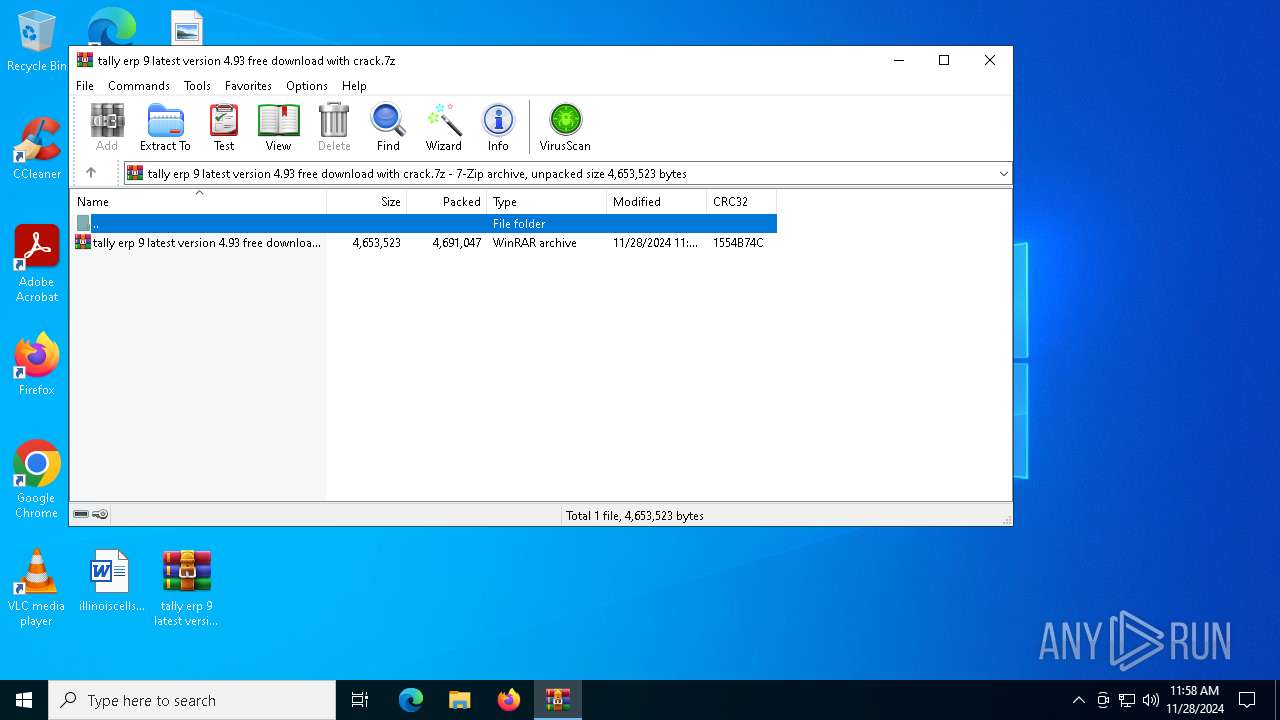
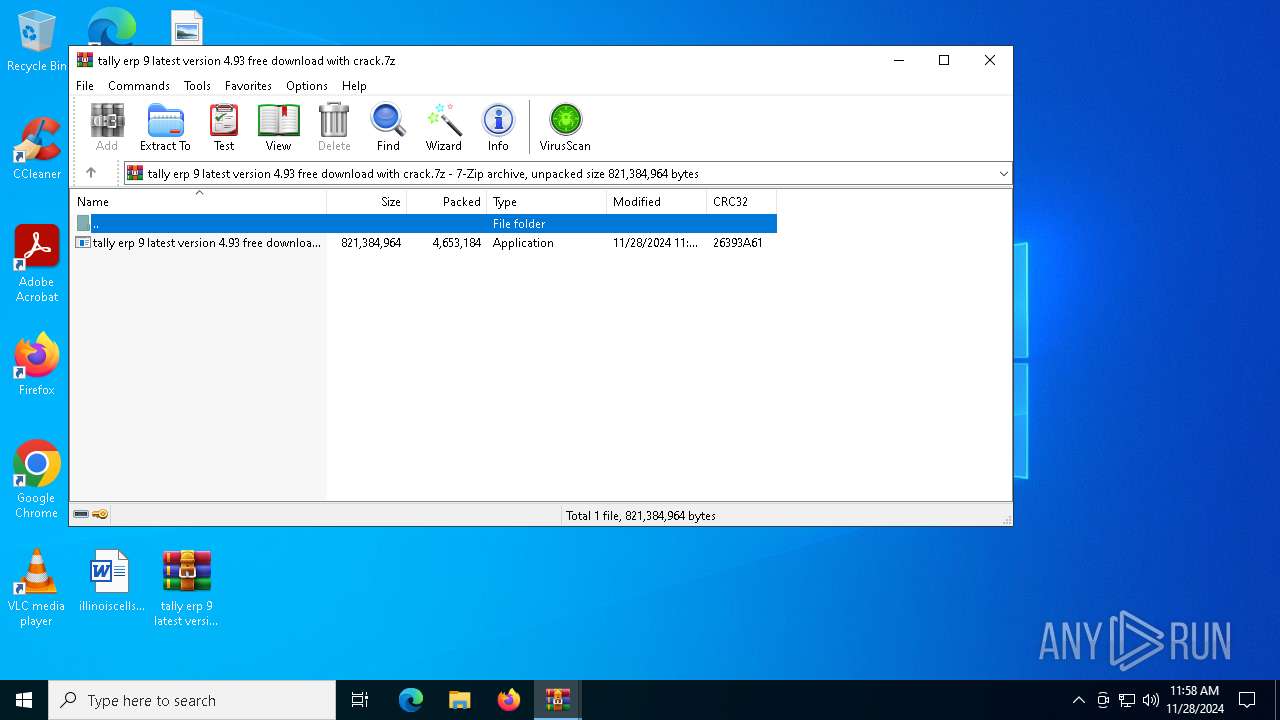
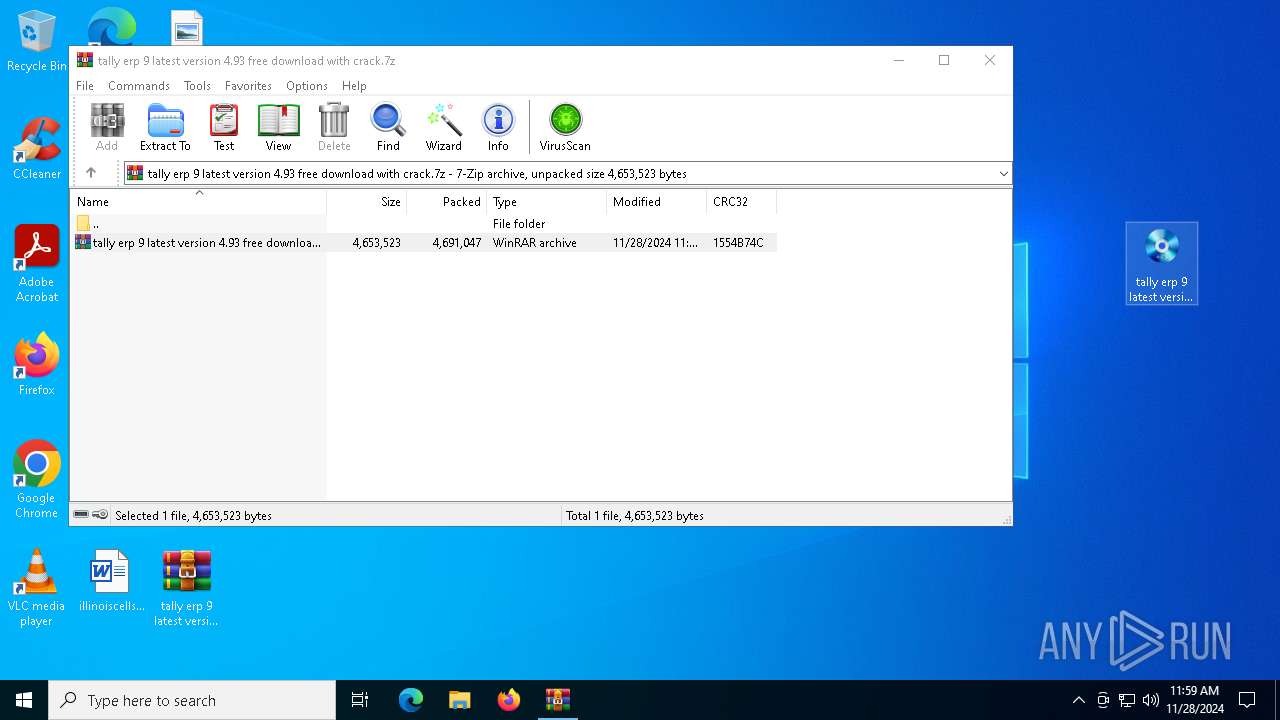
| File name: | tally erp 9 latest version 4.93 free download with crack.7z |
| Full analysis: | https://app.any.run/tasks/dd16ac53-7833-45fe-a2c7-e3a1108211ba |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | November 28, 2024, 11:58:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 89096B15BDC342F0E452B4B897DC7A73 |
| SHA1: | 43D62C8920487D6598225914D0006357E7661056 |
| SHA256: | FC185DC2D3179D8BAFABDE7390DABF20B5ECE87CAB0E744AA2E057B17A57AD84 |
| SSDEEP: | 98304:1RHQGdWk3X4UsMENwCcba5Sw0aBU7zc2GOuXazJYBARNn6dgDB6Jqu4OdjkZH/xN:rVb9K7EPZrn |
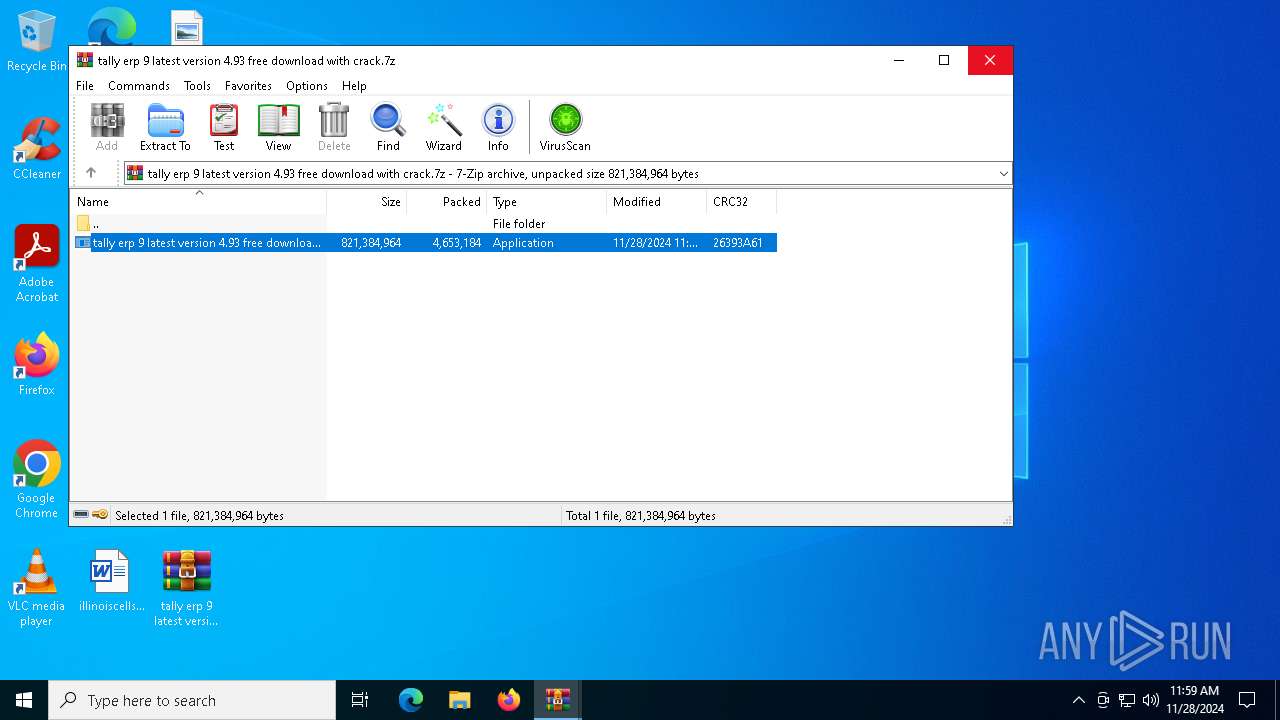
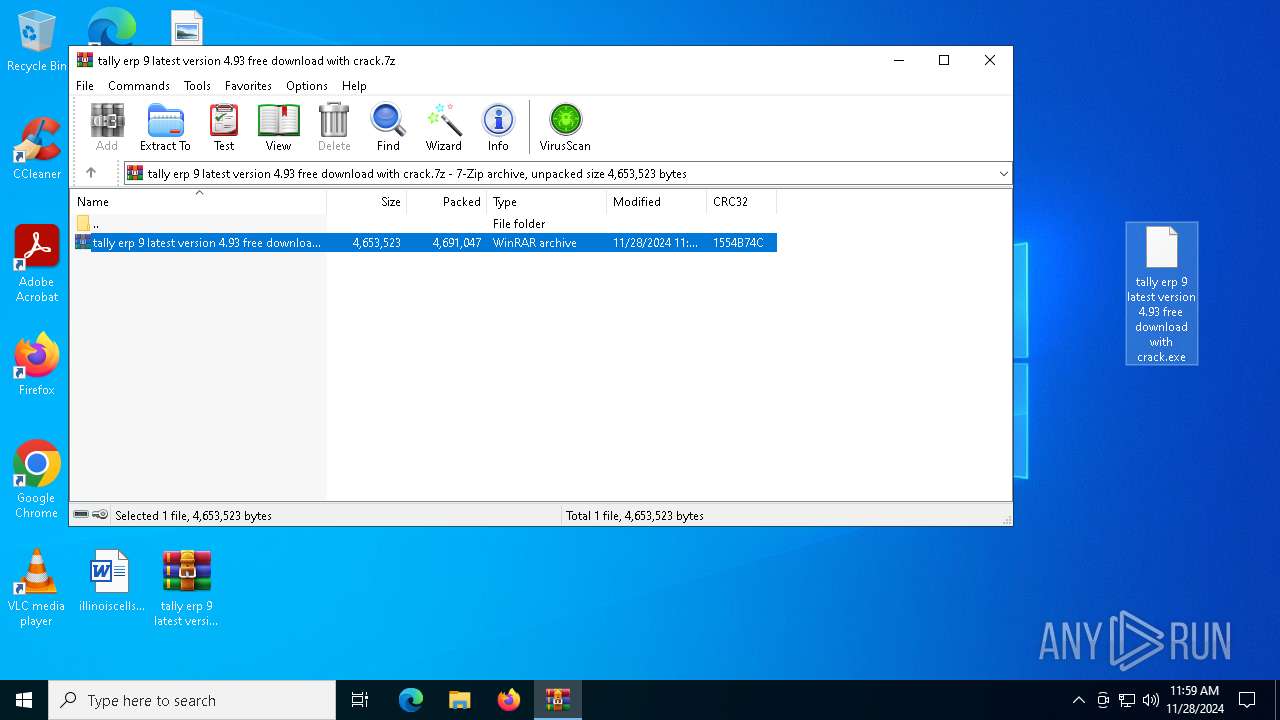
MALICIOUS
LUMMA has been detected (SURICATA)
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
Changes powershell execution policy (Bypass)
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
LUMMA has been detected (YARA)
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
Bypass execution policy to execute commands
- powershell.exe (PID: 4540)
- powershell.exe (PID: 3224)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6284)
Generic archive extractor
- WinRAR.exe (PID: 6284)
Application launched itself
- WinRAR.exe (PID: 6284)
The process executes Powershell scripts
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
Starts POWERSHELL.EXE for commands execution
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4540)
INFO
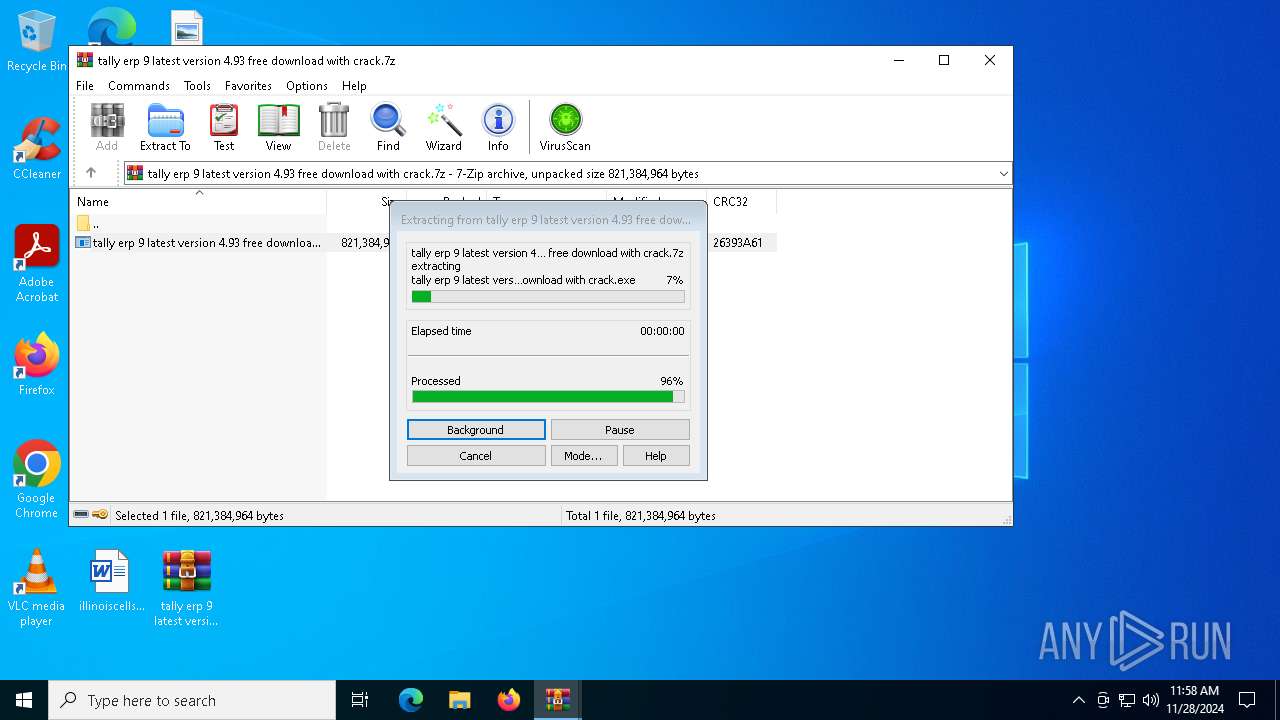
Manual execution by a user
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
The process uses the downloaded file
- WinRAR.exe (PID: 6740)
- WinRAR.exe (PID: 6284)
Reads the software policy settings
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3224)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4540)
- powershell.exe (PID: 3224)
Reads the computer name
- tally erp 9 latest version 4.93 free download with crack.exe (PID: 6980)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2024:11:28 11:57:31+00:00 |
| ArchivedFileName: | tally erp 9 latest version 4.93 free download with crack.7z |
Total processes
139
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1580 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3224 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\OODVRQB6548WE7SLHWF6H8J2HSK.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | tally erp 9 latest version 4.93 free download with crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\TFUZ3VBI6LJY5HSKMP9XVOY.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | tally erp 9 latest version 4.93 free download with crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
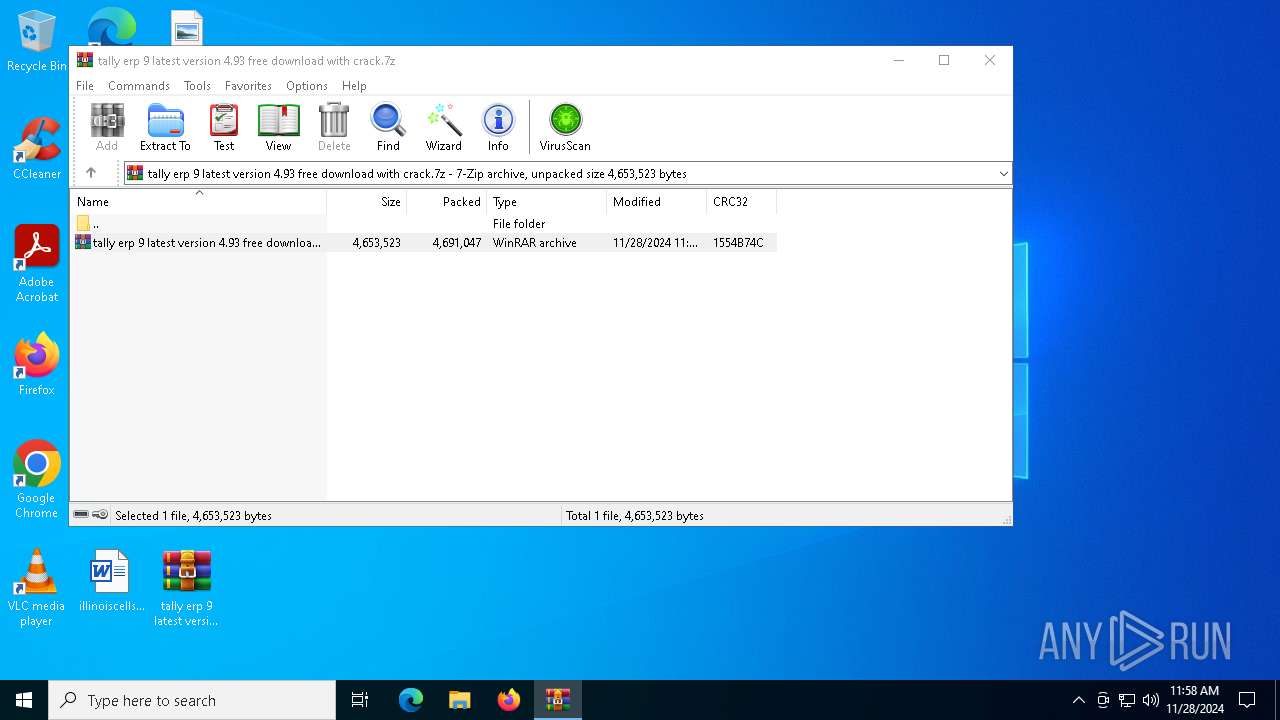
| 6284 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\tally erp 9 latest version 4.93 free download with crack.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
