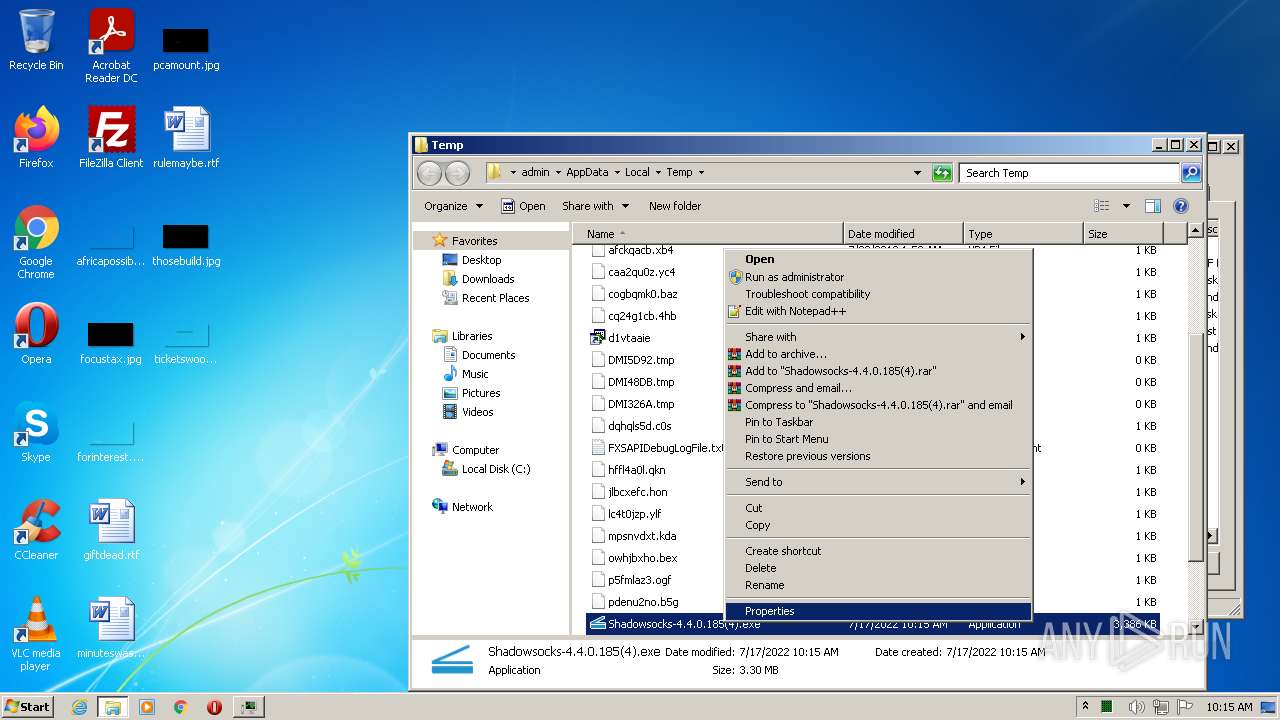
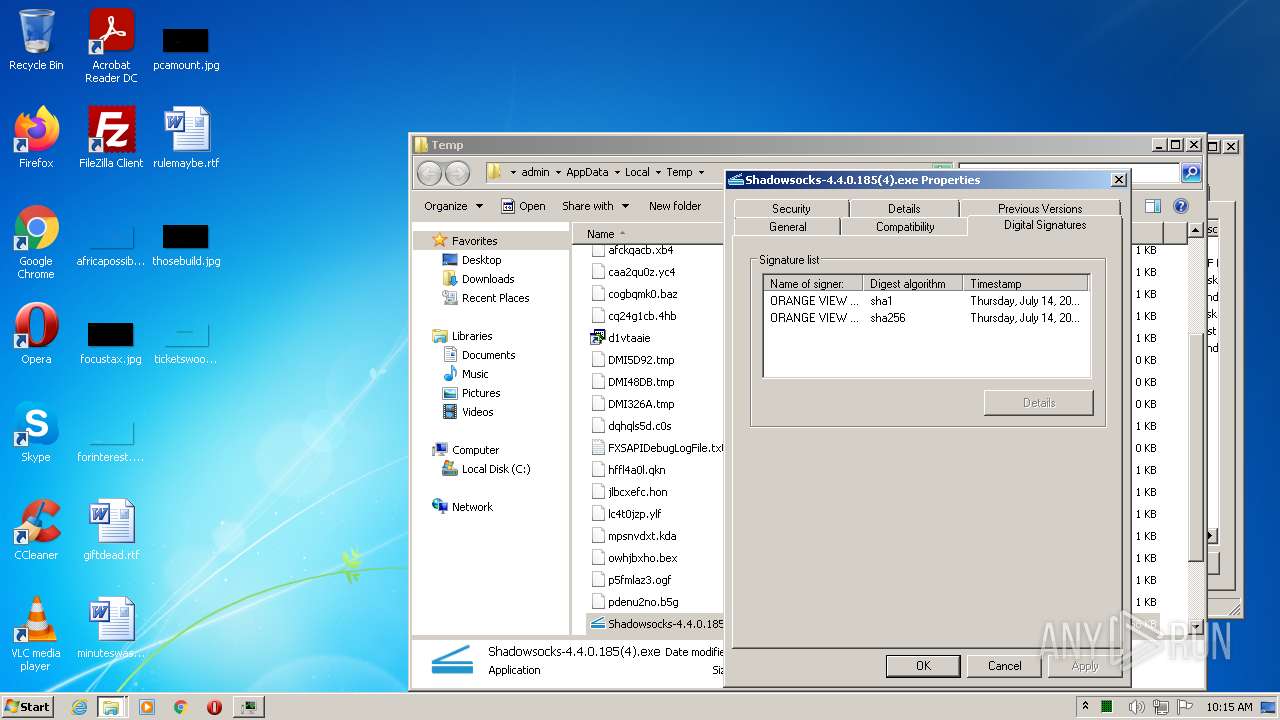
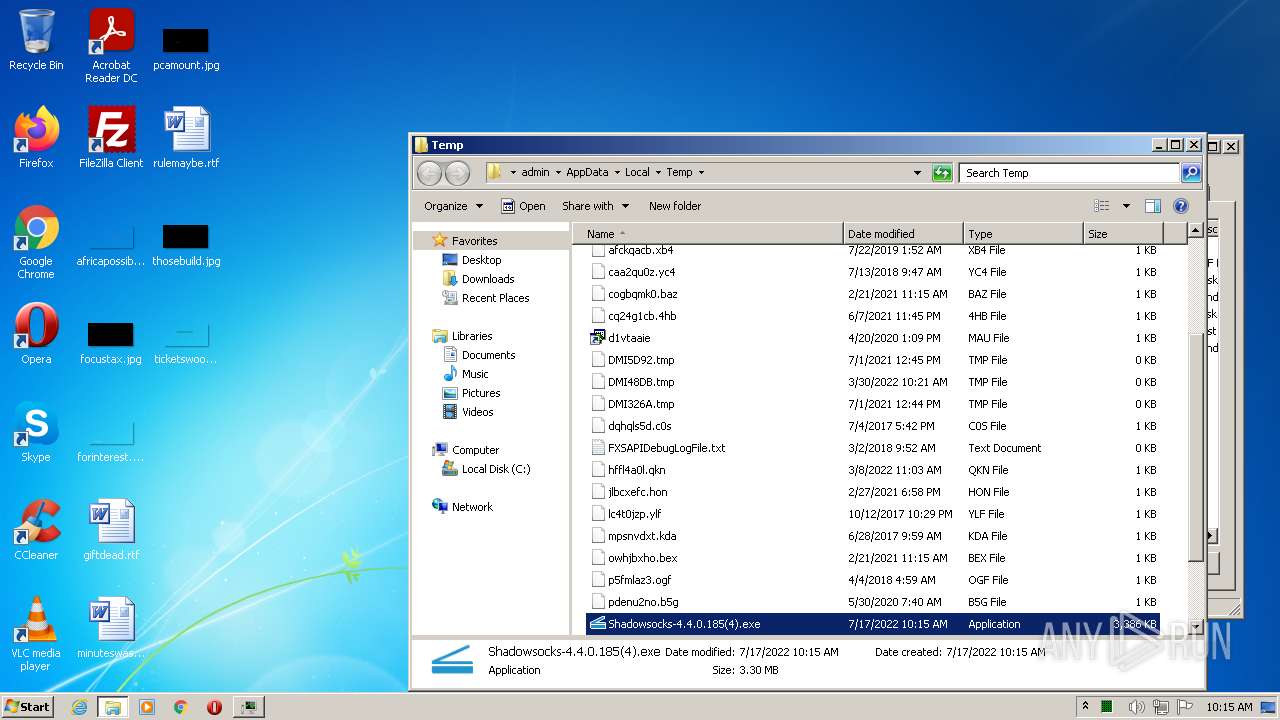
| File name: | Shadowsocks-4.4.0.185(4).exe |
| Full analysis: | https://app.any.run/tasks/5d170fbe-e86c-40e5-b4b7-20590e00f109 |
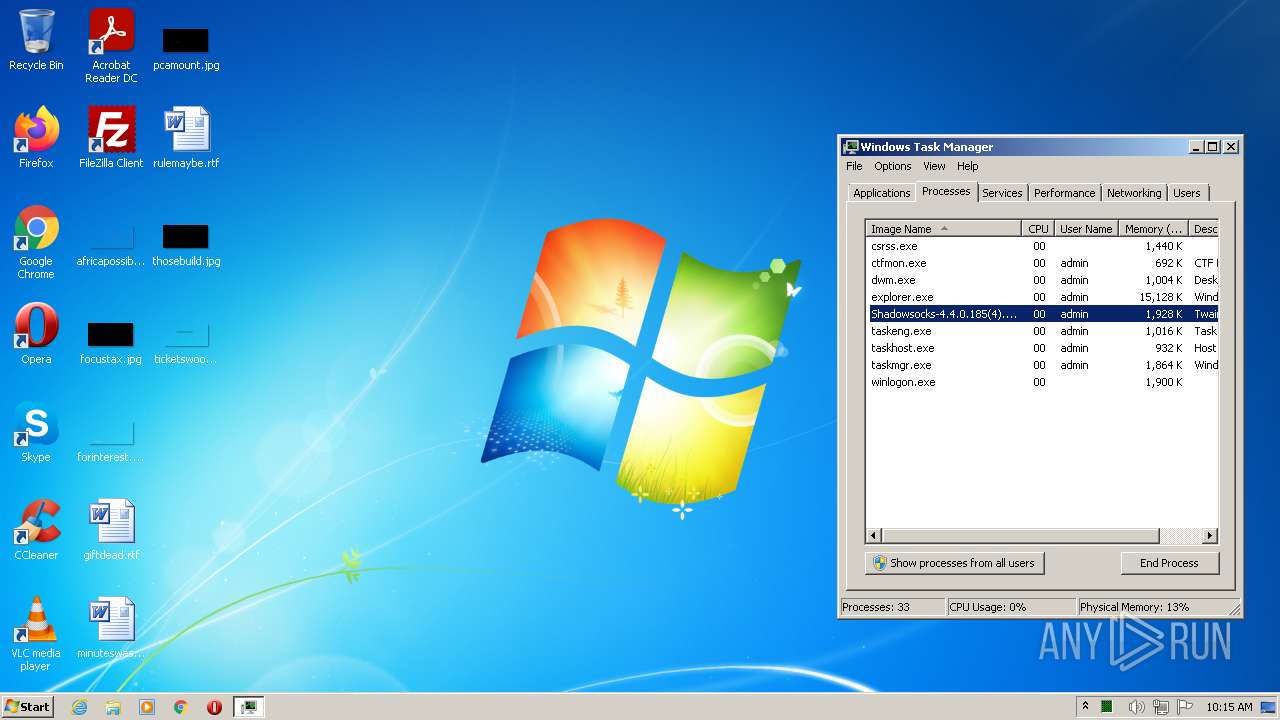
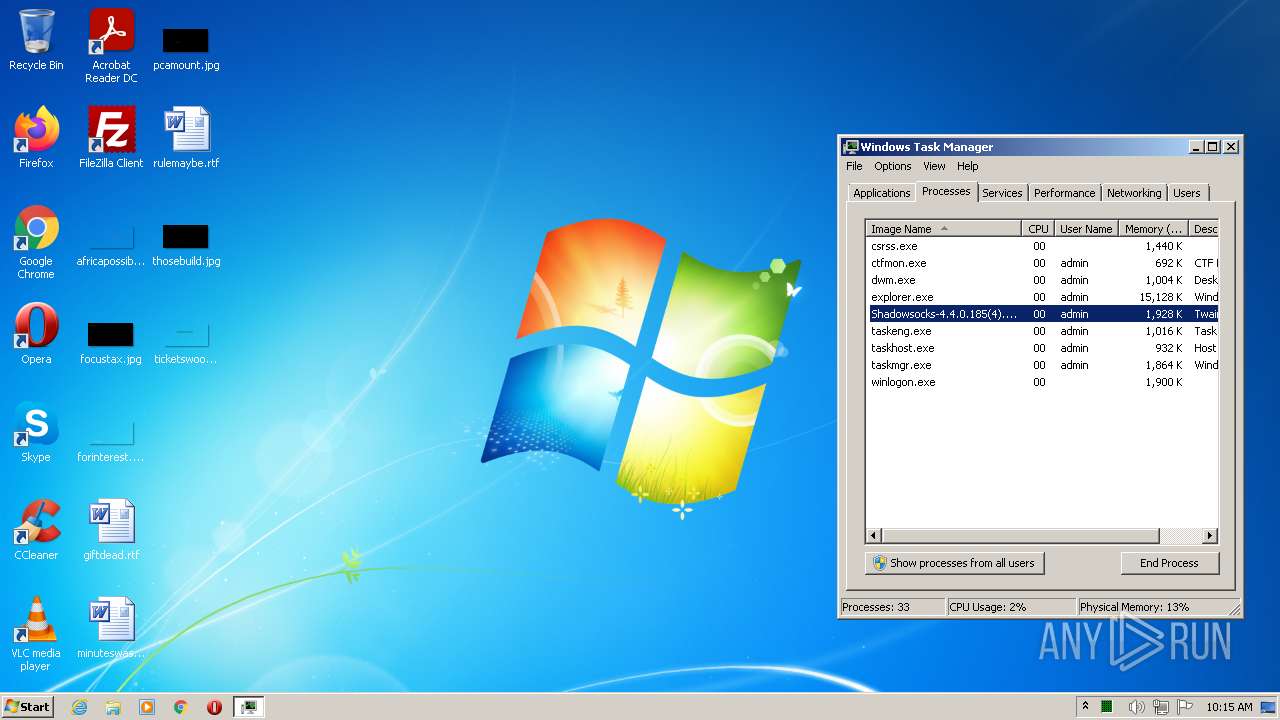
| Verdict: | Malicious activity |
| Threats: | Netwire is an advanced RAT — it is a malware that takes control of infected PCs and allows its operators to perform various actions. Unlike many RATs, this one can target every major operating system, including Windows, Linux, and MacOS. |
| Analysis date: | July 17, 2022, 09:15:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5FE11B99B677A2003DAABB664D6C0FCF |
| SHA1: | FC867BB1DA1D509E77C21E72915E64F74F600C0E |
| SHA256: | FD43F0A3AA3122D62D50085980767DBA08DDFEEF9DB3BFBB6BA31D1BCC720594 |
| SSDEEP: | 98304:EaAHG4Ah2icXUrTFrE2cInIpzd5TGFLOAkGkz9YgBjHKnP7:t9w++pzd5TGFLOPYgHKnP7 |
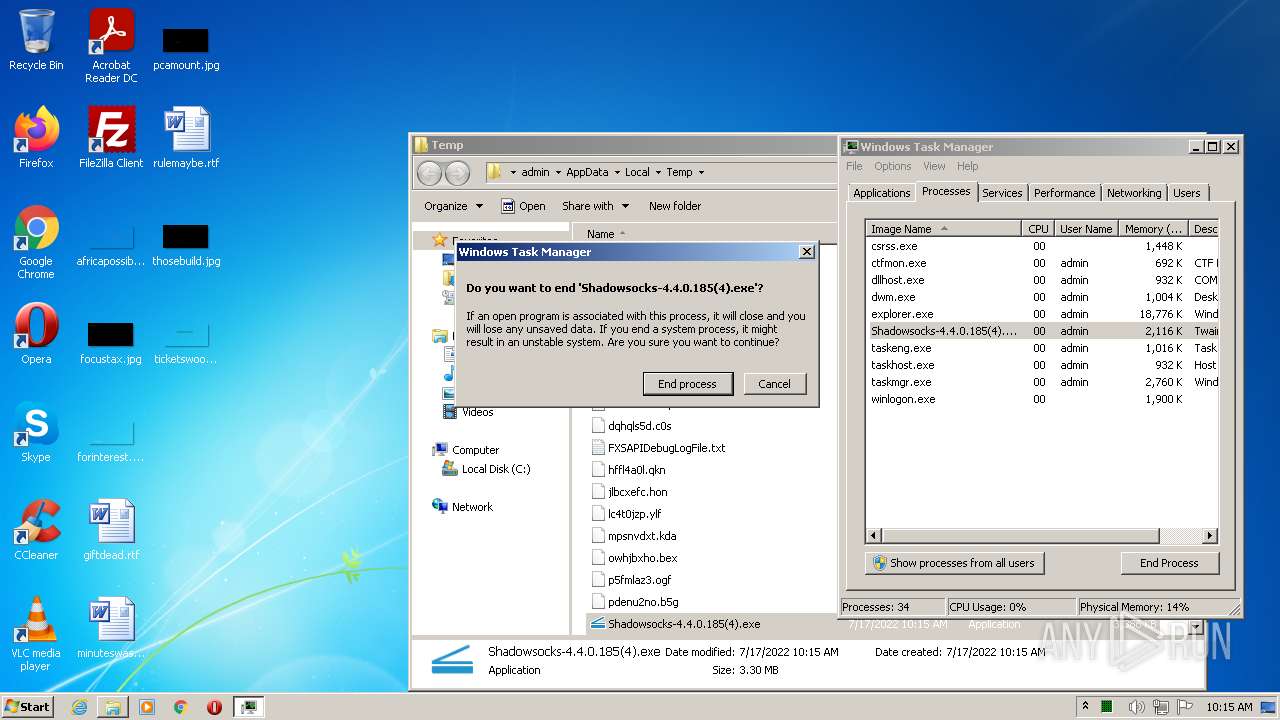
MALICIOUS
Connects to CnC server
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
NETWIRE was detected
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
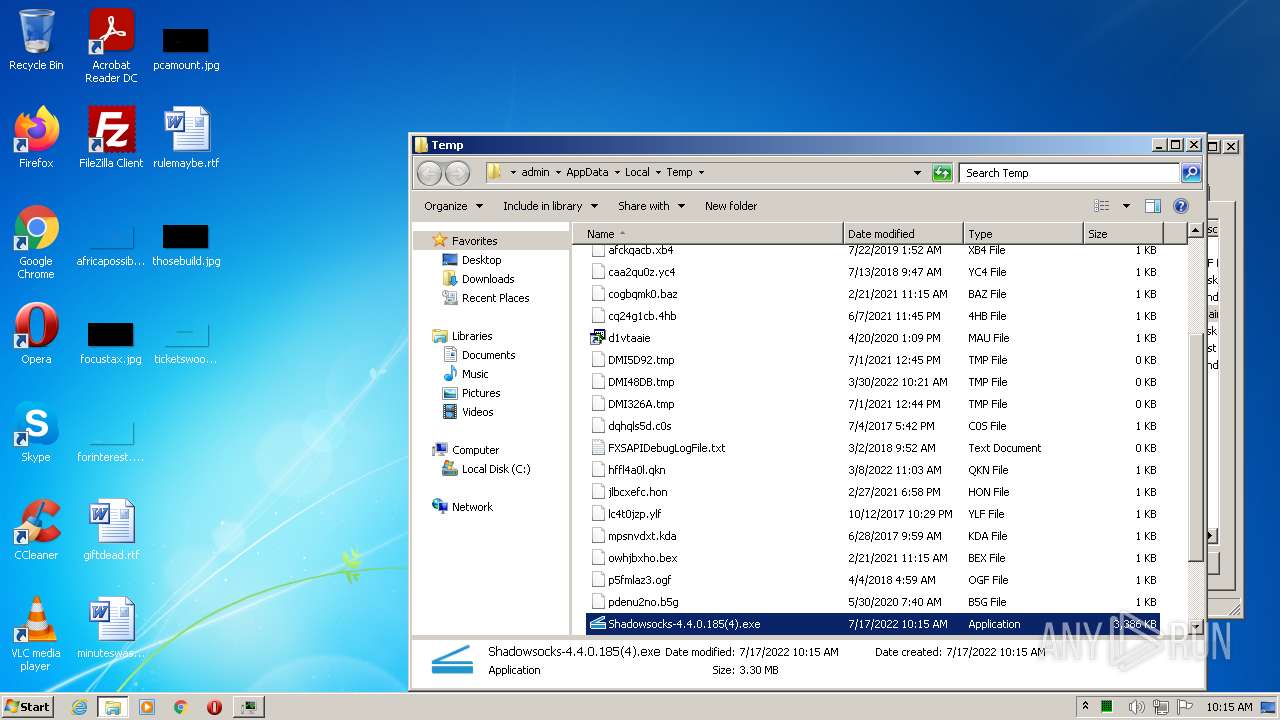
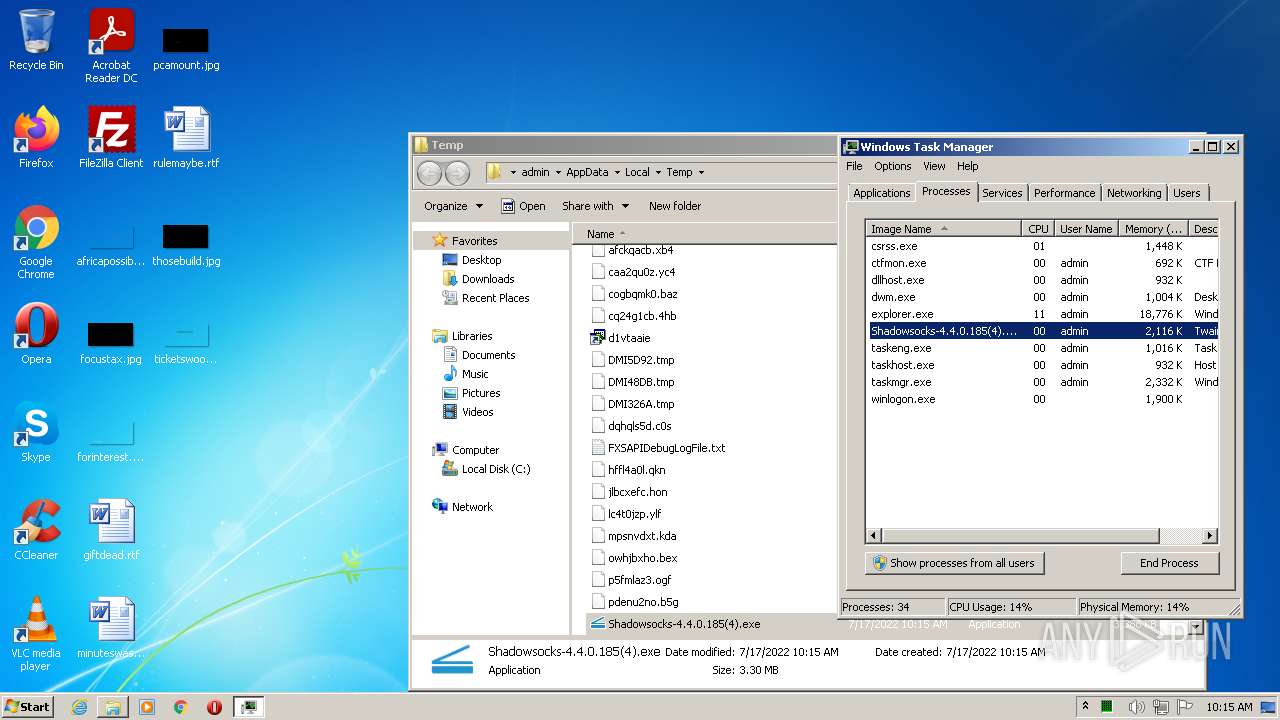
Drops executable file immediately after starts
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
NETWIRE detected by memory dumps
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
SUSPICIOUS
Checks supported languages
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
Reads the computer name
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
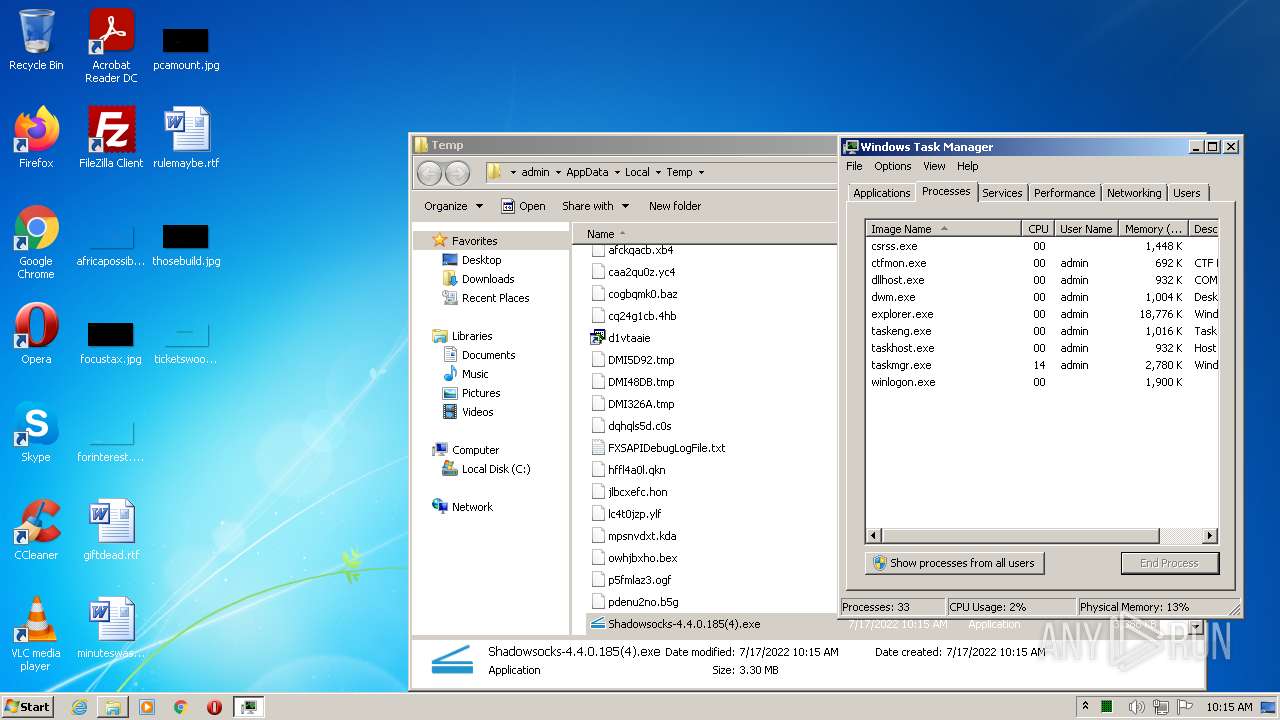
Creates files in the user directory
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
Executable content was dropped or overwritten
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
Drops a file with a compile date too recent
- Shadowsocks-4.4.0.185(4).exe (PID: 3024)
INFO
Checks supported languages
- taskmgr.exe (PID: 3612)
Reads the computer name
- taskmgr.exe (PID: 3612)
Manual execution by user
- taskmgr.exe (PID: 3612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NetWire
(PID) Process(3024) Shadowsocks-4.4.0.185(4).exe
C2 (1)s2awscloudupdates.com:8081
HostHostId-ysW6Yg
Credentials
Passwordhappy666
Options
Mutex-
Install_path-
Startup_name
ActiveXfalse
ProxyDirect_connection
Copy_executablefalse
Delete_originalfalse
Lock_executablefalse
Registry_autorunfalse
Use_a_mutexfalse
Offline_keyloggertrue
Sleep(s)75
Keylogger_directoryC:\Users\admin\AppData\Roaming\Logs\
Keys
RC4_keybecfd056e9fb173e7f3f3679383fbd5c
Strings (111)GetProcessImageFileNameA
CONNECT %s:%d HTTP/1.0
Local Disk
%s\%s.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Run\
SOFTWARE\Microsoft\Active Setup\Installed Components\%s
StubPath
WinHttpOpen
WinHttpGetIEProxyConfigForCurrentUser
SOFTWARE\Microsoft\Windows\CurrentVersion\Run\
SOFTWARE\Microsoft\Active Setup\Installed Components
[Backspace]
[Enter]
[Tab]
[Arrow Left]
[Arrow Up]
[Arrow Right]
[Arrow Down]
[Home]
[Page Up]
[Page Down]
[End]
[Break]
[Delete]
[Insert]
[Print Screen]
[Scroll Lock]
[Caps Lock]
[Esc]
[Ctrl+%c]
Secur32.dll
LsaGetLogonSessionData
Email
POP3 User
POP3 Server
POP3 Password
IMAP User
IMAP Server
IMAP Password
HTTP User
HTTP Server
HTTP Password
SMTP User
SMTP Server
SMTP Password
EAS User
EAS Server URL
EAS Password
Email
POP3 User
POP3 Server
POP3 Password
IMAP User
IMAP Server
IMAP Password
HTTP User
HTTP Server
HTTP Password
SMTP User
SMTP Server
SMTP Password
EAS User
EAS Server URL
EAS Password
sqlite3_open
sqlite3_close
sqlite3_step
sqlite3_column_text
index.dat
VaultOpenVault
%s\Mozilla\SeaMonkey\profiles.ini
%s\Thunderbird\profiles.ini
%s\Mozilla\Firefox\profiles.ini
%s\Mozilla\Firefox\%s
%s\signons.sqlite
%s\logins.json
PK11_GetInternalKeySlot
PK11_Authenticate
PL_Base64Decode
SECITEM_ZfreeItem
PK11SDR_Decrypt
PK11_FreeSlot
NSS_Shutdown
sqlite3_open
sqlite3_close
sqlite3_prepare_v2
sqlite3_step
sqlite3_column_text
select * from moz_logins
select * from moz_logins
hostname
hostname
%s\.purple\accounts.xml
<protocol>
<name>
<password>
SOFTWARE\Mozilla\%s\
CurrentVersion
SOFTWARE\Mozilla\%s\%s\Main
Install Directory
mozutils.dll
mozglue.dll
mozsqlite3.dll
GetModuleFileNameExA
GetModuleFileNameExA
%s\system32\cmd.exe
GetNativeSystemInfo
kernel32.dll
GetNativeSystemInfo
kernel32.dll
HARDWARE\DESCRIPTION\System\CentralProcessor\0
TRiD
| .exe | | | Win64 Executable (generic) (17.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
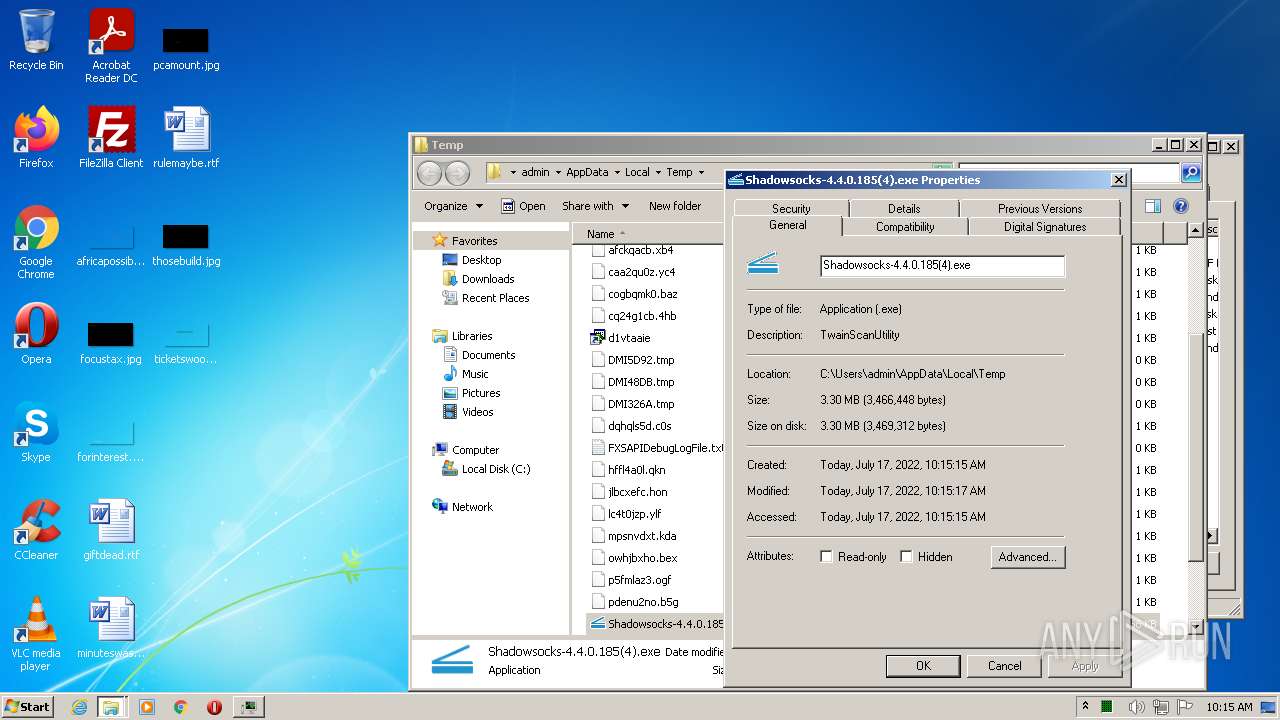
| ProductVersion: | 39.0.0.1 |
|---|---|
| ProductName: | HP Scan Twain Utility |
| OriginalFileName: | TwainScanUtility.exe |
| LegalCopyright: | © Copyright 2015 HP Development Company,L.P. |
| InternalName: | TwainScanUtility.exe |
| FileVersion: | 39.0.0.1 |
| FileDescription: | TwainScanUtility |
| CompanyName: | HP Inc. |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x131fbc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2040832 |
| CodeSize: | 1435136 |
| LinkerVersion: | 12 |
| PEType: | PE32 |
| TimeStamp: | 2017:04:18 08:10:06+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Apr-2017 06:10:06 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | HP Inc. |
| FileDescription: | TwainScanUtility |
| FileVersion: | 39.0.0.1 |
| InternalName: | TwainScanUtility.exe |
| LegalCopyright: | © Copyright 2015 HP Development Company,L.P. |
| OriginalFilename: | TwainScanUtility.exe |
| ProductName: | HP Scan Twain Utility |
| ProductVersion: | 39.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Apr-2017 06:10:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0015E480 | 0x0015E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.53355 |
.rdata | 0x00160000 | 0x00054444 | 0x00054600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99752 |
.data | 0x001B5000 | 0x0000E860 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.74856 |
.rsrc | 0x001C4000 | 0x00170A50 | 0x00170C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.37164 |
.reloc | 0x00335000 | 0x0001E668 | 0x0001E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47089 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.12107 | 796 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.31005 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 2.90649 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.01944 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 2.63275 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 2.27981 | 67624 | UNKNOWN | English - United States | RT_ICON |
7 | 2.16337 | 78 | UNKNOWN | English - United States | RT_STRING |
8 | 3.02695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.74274 | 180 | UNKNOWN | English - United States | RT_CURSOR |
10 | 2.34038 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
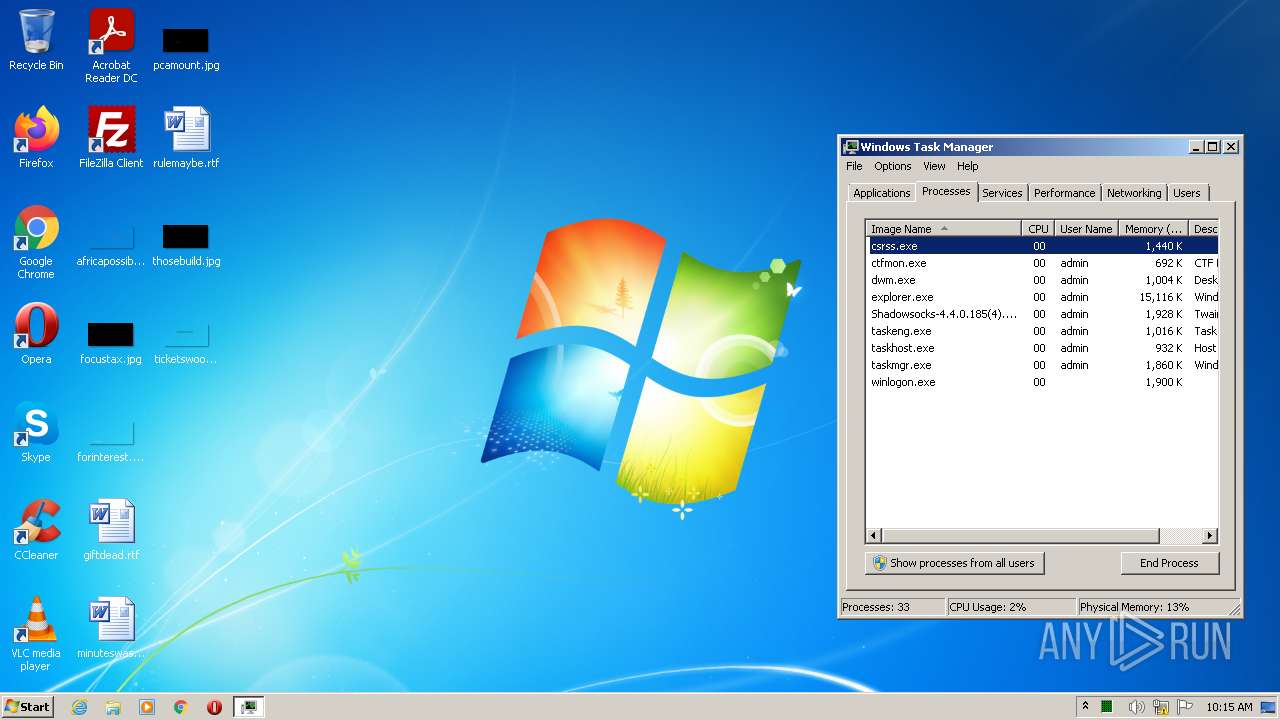
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
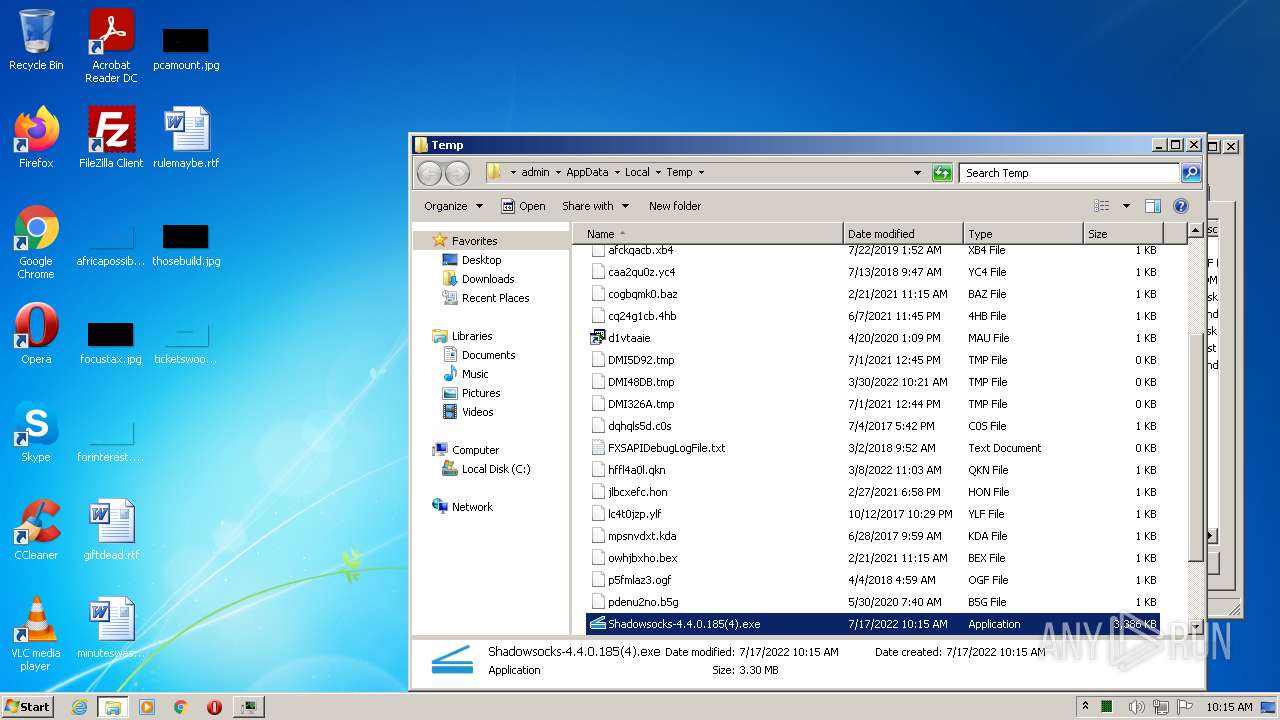
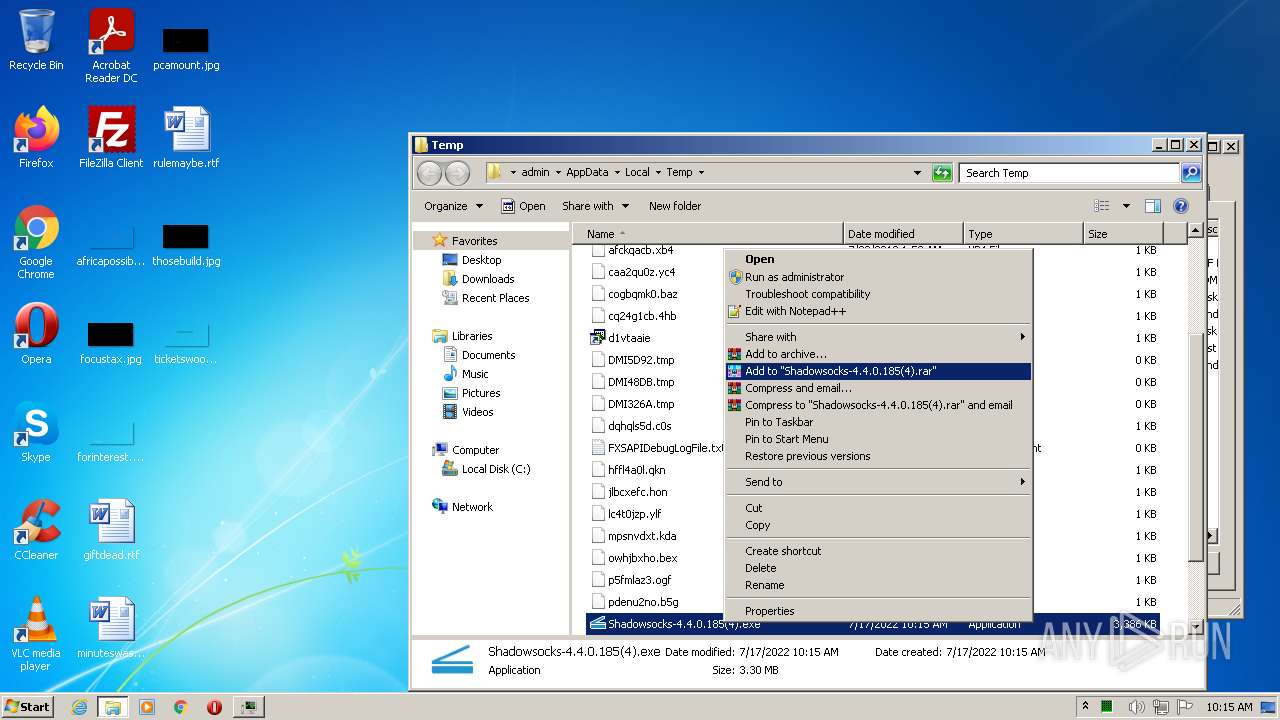
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3024 | "C:\Users\admin\AppData\Local\Temp\Shadowsocks-4.4.0.185(4).exe" | C:\Users\admin\AppData\Local\Temp\Shadowsocks-4.4.0.185(4).exe | Explorer.EXE | ||||||||||||
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: TwainScanUtility Exit code: 1 Version: 39.0.0.1 Modules
NetWire(PID) Process(3024) Shadowsocks-4.4.0.185(4).exe C2 (1)s2awscloudupdates.com:8081 HostHostId-ysW6Yg Credentials Passwordhappy666 Options Mutex- Install_path- Startup_name ActiveXfalse ProxyDirect_connection Copy_executablefalse Delete_originalfalse Lock_executablefalse Registry_autorunfalse Use_a_mutexfalse Offline_keyloggertrue Sleep(s)75 Keylogger_directoryC:\Users\admin\AppData\Roaming\Logs\ Keys RC4_keybecfd056e9fb173e7f3f3679383fbd5c Strings (111)GetProcessImageFileNameA CONNECT %s:%d HTTP/1.0 Local Disk %s\%s.exe SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ SOFTWARE\Microsoft\Active Setup\Installed Components\%s StubPath WinHttpOpen WinHttpGetIEProxyConfigForCurrentUser SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ SOFTWARE\Microsoft\Active Setup\Installed Components [Backspace] [Enter] [Tab] [Arrow Left] [Arrow Up] [Arrow Right] [Arrow Down] [Home] [Page Up] [Page Down] [End] [Break] [Delete] [Insert] [Print Screen] [Scroll Lock] [Caps Lock] [Esc] [Ctrl+%c] Secur32.dll LsaGetLogonSessionData Email POP3 User POP3 Server POP3 Password IMAP User IMAP Server IMAP Password HTTP User HTTP Server HTTP Password SMTP User SMTP Server SMTP Password EAS User EAS Server URL EAS Password Email POP3 User POP3 Server POP3 Password IMAP User IMAP Server IMAP Password HTTP User HTTP Server HTTP Password SMTP User SMTP Server SMTP Password EAS User EAS Server URL EAS Password sqlite3_open sqlite3_close sqlite3_step sqlite3_column_text index.dat VaultOpenVault %s\Mozilla\SeaMonkey\profiles.ini %s\Thunderbird\profiles.ini %s\Mozilla\Firefox\profiles.ini %s\Mozilla\Firefox\%s %s\signons.sqlite %s\logins.json PK11_GetInternalKeySlot PK11_Authenticate PL_Base64Decode SECITEM_ZfreeItem PK11SDR_Decrypt PK11_FreeSlot NSS_Shutdown sqlite3_open sqlite3_close sqlite3_prepare_v2 sqlite3_step sqlite3_column_text select * from moz_logins select * from moz_logins hostname hostname %s\.purple\accounts.xml <protocol> <name> <password> SOFTWARE\Mozilla\%s\ CurrentVersion SOFTWARE\Mozilla\%s\%s\Main Install Directory mozutils.dll mozglue.dll mozsqlite3.dll GetModuleFileNameExA GetModuleFileNameExA %s\system32\cmd.exe GetNativeSystemInfo kernel32.dll GetNativeSystemInfo kernel32.dll HARDWARE\DESCRIPTION\System\CentralProcessor\0 | |||||||||||||||
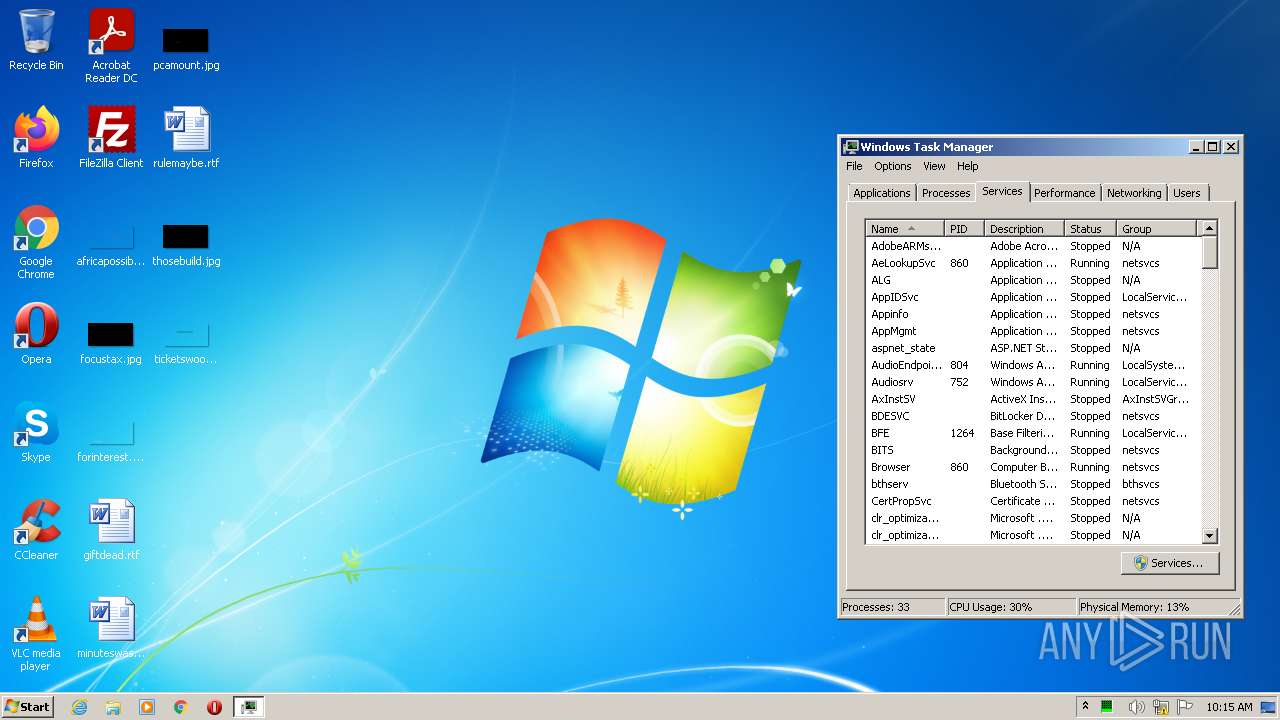
| 3612 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 470
Read events
1 470
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | Shadowsocks-4.4.0.185(4).exe | C:\Users\admin\AppData\Roaming\Sqlite3\sqlite3.dll | executable | |
MD5:1023DF7ABD2D9B7F0BDC77024C978F0B | SHA256:D7067D18AFF17BBD5013A708F02E5D87BEB20AF19F2381986952A119CE5CF420 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | Shadowsocks-4.4.0.185(4).exe | 198.44.237.131:8081 | s2awscloudupdates.com | HOSTSPACE NETWORKS LLC | US | malicious |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
s2awscloudupdates.com |
| malicious |
Threats
1 ETPRO signatures available at the full report