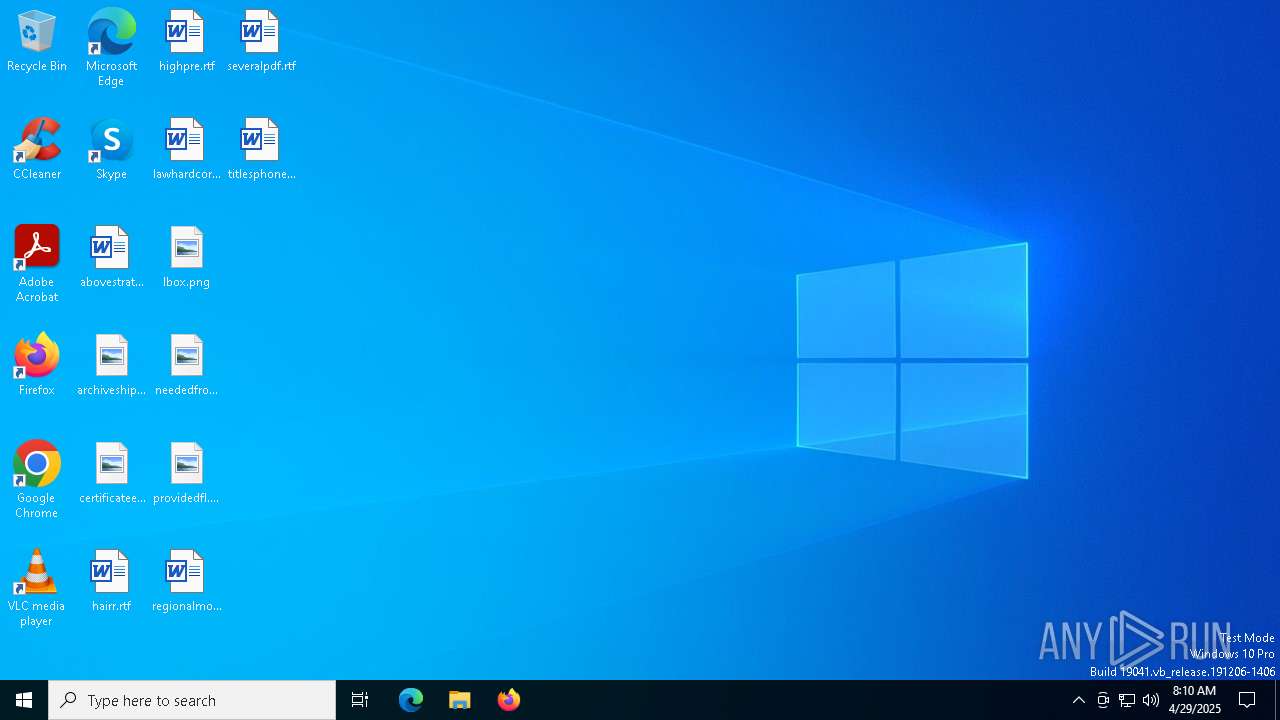
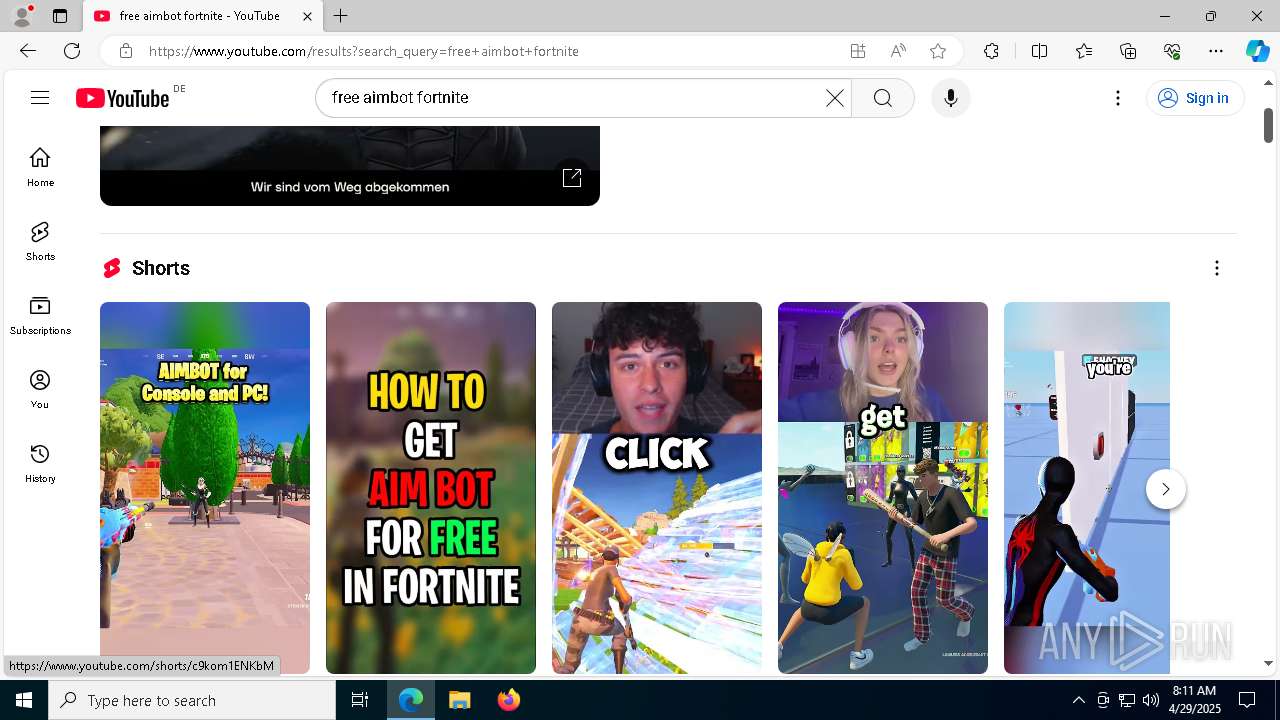
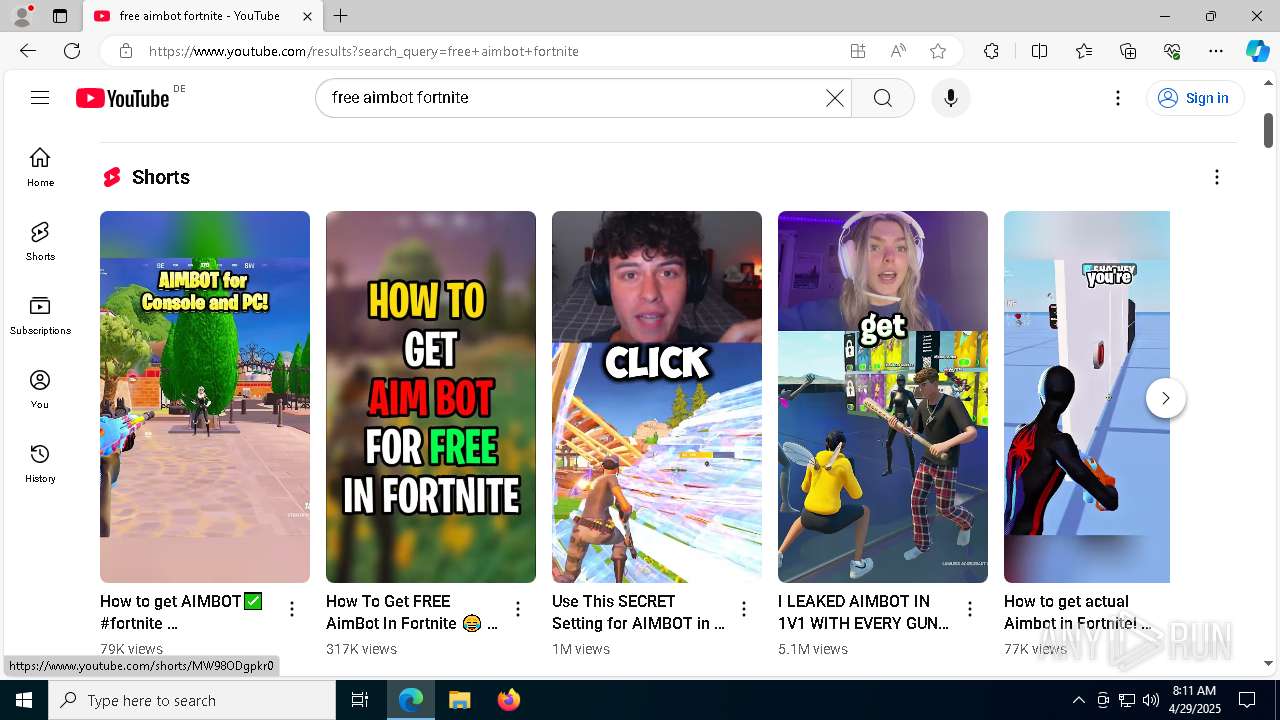
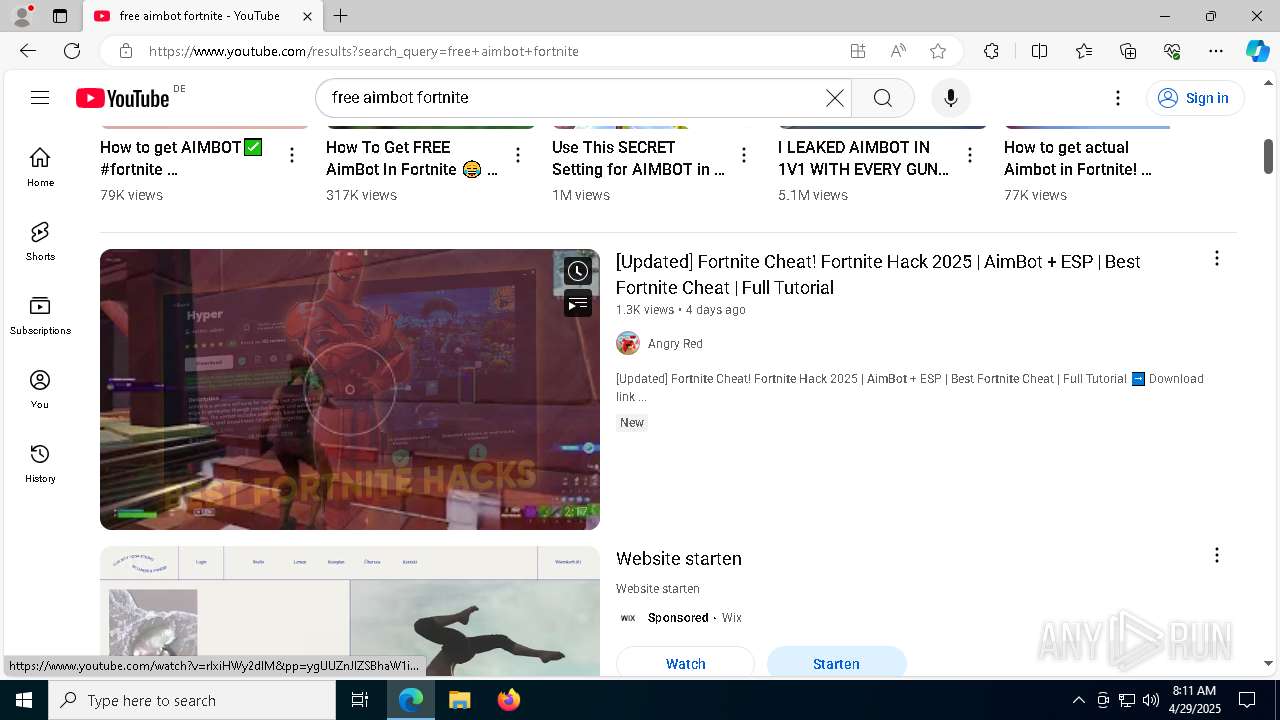
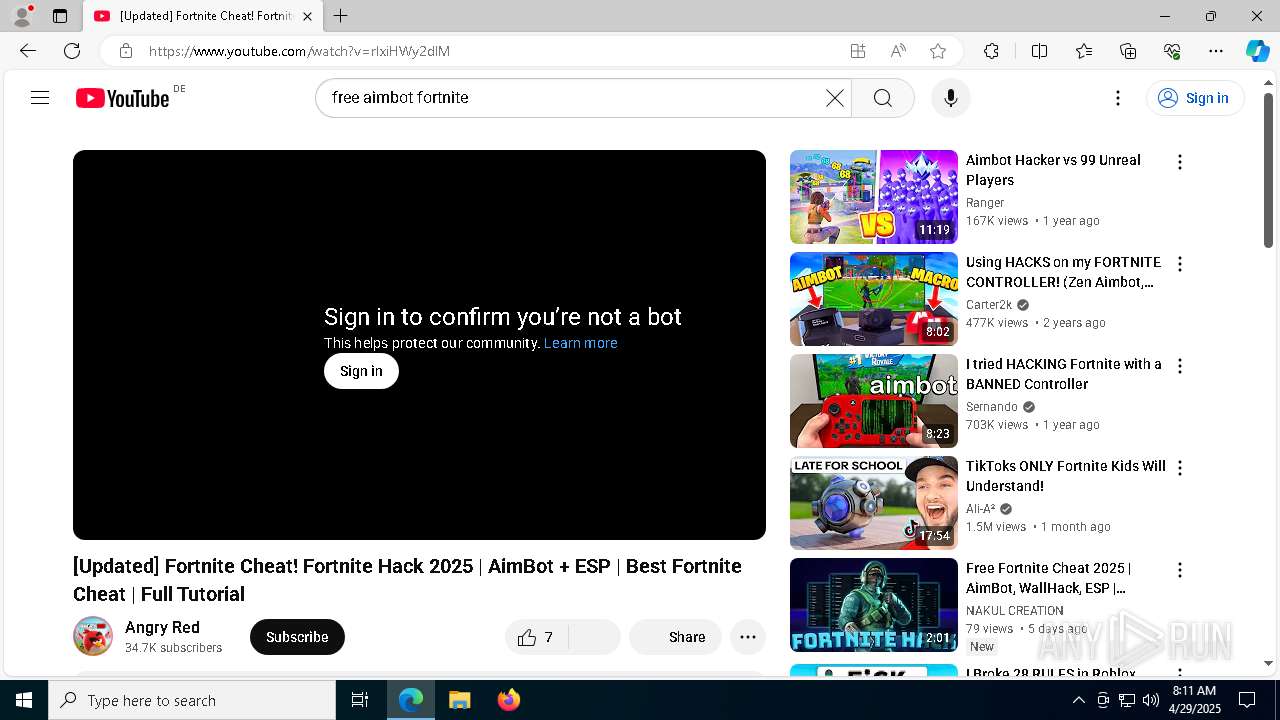
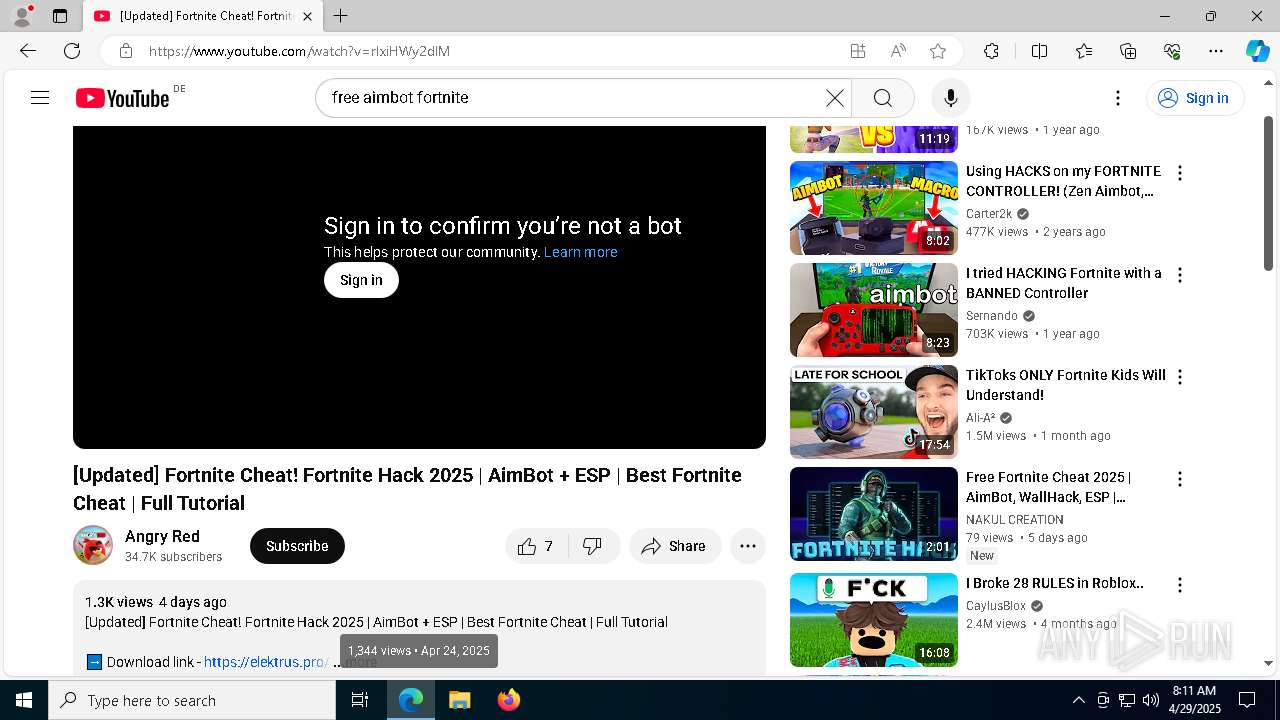
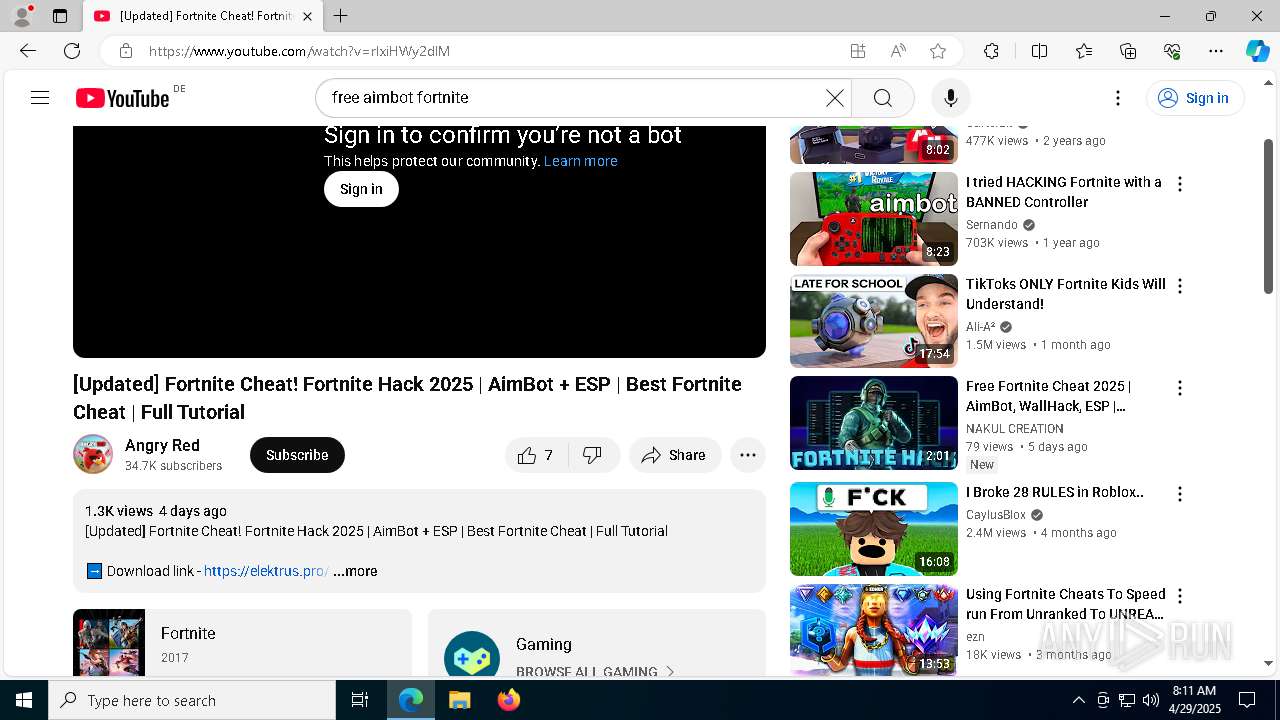
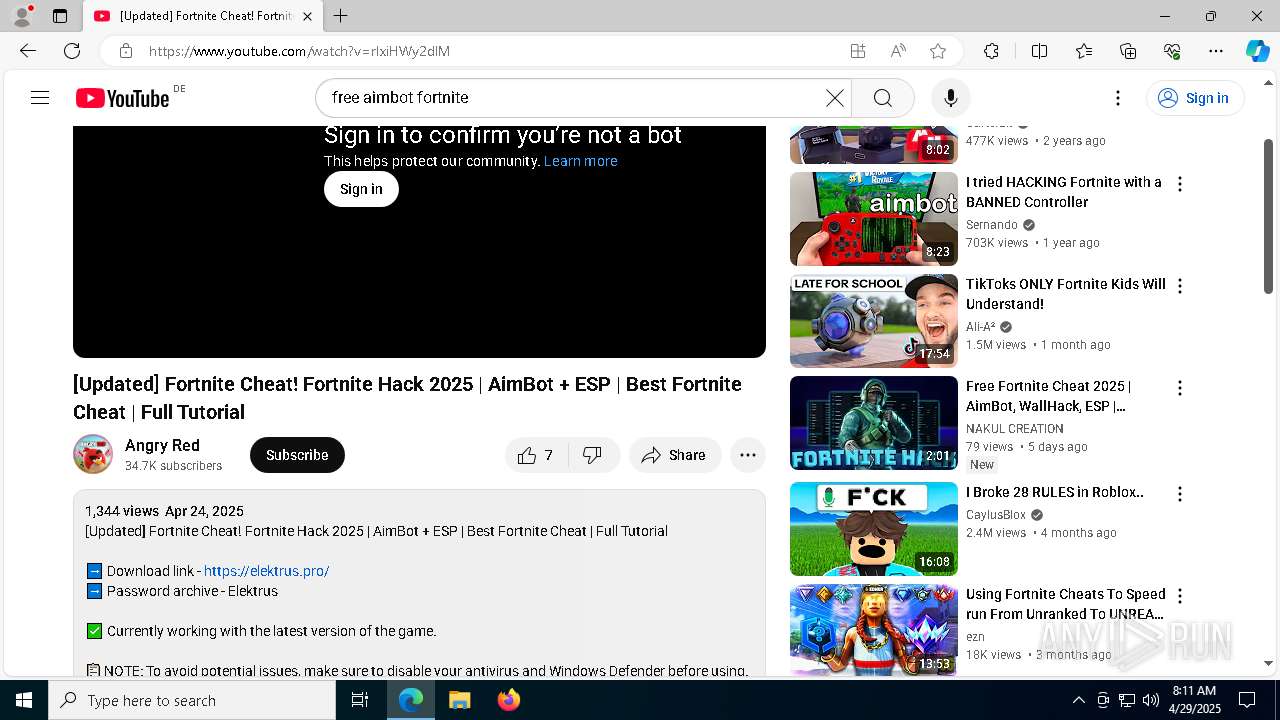
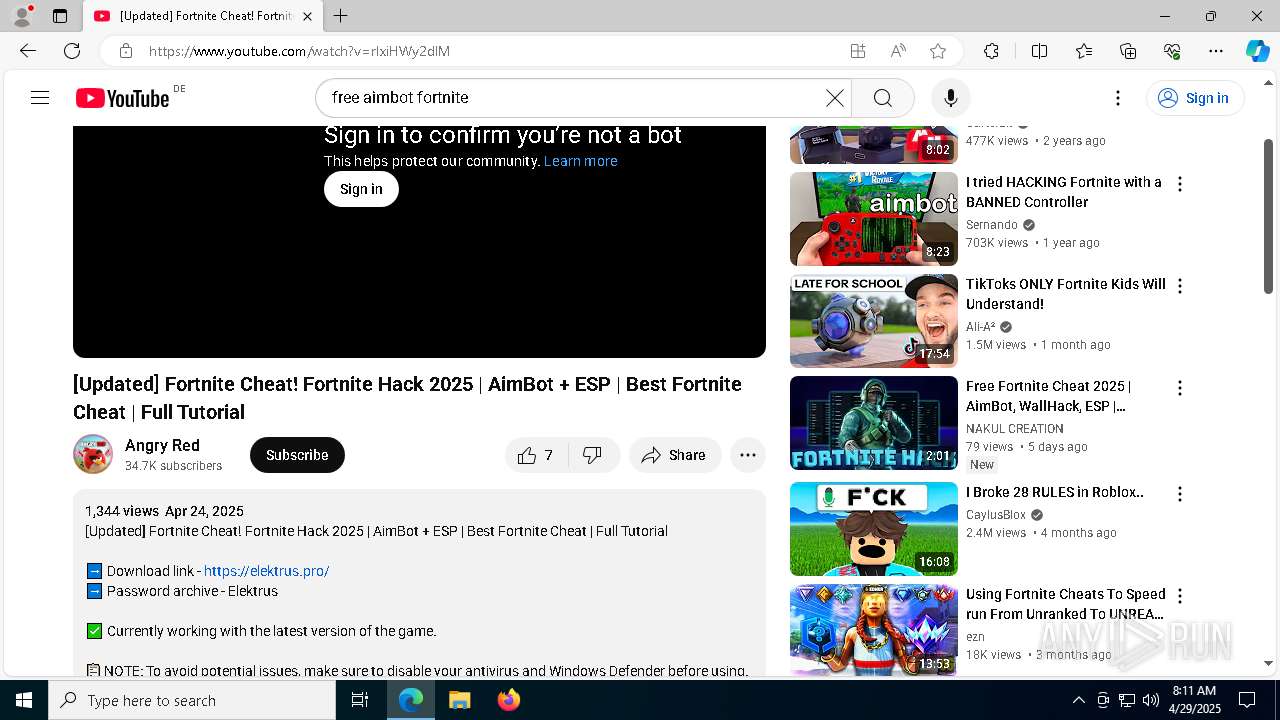
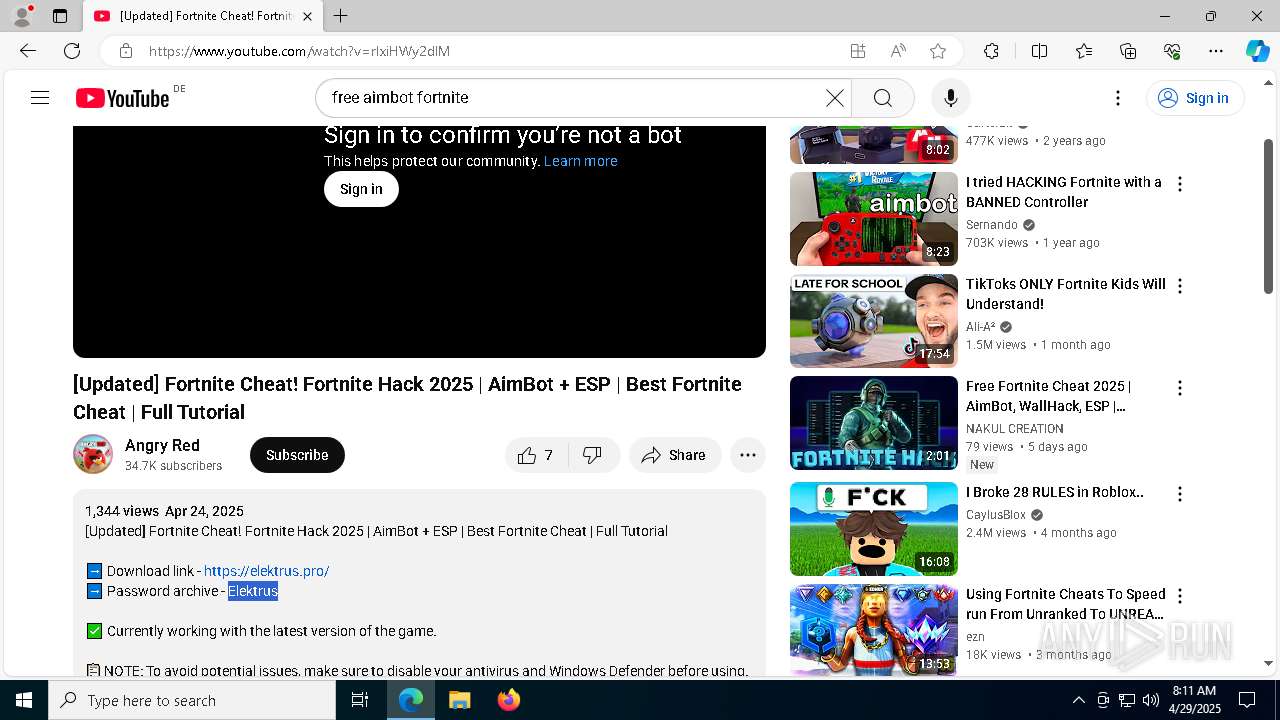
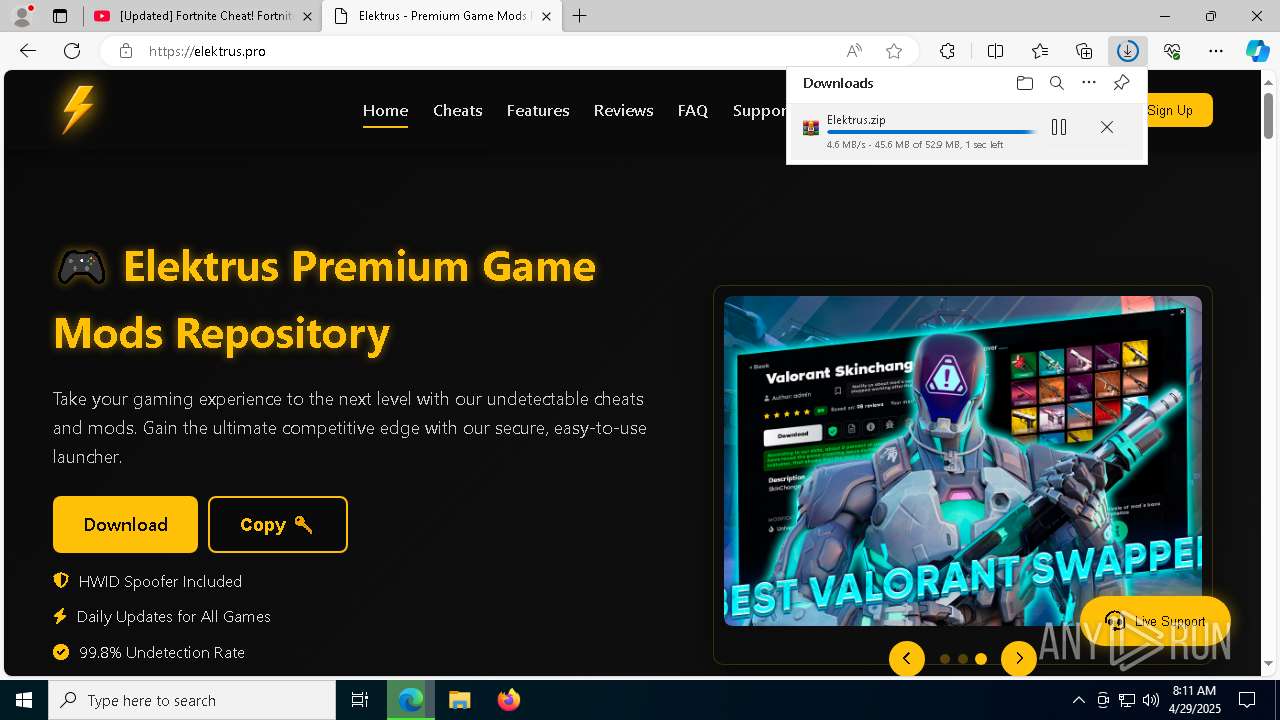
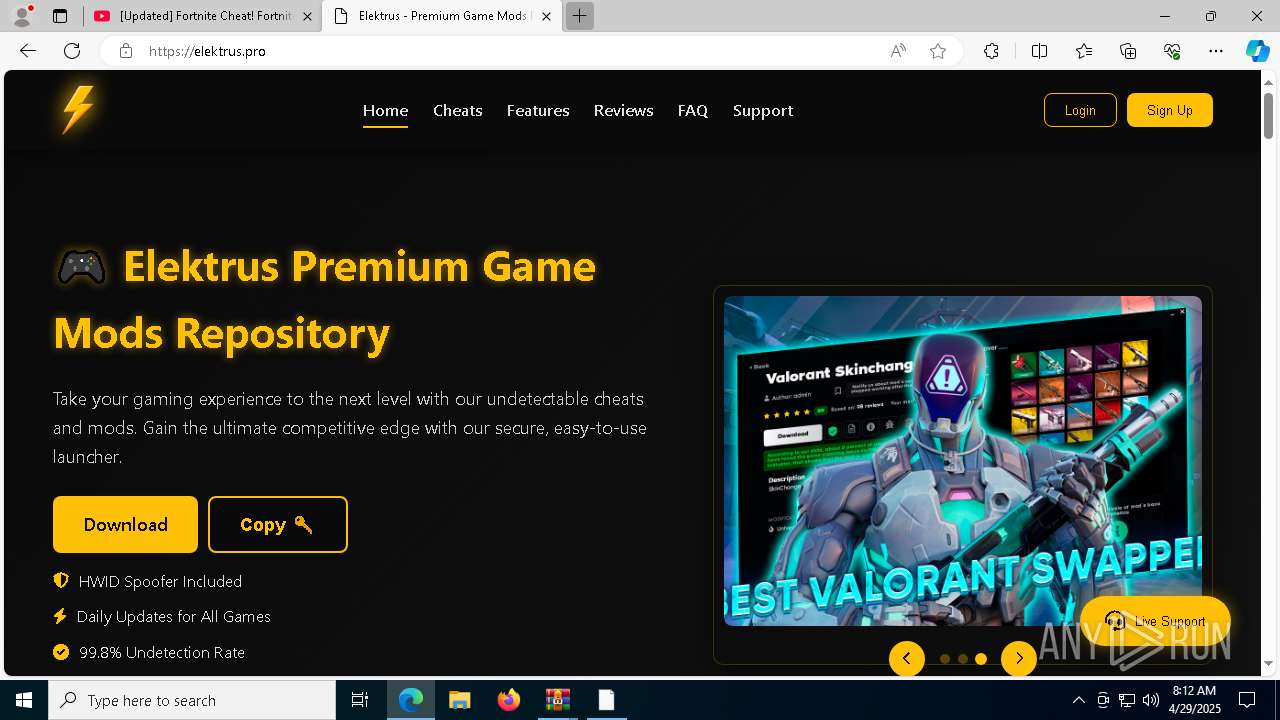
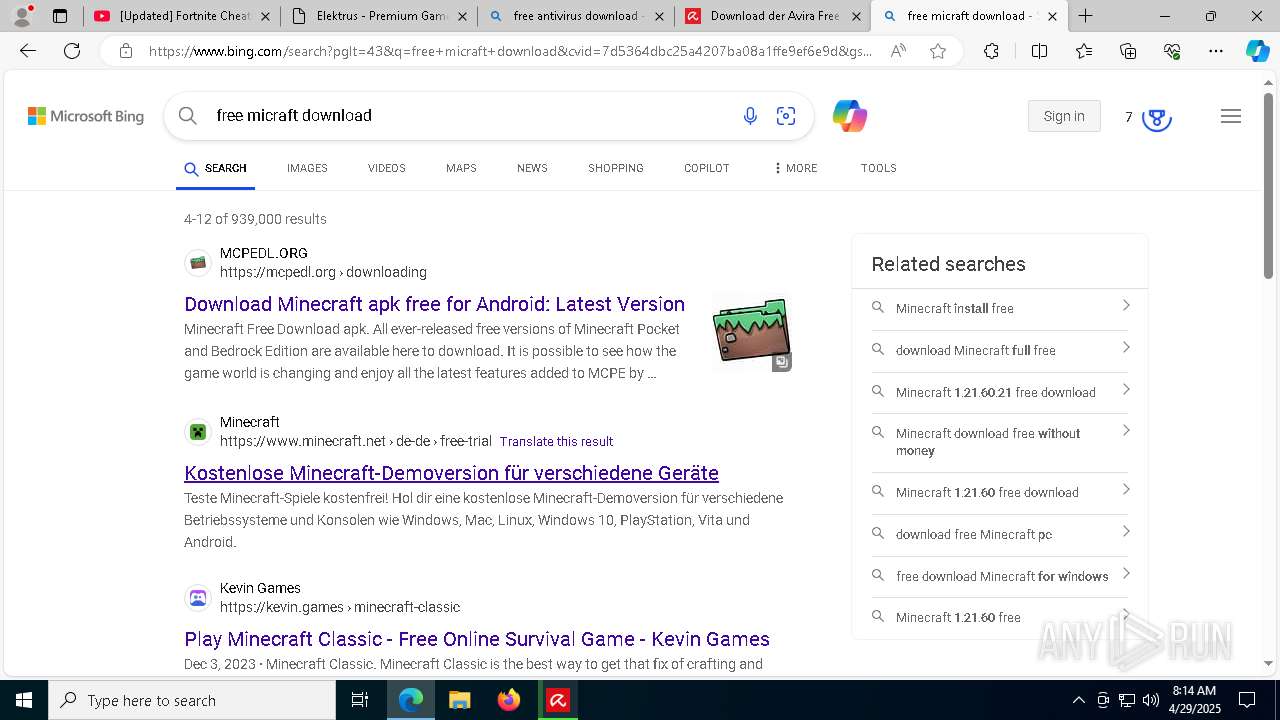
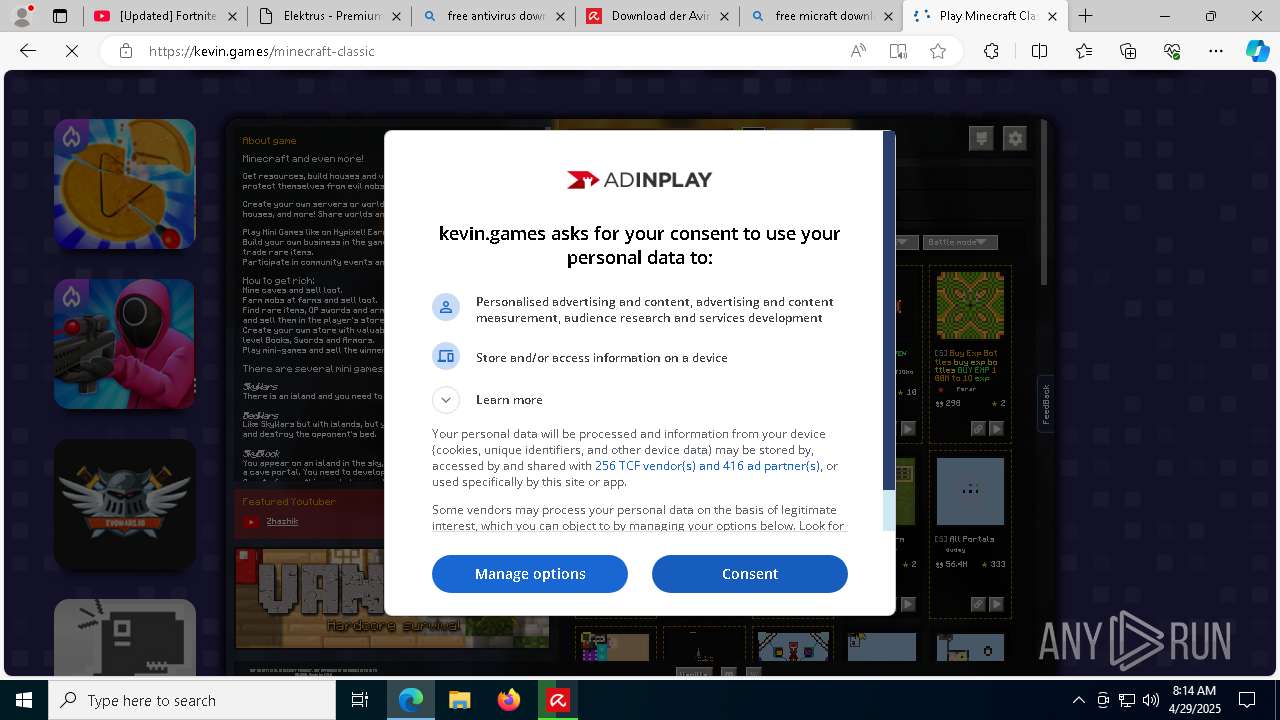
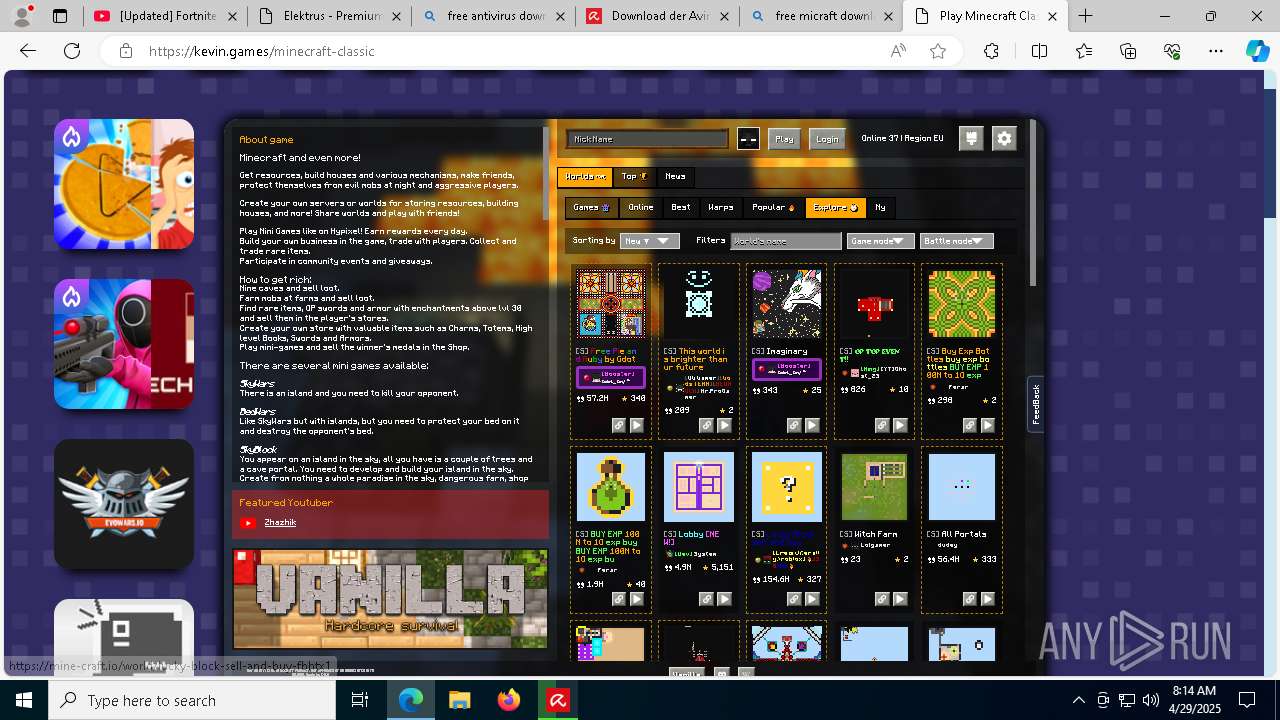
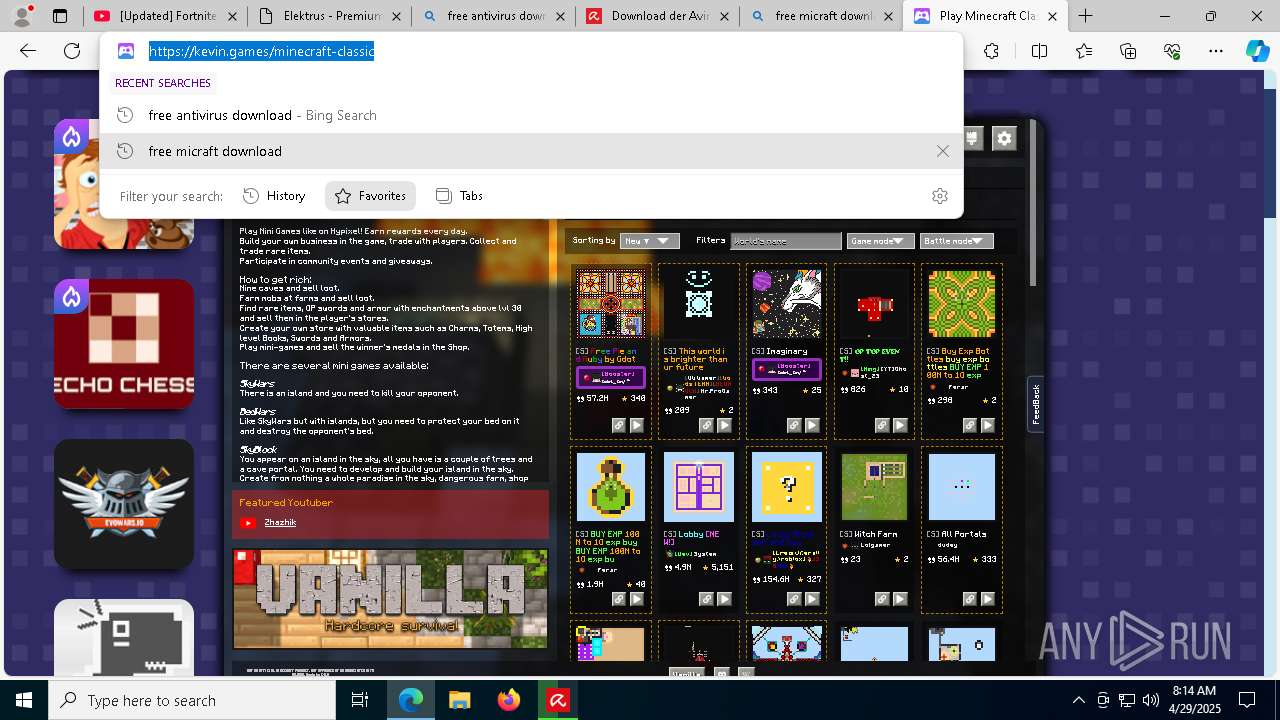
| URL: | youtub.com |
| Full analysis: | https://app.any.run/tasks/c1ee0504-0c14-4f42-8240-676078ceb1f6 |
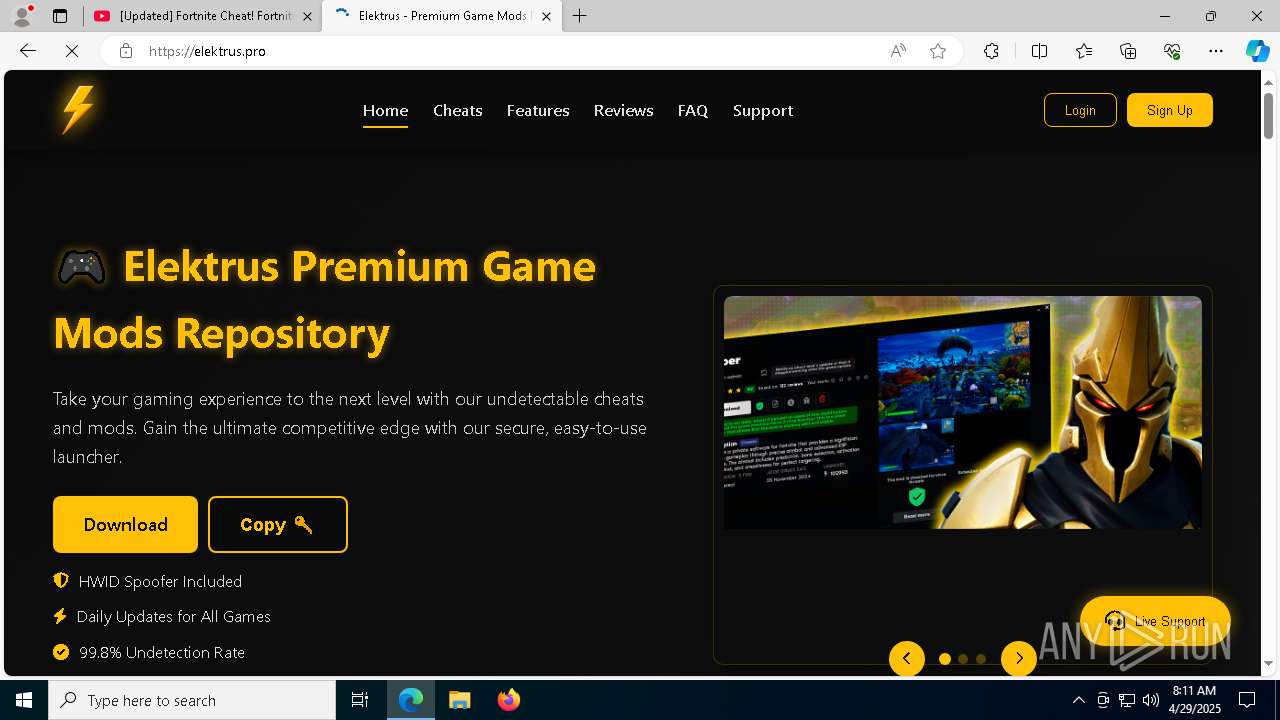
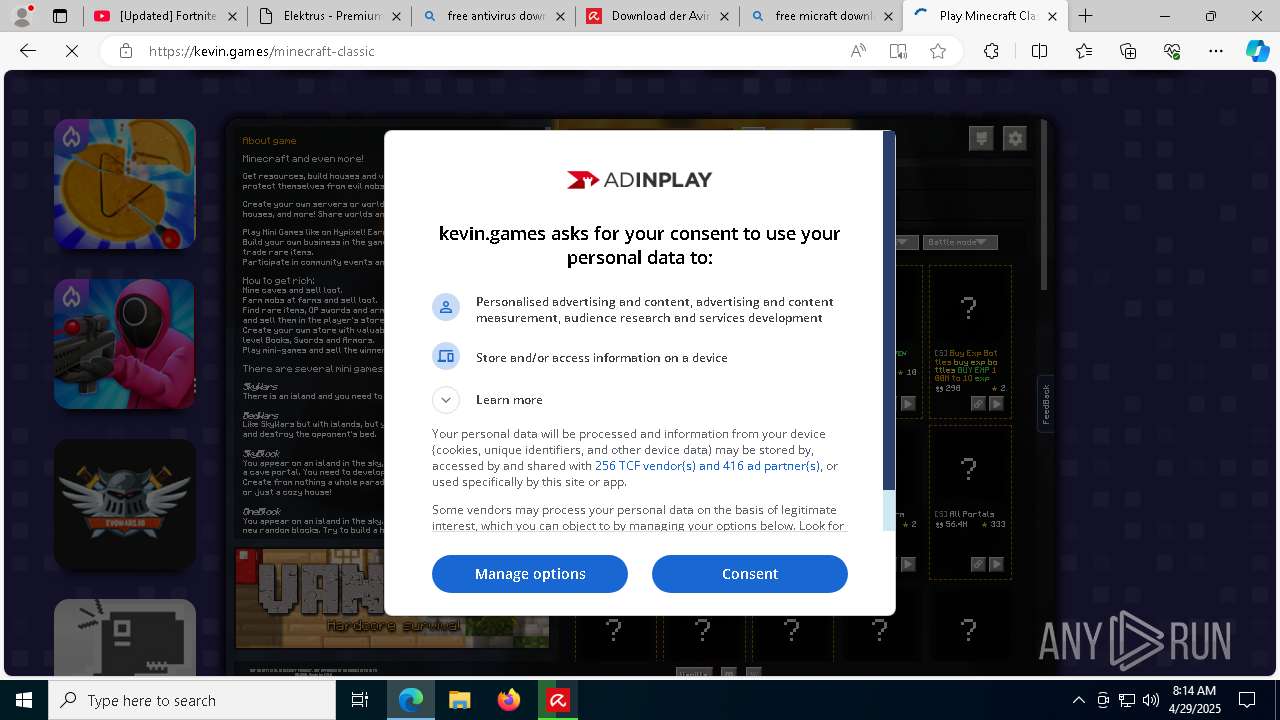
| Verdict: | Malicious activity |
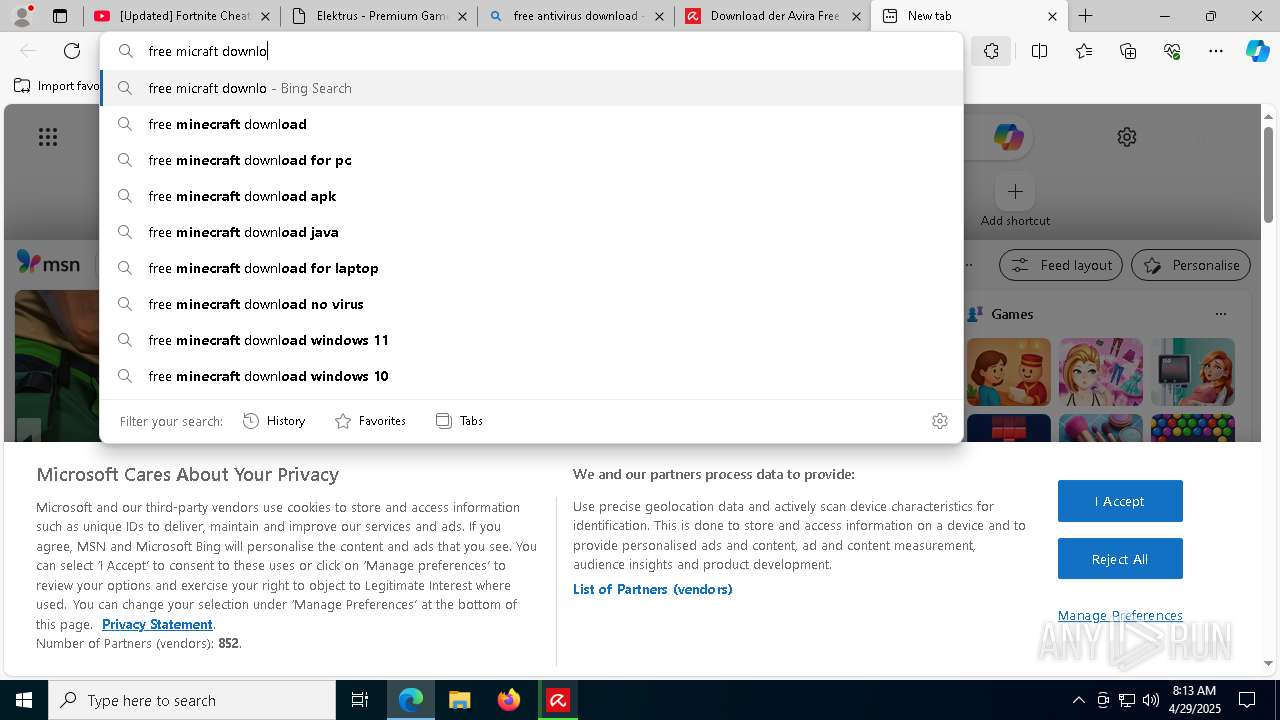
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 29, 2025, 08:10:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
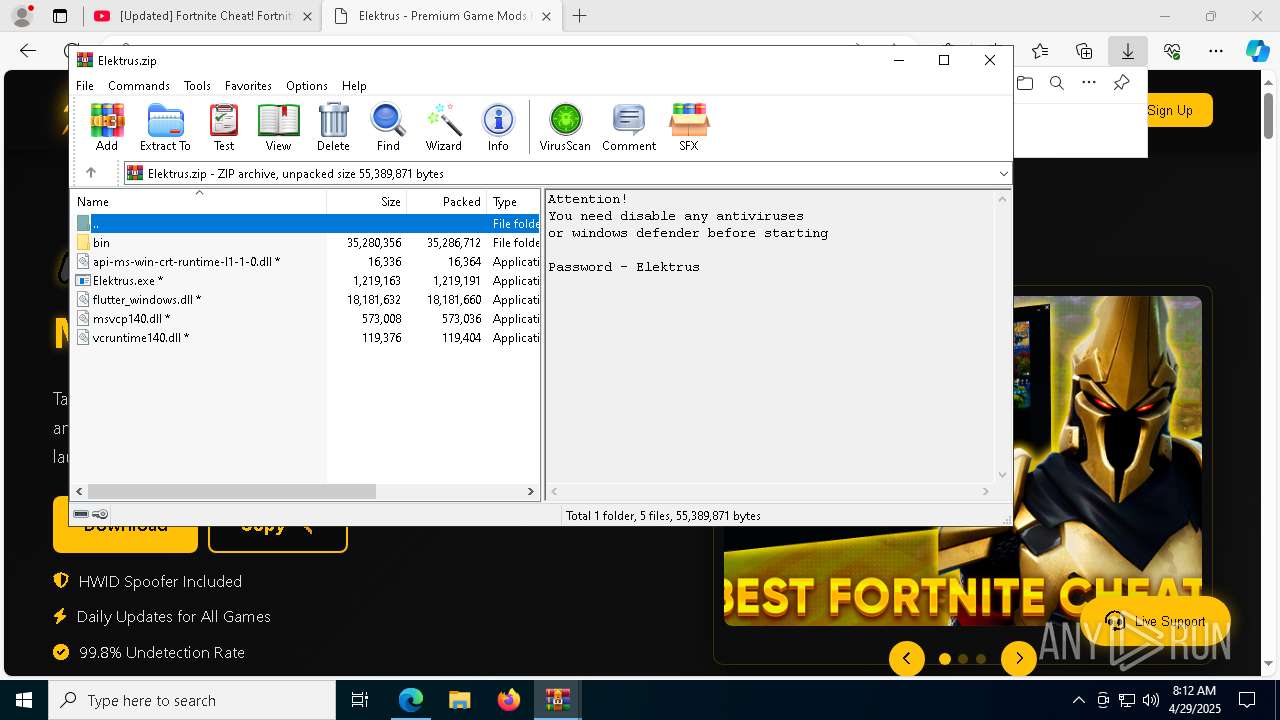
| MD5: | BF683B763993DB630621894115909BBF |
| SHA1: | 8BA099DEABB1EE5ADD01927E03D2B28CE971960C |
| SHA256: | FDA34BA8DD7FCF9B8A39EA50A61B2CD5D36B9AE5AA6E19076BB147F351CF4590 |
| SSDEEP: | 3:7QR4GT:BGT |
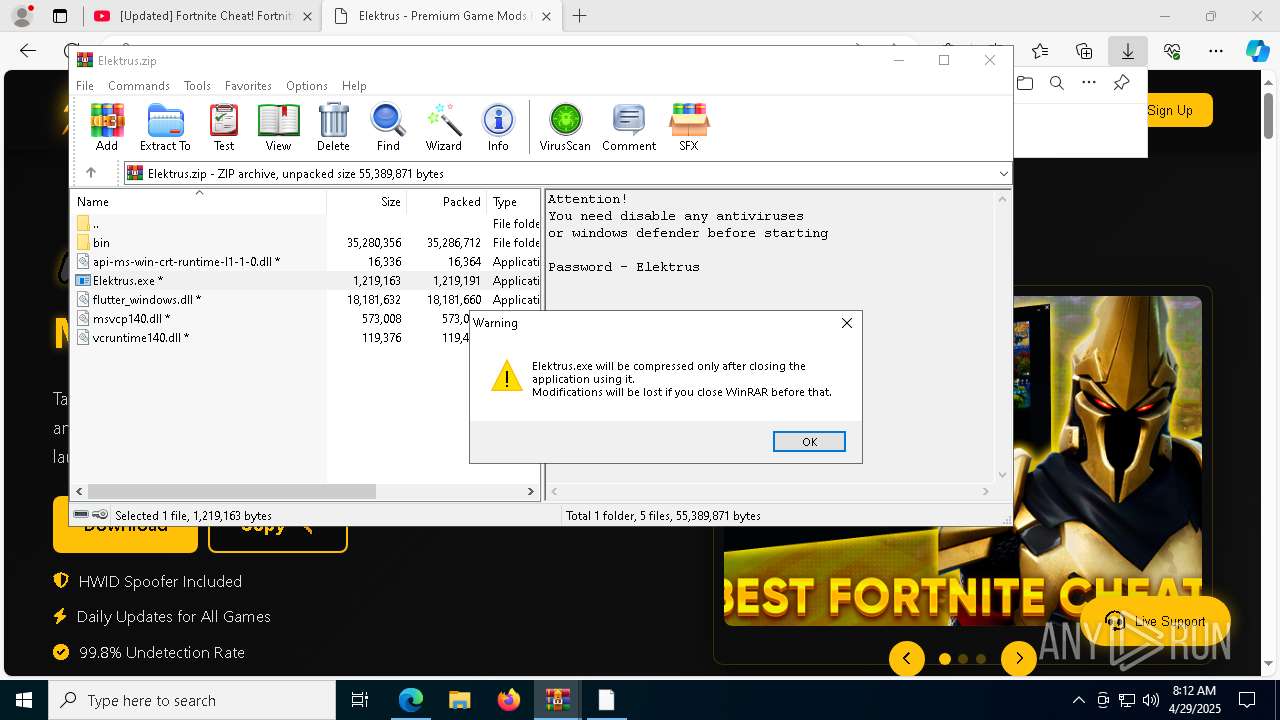
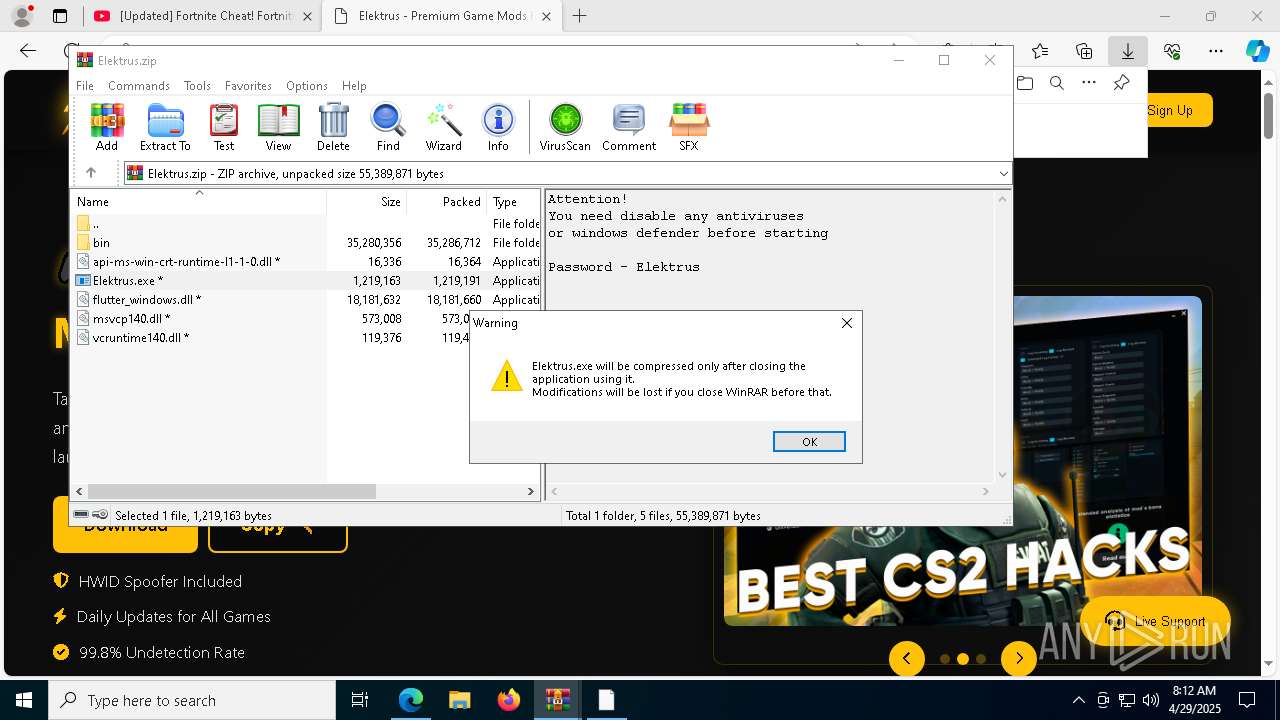
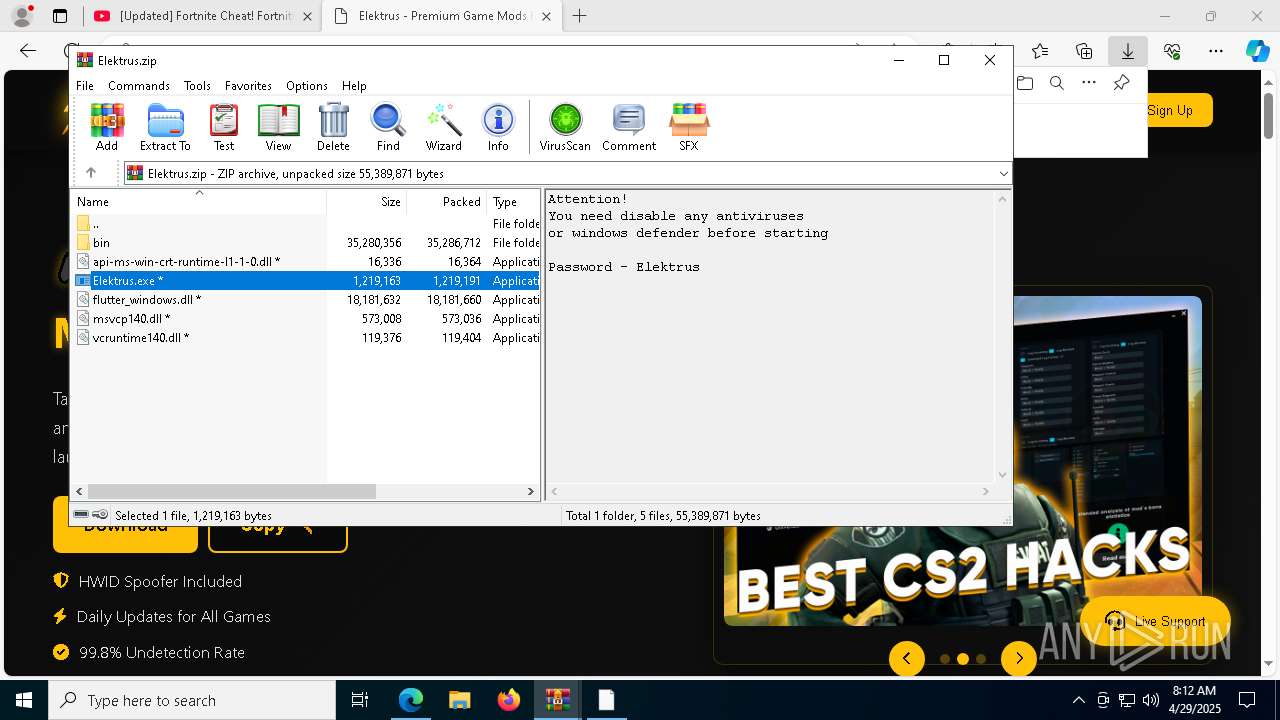
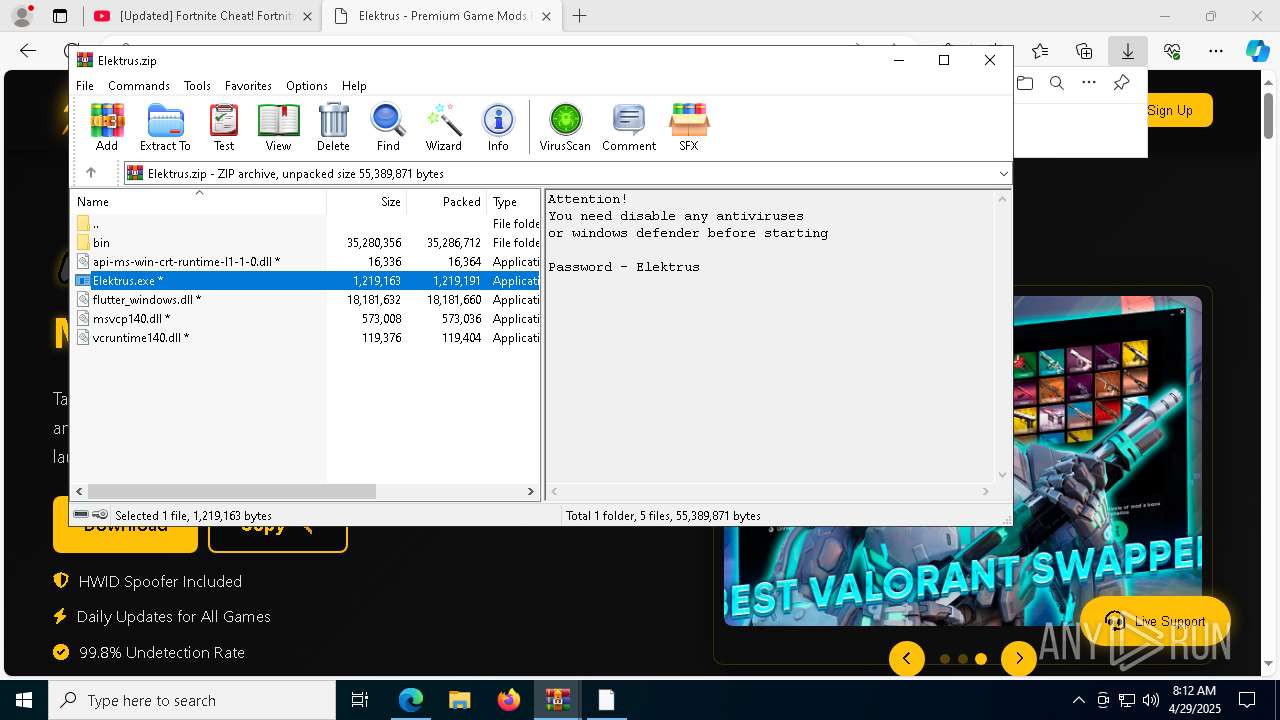
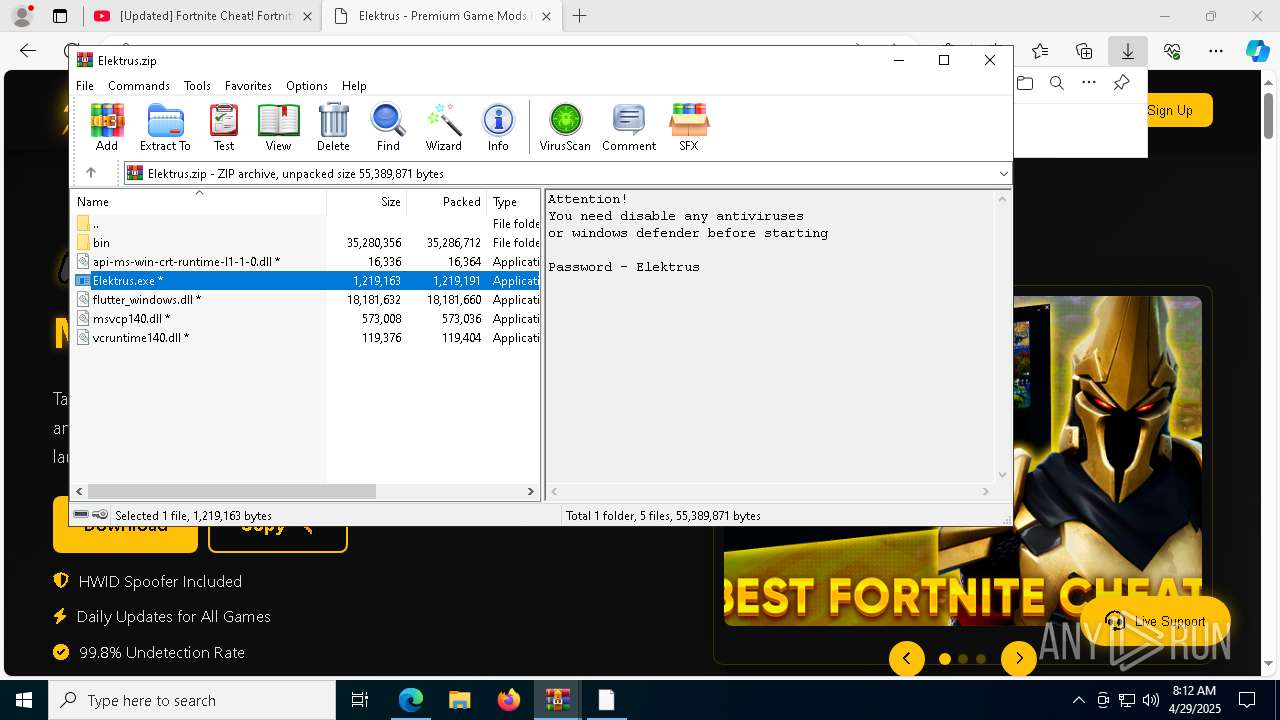
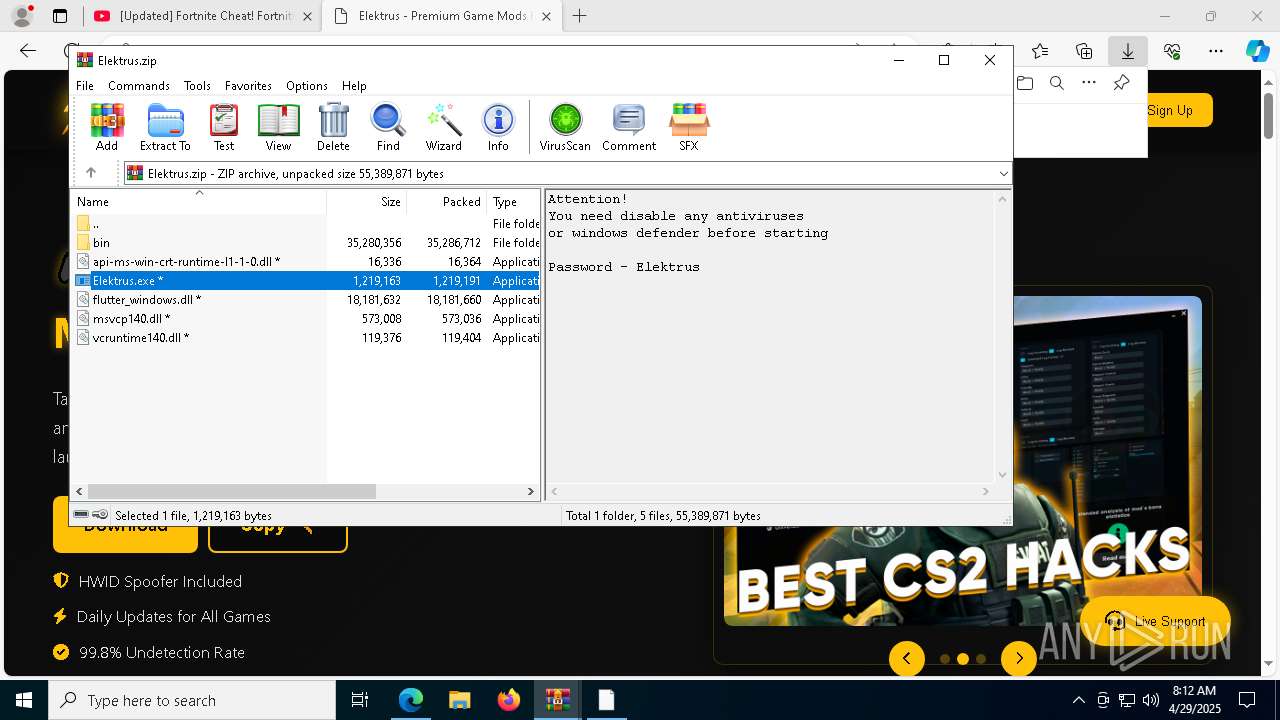
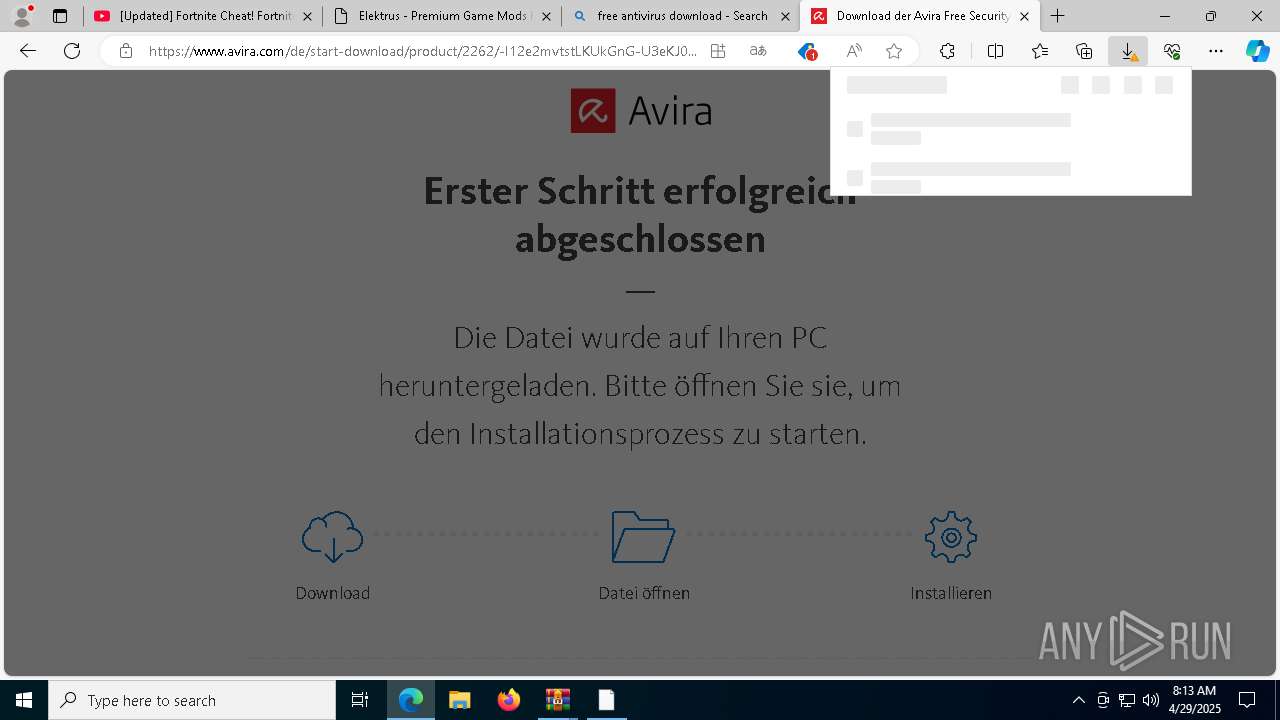
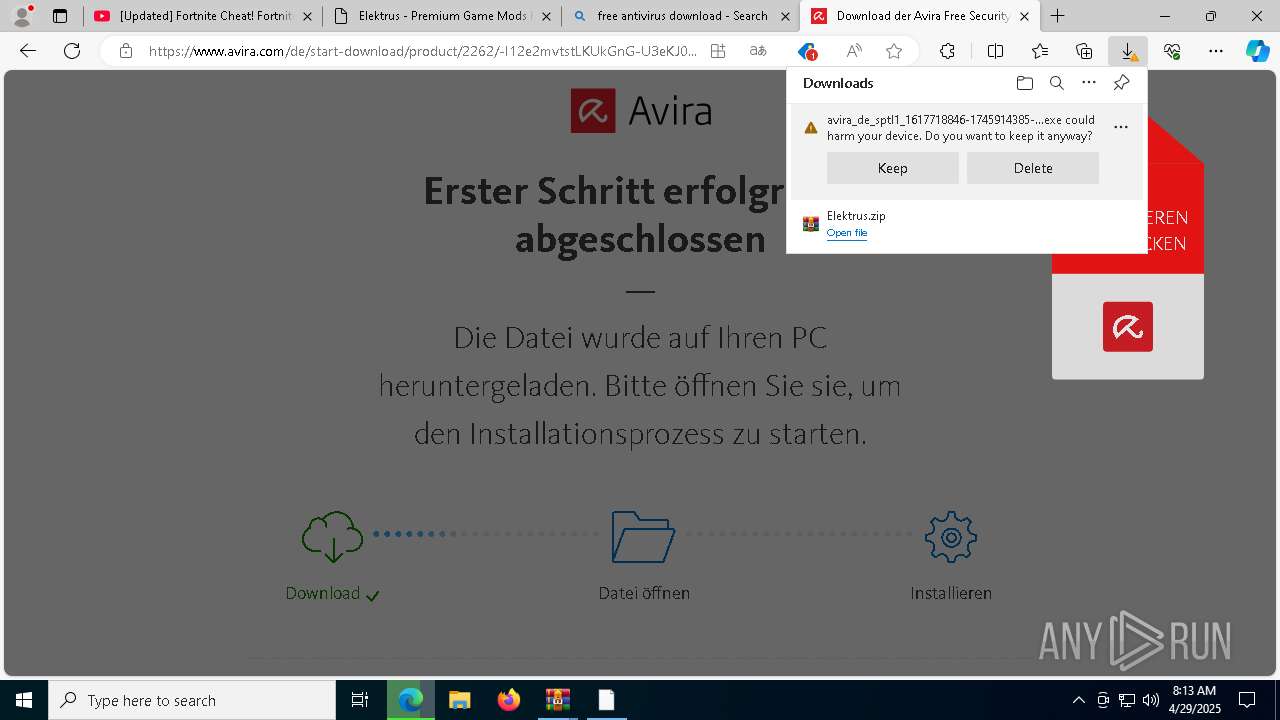
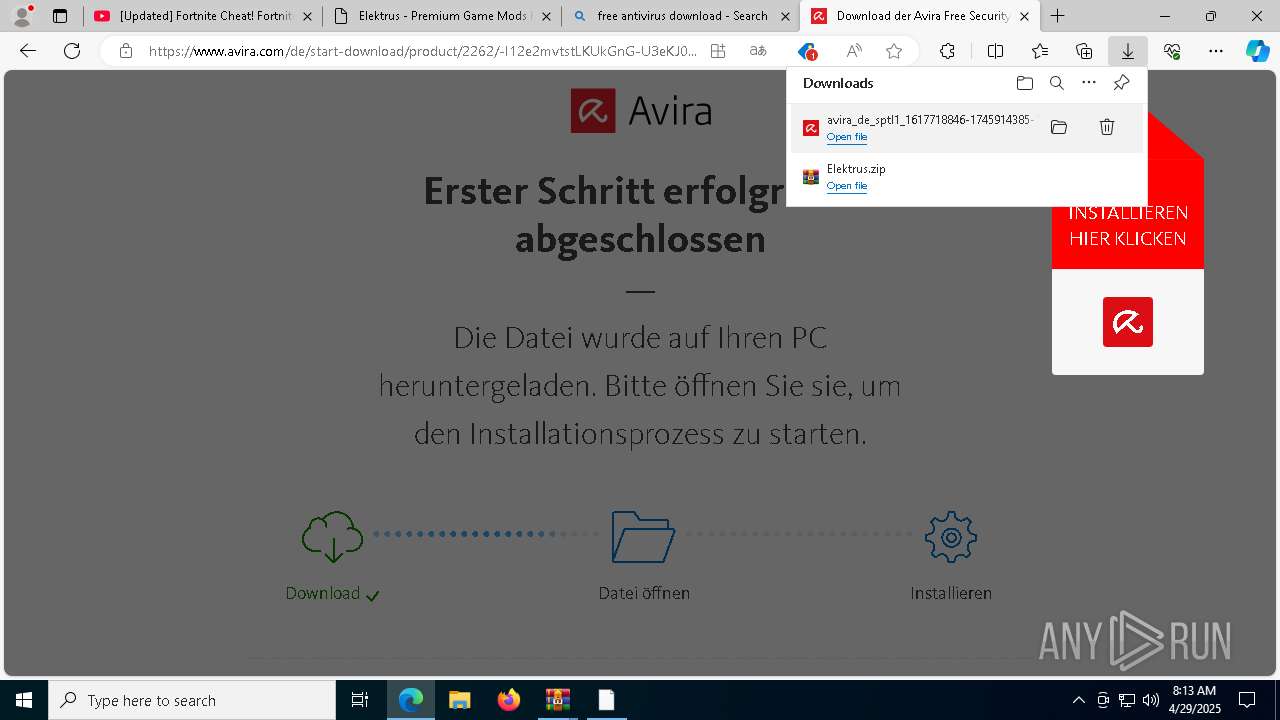
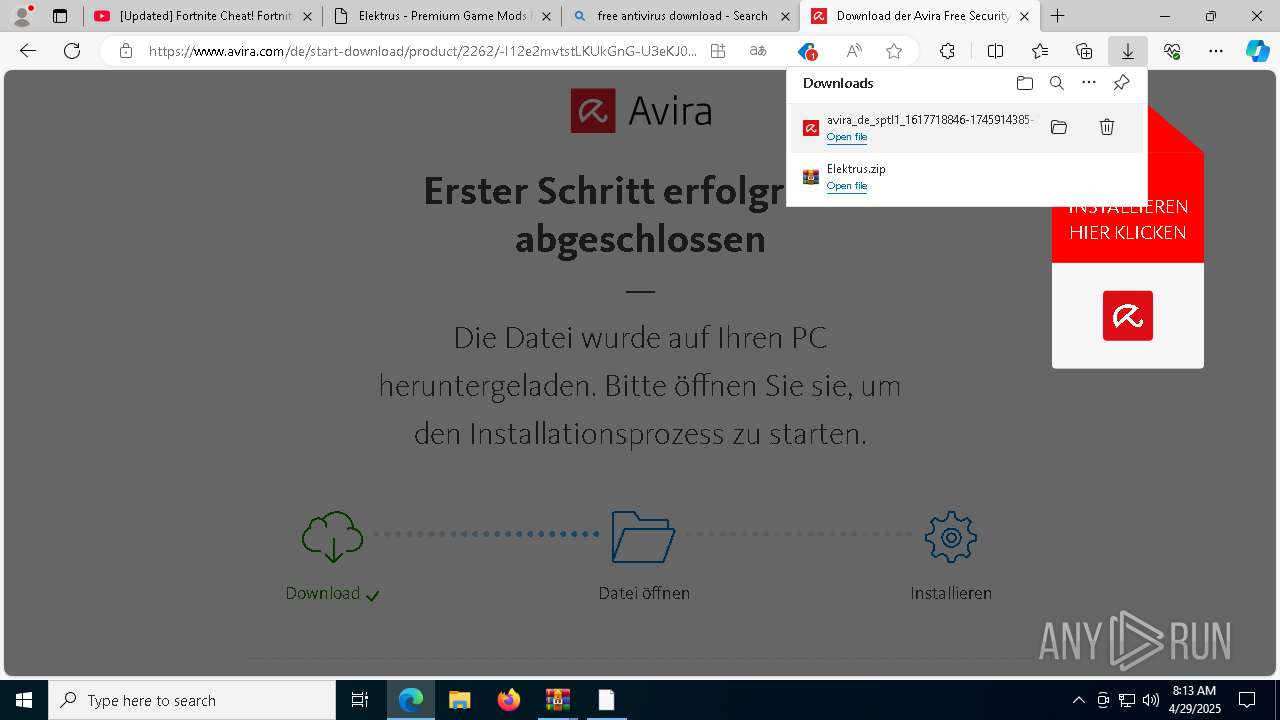
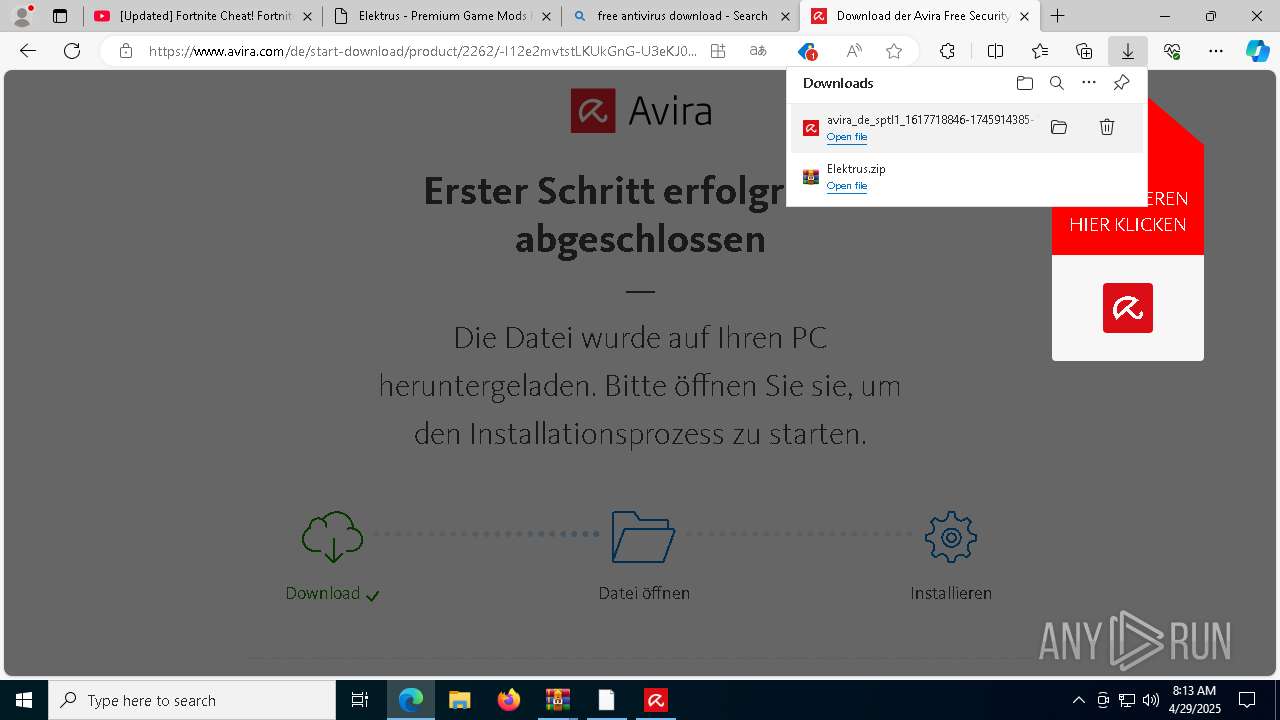
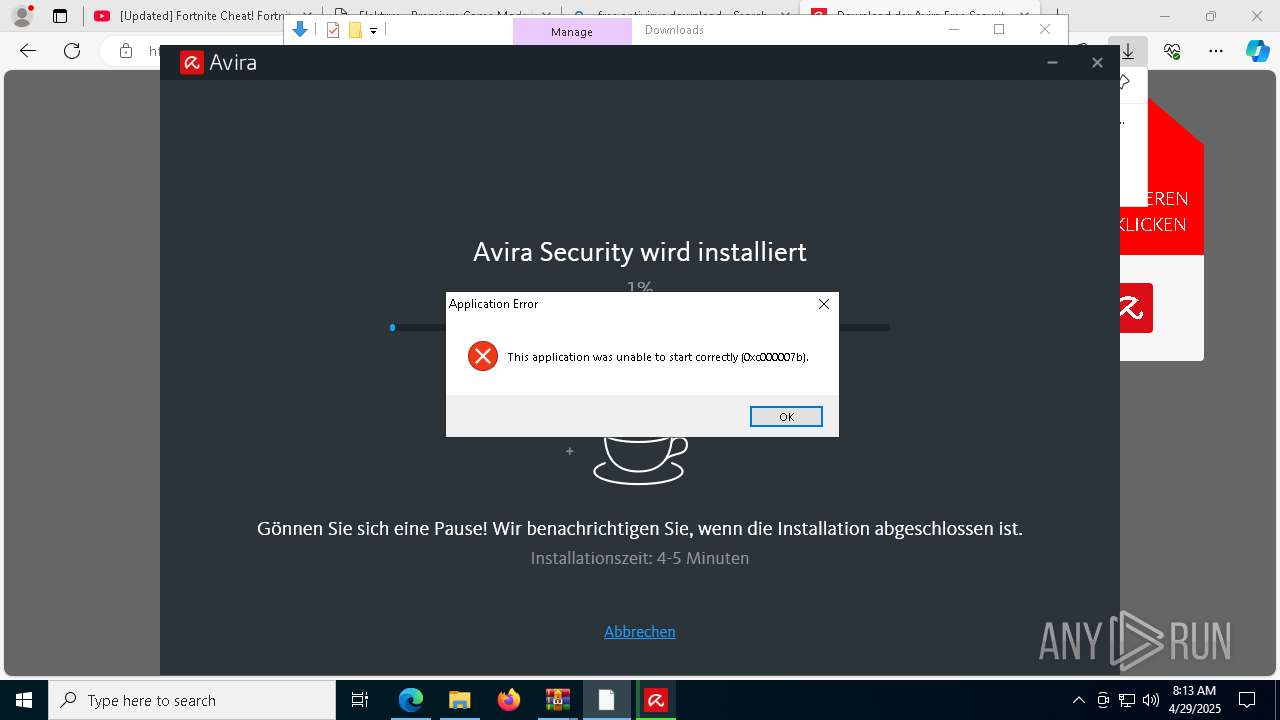
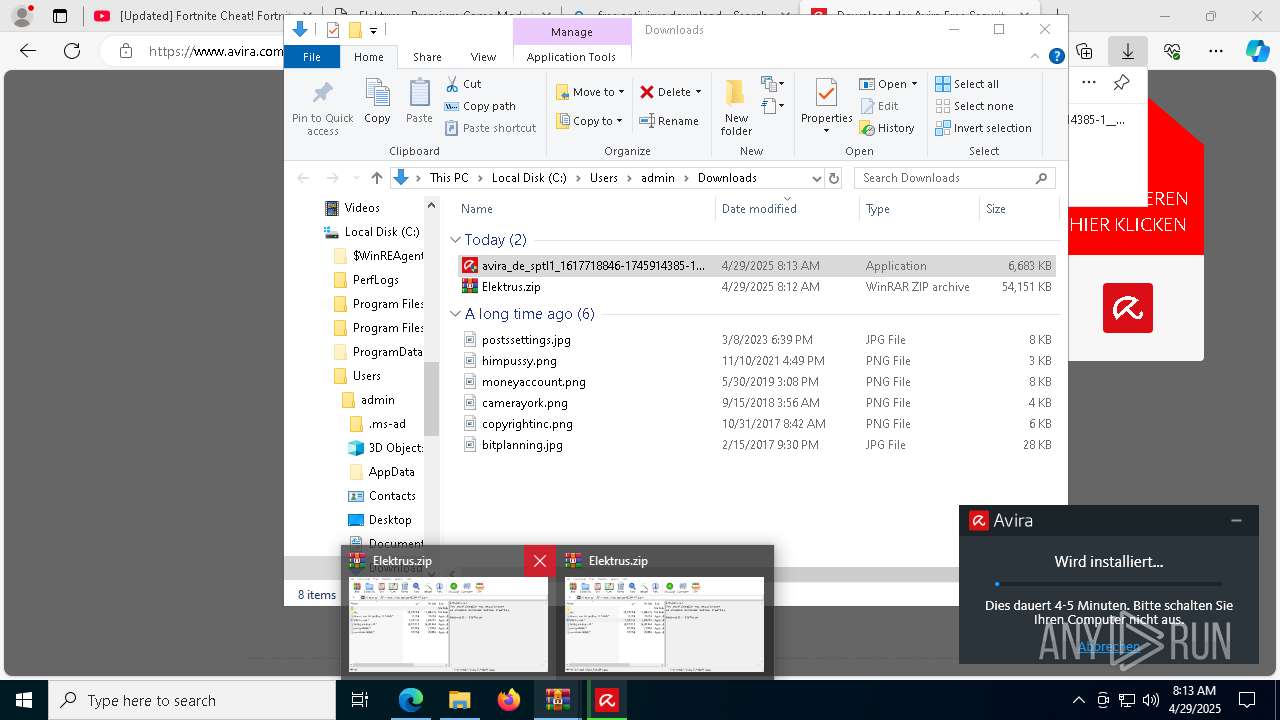
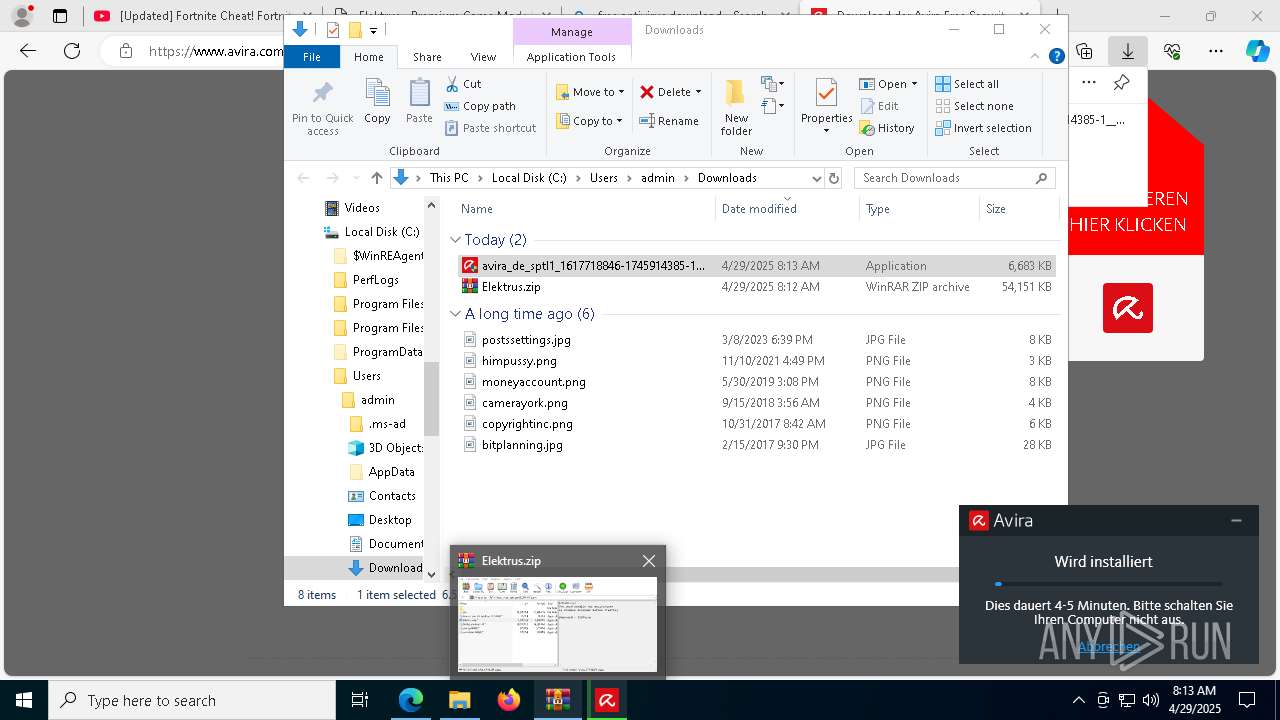
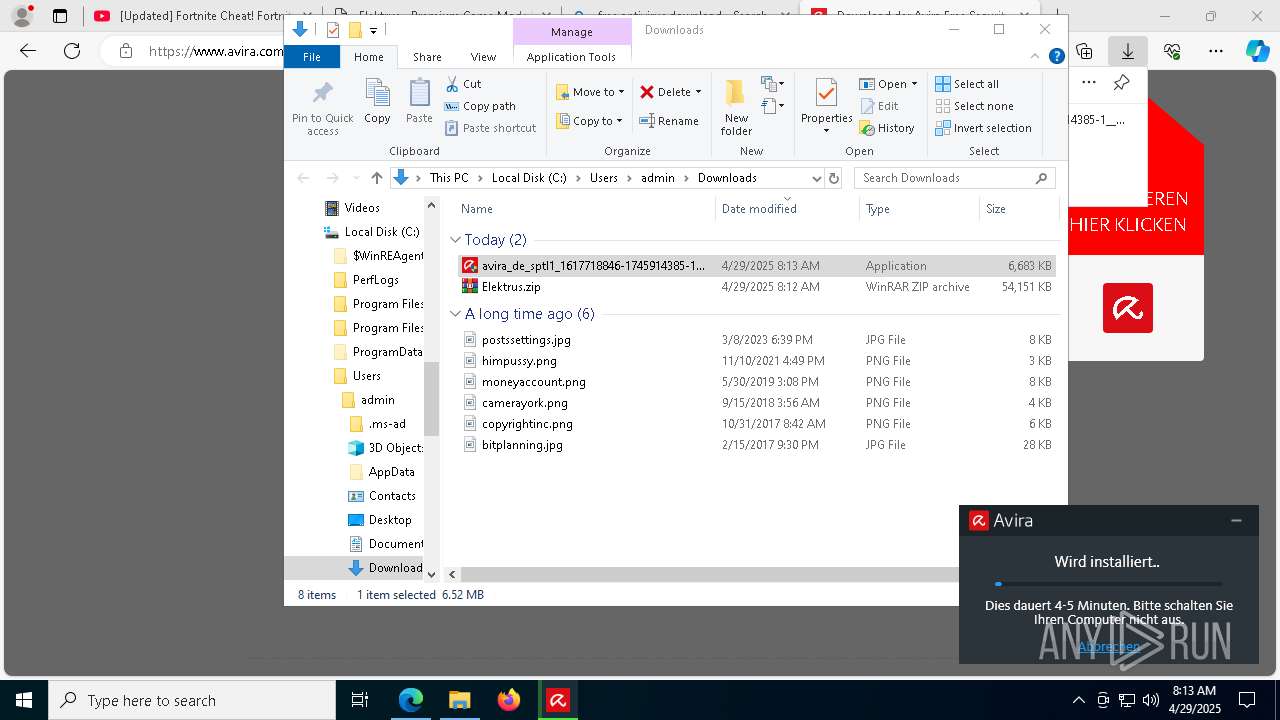
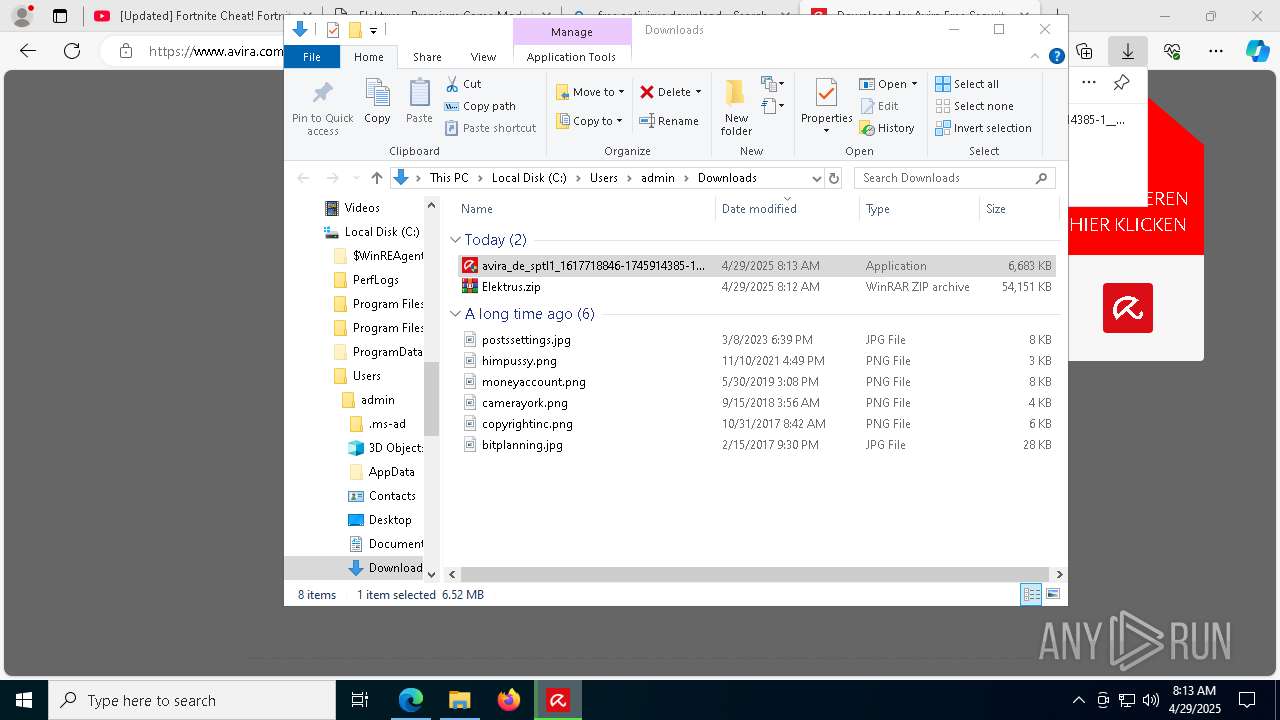
MALICIOUS
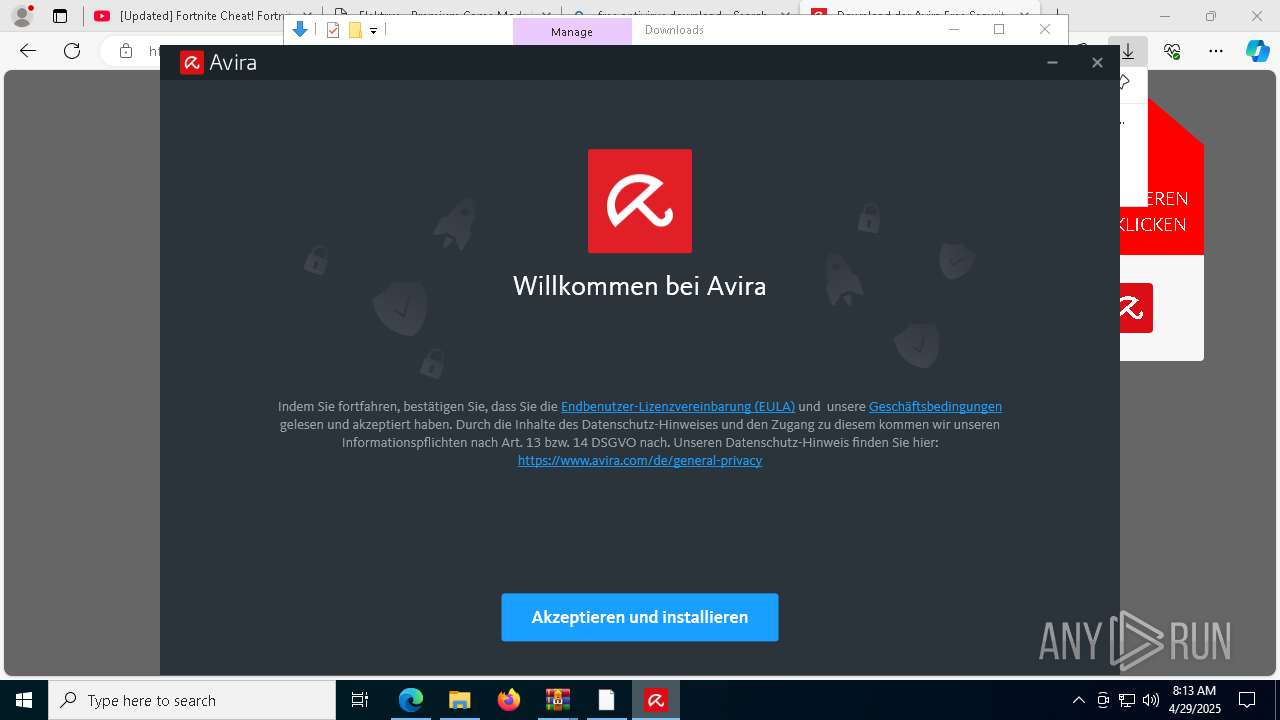
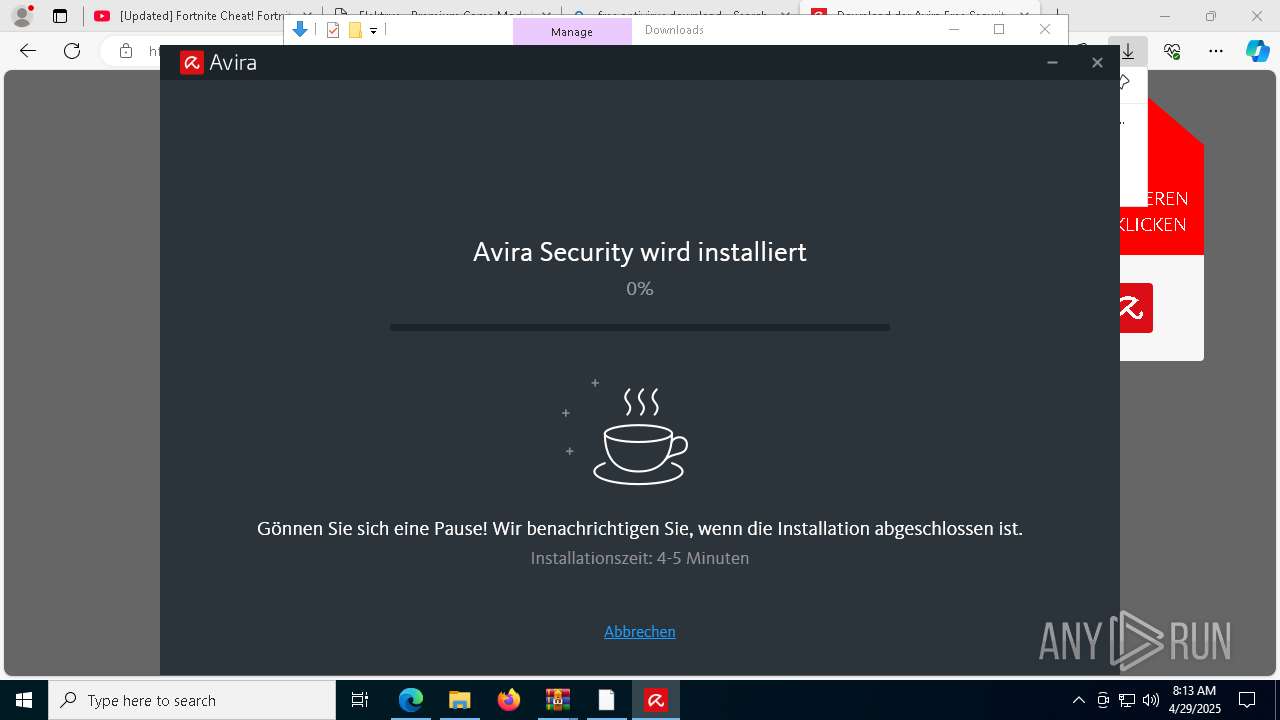
Executing a file with an untrusted certificate
- Elektrus.exe (PID: 9028)
AutoIt loader has been detected (YARA)
- Operators.com (PID: 8128)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- Operators.com (PID: 8128)
- svchost.exe (PID: 2196)
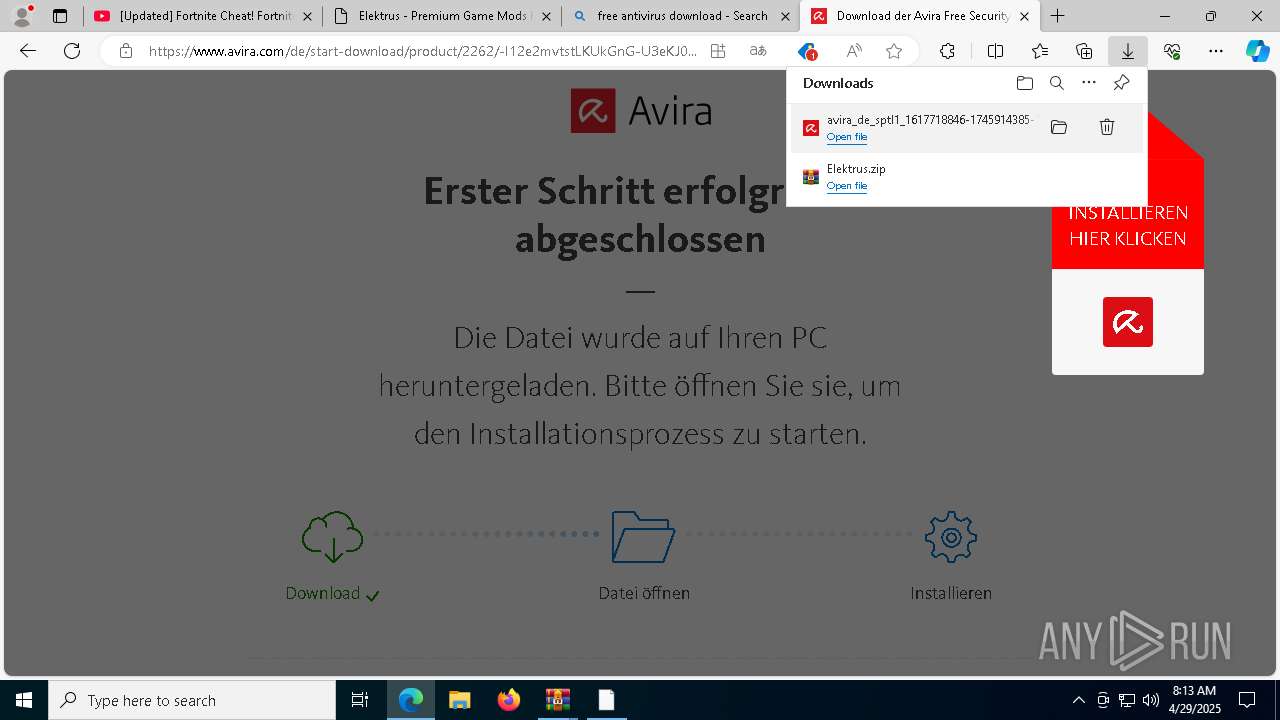
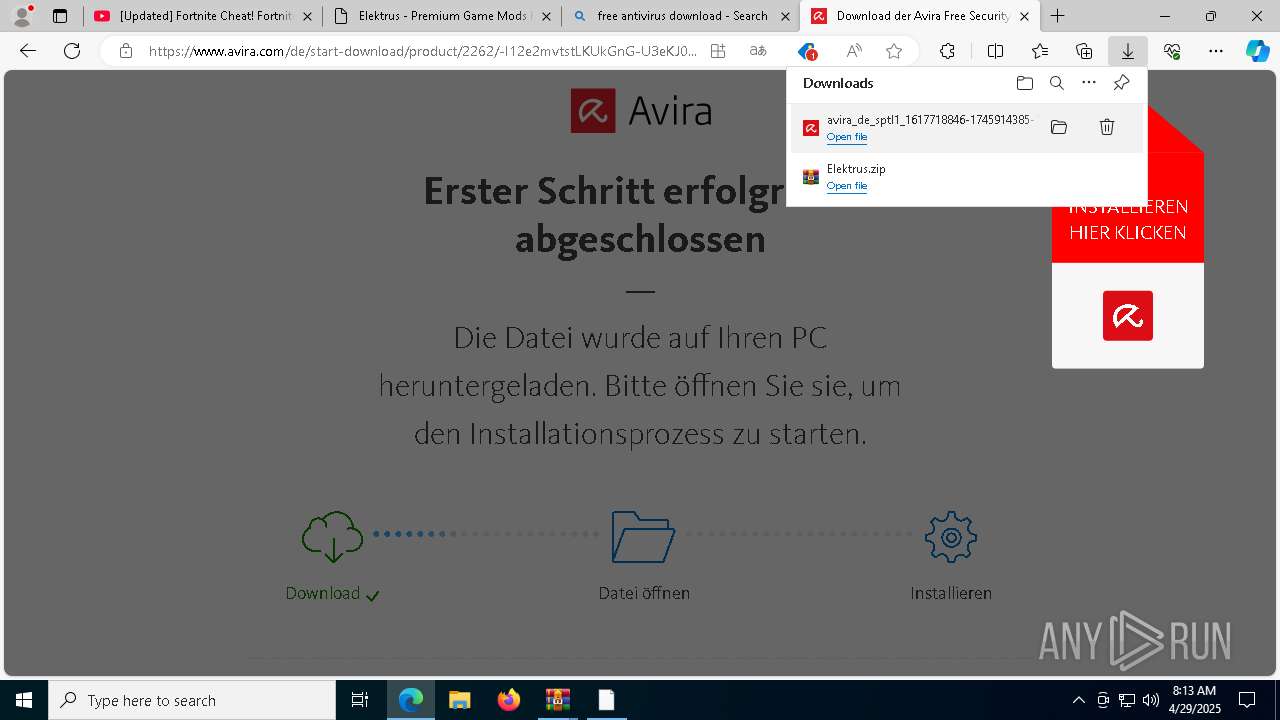
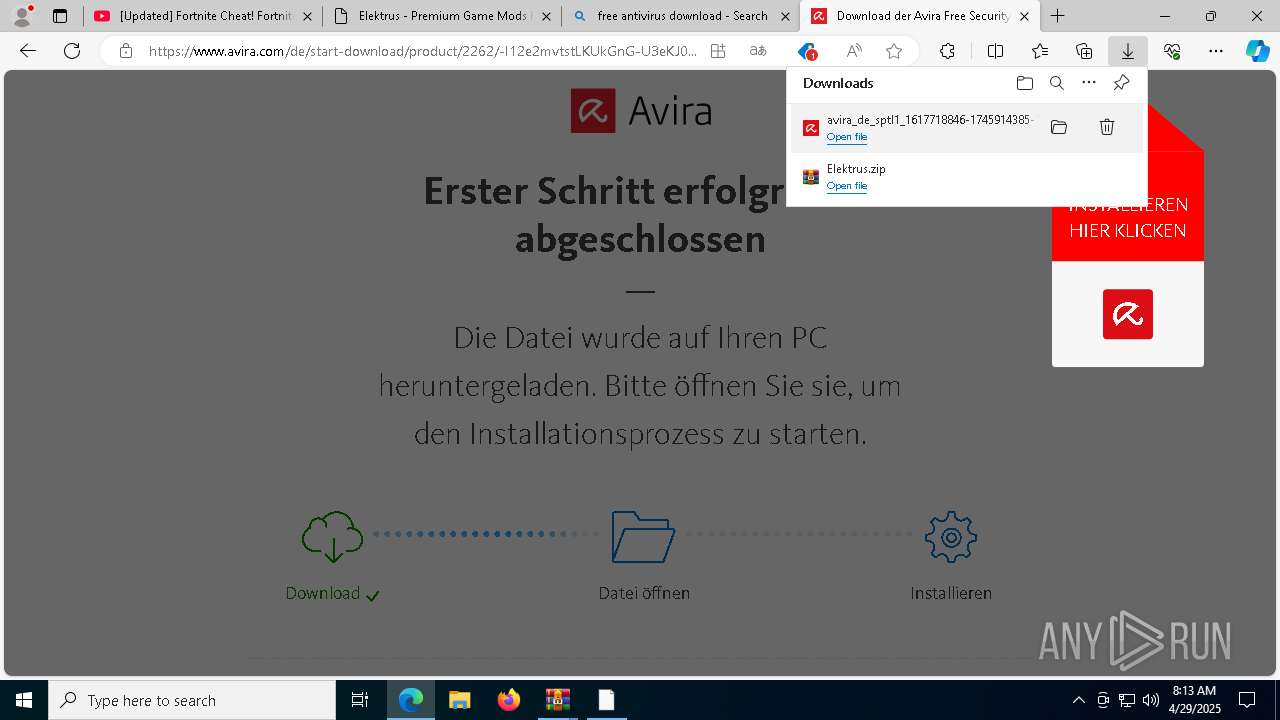
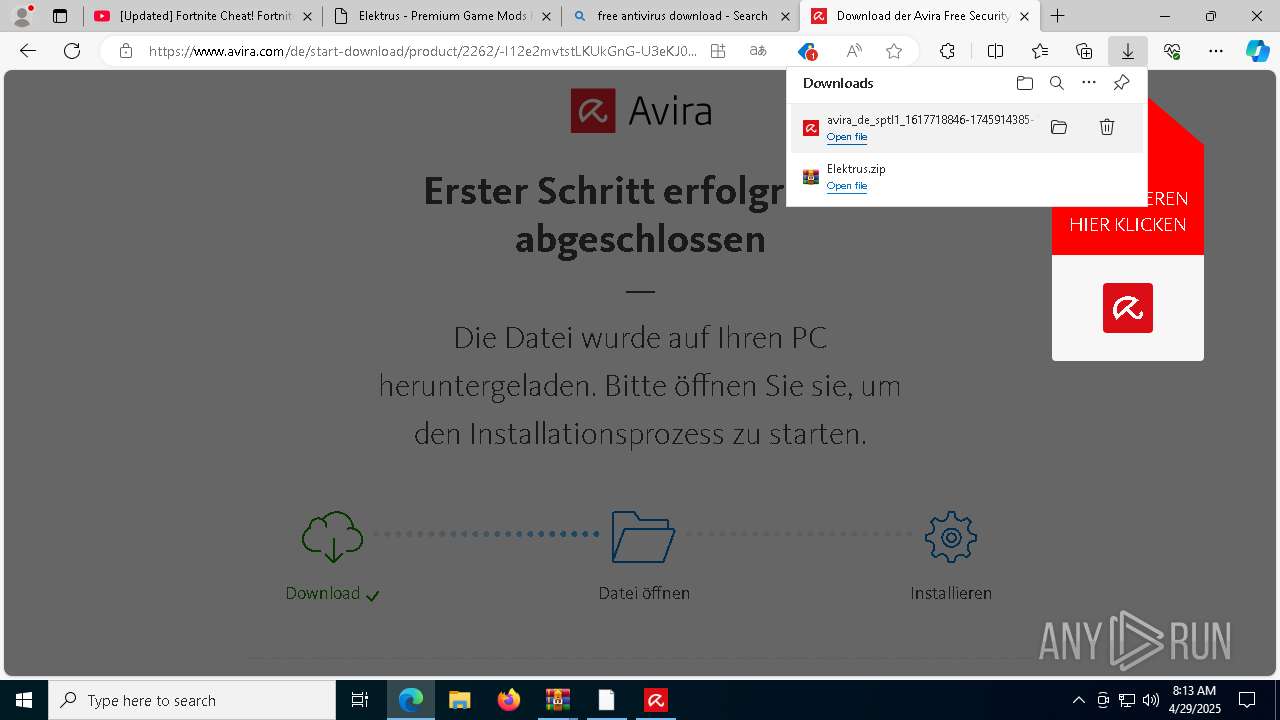
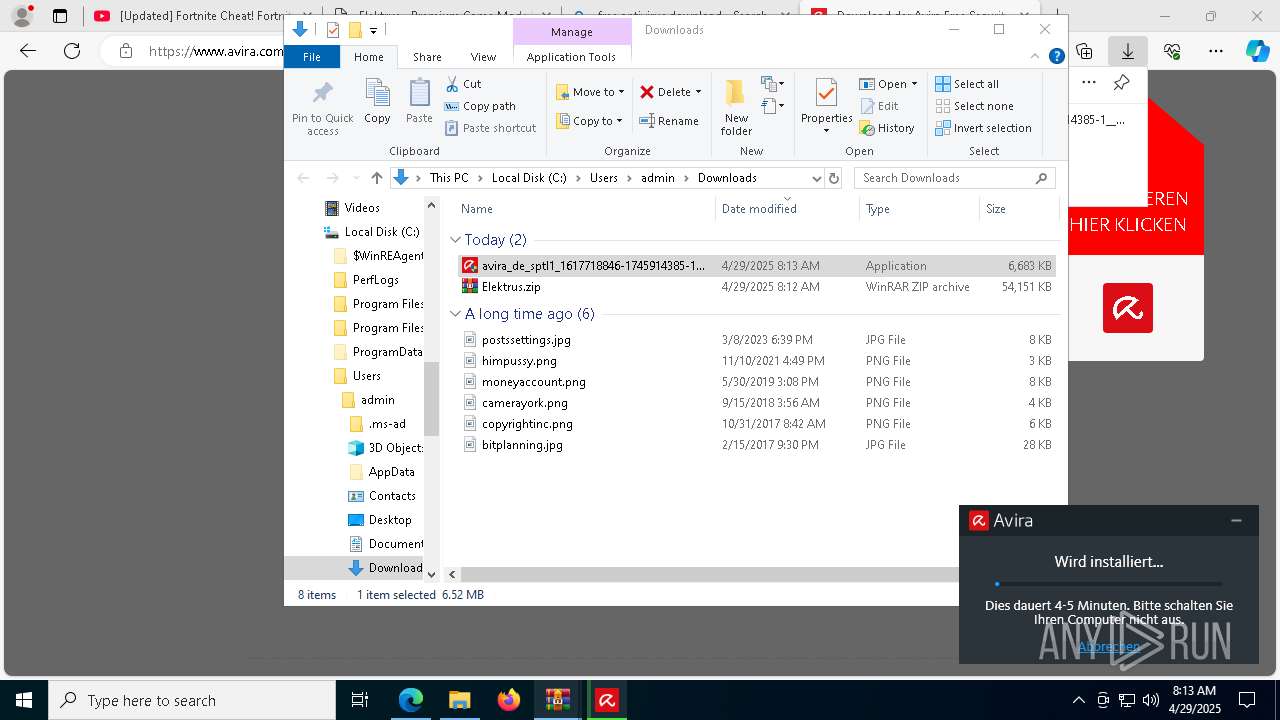
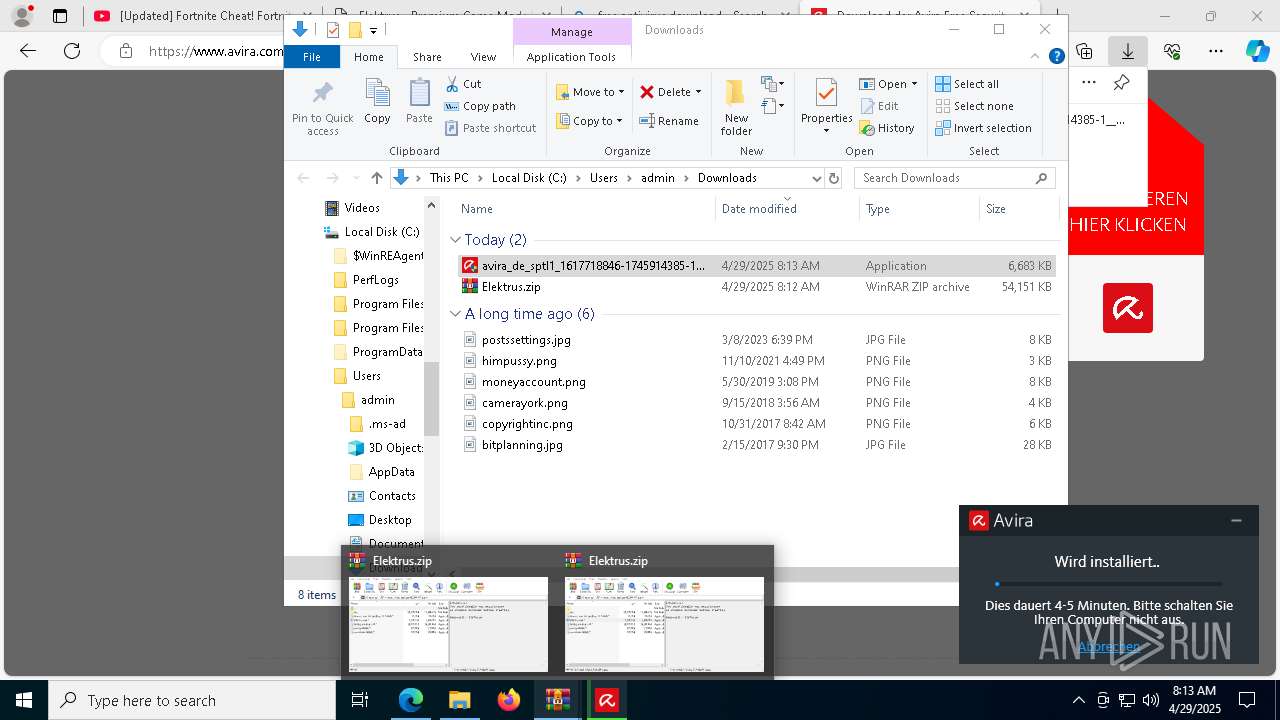
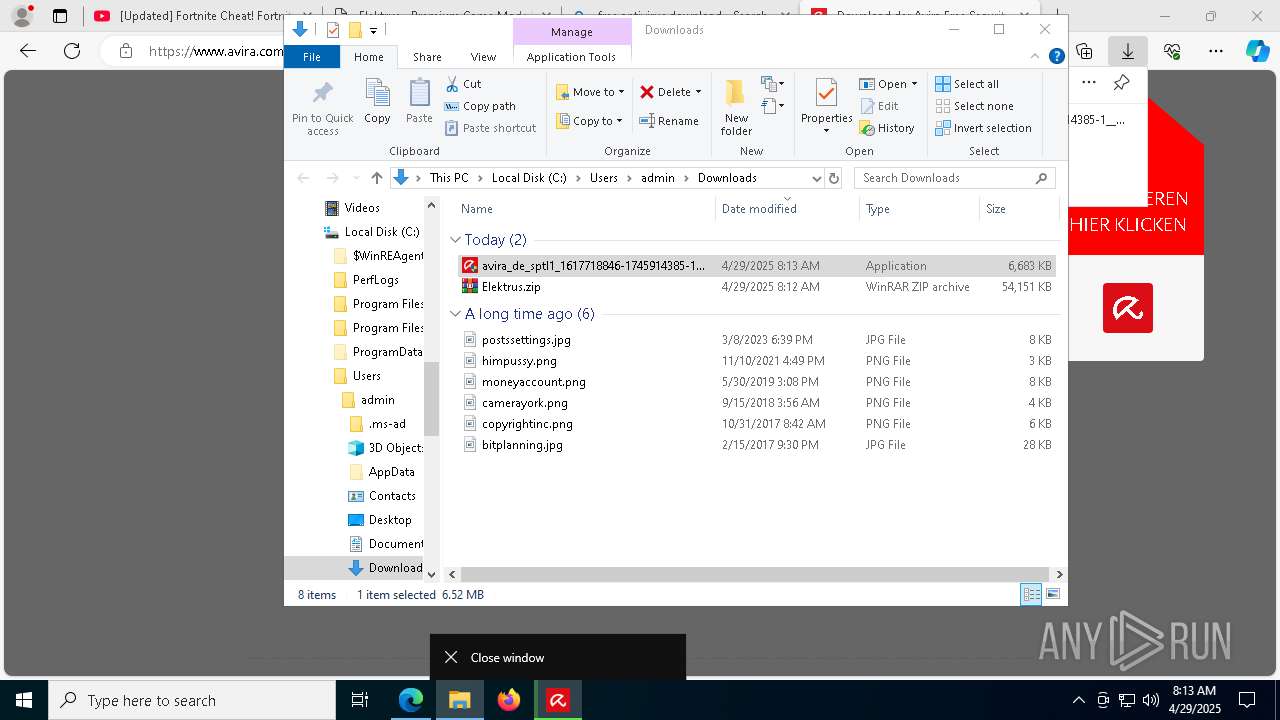
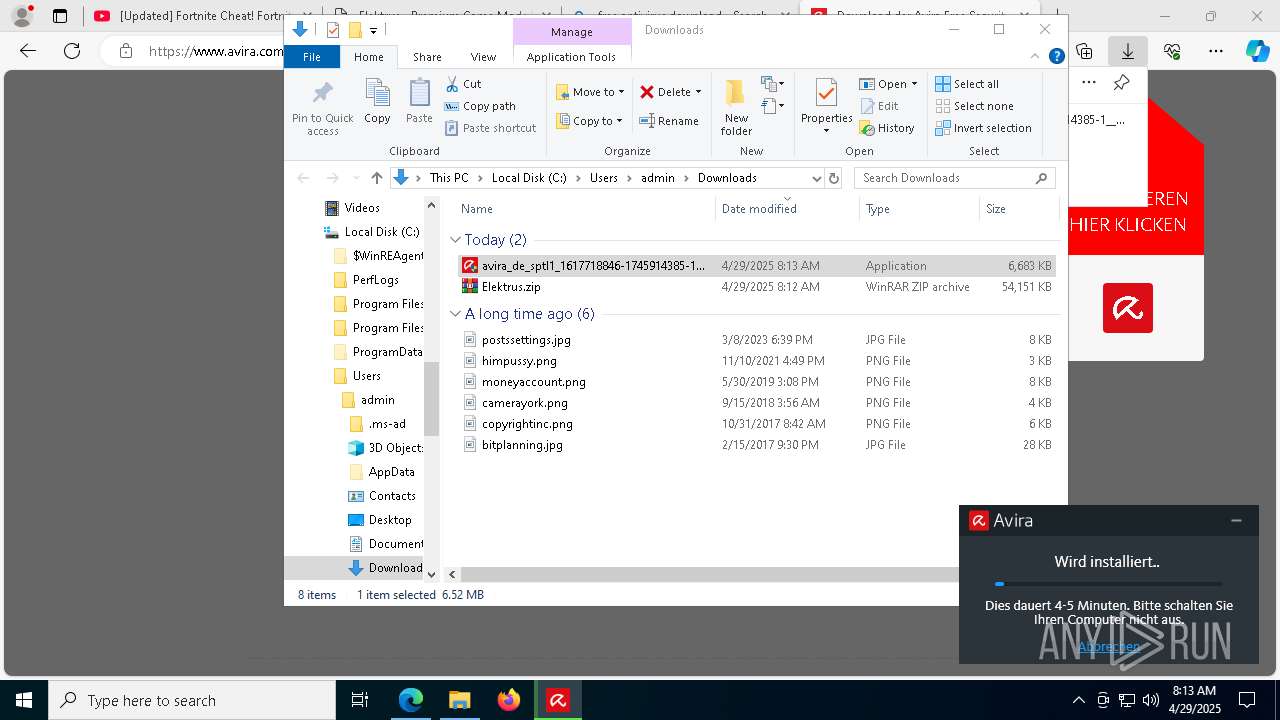
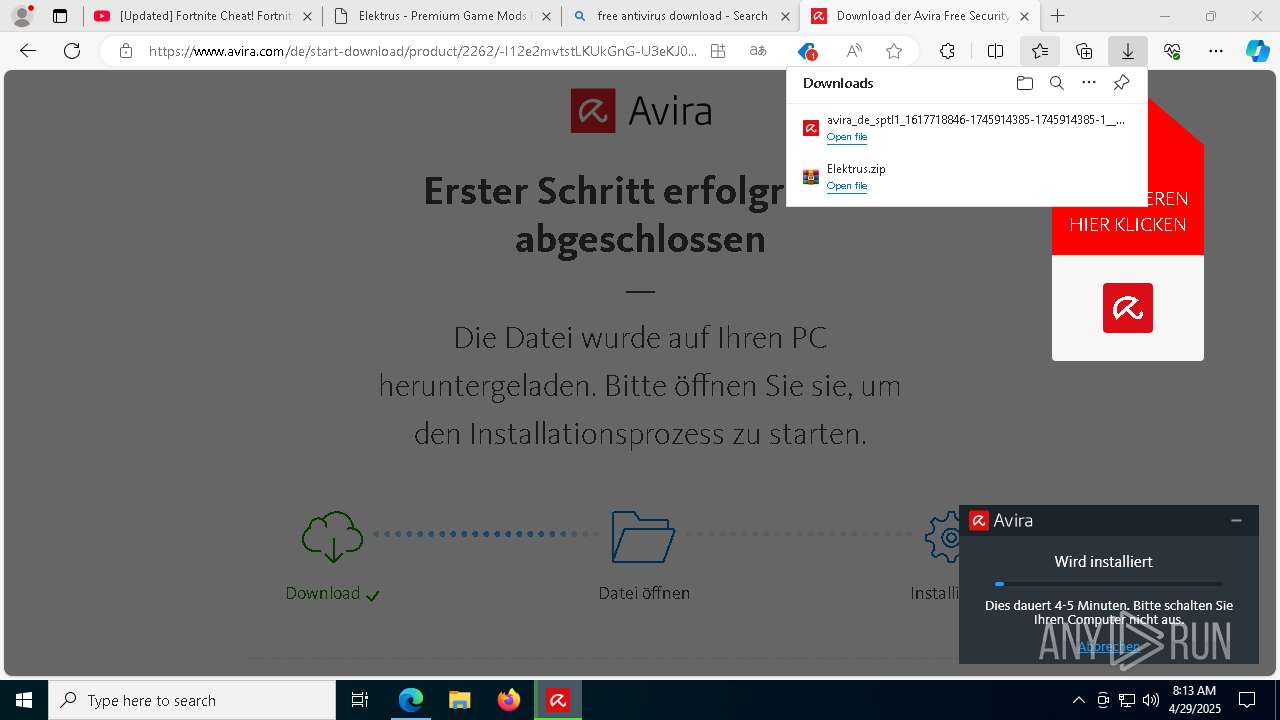
Uses Task Scheduler to run other applications
- avira_de_sptl1_1617718846-1745914385-1745914385-1__pavwws-spotlight-release.exe (PID: 6852)
SUSPICIOUS
Reads security settings of Internet Explorer
- Elektrus.exe (PID: 9028)
- WinRAR.exe (PID: 6808)
Application launched itself
- cmd.exe (PID: 9008)
Starts CMD.EXE for commands execution
- Elektrus.exe (PID: 9028)
- cmd.exe (PID: 9008)
Get information on the list of running processes
- cmd.exe (PID: 9008)
Starts the AutoIt3 executable file
- cmd.exe (PID: 9008)
The executable file from the user directory is run by the CMD process
- Operators.com (PID: 8128)
Starts application with an unusual extension
- cmd.exe (PID: 9008)
Executing commands from a ".bat" file
- Elektrus.exe (PID: 9028)
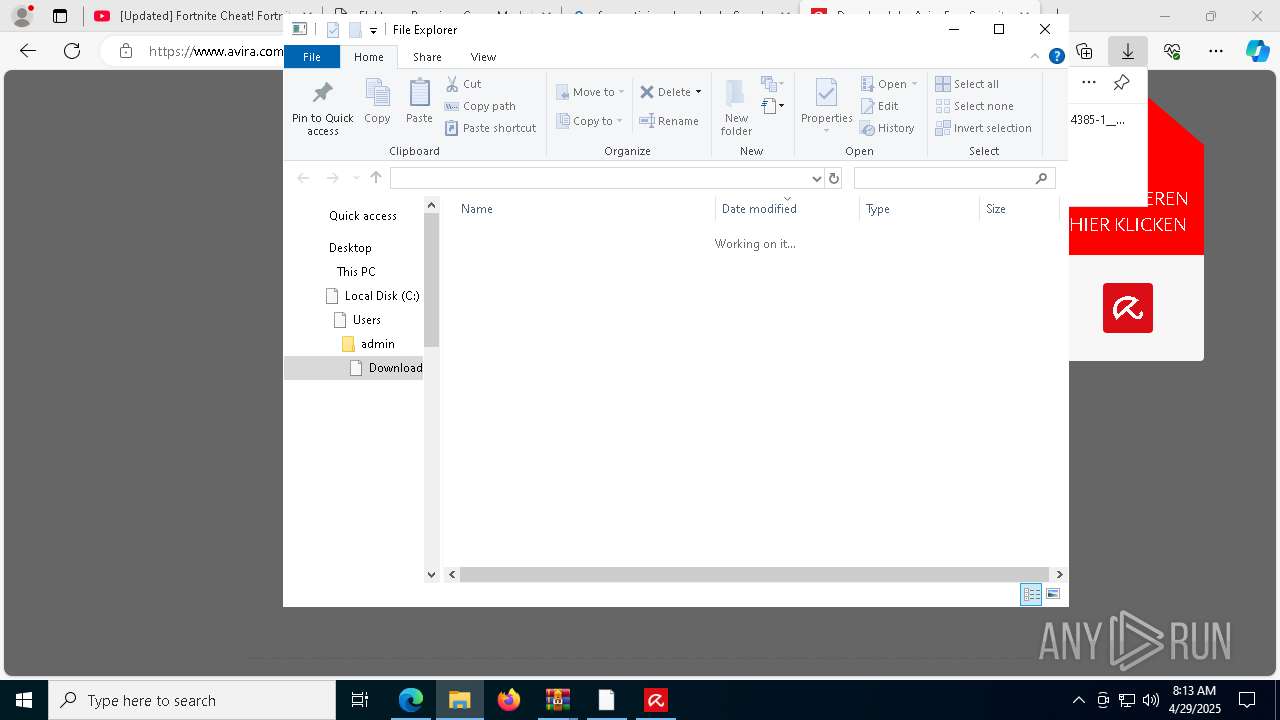
Process drops legitimate windows executable
- WinRAR.exe (PID: 6808)
- MicrosoftEdgeUpdate.exe (PID: 7548)
- MicrosoftEdgeWebView2RuntimeInstallerX64.exe (PID: 7544)
There is functionality for taking screenshot (YARA)
- Operators.com (PID: 8128)
- AVIRA.SPOTLIGHT.BOOTSTRAPPER.EXE (PID: 9032)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- Operators.com (PID: 8128)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 9008)
Executable content was dropped or overwritten
- AVIRA.SPOTLIGHT.BOOTSTRAPPER.EXE (PID: 9032)
- MicrosoftEdgeWebView2RuntimeInstallerX64.exe (PID: 7544)
- avira_de_sptl1_1617718846-1745914385-1745914385-1__pavwws-spotlight-release.exe (PID: 6852)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebView2RuntimeInstallerX64.exe (PID: 7544)
- MicrosoftEdgeUpdate.exe (PID: 7548)
- MicrosoftEdgeWebView2RuntimeInstallerX64.exe (PID: 8388)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Operators.com (PID: 8128)
INFO
Checks supported languages
- identity_helper.exe (PID: 8000)
- extrac32.exe (PID: 7052)
- Operators.com (PID: 8128)
- Elektrus.exe (PID: 9028)
Application launched itself
- msedge.exe (PID: 5640)
The sample compiled with english language support
- WinRAR.exe (PID: 6808)
- msedge.exe (PID: 5960)
- MicrosoftEdgeWebView2RuntimeInstallerX64.exe (PID: 7544)
- AVIRA.SPOTLIGHT.BOOTSTRAPPER.EXE (PID: 9032)
- MicrosoftEdgeUpdate.exe (PID: 7548)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5640)
Reads the computer name
- Elektrus.exe (PID: 9028)
- extrac32.exe (PID: 7052)
- identity_helper.exe (PID: 8000)
Create files in a temporary directory
- Elektrus.exe (PID: 9028)
- extrac32.exe (PID: 7052)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6808)
- msedge.exe (PID: 7232)
- msedge.exe (PID: 5960)
- msedge.exe (PID: 5640)
Process checks computer location settings
- Elektrus.exe (PID: 9028)
Reads Environment values
- identity_helper.exe (PID: 8000)
Creates a new folder
- cmd.exe (PID: 9172)
Reads the software policy settings
- slui.exe (PID: 7572)
Reads mouse settings
- Operators.com (PID: 8128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
277
Monitored processes
132
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=63 --mojo-platform-channel-handle=8920 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=76 --mojo-platform-channel-handle=8560 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=40 --mojo-platform-channel-handle=5512 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6256 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
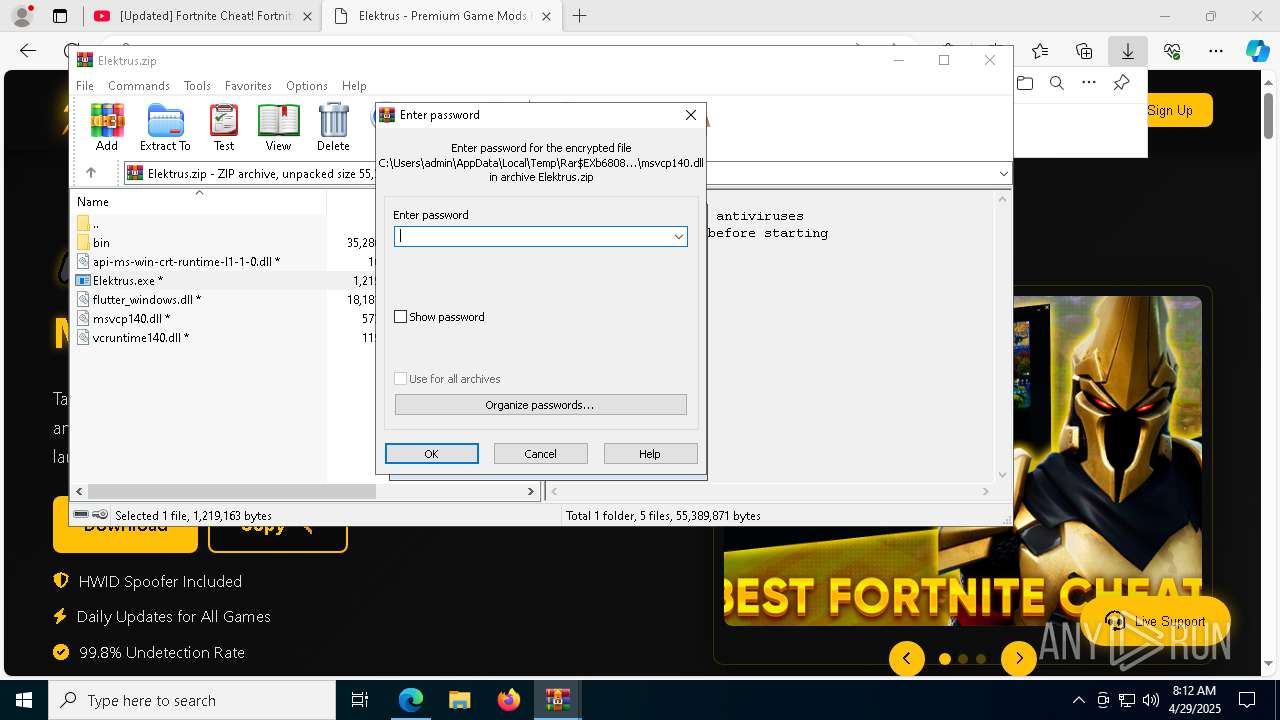
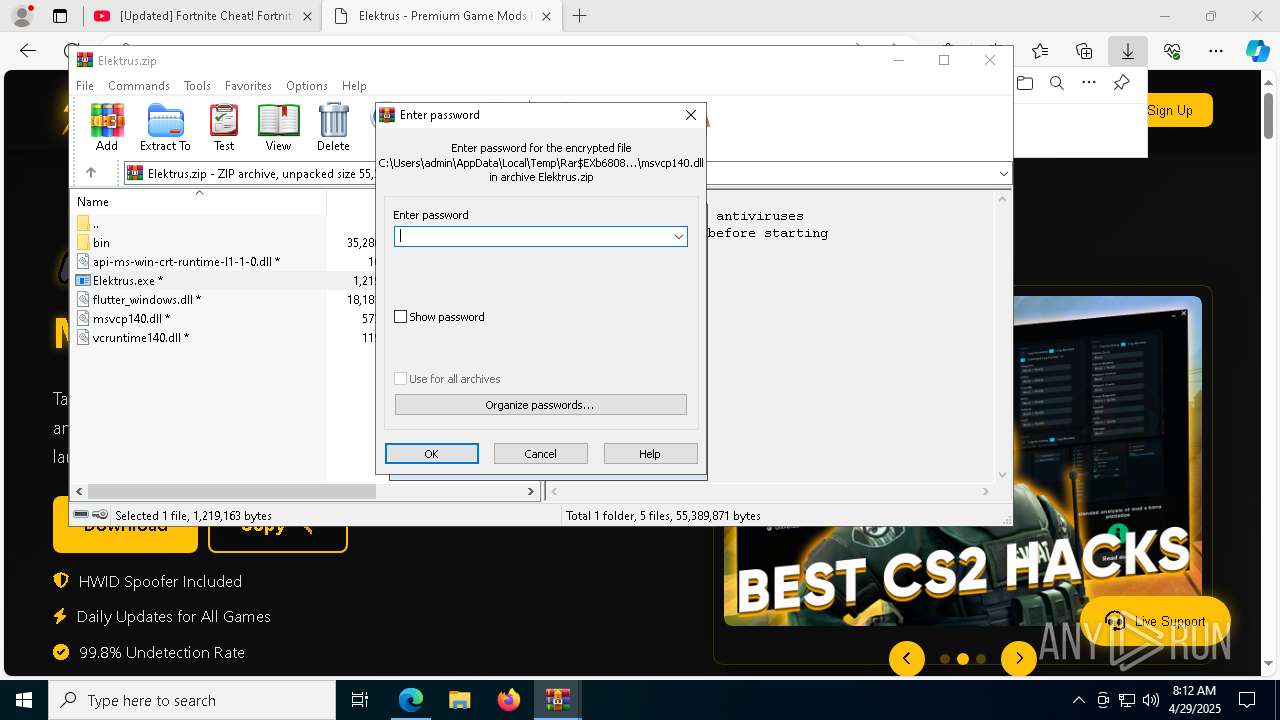
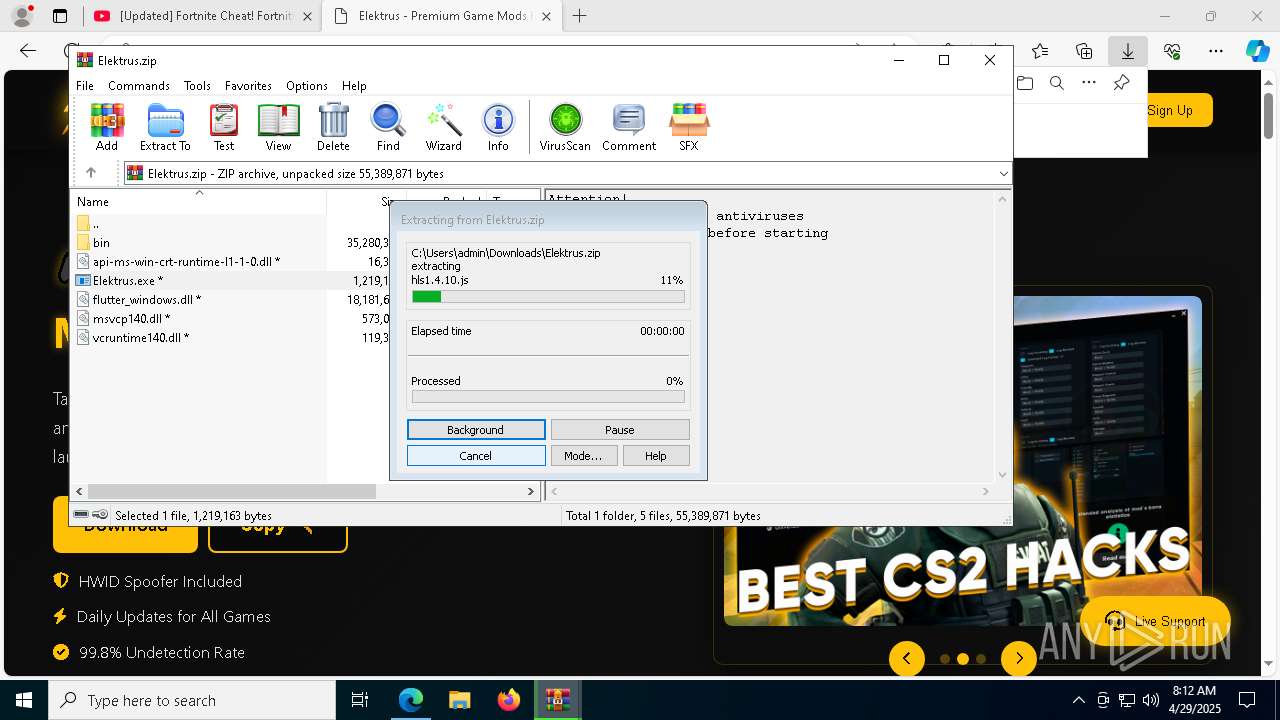
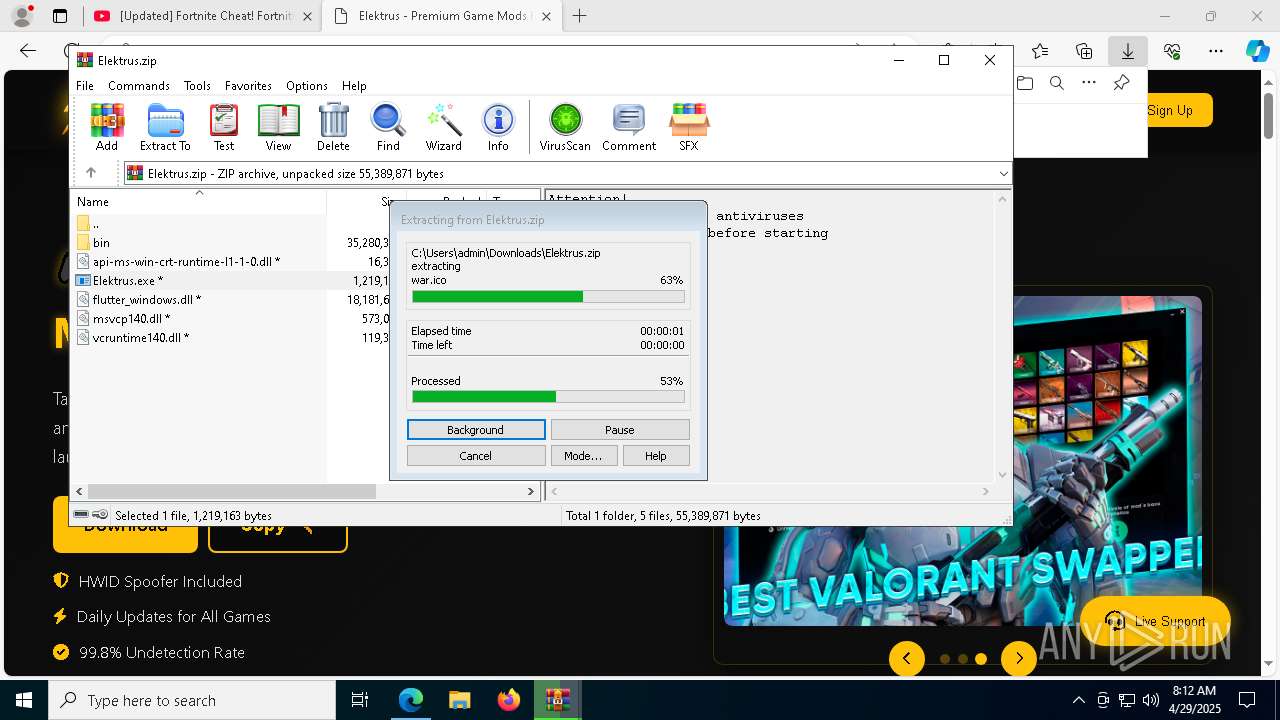
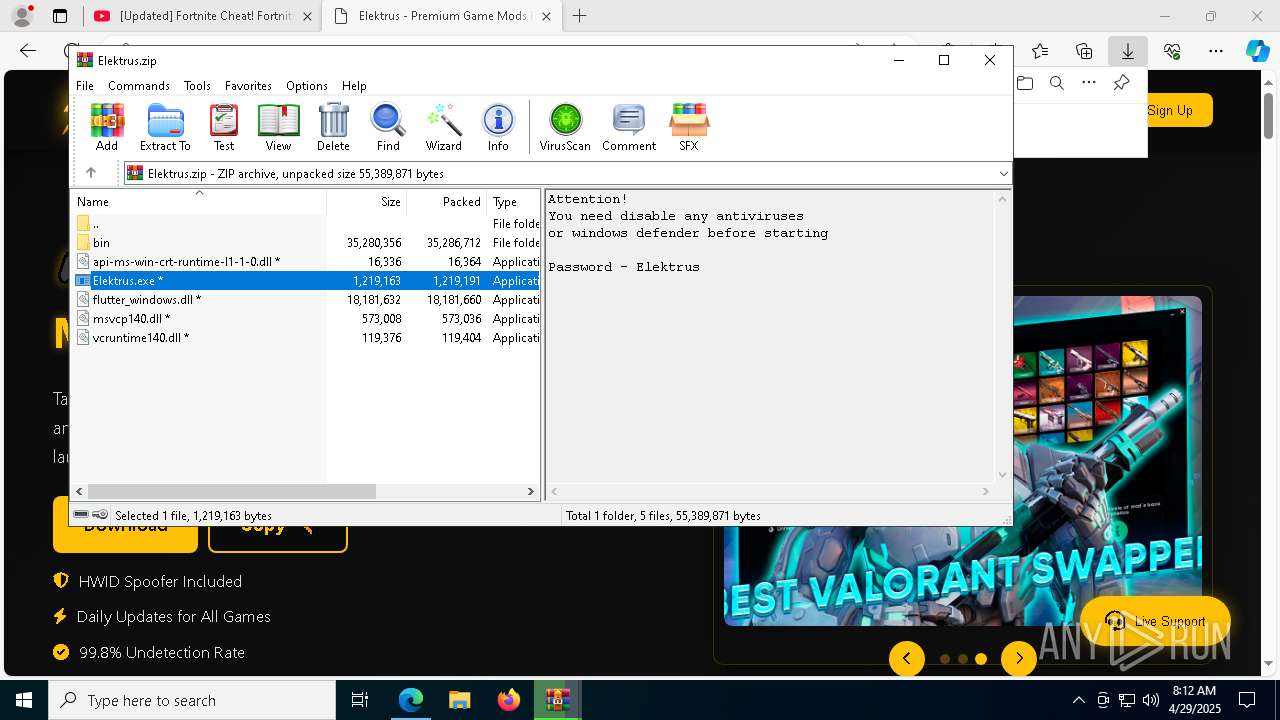
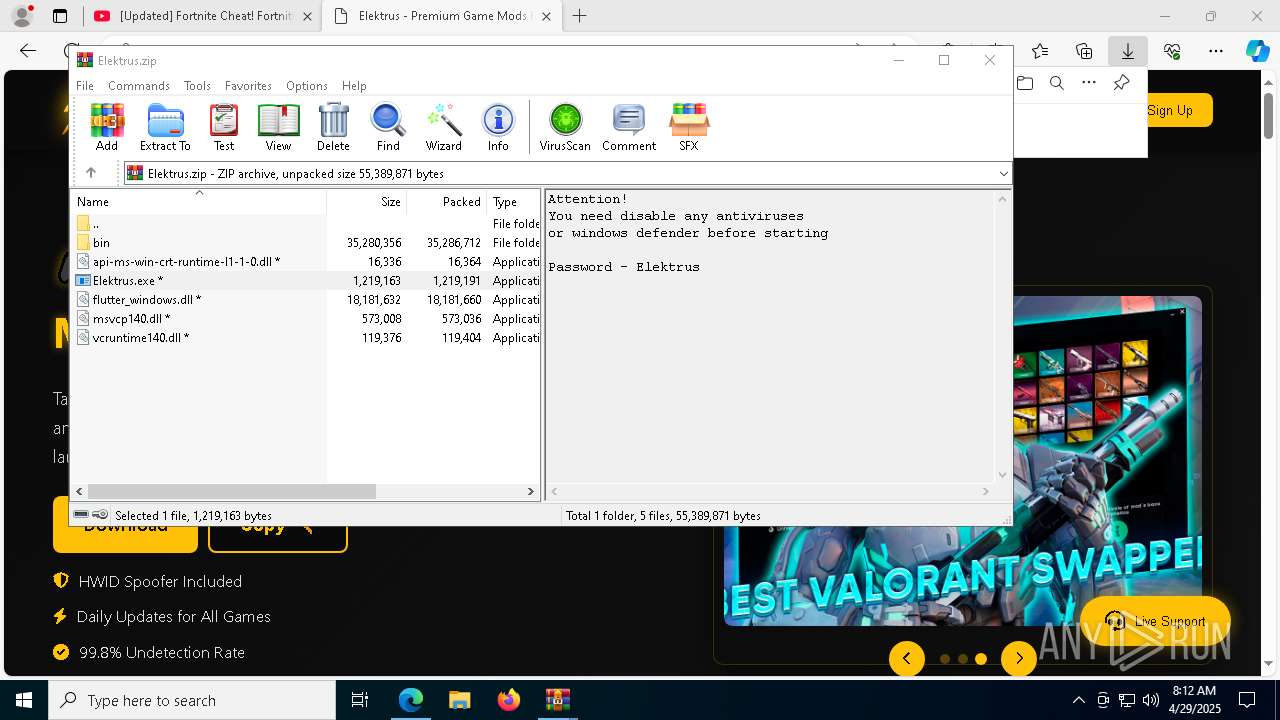
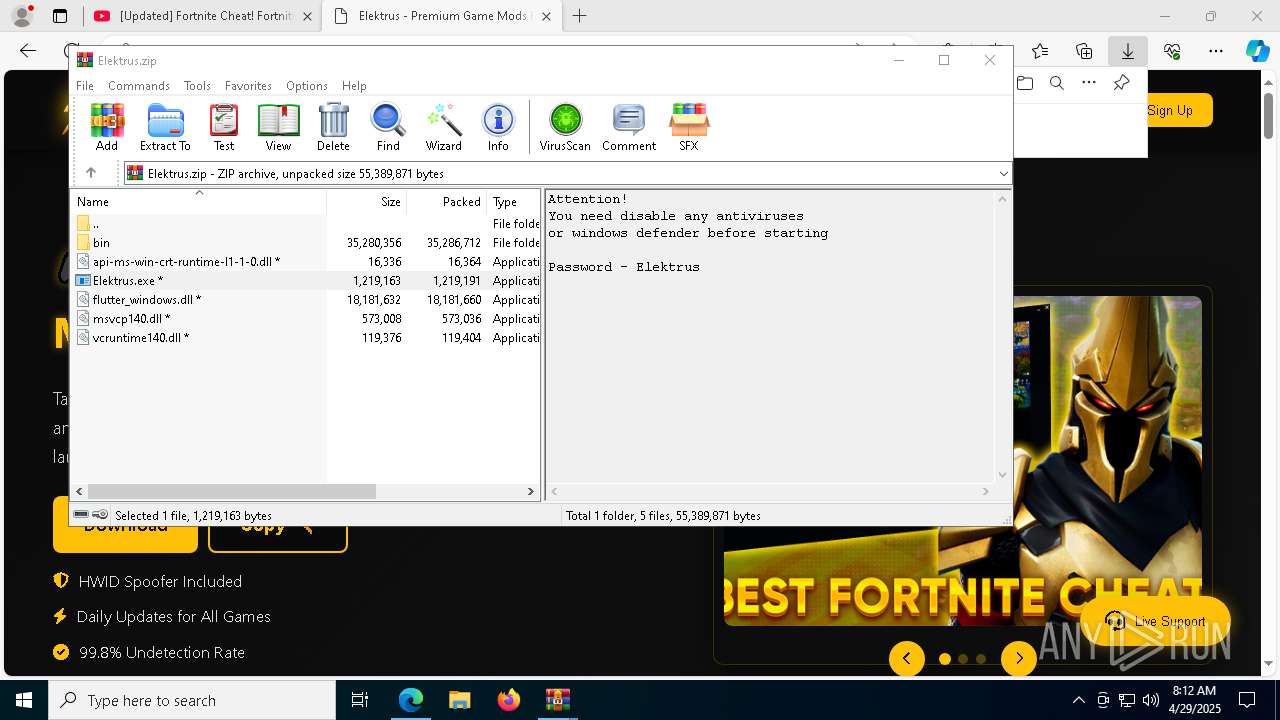
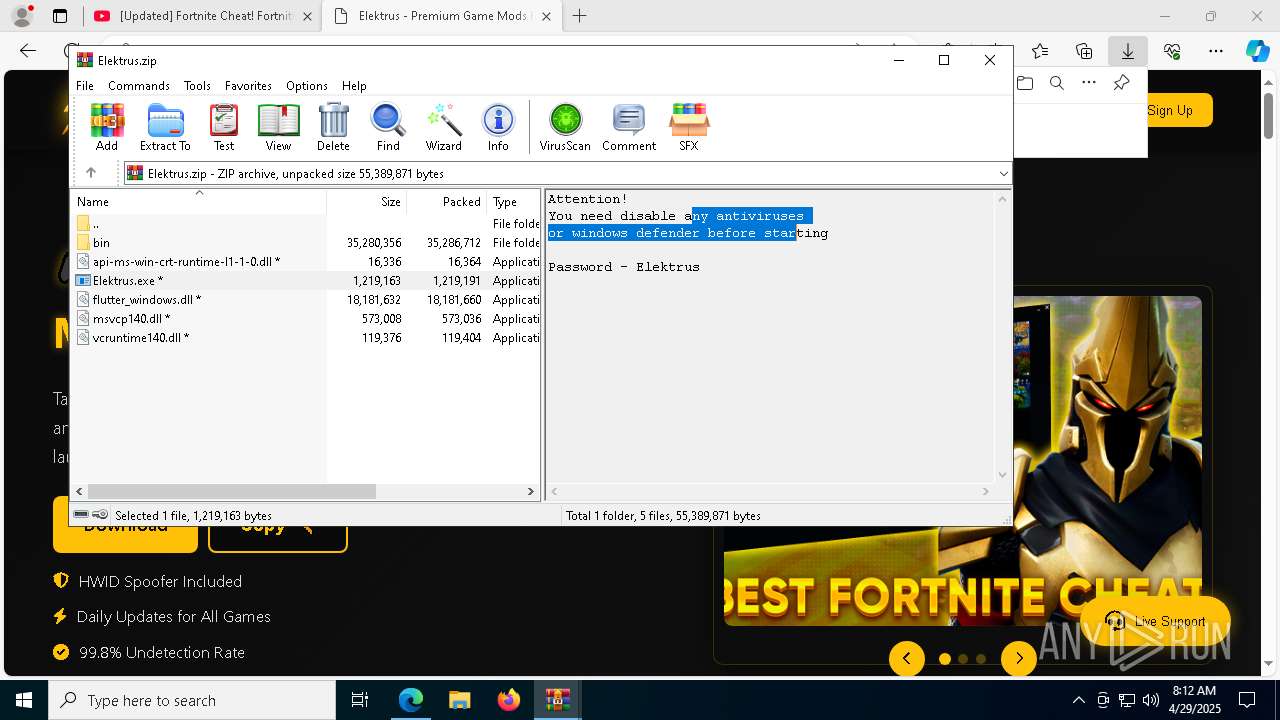
| 1168 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Elektrus.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=75 --mojo-platform-channel-handle=5932 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6516 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=86 --mojo-platform-channel-handle=8904 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=65 --mojo-platform-channel-handle=8608 --field-trial-handle=2352,i,12362162349318907501,16506823585735024591,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
88 020
Read events
87 397
Write events
584
Delete events
39
Modification events
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 77114D9F7C922F00 | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 165B579F7C922F00 | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C3A2A359-F23D-4240-8FE3-3391D7E31895} | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A2650C17-316C-4171-B314-A6664DC4AAB6} | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 94ED909F7C922F00 | |||
| (PID) Process: | (5640) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
290
Suspicious files
1 457
Text files
455
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10baa7.TMP | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 5640 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
439
DNS requests
576
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8904 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8904 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
900 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418006&P2=404&P3=2&P4=man%2b006fLHr1c7xJoyMiSoRiCvwa25f9b7hau7UGjXngVzUI53RdfwRgY8s0uzqCtw9ZWWizkOf1z1r3QC7jeQ%3d%3d | unknown | — | — | whitelisted |
900 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746418005&P2=404&P3=2&P4=O7HX9sHhLt8nGlJ%2bTwHhKIHgxGeI88jE%2fgRaagT1eyRkeFg5vATfgSPp8BW8Ut7skg%2bb%2fEHOuP2n066Z7RXaVQ%3d%3d | unknown | — | — | whitelisted |
900 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1746418005&P2=404&P3=2&P4=NpvfJVp%2bN8muMxyHfmaZfgOp77fqNZ4x2jdhwr3QlADGySN%2bkBmlW%2ftpTXI8gduczTP5FJof6HV1dUtb9zC10A%3d%3d | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418006&P2=404&P3=2&P4=man%2b006fLHr1c7xJoyMiSoRiCvwa25f9b7hau7UGjXngVzUI53RdfwRgY8s0uzqCtw9ZWWizkOf1z1r3QC7jeQ%3d%3d | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418006&P2=404&P3=2&P4=man%2b006fLHr1c7xJoyMiSoRiCvwa25f9b7hau7UGjXngVzUI53RdfwRgY8s0uzqCtw9ZWWizkOf1z1r3QC7jeQ%3d%3d | unknown | — | — | whitelisted |
900 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1746418006&P2=404&P3=2&P4=eBKEpRK3fn%2fC%2fcwFki5znJDSTy9aa0xqkE5CrSwMQ%2fcBzO1YYmKjqSe5i2da56qYy1JyI0PYbuk9Vim1uHOWvQ%3d%3d | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1746418006&P2=404&P3=2&P4=eBKEpRK3fn%2fC%2fcwFki5znJDSTy9aa0xqkE5CrSwMQ%2fcBzO1YYmKjqSe5i2da56qYy1JyI0PYbuk9Vim1uHOWvQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7232 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5640 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7232 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
youtub.com |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
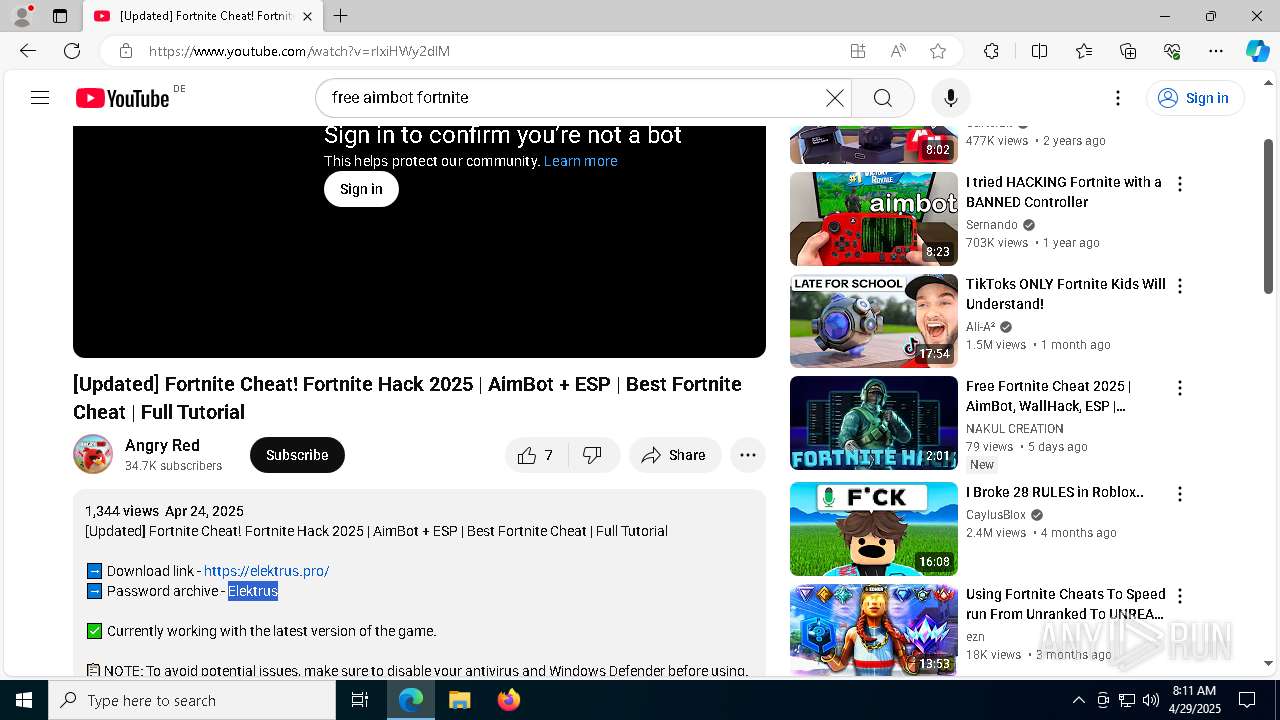
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
8128 | Operators.com | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (mediaflowq .run) |