| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/b24b6ad6-3c50-4e69-b7d1-6e6f0d4aec80 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | November 12, 2024, 21:48:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, Nullsoft Installer self-extracting archive, 7 sections |
| MD5: | D5DAF25A86BEBE285DA31E8E3ED4A2B6 |
| SHA1: | 4D77DDE16058FBB8B5F2C8AF72C532E8C9C700DA |
| SHA256: | FDC9DF9F23184762D3B7BB921CAC852E4ED5A348D8B64C8EB60F158AF33A6AB6 |
| SSDEEP: | 98304:5KENt9QLzvj2bXanH4rmXPprbyN4RMsPkZiSQn+0+KyXhrWl2fNIDw8PtiSfPYv2:9OyKVRH7 |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2172)
- explorer.exe (PID: 6208)
HIJACKLOADER has been detected (YARA)
- Setup.exe (PID: 3276)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2172)
- vbc.exe (PID: 3792)
Bypass execution policy to execute commands
- powershell.exe (PID: 5612)
- powershell.exe (PID: 4164)
Changes powershell execution policy (Bypass)
- vbc.exe (PID: 3792)
- powershell.exe (PID: 5612)
Actions looks like stealing of personal data
- vbc.exe (PID: 3792)
Changes the autorun value in the registry
- C4LVOY.pif (PID: 2796)
AMADEY has been detected (SURICATA)
- explorer.exe (PID: 6208)
SUSPICIOUS
Starts application with an unusual extension
- Setup.exe (PID: 3276)
- vbc.exe (PID: 3792)
Executable content was dropped or overwritten
- Setup.exe (PID: 3276)
- vbc.exe (PID: 3792)
- C4LVOY.pif (PID: 2796)
The process executes VB scripts
- more.com (PID: 6860)
- C4LVOY.pif (PID: 2796)
Contacting a server suspected of hosting an CnC
- vbc.exe (PID: 3792)
- svchost.exe (PID: 2172)
- explorer.exe (PID: 6208)
Starts POWERSHELL.EXE for commands execution
- vbc.exe (PID: 3792)
- powershell.exe (PID: 5612)
The process executes Powershell scripts
- vbc.exe (PID: 3792)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5612)
Application launched itself
- powershell.exe (PID: 5612)
Base64-obfuscated command line is found
- powershell.exe (PID: 5612)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 5612)
There is functionality for communication over UDP network (YARA)
- OZQCWM8Z2UBM5PR99MIJK90J437YG.exe (PID: 1580)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 5612)
Checks whether the computer is part of a domain (POWERSHELL)
- powershell.exe (PID: 4164)
Drops a file with a rarely used extension (PIF)
- vbc.exe (PID: 3792)
Possible Social Engineering Attempted
- svchost.exe (PID: 2172)
Checks for Java to be installed
- nc.exe (PID: 1168)
INFO
Creates files or folders in the user directory
- Setup.exe (PID: 3276)
- vbc.exe (PID: 3792)
Create files in a temporary directory
- Setup.exe (PID: 3276)
- nc.exe (PID: 1168)
- more.com (PID: 6860)
- vbc.exe (PID: 3792)
- OZQCWM8Z2UBM5PR99MIJK90J437YG.exe (PID: 1580)
- choice.exe (PID: 2588)
Reads the computer name
- Setup.exe (PID: 3276)
- more.com (PID: 6860)
- OZQCWM8Z2UBM5PR99MIJK90J437YG.exe (PID: 1580)
- vbc.exe (PID: 3792)
- C4LVOY.pif (PID: 2796)
Checks supported languages
- more.com (PID: 6860)
- Setup.exe (PID: 3276)
- nc.exe (PID: 1168)
- OZQCWM8Z2UBM5PR99MIJK90J437YG.exe (PID: 1580)
- vbc.exe (PID: 3792)
- C4LVOY.pif (PID: 2796)
Reads the software policy settings
- vbc.exe (PID: 3792)
Creates files in the program directory
- nc.exe (PID: 1168)
Checks proxy server information
- powershell.exe (PID: 5612)
- explorer.exe (PID: 6208)
Disables trace logs
- powershell.exe (PID: 5612)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4164)
Reads mouse settings
- C4LVOY.pif (PID: 2796)
Reads Windows Product ID
- C4LVOY.pif (PID: 2796)
Reads CPU info
- C4LVOY.pif (PID: 2796)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:07:08 05:26:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 910336 |
| InitializedDataSize: | 5261312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcdb10 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.6.4.1 |
| ProductVersionNumber: | 11.6.4.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Quick Access Popup (Windows launcher) |
| FileVersion: | 11.6.4.1 |
| InternalName: | Quick Access Popup |
| LegalCopyright: | (c) Jean Lalonde since 2013 |
| CompanyName: | Jean Lalonde |
| OriginalFileName: | QuickAccessPopup.exe |
| ProductName: | Quick Access Popup |
| ProductVersion: | 11.6.4.1 |
Total processes
181
Monitored processes
56
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
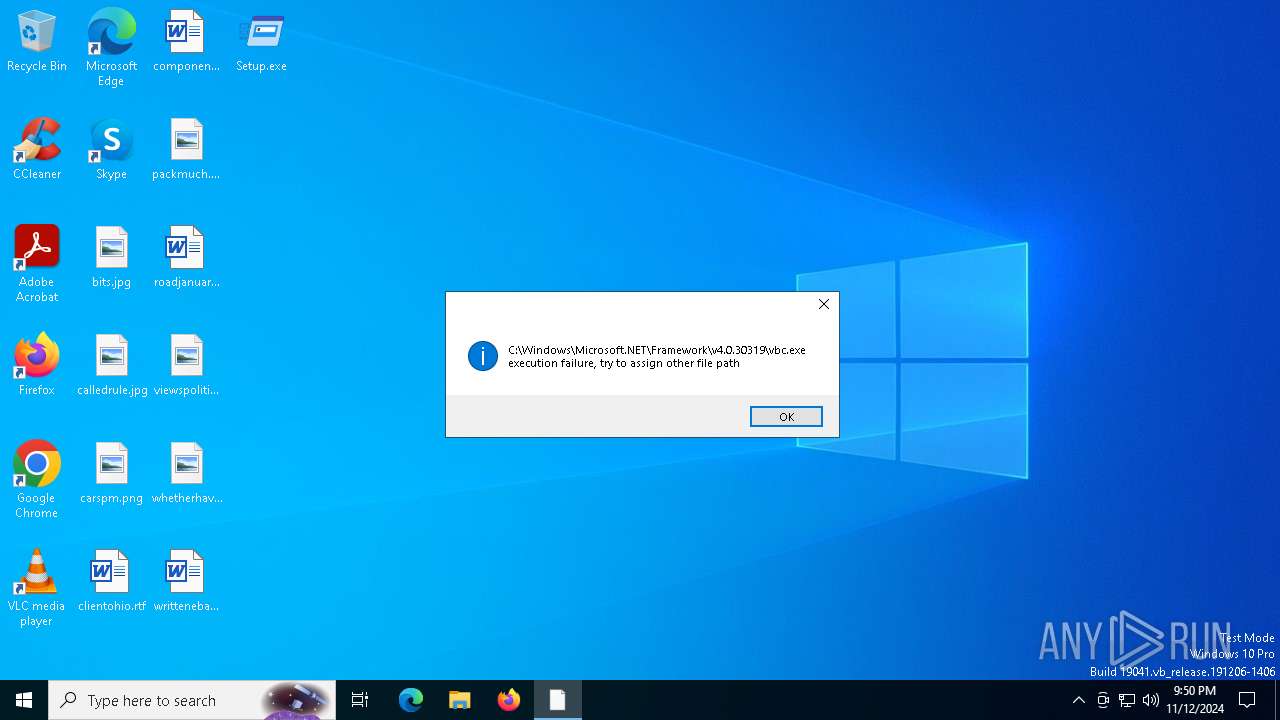
| 824 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | C4LVOY.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 1168 | C:\Users\admin\AppData\Roaming\Kmbeac\VFPMQBBYEKVQDIFXKPEBGPMG\nc.exe | C:\Users\admin\AppData\Roaming\Kmbeac\VFPMQBBYEKVQDIFXKPEBGPMG\nc.exe | — | Setup.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.3810.9 Modules
| |||||||||||||||
| 1180 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | C4LVOY.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\AppData\Local\Temp\OZQCWM8Z2UBM5PR99MIJK90J437YG.exe" | C:\Users\admin\AppData\Local\Temp\OZQCWM8Z2UBM5PR99MIJK90J437YG.exe | vbc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1584 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | C4LVOY.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 1764 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | C4LVOY.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 1788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2068 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | C4LVOY.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 2100 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | C4LVOY.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 732
Read events
10 713
Write events
19
Delete events
0
Modification events
| (PID) Process: | (1580) OZQCWM8Z2UBM5PR99MIJK90J437YG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\PSPad |
| Operation: | write | Name: | Ready5 |
Value: 0 | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5612) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
4
Suspicious files
4
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6860 | more.com | C:\Users\admin\AppData\Local\Temp\emrfp | — | |
MD5:— | SHA256:— | |||
| 3792 | vbc.exe | C:\Users\admin\AppData\Roaming\T5GS3T.dif | — | |
MD5:— | SHA256:— | |||
| 2796 | C4LVOY.pif | C:\ehfecbk\dbabech.a3x | — | |
MD5:— | SHA256:— | |||
| 2588 | choice.exe | C:\Users\admin\AppData\Local\Temp\msdbynmqyivdei | — | |
MD5:— | SHA256:— | |||
| 3792 | vbc.exe | C:\Users\admin\AppData\Local\Temp\OZQCWM8Z2UBM5PR99MIJK90J437YG.exe | executable | |
MD5:D7D783D594300F6DDCC79989DD7CEE7F | SHA256:DA63A2D8FFFB5FCCD40785E59C3E50804456395BBA9A1B4B2BECBD8988360754 | |||
| 3276 | Setup.exe | C:\Users\admin\AppData\Local\Temp\7b40ddda | image | |
MD5:F329F51D945F116C1188F1A5E7F197F7 | SHA256:0A68E58C2E4EF165847E7E3265B7BD27C388196179080923C7EAFB7A32BB1FBE | |||
| 4164 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:8A67E57408FB214A1165BE9C25466070 | SHA256:FE3763B0BAE13A490F6547E6D37DF052BCCB9E9DD90FBD31003D05E117D5F3C3 | |||
| 4164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bnil5efr.jr0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1580 | OZQCWM8Z2UBM5PR99MIJK90J437YG.exe | C:\Users\admin\AppData\Local\Temp\89c2c13a | binary | |
MD5:EFFF6235DDA2068470191FC545CA832C | SHA256:3F86E6B09AF69168590D002036AE2F067987FED762950081A987FEB7258FBA58 | |||
| 5612 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iapgxumm.er0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
53
DNS requests
29
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4700 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1172 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1172 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6208 | explorer.exe | POST | — | 172.67.213.173:80 | http://moviecentral-petparade.com/g9jvjfd73/index.php | unknown | — | — | whitelisted |
6208 | explorer.exe | POST | — | 172.67.213.173:80 | http://moviecentral-petparade.com/g9jvjfd73/index.php | unknown | — | — | whitelisted |
5616 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4700 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (wellnesshub-chefparadise .shop) |
3792 | vbc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (wellnesshub-chefparadise .shop in TLS SNI) |
3792 | vbc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (wellnesshub-chefparadise .shop in TLS SNI) |
3792 | vbc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (wellnesshub-chefparadise .shop in TLS SNI) |
3792 | vbc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (wellnesshub-chefparadise .shop in TLS SNI) |
3792 | vbc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (wellnesshub-chefparadise .shop in TLS SNI) |
3792 | vbc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (wellnesshub-chefparadise .shop in TLS SNI) |
2172 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious Domain by Cloudflare (moviecentral-petparade .com) |
6208 | explorer.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
4 ETPRO signatures available at the full report