| File name: | fb83b15bc4a45c9ee20ed67c6a7aba8cd0a9132b2300a44b3fefed90d02a273f |
| Full analysis: | https://app.any.run/tasks/99f0043e-a1ab-4398-b953-3c0b5896da21 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | August 13, 2019, 18:31:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
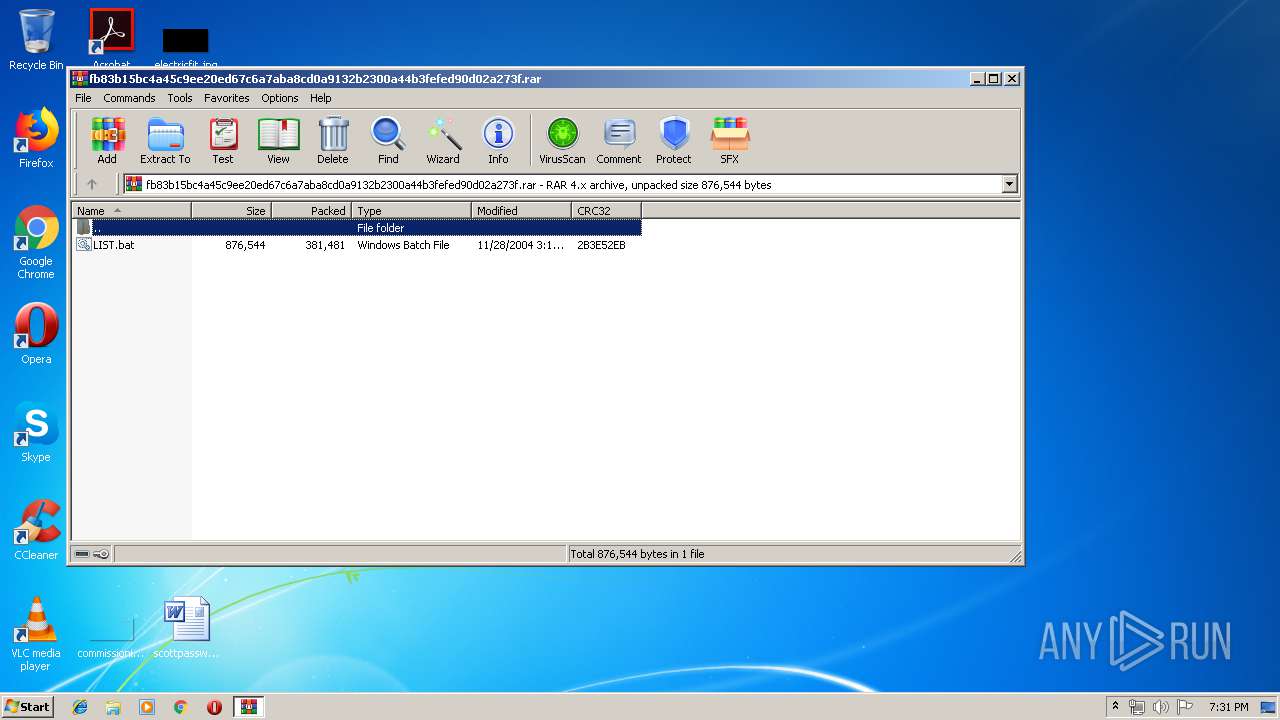
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 4FEDE09579AA59F06755AE67E07DEC4C |
| SHA1: | F36D5B8F90EB2E4B3C4B1EAB0B0285F38F210D57 |
| SHA256: | FB83B15BC4A45C9EE20ED67C6A7ABA8CD0A9132B2300A44B3FEFED90D02A273F |
| SSDEEP: | 6144:vMf1Jg83zp+qwQKsbuIvS9am8HXCP/CfJu8eRifs+JwFURuiKHOIfKxs5:vMf1S839+9QBbuIa6HXpfU8ewkGwFRio |
MALICIOUS
Application was dropped or rewritten from another process
- LIST.bat (PID: 300)
- LIST.bat (PID: 2604)
AGENTTESLA was detected
- LIST.bat (PID: 2604)
Actions looks like stealing of personal data
- LIST.bat (PID: 2604)
SUSPICIOUS
Application launched itself
- LIST.bat (PID: 300)
Starts application with an unusual extension
- LIST.bat (PID: 300)
Checks for external IP
- LIST.bat (PID: 2604)
Reads Internet Cache Settings
- LIST.bat (PID: 2604)
Connects to SMTP port
- LIST.bat (PID: 2604)
INFO
Manual execution by user
- LIST.bat (PID: 300)
Application was crashed
- LIST.bat (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 381512 |
|---|---|
| UncompressedSize: | 876544 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2004:11:28 03:11:28 |
| PackingMethod: | Normal |
| ArchivedFileName: | LIST.bat |
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\Desktop\LIST.bat" | C:\Users\admin\Desktop\LIST.bat | — | explorer.exe | |||||||||||
User: admin Company: GiullaresPerformer3 Integrity Level: MEDIUM Exit code: 0 Version: 3.06.0006 Modules
| |||||||||||||||
| 2248 | dw20.exe -x -s 1400 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | LIST.bat | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2604 | "C:\Users\admin\Desktop\LIST.bat" | C:\Users\admin\Desktop\LIST.bat | LIST.bat | ||||||||||||
User: admin Company: GiullaresPerformer3 Integrity Level: MEDIUM Exit code: 3221225477 Version: 3.06.0006 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\fb83b15bc4a45c9ee20ed67c6a7aba8cd0a9132b2300a44b3fefed90d02a273f.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
506
Read events
484
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\fb83b15bc4a45c9ee20ed67c6a7aba8cd0a9132b2300a44b3fefed90d02a273f.rar | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (2604) LIST.bat | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LIST_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
1
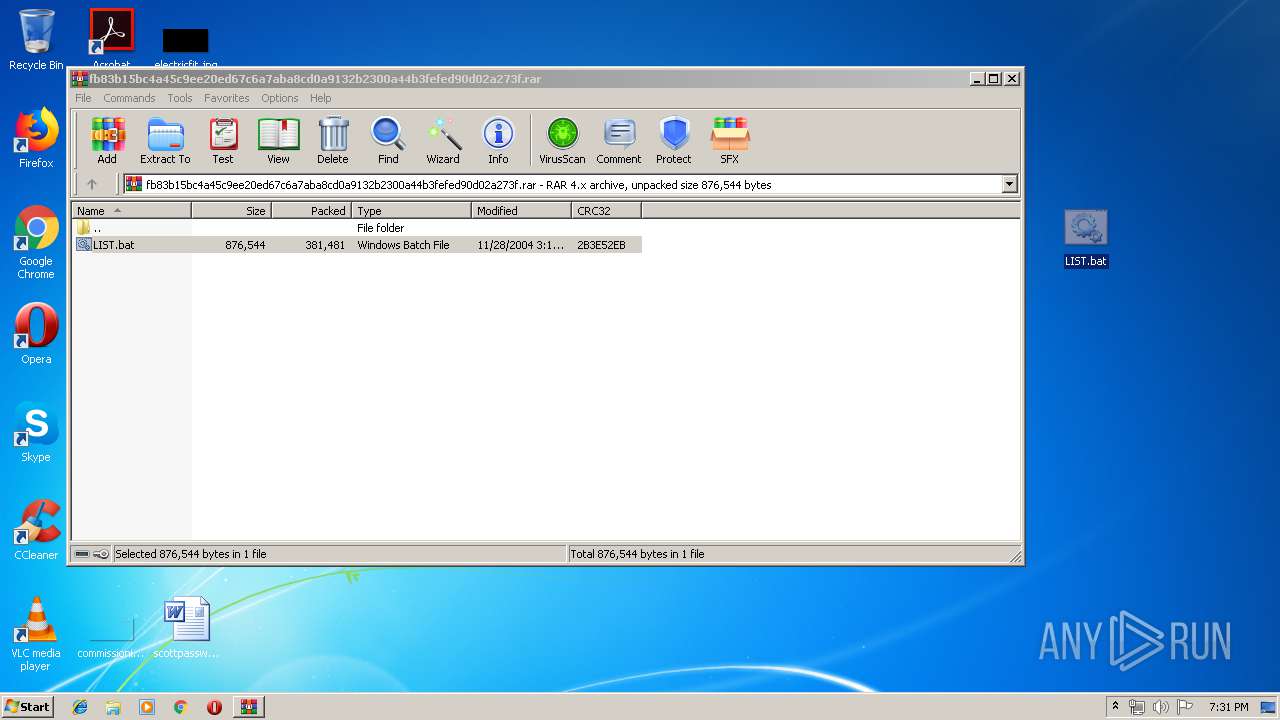
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2612.11707\LIST.bat | — | |
MD5:— | SHA256:— | |||
| 2604 | LIST.bat | C:\Users\admin\AppData\Local\Temp\637013215447355000_4bdef398-5941-4125-a1f9-717c831189ef.db | sqlite | |
MD5:— | SHA256:— | |||
| 2248 | dw20.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_LIST.bat_ffa376179793d5fa5e4c1029322bc84561e6c9e_08f04ecb\Report.wer | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2604 | LIST.bat | GET | 200 | 52.44.169.135:80 | http://checkip.amazonaws.com/ | US | text | 14 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2604 | LIST.bat | 208.91.199.224:587 | us2.smtp.mailhostbox.com | PDR | US | shared |
2604 | LIST.bat | 52.44.169.135:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
us2.smtp.mailhostbox.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2604 | LIST.bat | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2604 | LIST.bat | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla variant outbound SMTP connection |
2604 | LIST.bat | A Network Trojan was detected | MALWARE [PTsecurity] Trojan-Spy.Keylogger.AgentTesla Exfiltration by SMTP |
3 ETPRO signatures available at the full report