| File name: | SecuriteInfo.com.Win32.Malware-gen.13144.21016 |
| Full analysis: | https://app.any.run/tasks/2b82a034-240b-4f38-9d59-729adeb0f2be |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 04, 2025, 07:10:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 4641A0BEC2101C82F575862F97BE861C |
| SHA1: | 0DD1EE06CDB7BA9EF2AA1DC44C80F1BC2586D33B |
| SHA256: | FC2AC17498BD7846607110E66426BDAD0AB5302F5C7978DD72C20D99166292E1 |
| SSDEEP: | 49152:jmBLhdzYN/vP5IQ4jzx1lbzqWnPIZ39qg5bpEZxBmcEs3D/8mQoNbVR/n6vfXSj+:jIhdzsX54j3xzPnPSb6sY/VQoJVR/6vB |
MALICIOUS
Actions looks like stealing of personal data
- Jordan.com (PID: 7876)
AutoIt loader has been detected (YARA)
- Jordan.com (PID: 7876)
LUMMA mutex has been found
- Jordan.com (PID: 7876)
Steals credentials from Web Browsers
- Jordan.com (PID: 7876)
SUSPICIOUS
Starts CMD.EXE for commands execution
- SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe (PID: 7344)
- cmd.exe (PID: 7384)
Get information on the list of running processes
- cmd.exe (PID: 7384)
Application launched itself
- cmd.exe (PID: 7384)
Reads security settings of Internet Explorer
- SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe (PID: 7344)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7384)
There is functionality for taking screenshot (YARA)
- Jordan.com (PID: 7876)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Jordan.com (PID: 7876)
Searches for installed software
- Jordan.com (PID: 7876)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7384)
Starts application with an unusual extension
- cmd.exe (PID: 7384)
The executable file from the user directory is run by the CMD process
- Jordan.com (PID: 7876)
Executing commands from a ".bat" file
- SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe (PID: 7344)
INFO
Process checks computer location settings
- SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe (PID: 7344)
Checks supported languages
- SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe (PID: 7344)
- extrac32.exe (PID: 7760)
- Jordan.com (PID: 7876)
Creates a new folder
- cmd.exe (PID: 7700)
Reads the computer name
- SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe (PID: 7344)
- extrac32.exe (PID: 7760)
- Jordan.com (PID: 7876)
Create files in a temporary directory
- SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe (PID: 7344)
- extrac32.exe (PID: 7760)
Reads the software policy settings
- Jordan.com (PID: 7876)
- slui.exe (PID: 7676)
Attempting to use instant messaging service
- Jordan.com (PID: 7876)
Reads mouse settings
- Jordan.com (PID: 7876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 12:19:06+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 25600 |
| InitializedDataSize: | 4094976 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x33ff |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
17
Malicious processes
3
Suspicious processes
0
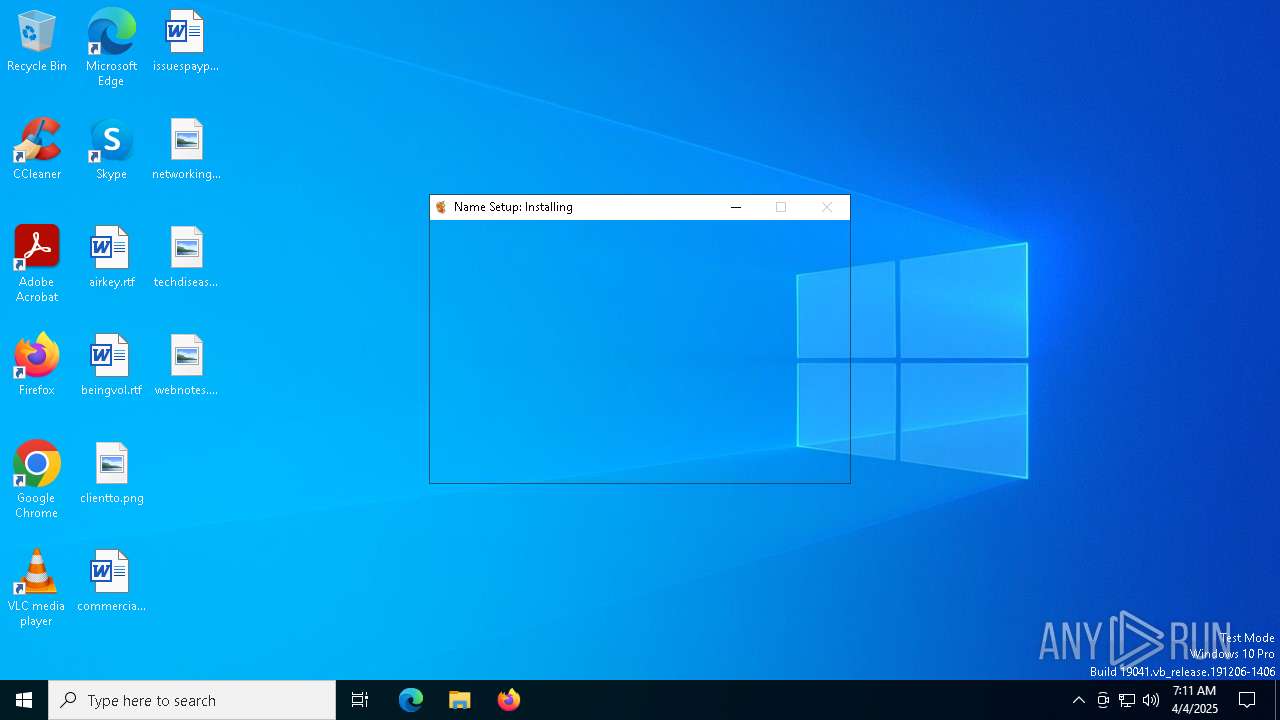
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4488 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7344 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7384 | "C:\WINDOWS\System32\cmd.exe" /c copy Cattle.psd Cattle.psd.bat & Cattle.psd.bat | C:\Windows\SysWOW64\cmd.exe | — | SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7392 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7468 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7476 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7584 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7592 | findstr "SophosHealth bdservicehost AvastUI AVGUI nsWscSvc ekrn" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7640 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7676 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 644
Read events
1 644
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
19
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7344 | SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe | C:\Users\admin\AppData\Local\Temp\Shoes.psd | binary | |
MD5:96C1576EA852A5E67ED19CD7AA36A96F | SHA256:7FD3F98ED83C81F1CED2C52E89B7A787FFECA8C97984BF3CCD456DCE9A7C281F | |||
| 7344 | SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe | C:\Users\admin\AppData\Local\Temp\Feel.psd | binary | |
MD5:B379695029DF2C12418DBD3669AD764A | SHA256:3EA1526911EE558BF646CFFE6B80C1223A95C893FBFBFD57B3A525D6F776192A | |||
| 7760 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Within | binary | |
MD5:ECDD69755748E3ECD359F1F1E549885D | SHA256:7DA2901F818982CD6EB29FC552D1FA3F80E679FDE104DE89A7CC1F8AEA76B1B8 | |||
| 7344 | SecuriteInfo.com.Win32.Malware-gen.13144.21016.exe | C:\Users\admin\AppData\Local\Temp\Bruce.psd | binary | |
MD5:BD138E8AADE8C0664B6306E35BEC9D18 | SHA256:D53E9ED9E94F2049778031405A7E9196CA6653F07CB3F96FB8DDDF6E0E1EC8B5 | |||
| 7760 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Illustrations | binary | |
MD5:D4064B252B0764839D6933922F3ABF12 | SHA256:74BFA8B3CEE5B0CBEF0577DA9E6546F44EB80C7359080FA15F20CBCB3175E0DF | |||
| 7760 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Pushed | binary | |
MD5:C5C384CE07970E9FFA5CD5961D08BDC7 | SHA256:469845E7267AE3538A946B9A3CE559D13DB80ED83EAA88D1585837E2AABEB08B | |||
| 7760 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Bg | binary | |
MD5:2752930460D0D3B746F2B5E2A45D1DA6 | SHA256:810B75D9CF6A706FC4FCBE84D921E4D6B85A9F3D1373E2F46992D113269F5DE7 | |||
| 7760 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Batteries | binary | |
MD5:0BF8C0D3A3AC566F5F7F7EBAAF007648 | SHA256:463AFCEAE3987A35621BCF00BF889C242495D9B5FBAA97858E311BA76158AEA0 | |||
| 7760 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Boss | binary | |
MD5:DFCE5DA157853581AD9C743EF4E1B987 | SHA256:1D4B8688E9840AC342278F05A956245A8EABA9208A6F21B72D4D13A70F0397DB | |||
| 7760 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Boards | binary | |
MD5:B0CA263D0796DB30DCFC455DE7ABA28B | SHA256:1E79A92A8E1337221A5E858064E555033DFD7FBE570AA4F4175E37D32A25C728 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
25
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 20.198.162.78:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7408 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7408 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
YrOjuzxSQpdrqVJKAQhkZpRwO.YrOjuzxSQpdrqVJKAQhkZpRwO |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7876 | Jordan.com | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |