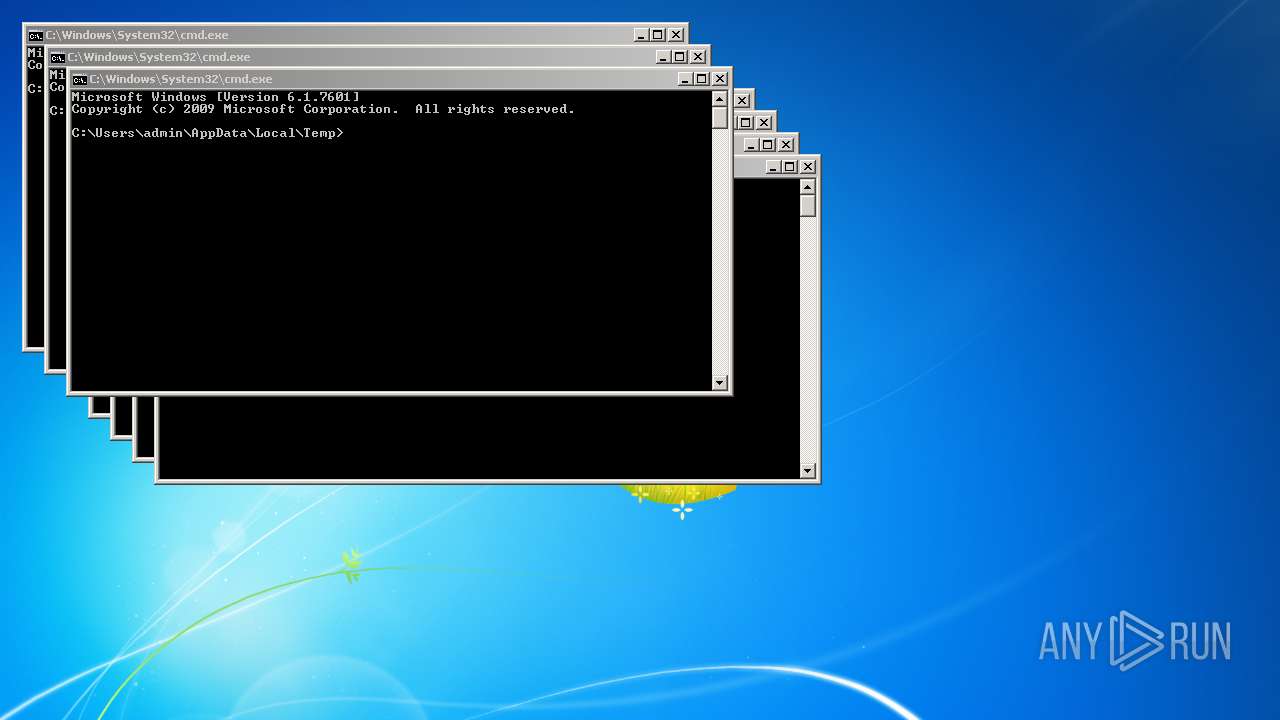
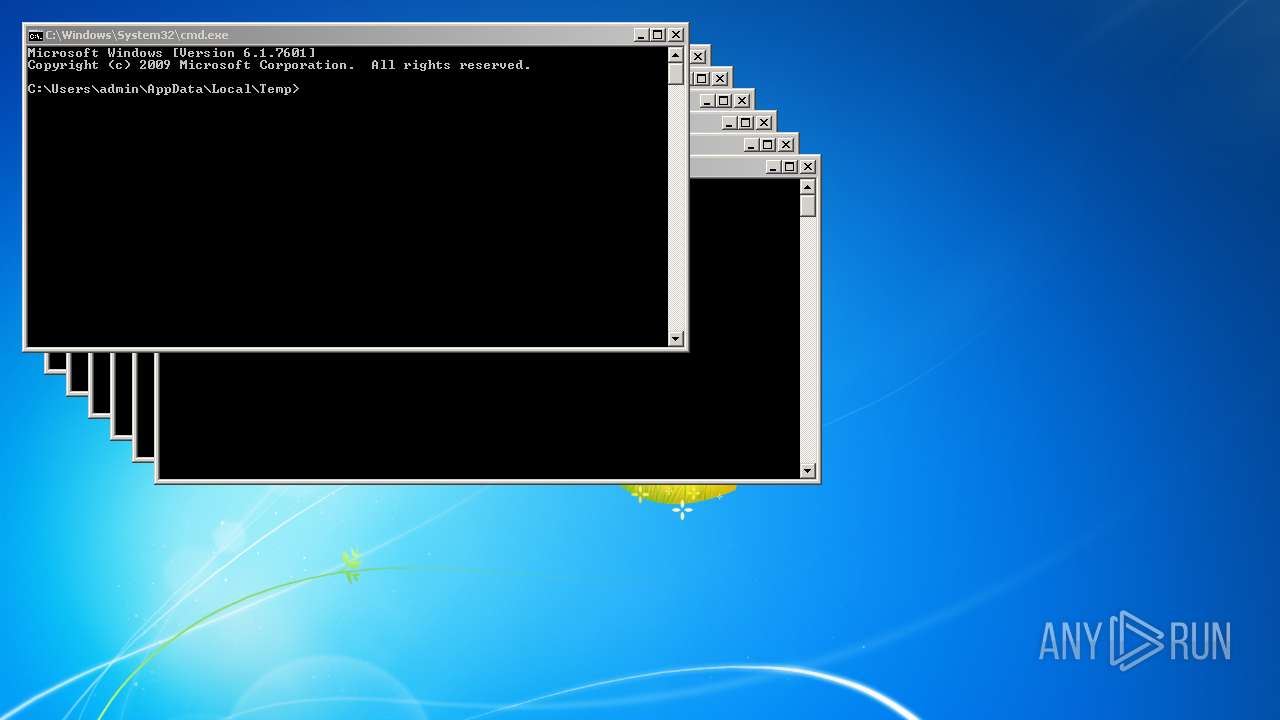
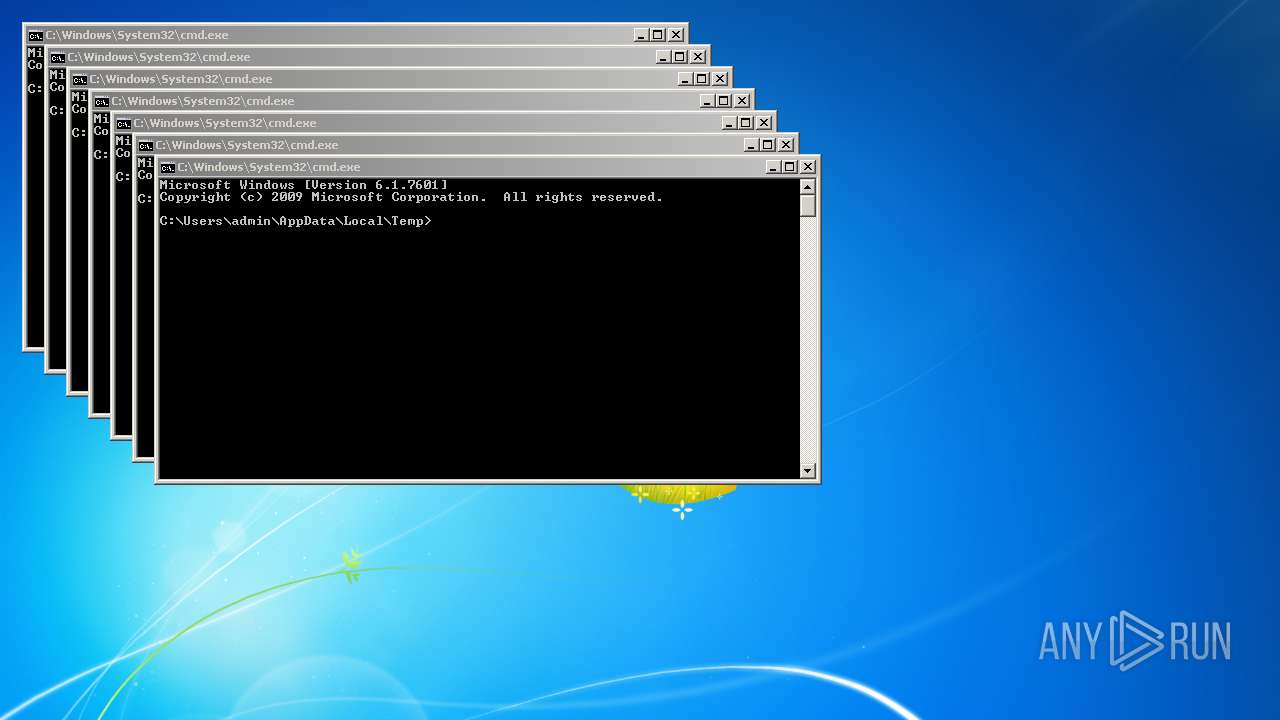
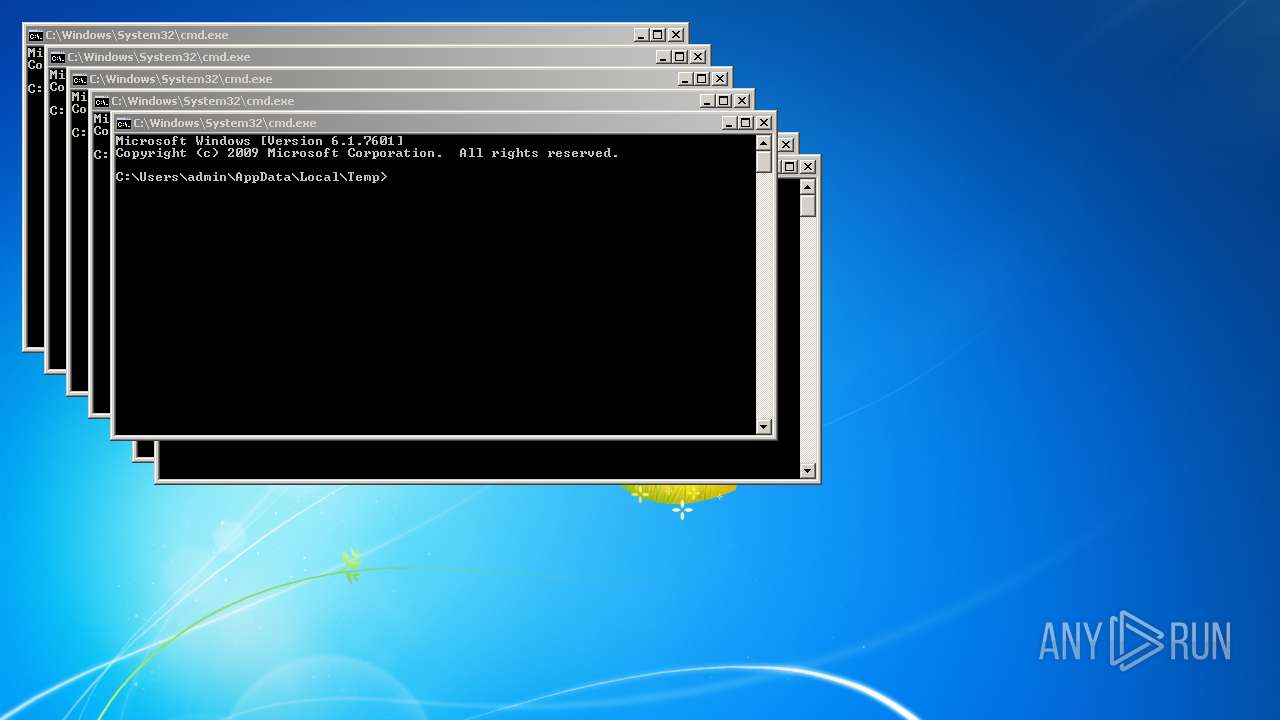
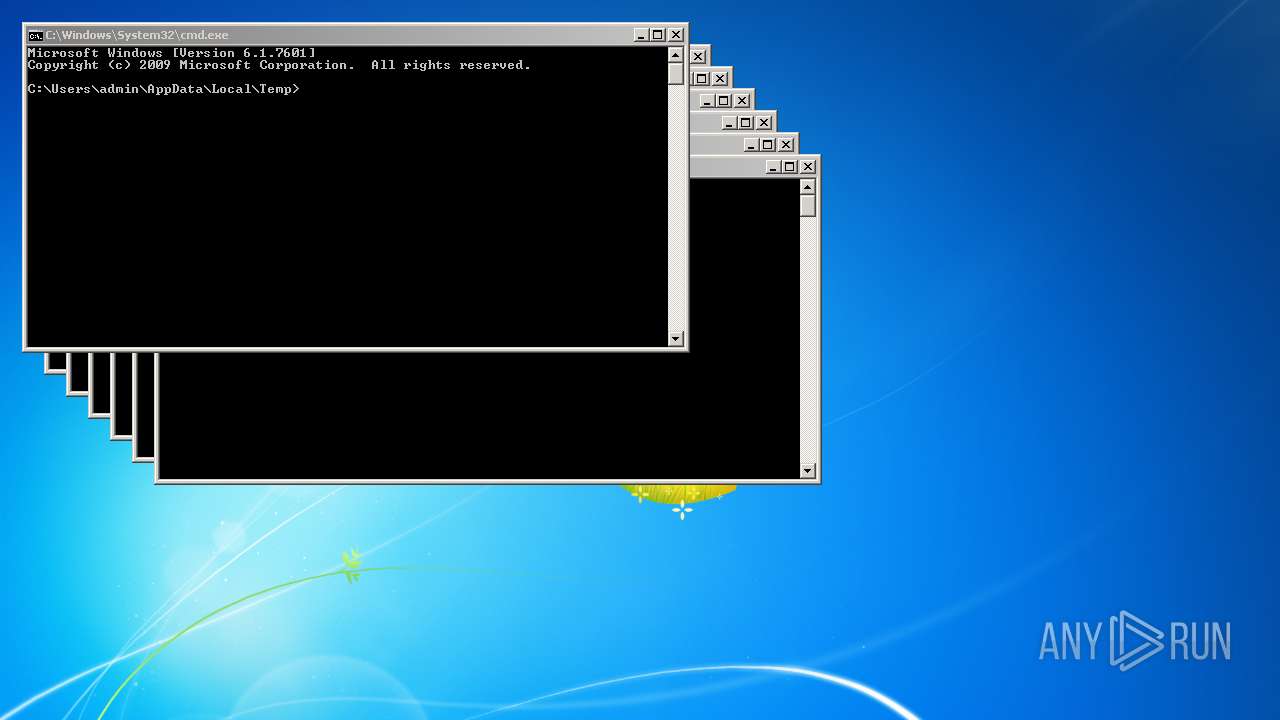
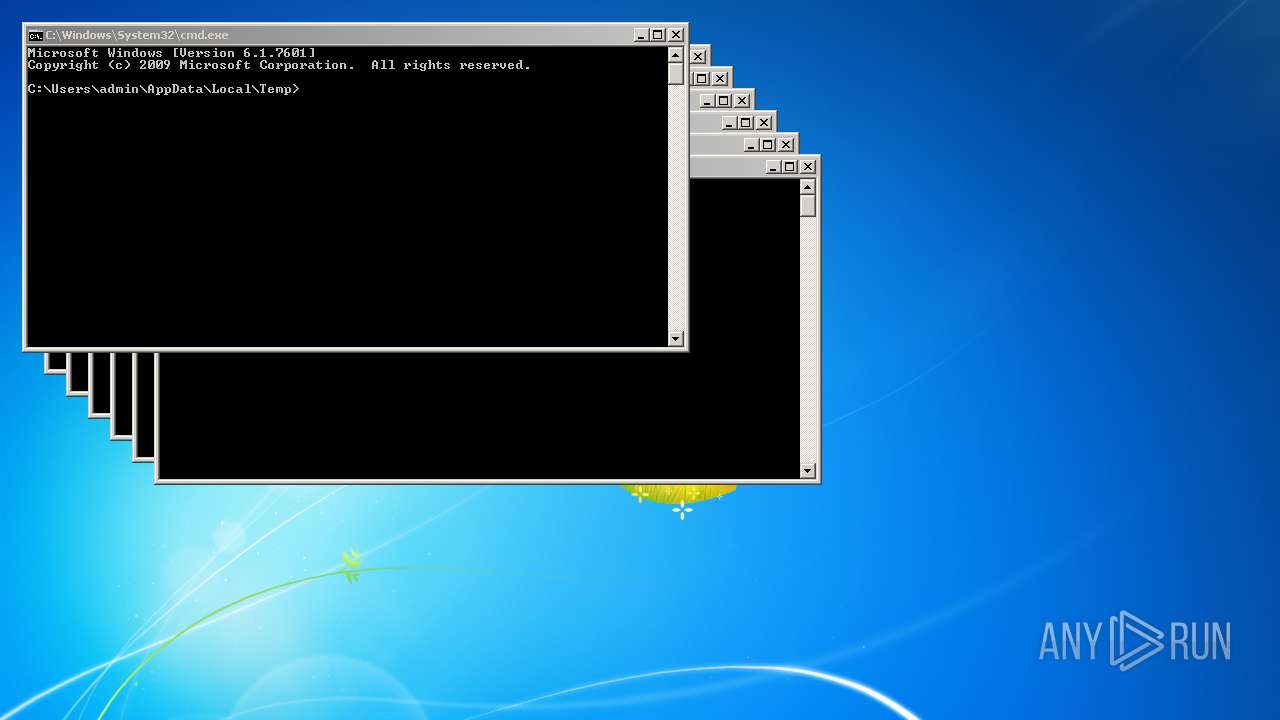
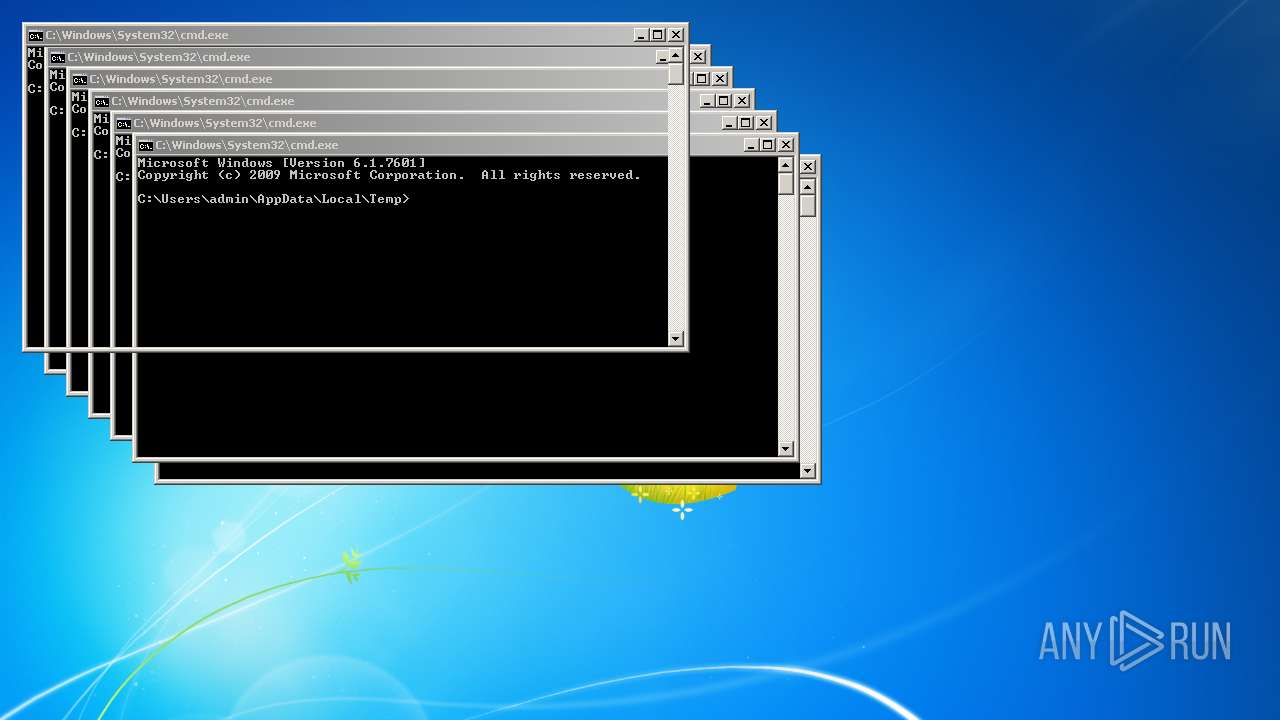
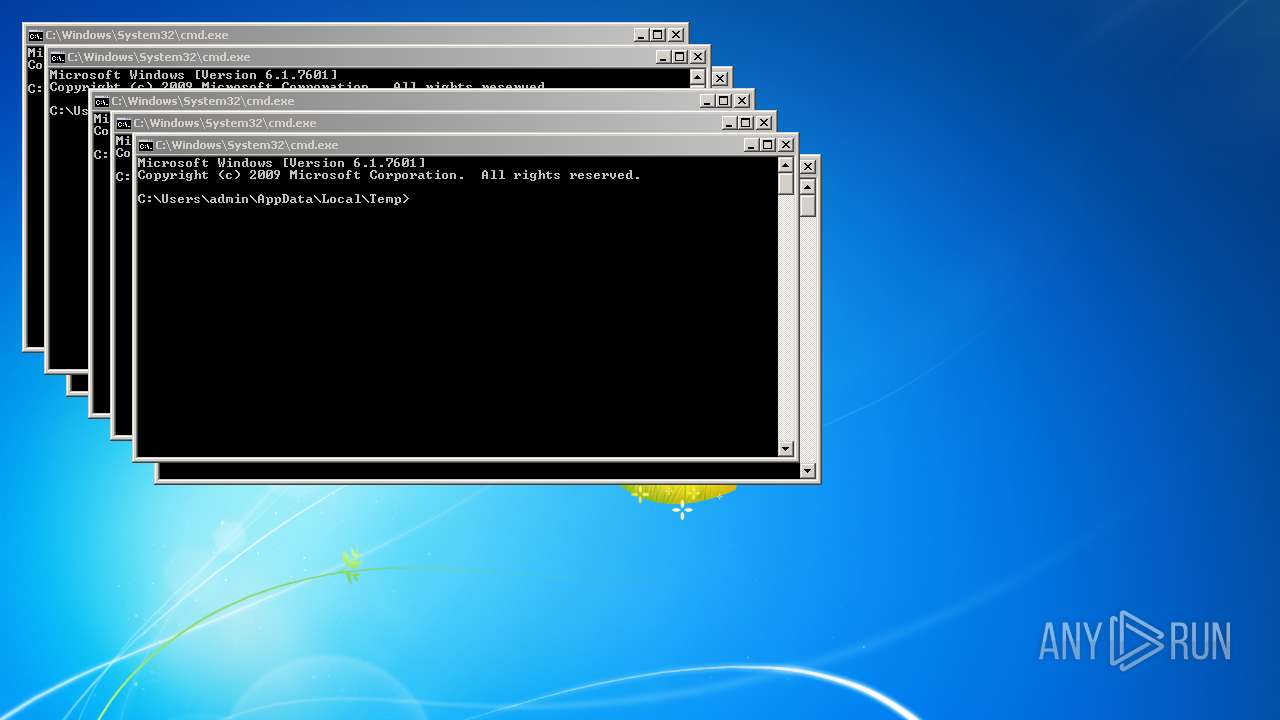
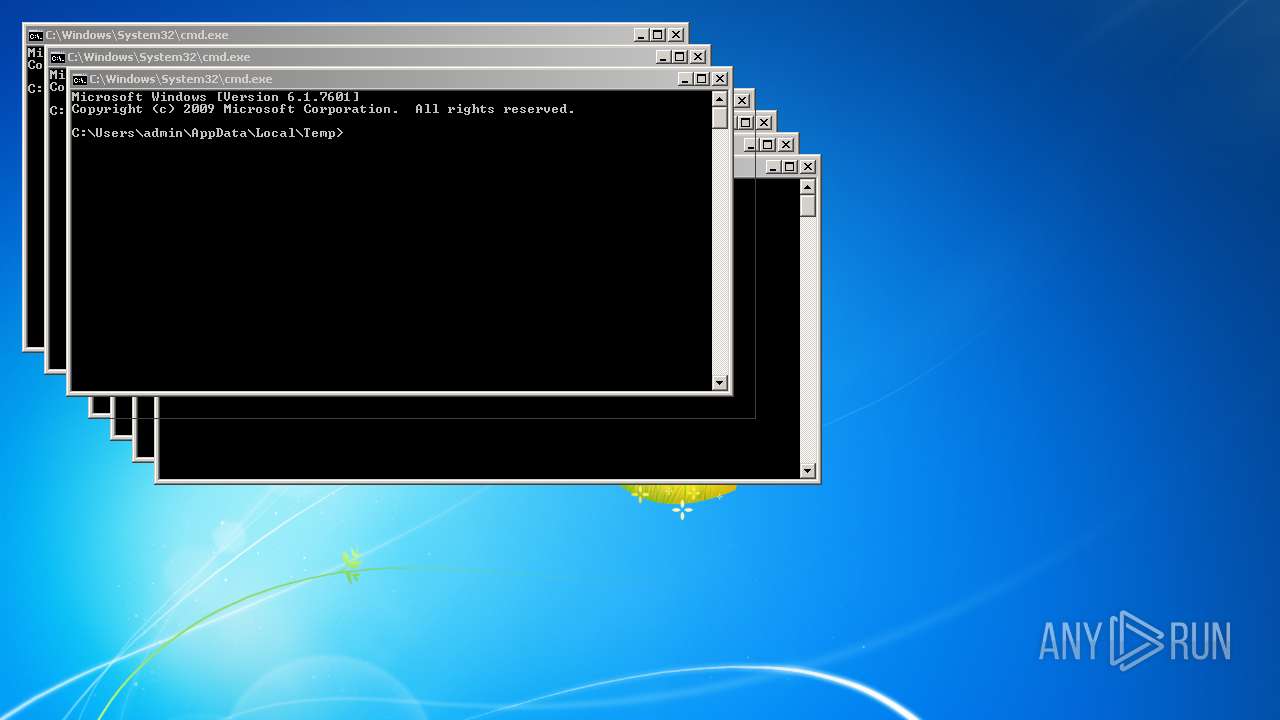
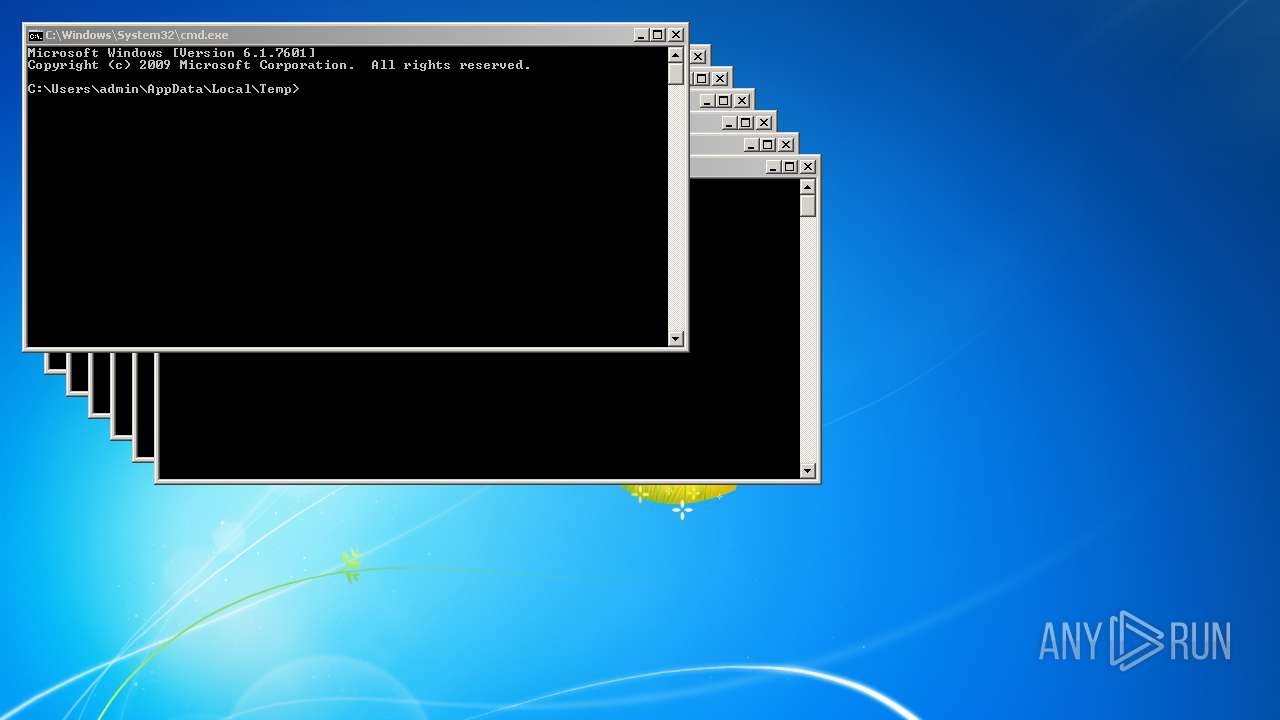
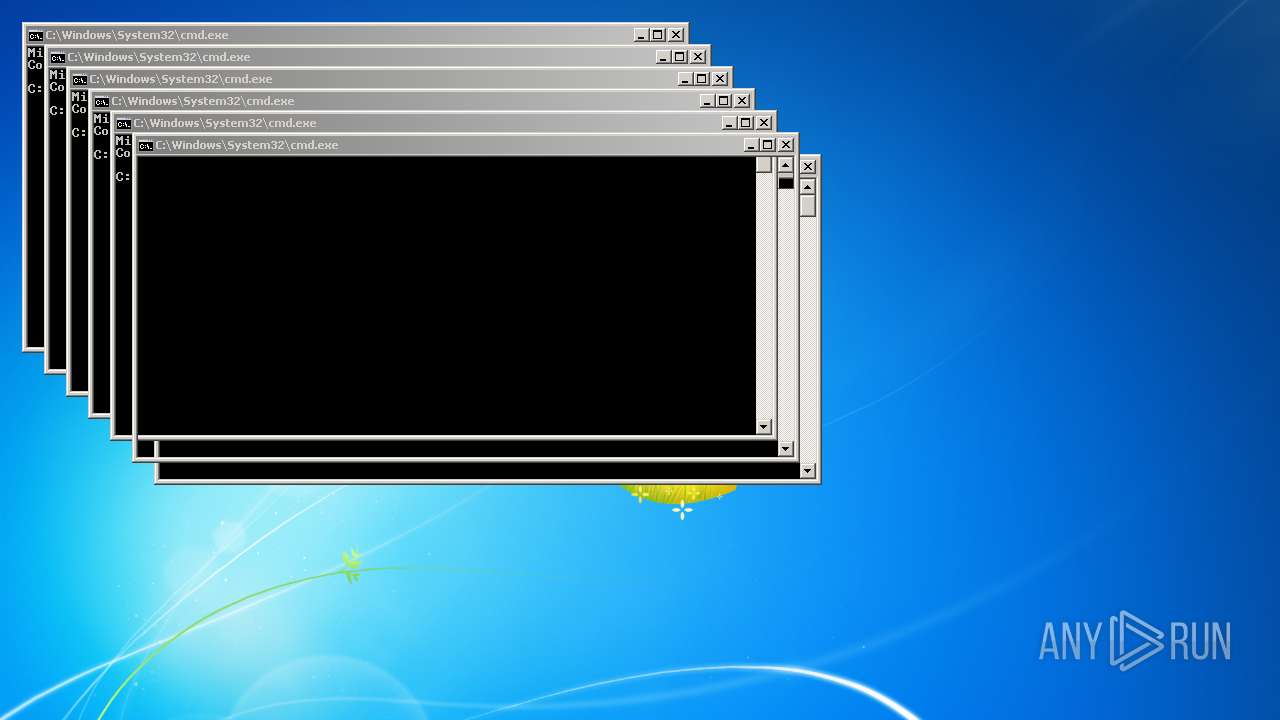
Runs app for hidden code execution
- Client.exe (PID: 3156)
SUSPICIOUS
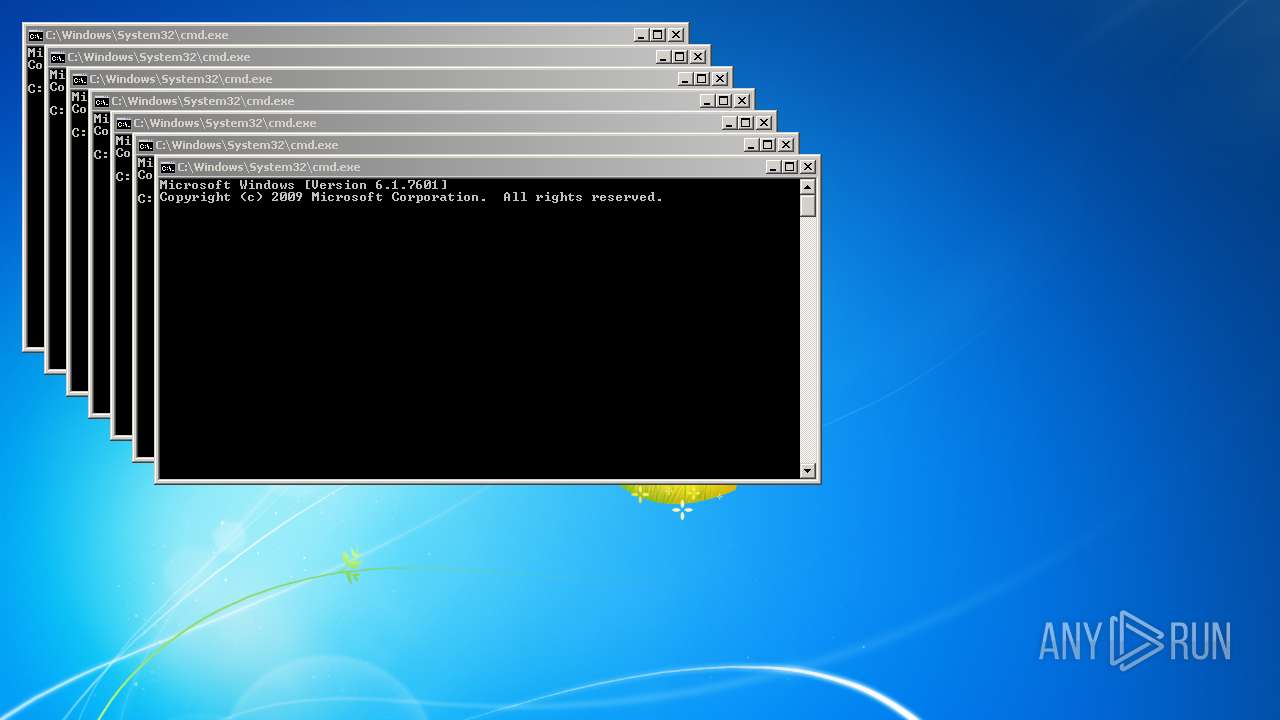
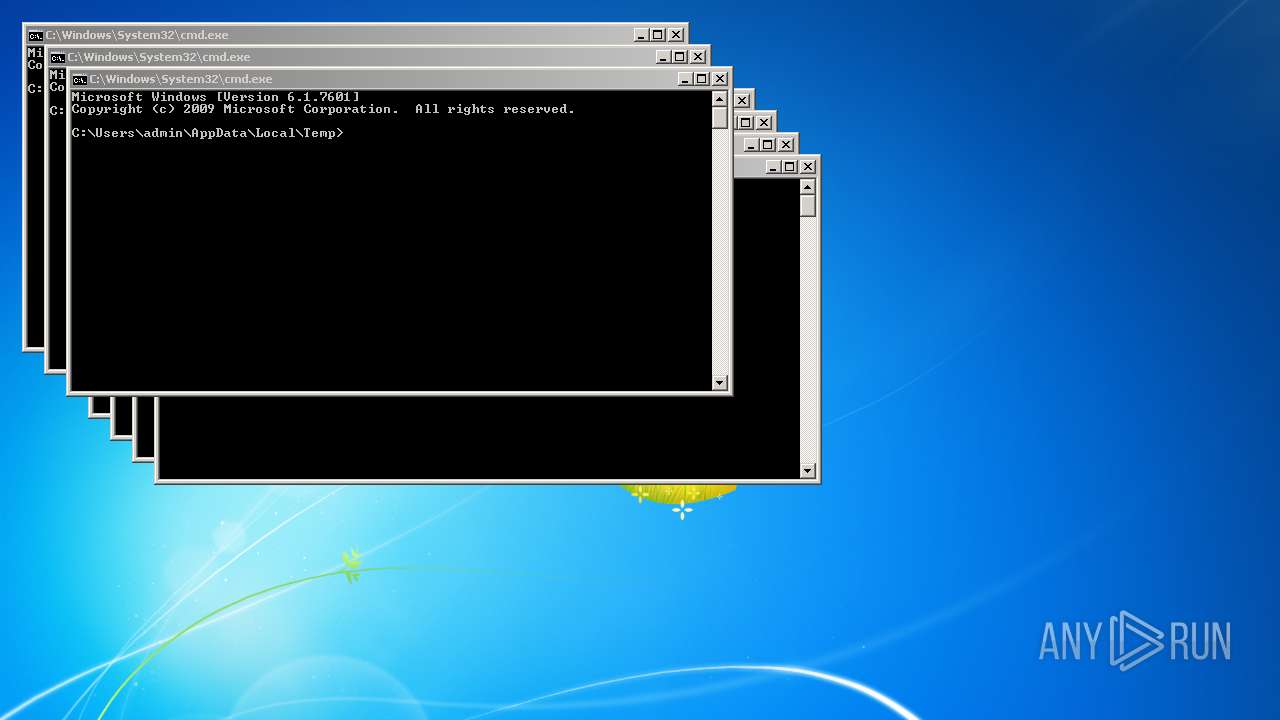
Checks supported languages
- Client.exe (PID: 3156)
- cmd.exe (PID: 3536)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 116)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 524)
- cmd.exe (PID: 408)
- cmd.exe (PID: 1584)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 3280)
- cmd.exe (PID: 3196)
- cmd.exe (PID: 956)
- cmd.exe (PID: 3288)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 2052)
- cmd.exe (PID: 1708)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 2952)
- cmd.exe (PID: 2348)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 2452)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 3668)
- cmd.exe (PID: 3612)
- cmd.exe (PID: 1960)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 1264)
- cmd.exe (PID: 3324)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 3236)
- cmd.exe (PID: 3660)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 2700)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 3496)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 1784)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 3596)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 2200)
- cmd.exe (PID: 1948)
- cmd.exe (PID: 1964)
- cmd.exe (PID: 412)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 3260)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 3744)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 3720)
- cmd.exe (PID: 2592)
- cmd.exe (PID: 2968)
- cmd.exe (PID: 3816)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 3060)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 3108)
- cmd.exe (PID: 448)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 4768)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 5692)
- cmd.exe (PID: 5132)
- cmd.exe (PID: 5940)
- cmd.exe (PID: 6120)
- cmd.exe (PID: 4168)
- cmd.exe (PID: 2640)
- cmd.exe (PID: 2636)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 5256)
- cmd.exe (PID: 4296)
- cmd.exe (PID: 4504)
- cmd.exe (PID: 1112)
- cmd.exe (PID: 2896)
- cmd.exe (PID: 1656)
- cmd.exe (PID: 3440)
- cmd.exe (PID: 5104)
- cmd.exe (PID: 4660)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 5316)
- cmd.exe (PID: 5516)
- cmd.exe (PID: 5688)
- cmd.exe (PID: 5824)
- cmd.exe (PID: 6064)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 4652)
- cmd.exe (PID: 5492)
- cmd.exe (PID: 600)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 4452)
- cmd.exe (PID: 4692)
- cmd.exe (PID: 4880)
- cmd.exe (PID: 5128)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 4428)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 4124)
- cmd.exe (PID: 5220)
- cmd.exe (PID: 4792)
- cmd.exe (PID: 4108)
- cmd.exe (PID: 5888)
- cmd.exe (PID: 6104)
- cmd.exe (PID: 2184)
- cmd.exe (PID: 4404)
- cmd.exe (PID: 4928)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 5908)
- cmd.exe (PID: 4796)
- cmd.exe (PID: 4376)
- cmd.exe (PID: 5176)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 5796)
- cmd.exe (PID: 4180)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 4656)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 5476)
- cmd.exe (PID: 4360)
- cmd.exe (PID: 6020)
- cmd.exe (PID: 4320)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 5916)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 4456)
- cmd.exe (PID: 4508)
- cmd.exe (PID: 5120)
- cmd.exe (PID: 5388)
- cmd.exe (PID: 5232)
- cmd.exe (PID: 6092)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4752)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 4568)
- cmd.exe (PID: 5264)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 4956)
- cmd.exe (PID: 5628)
- cmd.exe (PID: 5792)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 4048)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 4800)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 4392)
- cmd.exe (PID: 5444)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 1492)
- cmd.exe (PID: 5020)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 6396)
- cmd.exe (PID: 6208)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 6944)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 4260)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 5092)
- cmd.exe (PID: 4588)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 6360)
- cmd.exe (PID: 7160)
- cmd.exe (PID: 4396)
- cmd.exe (PID: 6348)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 6544)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 8064)
- cmd.exe (PID: 7140)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 8172)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6880)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 6300)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 4100)
- cmd.exe (PID: 7092)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 6760)
- cmd.exe (PID: 6740)
- cmd.exe (PID: 7100)
- cmd.exe (PID: 7428)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 5864)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 6492)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 6404)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7636)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 6856)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 7284)
- cmd.exe (PID: 7484)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 6476)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 6452)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 8556)
- cmd.exe (PID: 8912)
- cmd.exe (PID: 6820)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 8100)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 8376)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 9104)
- cmd.exe (PID: 9272)
- cmd.exe (PID: 2784)
- cmd.exe (PID: 7876)
Reads the computer name
- Client.exe (PID: 3156)
Reads Environment values
- Client.exe (PID: 3156)
Starts CMD.EXE for commands execution
- Client.exe (PID: 3156)
INFO
Reads settings of System Certificates
- Client.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3156) Client.exe
C2 (2)
7.tcp.eu.ngrok.io
Ports (1)14756
VersionVenomRAT_HVNC 5.0.4
Autorunfalse
Mutexxugzaxzzxxbac
CertificateMIICMzCCAZygAwIBAgIVAKzuRlIrdEiNLAmu9VrDOC0NkctxMA0GCSqGSIb3DQEBDQUAMGcxGDAWBgNVBAMMD1Zlbm9tUkFUIFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIxMDcwMTEyNDA0MVoXDTMyMDQwOTEyNDA0MVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQAD...
Server_Signaturedj5l9sjZVgN4z0tdGsWrYq4SrjzXqVj5yaLAT4NWvFBXO64Ar1DTv8UsWoCDUxsp5VHLn1pPaOVwIdBW9O+lGV92m/5HqDoTqNRXPUPfpq0A4dY2LyYp3IgXxY5ffR2RB9jfOpOBjntcMubeOn3xKO6xRYiGtzGS+ItVPhh6Tzs=
AntiVMfalse
PasteBinnull
bdosfalse
Botnetvenom clients
Aes_Key31c785911cede401be713bdd112ef605ff189e5e6185d5df393ef3a4e117da8c
SaltDcRatByqwqdanchun
Install_Folder%AppData%
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2021-Nov-07 01:16:03 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 5.0.0.3 |
| InternalName: | Client.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Client.exe |
| ProductName: | - |
| ProductVersion: | 5.0.0.3 |
| Assembly Version: | 5.0.0.3 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2021-Nov-07 01:16:03 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 62260 | 62464 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.86787 |
.rsrc | 73728 | 3509 | 3584 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02623 |
.reloc | 81920 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.19253 | 724 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#2) | 5.09187 | 2625 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
629
Monitored processes
299
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 408 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 412 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 448 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 524 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 600 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1040 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1112 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1264 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
10 270
Read events
10 248
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3156) Client.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3156) Client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3156) Client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3156) Client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3156) Client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | Client.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3156 | Client.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3156 | Client.exe | C:\Users\admin\AppData\Local\Temp\TarF1C1.tmp | cat | |
MD5:— | SHA256:— | |||
| 3156 | Client.exe | C:\Users\admin\AppData\Local\Temp\CabF1C0.tmp | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | Client.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c8339810ae0e2b3e | US | compressed | 60.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3156 | Client.exe | 3.67.15.169:14756 | 7.tcp.eu.ngrok.io | AMAZON-02 | DE | malicious |
3156 | Client.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
7.tcp.eu.ngrok.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
2 ETPRO signatures available at the full report