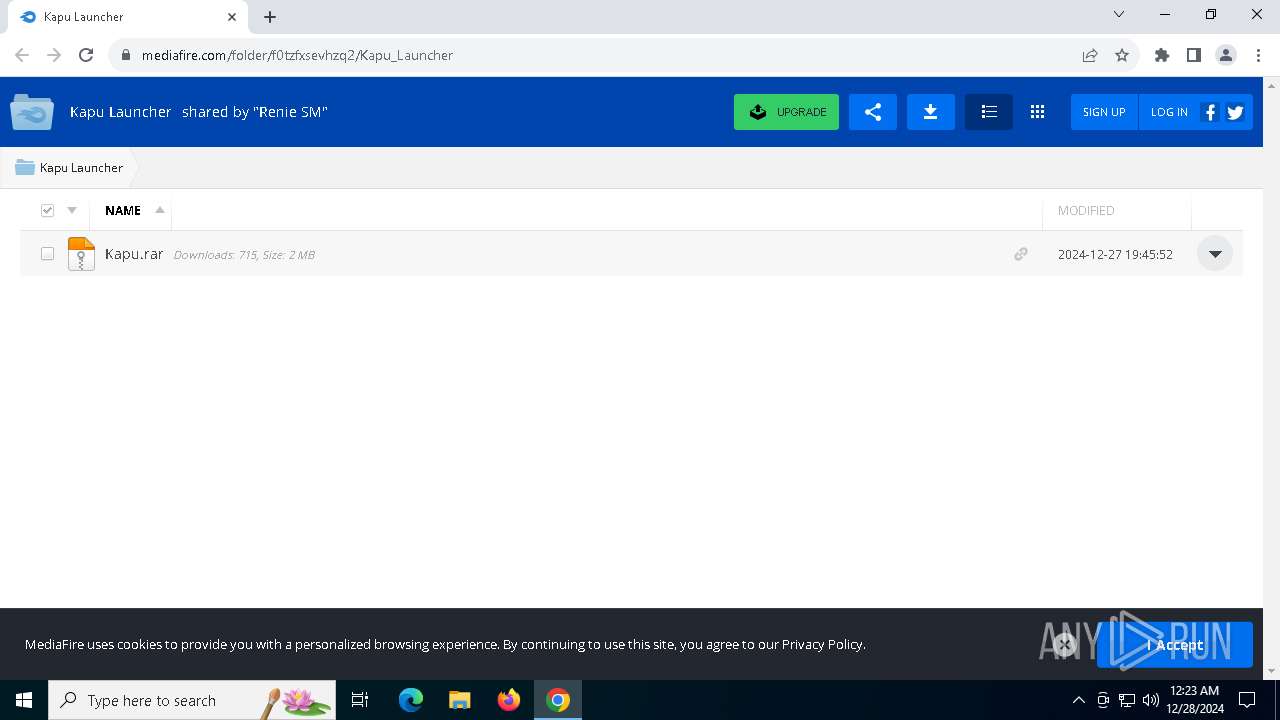
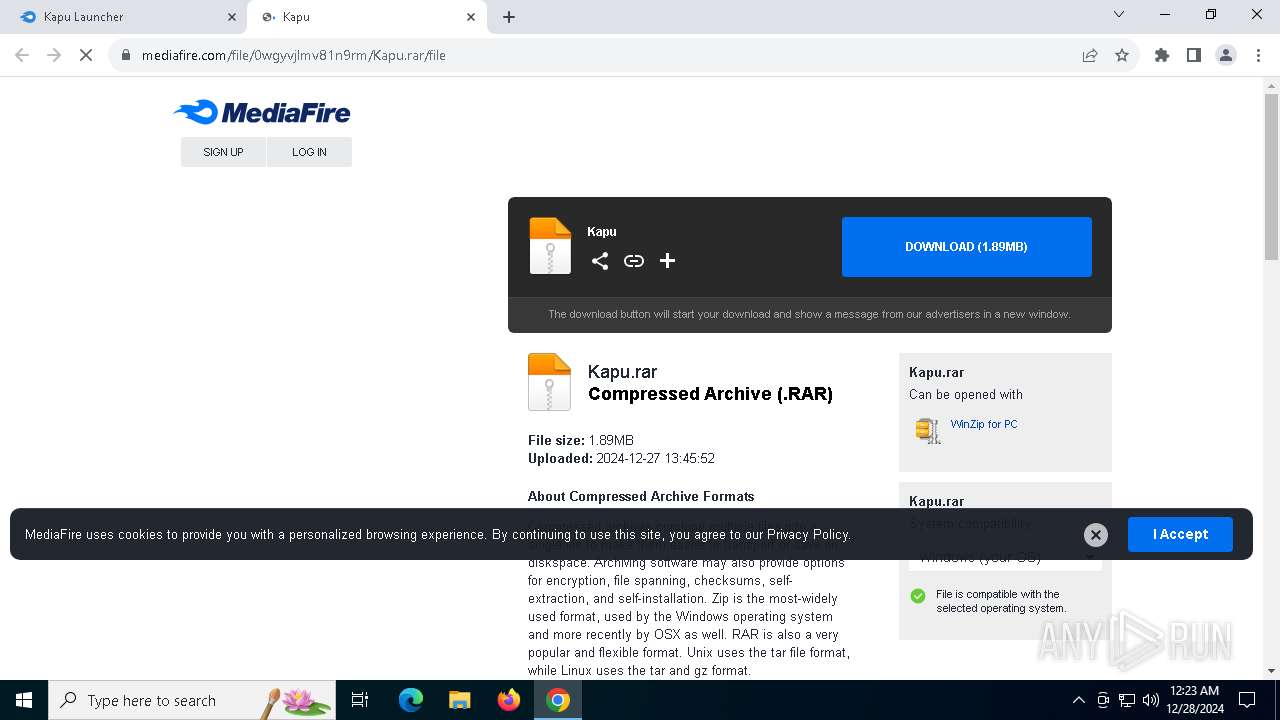
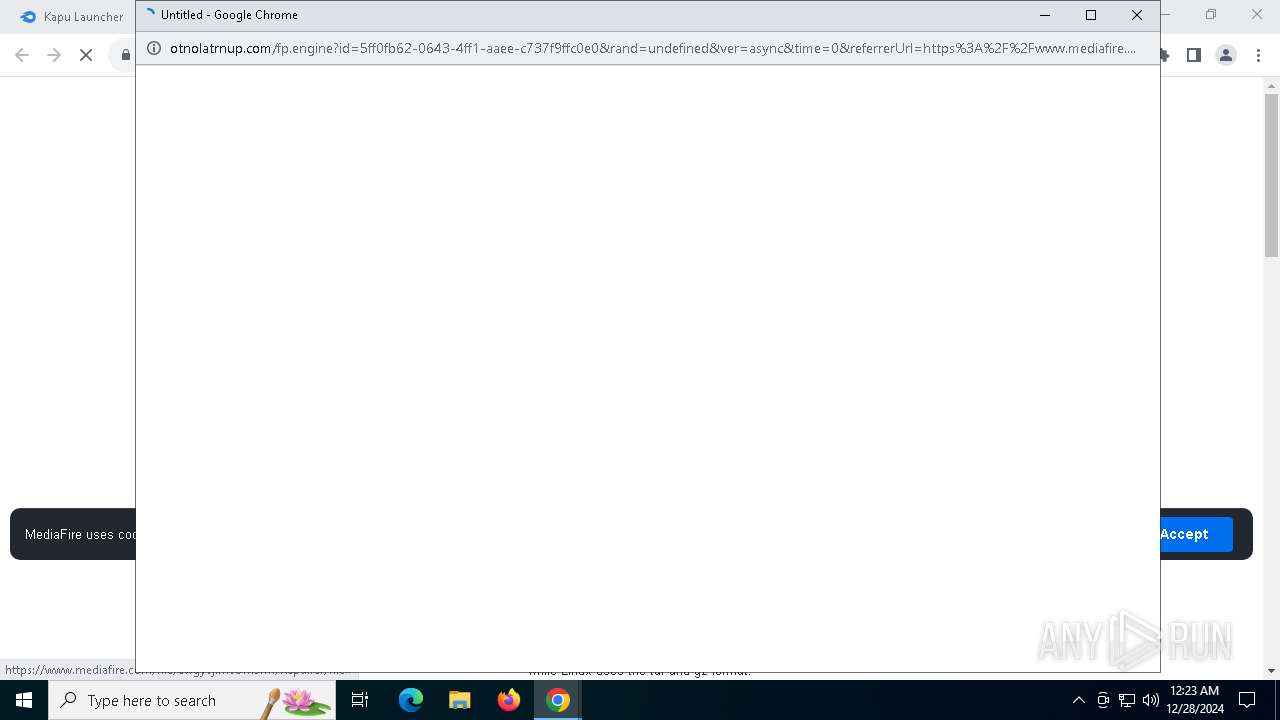
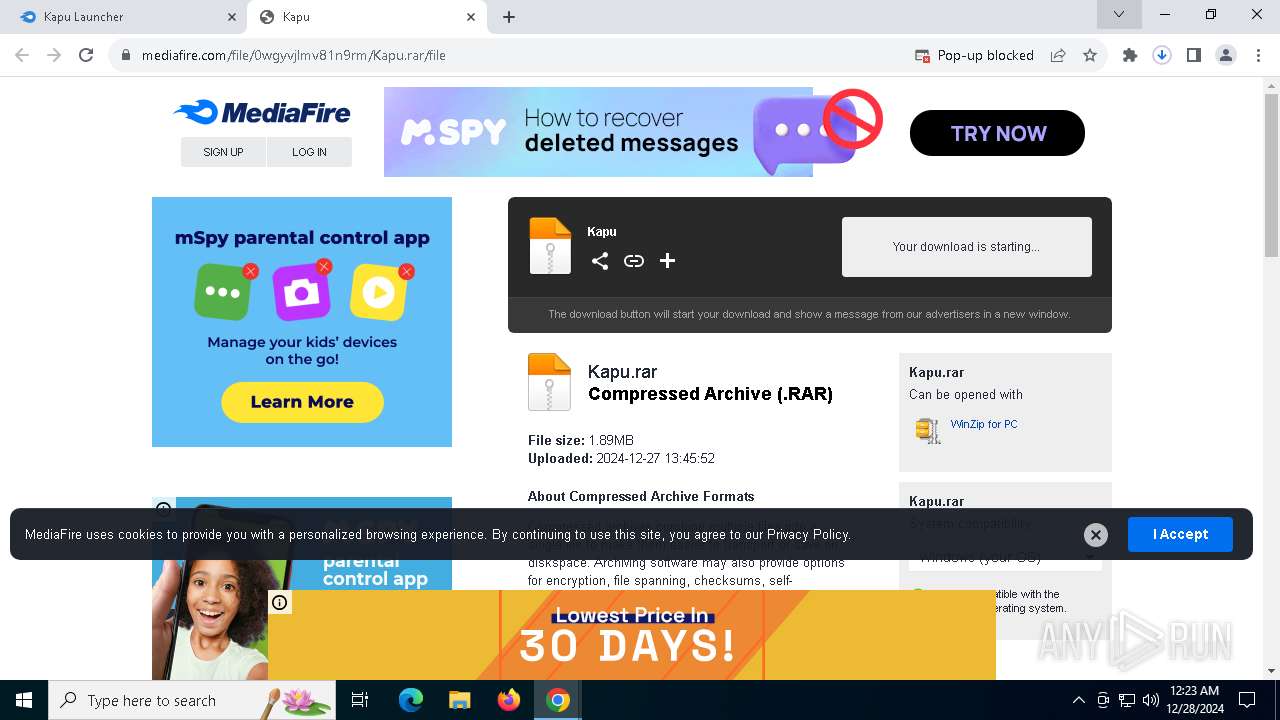
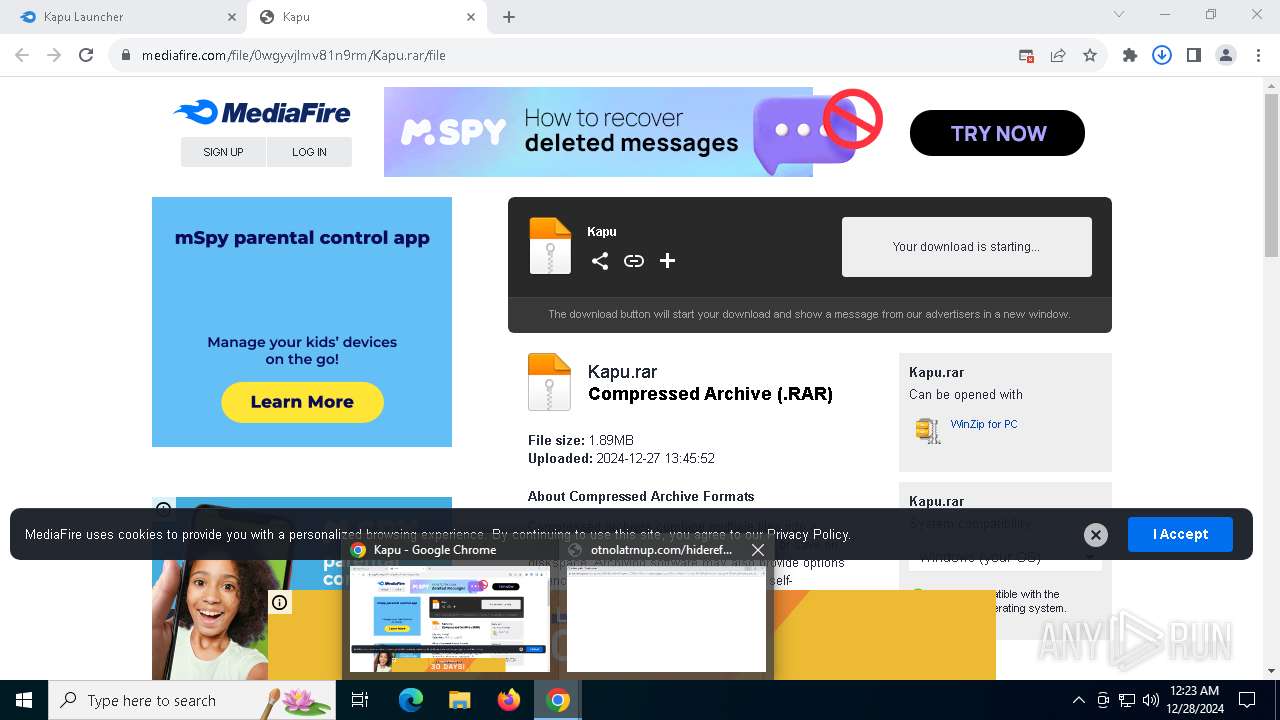
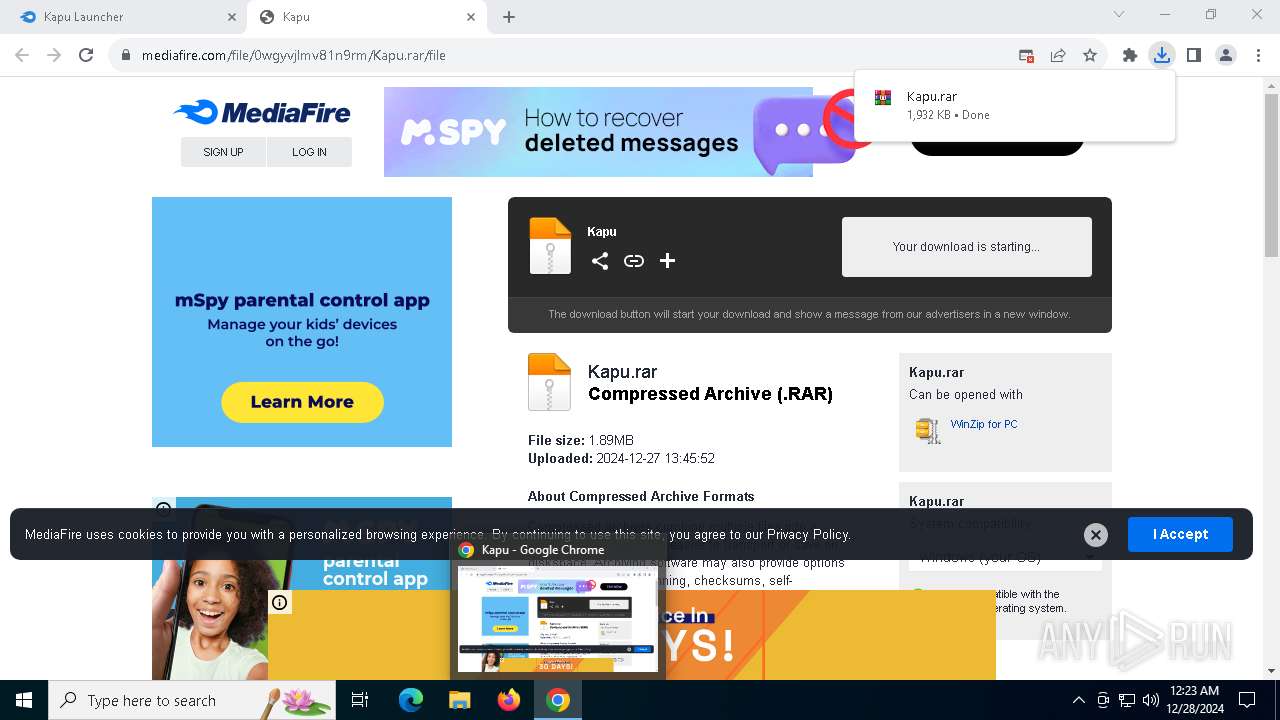
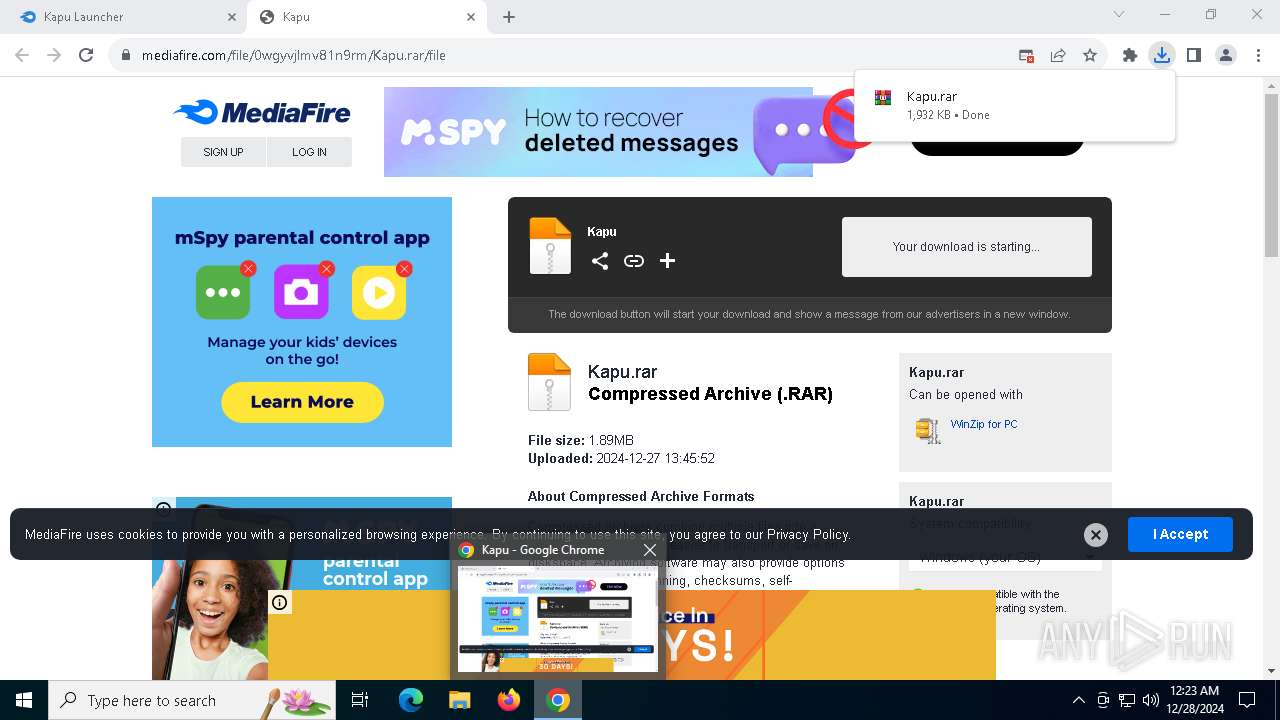
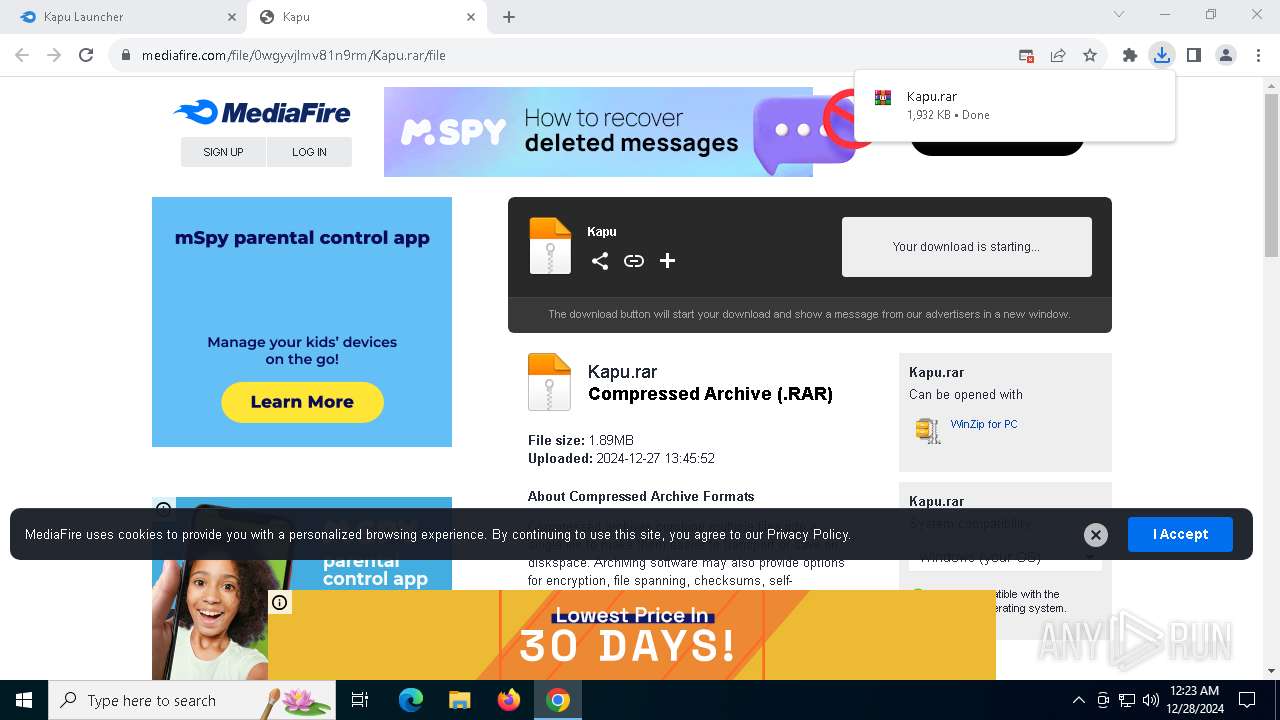
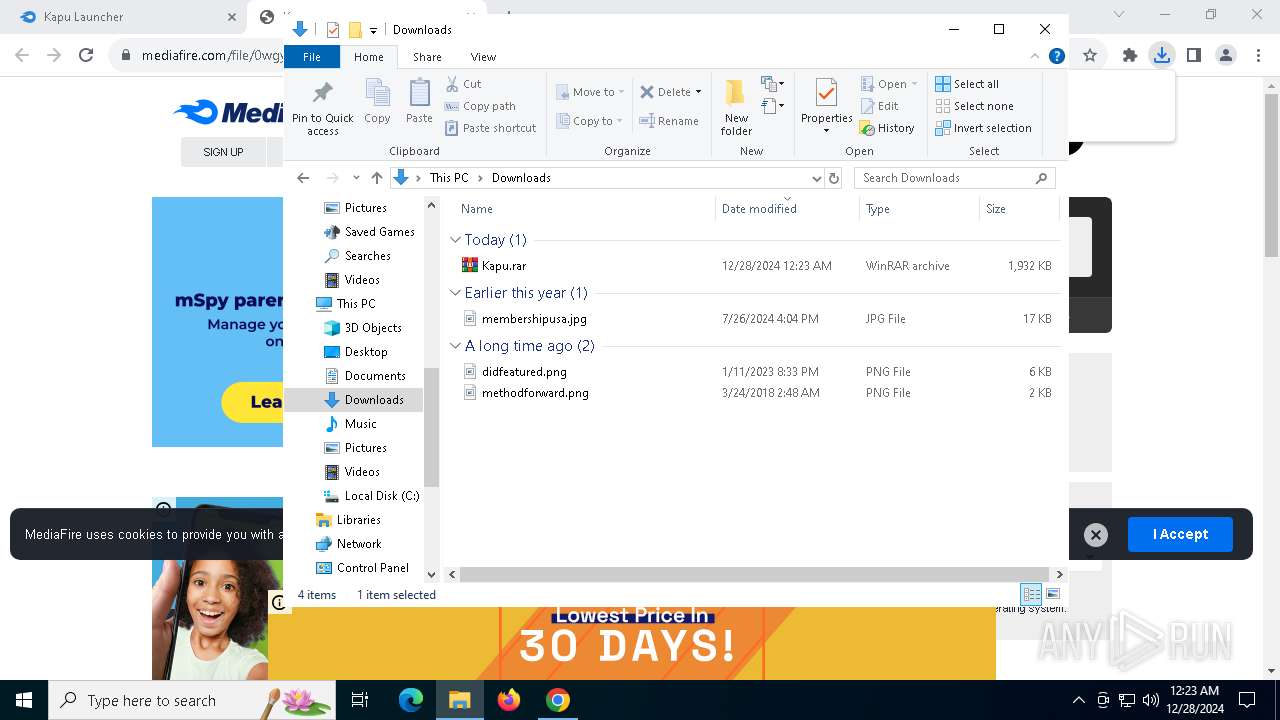
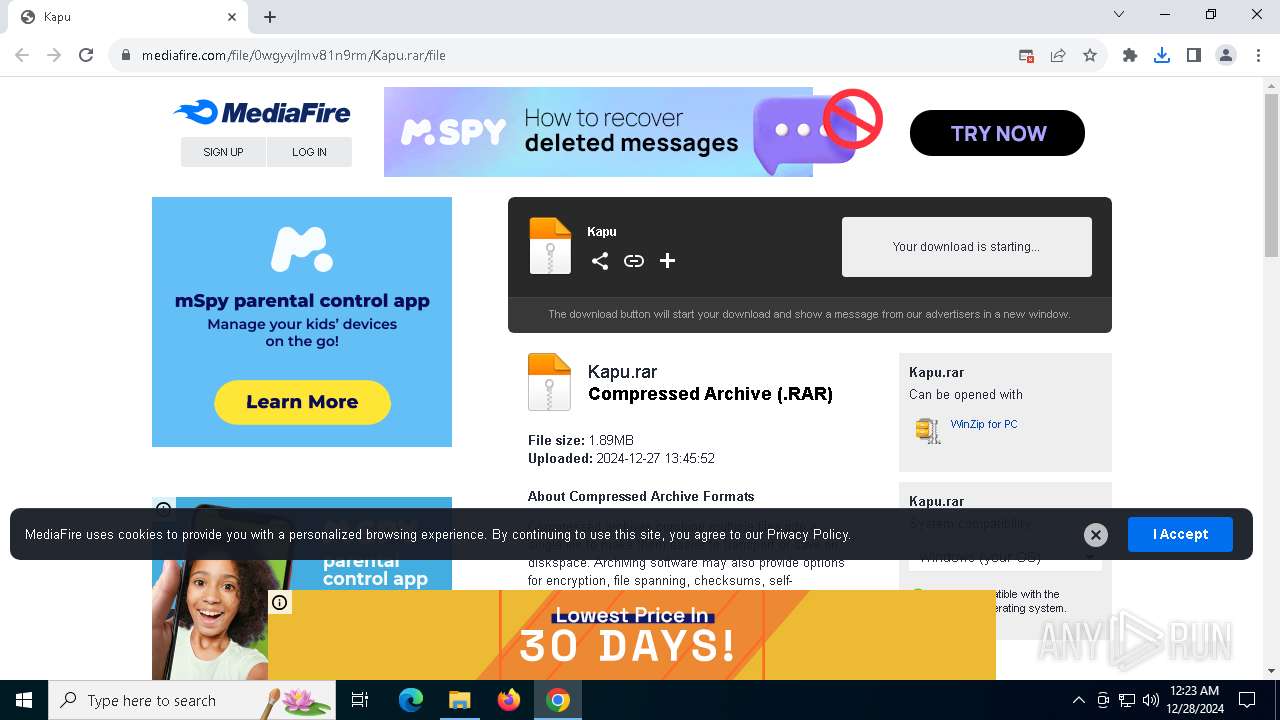
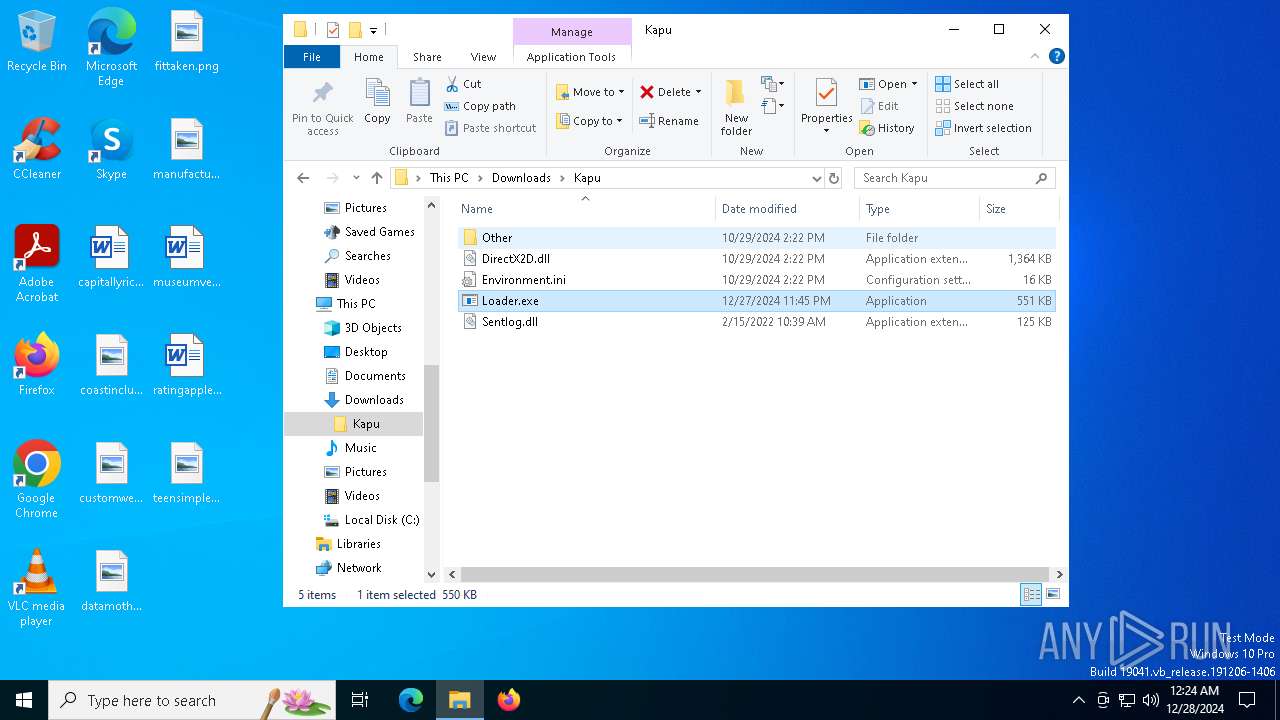
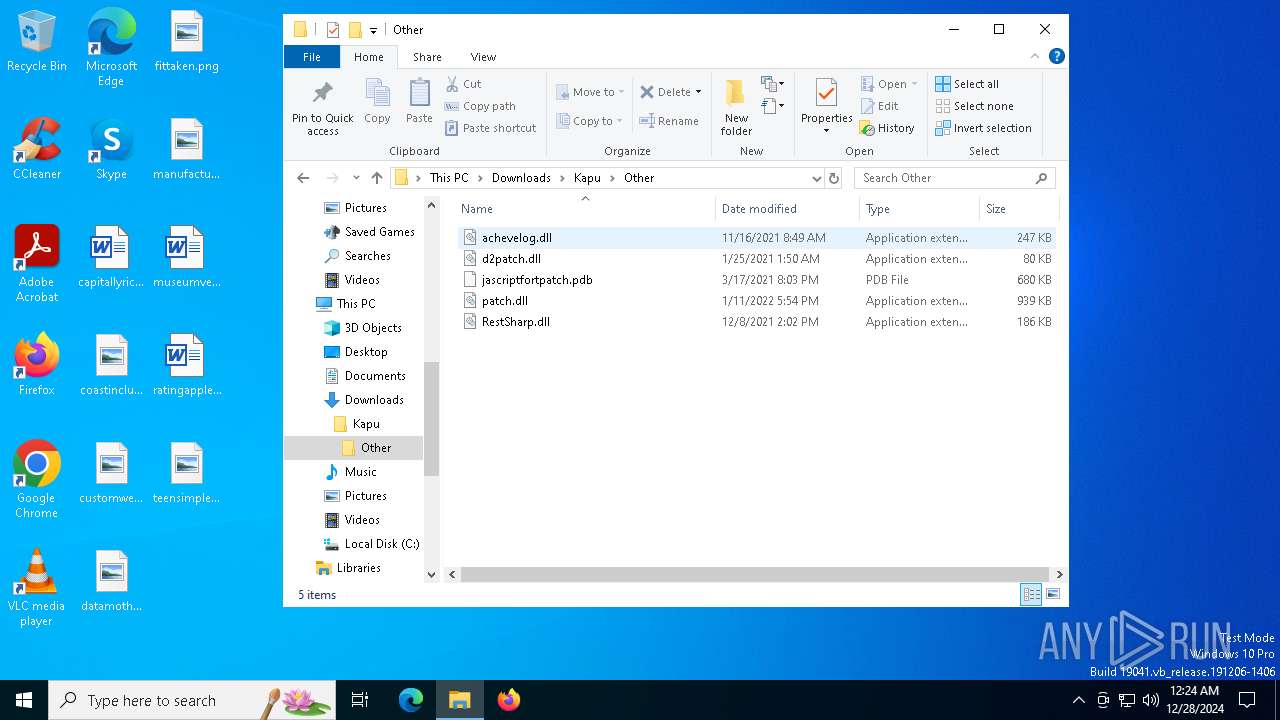
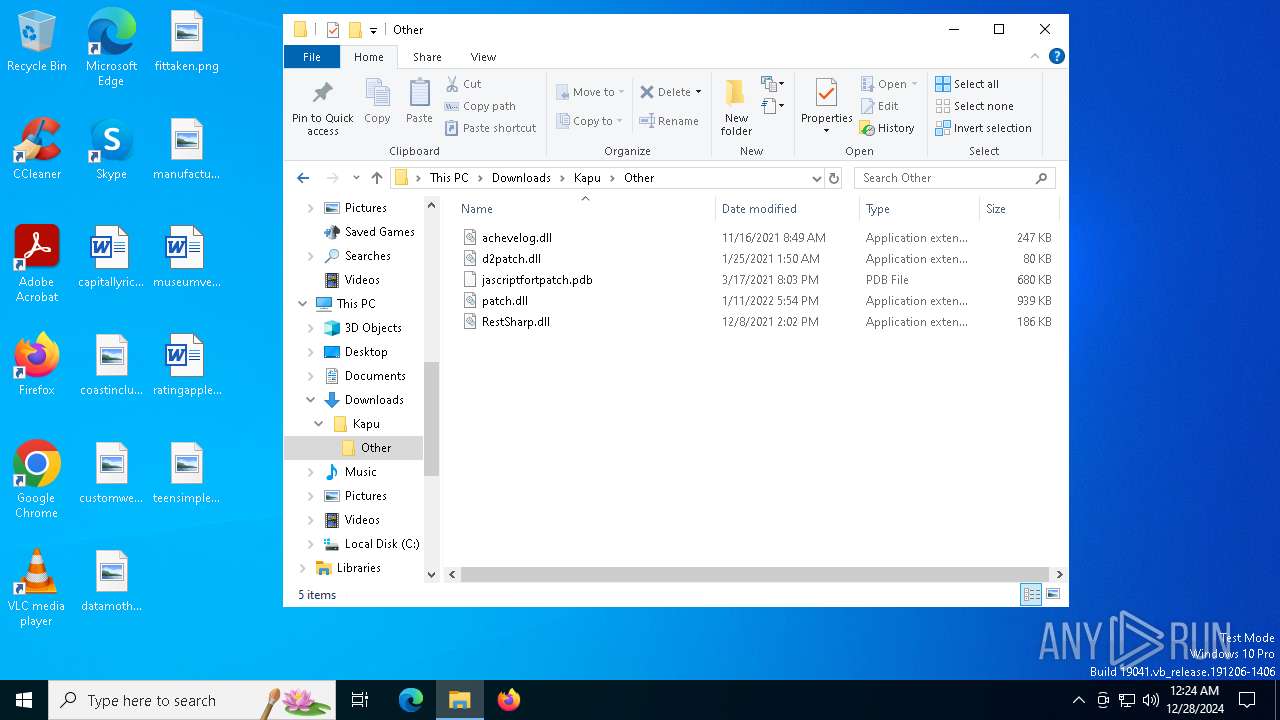
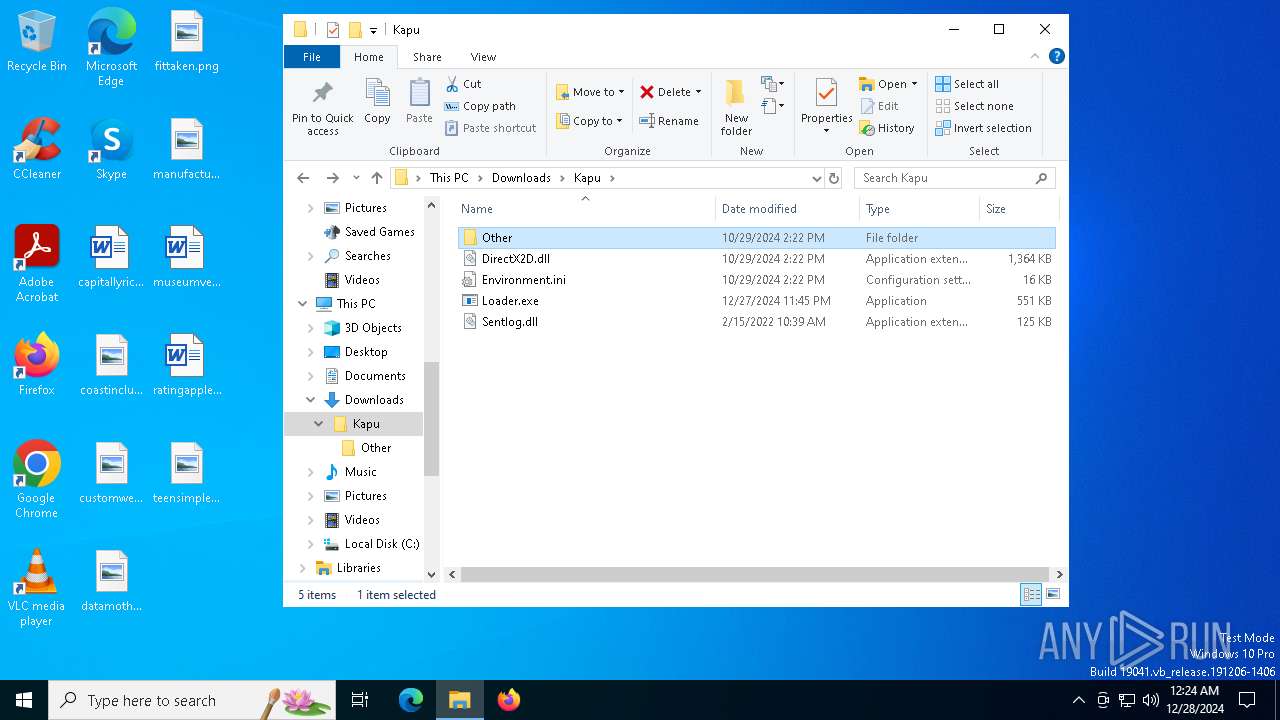
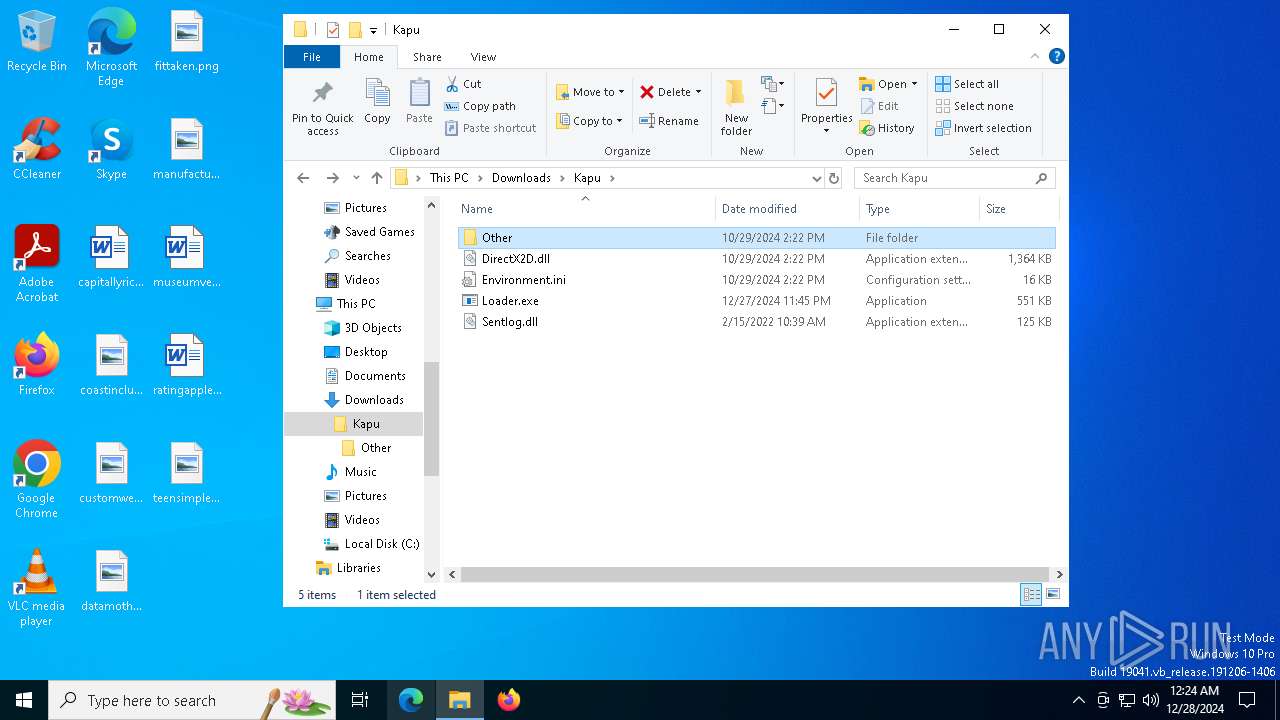
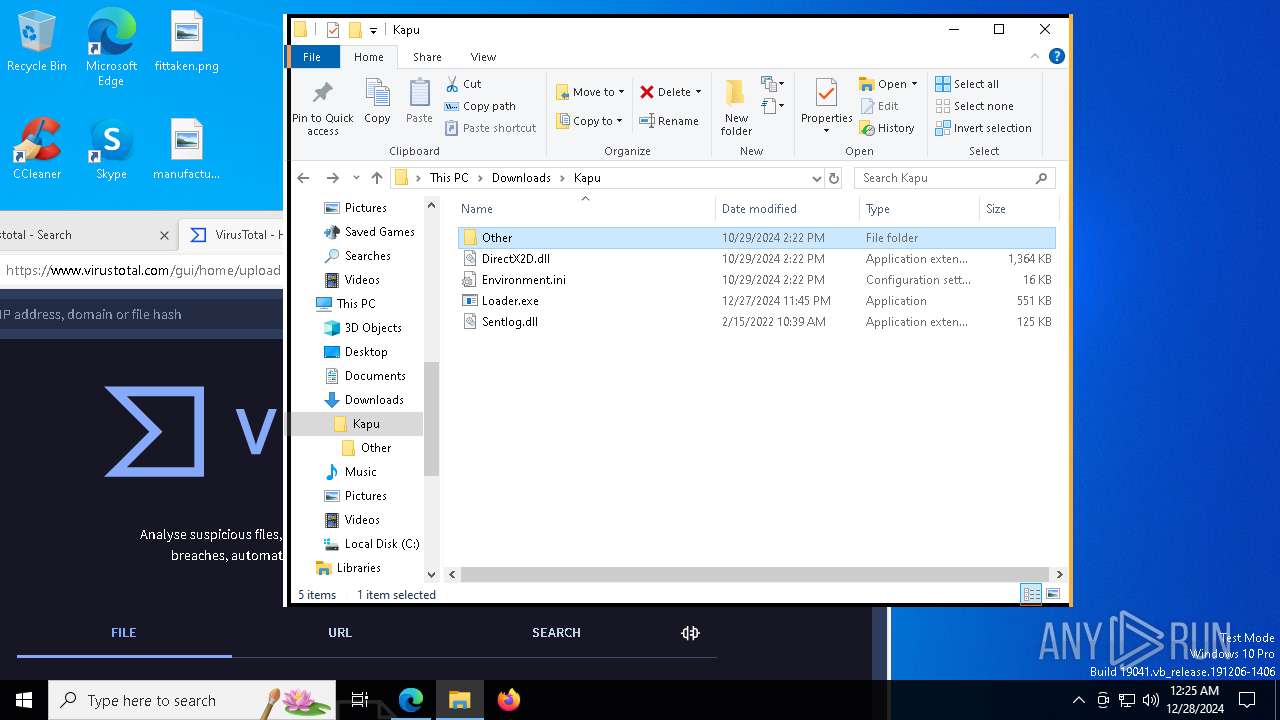
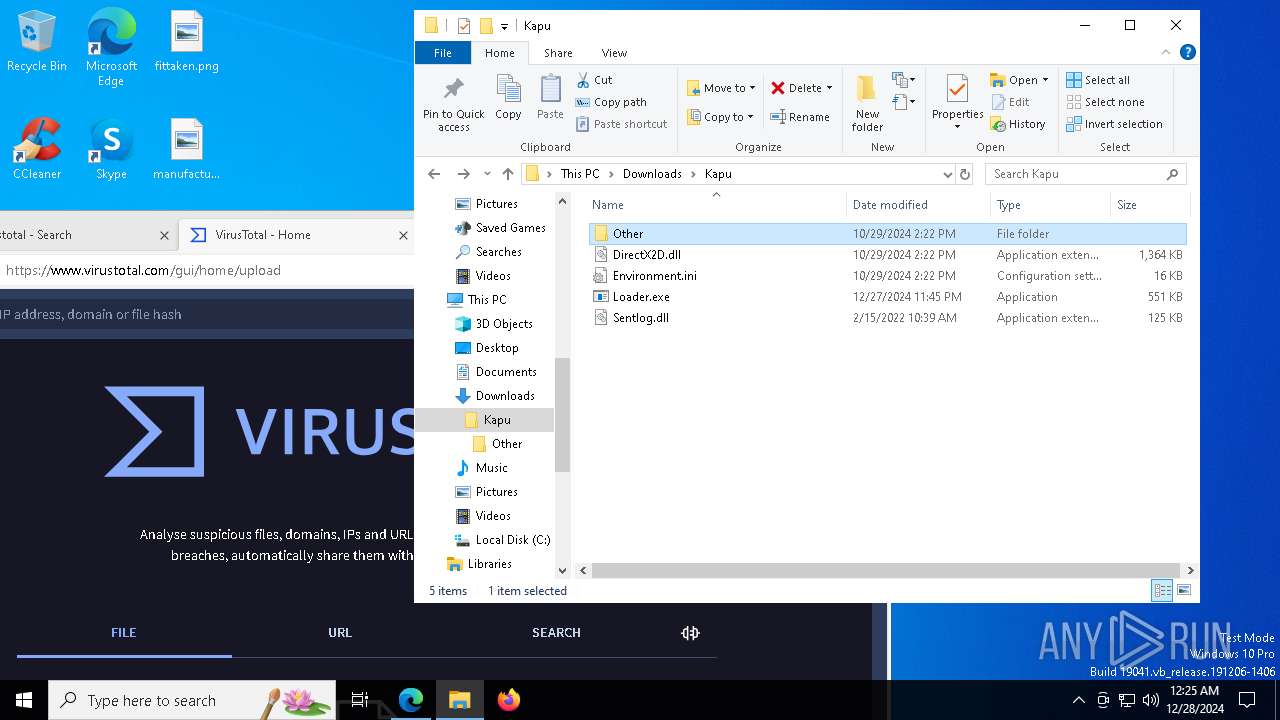
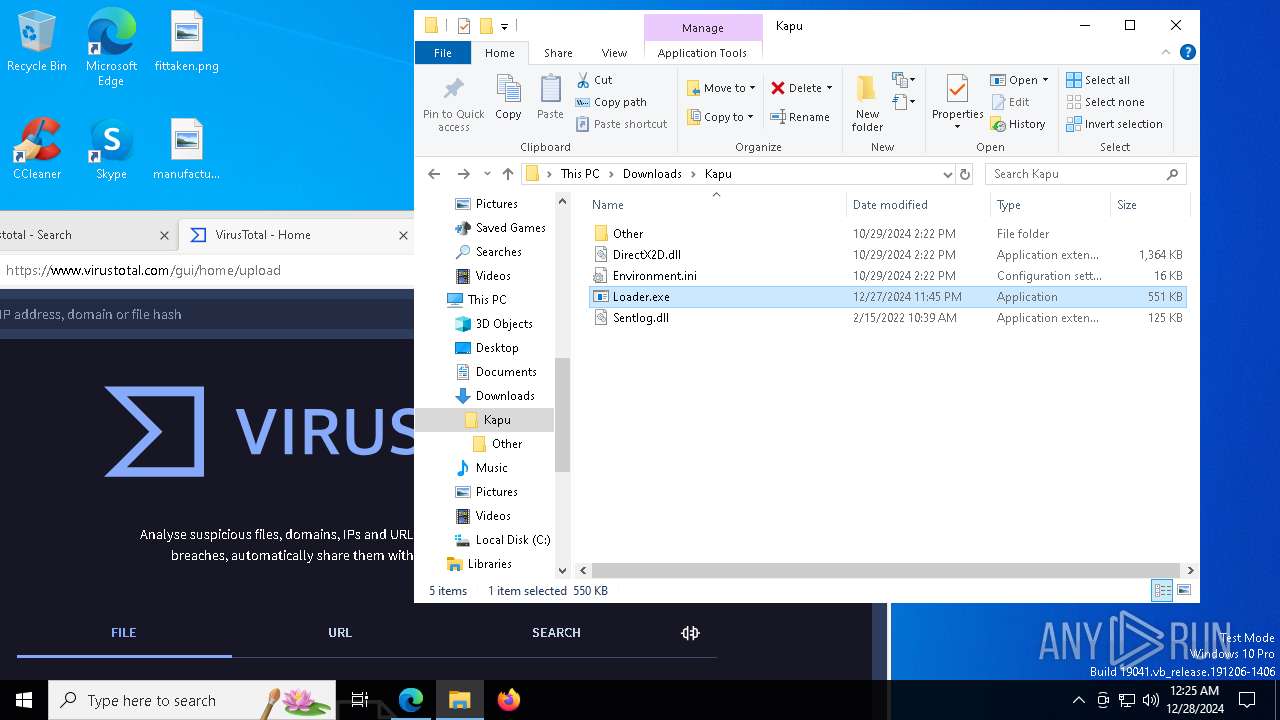
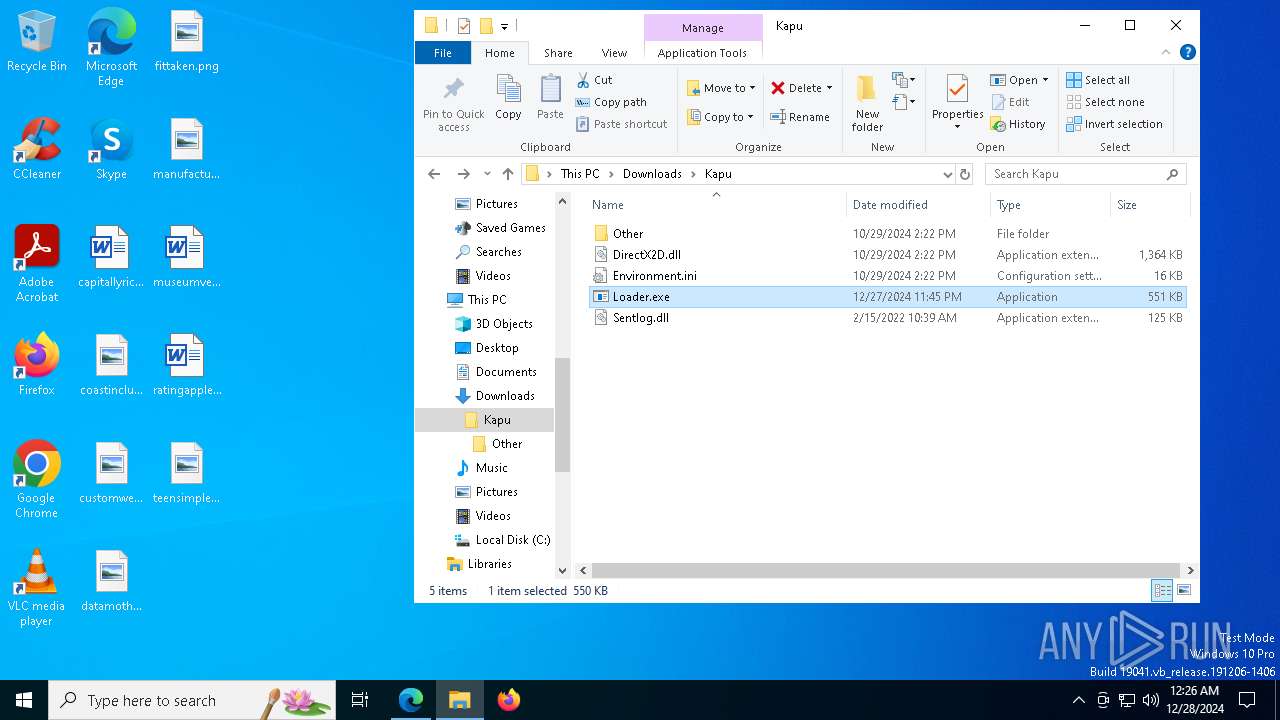
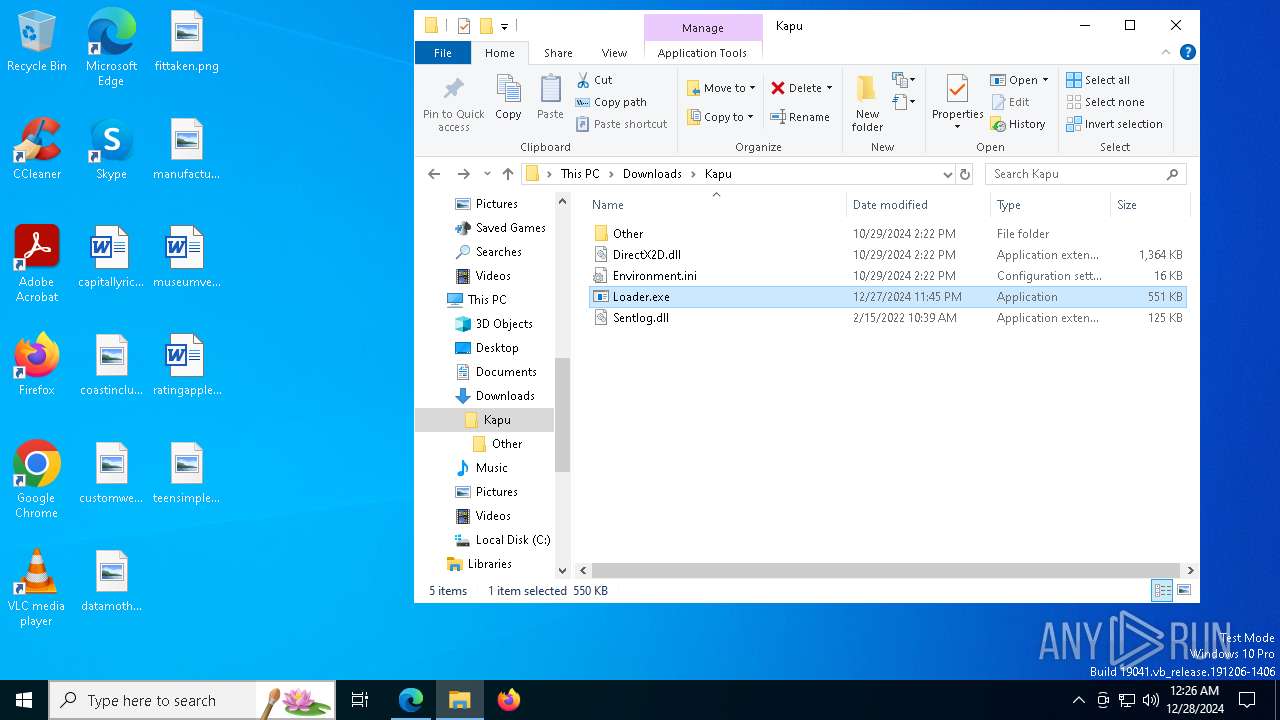
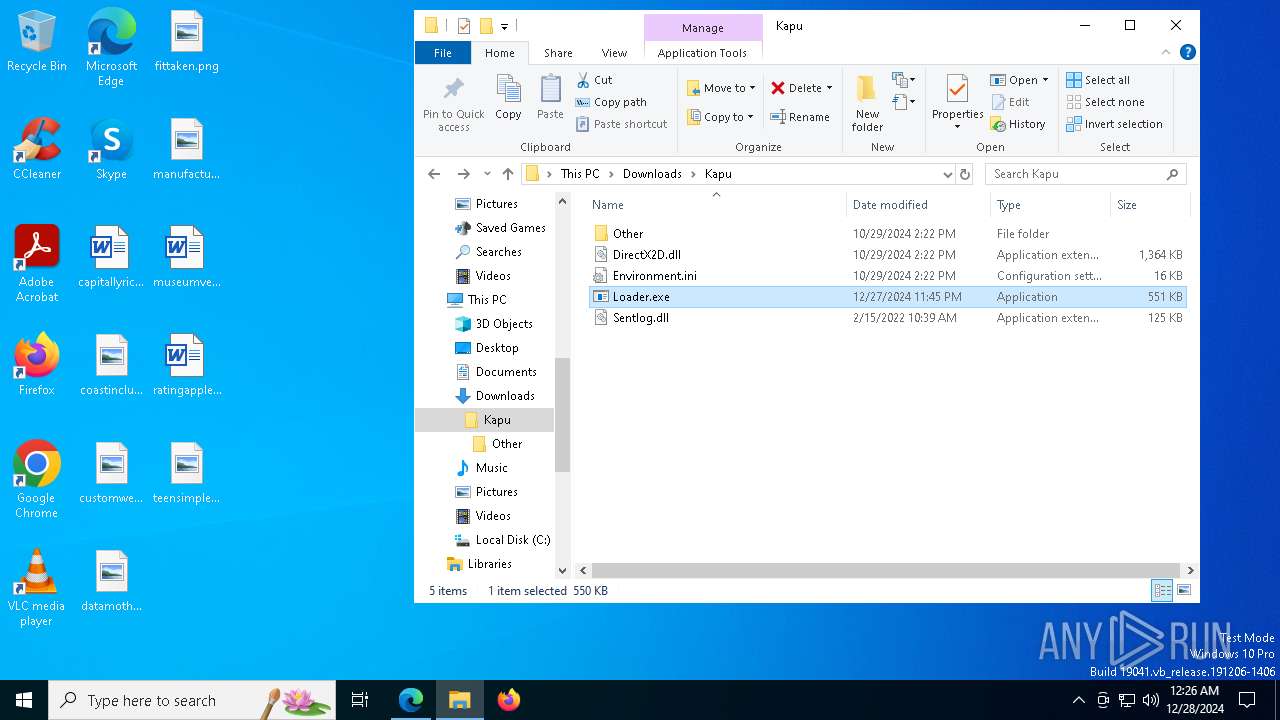
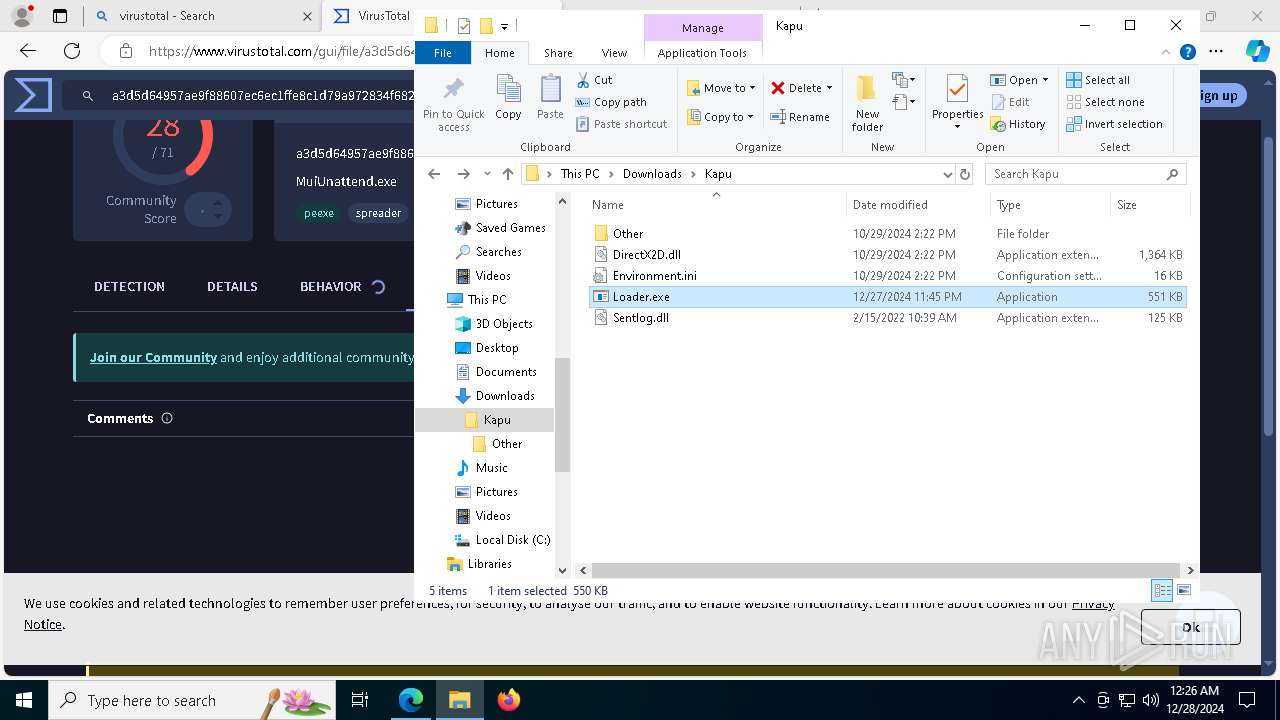
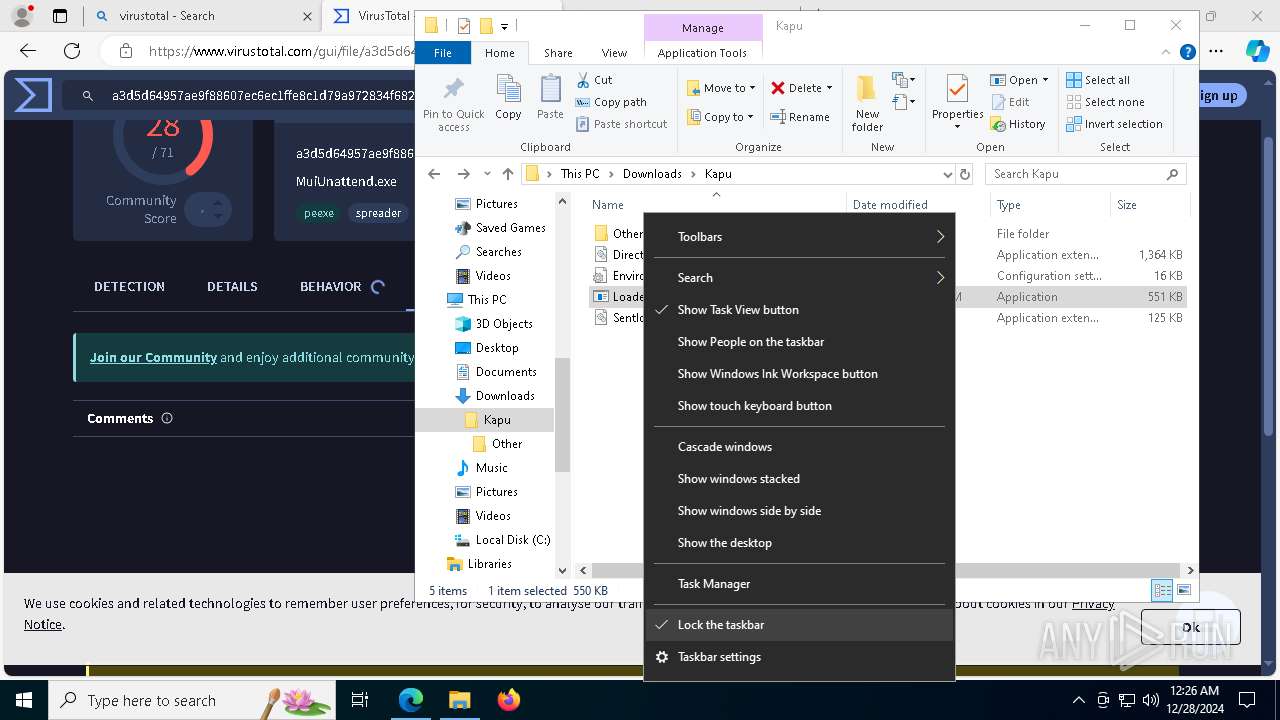
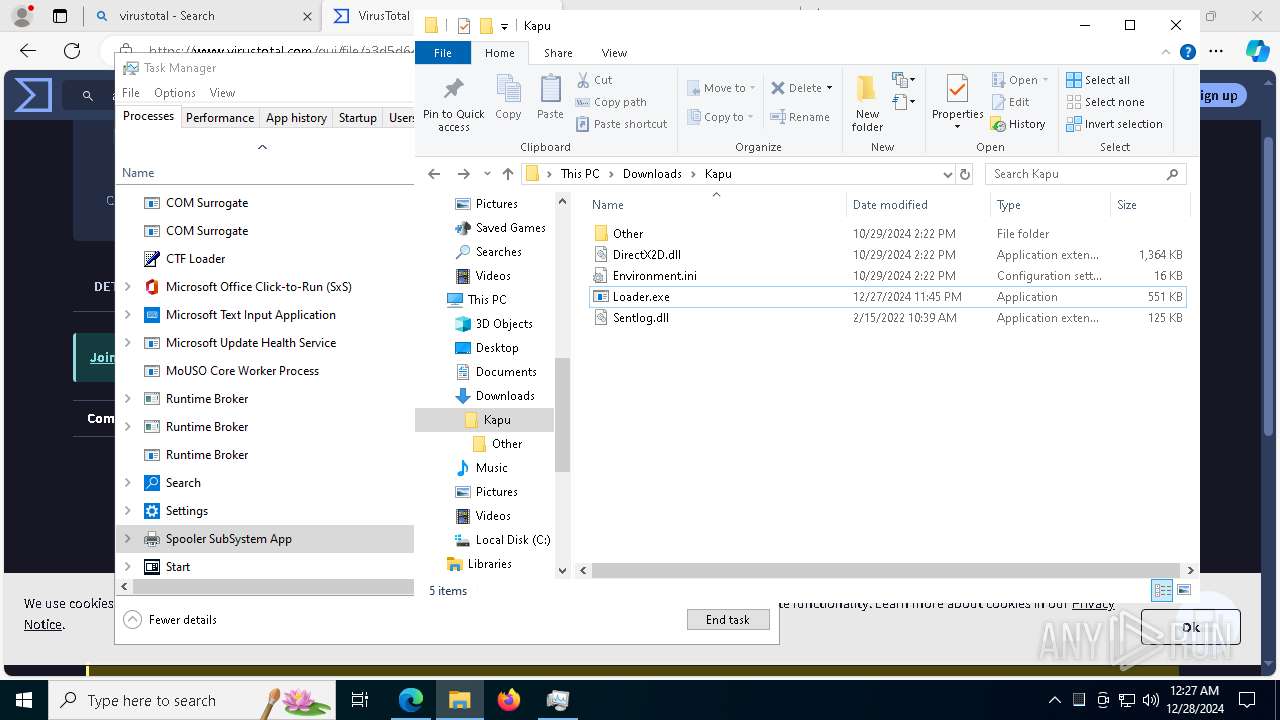
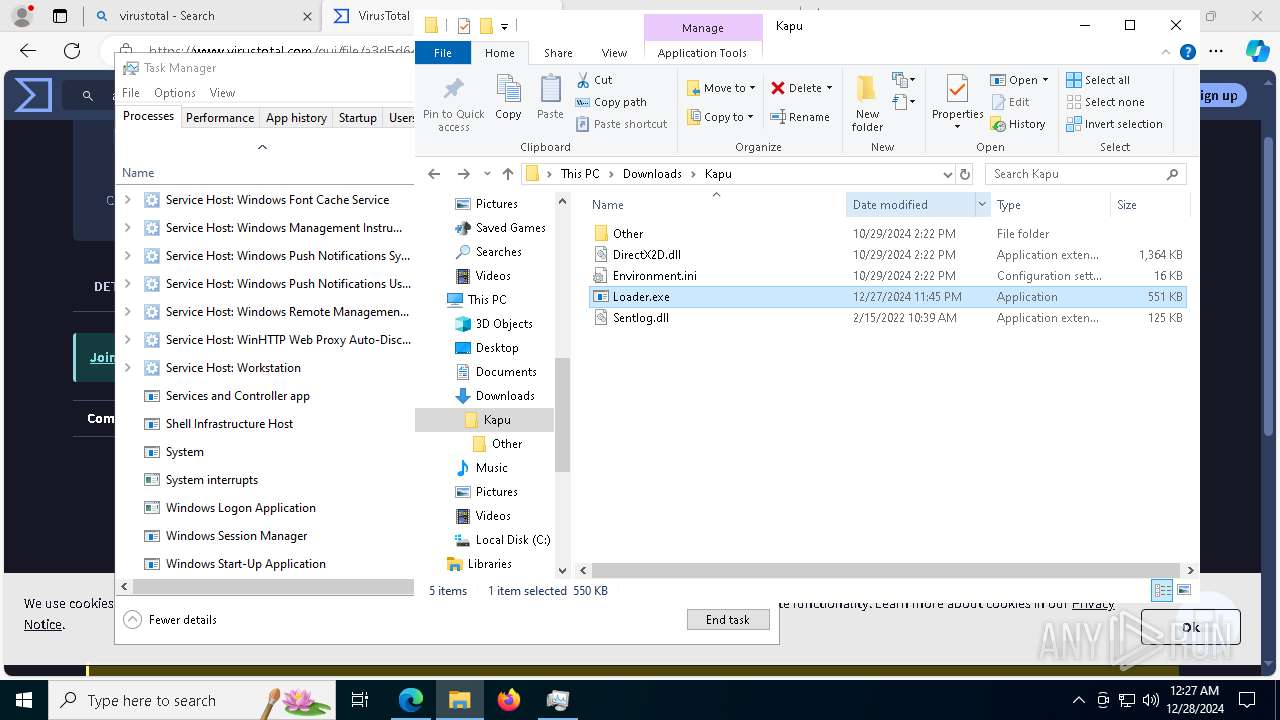
| URL: | mediafire.com/folder/f0tzfxsevhzq2/Kapu_Launcher |
| Full analysis: | https://app.any.run/tasks/016d8f37-382f-49d0-bcbd-98dc3f1cf870 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
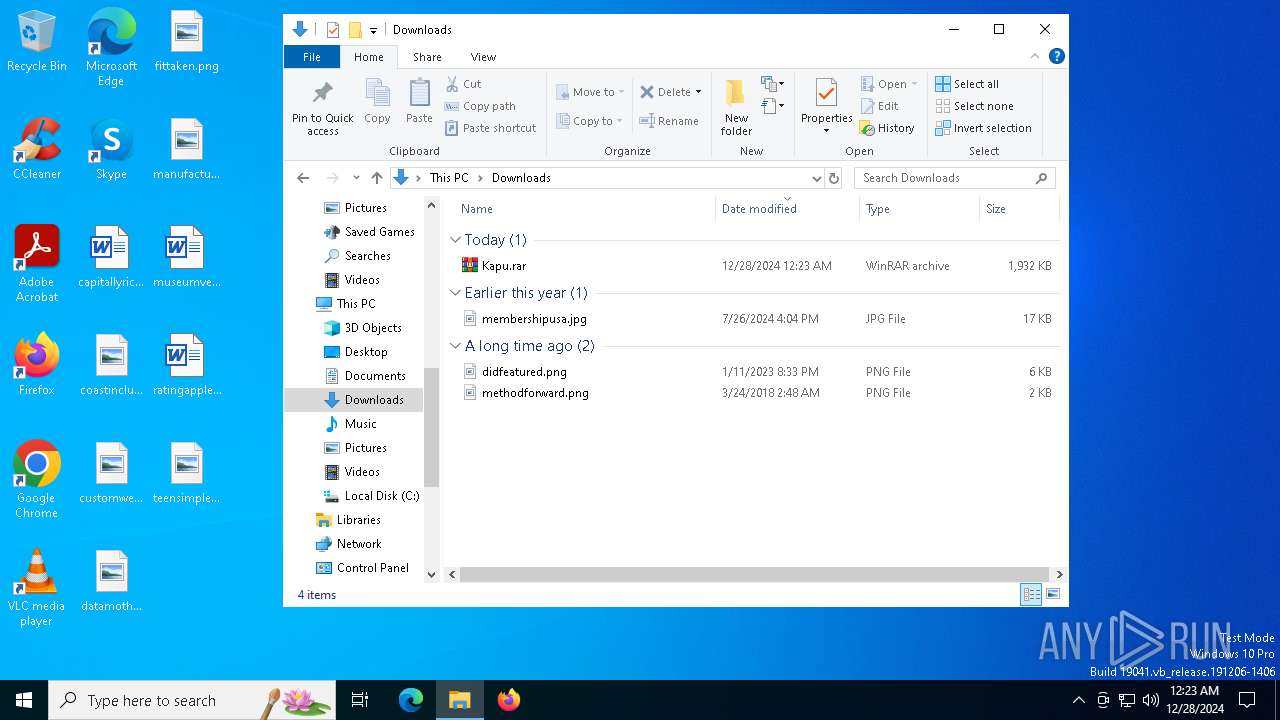
| Analysis date: | December 28, 2024, 00:23:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
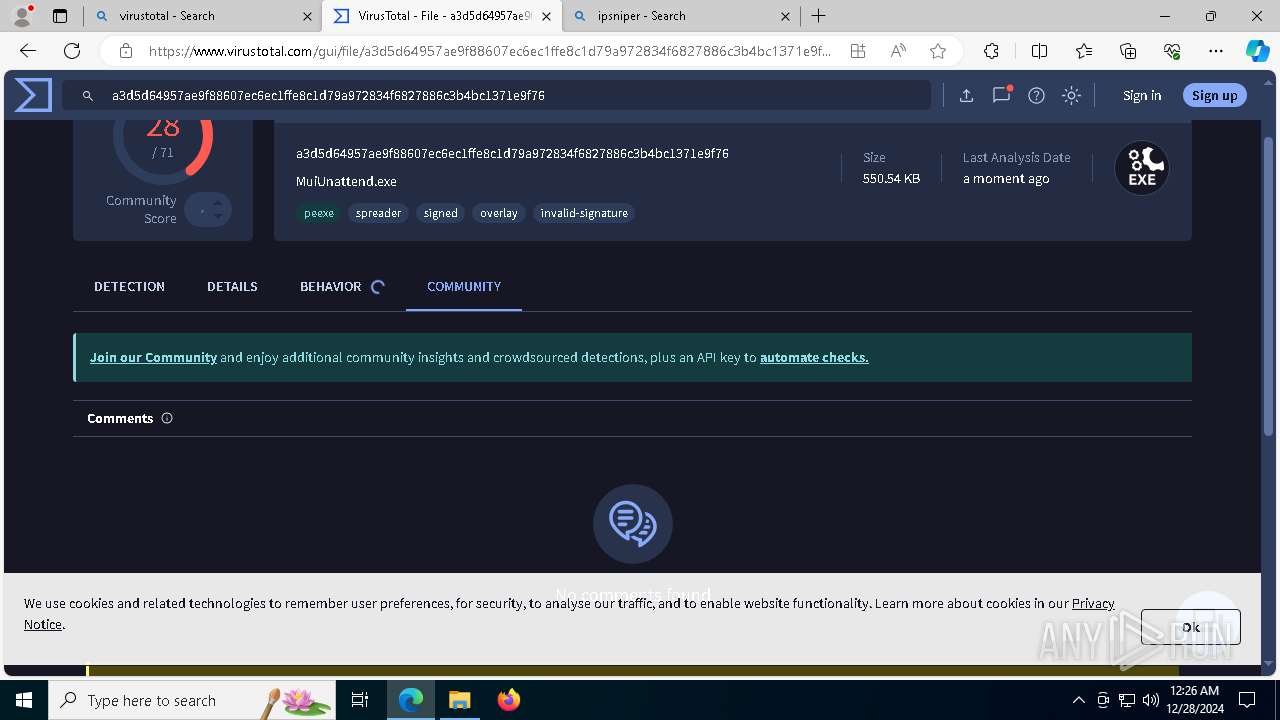
| MD5: | F6DBE27FF5EB8DCDC613F4166A9415ED |
| SHA1: | A275C1A52890154690C5873D0C6DE5F0108DF854 |