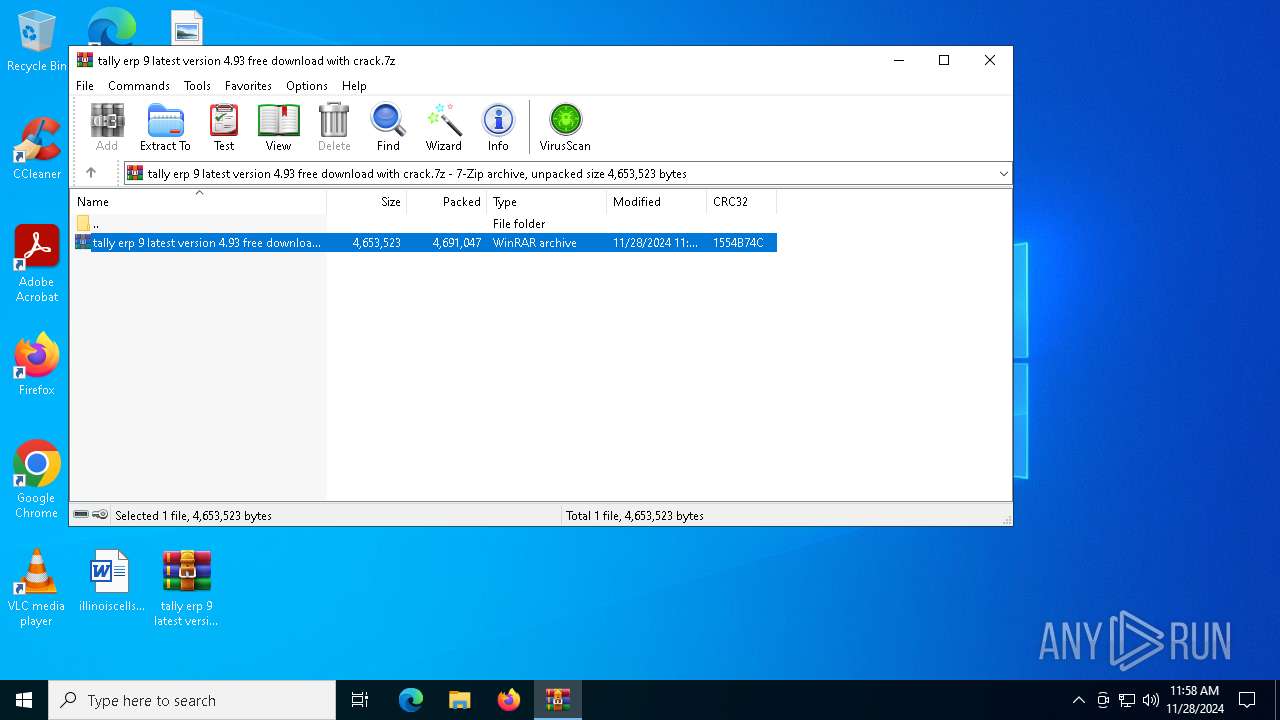
| 6740 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa6284.43522\tally erp 9 latest version 4.93 free download with crack.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6980 | "C:\Users\admin\Desktop\tally erp 9 latest version 4.93 free download with crack.exe" | C:\Users\admin\Desktop\tally erp 9 latest version 4.93 free download with crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6992 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tally erp 9 latest version 4.93 free download with crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 471
Read events
13 420
Write events
51
Delete events
0
Modification events
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\tally erp 9 latest version 4.93 free download with crack.7z | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
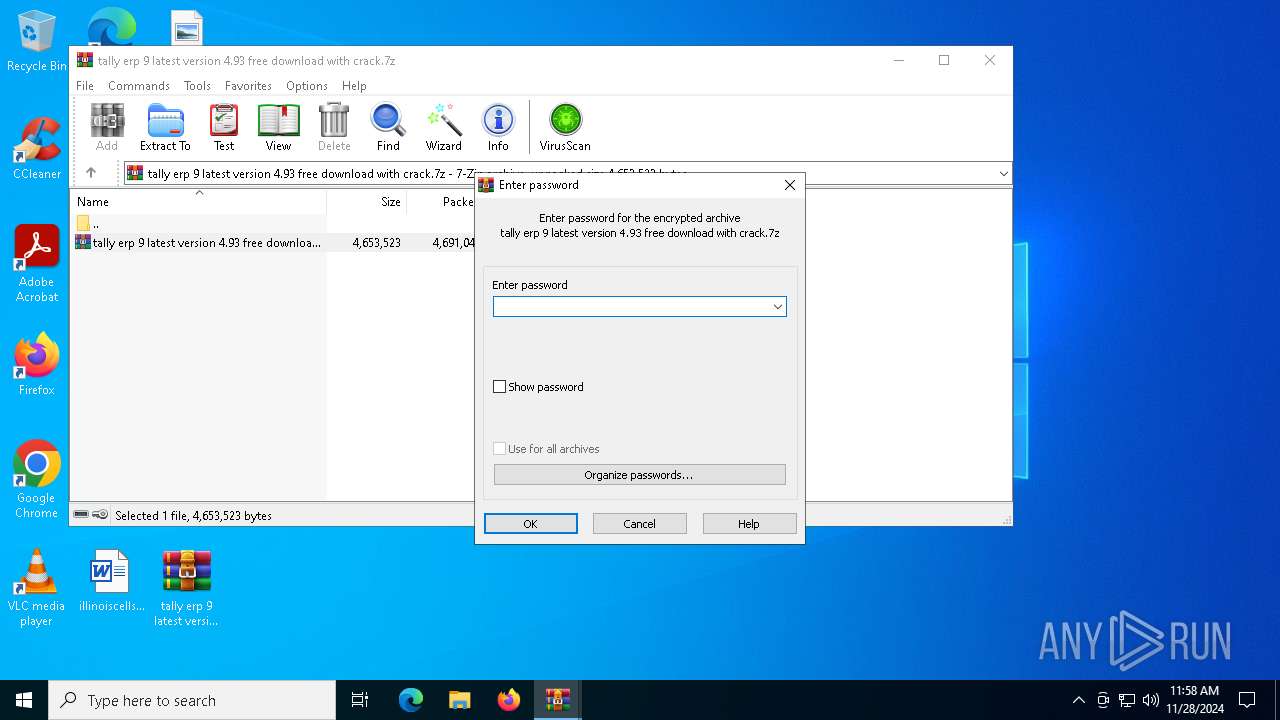
| (PID) Process: | (6740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
0
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6284.43522\tally erp 9 latest version 4.93 free download with crack.7z | — | |
MD5:— | SHA256:— | |||
| 6740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6740.44356\tally erp 9 latest version 4.93 free download with crack.exe | — | |
MD5:— | SHA256:— | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pxktli21.5wp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4540 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:44DC9F5E47AFF9959B8990E860DF407B | SHA256:8F221777ED70D45C115C2467DEAF7048298697A519B4B6F16BC0ABC114C66299 | |||
| 6980 | tally erp 9 latest version 4.93 free download with crack.exe | C:\Users\admin\AppData\Local\Temp\OODVRQB6548WE7SLHWF6H8J2HSK.ps1 | text | |
MD5:909DABB4B6591DDCBE2DF0395650DCCA | SHA256:2A29C9904D1860EA3177DA7553C8B1BF1944566E5BC1E71340D9E0FF079F0BD3 | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hkllmekw.fko.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sqm5zg5s.myz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4540 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iwypimte.5aq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zem0d4q1.rnl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4540 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ops1ucuw.o3k.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3692 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
876 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3692 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1688 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
lumhiddenforest.shop |
| unknown |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6980 | tally erp 9 latest version 4.93 free download with crack.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |