| download: | index.html |
| Full analysis: | https://app.any.run/tasks/20a9894e-6e76-459f-af79-a69e195933d5 |
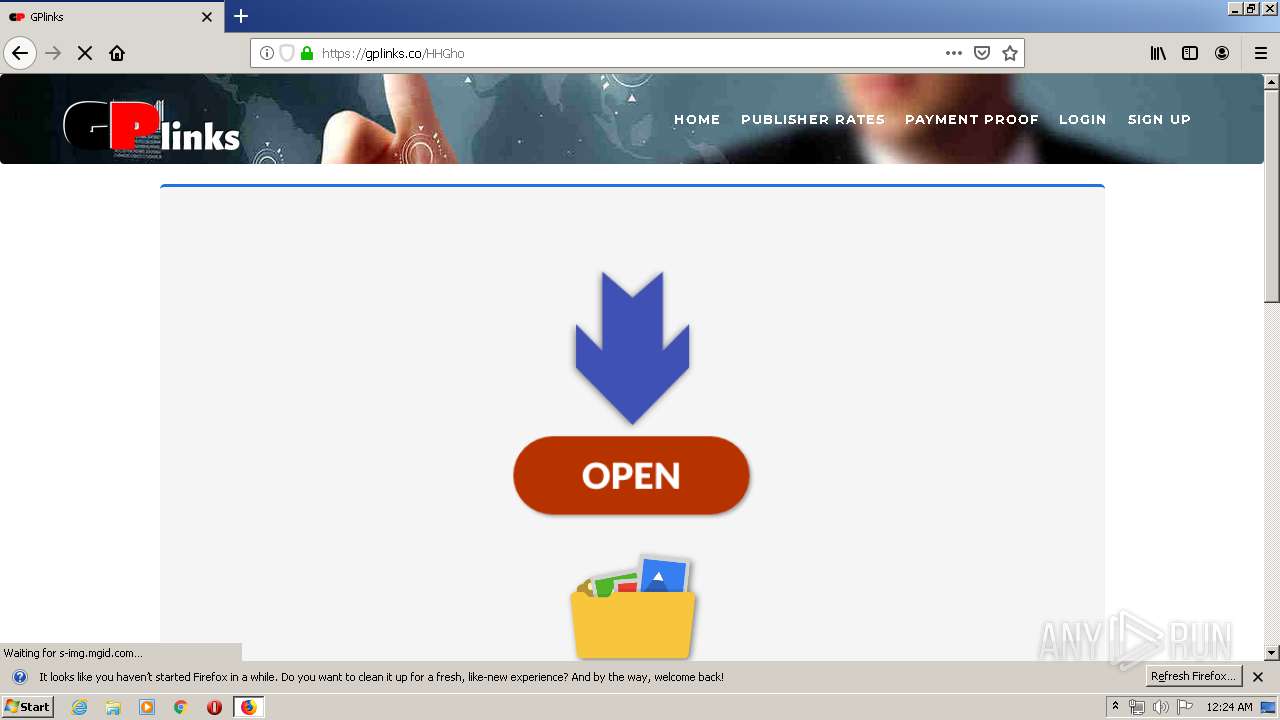
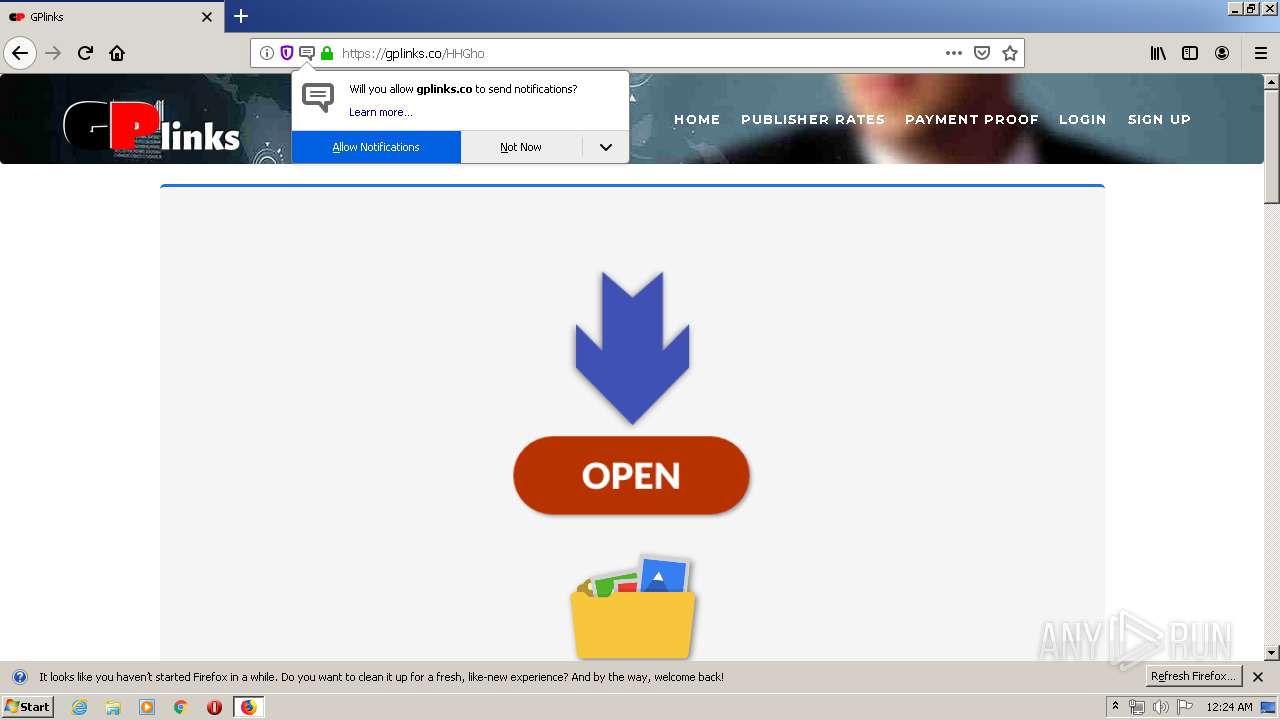
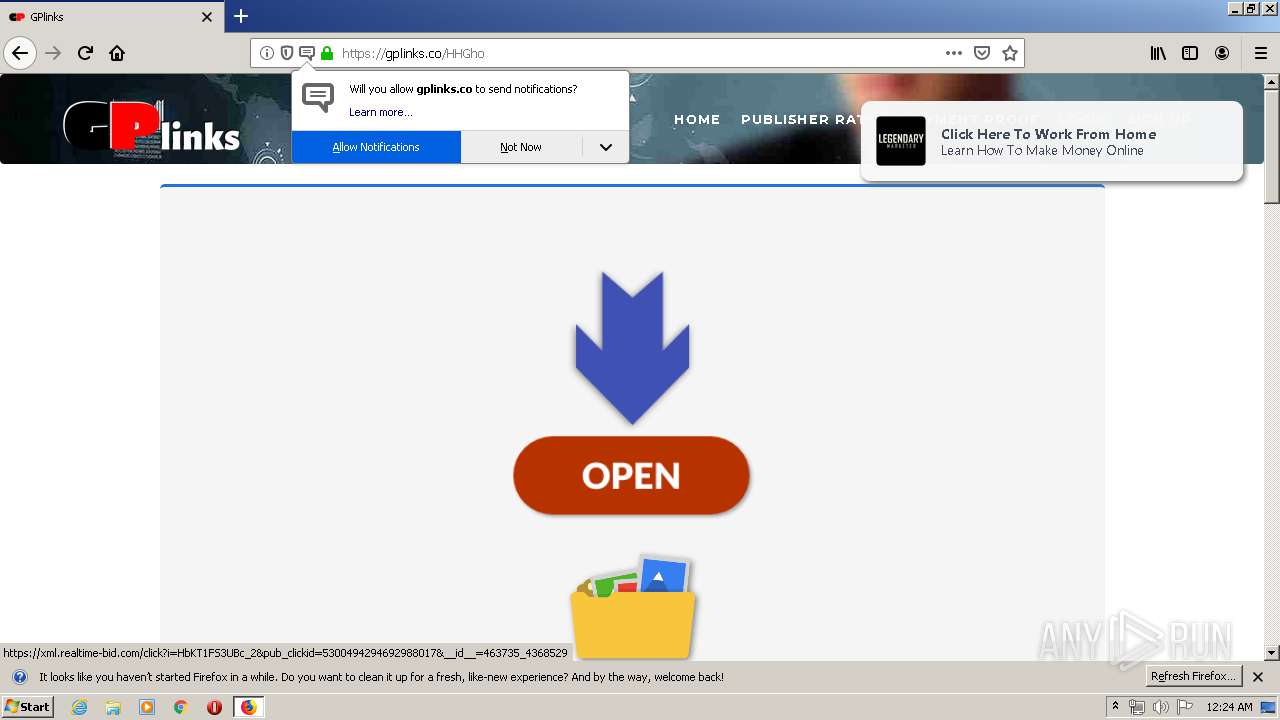
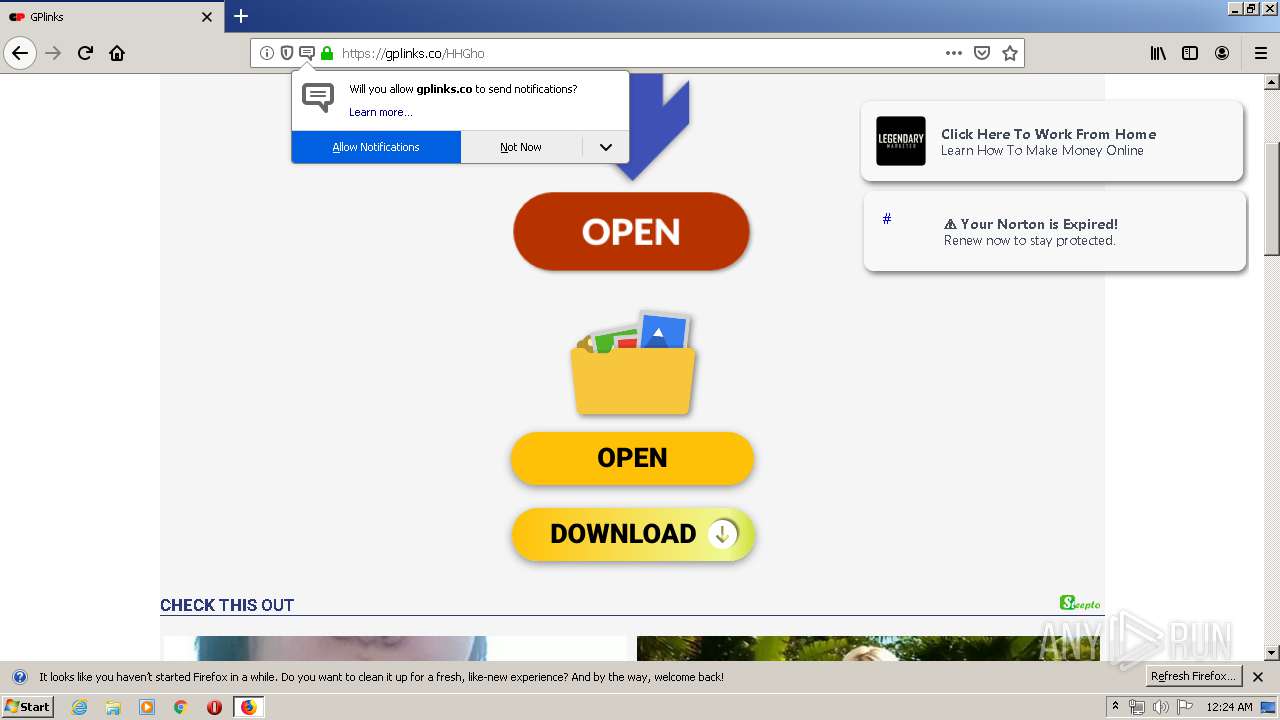
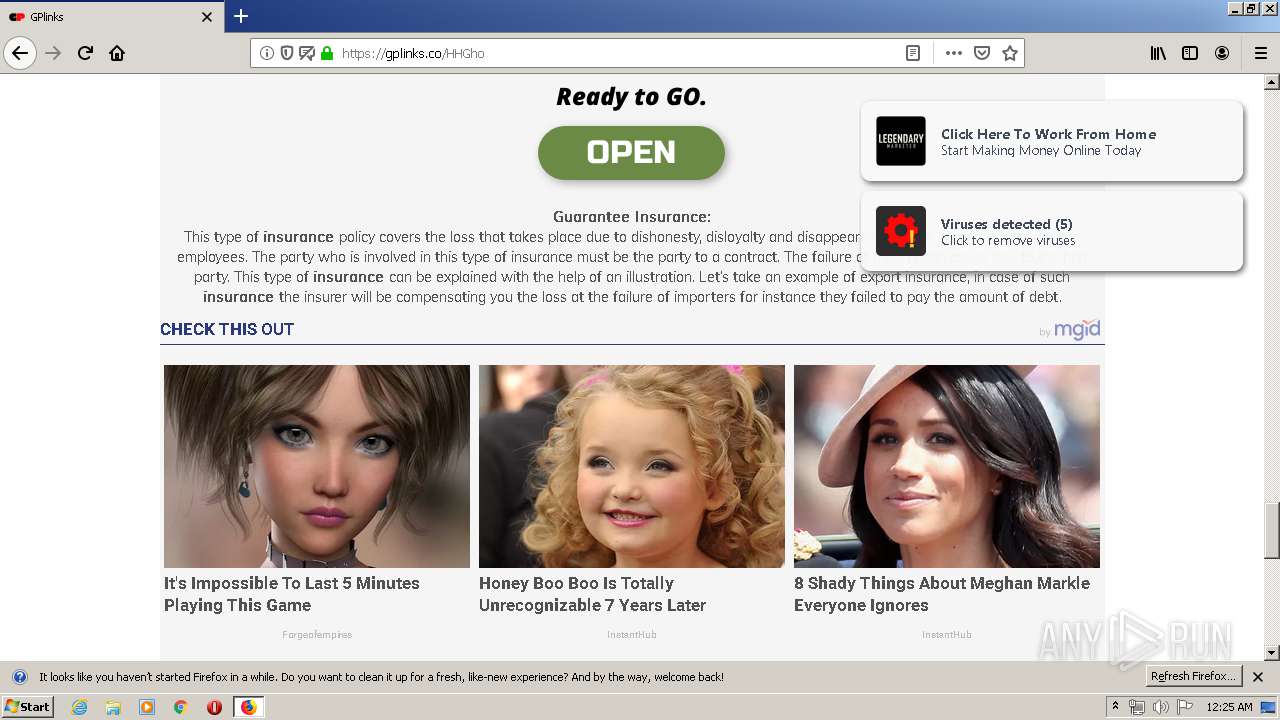
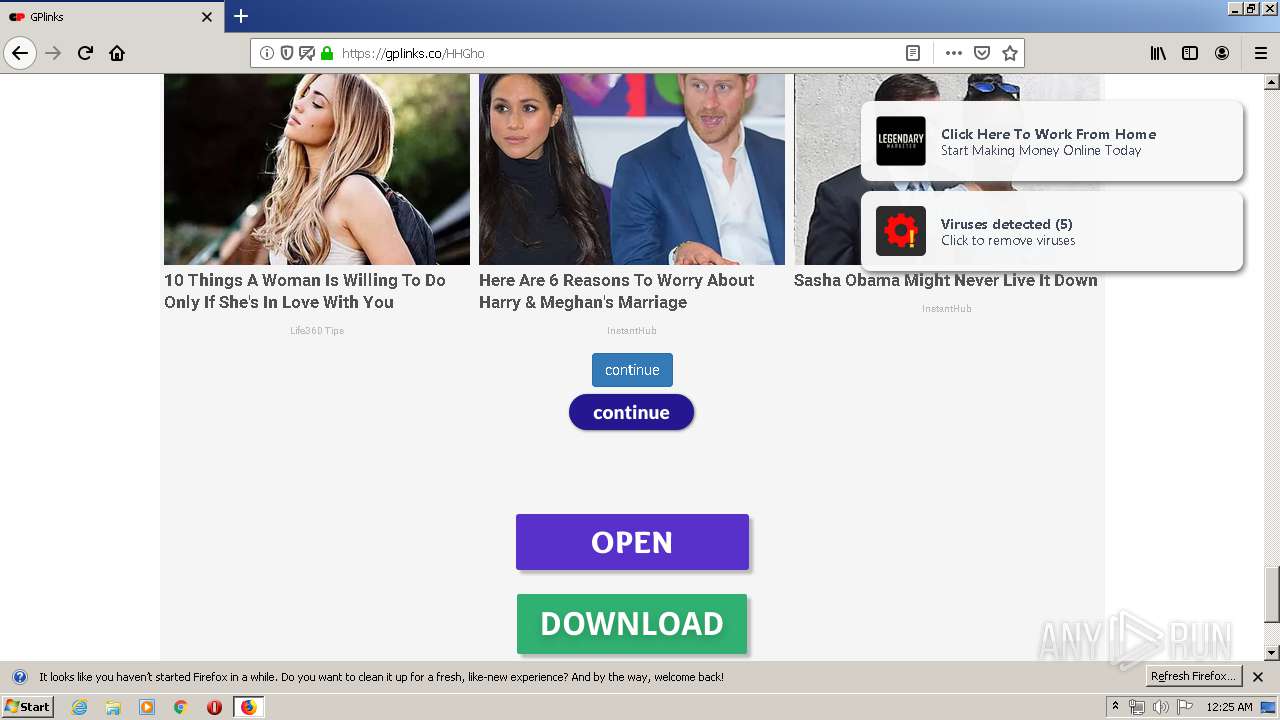
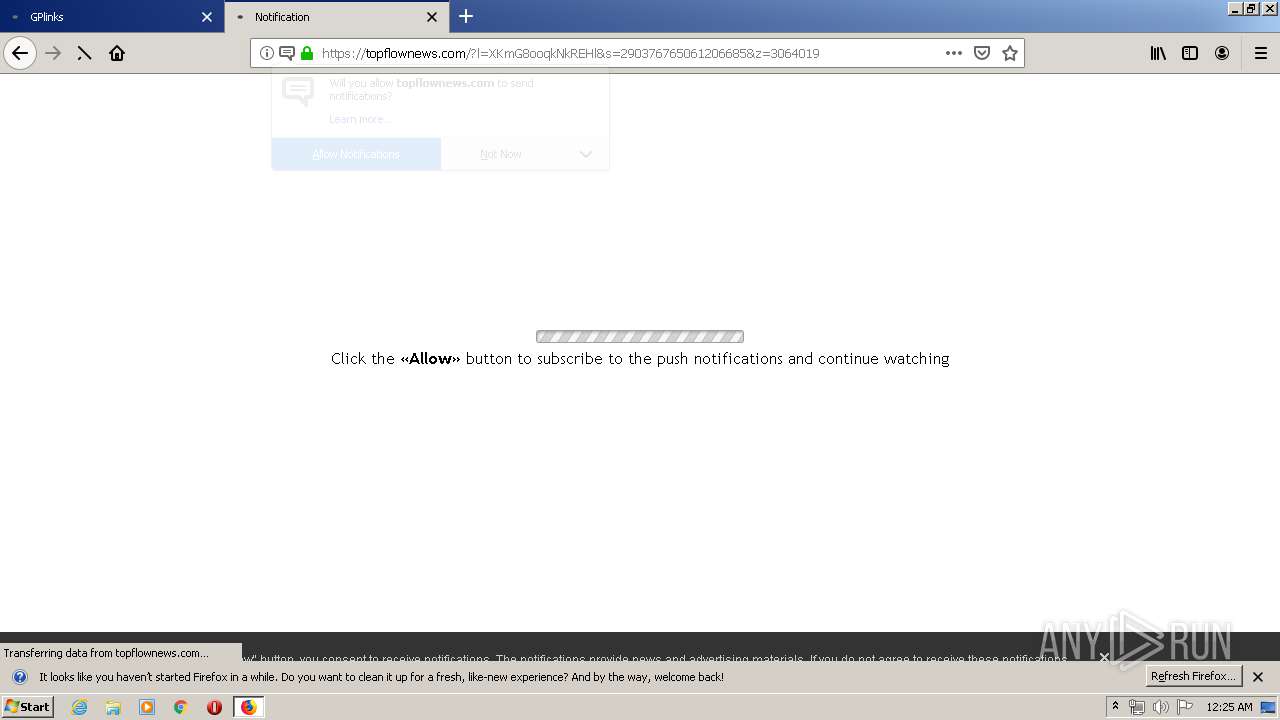
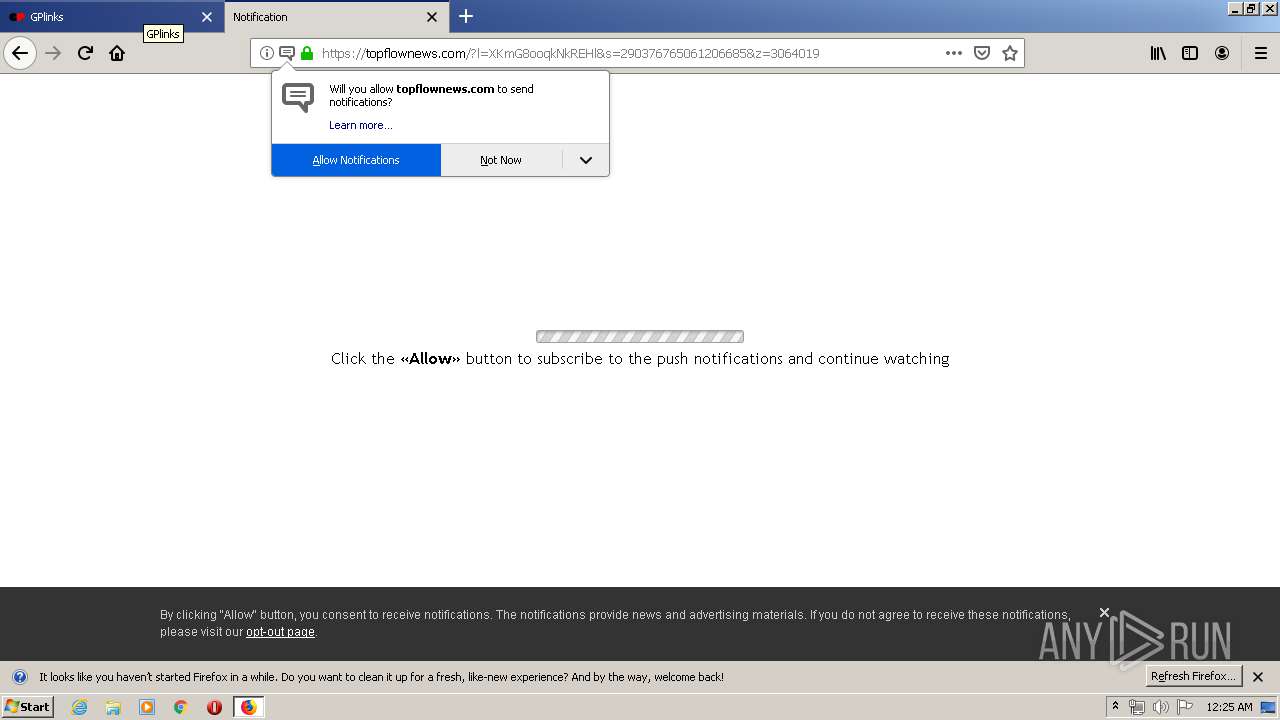
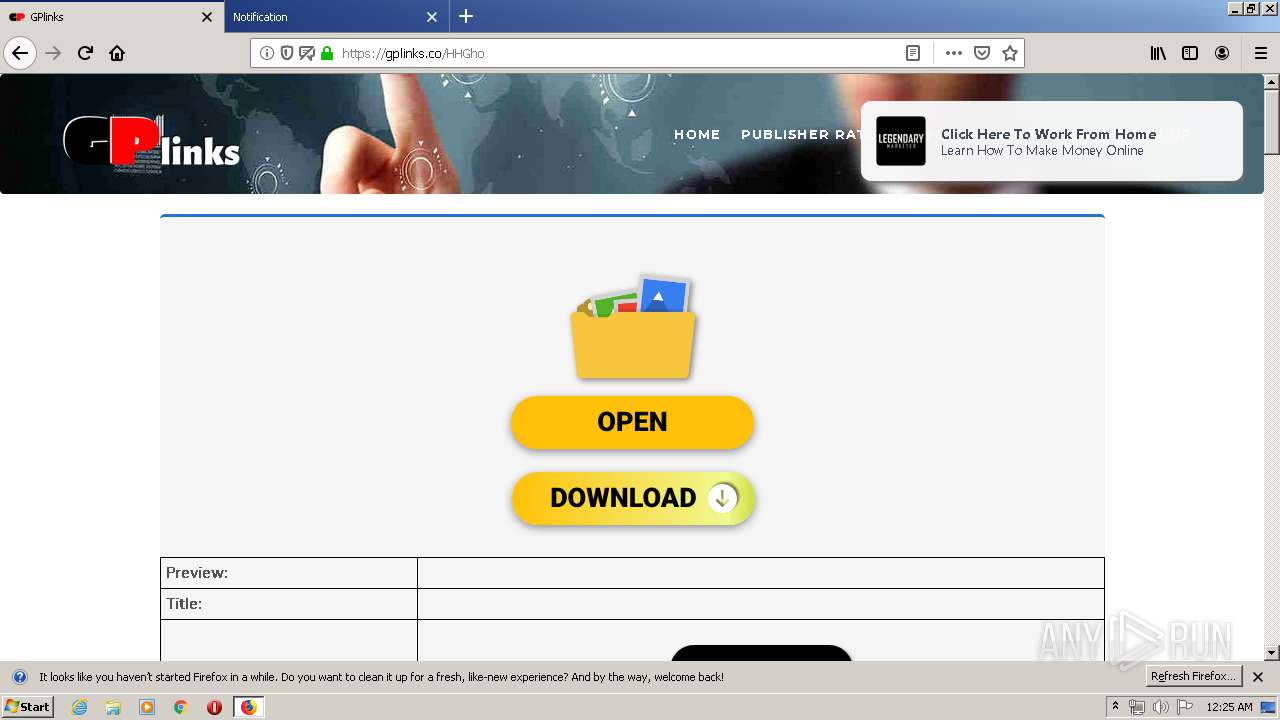
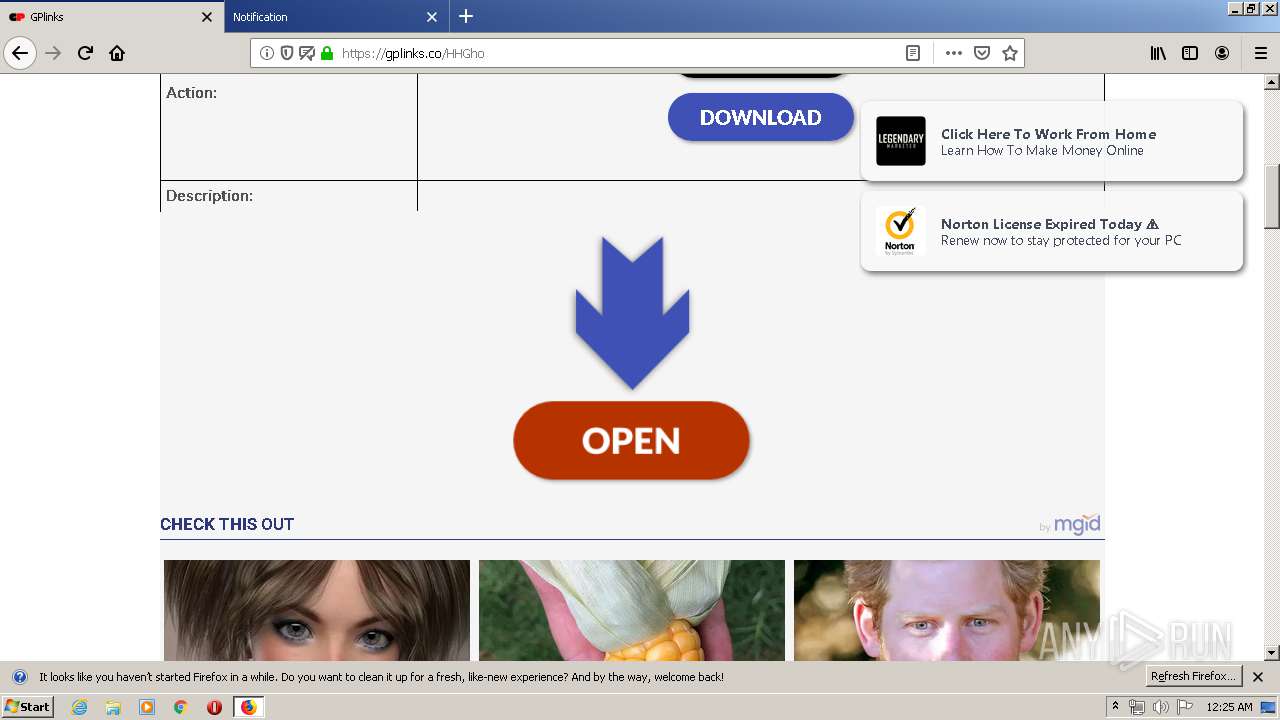
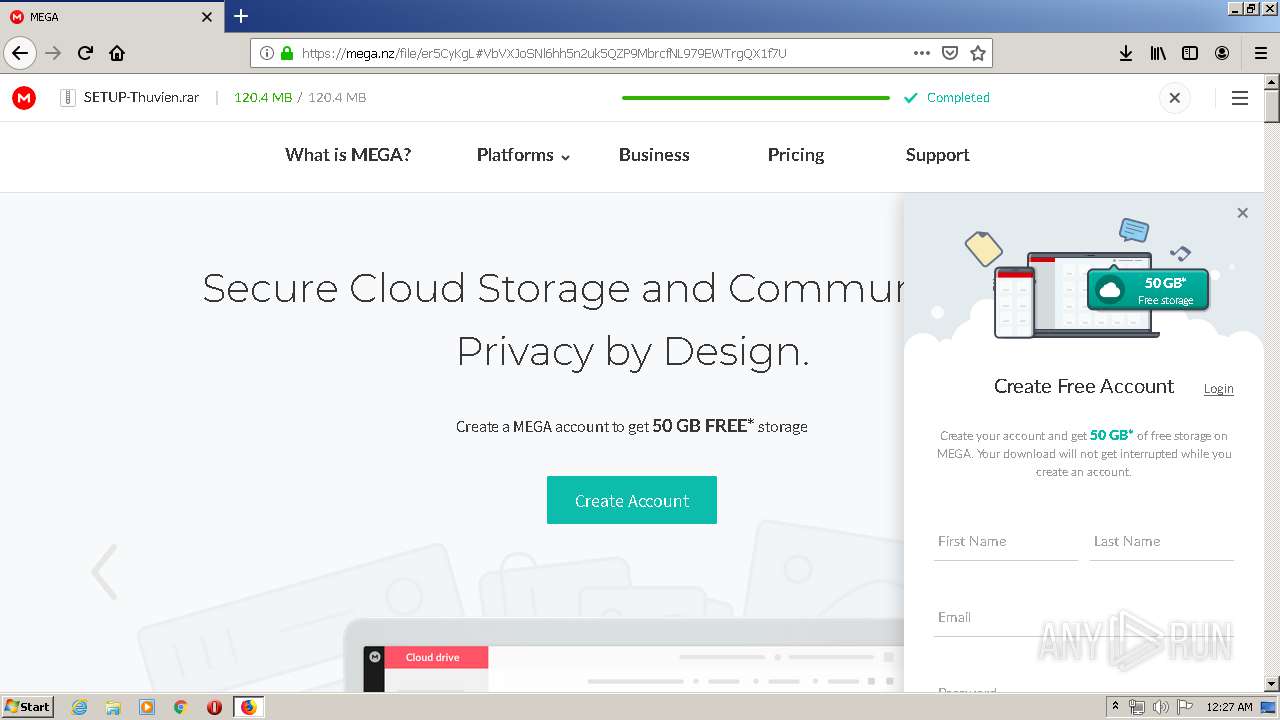
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | May 29, 2020, 23:23:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | EFD7252BBD0F532D60D606633A9DBCD3 |
| SHA1: | EAC9530D75EC32A12CBFBD3BDF12ACEB88EDD495 |
| SHA256: | FC6F931FD99E1CEEDA12539C3096F3F5F999DCA3739283A1D6237607BA2BA3CE |
| SSDEEP: | 3072:P6+ChrmdcUDl0A8Cup+8OIAk8CQn93Wqb3E3P3Bvo3v3pQo3v3/WgG/kPJmG+Jm9:PB6ChDlJWgSUJN+JmKoma |
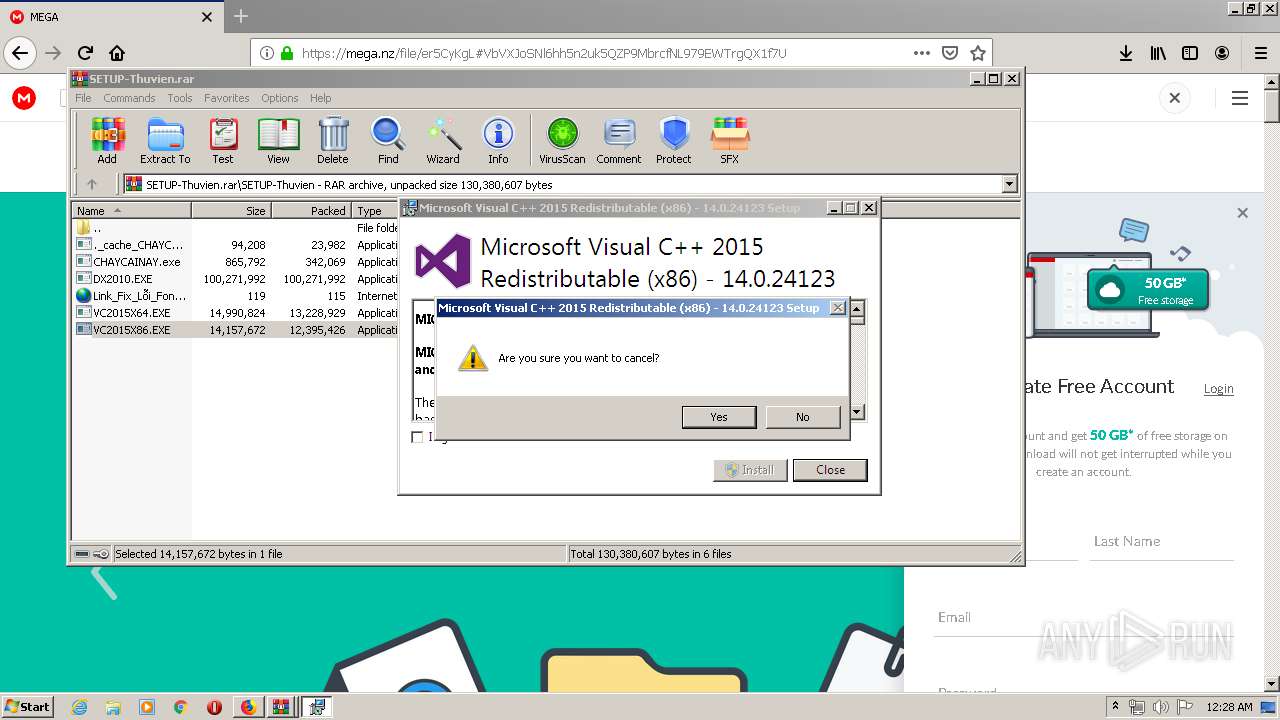
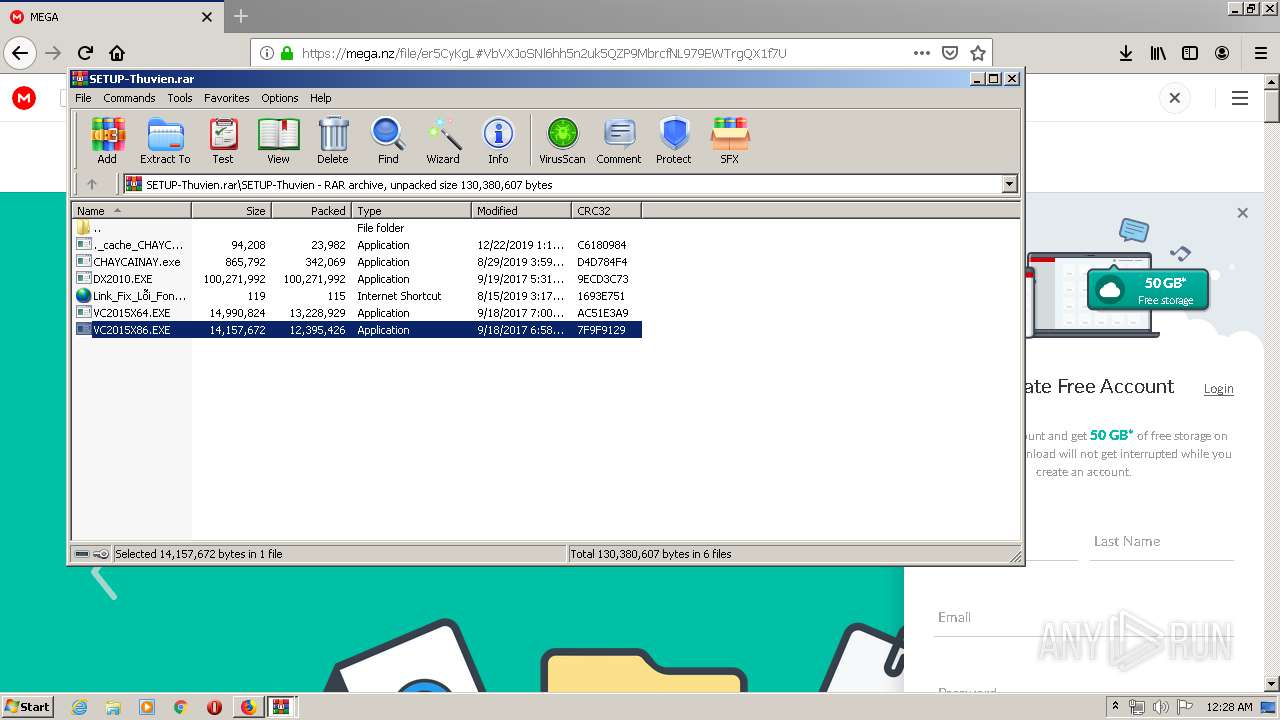
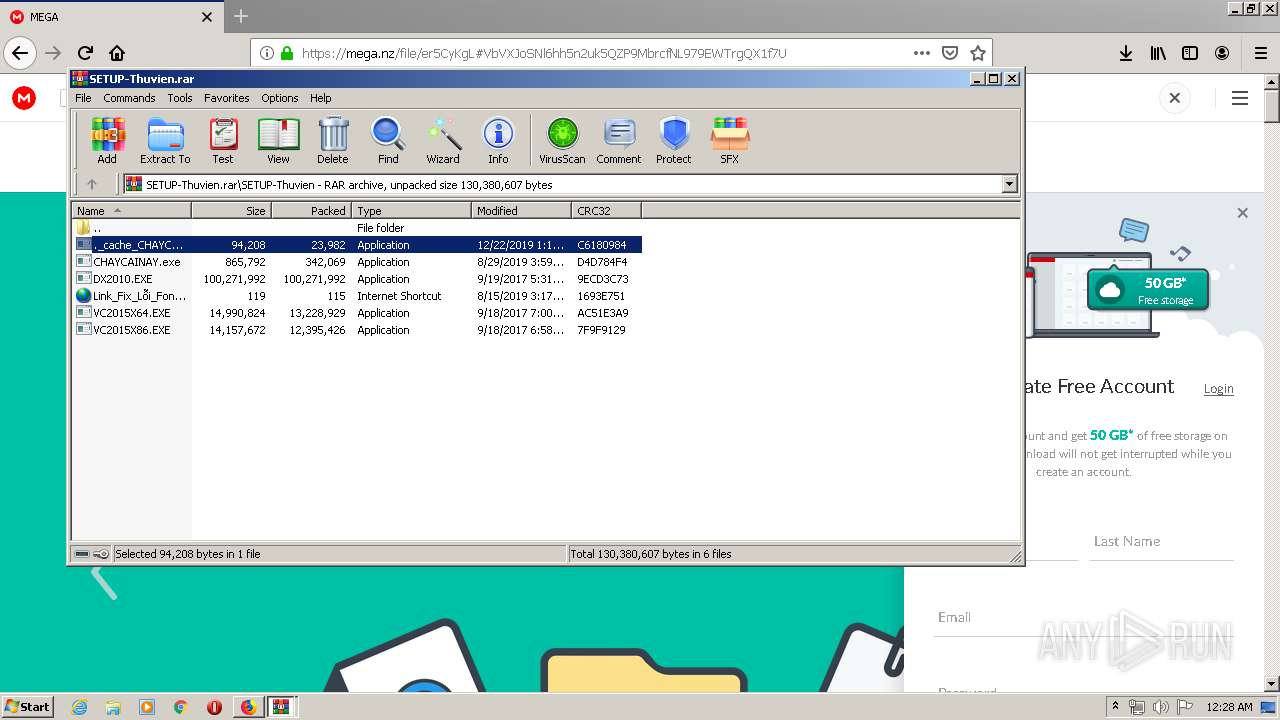
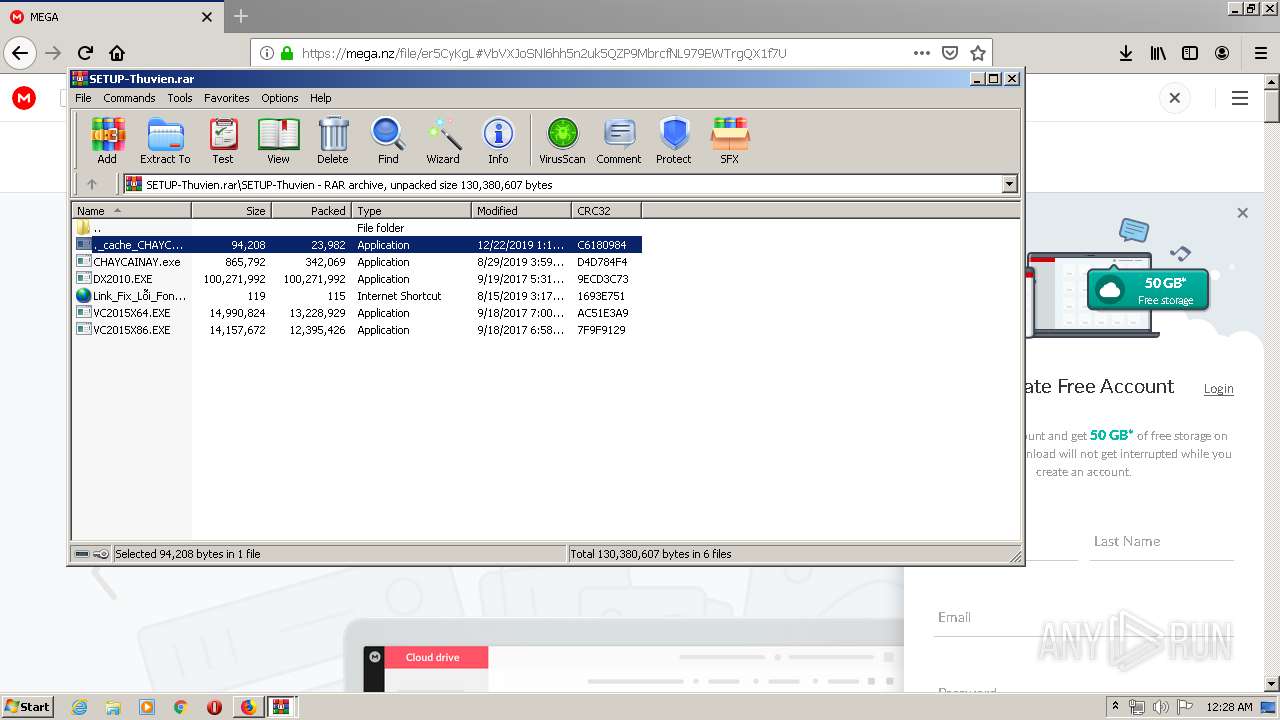
MALICIOUS
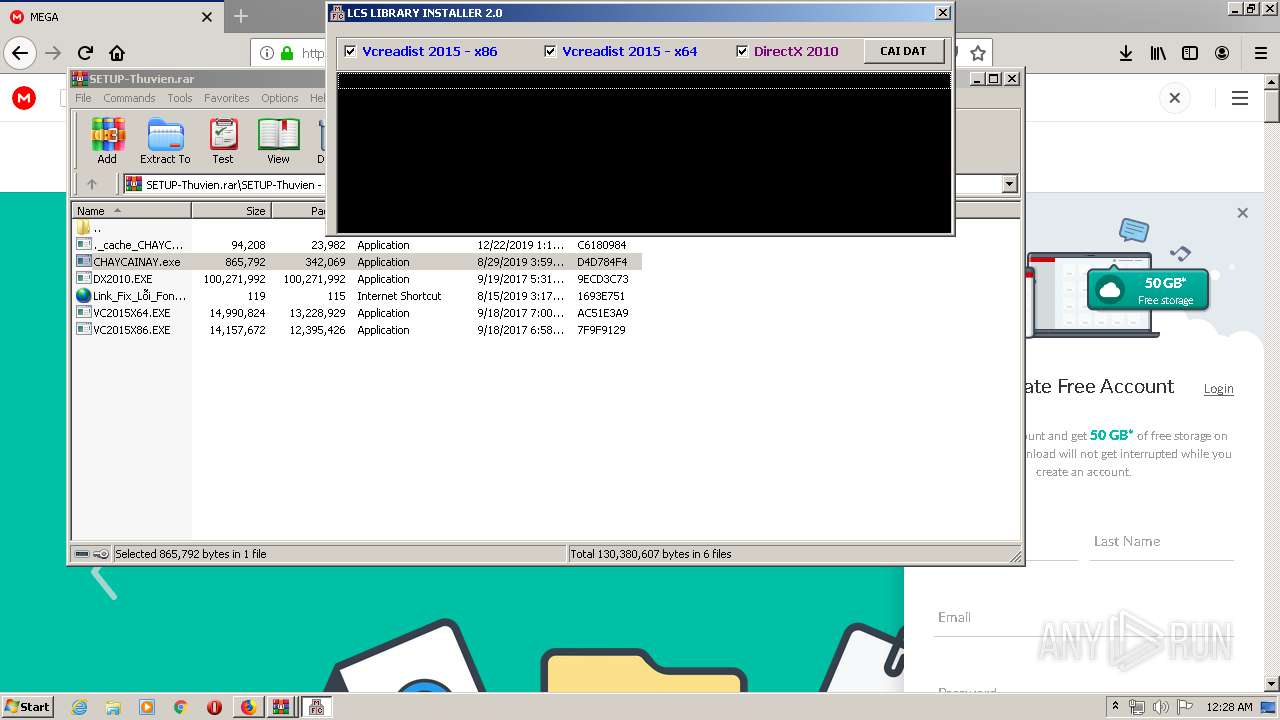
Application was dropped or rewritten from another process
- ._cache_CHAYCAINAY.exe (PID: 2484)
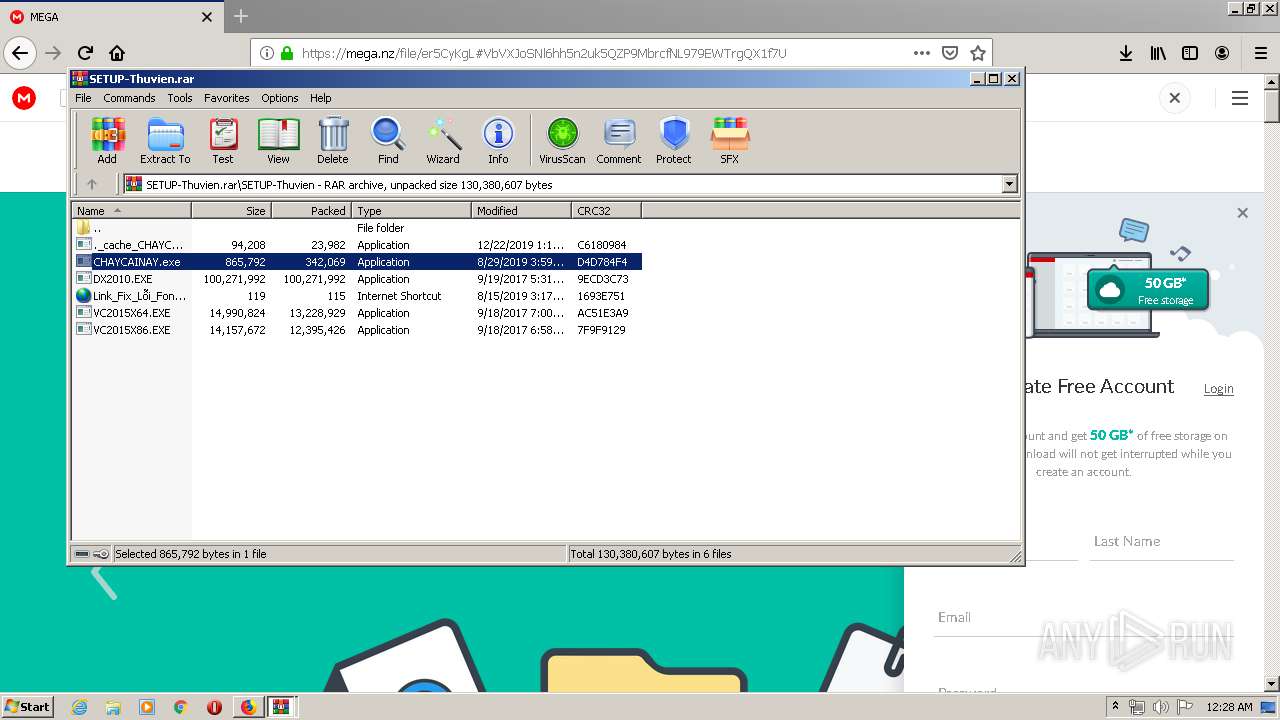
- CHAYCAINAY.exe (PID: 1548)
- ._cache_CHAYCAINAY.exe (PID: 1896)
- Synaptics.exe (PID: 2476)
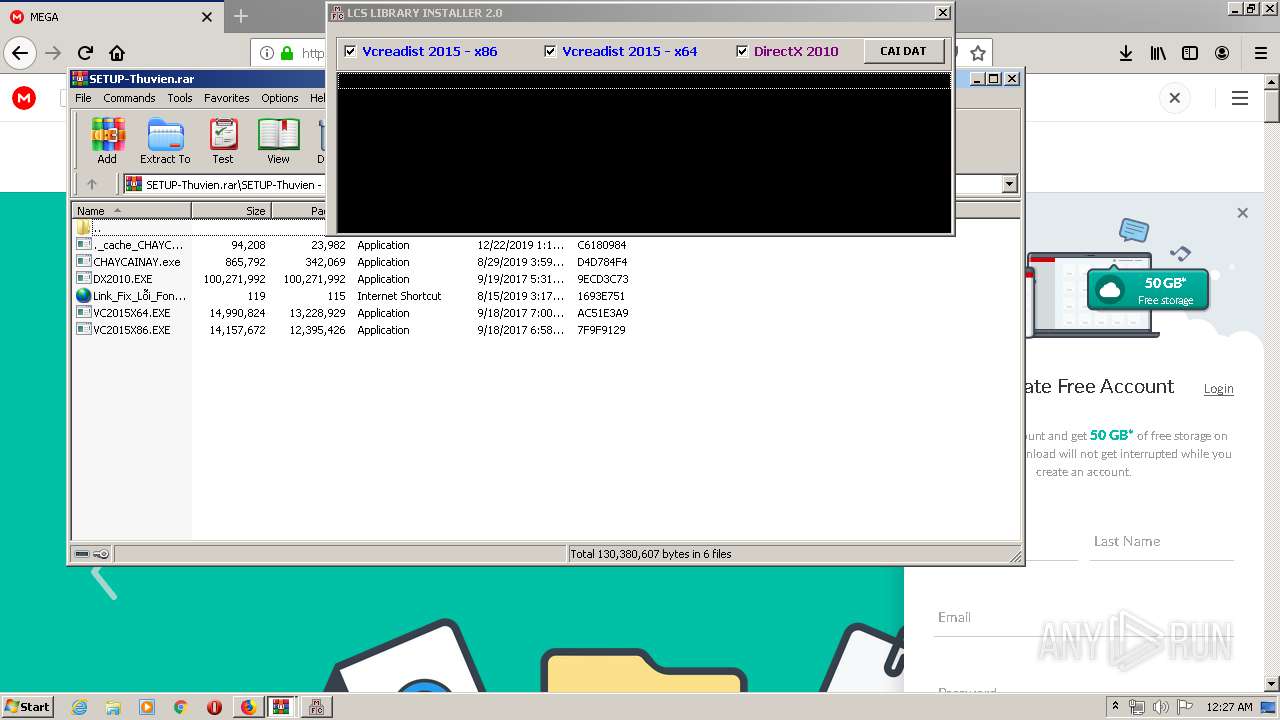
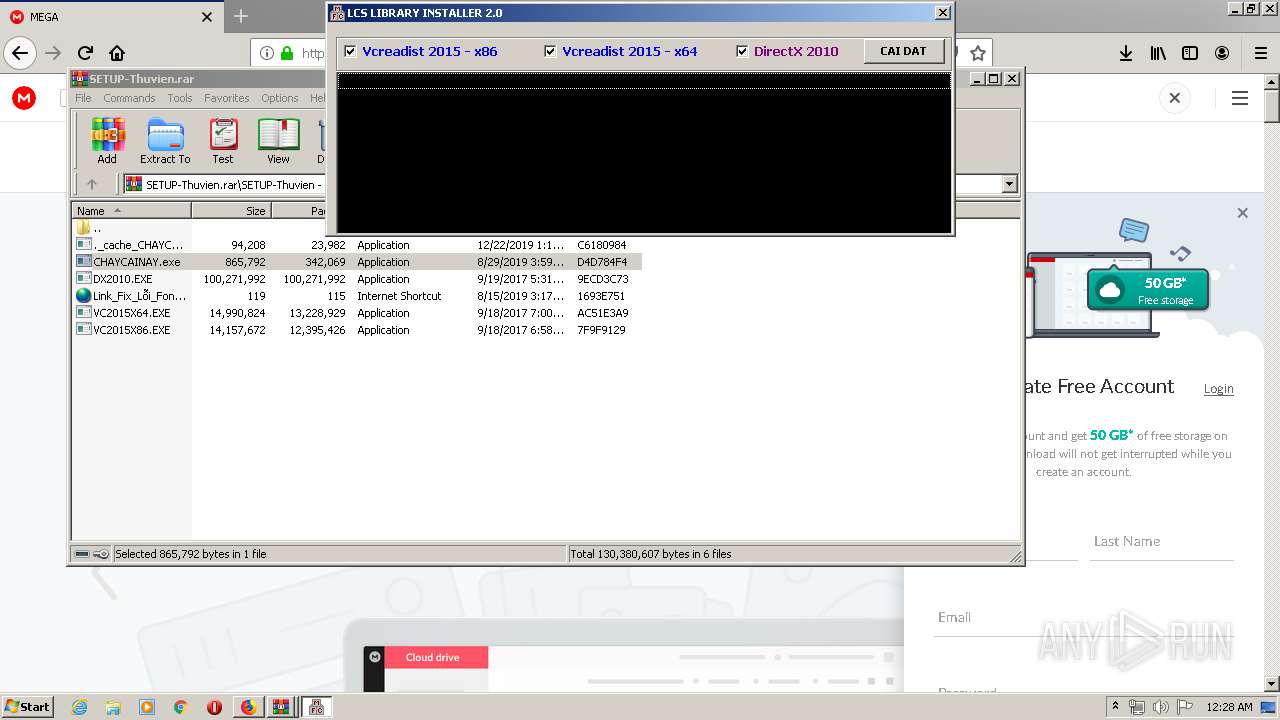
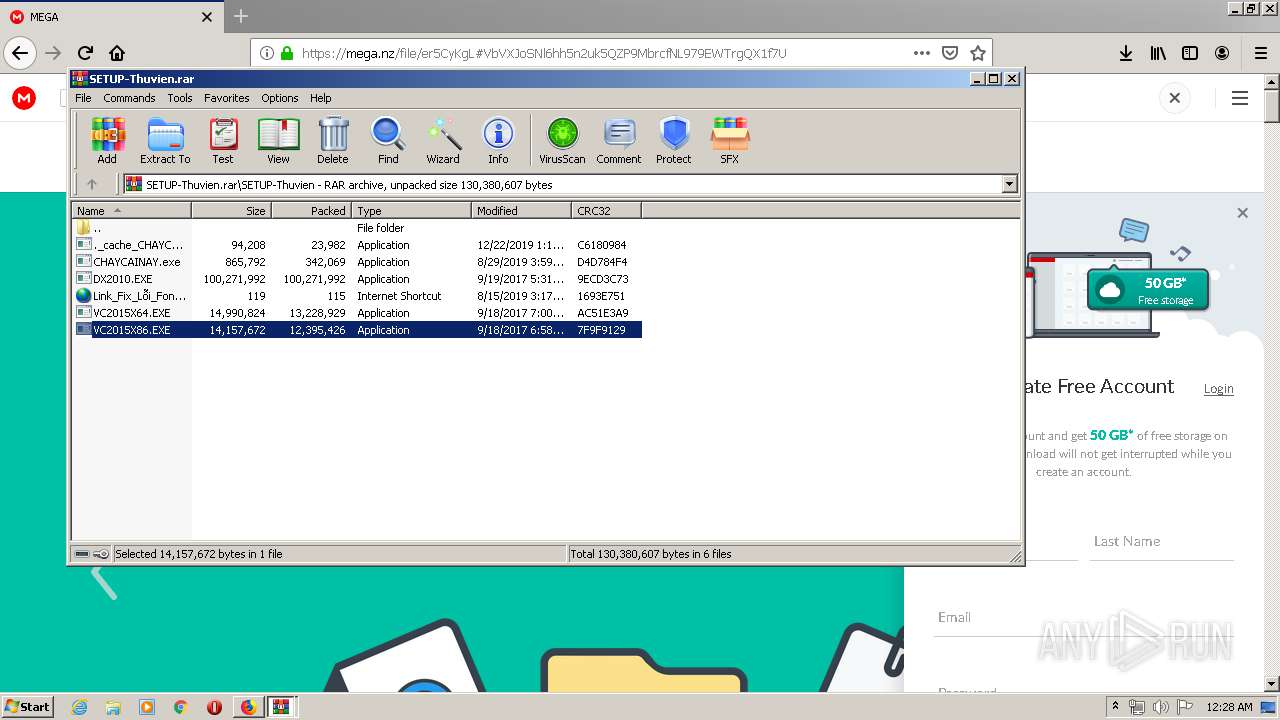
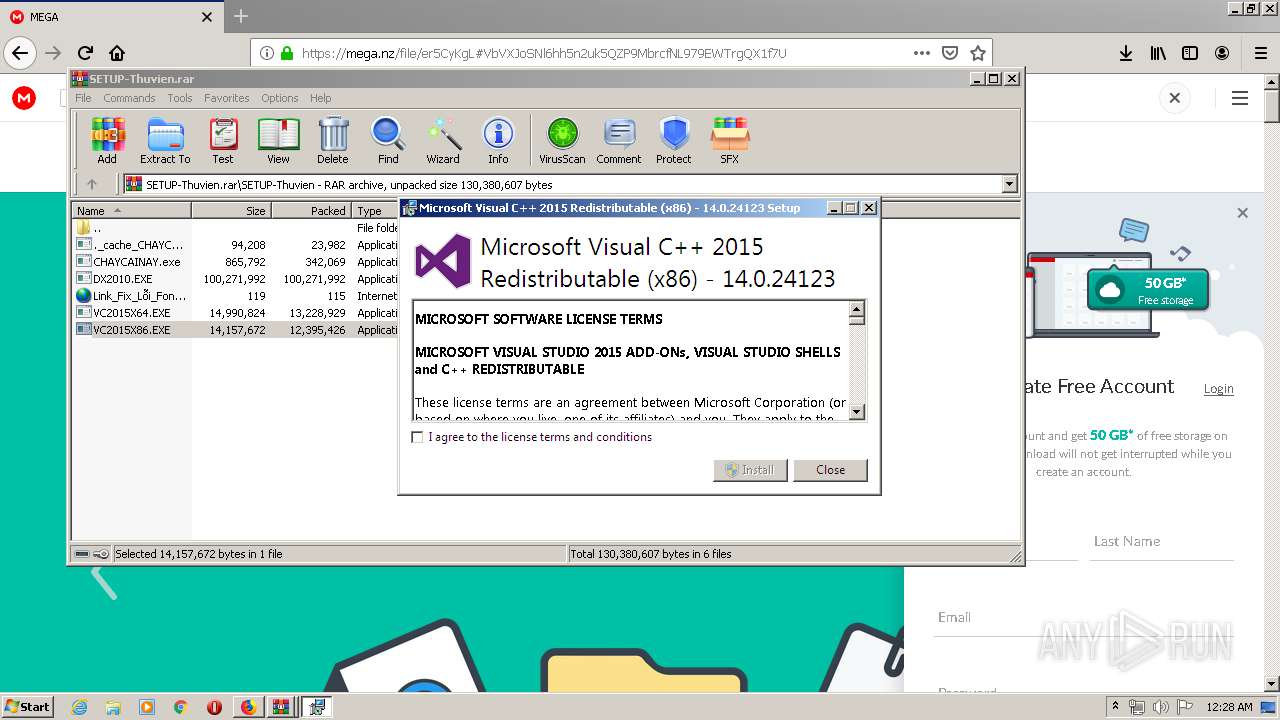
- VC2015X86.EXE (PID: 2792)
- ._cache_CHAYCAINAY.exe (PID: 2724)
Changes the autorun value in the registry
- CHAYCAINAY.exe (PID: 1548)
Loads dropped or rewritten executable
- VC2015X86.EXE (PID: 2792)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2716)
- CHAYCAINAY.exe (PID: 1548)
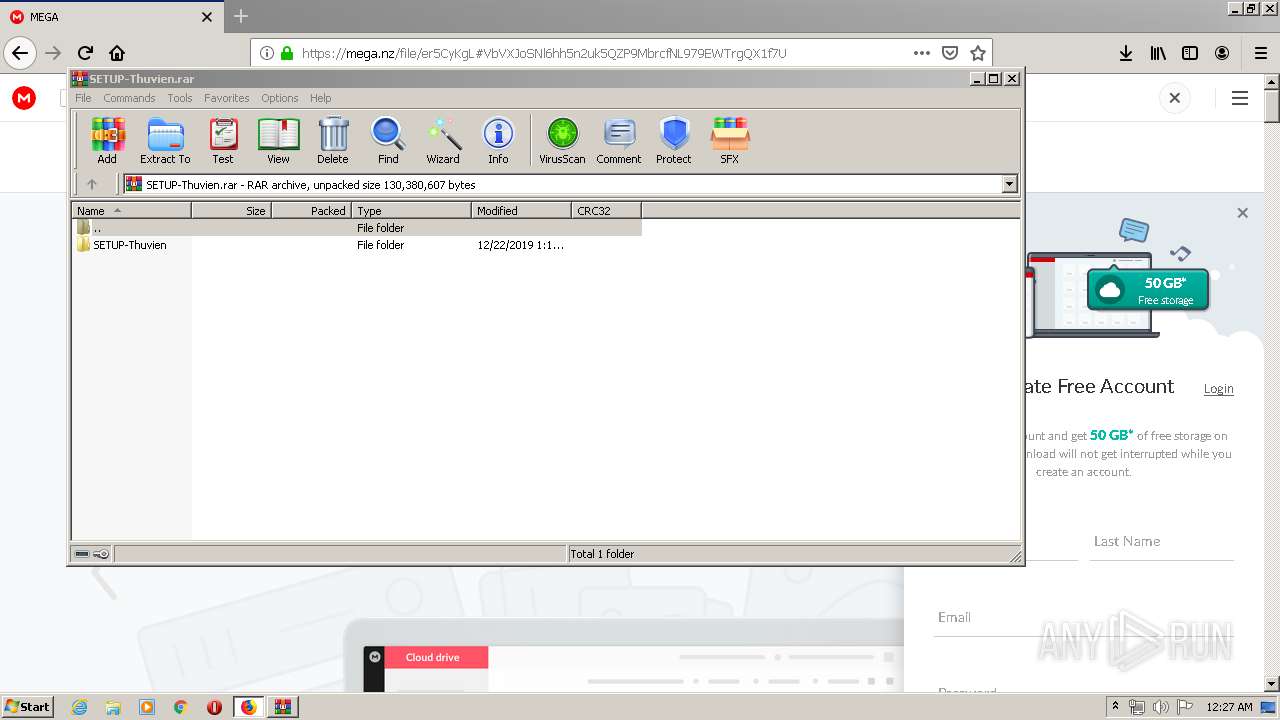
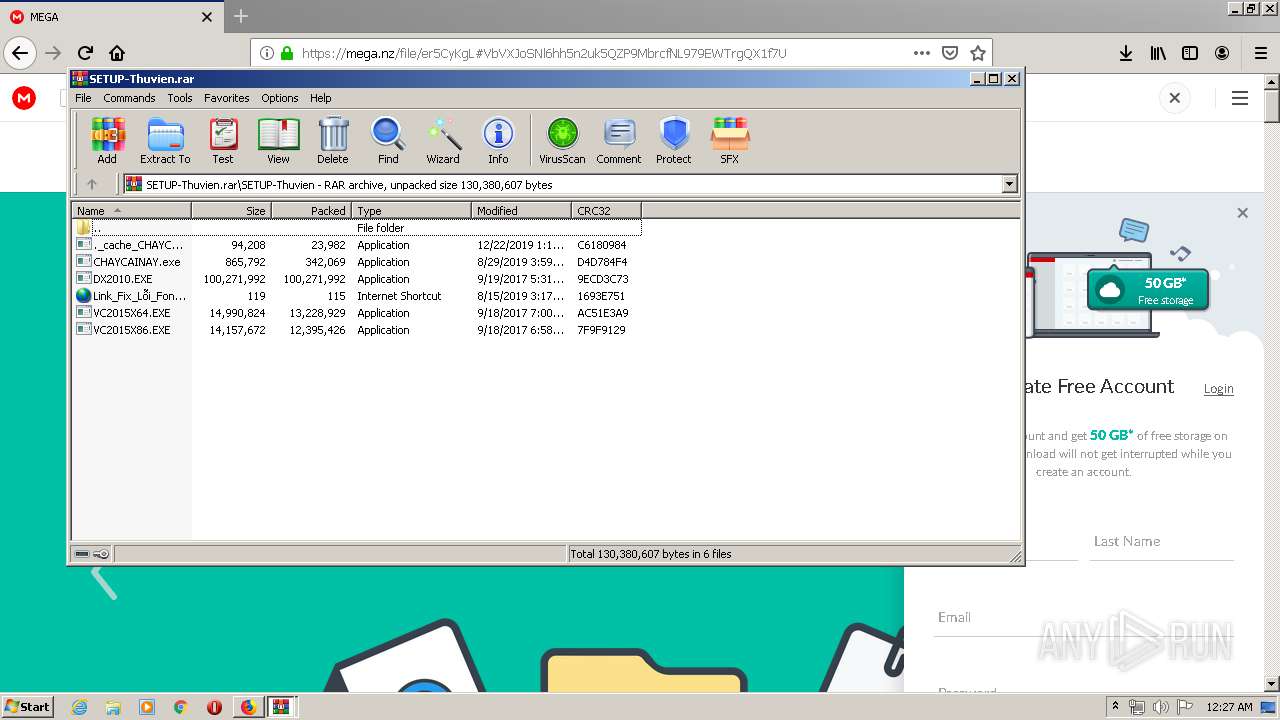
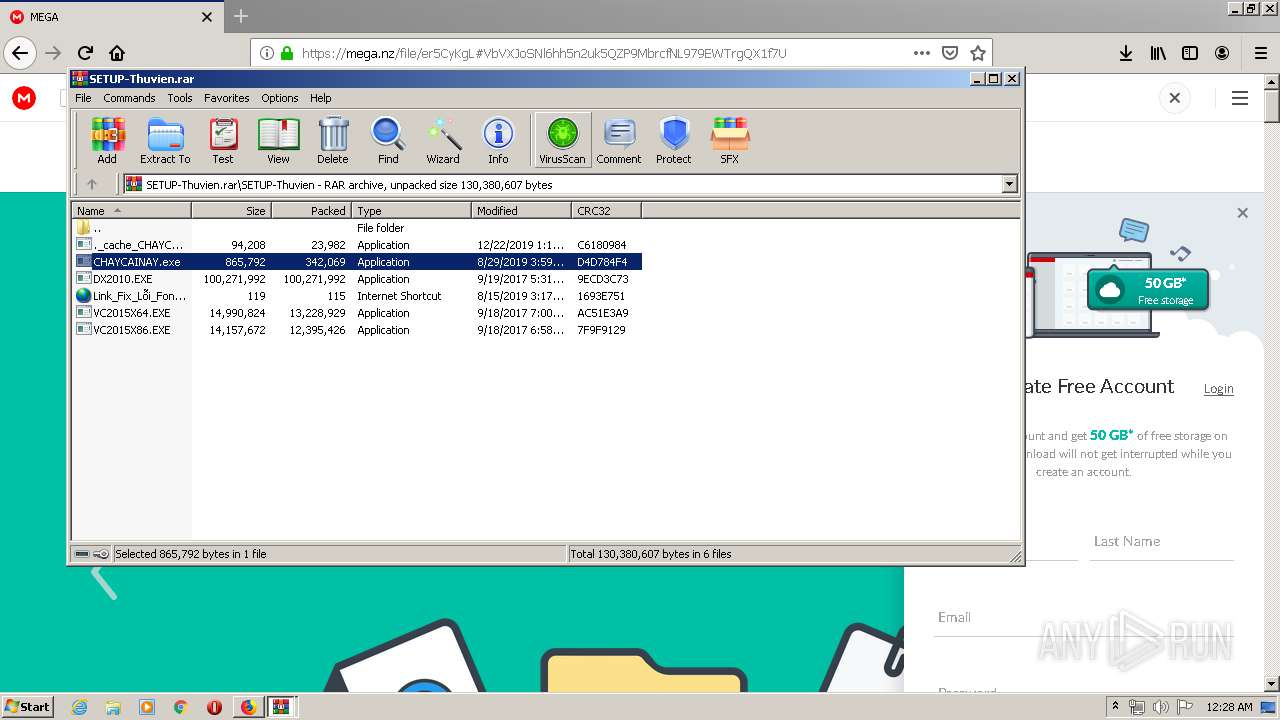
Executable content was dropped or overwritten
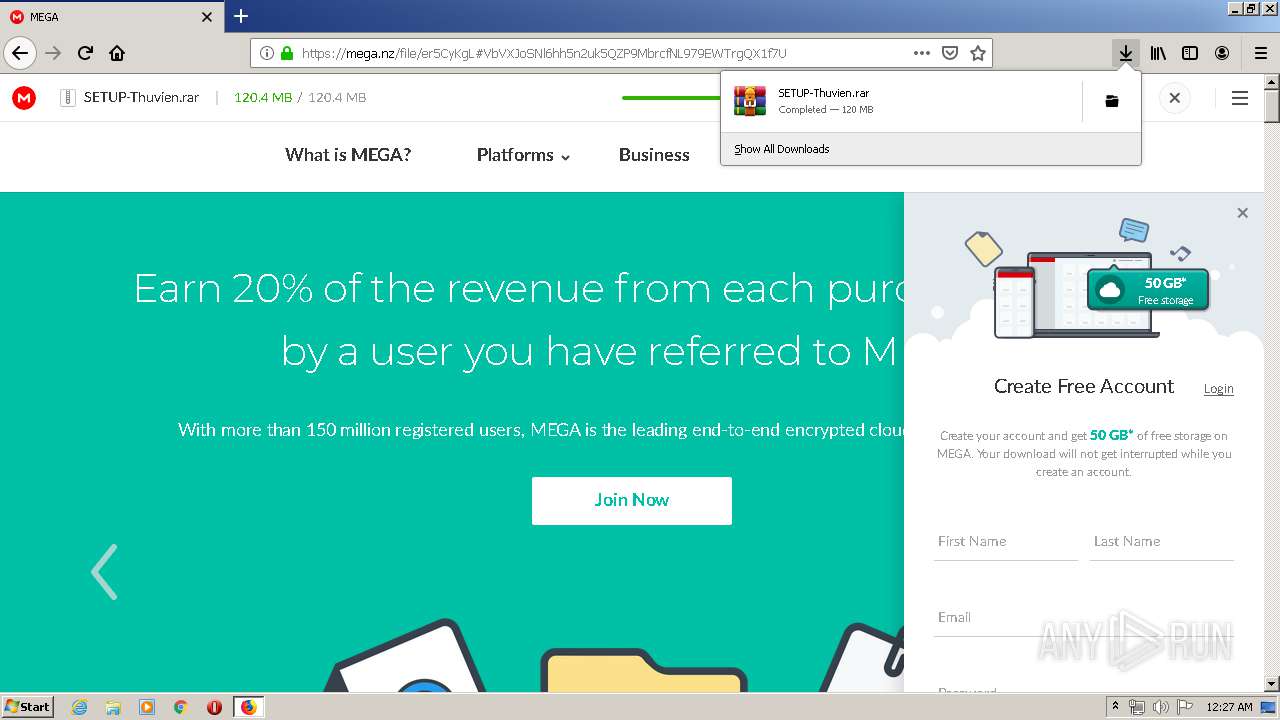
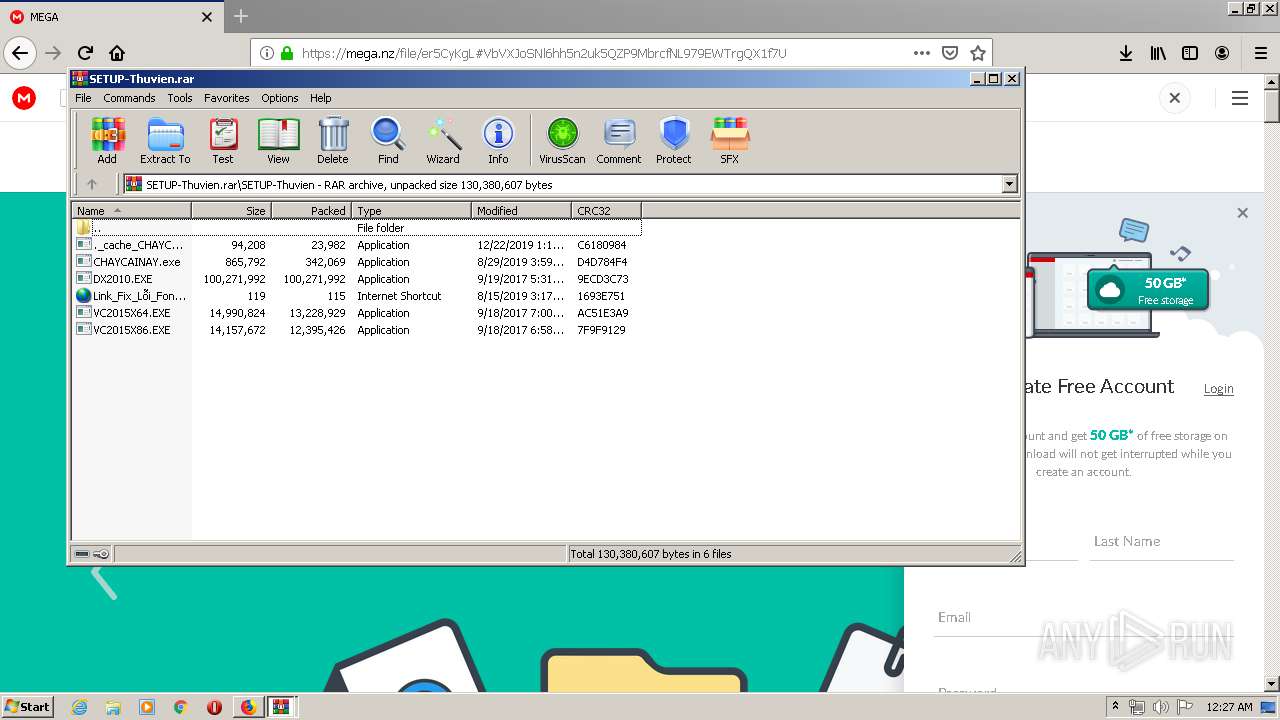
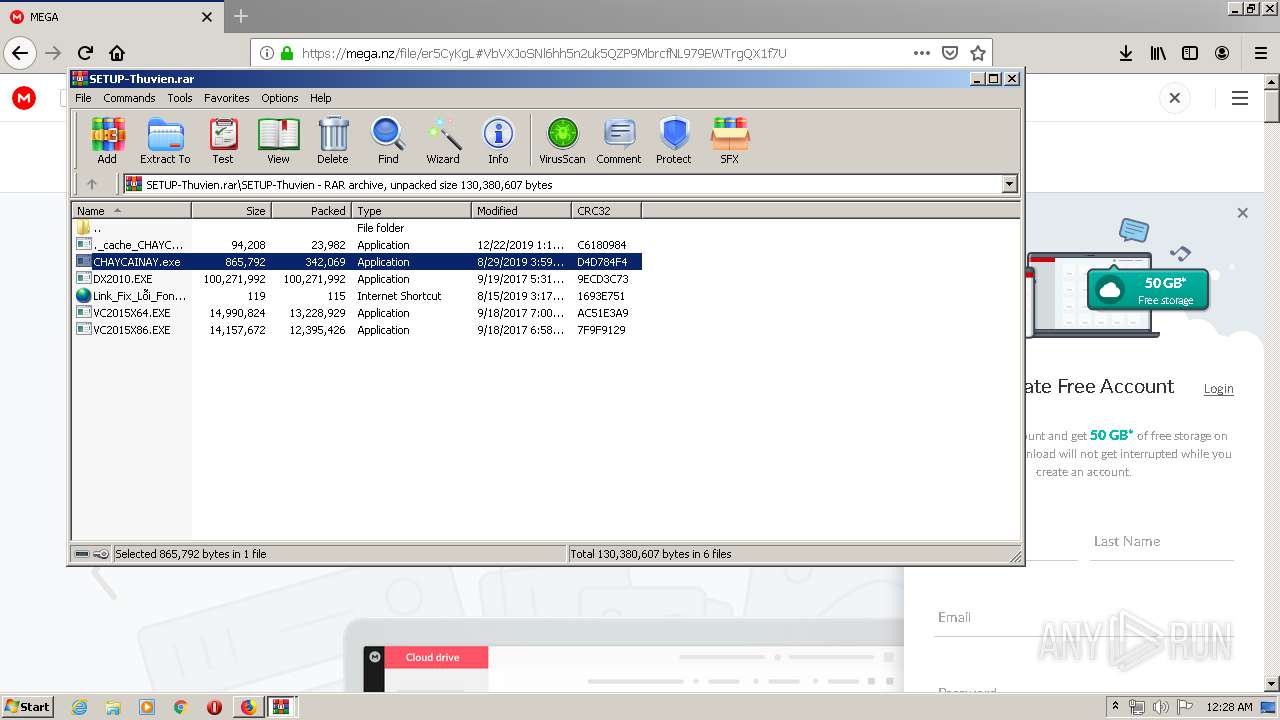
- WinRAR.exe (PID: 4008)
- CHAYCAINAY.exe (PID: 1548)
- WinRAR.exe (PID: 1904)
- VC2015X86.EXE (PID: 2792)
Reads Internet Cache Settings
- ._cache_CHAYCAINAY.exe (PID: 1896)
- ._cache_CHAYCAINAY.exe (PID: 2484)
- Synaptics.exe (PID: 2476)
- ._cache_CHAYCAINAY.exe (PID: 2724)
Searches for installed software
- VC2015X86.EXE (PID: 2792)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 832)
Reads CPU info
- firefox.exe (PID: 2716)
Reads Internet Cache Settings
- iexplore.exe (PID: 1192)
- firefox.exe (PID: 2716)
Manual execution by user
- firefox.exe (PID: 380)
Application launched itself
- firefox.exe (PID: 2716)
Changes internet zones settings
- iexplore.exe (PID: 1192)
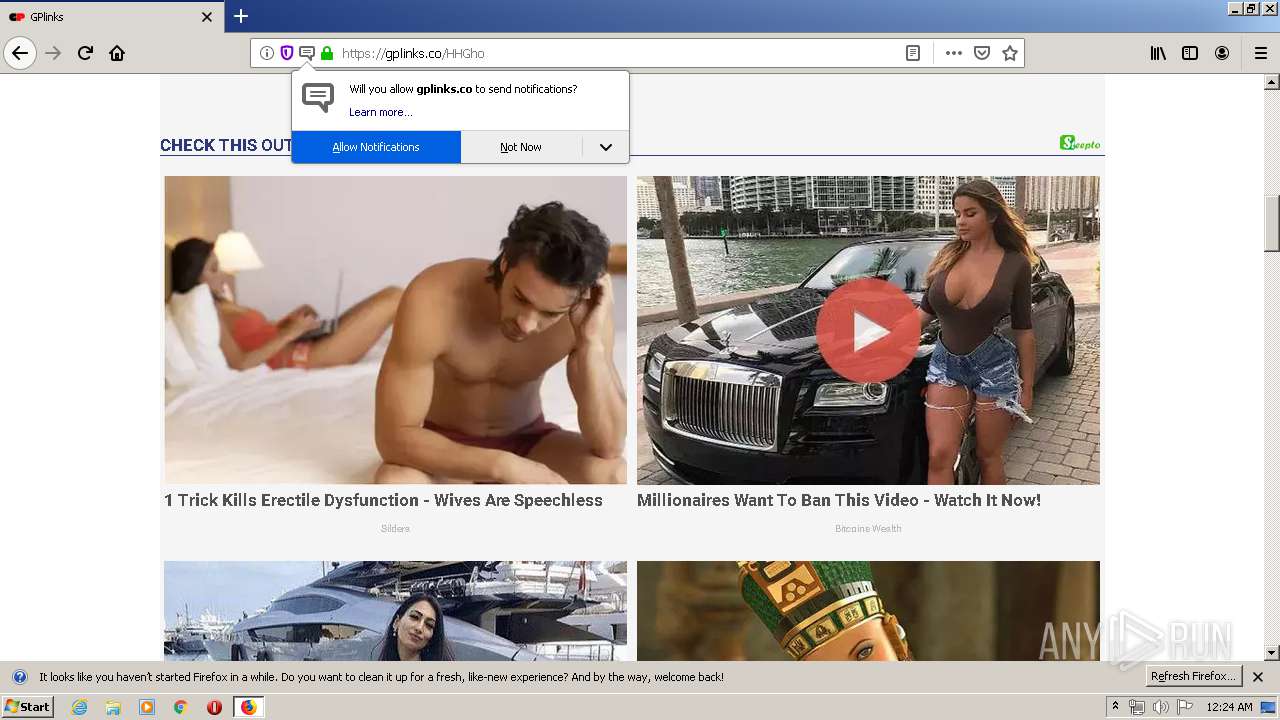
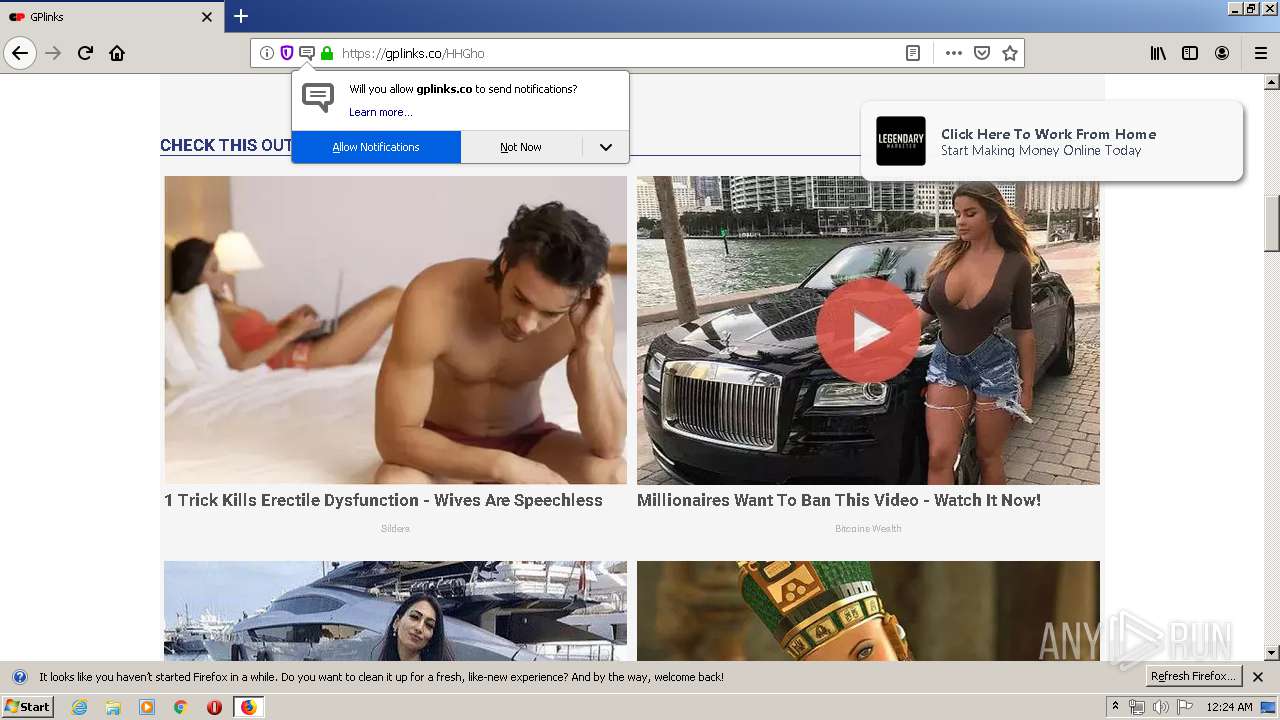
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2716)
Creates files in the user directory
- firefox.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml/atom | | | Atom web feed (92.2) |
|---|---|---|
| .html | | | HyperText Markup Language (7.7) |
EXIF
HTML
| msvalidate01: | BD9F757CB13949150F5BD95C75056F1F |
|---|---|
| googleSiteVerification: | xPvbMKtymrsIa1kxhbmbXOH0zfoovK087jzqA68FIWE |
| viewport: | width=device-width, initial-scale=1, maximum-scale=1 |
| ContentType: | text/html; charset=UTF-8 |
| Generator: | blogger |
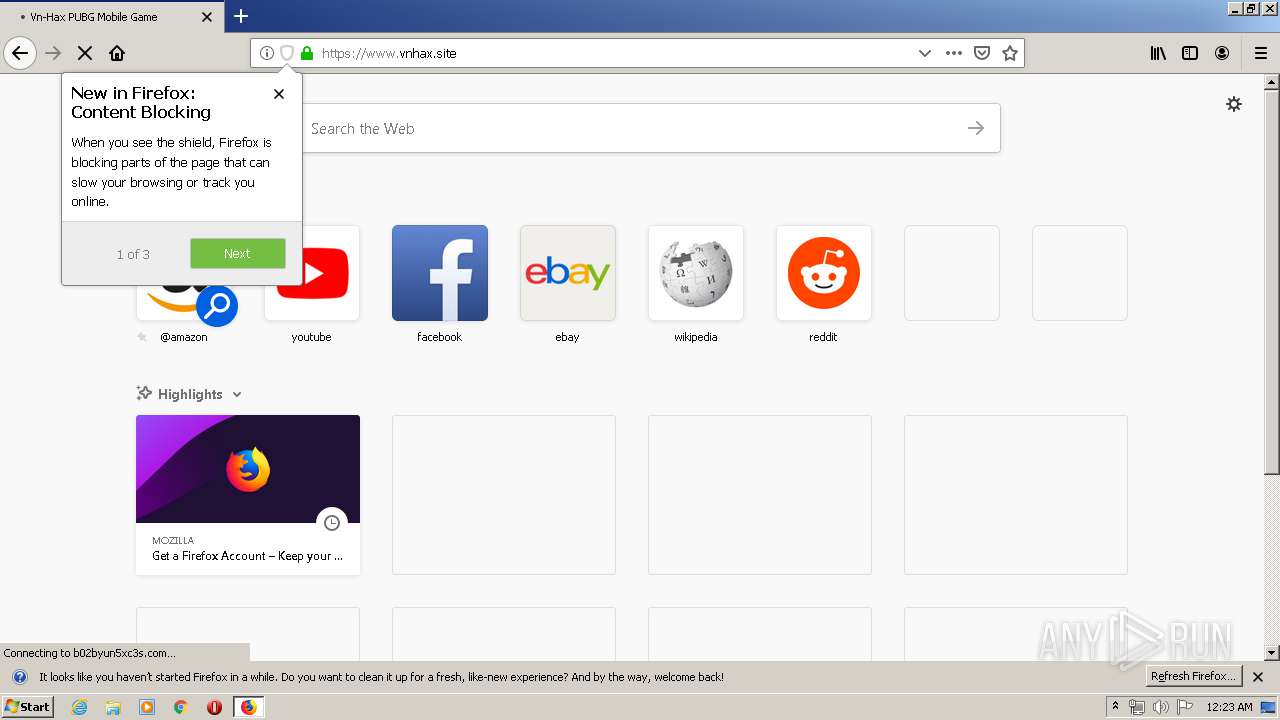
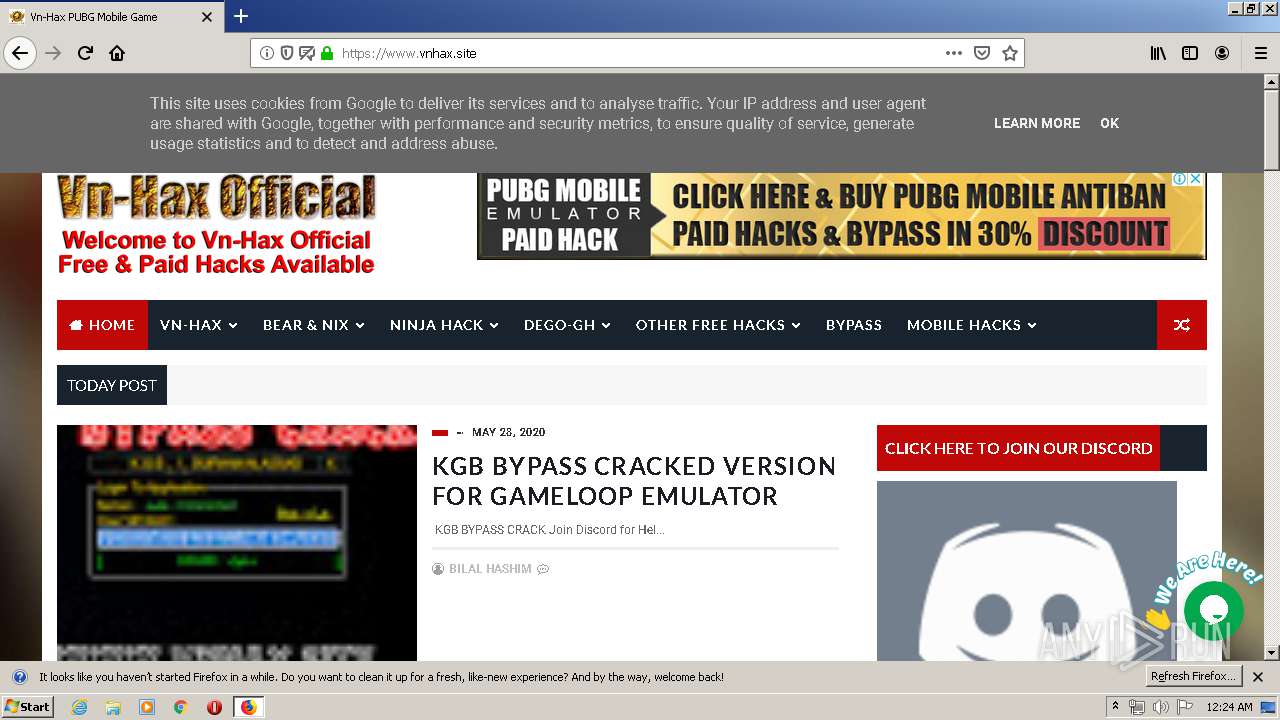
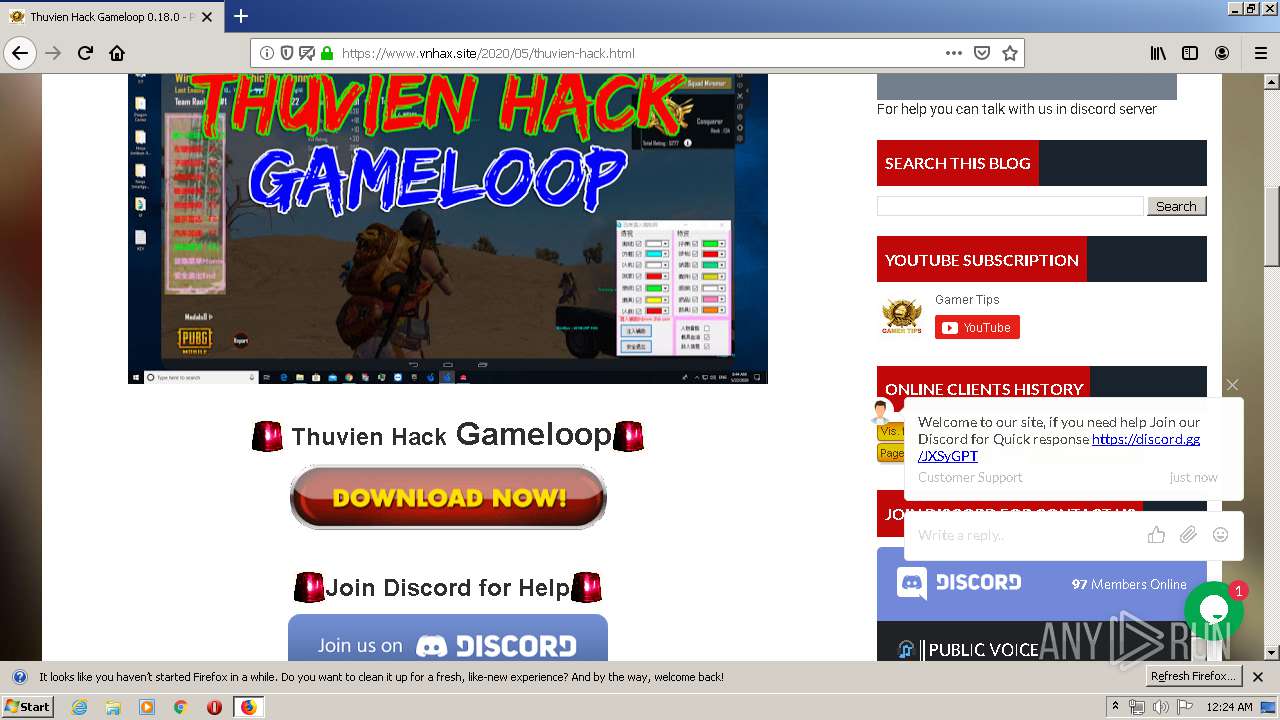
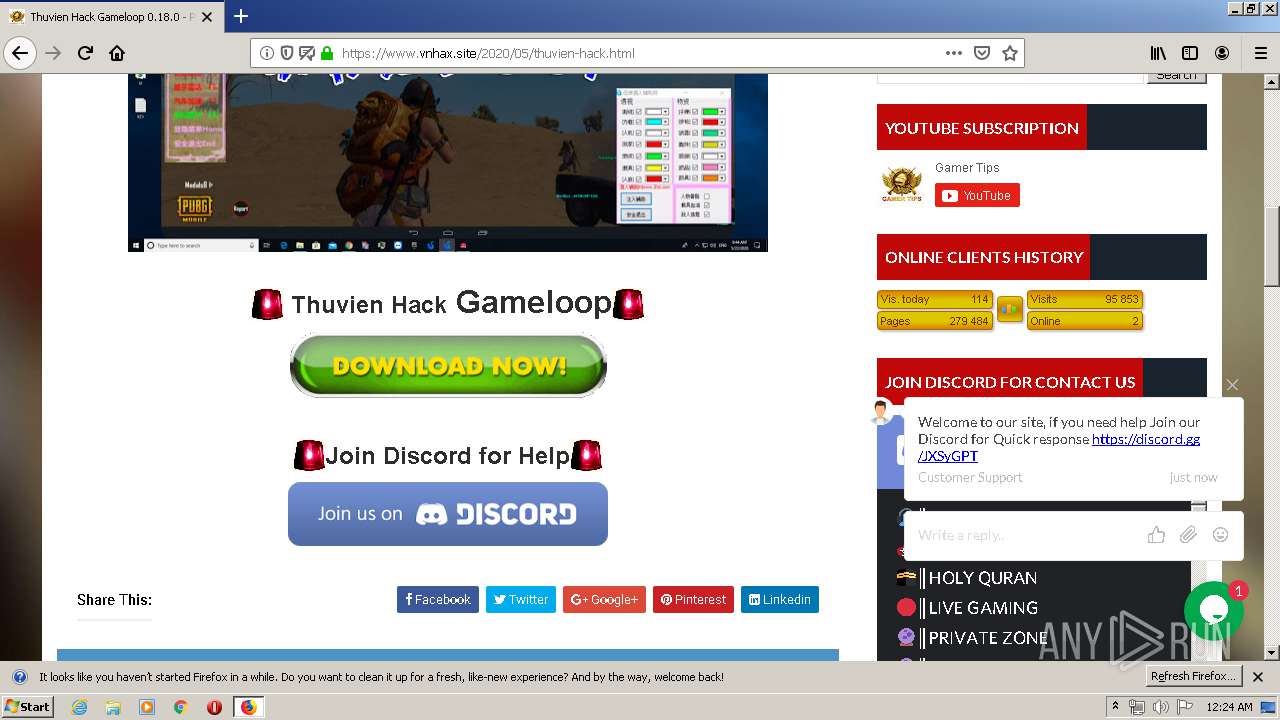
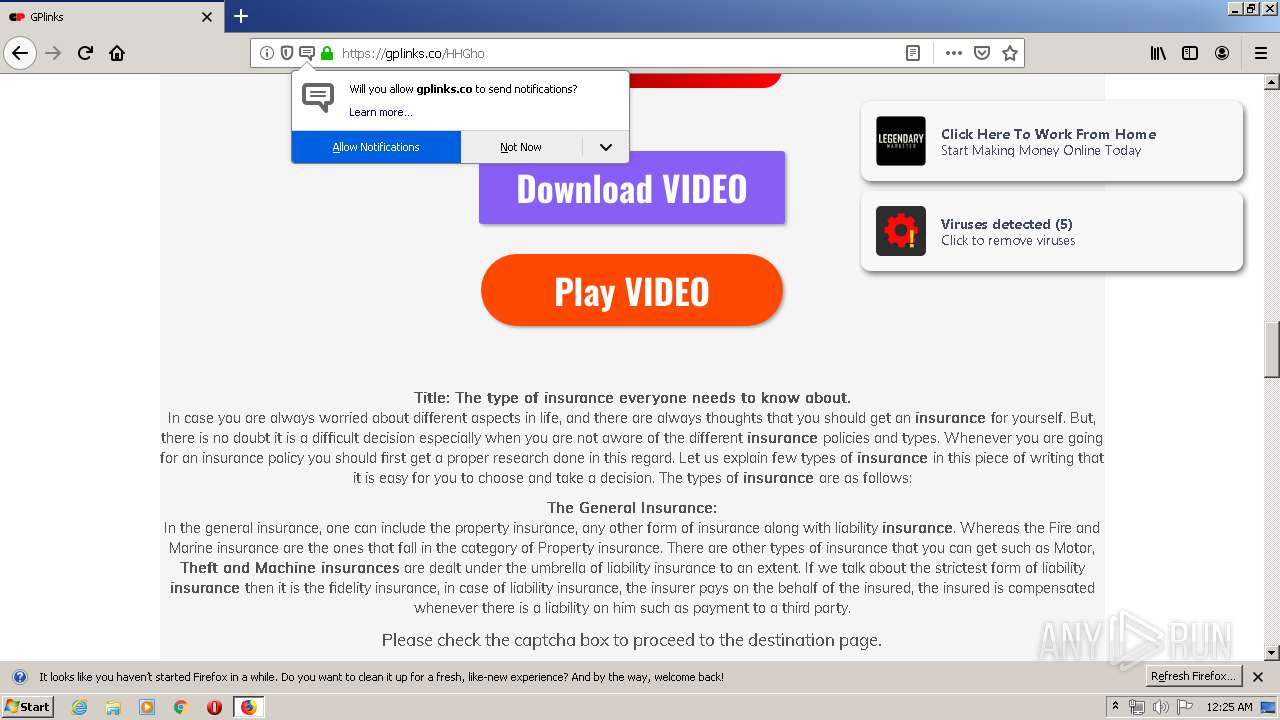
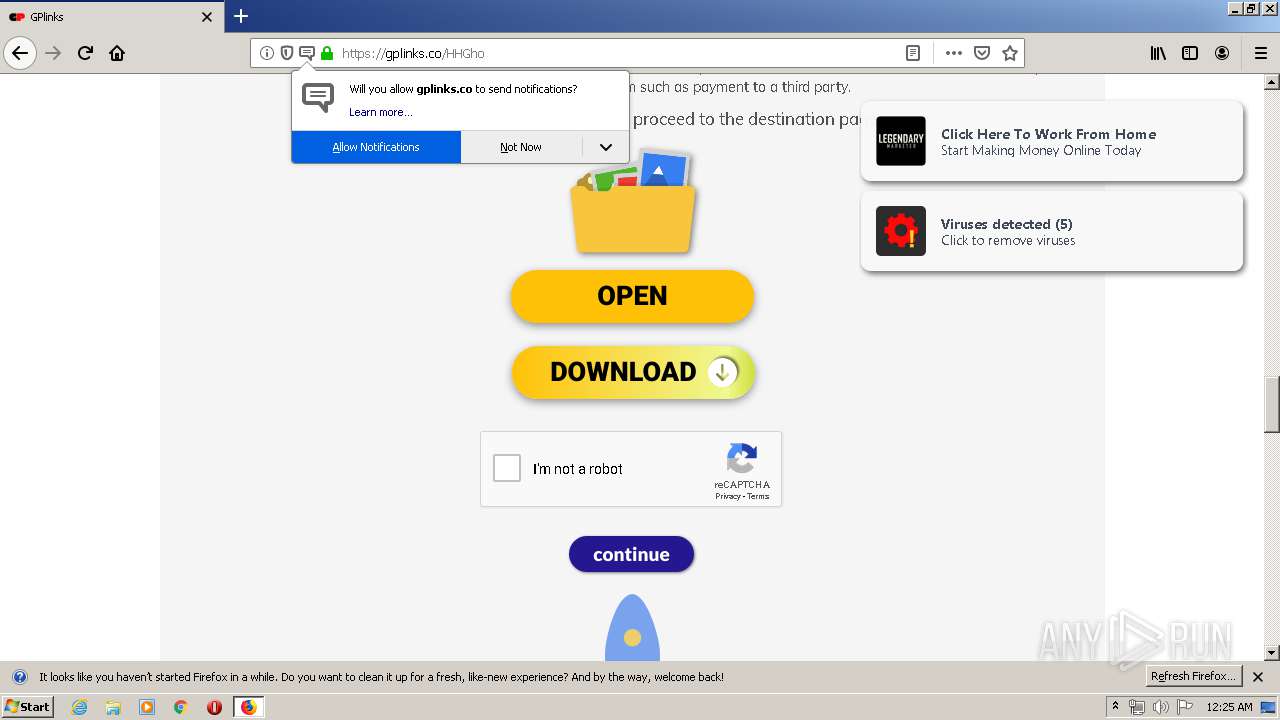
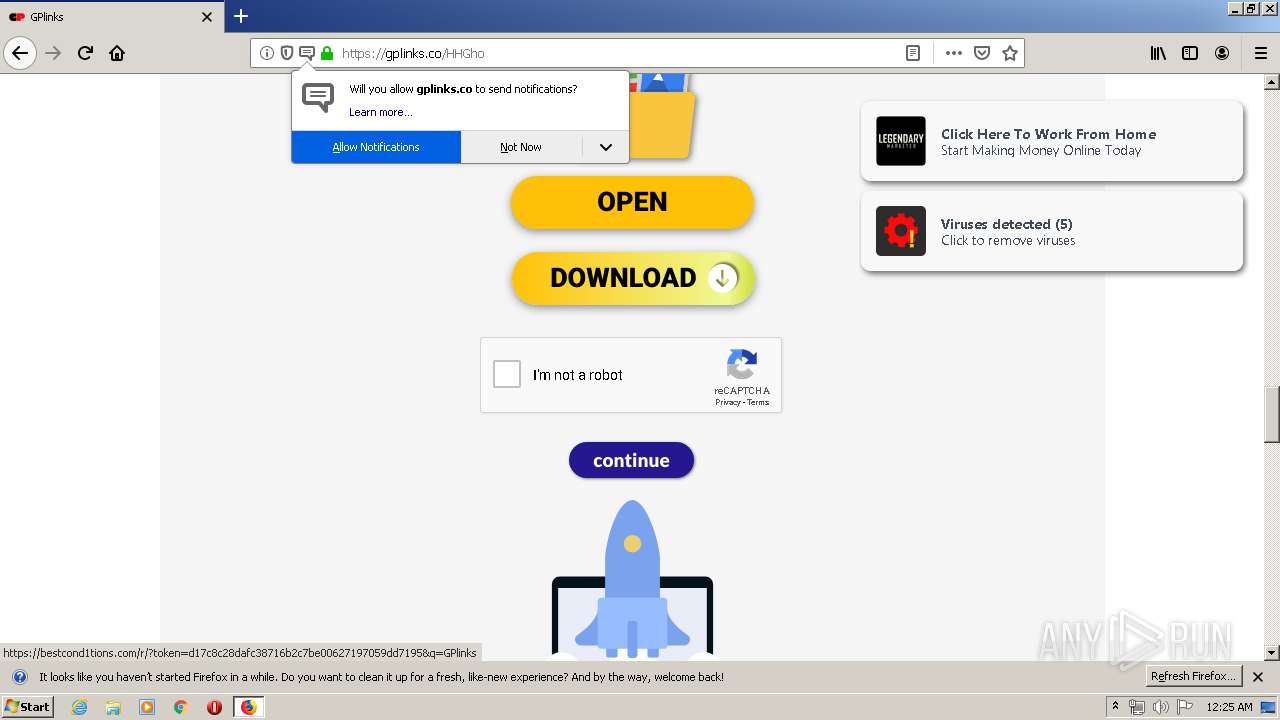
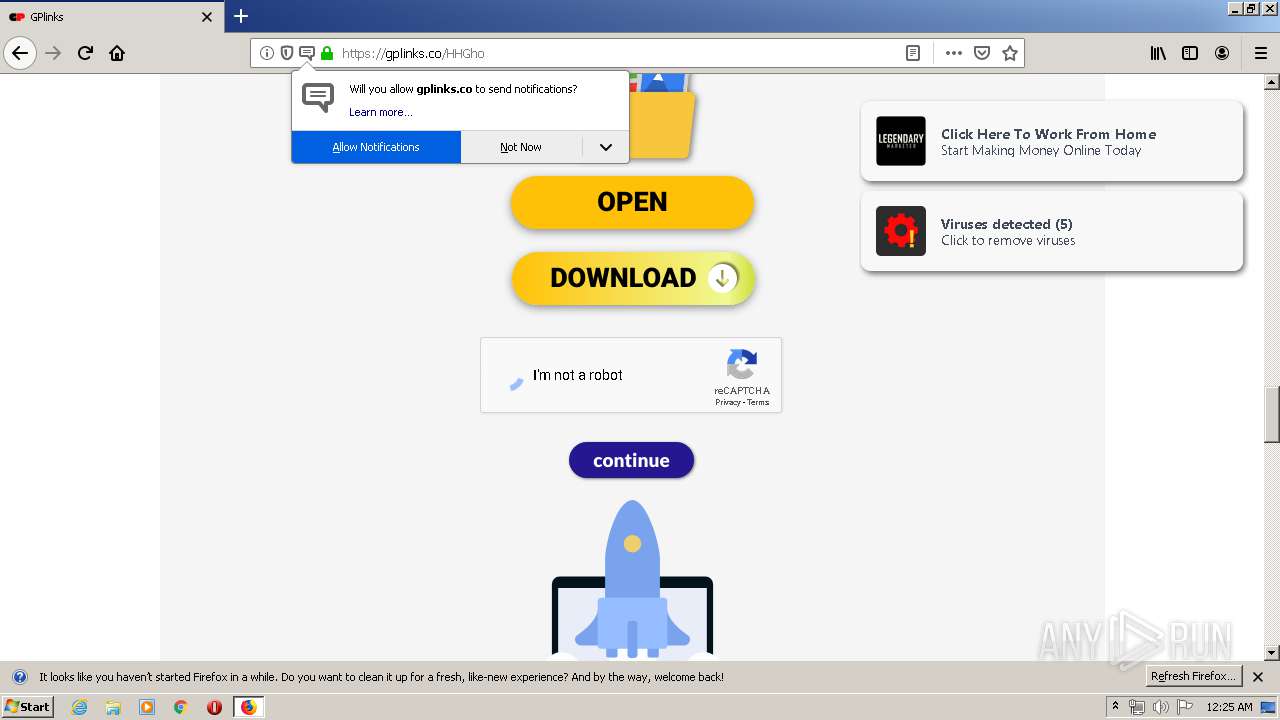
| Title: | Vn-Hax PUBG Mobile Game |
| Description: | YOUR DESCRIPTION HERE |
| Keywords: | YOUR KEYWORDS HERE |
| twitterDomain: | https://www.vnhax.site/ |
| twitterCard: | summary |
| twitterTitle: | - |
| twitterSite: | @username |
| twitterCreator: | @username |
Total processes
60
Monitored processes
17
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 380 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1192 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
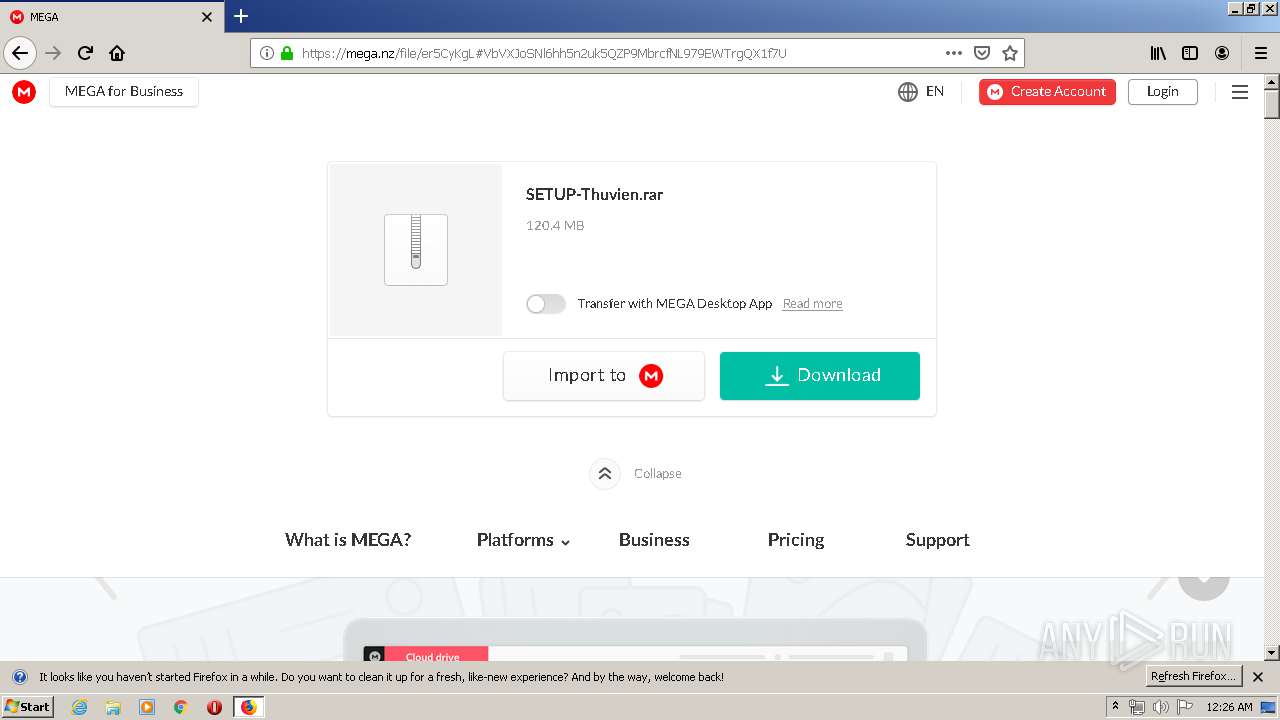
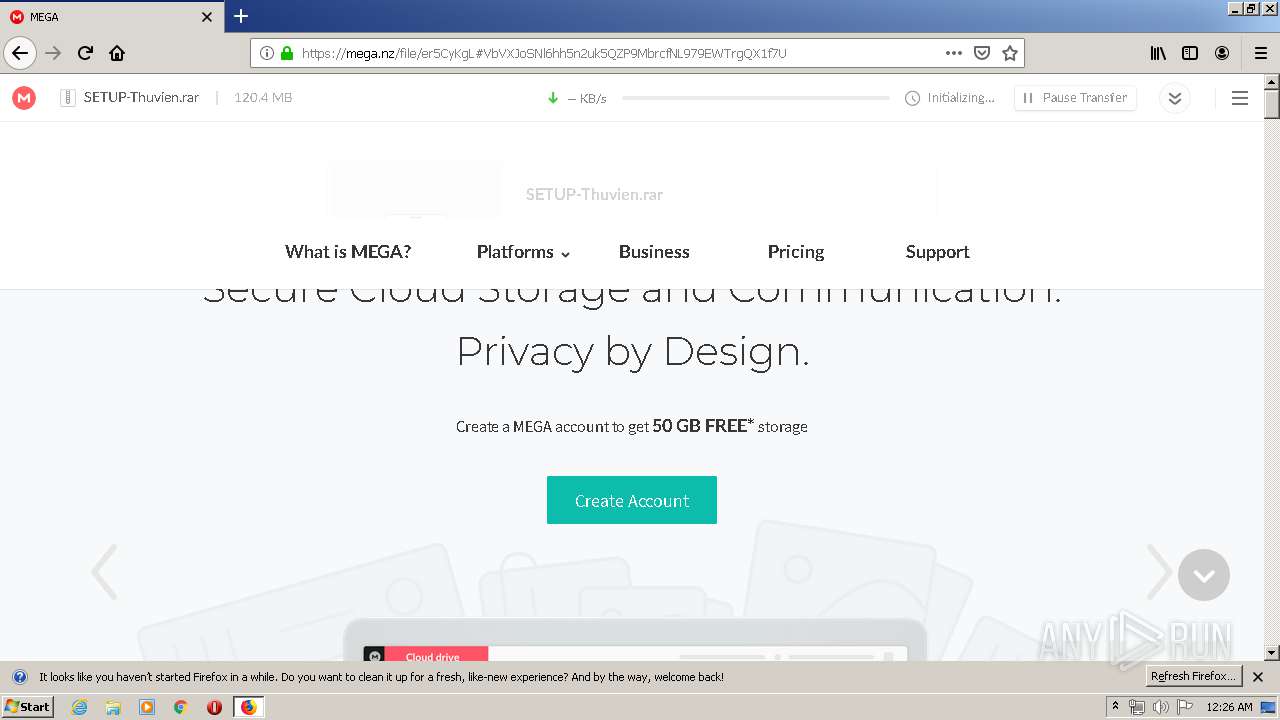
| 1548 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1904.21084\SETUP-Thuvien\CHAYCAINAY.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1904.21084\SETUP-Thuvien\CHAYCAINAY.exe | WinRAR.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: MEDIUM Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 1896 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4008.20246\SETUP-Thuvien\._cache_CHAYCAINAY.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4008.20246\SETUP-Thuvien\._cache_CHAYCAINAY.exe | WinRAR.exe | ||||||||||||
User: admin Company: BOLLOL.COM Integrity Level: MEDIUM Description: BOLLOL.COM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
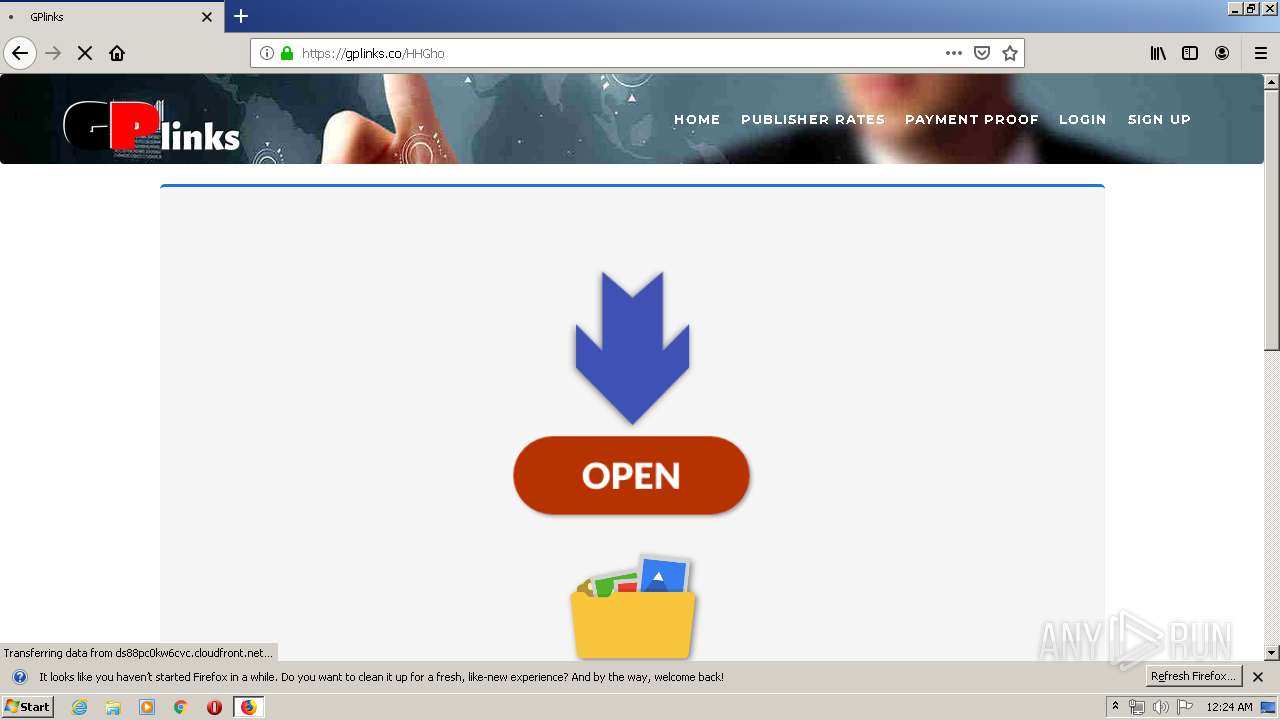
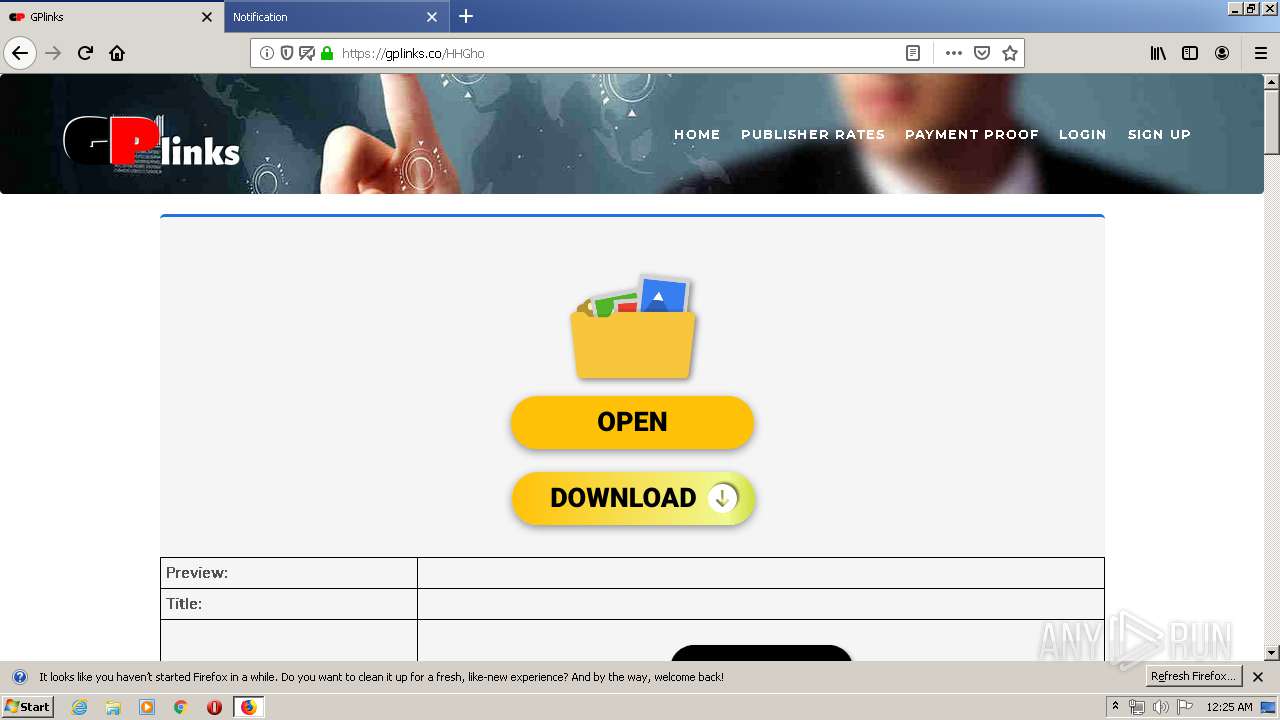
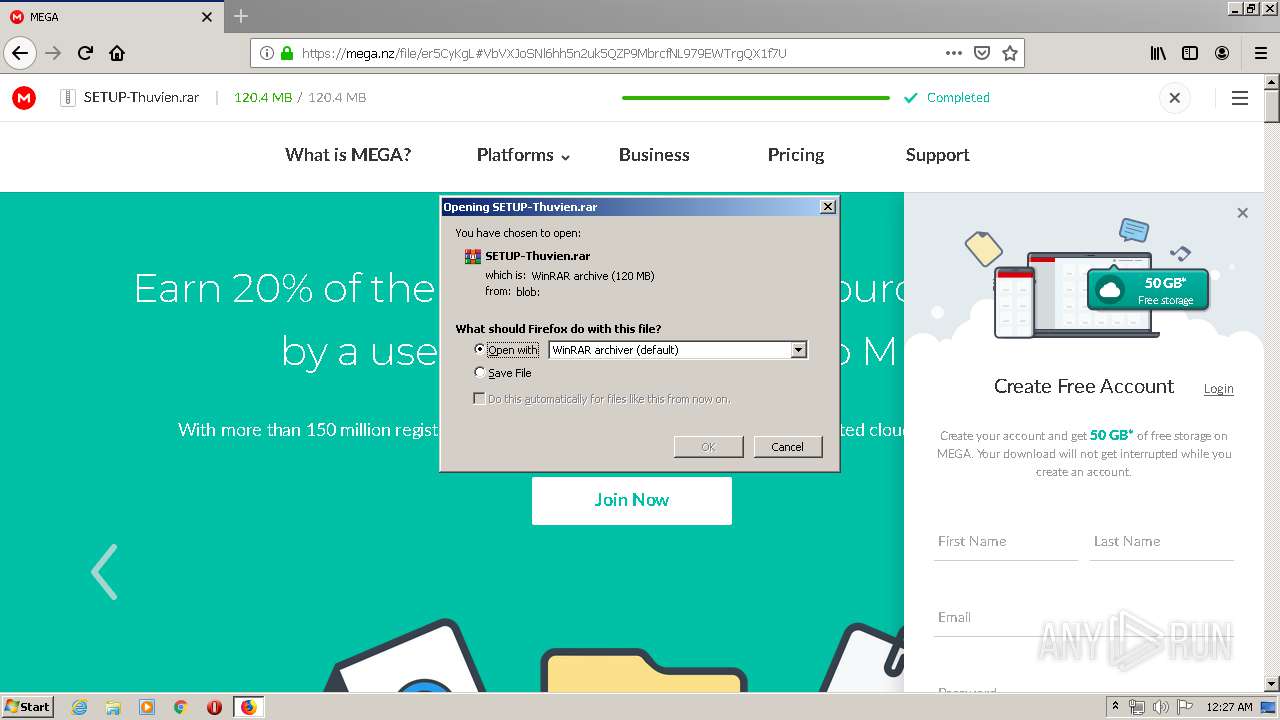
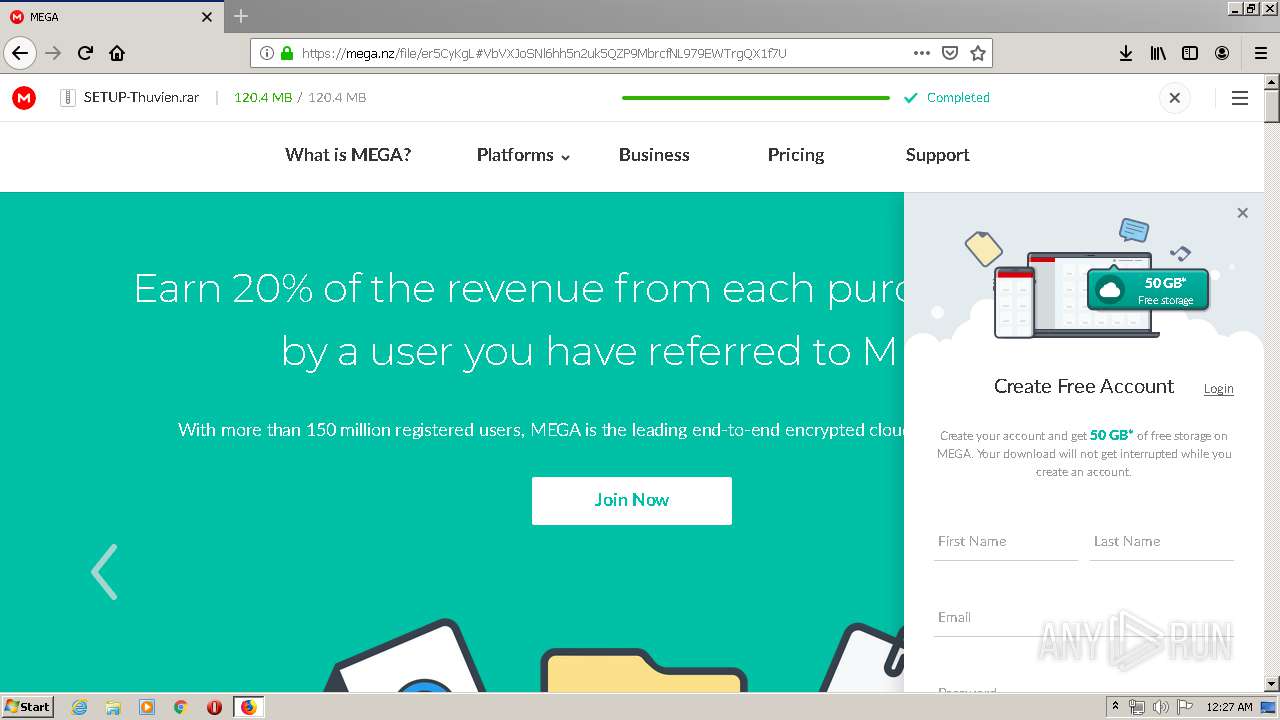
| 1904 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SETUP-Thuvien.rar" | C:\Program Files\WinRAR\WinRAR.exe | firefox.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2716.0.493259387\1219946460" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2716 "\\.\pipe\gecko-crash-server-pipe.2716" 1188 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2716.3.1392187240\2044403809" -childID 1 -isForBrowser -prefsHandle 1700 -prefMapHandle 1672 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2716 "\\.\pipe\gecko-crash-server-pipe.2716" 1688 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2476 | "C:\ProgramData\Synaptics\Synaptics.exe" InjUpdate | C:\ProgramData\Synaptics\Synaptics.exe | CHAYCAINAY.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: HIGH Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1904.21084\SETUP-Thuvien\._cache_CHAYCAINAY.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1904.21084\SETUP-Thuvien\._cache_CHAYCAINAY.exe | CHAYCAINAY.exe | ||||||||||||
User: admin Company: BOLLOL.COM Integrity Level: MEDIUM Description: BOLLOL.COM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
2 904
Read events
2 721
Write events
179
Delete events
4
Modification events
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 973048790 | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30815760 | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
16
Suspicious files
571
Text files
338
Unknown types
284
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1192 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9FB1A45ED5180F41.TMP | — | |
MD5:— | SHA256:— | |||
| 1192 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF331C36C92FF1603B.TMP | — | |
MD5:— | SHA256:— | |||
| 1192 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8CD42A5A7163B533.TMP | — | |
MD5:— | SHA256:— | |||
| 1192 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{65BE88EF-A203-11EA-9EB1-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1192 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF71D61B06E87D1CAA.TMP | — | |
MD5:— | SHA256:— | |||
| 2716 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2716 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2716 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2716 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
91
TCP/UDP connections
291
DNS requests
574
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
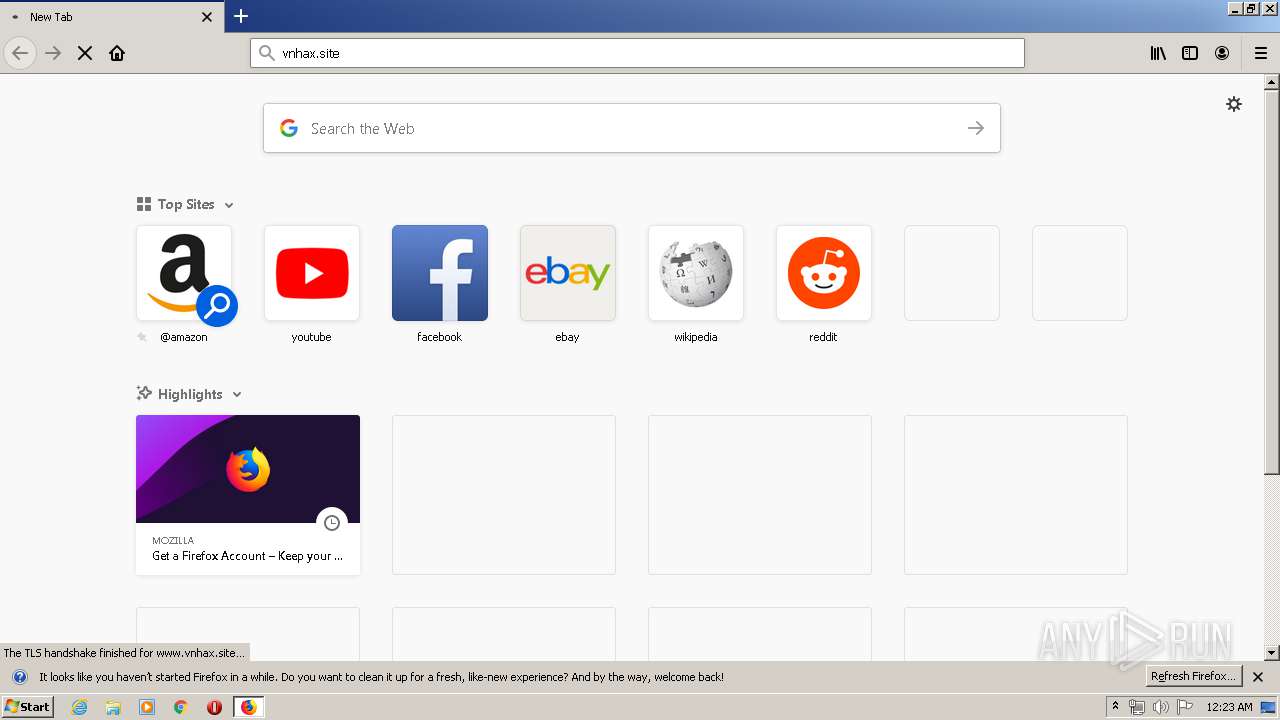
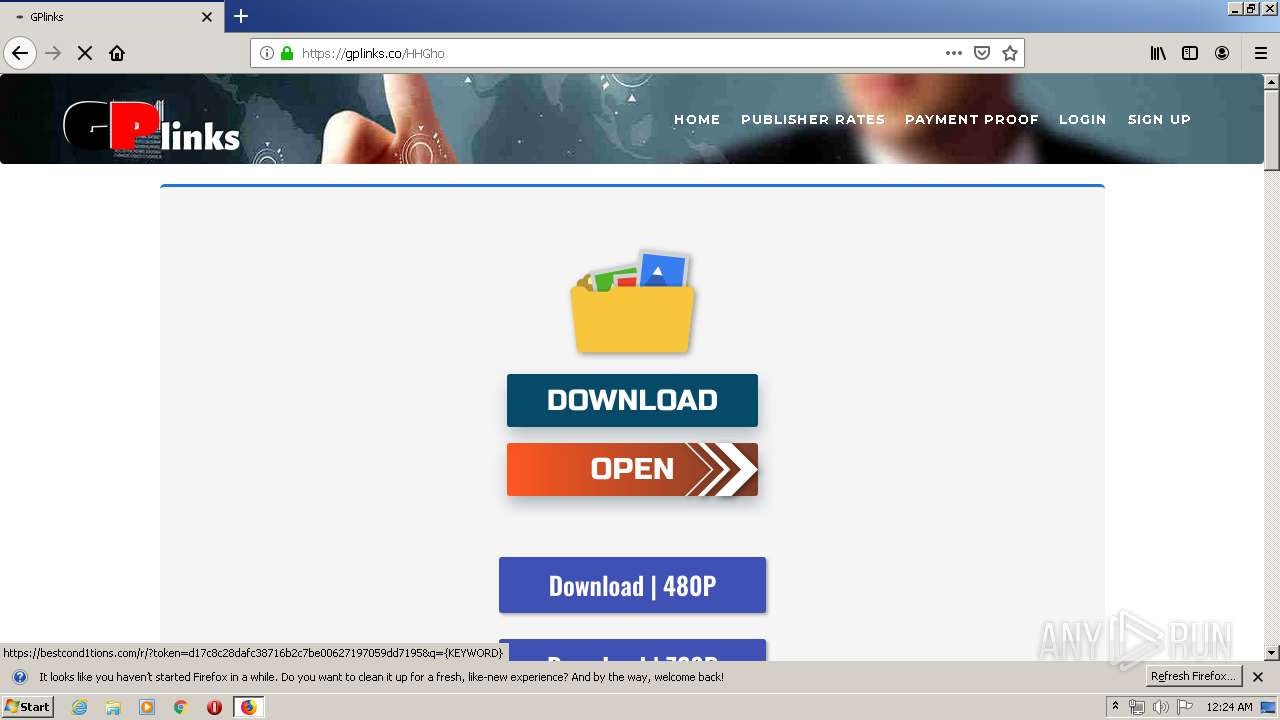
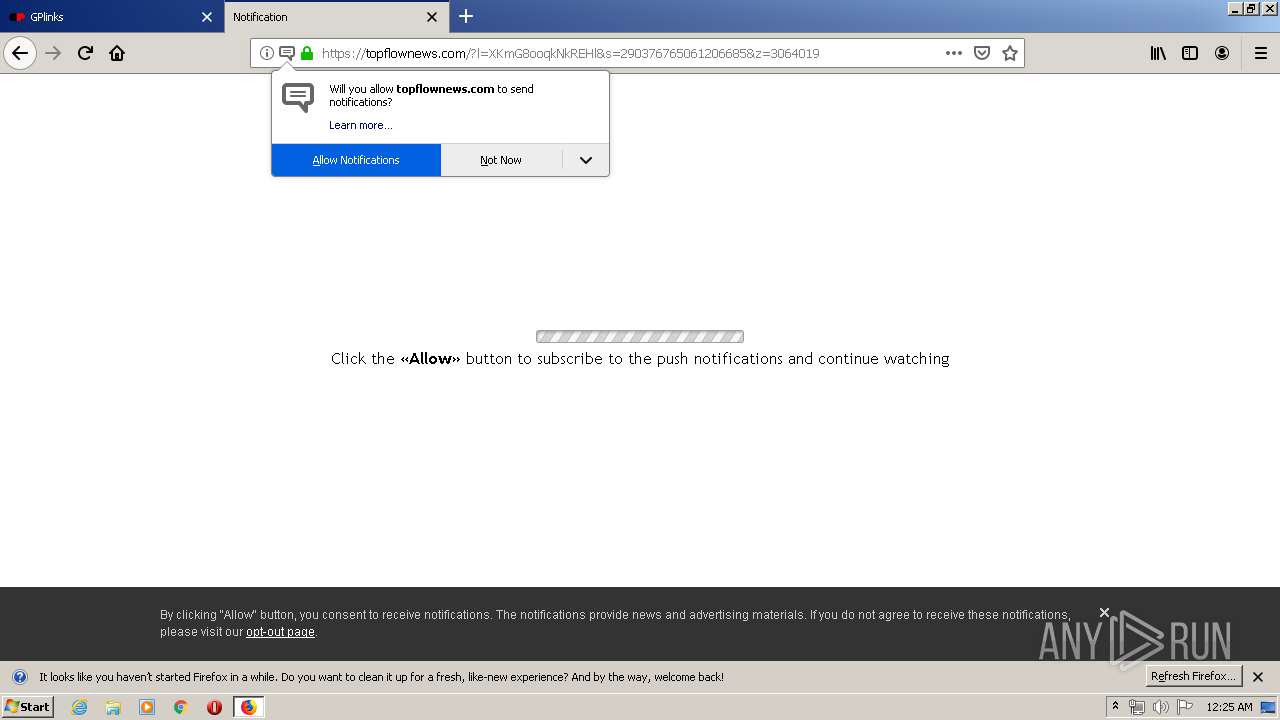
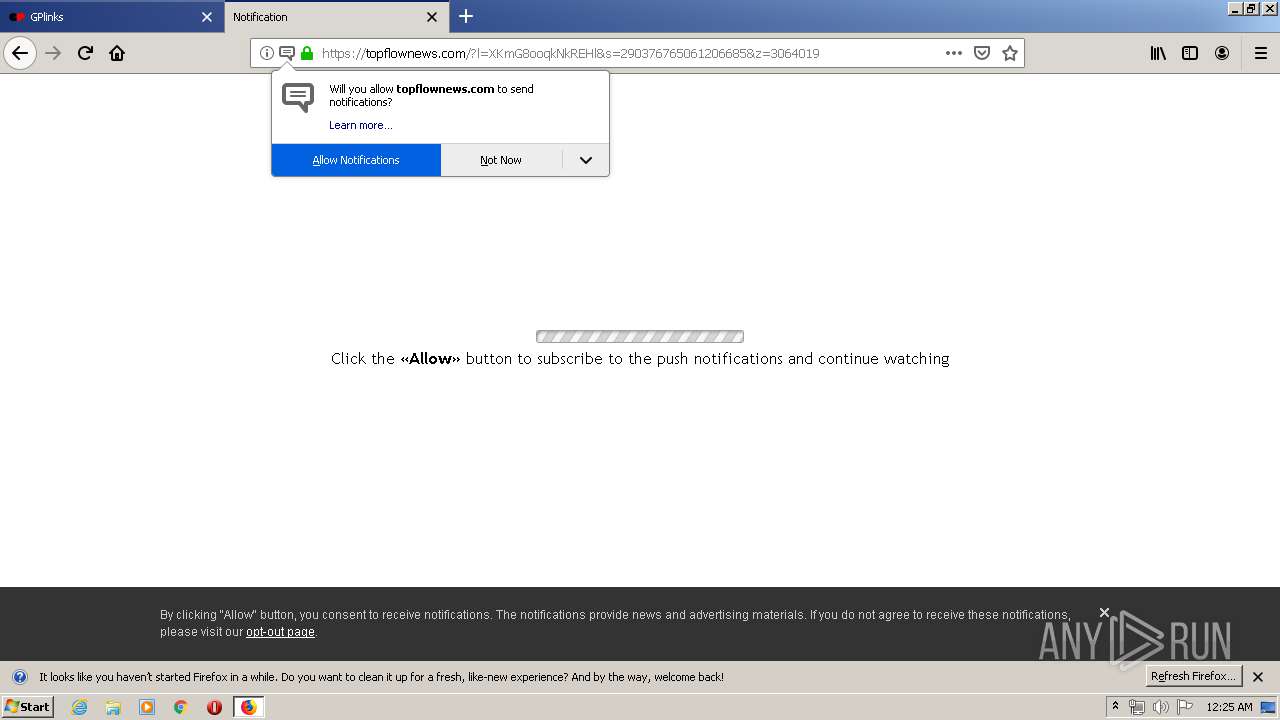
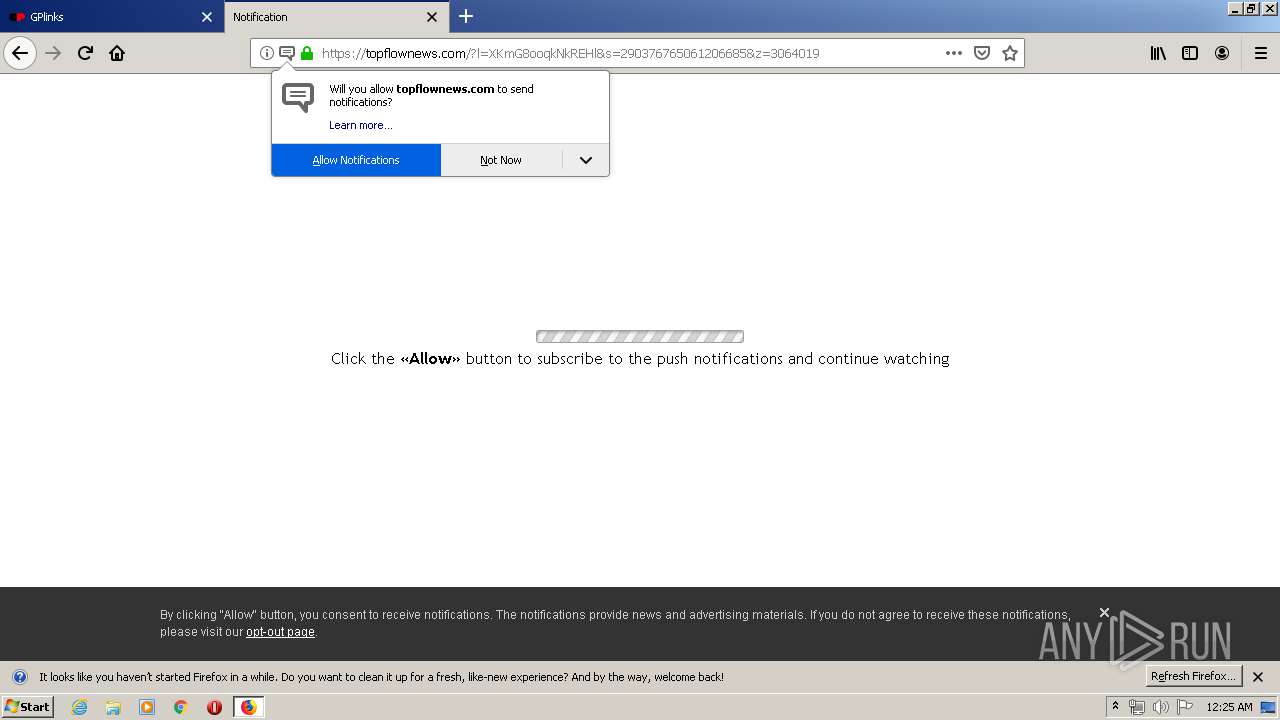
2716 | firefox.exe | GET | 301 | 216.239.36.21:80 | http://vnhax.site/ | US | html | 219 b | malicious |
2716 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2716 | firefox.exe | POST | 200 | 195.138.255.16:80 | http://ocsp.int-x3.letsencrypt.org/ | DE | der | 527 b | whitelisted |
2716 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2716 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2716 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2716 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2716 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/ | US | der | 279 b | whitelisted |
2716 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2716 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 216.58.208.42:139 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2716 | firefox.exe | 34.211.106.52:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2716 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4 | System | 216.58.208.42:445 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2716 | firefox.exe | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
2716 | firefox.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2716 | firefox.exe | 216.239.34.21:80 | vnhax.site | Google Inc. | US | whitelisted |
2716 | firefox.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2716 | firefox.exe | 216.239.36.21:80 | vnhax.site | Google Inc. | US | whitelisted |
2716 | firefox.exe | 2.16.107.40:80 | detectportal.firefox.com | Akamai International B.V. | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fonts.googleapis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
3 ETPRO signatures available at the full report