| SHA256: | FD73AF641B08D7C0AFFC8A2DC006F40883941187A8D35D2D8740C3483540D77A |
| SSDEEP: | 3:9oeGUbKxWATNG1EVxsy:2eG+n2Ns8D |
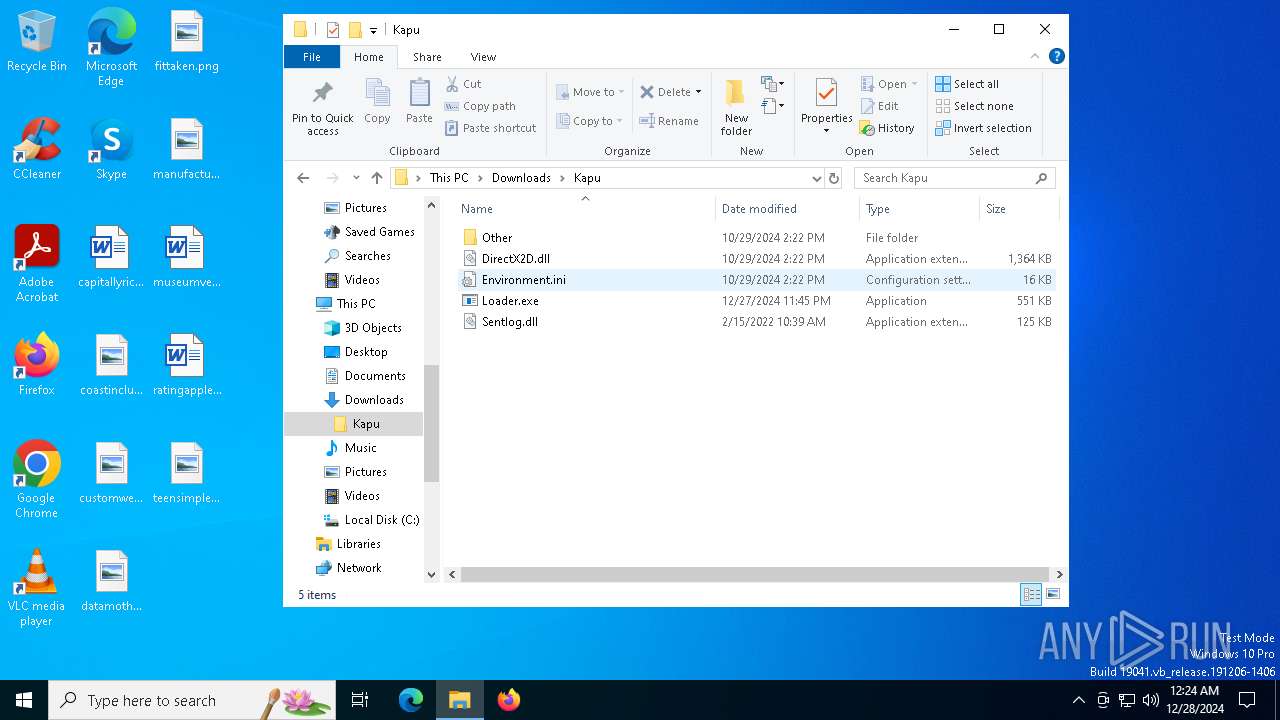
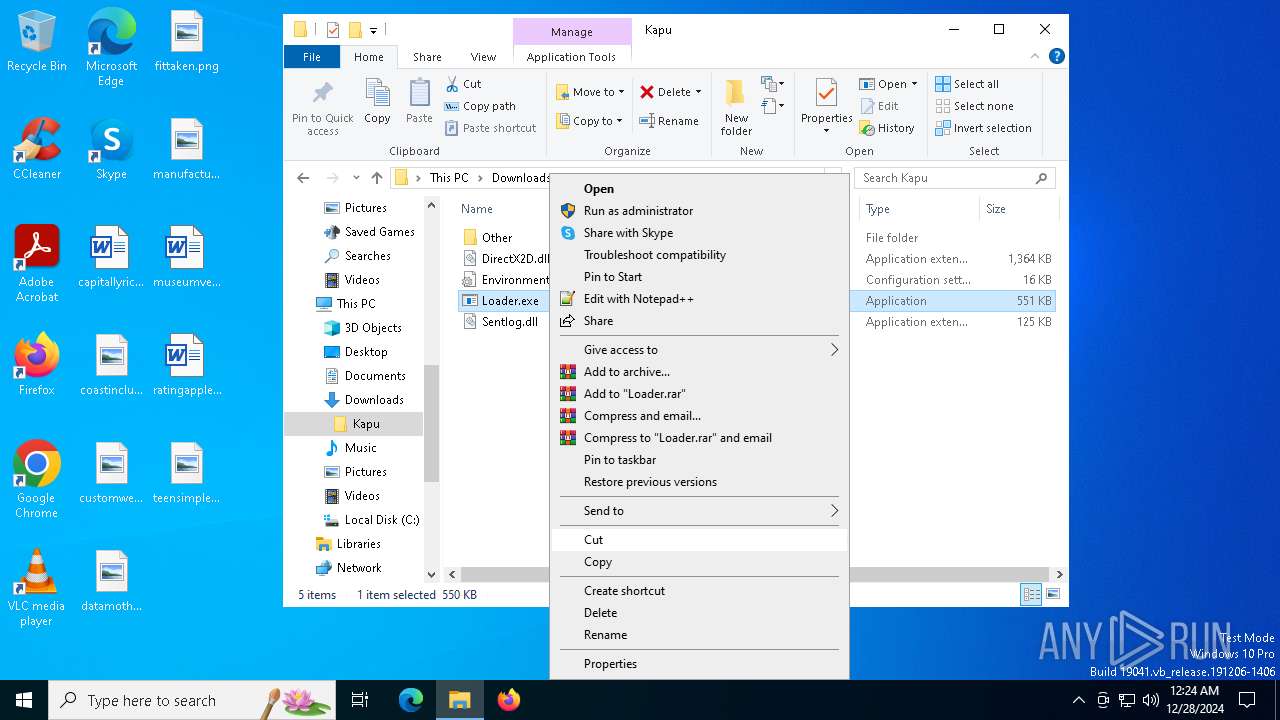
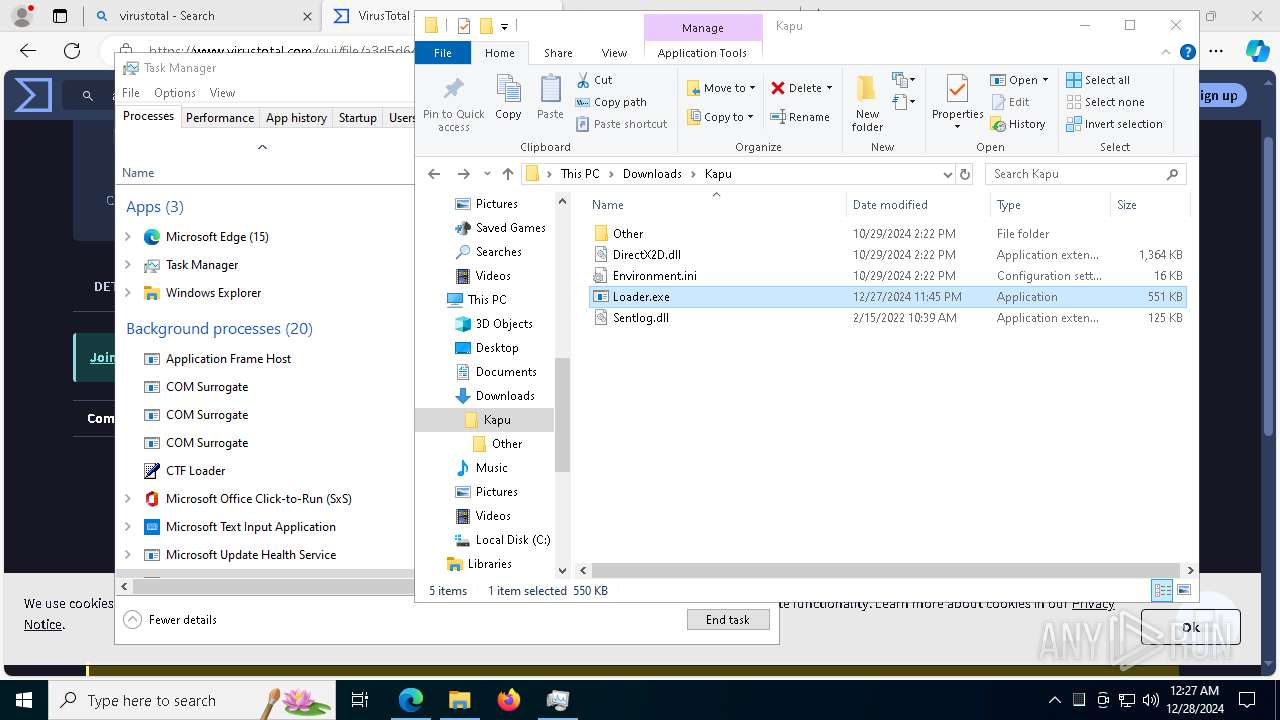
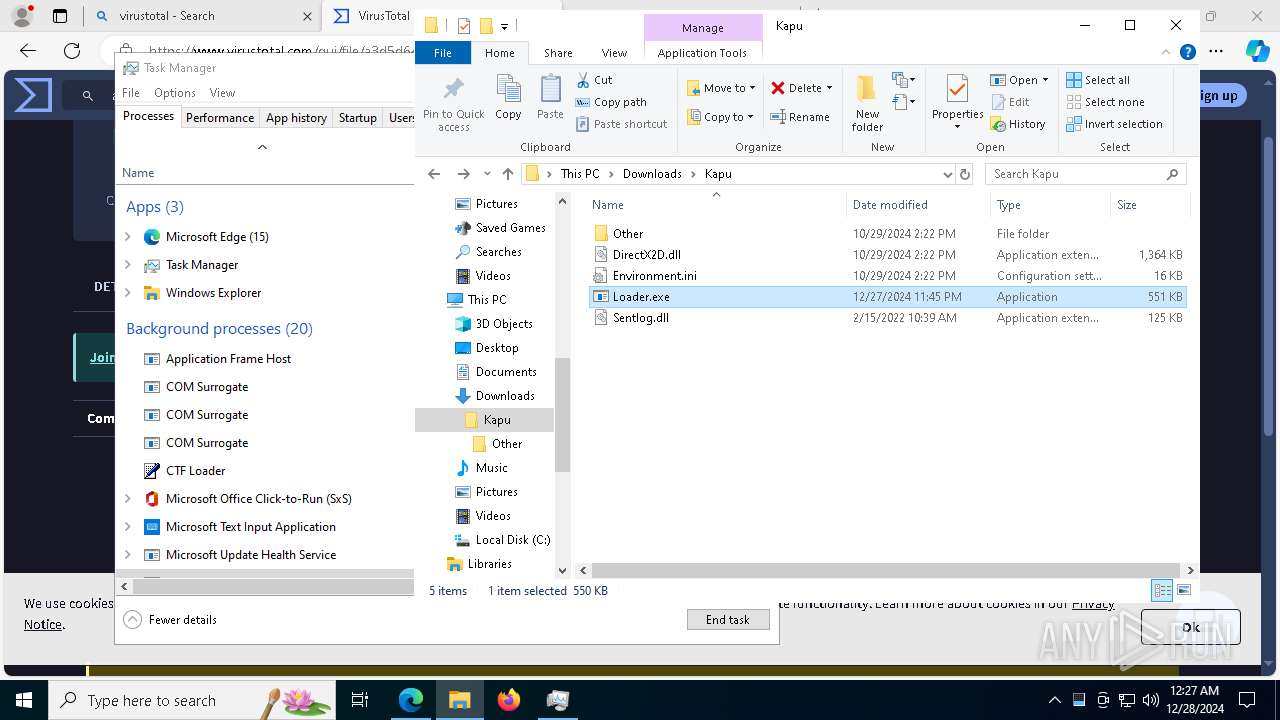
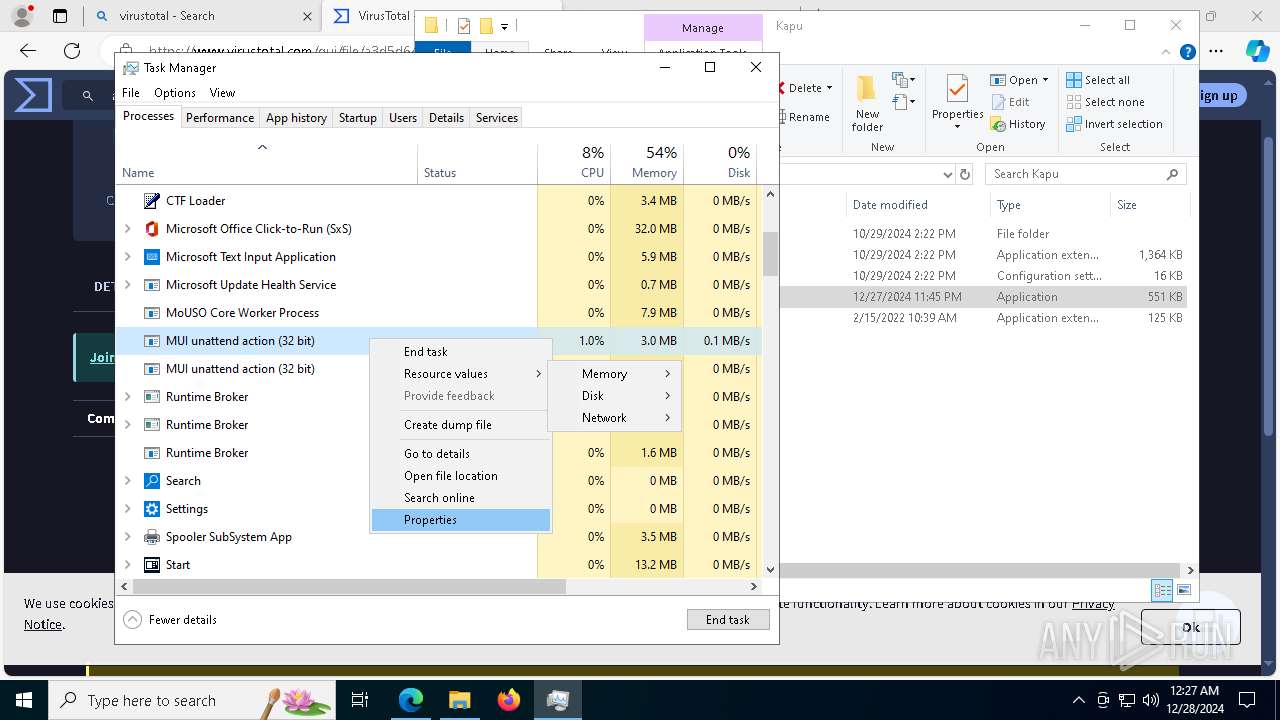
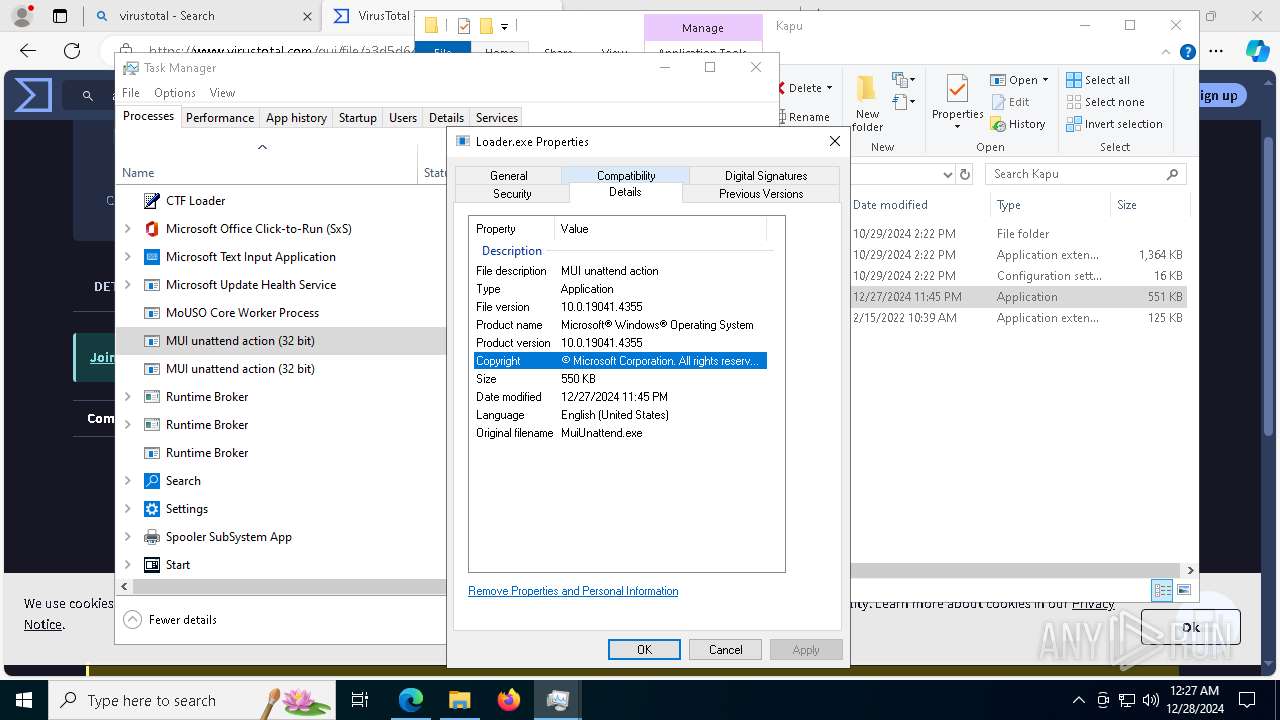
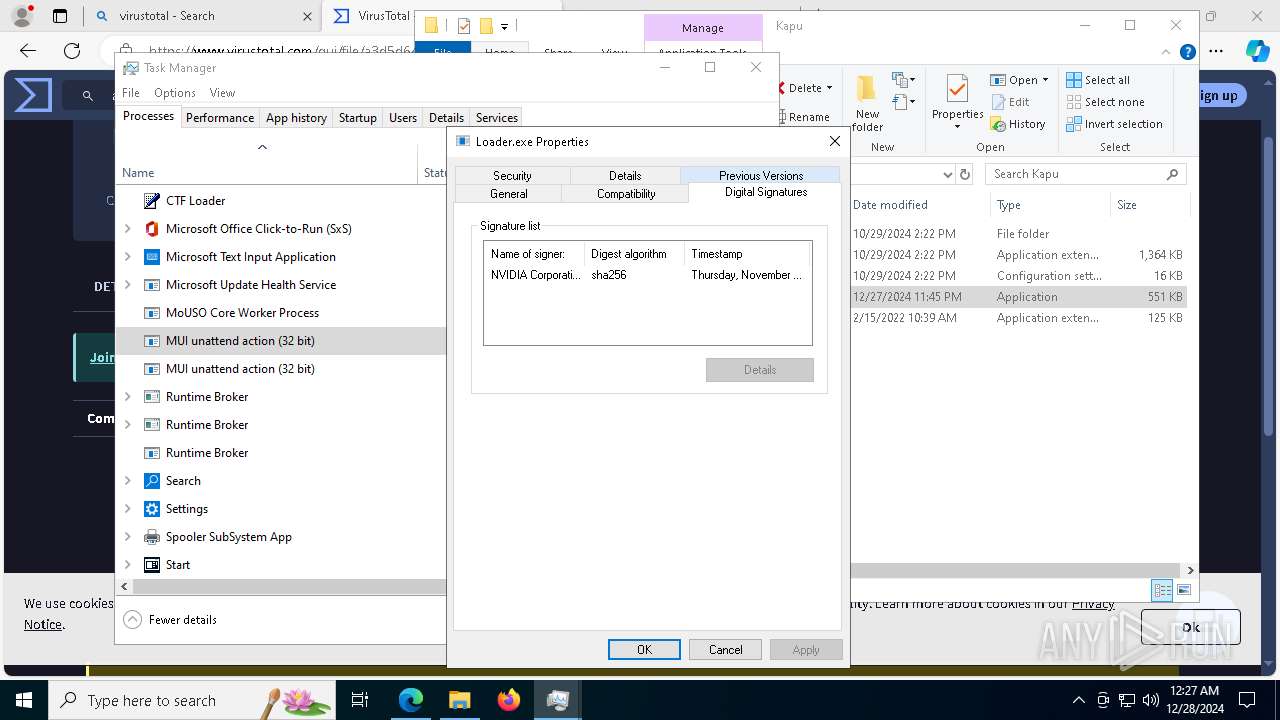
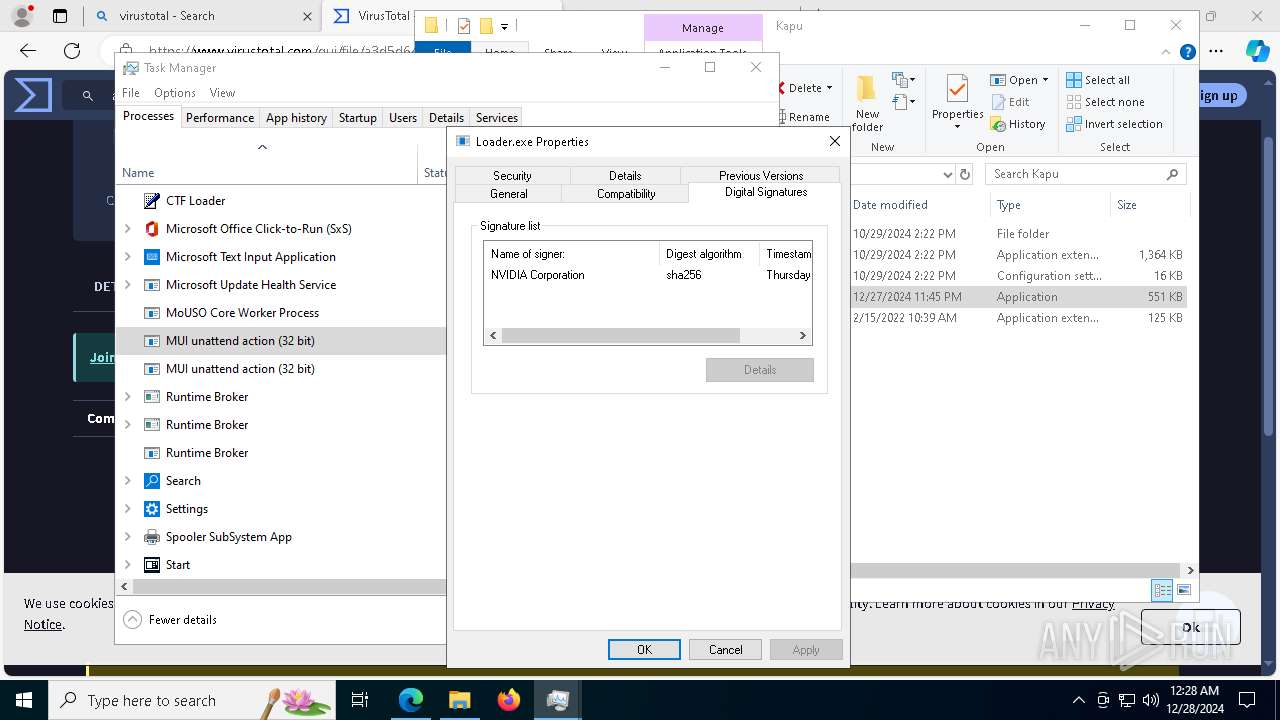
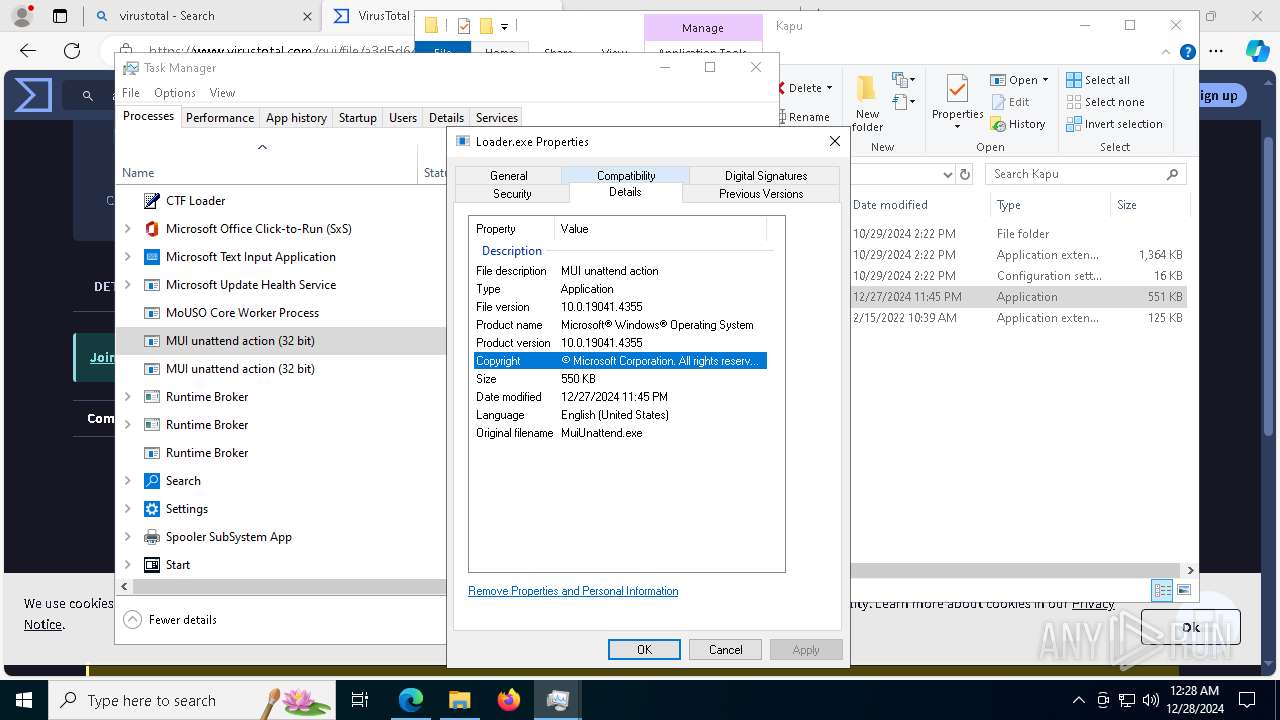
MALICIOUS
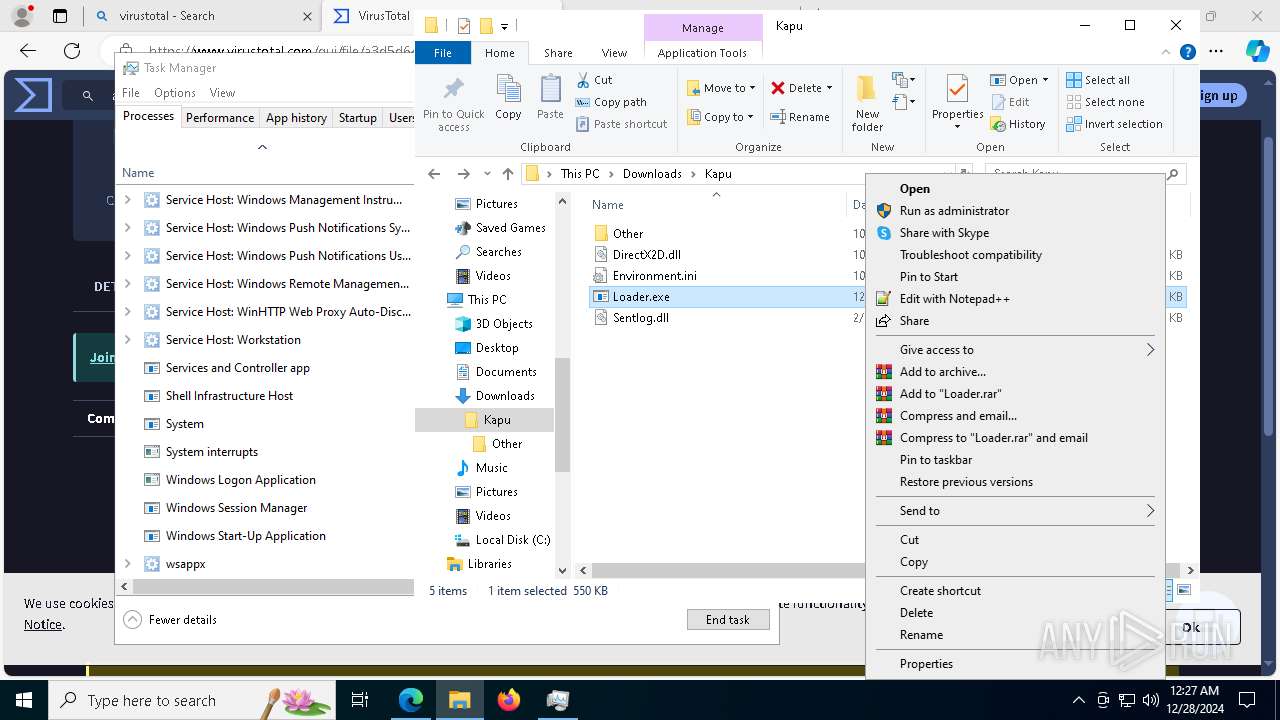
Executing a file with an untrusted certificate
- Loader.exe (PID: 5212)
- Loader.exe (PID: 6228)
- Loader.exe (PID: 7964)
- Loader.exe (PID: 6564)
- Loader.exe (PID: 7080)
- Loader.exe (PID: 7960)
- Loader.exe (PID: 7496)
- Loader.exe (PID: 1612)
LUMMA mutex has been found
- Loader.exe (PID: 7080)
- Loader.exe (PID: 7960)
Steals credentials from Web Browsers
- Loader.exe (PID: 7080)
- Loader.exe (PID: 7960)
Actions looks like stealing of personal data
- Loader.exe (PID: 7080)
- Loader.exe (PID: 7960)
LUMMA has been detected (YARA)
- Loader.exe (PID: 7960)
SUSPICIOUS
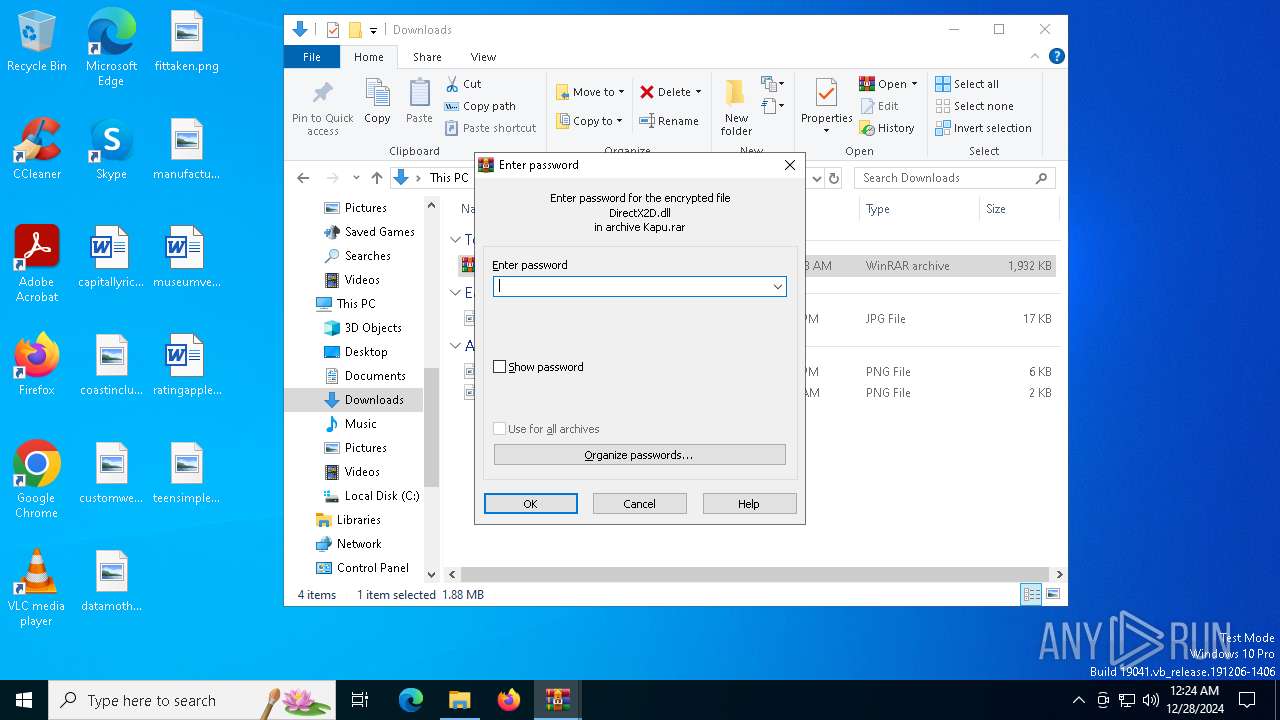
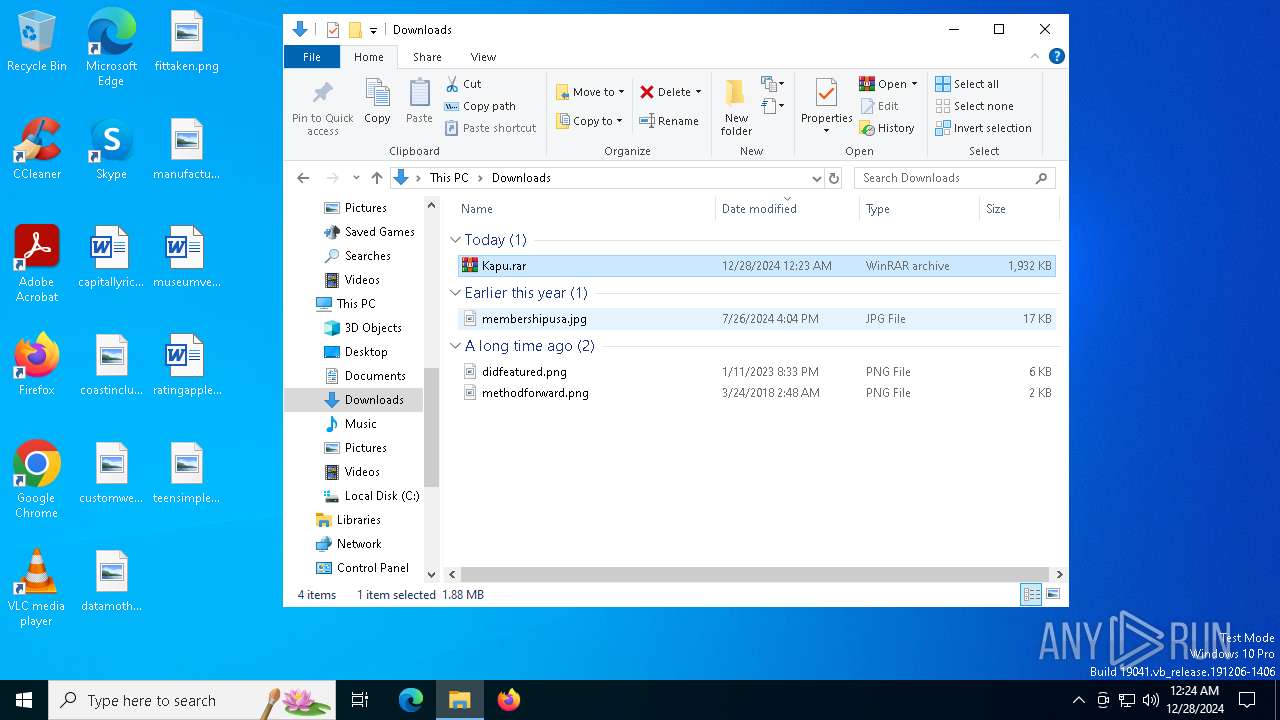
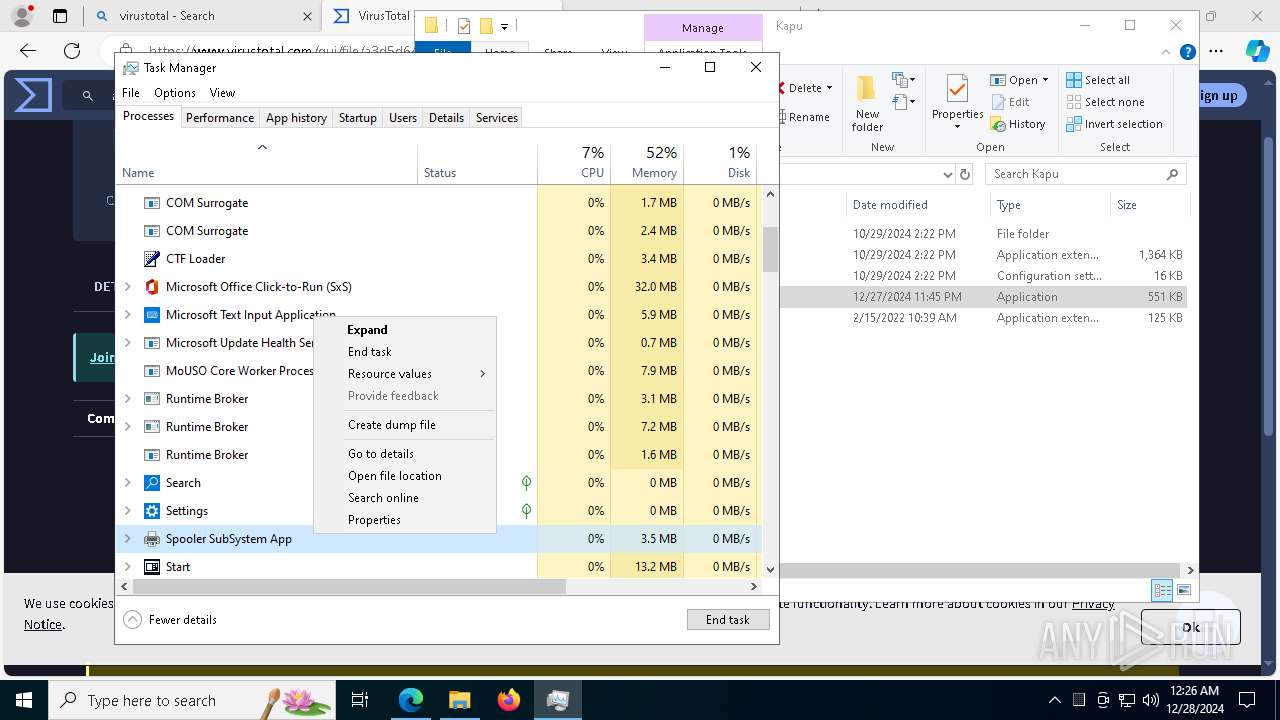
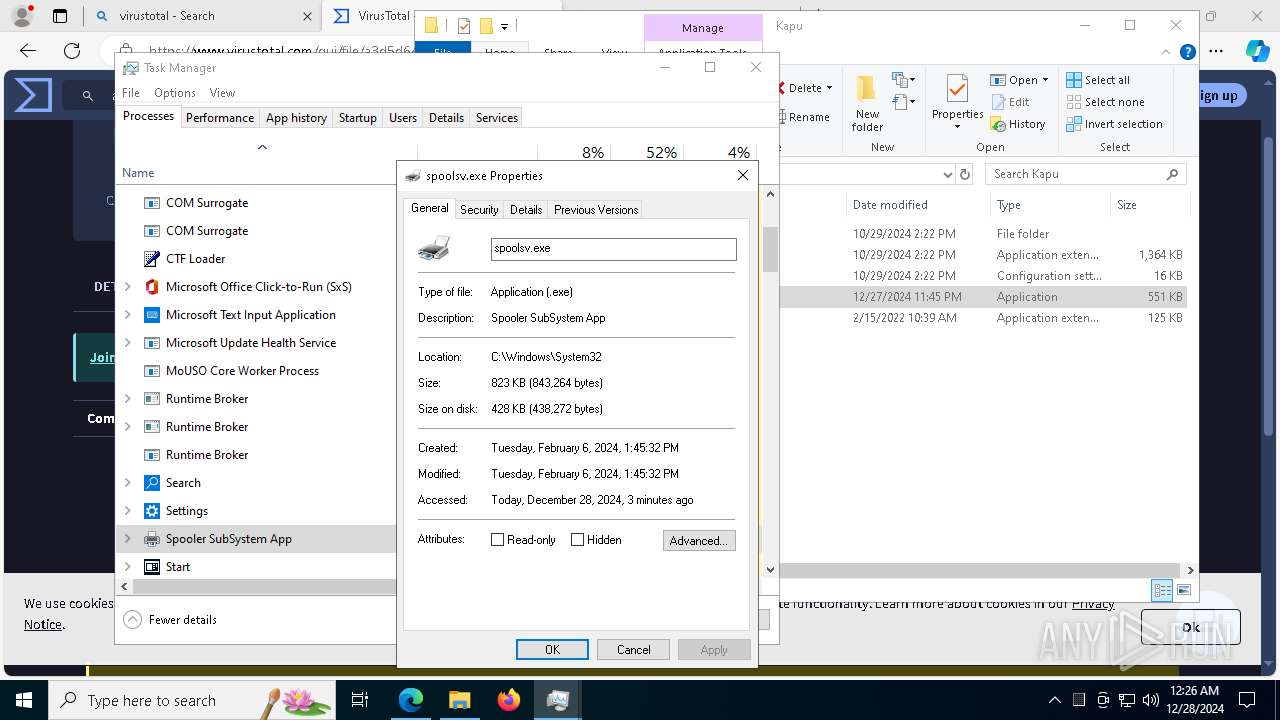
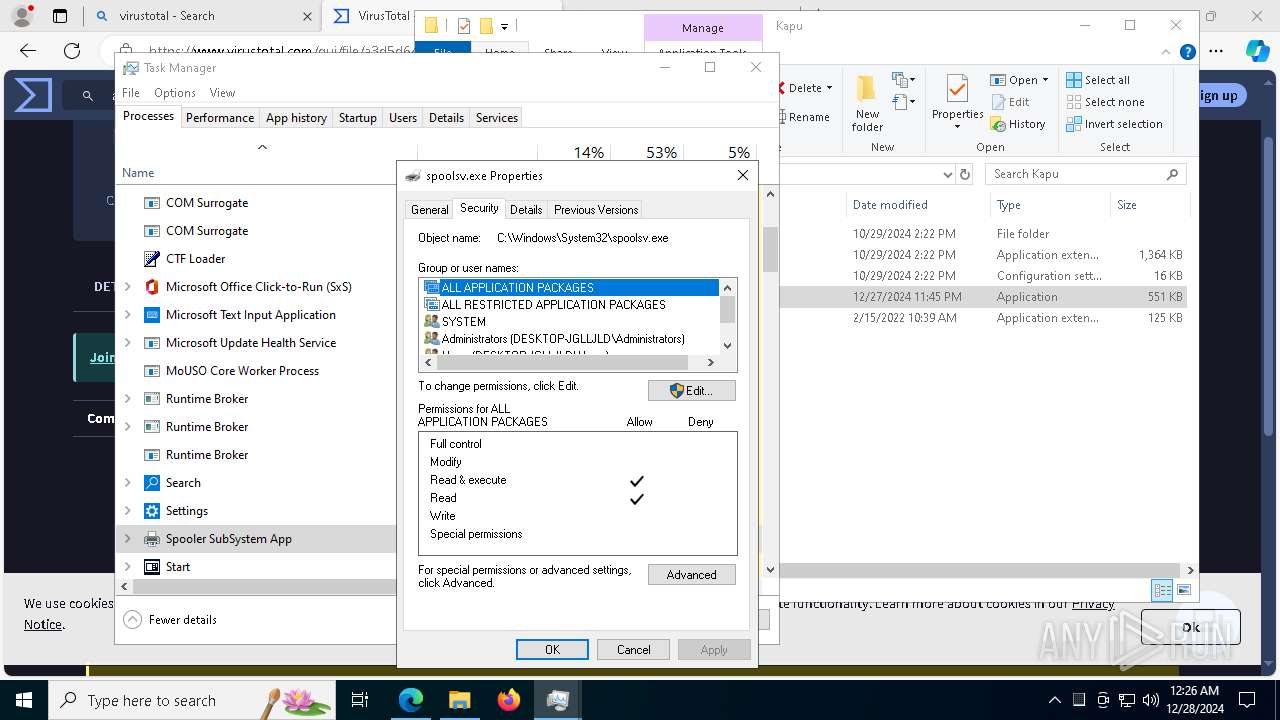
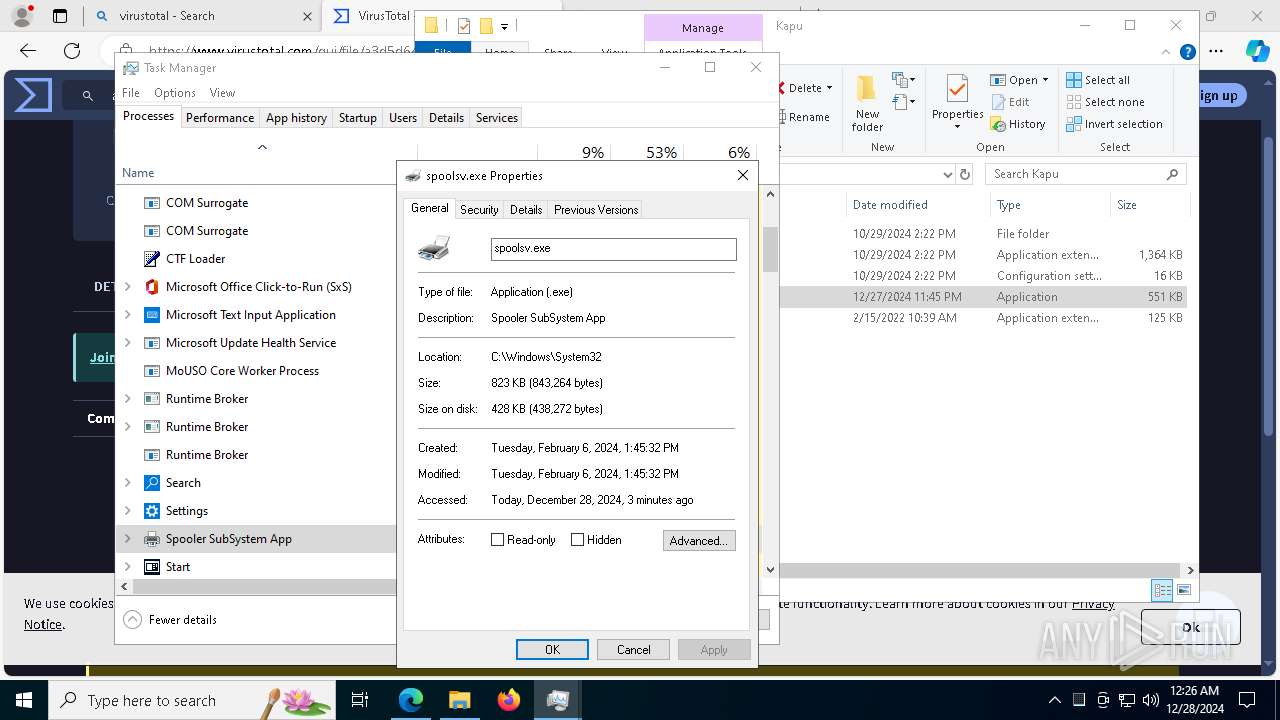
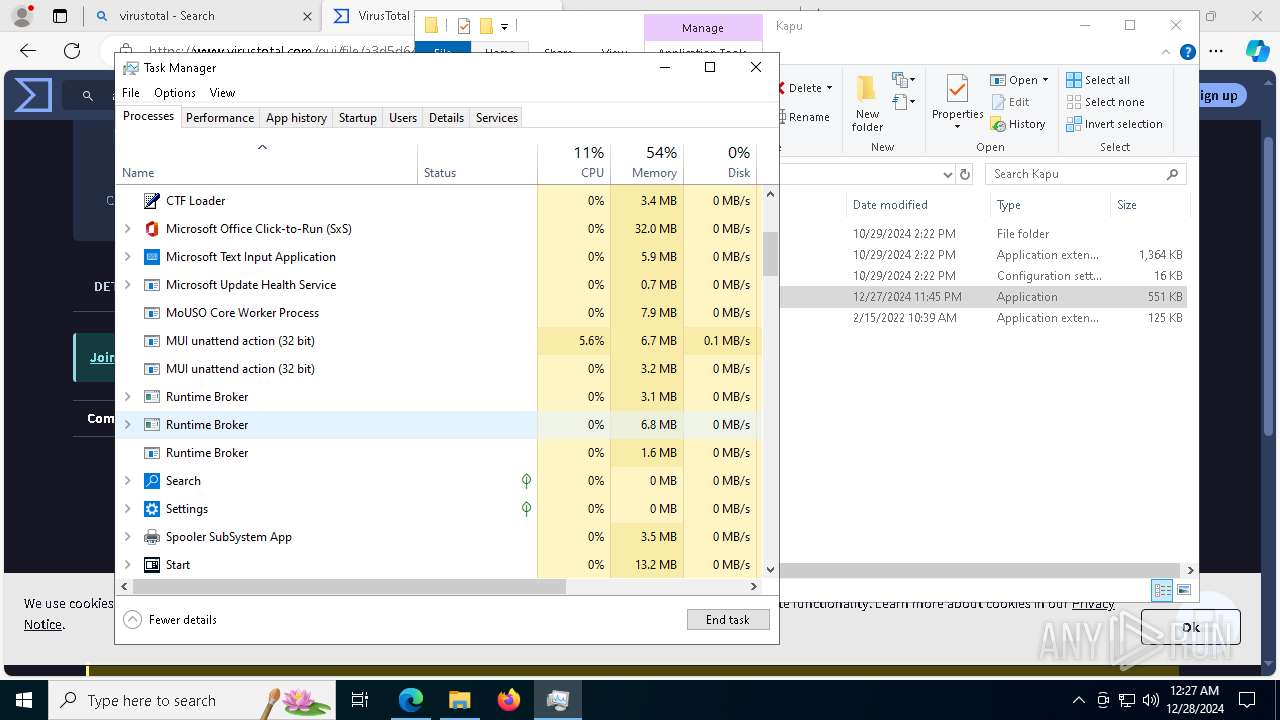
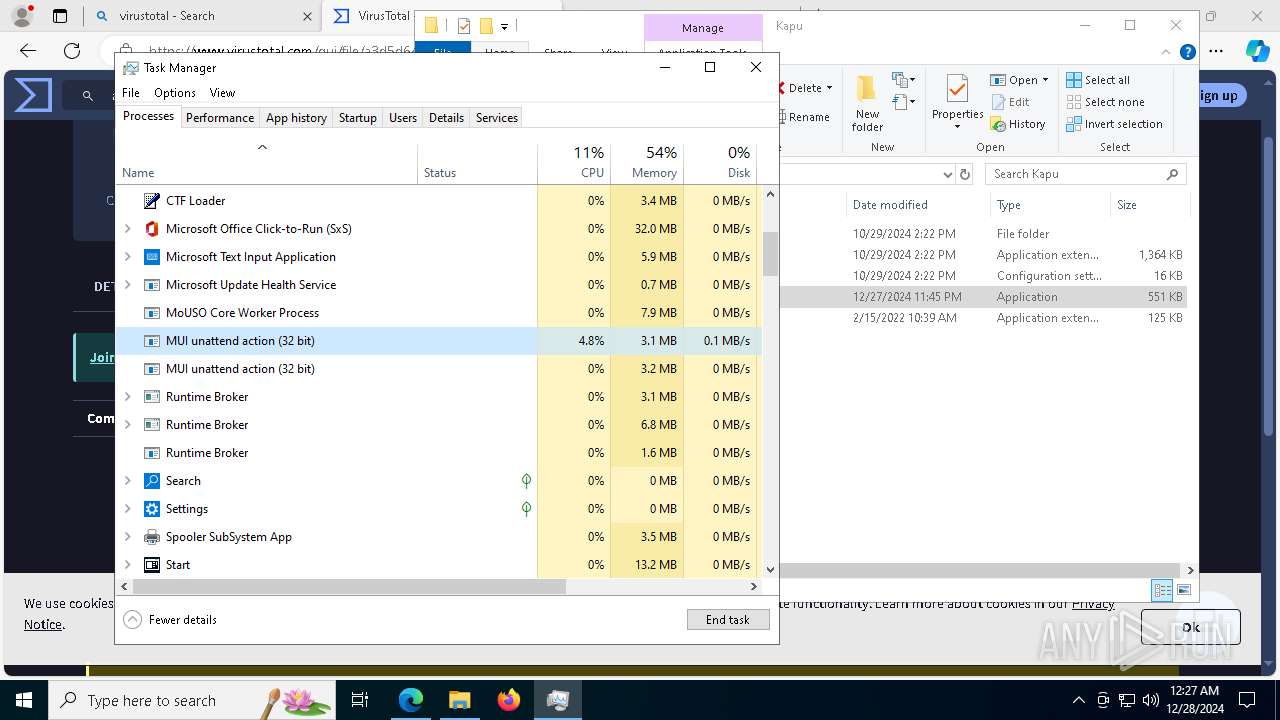
Process drops legitimate windows executable
