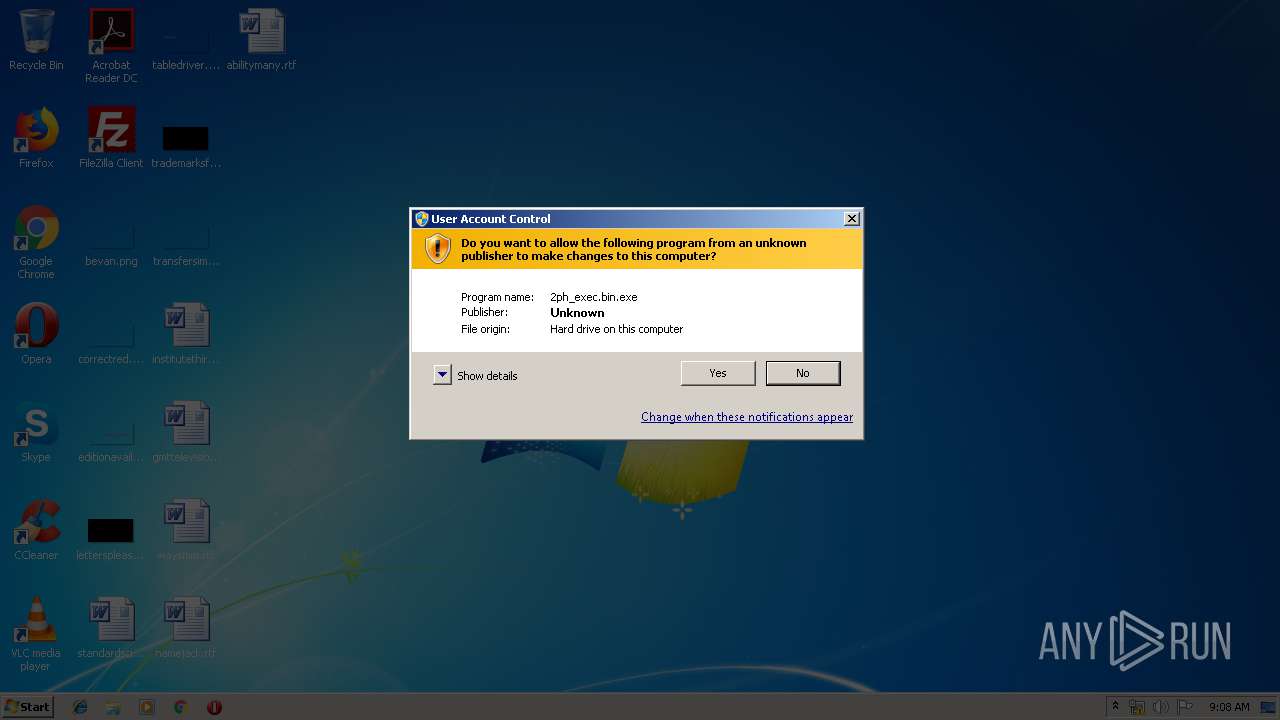
| File name: | 2ph_exec.bin |
| Full analysis: | https://app.any.run/tasks/17b7d253-7400-497d-9cff-593c27f812e1 |
| Verdict: | Malicious activity |
| Threats: | Phobos is a ransomware that locks or encrypts files to demand a ransom. It uses AES encryption with different extensions, which leaves no chance to recover the infected files. |
| Analysis date: | May 24, 2019, 08:08:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 384EF3857536D5CEBD3294016527826D |
| SHA1: | EA63673419F637A5B27E76AFF7093E6AEA21AF94 |
| SHA256: | FE09ED8D78D213346D50966CD4835D3071E39C9C13C19FC106590A235A0CB907 |
| SSDEEP: | 1536:SkGB8nHbKUvryElSpi8jCZGcqDKlKnr8daTFpJCOA:SFBMHRvrAjCZmKcnr8IJCt |
MALICIOUS
Changes the autorun value in the registry
- 2ph_exec.bin.exe (PID: 2128)
- 2ph_exec.bin.exe (PID: 2500)
Runs app for hidden code execution
- 2ph_exec.bin.exe (PID: 2500)
Turns off the firewall via NETSH.EXE
- cmd.exe (PID: 3384)
Deletes shadow copies
- cmd.exe (PID: 3128)
Writes to a start menu file
- 2ph_exec.bin.exe (PID: 2500)
- 2ph_exec.bin.exe (PID: 2128)
Renames files like Ransomware
- 2ph_exec.bin.exe (PID: 2500)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3128)
SUSPICIOUS
Executable content was dropped or overwritten
- 2ph_exec.bin.exe (PID: 2128)
- 2ph_exec.bin.exe (PID: 2500)
Application launched itself
- 2ph_exec.bin.exe (PID: 2128)
Creates files in the user directory
- 2ph_exec.bin.exe (PID: 2128)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3384)
Starts CMD.EXE for commands execution
- 2ph_exec.bin.exe (PID: 2500)
Executed as Windows Service
- vssvc.exe (PID: 3808)
Creates files in the program directory
- 2ph_exec.bin.exe (PID: 2500)
INFO
Dropped object may contain Bitcoin addresses
- 2ph_exec.bin.exe (PID: 2500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:14 12:57:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 39936 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6652 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-May-2019 10:57:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-May-2019 10:57:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00009A08 | 0x00009C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51008 |
.rdata | 0x0000B000 | 0x000025E0 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.90307 |
.data | 0x0000E000 | 0x00001E44 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.22188 |
.rsrc | 0x00010000 | 0x000001B4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09036 |
.reloc | 0x00011000 | 0x00000A8E | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.2251 |
.cdata | 0x00012000 | 0x00002E7C | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.84038 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MPR.dll |
SHELL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
50
Monitored processes
11
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | wmic shadowcopy delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | bcdedit /set {default} recoveryenabled no | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\AppData\Local\Temp\2ph_exec.bin.exe" | C:\Users\admin\AppData\Local\Temp\2ph_exec.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2236 | netsh advfirewall set currentprofile state off | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\Temp\2ph_exec.bin.exe" | C:\Users\admin\AppData\Local\Temp\2ph_exec.bin.exe | 2ph_exec.bin.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3124 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3128 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | 2ph_exec.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3292 | netsh firewall set opmode mode=disable | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | 2ph_exec.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3808 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
494
Read events
385
Write events
109
Delete events
0
Modification events
| (PID) Process: | (2128) 2ph_exec.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2128) 2ph_exec.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2128) 2ph_exec.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 2ph_exec.bin |
Value: C:\Users\admin\AppData\Local\2ph_exec.bin.exe | |||
| (PID) Process: | (2500) 2ph_exec.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 2ph_exec.bin |
Value: C:\Users\admin\AppData\Local\2ph_exec.bin.exe | |||
| (PID) Process: | (2500) 2ph_exec.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 2ph_exec.bin |
Value: C:\Users\admin\AppData\Local\2ph_exec.bin.exe | |||
| (PID) Process: | (2236) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2236) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2236) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2236) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2236) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
Executable files
4
Suspicious files
228
Text files
0
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2500 | 2ph_exec.bin.exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelLR.cab.id[C4BA3647-1104].[kew07@qq.com].actin | — | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\PptLR.cab.id[C4BA3647-1104].[kew07@qq.com].actin | — | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\autoexec.bat.id[C4BA3647-1104].[kew07@qq.com].actin | binary | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\programdata\microsoft\windows\start menu\programs\startup\2ph_exec.bin.exe | executable | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\desktop.ini.id[C4BA3647-1104].[kew07@qq.com].actin | binary | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\config.sys.id[C4BA3647-1104].[kew07@qq.com].actin | binary | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\Setup.xml.id[C4BA3647-1104].[kew07@qq.com].actin | binary | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\PubLR.cab.id[C4BA3647-1104].[kew07@qq.com].actin | — | |
MD5:— | SHA256:— | |||
| 2500 | 2ph_exec.bin.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\SIWW.cab.id[C4BA3647-1104].[kew07@qq.com].actin | — | |
MD5:— | SHA256:— | |||
| 2128 | 2ph_exec.bin.exe | C:\users\admin\appdata\roaming\microsoft\windows\start menu\programs\startup\2ph_exec.bin.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report