- WinRAR.exe (PID: 6856)
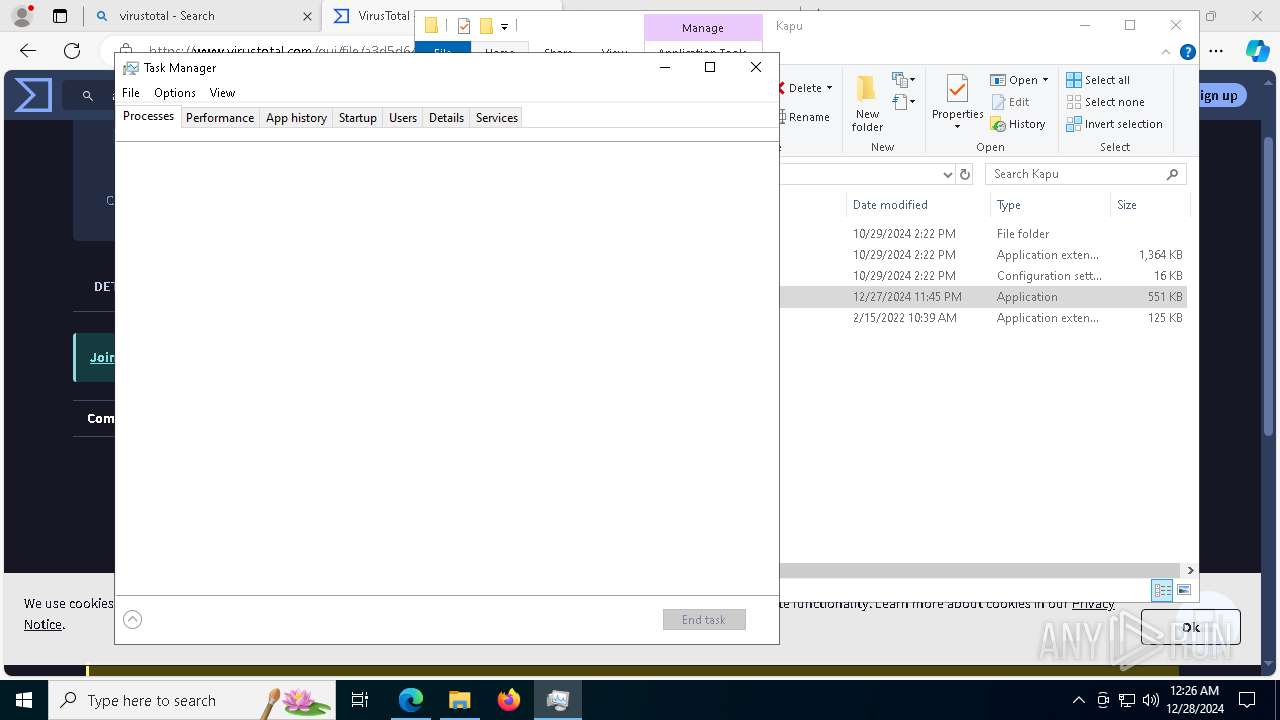
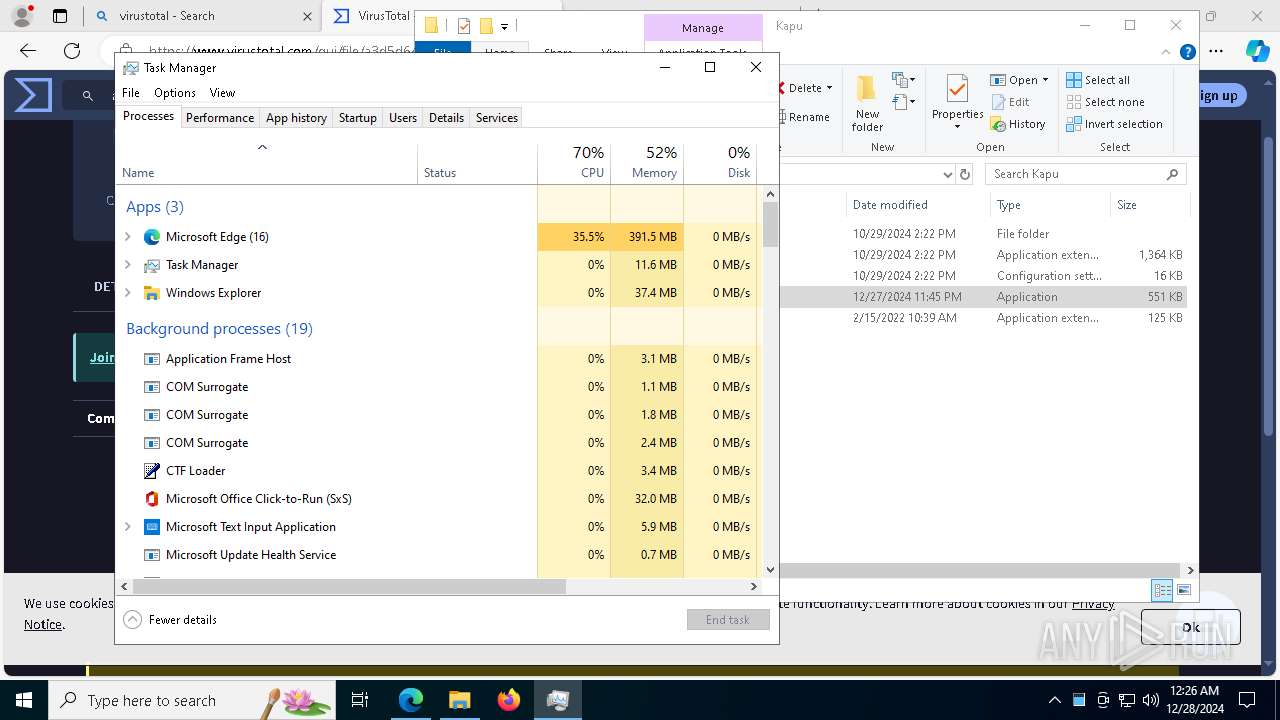
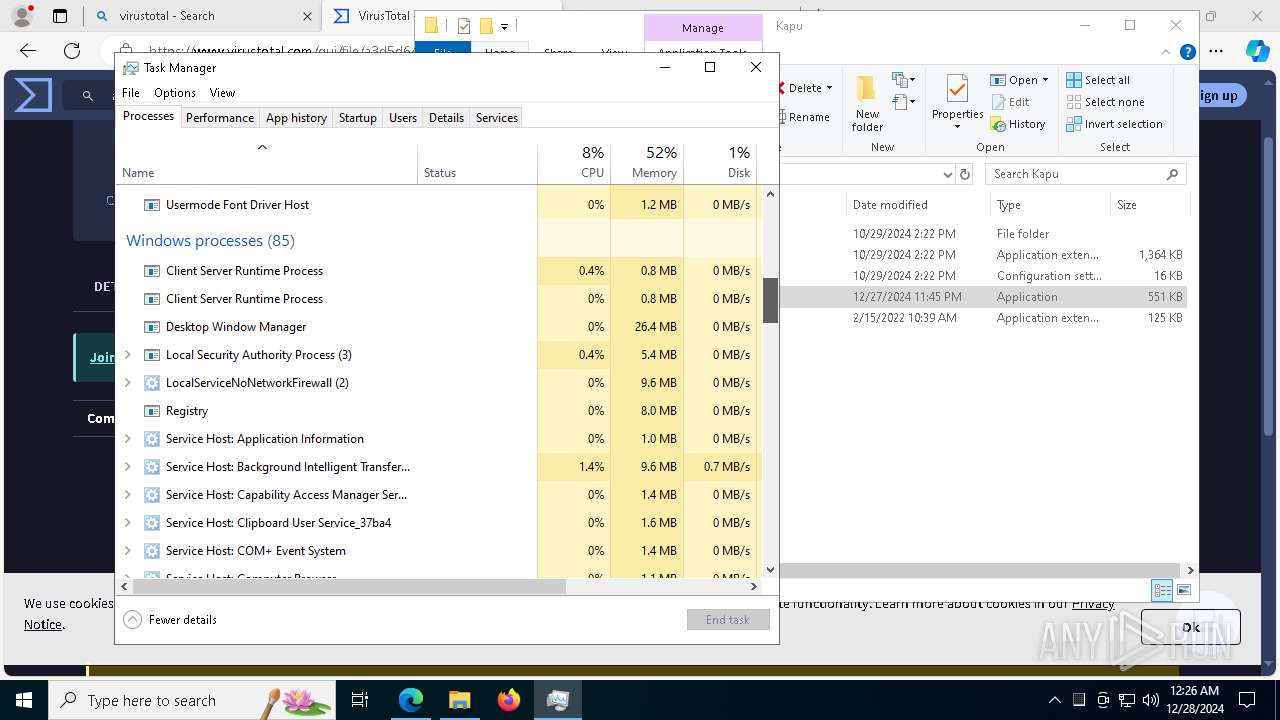
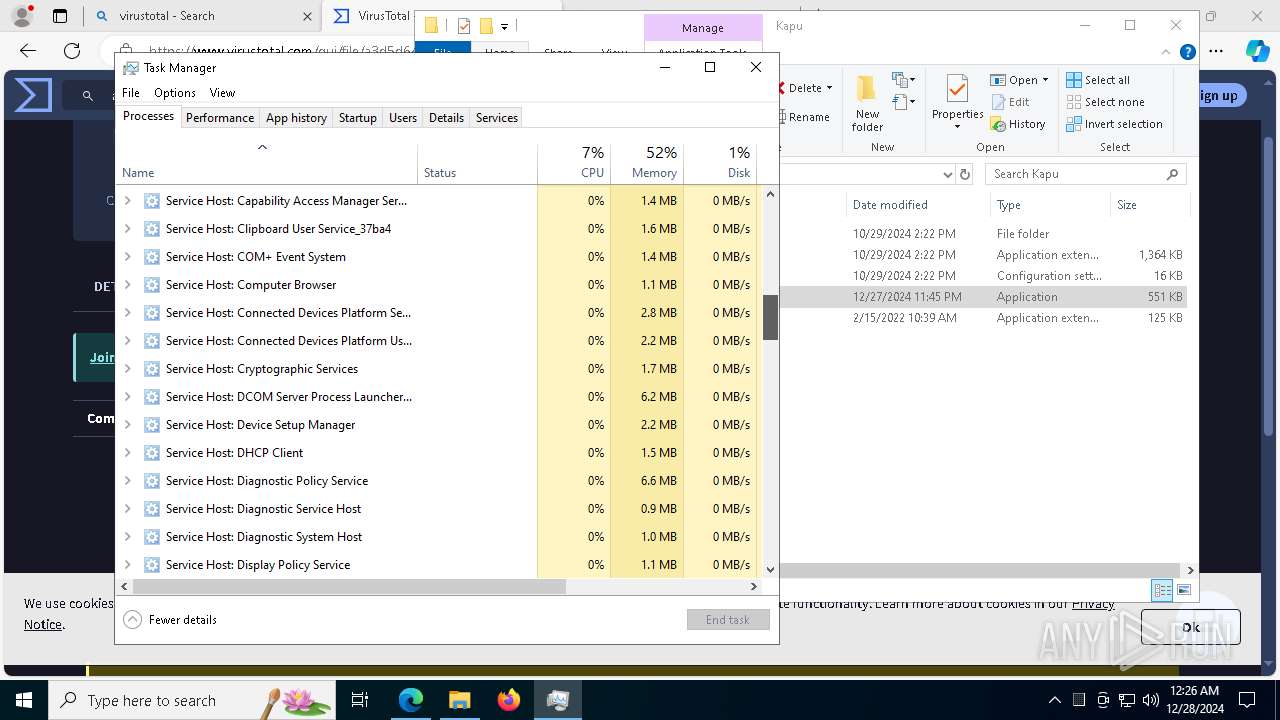
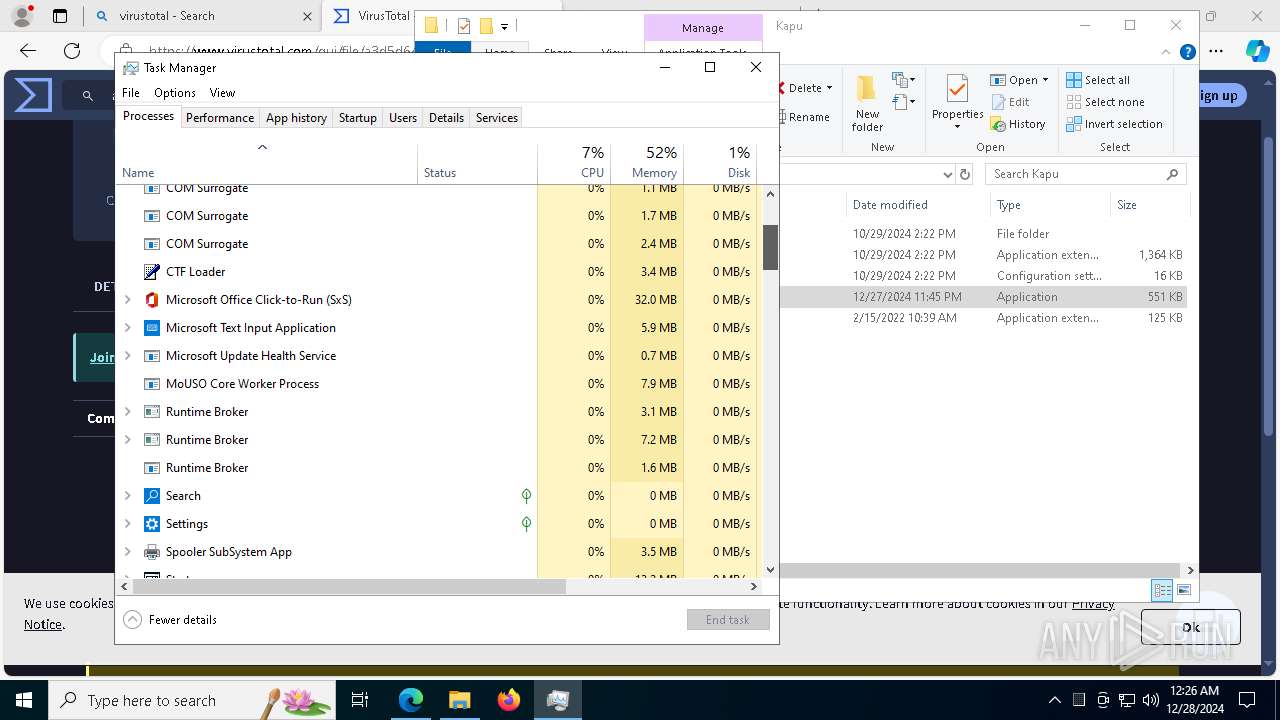
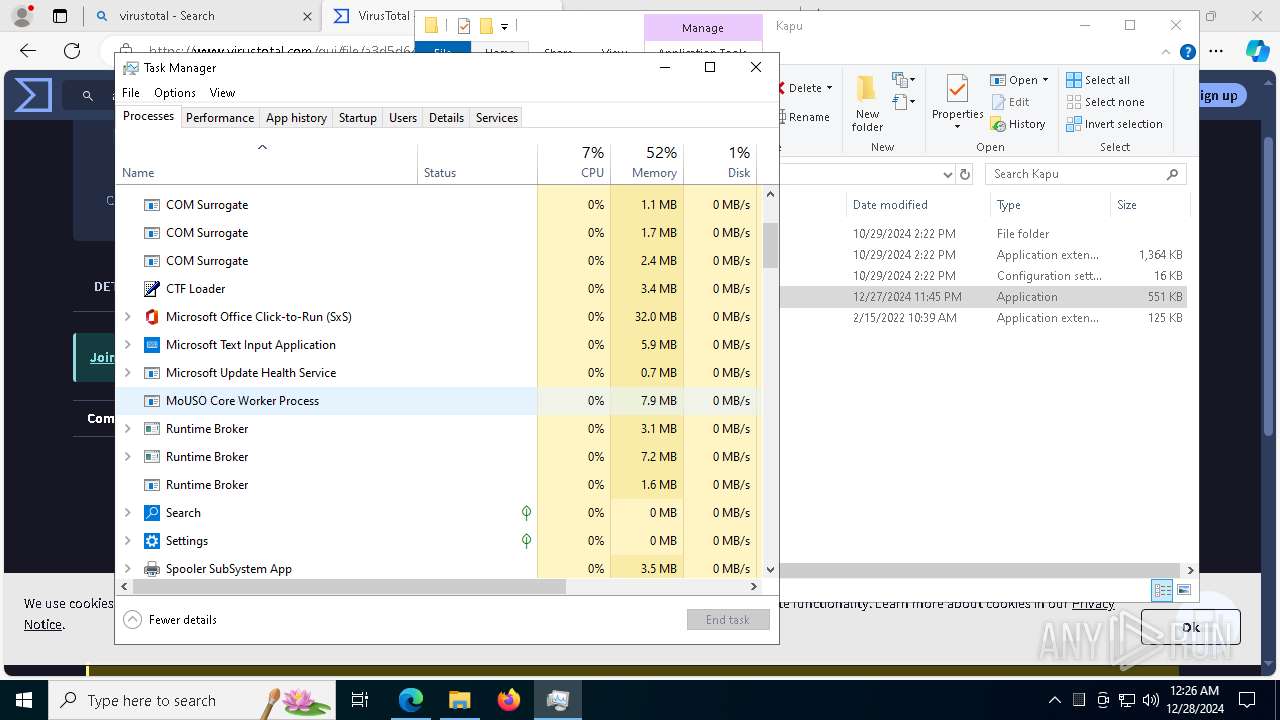
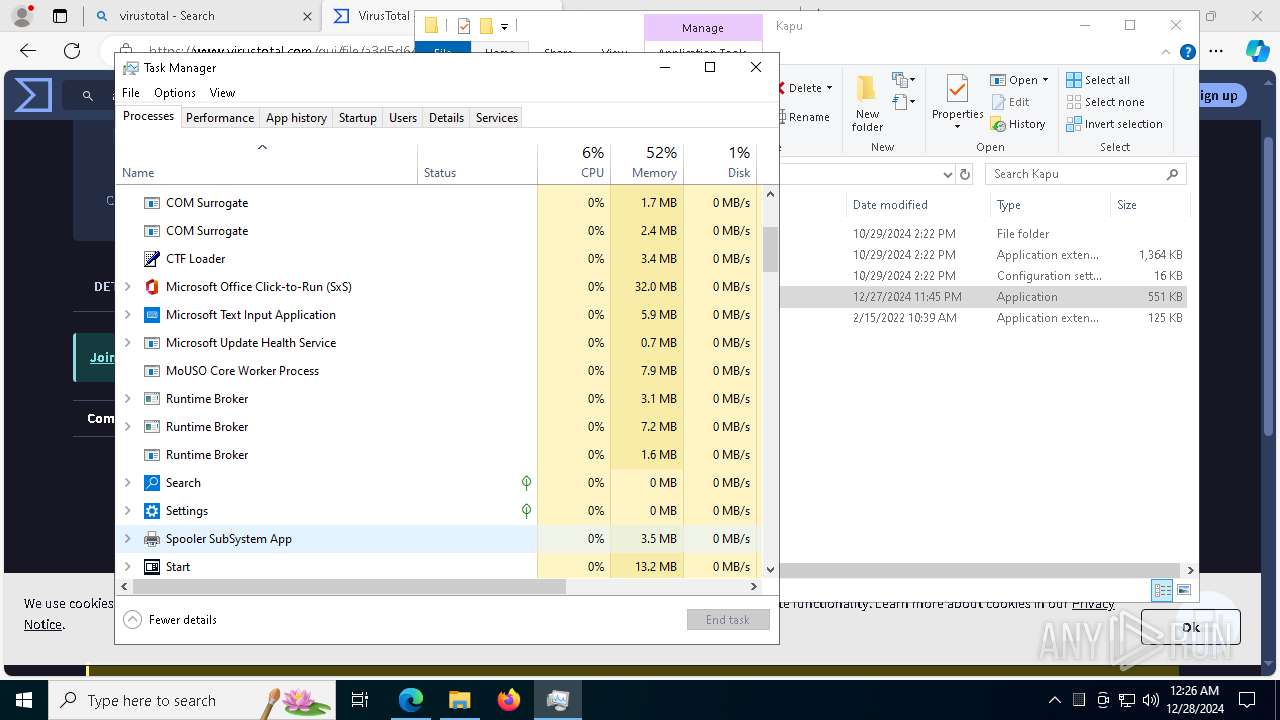
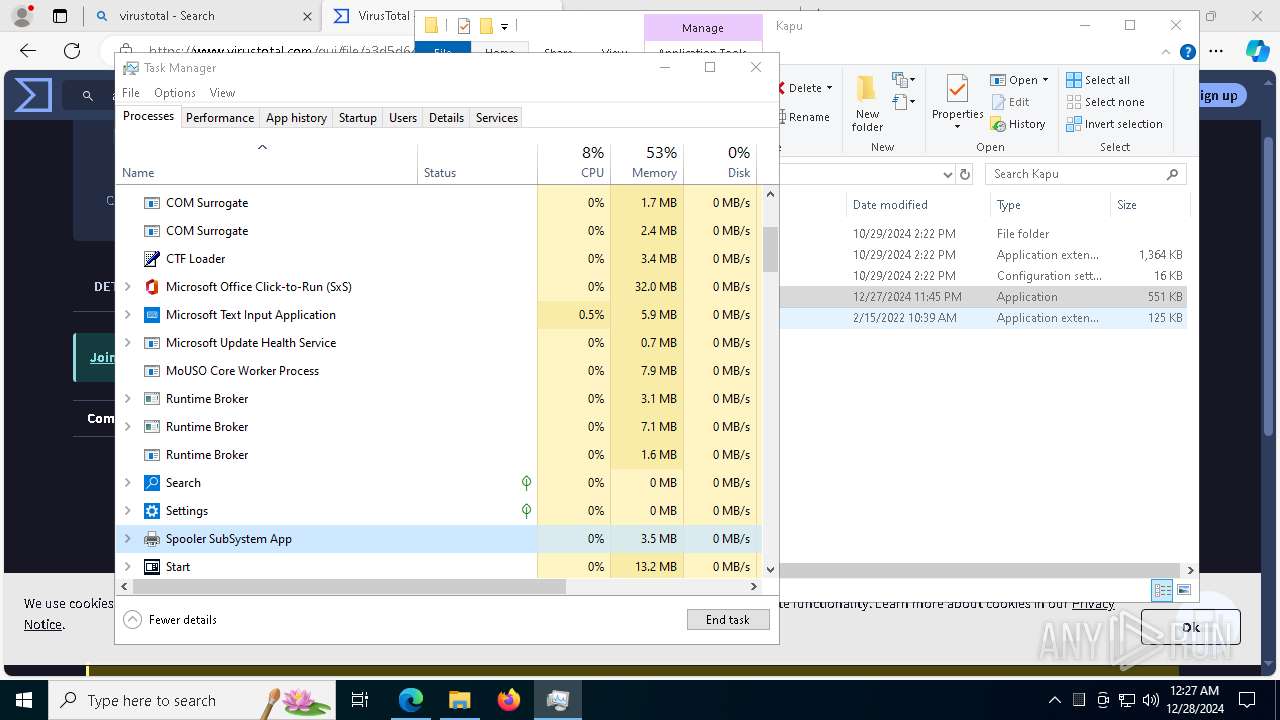
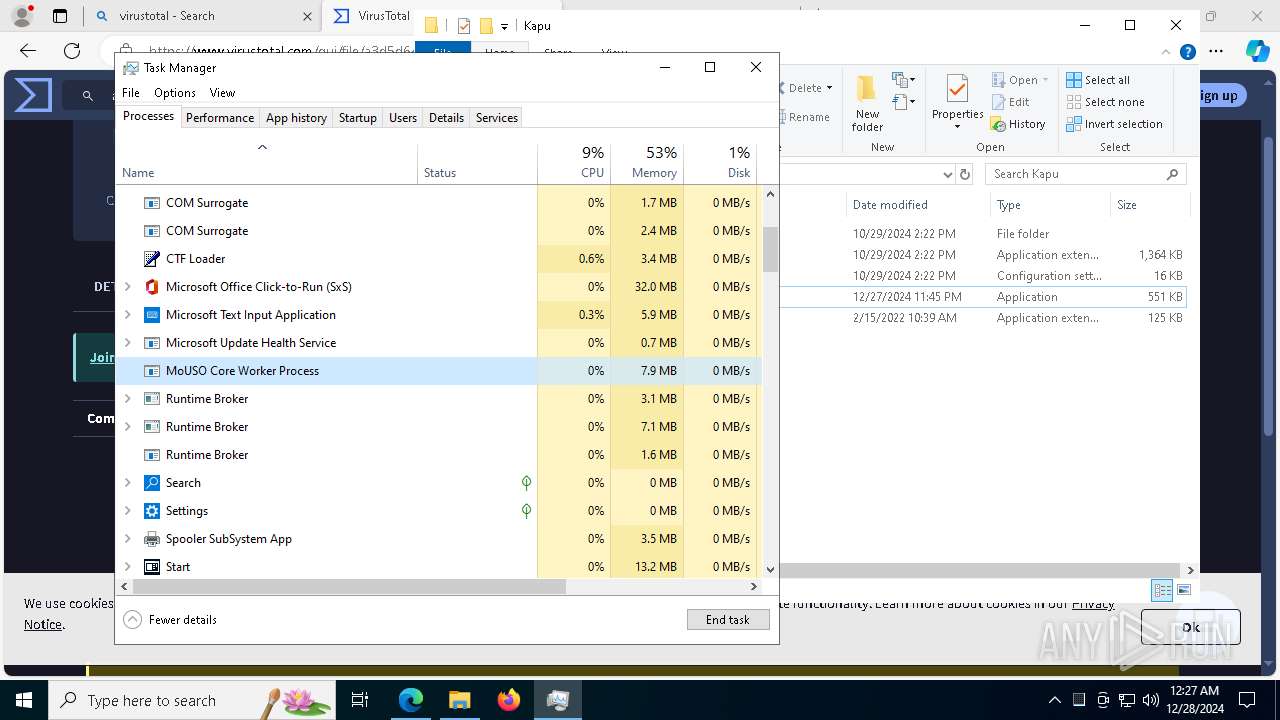
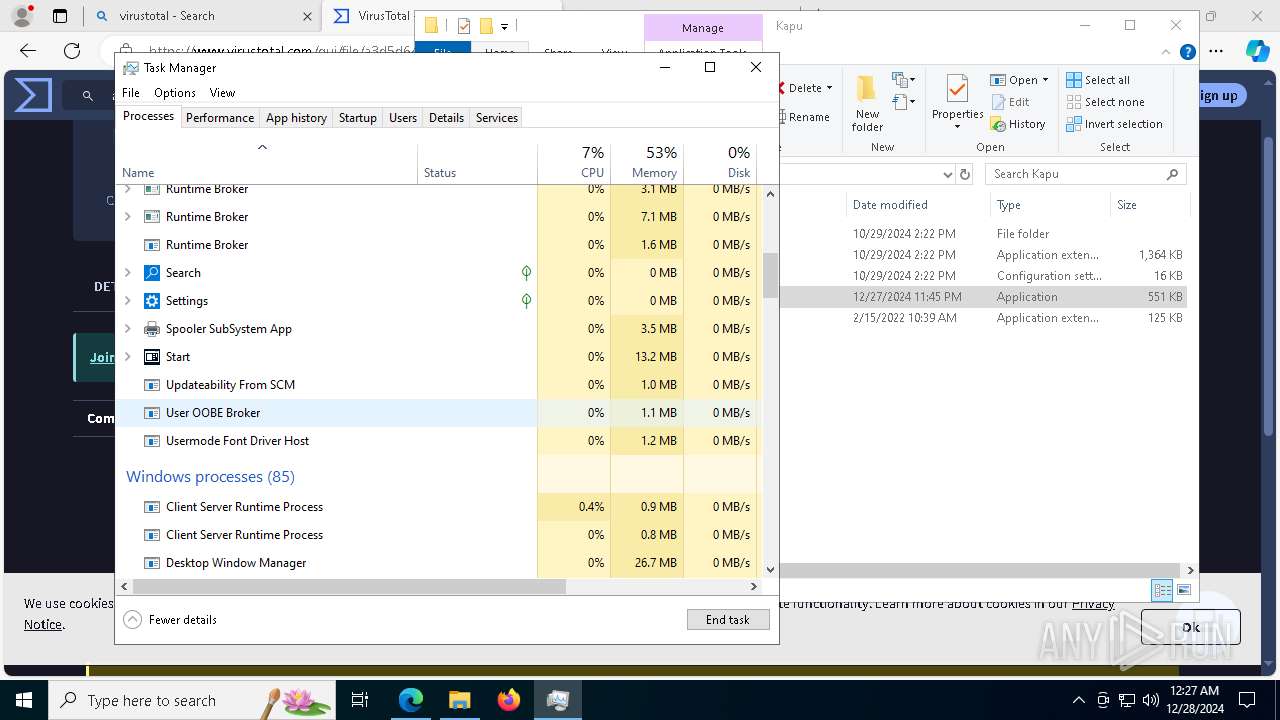
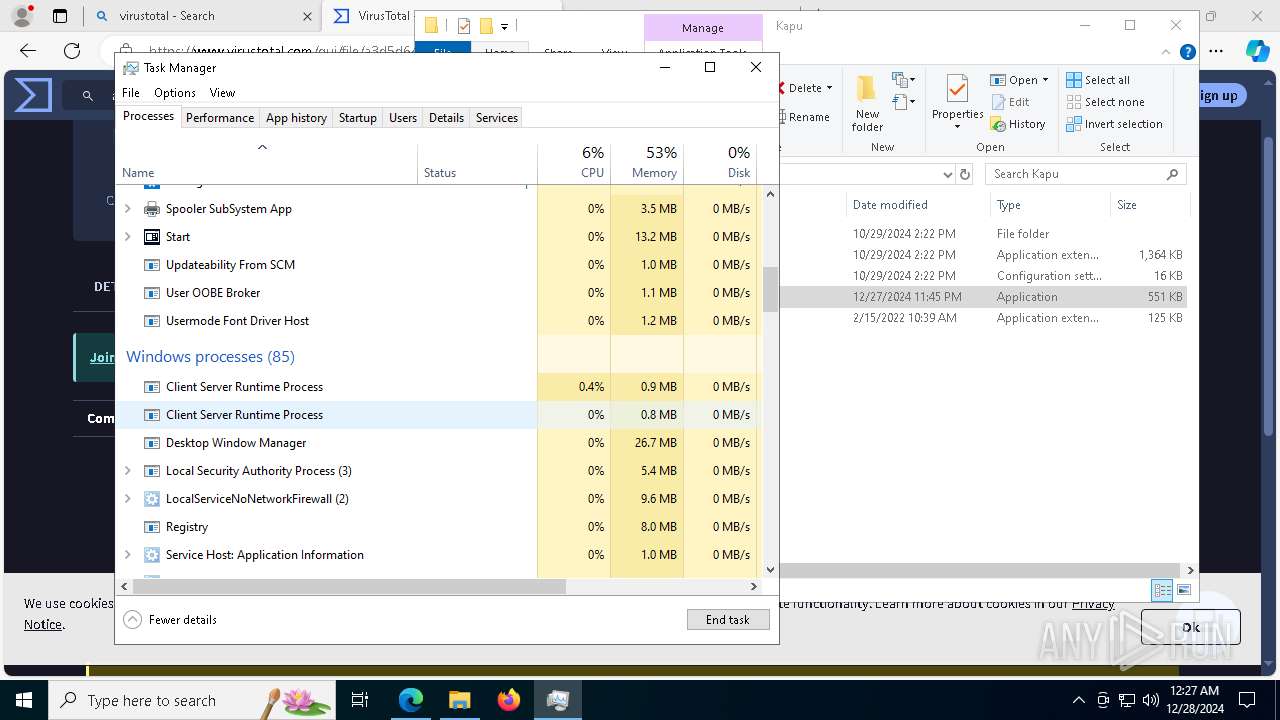
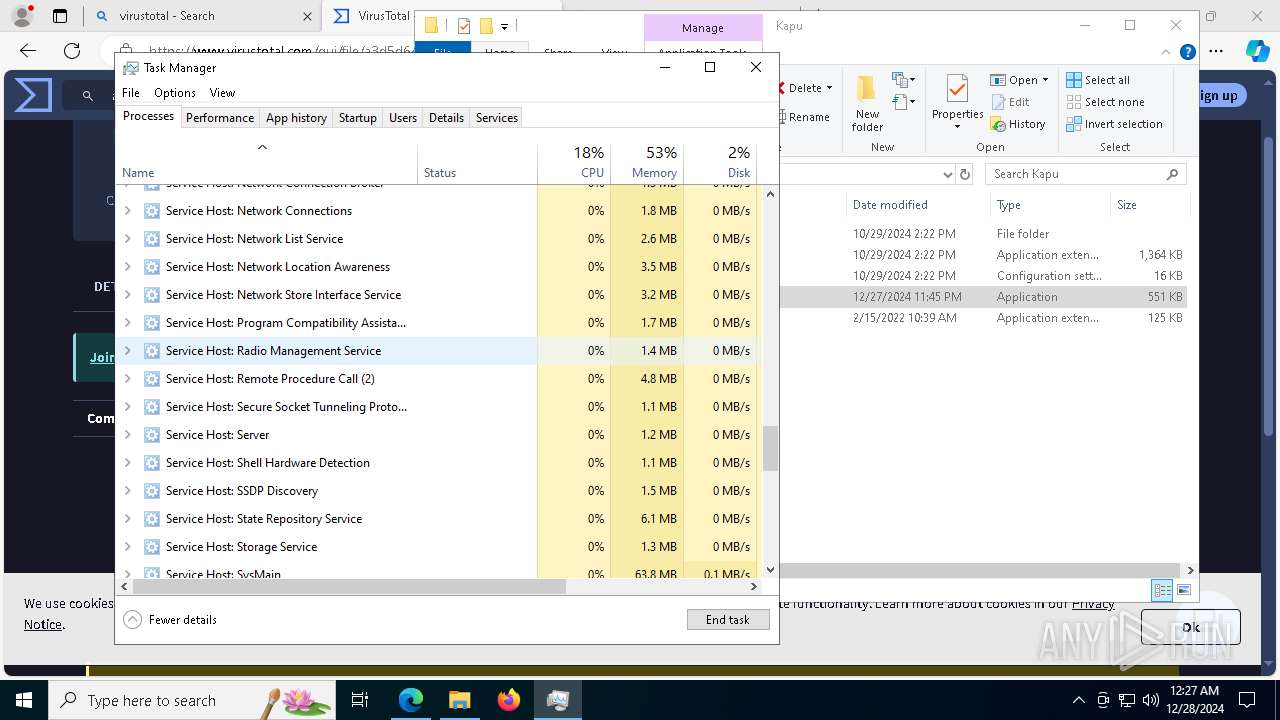
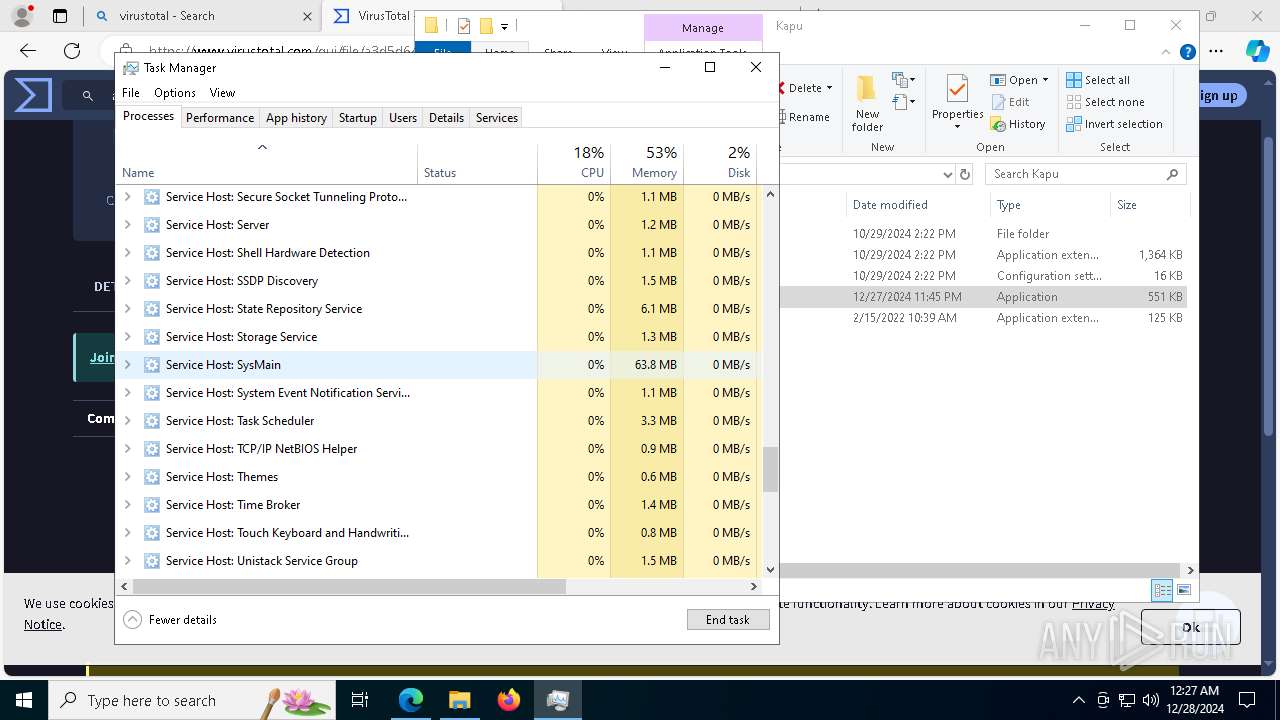
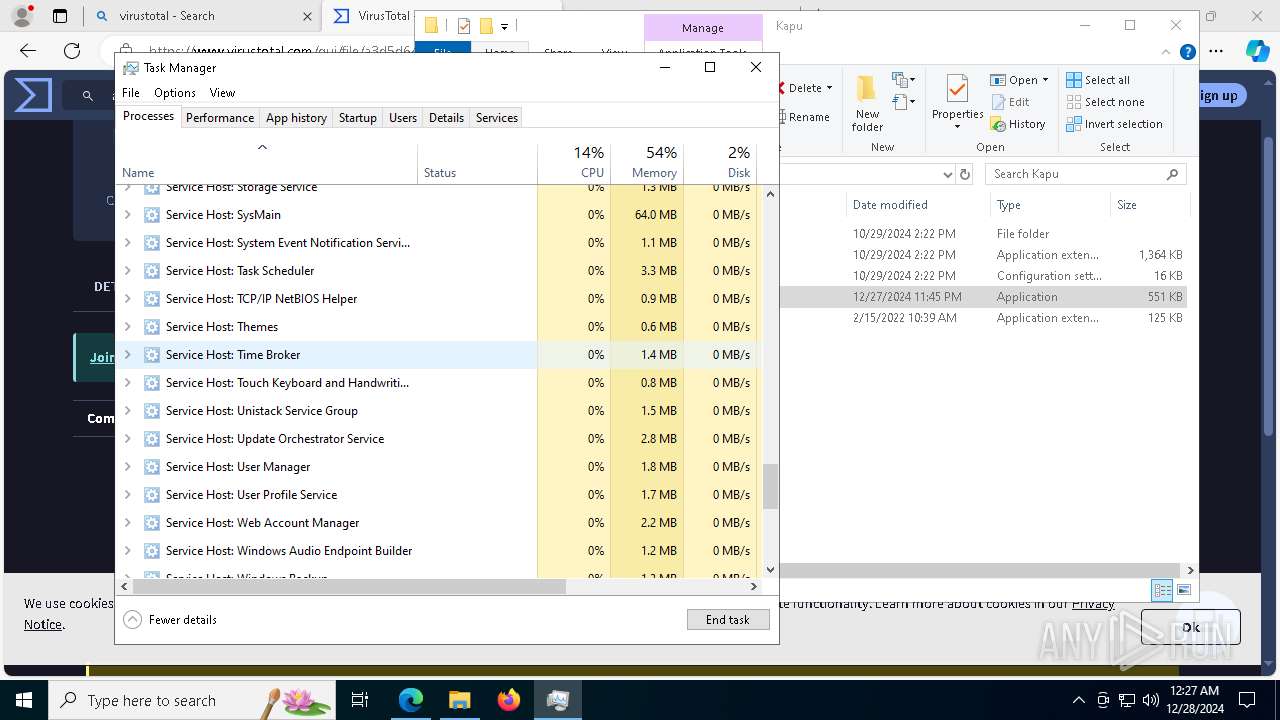
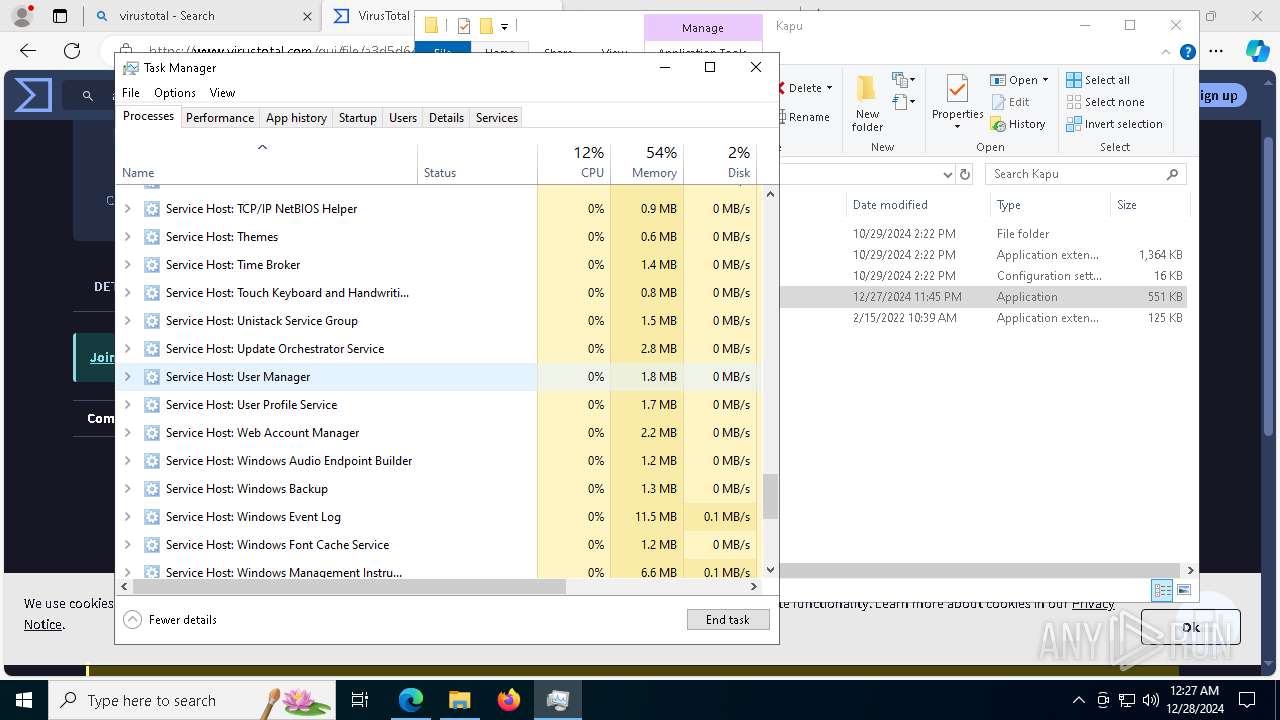
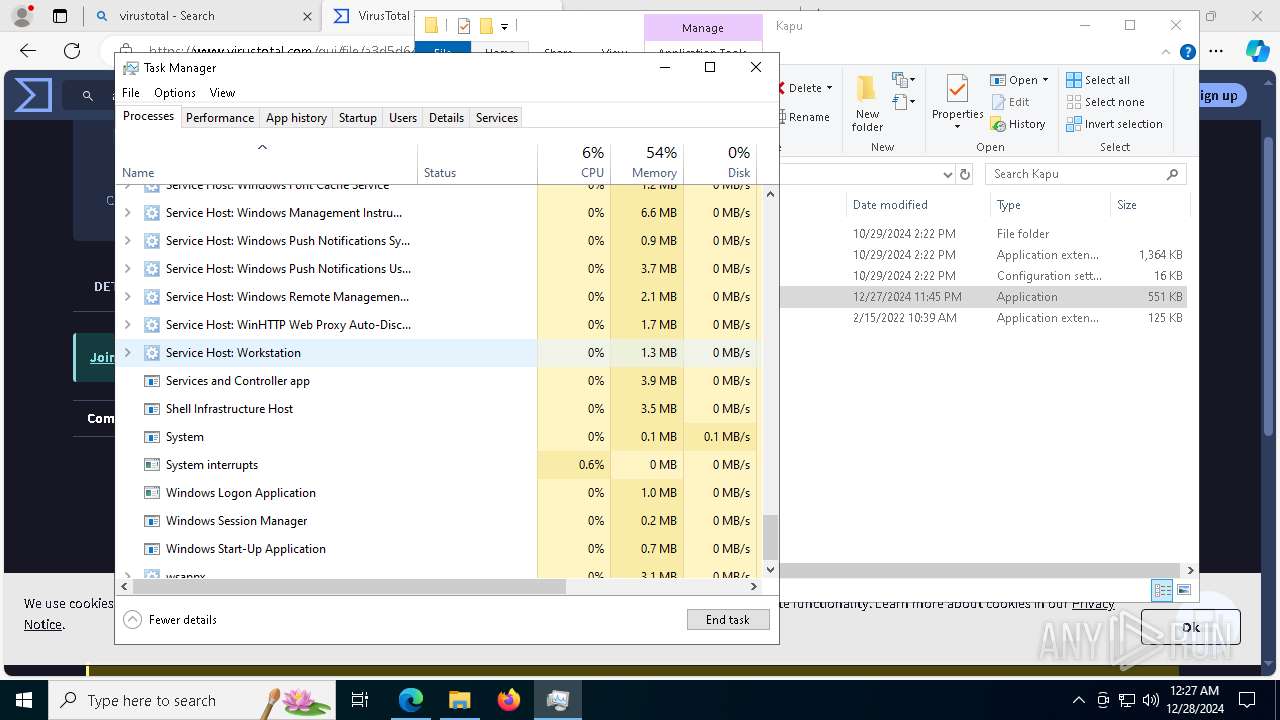
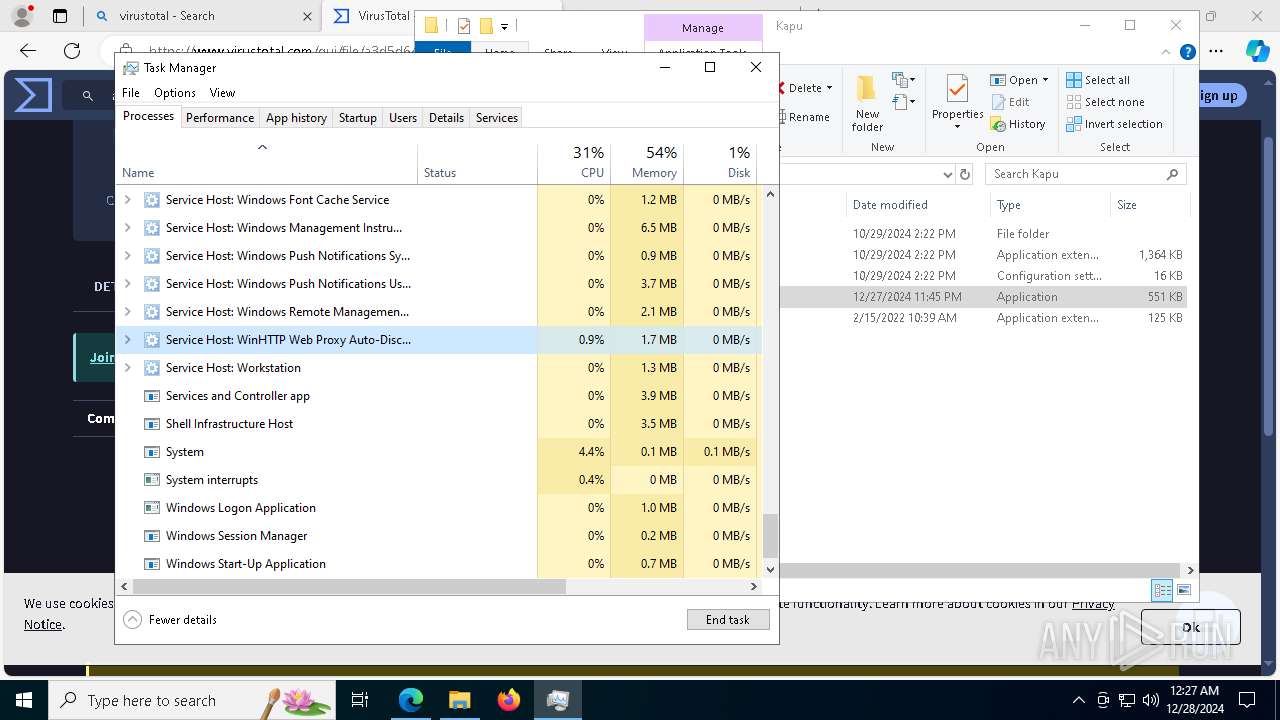
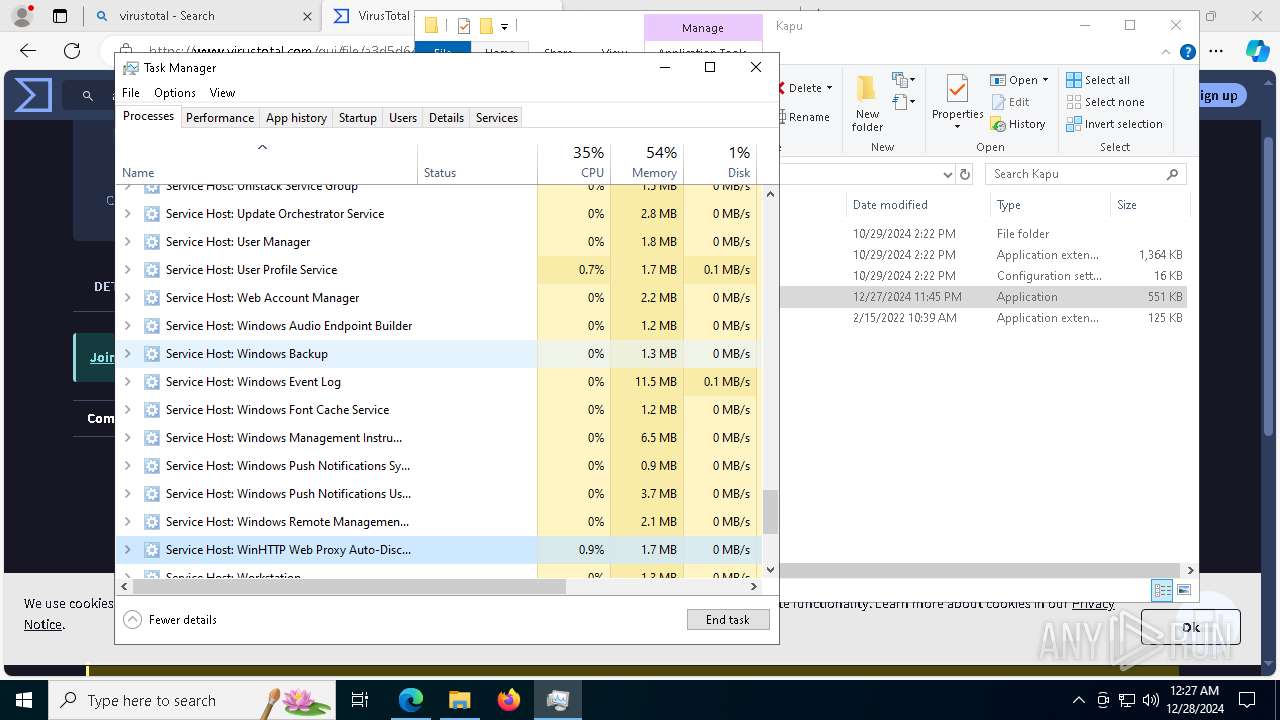
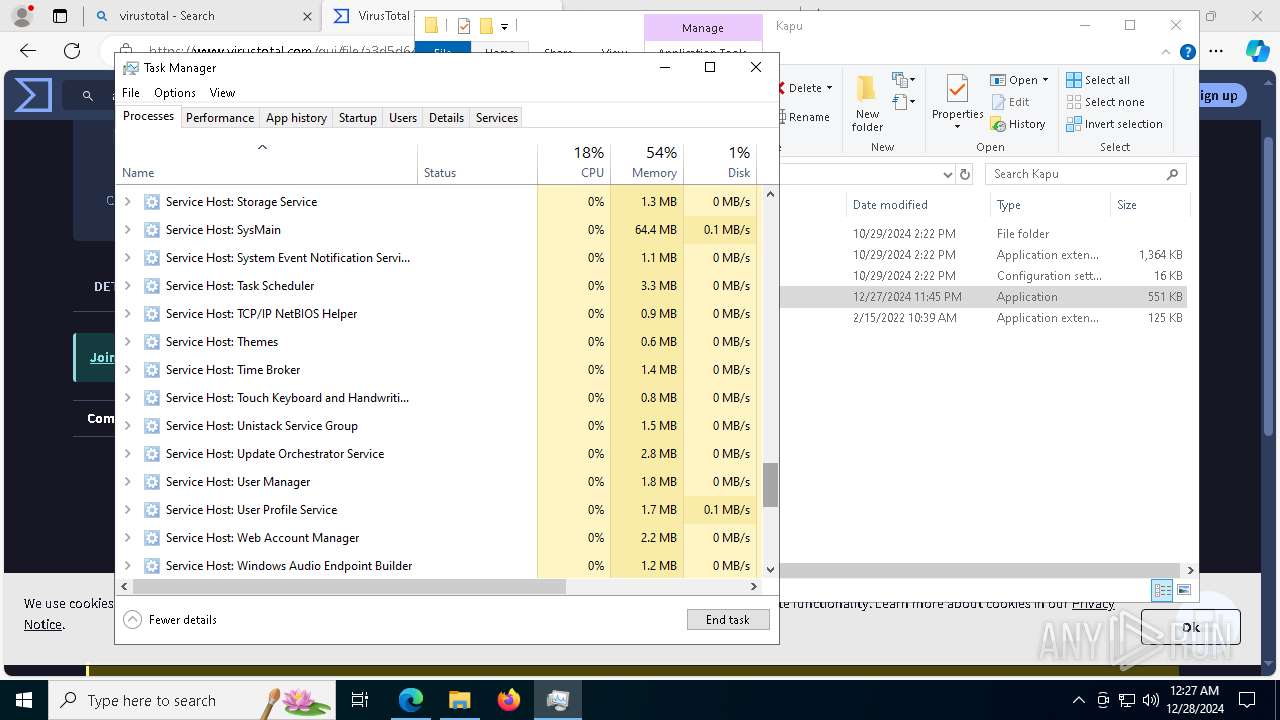
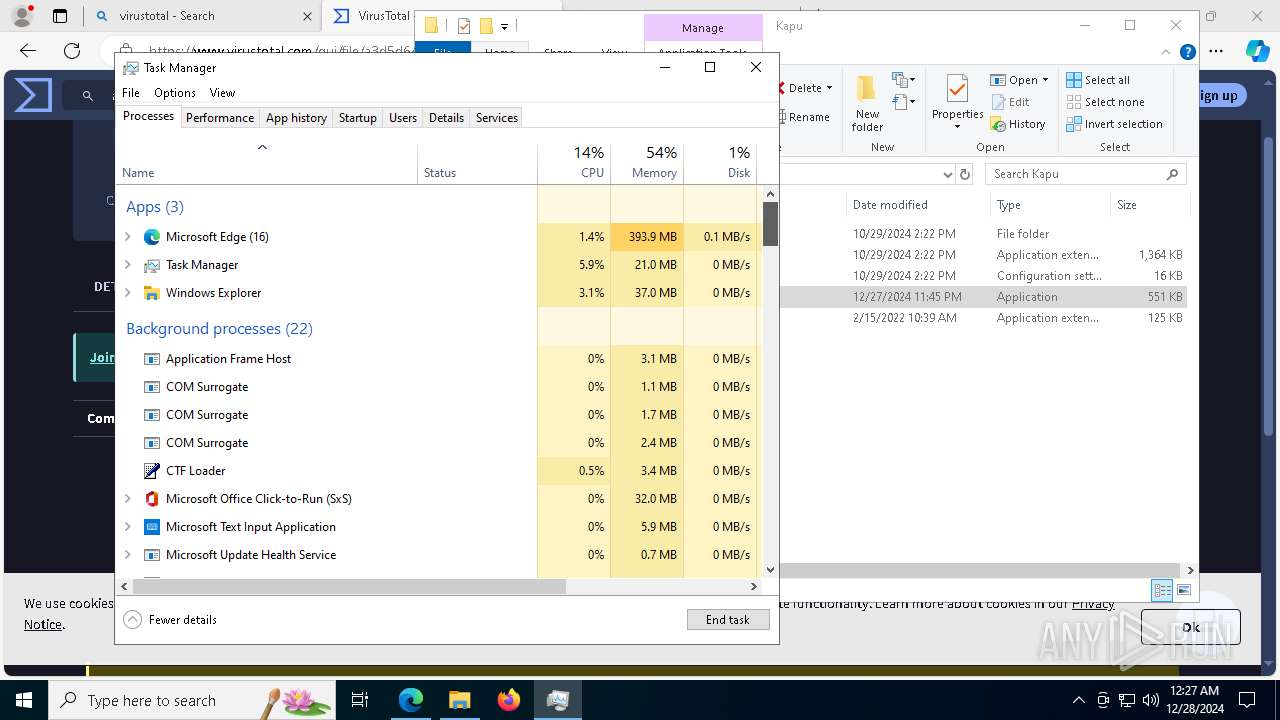
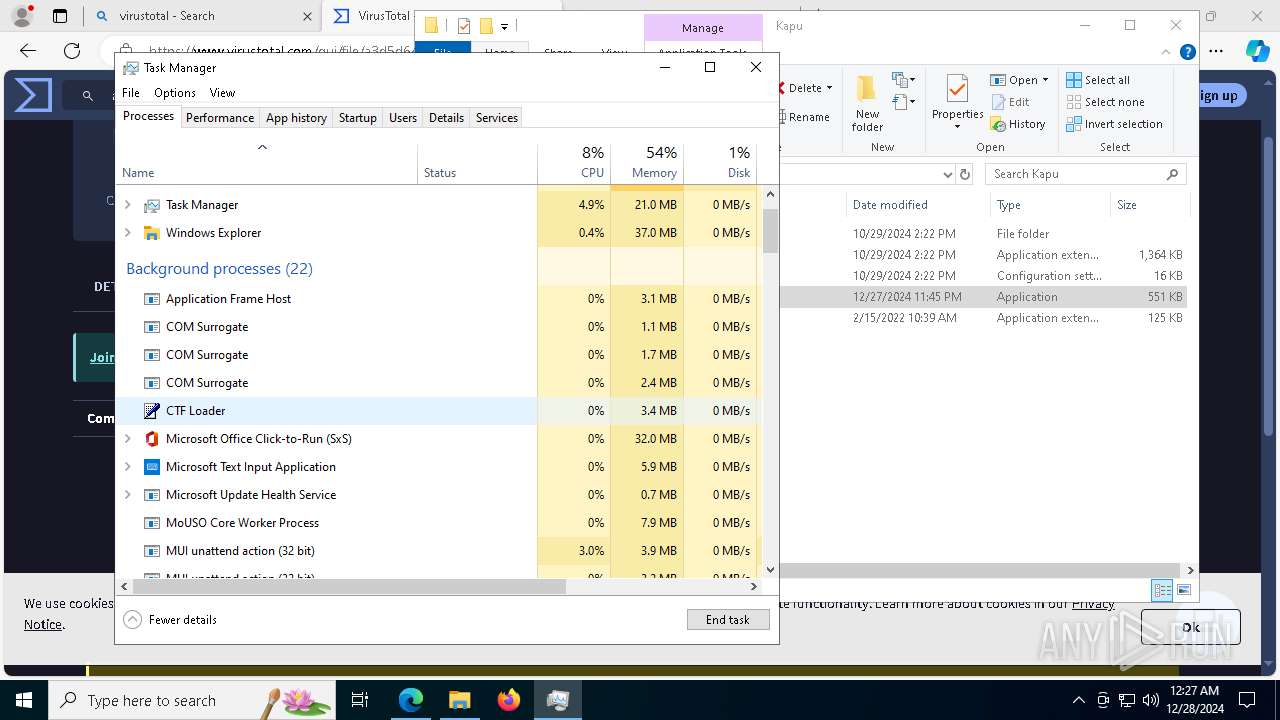
Uses pipe srvsvc via SMB (transferring data)
- Taskmgr.exe (PID: 2972)
Application launched itself
- Loader.exe (PID: 6228)
- Loader.exe (PID: 1612)
- Loader.exe (PID: 5212)
INFO
The process uses the downloaded file
- chrome.exe (PID: 2212)
- WinRAR.exe (PID: 6856)
- Taskmgr.exe (PID: 2972)
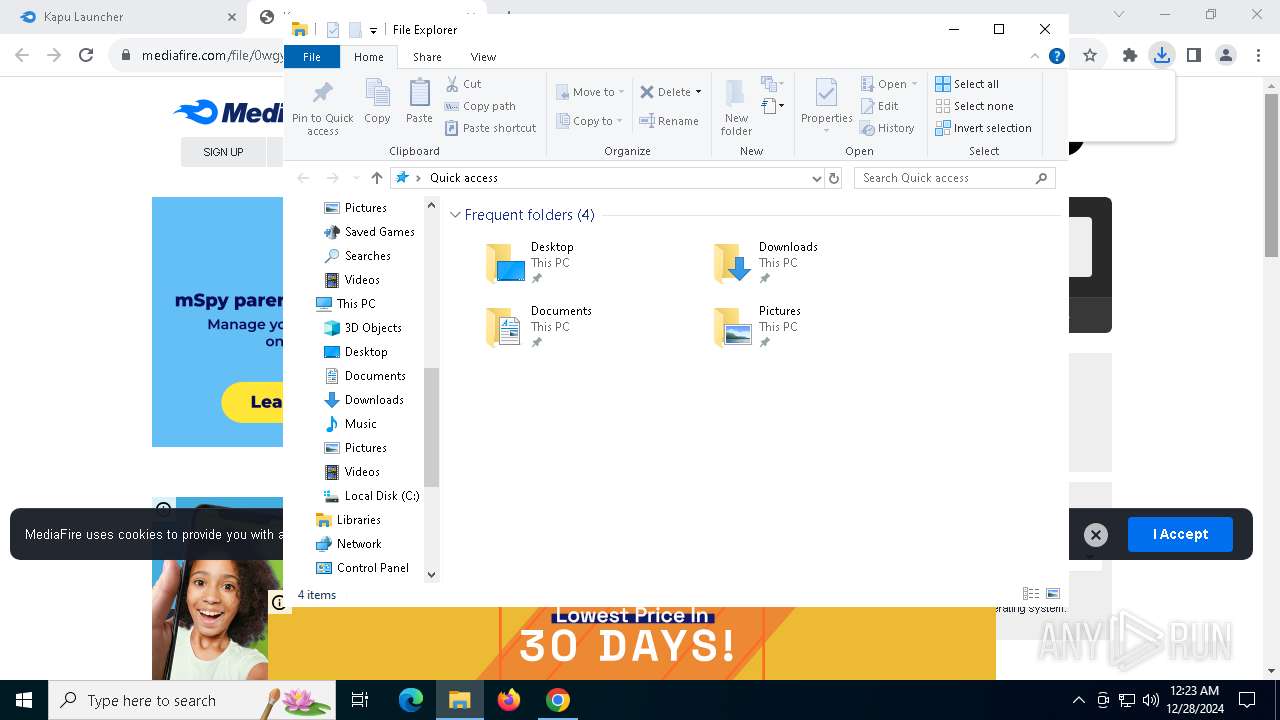
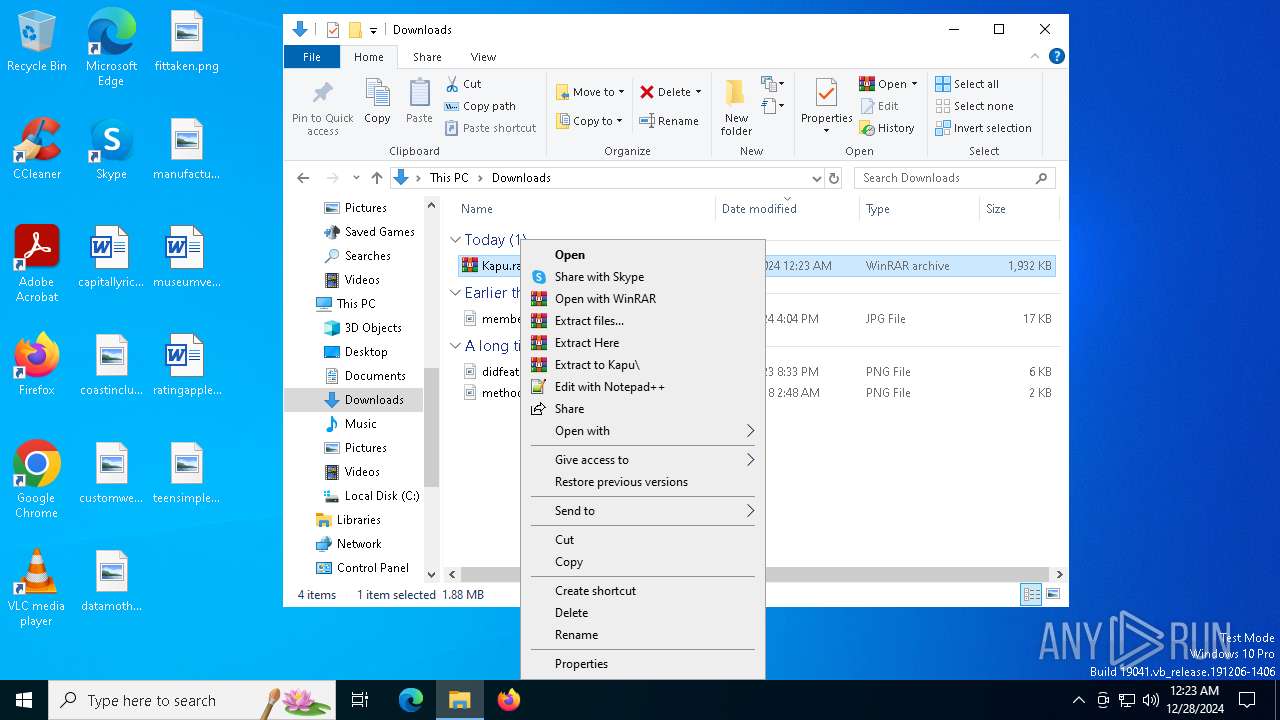
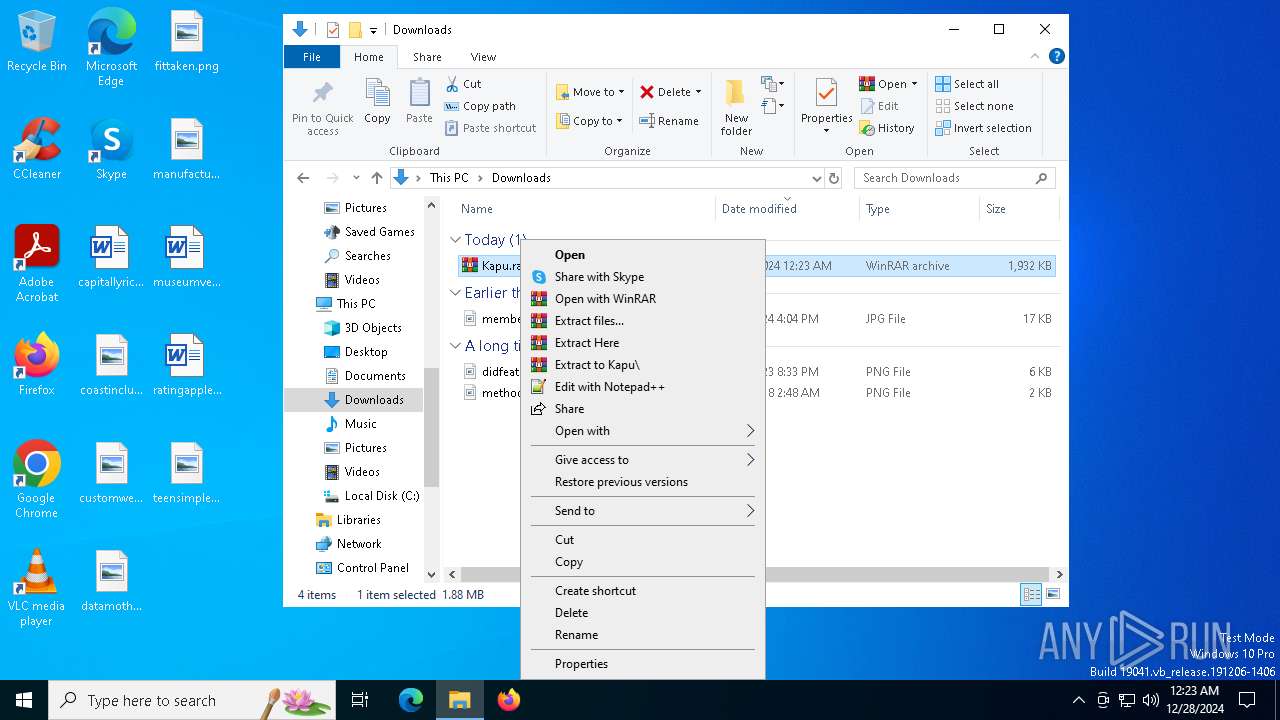
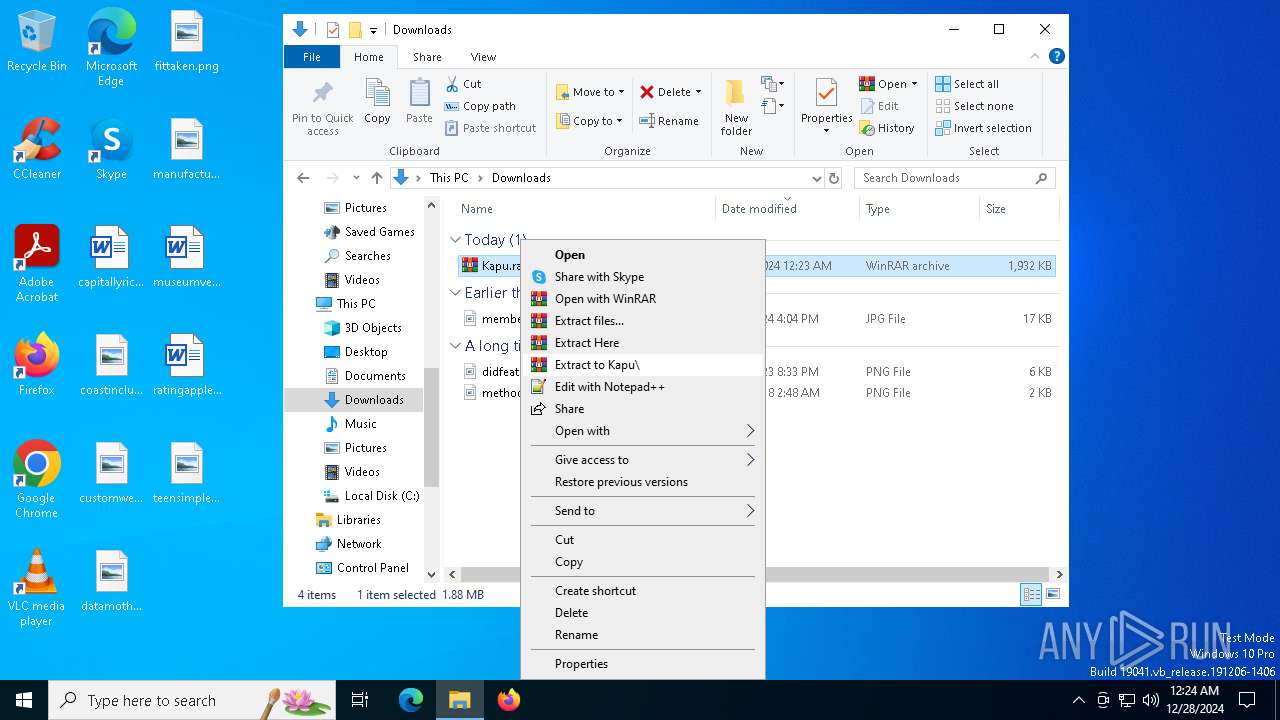
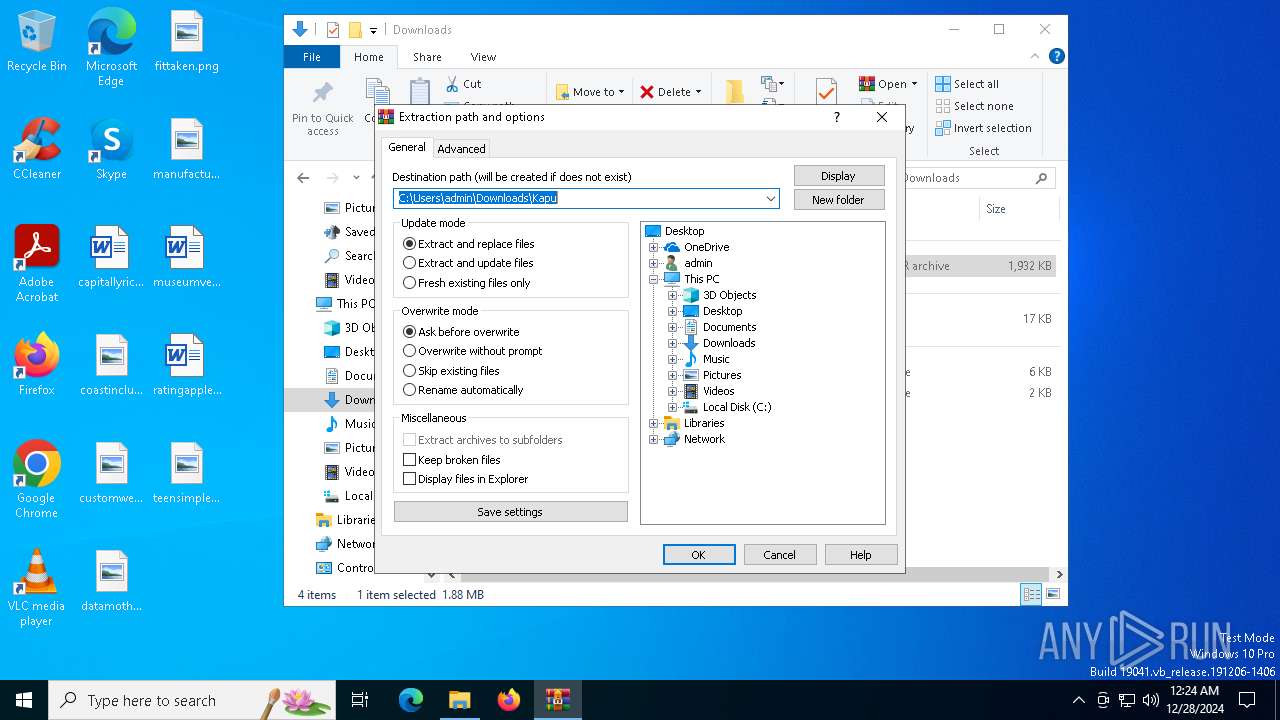
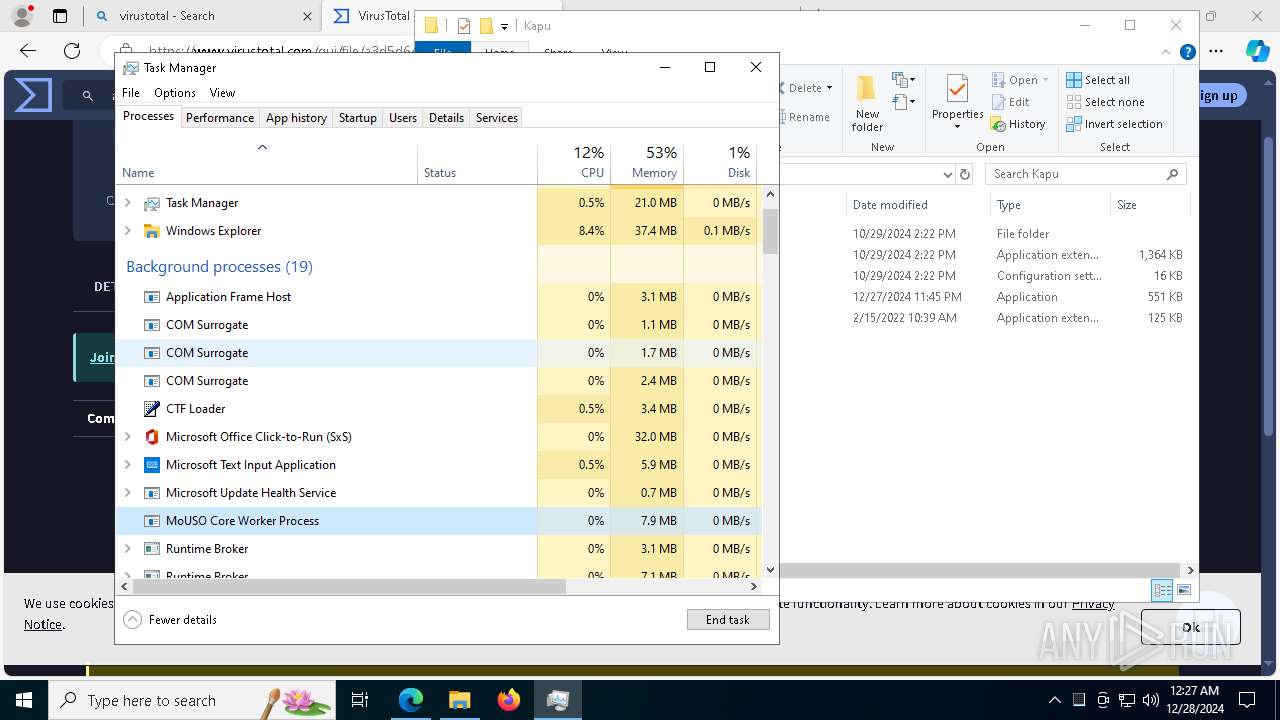
Manual execution by a user
- WinRAR.exe (PID: 6856)
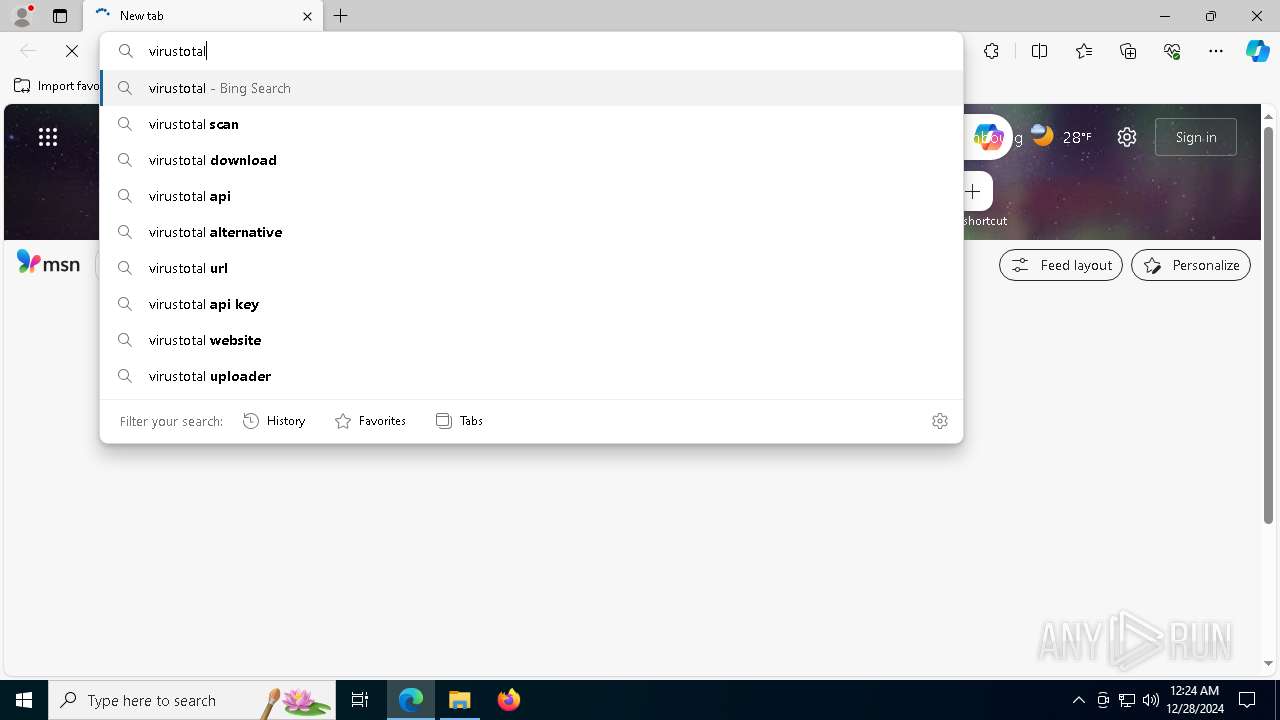
- msedge.exe (PID: 1544)
- Taskmgr.exe (PID: 2972)
- Loader.exe (PID: 6228)
- Taskmgr.exe (PID: 6684)
- Loader.exe (PID: 1612)
- Loader.exe (PID: 5212)
Application launched itself
- chrome.exe (PID: 5628)
- msedge.exe (PID: 1544)
The sample compiled with english language support
- WinRAR.exe (PID: 6856)
- msedge.exe (PID: 4980)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6856)
- msedge.exe (PID: 4980)
Checks supported languages
- identity_helper.exe (PID: 4972)
- Loader.exe (PID: 6228)
- Loader.exe (PID: 7964)
- Loader.exe (PID: 7080)
- Loader.exe (PID: 5212)
- Loader.exe (PID: 1612)
- Loader.exe (PID: 7960)
Reads the computer name
- identity_helper.exe (PID: 4972)
- Loader.exe (PID: 7964)
- Loader.exe (PID: 7080)
- Loader.exe (PID: 7960)
Reads Environment values
- identity_helper.exe (PID: 4972)
Reads the software policy settings
- Loader.exe (PID: 7964)
- Loader.exe (PID: 7080)
- Loader.exe (PID: 7960)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
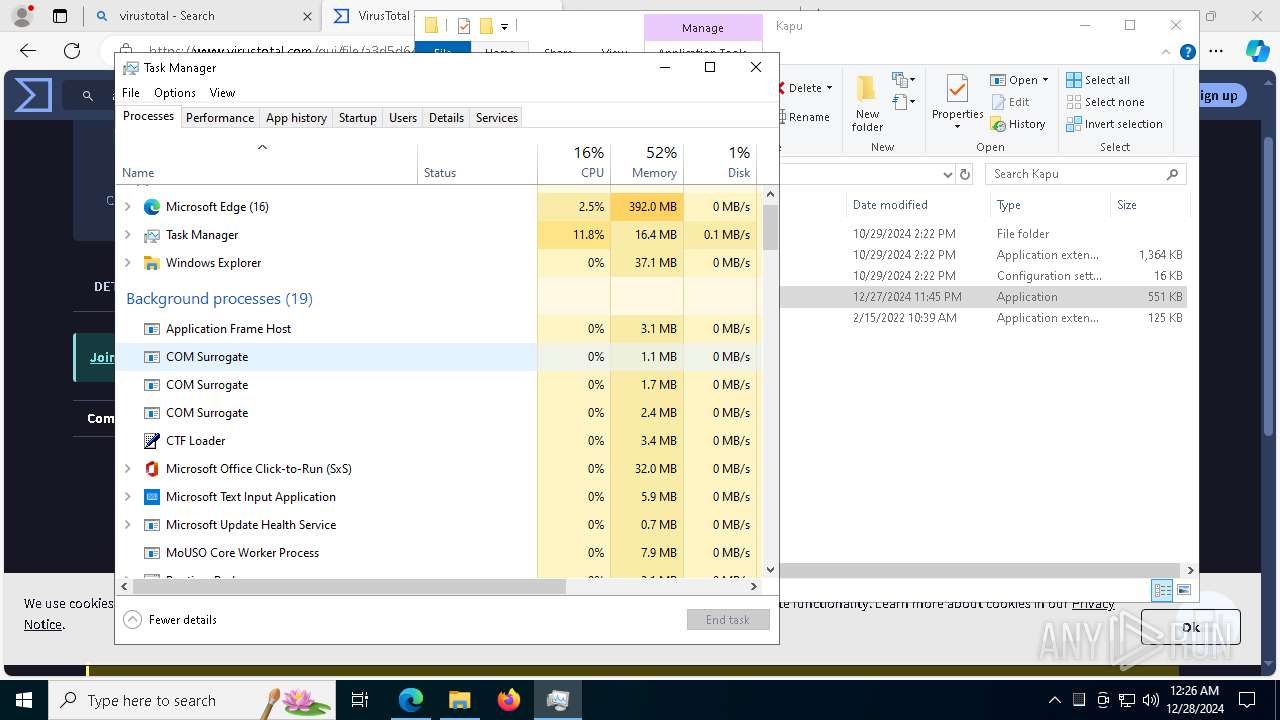
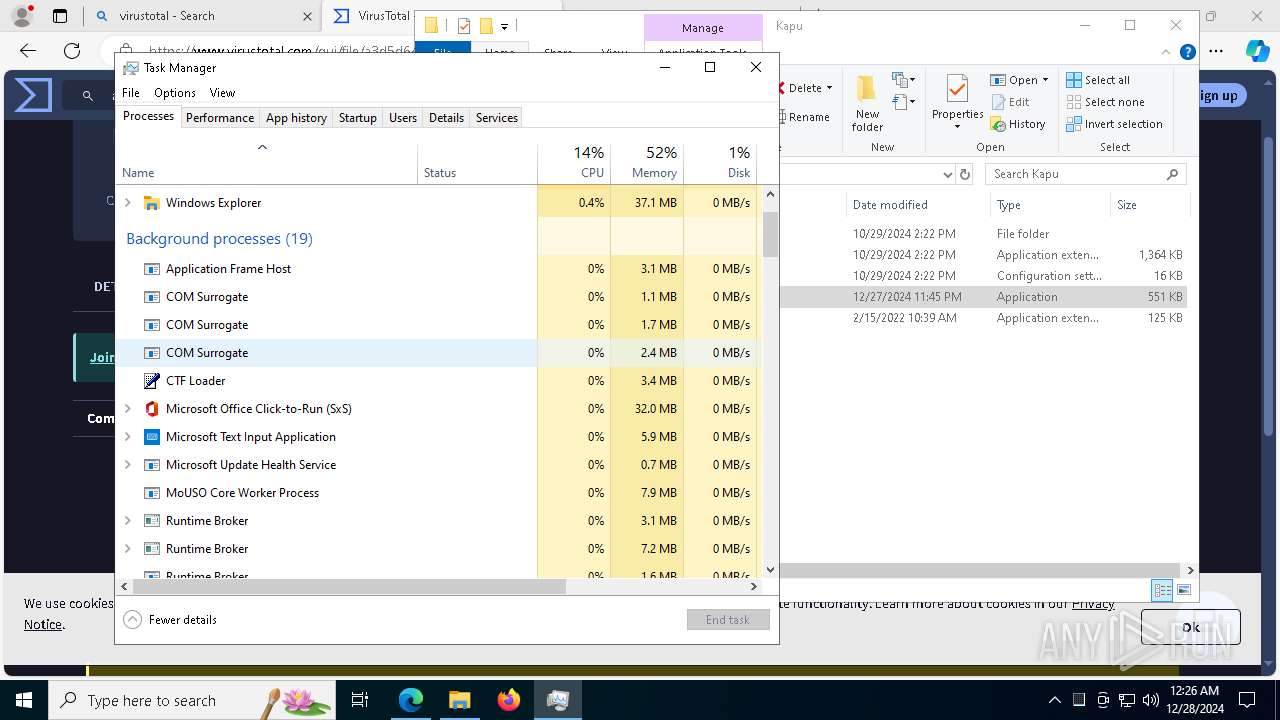
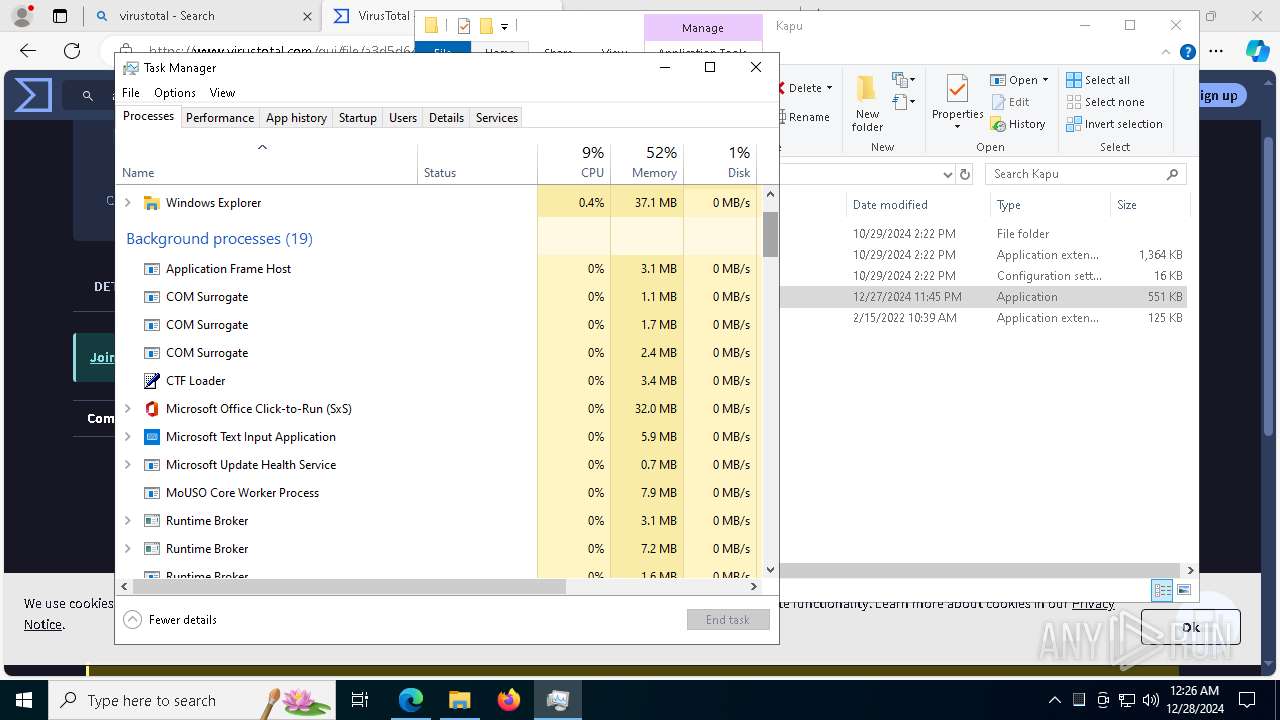
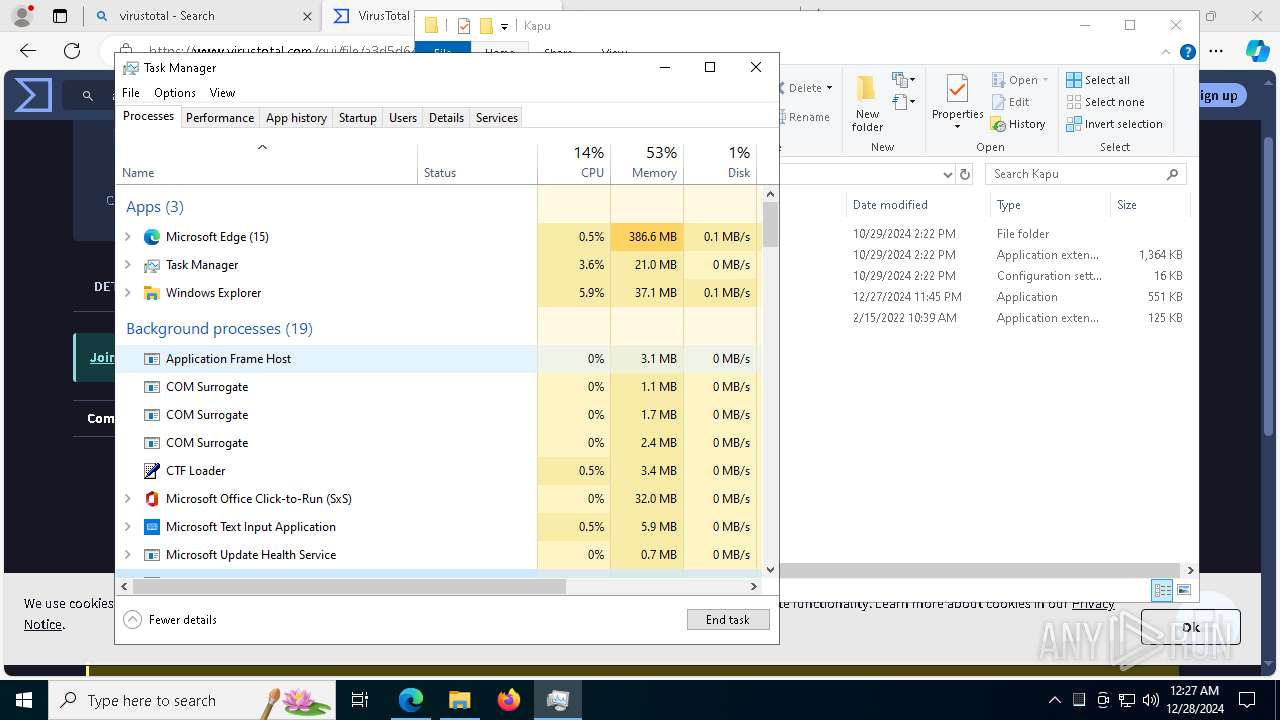
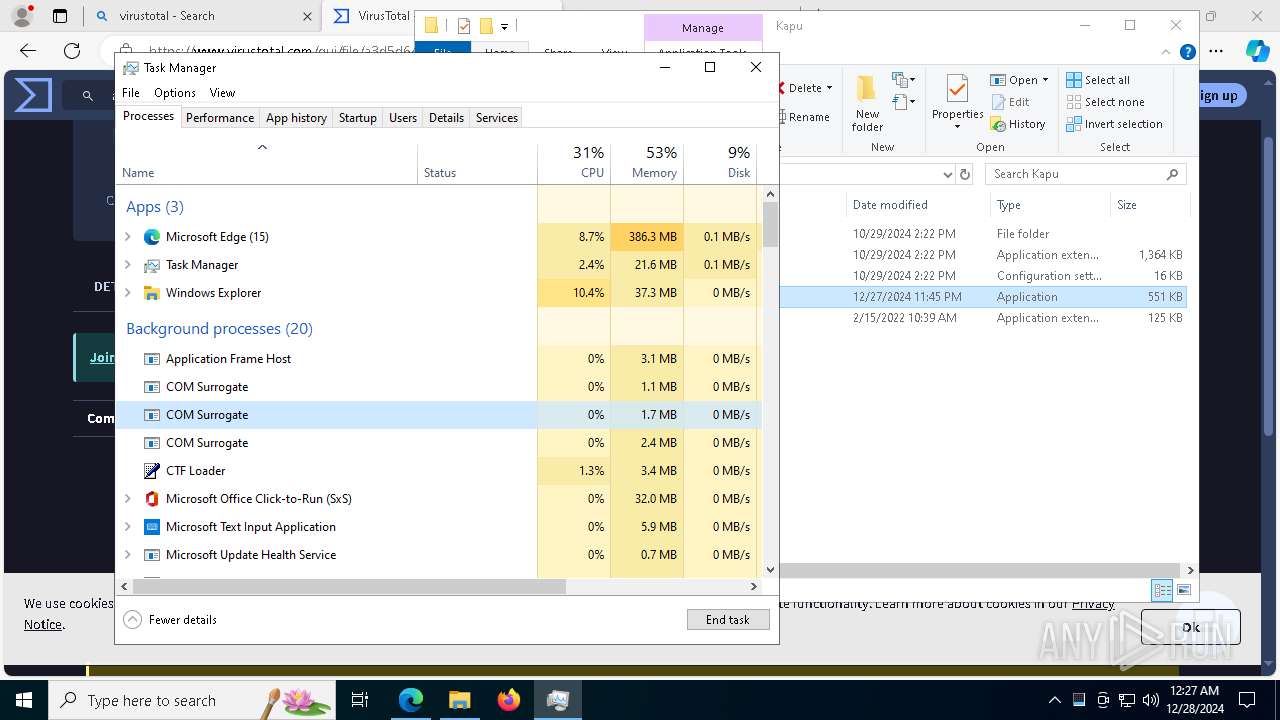
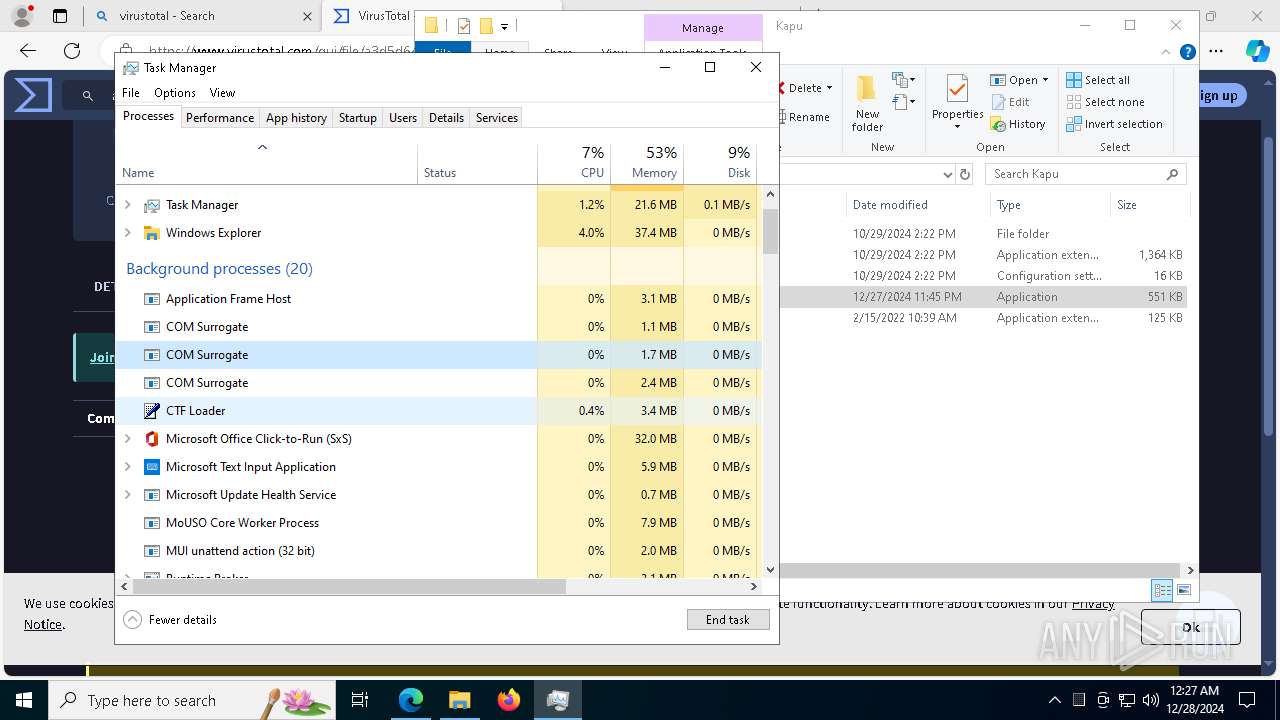
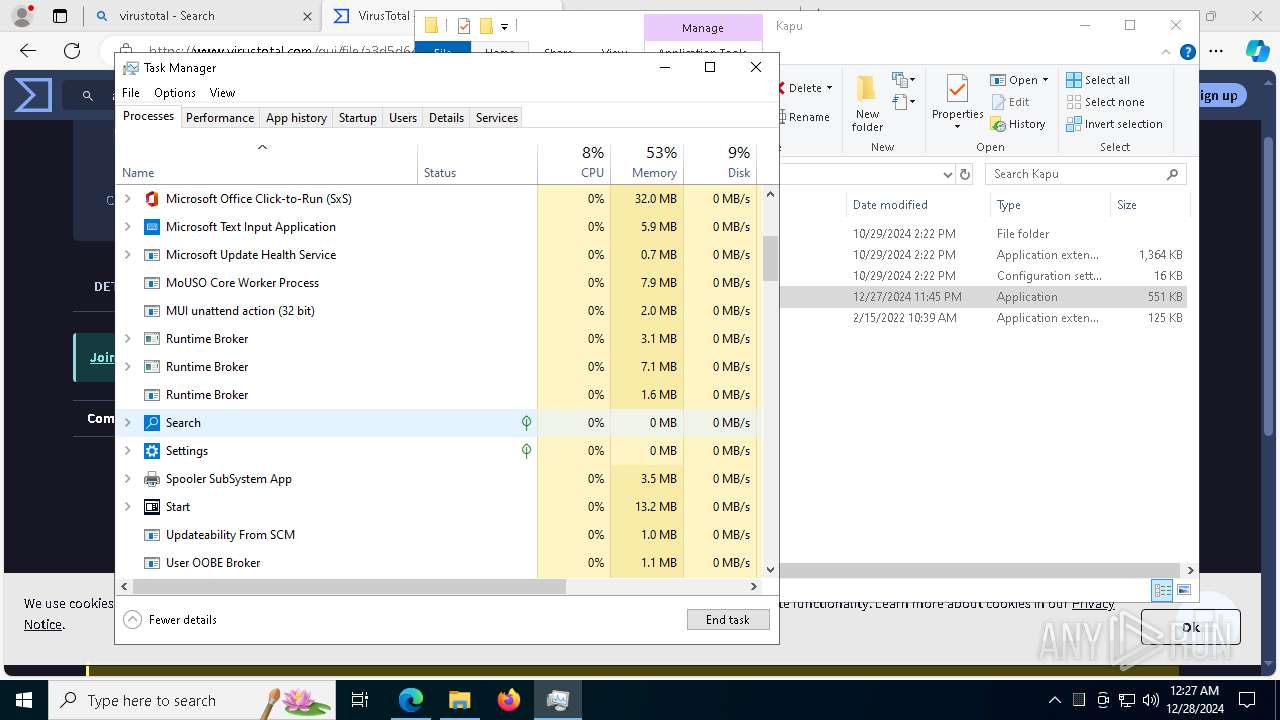
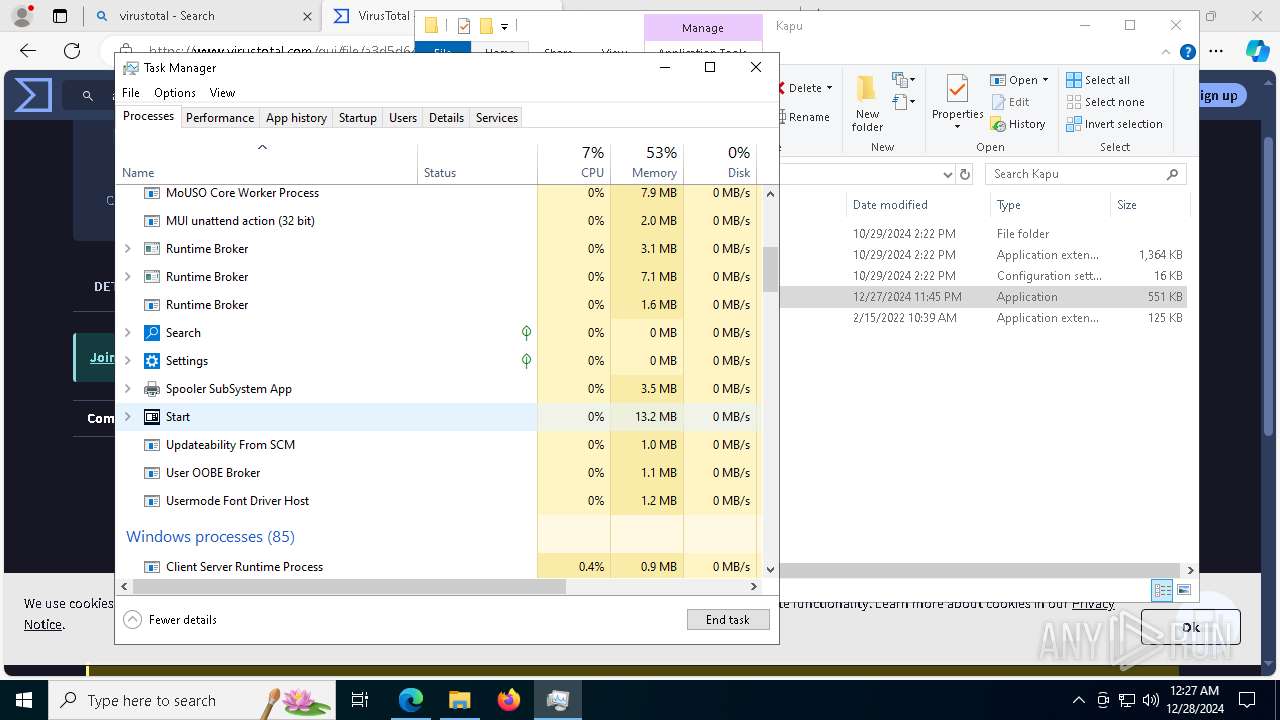
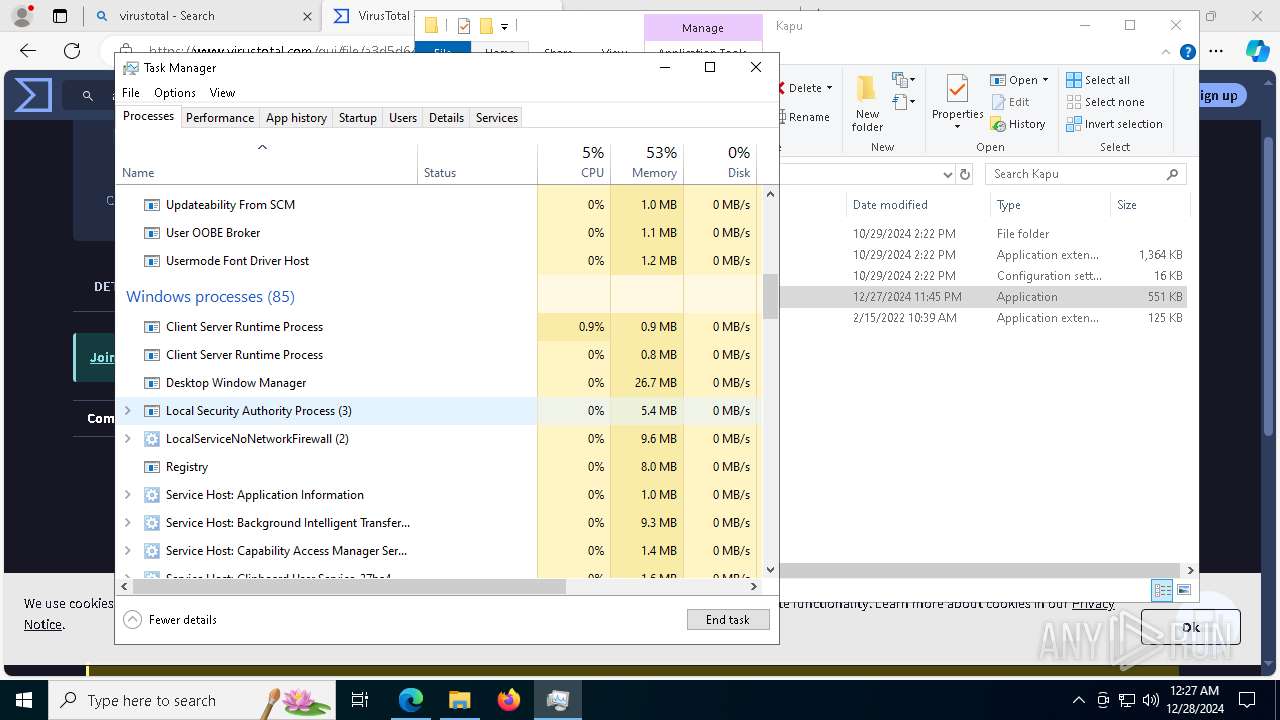
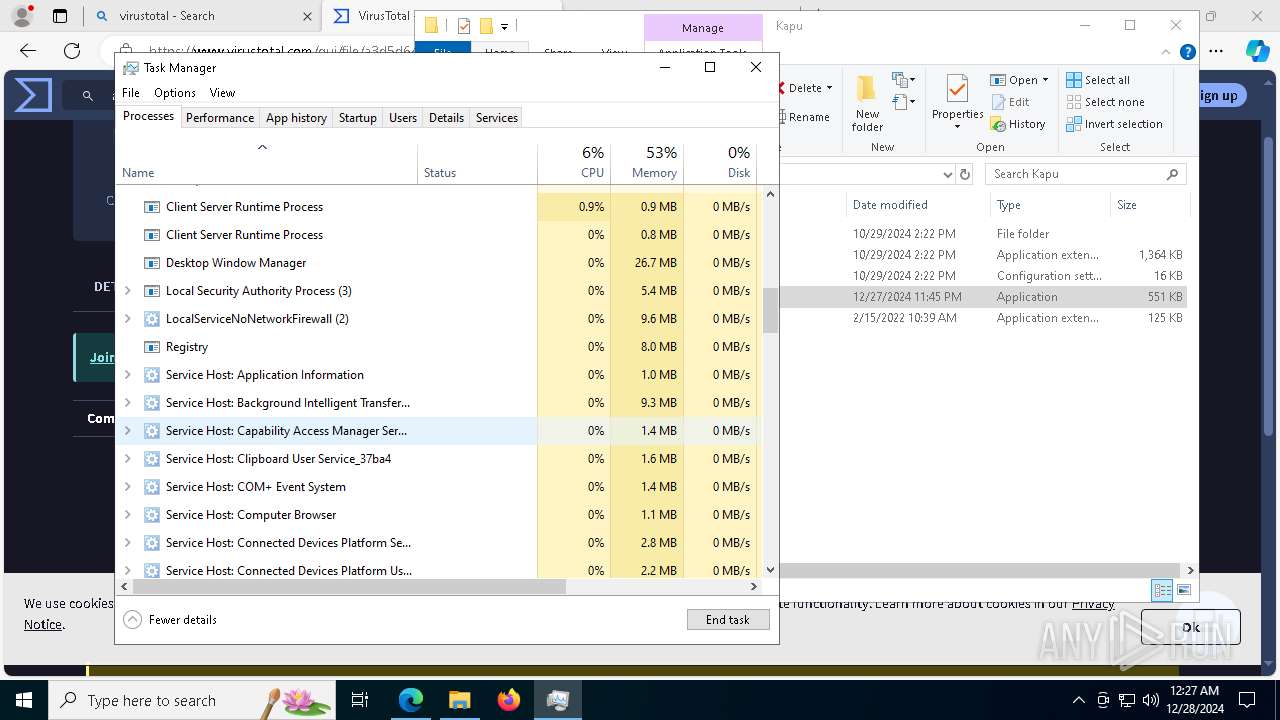
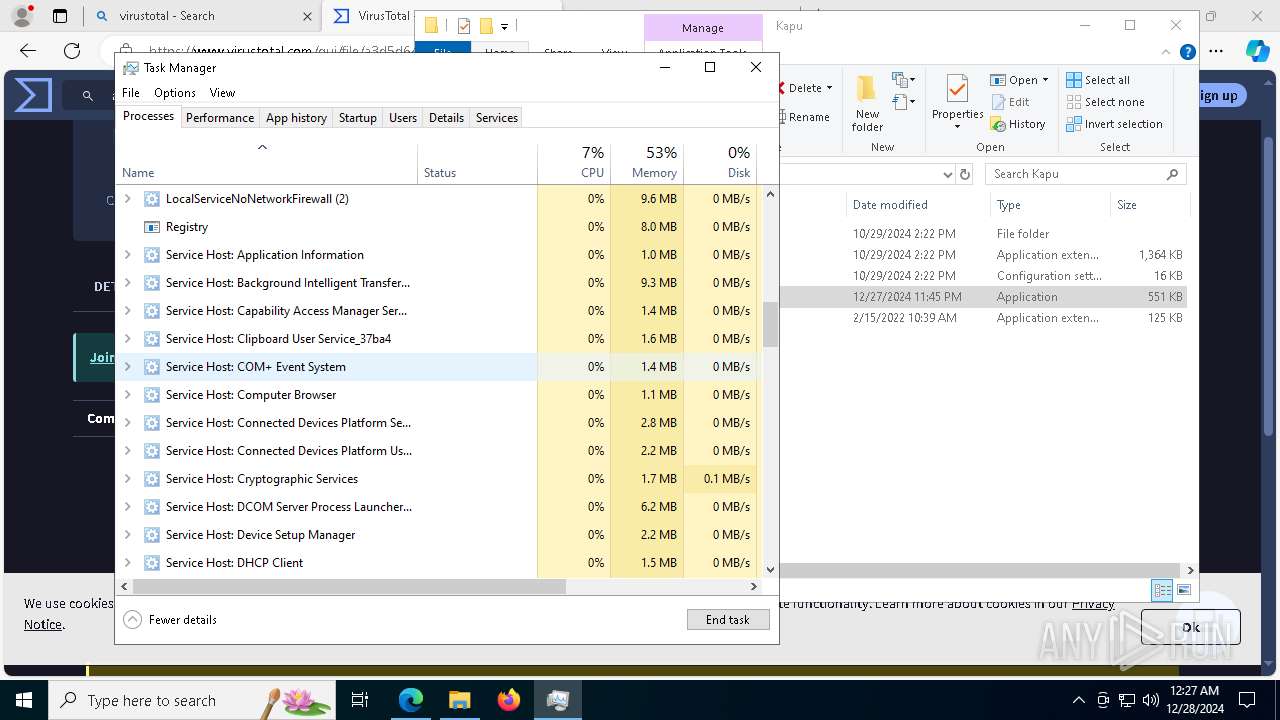
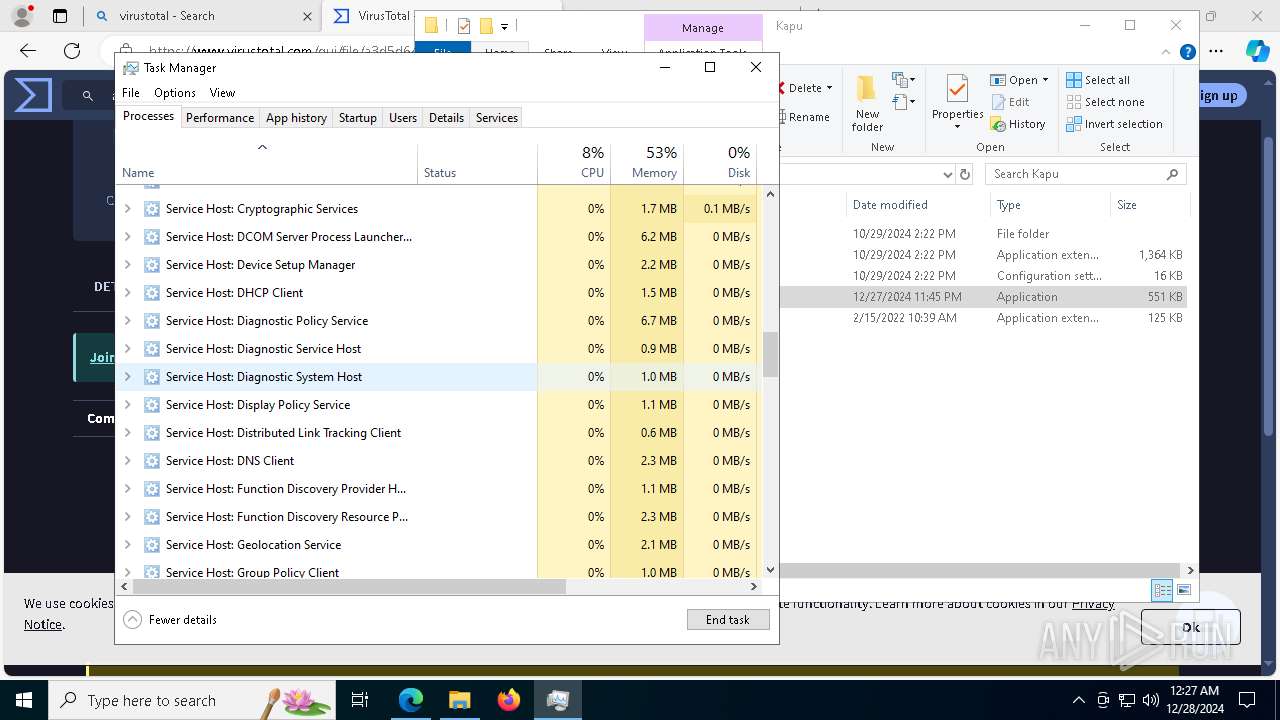
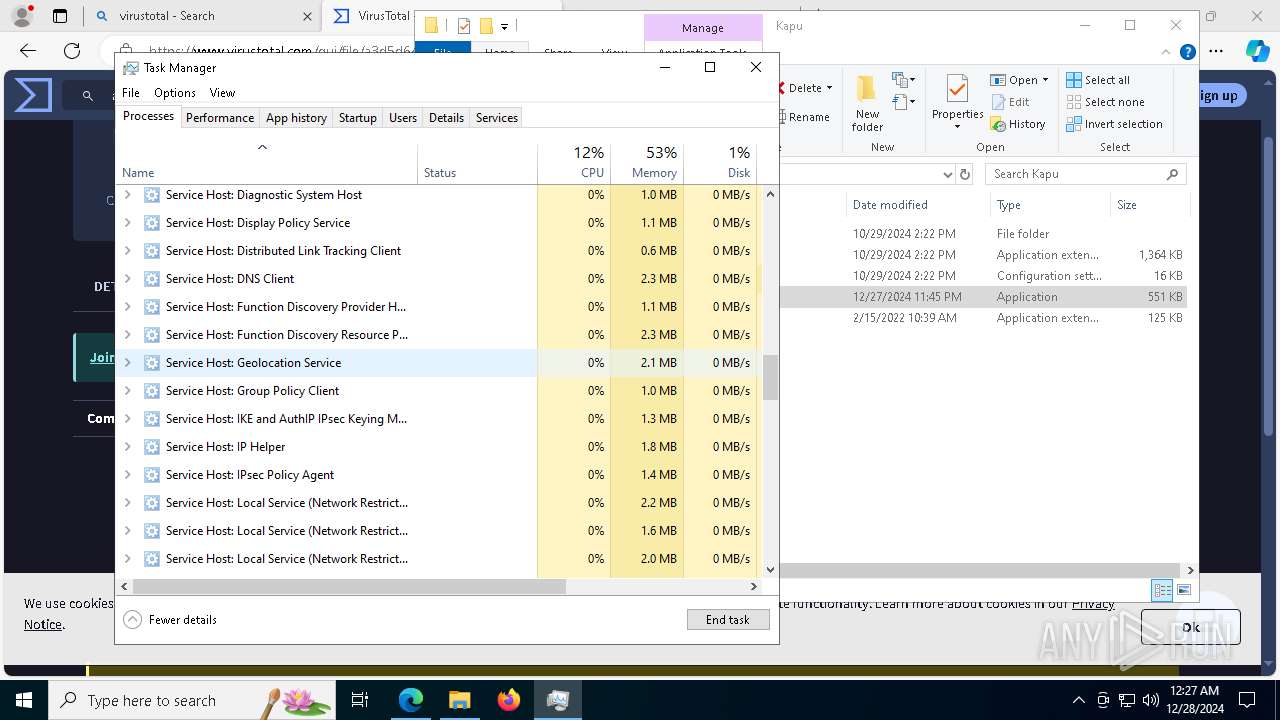
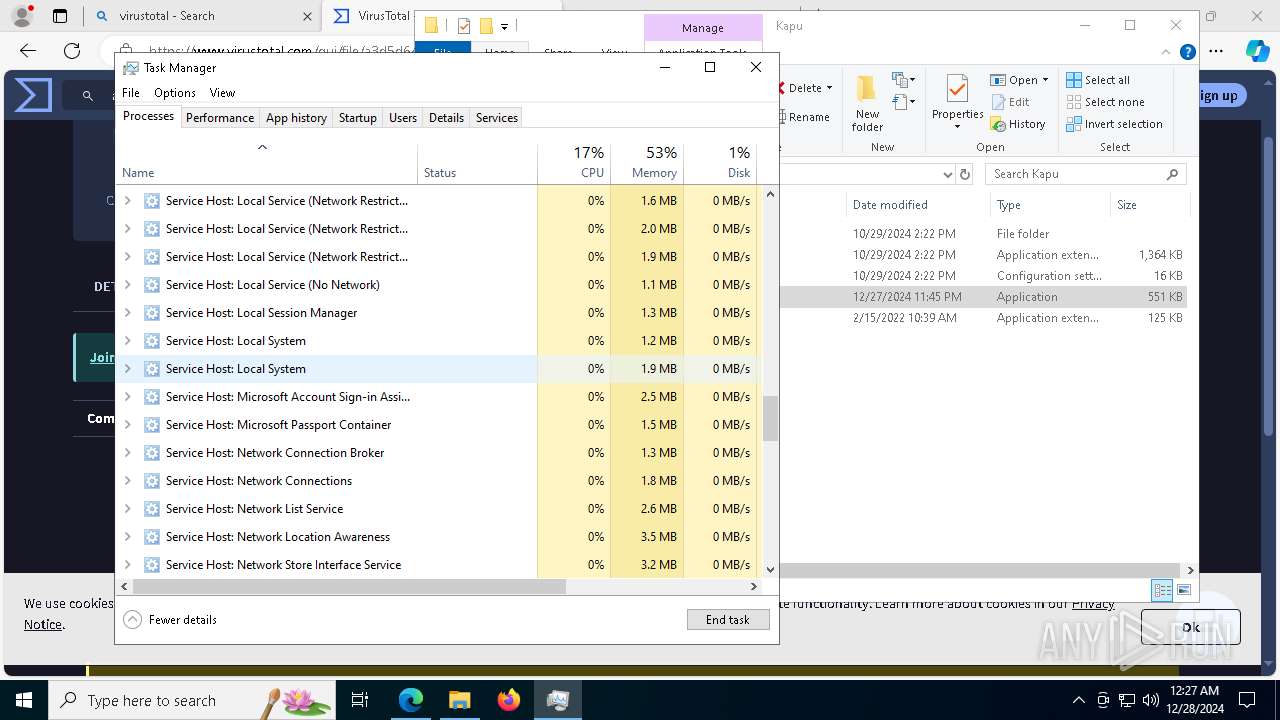
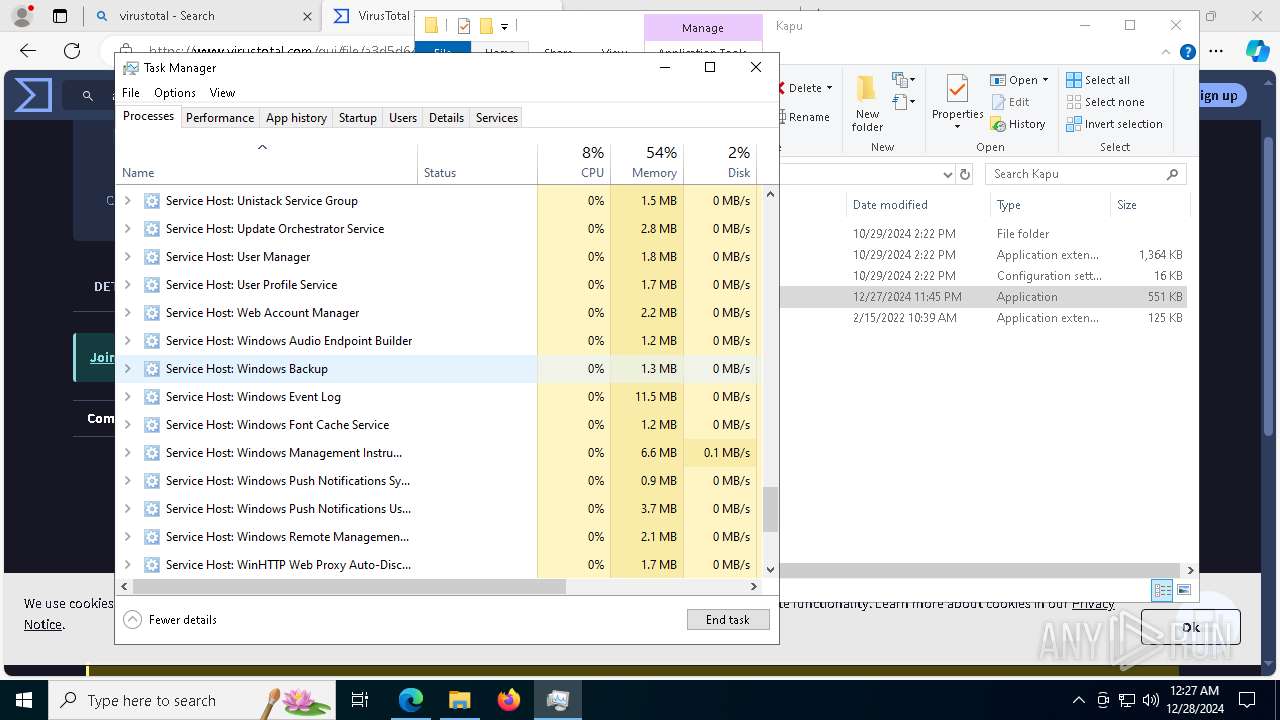
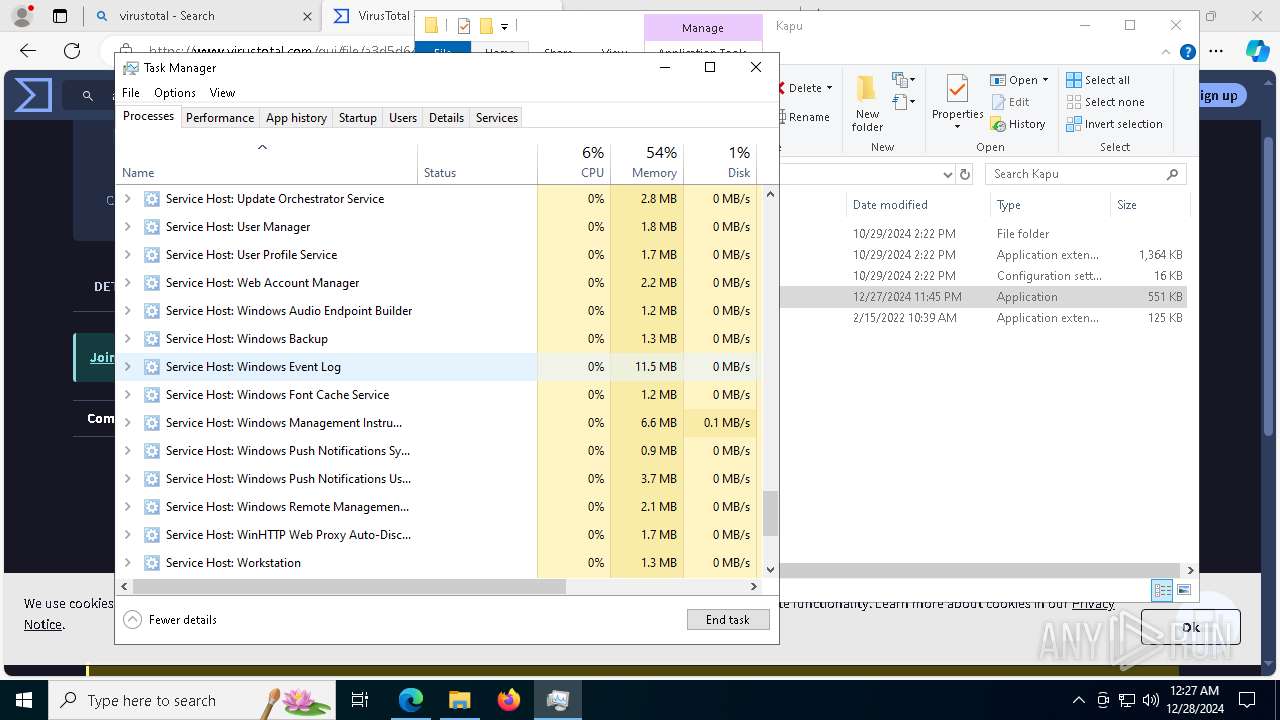
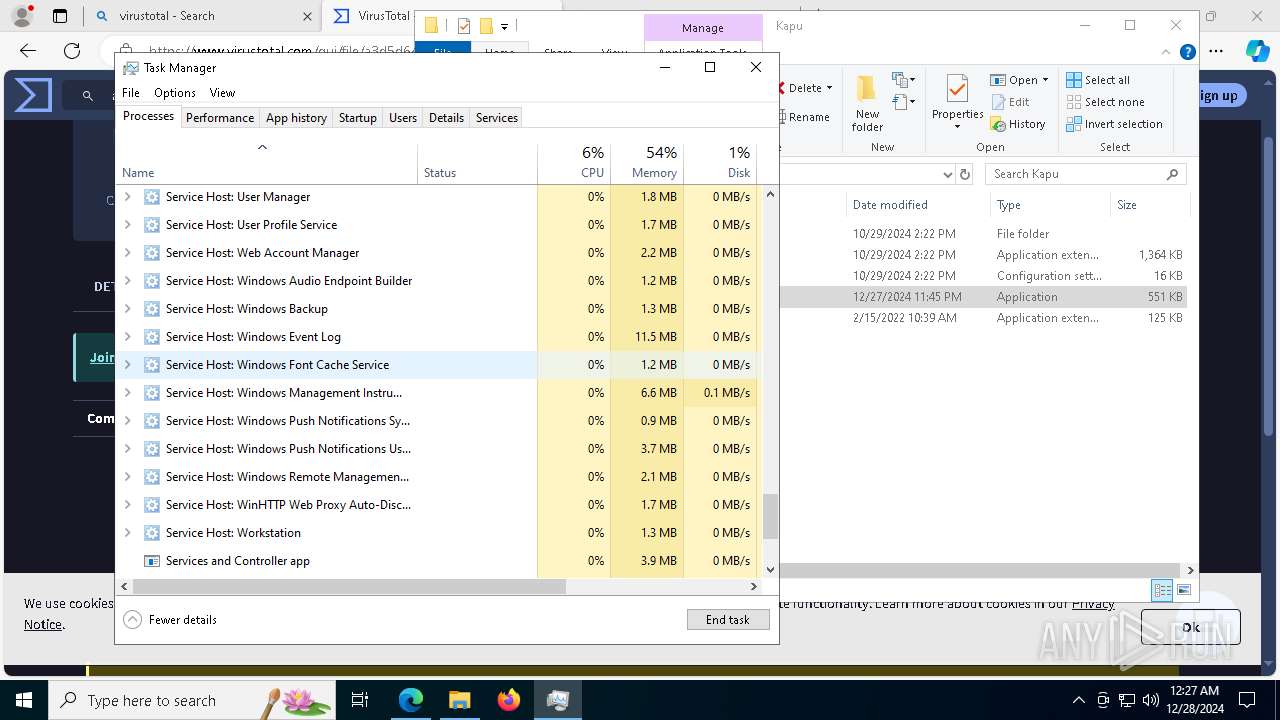
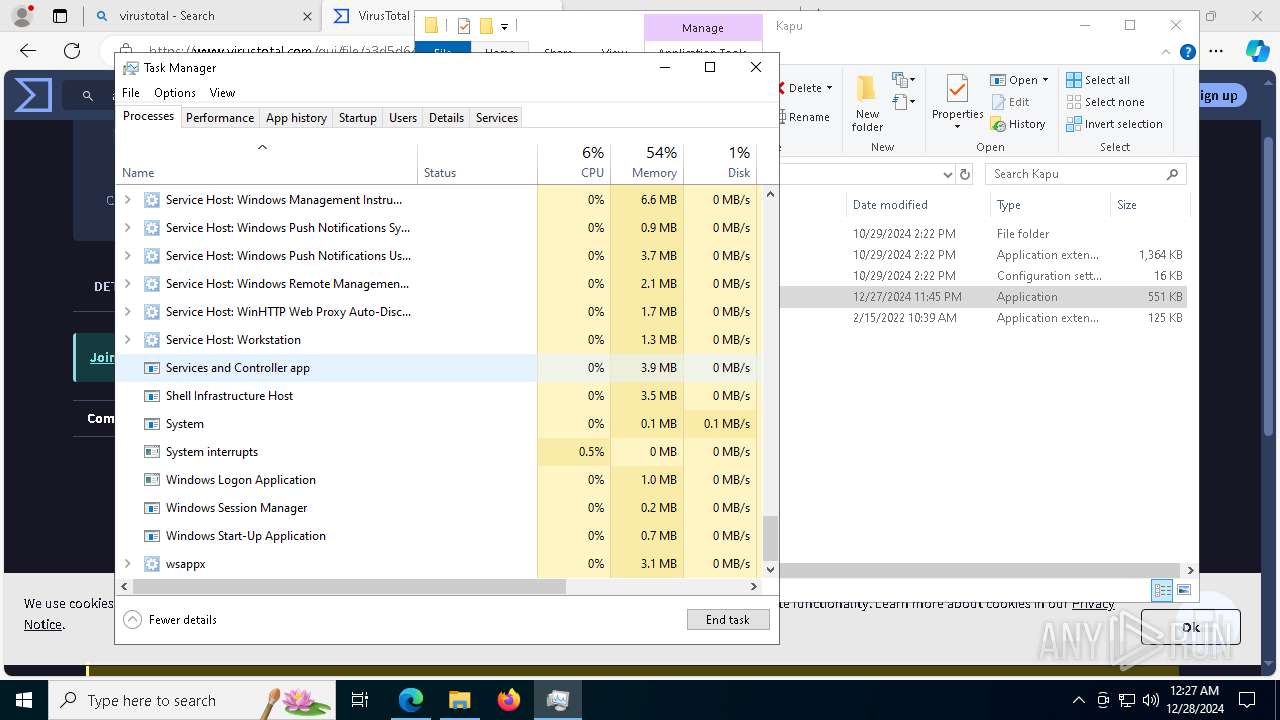
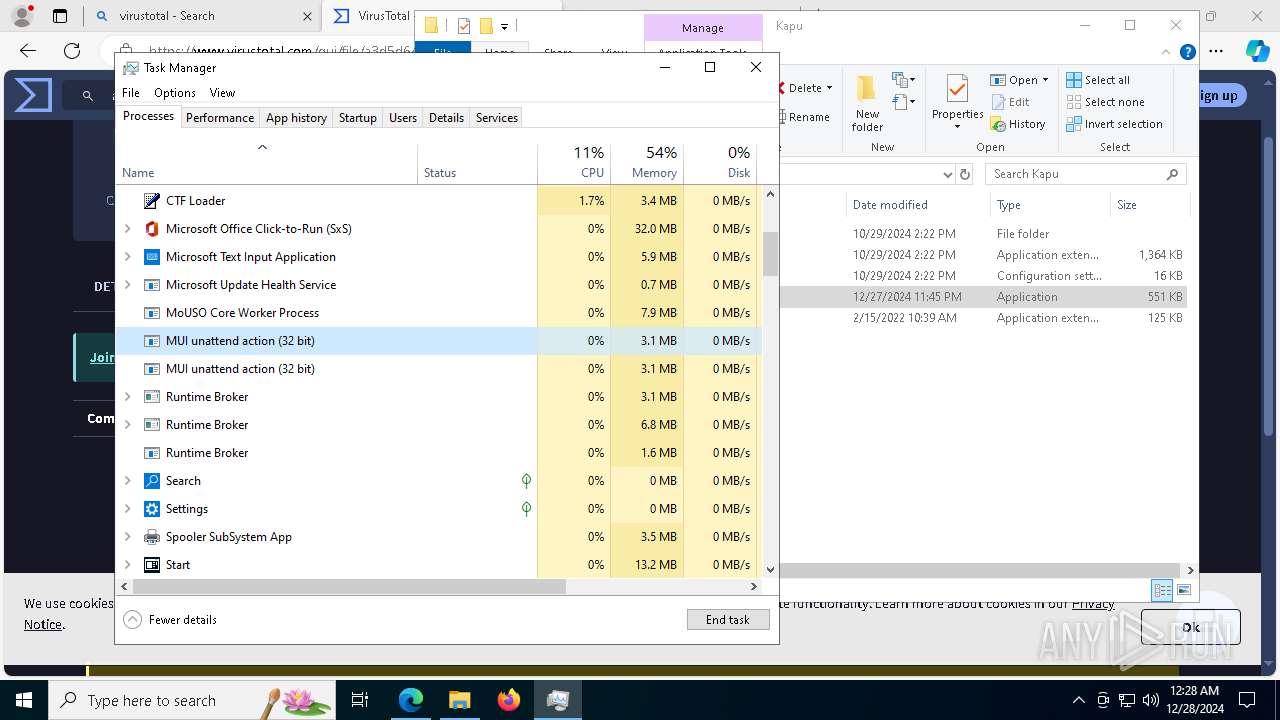
Total processes
232
Monitored processes
97
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=7348 --field-trial-handle=2340,i,6939149805157437803,3081374557599236460,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=9428 --field-trial-handle=2340,i,6939149805157437803,3081374557599236460,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=8128 --field-trial-handle=2340,i,6939149805157437803,3081374557599236460,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6372 --field-trial-handle=2340,i,6939149805157437803,3081374557599236460,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=6260 --field-trial-handle=2340,i,6939149805157437803,3081374557599236460,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
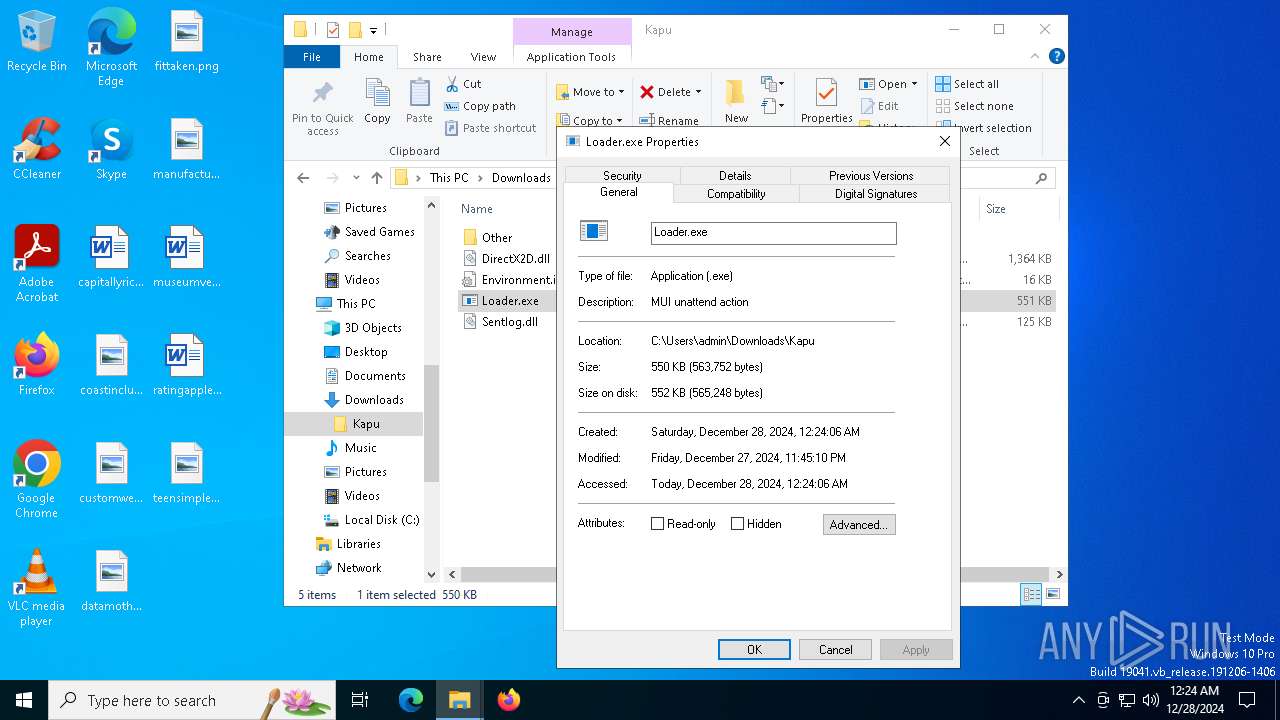
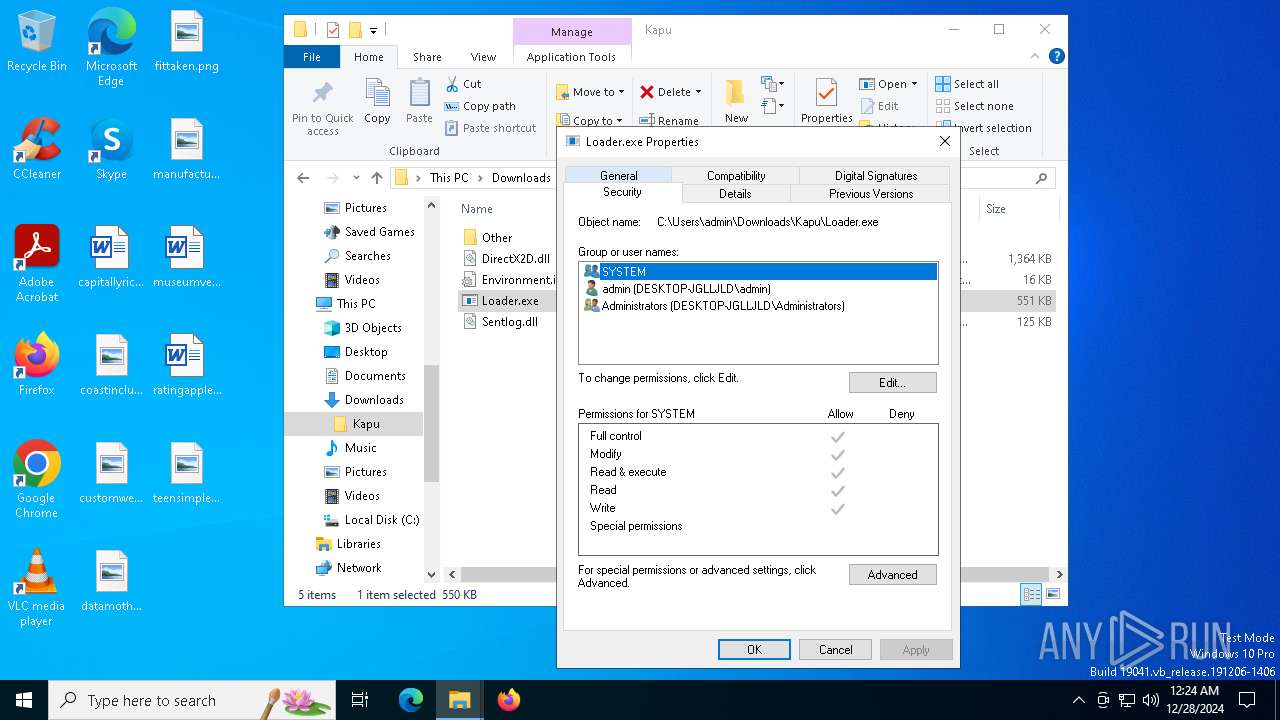
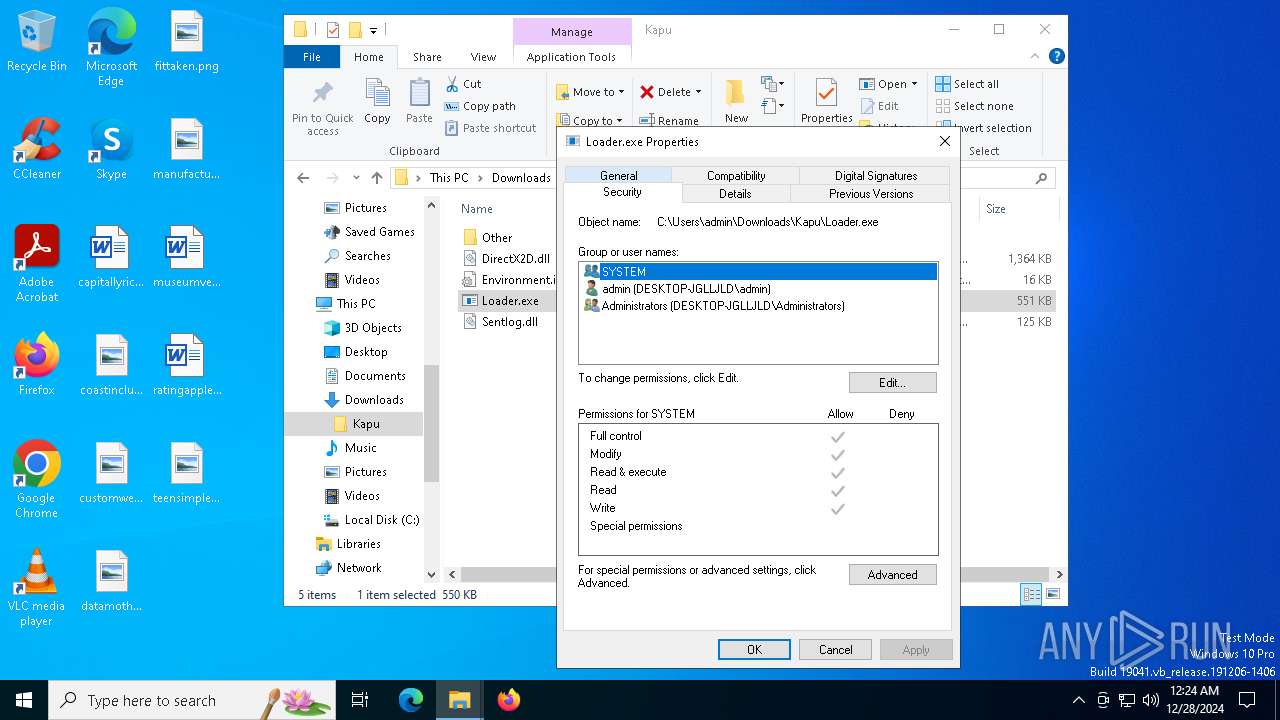
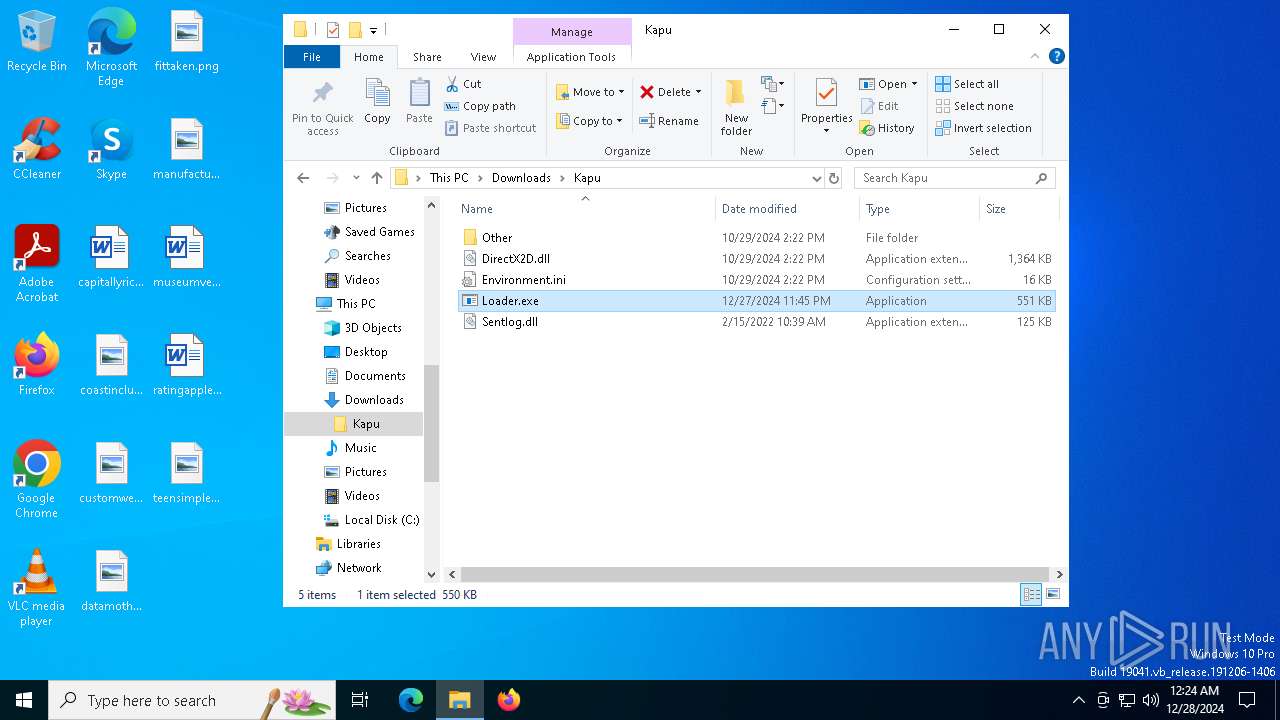
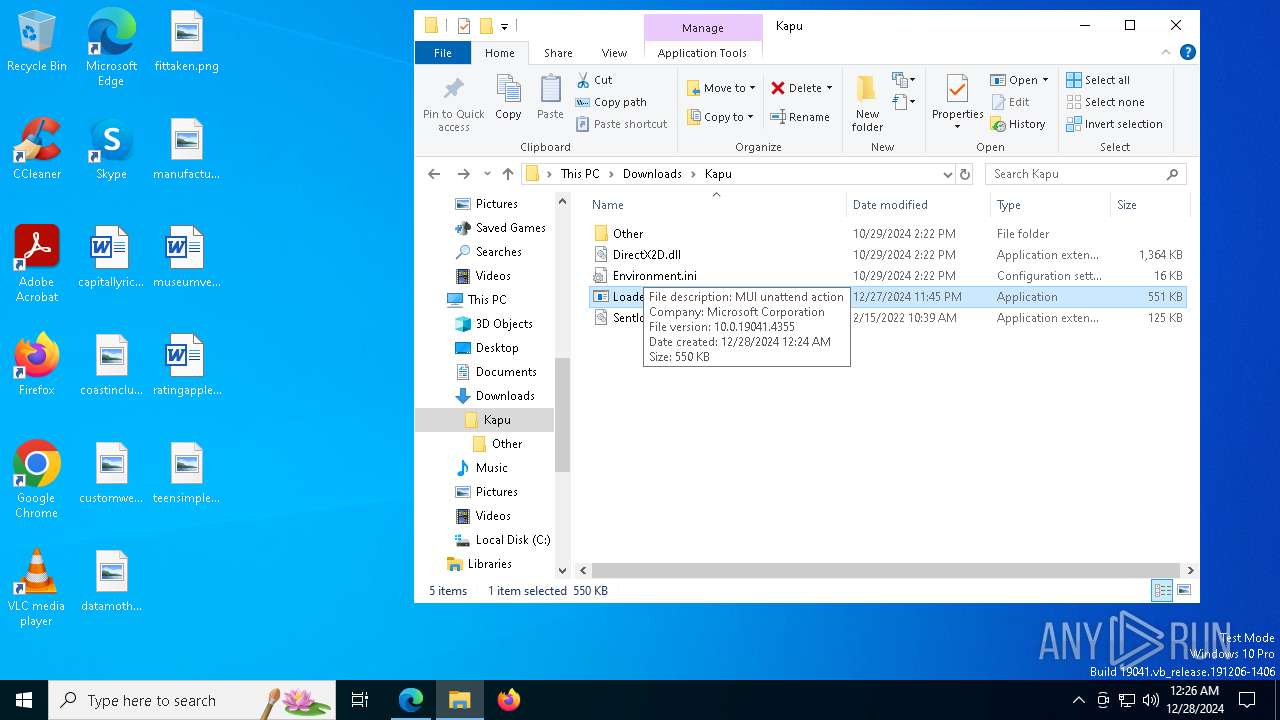
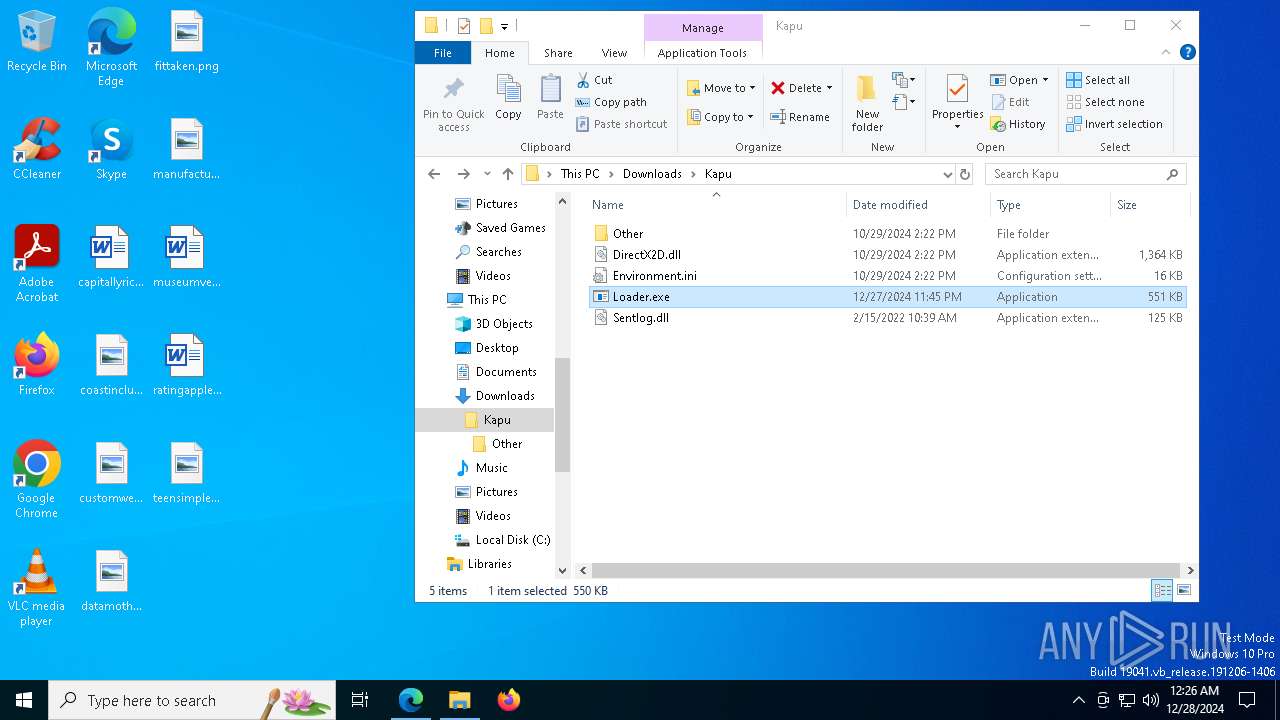
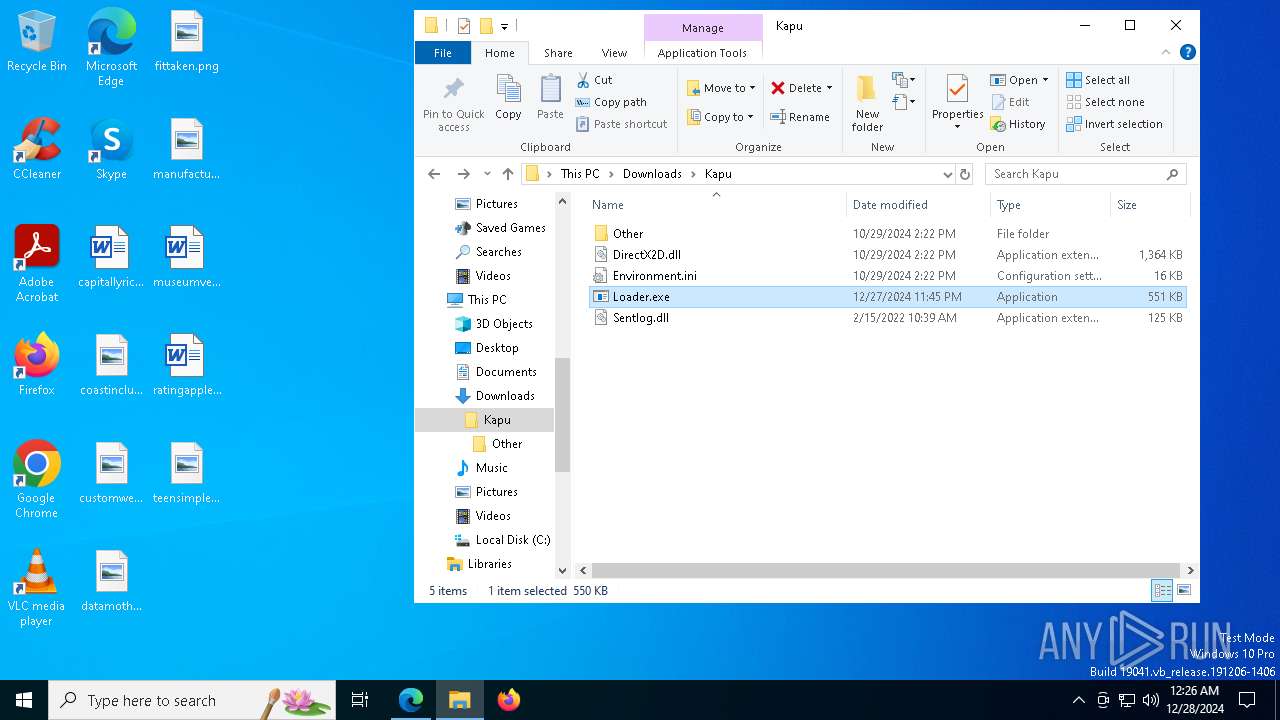
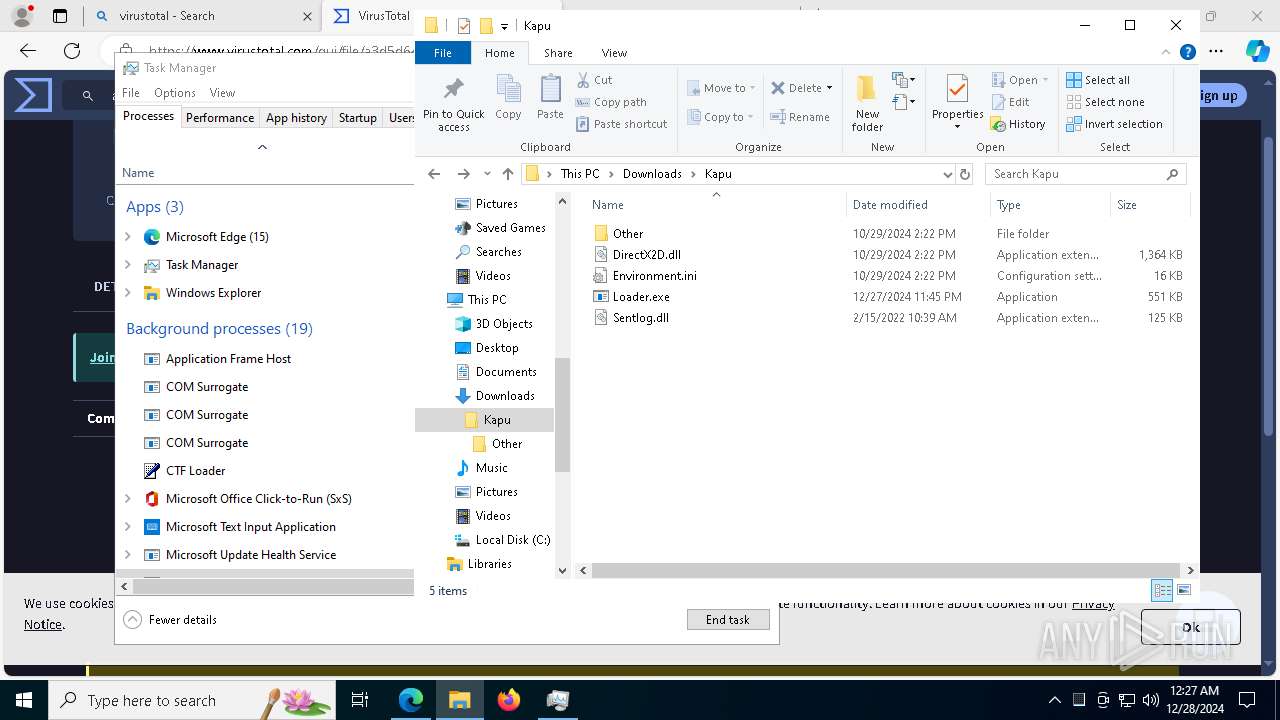
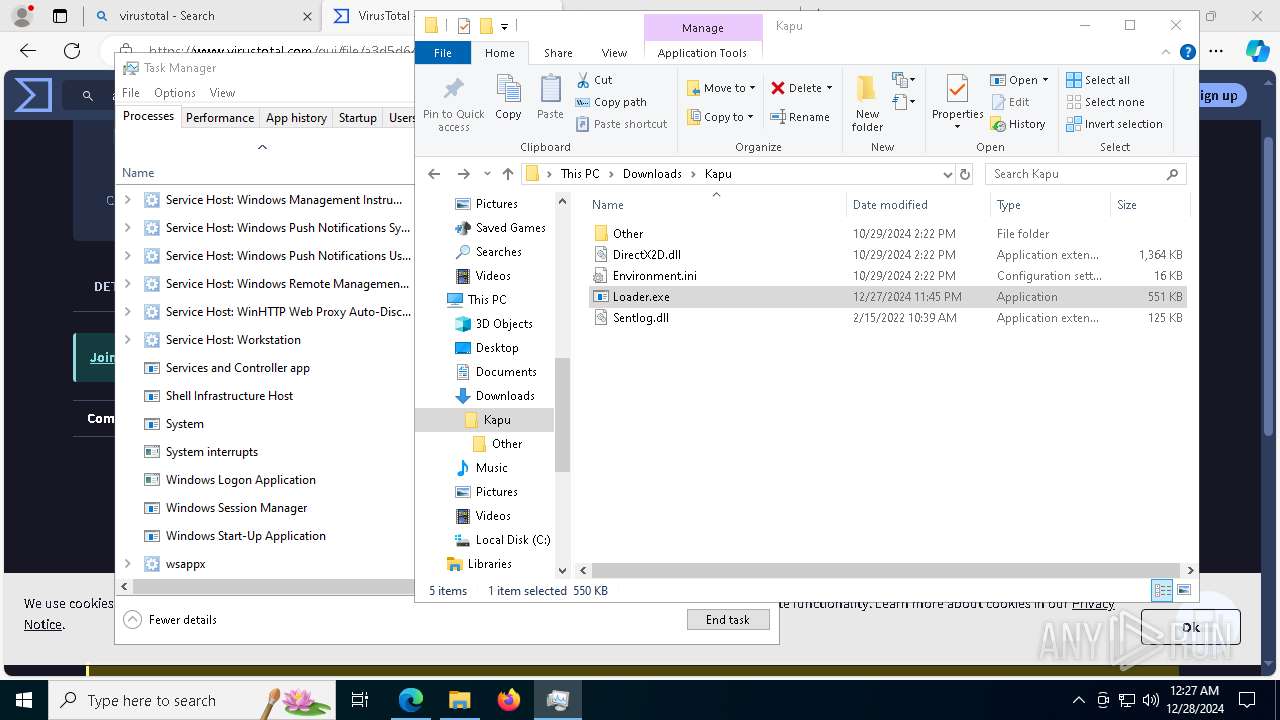
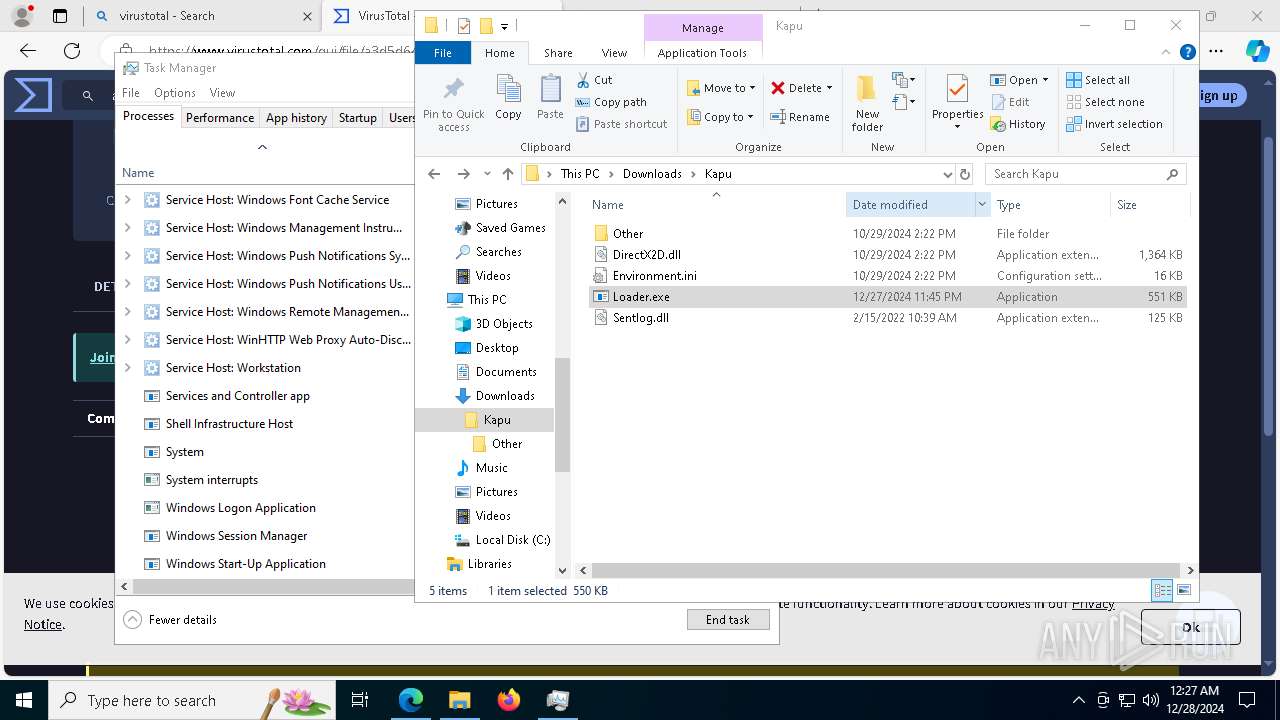
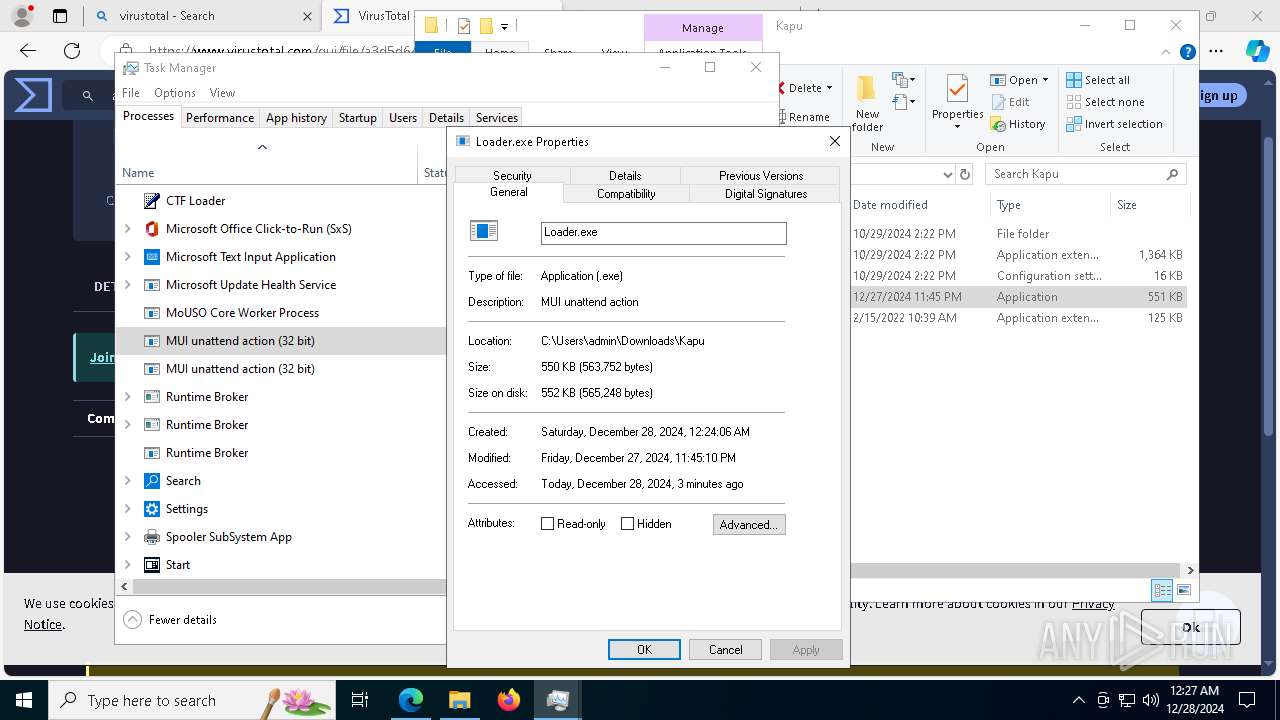
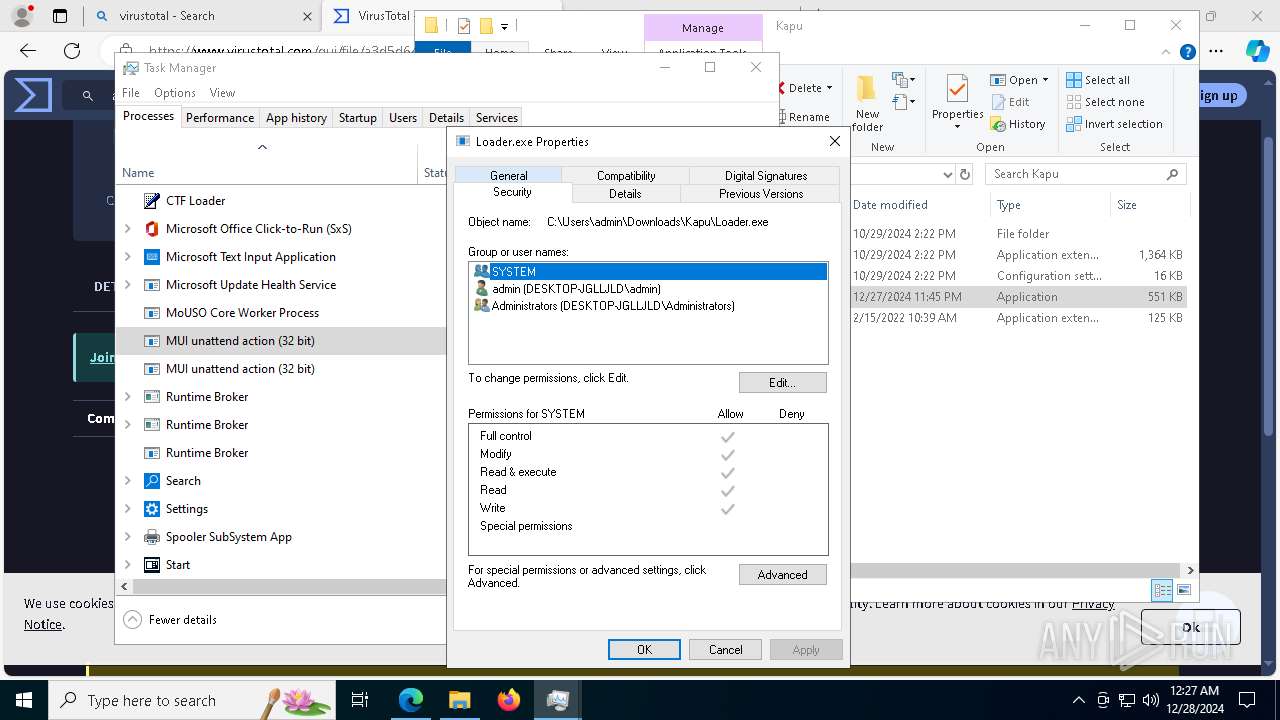
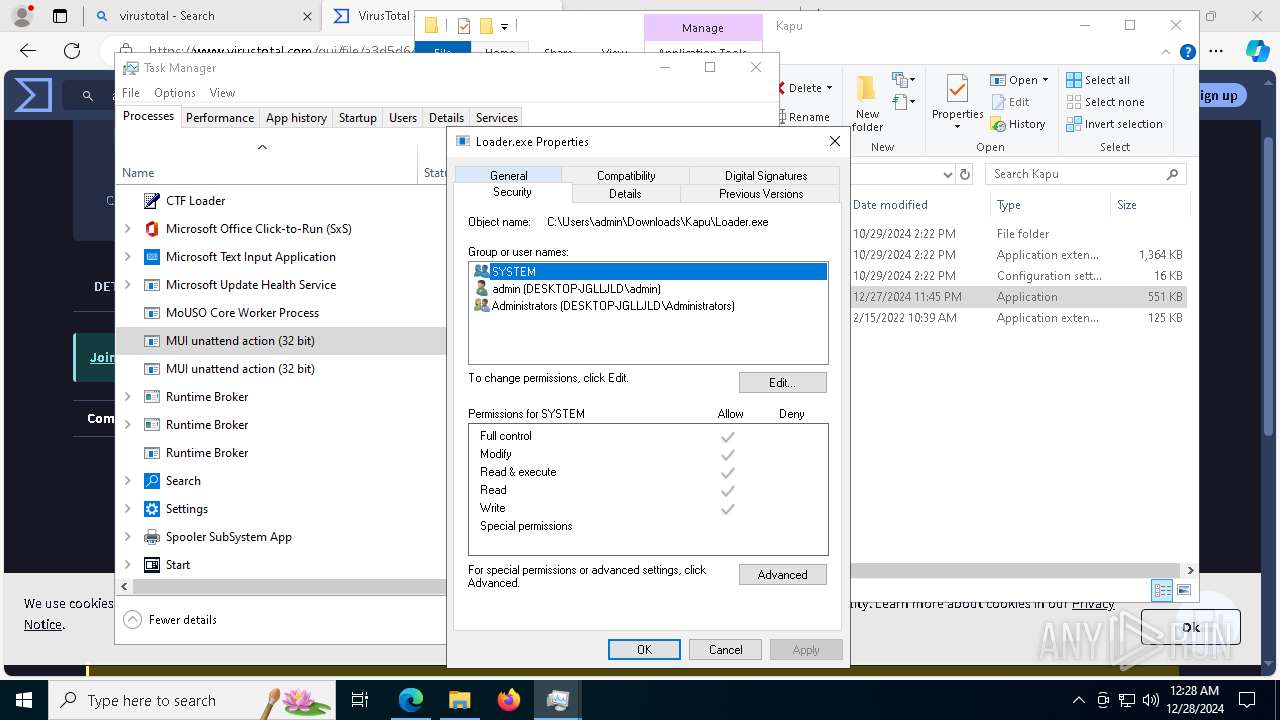
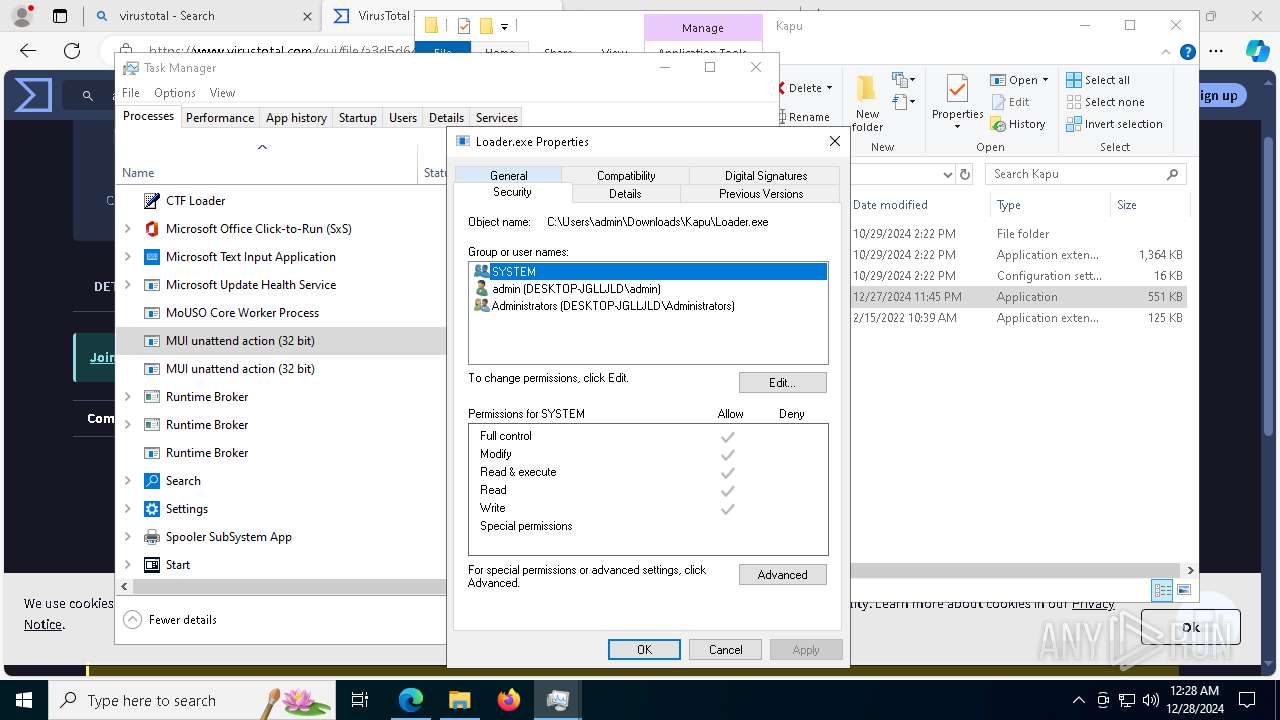
| 1612 | "C:\Users\admin\Downloads\Kapu\Loader.exe" | C:\Users\admin\Downloads\Kapu\Loader.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MUI unattend action Exit code: 0 Version: 10.0.19041.4355 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5304 --field-trial-handle=2052,i,8390452308882676060,16899787301439269855,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
16 104
Read events
15 992
Write events
97
Delete events
15
Modification events
| (PID) Process: | (5628) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5628) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5628) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5628) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5628) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000017C2B3BEBE58DB01 | |||
| (PID) Process: | (5628) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (5628) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (6856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\ext | |||
| (PID) Process: | (6856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Kapu | |||
Executable files
36
Suspicious files
1 030
Text files
213
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135ba0.TMP | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135ba0.TMP | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135ba0.TMP | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135bb0.TMP | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135bb0.TMP | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
483
DNS requests
591
Threats
39
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1356 | svchost.exe | GET | 200 | 2.21.245.134:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 206 | 217.20.57.20:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1735949367&P2=404&P3=2&P4=E5o5RNK%2bdFdJMmkI5x1OkSG5s99ZLUlvi5HZYsYU1BTdRSYM76dkWpFh2FU868GlEW%2fbF15LpeZzsMD81F%2b4Xg%3d%3d | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 206 | 217.20.57.20:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1735949367&P2=404&P3=2&P4=E5o5RNK%2bdFdJMmkI5x1OkSG5s99ZLUlvi5HZYsYU1BTdRSYM76dkWpFh2FU868GlEW%2fbF15LpeZzsMD81F%2b4Xg%3d%3d | unknown | — | — | whitelisted |
1448 | svchost.exe | HEAD | 200 | 217.20.57.20:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1735351767&P2=404&P3=2&P4=hxzdVqSXiFXVFy6L2%2fYHFTA8KQZoEk1DuZrFWZCv8NYv9XSa%2fqZ8%2bQFEdNk8vPO96LUV2qsMIrwRBEYTGgZTSw%3d%3d | unknown | — | — | whitelisted |
1448 | svchost.exe | HEAD | 200 | 217.20.57.20:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1735949367&P2=404&P3=2&P4=E5o5RNK%2bdFdJMmkI5x1OkSG5s99ZLUlvi5HZYsYU1BTdRSYM76dkWpFh2FU868GlEW%2fbF15LpeZzsMD81F%2b4Xg%3d%3d | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.21.245.134:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1356 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1448 | svchost.exe | HEAD | 200 | 217.20.57.20:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1735351766&P2=404&P3=2&P4=Zdb%2b6MddNJ0QtBDYuAfpQUGEgubb3dzICJniXtlWCM88y0QHu9rOZPWZbHz1mkKBycMFdfVMQfh52d1mrtCkqQ%3d%3d | unknown | — | — | whitelisted |
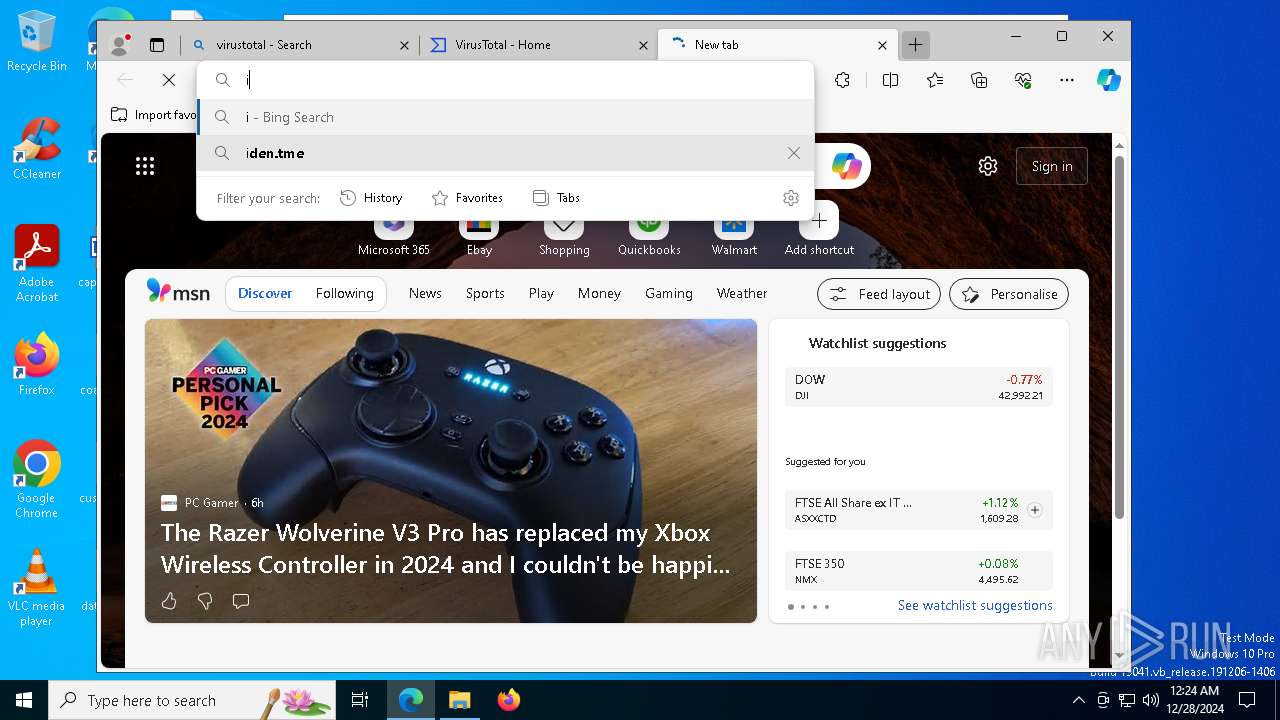
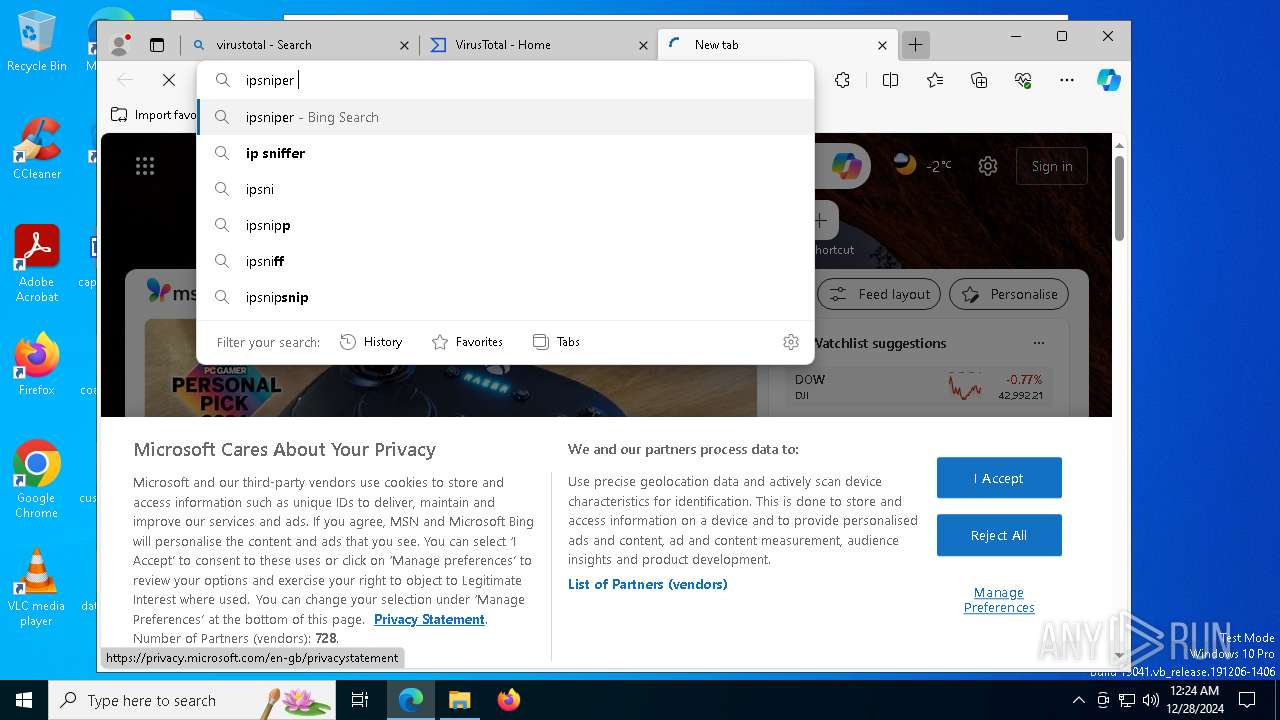
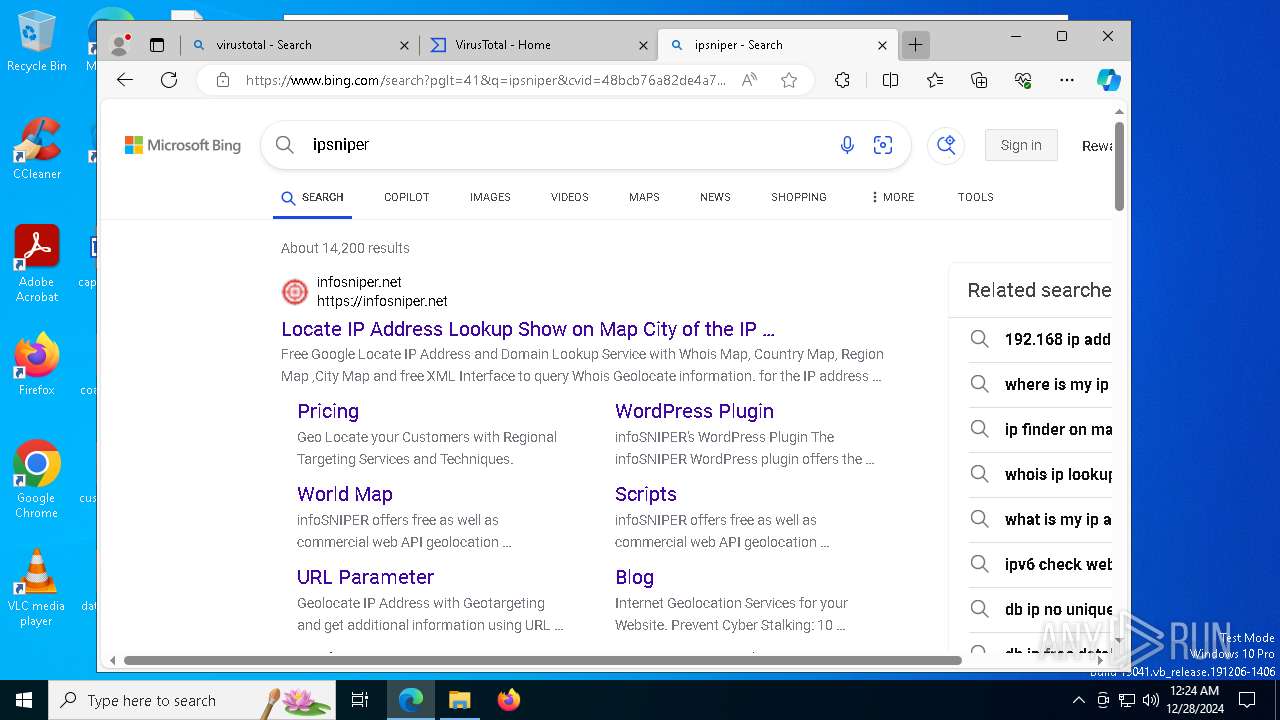
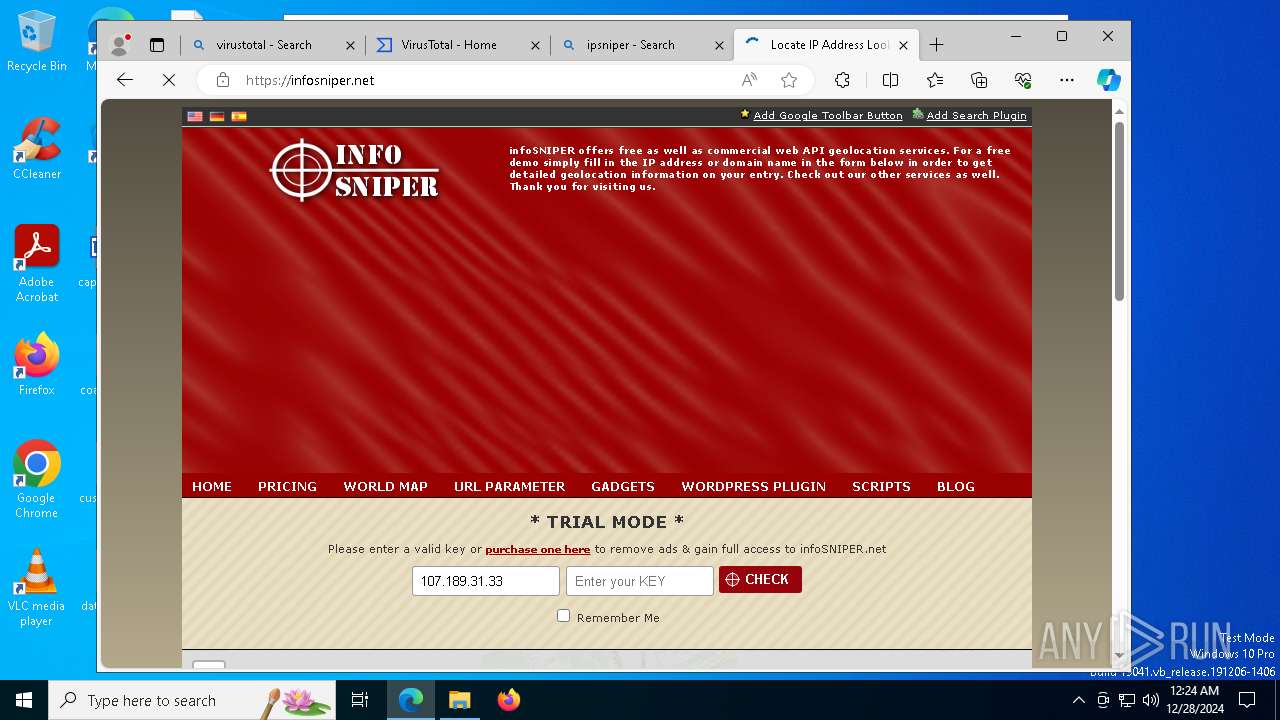
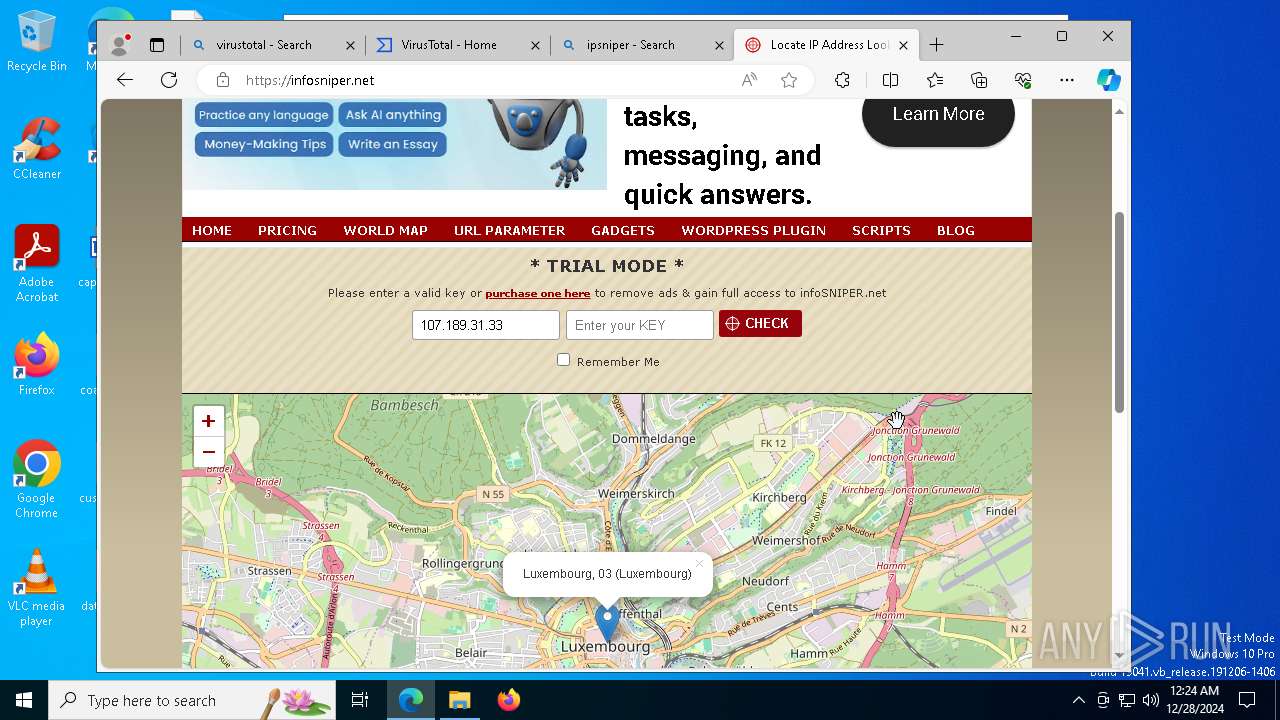
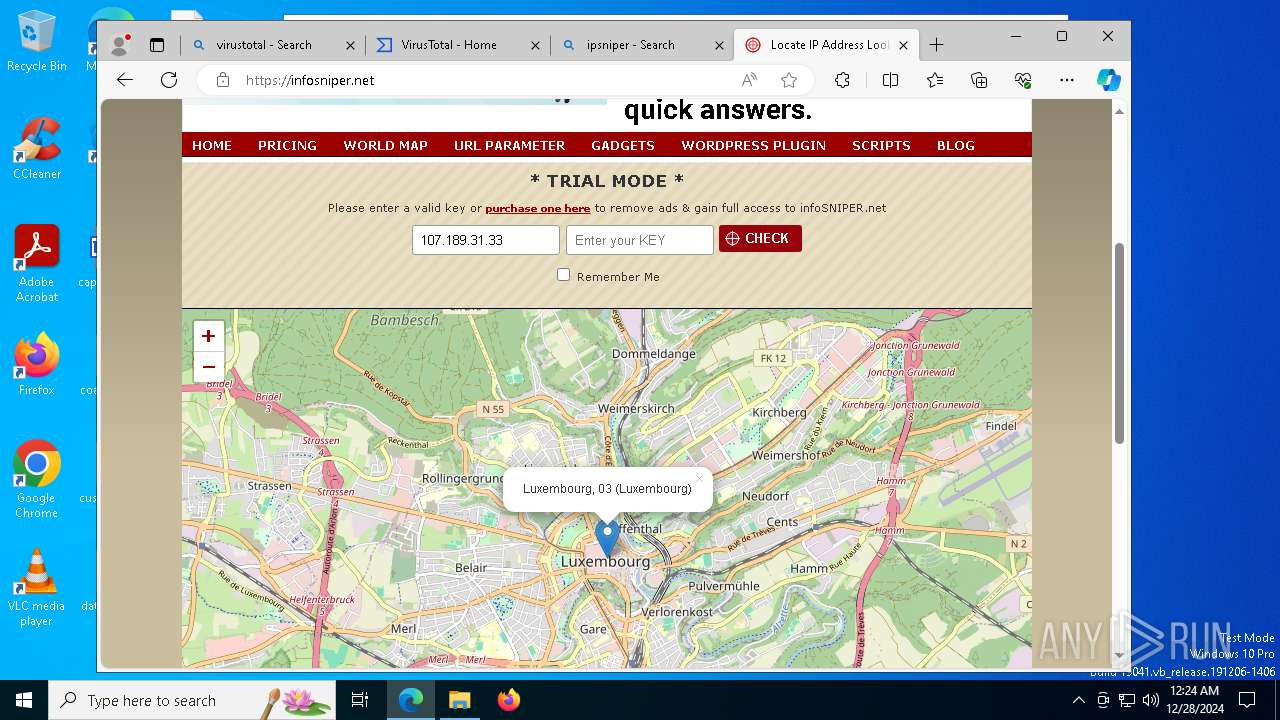
3560 | msedge.exe | GET | — | 188.114.96.3:80 | http://infosniper.net/plugin/InfoSniper.xml | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1356 | svchost.exe | 2.21.245.134:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.21.245.134:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1356 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1356 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6184 | chrome.exe | 104.17.150.117:80 | mediafire.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
mediafire.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6184 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6184 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6184 | chrome.exe | Misc activity | ET INFO Observed File Sharing Related Domain in TLS SNI (mediafire .com) |
6184 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6184 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6184 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6184 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |